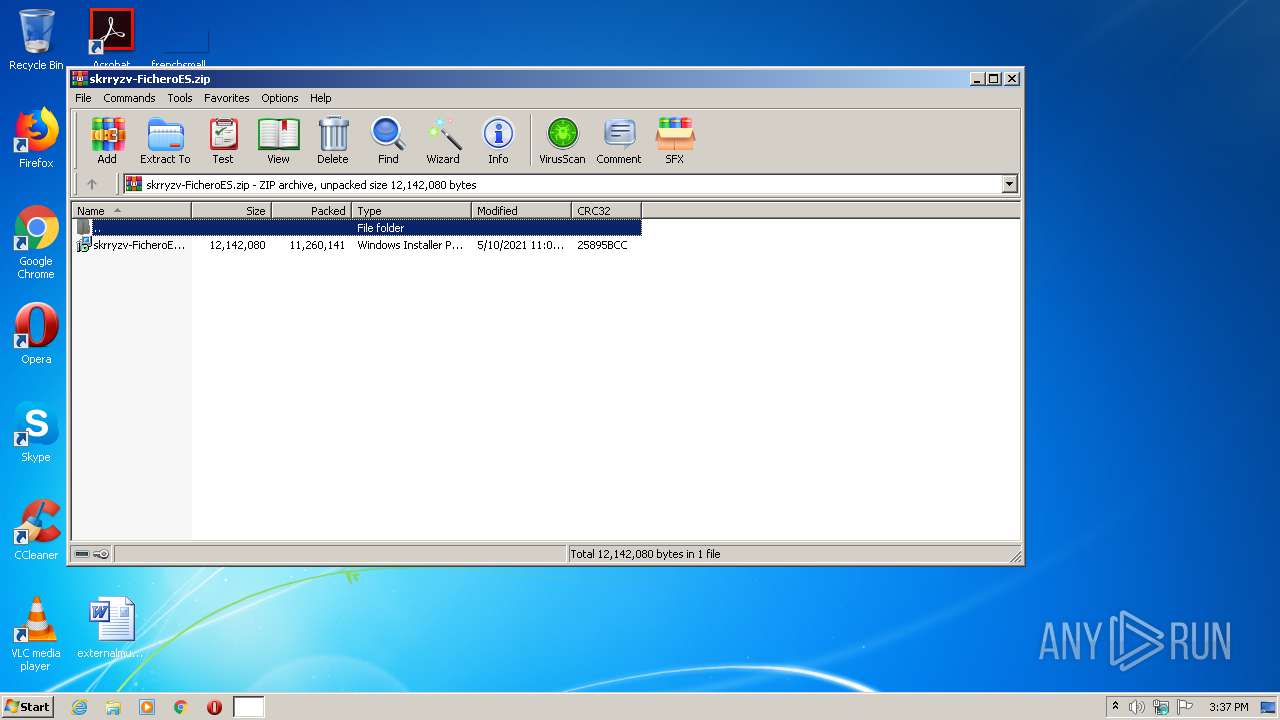
| File name: | skrryzv-FicheroES.zip |
| Full analysis: | https://app.any.run/tasks/a1ccc844-1ebc-4895-819a-7b31103ee125 |
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2021, 14:36:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4BFB59CCEDD21C7AA963898098E35C80 |
| SHA1: | 32D35961889FC9DE66EEB2A5C9D5B26B44C96F75 |
| SHA256: | 463F59001739163E382569F5CFC7B0FCCD1CBEF01A9D396C1933D82369BF88EE |
| SSDEEP: | 196608:hUipAsYD+Fhh3d/c1CXGW0ddGk/CGuNd6UNfEzCfigbVGF2r1lfQYVJojkXf:+ipAsoKt/c0juGPGuNdrsCfXGF2T/VJj |
MALICIOUS
Loads dropped or rewritten executable
- CMG.exe (PID: 3472)
- SearchProtocolHost.exe (PID: 2684)
Application was dropped or rewritten from another process
- CMG.exe (PID: 3472)
SUSPICIOUS
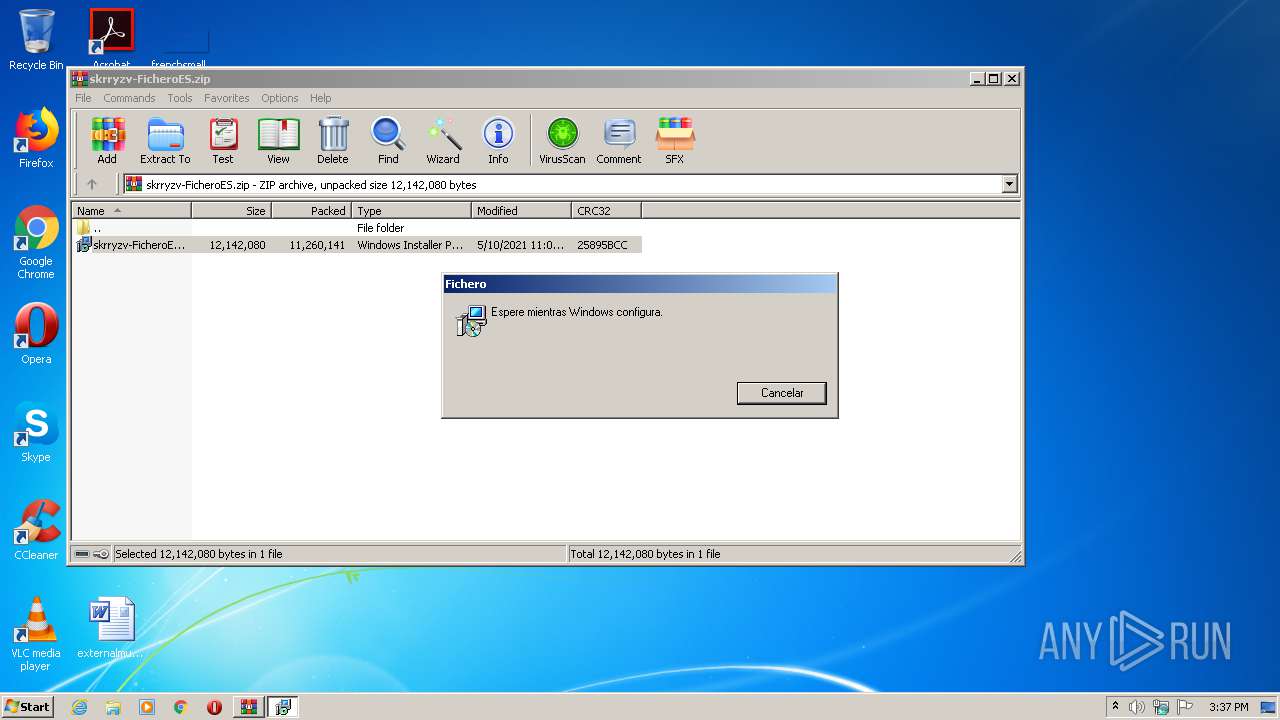
Starts Microsoft Installer
- WinRAR.exe (PID: 3720)
Disables Form Suggestion in IE
- CMG.exe (PID: 3472)
Changes the autorun value in the registry
- MsiExec.exe (PID: 1744)
Executable content was dropped or overwritten
- MsiExec.exe (PID: 1744)
Drops a file with a compile date too recent
- MsiExec.exe (PID: 1744)
Reads Environment values
- CMG.exe (PID: 3472)
Creates files in the program directory
- CMG.exe (PID: 3472)
INFO
Application launched itself
- msiexec.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | skrryzv-FicheroES.msi |
|---|---|
| ZipUncompressedSize: | 12142080 |
| ZipCompressedSize: | 11260141 |
| ZipCRC: | 0x25895bcc |
| ZipModifyDate: | 2021:05:10 19:00:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
41
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | C:\Windows\system32\MsiExec.exe -Embedding 9FA346A4385C6771CE27F3C02474BAF4 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3472 | "C:\Users\Public\kyrhsbzz\CMG.exe" | C:\Users\Public\kyrhsbzz\CMG.exe | MsiExec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AutoHotkey Unicode 32-bit Exit code: 0 Version: 1.1.33.06 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\skrryzv-FicheroES.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4032 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.17758\skrryzv-FicheroES.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 340
Read events
1 273
Write events
52
Delete events
15
Modification events
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\skrryzv-FicheroES.zip | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3720) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
Executable files
3
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3720.17758\skrryzv-FicheroES.msi | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\4d1c3.msi | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\MSID28E.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\MSID34B.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\MSID36B.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\MSID447.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFD02E007B46FDB05B.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\MSID513.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF93EB7B3B3FF3E0FE.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | msiexec.exe | C:\Windows\Installer\4d1c5.ipi | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3472 | CMG.exe | POST | 200 | 49.235.164.123:80 | http://prettypet.net/archivo/hdu19h2d129dr1h2d28d012d2.php | CN | binary | 1 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.154:137 | — | — | — | malicious |
3472 | CMG.exe | 13.107.42.12:443 | vxzl2w.ch.files.1drv.com | Microsoft Corporation | US | suspicious |
3472 | CMG.exe | 13.107.43.13:443 | onedrive.live.com | Microsoft Corporation | US | malicious |
3472 | CMG.exe | 49.235.164.123:80 | prettypet.net | — | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onedrive.live.com |
| shared |
vxzl2w.ch.files.1drv.com |
| suspicious |
prettypet.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3472 | CMG.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Windows NT Version 5.0 |