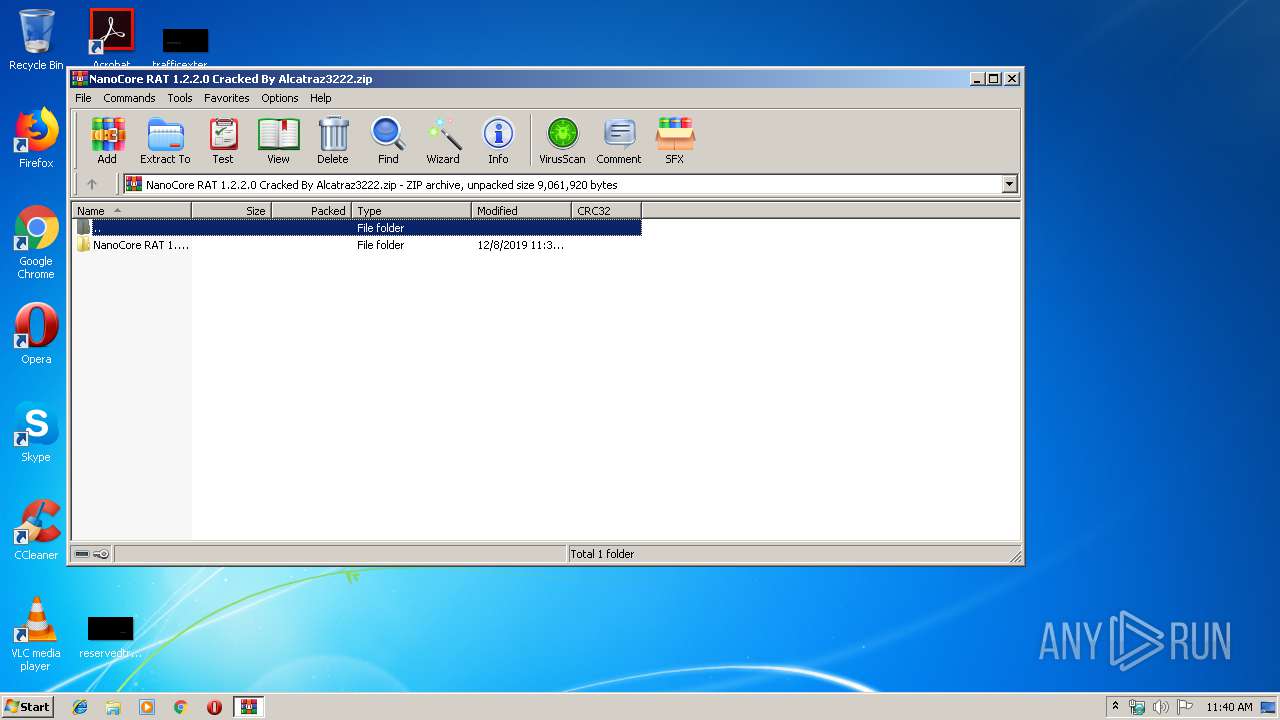
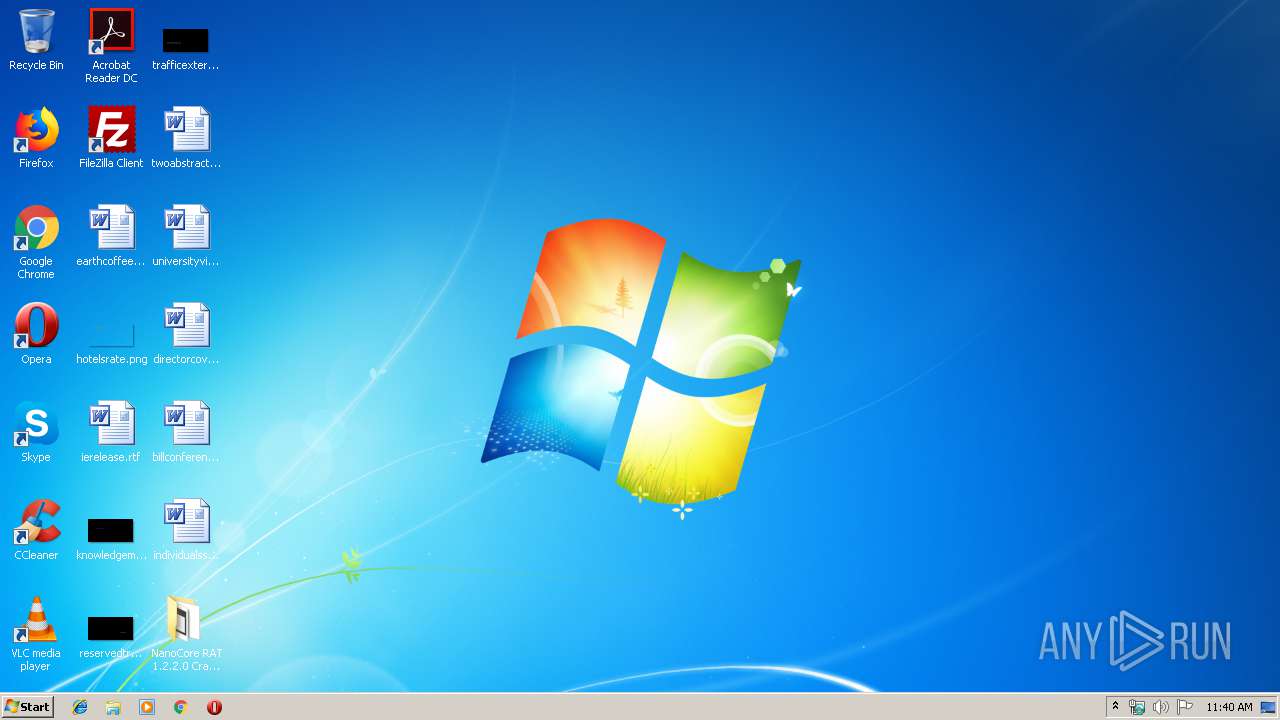
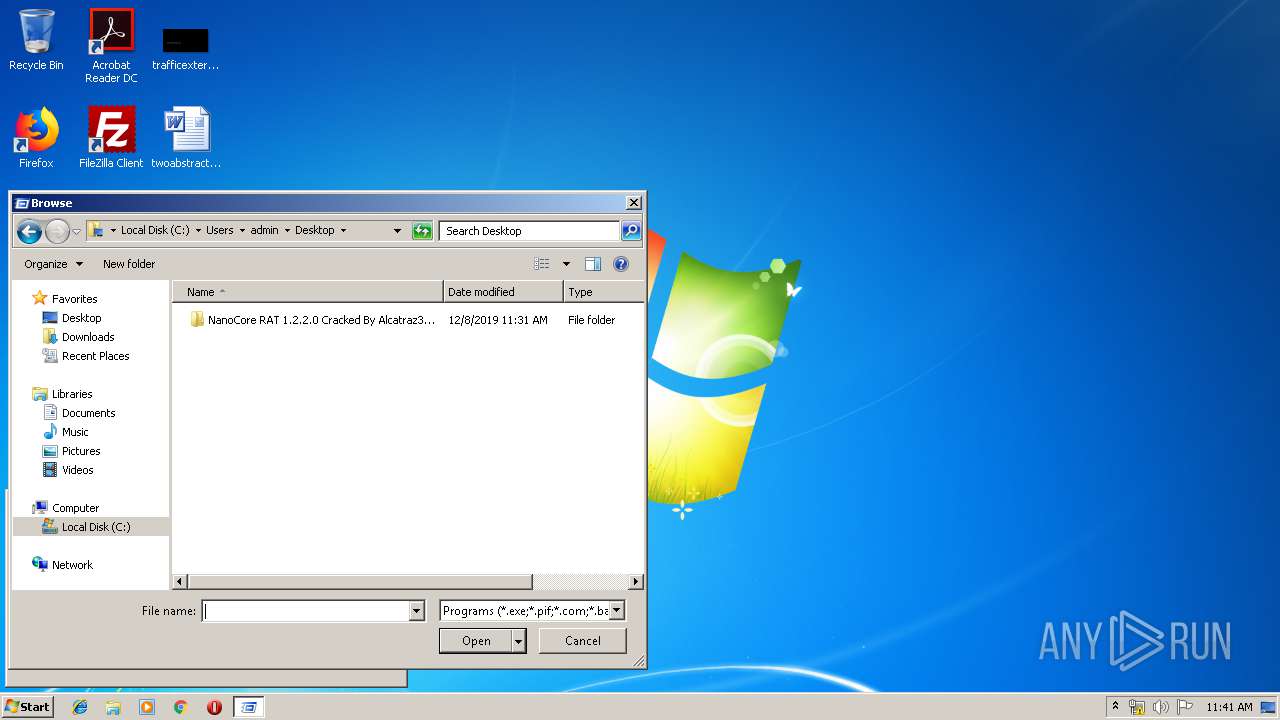
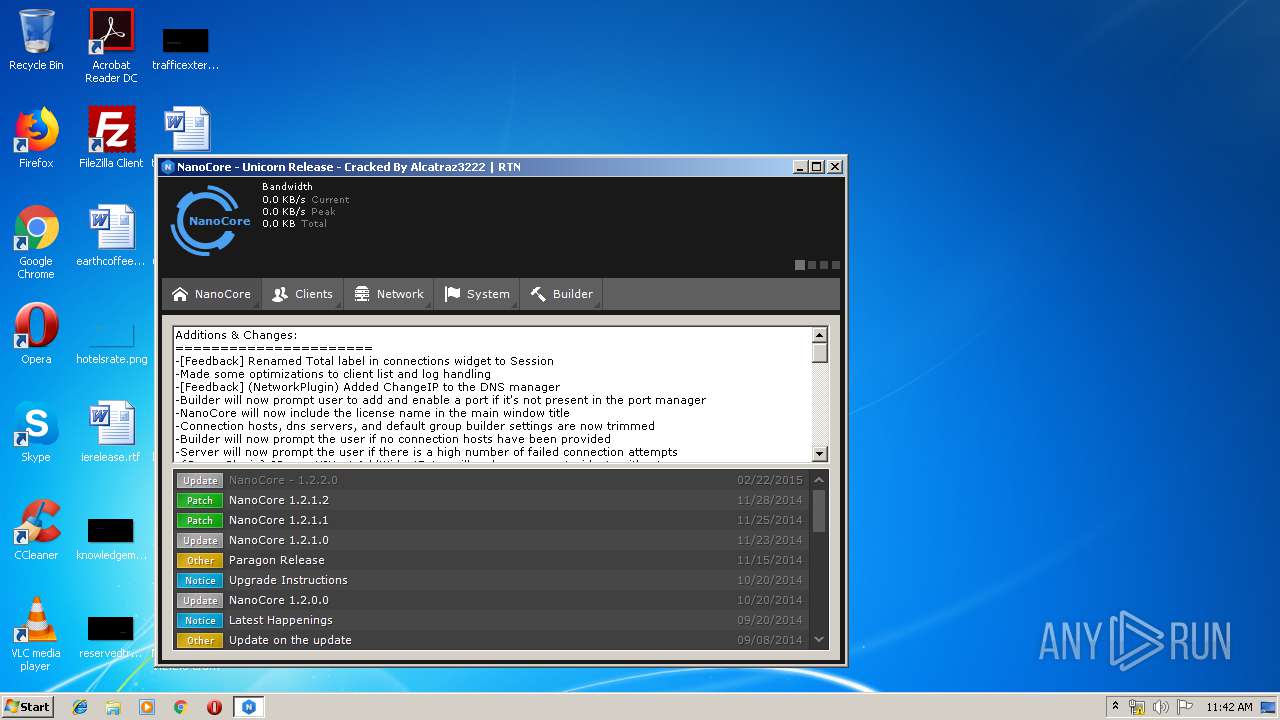
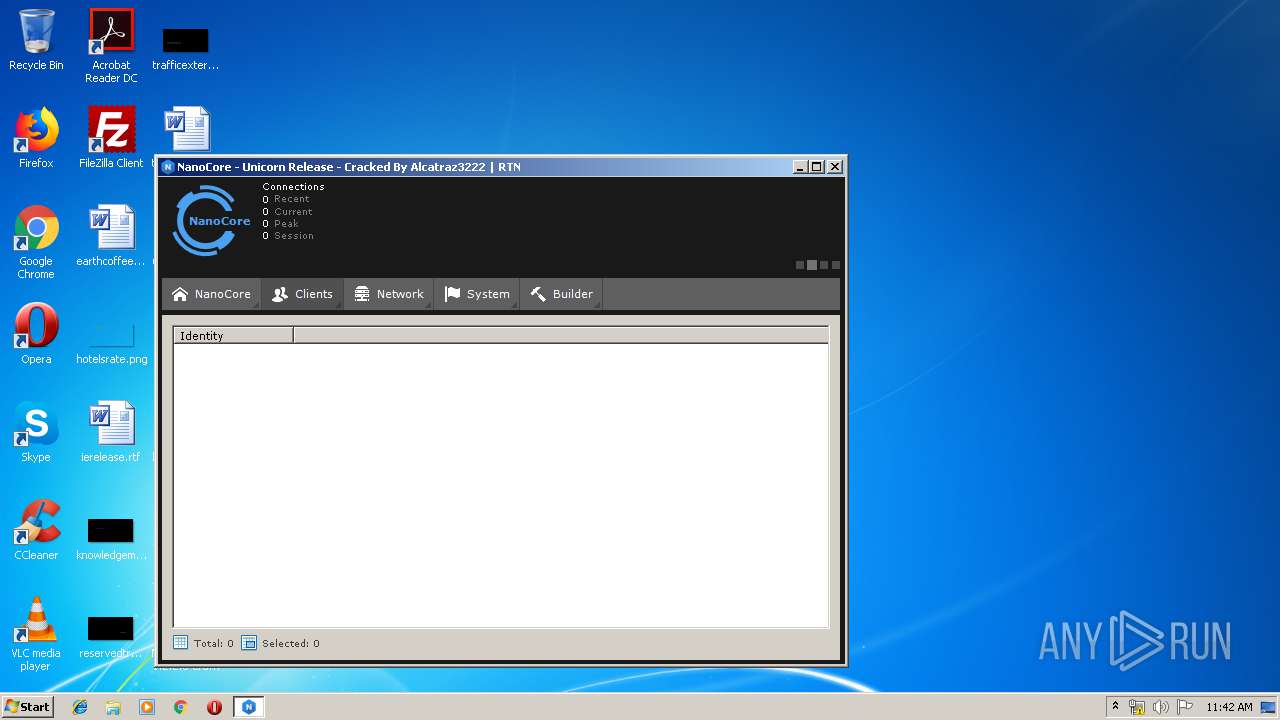
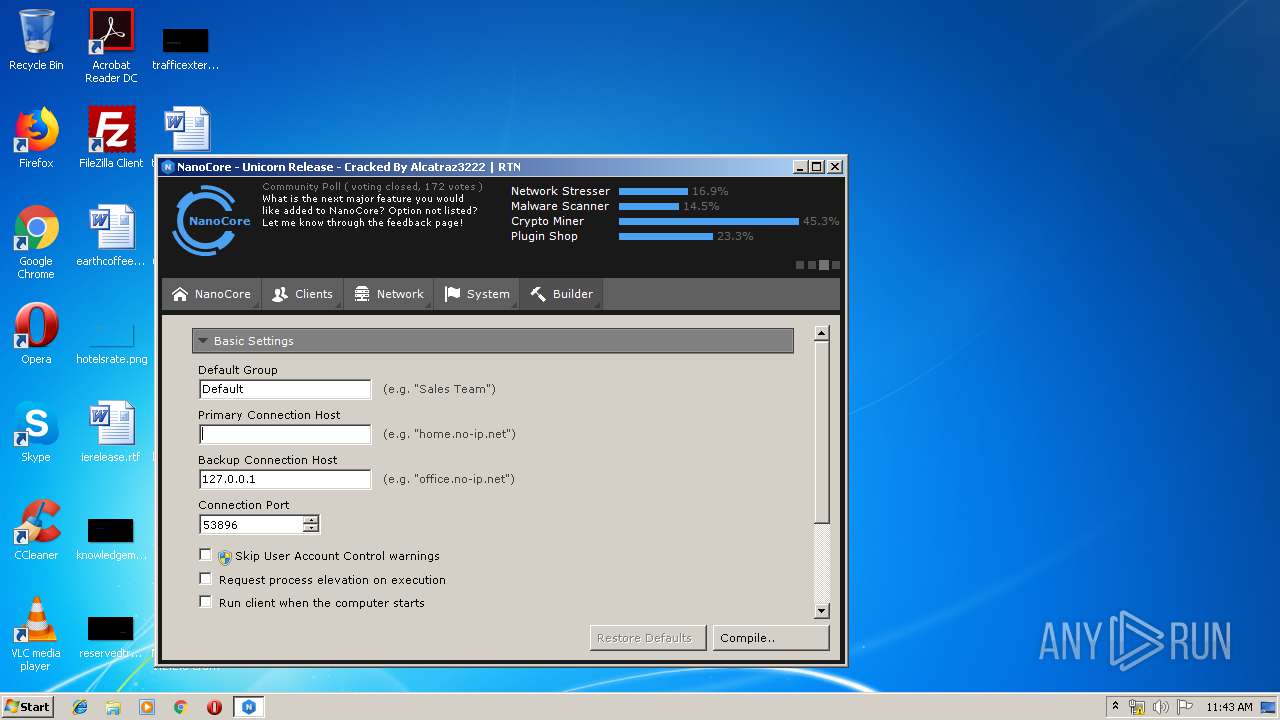
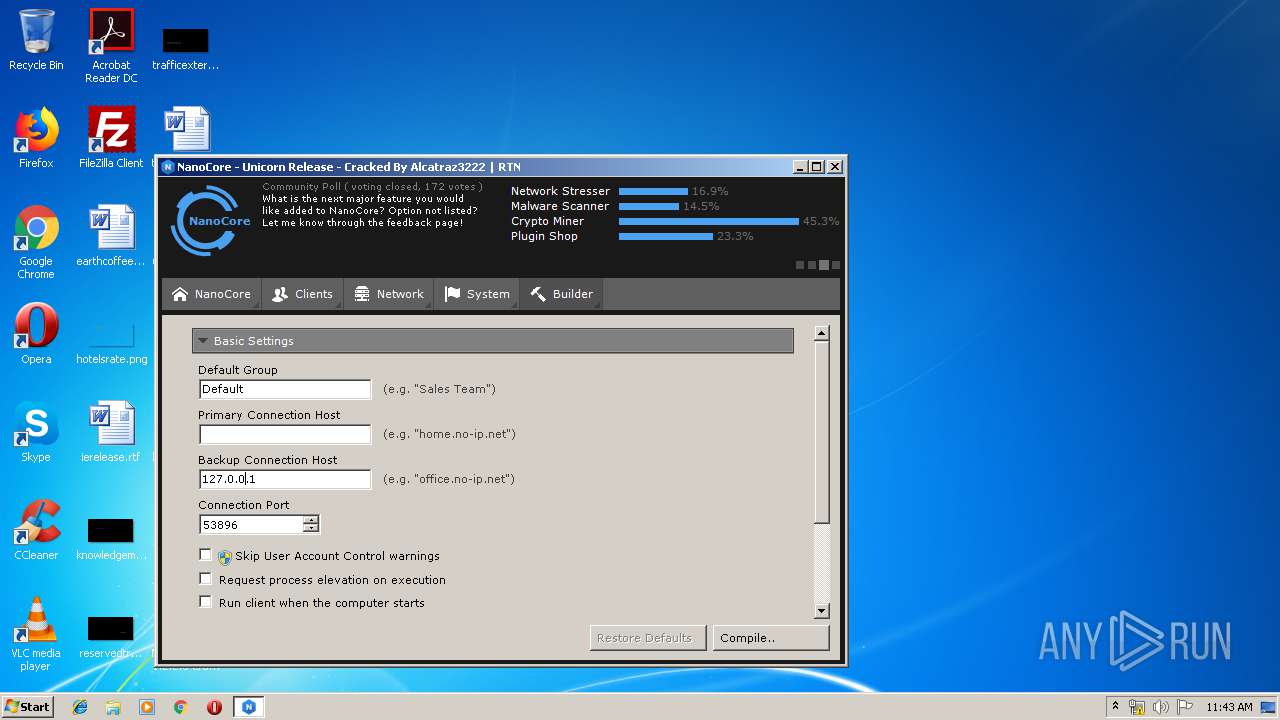
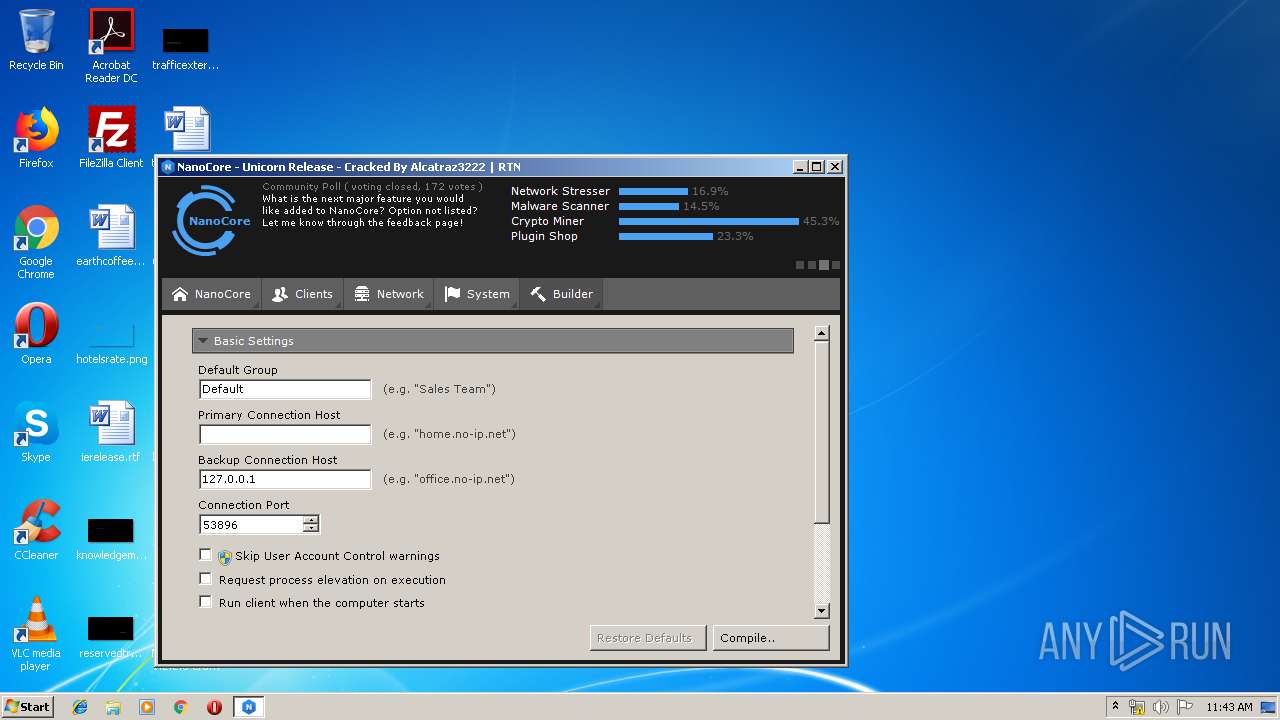
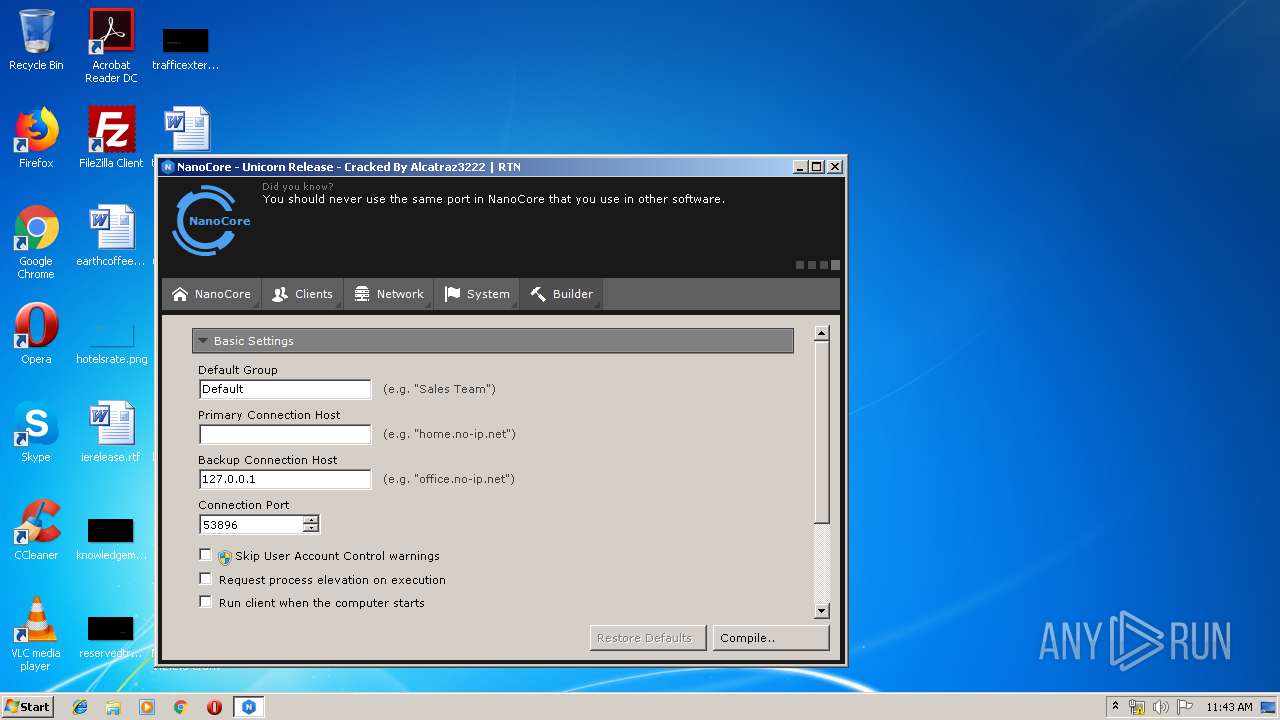
| File name: | NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222.zip |
| Full analysis: | https://app.any.run/tasks/1b83628e-da40-407b-b776-a307d694c945 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2019, 11:39:55 |
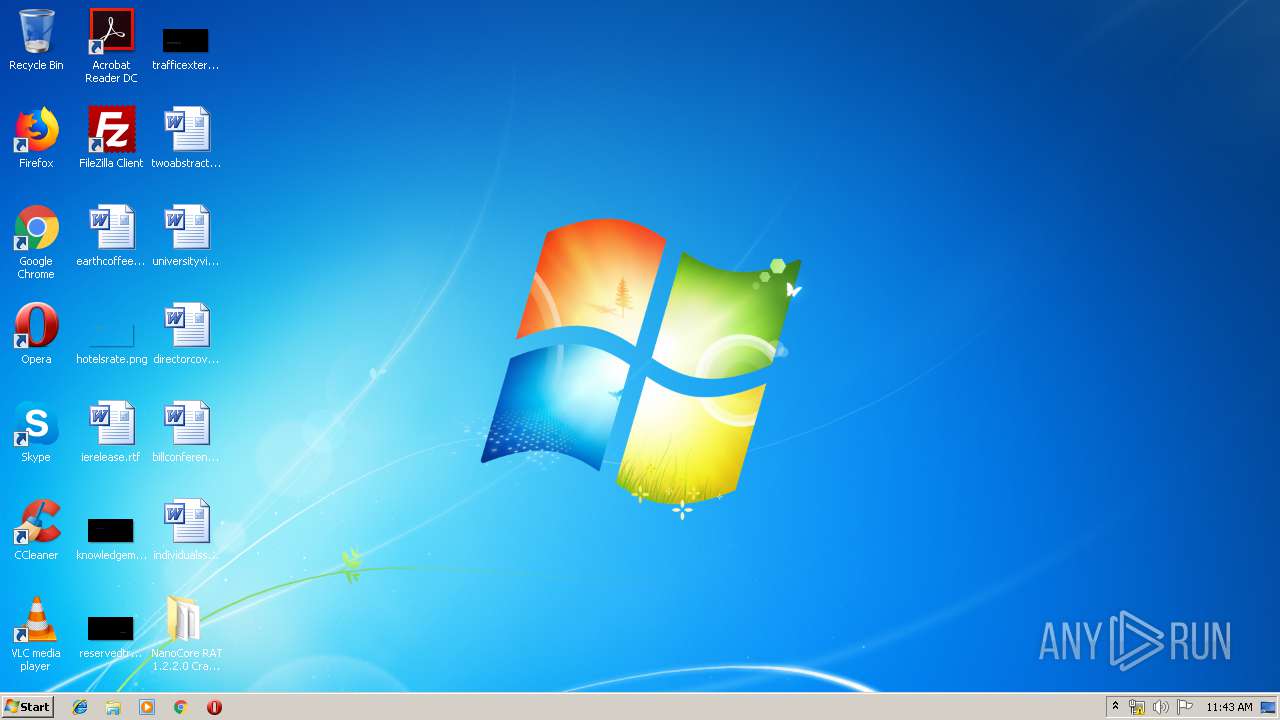
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 3E0D187FE72645BFAA36F24E5A4D5628 |
| SHA1: | 436EA5F547A7DB373E089811636688D7375BB3E9 |
| SHA256: | 4673160318A197B6FCFC68462CCF1645C93B6EC34DBE8B7BDFE8EEB898AB7085 |
| SSDEEP: | 98304:C4hXhlsPxTGDVZdnV1dmR4joXmrvbbZxJCjQzzm/QDwFZb3nI12gfDY7yDzcbzqZ:fhxeAfdnzdmRfubIjA3k7zI1jrYODzvZ |
MALICIOUS
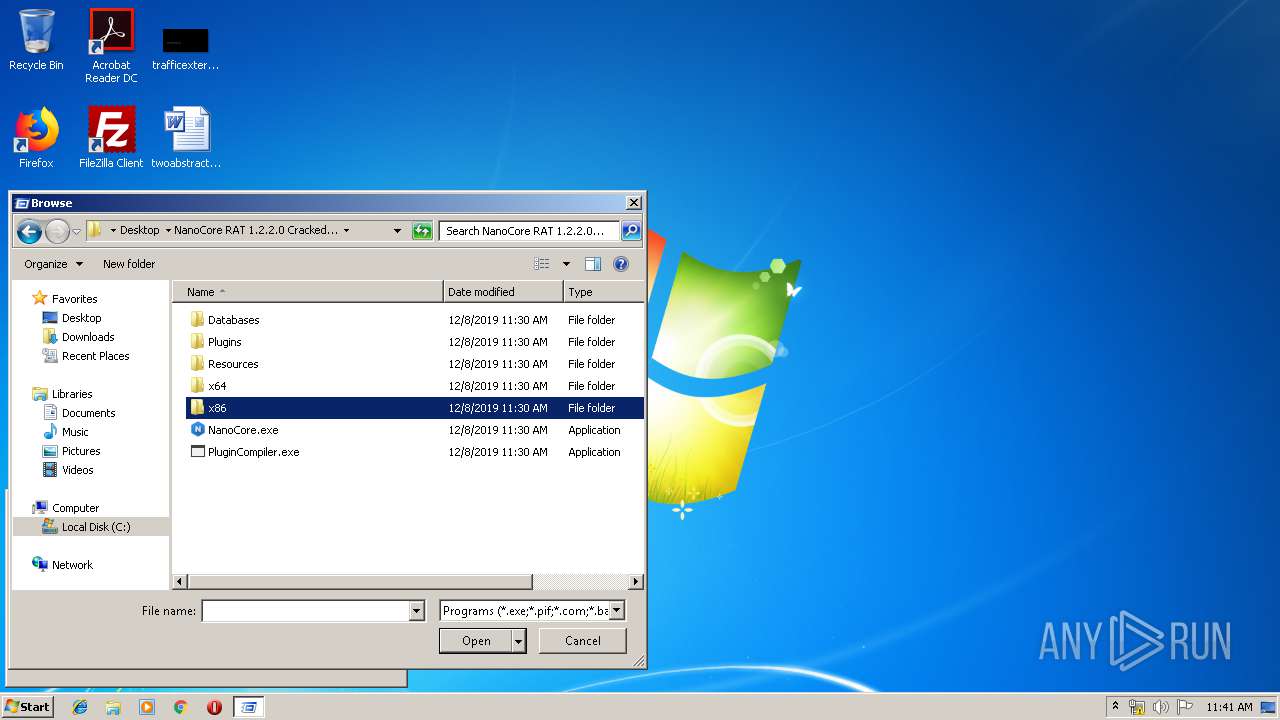
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3148)
- NanoCore.exe (PID: 3680)
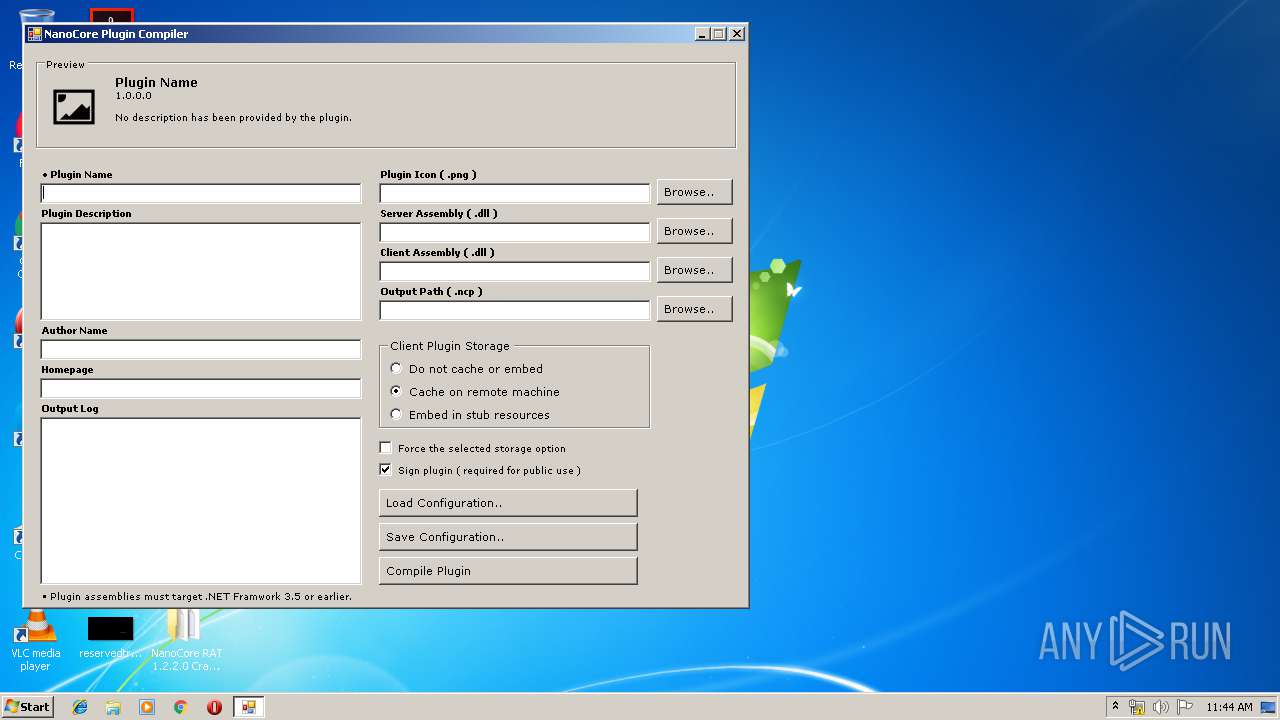
- PluginCompiler.exe (PID: 3540)
Application was dropped or rewritten from another process
- NanoCore.exe (PID: 3680)
- PluginCompiler.exe (PID: 3540)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2764)
Checks for external IP
- NanoCore.exe (PID: 3680)
INFO
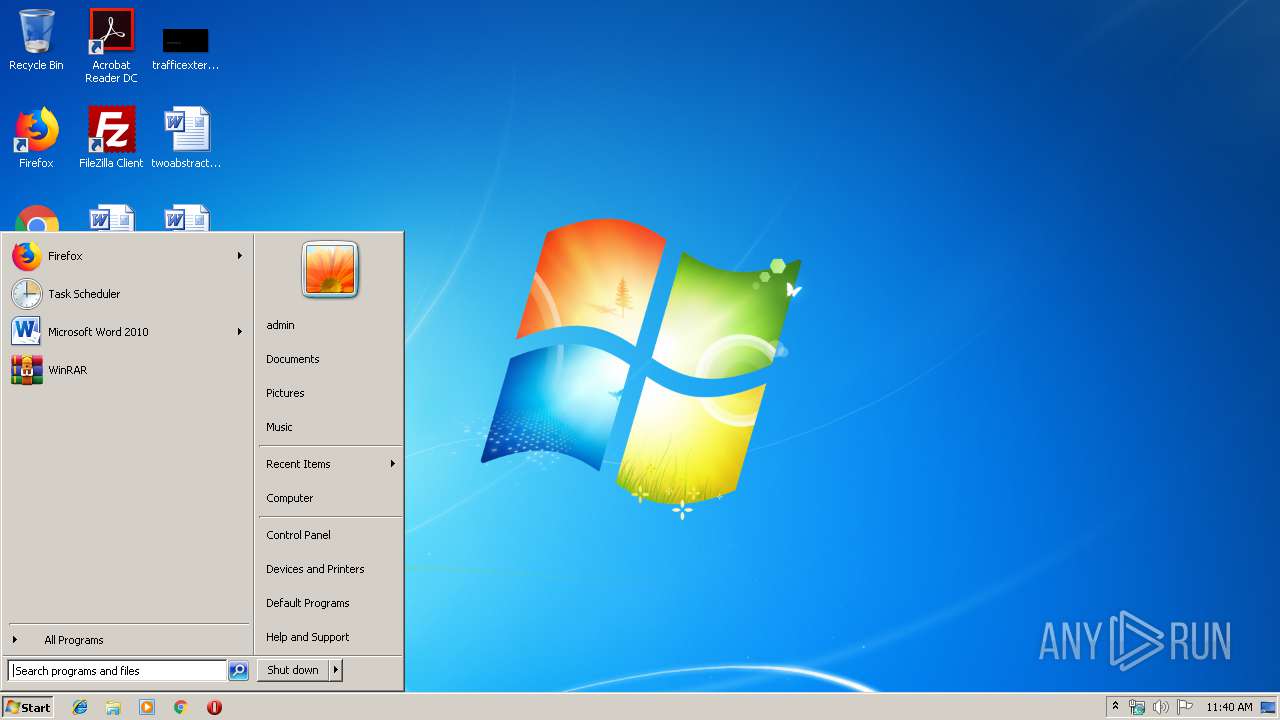
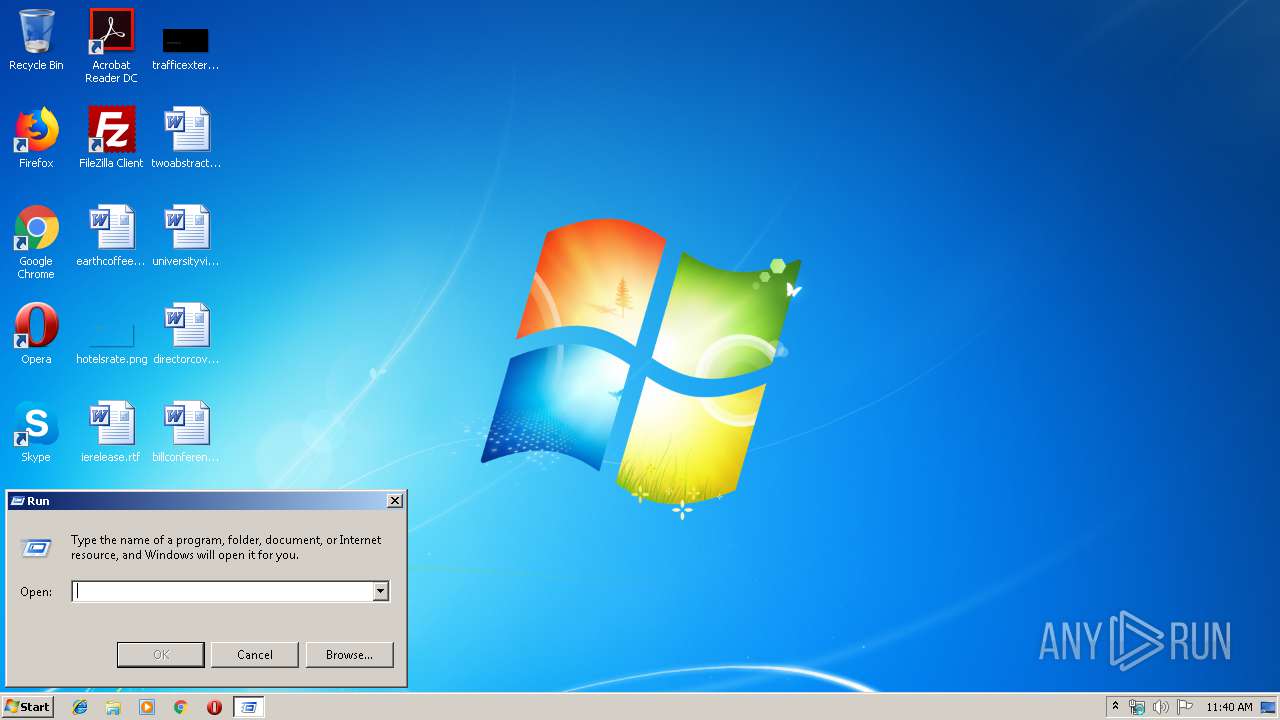
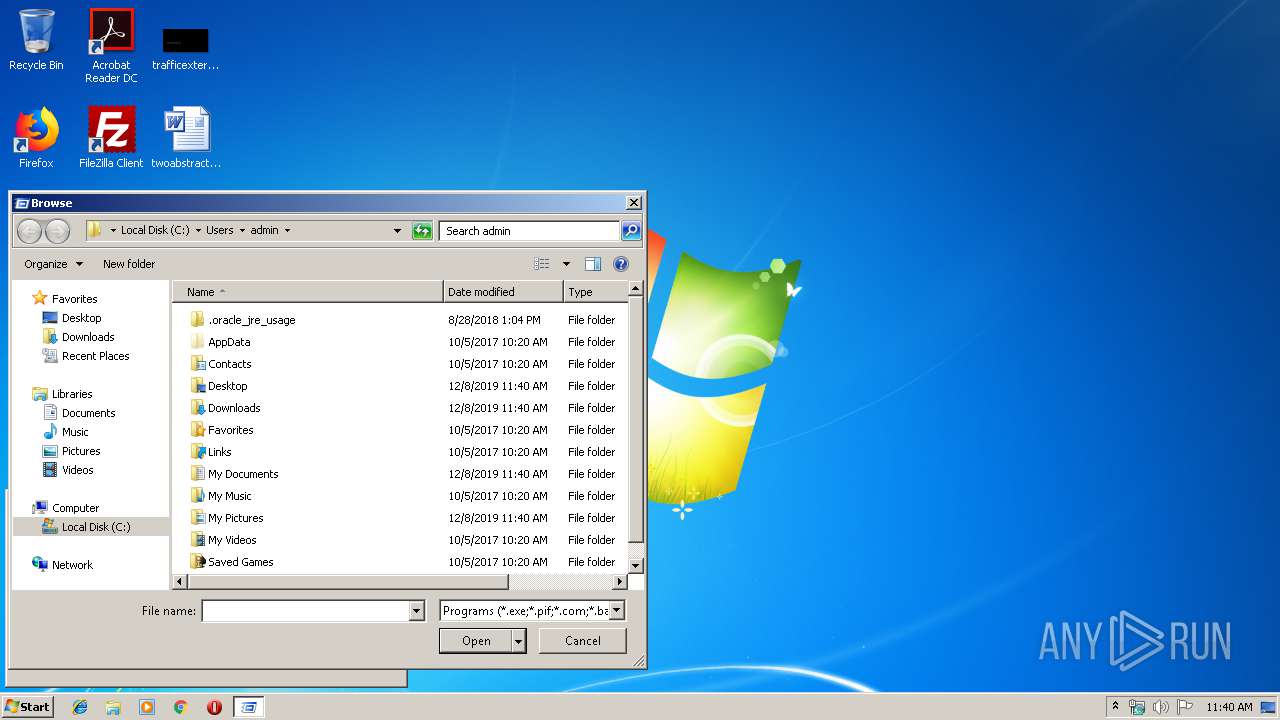
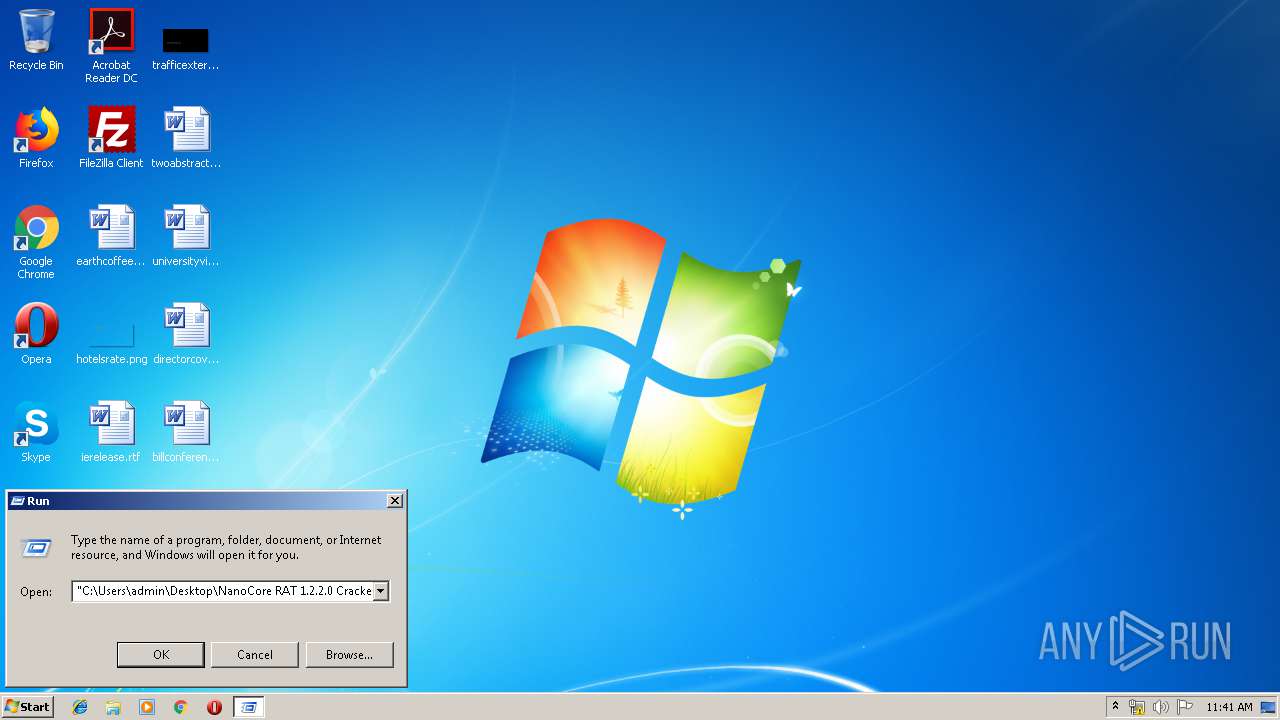
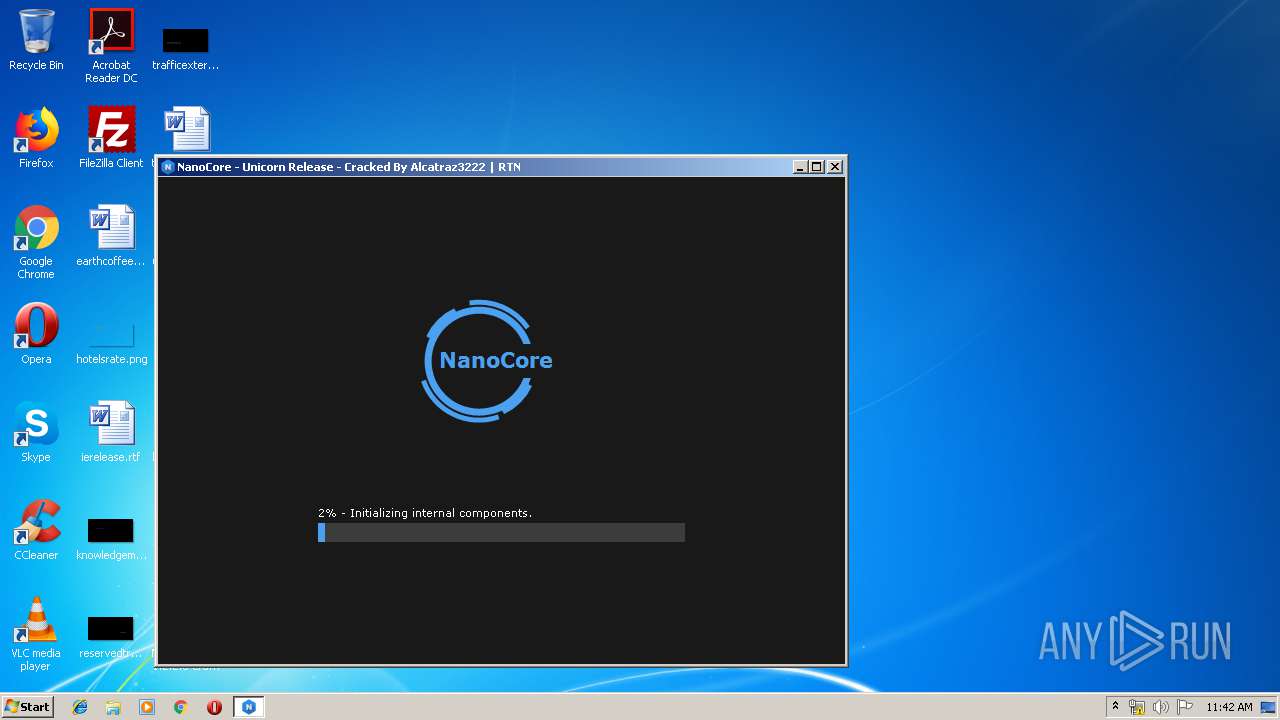
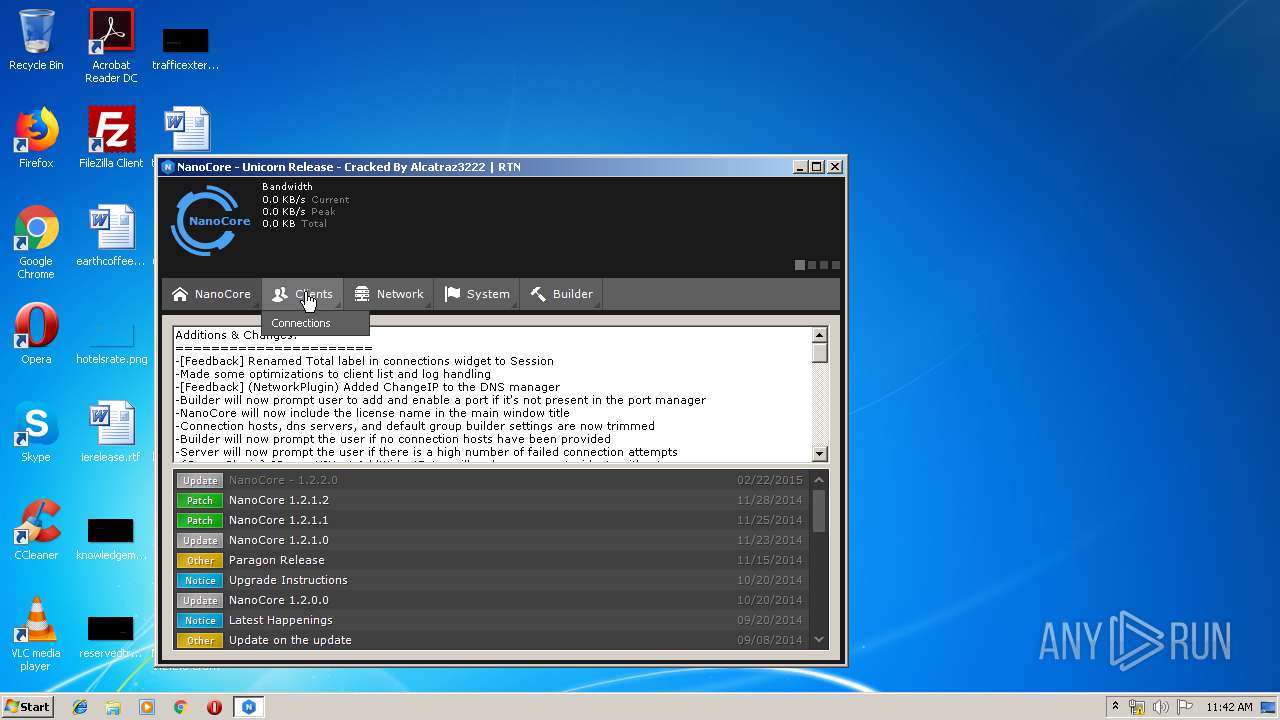
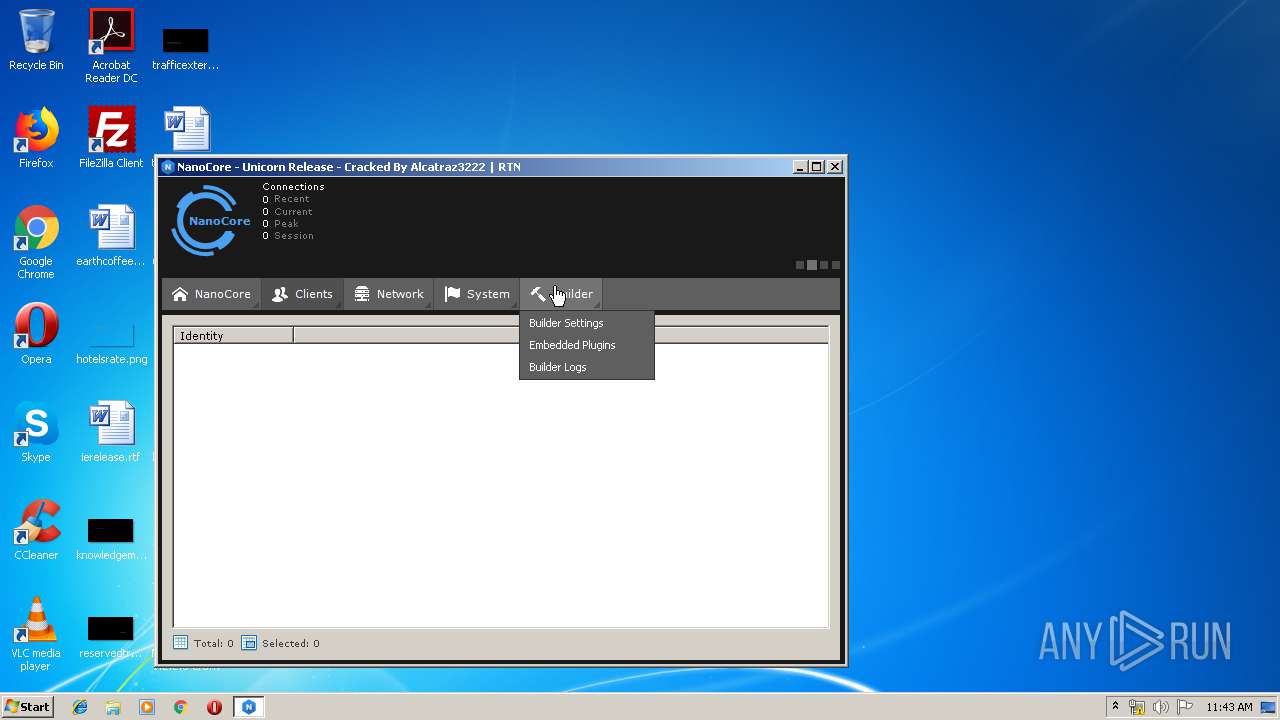
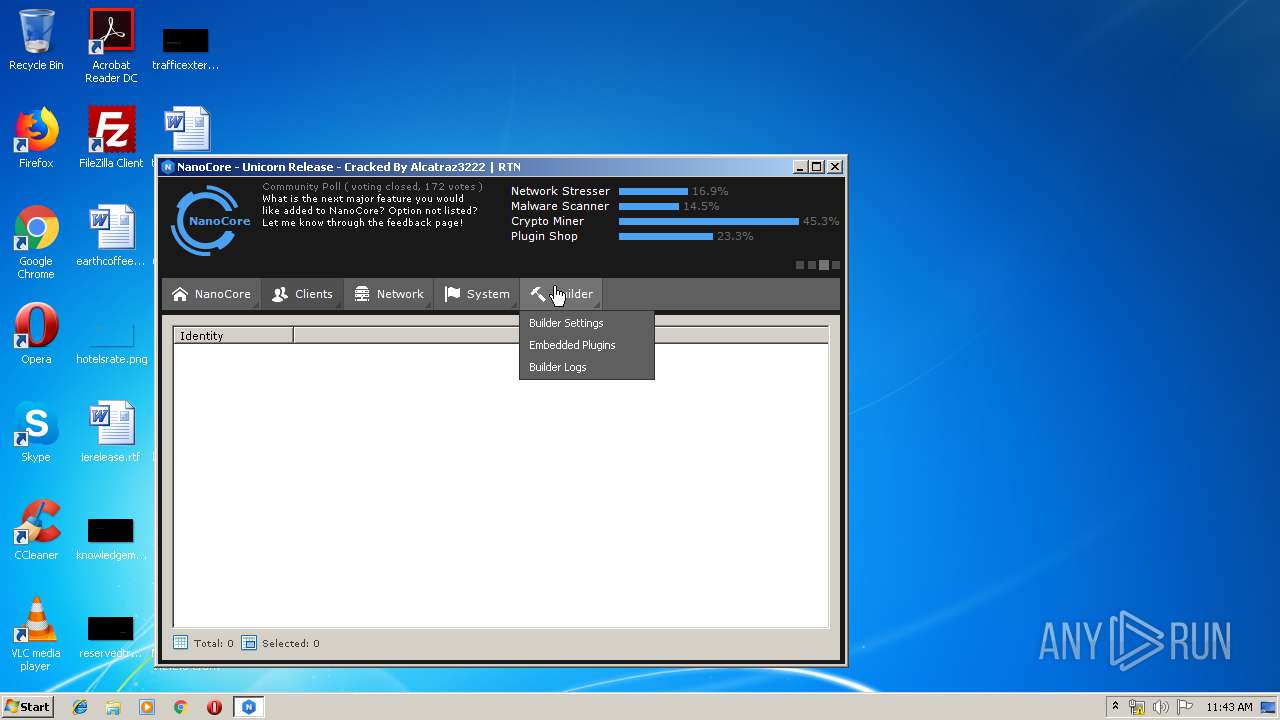
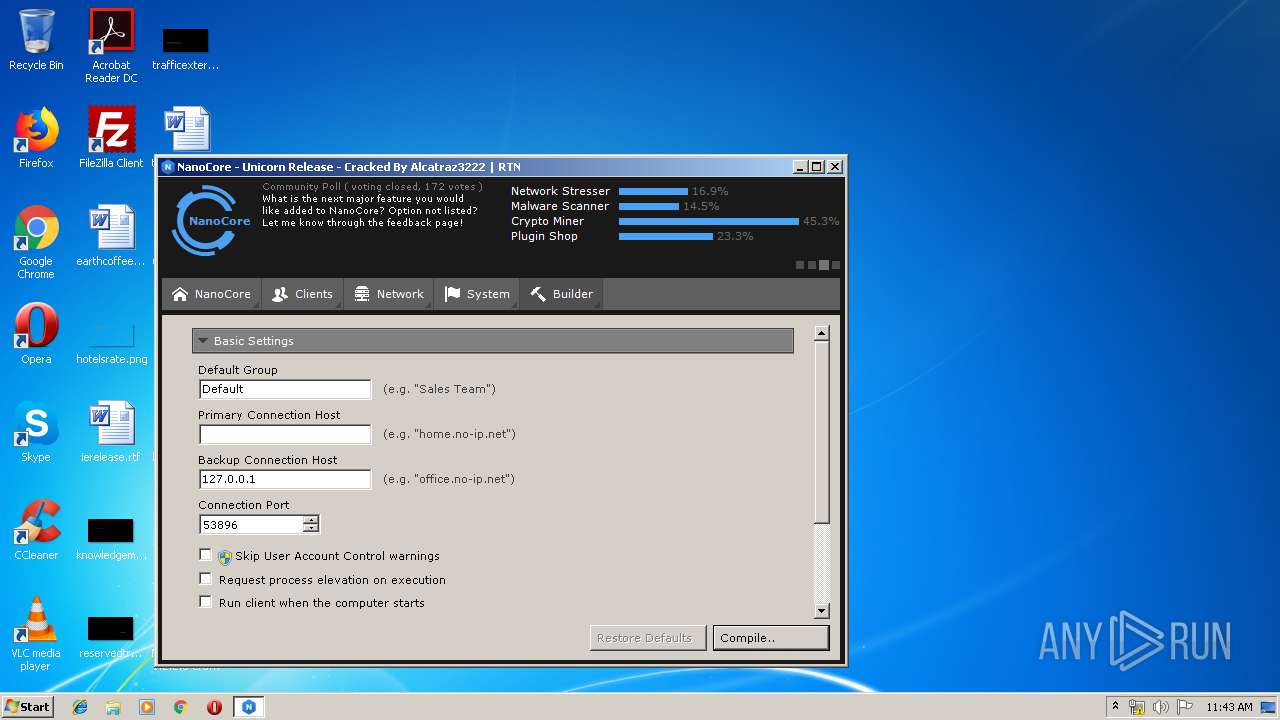
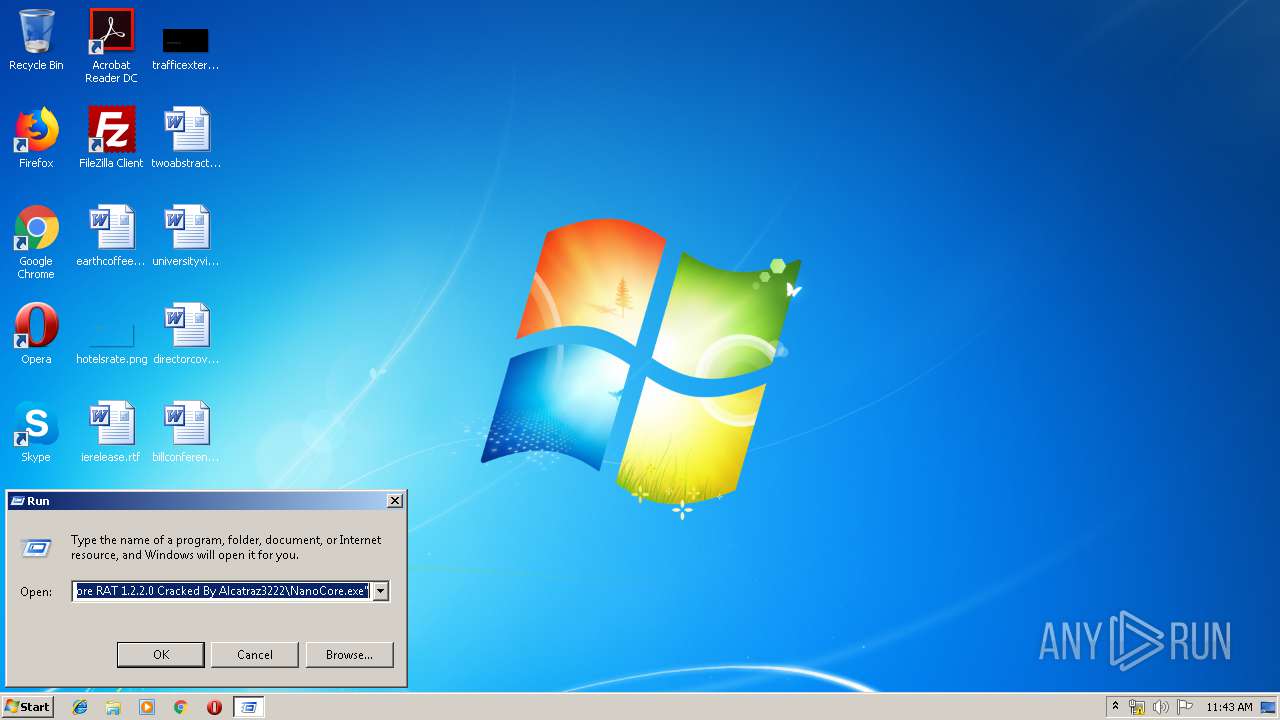
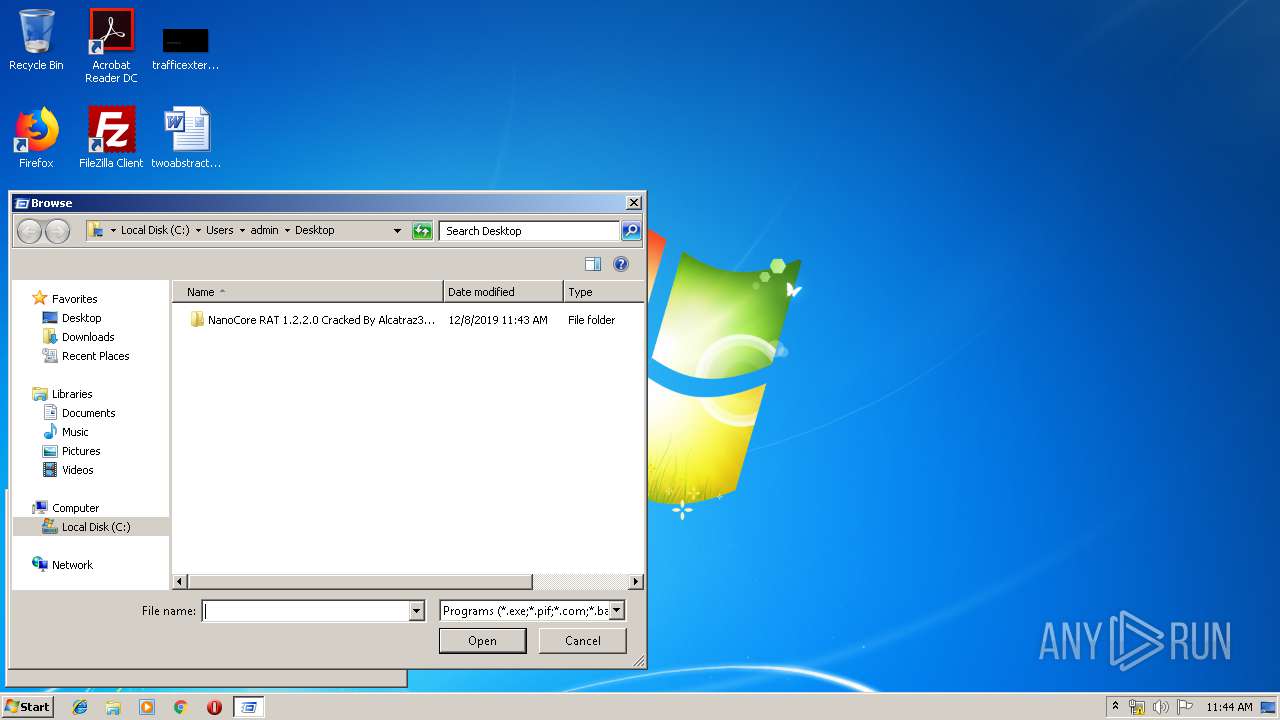
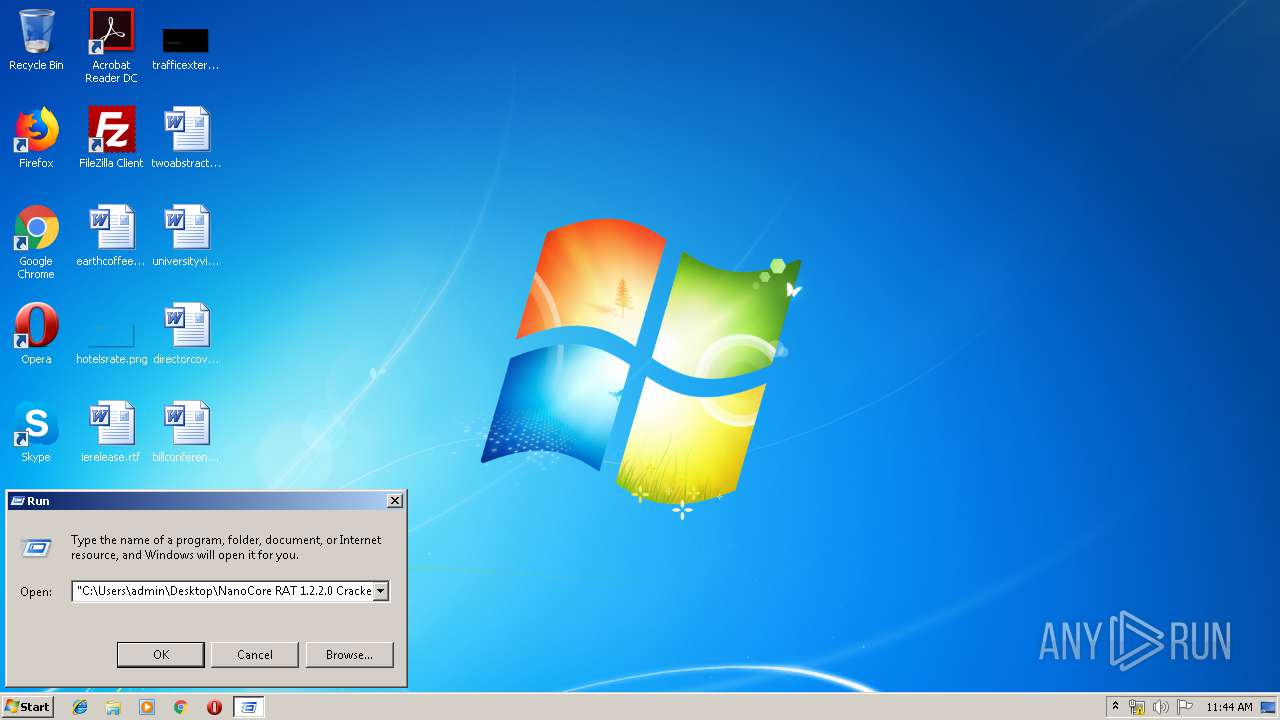
Manual execution by user
- NanoCore.exe (PID: 3680)
- PluginCompiler.exe (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:12:08 19:31:04 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222/ |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
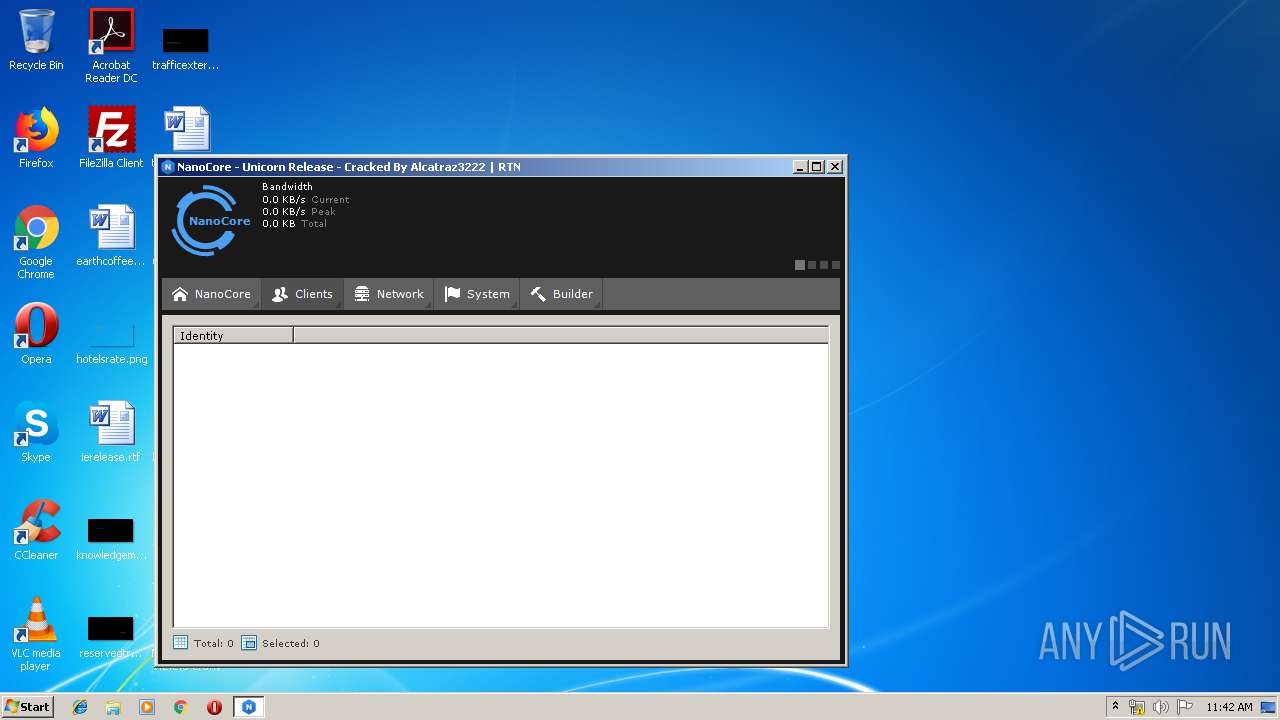
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
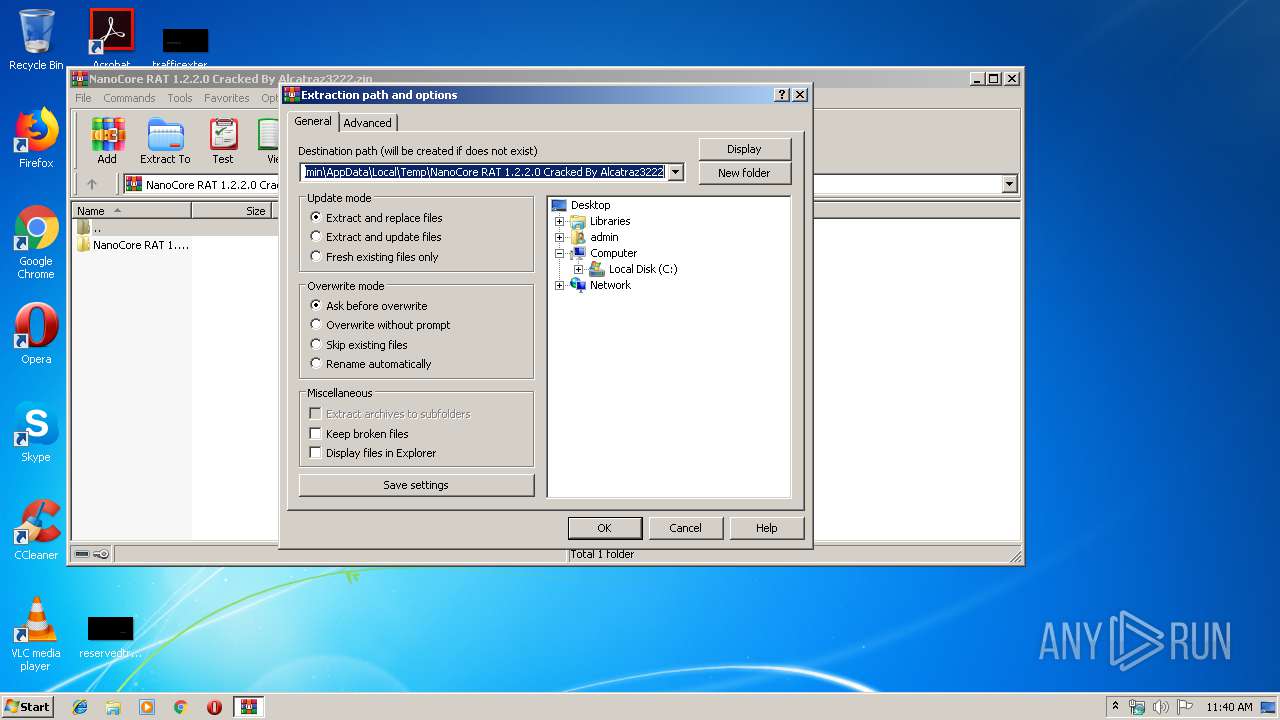
| 2764 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3148 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
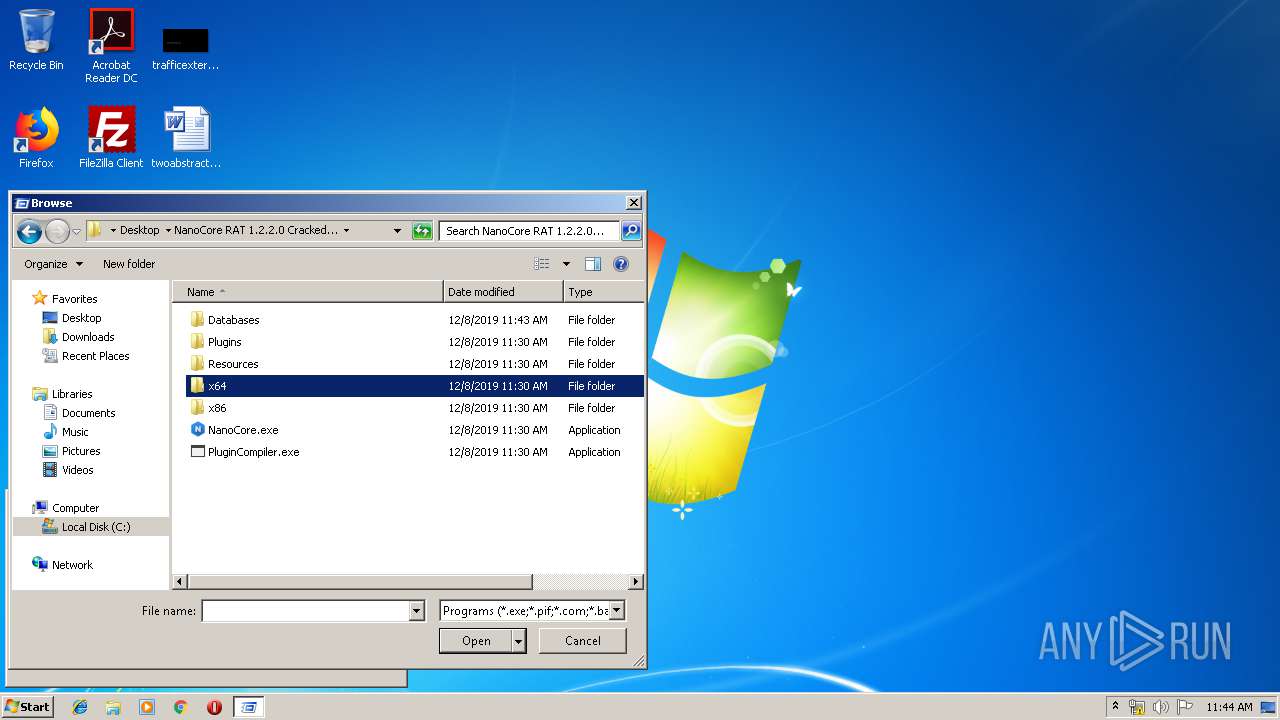
| 3540 | "C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\PluginCompiler.exe" | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\PluginCompiler.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 1.2.0.0 Modules
| |||||||||||||||
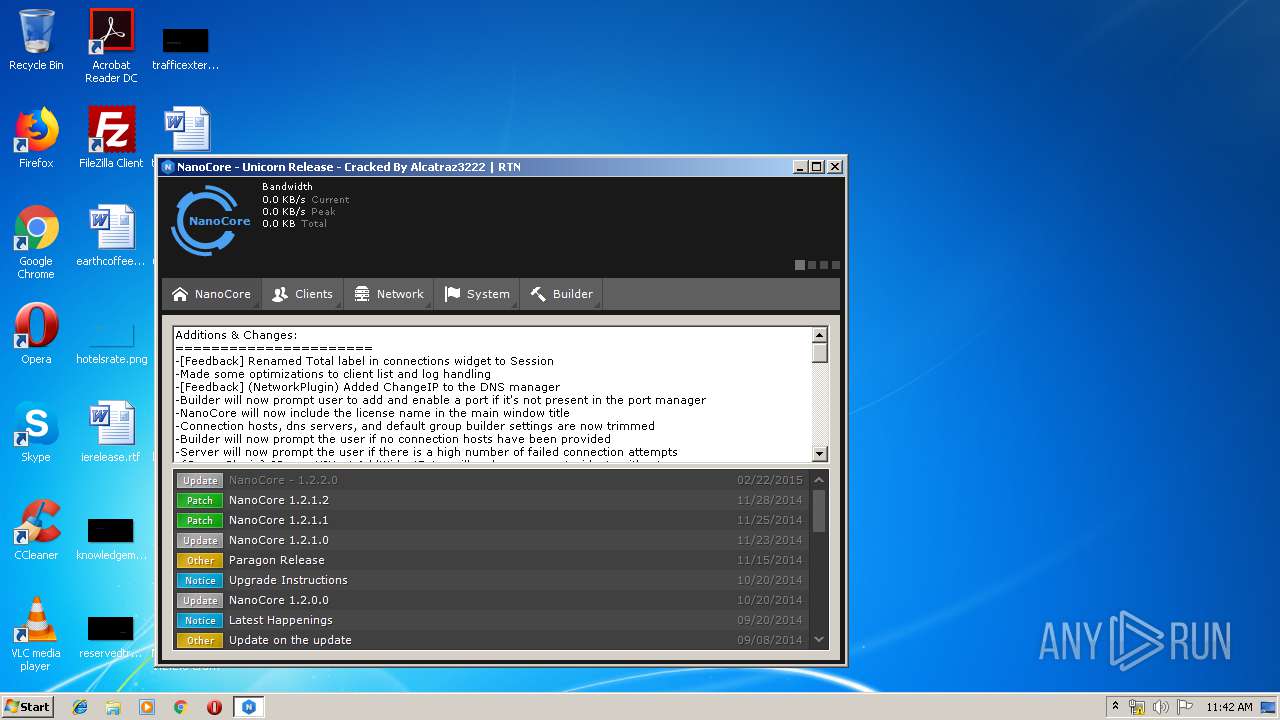
| 3680 | "C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\NanoCore.exe" | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\NanoCore.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: NanoCore Exit code: 0 Version: 1.2.2.0 Modules
| |||||||||||||||
Total events
857
Read events
821
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
8
Suspicious files
9
Text files
337
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\application_delete.png | image | |
MD5:333C3E0CC3FF3A57B9CA358DE9BD39CB | SHA256:9E3DE440BEC32E23846A9EF37235453EA627A8AEB0A17AC0AFEDB433FCB448EE | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\Audio\camera.wav | wav | |
MD5:4567DBE9CC7CFDFE3A13A609E20A205E | SHA256:F49EC225A0DF03534F4B9B265AEDA561FD0A6B11D53038ABAA27B3858DB41AA1 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\arrow_refresh.png | image | |
MD5:9B1A30AC871AF0684BAA0E4E76911D48 | SHA256:6141EAF716680EF3030C0DB1252BB39BF3145E4A17225D787808C7731BA9358D | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\books_stack.png | image | |
MD5:F85AA7E604E376846E22060F39ED5CEF | SHA256:E10F4DD9DAAF95F3AA0F6009E2D82D5C09981CCED09C253BF105931A40673750 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\book_open.png | image | |
MD5:96DA8A3C55290589DEE7606C5331B21A | SHA256:EB88A9E3A64EF9793DEB04BFE87234585217057A13D83828AFB1DCEB25A514D2 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\clipboard.png | image | |
MD5:BBA5ACFE2A3448910760402AF17B2057 | SHA256:BC6045247ED76340995951F6FDEB18C24B8EE53DB3450A3426B8ACA85175B308 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\computer.png | image | |
MD5:C0DC4D56147B86B211C7419F727BE0A3 | SHA256:B0B606F3F84B5E1F8C7F8558DD3F092ADCE374F5C810613845276D47A6401D58 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\cog.png | image | |
MD5:3D04274979A97BDBEB73E7EFBFAFA919 | SHA256:9B15C687DC9E4AEBE320B6C8A8E44616657B3134CE2C29FFAB0647322EF4D906 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\control_panel.png | image | |
MD5:49811B46491E436958BE941D0E5E2BD2 | SHA256:04030A3E3E23BAAF7573E297CA0B83F5D196F905568FCEEFBA0B1E0413D1A063 | |||
| 2764 | WinRAR.exe | C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\Resources\ContextIcons\cancel.png | image | |
MD5:79DF717E10F007D91124673E028FA212 | SHA256:03E31685554582EC7331A4F364C72D159DA6271742BD23027B26ADFF05B9FB5E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3680 | NanoCore.exe | GET | 200 | 50.19.218.16:80 | http://api.ipify.org/ | US | text | 12 b | shared |
3680 | NanoCore.exe | GET | 200 | 50.19.218.16:80 | http://api.ipify.org/ | US | text | 12 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | NanoCore.exe | 50.19.218.16:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3680 | NanoCore.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
3680 | NanoCore.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
Process | Message |
|---|---|
NanoCore.exe | Trying to load native SQLite library "C:\Users\admin\Desktop\NanoCore RAT 1.2.2.0 Cracked By Alcatraz3222\x86\SQLite.Interop.dll"...
|