| File name: | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/bc49bc78-a6be-4302-a0d4-829b075d509e |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 04:04:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | B2A6904D2BF5295FE7820271122B6E4C |
| SHA1: | 6922335772823CCB547CC383BD636ACC52EEBAC9 |
| SHA256: | 4699993A531471E03D5BA46E3433F300D5876D93A6872D9E63F992ABB46E9A37 |
| SSDEEP: | 98304:iefUuZuKAuf5jTFEkOefUuZuKAuf5jTFziy9/W10abzzpQXPJP0jjiGHaGx/LOLp:kySbzzdr0ijelYM |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 1676)
Starts NET.EXE for service management
- cmd.exe (PID: 6048)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 4696)
- net.exe (PID: 7532)
- net.exe (PID: 7580)
- net.exe (PID: 7564)
- net.exe (PID: 7512)
- net.exe (PID: 7572)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 3900)
- net.exe (PID: 7532)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 5380)
- net.exe (PID: 7556)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 4696)
- net.exe (PID: 7572)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 5512)
- net.exe (PID: 7620)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 4988)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 1676)
Process drops legitimate windows executable
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
Starts itself from another location
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
Executing commands from a ".bat" file
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
Starts CMD.EXE for commands execution
- UpdatAuto.exe (PID: 6816)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 6816)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
Executable content was dropped or overwritten
- UpdatAuto.exe (PID: 6816)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
Windows service management via SC.EXE
- sc.exe (PID: 7176)
- sc.exe (PID: 7264)
- sc.exe (PID: 7276)
- sc.exe (PID: 7208)
- sc.exe (PID: 7236)
INFO
The sample compiled with chinese language support
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
Create files in a temporary directory
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 1676)
Checks supported languages
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 1676)
Reads Environment values
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe (PID: 1676)
Reads the computer name
- UpdatAuto.exe (PID: 6816)
Creates files in the program directory
- 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe (PID: 6424)
- UpdatAuto.exe (PID: 6816)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7988)
- BackgroundTransferHost.exe (PID: 4920)
- BackgroundTransferHost.exe (PID: 7212)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7212)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7212)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (33.5) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (12.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.6) |
| .exe | | | Win32 Executable (generic) (1.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
178
Monitored processes
51
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | UpdatAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\Desktop\2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | — | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Crash Dump Generator Exit code: 0 Version: 8,0,224,6711 @Commit: 1381d5ebd2ab1f292848d5b19b80cf71ac332 Modules
| |||||||||||||||
| 2096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | cmd.exe /c net start TlntSvr | C:\Windows\SysWOW64\cmd.exe | — | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3900 | cmd.exe /c net stop wscsvc | C:\Windows\SysWOW64\cmd.exe | — | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | cmd.exe /c net stop wuauserv | C:\Windows\SysWOW64\cmd.exe | — | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 935
Read events
4 926
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7988) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7988) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7988) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7212) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4920) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
19
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
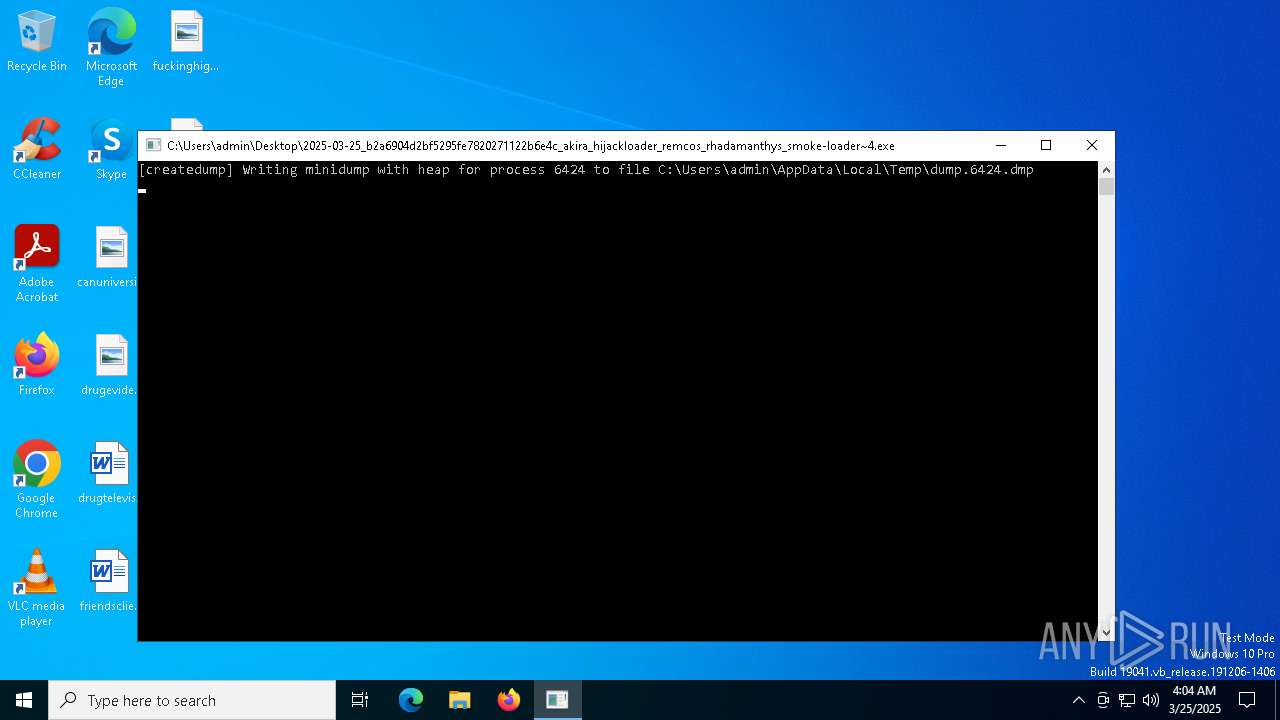
| 1676 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\AppData\Local\Temp\dump.6424.dmp | — | |
MD5:— | SHA256:— | |||
| 6424 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\Option.bat | text | |
MD5:1D04ABF39E9DF55EED1D04430CC21EB8 | SHA256:0BC485263CF8A962E64DB0B88F156F2A9AF1B81ECFDB1CF9111D497E85DF70F3 | |||
| 7212 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\452a897b-80af-4a79-be8e-993a16681382.down_data | — | |
MD5:— | SHA256:— | |||
| 6424 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\ntldr~6 | executable | |
MD5:76EE45F7B49736F610D00D5245DD38DB | SHA256:815BE50554C23C8522F83AE6466471300CE47D3B483435C7F4EFC069DE6AF984 | |||
| 6424 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\UpdatAuto.exe | executable | |
MD5:76EE45F7B49736F610D00D5245DD38DB | SHA256:815BE50554C23C8522F83AE6466471300CE47D3B483435C7F4EFC069DE6AF984 | |||
| 6816 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | executable | |
MD5:E31964B5DF037F59E0A2901E36B4E0DE | SHA256:2A3F2DA5A6C5523B49C300961F1D75F8A5A8751B38FD0E7B682EEA5547894F3B | |||
| 6424 | 2025-03-25_b2a6904d2bf5295fe7820271122b6e4c_akira_hijackloader_remcos_rhadamanthys_smoke-loader.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AdobeCollabSync.exe | — | |
MD5:— | SHA256:— | |||
| 6816 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRLogTransport.exe | — | |
MD5:— | SHA256:— | |||
| 6816 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRWindowsClientService.exe | — | |
MD5:— | SHA256:— | |||
| 6816 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcrobatInfo.exe | executable | |
MD5:246018C086E087F975195332F3C756B8 | SHA256:27093DED885559BE2CF705C600F9E77864EBE039C6D39ECDAFC6A35216BA314B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
51
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7260 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | POST | 200 | 40.126.31.130:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | GET | 200 | 20.74.47.205:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=310091&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20250325T040426Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=7a06fa4caab84ab79e1ead589ef0fd47&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.3636&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19045.4046&disphorzres=1280&dispsize=15.3&dispvertres=720&fosver=16299&isu=0&lo=3968403&metered=false&nettype=ethernet&npid=sc-310091&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&rver=2&smBiosDm=DELL&stabedgever=122.0.2365.59&tl=2&tsu=1358933&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | binary | 4.23 Kb | whitelisted |
— | — | POST | 400 | 40.126.31.67:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | GET | 200 | 20.74.47.205:443 | https://arc.msn.com/v3/Delivery/Placement?pubid=da63df93-3dbc-42ae-a505-b34988683ac7&pid=88000045&adm=2&w=1&h=1&wpx=1&hpx=1&fmt=json&cltp=app&dim=le&rafb=0&nct=1&pm=1&cfmt=text,image,poly&sft=jpeg,png,gif&topt=1&poptin=0&localid=w:AC7699B0-48EA-FD22-C8DC-06A02098A0F0&ctry=US&time=20250325T040426Z&lc=en-US&pl=en-US&idtp=mid&uid=9115d6d1-9f4e-4053-9297-2a8c833b3912&aid=00000000-0000-0000-0000-000000000000&ua=WindowsShellClient%2F9.0.40929.0%20%28Windows%29&asid=8bb940b2d6ac4e9caaf183f3f1212fc1&ctmode=MultiSession&arch=x64&betaedgever=0.0.0.0&canedgever=0.0.0.0&cdm=1&cdmver=10.0.19041.3636&currsel=137271744000000000&devedgever=0.0.0.0&devfam=Windows.Desktop&devform=Unknown&devosver=10.0.19045.4046&disphorzres=1280&dispsize=15.3&dispvertres=720&fosver=16299&isu=0&lo=3968403&metered=false&nettype=ethernet&npid=sc-88000045&oemName=DELL&oemid=DELL&ossku=Professional&prevosver=15063&smBiosDm=DELL&stabedgever=122.0.2365.59&tl=2&tsu=1358933&waasBldFlt=1&waasCfgExp=1&waasCfgSet=1&waasRetail=1&waasRing=&svoffered=2 | unknown | binary | 2.96 Kb | whitelisted |
7260 | SIHClient.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.126.37.170:443 | https://www.bing.com/th?id=OADD2.10239414284817_1UVYYSBXC4CID8KBL&pid=21.2&c=16&roil=0&roit=0&roir=1&roib=1&w=48&h=48&dynsize=1&qlt=90 | unknown | image | 1.93 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6240 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7212 | BackgroundTransferHost.exe | 2.19.122.31:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |