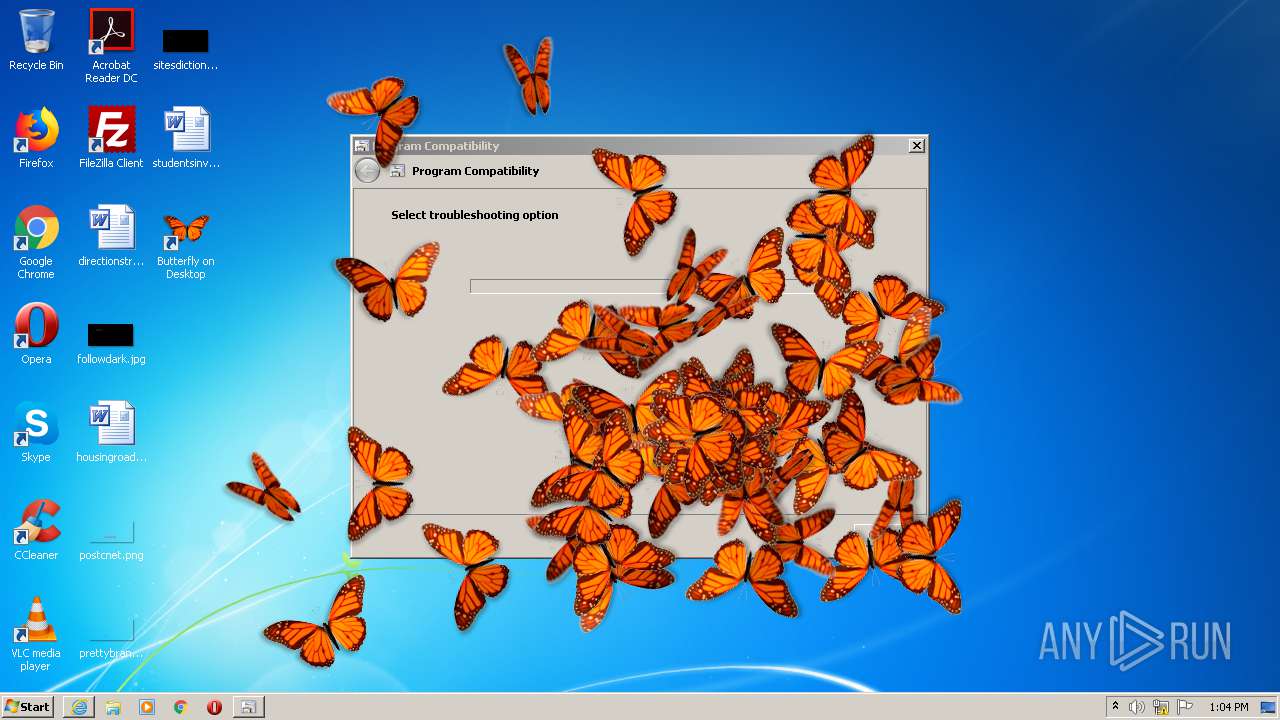
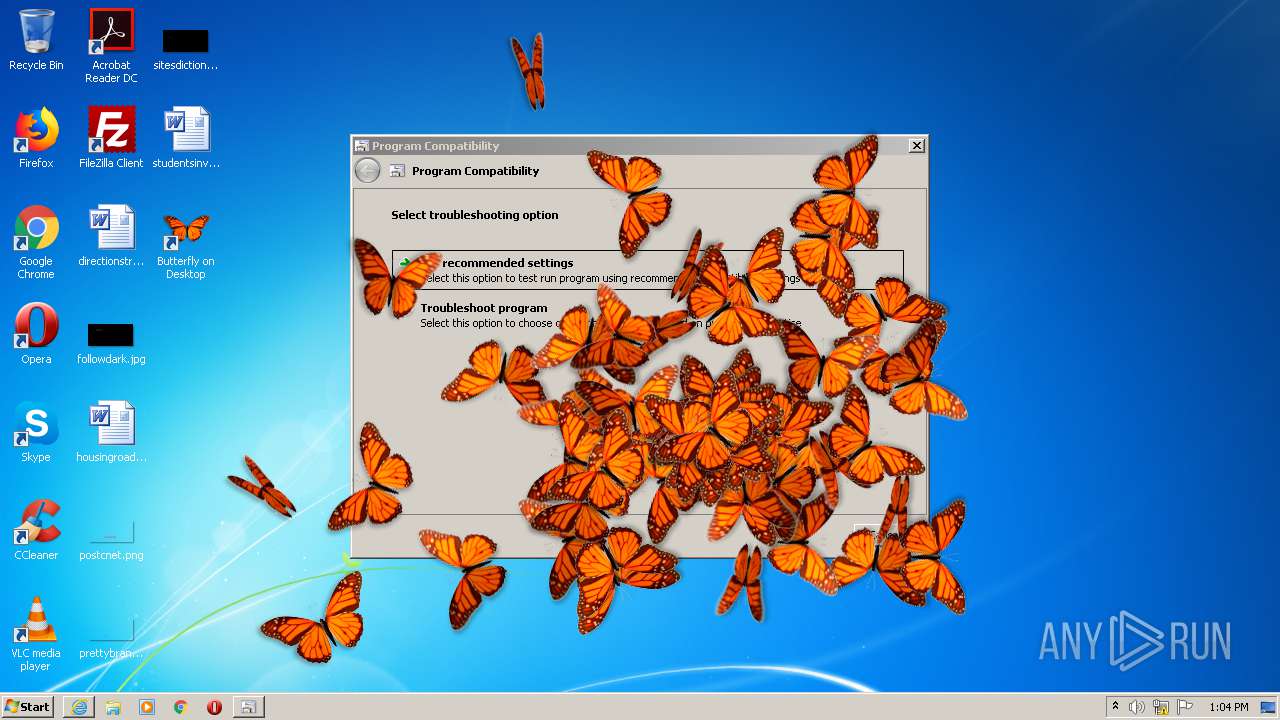
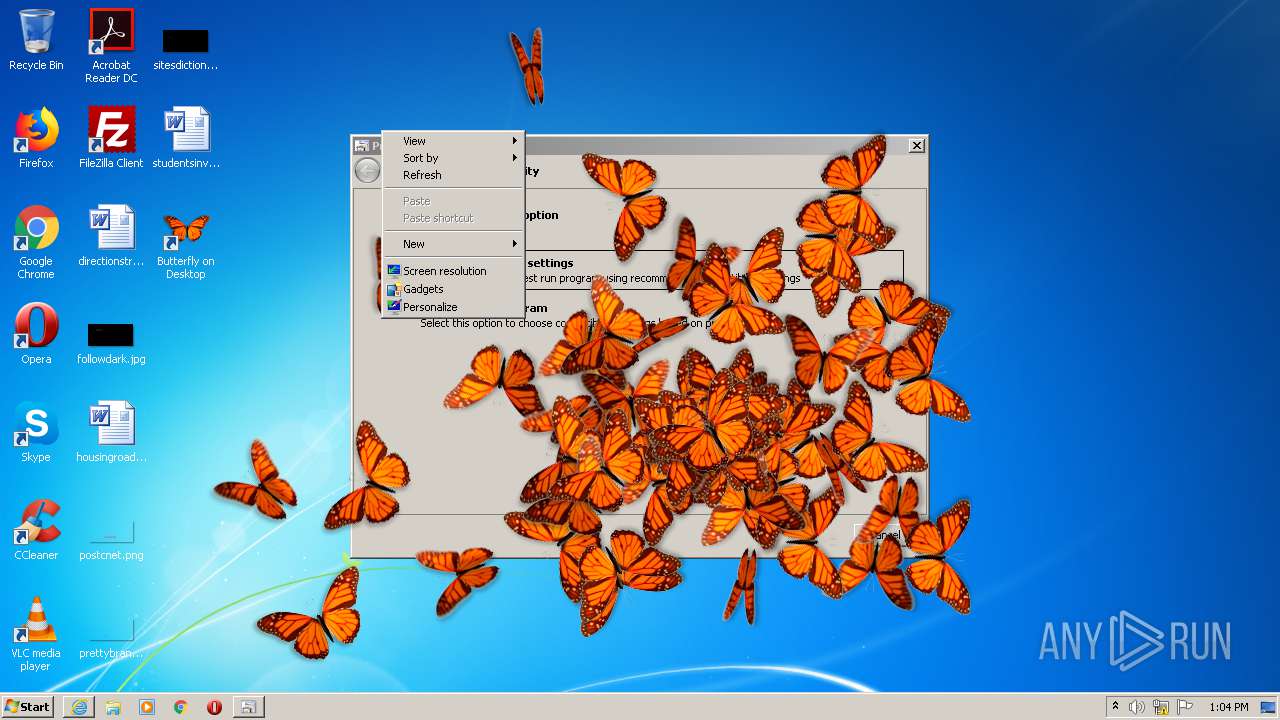
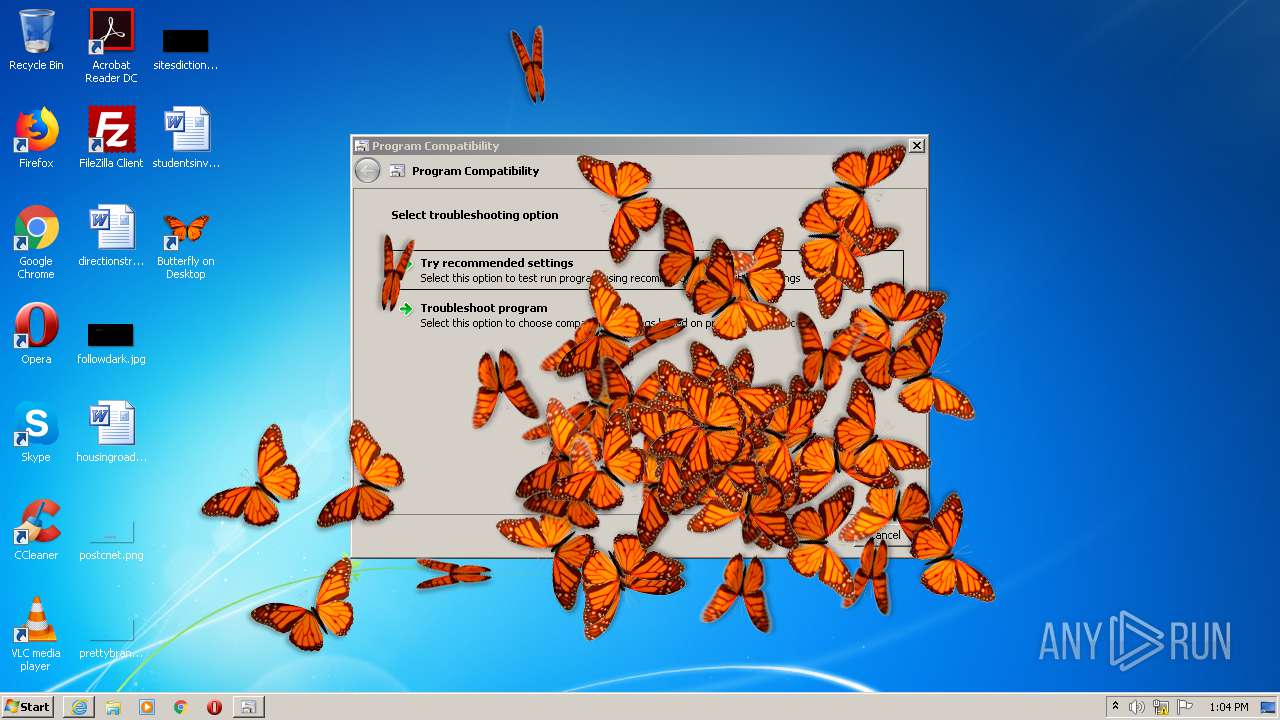
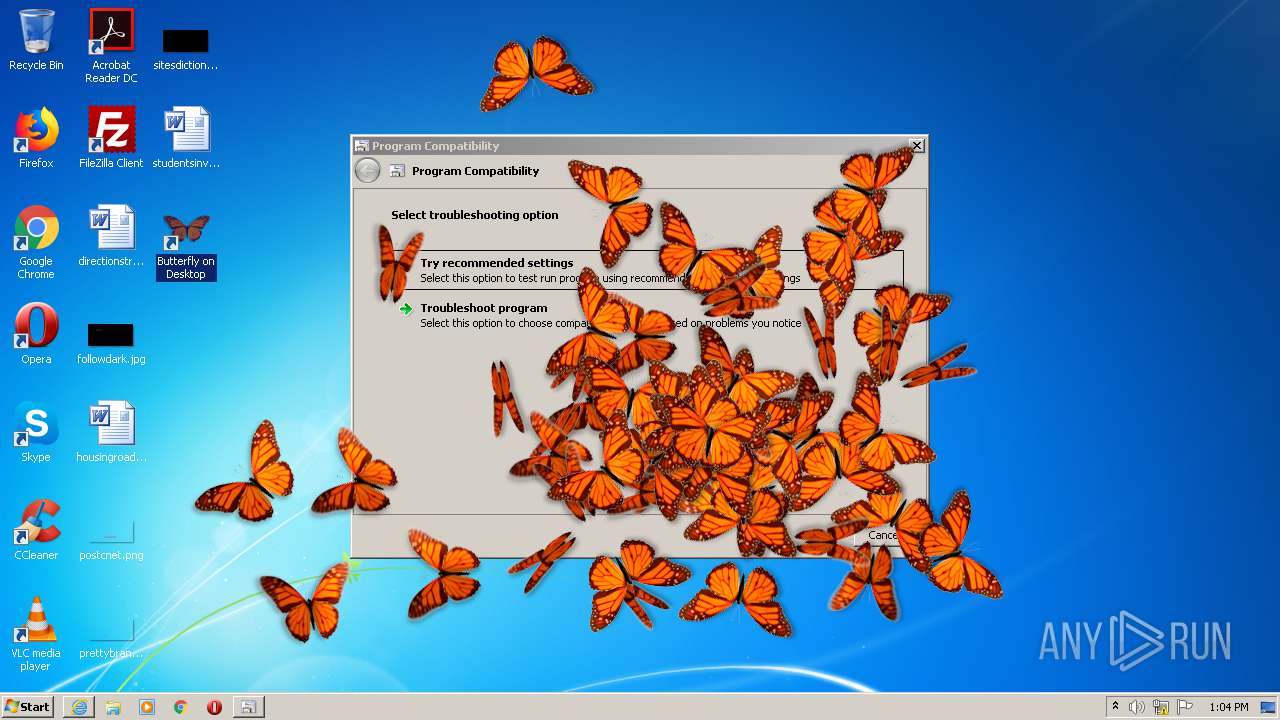
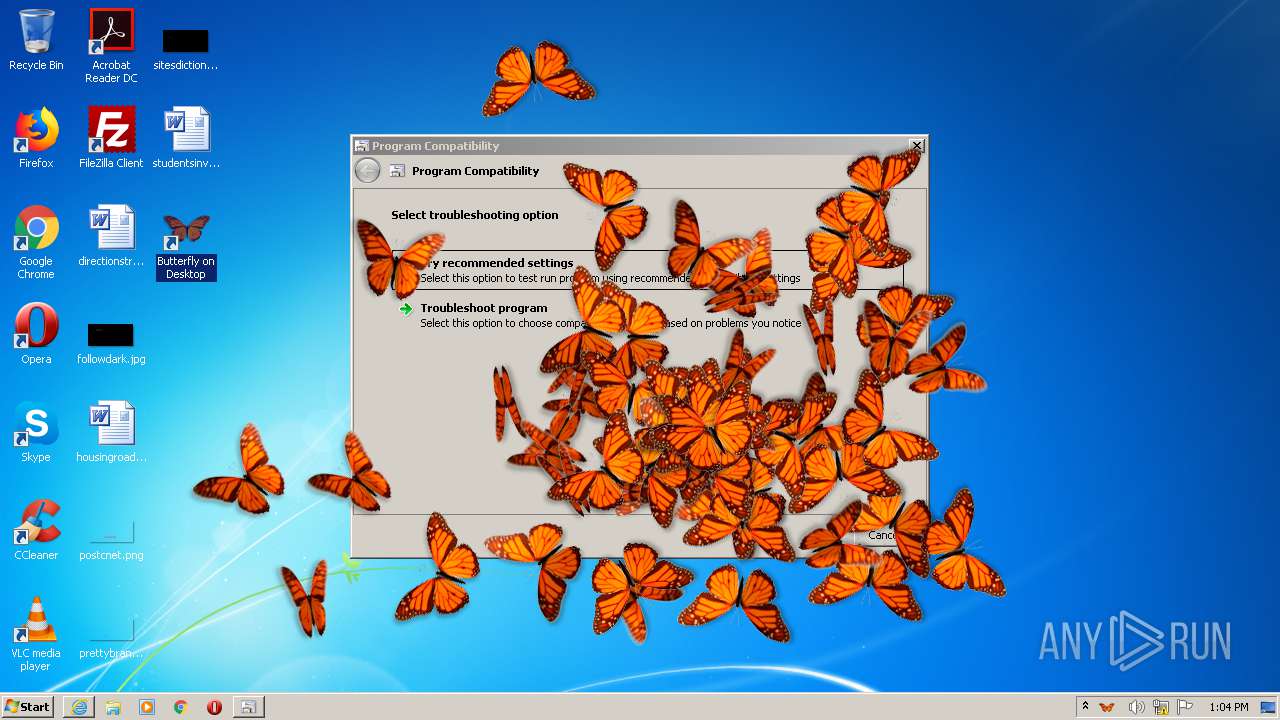
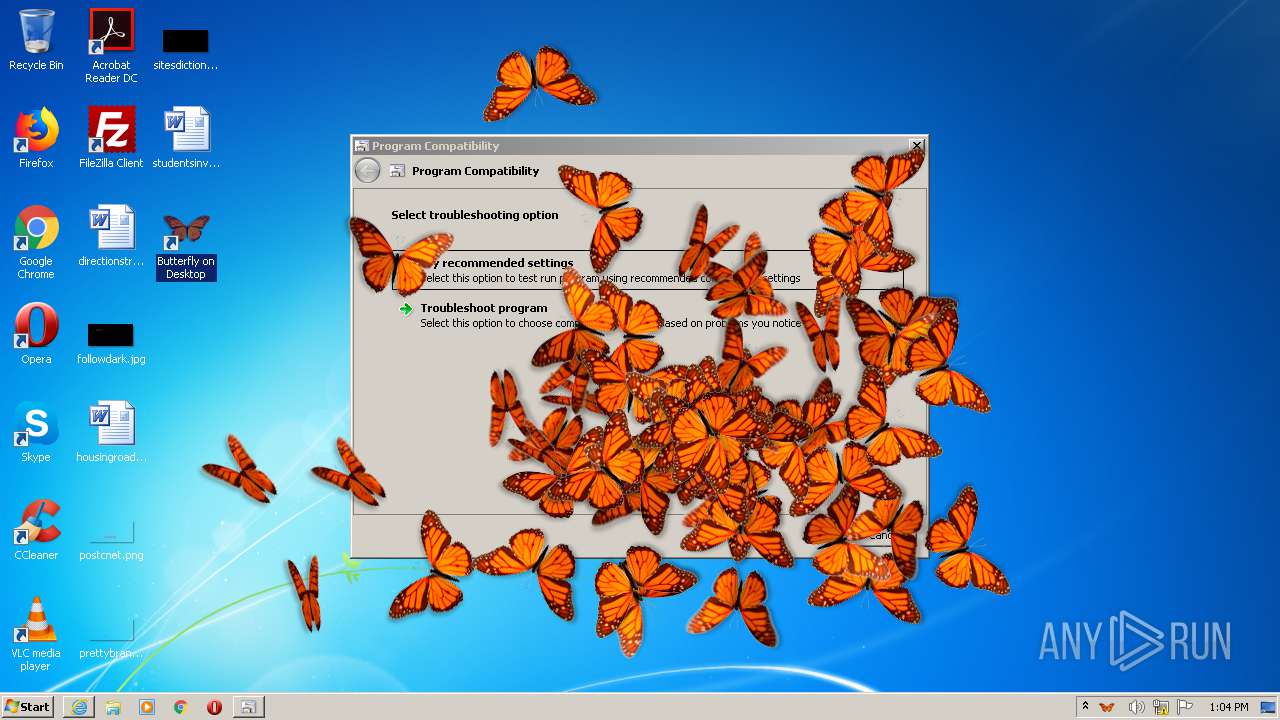
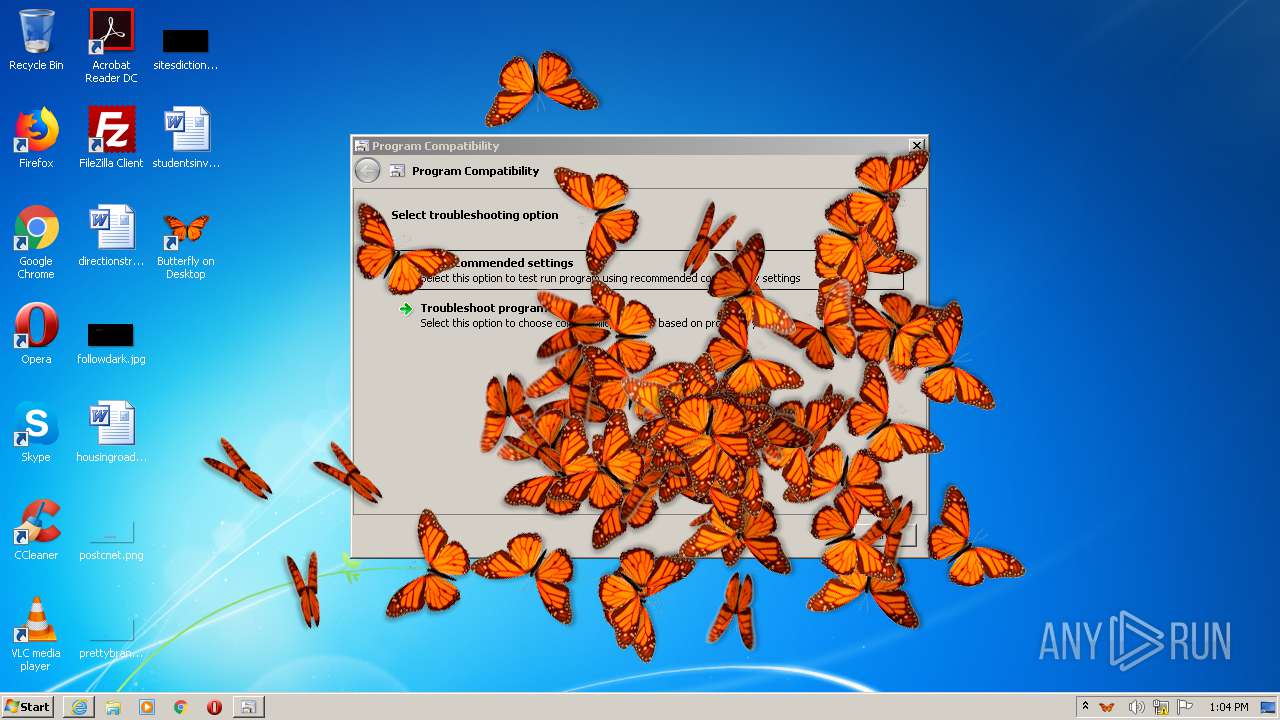
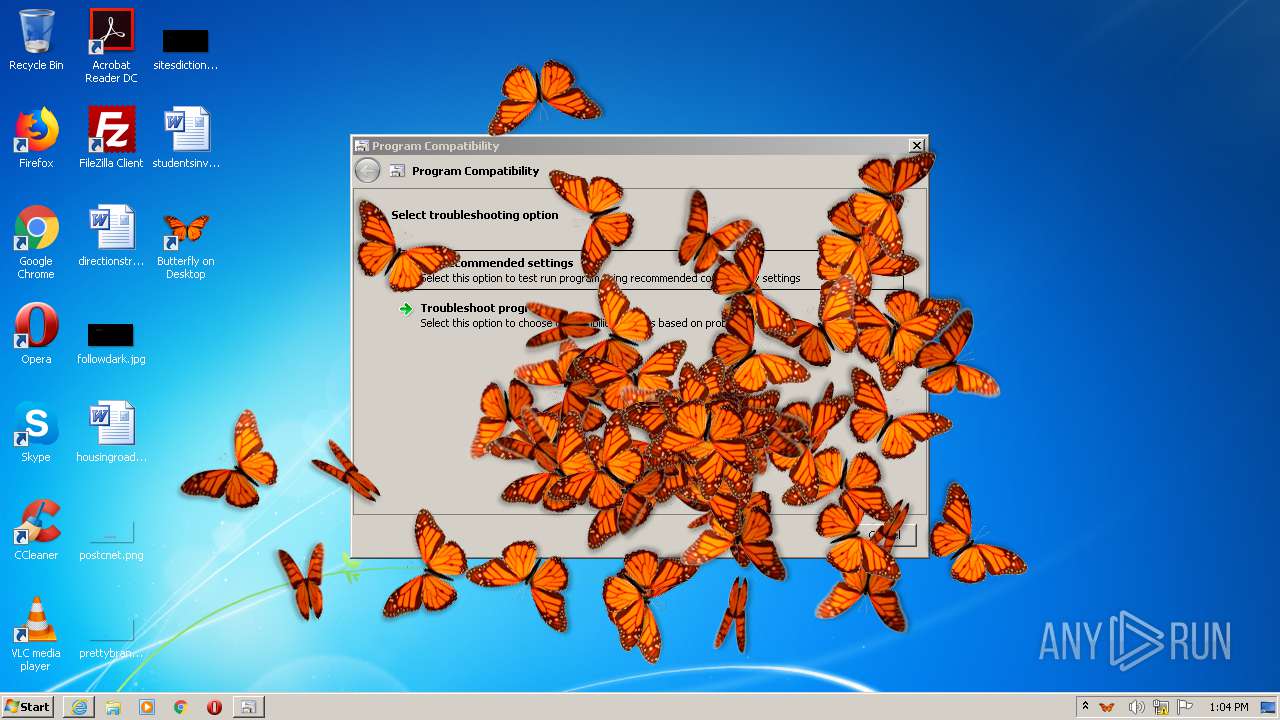
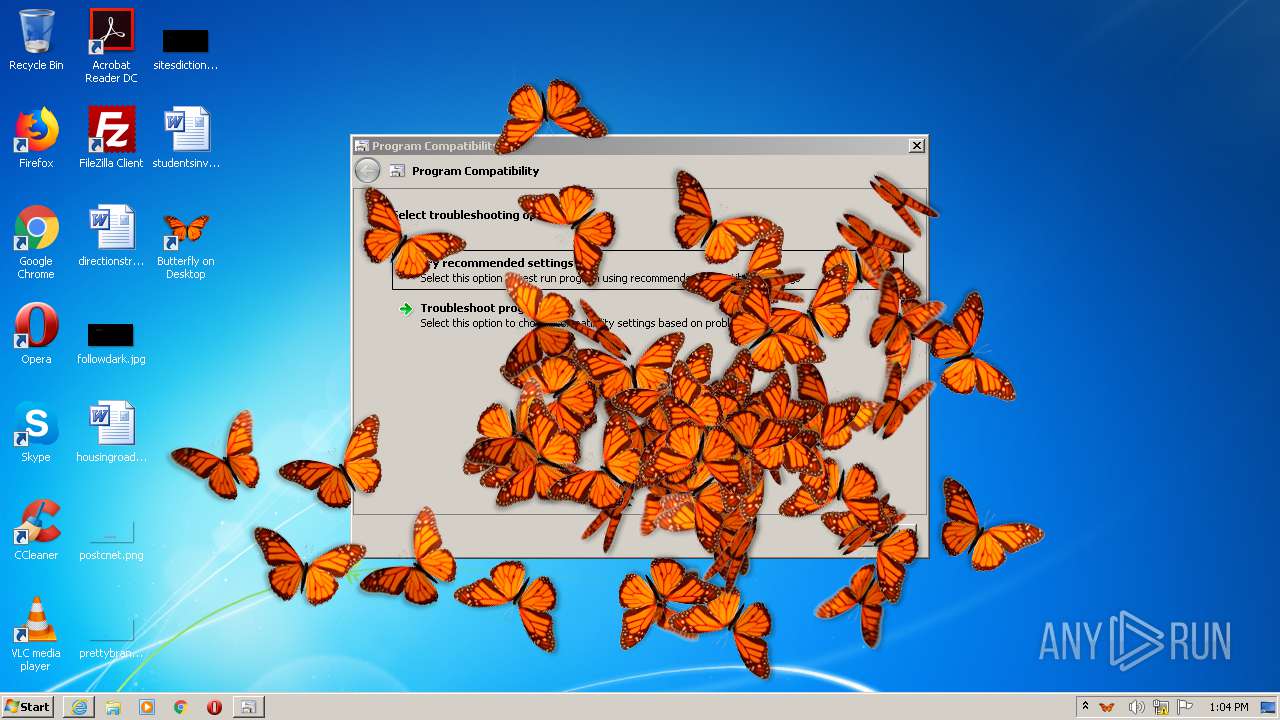
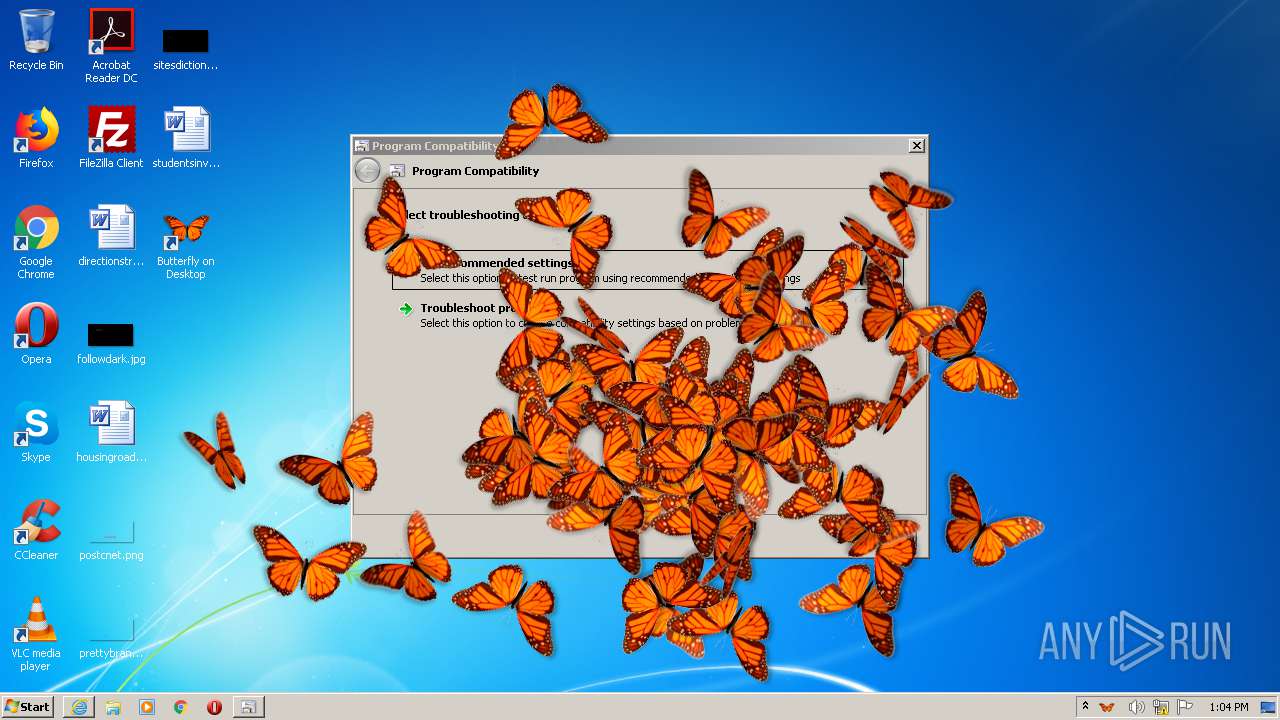
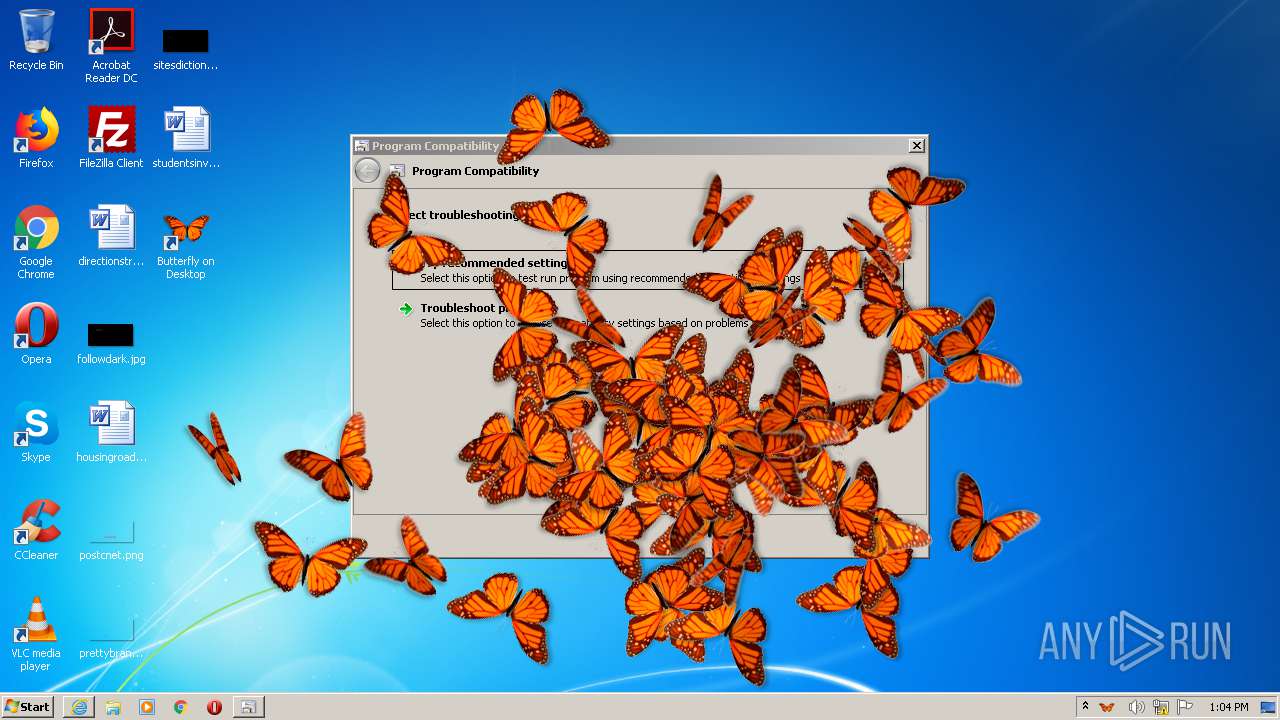
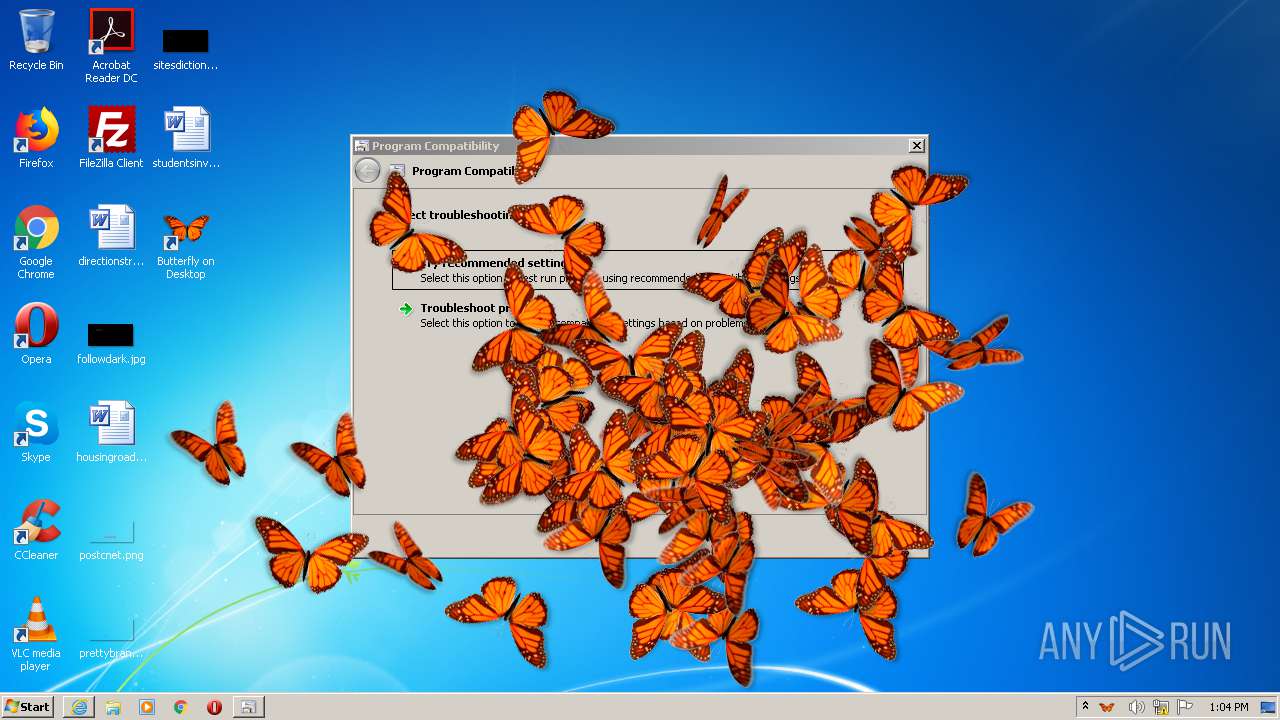
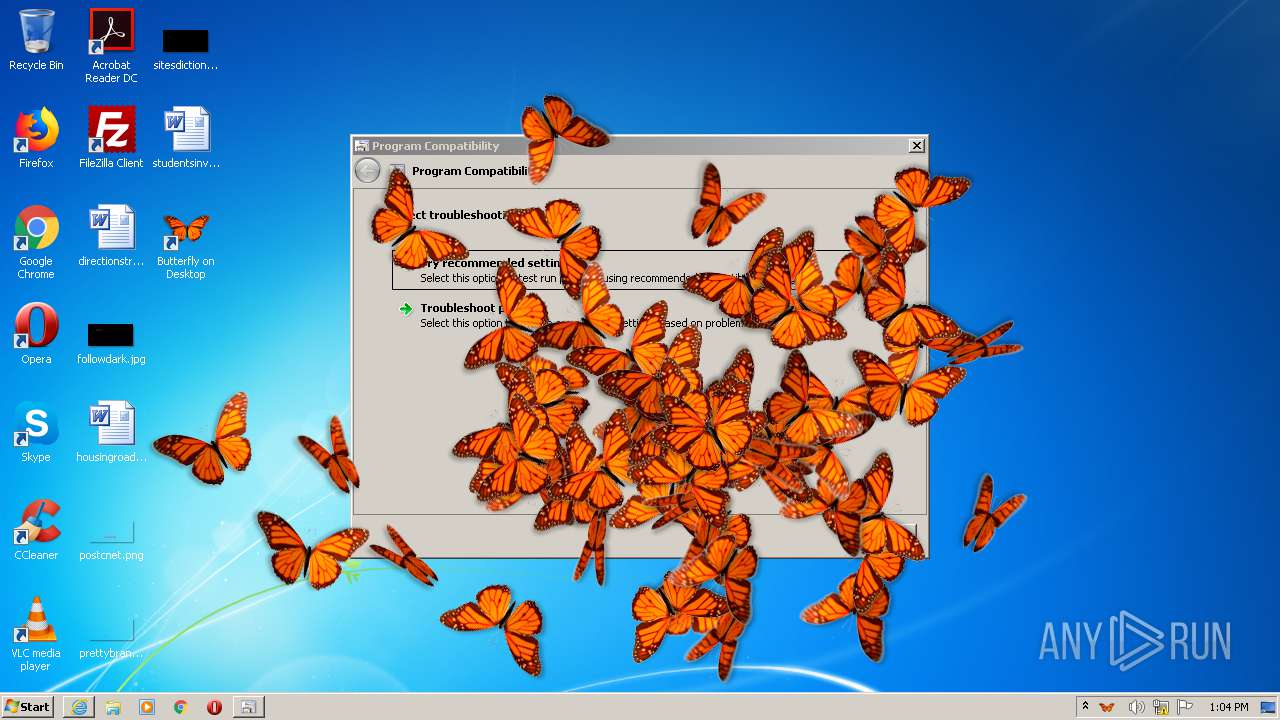
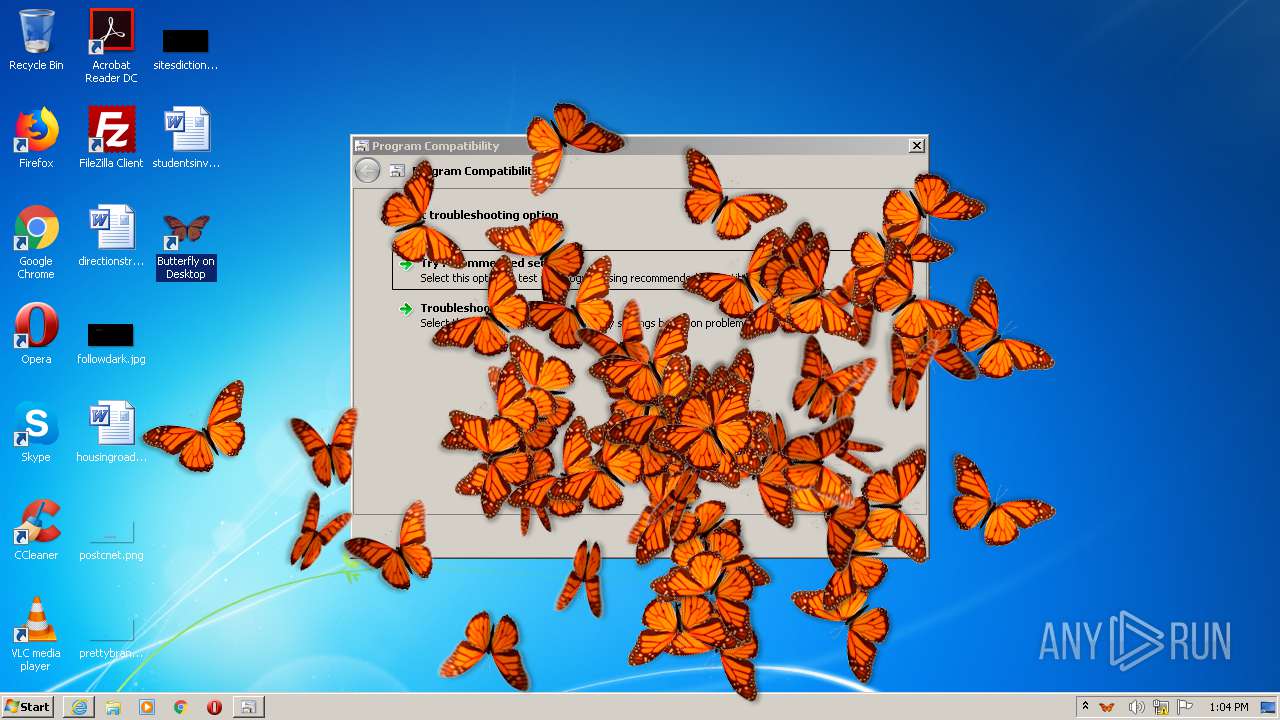
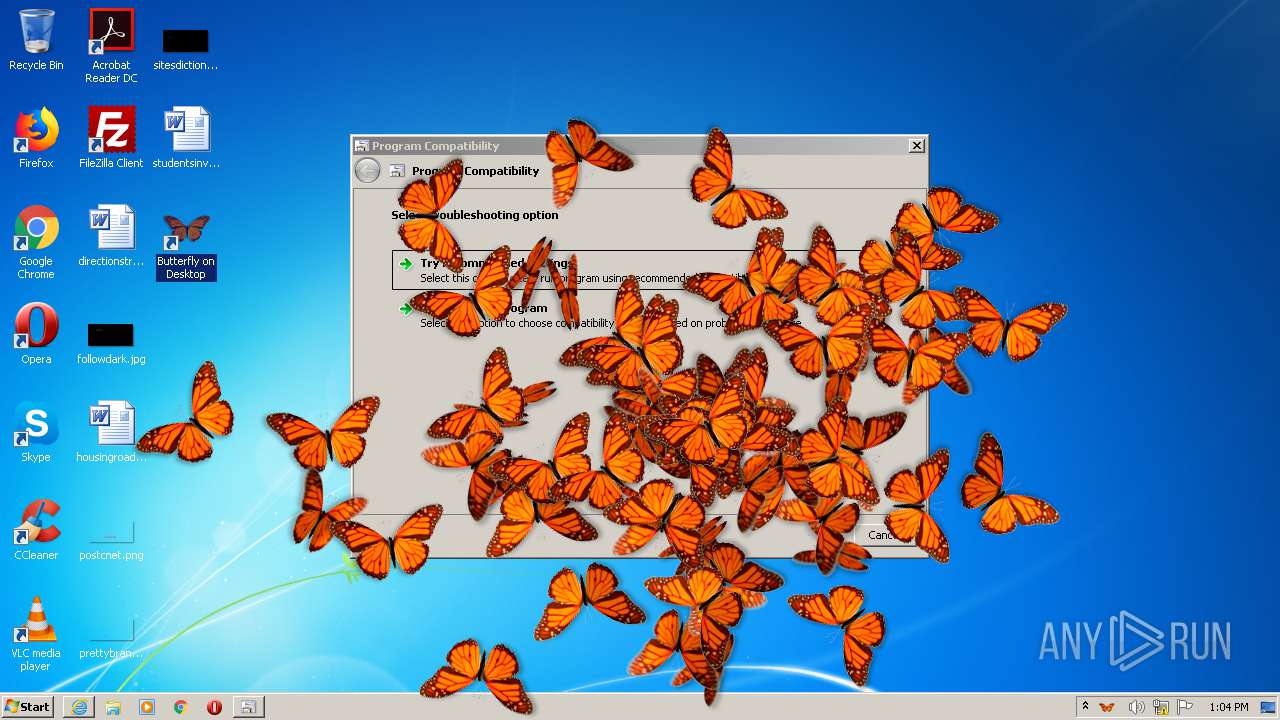
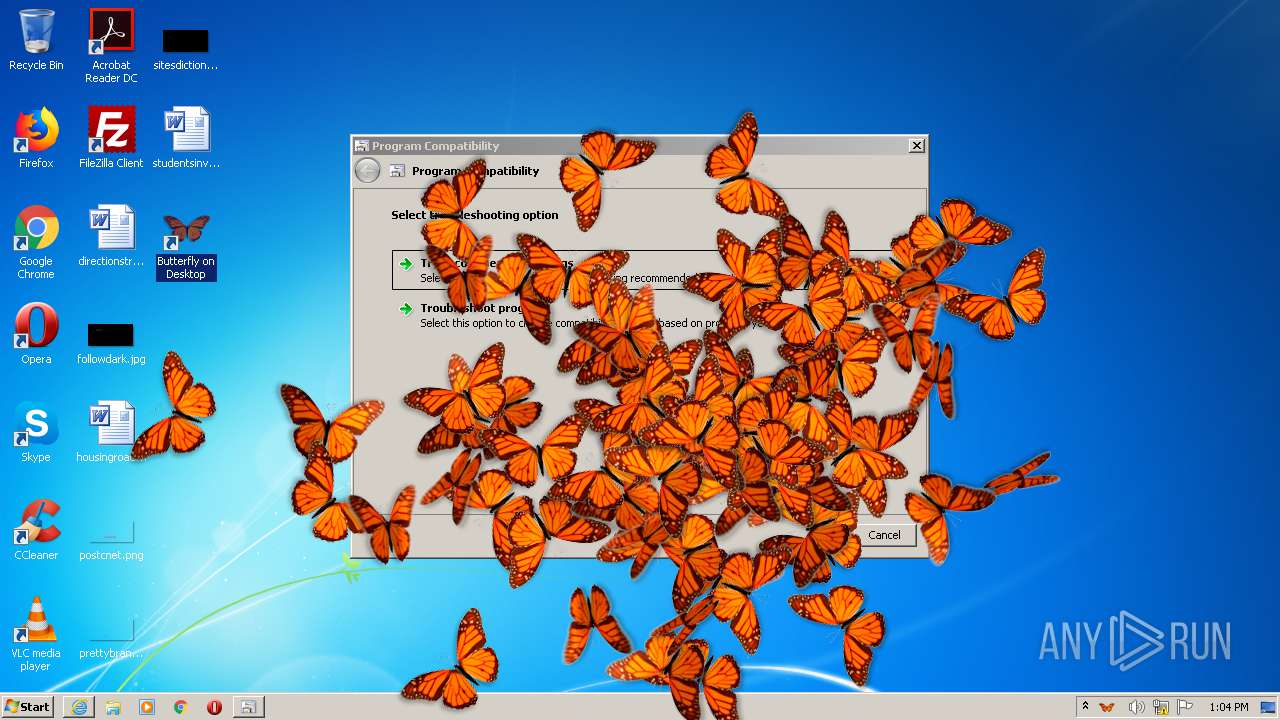
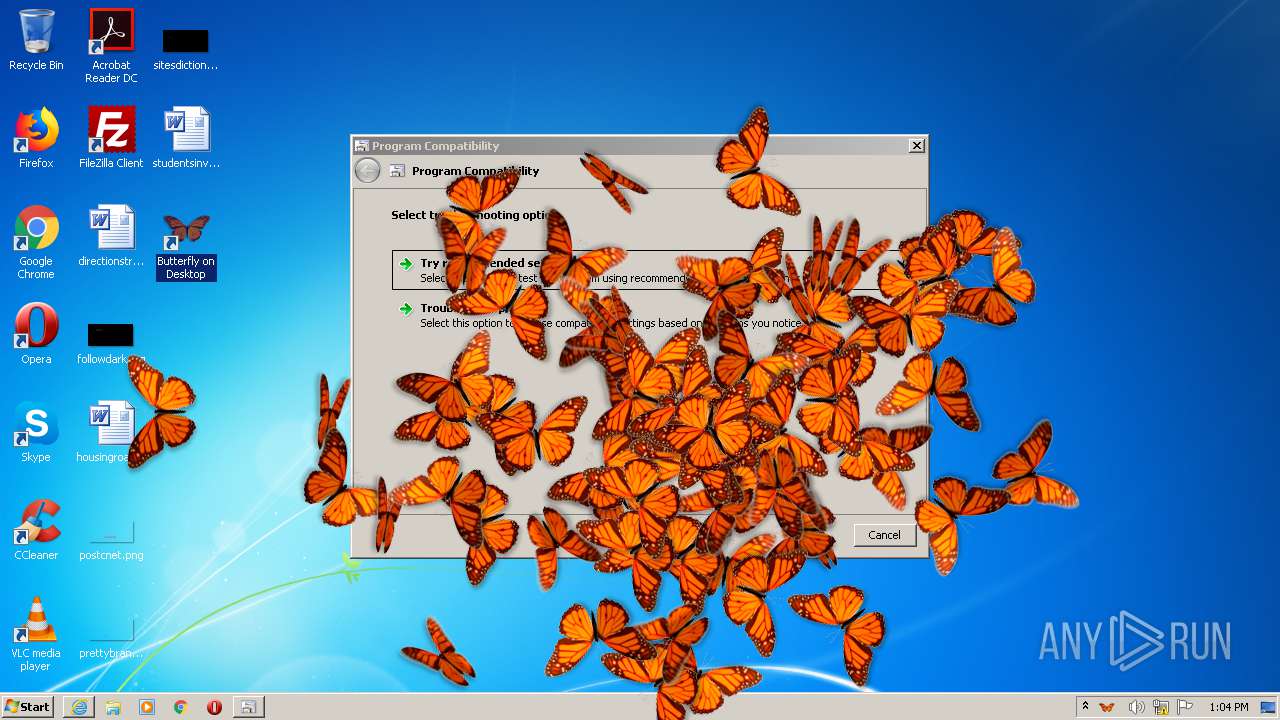
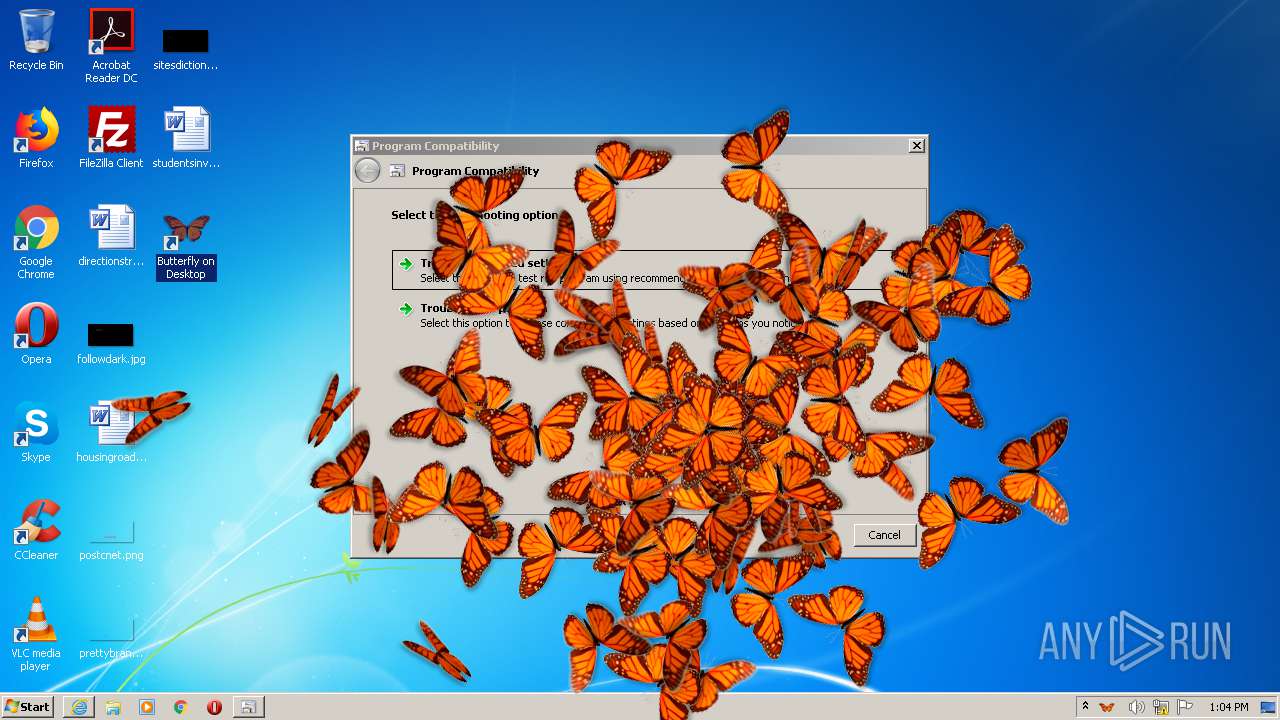
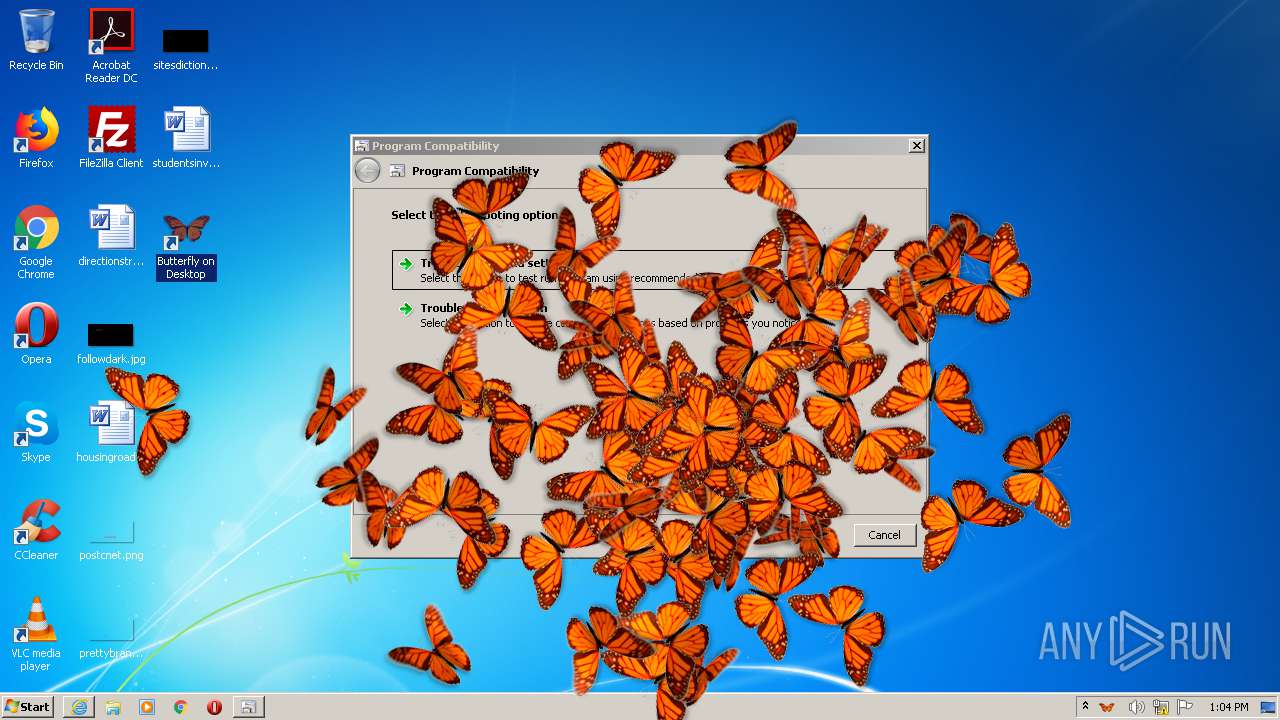
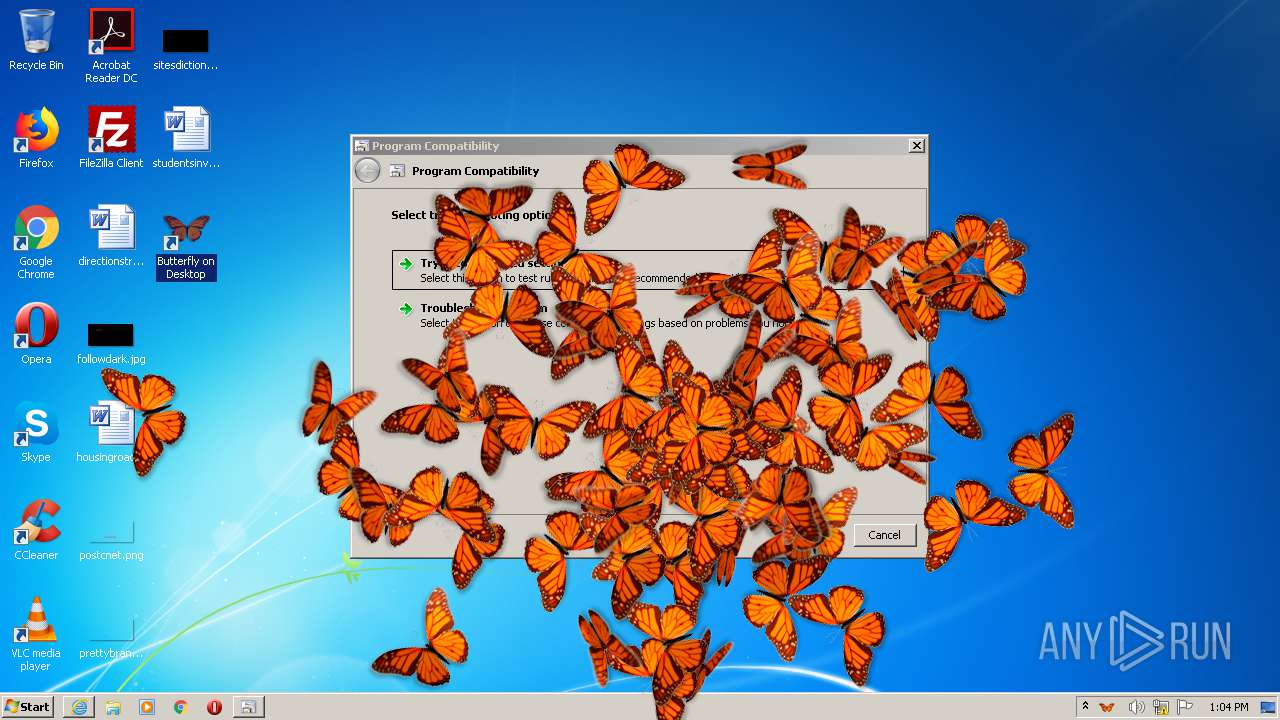
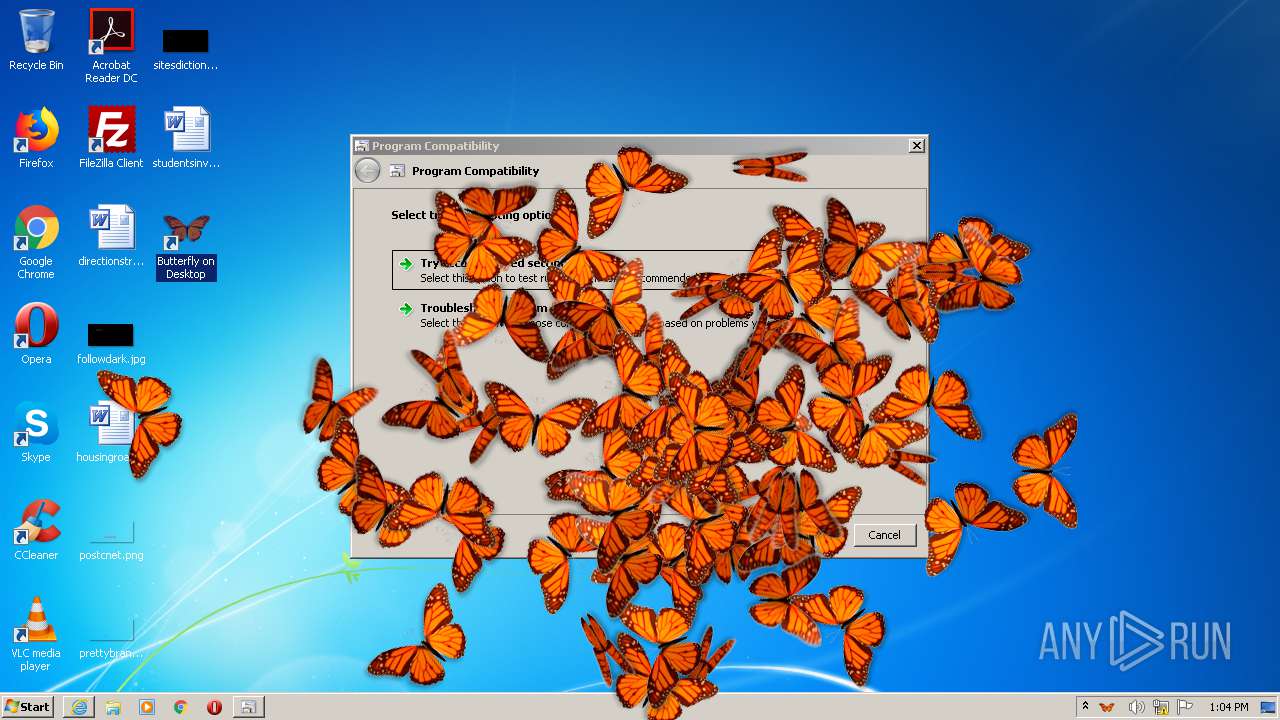
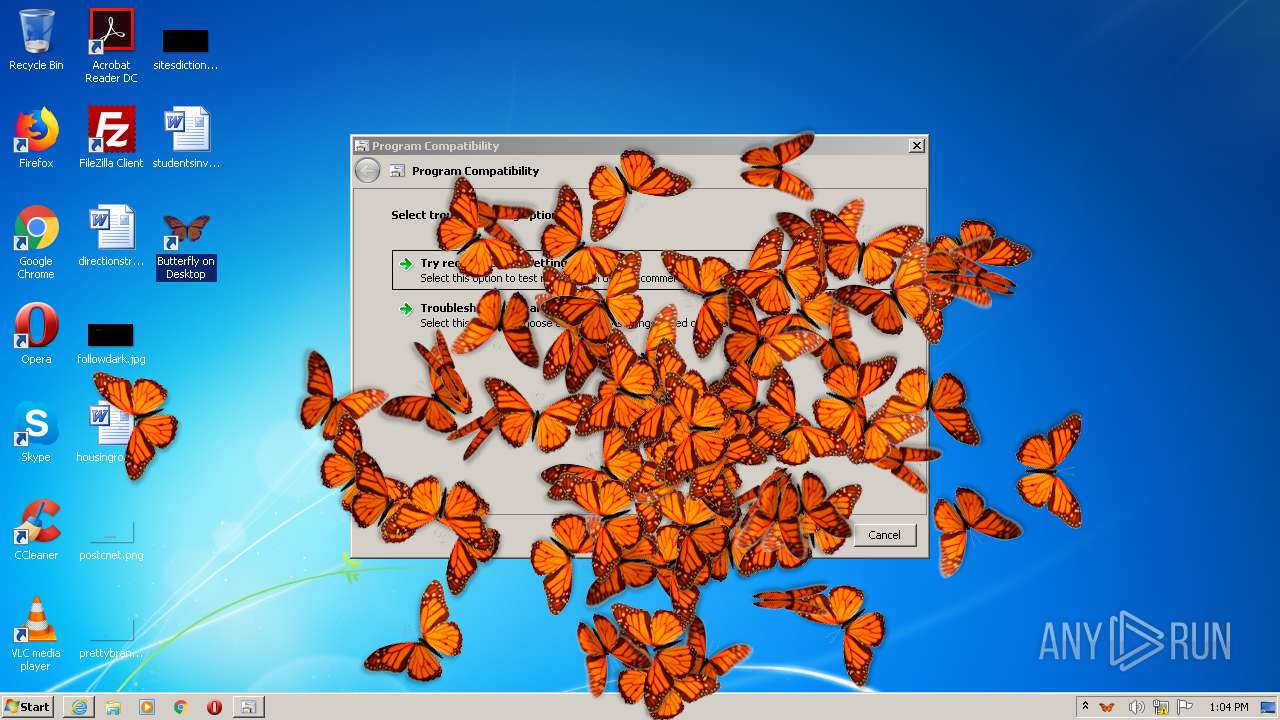
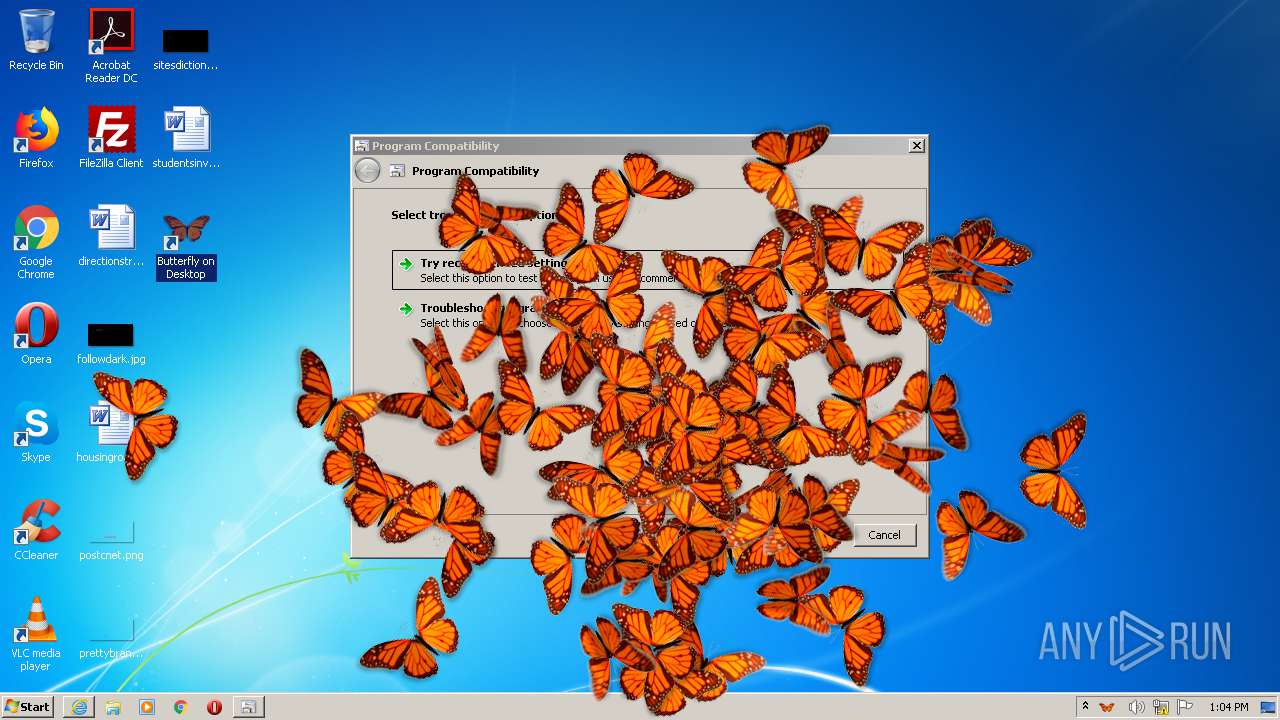
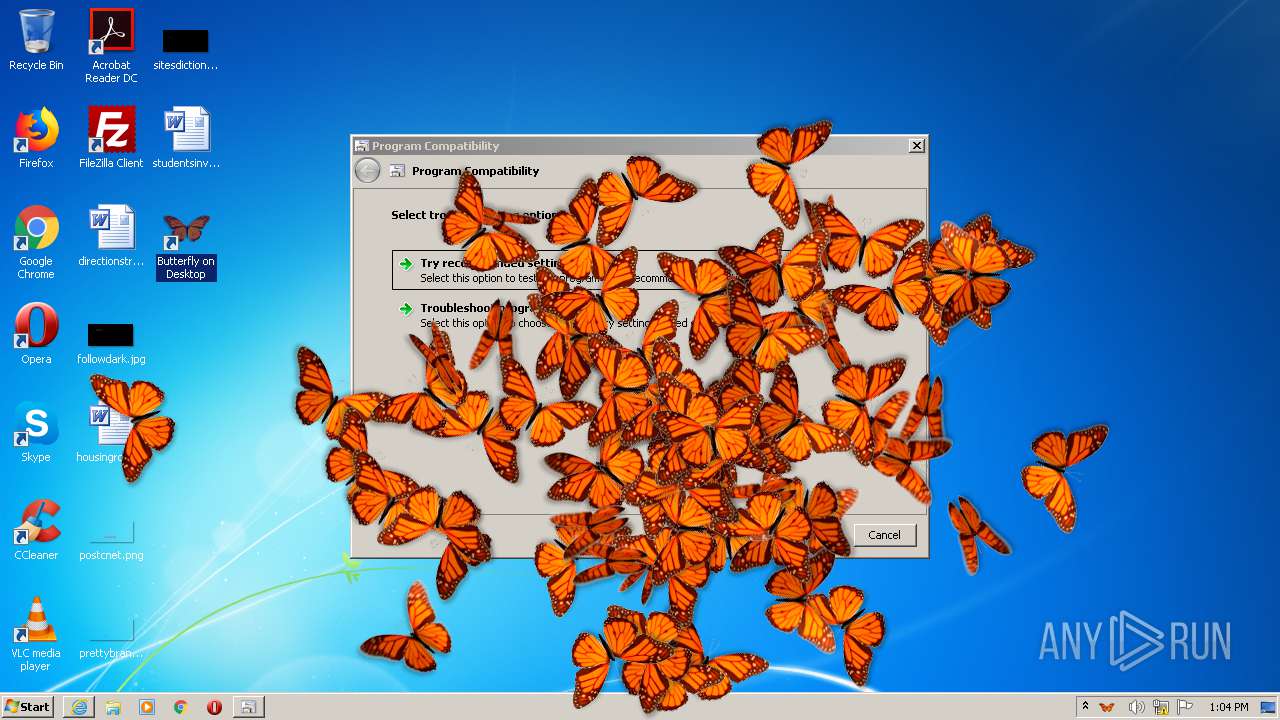
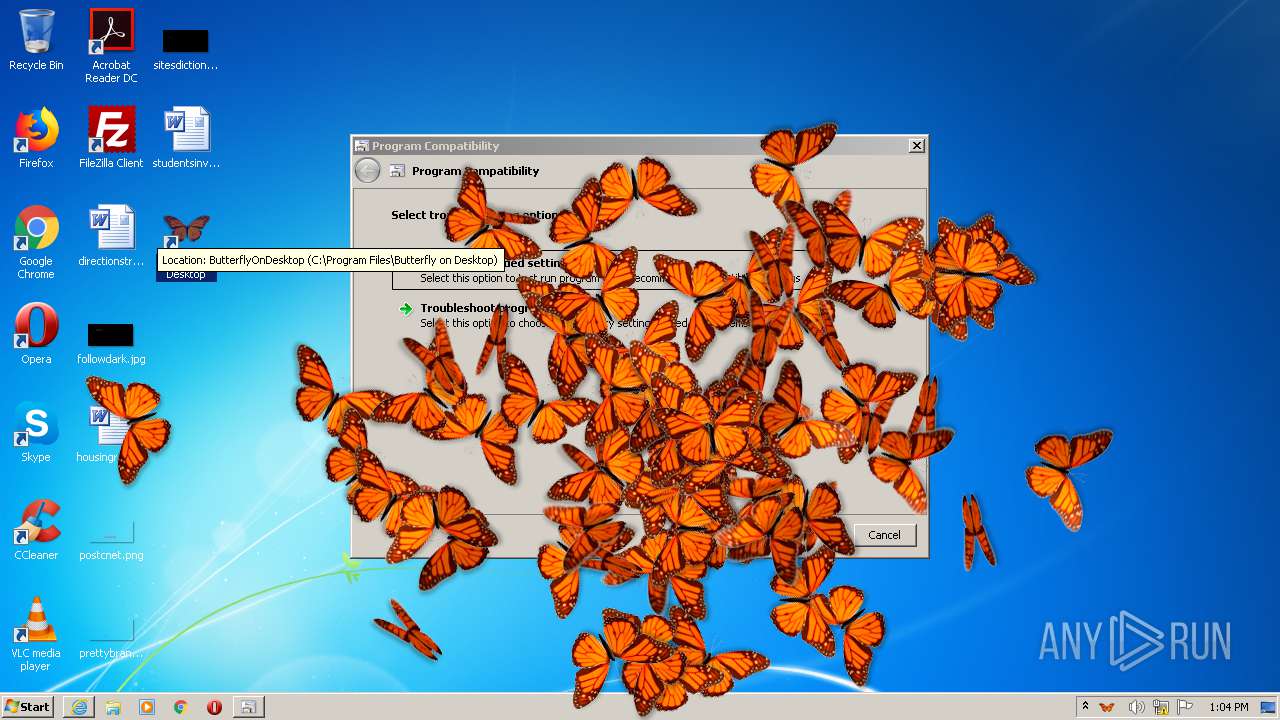
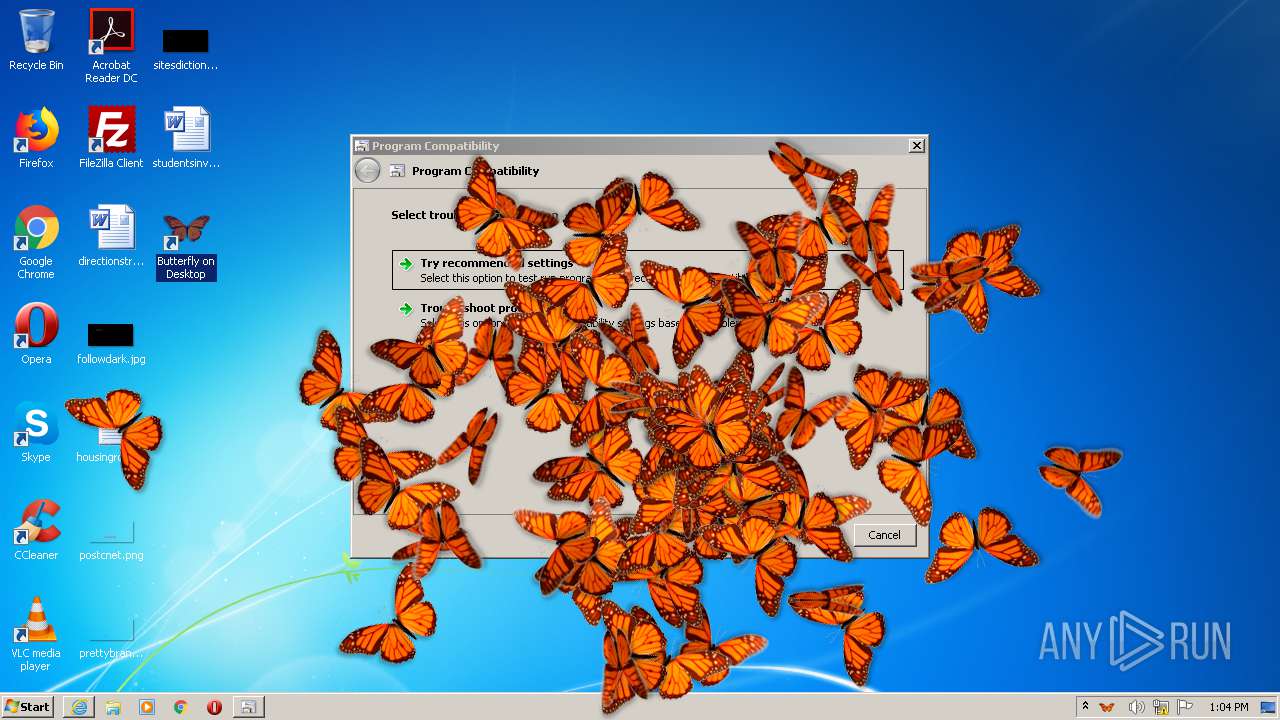
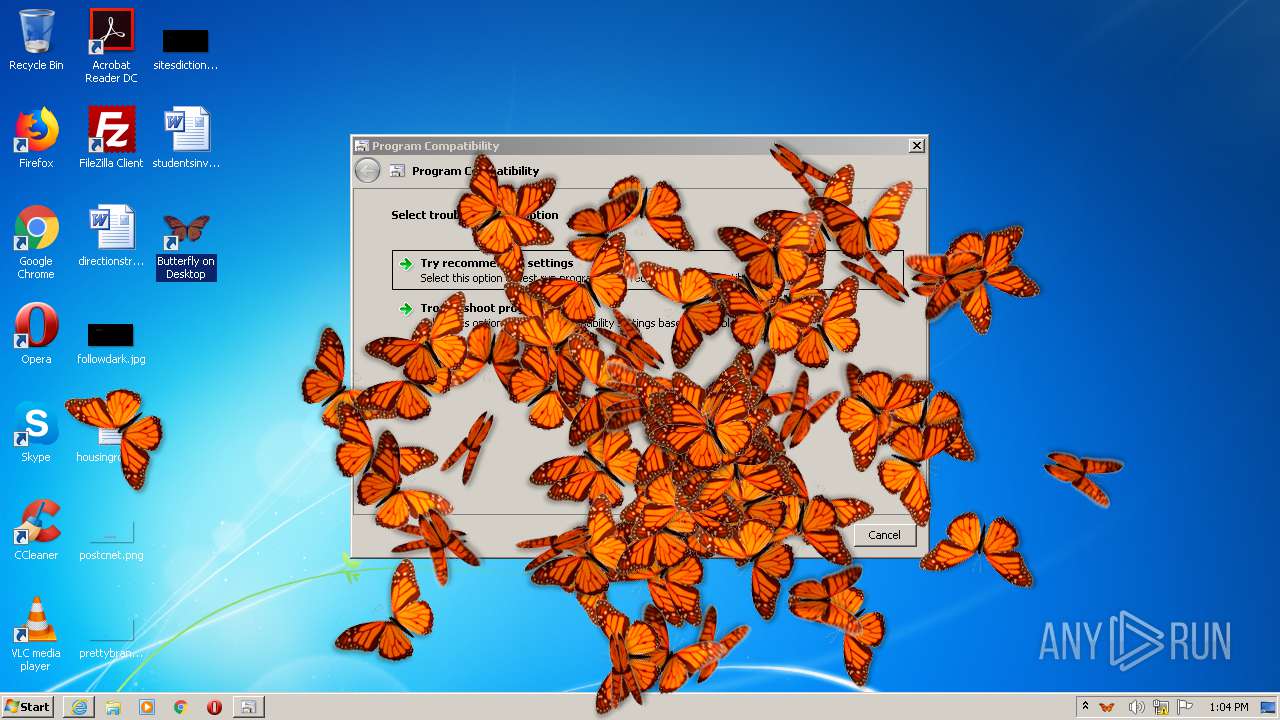
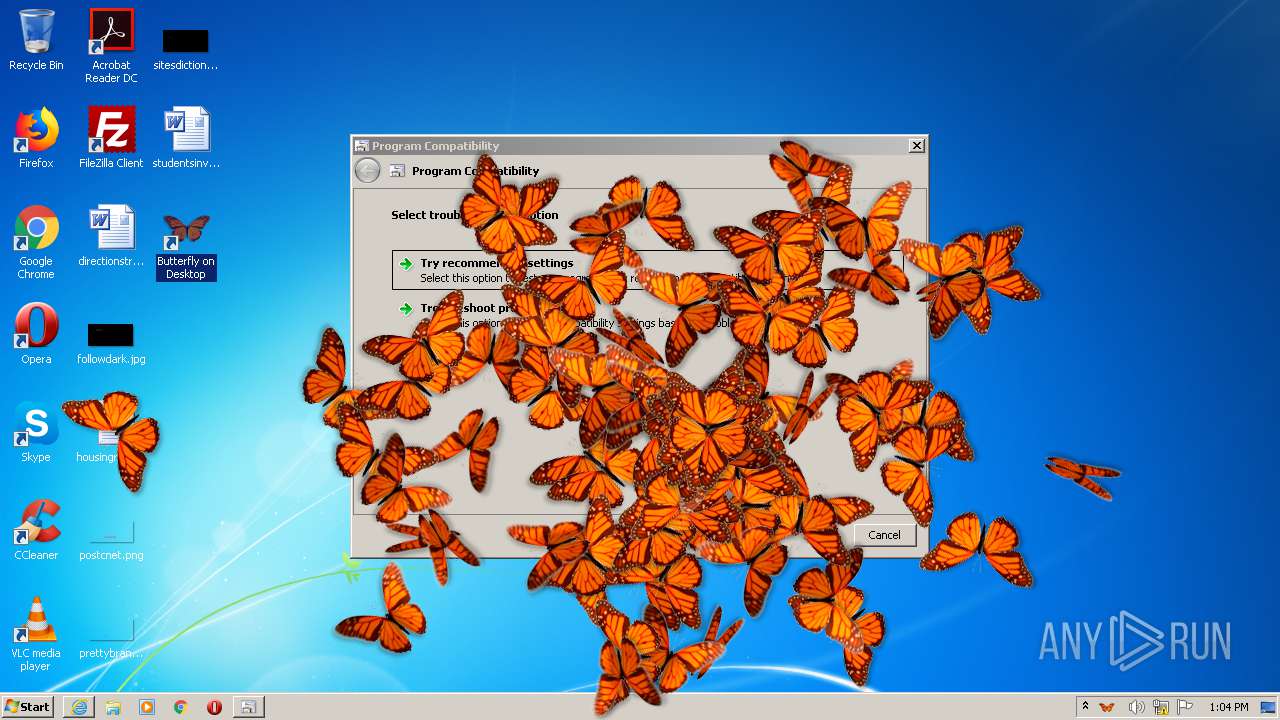
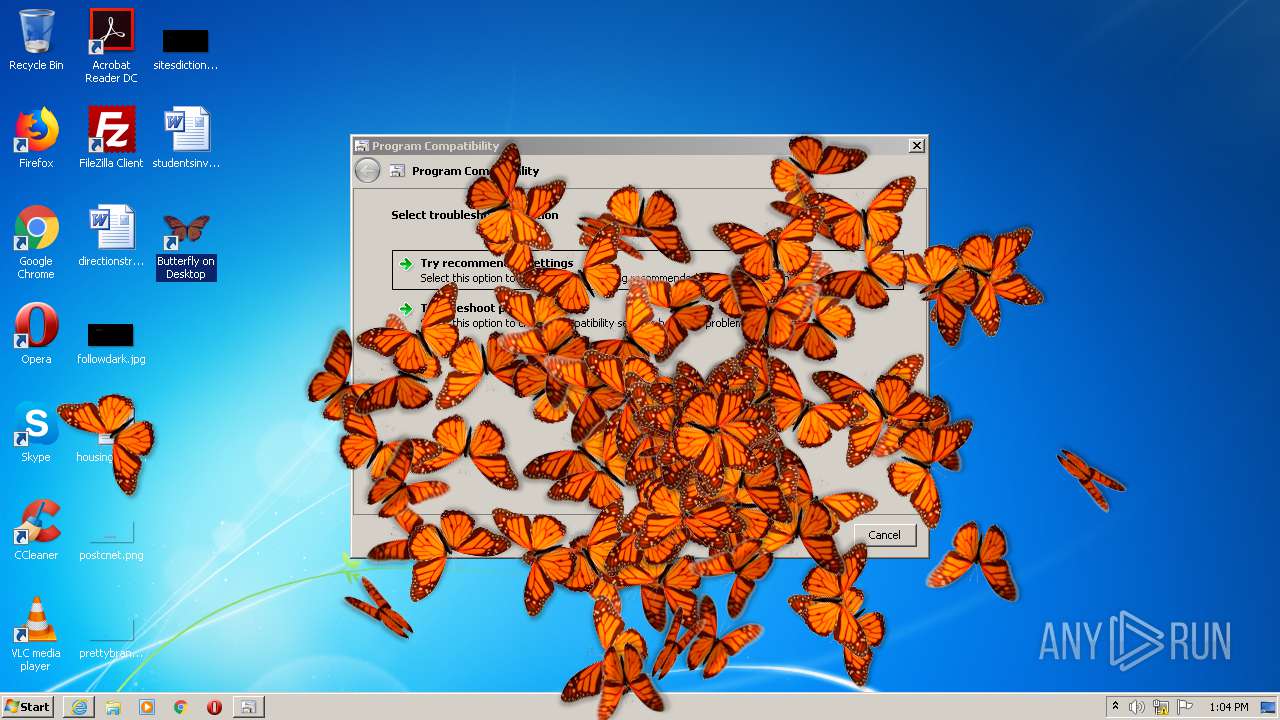
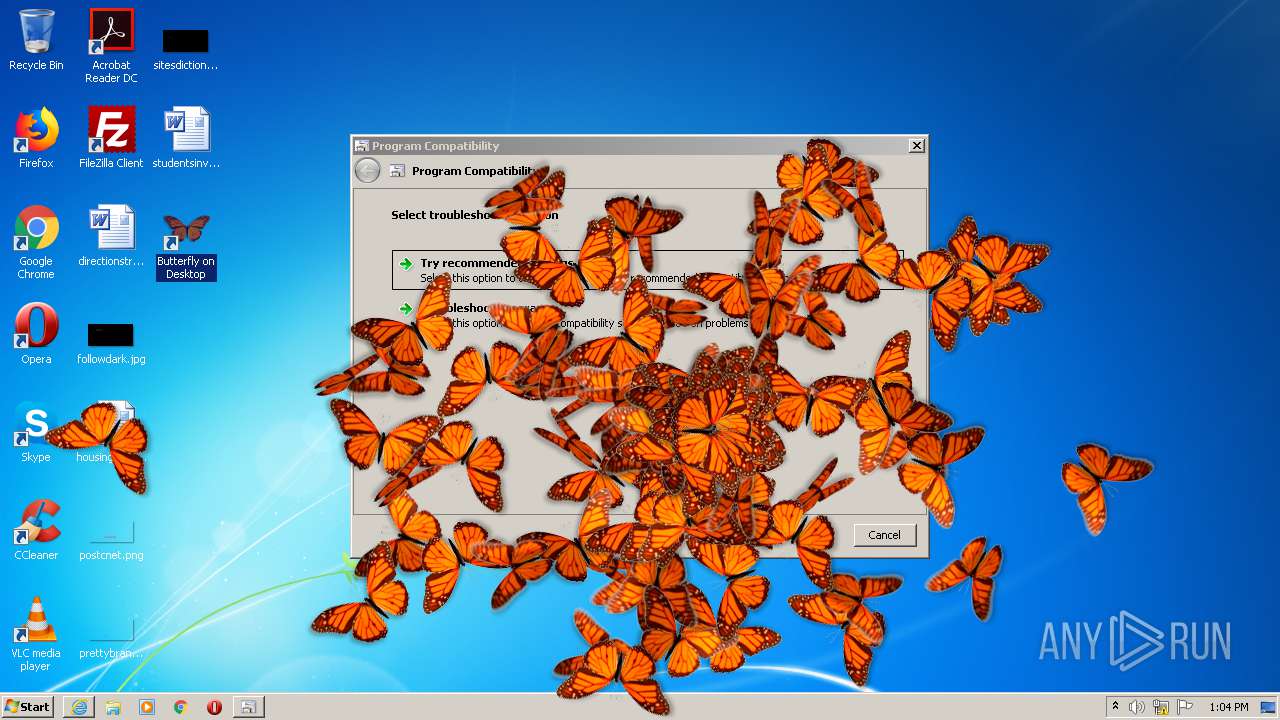
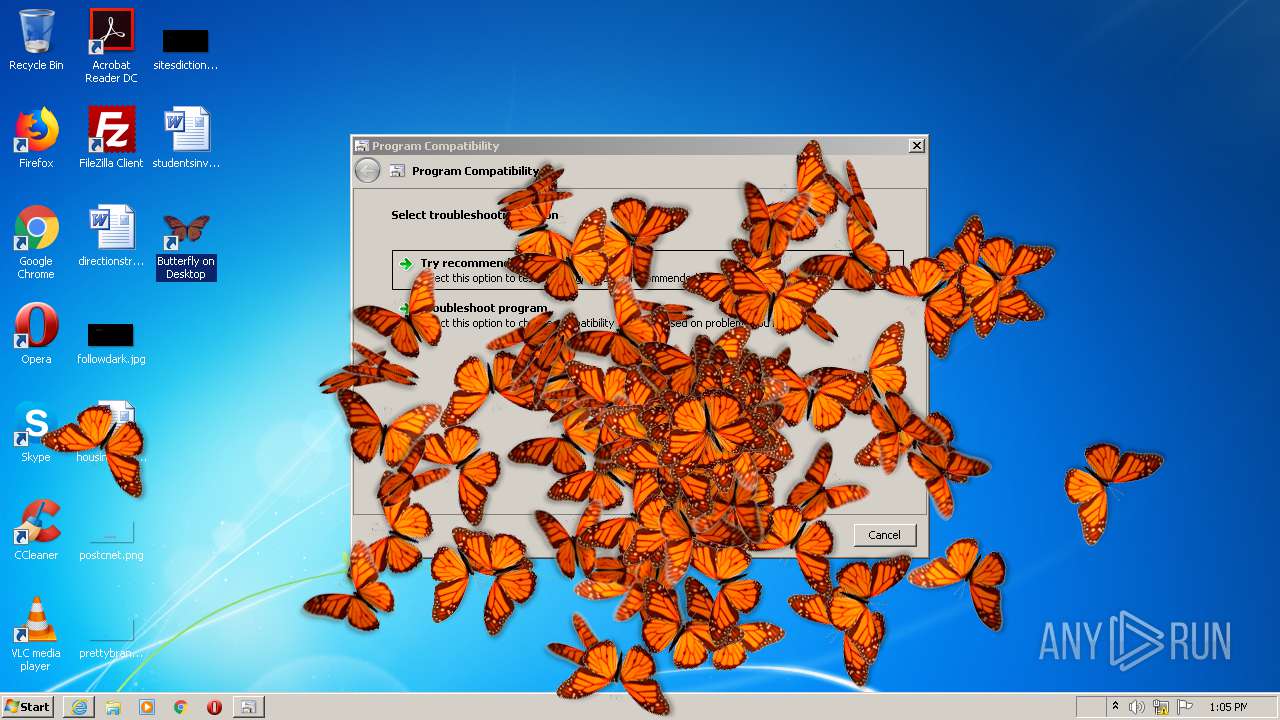
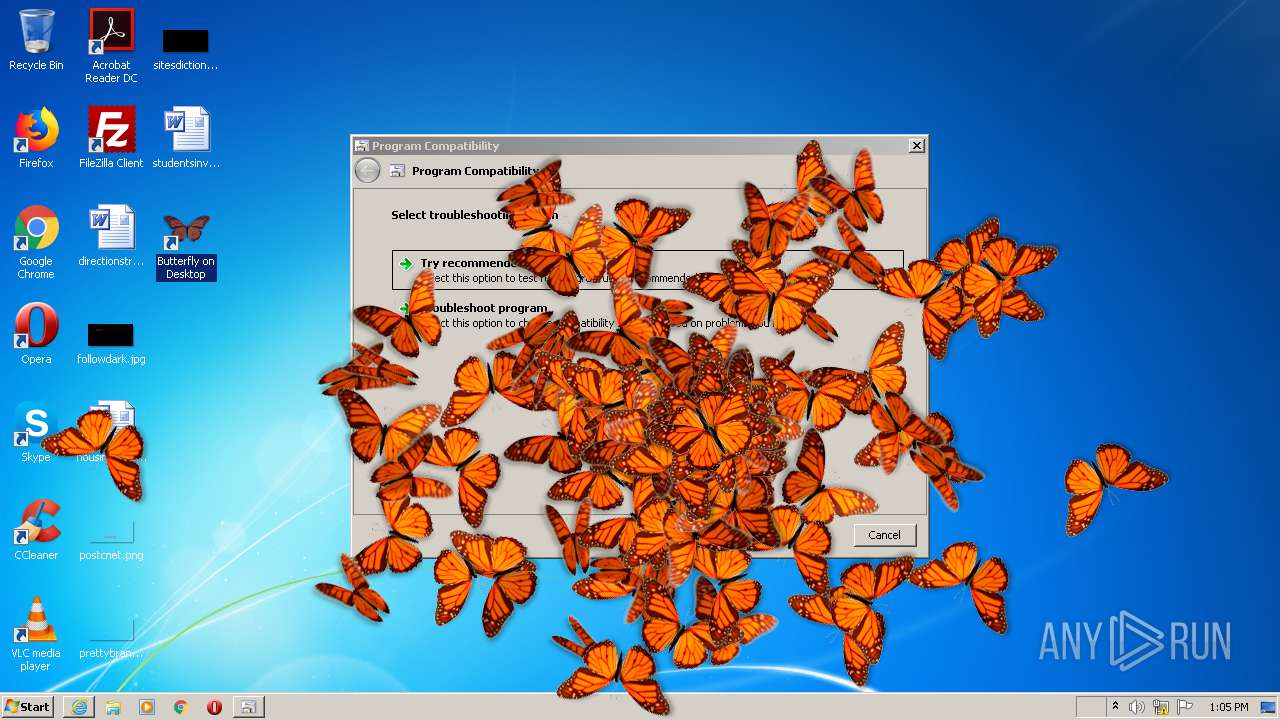
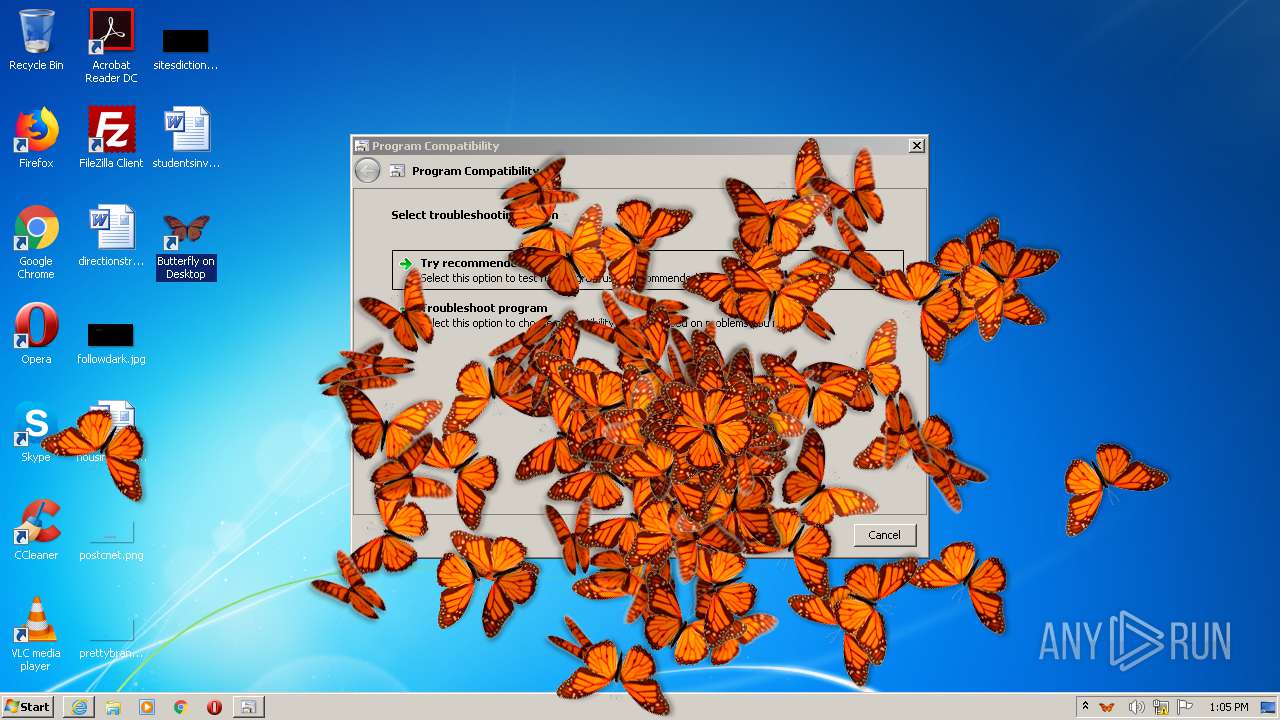
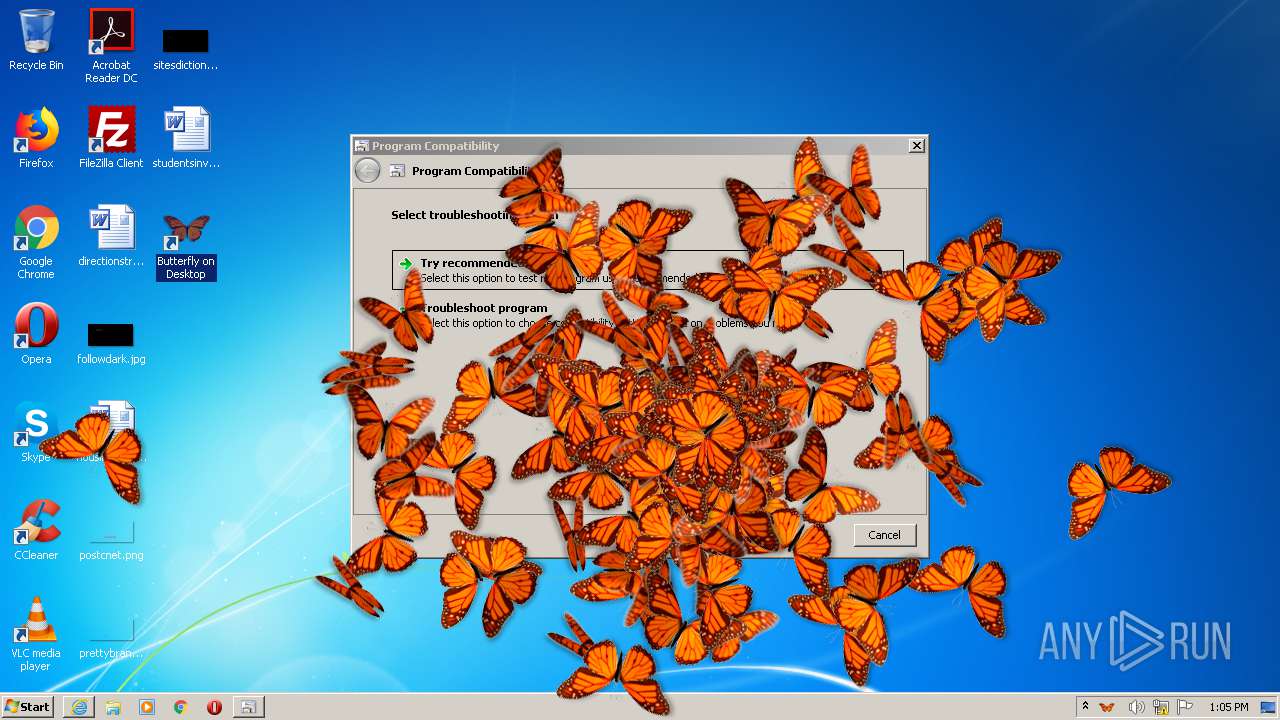
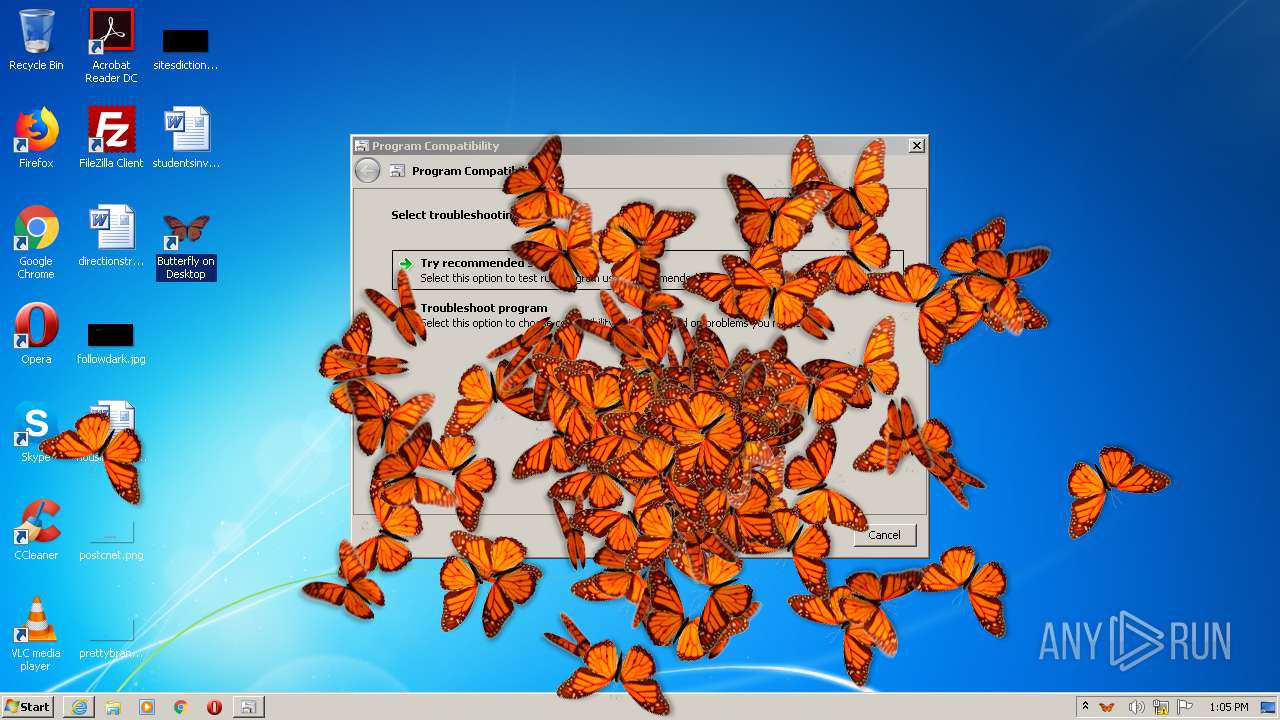
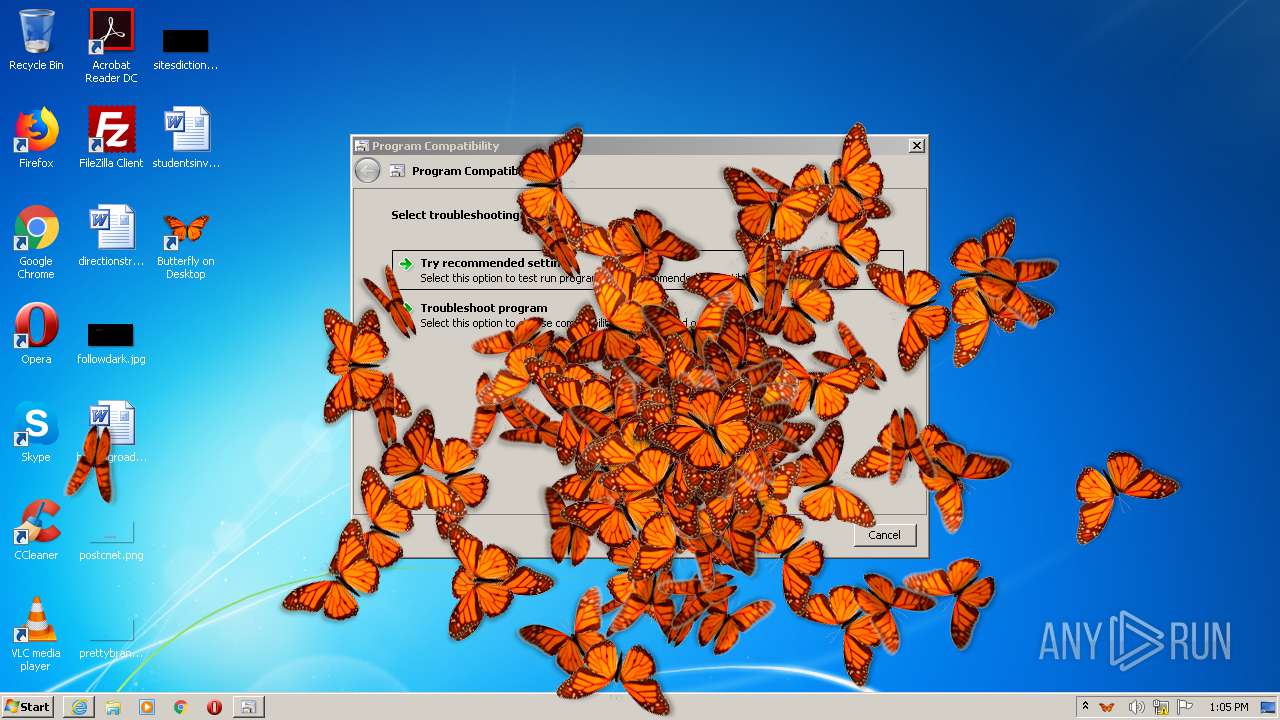
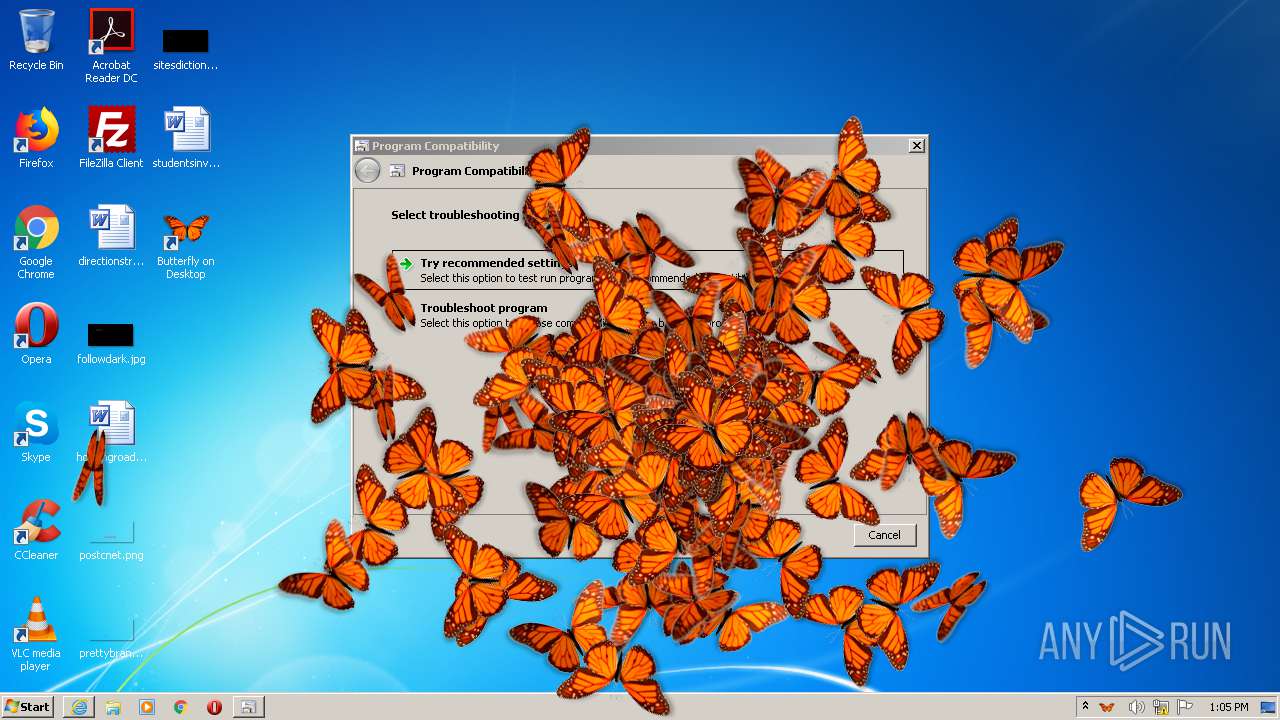
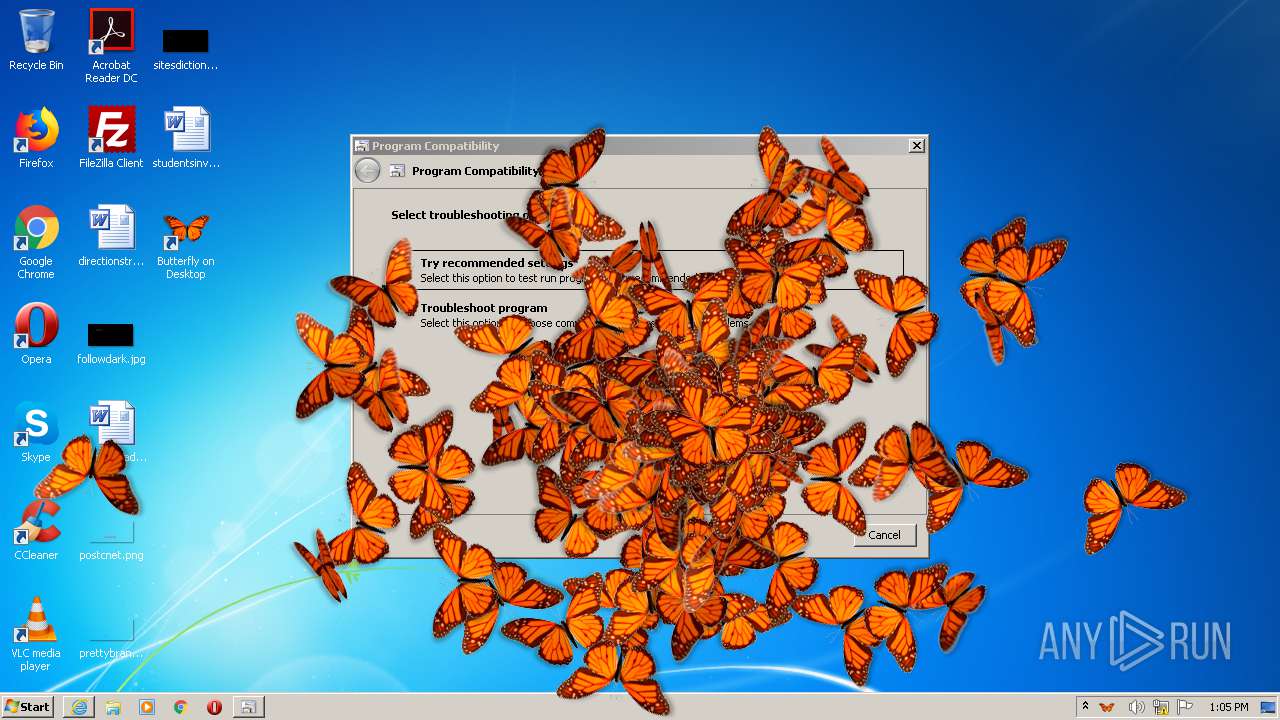
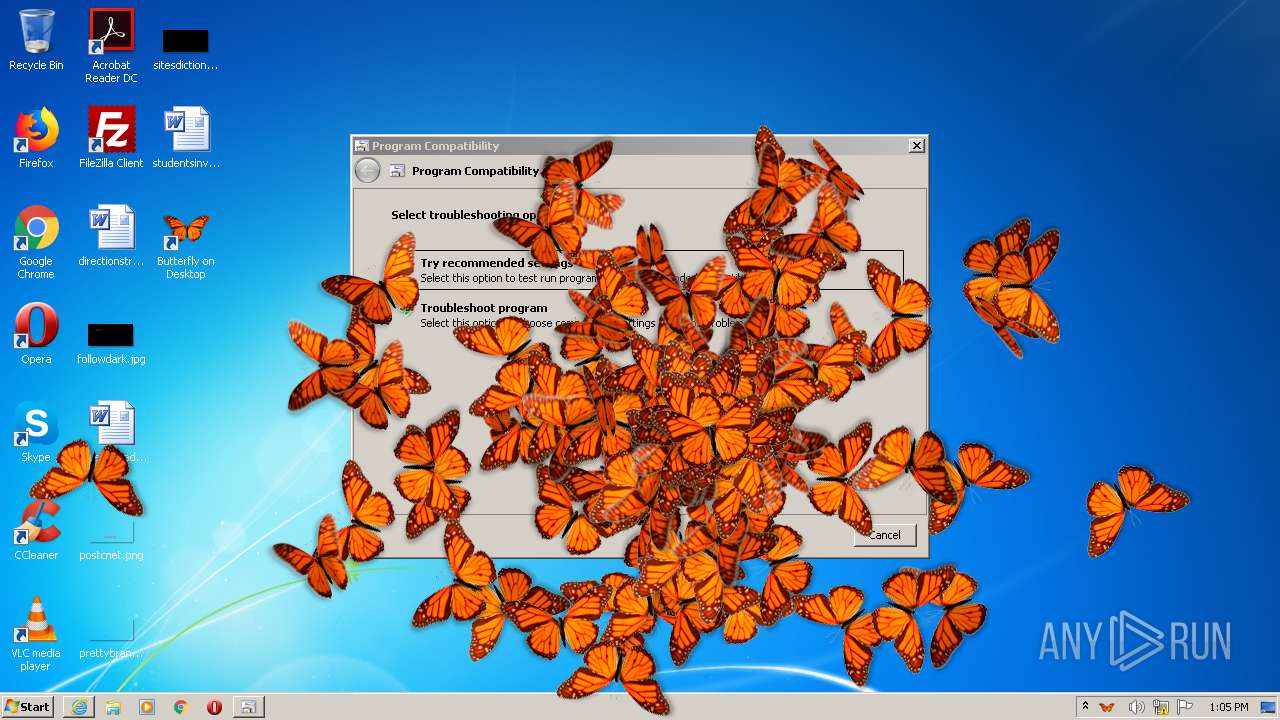
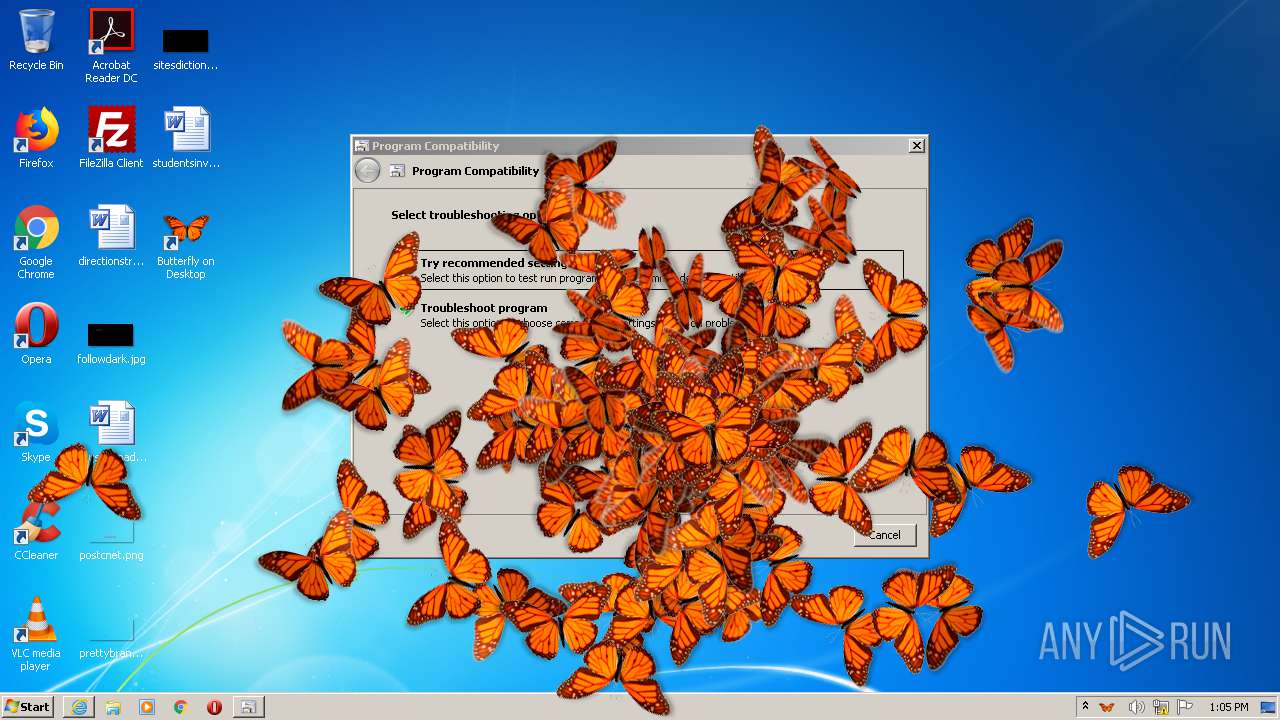
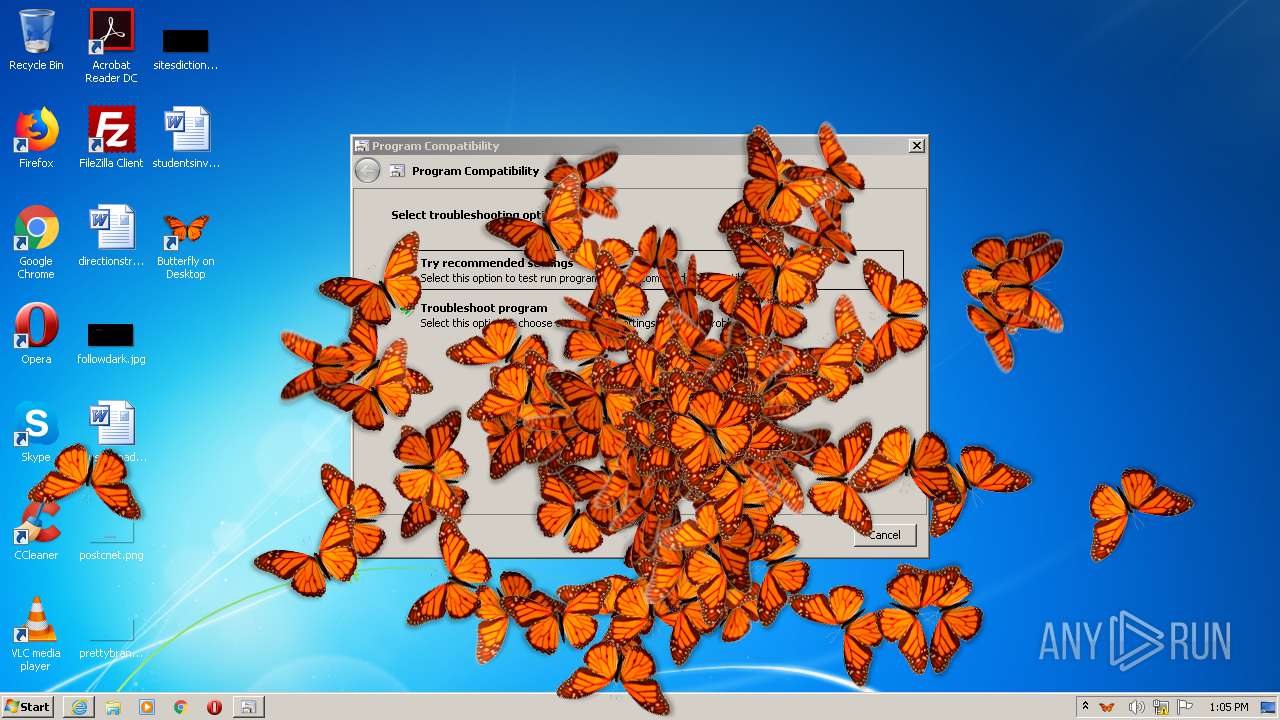
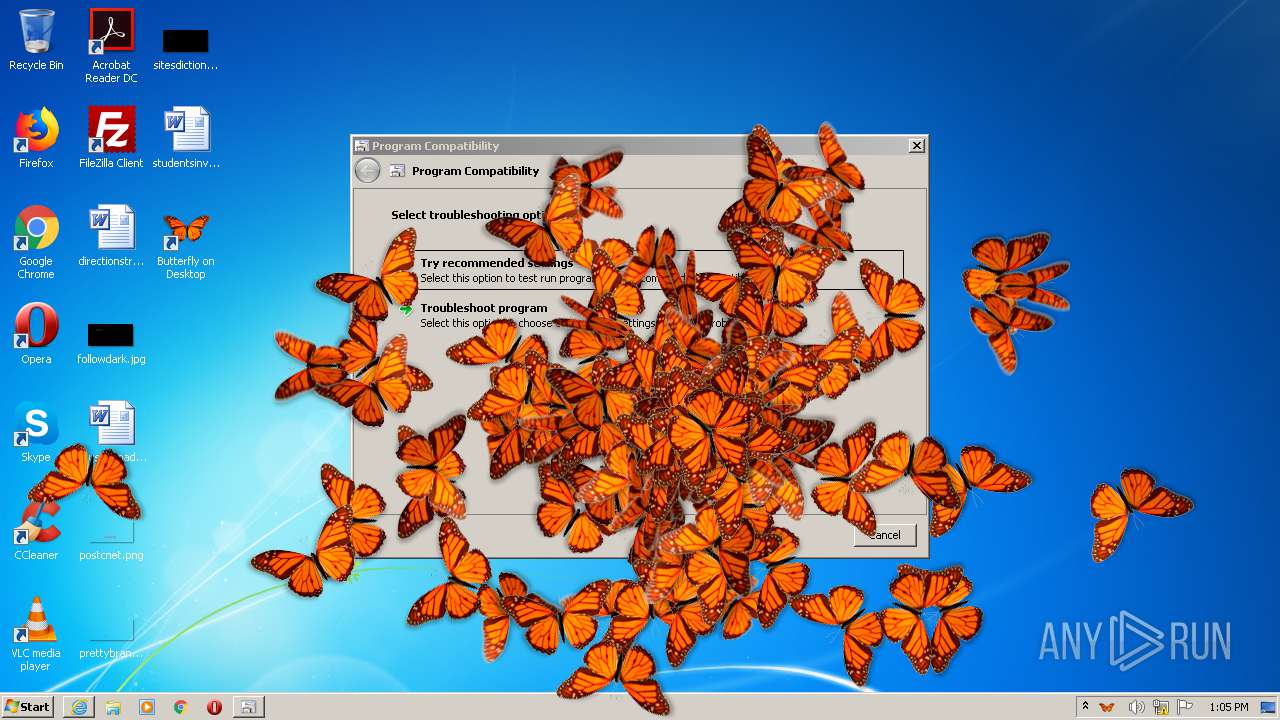
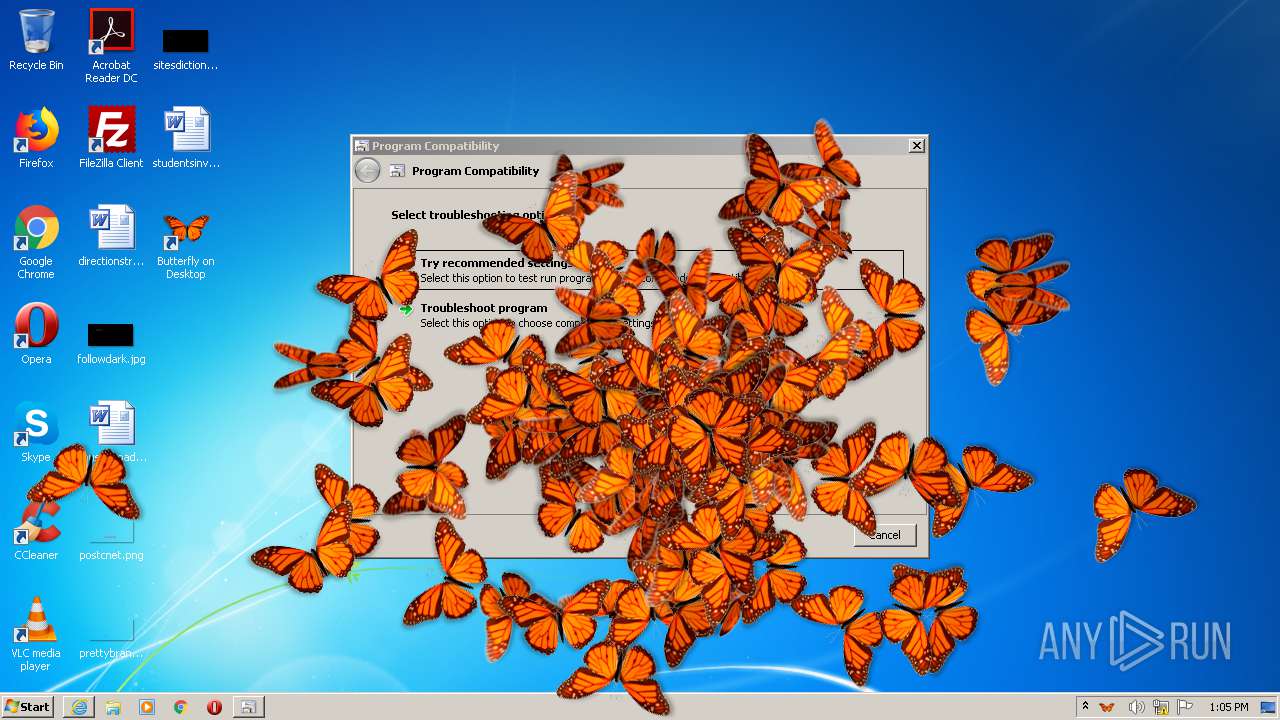
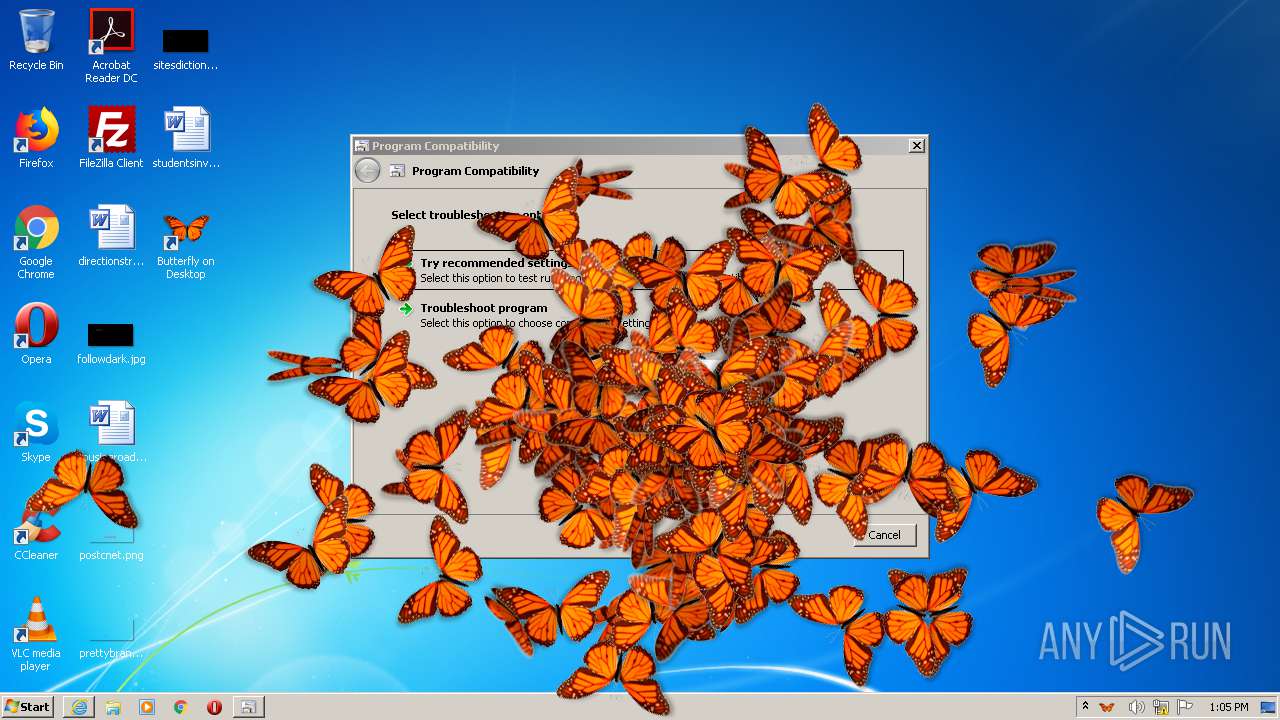
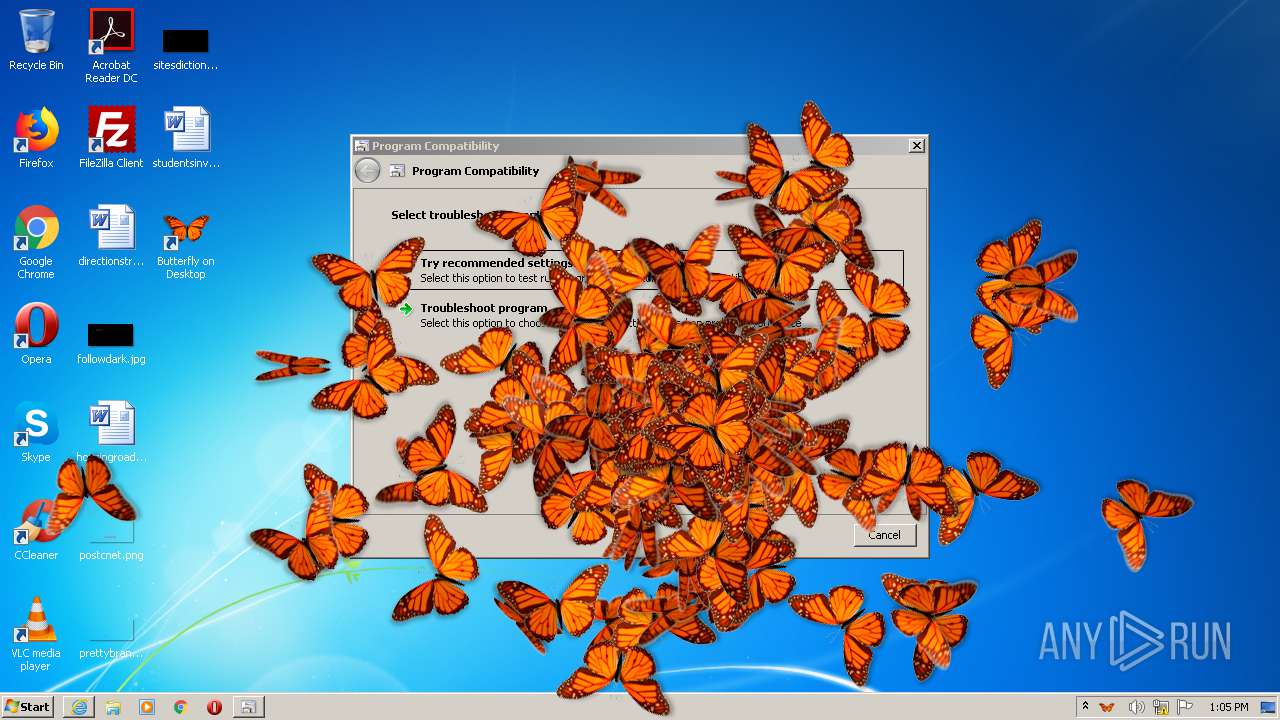
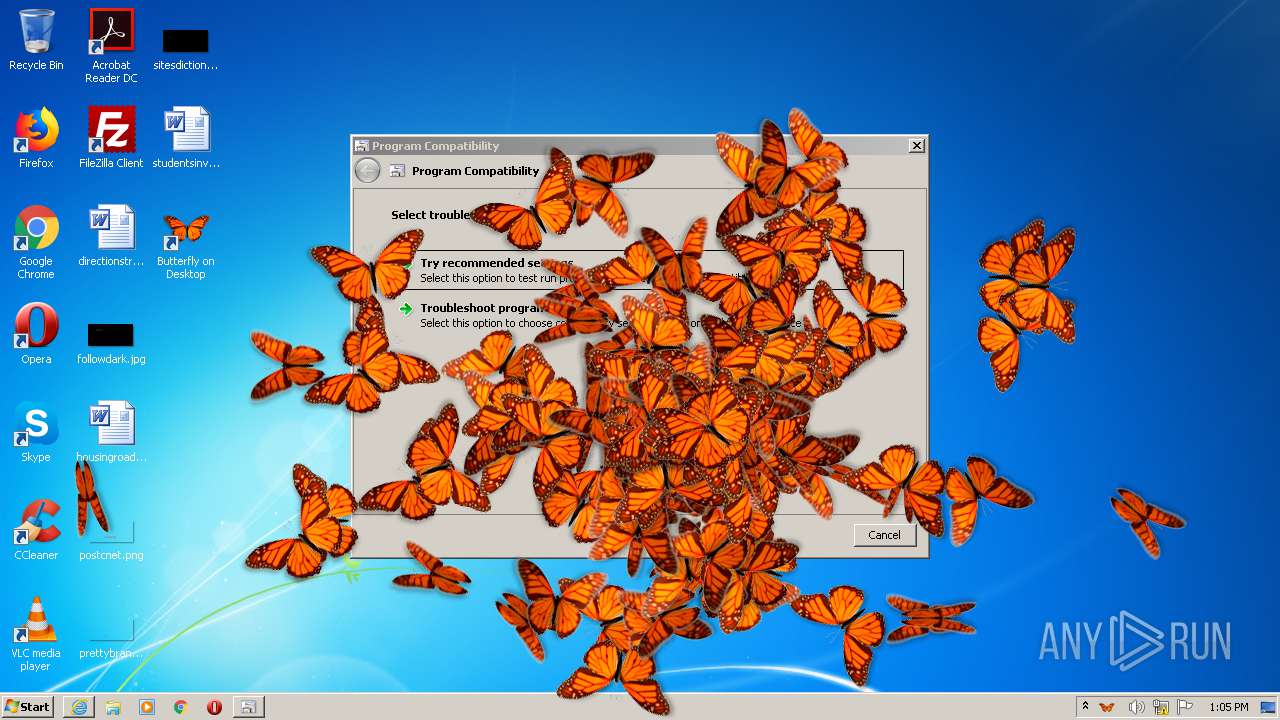
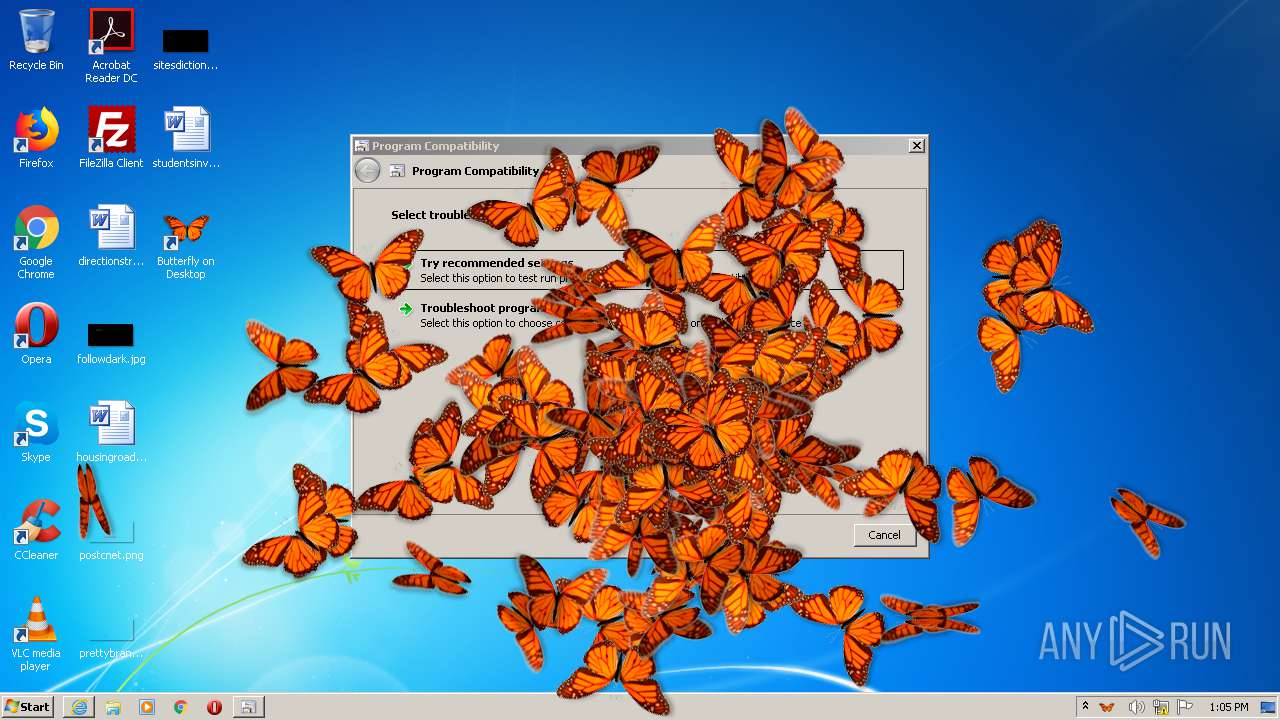
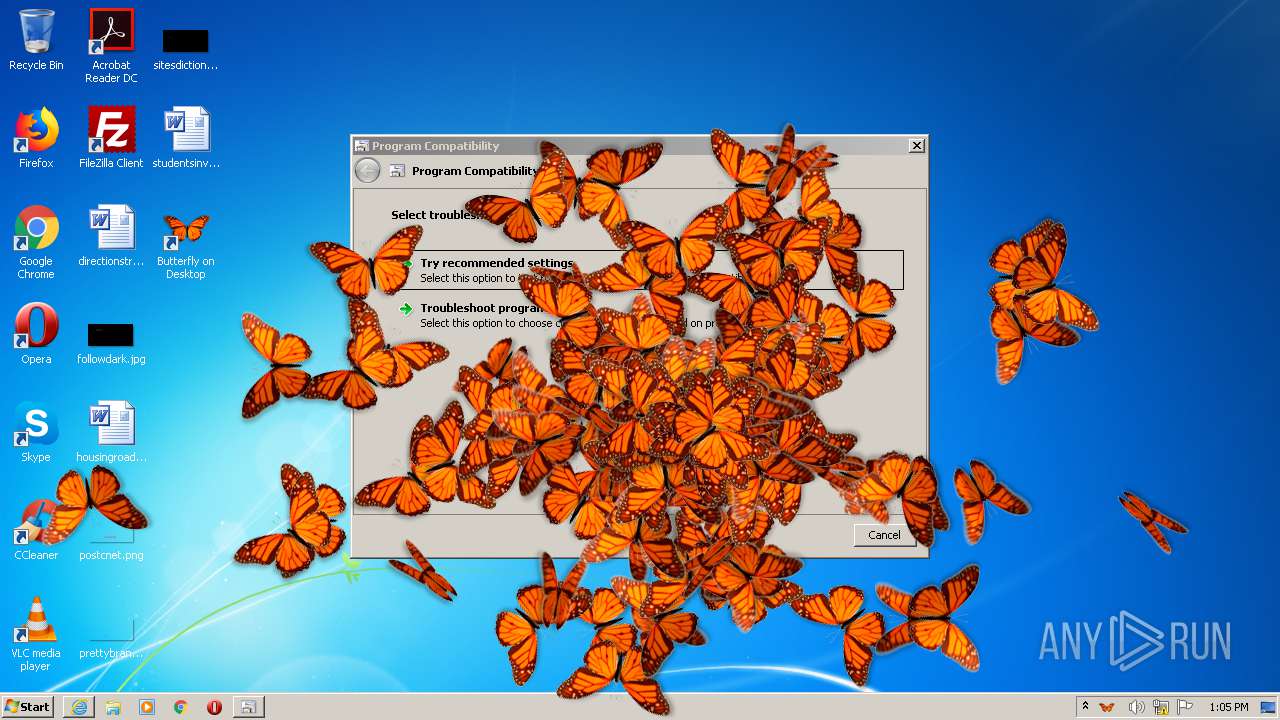
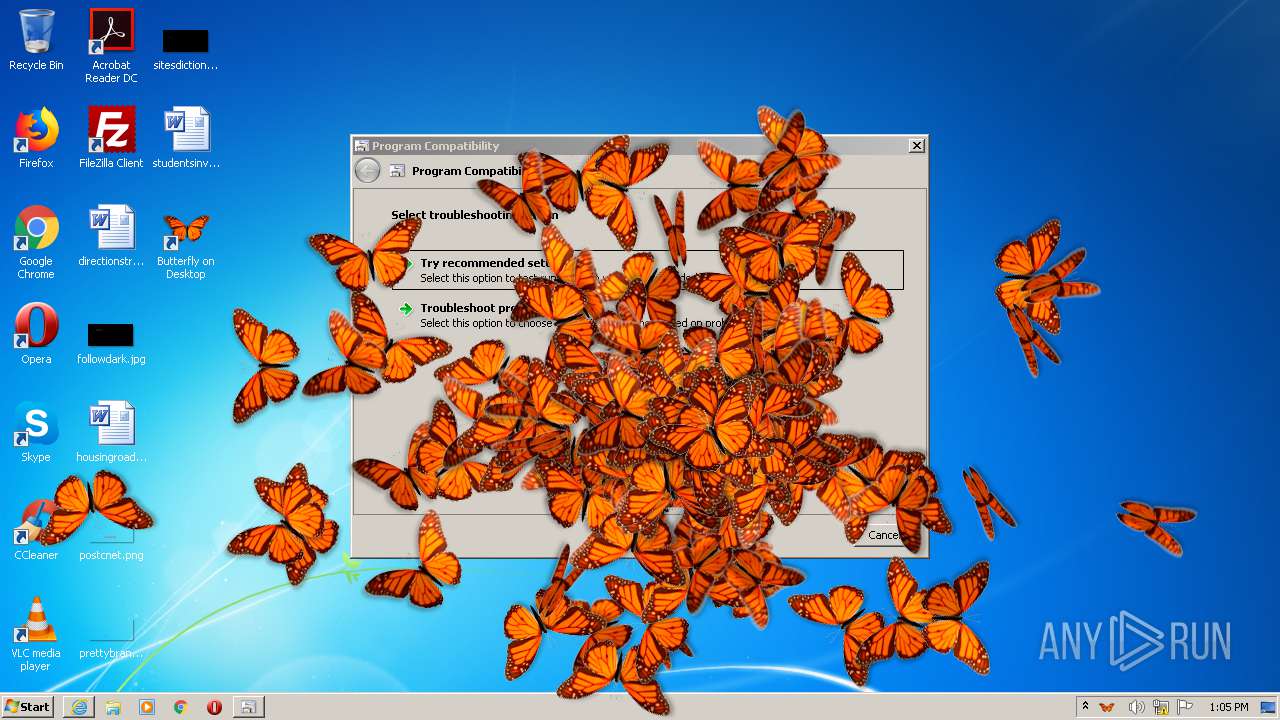
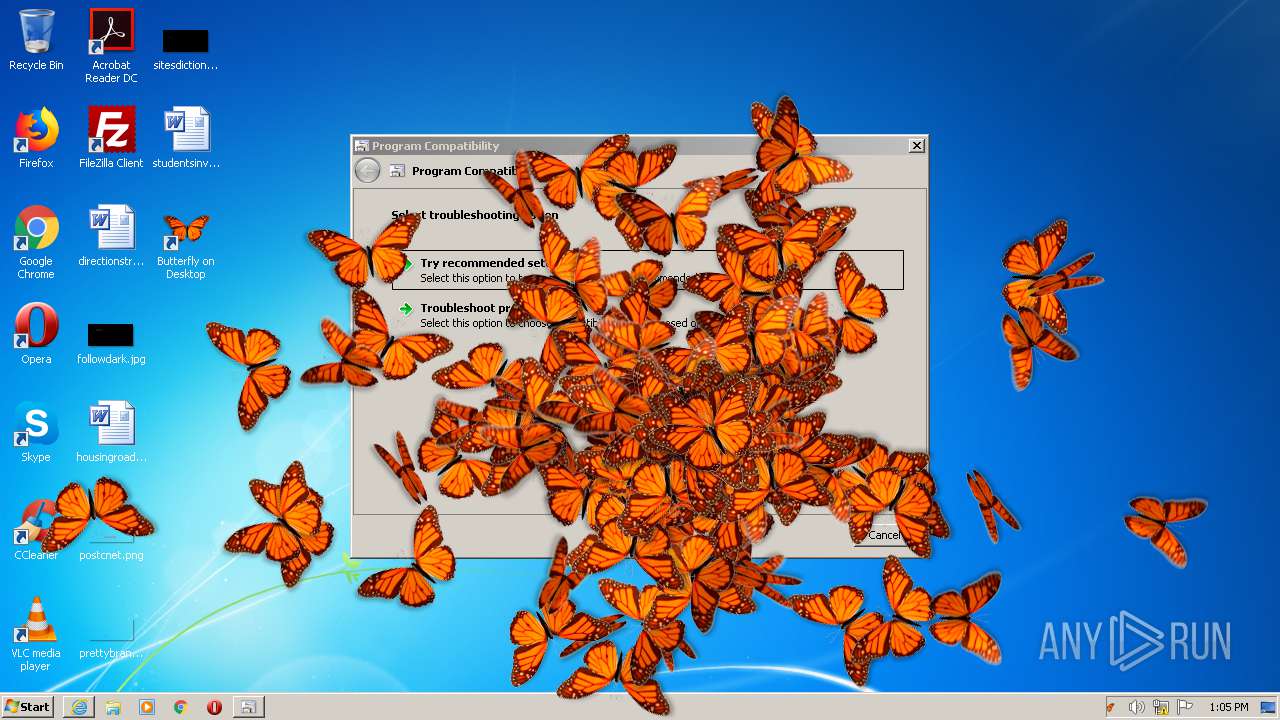
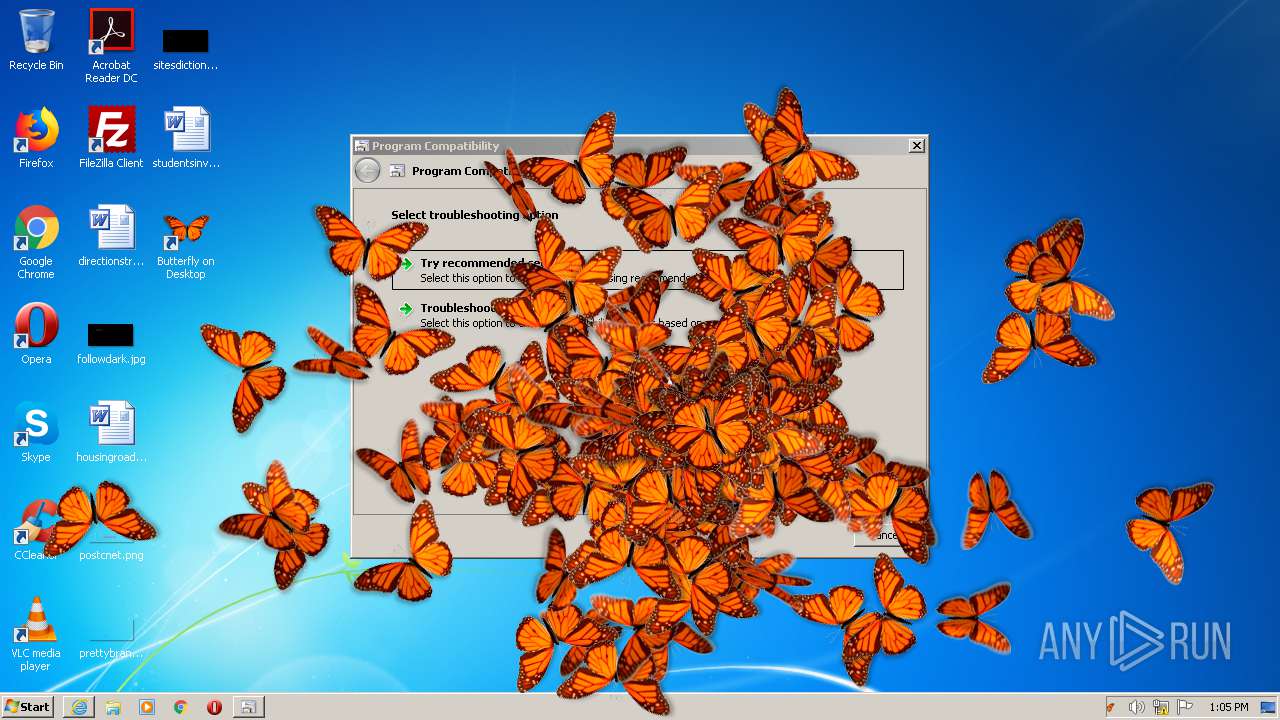
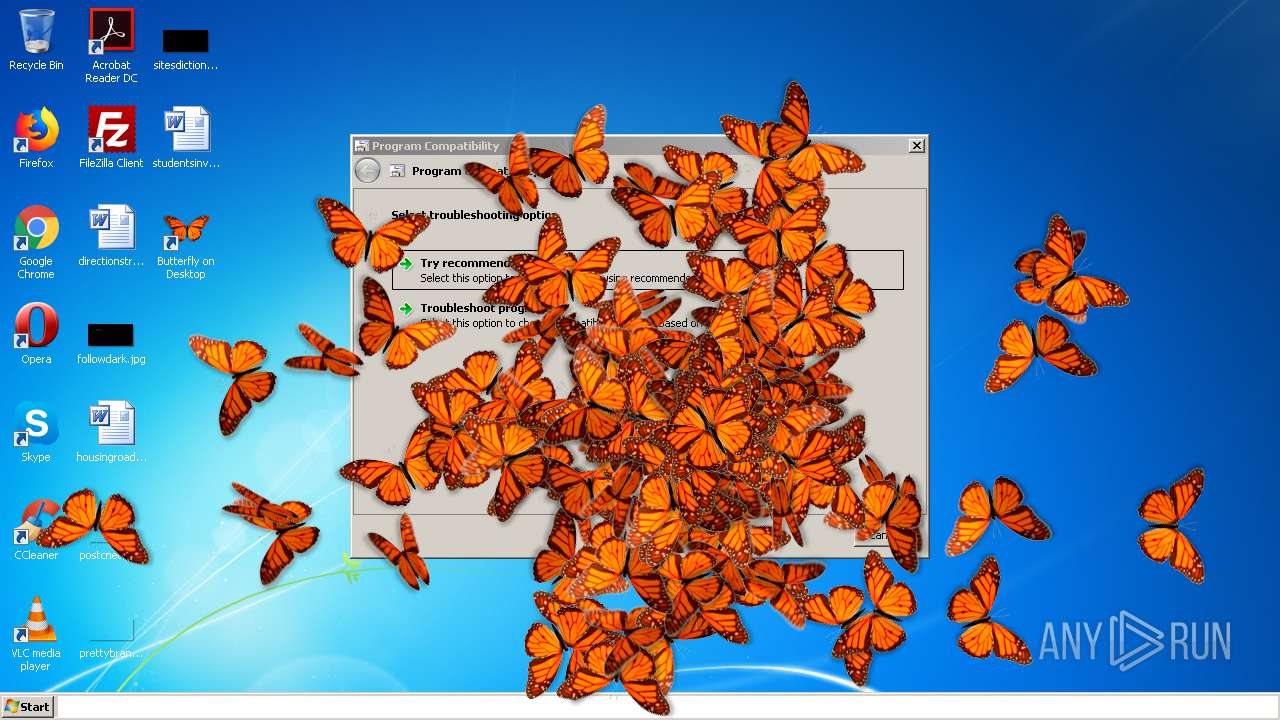
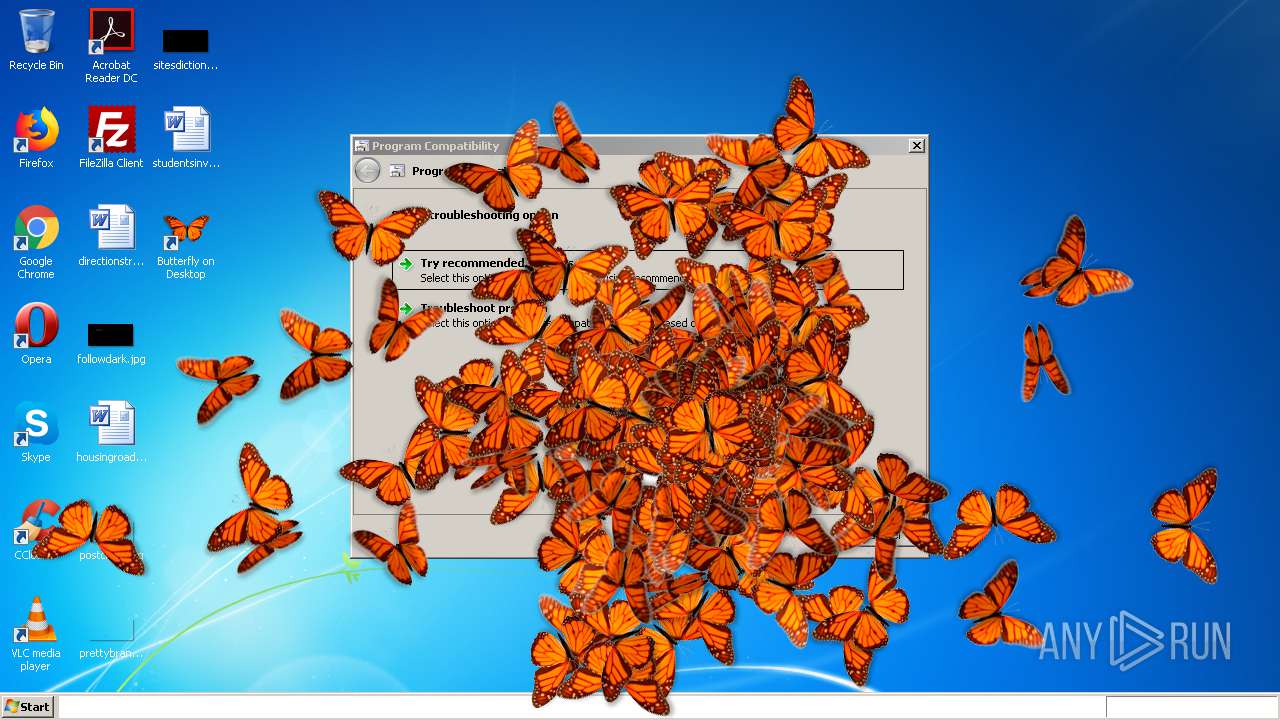
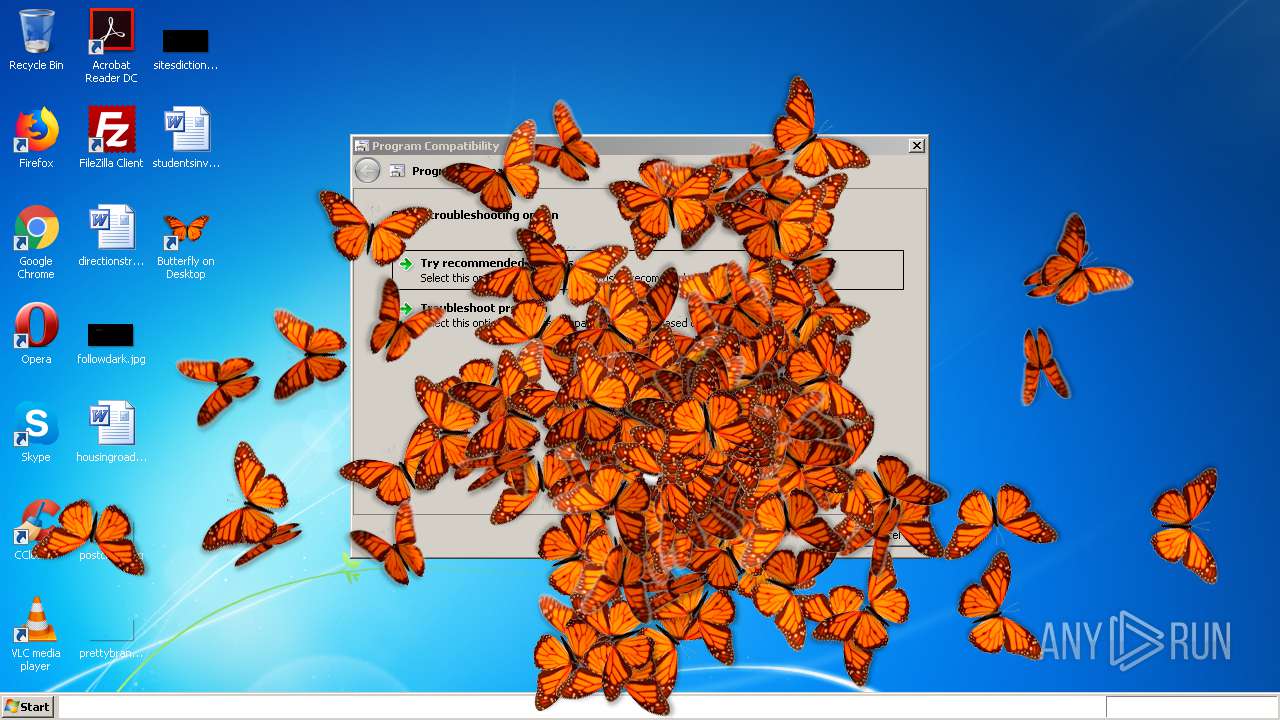
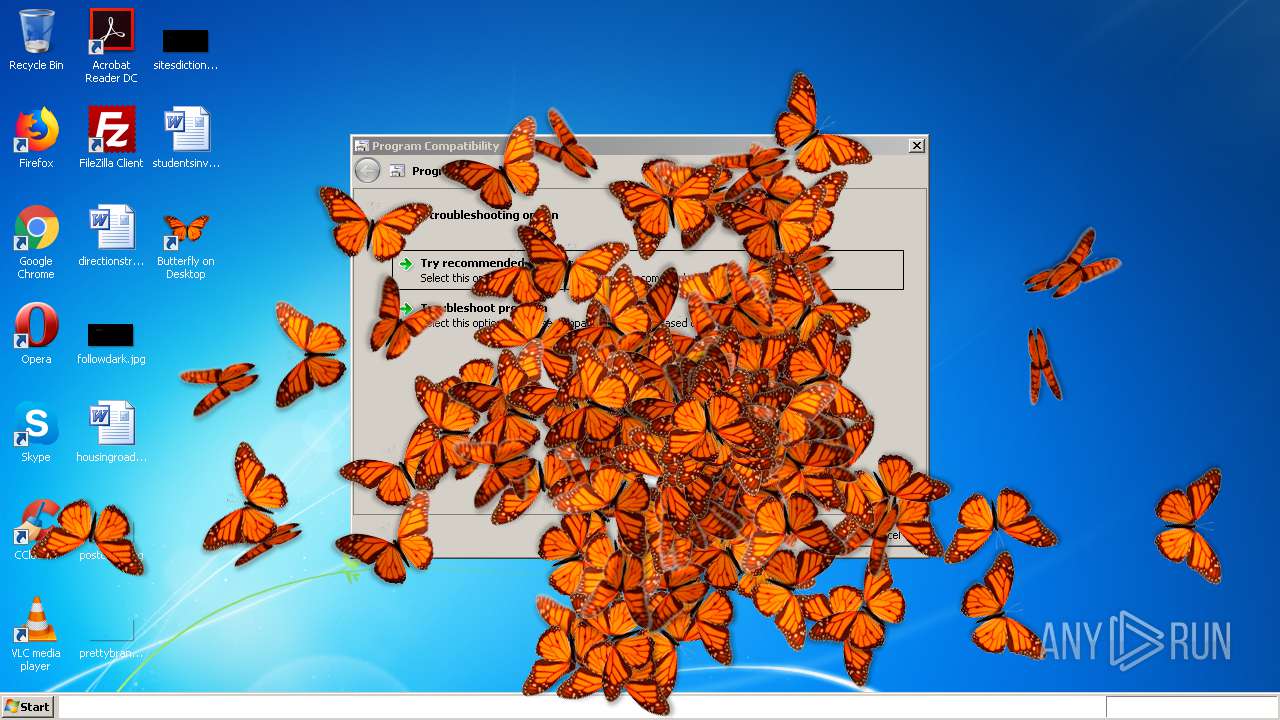
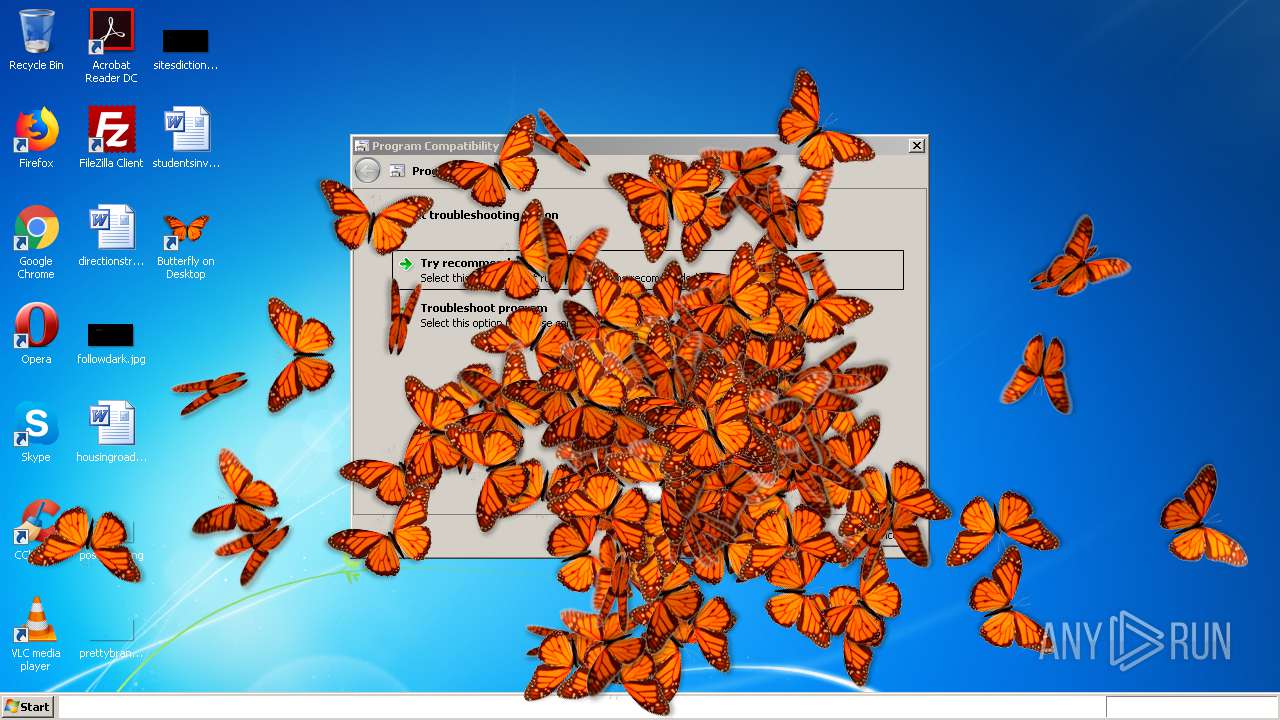
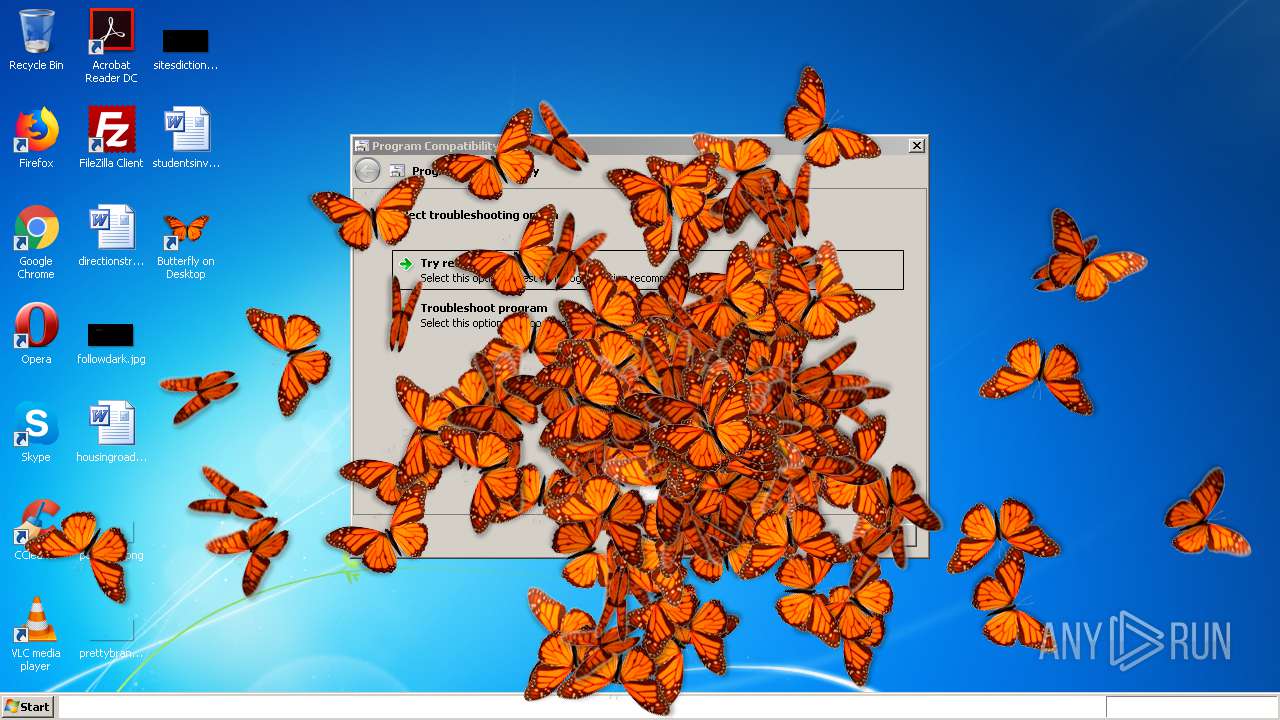
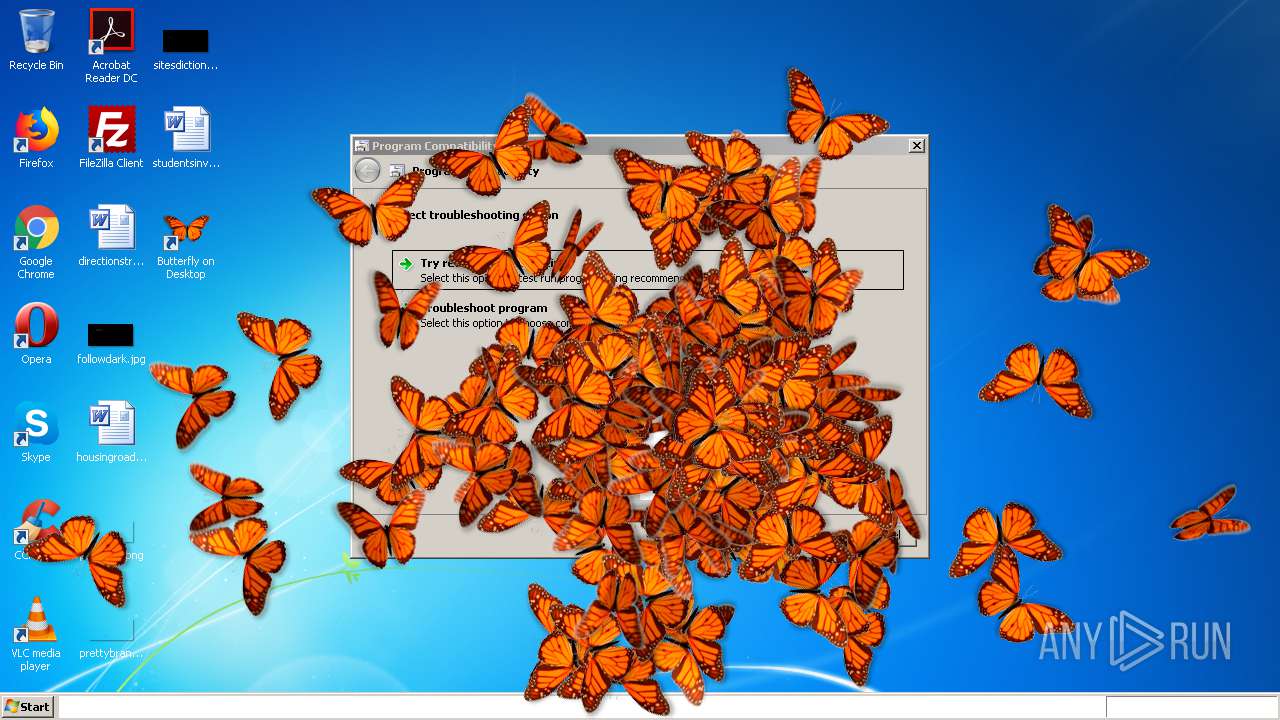
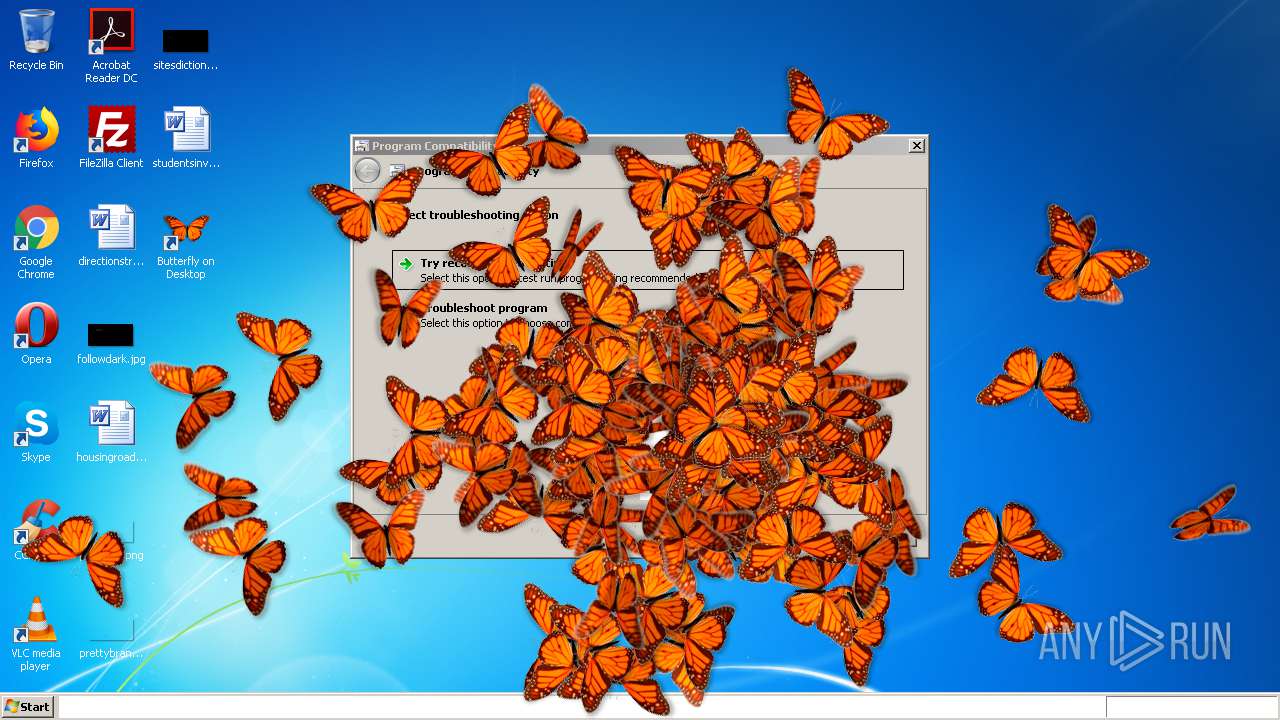
| File name: | butterflyondesktop.exe |
| Full analysis: | https://app.any.run/tasks/bd36d9b2-360f-48bc-af9c-ffea538e8740 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2021, 13:02:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1535AA21451192109B86BE9BCC7C4345 |
| SHA1: | 1AF211C686C4D4BF0239ED6620358A19691CF88C |
| SHA256: | 4641AF6A0071E11E13AD3B1CD950E01300542C2B9EFB6AE92FFECEDDE974A4A6 |
| SSDEEP: | 49152:5aA7f7tlVmdqK23H2bpHI4Qs5ABV9WRHZRsgI82lcHGAaKLinXBgJ:Q+VMkX224QsWBq5SfARGRgJ |
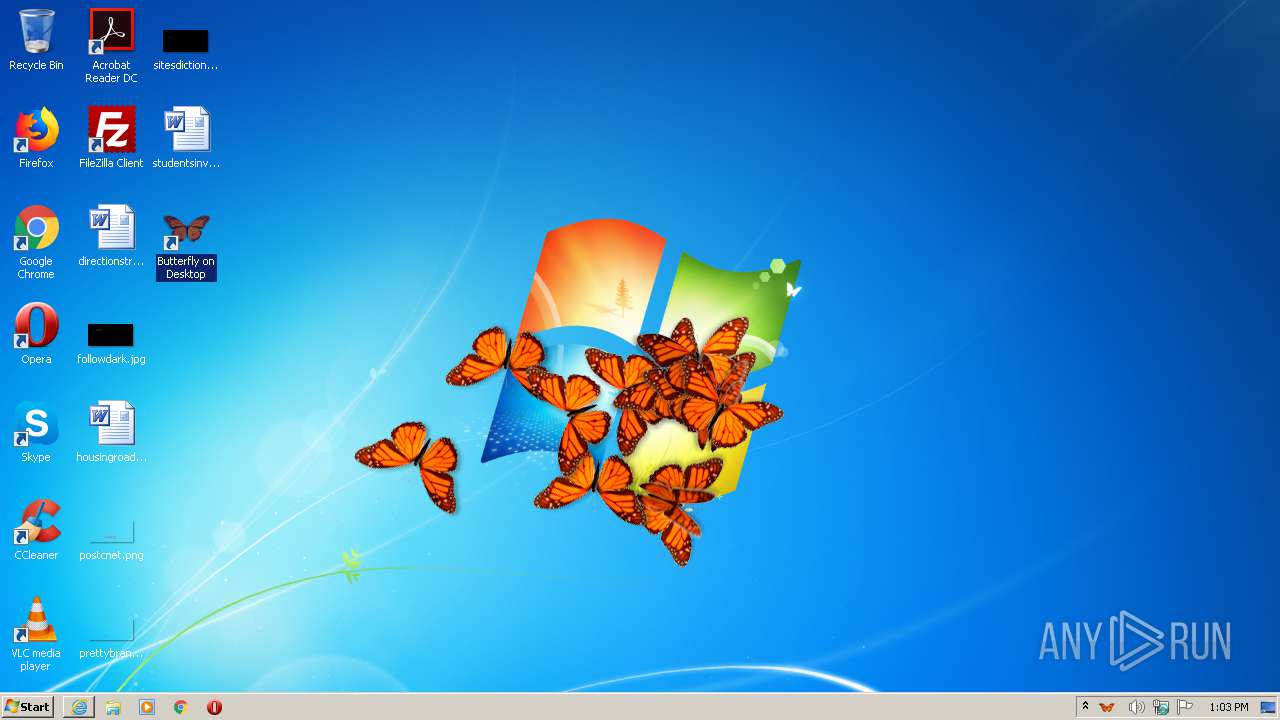
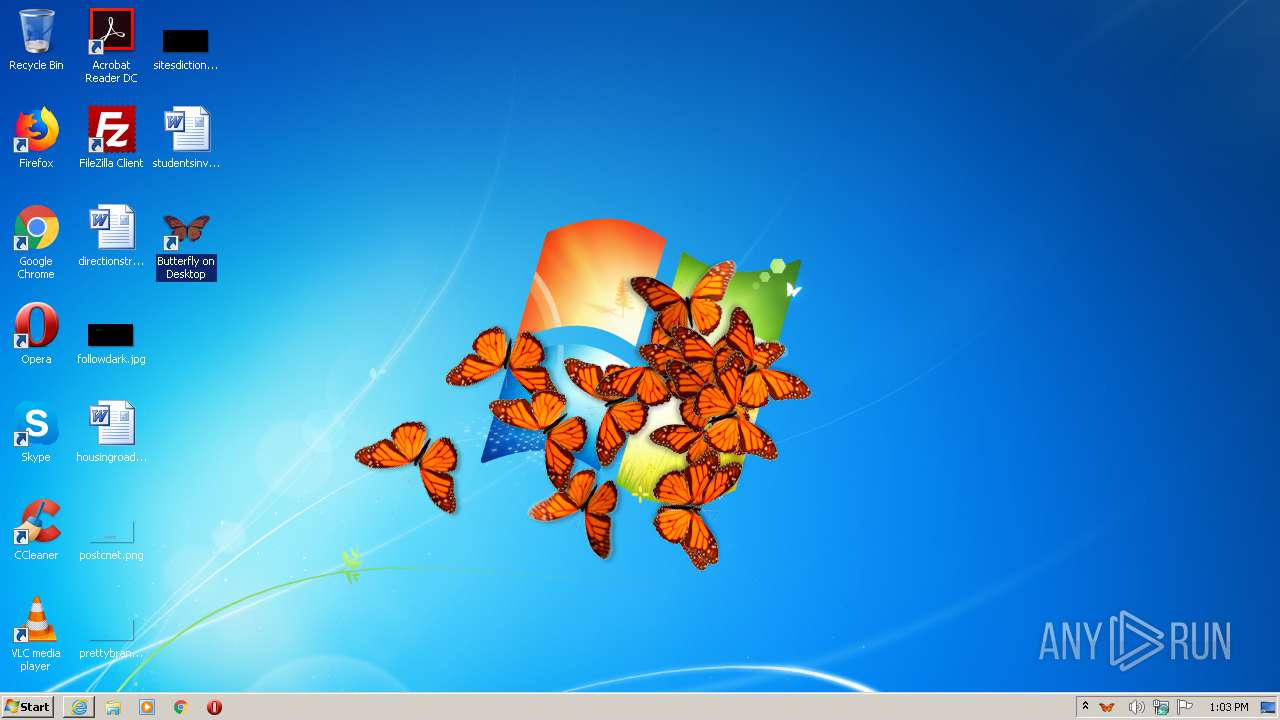
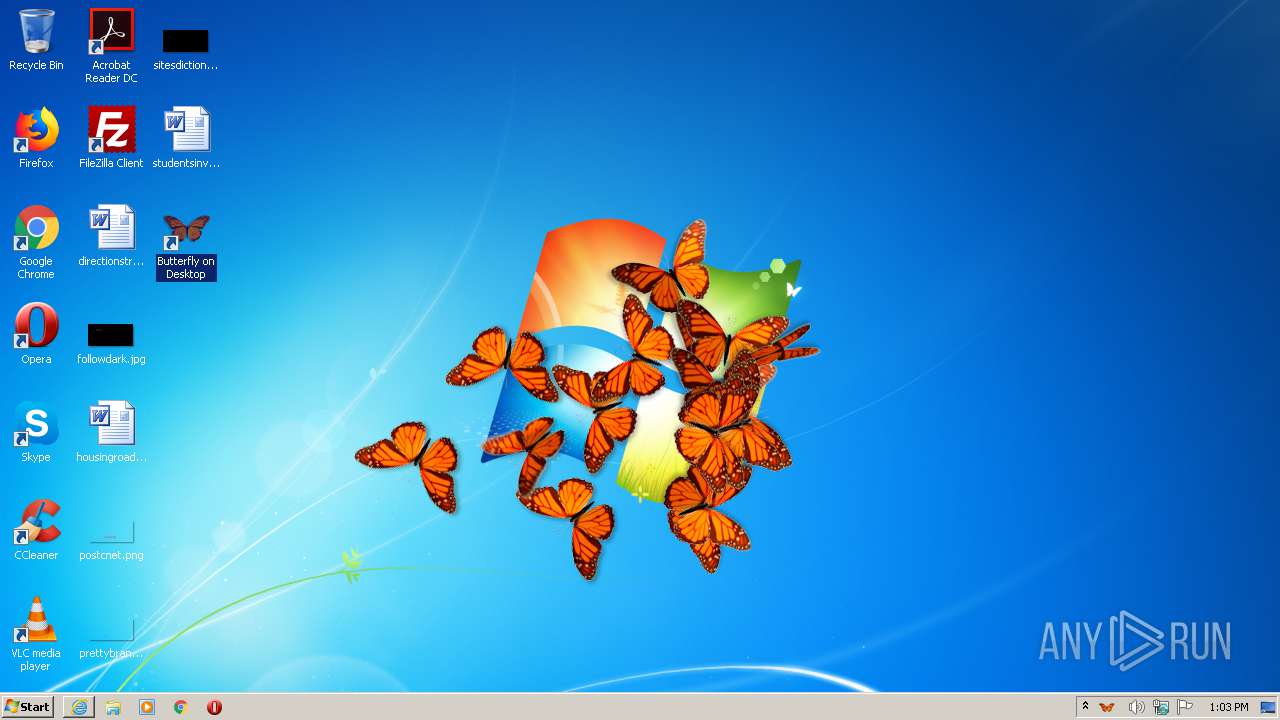
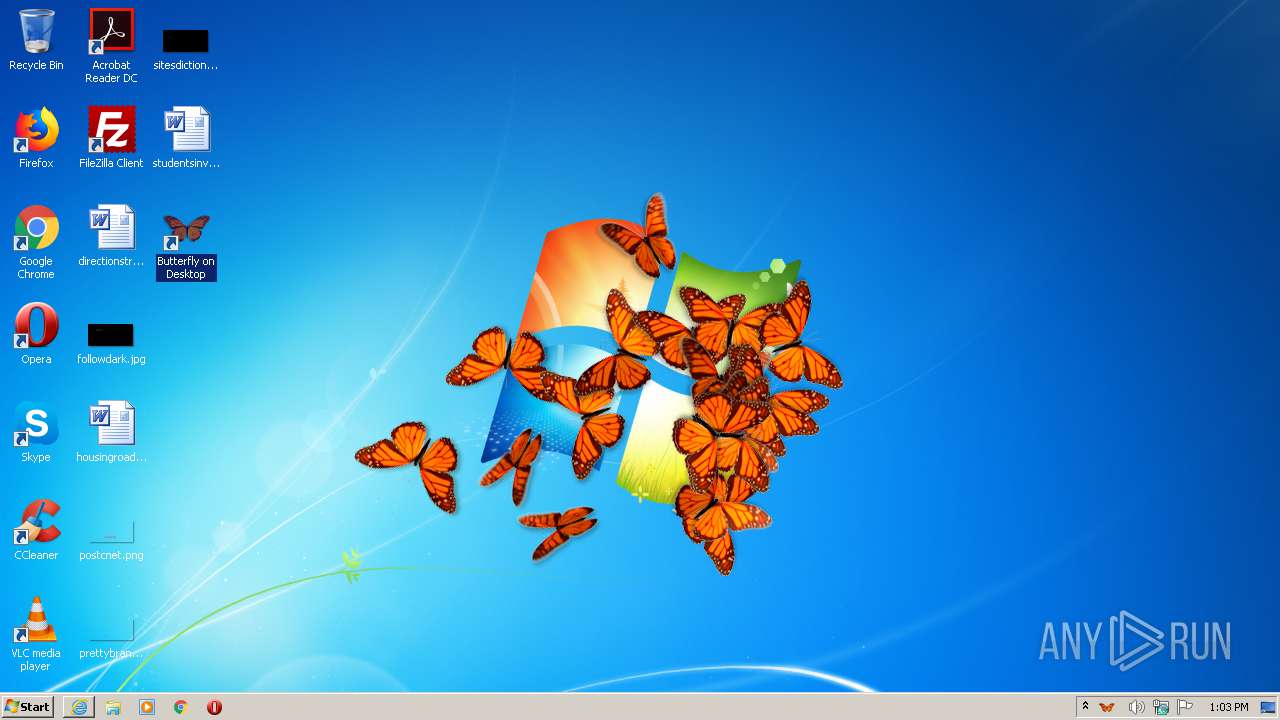
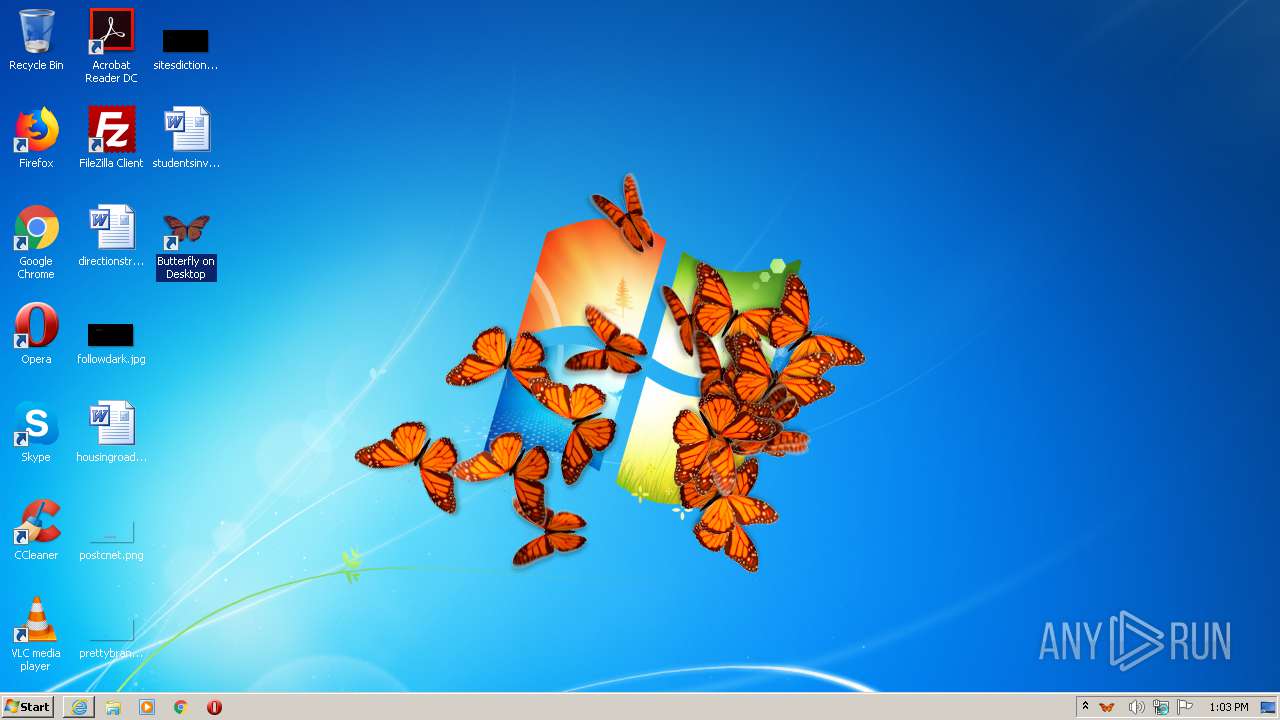
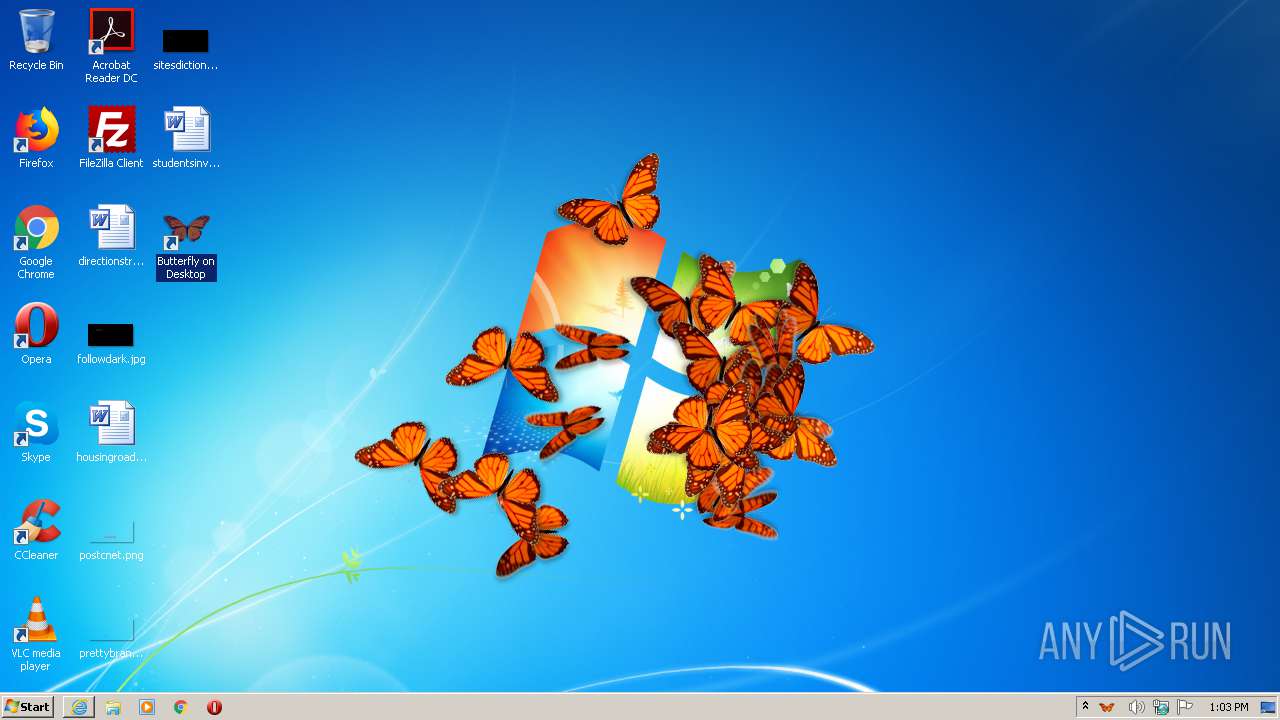
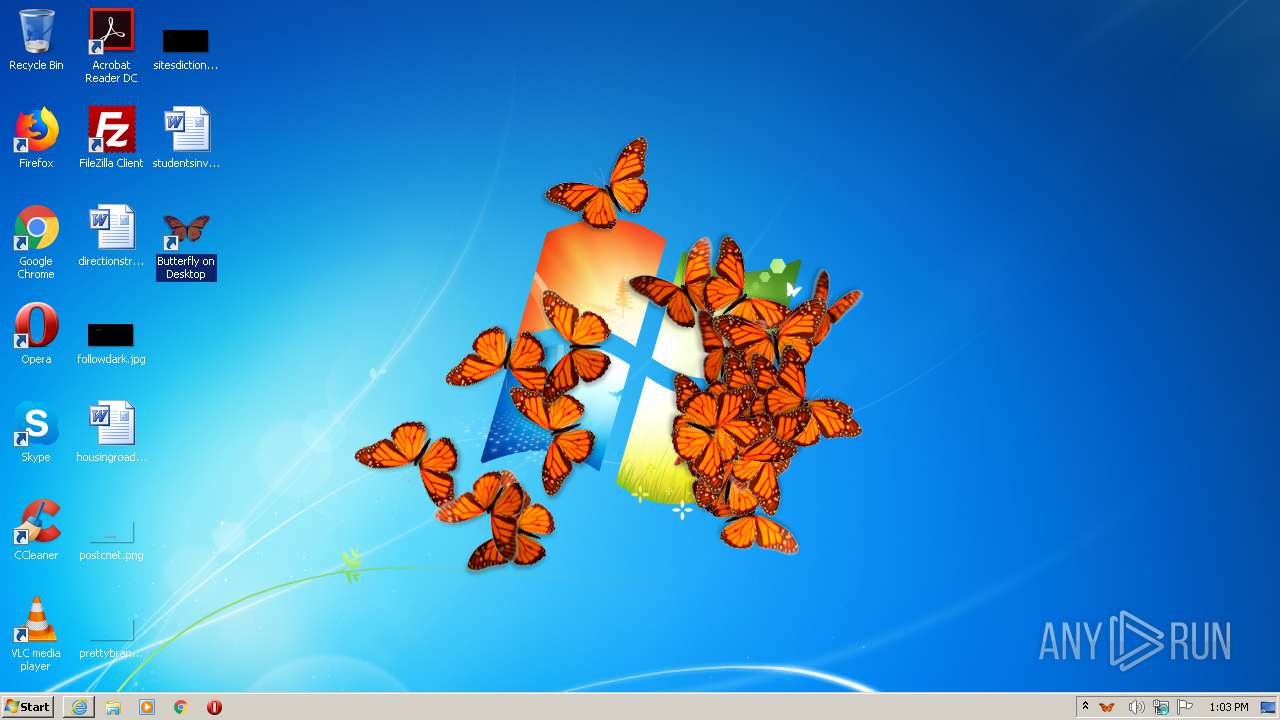
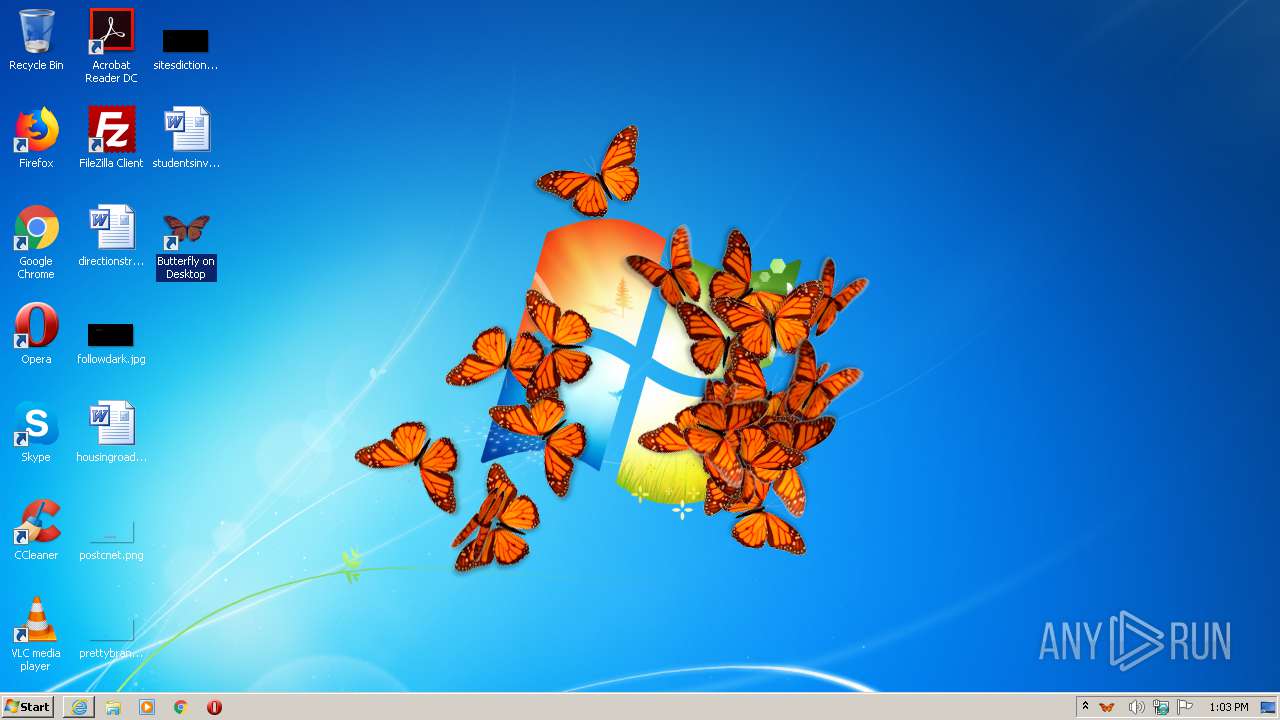
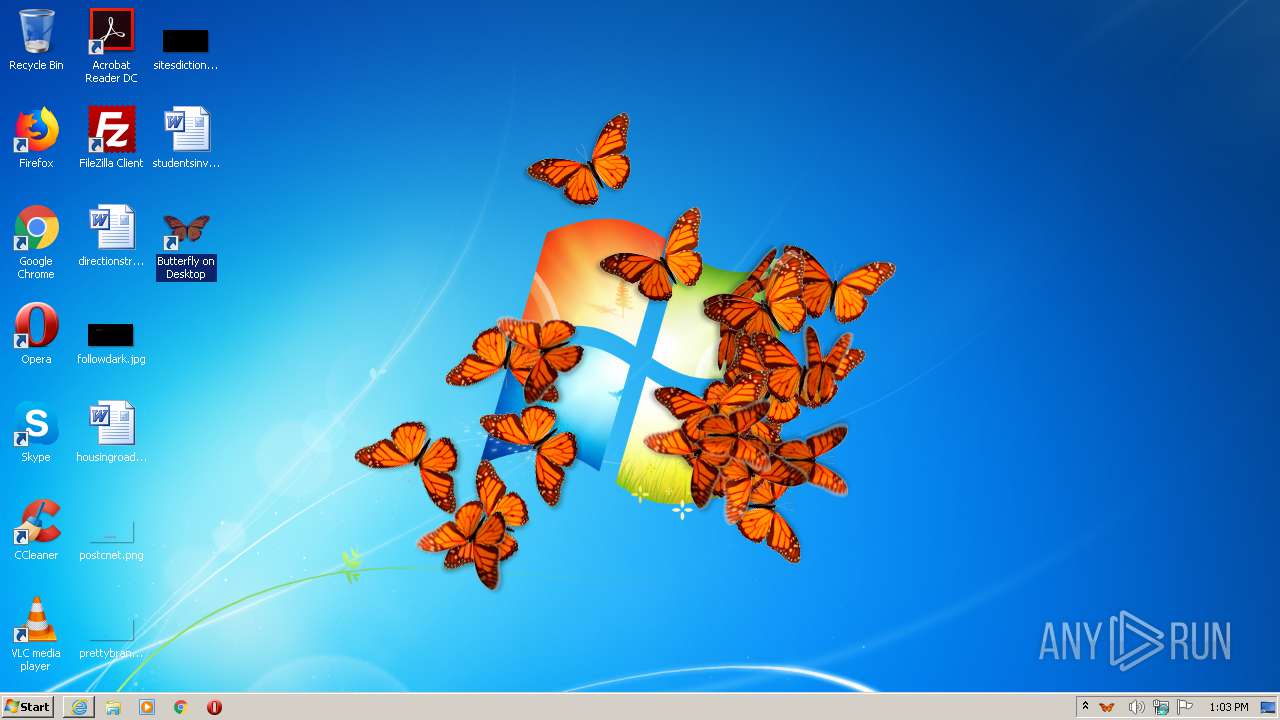
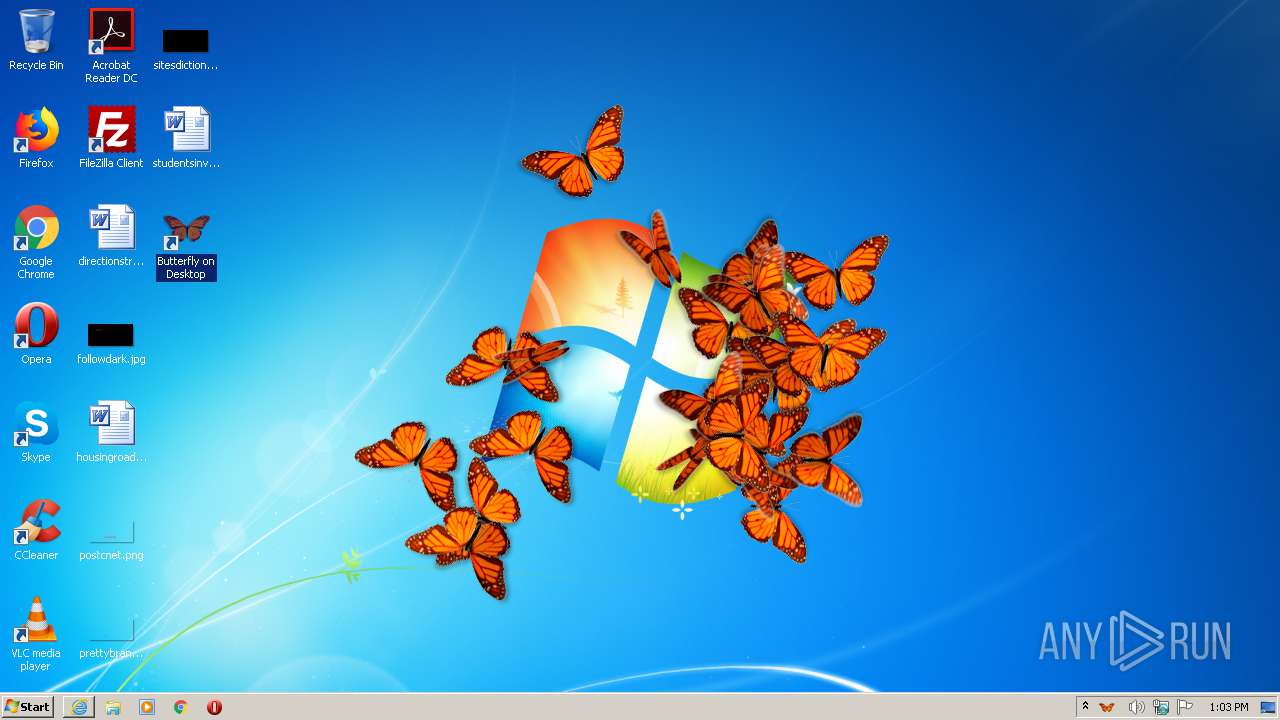
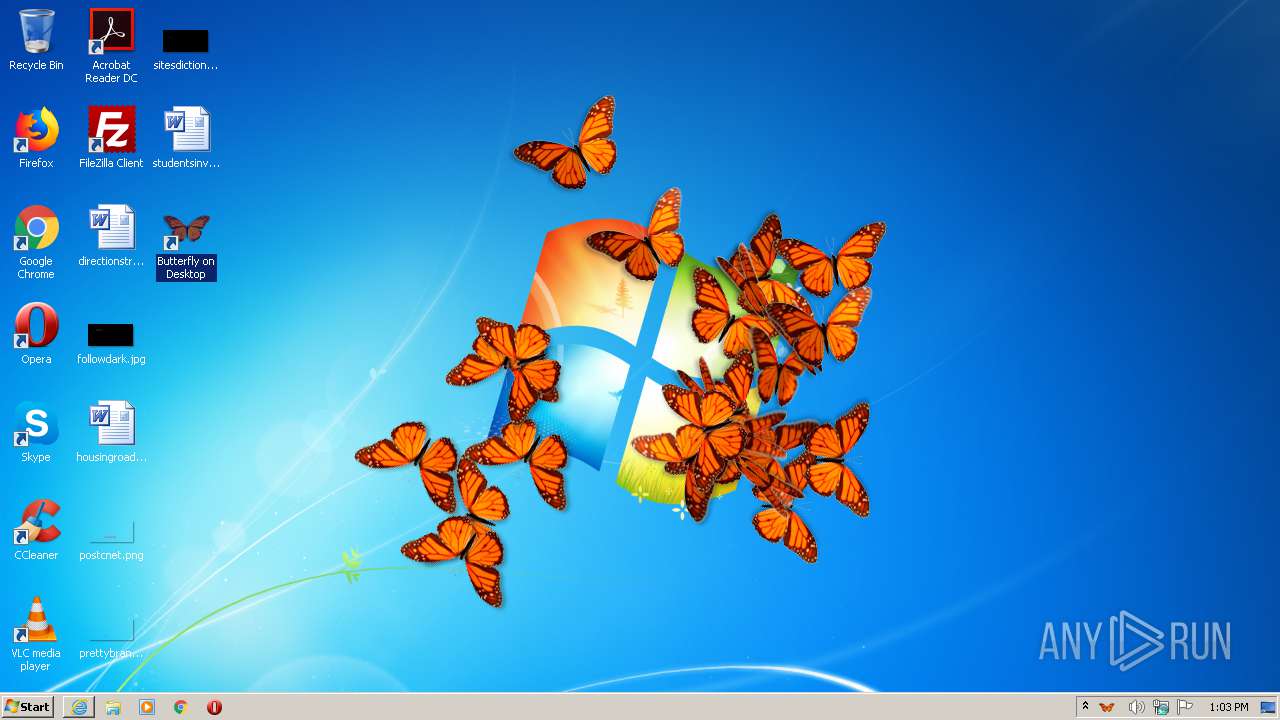
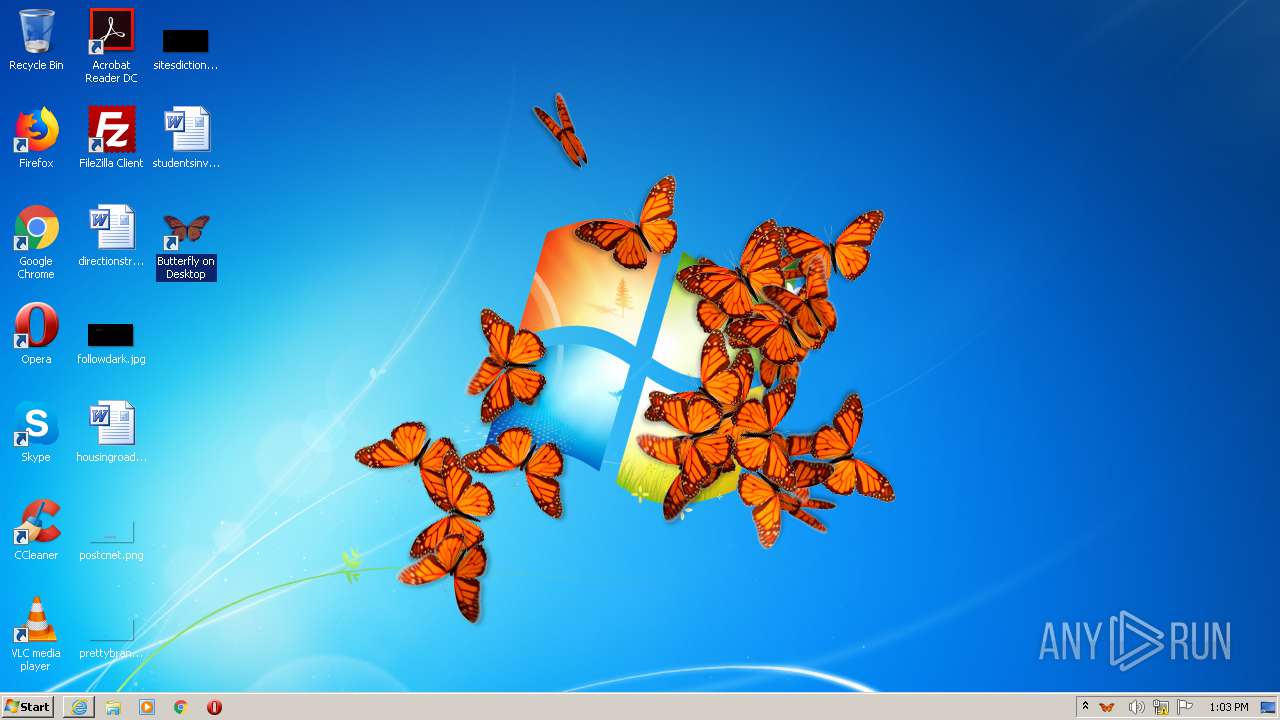
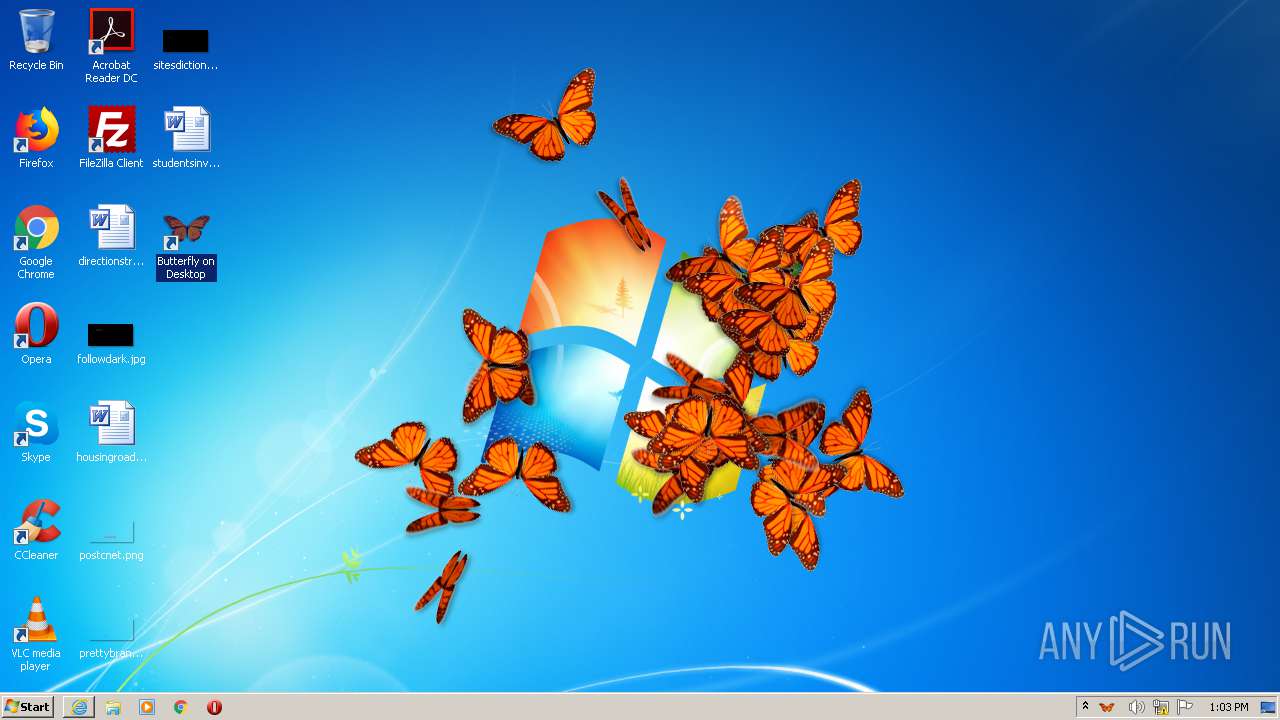
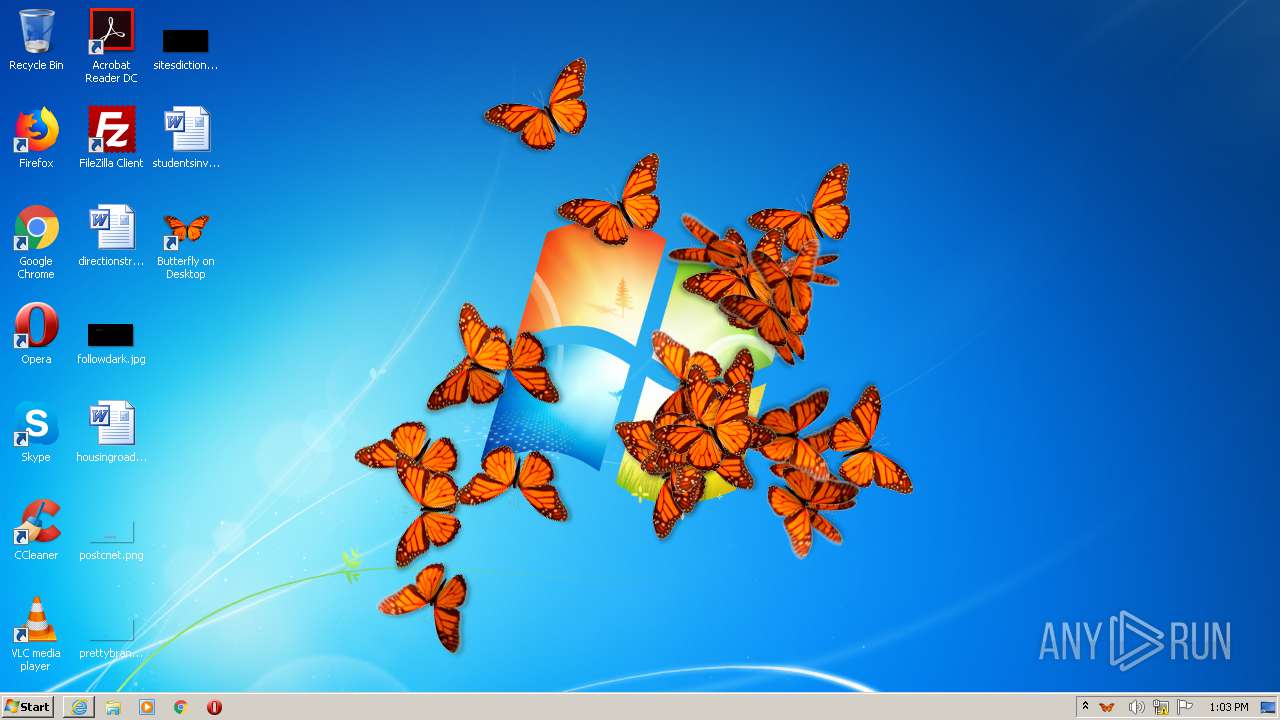
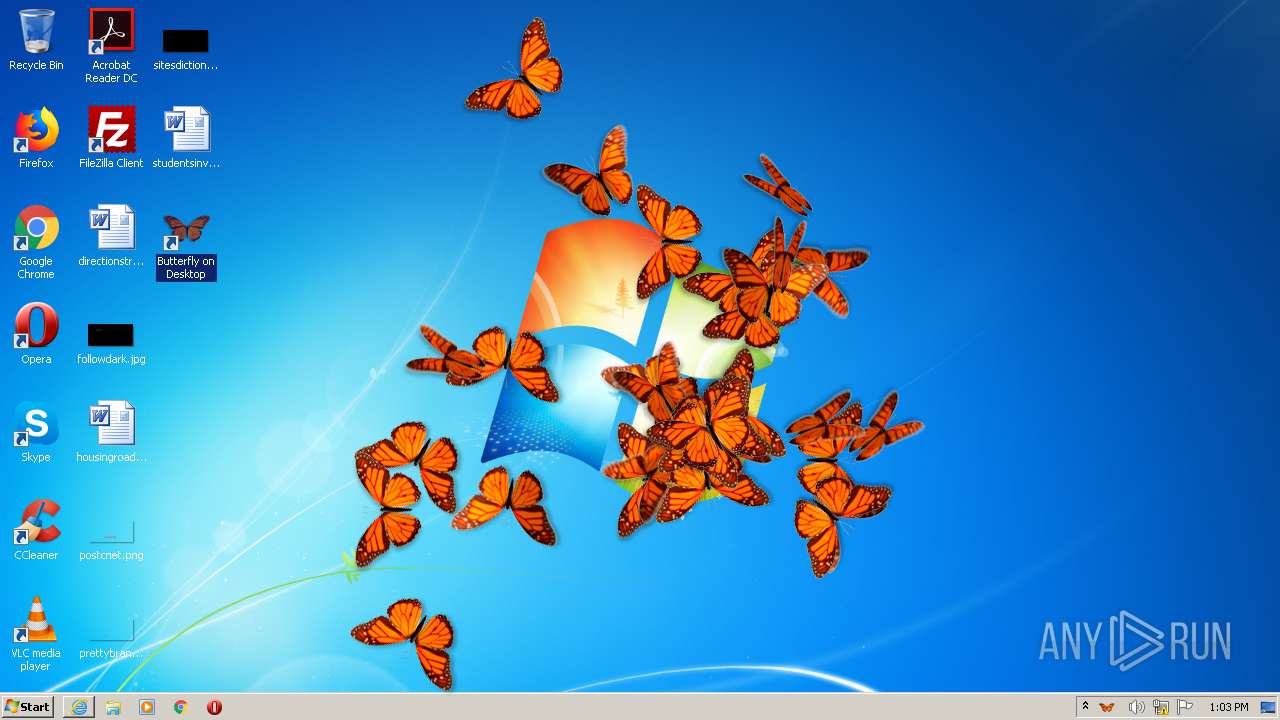
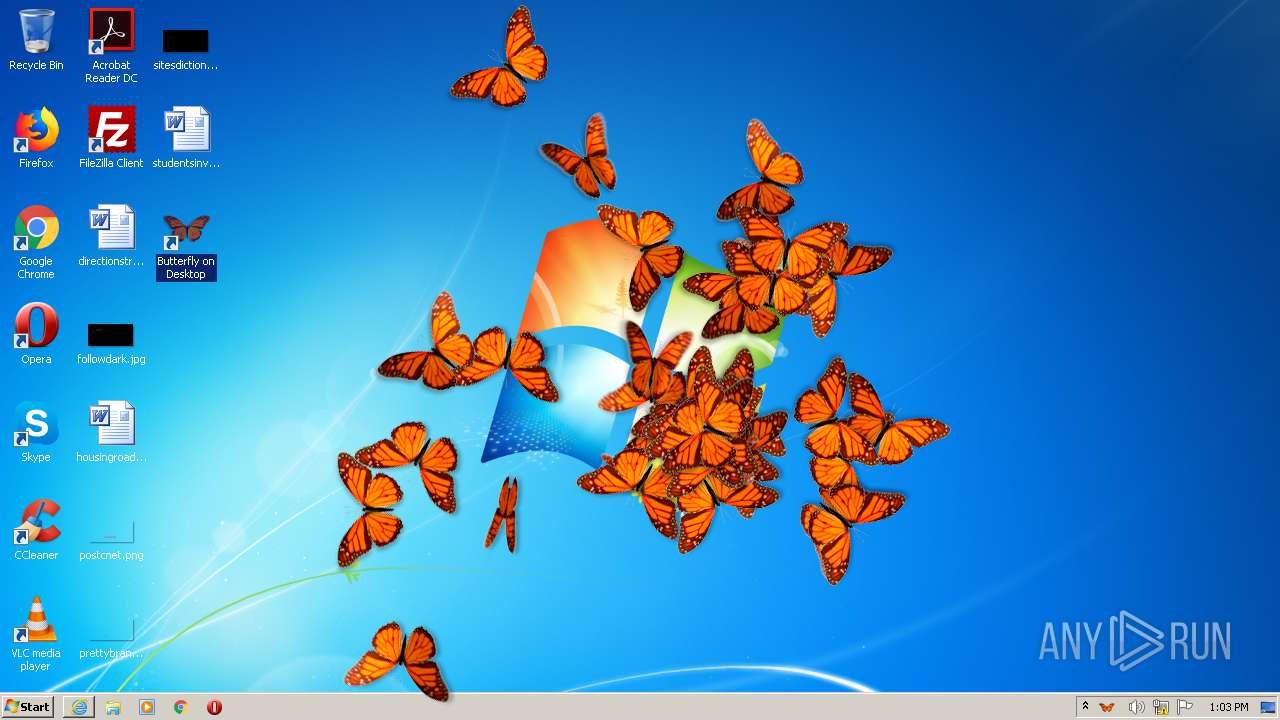
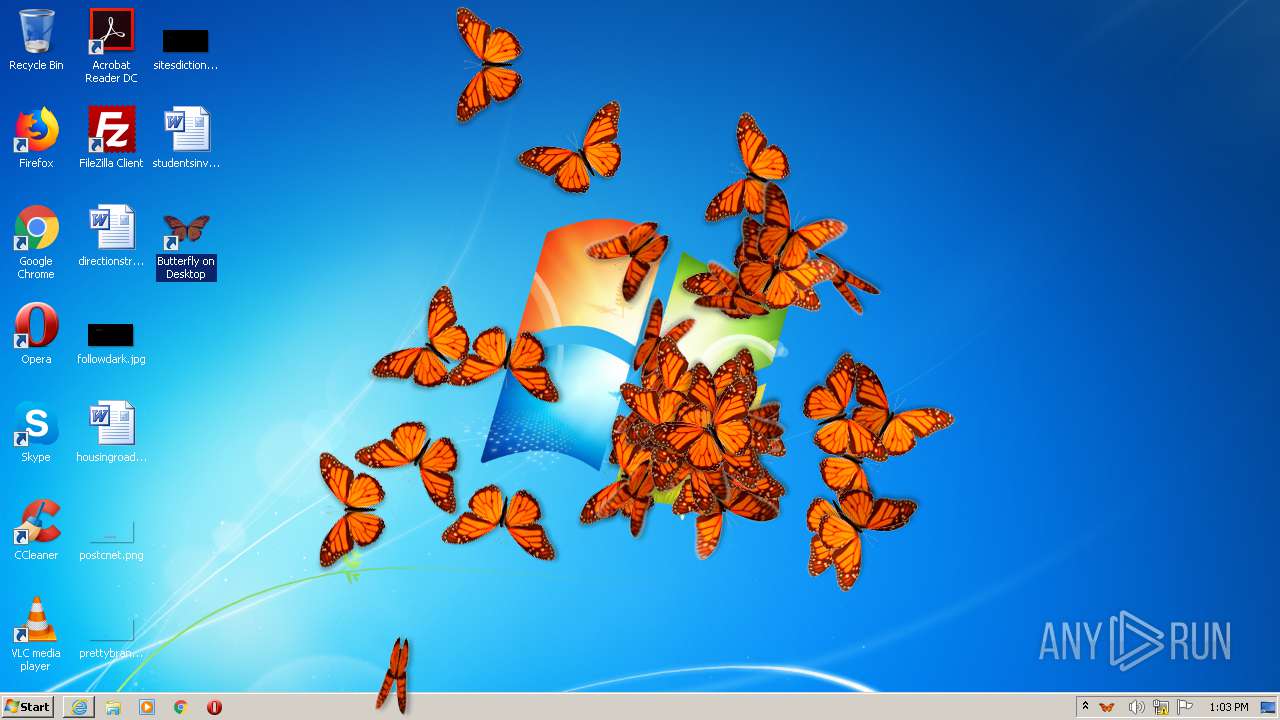
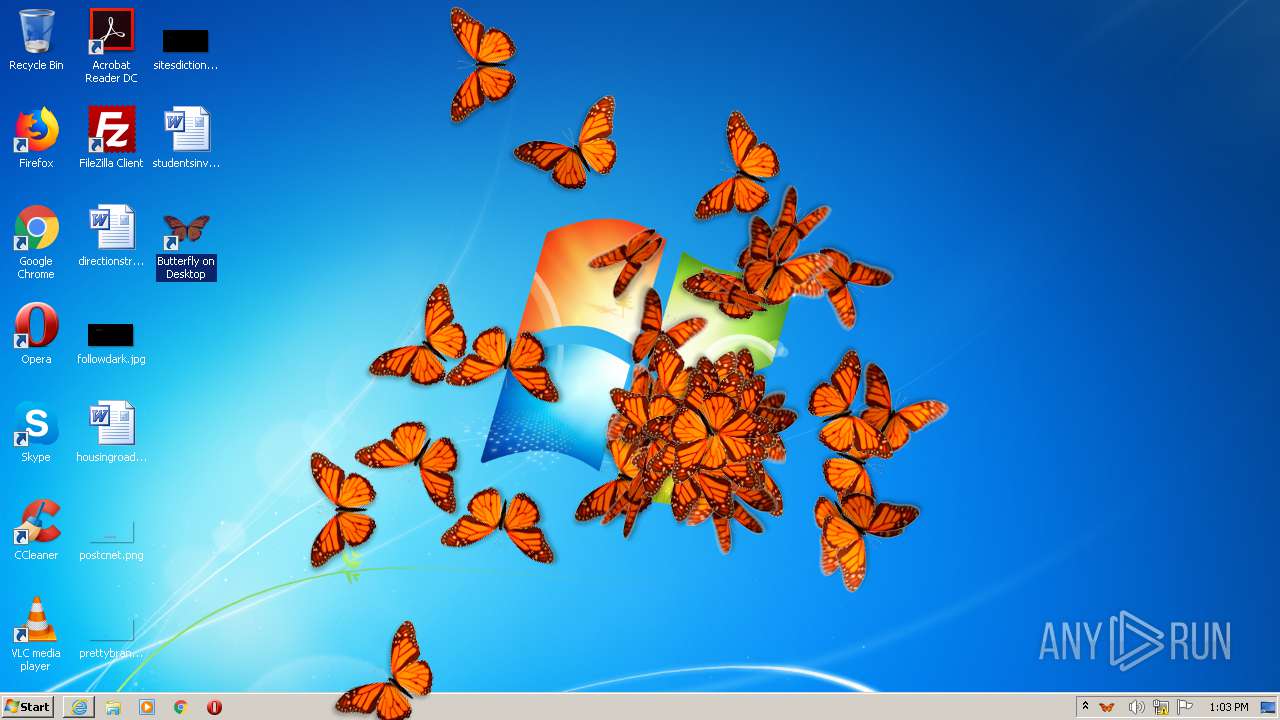
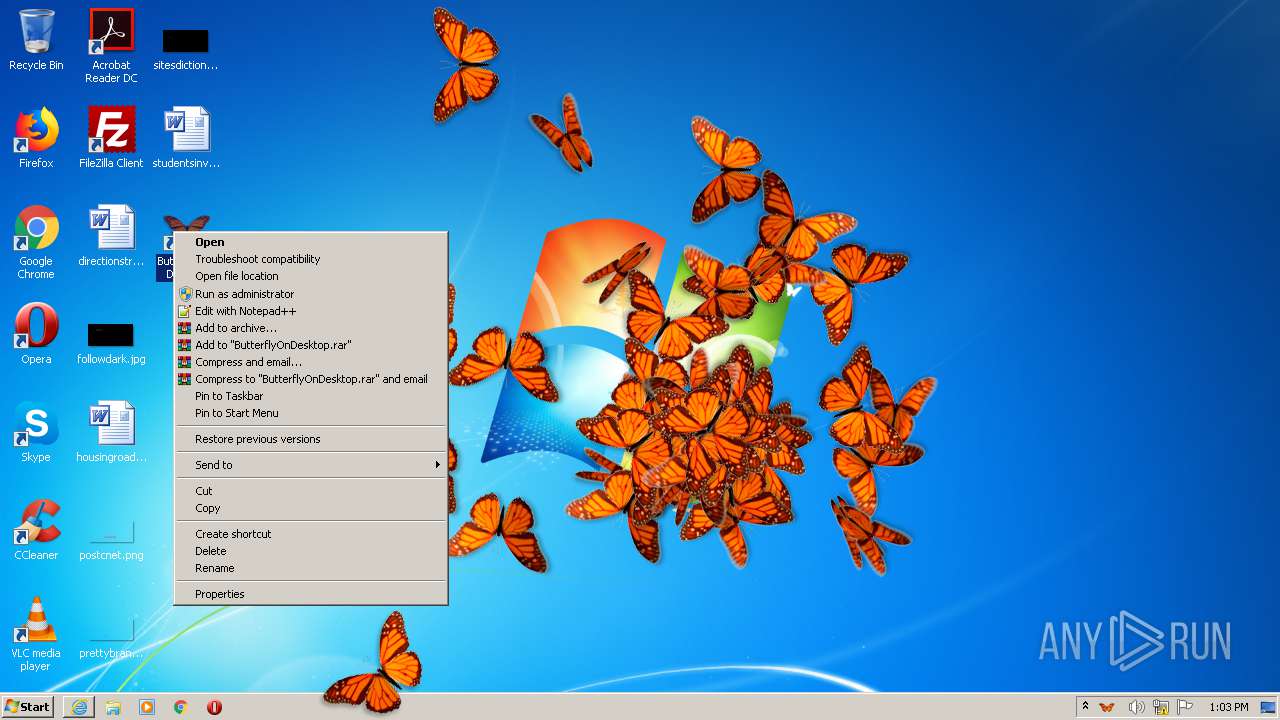
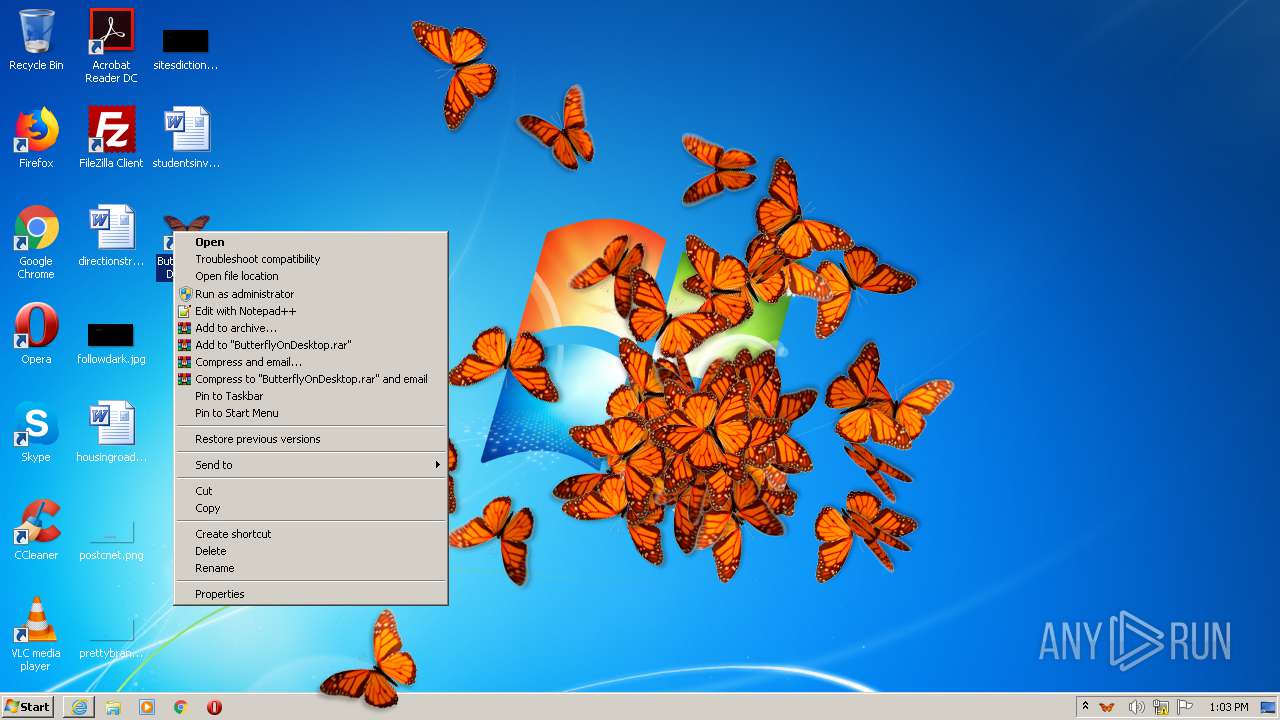
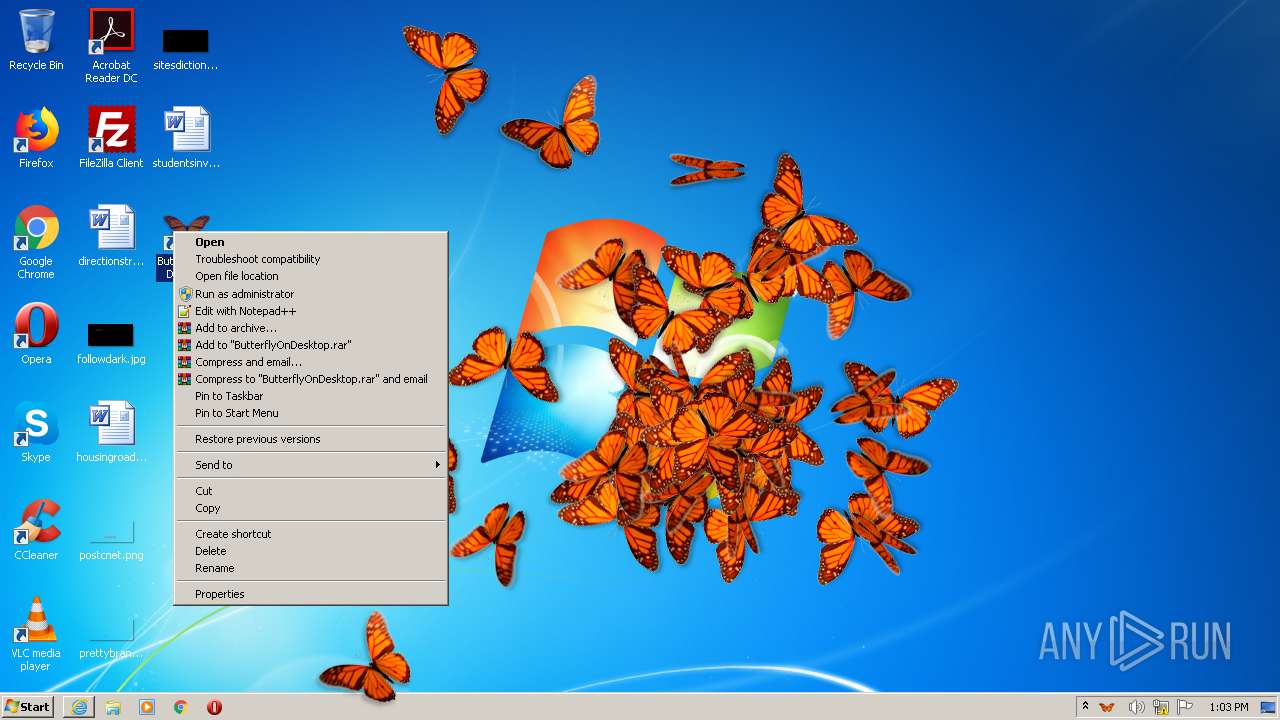
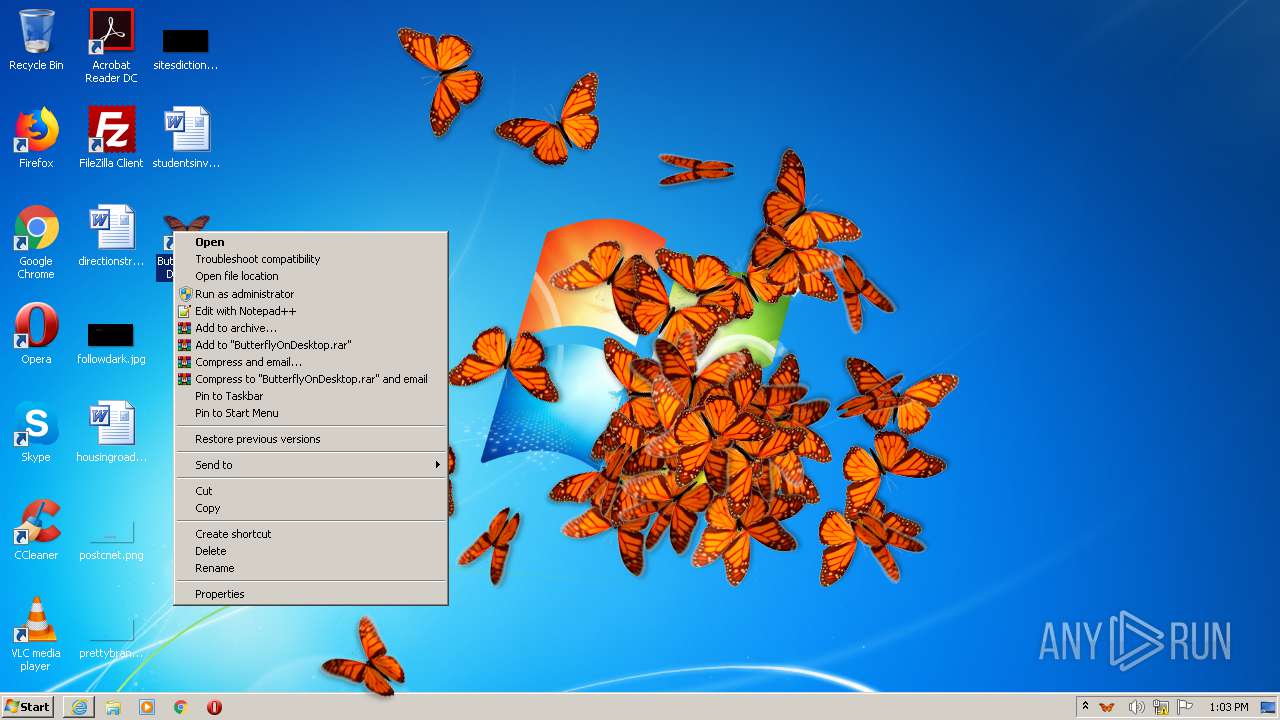
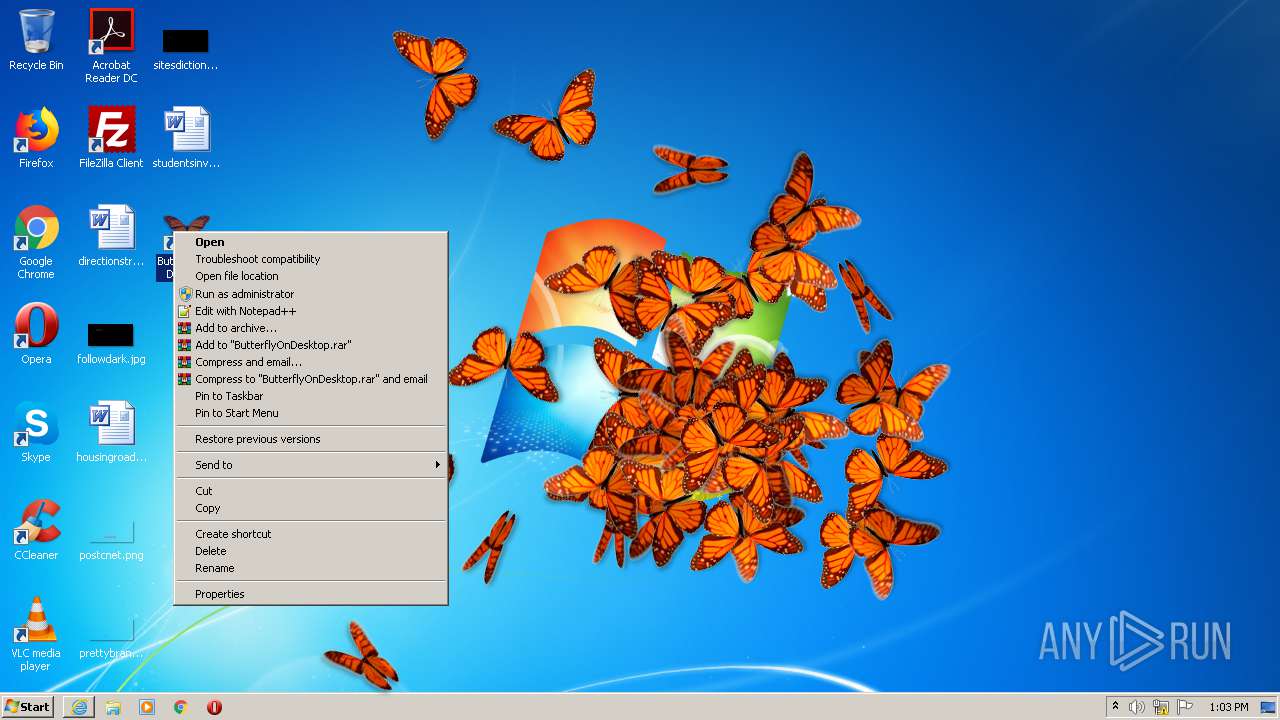
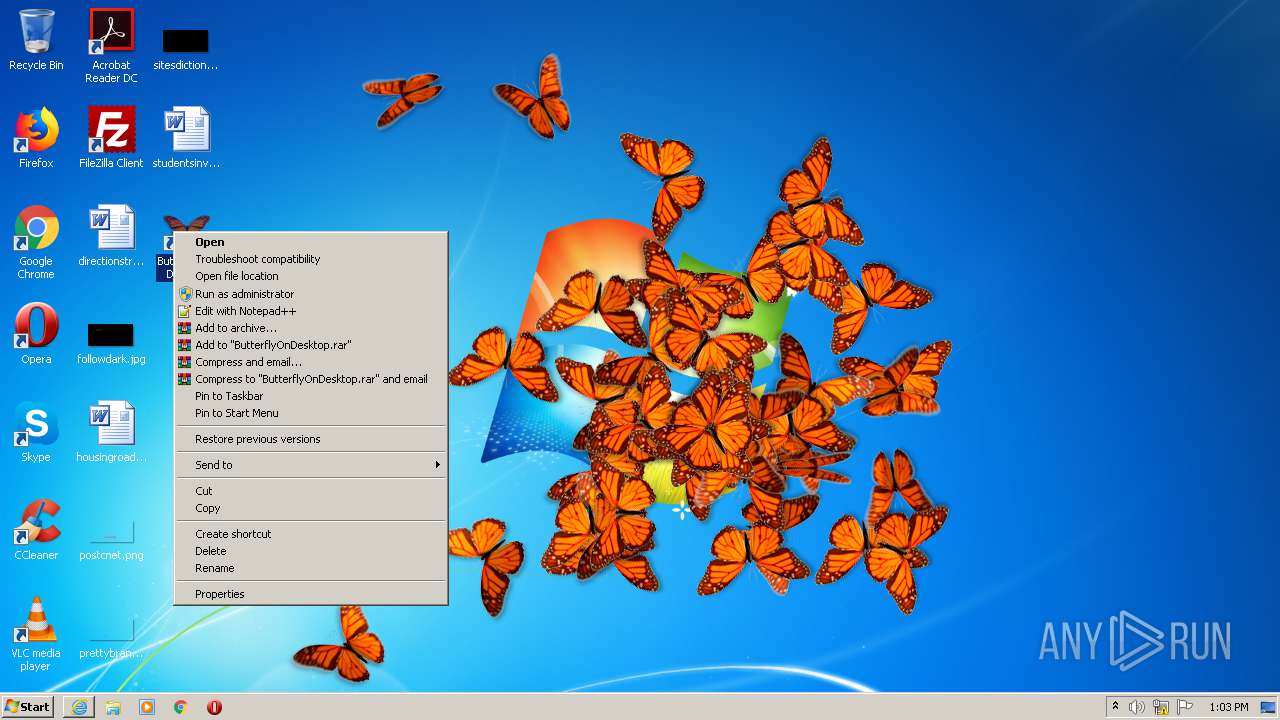
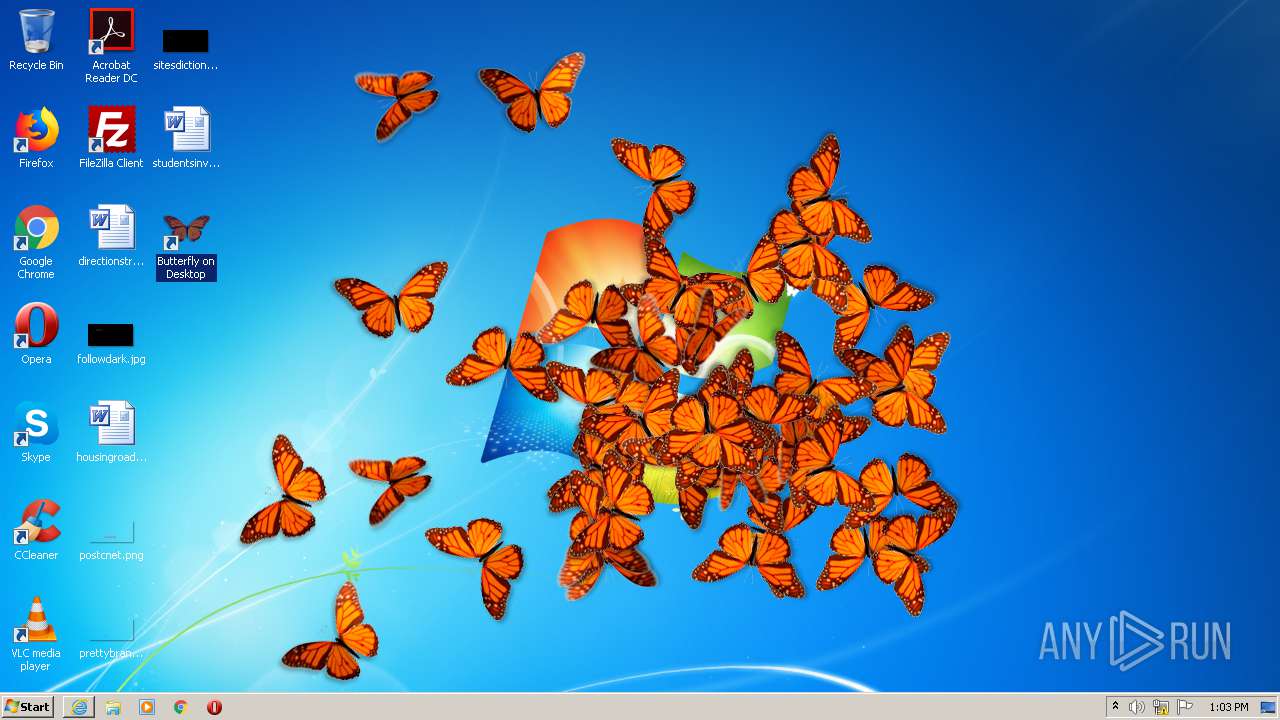
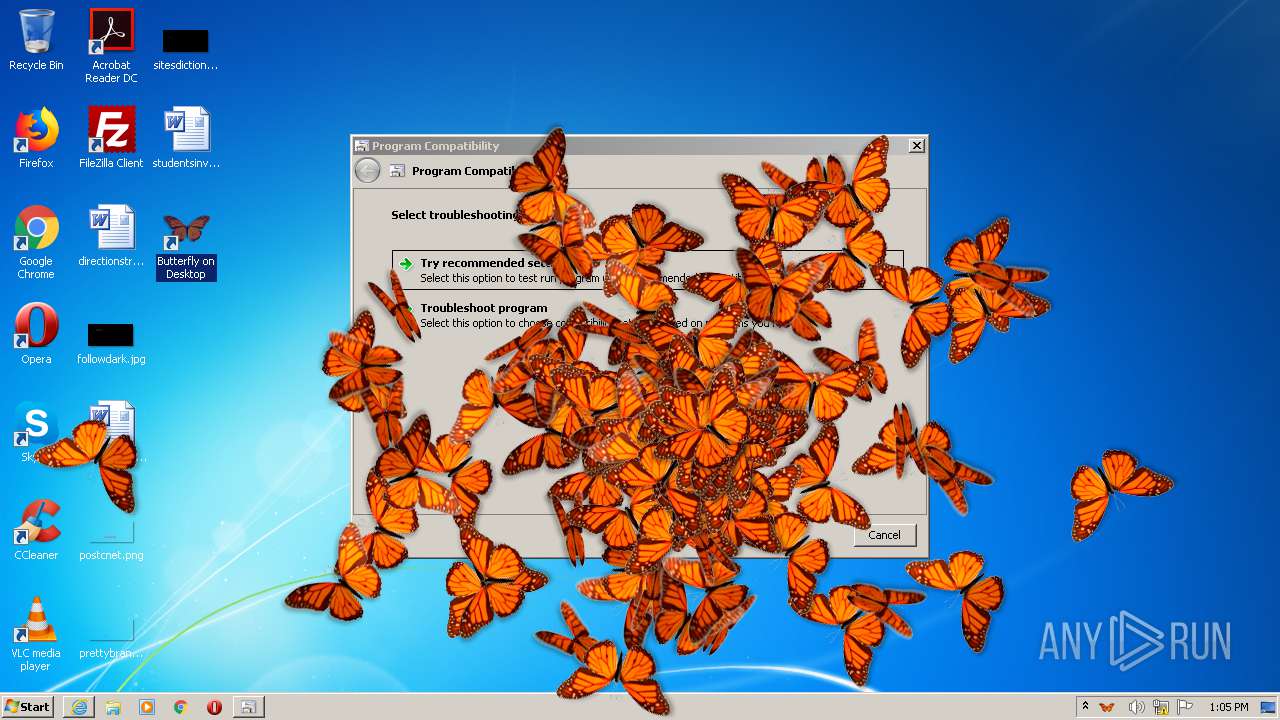
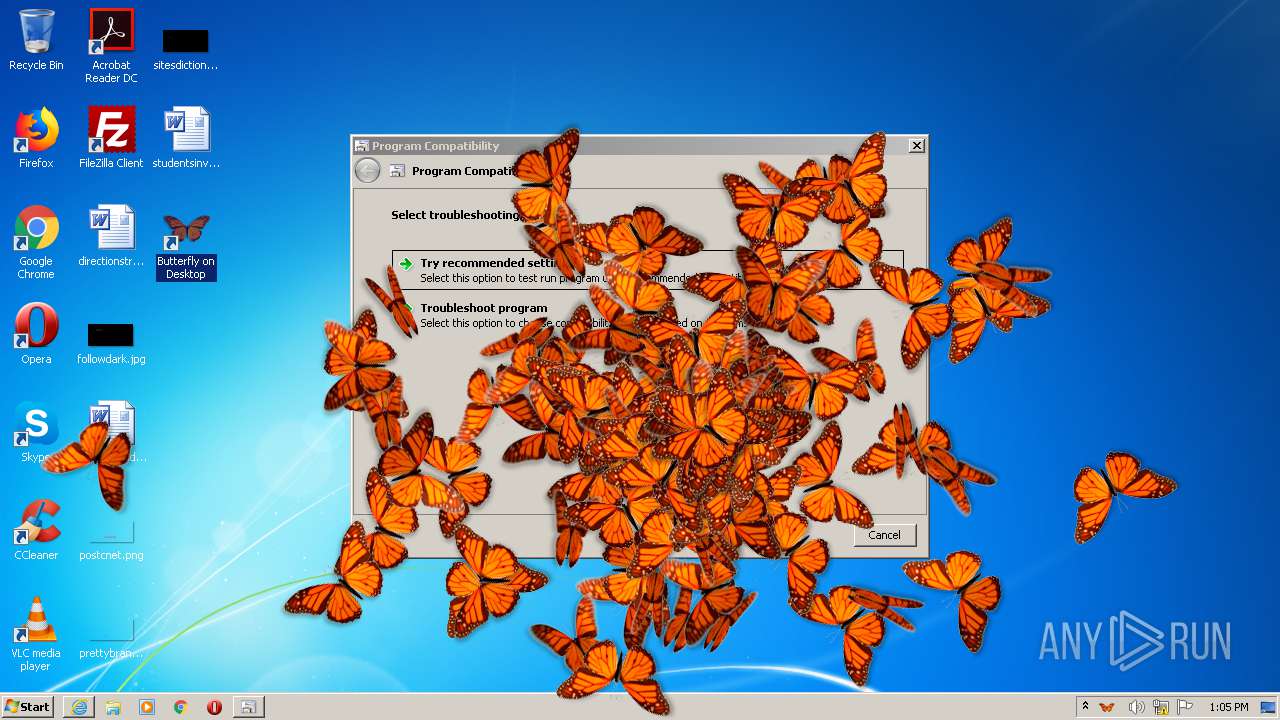
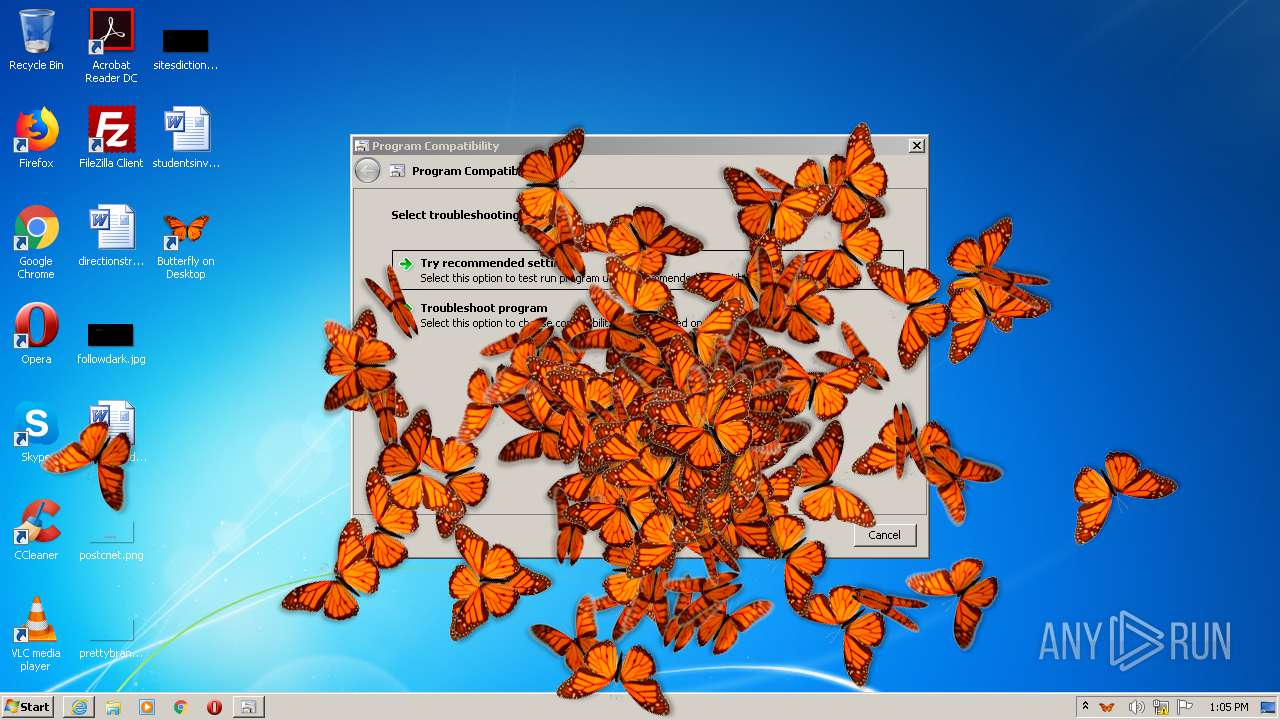
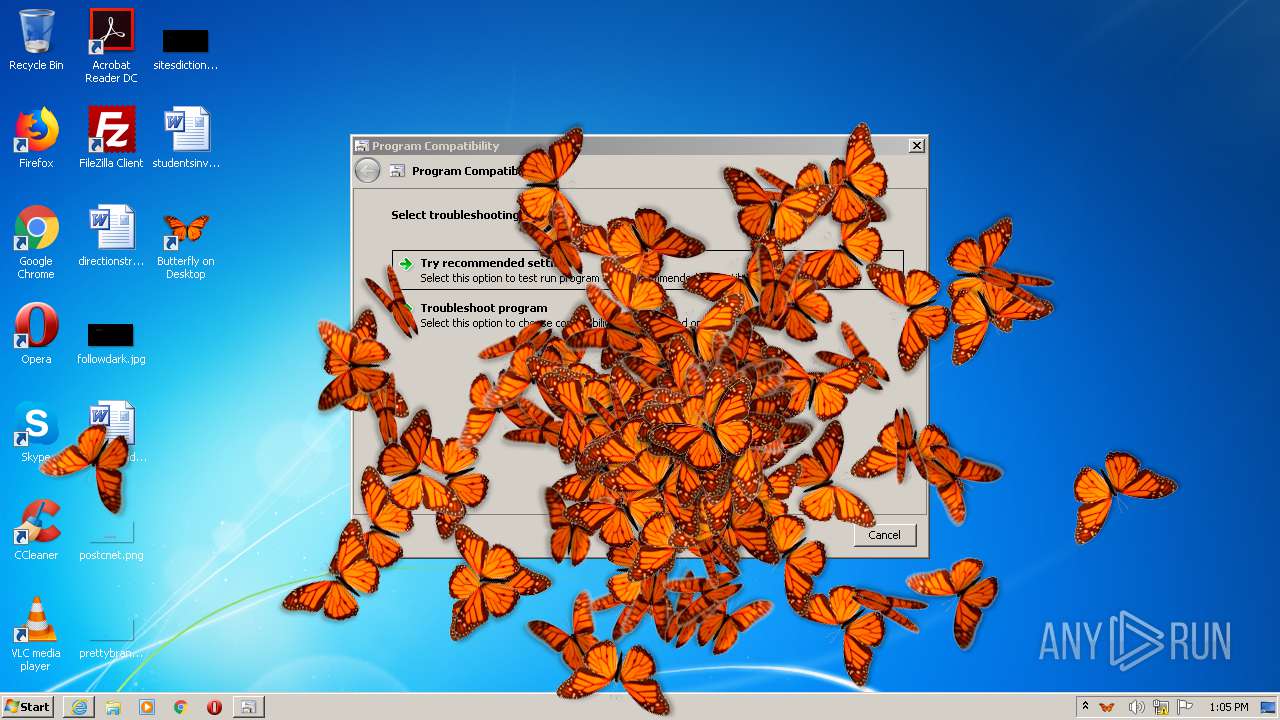
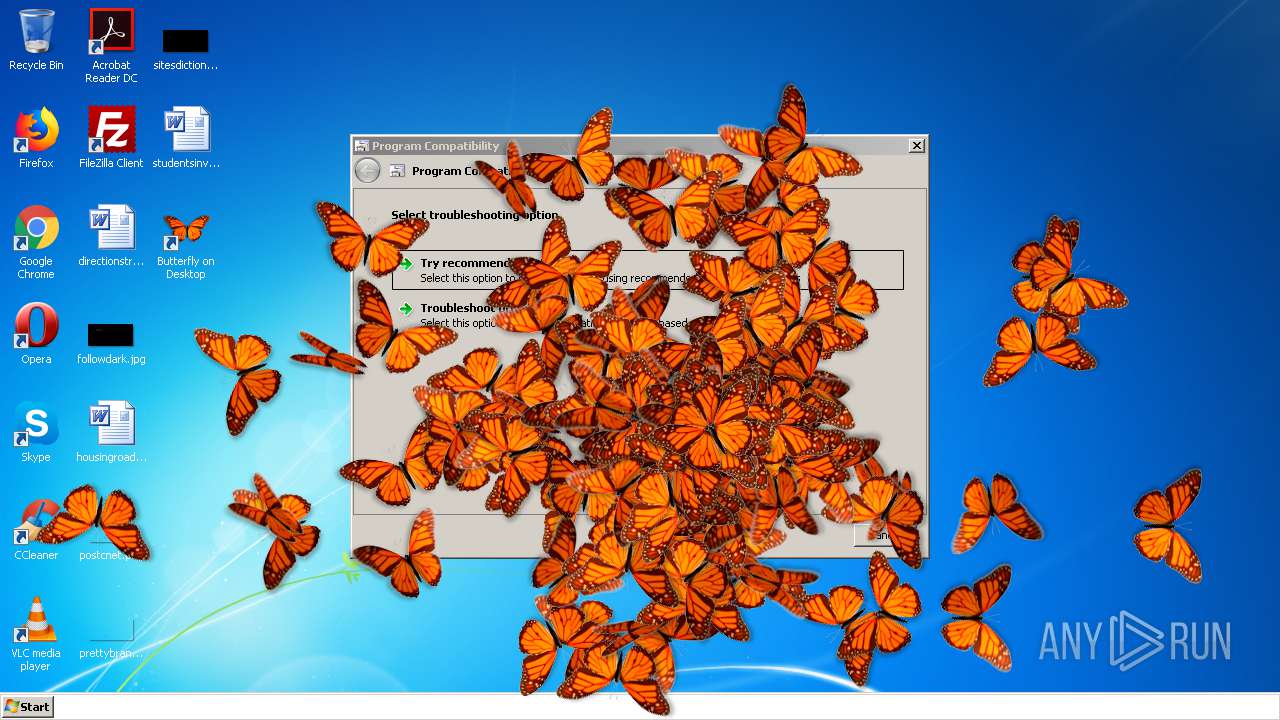
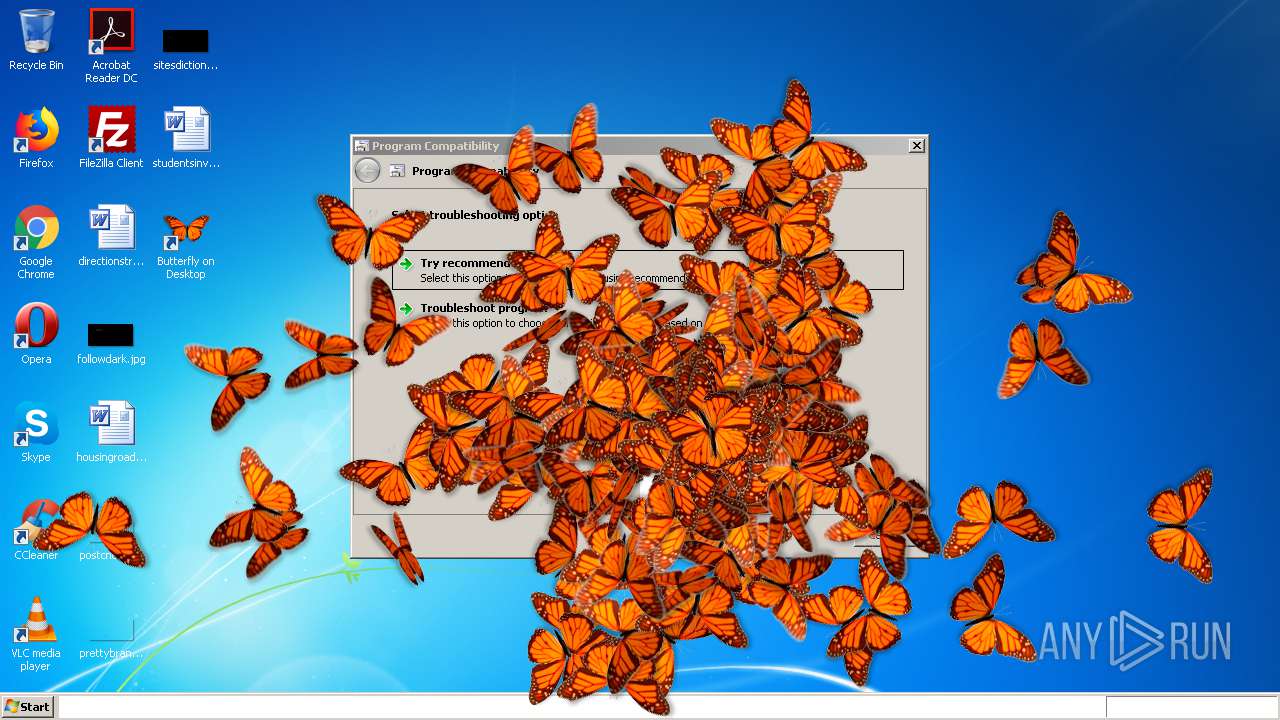
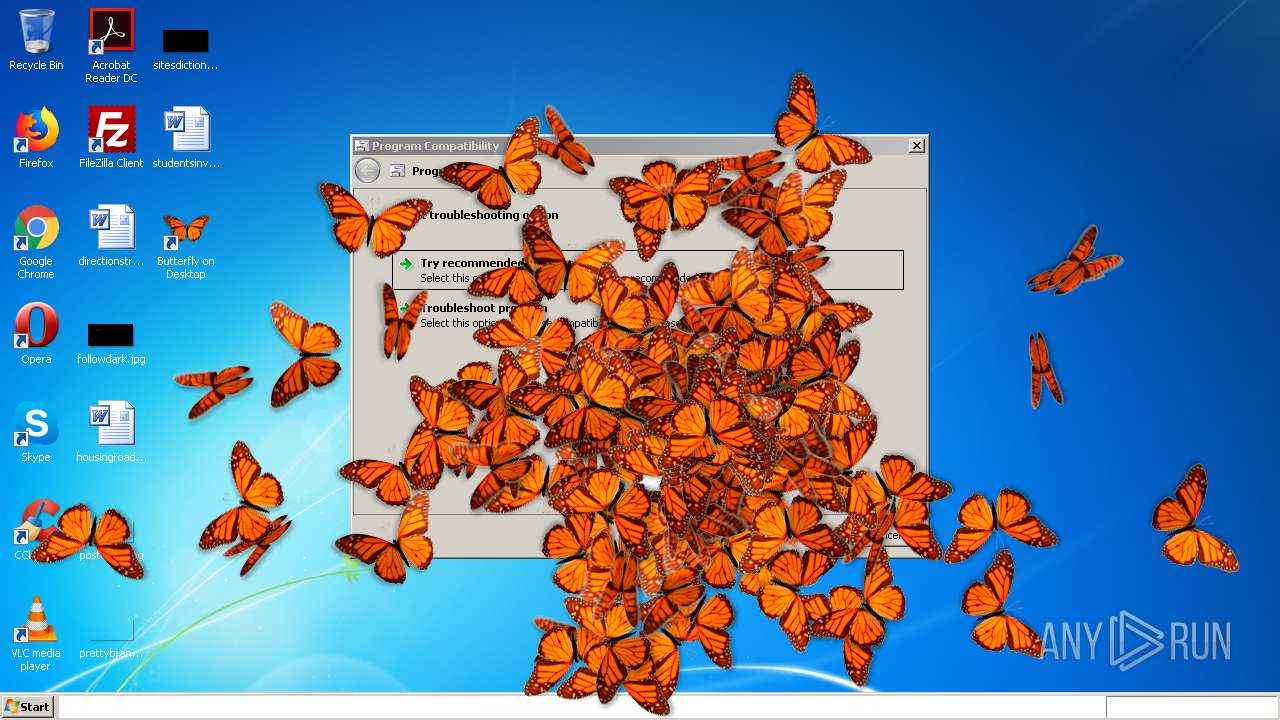
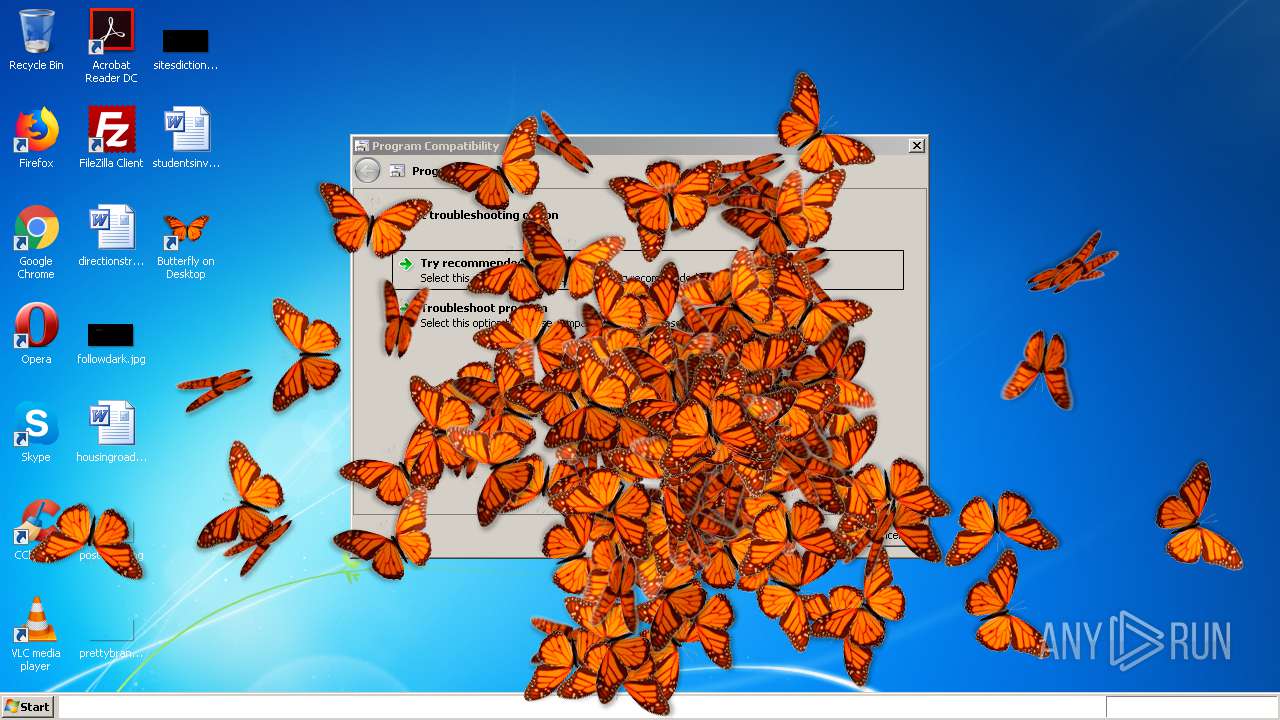
MALICIOUS
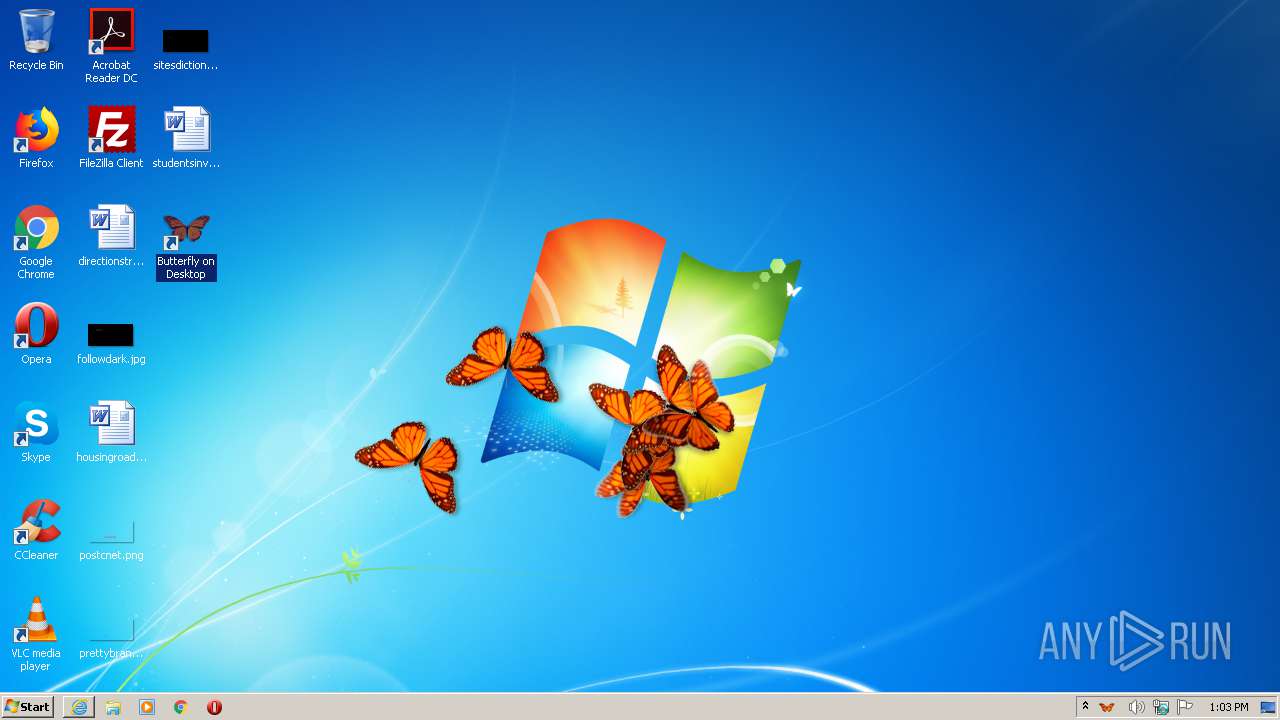
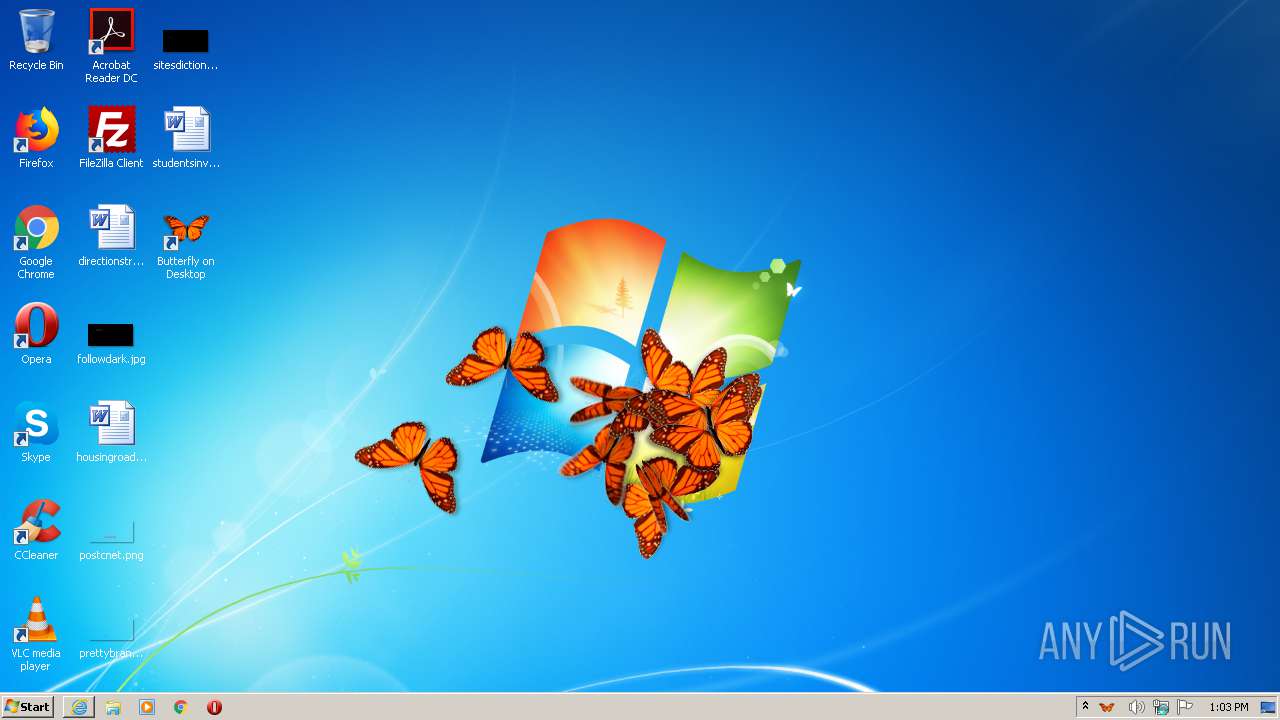
Drops executable file immediately after starts
- butterflyondesktop.exe (PID: 556)
- msdt.exe (PID: 1712)
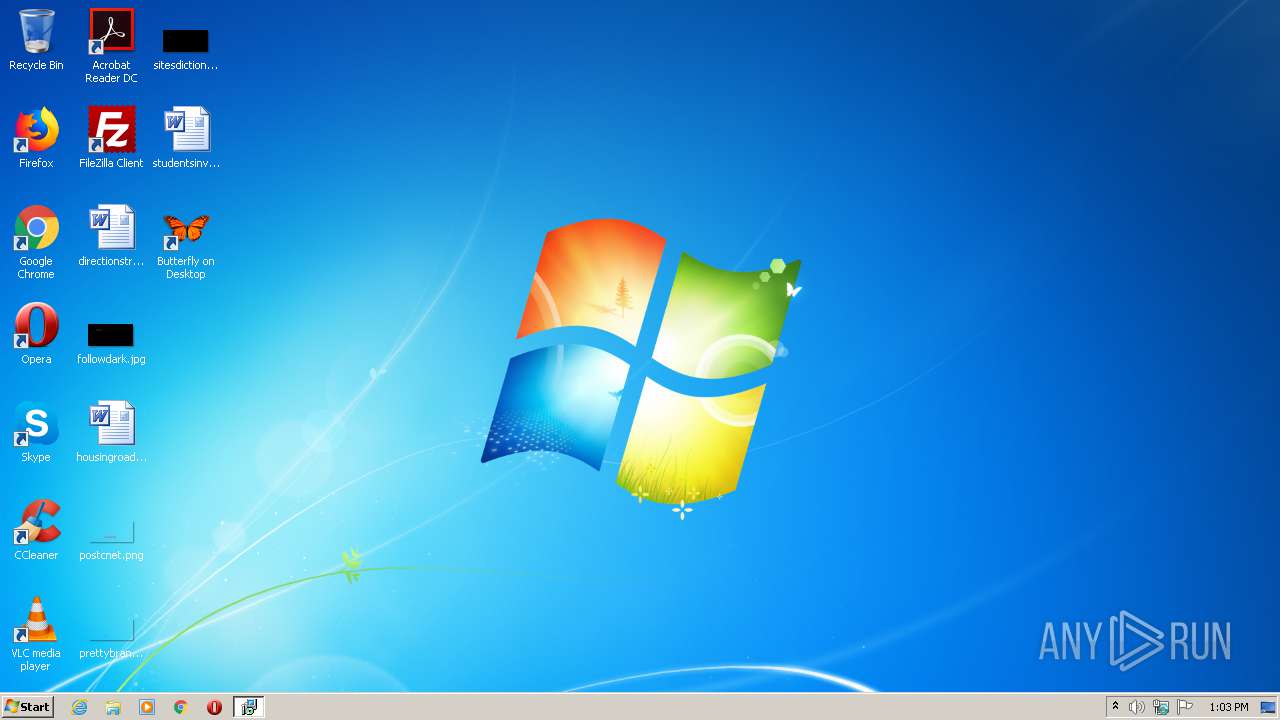
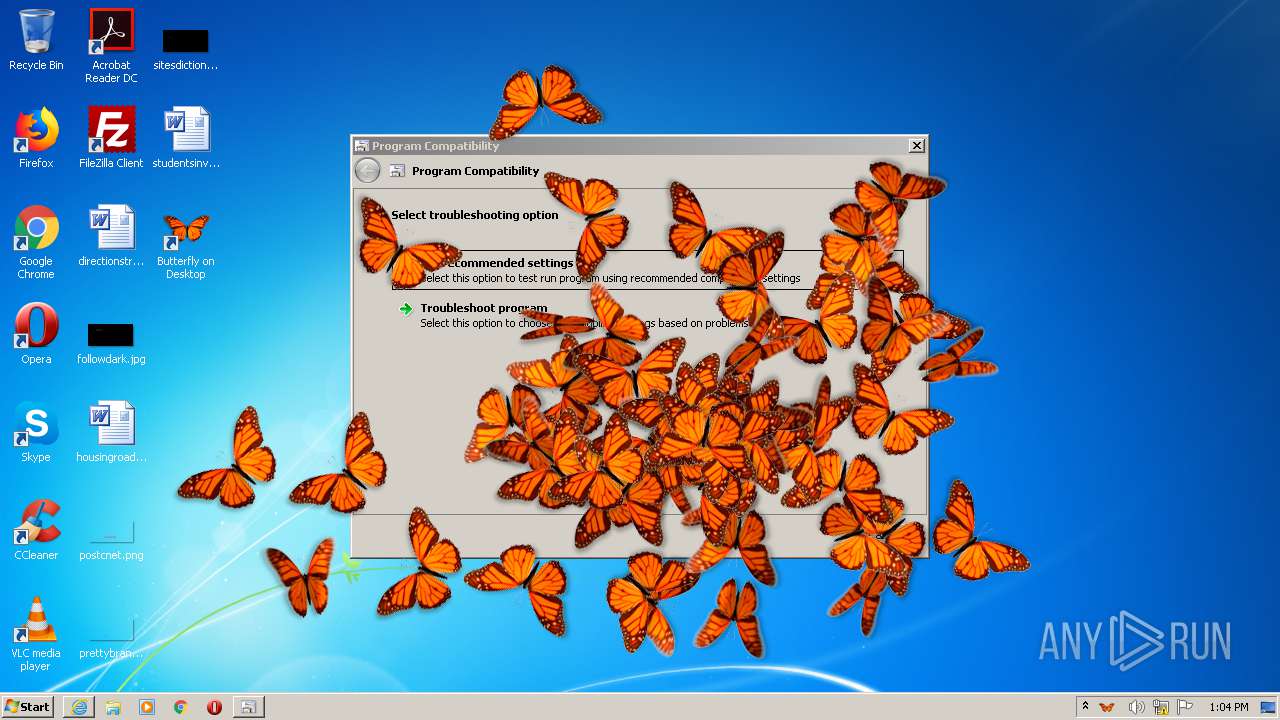
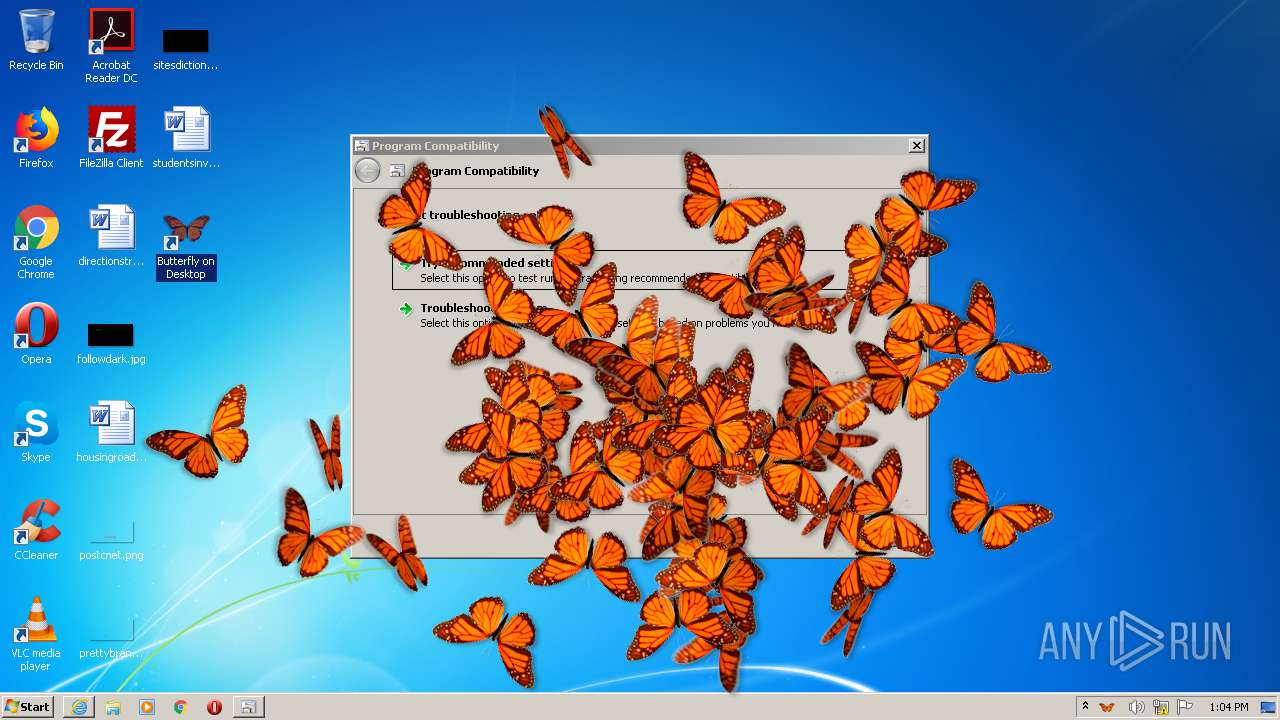
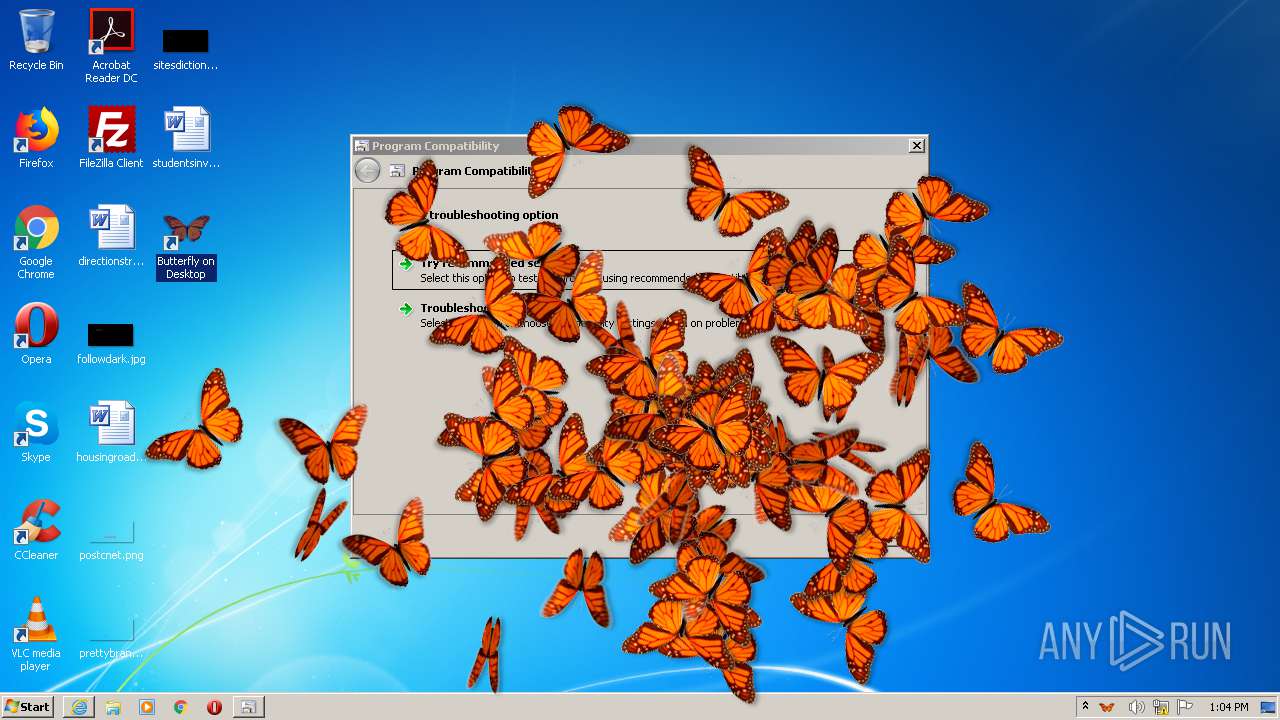
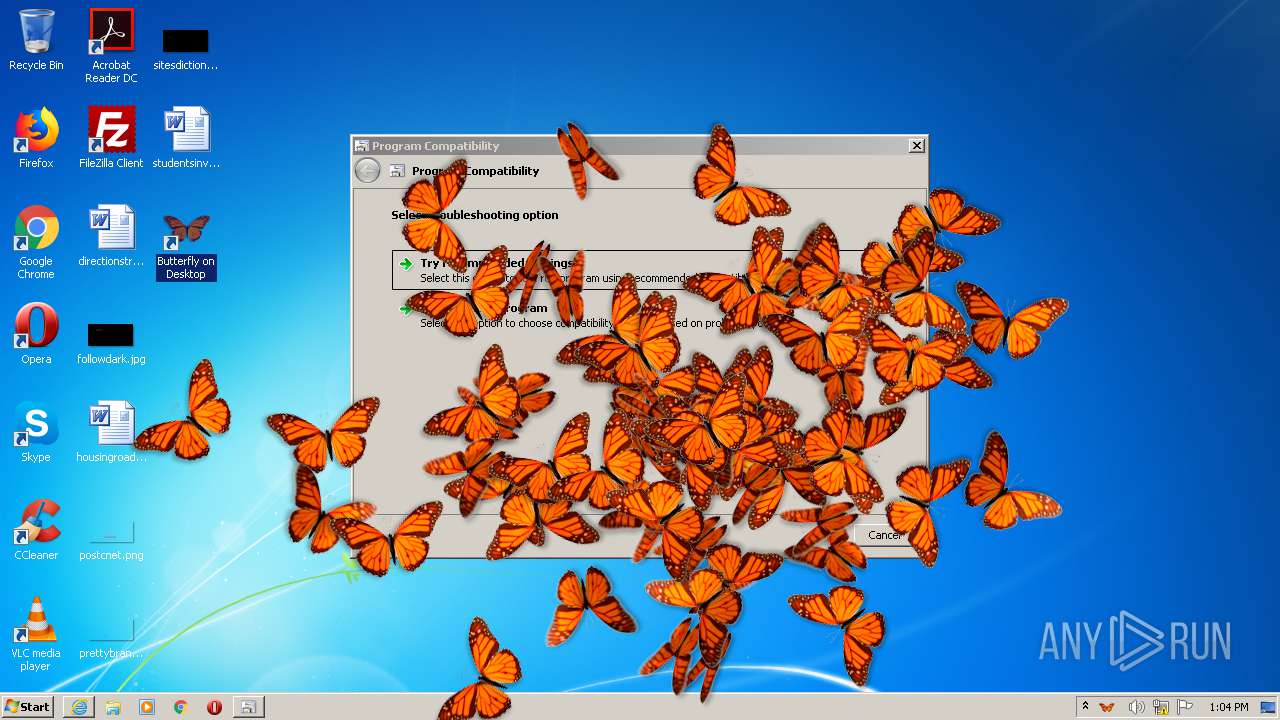
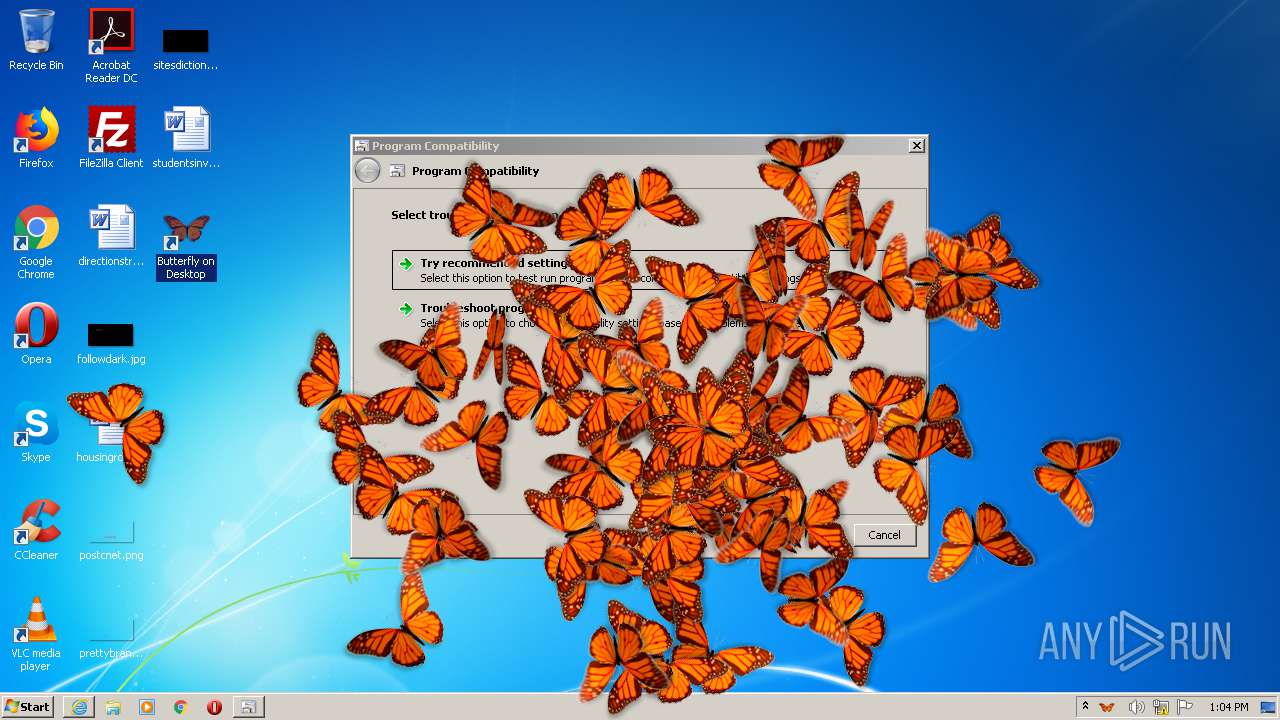
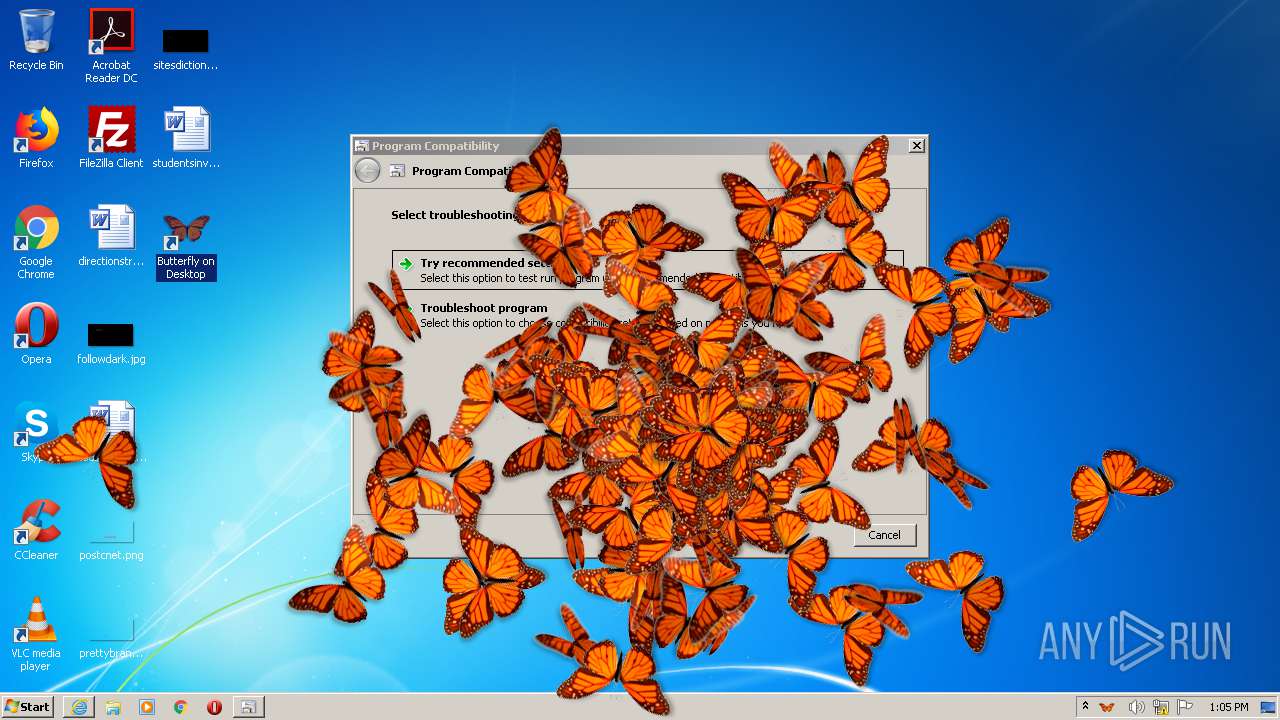
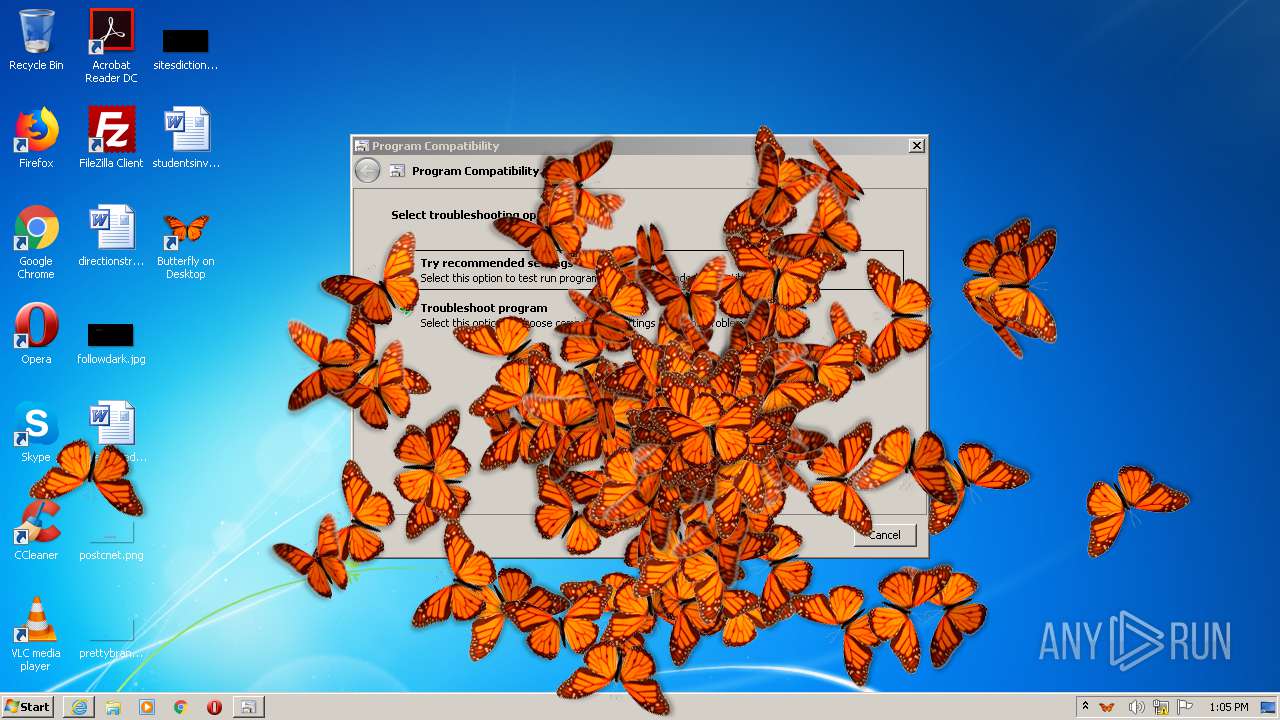
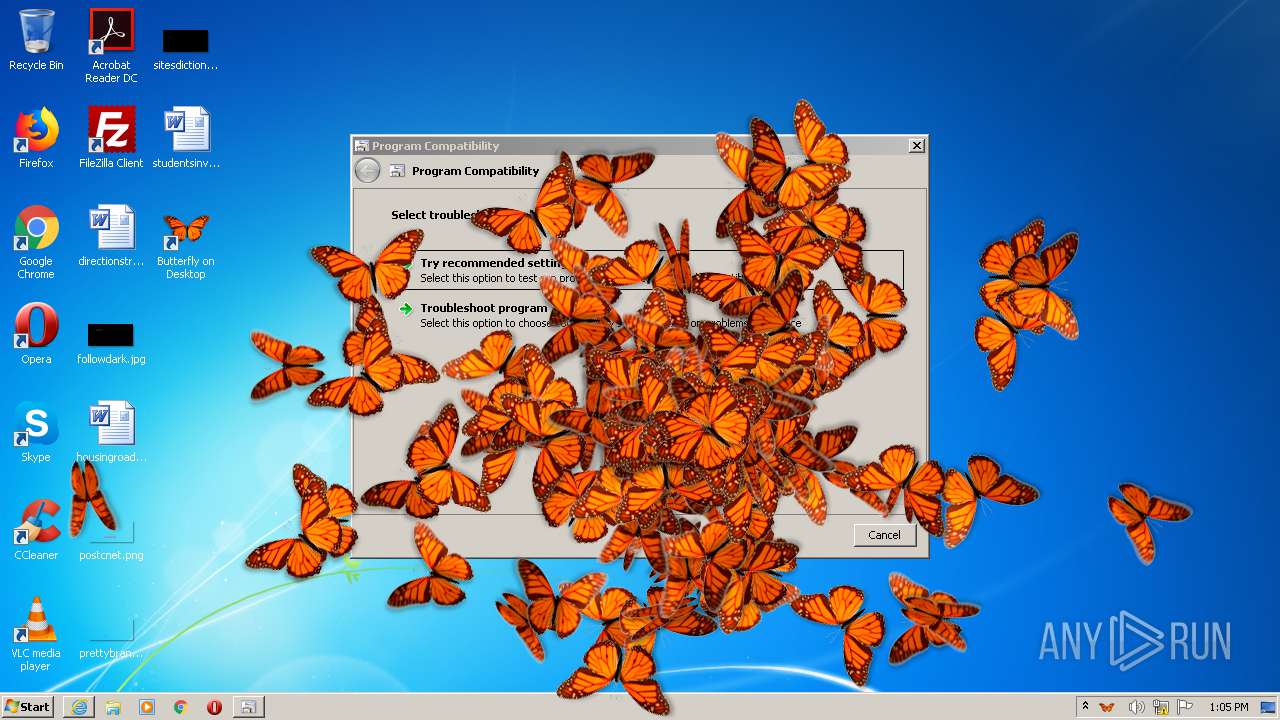
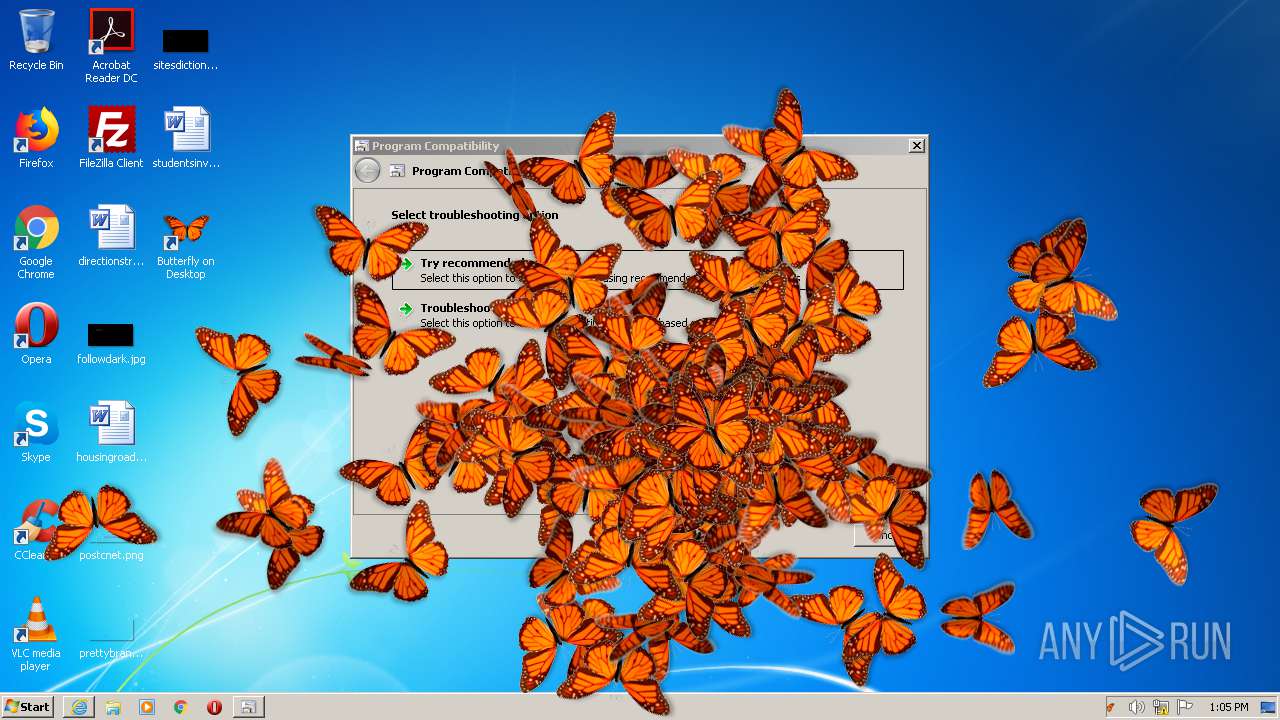
Changes the autorun value in the registry
- butterflyondesktop.tmp (PID: 3804)
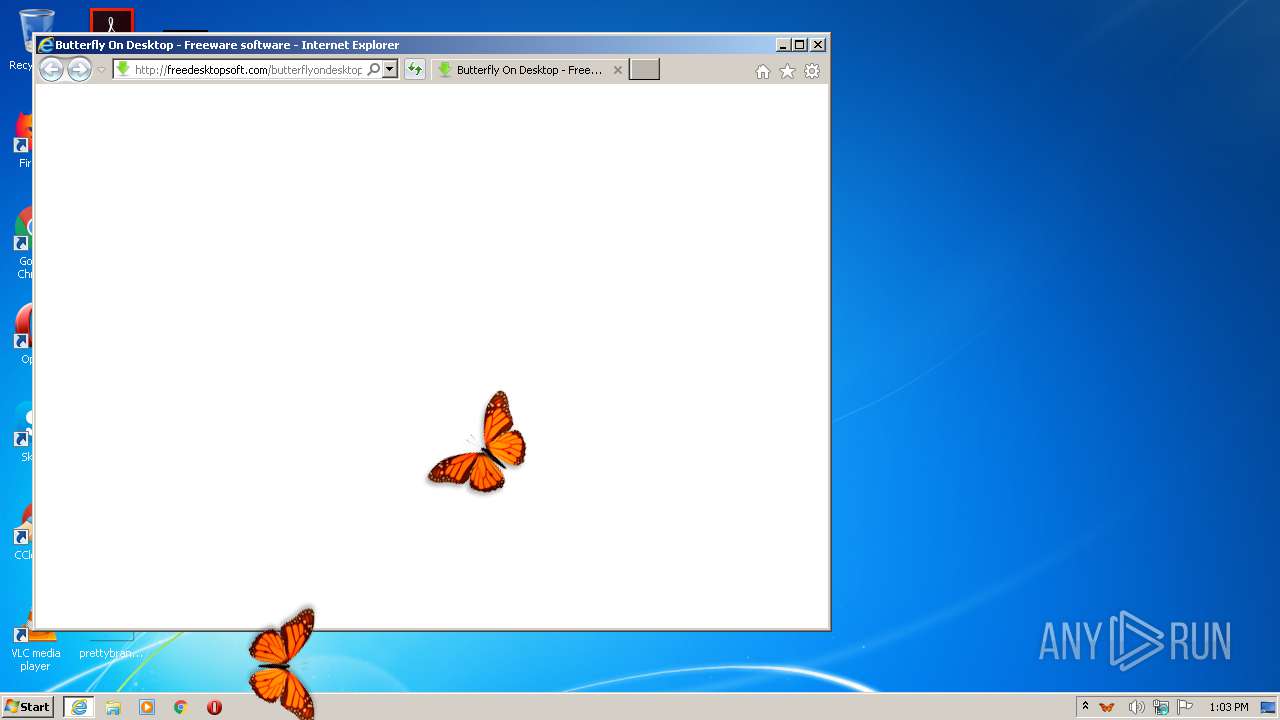
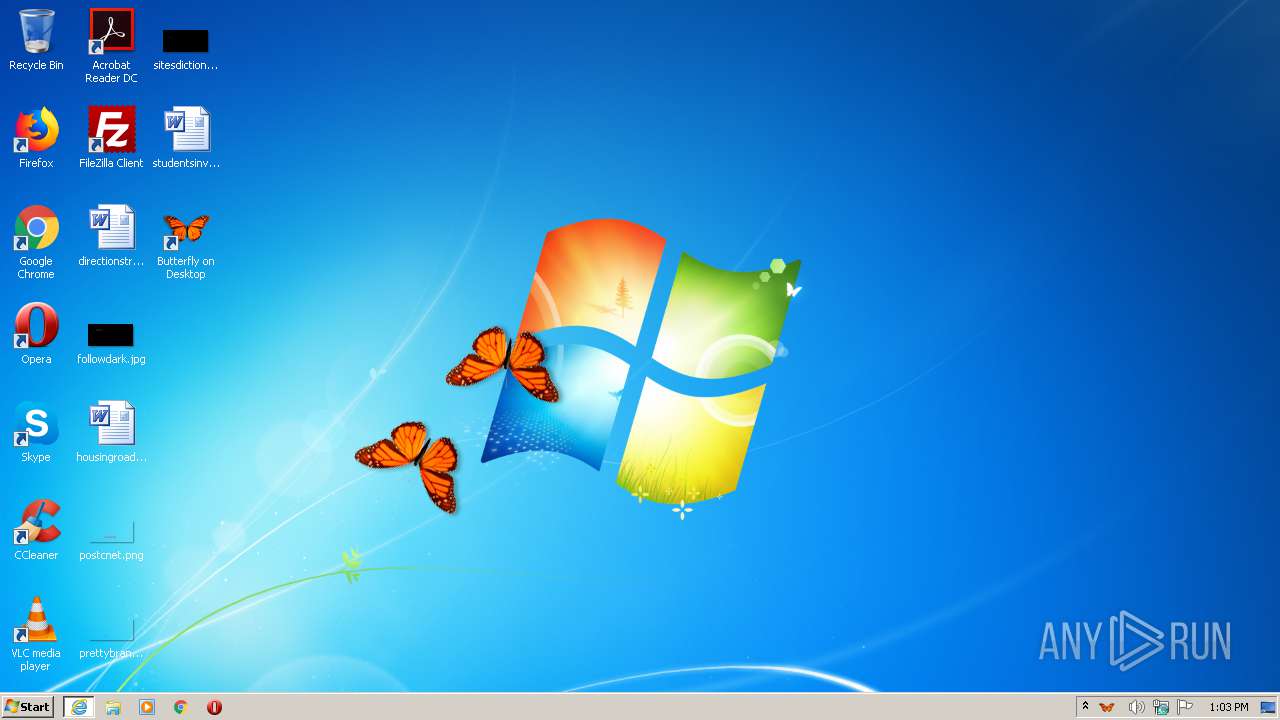
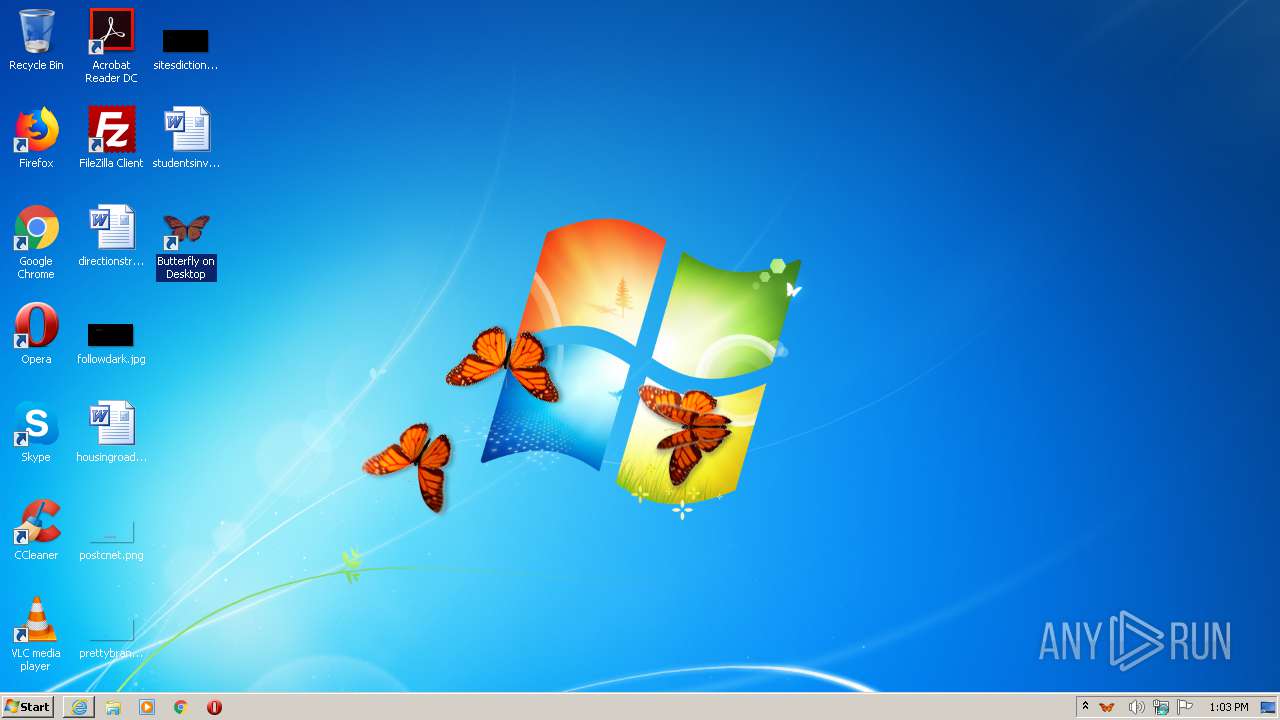
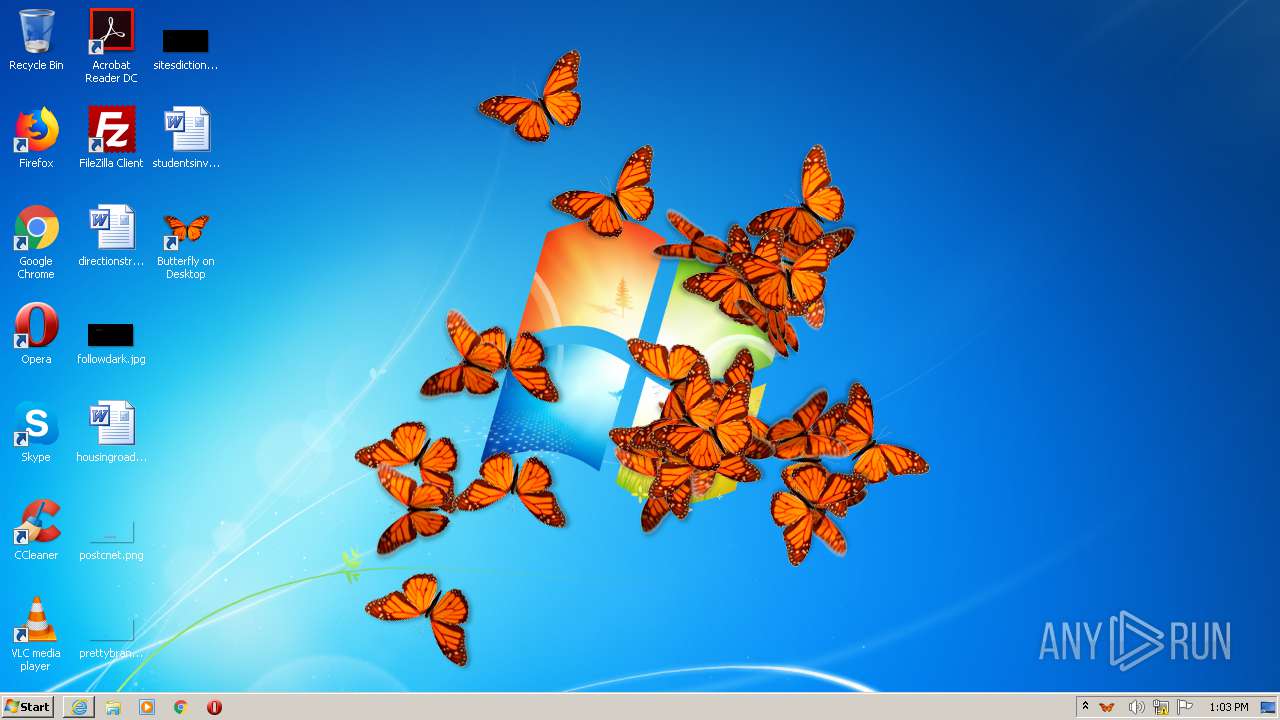
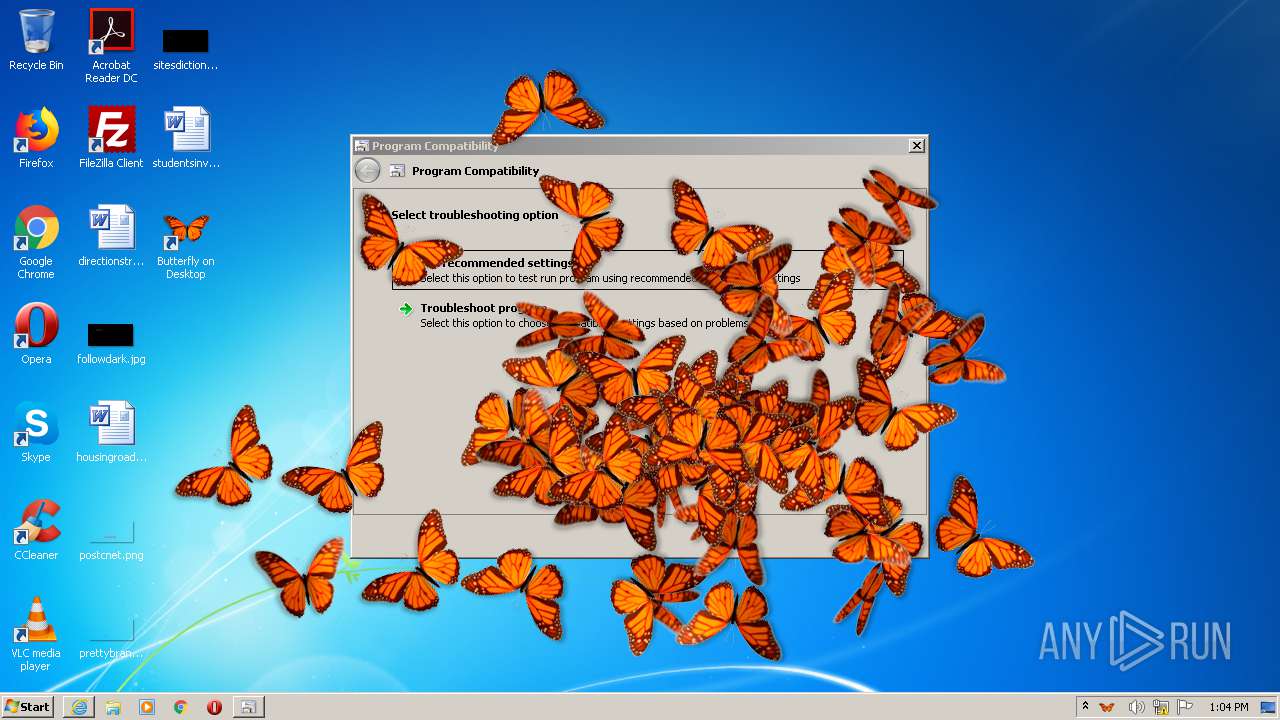
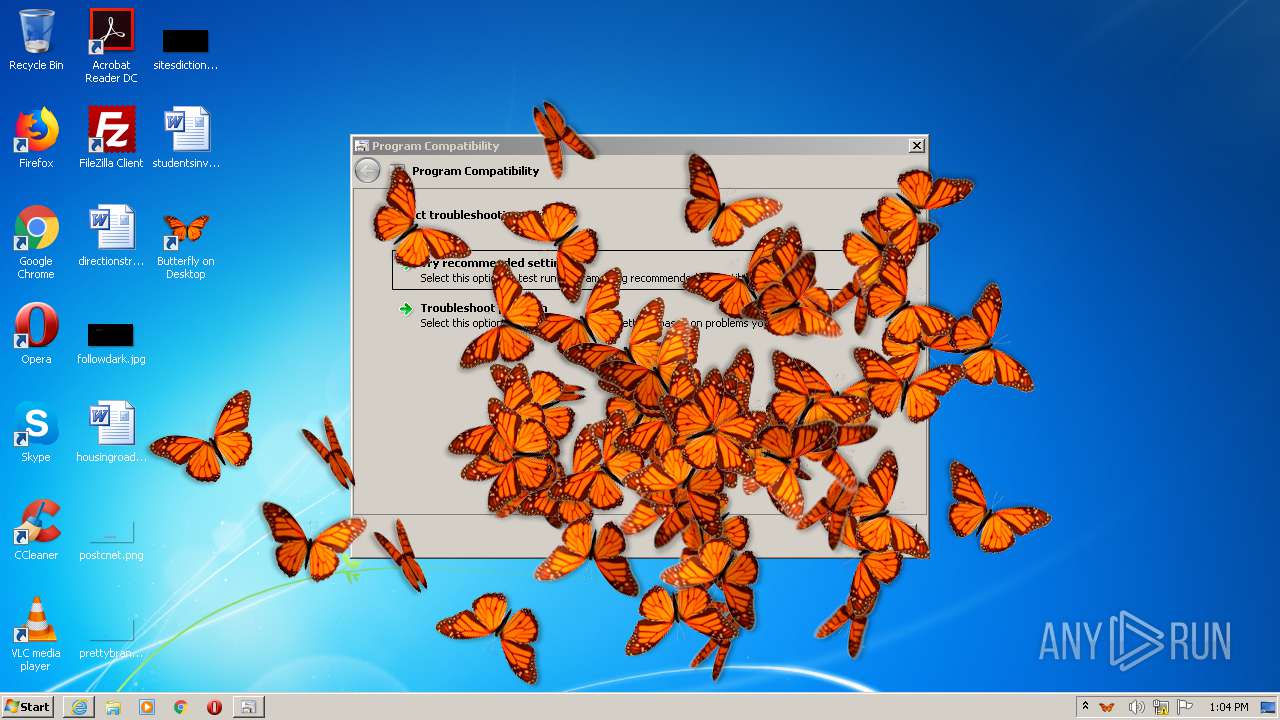
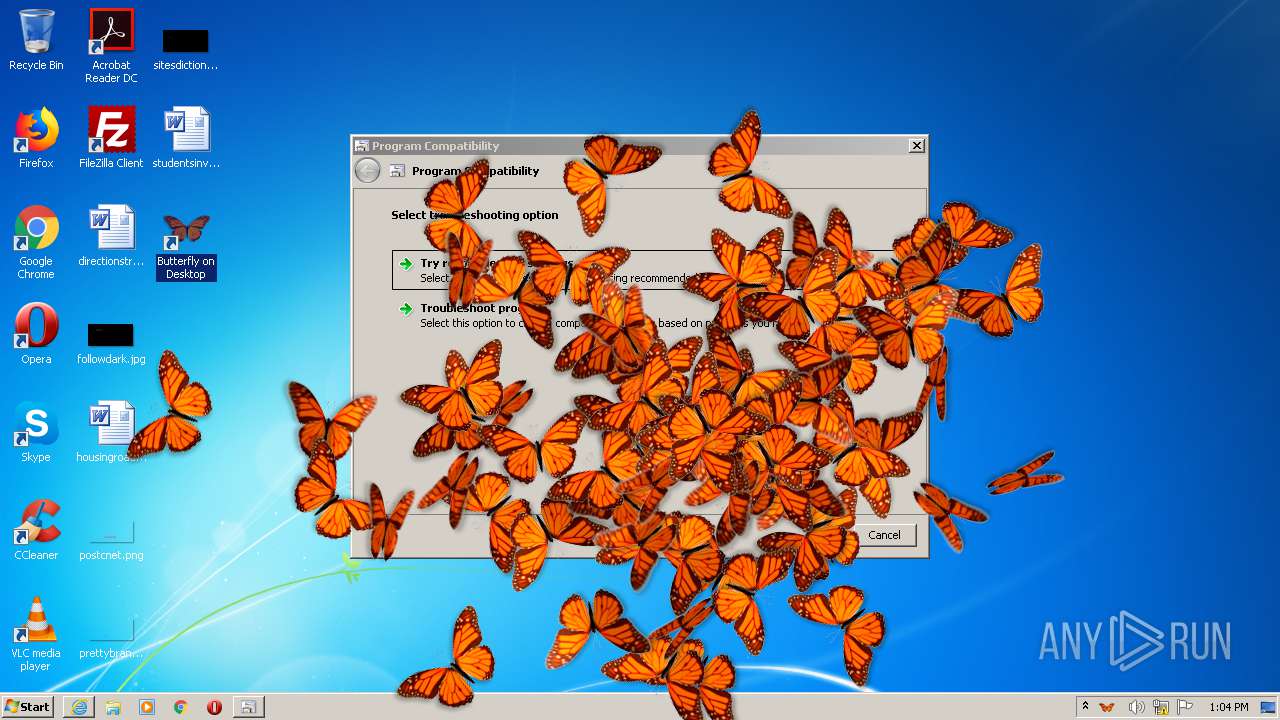
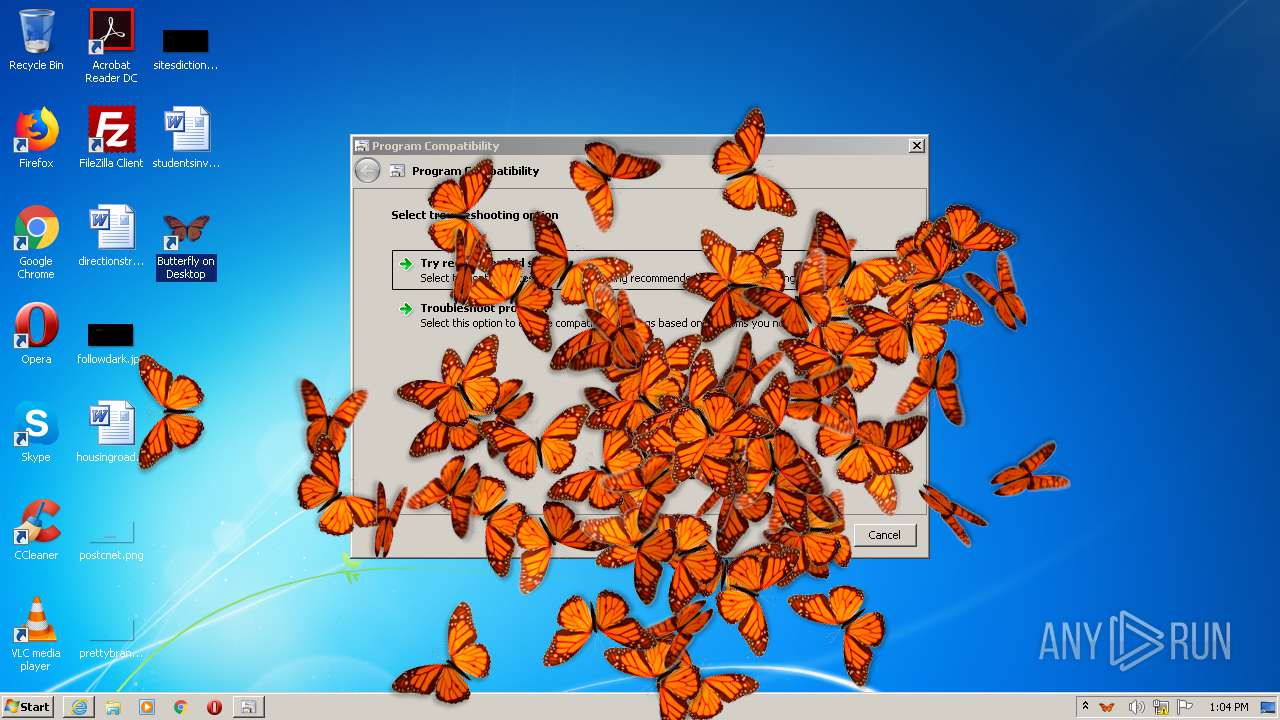
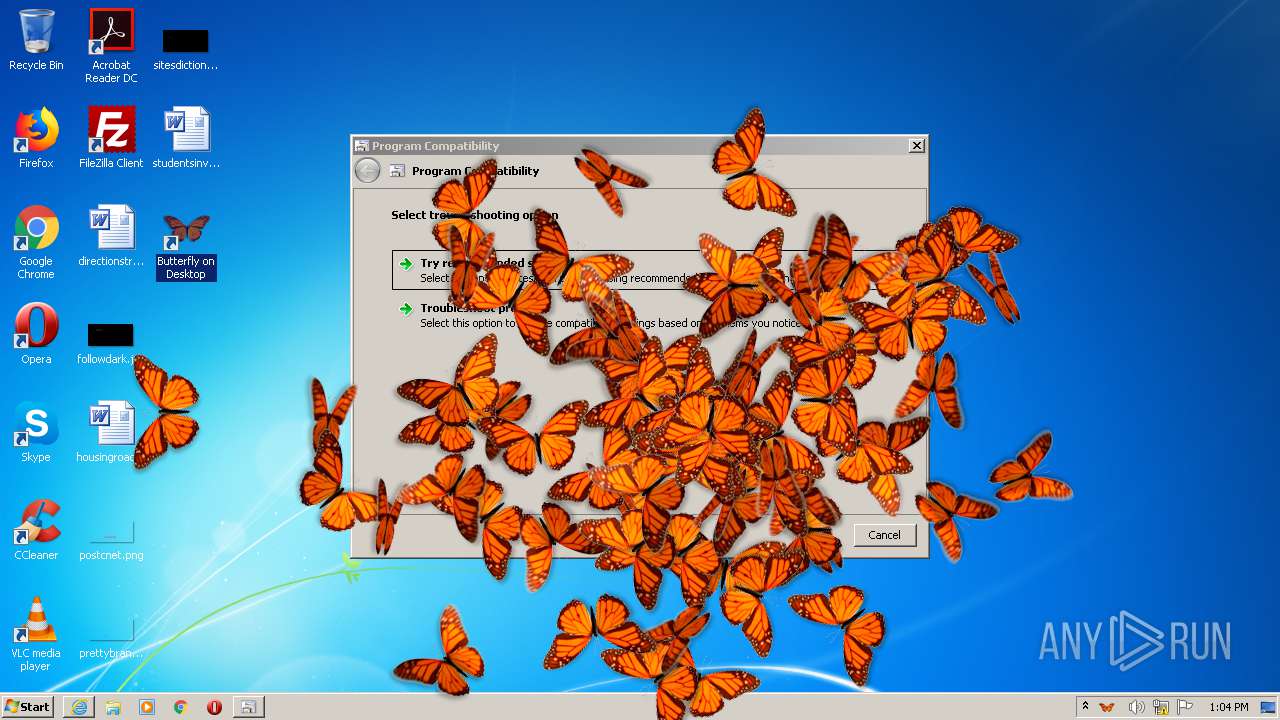
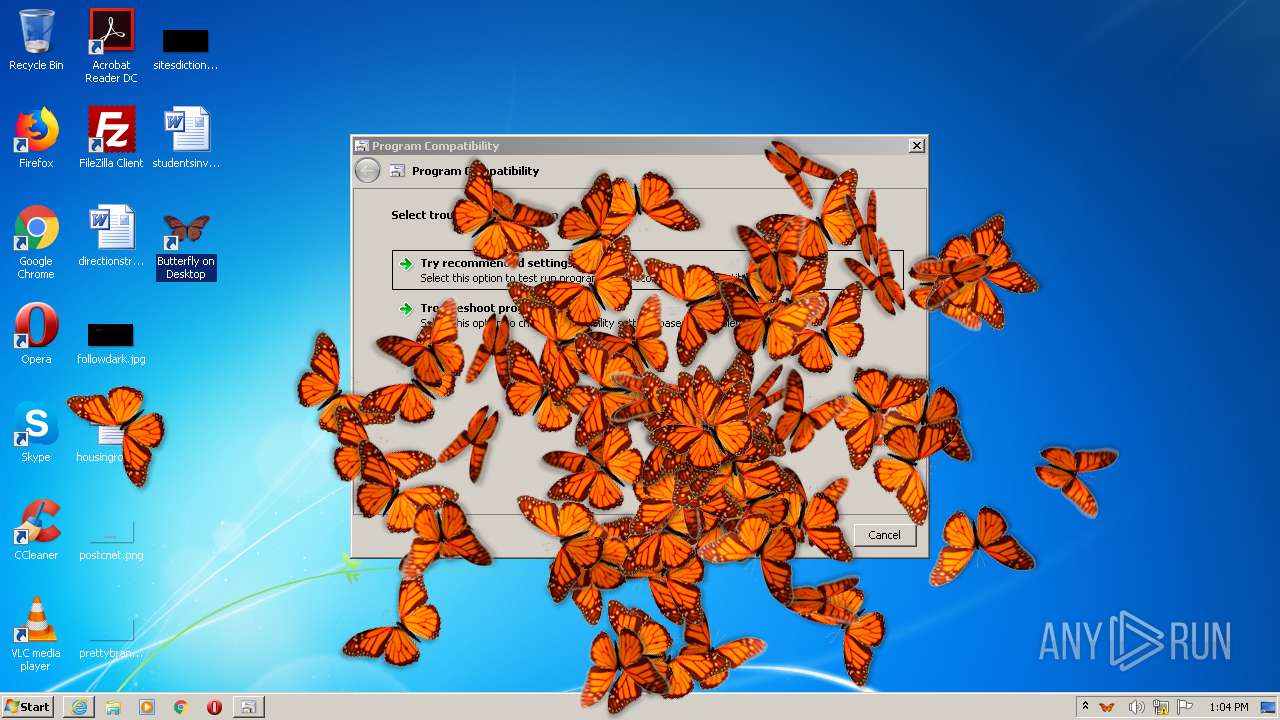
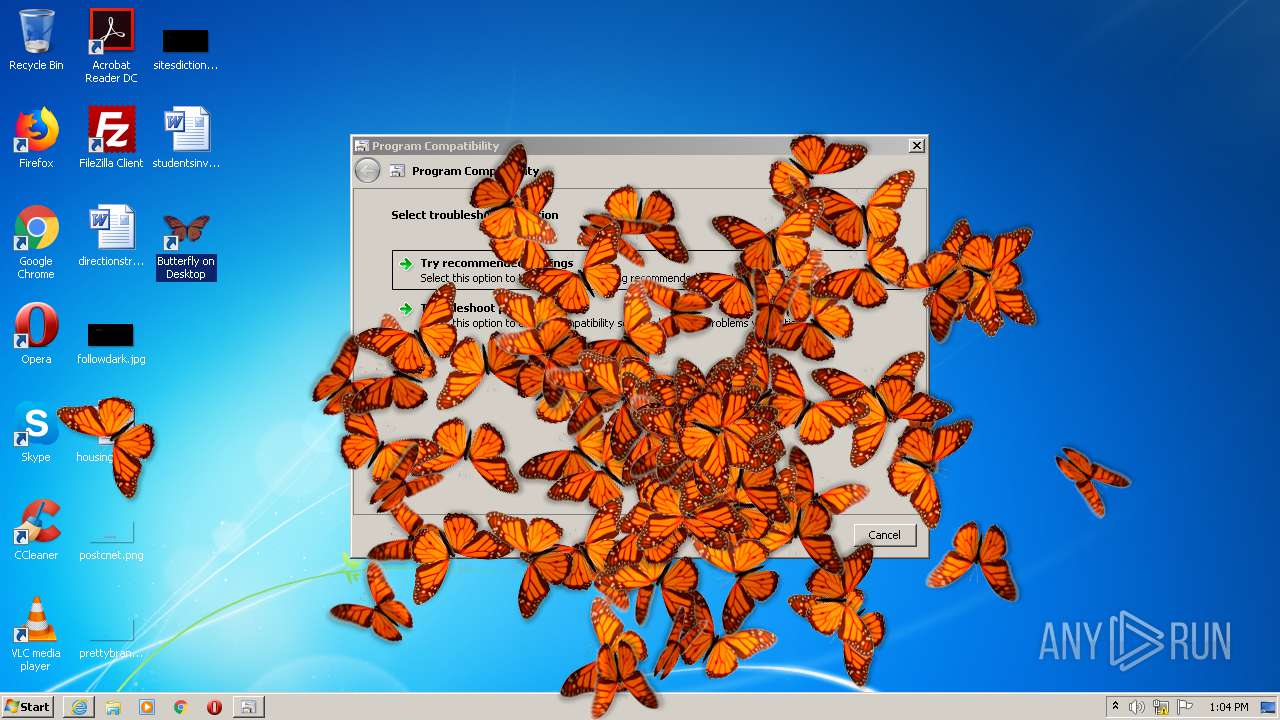
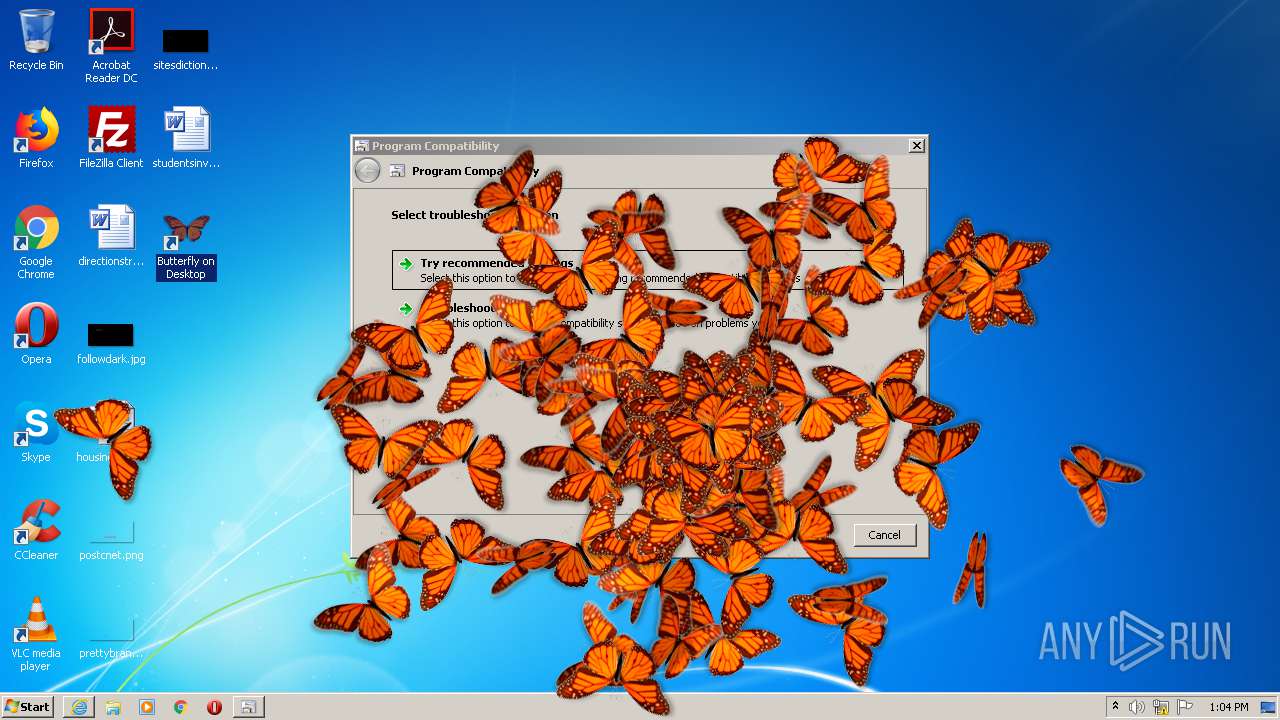
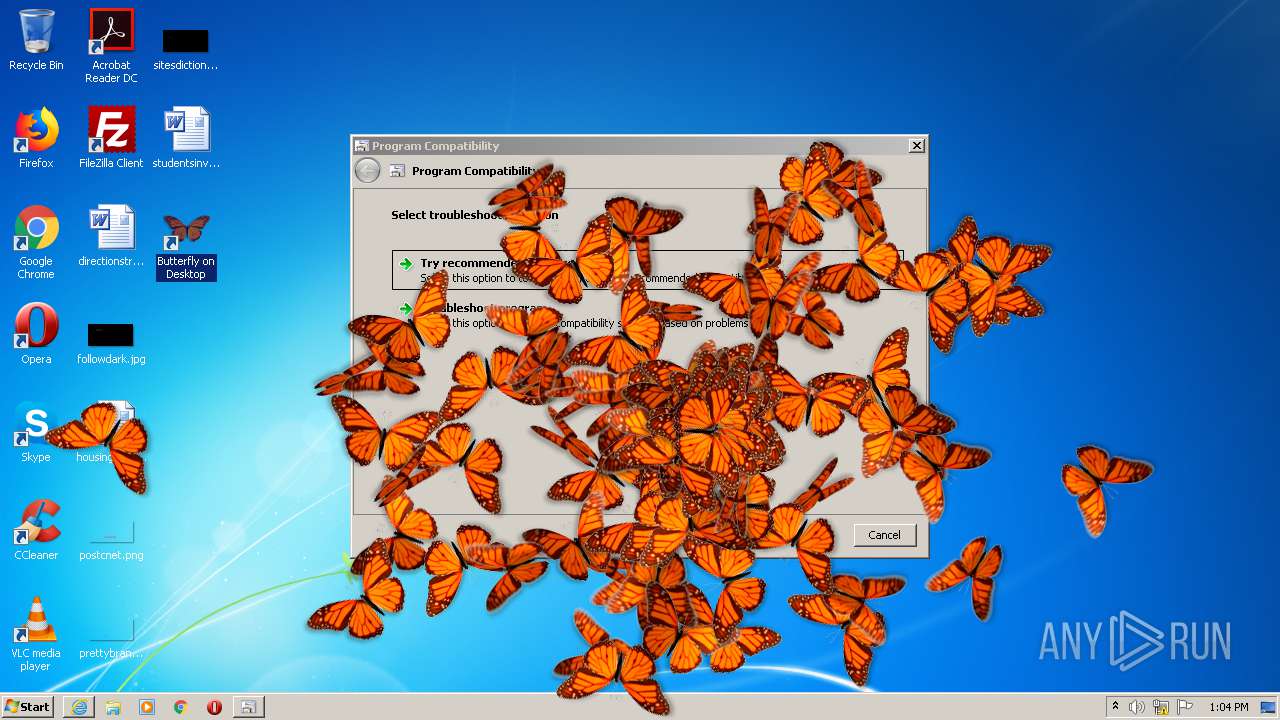
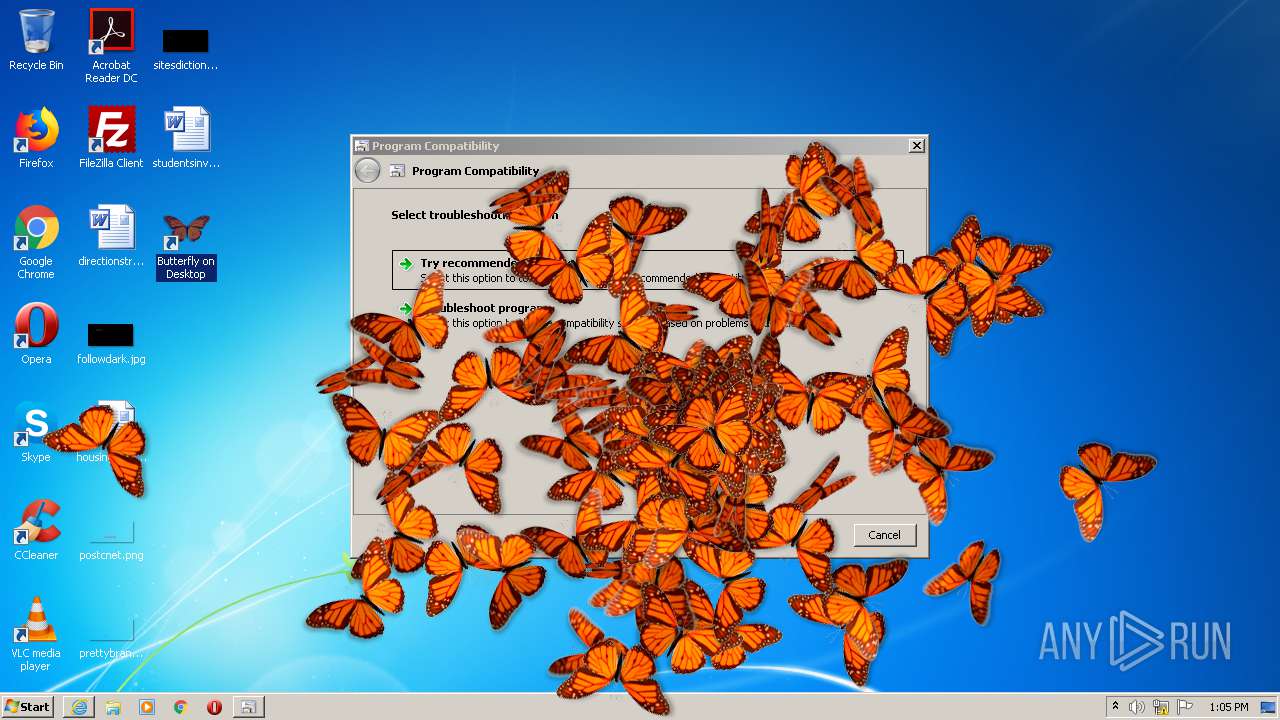
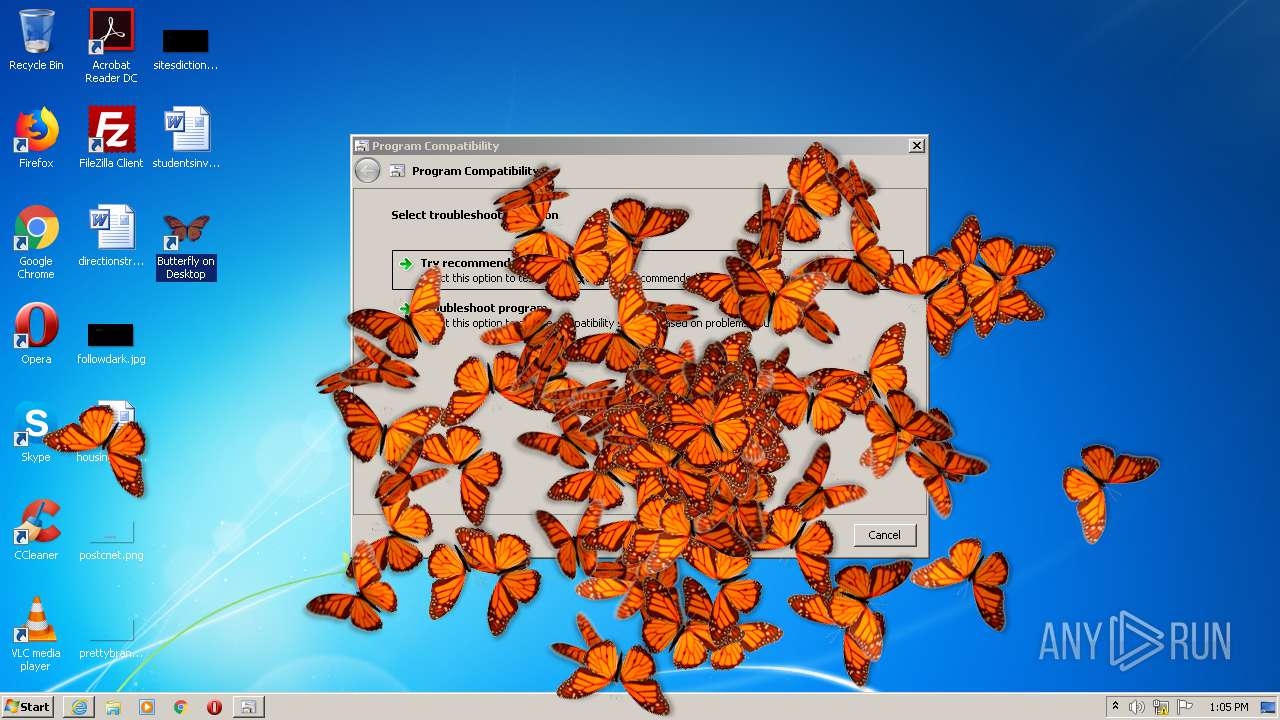
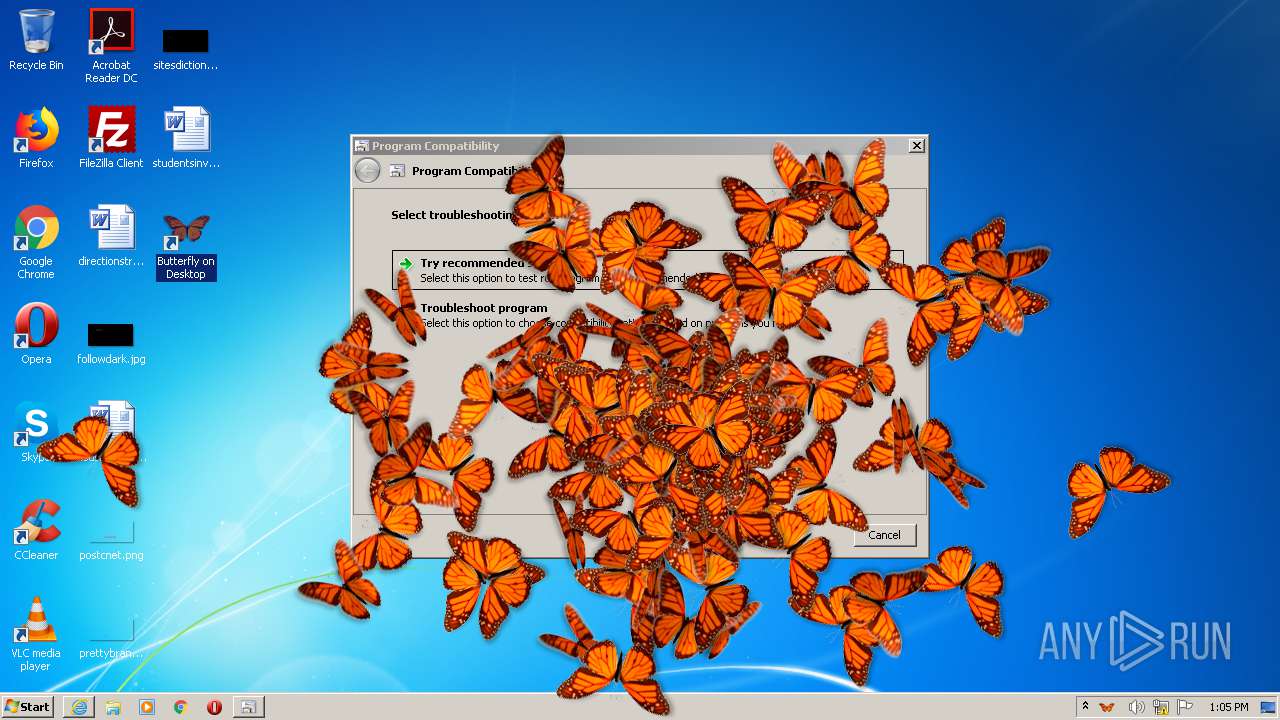
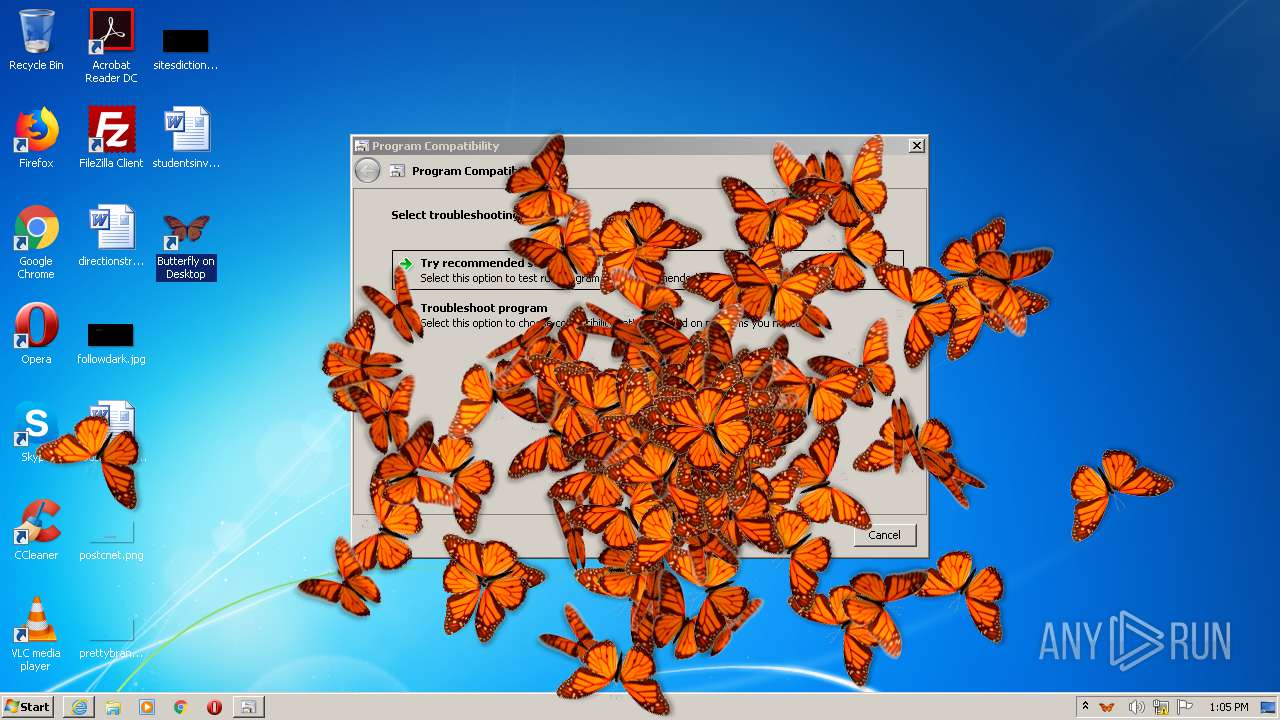
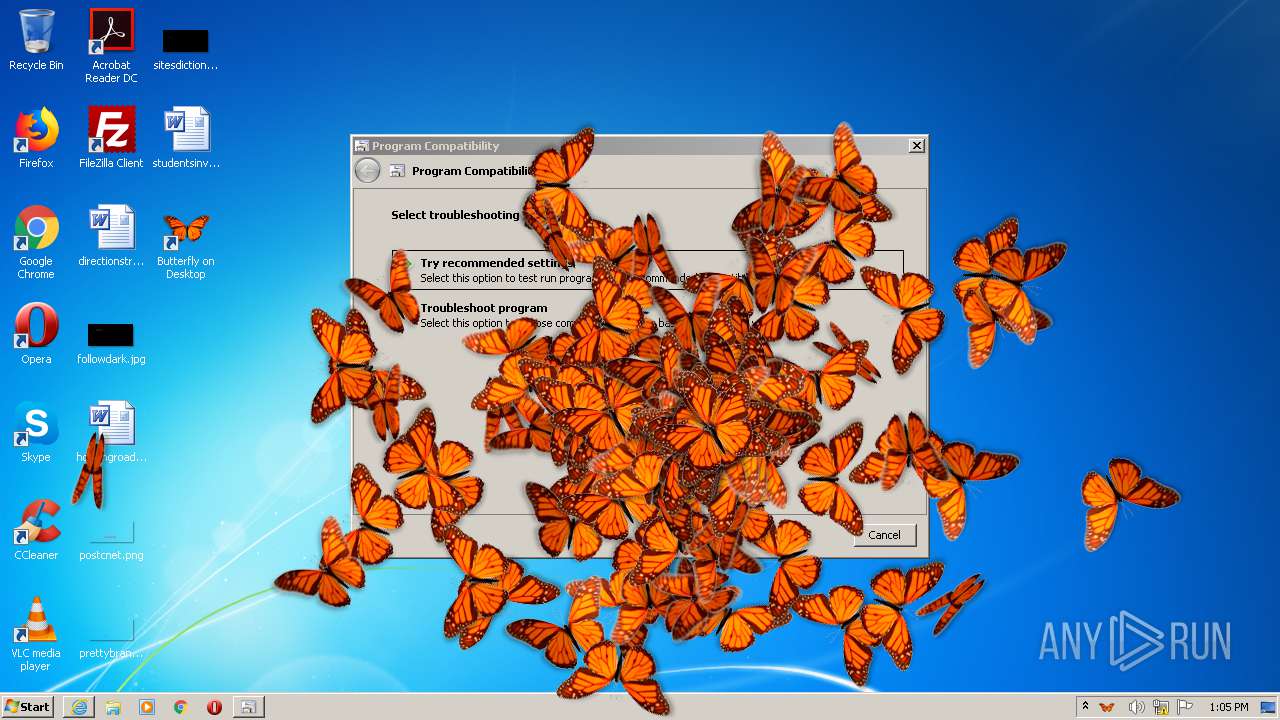
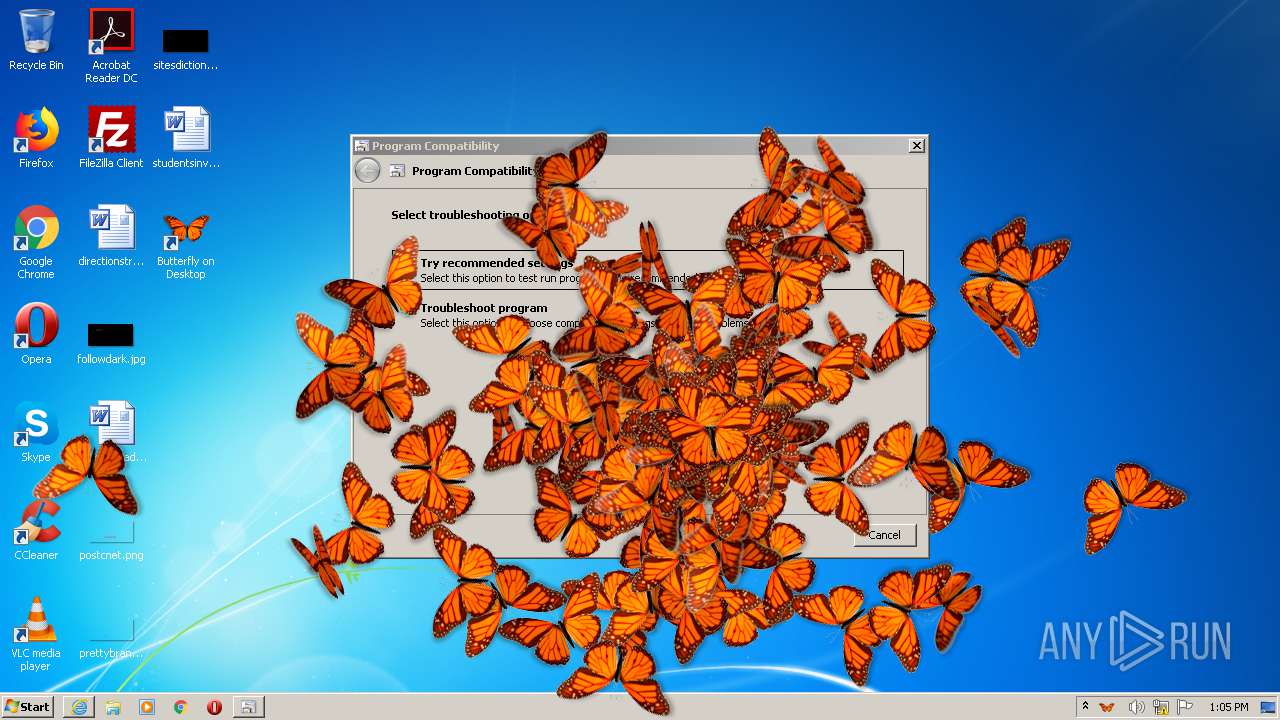
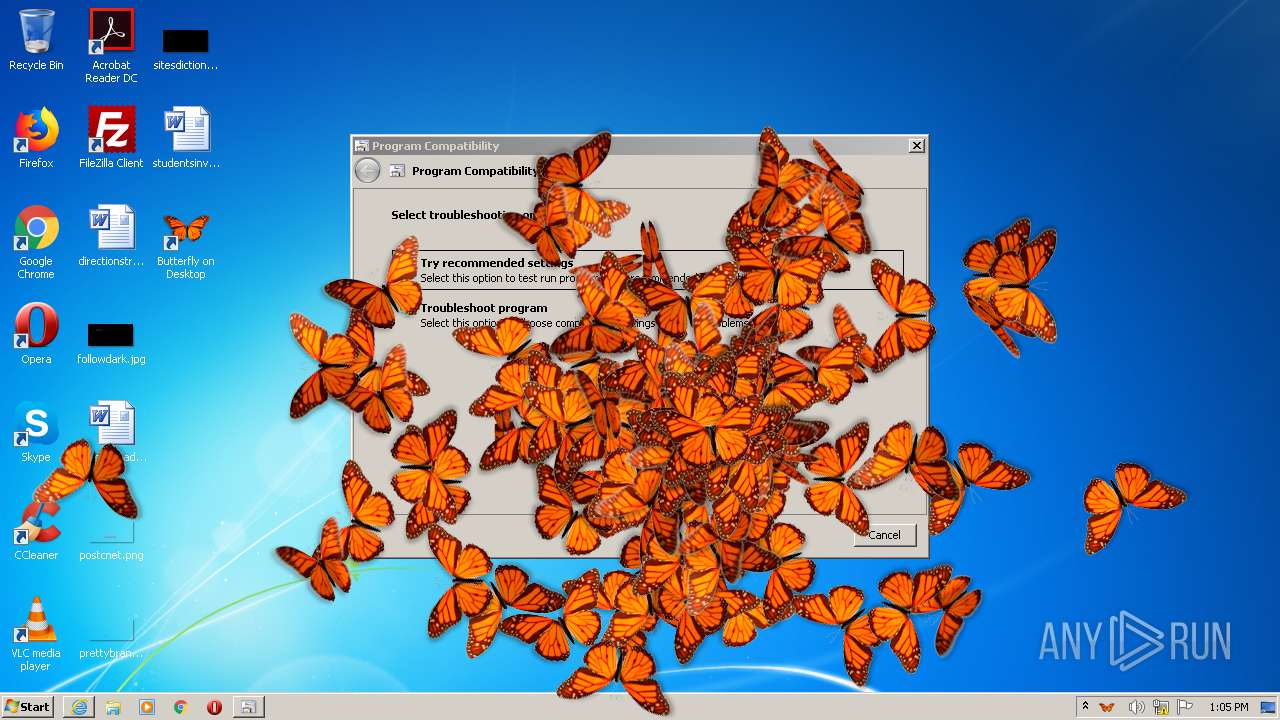
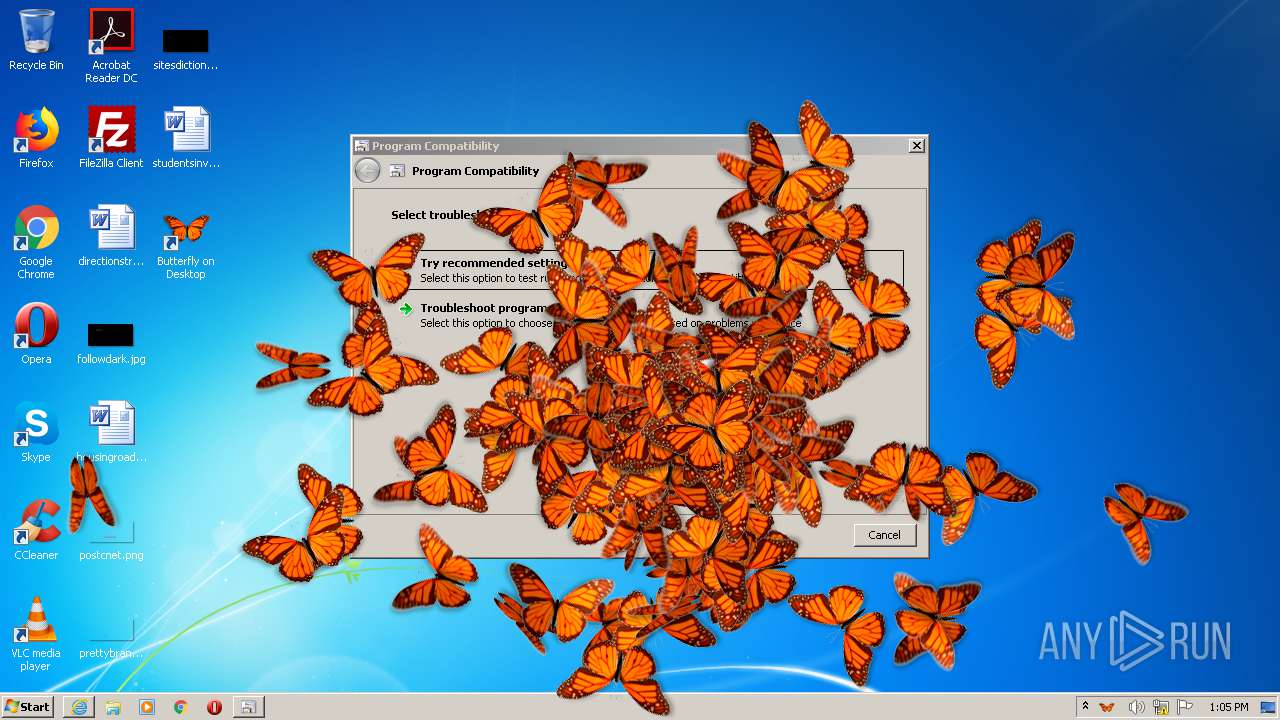
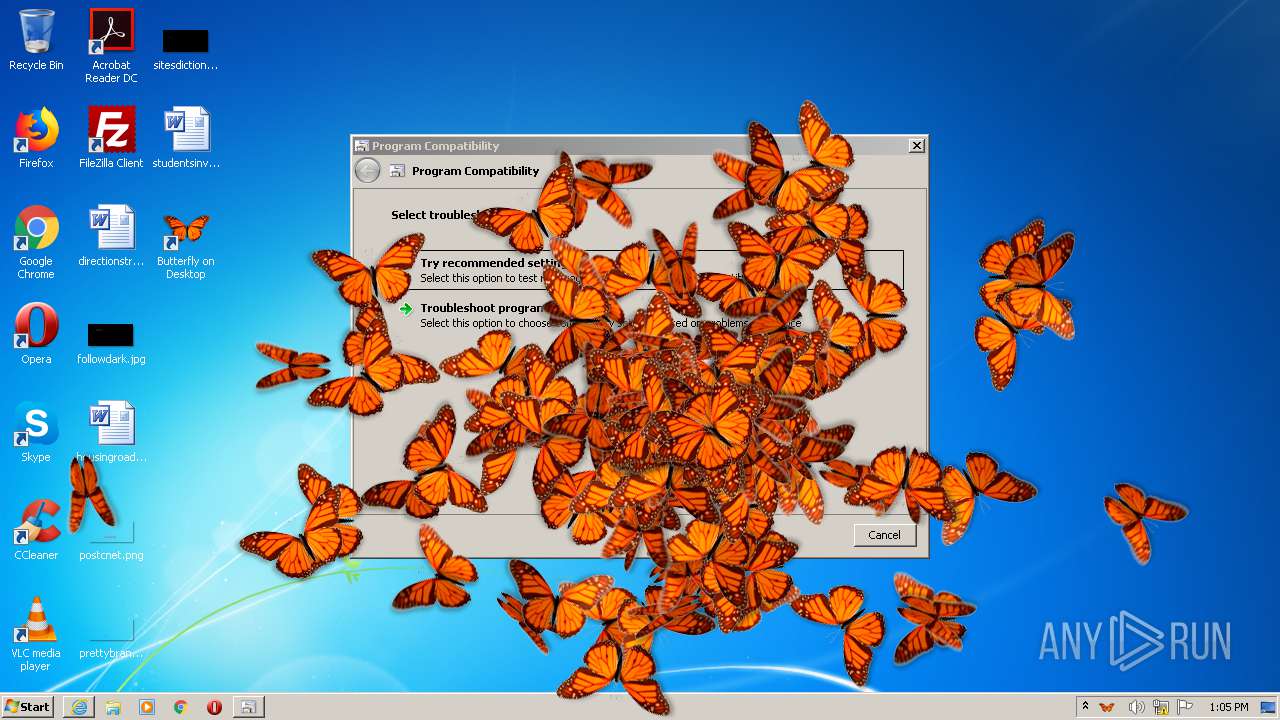
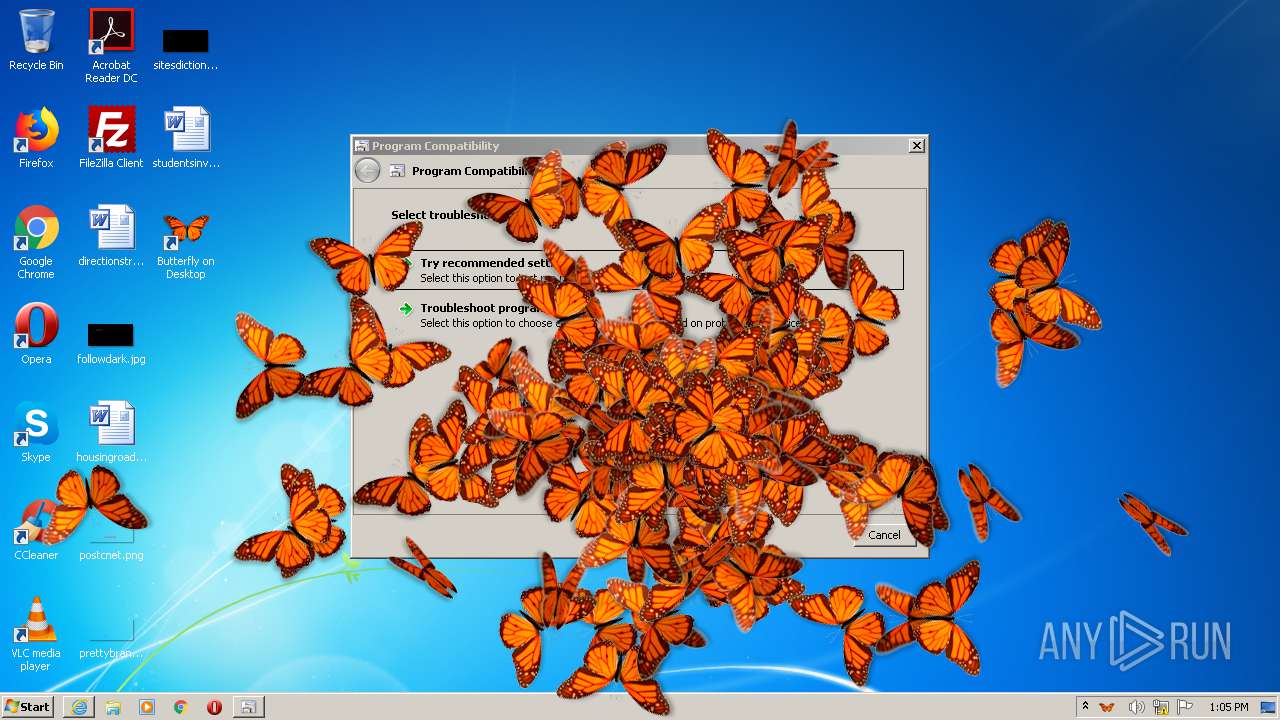
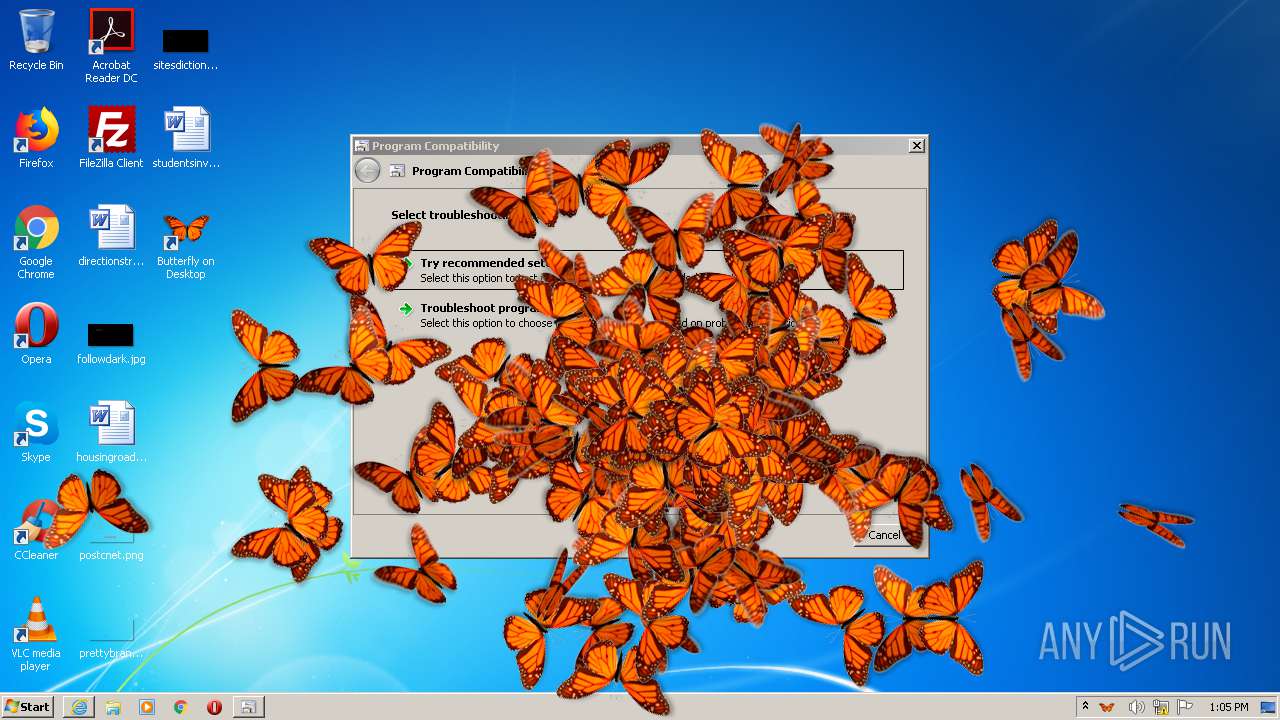
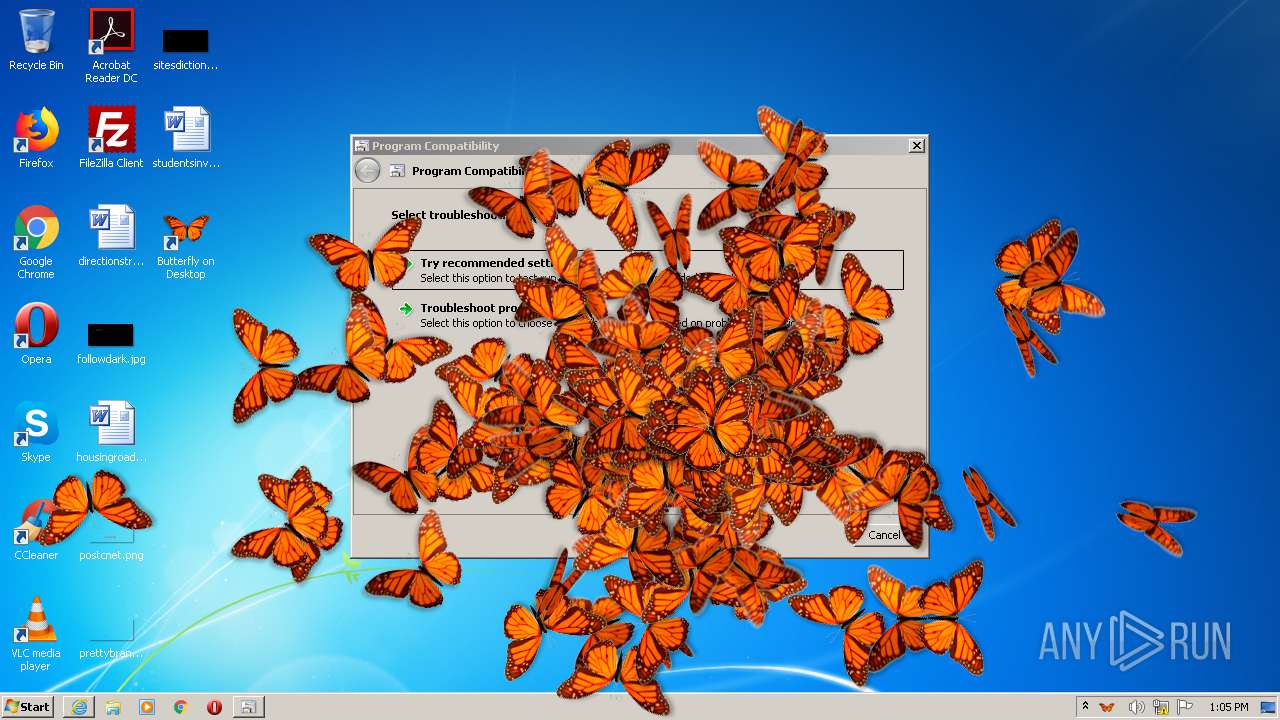
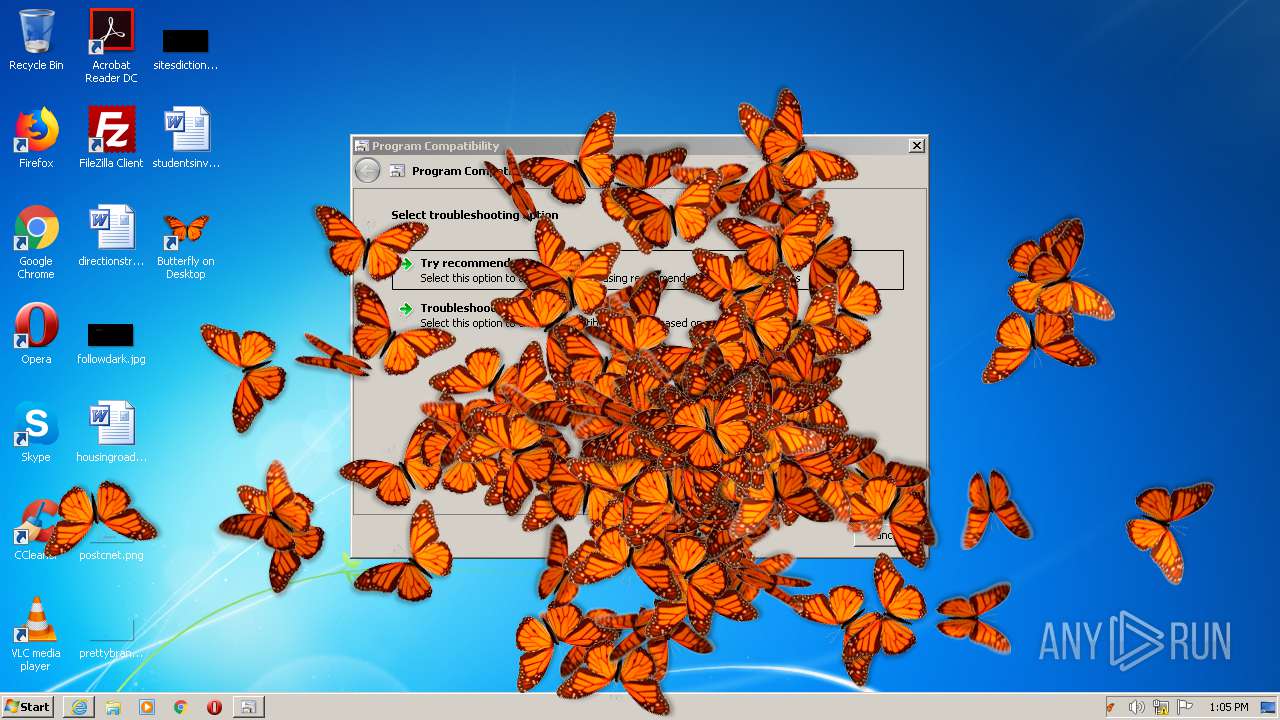
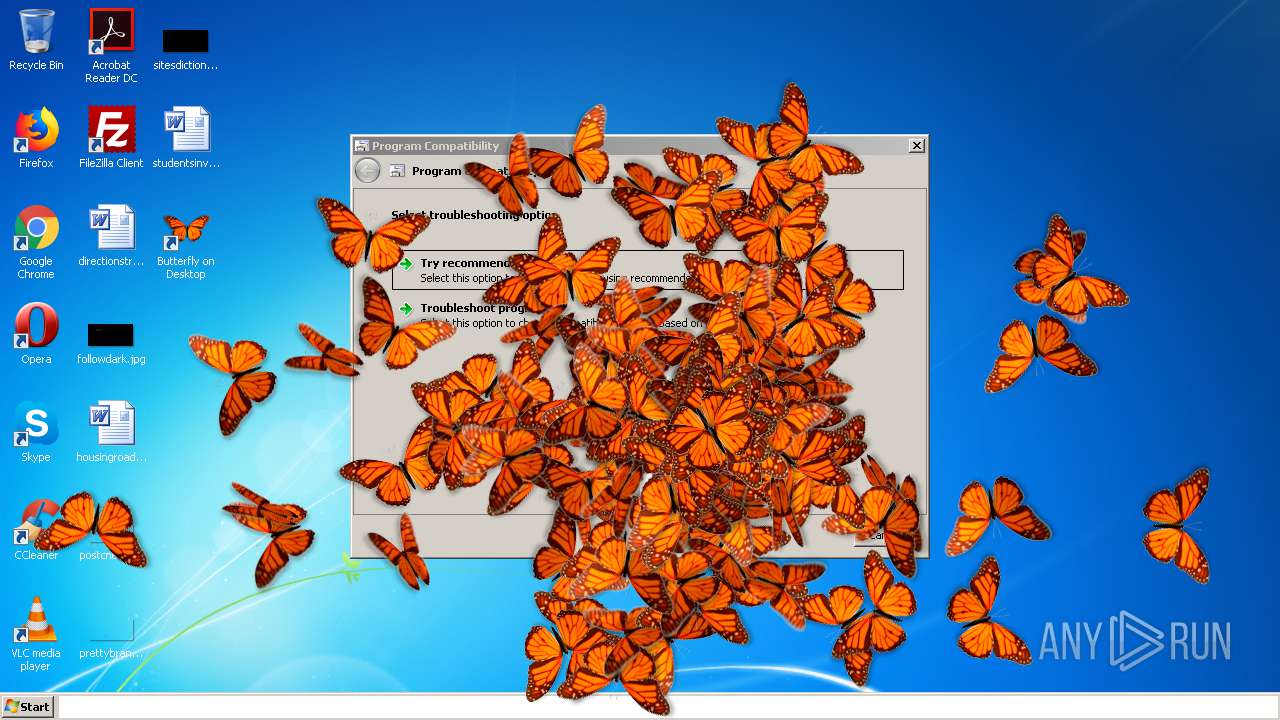
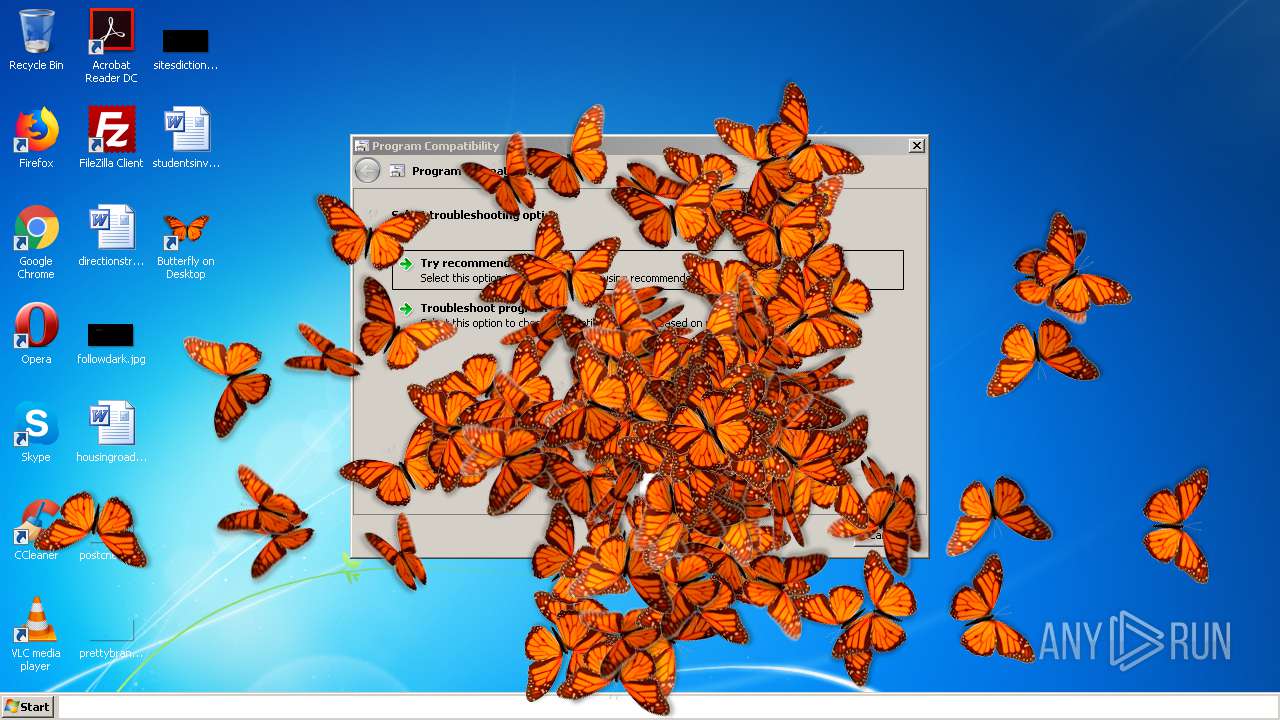
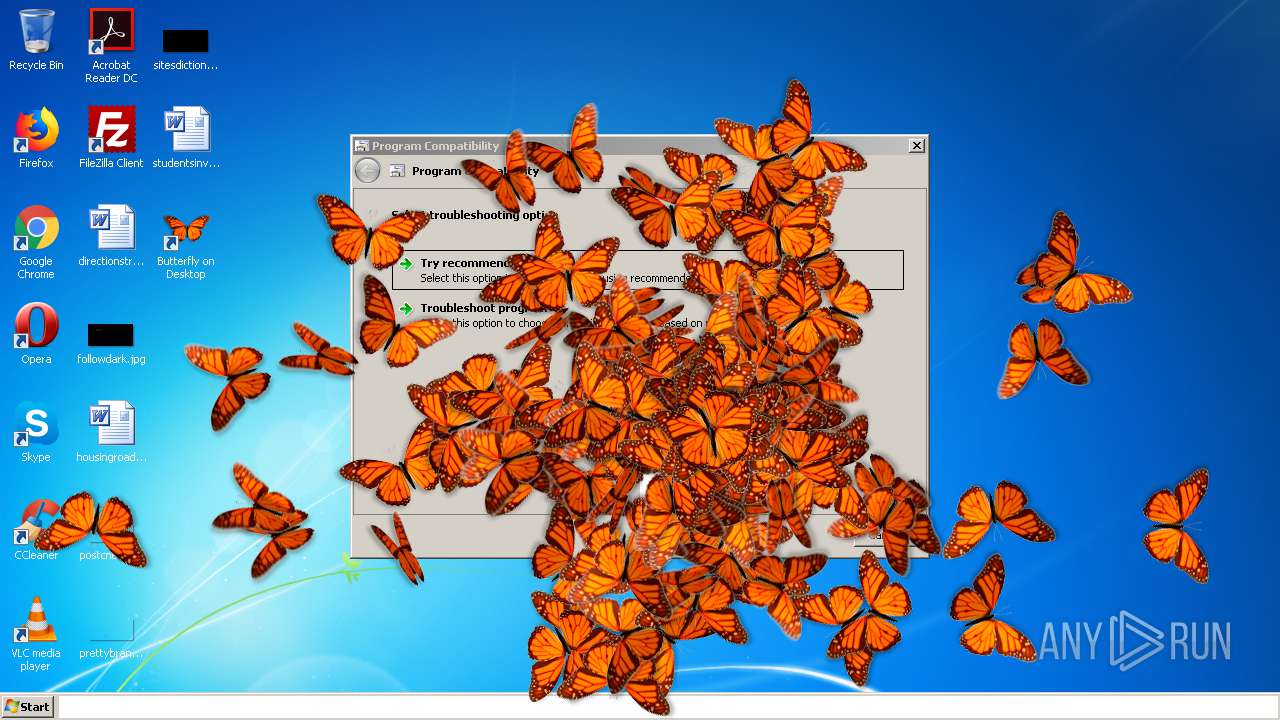
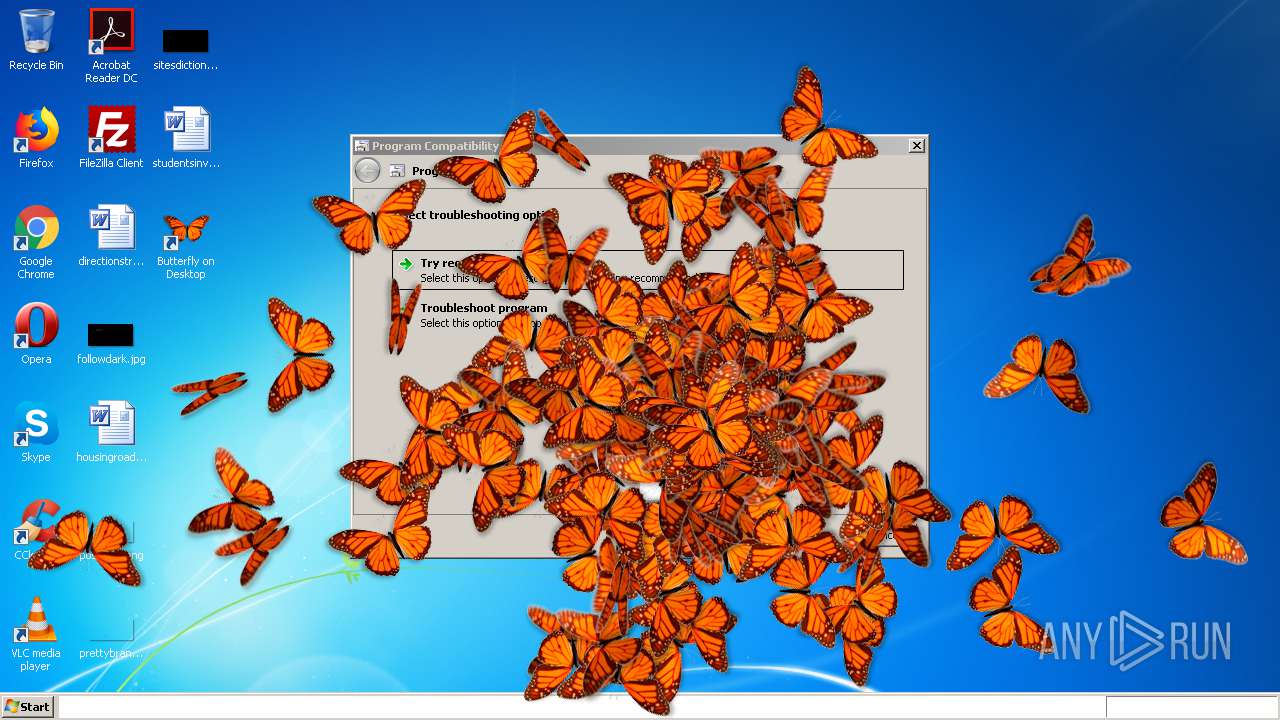
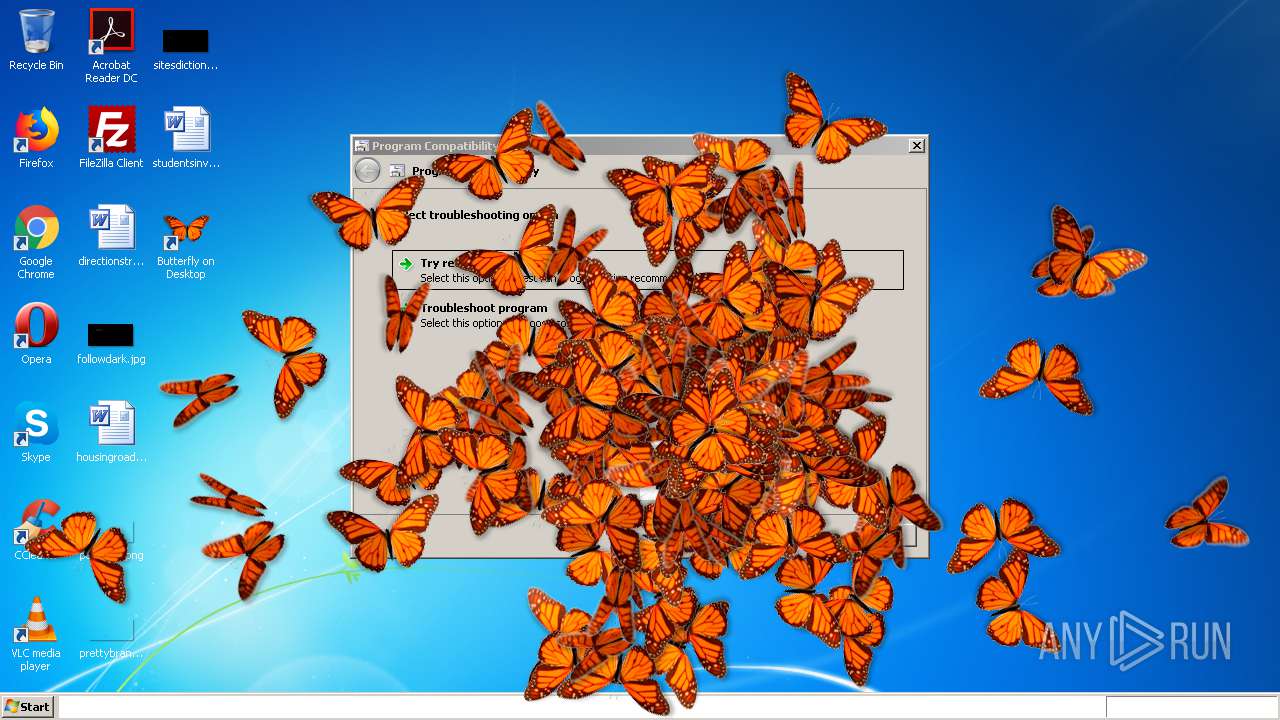
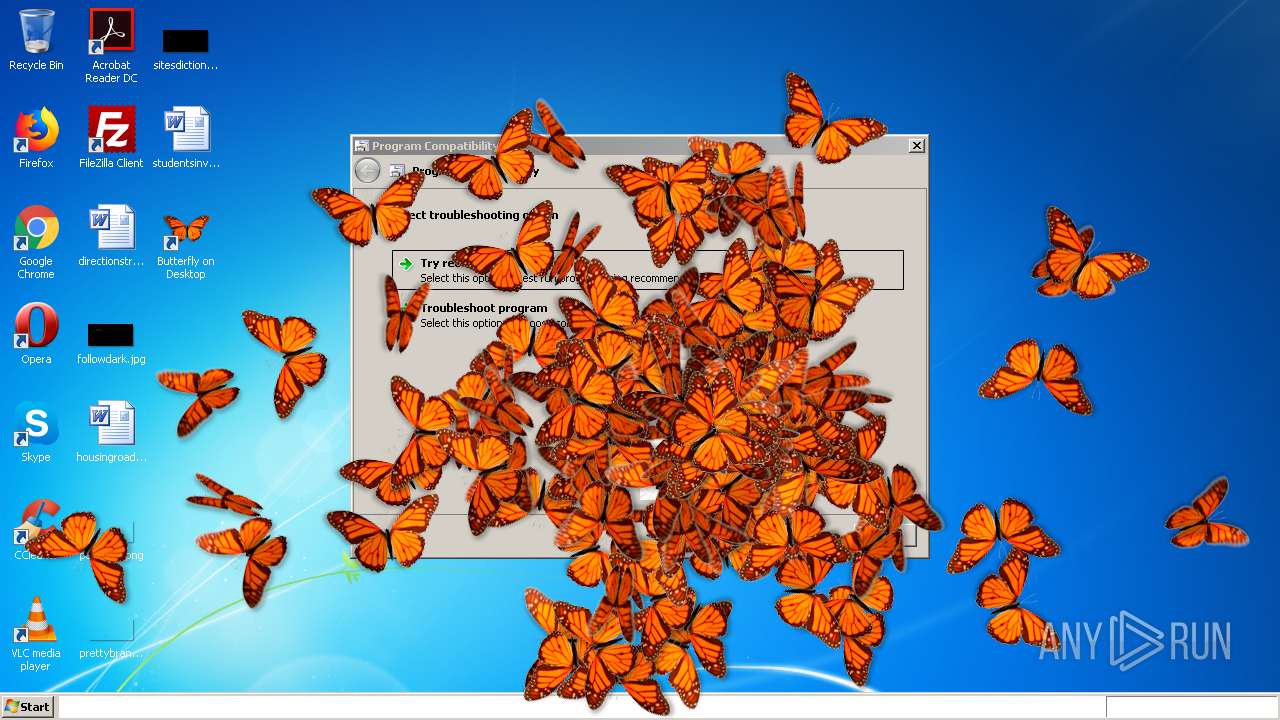
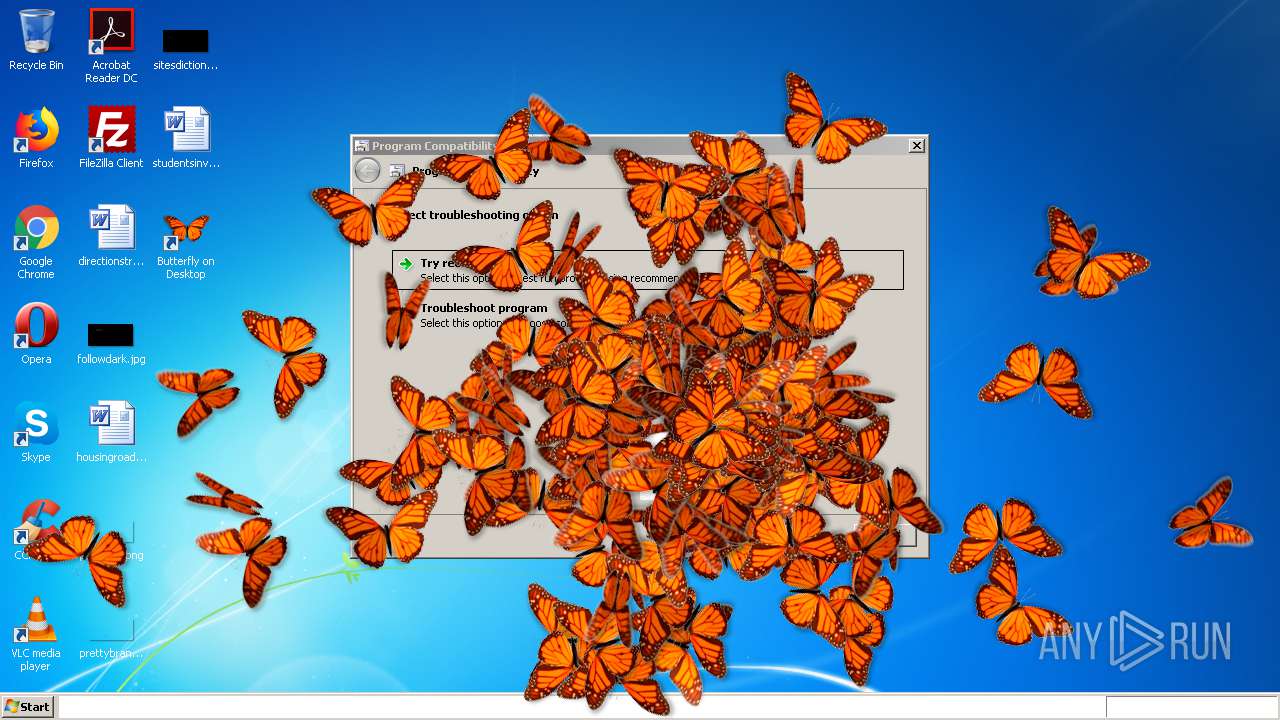
Application was dropped or rewritten from another process
- ButterflyOnDesktop.exe (PID: 1296)
- ButterflyOnDesktop.exe (PID: 4012)
- ButterflyOnDesktop.exe (PID: 2156)
- ButterflyOnDesktop.exe (PID: 760)
- ButterflyOnDesktop.exe (PID: 624)
- ButterflyOnDesktop.exe (PID: 2492)
- ButterflyOnDesktop.exe (PID: 3688)
- ButterflyOnDesktop.exe (PID: 2956)
- ButterflyOnDesktop.exe (PID: 2132)
- ButterflyOnDesktop.exe (PID: 1160)
- ButterflyOnDesktop.exe (PID: 1736)
- ButterflyOnDesktop.exe (PID: 2424)
- ButterflyOnDesktop.exe (PID: 3836)
- ButterflyOnDesktop.exe (PID: 3968)
- ButterflyOnDesktop.exe (PID: 2212)
- ButterflyOnDesktop.exe (PID: 1660)
- ButterflyOnDesktop.exe (PID: 2260)
- ButterflyOnDesktop.exe (PID: 3208)
- ButterflyOnDesktop.exe (PID: 2360)
- ButterflyOnDesktop.exe (PID: 1556)
- ButterflyOnDesktop.exe (PID: 3676)
- ButterflyOnDesktop.exe (PID: 3236)
- ButterflyOnDesktop.exe (PID: 1996)
- ButterflyOnDesktop.exe (PID: 3076)
- ButterflyOnDesktop.exe (PID: 1532)
- ButterflyOnDesktop.exe (PID: 1936)
- ButterflyOnDesktop.exe (PID: 1800)
- ButterflyOnDesktop.exe (PID: 3860)
- ButterflyOnDesktop.exe (PID: 1860)
- ButterflyOnDesktop.exe (PID: 3168)
- ButterflyOnDesktop.exe (PID: 1516)
- ButterflyOnDesktop.exe (PID: 3876)
- ButterflyOnDesktop.exe (PID: 2948)
- ButterflyOnDesktop.exe (PID: 2896)
- ButterflyOnDesktop.exe (PID: 1756)
- ButterflyOnDesktop.exe (PID: 3364)
- ButterflyOnDesktop.exe (PID: 2640)
- ButterflyOnDesktop.exe (PID: 3384)
- ButterflyOnDesktop.exe (PID: 2344)
- ButterflyOnDesktop.exe (PID: 4072)
- ButterflyOnDesktop.exe (PID: 2348)
- ButterflyOnDesktop.exe (PID: 3496)
- ButterflyOnDesktop.exe (PID: 2664)
- ButterflyOnDesktop.exe (PID: 3888)
- ButterflyOnDesktop.exe (PID: 3032)
- ButterflyOnDesktop.exe (PID: 2788)
- ButterflyOnDesktop.exe (PID: 2632)
- ButterflyOnDesktop.exe (PID: 2316)
- ButterflyOnDesktop.exe (PID: 2416)
- ButterflyOnDesktop.exe (PID: 2368)
- ButterflyOnDesktop.exe (PID: 1868)
- ButterflyOnDesktop.exe (PID: 3608)
- ButterflyOnDesktop.exe (PID: 3832)
- ButterflyOnDesktop.exe (PID: 2648)
- ButterflyOnDesktop.exe (PID: 3256)
- ButterflyOnDesktop.exe (PID: 1672)
- ButterflyOnDesktop.exe (PID: 768)
- ButterflyOnDesktop.exe (PID: 3564)
- ButterflyOnDesktop.exe (PID: 764)
- ButterflyOnDesktop.exe (PID: 3920)
- ButterflyOnDesktop.exe (PID: 4092)
- ButterflyOnDesktop.exe (PID: 2332)
- ButterflyOnDesktop.exe (PID: 2880)
- ButterflyOnDesktop.exe (PID: 3192)
- ButterflyOnDesktop.exe (PID: 3872)
- ButterflyOnDesktop.exe (PID: 3884)
- ButterflyOnDesktop.exe (PID: 3988)
- ButterflyOnDesktop.exe (PID: 1780)
- ButterflyOnDesktop.exe (PID: 3456)
- ButterflyOnDesktop.exe (PID: 2044)
- ButterflyOnDesktop.exe (PID: 1940)
- ButterflyOnDesktop.exe (PID: 2992)
- ButterflyOnDesktop.exe (PID: 3684)
- ButterflyOnDesktop.exe (PID: 3052)
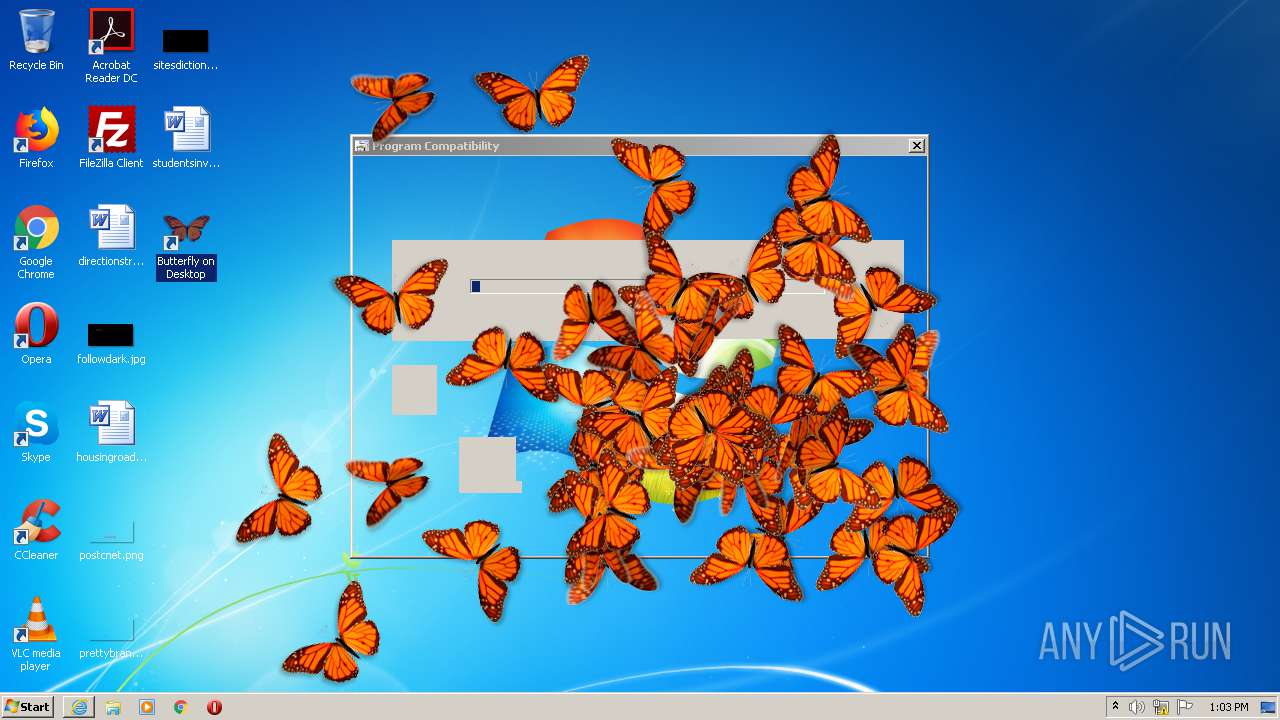
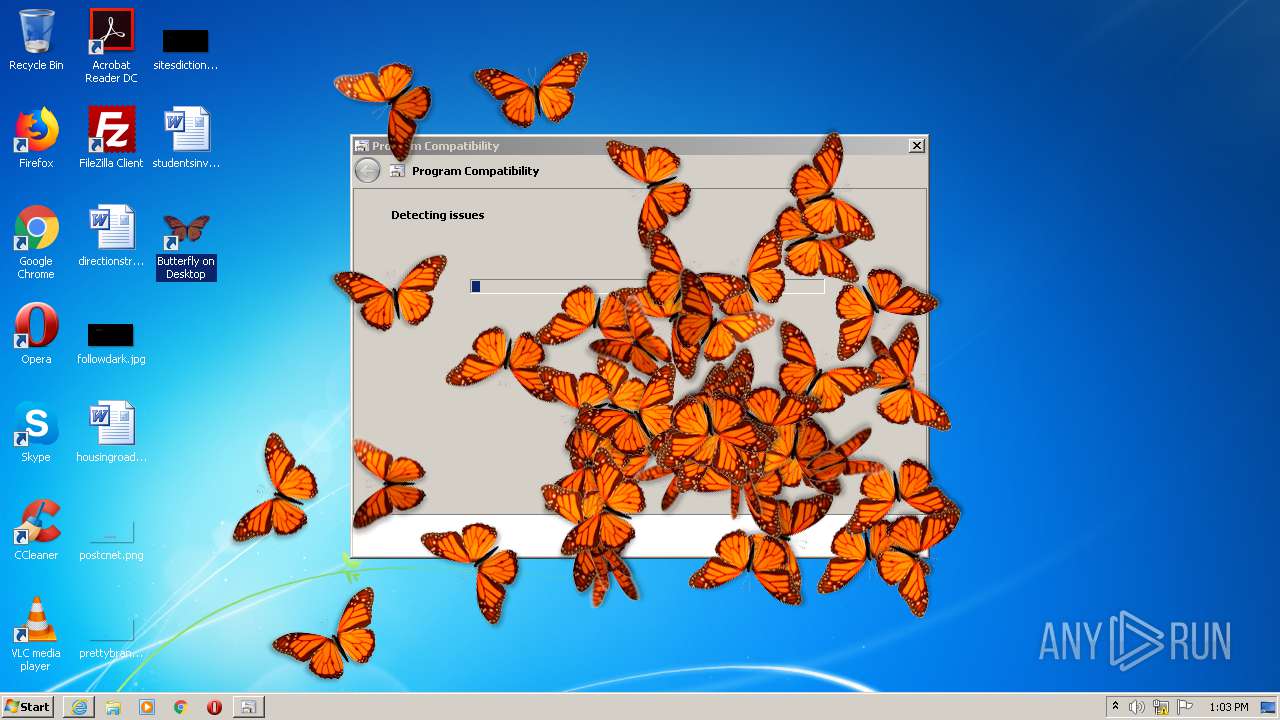
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2944)
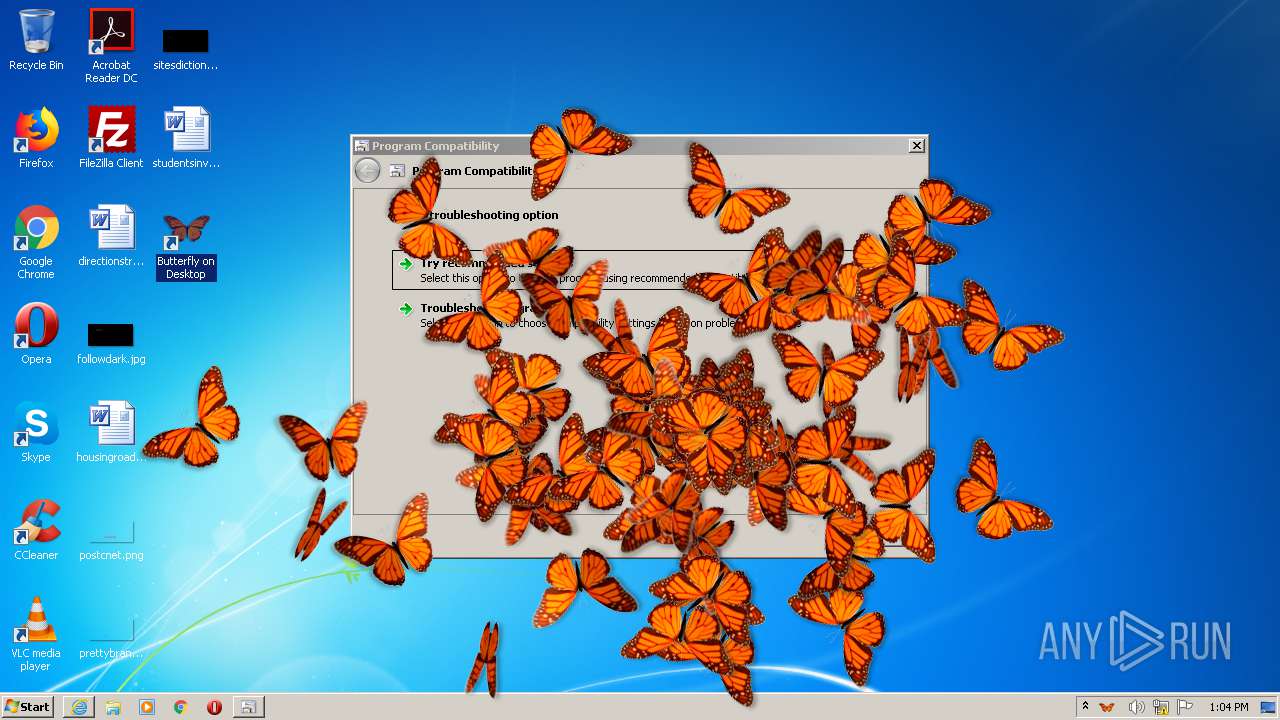
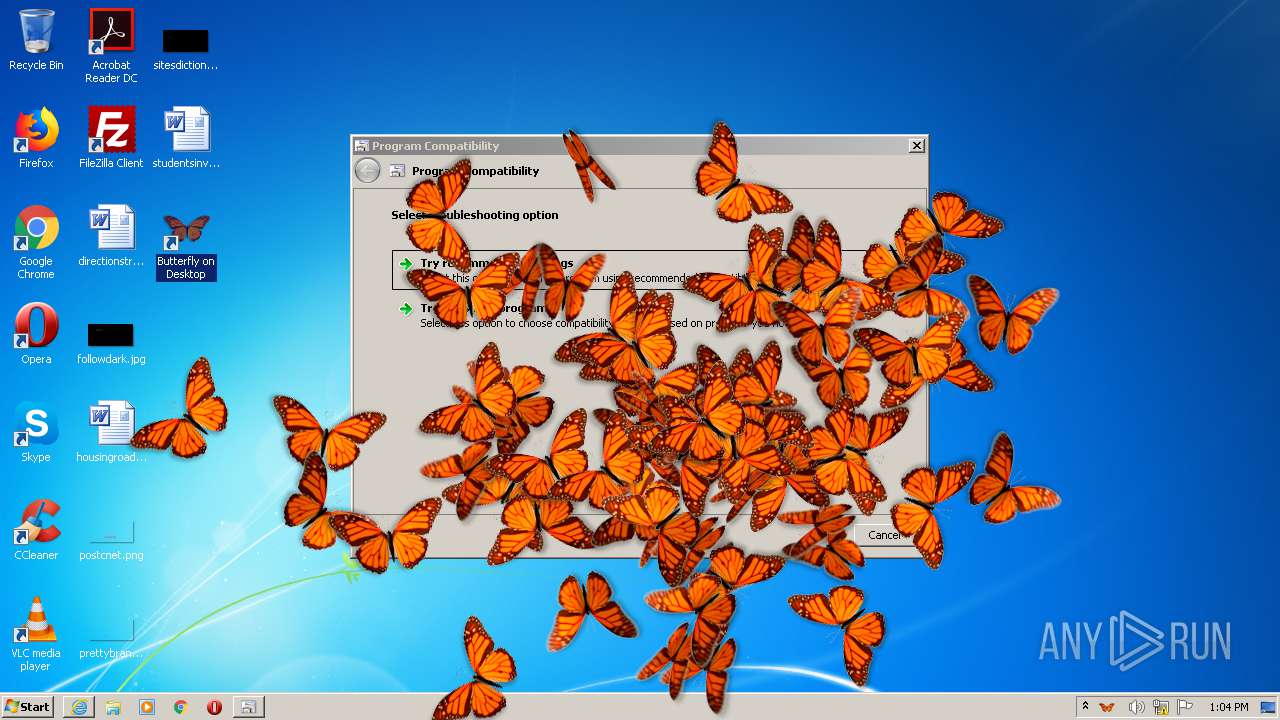
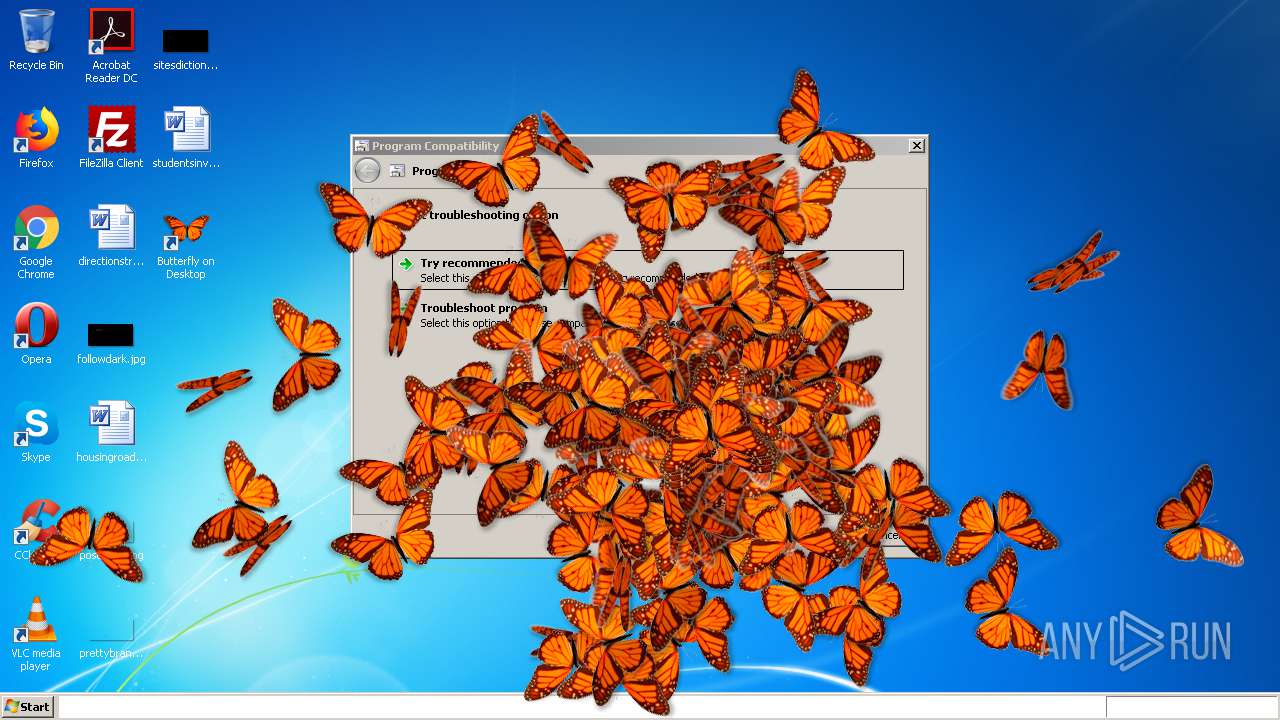
SUSPICIOUS
Executable content was dropped or overwritten
- butterflyondesktop.exe (PID: 556)
- butterflyondesktop.exe (PID: 2916)
- butterflyondesktop.tmp (PID: 3804)
- msdt.exe (PID: 1712)
Drops a file with too old compile date
- butterflyondesktop.exe (PID: 556)
- butterflyondesktop.exe (PID: 2916)
- butterflyondesktop.tmp (PID: 3804)
- msdt.exe (PID: 1712)
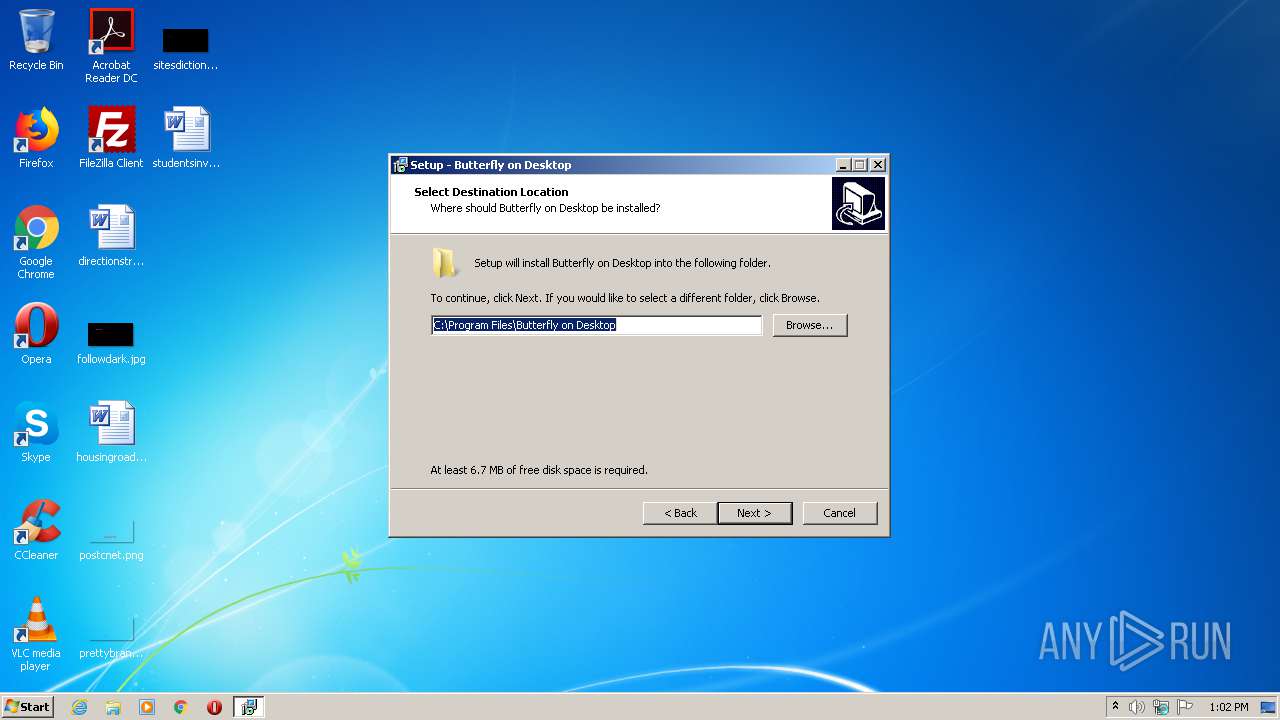
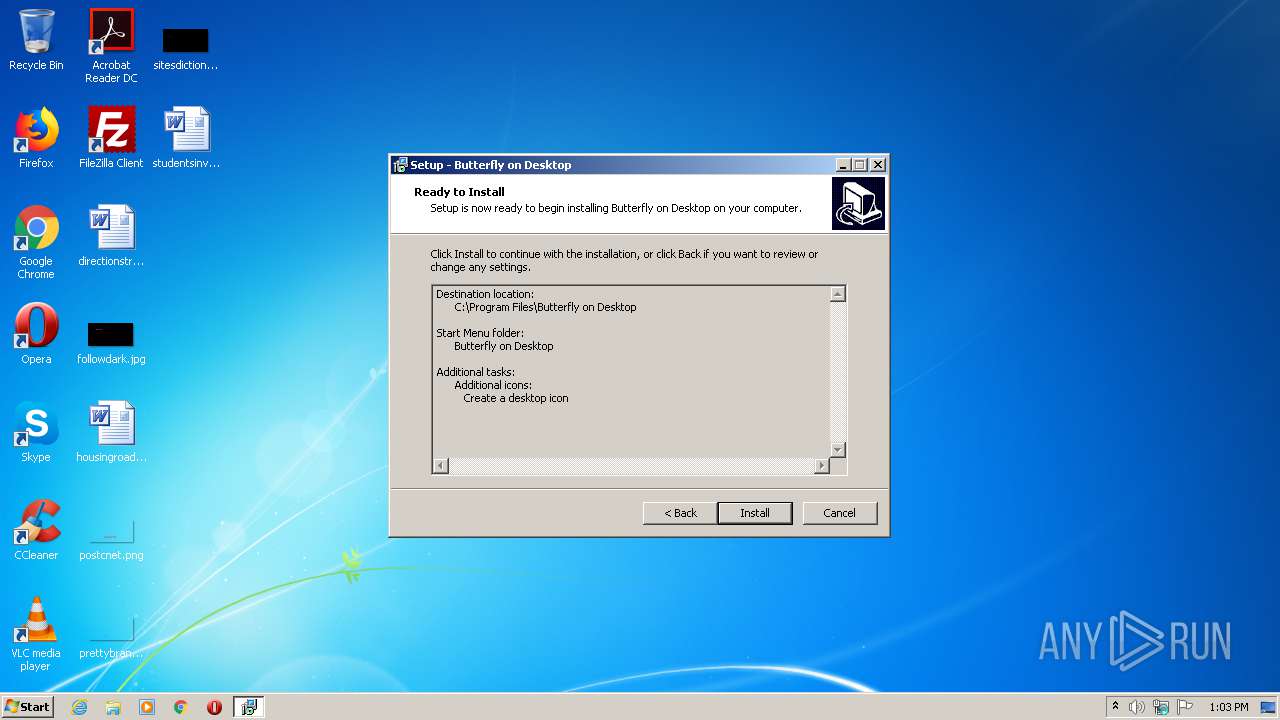
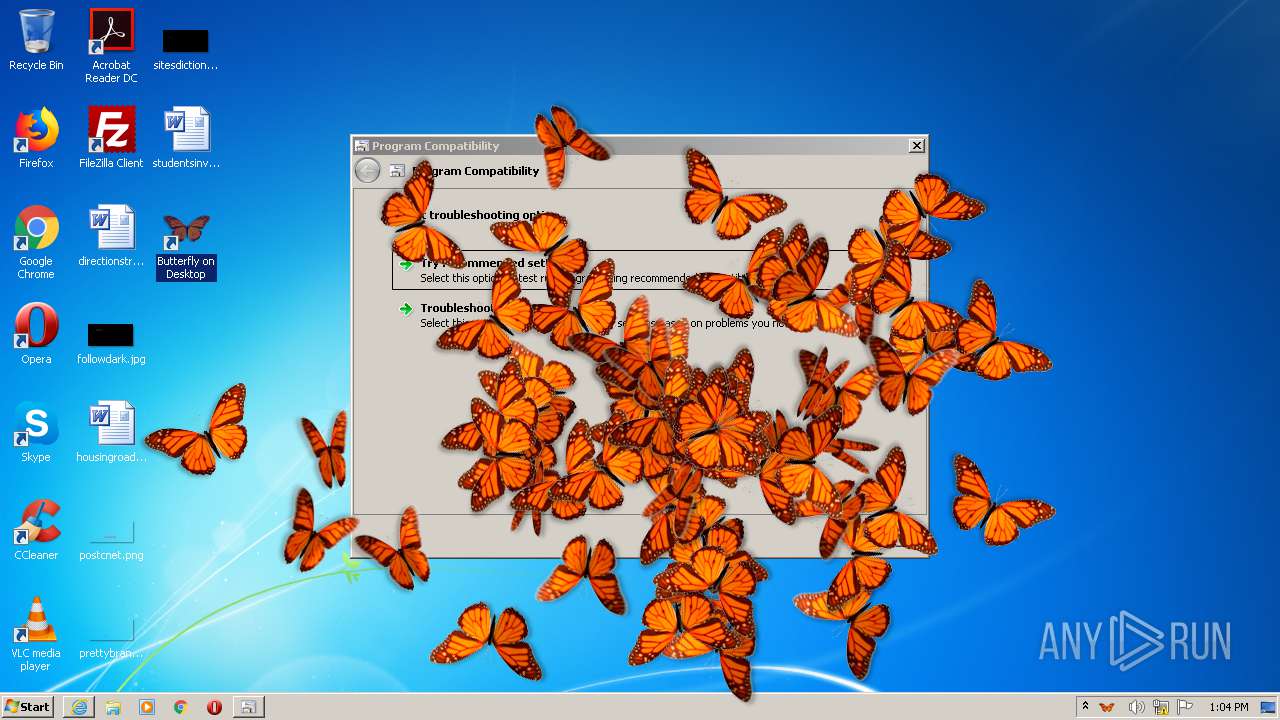
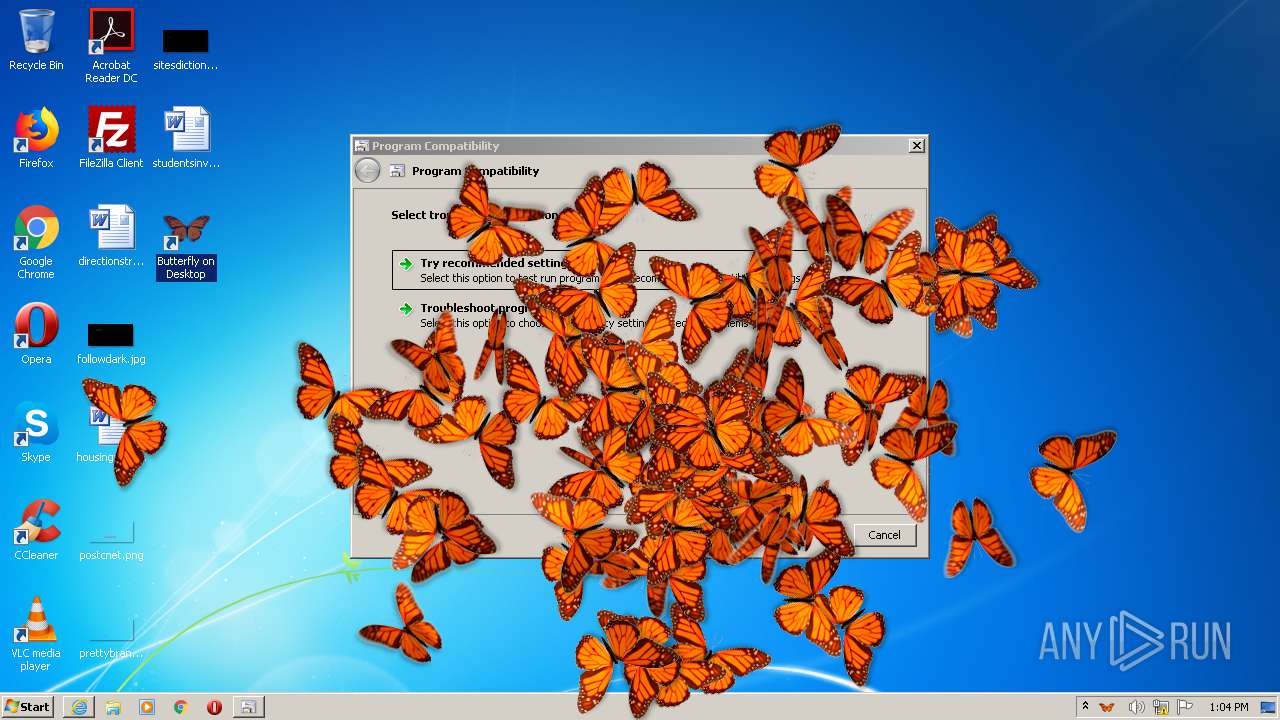
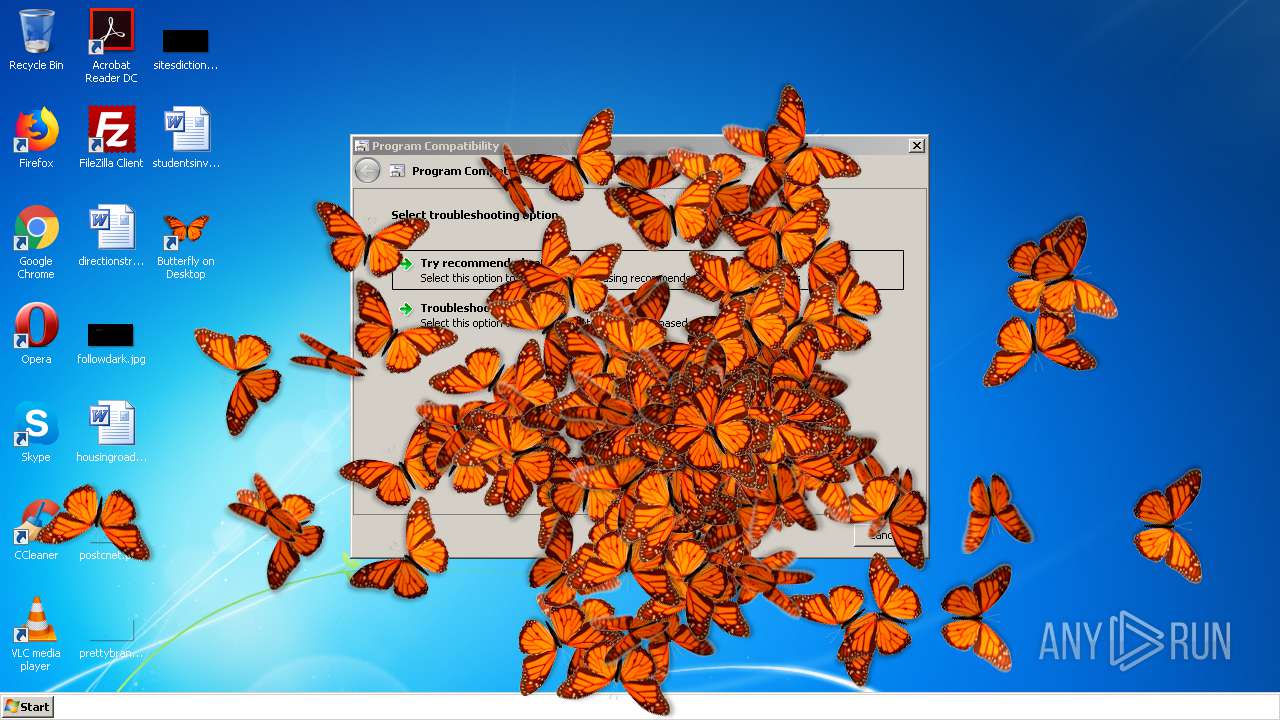
Creates a directory in Program Files
- butterflyondesktop.tmp (PID: 3804)
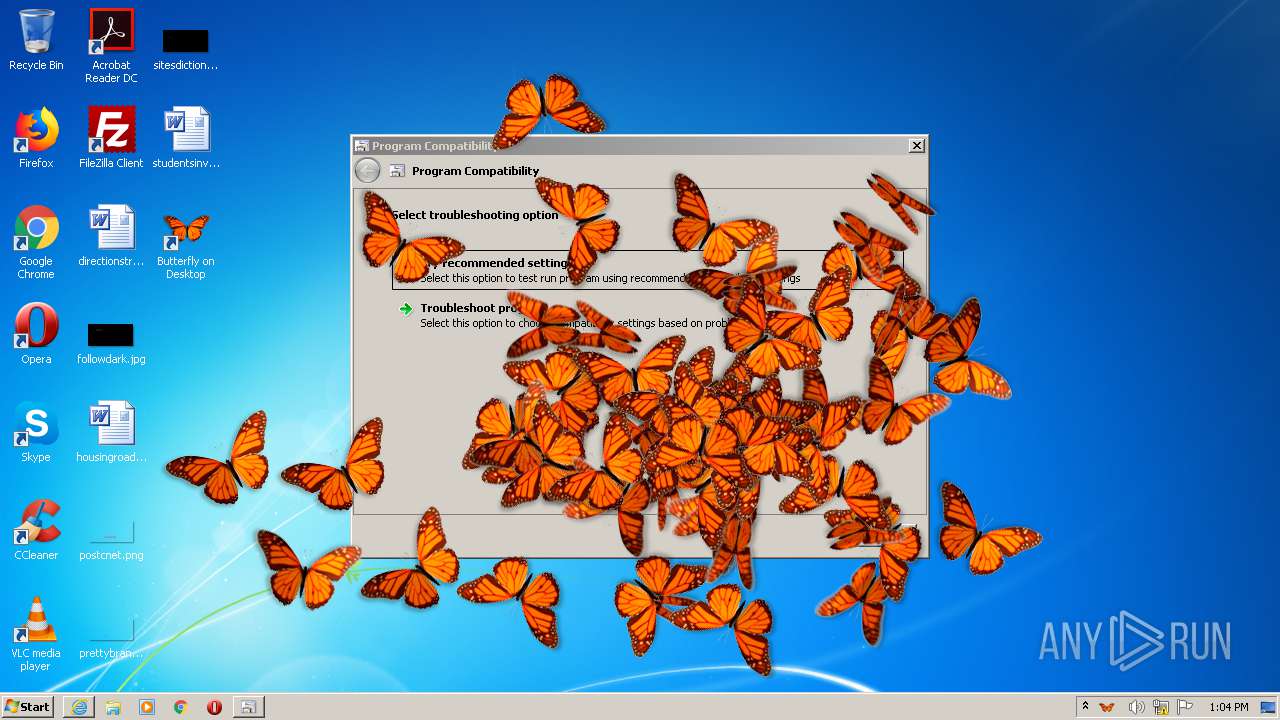
Drops a file that was compiled in debug mode
- butterflyondesktop.tmp (PID: 3804)
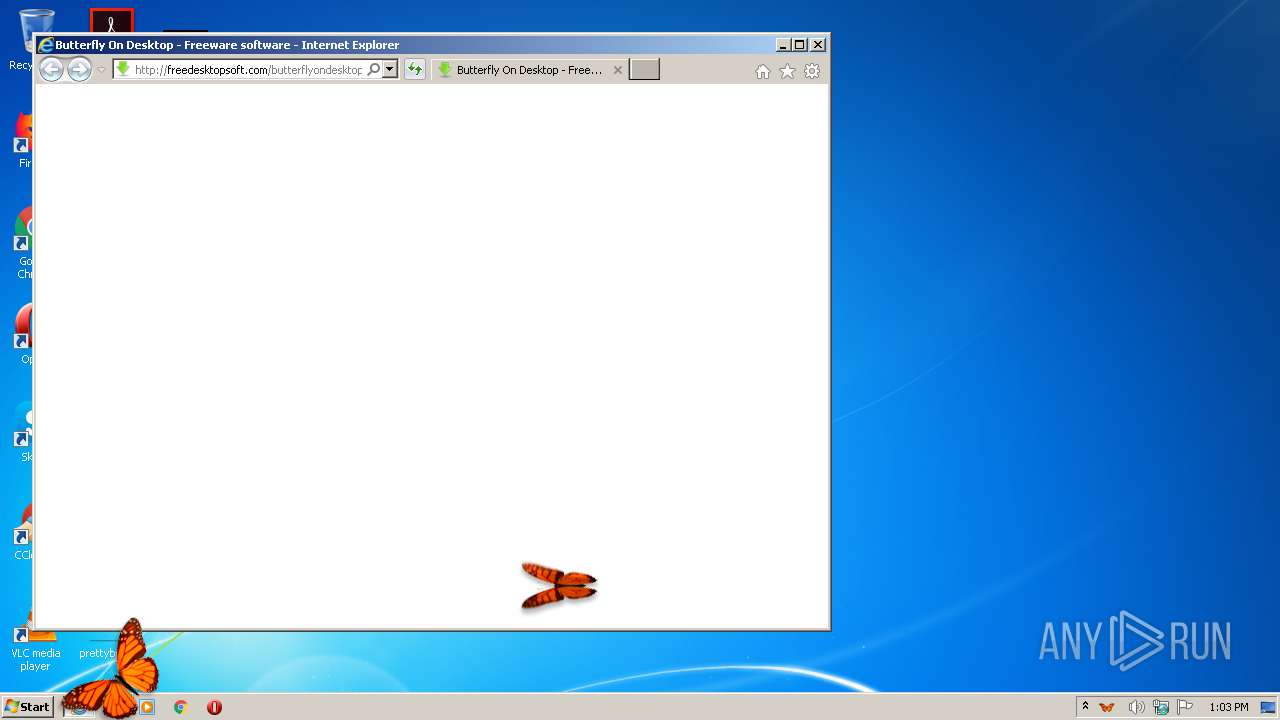
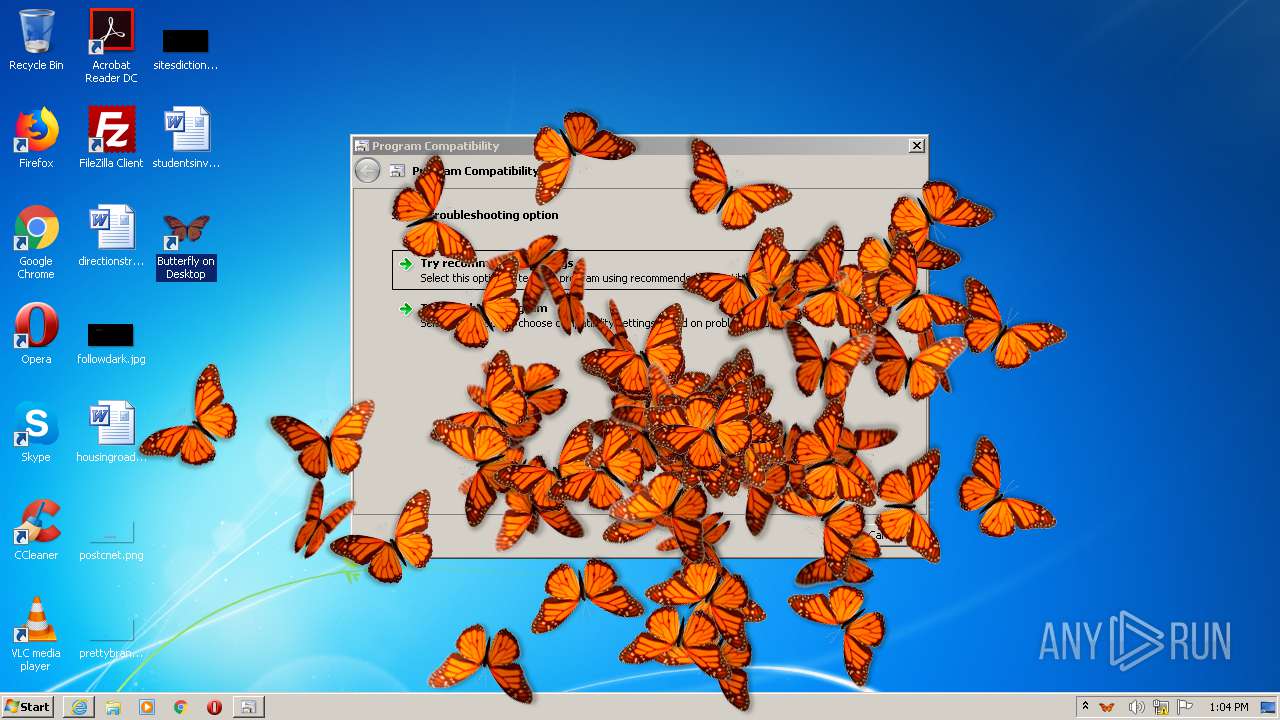
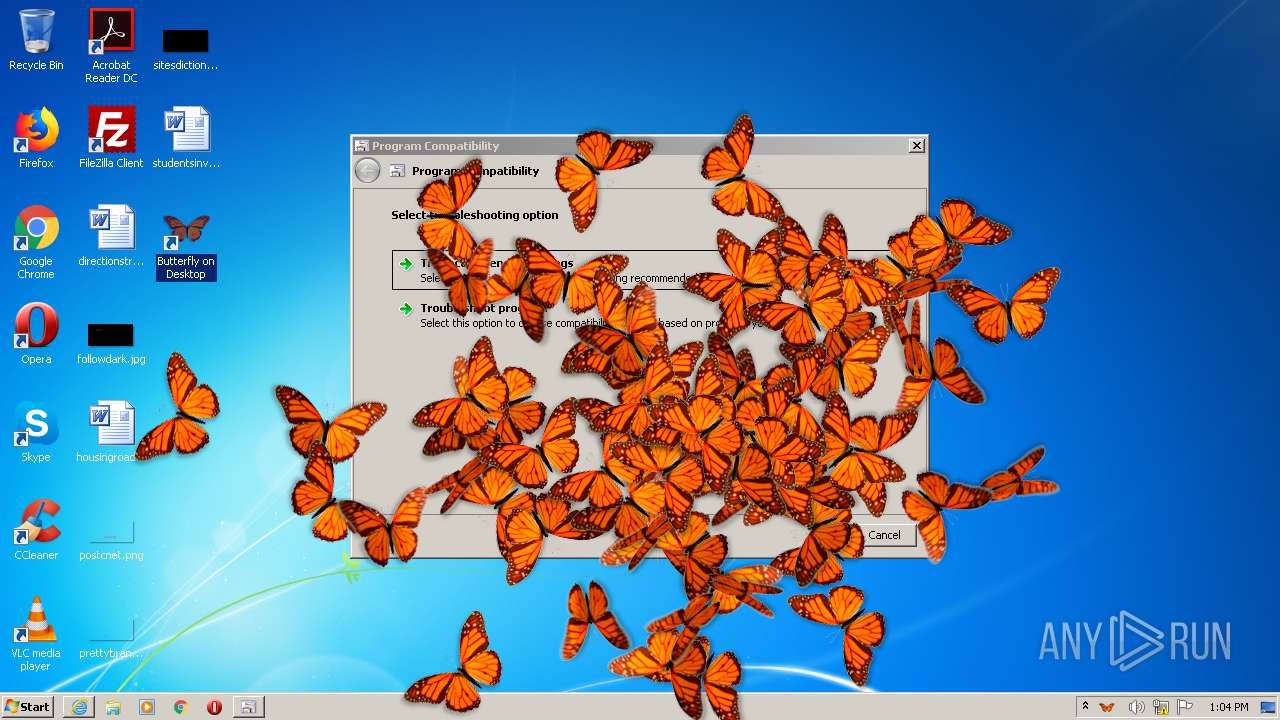
Starts Internet Explorer
- butterflyondesktop.tmp (PID: 3804)
Executed via COM
- sdiagnhost.exe (PID: 2944)
INFO
Application was dropped or rewritten from another process
- butterflyondesktop.tmp (PID: 3748)
- butterflyondesktop.tmp (PID: 3804)
Creates files in the program directory
- butterflyondesktop.tmp (PID: 3804)
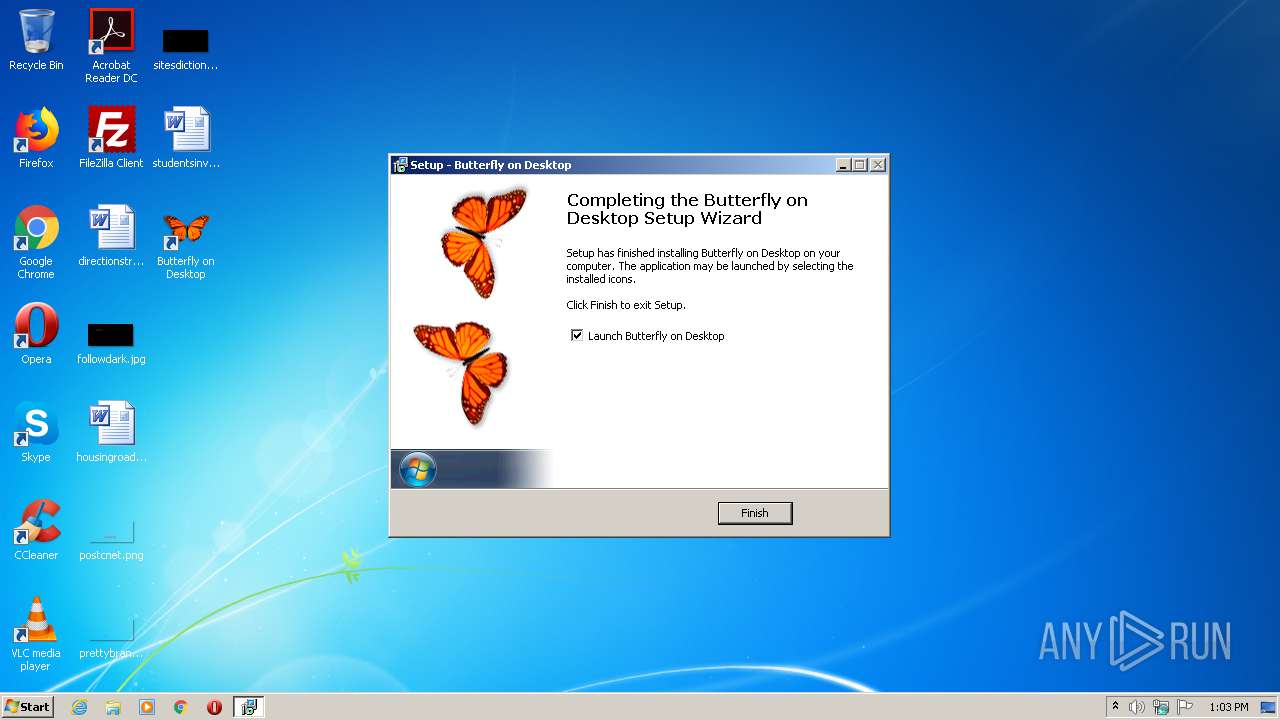
Creates a software uninstall entry
- butterflyondesktop.tmp (PID: 3804)
Application launched itself
- iexplore.exe (PID: 3068)
Changes internet zones settings
- iexplore.exe (PID: 3068)
Reads settings of System Certificates
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3068)
Reads internet explorer settings
- iexplore.exe (PID: 3768)
Creates files in the user directory
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3068)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3068)
Manual execution by user
- ButterflyOnDesktop.exe (PID: 760)
- ButterflyOnDesktop.exe (PID: 4012)
- ButterflyOnDesktop.exe (PID: 624)
- ButterflyOnDesktop.exe (PID: 2492)
- ButterflyOnDesktop.exe (PID: 2132)
- ButterflyOnDesktop.exe (PID: 3688)
- ButterflyOnDesktop.exe (PID: 2156)
- ButterflyOnDesktop.exe (PID: 2260)
- ButterflyOnDesktop.exe (PID: 2956)
- ButterflyOnDesktop.exe (PID: 1736)
- ButterflyOnDesktop.exe (PID: 1160)
- ButterflyOnDesktop.exe (PID: 3968)
- ButterflyOnDesktop.exe (PID: 3836)
- ButterflyOnDesktop.exe (PID: 2424)
- ButterflyOnDesktop.exe (PID: 2212)
- ButterflyOnDesktop.exe (PID: 1660)
- ButterflyOnDesktop.exe (PID: 3208)
- ButterflyOnDesktop.exe (PID: 2360)
- ButterflyOnDesktop.exe (PID: 3676)
- ButterflyOnDesktop.exe (PID: 1556)
- ButterflyOnDesktop.exe (PID: 3236)
- ButterflyOnDesktop.exe (PID: 1996)
- ButterflyOnDesktop.exe (PID: 3076)
- ButterflyOnDesktop.exe (PID: 1936)
- ButterflyOnDesktop.exe (PID: 1532)
- ButterflyOnDesktop.exe (PID: 1800)
- ButterflyOnDesktop.exe (PID: 3860)
- ButterflyOnDesktop.exe (PID: 1860)
- ButterflyOnDesktop.exe (PID: 3168)
- pcwrun.exe (PID: 3736)
- ButterflyOnDesktop.exe (PID: 2948)
- ButterflyOnDesktop.exe (PID: 3876)
- ButterflyOnDesktop.exe (PID: 3364)
- ButterflyOnDesktop.exe (PID: 1516)
- ButterflyOnDesktop.exe (PID: 1756)
- ButterflyOnDesktop.exe (PID: 2896)
- ButterflyOnDesktop.exe (PID: 4072)
- ButterflyOnDesktop.exe (PID: 2640)
- ButterflyOnDesktop.exe (PID: 3384)
- ButterflyOnDesktop.exe (PID: 2344)
- ButterflyOnDesktop.exe (PID: 2348)
- ButterflyOnDesktop.exe (PID: 3496)
- ButterflyOnDesktop.exe (PID: 2664)
- ButterflyOnDesktop.exe (PID: 3888)
- ButterflyOnDesktop.exe (PID: 3032)
- ButterflyOnDesktop.exe (PID: 2632)
- ButterflyOnDesktop.exe (PID: 2416)
- ButterflyOnDesktop.exe (PID: 1868)
- ButterflyOnDesktop.exe (PID: 2368)
- ButterflyOnDesktop.exe (PID: 3608)
- ButterflyOnDesktop.exe (PID: 2316)
- ButterflyOnDesktop.exe (PID: 3832)
- ButterflyOnDesktop.exe (PID: 2648)
- ButterflyOnDesktop.exe (PID: 2788)
- ButterflyOnDesktop.exe (PID: 768)
- ButterflyOnDesktop.exe (PID: 764)
- ButterflyOnDesktop.exe (PID: 1672)
- ButterflyOnDesktop.exe (PID: 3564)
- ButterflyOnDesktop.exe (PID: 3920)
- ButterflyOnDesktop.exe (PID: 4092)
- ButterflyOnDesktop.exe (PID: 2332)
- ButterflyOnDesktop.exe (PID: 3684)
- ButterflyOnDesktop.exe (PID: 2880)
- ButterflyOnDesktop.exe (PID: 3256)
- ButterflyOnDesktop.exe (PID: 3884)
- ButterflyOnDesktop.exe (PID: 1780)
- ButterflyOnDesktop.exe (PID: 3988)
- ButterflyOnDesktop.exe (PID: 2992)
- ButterflyOnDesktop.exe (PID: 2044)
- ButterflyOnDesktop.exe (PID: 3456)
- ButterflyOnDesktop.exe (PID: 3192)
- ButterflyOnDesktop.exe (PID: 1940)
- ButterflyOnDesktop.exe (PID: 3872)
- ButterflyOnDesktop.exe (PID: 3052)
Changes settings of System certificates
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Drive Software Company |
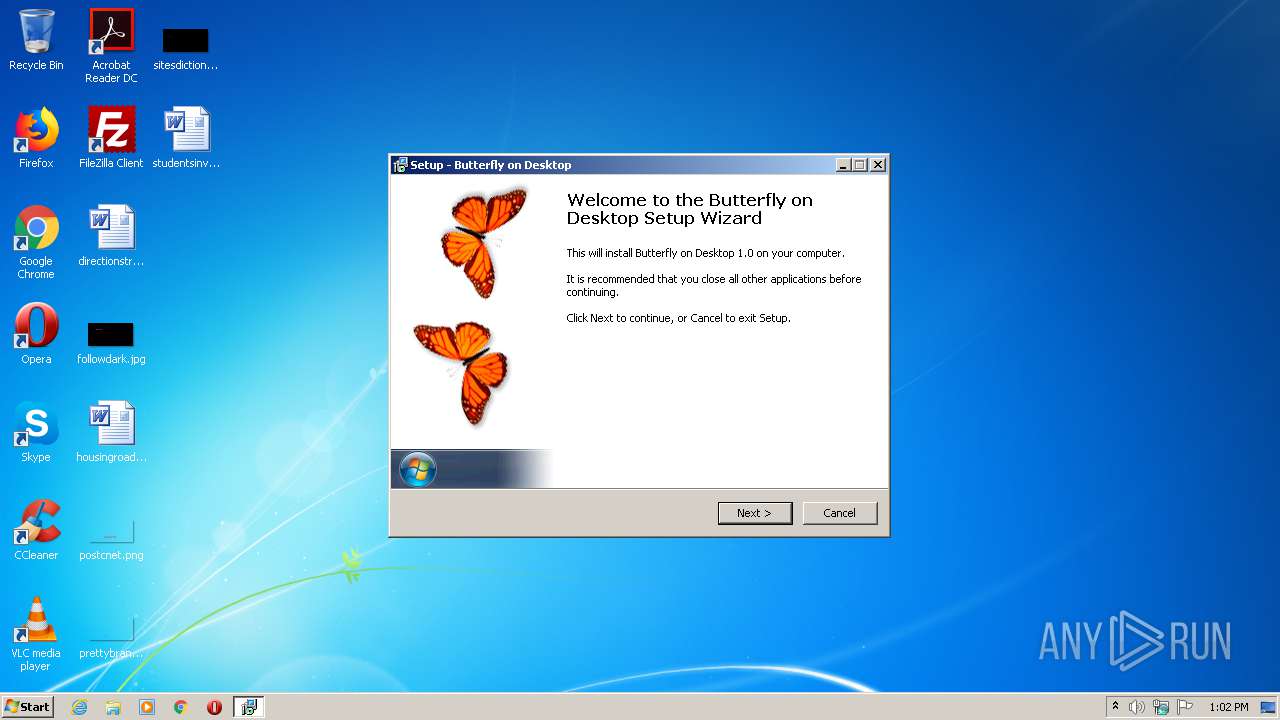
| FileDescription: | Butterfly on Desktop Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Butterfly on Desktop |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Drive Software Company |
| FileDescription: | Butterfly on Desktop Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Butterfly on Desktop |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009364 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56223 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75348 |
BSS | 0x0000C000 | 0x00000E4C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.46081 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
132
Monitored processes
89
Malicious processes
42
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\AppData\Local\Temp\butterflyondesktop.exe" | C:\Users\admin\AppData\Local\Temp\butterflyondesktop.exe | explorer.exe | ||||||||||||
User: admin Company: Drive Software Company Integrity Level: MEDIUM Description: Butterfly on Desktop Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 624 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1148 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\oukuosik.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | butterflyondesktop.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe" | C:\Program Files\Butterfly on Desktop\ButterflyOnDesktop.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 779
Read events
1 613
Write events
165
Delete events
1
Modification events
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ButterflyOnDesktop |
Value: | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.4.2 (a) | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Butterfly on Desktop | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Butterfly on Desktop\ | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Butterfly on Desktop | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: butterflyondesktop | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: eng | |||
| (PID) Process: | (3804) butterflyondesktop.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Butterfly on Desktop_is1 |
| Operation: | write | Name: | DisplayName |
Value: Butterfly on Desktop 1.0 | |||
Executable files
8
Suspicious files
23
Text files
48
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3804 | butterflyondesktop.tmp | C:\Program Files\Butterfly on Desktop\is-V6570.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\Program Files\Butterfly on Desktop\is-6R16L.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\Program Files\Butterfly on Desktop\is-0G5S9.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\Program Files\Butterfly on Desktop\is-5P0SI.tmp | — | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Butterfly on Desktop\Uninstall Butterfly on Desktop.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\Program Files\Butterfly on Desktop\unins000.dat | dat | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Butterfly on Desktop\Butterfly on Desktop.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3768 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\CZ4M3VO4.txt | — | |
MD5:— | SHA256:— | |||
| 3804 | butterflyondesktop.tmp | C:\Users\admin\Desktop\Butterfly on Desktop.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3768 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\JJ0X5F3Q.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3768 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3768 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFHpLXWzg0SiAwAAAADLk4Y%3D | US | der | 471 b | whitelisted |
3768 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAN37dz6%2BL40uiM8fCuaMX8%3D | US | der | 471 b | whitelisted |
3768 | iexplore.exe | GET | 200 | 157.240.20.19:80 | http://connect.facebook.net/en_US/all.js | US | text | 1.74 Kb | whitelisted |
3768 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFHpLXWzg0SiAwAAAADLk4Y%3D | US | der | 471 b | whitelisted |
3768 | iexplore.exe | GET | 200 | 78.46.117.95:80 | http://freedesktopsoft.com/images/menubackgroundside2.jpg | DE | image | 1.35 Kb | suspicious |
3768 | iexplore.exe | GET | 200 | 78.46.117.95:80 | http://freedesktopsoft.com/slider/slider.css | DE | text | 6.40 Kb | suspicious |
3768 | iexplore.exe | GET | 200 | 78.46.117.95:80 | http://freedesktopsoft.com/main.css | DE | text | 4.15 Kb | suspicious |
3768 | iexplore.exe | GET | 200 | 78.46.117.95:80 | http://freedesktopsoft.com/images/banner3.jpg | DE | image | 41.3 Kb | suspicious |
3768 | iexplore.exe | GET | 200 | 78.46.117.95:80 | http://freedesktopsoft.com/button.css | DE | text | 2.71 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3768 | iexplore.exe | 216.58.212.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3768 | iexplore.exe | 78.46.117.95:80 | freedesktopsoft.com | Hetzner Online GmbH | DE | suspicious |
3768 | iexplore.exe | 157.240.20.19:80 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
3768 | iexplore.exe | 142.250.185.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3768 | iexplore.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
1048 | svchost.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3068 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3068 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3068 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3768 | iexplore.exe | 142.250.185.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
freedesktopsoft.com |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|