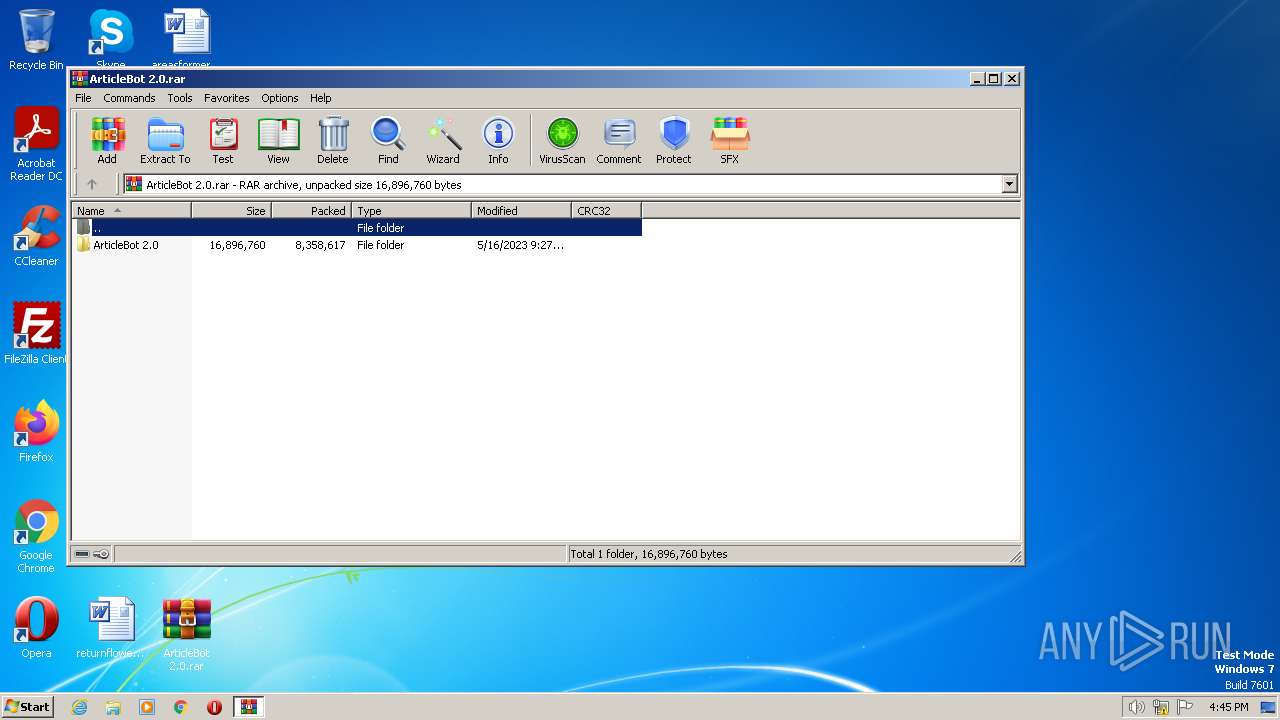
| File name: | ArticleBot 2.0.rar |
| Full analysis: | https://app.any.run/tasks/8ef623d9-dd4e-4645-9651-453ff17b7612 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 15:44:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 552B8961A8B46FA5B218C1A6F9D3AE96 |
| SHA1: | 02824FF3AD4D03FEBB693C422A5600B768709B93 |
| SHA256: | 46674452EA1AC8CCCE8482973158AA752281C6F3DA484B63BD091FC57631F25C |
| SSDEEP: | 196608:xcgPQAQ1I10bKc7gPQAQ1I10bK5J3d3hLWGmTYtVTWtq5dB:fPQAuI1dPQAuI1vBhUYthW+3 |
MALICIOUS
Application was dropped or rewritten from another process
- ArticleBot.exe (PID: 3960)
- Launcher.exe (PID: 2500)
- Secure System Shell.exe (PID: 3396)
- Runtime Explorer.exe (PID: 3572)
- Windows Services.exe (PID: 2464)
- Runtime Explorer.exe (PID: 2120)
- ab.exe (PID: 2596)
Loads dropped or rewritten executable
- Launcher.exe (PID: 2500)
Adds path to the Windows Defender exclusion list
- Launcher.exe (PID: 2500)
Create files in the Startup directory
- Launcher.exe (PID: 2500)
SUSPICIOUS
Reads the Internet Settings
- ArticleBot.exe (PID: 3960)
- Launcher.exe (PID: 2500)
- Windows Services.exe (PID: 2464)
- powershell.exe (PID: 672)
Starts POWERSHELL.EXE for commands execution
- Launcher.exe (PID: 2500)
Script adds exclusion path to Windows Defender
- Launcher.exe (PID: 2500)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 672)
The process creates files with name similar to system file names
- Launcher.exe (PID: 2500)
Executable content was dropped or overwritten
- Launcher.exe (PID: 2500)
INFO
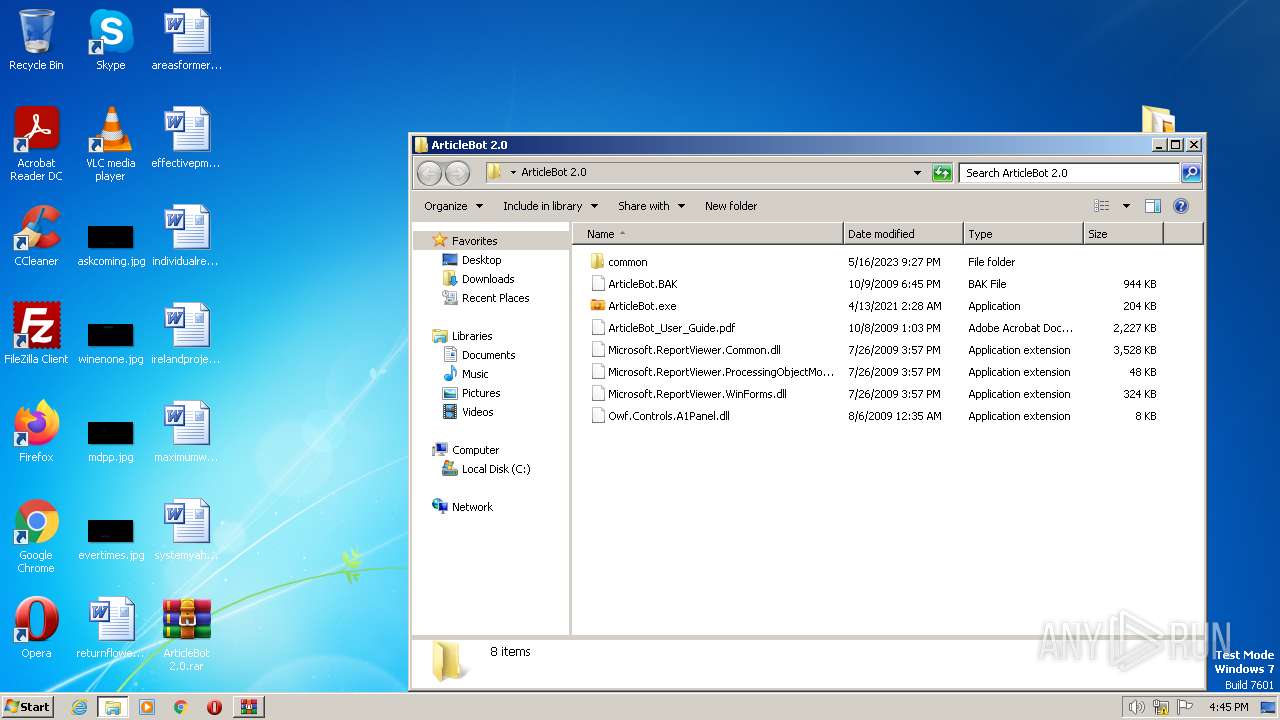
Manual execution by a user
- ArticleBot.exe (PID: 3960)
The process checks LSA protection
- ArticleBot.exe (PID: 3960)
- Launcher.exe (PID: 2500)
- Windows Services.exe (PID: 2464)
- Runtime Explorer.exe (PID: 3572)
- dw20.exe (PID: 548)
- Runtime Explorer.exe (PID: 2120)
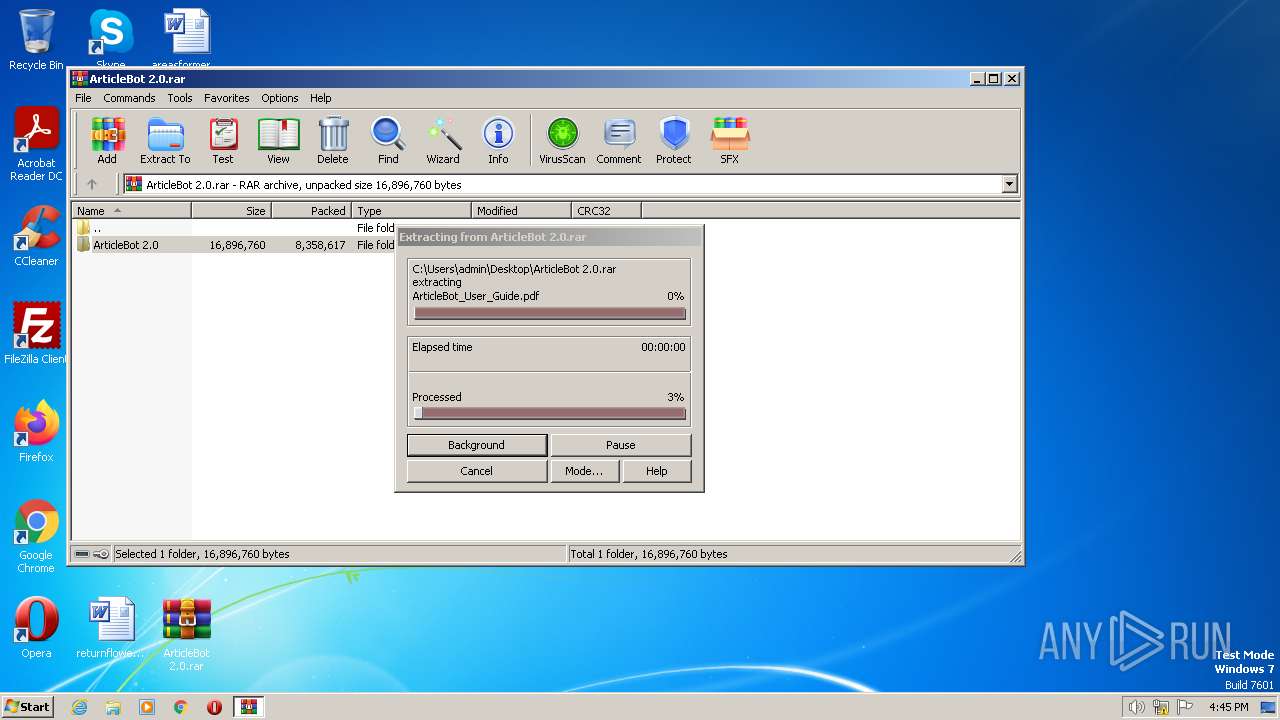
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1008)
Checks supported languages
- ArticleBot.exe (PID: 3960)
- Launcher.exe (PID: 2500)
- ab.exe (PID: 2596)
- dw20.exe (PID: 548)
- Windows Services.exe (PID: 2464)
- Secure System Shell.exe (PID: 3396)
- Runtime Explorer.exe (PID: 3572)
- Runtime Explorer.exe (PID: 2120)
Reads the computer name
- ArticleBot.exe (PID: 3960)
- Launcher.exe (PID: 2500)
- dw20.exe (PID: 548)
- Windows Services.exe (PID: 2464)
- Secure System Shell.exe (PID: 3396)
Reads the machine GUID from the registry
- Launcher.exe (PID: 2500)
- ArticleBot.exe (PID: 3960)
- Runtime Explorer.exe (PID: 3572)
- dw20.exe (PID: 548)
- Runtime Explorer.exe (PID: 2120)
Creates files or folders in the user directory
- Launcher.exe (PID: 2500)
Create files in a temporary directory
- Runtime Explorer.exe (PID: 3572)
- Runtime Explorer.exe (PID: 2120)
Creates files in the program directory
- dw20.exe (PID: 548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
11
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | dw20.exe -x -s 396 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\dw20.exe | — | ab.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Error Reporting Shim Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 672 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" add-mppreference -exclusionpath C:\Windows\IMF\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 956 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 1008 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ArticleBot 2.0.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
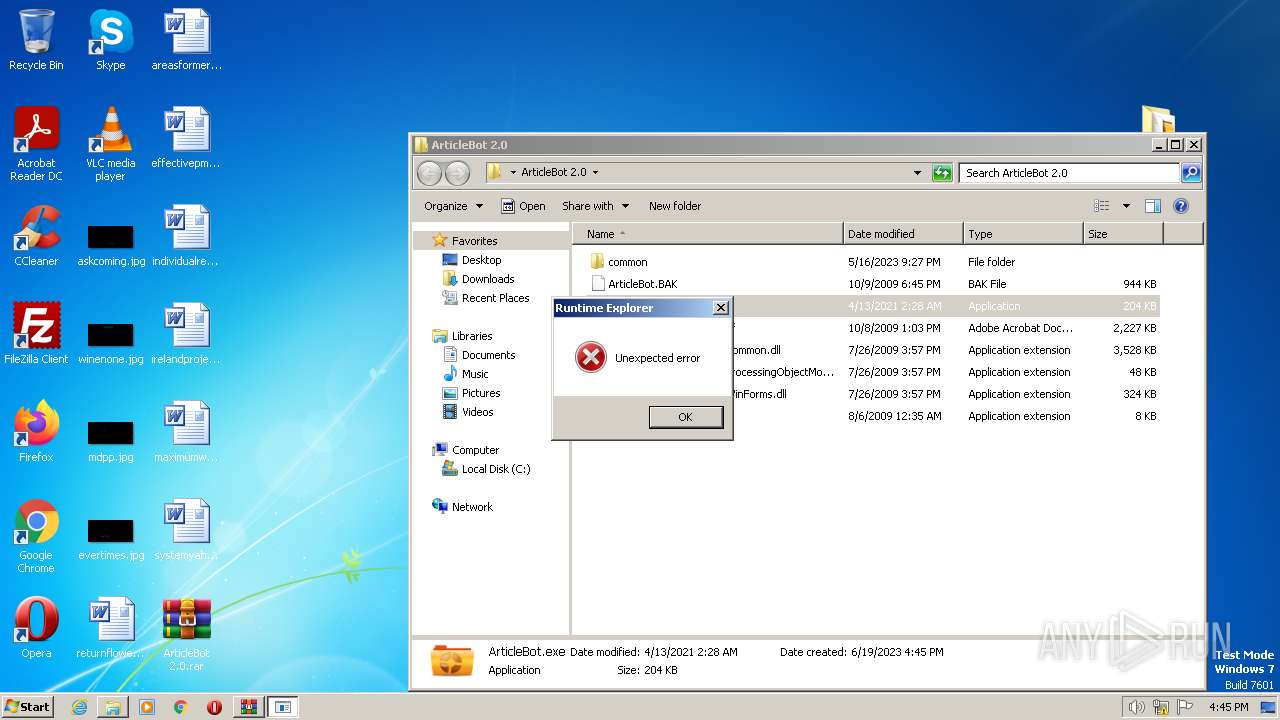
| 2120 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2464 | "C:\Windows\IMF\Windows Services.exe" {Arguments If Needed} | C:\Windows\IMF\Windows Services.exe | — | Launcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Windows Services Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\Desktop\ArticleBot 2.0\common\Launcher.exe" | C:\Users\admin\Desktop\ArticleBot 2.0\common\Launcher.exe | ArticleBot.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
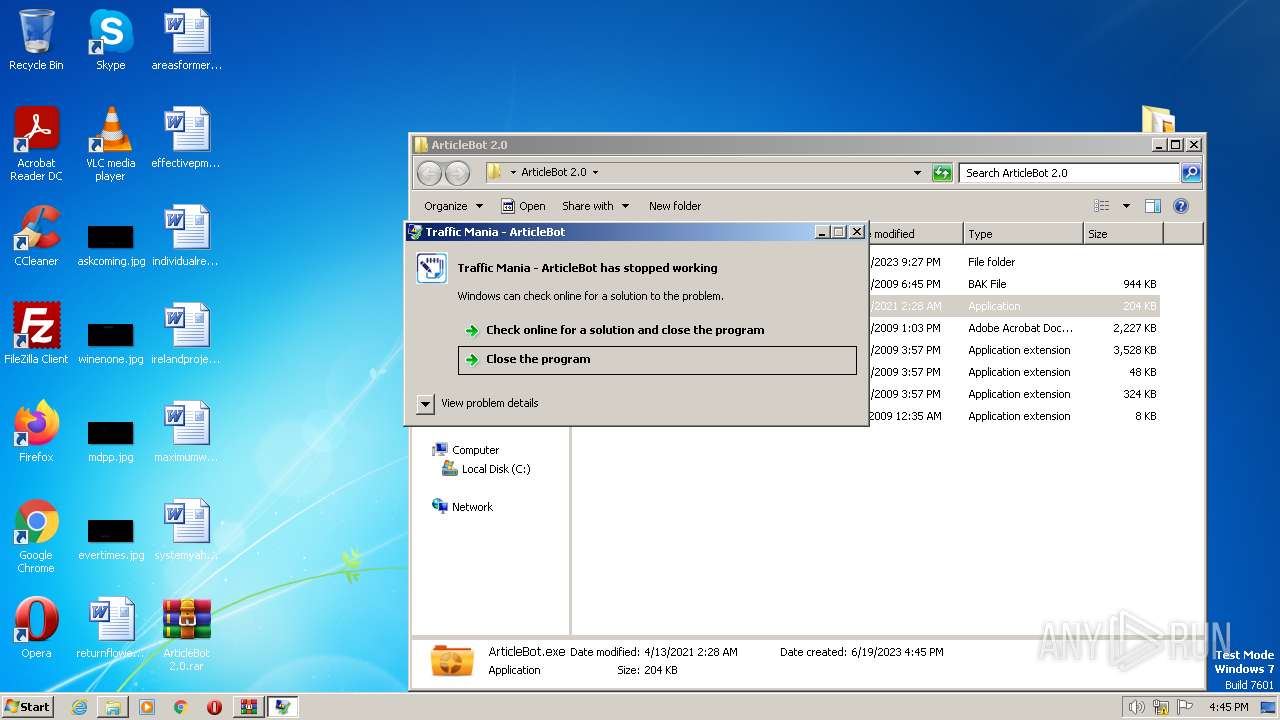
| 2596 | "C:\Users\admin\Desktop\ArticleBot 2.0\common\ab.exe" | C:\Users\admin\Desktop\ArticleBot 2.0\common\ab.exe | ArticleBot.exe | ||||||||||||
User: admin Company: Incansoft Integrity Level: HIGH Description: Traffic Mania - ArticleBot Exit code: 3762507597 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3396 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3572 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Microsoft Windows Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
6 151
Read events
6 097
Write events
54
Delete events
0
Modification events
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3960) ArticleBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3960) ArticleBot.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
21
Suspicious files
11
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\ArticleBot.BAK | executable | |
MD5:A6CB4B8B91D0CFF9E6D12C583E2A63CB | SHA256:A3C875AB07D2121140A9ED7593131F033ECD24F811611C42ABAE9ABAE4A9F4F3 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\ArticleBot.BAK | executable | |
MD5:A6CB4B8B91D0CFF9E6D12C583E2A63CB | SHA256:A3C875AB07D2121140A9ED7593131F033ECD24F811611C42ABAE9ABAE4A9F4F3 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\Launcher.exe | executable | |
MD5:C6D4C881112022EB30725978ECD7C6EC | SHA256:0D87B9B141A592711C52E7409EC64DE3AB296CDDC890BE761D9AF57CEA381B32 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\ab.exe | executable | |
MD5:A6CB4B8B91D0CFF9E6D12C583E2A63CB | SHA256:A3C875AB07D2121140A9ED7593131F033ECD24F811611C42ABAE9ABAE4A9F4F3 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\LICENCE.dat | compressed | |
MD5:F7D55578B3709F1519805272E3E64C33 | SHA256:3147A9C9015F7E54C8ACDB8D413DA93EF3E4B04FB27EC578DCD188A70BB53301 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\Ionic.Zip.dll | executable | |
MD5:F6933BF7CEE0FD6C80CDF207FF15A523 | SHA256:17BB0C9BE45289A2BE56A5F5A68EC9891D7792B886E0054BC86D57FE84D01C89 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\Microsoft.ReportViewer.ProcessingObjectModel.dll | executable | |
MD5:F528B1A0141EE32091379DF3DAFC3C53 | SHA256:E1EB0BA27526BE368C2F22CFB0BB3A7874836E47BACBF038D5DDA89EFDDA55DC | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\Microsoft.ReportViewer.WinForms.dll | executable | |
MD5:C681107AE23761C50FAEA1E38F4308FA | SHA256:62EC637C0526C1AAA9C9158A72B16362EA0A0FEC15F0AA53E8196E22A498B852 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\README FIRST! - Upgrade Guide.pdf | ||
MD5:D62AB01E9F45F9C962ADE1D7E78CDC4A | SHA256:838A8C205606931D7C56108C601C8336775434746C6A89E741972AD62FF74F72 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.49378\ArticleBot 2.0\common\Microsoft.ReportViewer.Common.dll | executable | |
MD5:209A03F25704BF9A130B15A85DCD1E30 | SHA256:26BEF26E5791290533A876FE65A3357C96C10B5F1B927932A15E5C9F076D792B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4052 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |