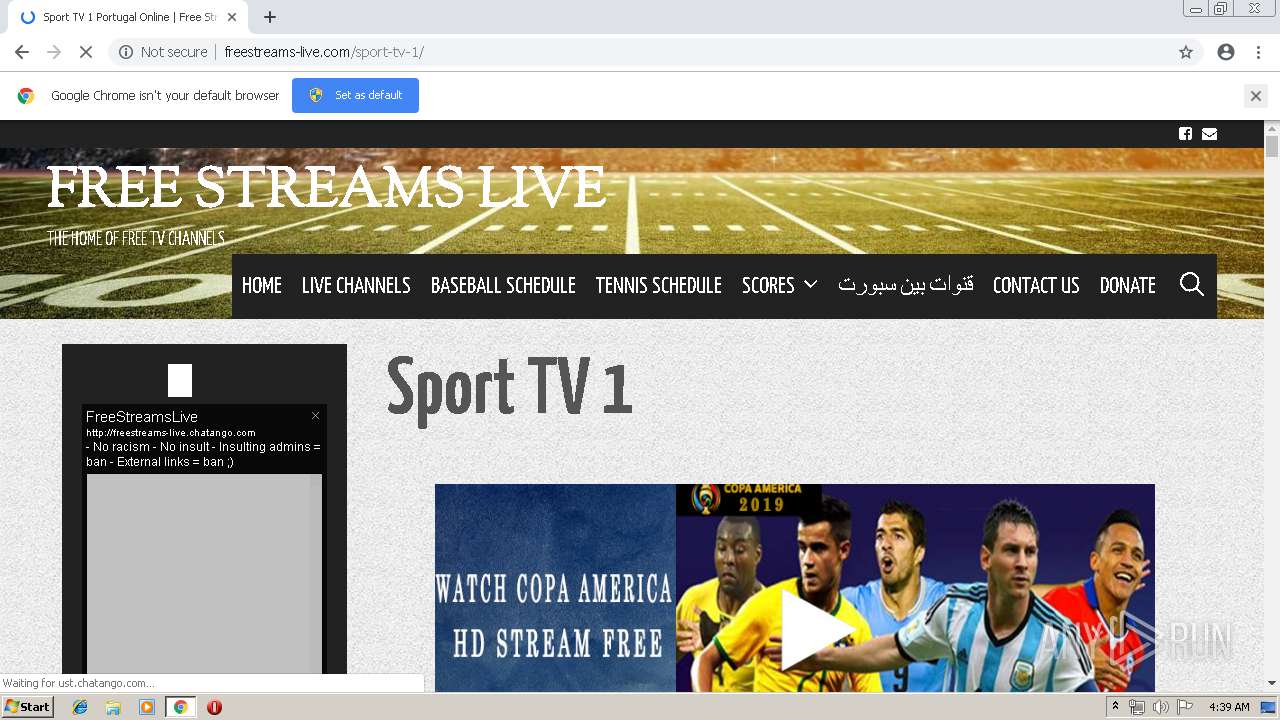
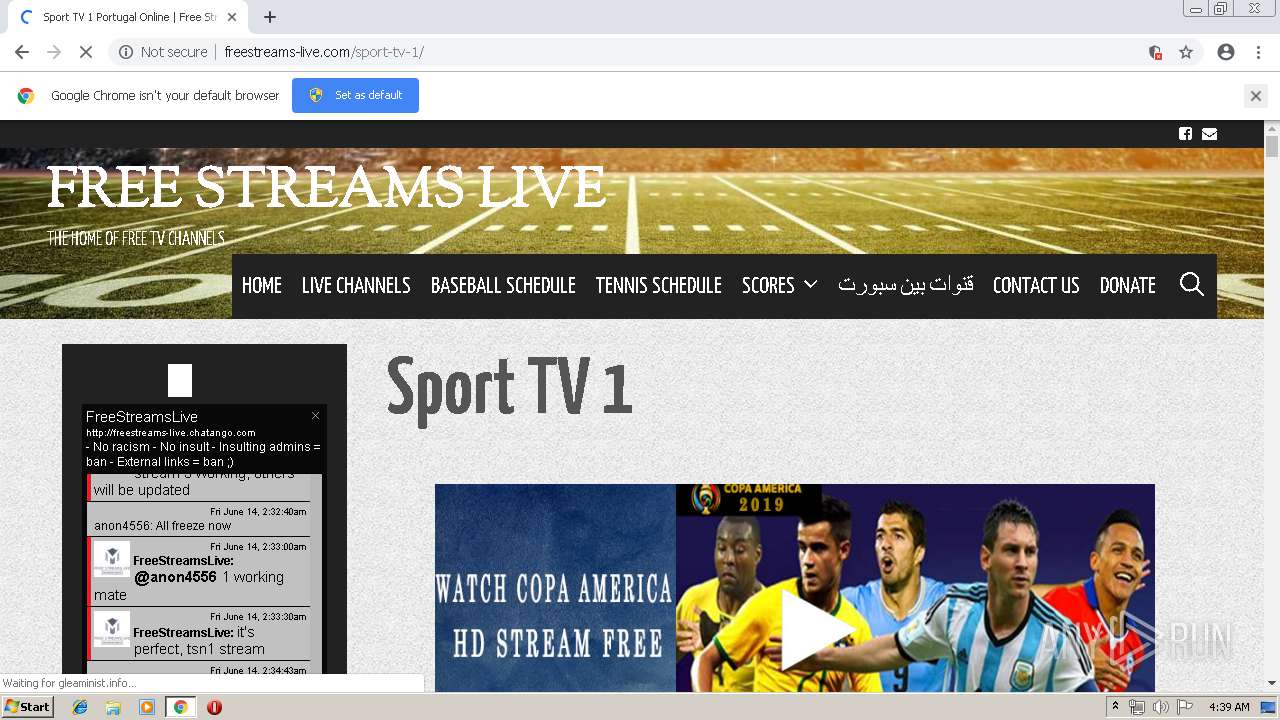
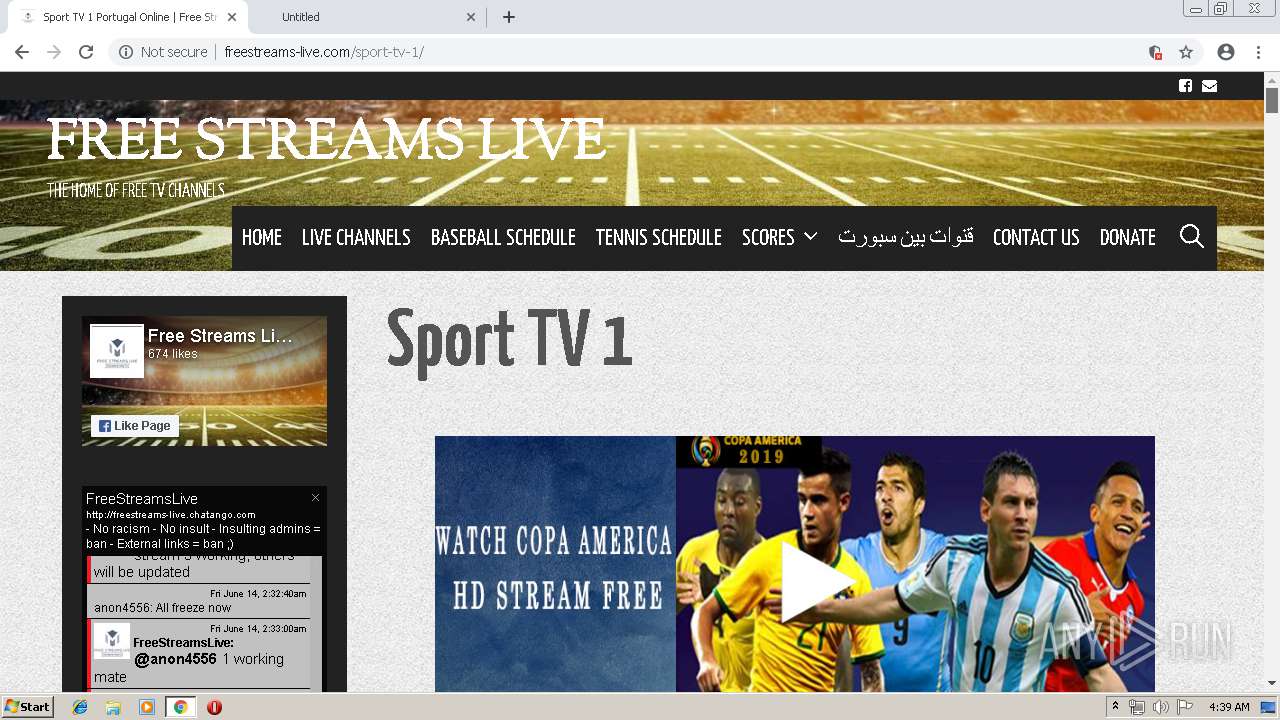
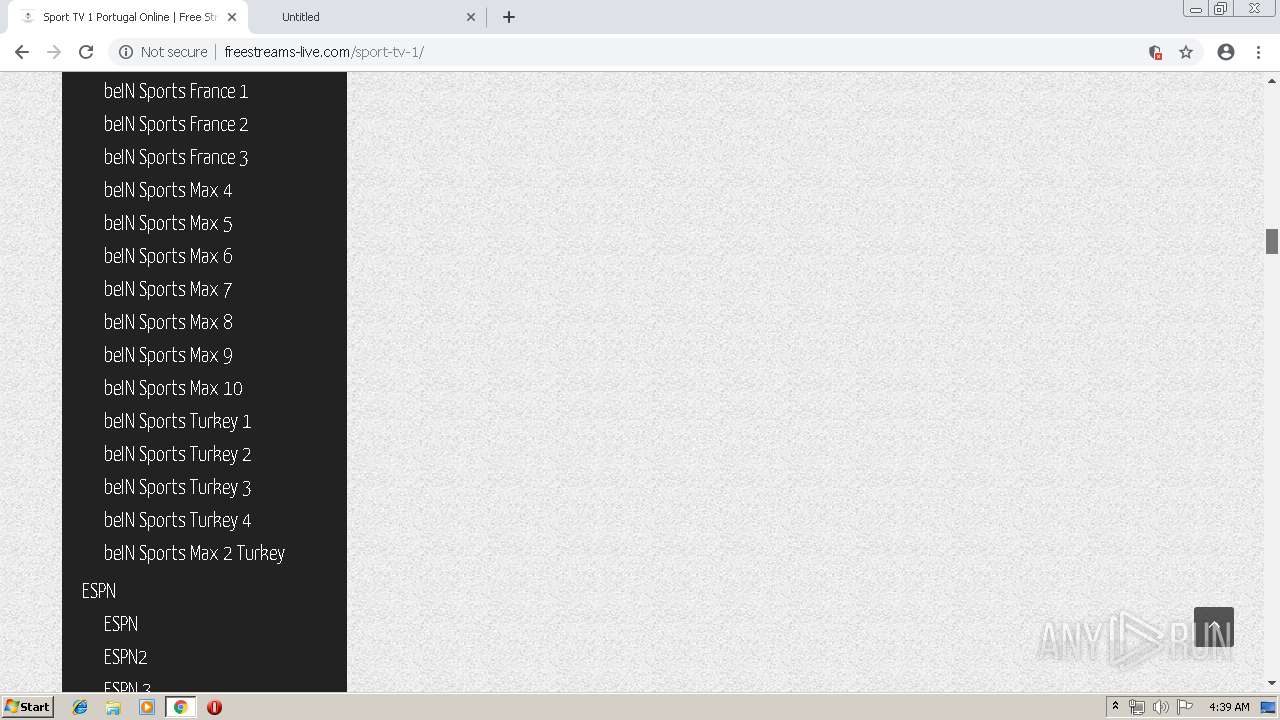
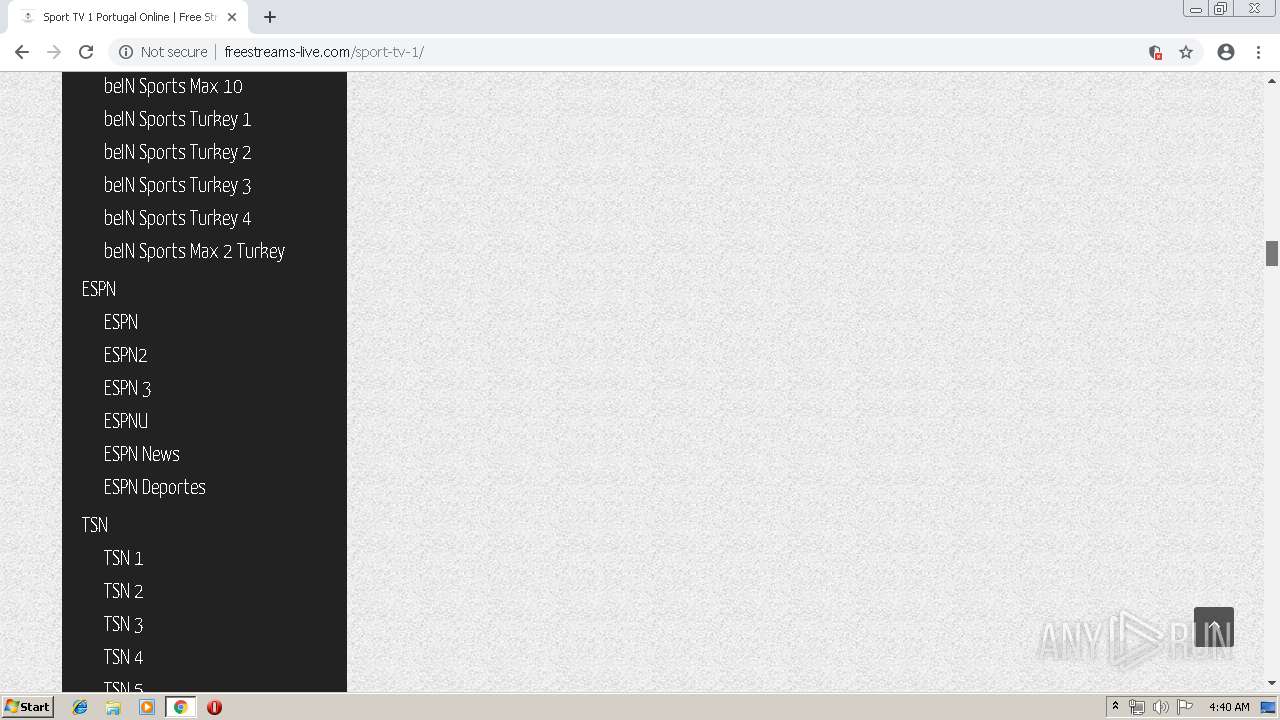
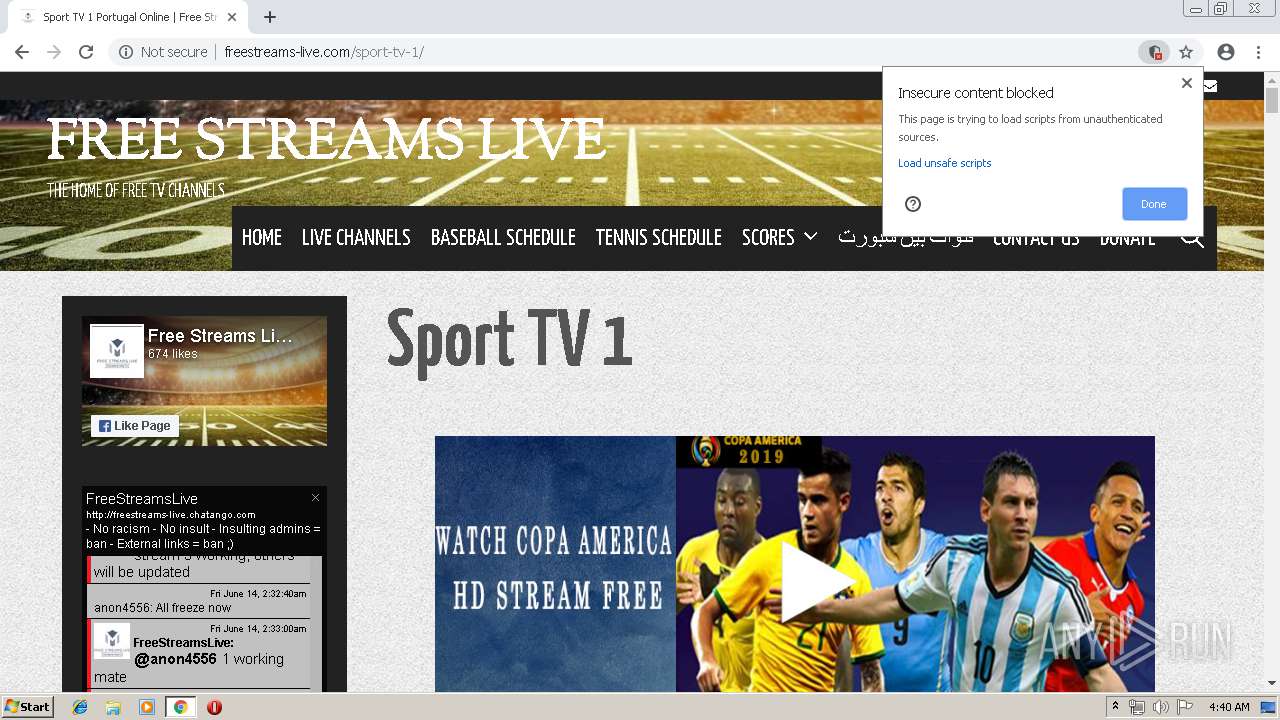
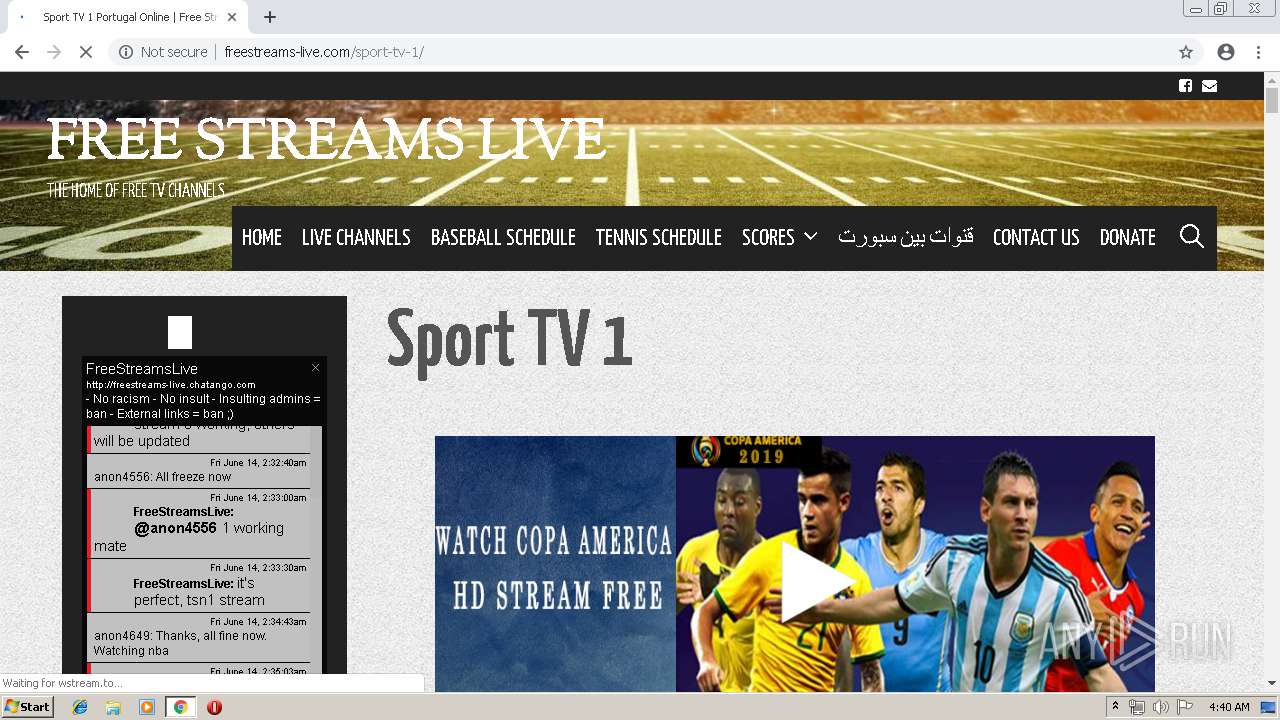
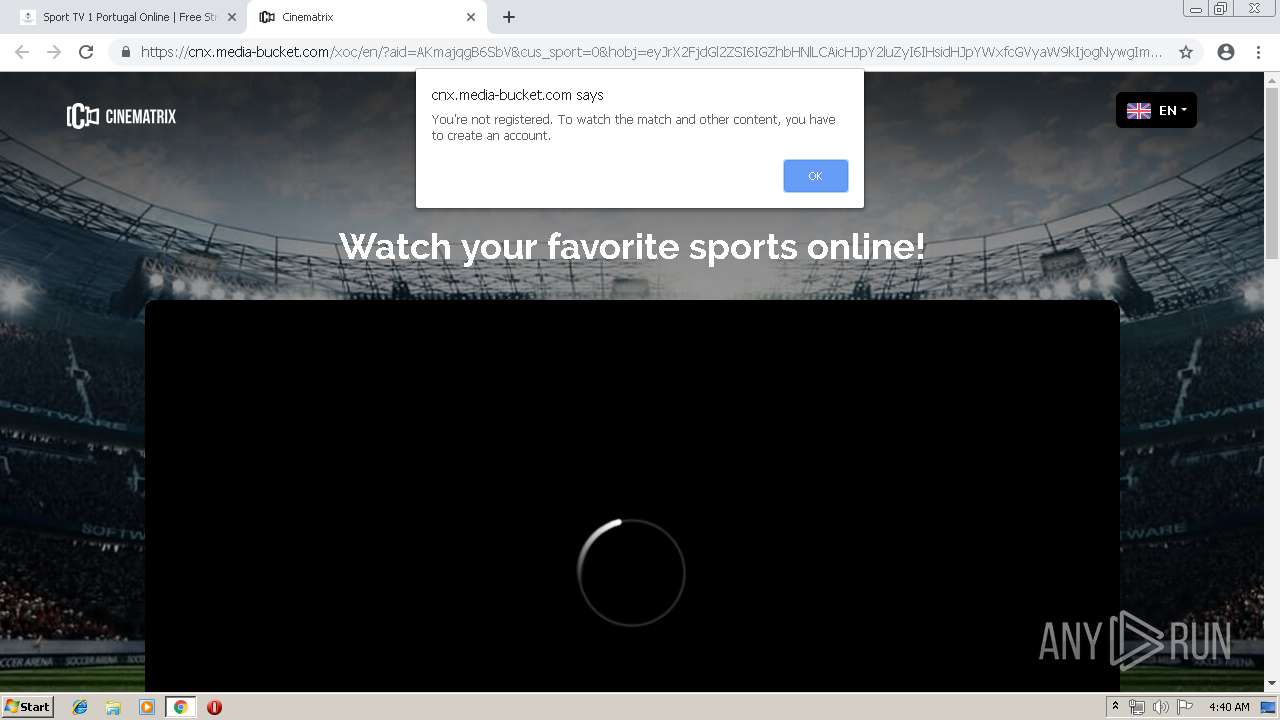
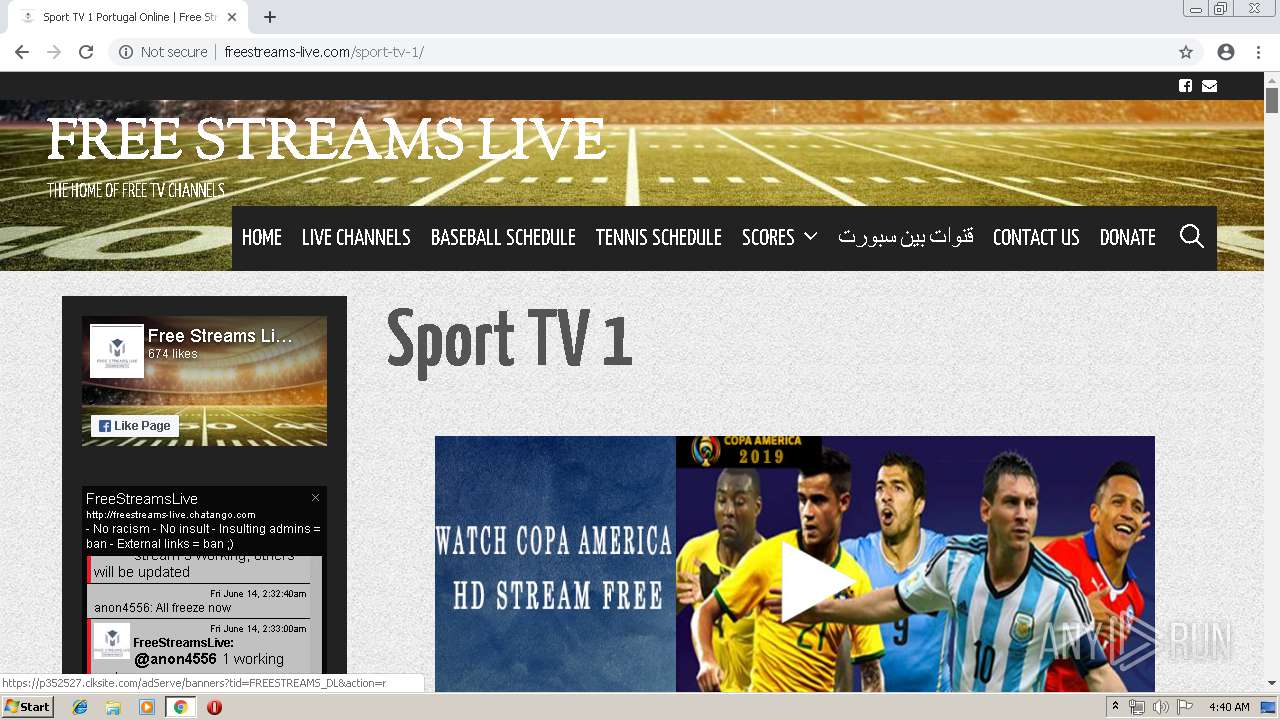
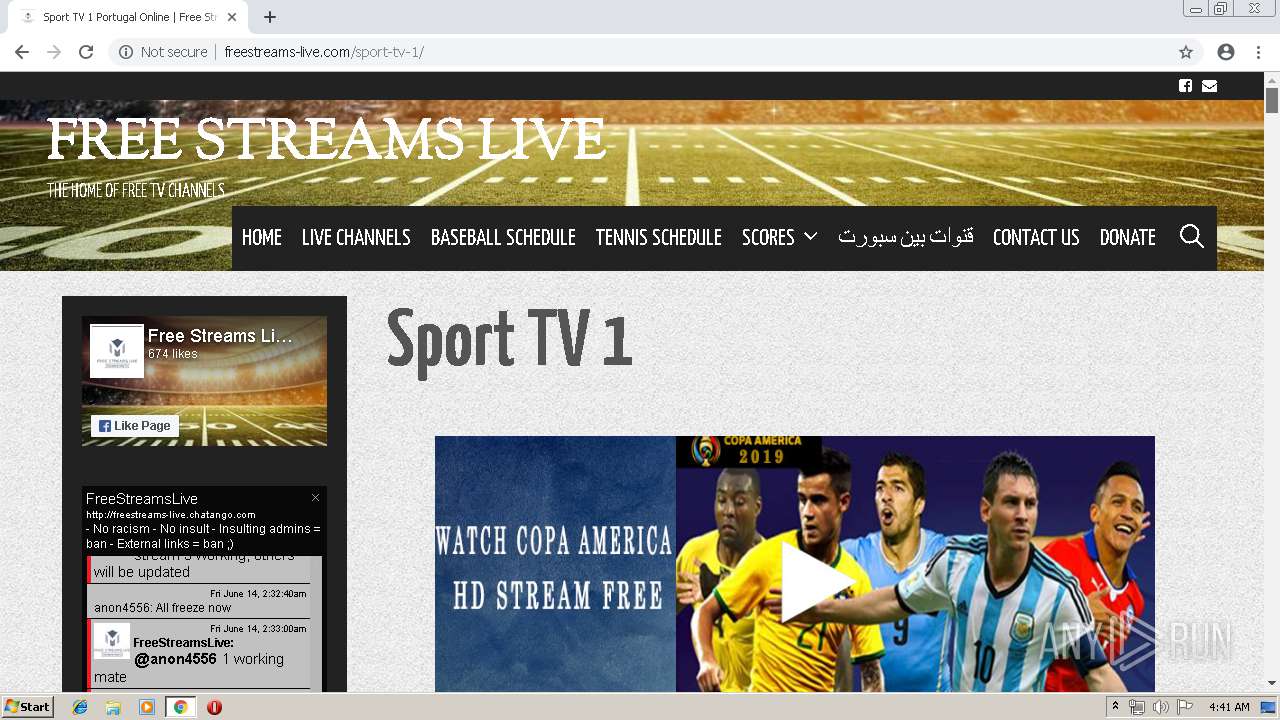
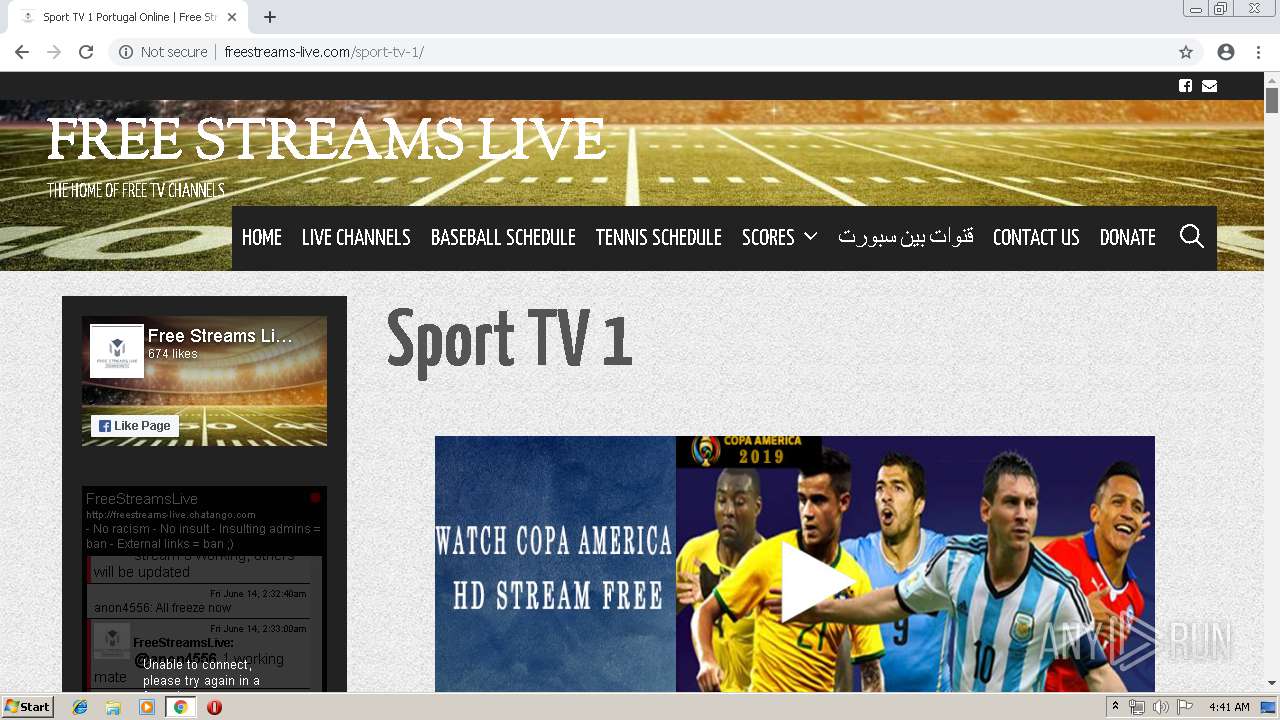
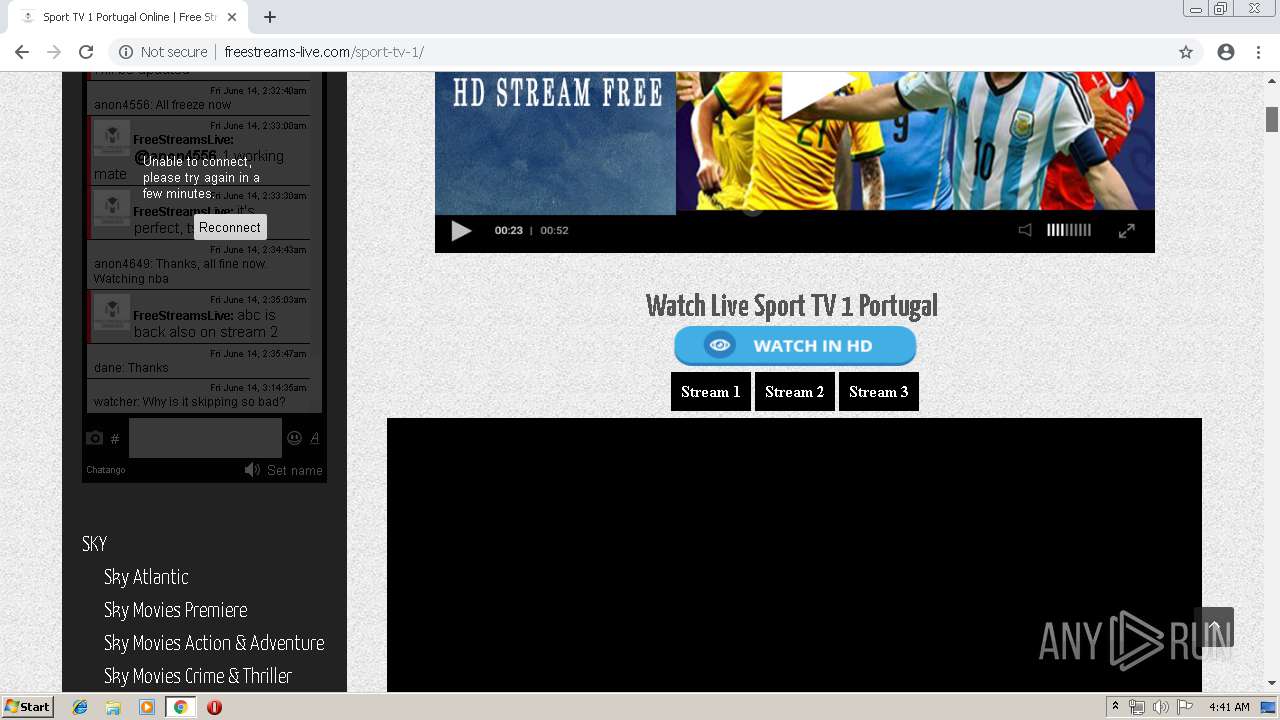
| URL: | http://freestreams-live.com/sport-tv-1/ |
| Full analysis: | https://app.any.run/tasks/1b6cd1f3-893a-4604-b4a1-8f0c3df66fb2 |
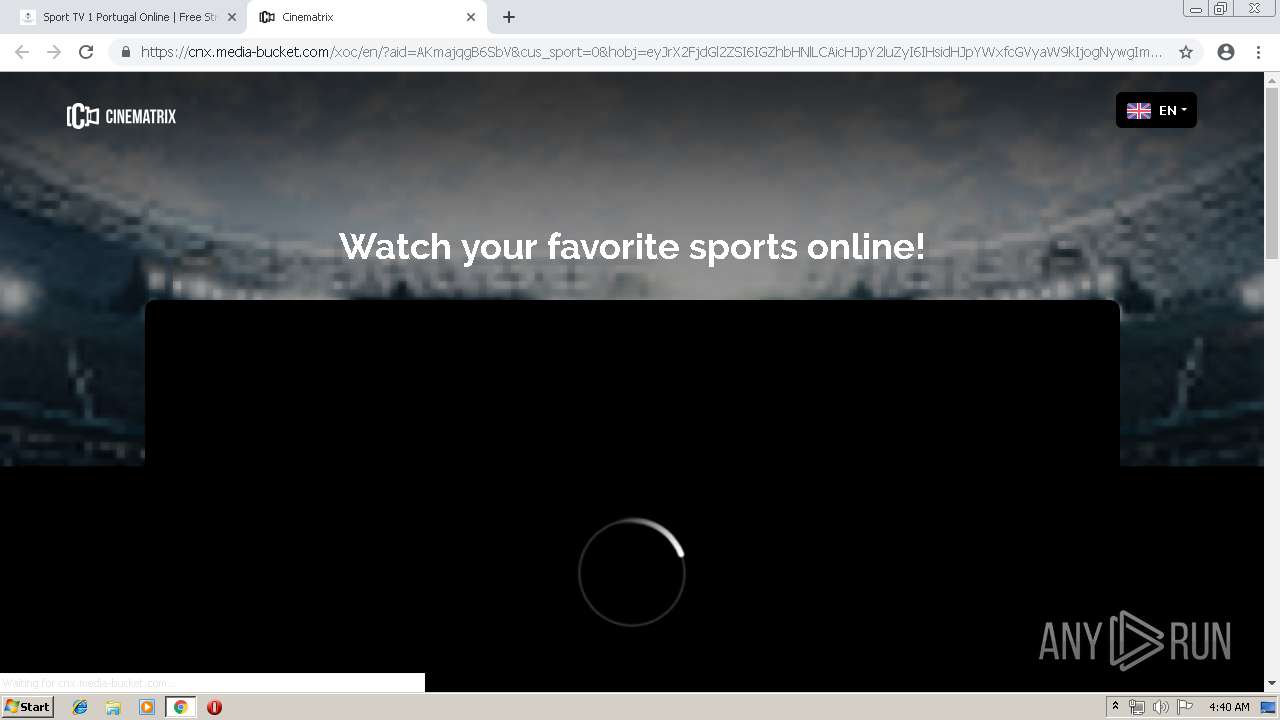
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2019, 03:38:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8CCFB534D23C02EC6D0F373996DA9EF2 |
| SHA1: | DD2ED57A30098342D79F0B920B54B465F19220E4 |
| SHA256: | 46A77CC95C5160CA3063A1FC1D7A804CA8207F8EA8751A6D05FD8C43245DBBB2 |
| SSDEEP: | 3:N1KYQzRRcJMMkVRKn:CY8TcJMzVsn |
MALICIOUS
No malicious indicators.SUSPICIOUS
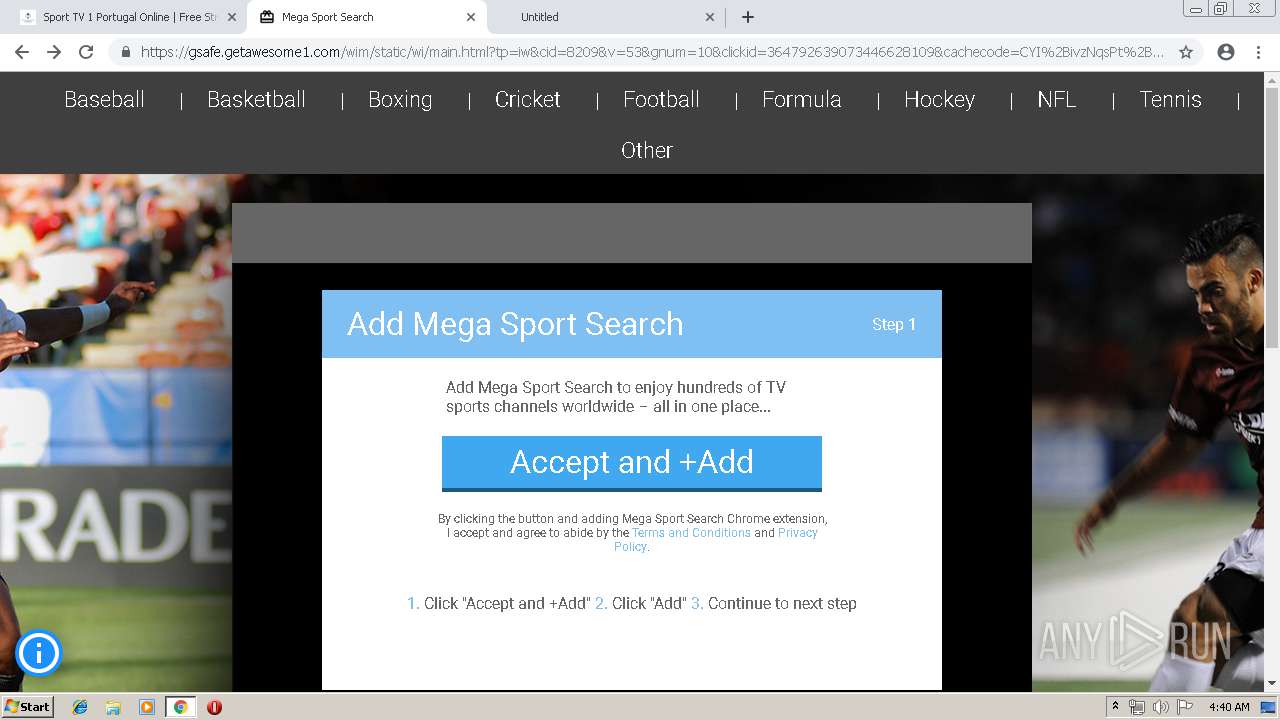
Modifies files in Chrome extension folder
- chrome.exe (PID: 1372)
INFO
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1372)
Changes settings of System certificates
- chrome.exe (PID: 1372)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1372)
Creates files in the user directory
- chrome.exe (PID: 1372)
Application launched itself
- chrome.exe (PID: 1372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
62
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13220159087329640999 --mojo-platform-channel-handle=8336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7164889642696026527 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7164889642696026527 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18200876123296690176 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18200876123296690176 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=160359516022259119 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=160359516022259119 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18363593717092022290 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18363593717092022290 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --service-pipe-token=3257158209150901429 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3257158209150901429 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1972 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10329292341742140823 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10329292341742140823 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=8696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7486788786263000076 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7486788786263000076 --renderer-client-id=60 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6491129014191746827 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6491129014191746827 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,15087736579650055368,10115477344319233266,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16435296789937349671 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16435296789937349671 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
666
Read events
548
Write events
114
Delete events
4
Modification events
| (PID) Process: | (1716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1372-13204957152636625 |
Value: 259 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1372) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
200
Text files
229
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2b4f5552-61c8-44b5-98be-fbb9bf3f097e.tmp | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1372 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
230
DNS requests
92
Threats
959
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/plugins/easy-facebook-likebox/public/assets/css/public.css?ver=4.4.0 | US | text | 3.06 Kb | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/sport-tv-1/ | US | html | 42.5 Kb | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-includes/css/dist/block-library/style.min.css?ver=5.2.1 | US | text | 5.75 Kb | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/plugins/bradmax-player/assets/css/style.css?ver=5.2.1 | US | text | 171 b | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/plugins/easy-facebook-likebox/public/assets/css/font-awesome.css?ver=4.4.0 | US | text | 6.29 Kb | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/themes/durga/css/unsemantic-grid.min.css?ver=1.0.0 | US | text | 2.91 Kb | malicious |
1372 | chrome.exe | GET | 200 | 216.58.207.42:80 | http://fonts.googleapis.com/css?family=Yanone+Kaffeesatz:200,300,regular,700|Sorts+Mill+Goudy:regular,italic | US | text | 749 b | whitelisted |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/plugins/easy-facebook-likebox/public/assets/popup/magnific-popup.css?ver=4.4.0 | US | text | 2.24 Kb | malicious |
1372 | chrome.exe | GET | 200 | 104.18.46.177:80 | http://freestreams-live.com/wp-content/plugins/show-hidecollapse-expand/assets/css/genericons/genericons.css?ver=5.2.1 | US | text | 16.4 Kb | malicious |
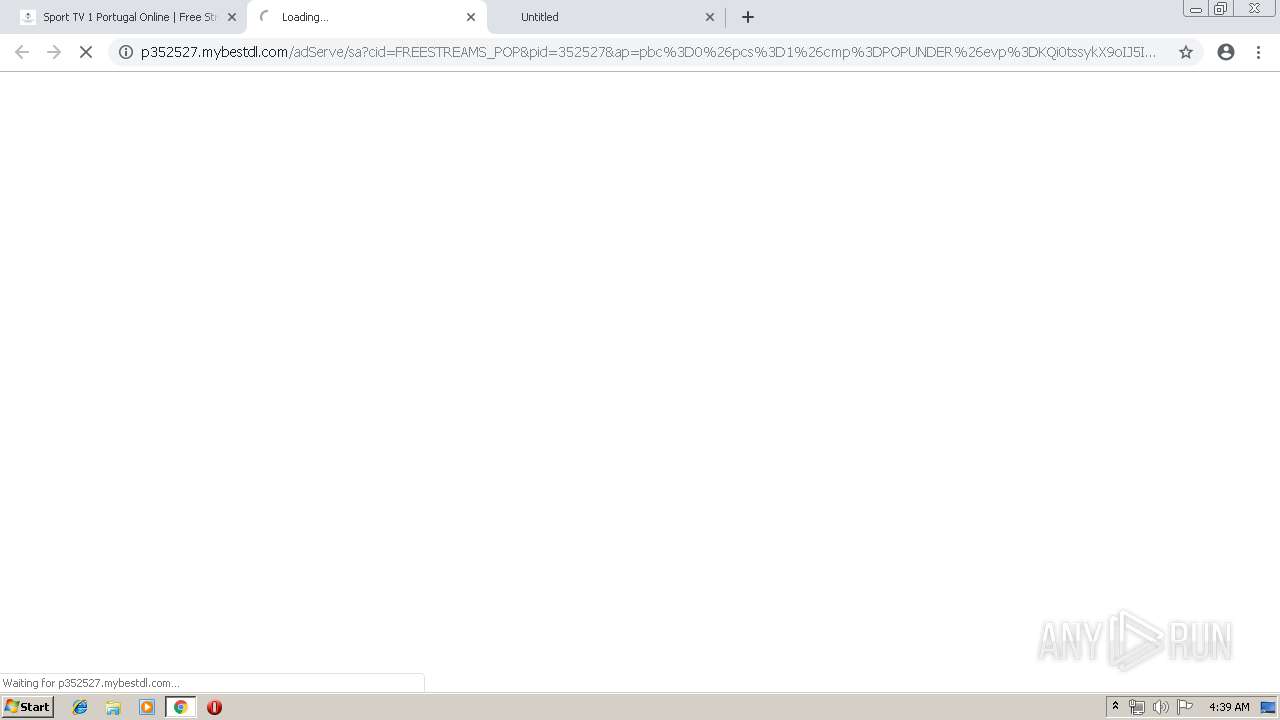
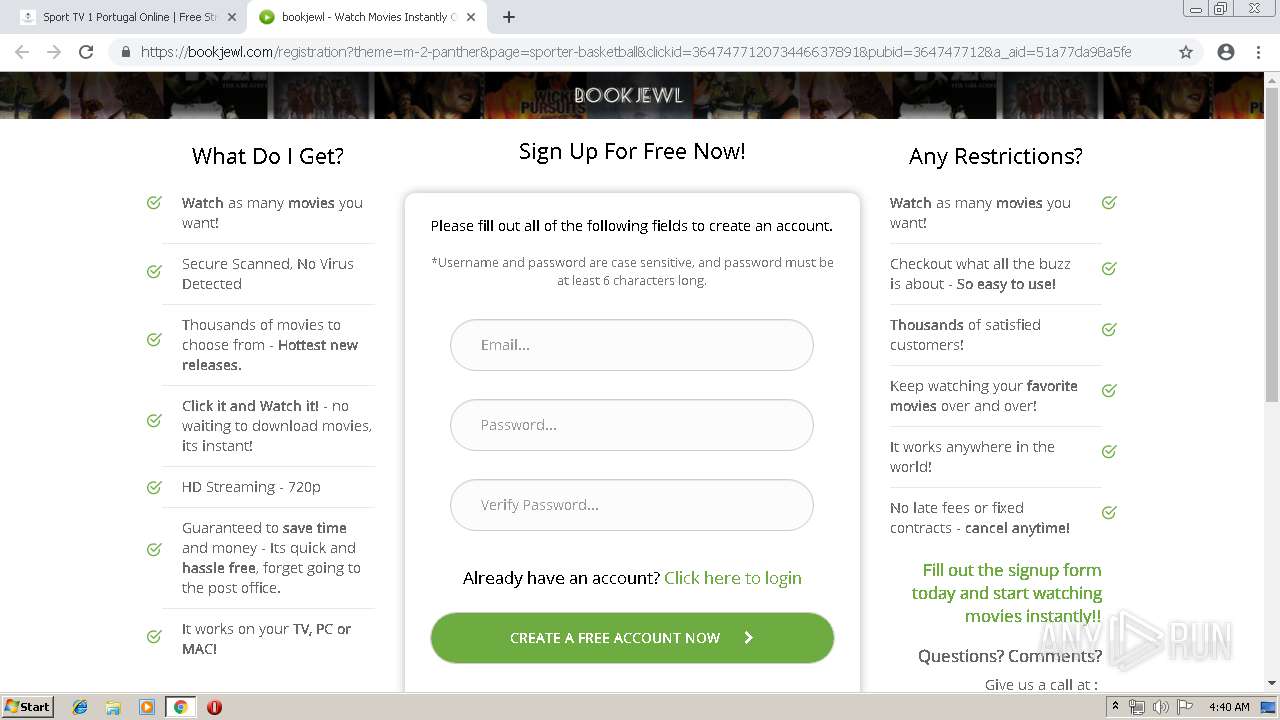
1372 | chrome.exe | GET | 301 | 173.192.101.24:80 | http://p352527.clksite.com/adServe/banners?tid=FREESTREAMS_POP&tagid=2&pop_dl=false&hybridPop=false | US | html | 178 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 104.18.46.177:80 | freestreams-live.com | Cloudflare Inc | US | shared |
1372 | chrome.exe | 216.58.207.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 172.217.22.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 172.217.18.99:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1372 | chrome.exe | 173.192.101.24:80 | p352527.clksite.com | SoftLayer Technologies Inc. | US | suspicious |
1372 | chrome.exe | 108.168.193.181:80 | mybestdl.com | SoftLayer Technologies Inc. | US | unknown |
1372 | chrome.exe | 208.93.230.24:80 | st.chatango.com | Chatango LLC | US | unknown |
1372 | chrome.exe | 18.194.12.121:443 | stats.bradmax.com | Amazon.com, Inc. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
freestreams-live.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
p352527.clksite.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
mybestdl.com |
| suspicious |
s.w.org |
| whitelisted |
stats.bradmax.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1372 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |