| File name: | Wahkah's Menyoo-360-16-01-1549155772.exe |
| Full analysis: | https://app.any.run/tasks/c1b22c4c-3df3-45a9-90d3-69efaba5b209 |
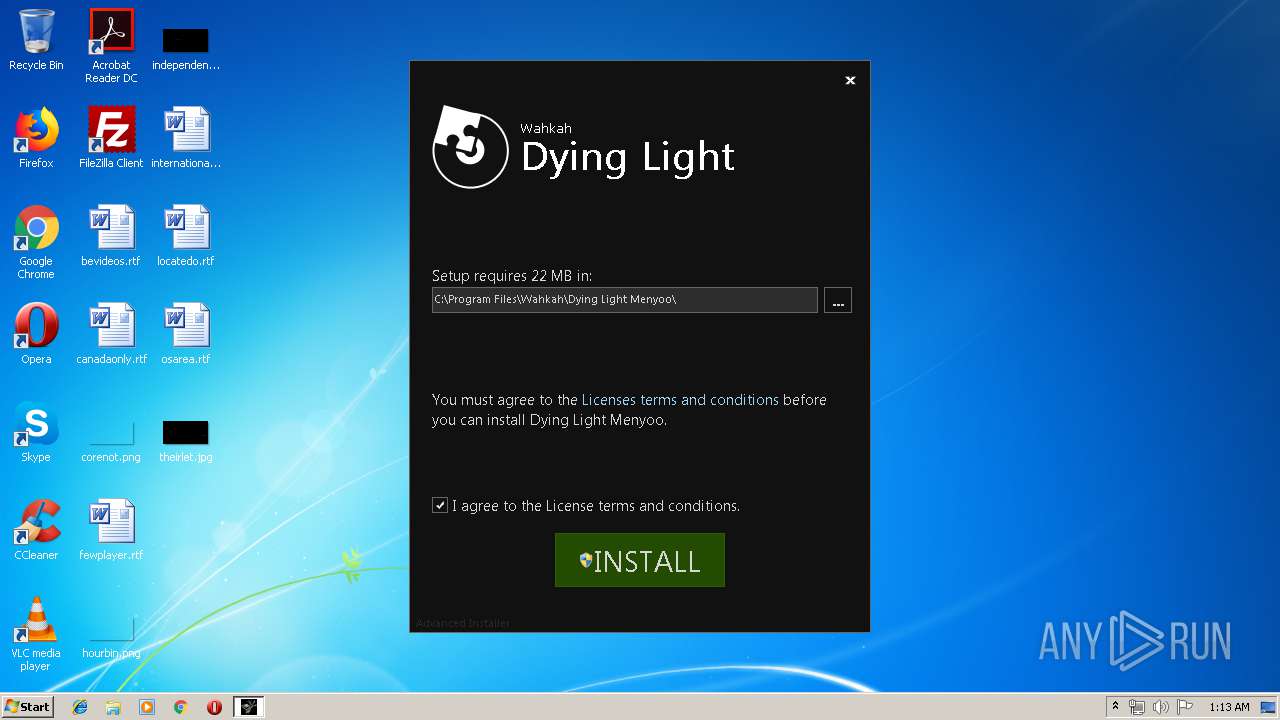
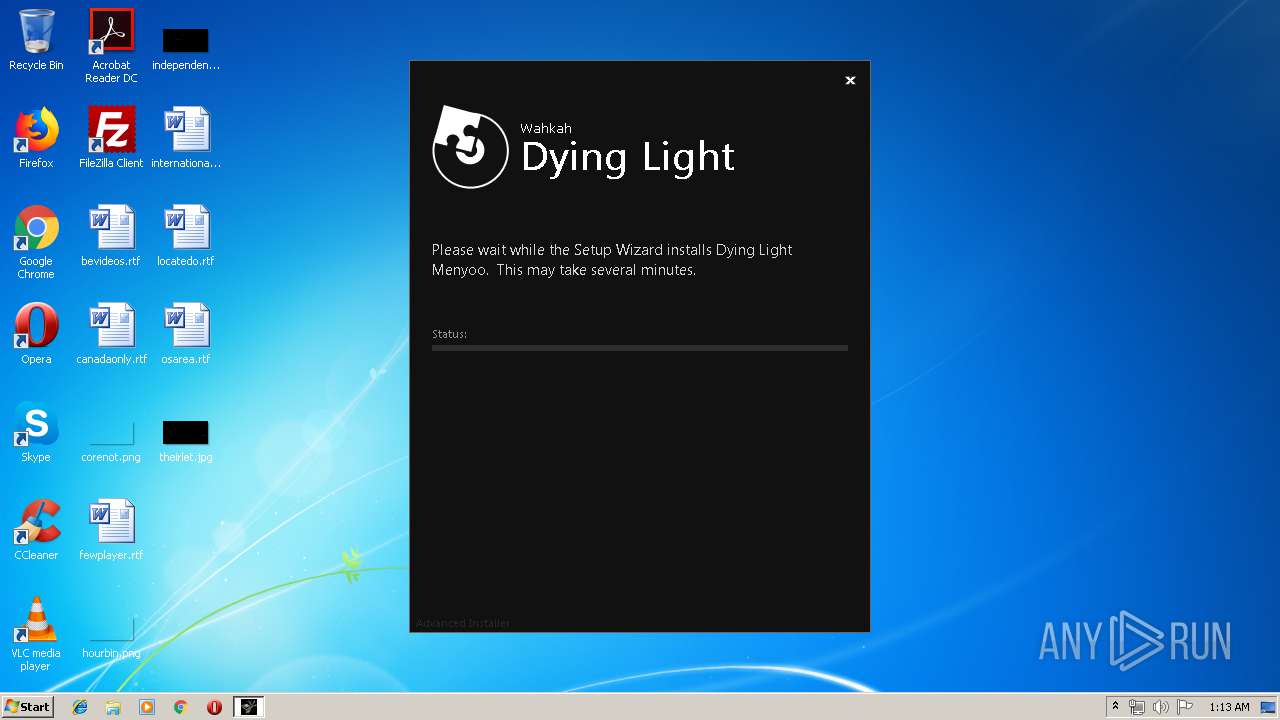
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2019, 01:13:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E90134343F3924C154CFA5E4A391AC51 |
| SHA1: | 4C74B6ECB451E9D43AA6FBB7F8A9EB602E98AE49 |
| SHA256: | 464195DE18CBD8C879A3895EF10B32001DF5C33D4C945D1F7DA2ADEADC44083F |
| SSDEEP: | 196608:IEOtA7FUEOtA7F7R8BY8z4F4lbM1uy/gDhxMzdDwM:IEOtASEOtAoBYW4ClbM1uy/uxIDwM |
MALICIOUS
Loads the Task Scheduler DLL interface
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2872)
SUSPICIOUS
Executable content was dropped or overwritten
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2872)
- msiexec.exe (PID: 1420)
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2000)
Creates files in the user directory
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2872)
Application launched itself
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2872)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 1968)
Creates files in the Windows directory
- msiexec.exe (PID: 1420)
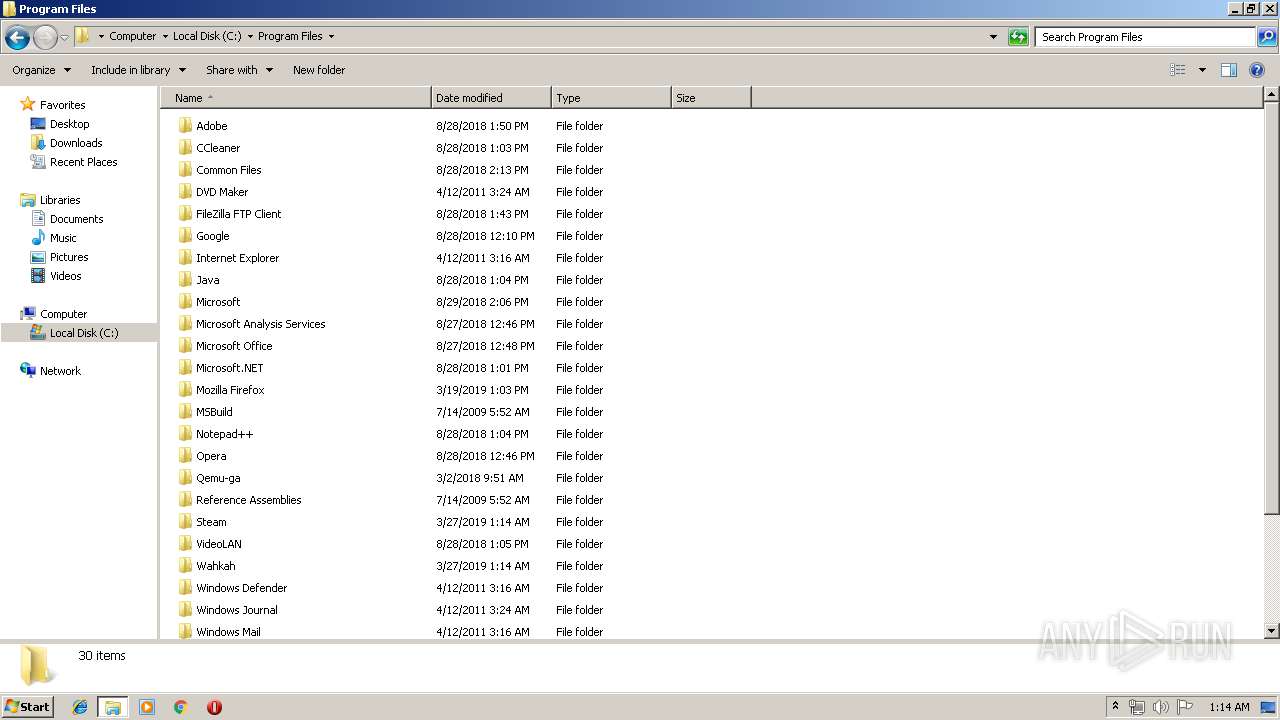
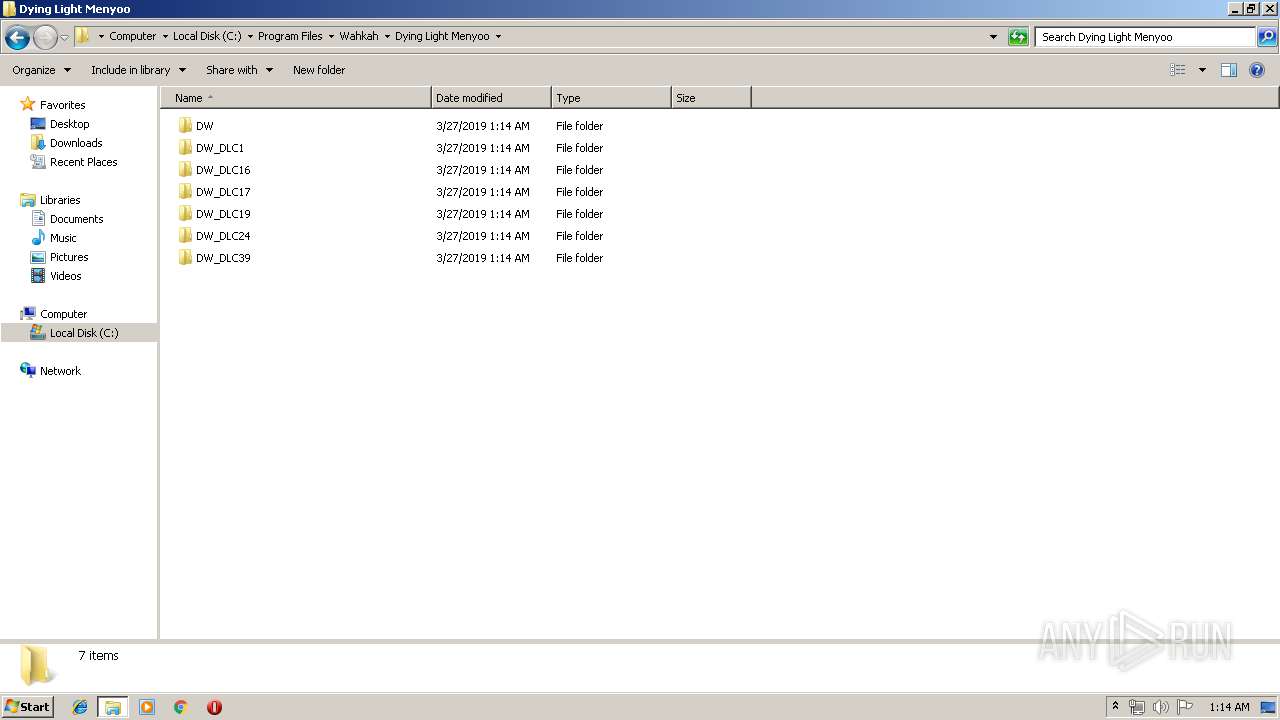
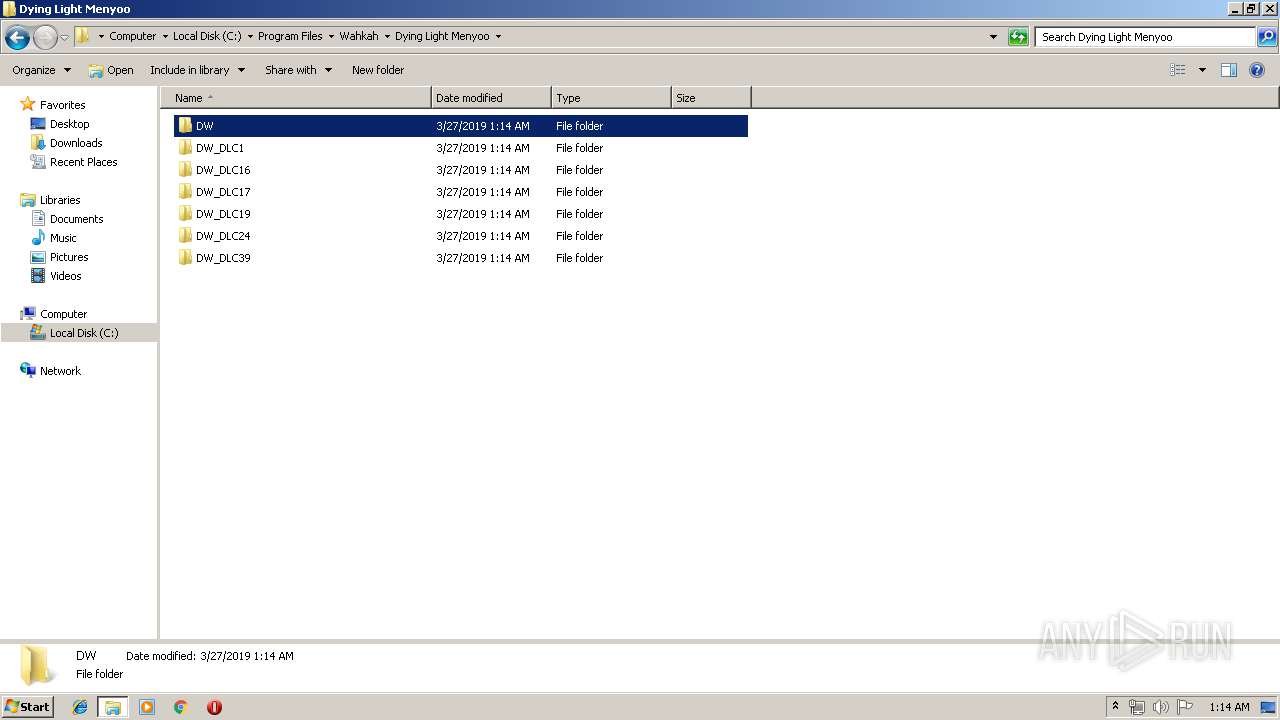
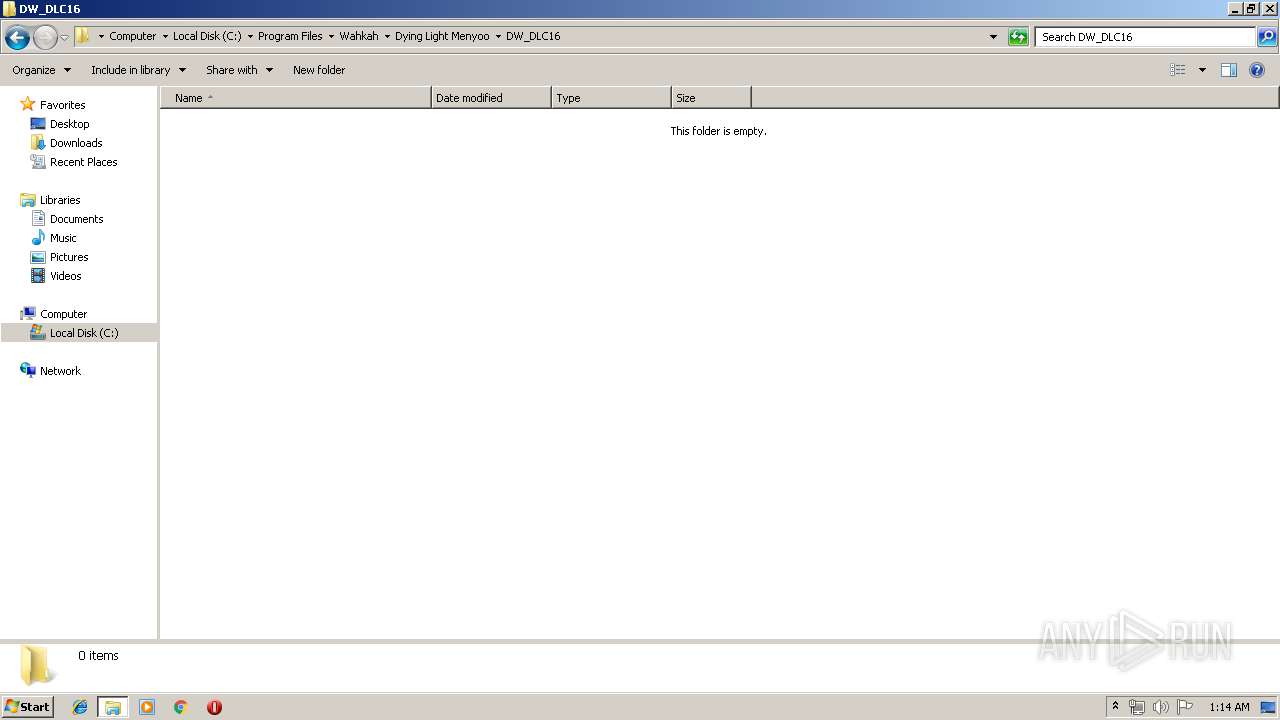
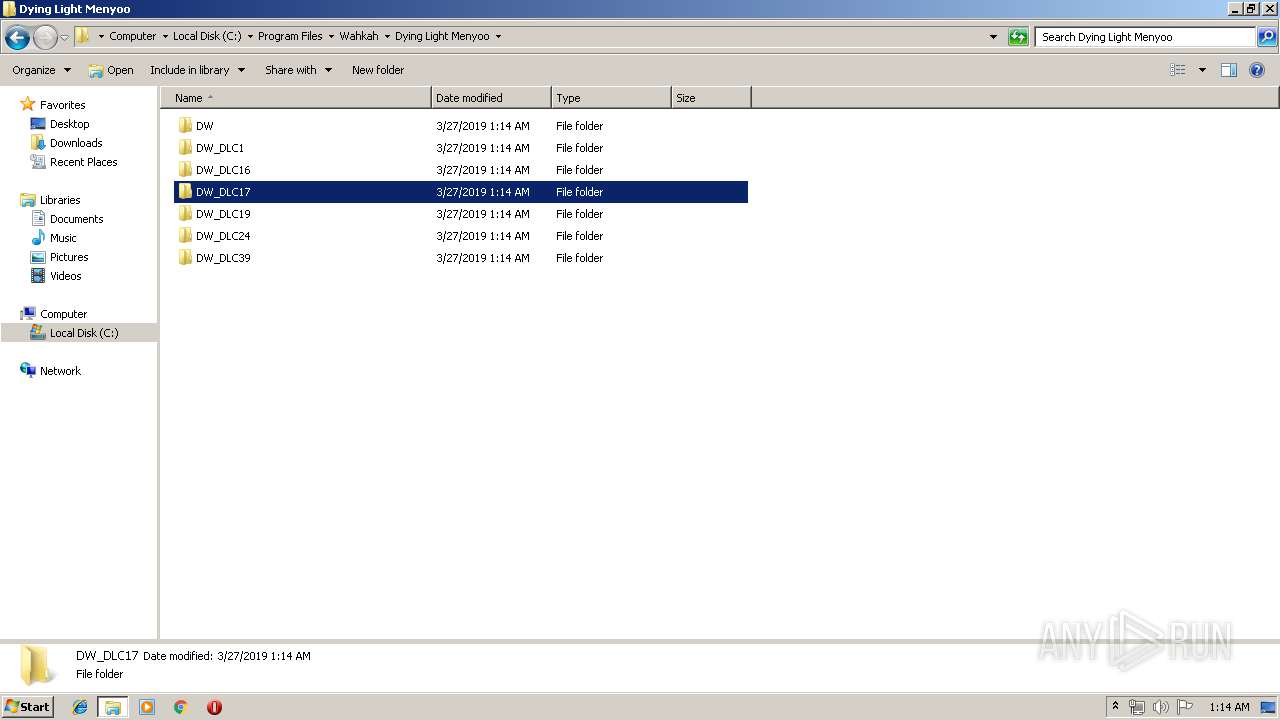
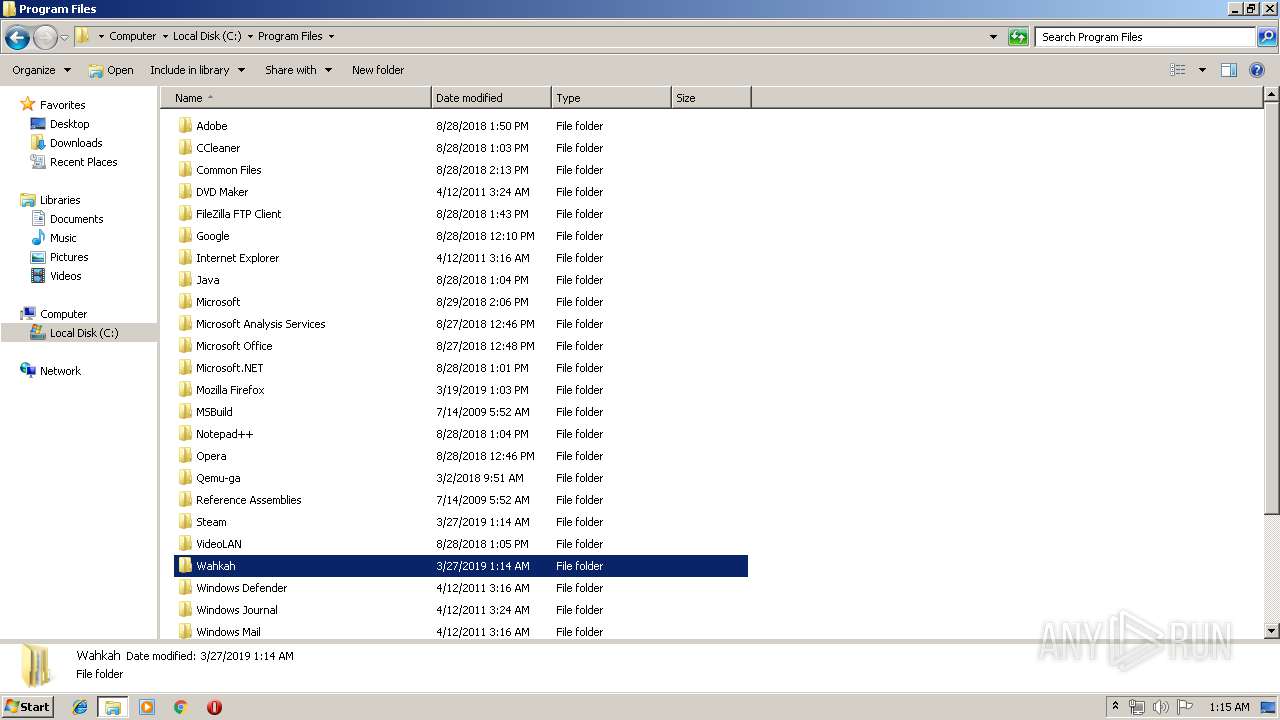
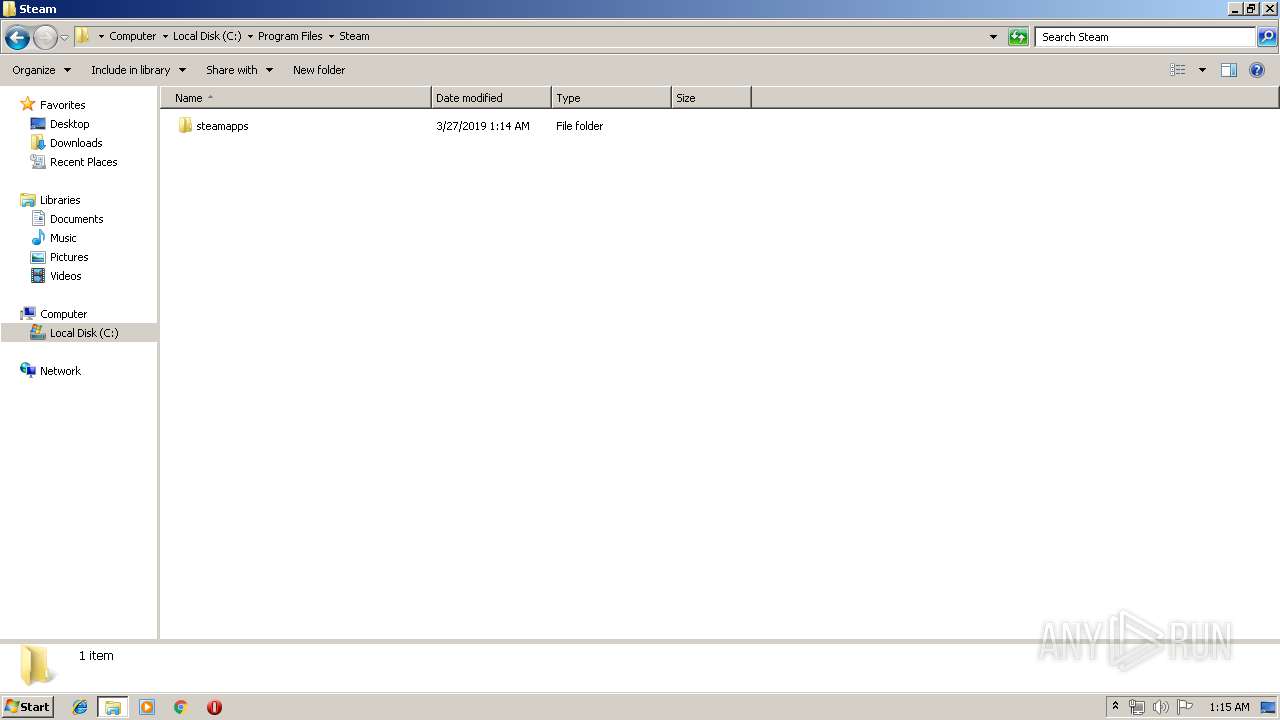
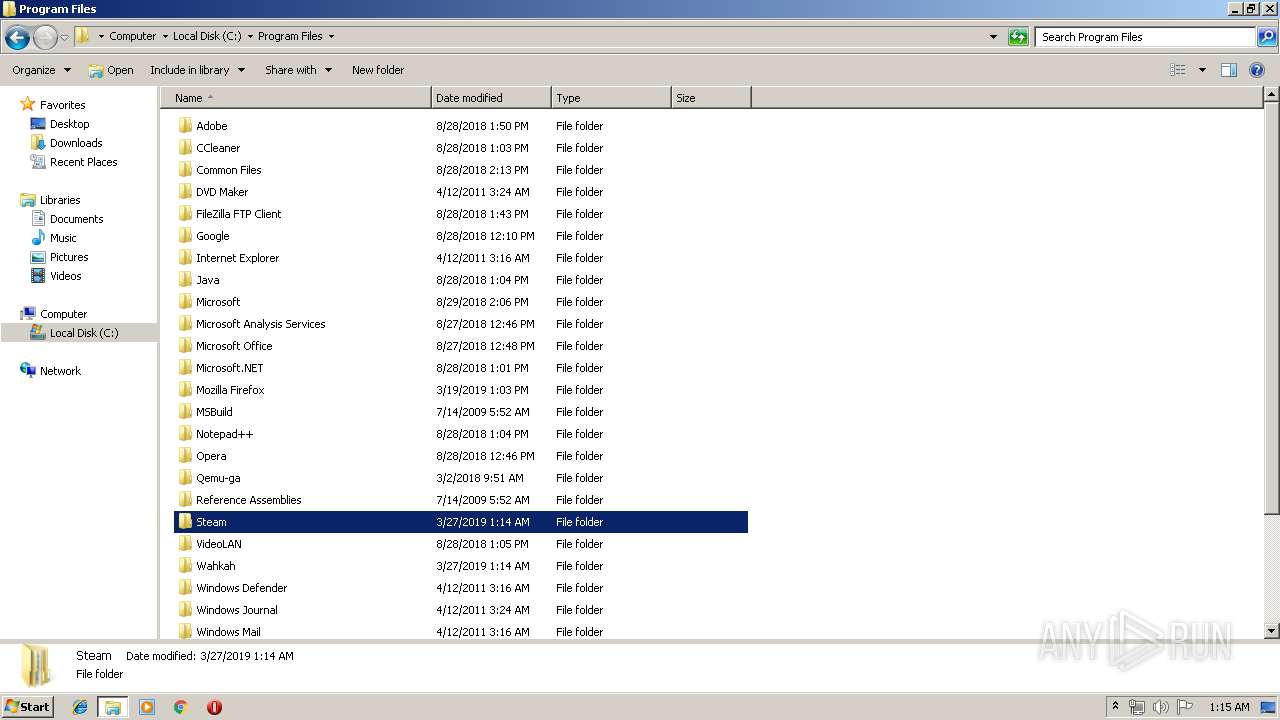
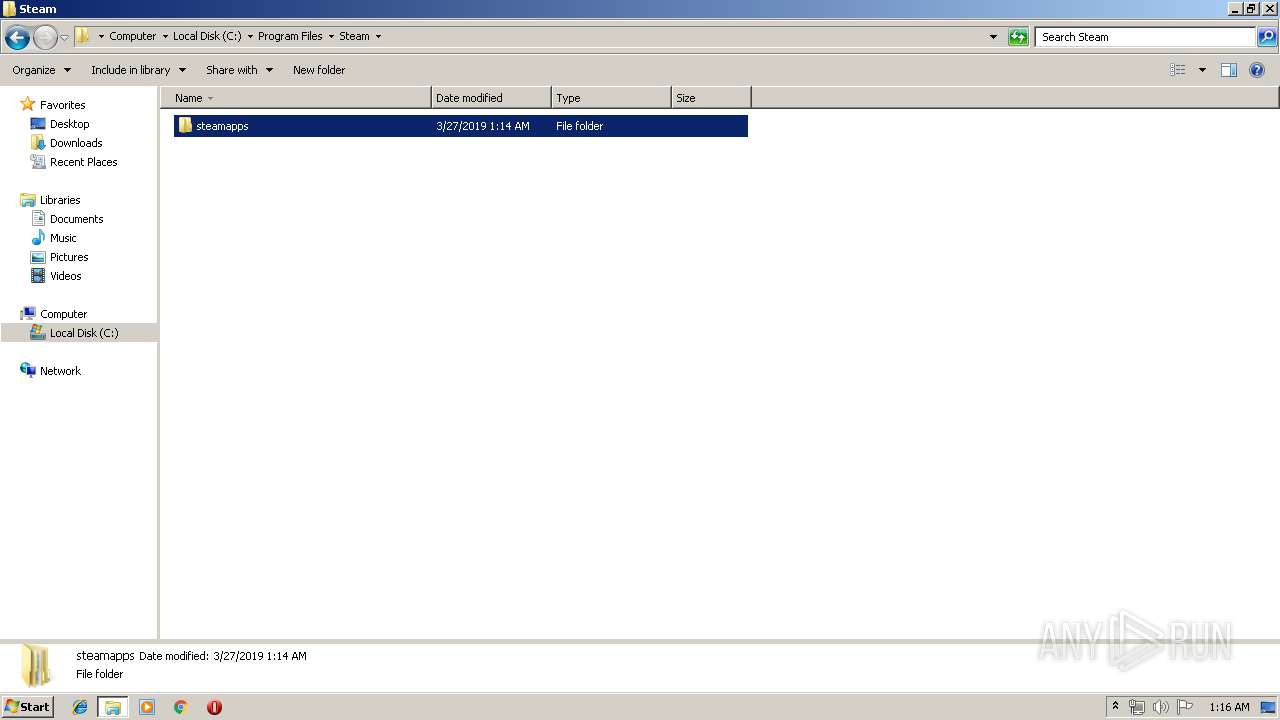
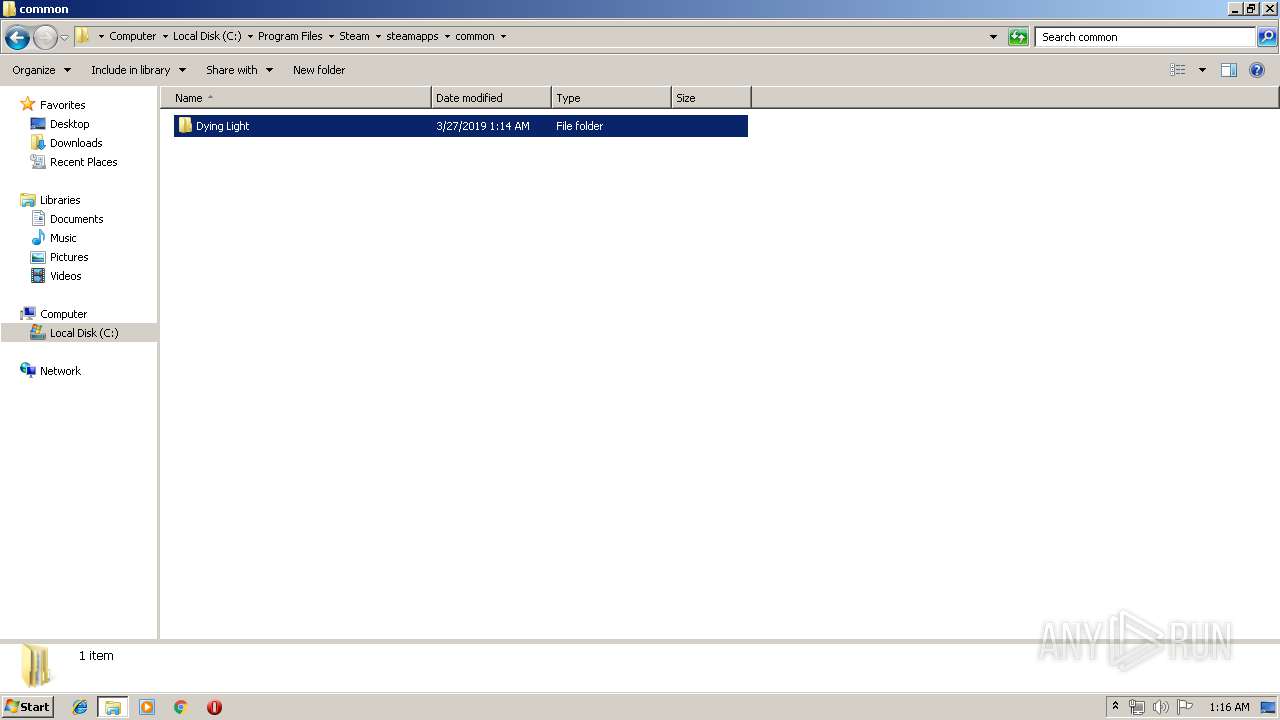
Creates files in the program directory
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2000)
Starts CMD.EXE for commands execution
- Wahkah's Menyoo-360-16-01-1549155772.exe (PID: 2872)
- cmd.exe (PID: 1968)
- cmd.exe (PID: 3324)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3324)
- cmd.exe (PID: 1968)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3208)
- MsiExec.exe (PID: 3332)
Searches for installed software
- msiexec.exe (PID: 1420)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2384)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2260)
Application launched itself
- msiexec.exe (PID: 1420)
Changes settings of System certificates
- DrvInst.exe (PID: 2260)
Creates a software uninstall entry
- msiexec.exe (PID: 1420)
Creates files in the program directory
- msiexec.exe (PID: 1420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:14 12:20:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1129472 |
| InitializedDataSize: | 661504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcc1f8 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
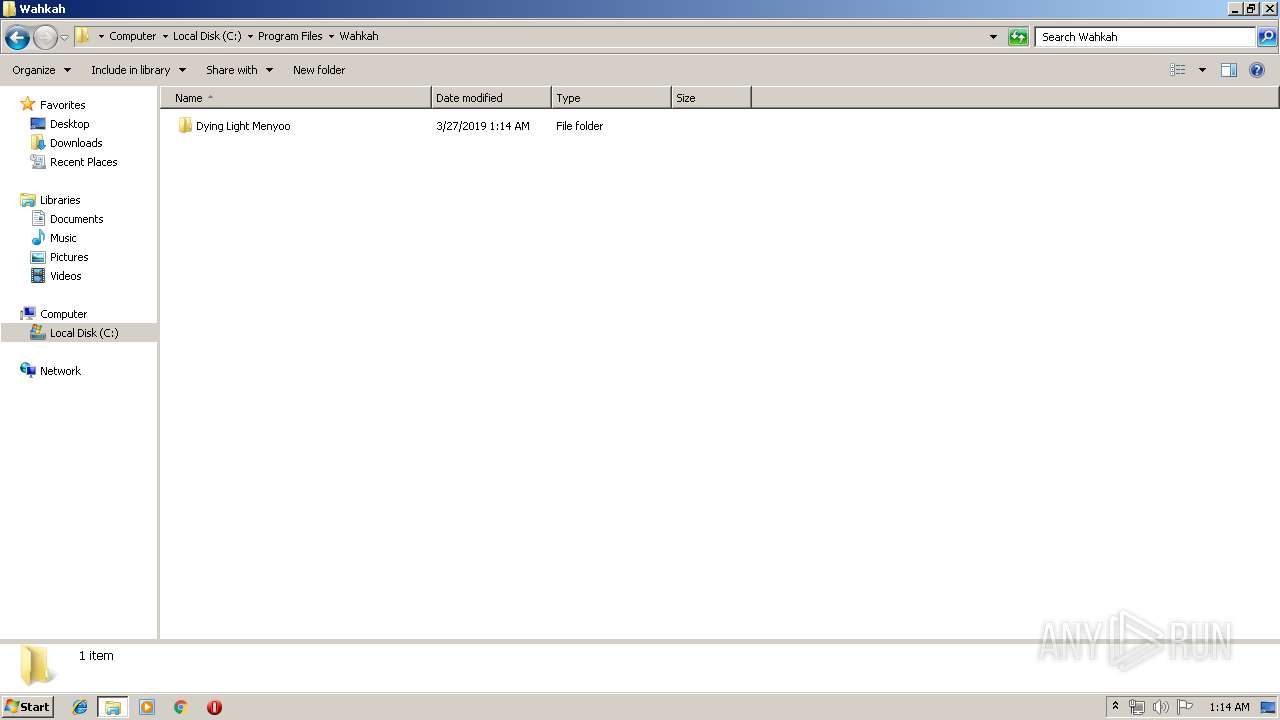
| CompanyName: | Wahkah |
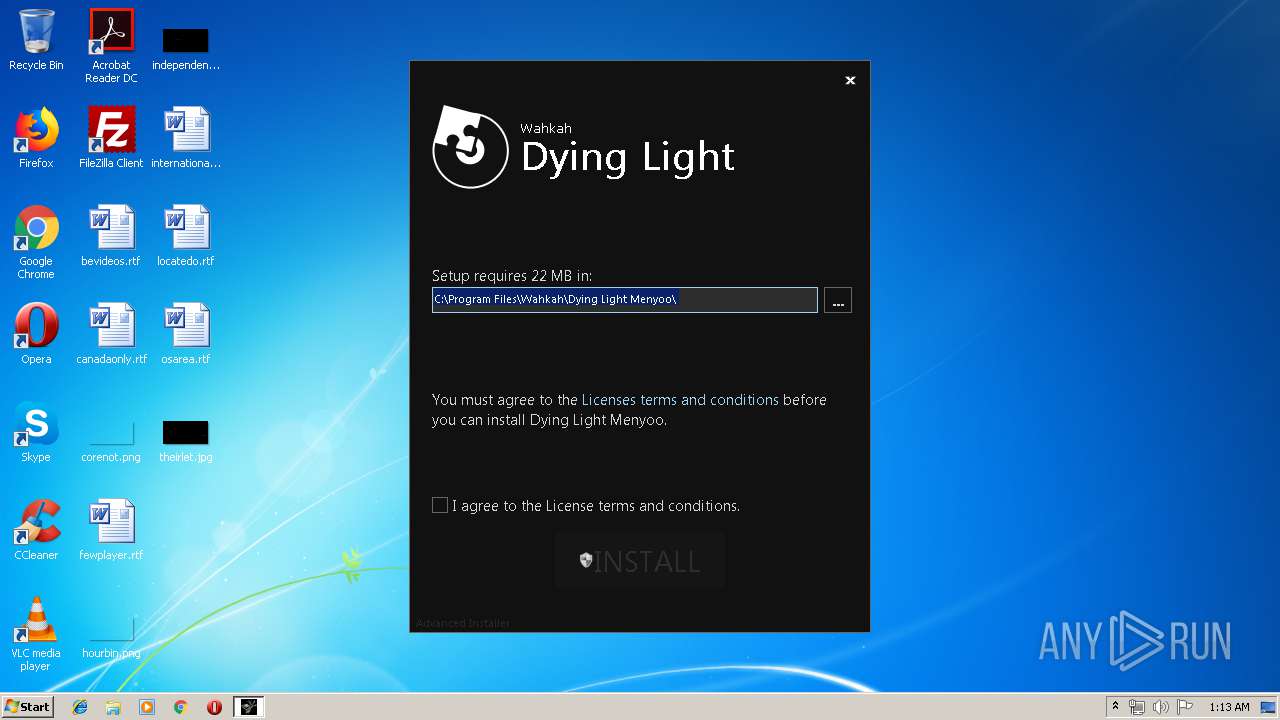
| FileDescription: | This installer database contains the logic and data required to install Dying Light Menyoo. |
| FileVersion: | 1.0.0 |
| InternalName: | Dying Light Menyoo |
| LegalCopyright: | Copyright (C) 2018 Wahkah |
| OriginalFileName: | Dying Light Menyoo.exe |
| ProductName: | Dying Light Menyoo |
| ProductVersion: | 1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Dec-2016 11:20:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Wahkah |
| FileDescription: | This installer database contains the logic and data required to install Dying Light Menyoo. |
| FileVersion: | 1.0.0 |
| InternalName: | Dying Light Menyoo |
| LegalCopyright: | Copyright (C) 2018 Wahkah |
| OriginalFileName: | Dying Light Menyoo.exe |
| ProductName: | Dying Light Menyoo |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Dec-2016 11:20:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00113B5C | 0x00113C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63264 |
.rdata | 0x00115000 | 0x00053334 | 0x00053400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54312 |
.data | 0x00169000 | 0x000071E4 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.12128 |
.gfids | 0x00171000 | 0x000003F0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.00634 |
.tls | 0x00172000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00173000 | 0x00033DE4 | 0x00033E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.11758 |
.reloc | 0x001A7000 | 0x00014A3C | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58944 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.09275 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.00832 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.85512 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.76993 | 139880 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.34109 | 1000 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
57
Monitored processes
18
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1420 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | cmd /c ""C:\Users\admin\AppData\Local\Temp\EXE16D.tmp.bat" " | C:\Windows\system32\cmd.exe | — | Wahkah's Menyoo-360-16-01-1549155772.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
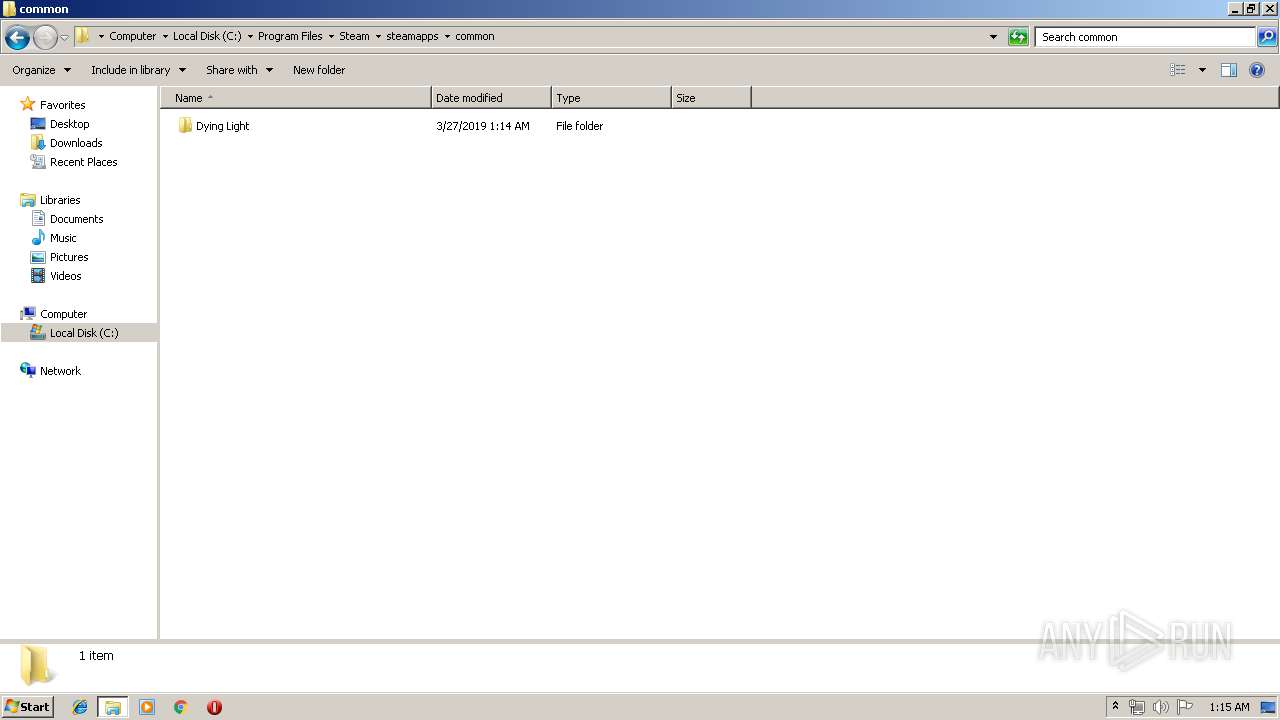
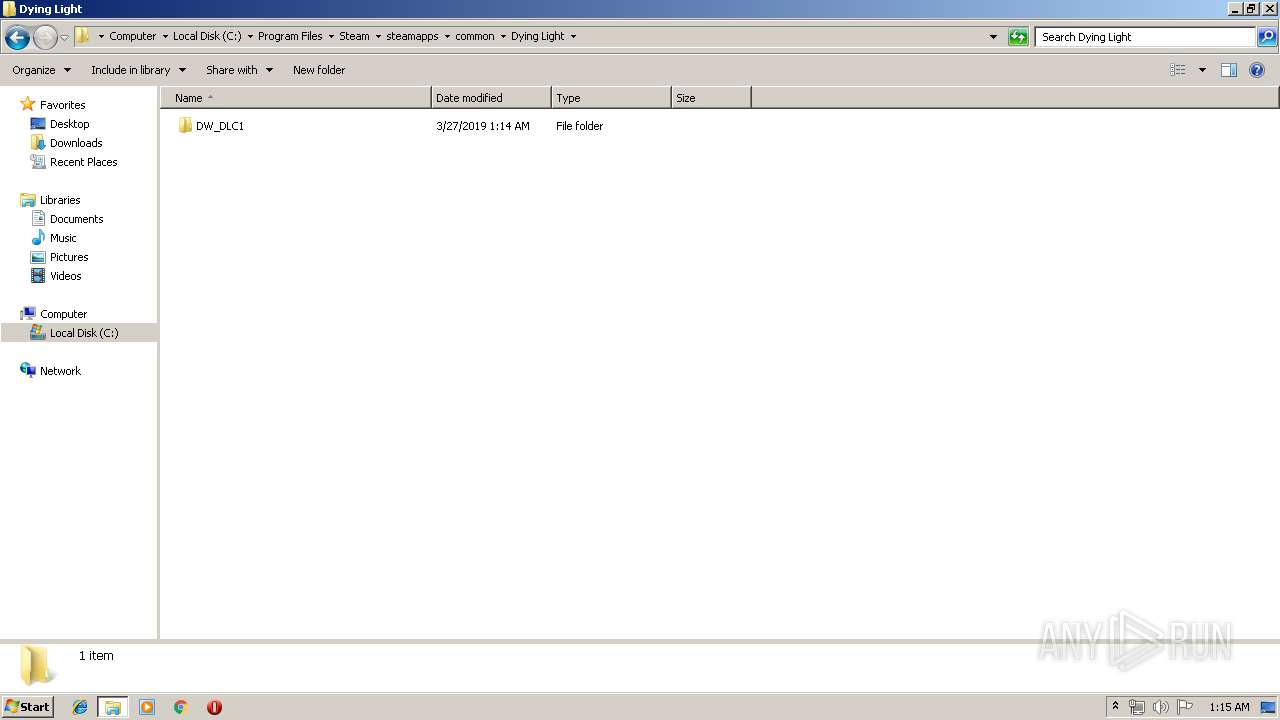
| 2000 | "C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe" /i "C:\Users\admin\AppData\Roaming\Wahkah\Dying Light Menyoo 1.0.0\install\Dying Light Menyoo.msi" APPDIR="C:\Program Files\Wahkah\Dying Light Menyoo" SEARCHDL="C:" STEAMLIBRARY="C:\Windows\system32" CLIENTPROCESSID="2872" SECONDSEQUENCE="1" CHAINERUIPROCESSID="2872Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="MainFeature" AGREE_CHECKBOX="Yes" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates " TARGETDIR="C:\" AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe" AI_INSTALL="1" | C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe | Wahkah's Menyoo-360-16-01-1549155772.exe | ||||||||||||
User: admin Company: Wahkah Integrity Level: HIGH Description: This installer database contains the logic and data required to install Dying Light Menyoo. Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2136 | C:\Windows\system32\cmd.exe /S /D /c" cls" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2260 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005C8" "000005B8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | C:\Windows\system32\cmd.exe /S /D /c" del "C:\Users\admin\AppData\Local\Temp\EXE16D.tmp.bat" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe" | C:\Users\admin\AppData\Local\Temp\Wahkah's Menyoo-360-16-01-1549155772.exe | explorer.exe | ||||||||||||
User: admin Company: Wahkah Integrity Level: MEDIUM Description: This installer database contains the logic and data required to install Dying Light Menyoo. Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2912 | ATTRIB -r "\\?\C:\Users\admin\AppData\Roaming\Wahkah\DYINGL~1.0\install\DYINGL~1.MSI" | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | C:\Windows\system32\cmd.exe /S /D /c" cls" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 441
Read events
1 052
Write events
376
Delete events
13
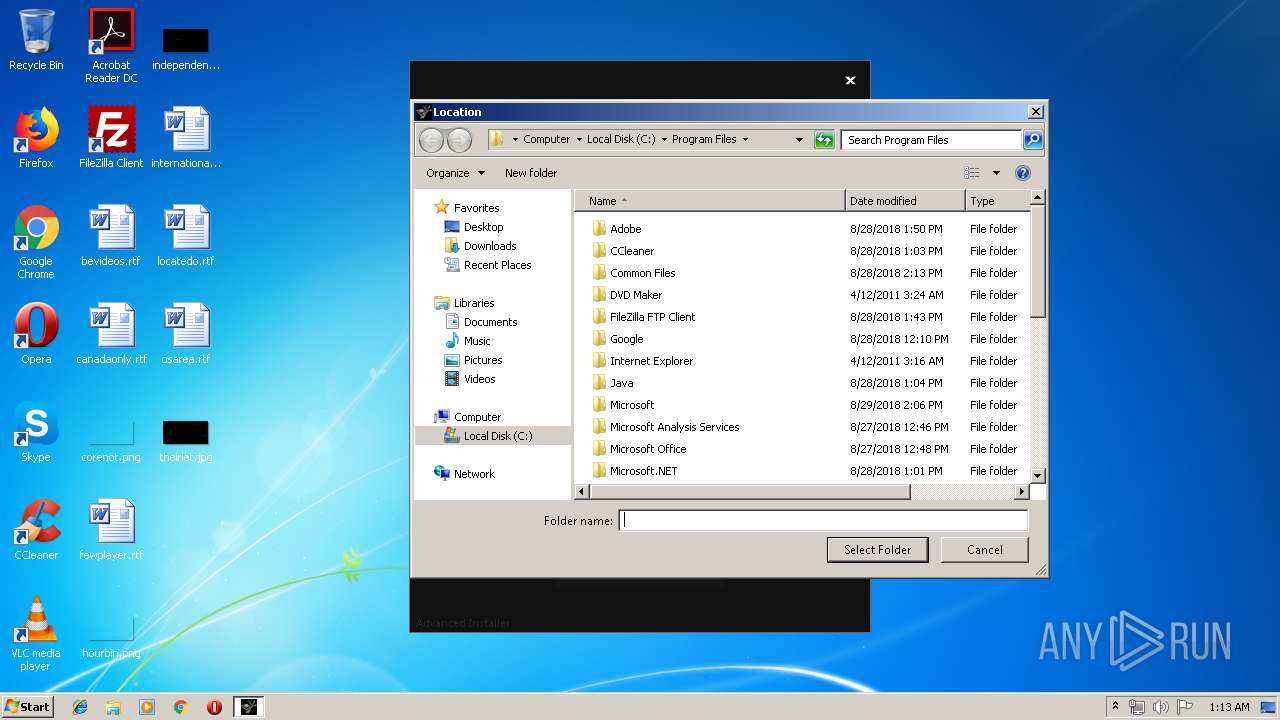
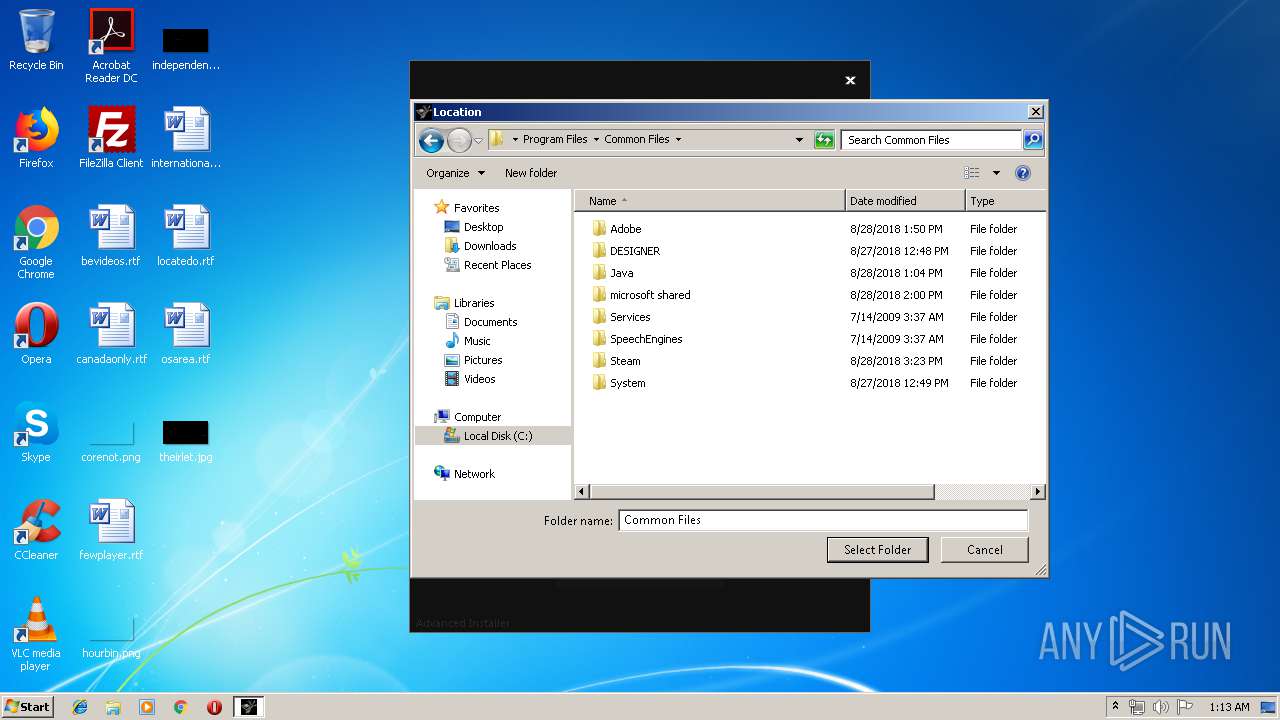
Modification events
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000070000000200000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000020000000400000003000000FFFFFFFF | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: 1092616257 | |||
| (PID) Process: | (2872) Wahkah's Menyoo-360-16-01-1549155772.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\35\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
12
Suspicious files
54
Text files
187
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Roaming\Wahkah\Dying Light Menyoo 1.0.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\MSI693C.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\MSI695C.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\MSI697D.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\MSI699D.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\MSI69CD.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Roaming\Wahkah\Dying Light Menyoo 1.0.0\install\Dying Light Menyoo.msi | executable | |
MD5:39448C2F7CD611F0B0C836BD71102F5C | SHA256:C60367D09BB49EC5C01803F6565B2F4F897008115F3A8DAB0548F18D4DF607C6 | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Roaming\Wahkah\Dying Light Menyoo 1.0.0\install\Dying Light Menyoo.aiui | executable | |
MD5:61302FF5E38AFBF5D550DA8FCDF8B514 | SHA256:FB292BB8177CCC28580C1DF5889BADE6337E77D6BD4350A7D030F0D605F62ECC | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2872\sys_min_down.png | image | |
MD5:5E947815D865ACF099FA753283E09179 | SHA256:C1D0663131FE901D890CDD9F18AF8F9A553BEE4848CBD978F5122E8383B5534B | |||
| 2872 | Wahkah's Menyoo-360-16-01-1549155772.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_2872\frame_top_mid.bmp | image | |
MD5:4E0AC65606B6AACD85E11C470CEB4E54 | SHA256:1D59FE11B3F1951C104F279C1338FC307940268971D016EBE929A9998A5038EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report