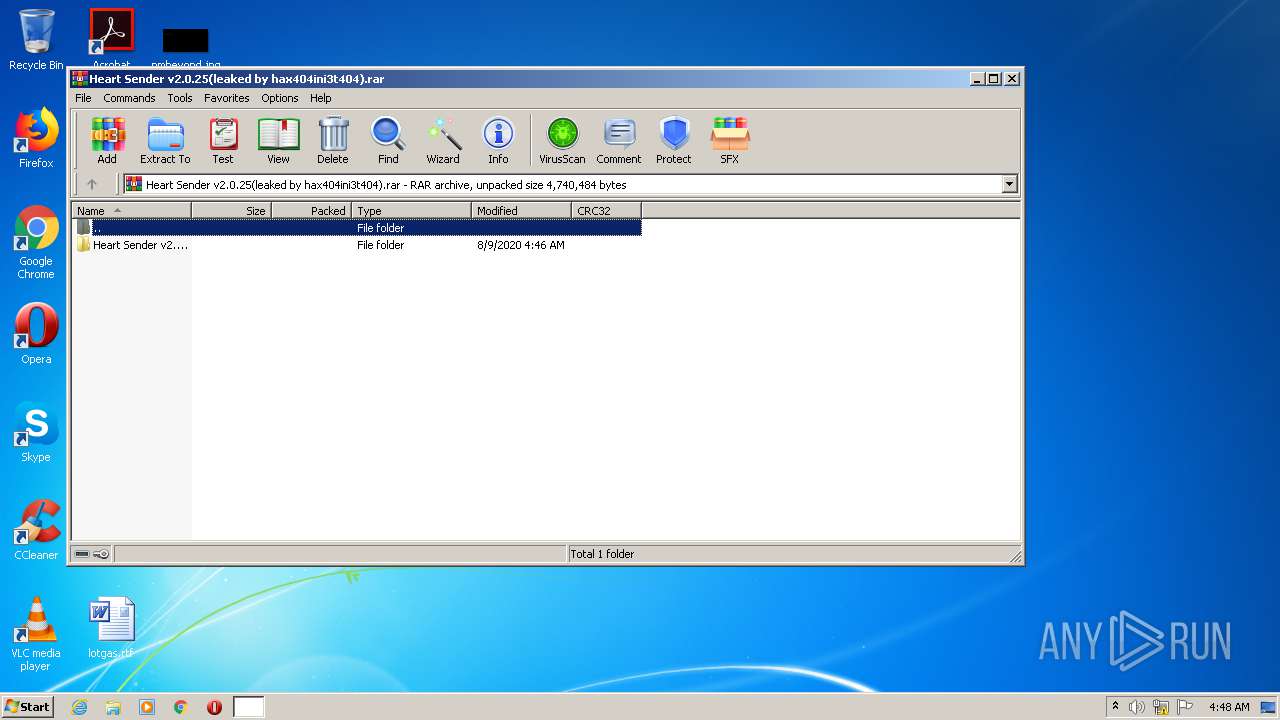
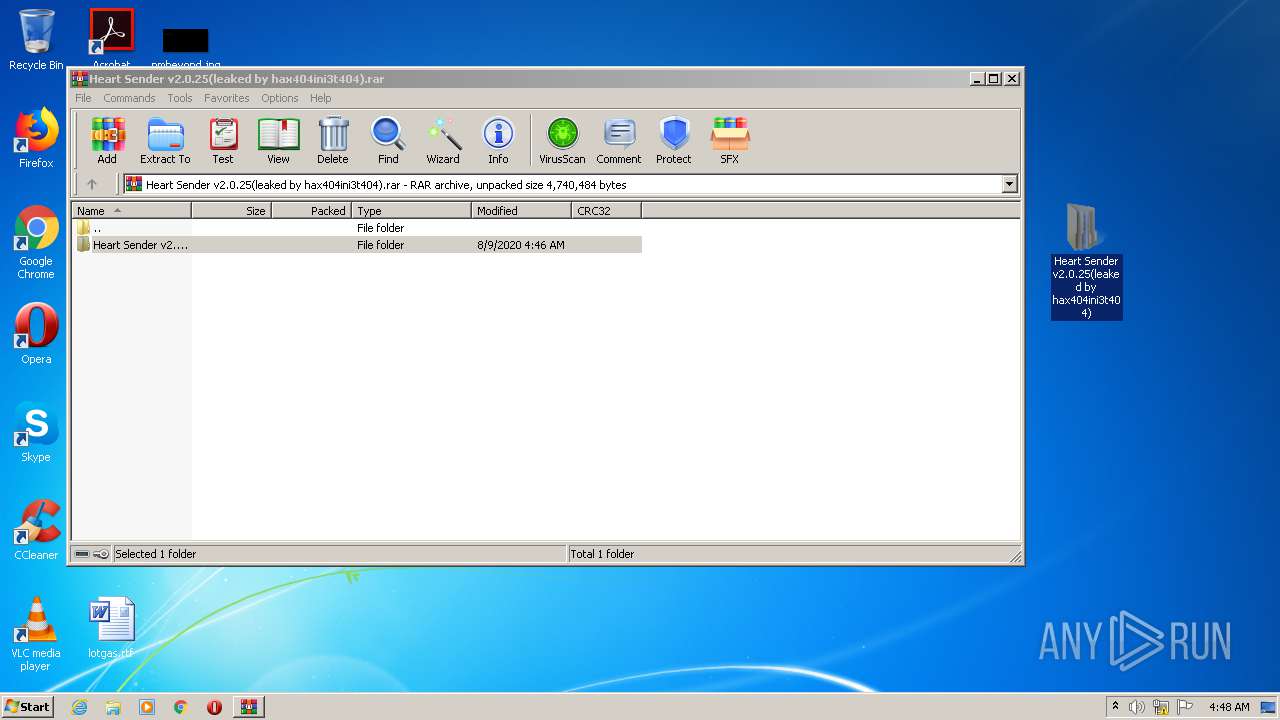
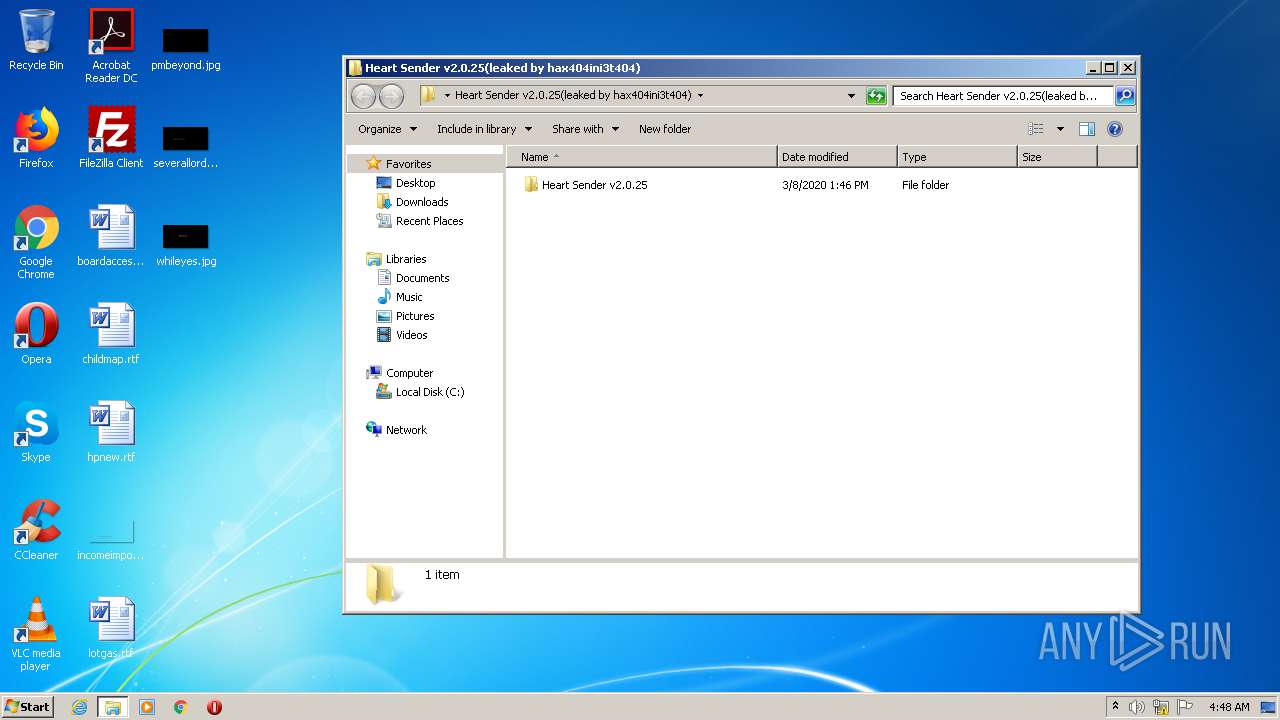
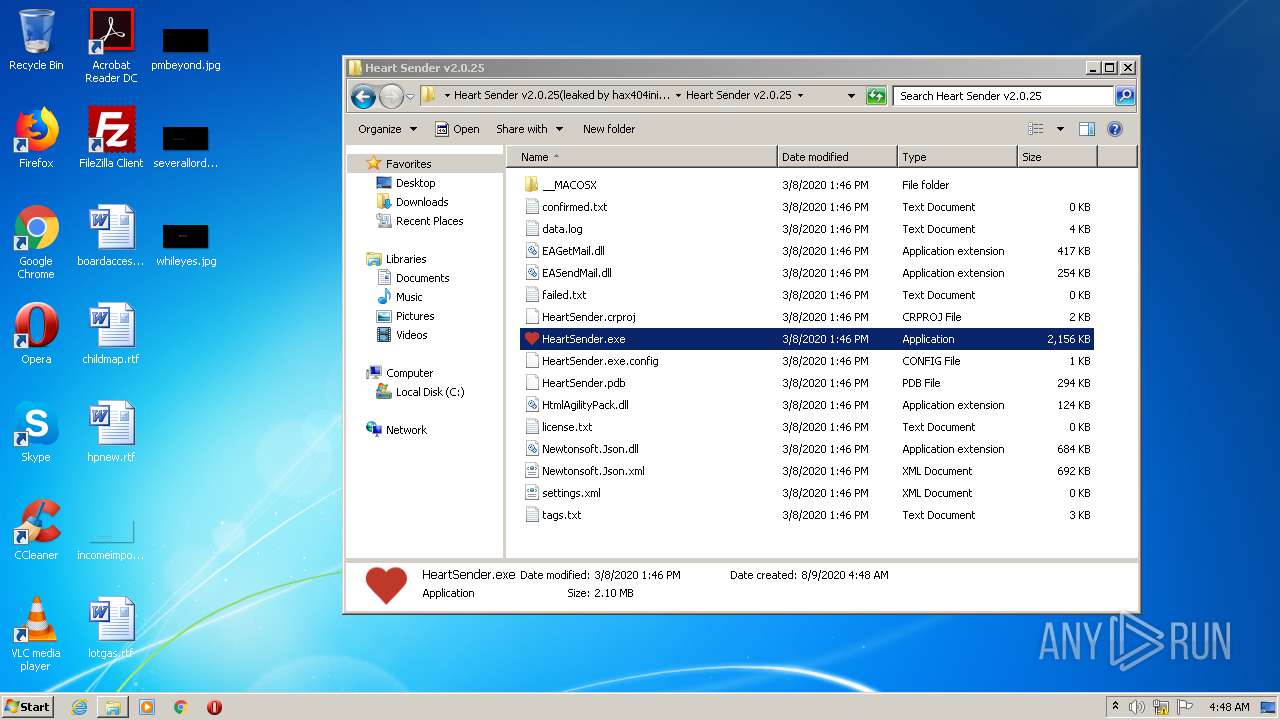
| File name: | Heart Sender v2.0.25(leaked by hax404ini3t404).rar |
| Full analysis: | https://app.any.run/tasks/6ffcd218-2c7f-4e1c-b5ca-1bf91b3a67cf |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2020, 03:47:54 |
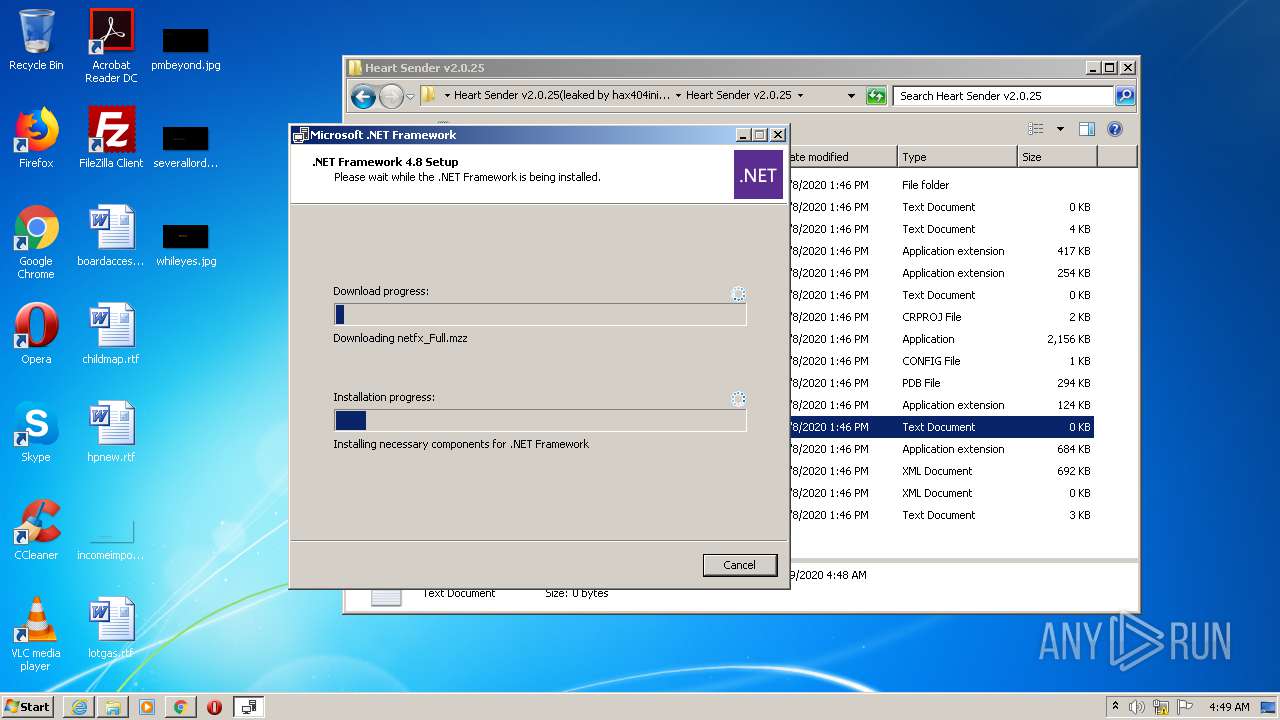
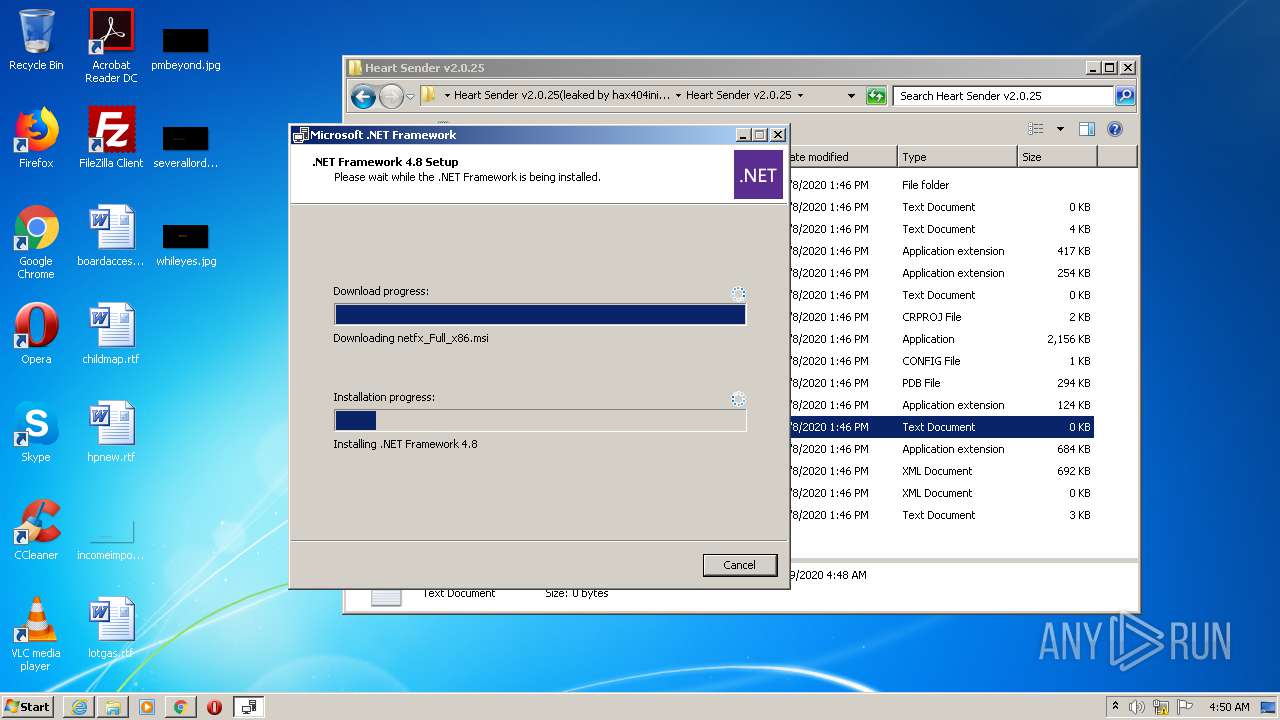
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
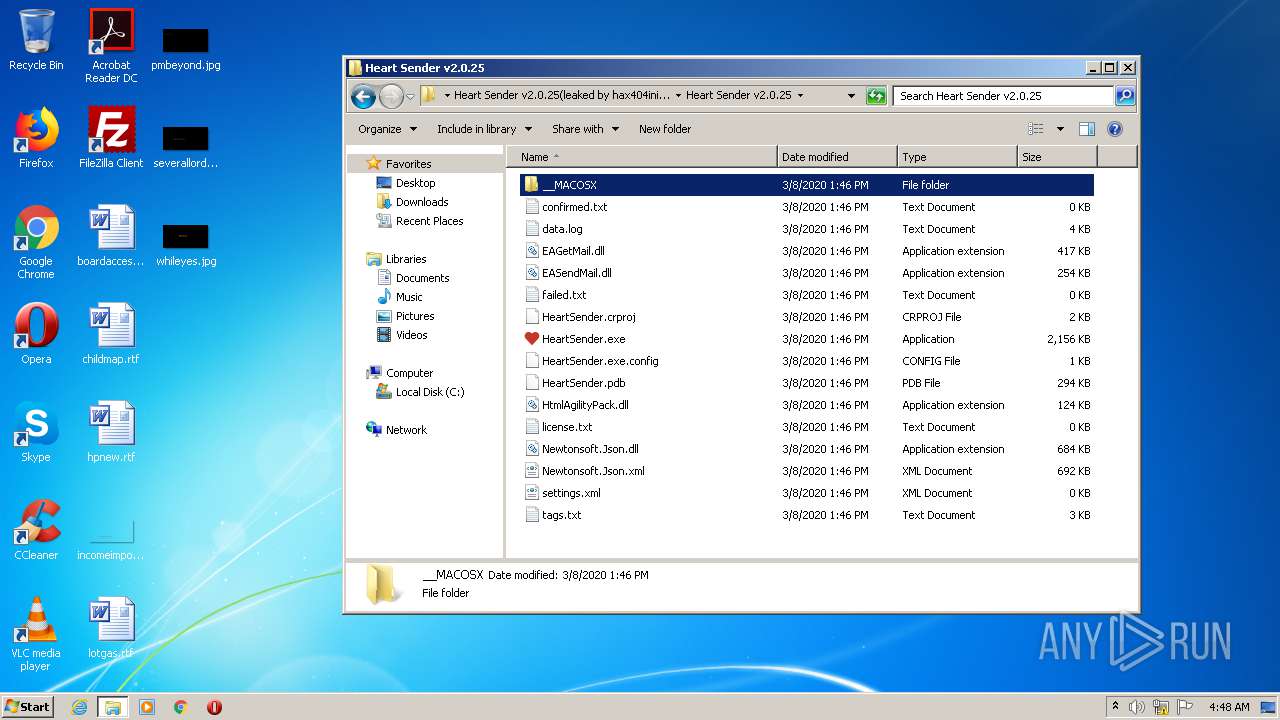
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | C63213E0DD13440ABB9AFEEEBE19FA18 |
| SHA1: | 4F28979AE77FFC7488F836C38E582A99280036F6 |
| SHA256: | 4695AF50C155586D6E4FAFD71B78E898DF249E21B7BC31D91B84402756F641E9 |
| SSDEEP: | 24576:84svRSxikNhNgIJKJhrR0ZazrTYUylg7h7W4rG:8vRaikbCI0ZR/rTzl8 |
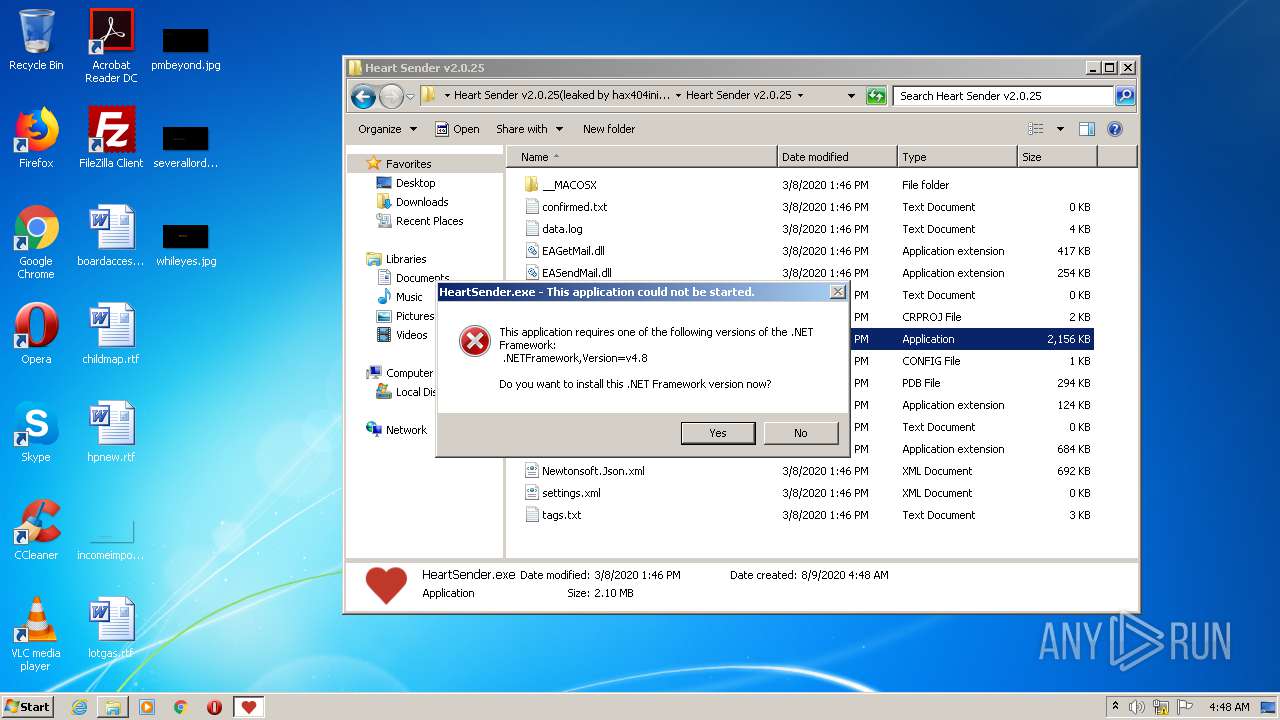
MALICIOUS
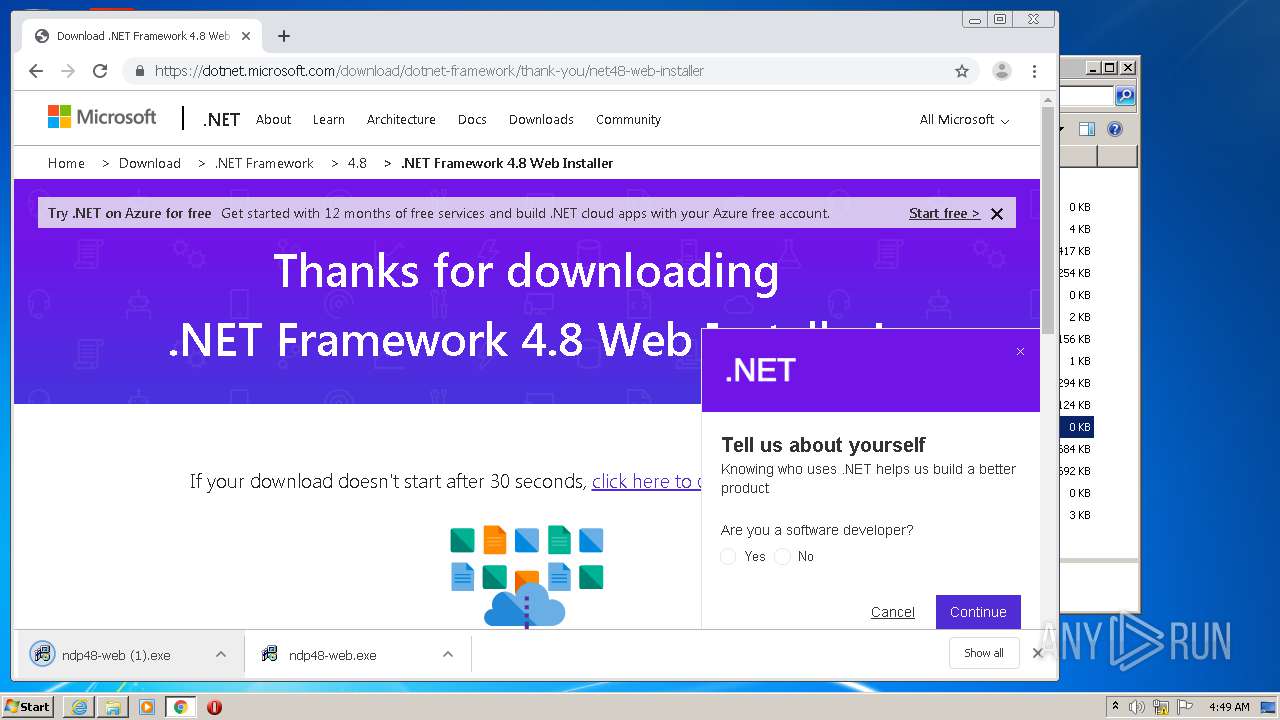
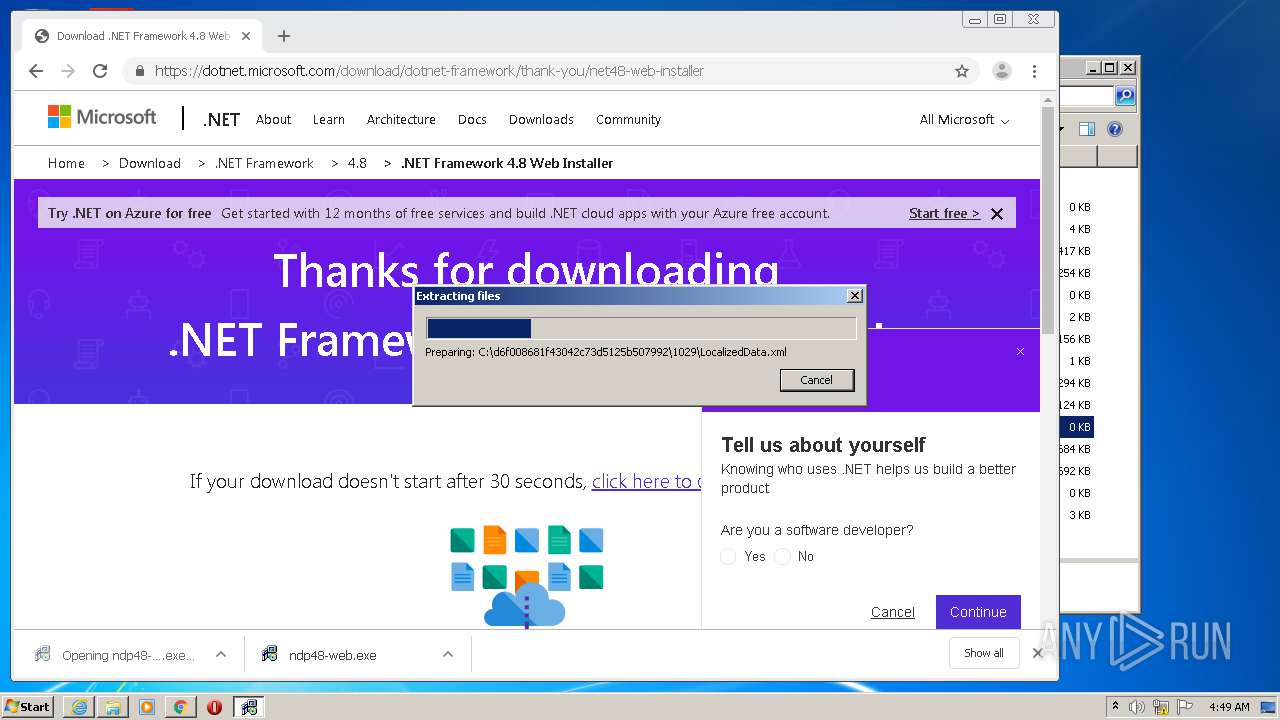
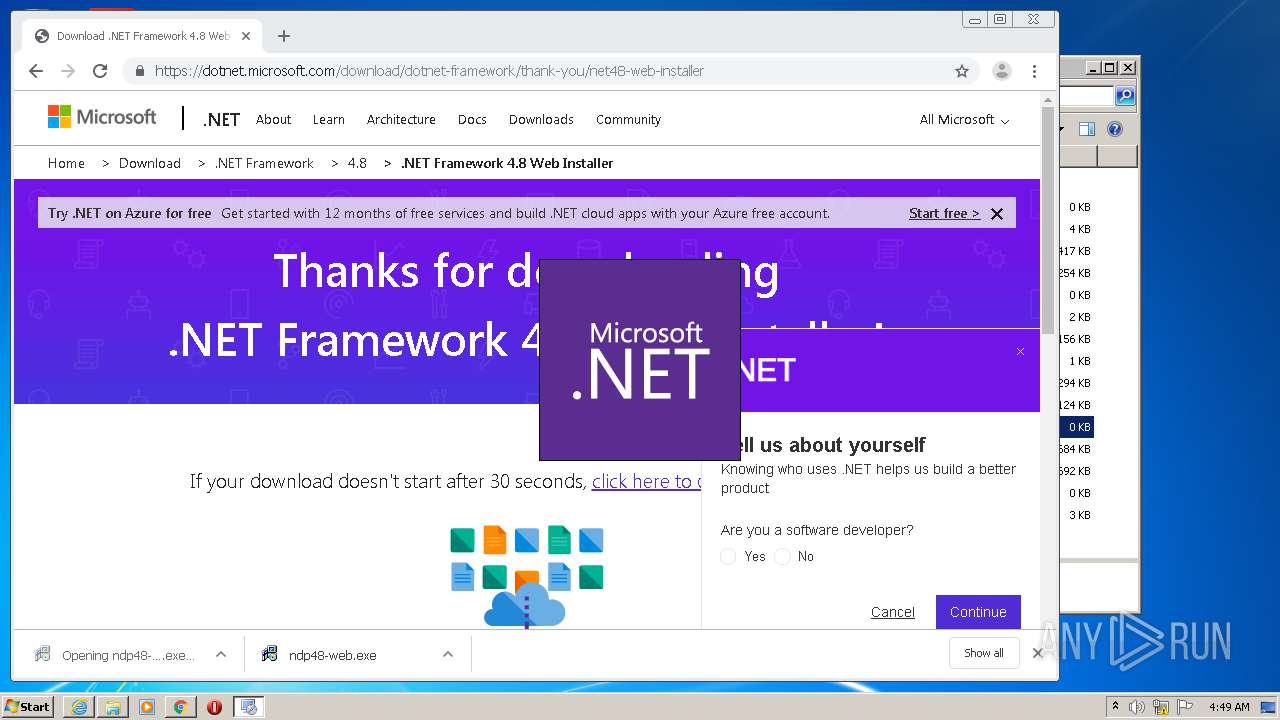
Application was dropped or rewritten from another process
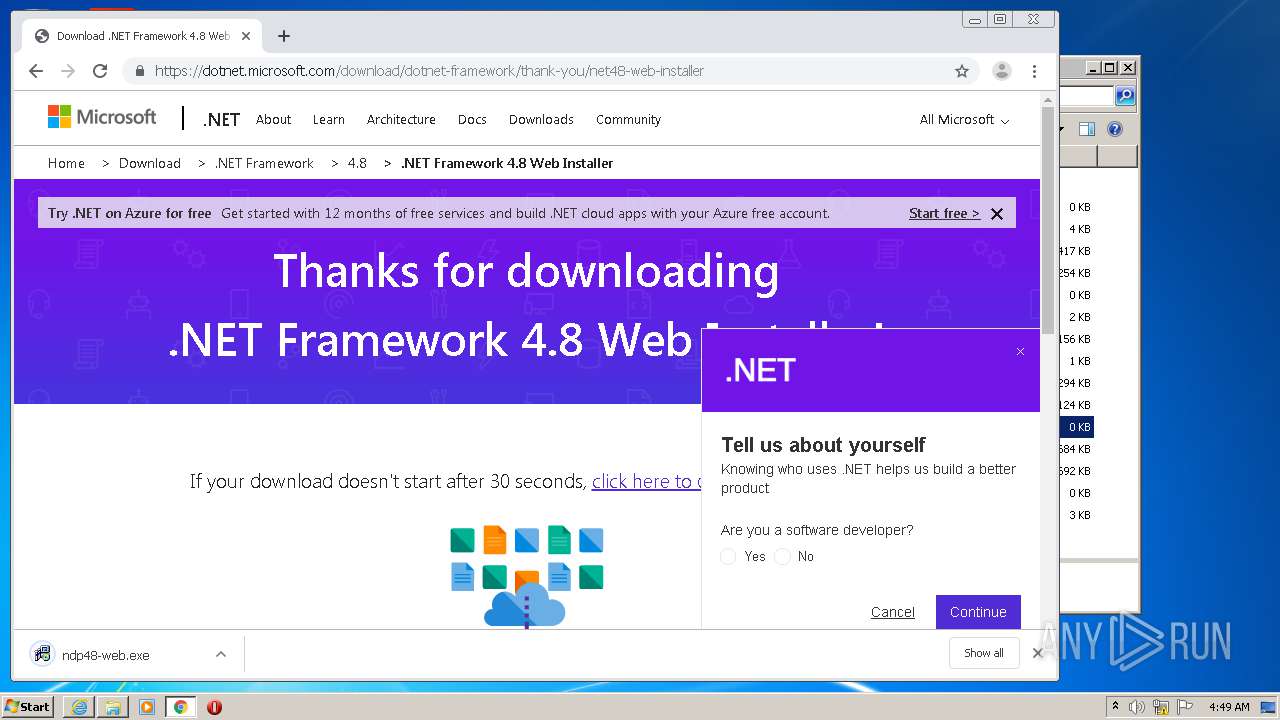
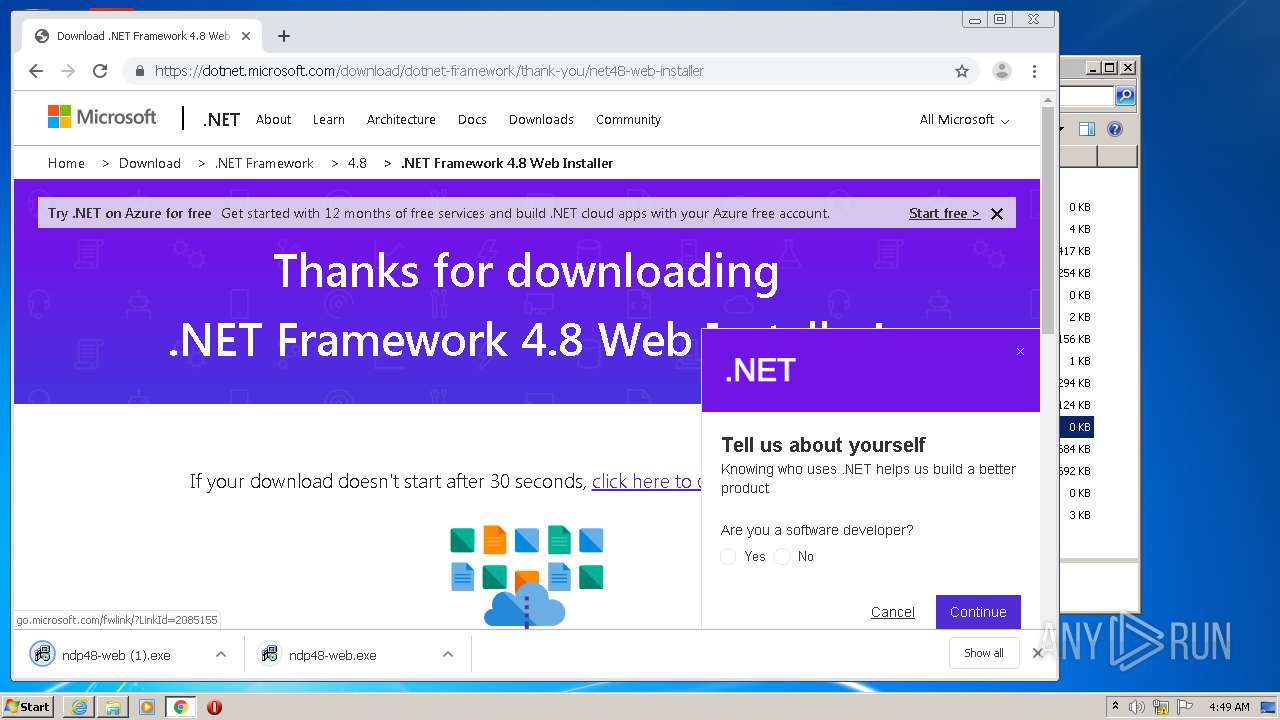
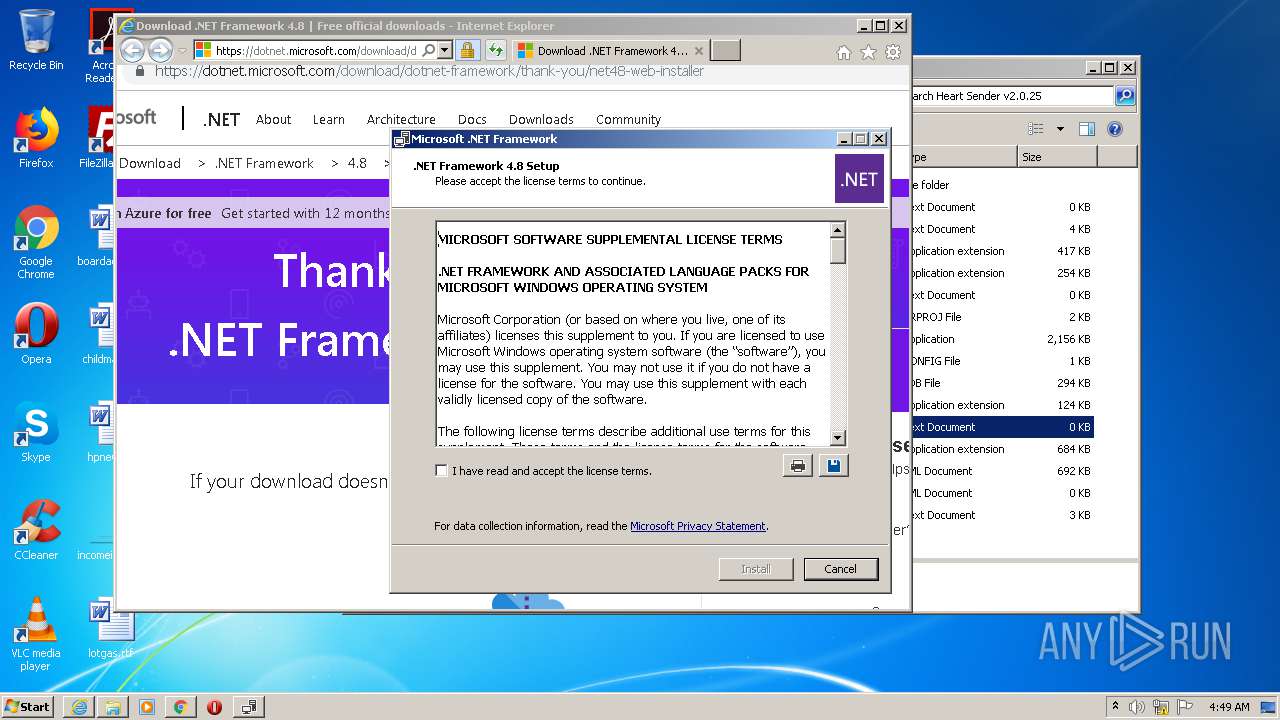
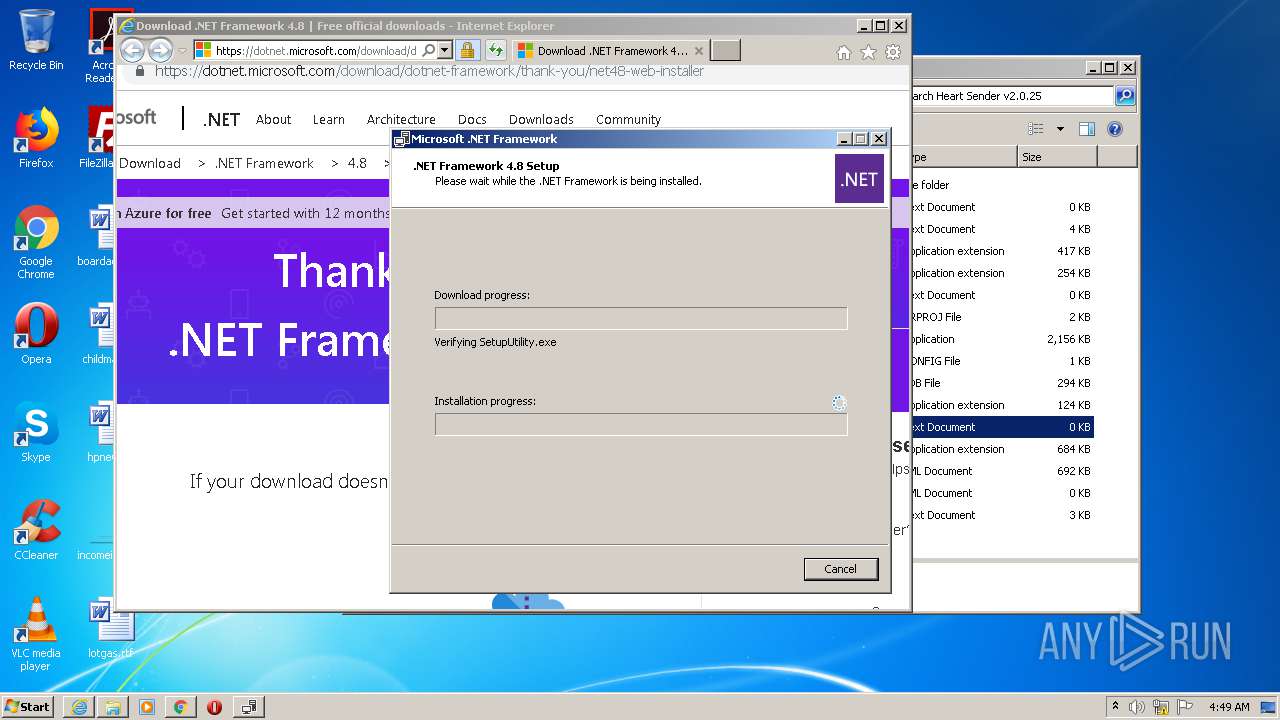
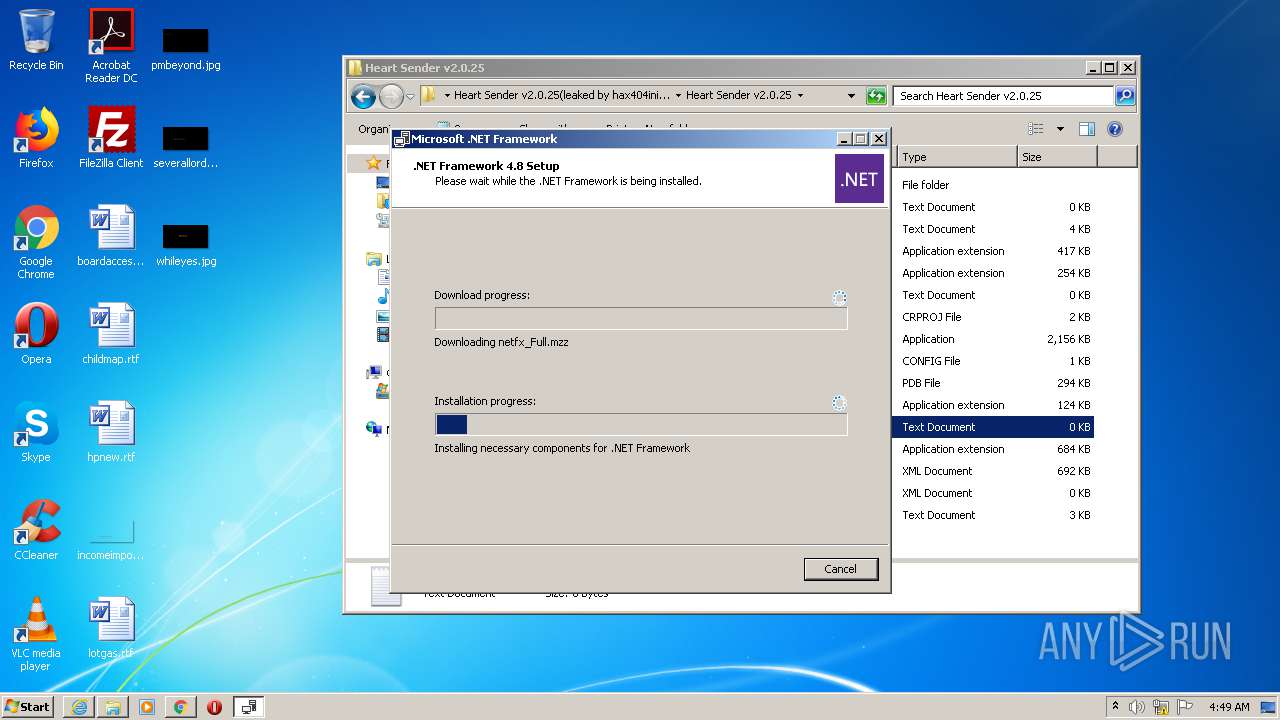
- ndp48-web (1).exe (PID: 3196)
- ndp48-web (1).exe (PID: 576)
- Setup.exe (PID: 3208)
- SetupUtility.exe (PID: 1256)
- SetupUtility.exe (PID: 2320)
- aspnet_regiis.exe (PID: 3416)
- ServiceModelReg.exe (PID: 3672)
- ngen.exe (PID: 1464)
- mscorsvw.exe (PID: 1768)
- ngen.exe (PID: 1492)
- ngen.exe (PID: 3284)
- mscorsvw.exe (PID: 3024)
- regtlibv12.exe (PID: 3932)
- regtlibv12.exe (PID: 2912)
- regtlibv12.exe (PID: 2720)
- regtlibv12.exe (PID: 1540)
- regtlibv12.exe (PID: 1120)
- regtlibv12.exe (PID: 2084)
- regtlibv12.exe (PID: 1692)
Actions looks like stealing of personal data
- ndp48-web (1).exe (PID: 576)
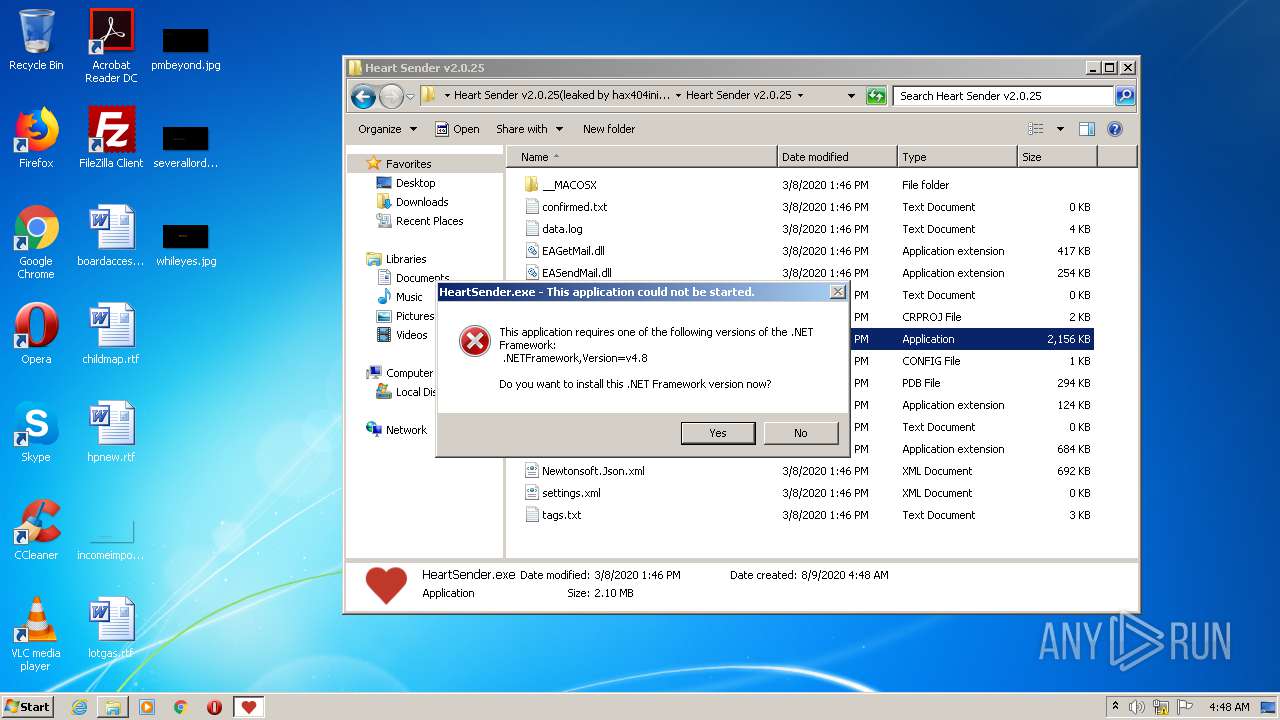
Loads dropped or rewritten executable
- Setup.exe (PID: 3208)
- wmiprvse.exe (PID: 1456)
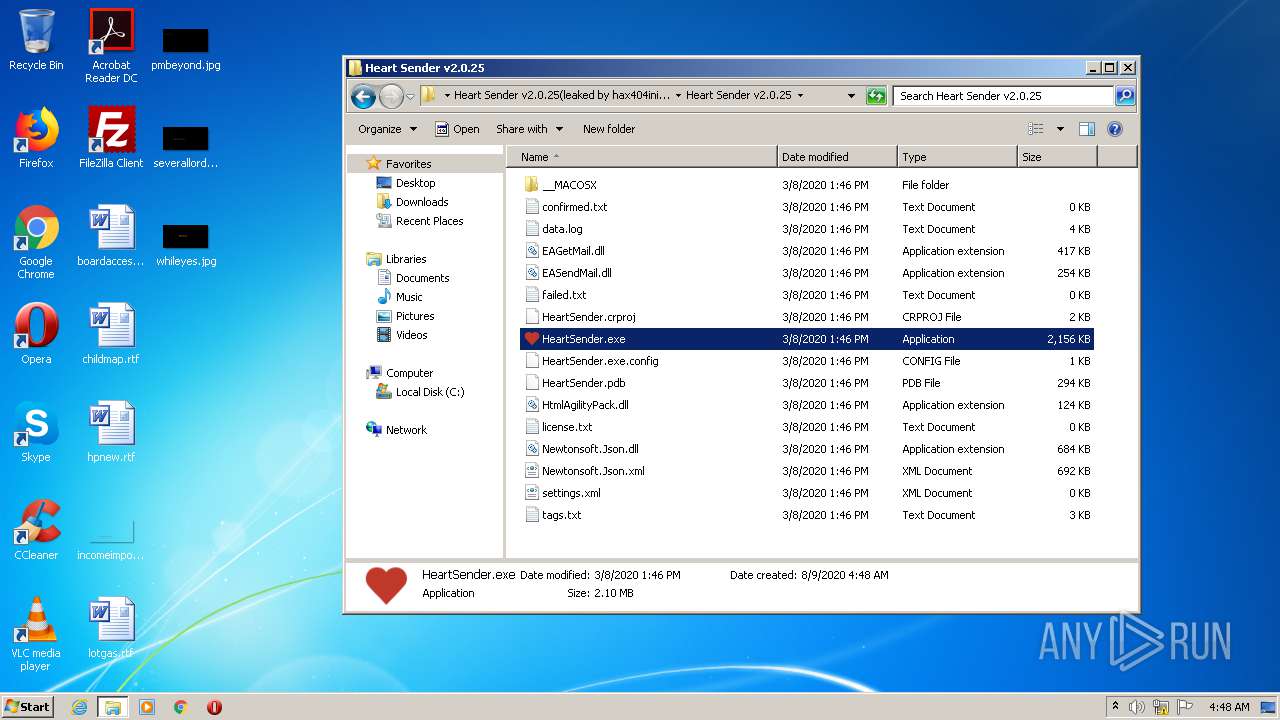
- HeartSender.exe (PID: 2332)
- HeartSender.exe (PID: 2420)
- svchost.exe (PID: 780)
- ngen.exe (PID: 1464)
- mscorsvw.exe (PID: 1768)
- ngen.exe (PID: 1492)
- ngen.exe (PID: 3284)
- mscorsvw.exe (PID: 3024)
Changes settings of System certificates
- Setup.exe (PID: 3208)
Loads the Task Scheduler COM API
- ngen.exe (PID: 1464)
- mscorsvw.exe (PID: 1768)
- ngen.exe (PID: 1492)
- ngen.exe (PID: 3284)
SUSPICIOUS
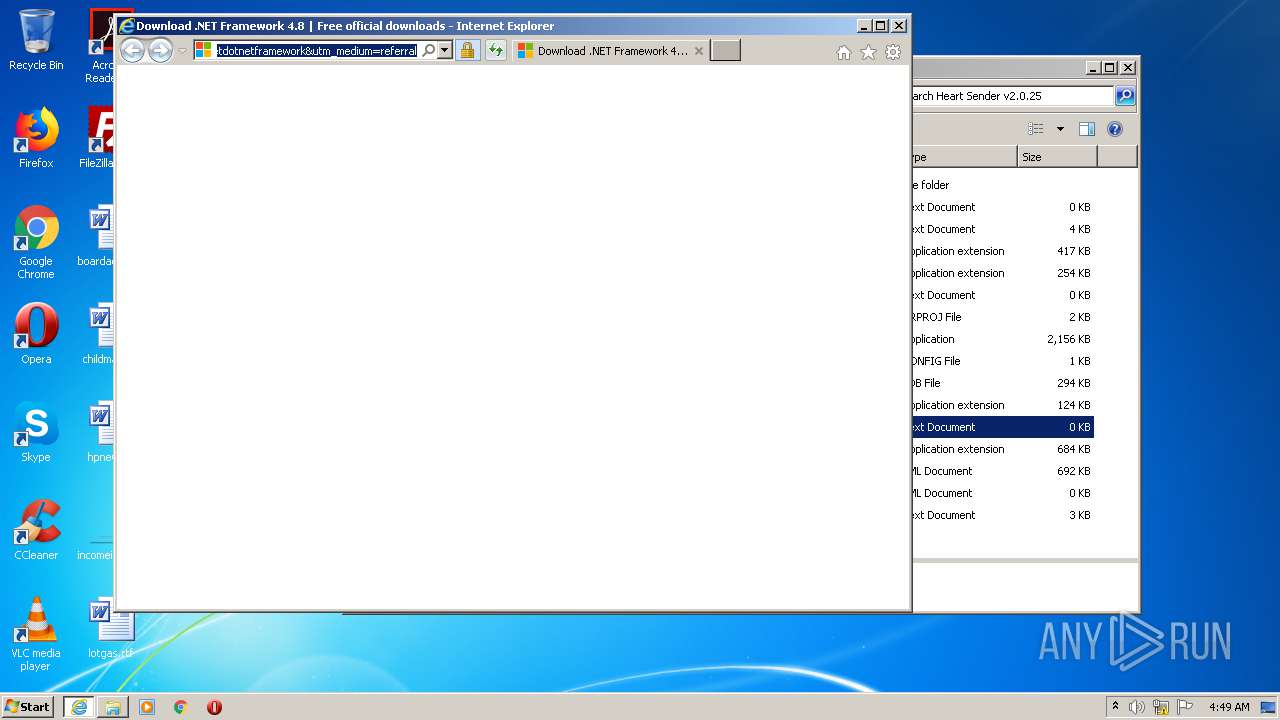
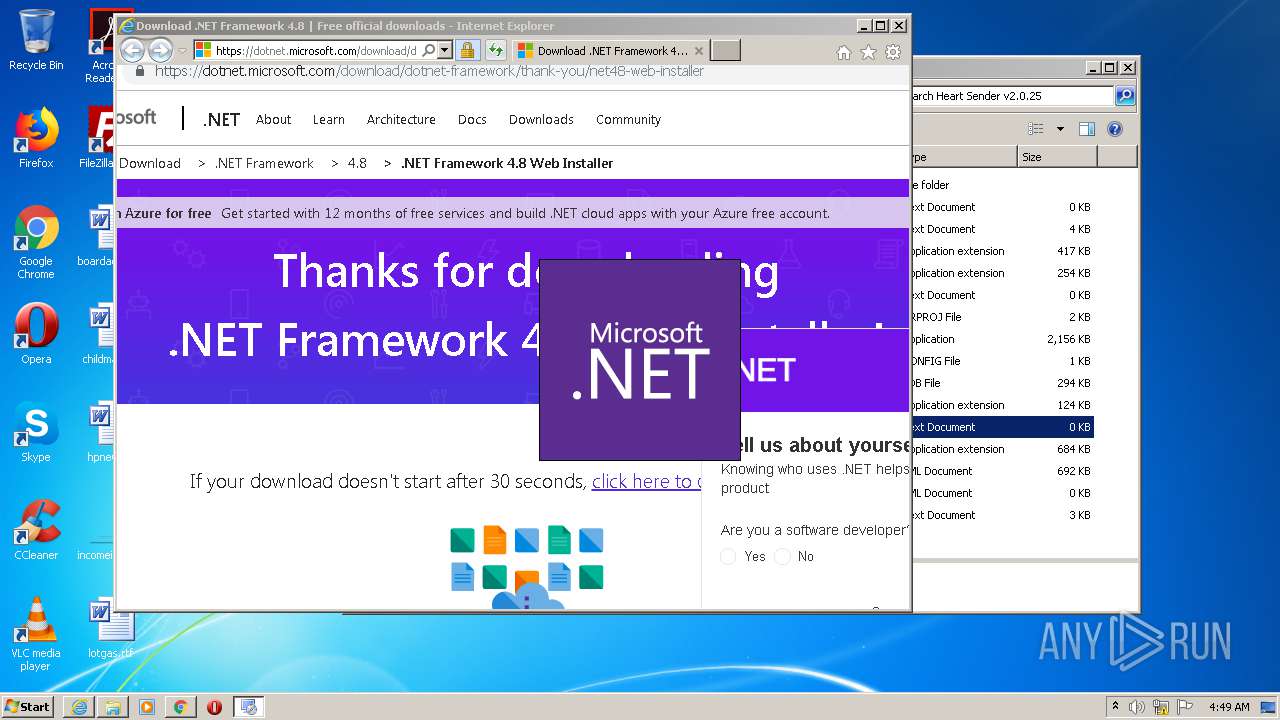
Starts Internet Explorer
- HeartSender.exe (PID: 2420)
- HeartSender.exe (PID: 2332)
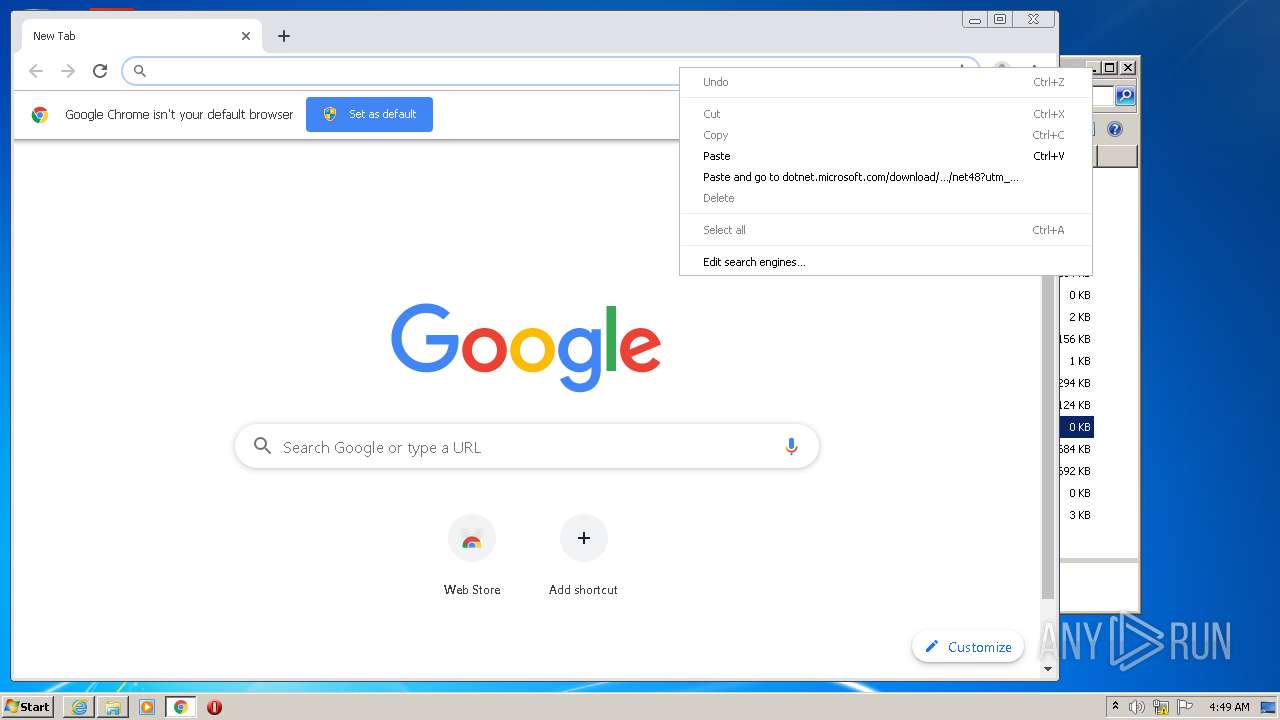
Executable content was dropped or overwritten
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3904)
- ndp48-web (1).exe (PID: 576)
- TMP8D07.tmp.exe (PID: 960)
- Setup.exe (PID: 3208)
- msiexec.exe (PID: 3508)
Adds / modifies Windows certificates
- Setup.exe (PID: 3208)
Reads Internet Cache Settings
- Setup.exe (PID: 3208)
Creates COM task schedule object
- msiexec.exe (PID: 3508)
- aspnet_regiis.exe (PID: 3416)
Changes the autorun value in the registry
- msiexec.exe (PID: 3508)
Removes files from Windows directory
- msiexec.exe (PID: 3508)
- lodctr.exe (PID: 1940)
- lodctr.exe (PID: 1012)
- aspnet_regiis.exe (PID: 3416)
- lodctr.exe (PID: 560)
- lodctr.exe (PID: 956)
- lodctr.exe (PID: 1352)
Creates files in the Windows directory
- aspnet_regiis.exe (PID: 3416)
- lodctr.exe (PID: 1940)
- ngen.exe (PID: 1464)
- msiexec.exe (PID: 3508)
- lodctr.exe (PID: 956)
- lodctr.exe (PID: 1012)
- lodctr.exe (PID: 1352)
- lodctr.exe (PID: 560)
- ngen.exe (PID: 3284)
- mscorsvw.exe (PID: 1768)
- ngen.exe (PID: 1492)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 3844)
- iexplore.exe (PID: 2768)
- chrome.exe (PID: 3460)
Reads internet explorer settings
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 2768)
Changes internet zones settings
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 3844)
Application launched itself
- iexplore.exe (PID: 3072)
- chrome.exe (PID: 1480)
- iexplore.exe (PID: 3844)
- chrome.exe (PID: 3460)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 3844)
Reads settings of System Certificates
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2768)
- chrome.exe (PID: 3904)
- iexplore.exe (PID: 3844)
- Setup.exe (PID: 3208)
- msiexec.exe (PID: 3508)
Changes settings of System certificates
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 3844)
Manual execution by user
- chrome.exe (PID: 1480)
- HeartSender.exe (PID: 2332)
- HeartSender.exe (PID: 2420)
- chrome.exe (PID: 3460)
Reads the hosts file
- chrome.exe (PID: 2940)
- chrome.exe (PID: 1480)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3904)
Creates files in the user directory
- iexplore.exe (PID: 2768)
- iexplore.exe (PID: 3844)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3072)
- msiexec.exe (PID: 3508)
- mscorsvw.exe (PID: 1768)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3912)
- MsiExec.exe (PID: 3404)
- msiexec.exe (PID: 3508)
Creates a software uninstall entry
- msiexec.exe (PID: 3508)
Creates or modifies windows services
- msiexec.exe (PID: 3508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
141
Monitored processes
76
Malicious processes
15
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1396078812274251795,8840982537346803278,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4609803446949102658 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1396078812274251795,8840982537346803278,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12054954574990624951 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 560 | "C:\Windows\system32\lodctr.exe" C:\Windows\Microsoft.NET\Framework\v4.0.30319\_Networkingperfcounters.ini | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
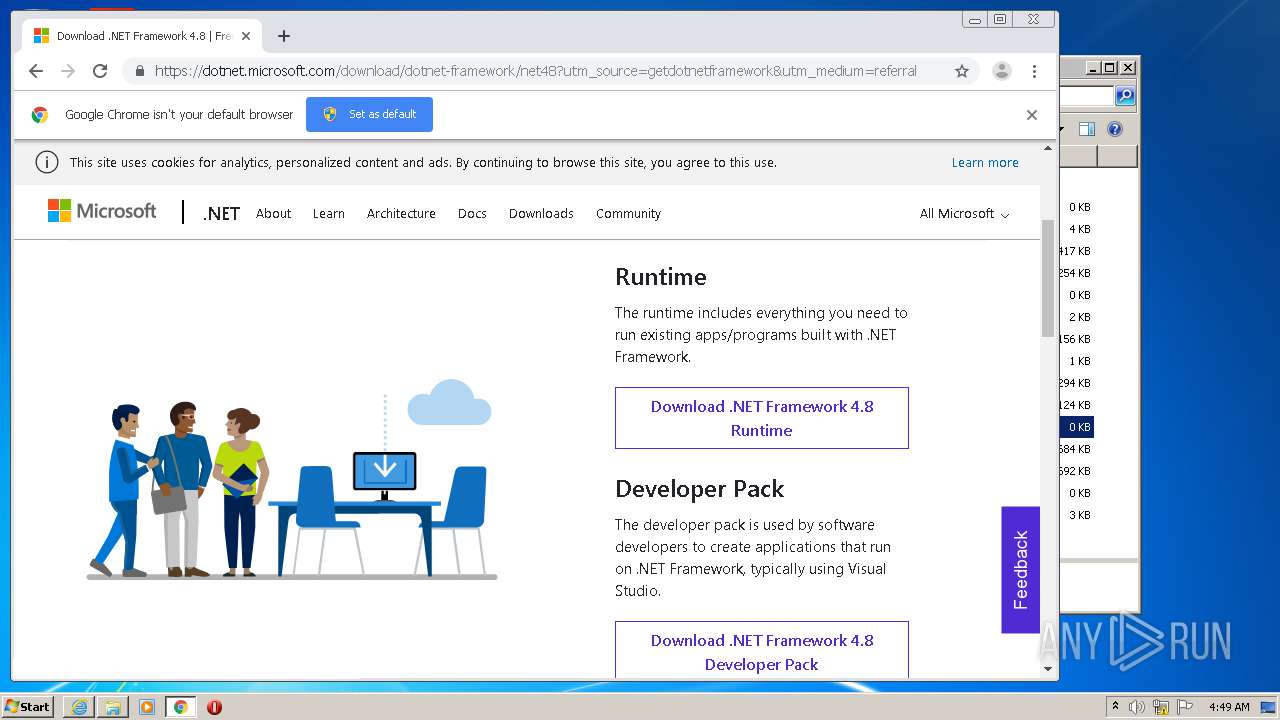
| 576 | "C:\Users\admin\Downloads\ndp48-web (1).exe" | C:\Users\admin\Downloads\ndp48-web (1).exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.03928.00 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1396078812274251795,8840982537346803278,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3970900493156501362 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,12177996723983127000,16002215231761166009,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16583816471410000428 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 772 | "C:\Windows\system32\wbem\mofcomp.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MOF\ServiceModel.mof" | C:\Windows\system32\wbem\mofcomp.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 780 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1396078812274251795,8840982537346803278,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3012947213901407251 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Windows\system32\lodctr.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\_TransactionBridgePerfCounters.ini" | C:\Windows\system32\lodctr.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Load PerfMon Counters Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
32 505
Read events
15 859
Write events
14 251
Delete events
2 395
Modification events
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Heart Sender v2.0.25(leaked by hax404ini3t404).rar | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2348) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1 835
Suspicious files
162
Text files
666
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
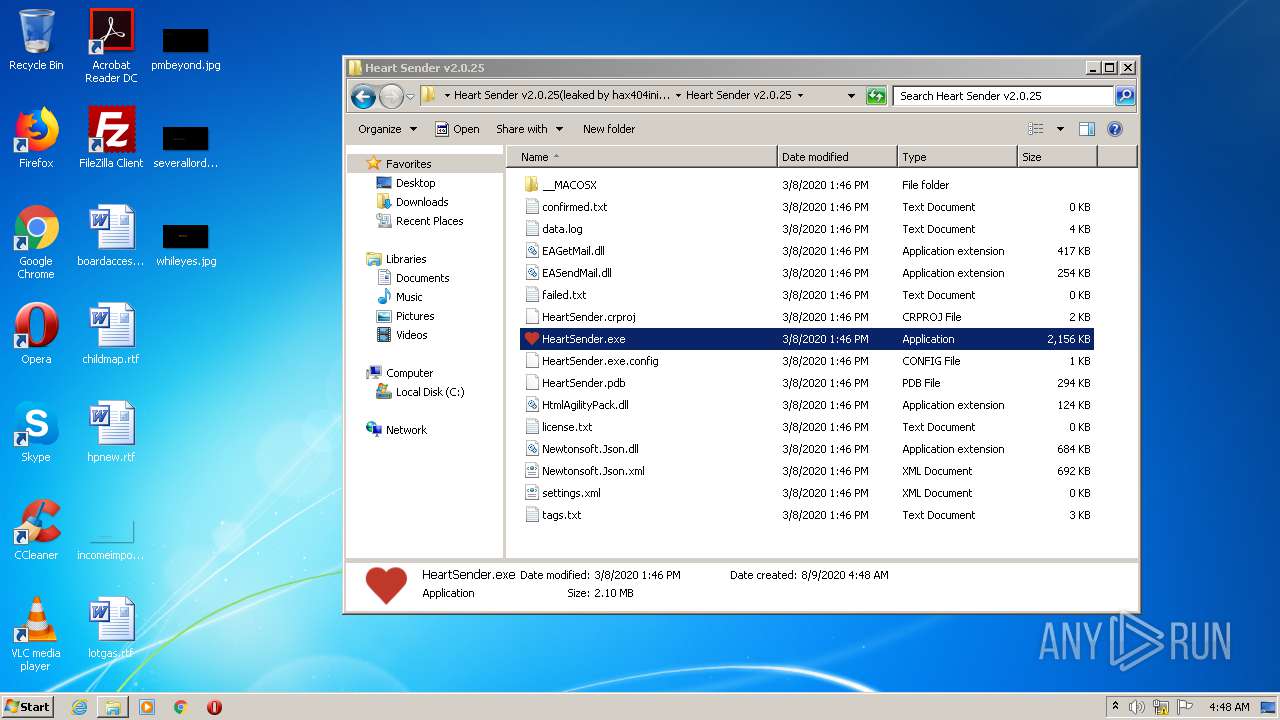
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\data.log | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\EAGetMail.dll | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\EASendMail.dll | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\HeartSender.crproj | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\HeartSender.exe | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\HeartSender.exe.config | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\HeartSender.pdb | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\HtmlAgilityPack.dll | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 2348 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2348.22451\Heart Sender v2.0.25(leaked by hax404ini3t404)\Heart Sender v2.0.25\Newtonsoft.Json.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
107
DNS requests
67
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
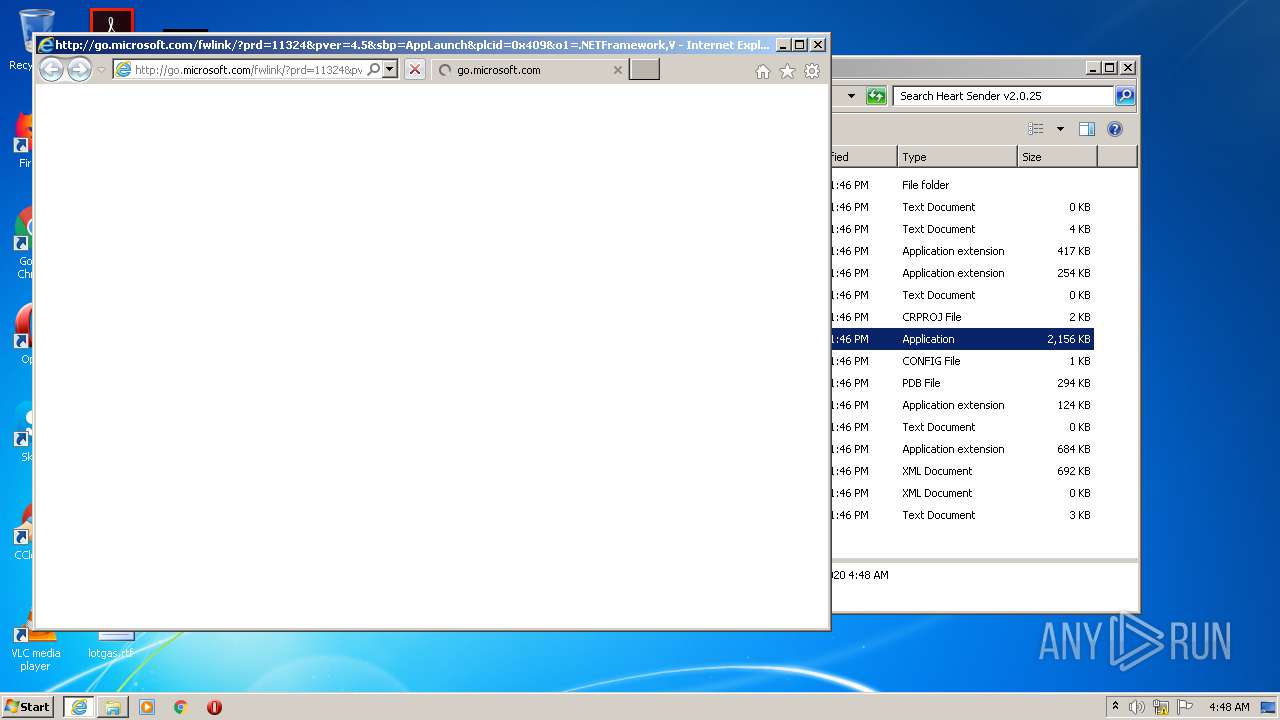
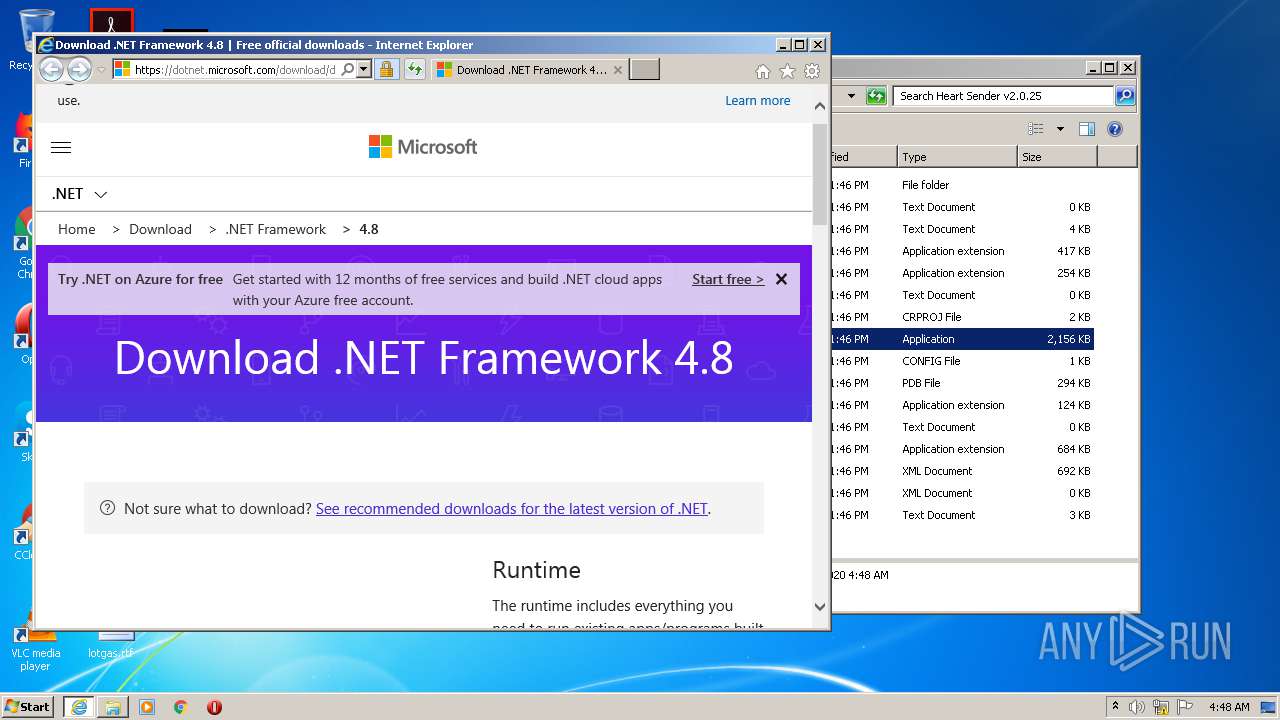
1704 | iexplore.exe | GET | 302 | 104.111.238.86:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.8&processName=HeartSender.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.0 | NL | — | — | whitelisted |
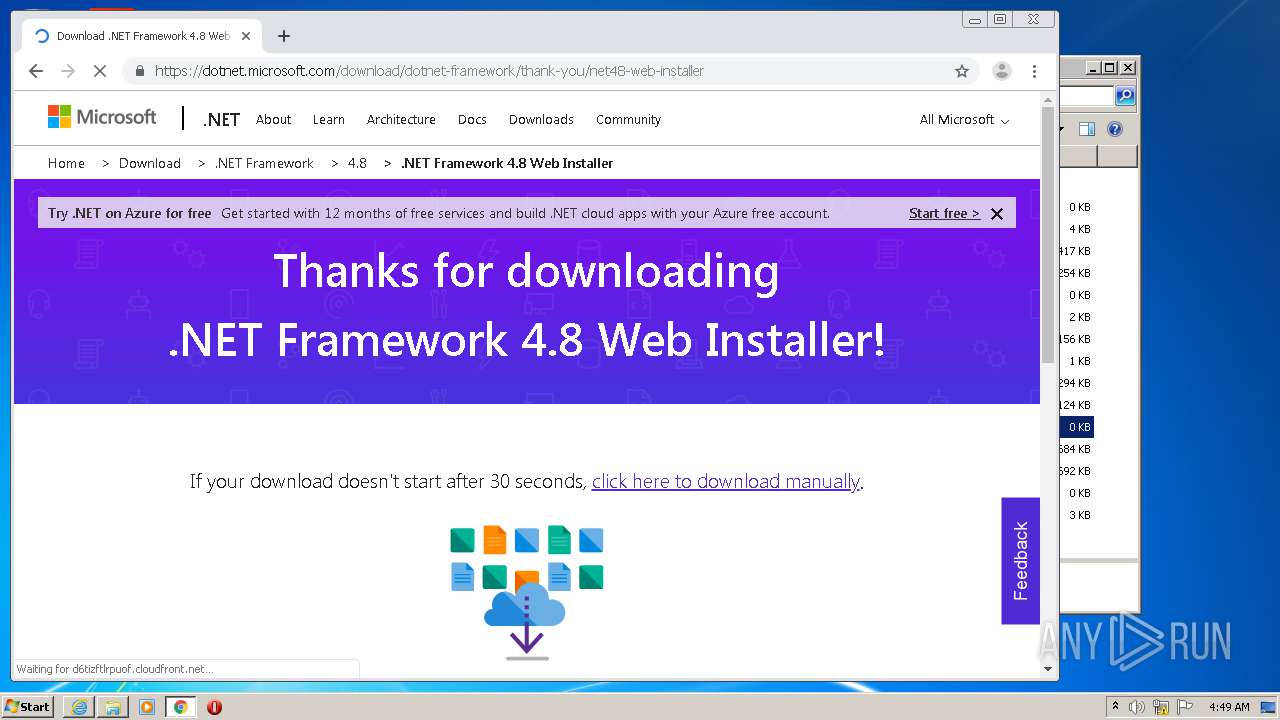
3904 | chrome.exe | GET | 302 | 104.111.238.86:80 | http://go.microsoft.com/fwlink/?LinkId=2085155 | NL | — | — | whitelisted |
3904 | chrome.exe | GET | 302 | 104.111.238.86:80 | http://go.microsoft.com/fwlink/?LinkId=2085155 | NL | — | — | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1704 | iexplore.exe | GET | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtb9ltrp%2FvQiykNkEU33uA%3D | US | der | 471 b | whitelisted |
1704 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | iexplore.exe | 104.111.238.86:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
1704 | iexplore.exe | 104.111.238.86:443 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
1704 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1704 | iexplore.exe | 13.107.246.10:443 | dotnet.microsoft.com | Microsoft Corporation | US | whitelisted |
1704 | iexplore.exe | 2.18.233.62:443 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
1704 | iexplore.exe | 2.16.186.32:443 | statics-marketingsites-wcus-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
1704 | iexplore.exe | 2.16.186.27:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
1704 | iexplore.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1704 | iexplore.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1704 | iexplore.exe | 152.199.21.175:443 | az416426.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
az416426.vo.msecnd.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |