| download: | ToDesk_Setup.exe |
| Full analysis: | https://app.any.run/tasks/7f0f9c39-a8cd-4233-9f5d-5609262c9304 |
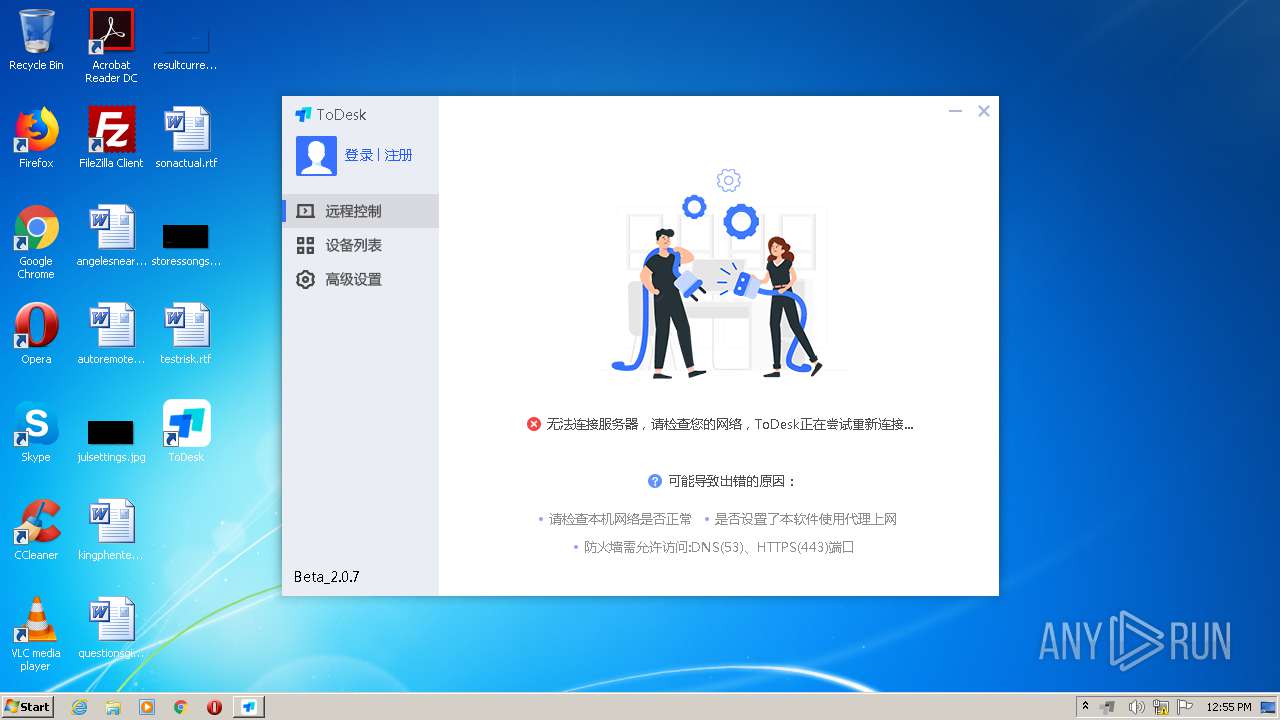
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2021, 12:54:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5B8D0EC98E3BF5C506BACB89859E590E |
| SHA1: | 39136C30E67B75E6ABFA364F77F8CAC40DB89929 |
| SHA256: | 464037A08EBB69116CACF060FC134D75A249A3B1AB3A7F7D2D23B6D2C88DA349 |
| SSDEEP: | 196608:nQS6gGGzs8Y3fnpDZLoox49kaPN+wAAiR+0glVbXdIbUK8KBO6Jh:QS8GgJBDiD9zF+FDMlVXdIYKJBO67 |
MALICIOUS
Application was dropped or rewritten from another process
- ns39AB.tmp (PID: 544)
- ns3AC5.tmp (PID: 3656)
- ns392D.tmp (PID: 2768)
- ns3BB1.tmp (PID: 2460)
- ns4836.tmp (PID: 2696)
- ns4DE5.tmp (PID: 340)
- ns4BB2.tmp (PID: 3008)
- ns4F9C.tmp (PID: 1332)
- ns5152.tmp (PID: 3056)
- ns5309.tmp (PID: 2396)
- ns4670.tmp (PID: 3064)
- ns54BF.tmp (PID: 4072)
- ToDesk_Service.exe (PID: 2340)
- ns5676.tmp (PID: 1524)
- ToDesk.exe (PID: 3716)
- ToDesk.exe (PID: 3444)
- ToDesk_Service.exe (PID: 3416)
- ToDesk_Service.exe (PID: 2456)
- ToDesk_Service.exe (PID: 2692)
- ToDesk_Service.exe (PID: 1912)
- ToDesk_Service.exe (PID: 1604)
- ToDesk_Service.exe (PID: 1924)
- ToDesk_Service.exe (PID: 3292)
- ToDesk.exe (PID: 3012)
- ToDesk_Service.exe (PID: 1712)
- ToDesk_Service.exe (PID: 3036)
- ToDesk_Service.exe (PID: 3912)
- ToDesk_Service.exe (PID: 2596)
Loads dropped or rewritten executable
- ToDesk_Setup.exe (PID: 4080)
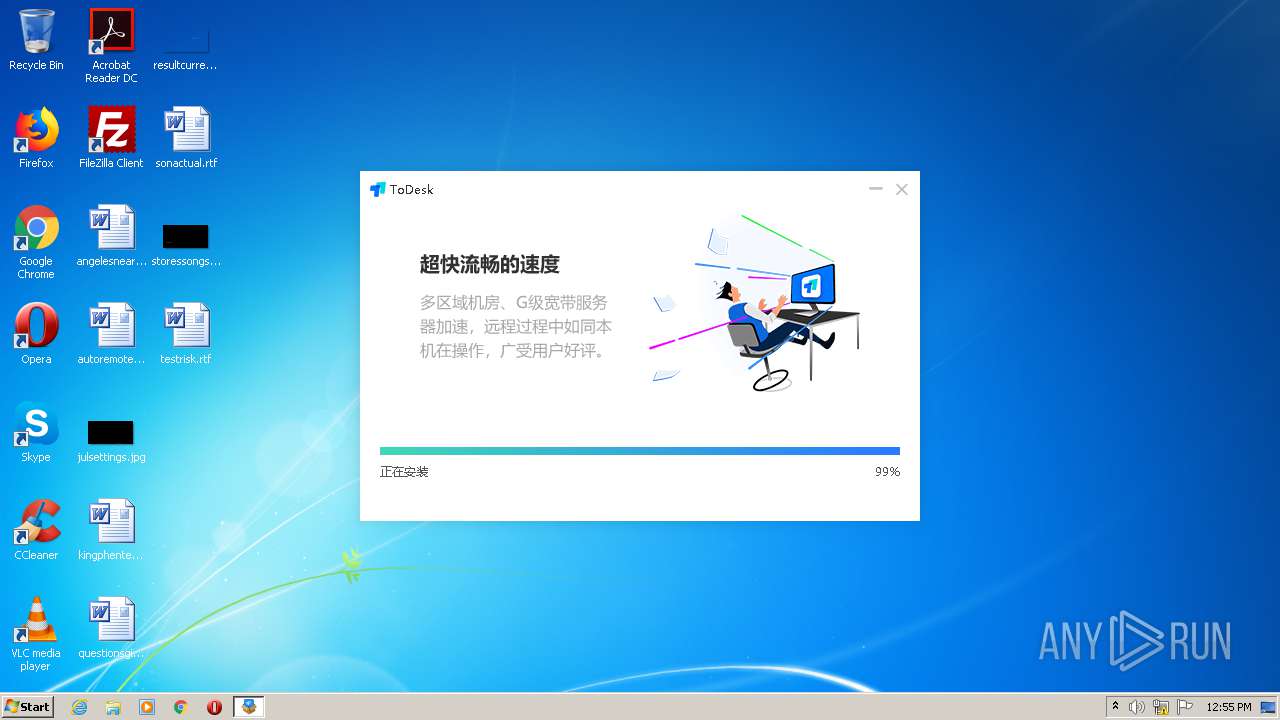
Adds new firewall rule via NETSH.EXE
- ns5152.tmp (PID: 3056)
- ns4DE5.tmp (PID: 340)
- ns4F9C.tmp (PID: 1332)
- ns5676.tmp (PID: 1524)
- ns5309.tmp (PID: 2396)
- ns54BF.tmp (PID: 4072)
SUSPICIOUS
Starts application with an unusual extension
- ToDesk_Setup.exe (PID: 4080)
Drops a file with too old compile date
- ToDesk_Setup.exe (PID: 4080)
Starts CMD.EXE for commands execution
- ns392D.tmp (PID: 2768)
- ns39AB.tmp (PID: 544)
- ns3BB1.tmp (PID: 2460)
- ns3AC5.tmp (PID: 3656)
Executable content was dropped or overwritten
- ToDesk_Setup.exe (PID: 4080)
Drops a file that was compiled in debug mode
- ToDesk_Setup.exe (PID: 4080)
Starts SC.EXE for service management
- cmd.exe (PID: 3100)
- cmd.exe (PID: 2204)
- cmd.exe (PID: 1852)
- cmd.exe (PID: 3292)
Drops a file with a compile date too recent
- ToDesk_Setup.exe (PID: 4080)
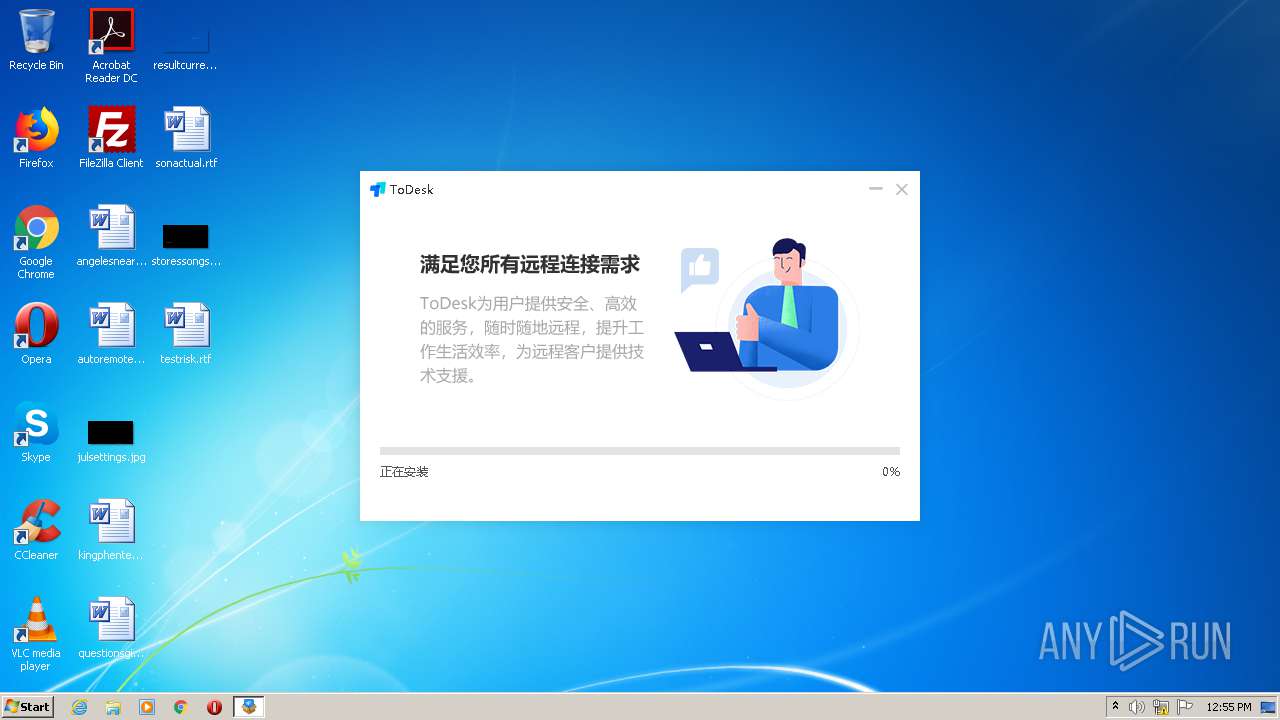
Creates a directory in Program Files
- ToDesk_Setup.exe (PID: 4080)
- ToDesk_Service.exe (PID: 2340)
Creates files in the program directory
- ToDesk_Setup.exe (PID: 4080)
- ToDesk_Service.exe (PID: 2340)
- ToDesk.exe (PID: 3444)
- ToDesk.exe (PID: 3012)
Creates a software uninstall entry
- ToDesk_Setup.exe (PID: 4080)
Uses NETSH.EXE for network configuration
- ns4670.tmp (PID: 3064)
- ns4BB2.tmp (PID: 3008)
- ns4836.tmp (PID: 2696)
- ns4DE5.tmp (PID: 340)
- ns4F9C.tmp (PID: 1332)
- ns5152.tmp (PID: 3056)
- ns5309.tmp (PID: 2396)
- ns54BF.tmp (PID: 4072)
- ns5676.tmp (PID: 1524)
Executed as Windows Service
- ToDesk_Service.exe (PID: 2340)
- ToDesk_Service.exe (PID: 1912)
- ToDesk_Service.exe (PID: 2692)
- ToDesk_Service.exe (PID: 2456)
- ToDesk_Service.exe (PID: 3292)
- ToDesk_Service.exe (PID: 1924)
- ToDesk_Service.exe (PID: 1604)
- ToDesk_Service.exe (PID: 3416)
- ToDesk_Service.exe (PID: 3036)
- ToDesk_Service.exe (PID: 2596)
- ToDesk_Service.exe (PID: 1712)
- ToDesk_Service.exe (PID: 3912)
Application launched itself
- ToDesk.exe (PID: 3444)
Creates files in the Windows directory
- ToDesk_Service.exe (PID: 2340)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.7.0 |
| ProductVersionNumber: | 2.0.7.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | Hainan YouQu Technology Co., Ltd |
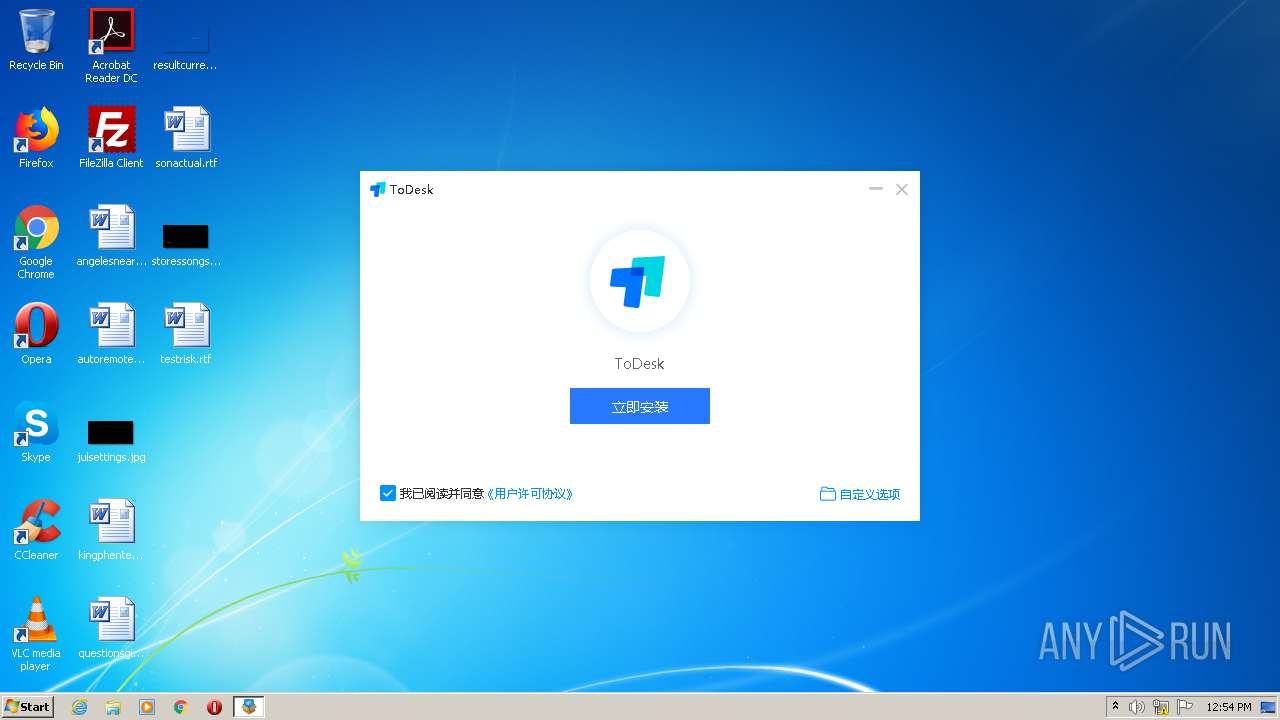
| FileDescription: | ToDesk 安装&移除包 |
| FileVersion: | 2.0.7.0 |
| InternalName: | ToDesk.exe |
| LegalCopyright: | Copyright© Hainan YouQu Technology Co., Ltd |
| ProductName: | ToDesk 远程控制软件 |
| ProductVersion: | 2.0.7.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| CompanyName: | Hainan YouQu Technology Co., Ltd |
| FileDescription: | ToDesk 安装&移除包 |
| FileVersion: | 2.0.7.0 |
| InternalName: | ToDesk.exe |
| LegalCopyright: | Copyright© Hainan YouQu Technology Co., Ltd |
| ProductName: | ToDesk 远程控制软件 |
| ProductVersion: | 2.0.7.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x000C9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0013C000 | 0x00042B58 | 0x00042C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.87375 |
.reloc | 0x0017F000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.226735 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.67095 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
97
Monitored processes
47
Malicious processes
2
Suspicious processes
23
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | netsh advfirewall firewall add rule name="ToDesk_Service" dir=out program="C:\Program Files\ToDesk\ToDesk_Service.exe" action=allow | C:\Windows\system32\netsh.exe | — | ns5309.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | netsh advfirewall firewall delete rule name="ToDesk_Session" | C:\Windows\system32\netsh.exe | — | ns4BB2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | "C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns4DE5.tmp" netsh advfirewall firewall add rule name="ToDesk" dir=in program="C:\Program Files\ToDesk\ToDesk.exe" edge=yes action=allow | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns4DE5.tmp | — | ToDesk_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 464 | netsh advfirewall firewall add rule name="ToDesk_Service" dir=in program="C:\Program Files\ToDesk\ToDesk_Service.exe" edge=yes action=allow | C:\Windows\system32\netsh.exe | — | ns5152.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | "C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns39AB.tmp" cmd.exe /c sc delete ToDesk_Service | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns39AB.tmp | — | ToDesk_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1060 Modules
| |||||||||||||||
| 648 | netsh advfirewall firewall delete rule name="ToDesk" | C:\Windows\system32\netsh.exe | — | ns4670.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1292 | sc stop ToDesk_Service | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns4F9C.tmp" netsh advfirewall firewall add rule name="ToDesk" dir=out program="C:\Program Files\ToDesk\ToDesk.exe" action=allow | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns4F9C.tmp | — | ToDesk_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1524 | "C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns5676.tmp" netsh advfirewall firewall add rule name="ToDesk_Session" dir=out program="C:\Program Files\ToDesk\ToDesk_Session.exe" action=allow | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns5676.tmp | — | ToDesk_Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1552 | netsh advfirewall firewall add rule name="ToDesk_Session" dir=in program="C:\Program Files\ToDesk\ToDesk_Session.exe" edge=yes action=allow | C:\Windows\system32\netsh.exe | — | ns54BF.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 320
Read events
910
Write events
410
Delete events
0
Modification events
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (648) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
25
Suspicious files
1
Text files
24
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns392D.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns3AC5.tmp | — | |
MD5:— | SHA256:— | |||
| 4080 | ToDesk_Setup.exe | C:\Program Files\ToDesk\app.7z | — | |
MD5:— | SHA256:— | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\skin.zip | compressed | |
MD5:28AA1DB6BB7DB97983F7F36ED6A8FFB6 | SHA256:BE63D8FCF38FDFC6487C8A0DAEEA1B9770139B3601F4CBCB7842522E02342AD8 | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns39AB.tmp | executable | |
MD5:30D31B3424FF6B7613EAAF79E9449E0F | SHA256:8F0F0E254113725B386FF4C6C2967D556ED4D568245FC8AF6F2DBEA697BA56BF | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\logo.ico | image | |
MD5:C876F4A7EB27BB98ECFE8EB1678A8C8D | SHA256:97D993161D4F51AF552824BE1FAB0D429CD70D78827F316C40BFABF76BC86D27 | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\SimpleSC.dll | executable | |
MD5:6876AD26FB12CF5C163EADF0DB0AEF7A | SHA256:81A60504618B32B36D33A0CEB982C3461EA0C5799E191524B7BB757201152358 | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\ns3BB1.tmp | executable | |
MD5:30D31B3424FF6B7613EAAF79E9449E0F | SHA256:8F0F0E254113725B386FF4C6C2967D556ED4D568245FC8AF6F2DBEA697BA56BF | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\nsSCM.dll | executable | |
MD5:C68ACA71E85B9615C16C45A3437B5558 | SHA256:00E701893AF9204D3E9669539BD47FD00E954C5583492B97647EFF7811D55181 | |||
| 4080 | ToDesk_Setup.exe | C:\Users\admin\AppData\Local\Temp\nsw1894.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
3444 | ToDesk.exe | 47.246.43.167:443 | update.todesk.com | — | US | suspicious |
2456 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
2692 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
1912 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
1924 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
3292 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
1604 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
3416 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
1712 | ToDesk_Service.exe | 106.75.129.46:443 | authd.todesk.com | CHINANET Guangdong province network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
authd.todesk.com |
| unknown |
update.todesk.com |
| malicious |
Threats
Process | Message |
|---|---|
ToDesk_Setup.exe | Window, size, 560,350
|
ToDesk_Setup.exe | Window, caption, 0,0,0,560
|
ToDesk_Setup.exe | Window, caption, 0,0,0,560
|
ToDesk_Setup.exe | Window, shadowimage, images/shadow.png
|
ToDesk_Setup.exe | Window, shadowimage, images/shadow.png
|
ToDesk_Setup.exe | Window, shadowcorner, 16,16,16,16
|
ToDesk_Setup.exe | Window, shadowcorner, 16,16,16,16
|
ToDesk_Setup.exe | ControlUI, padding, 215,45,0,0
|
ToDesk_Setup.exe | ControlUI, height, 130
|
ToDesk_Setup.exe | ControlUI, height, 130
|