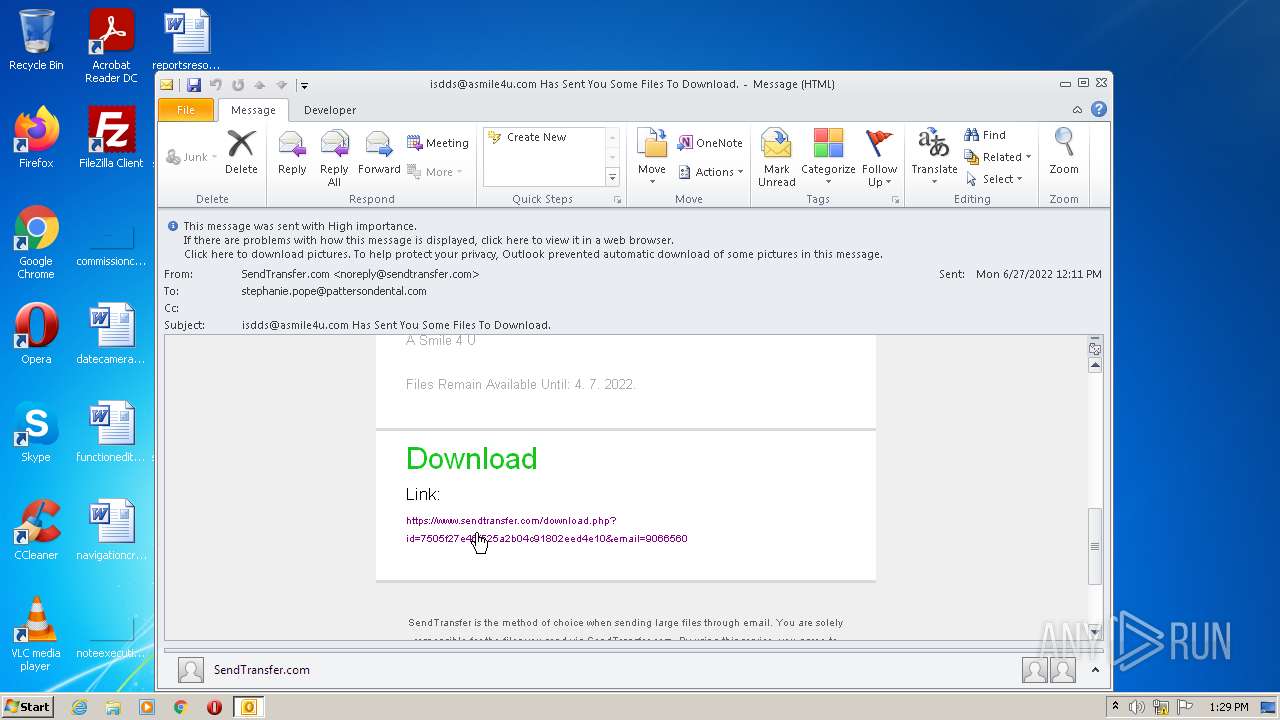
| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/80d70efd-b5e1-4f37-a642-25a320326add |
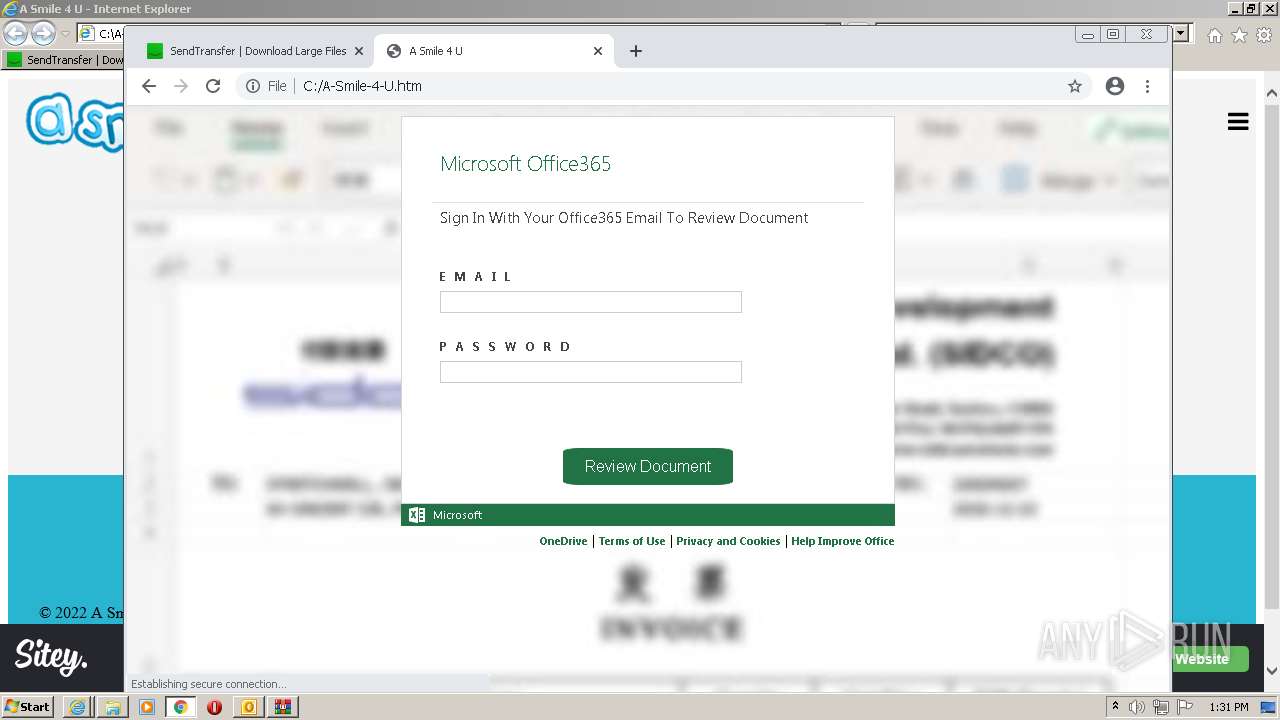
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 12:29:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 7DDD33C03903C1B9592FAAD845C35558 |
| SHA1: | 7BB8A4D5873053C2294D678CF3C0ED9C990F401D |
| SHA256: | 4631B6F6F45A36C72F5F75C0910E5F7E70C29411FAB3B9DF90E6928A2237402B |
| SSDEEP: | 192:O7+rFtpNC+kXaL0eF5GlXhEVMh2JnLMNg7Pfu6KDBMSdRmjirCH6wZnUe:OKrFrkY0FLInjJj0MUe |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- OUTLOOK.EXE (PID: 3692)
- WinRAR.exe (PID: 1888)
- WinRAR.exe (PID: 3440)
Searches for installed software
- OUTLOOK.EXE (PID: 3692)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3692)
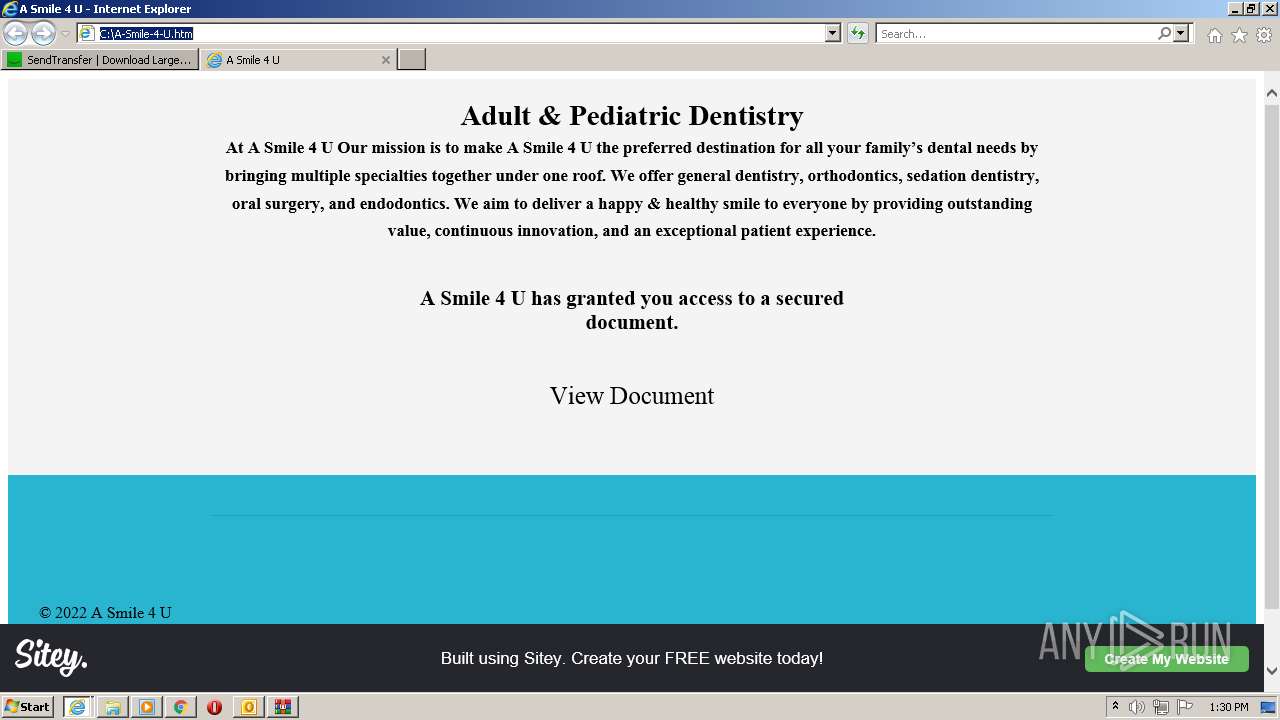
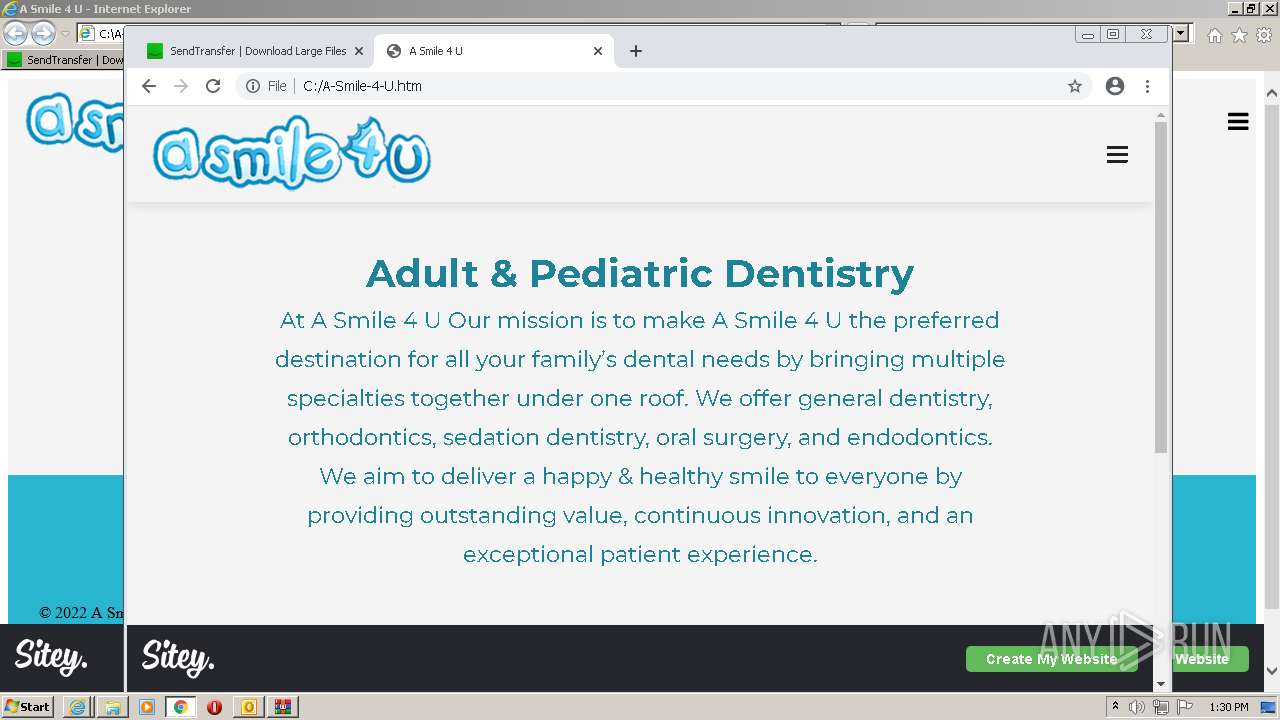
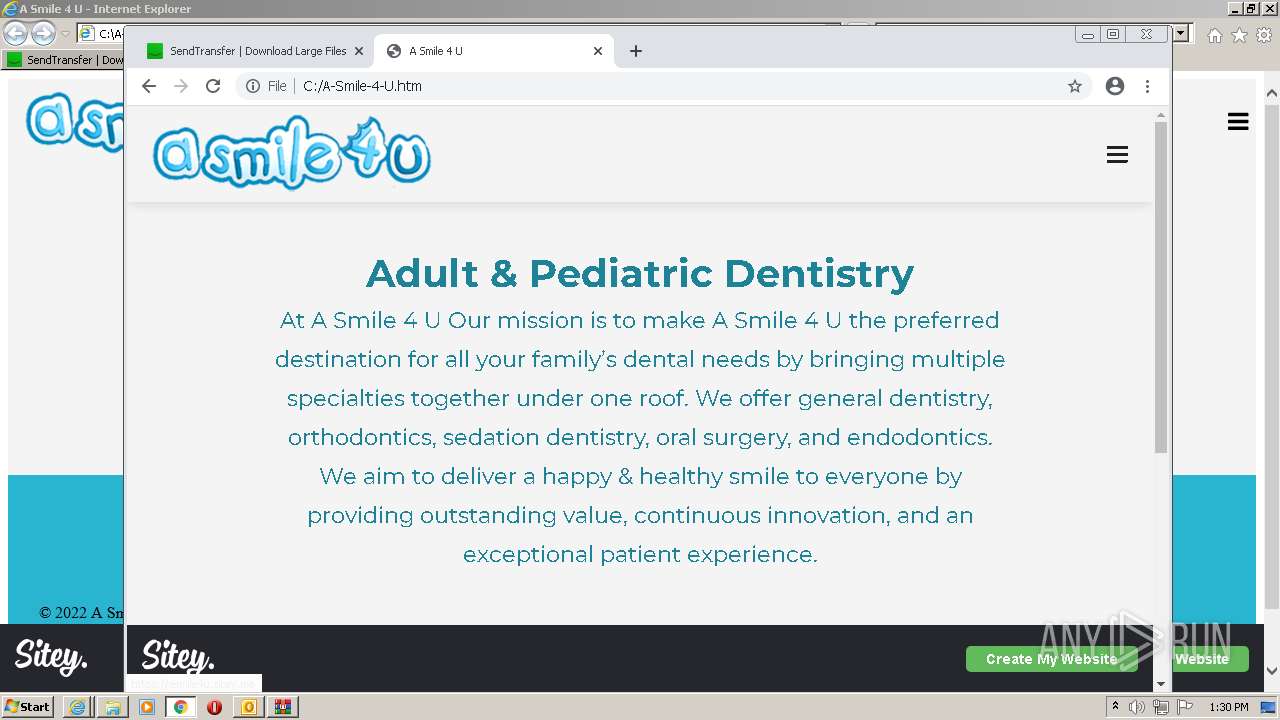
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3692)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 2996)
Checks supported languages
- OUTLOOK.EXE (PID: 3692)
- WinRAR.exe (PID: 3440)
- WinRAR.exe (PID: 1888)
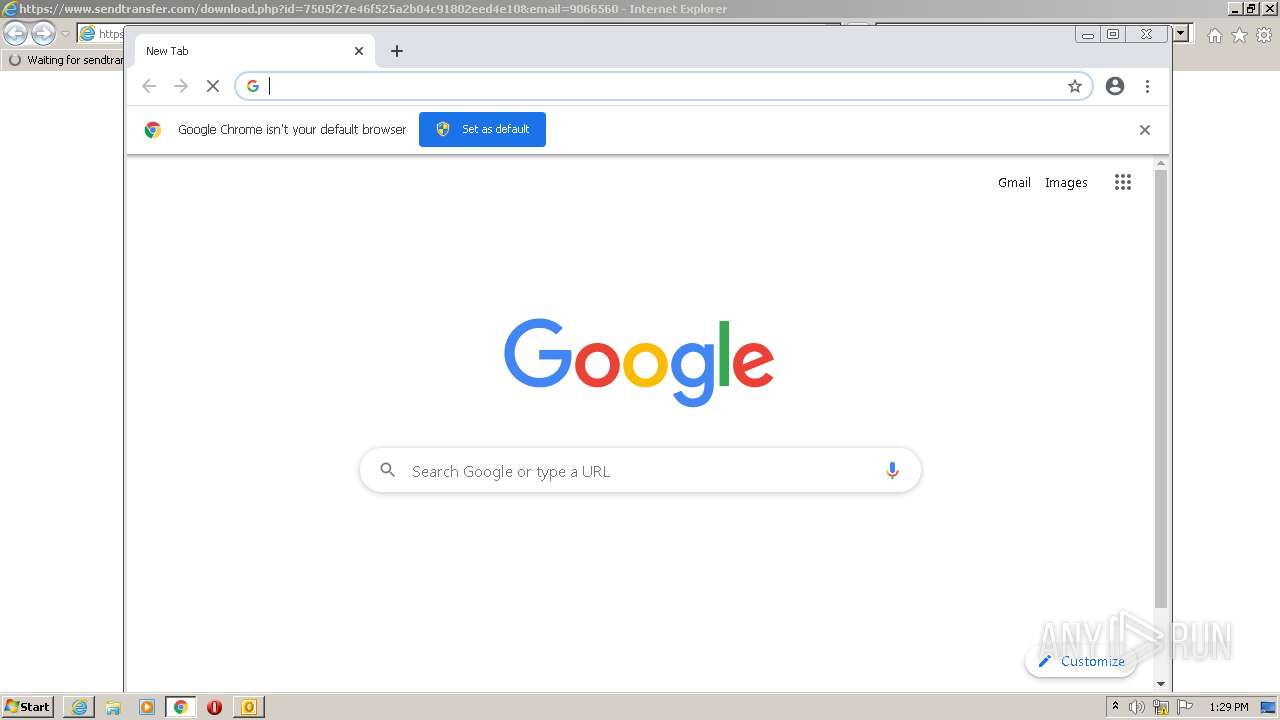
Modifies files in Chrome extension folder
- chrome.exe (PID: 556)
Application launched itself
- WinRAR.exe (PID: 1888)
INFO
Reads the computer name
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 556)
- iexplore.exe (PID: 2628)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 304)
- chrome.exe (PID: 1916)
- explorer.exe (PID: 2624)
- iexplore.exe (PID: 2996)
- chrome.exe (PID: 1964)
- chrome.exe (PID: 3212)
Changes internet zones settings
- iexplore.exe (PID: 2988)
Checks supported languages
- chrome.exe (PID: 556)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2628)
- chrome.exe (PID: 3800)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 2192)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3196)
- explorer.exe (PID: 2624)
- chrome.exe (PID: 3460)
- iexplore.exe (PID: 2996)
- chrome.exe (PID: 1916)
- chrome.exe (PID: 1964)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 1036)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 948)
- chrome.exe (PID: 584)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 1928)
- chrome.exe (PID: 3536)
Application launched itself
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 556)
Checks Windows Trust Settings
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2996)
Manual execution by user
- chrome.exe (PID: 556)
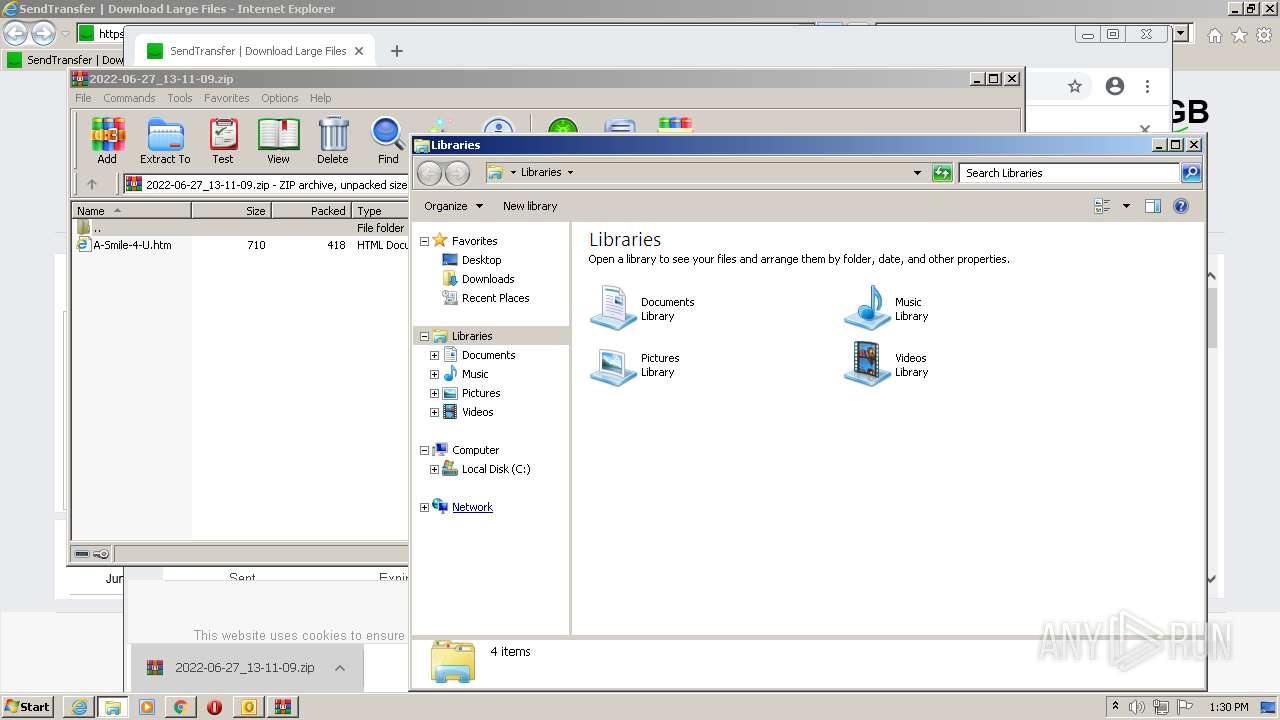
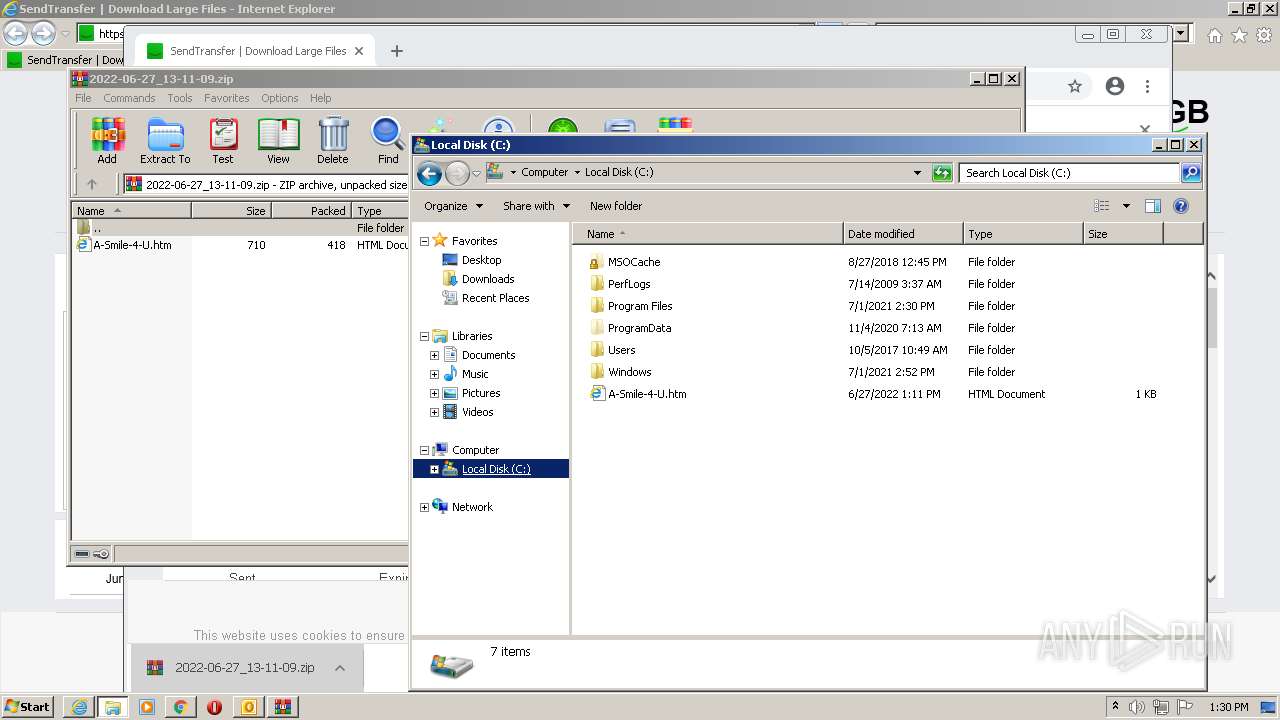
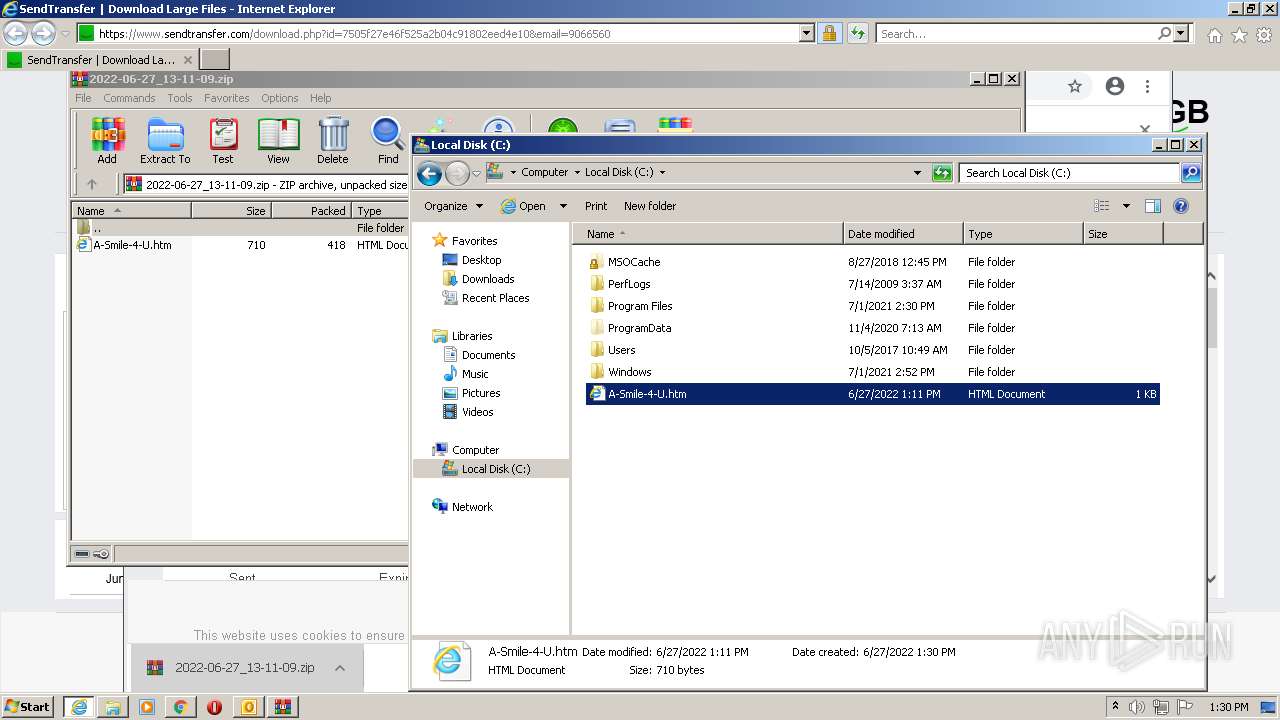
- explorer.exe (PID: 2624)
Reads settings of System Certificates
- iexplore.exe (PID: 2628)
- chrome.exe (PID: 2432)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2996)
Reads the hosts file
- chrome.exe (PID: 2432)
- chrome.exe (PID: 556)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3692)
Creates files in the user directory
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 2988)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2996)
Changes settings of System certificates
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2996)
Reads internet explorer settings
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 2996)
Reads the date of Windows installation
- chrome.exe (PID: 304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
84
Monitored processes
40
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
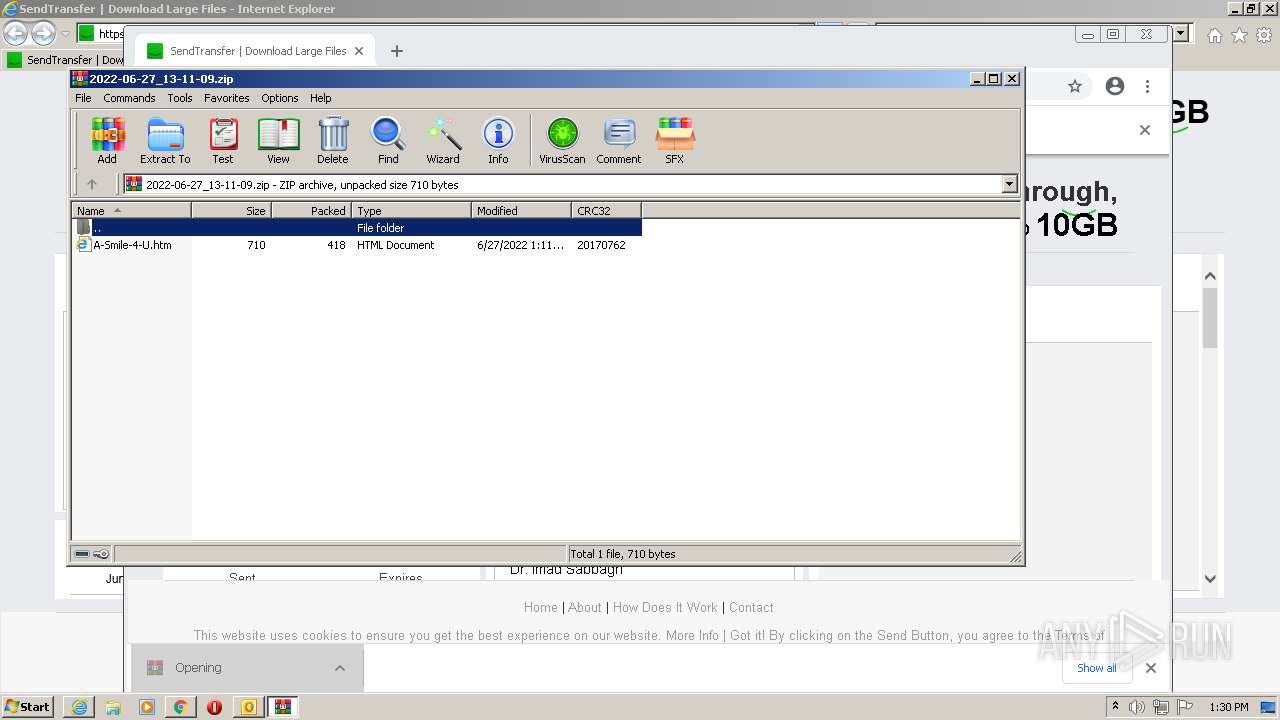
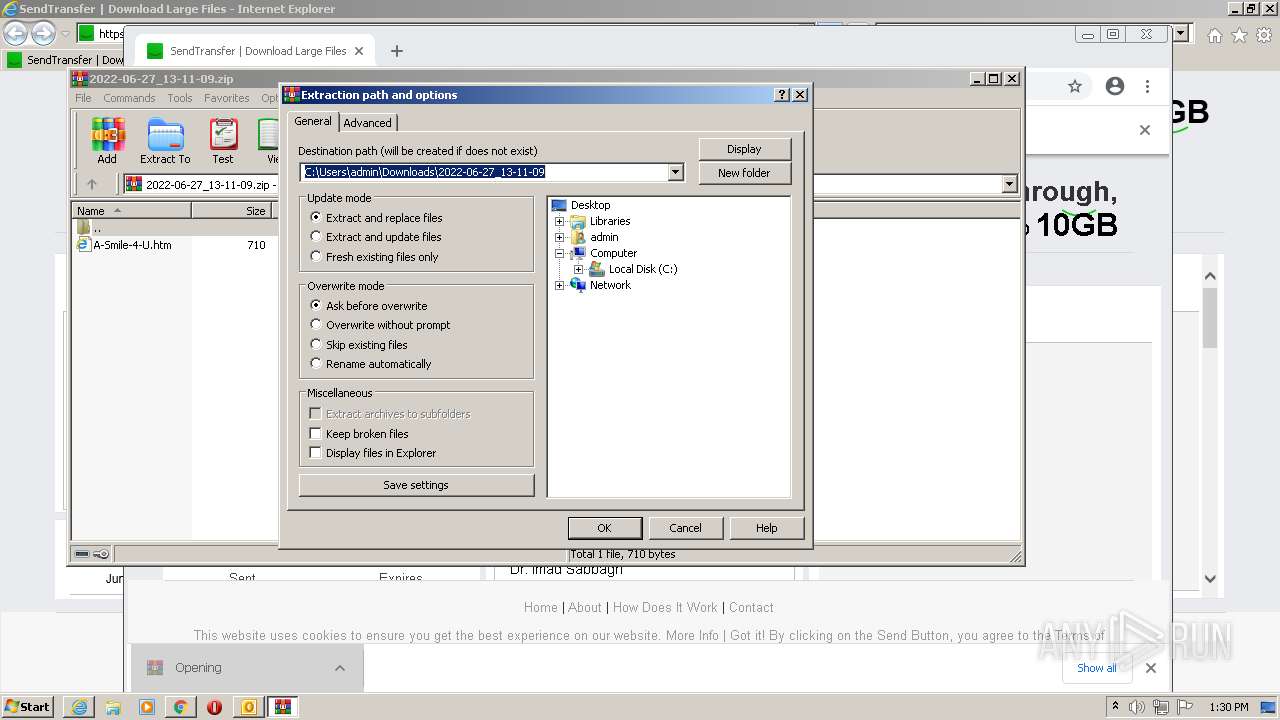
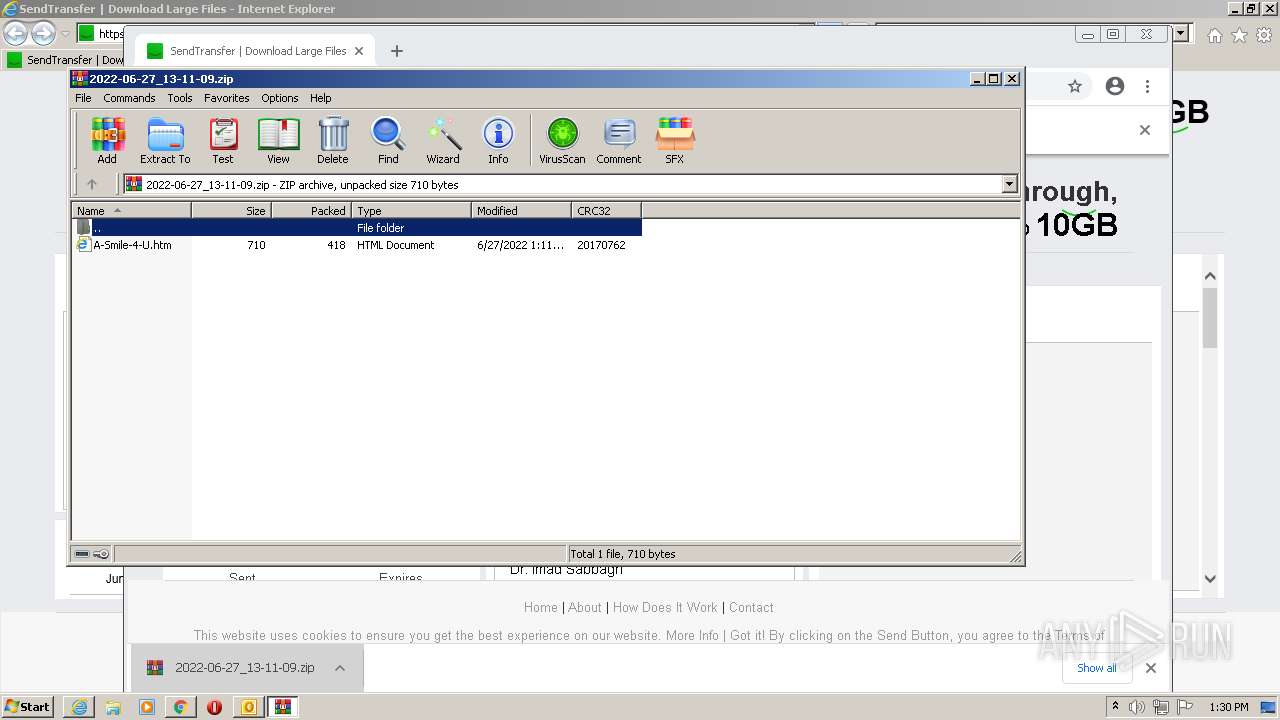
| 1888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\2022-06-27_13-11-09.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,11728589940873569070,8965619404436003117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
45 355
Read events
44 348
Write events
968
Delete events
39
Modification events
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3692) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
186
Text files
189
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9810.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62B9A2B4-22C.pma | — | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3692 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_057EE6FC91DBB14FA6EDB4F202A89AA5.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
159
DNS requests
82
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2628 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
2432 | chrome.exe | GET | 200 | 8.252.191.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8e0dfe6d5c52588e | US | compressed | 60.0 Kb | whitelisted |
2628 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECED1DMp0xqIaTLPZArXCqABY%3D | US | der | 471 b | whitelisted |
2628 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAT%2FrubUb6nOEpcsoEFY3SI%3D | US | der | 471 b | whitelisted |
2628 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG8ah82mu6j%2FCizjSGtvLoA%3D | US | der | 471 b | whitelisted |
2628 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2628 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDVyp94CxnOOApHadxSXjuI | US | der | 472 b | whitelisted |
2628 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFis5ZQLQXhkEp1TGjnLAGc%3D | US | der | 471 b | whitelisted |
2996 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3692 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
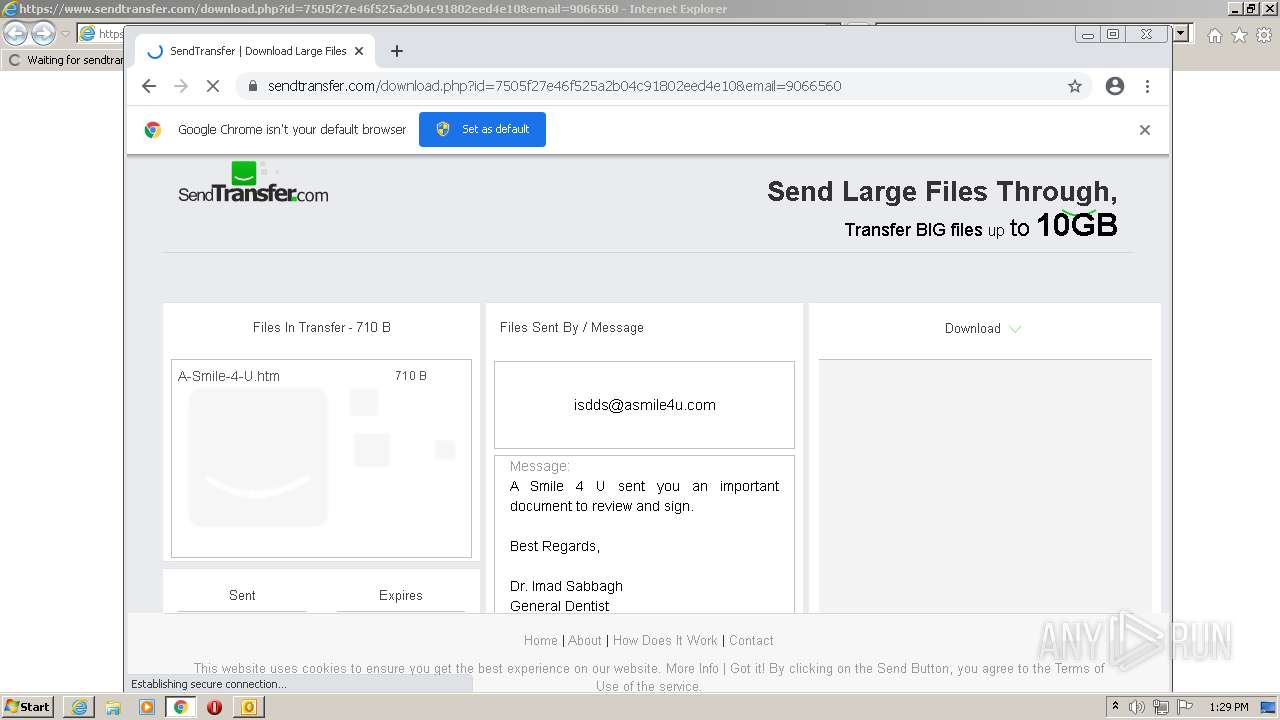
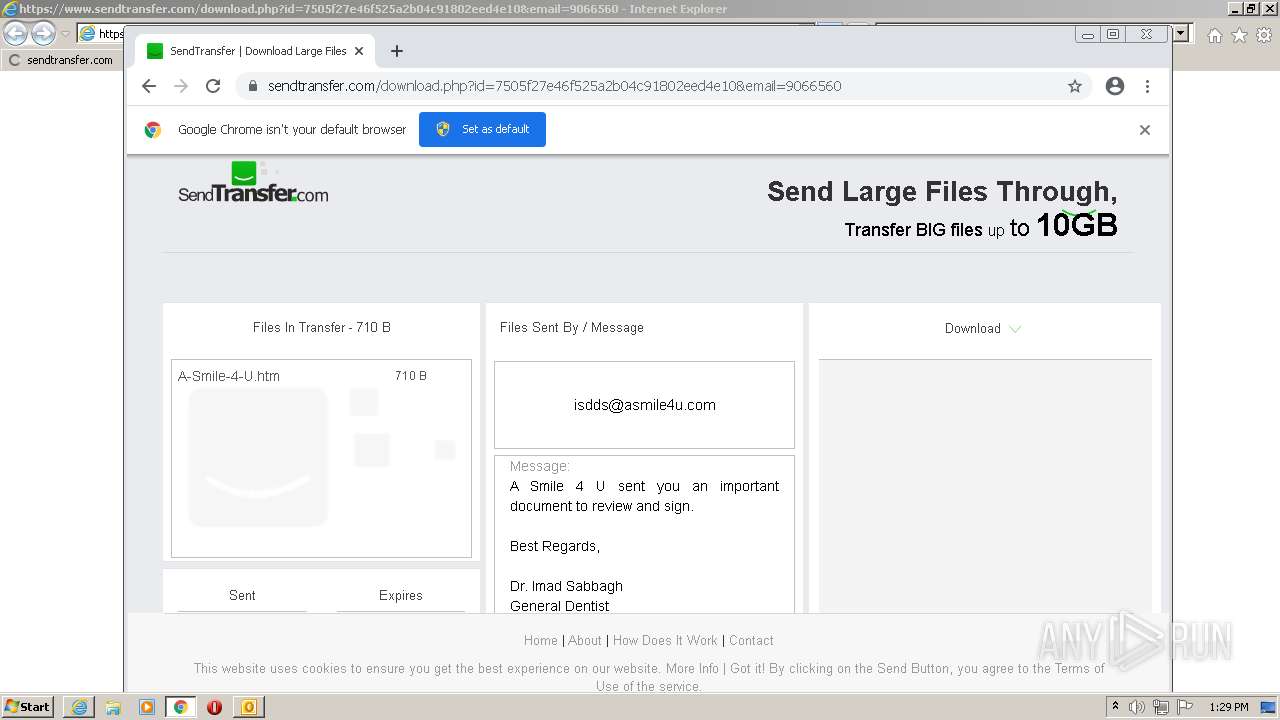
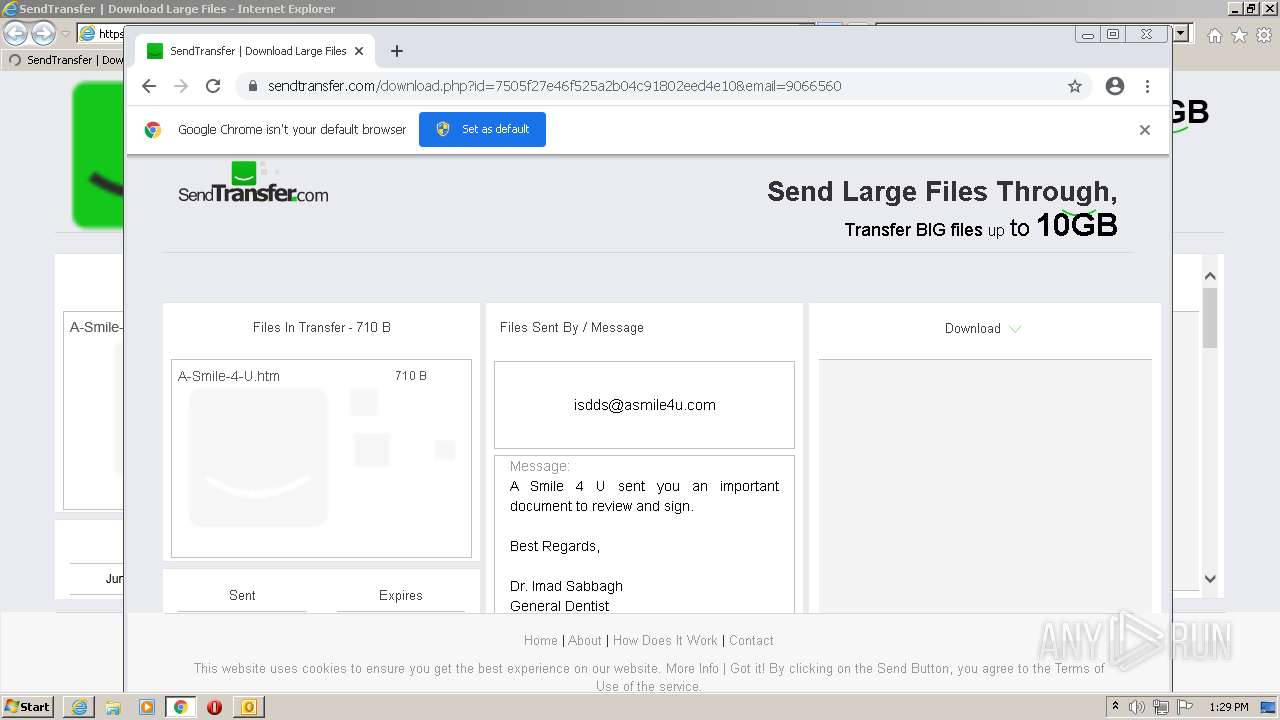
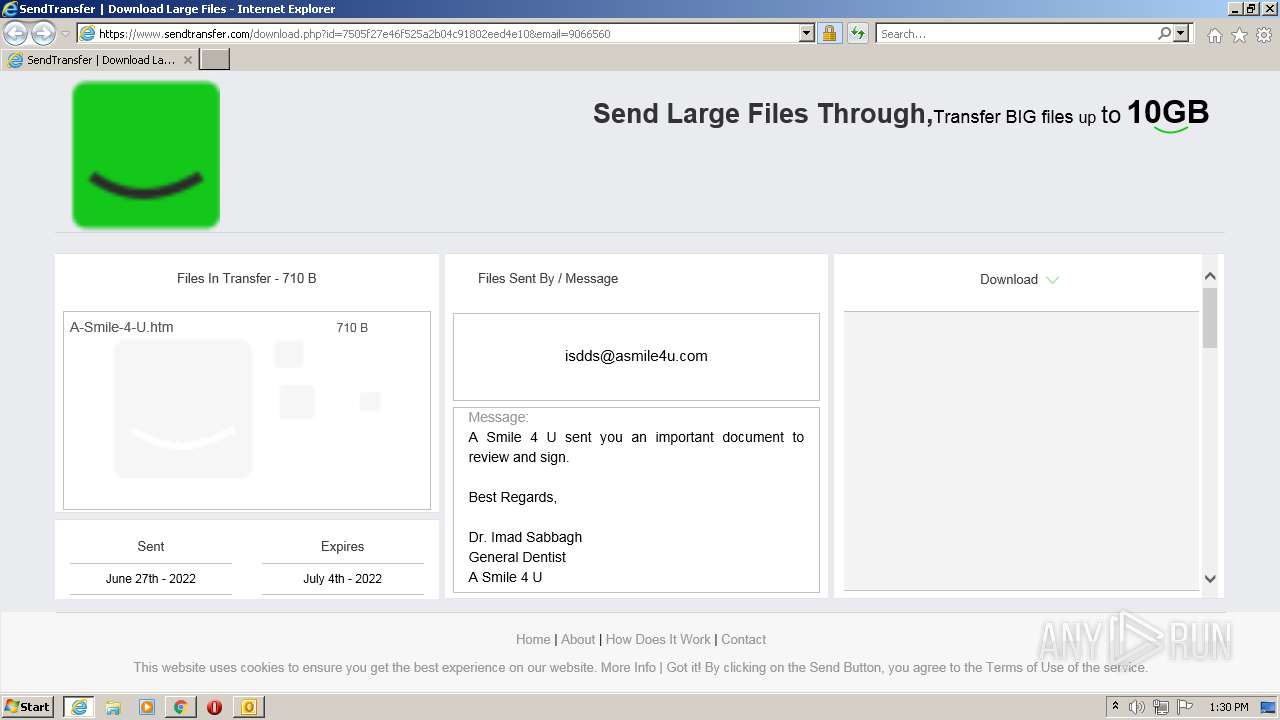
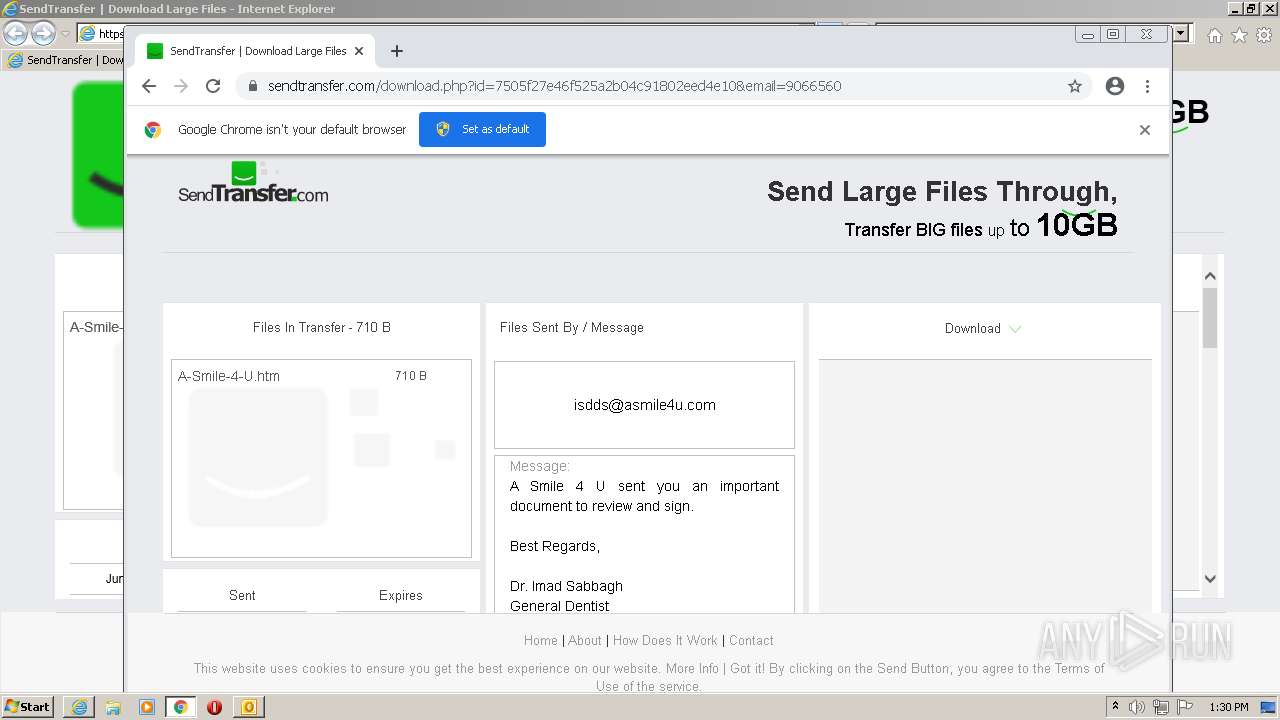
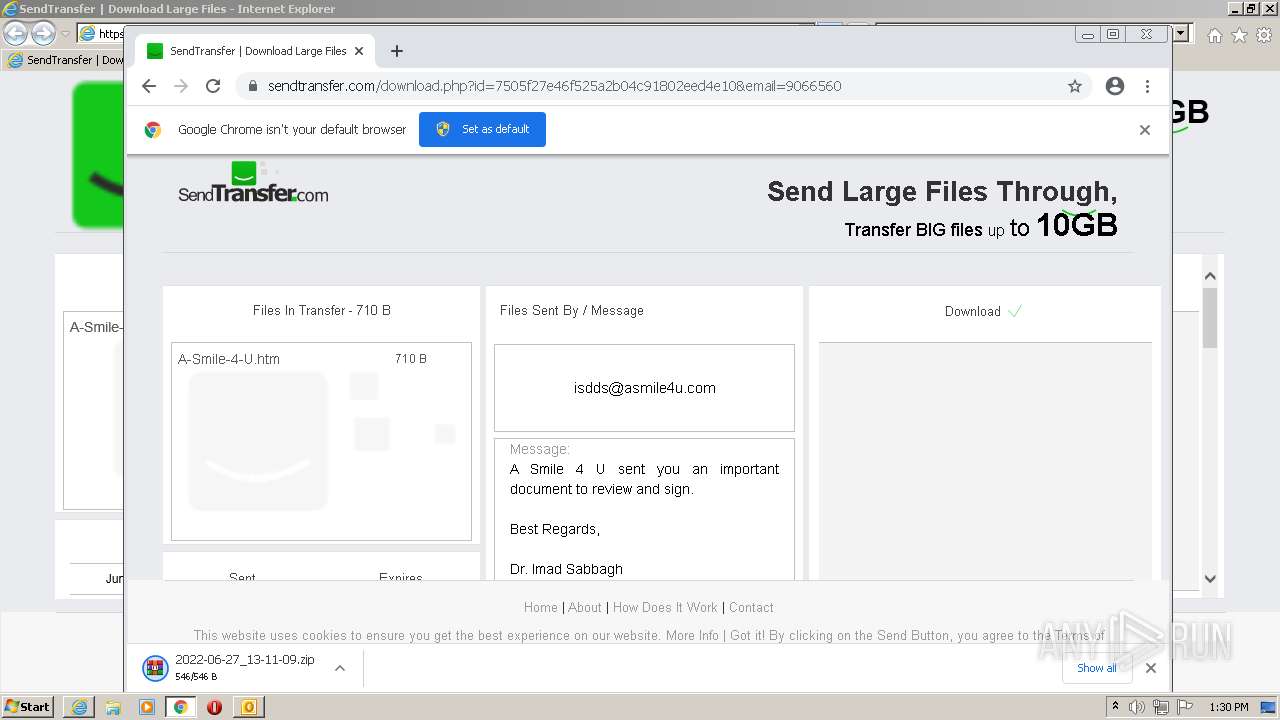
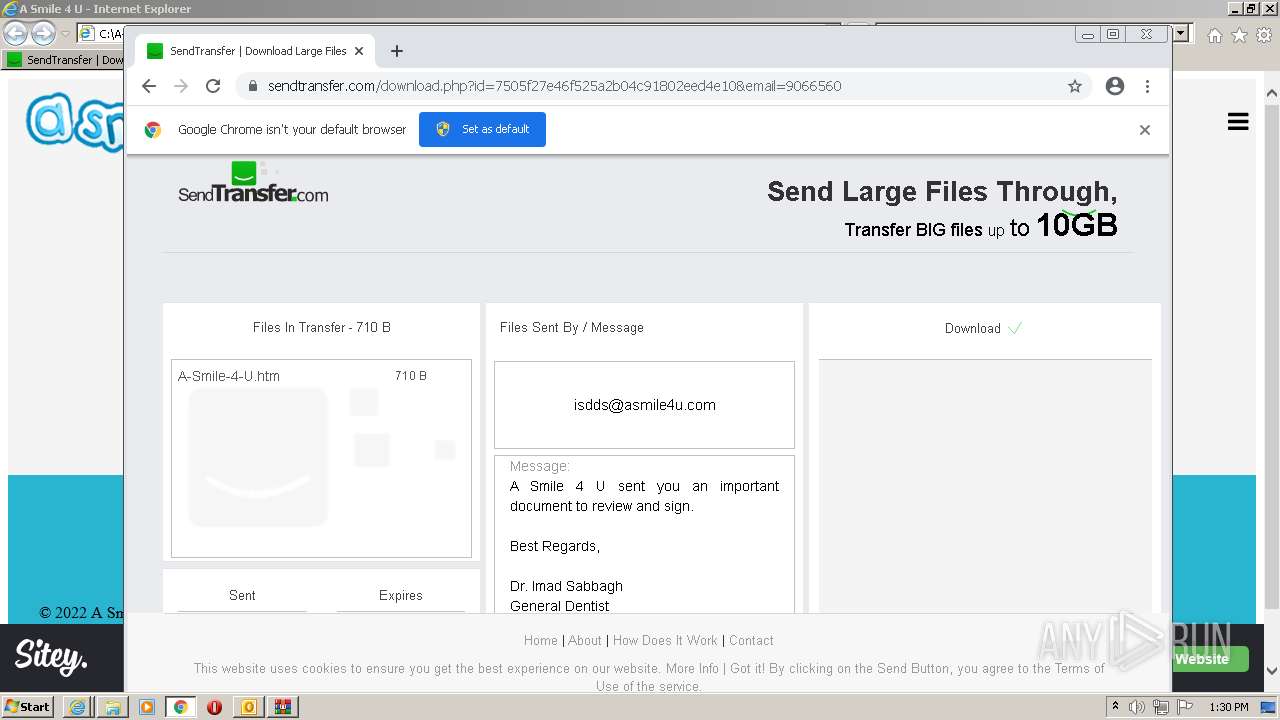
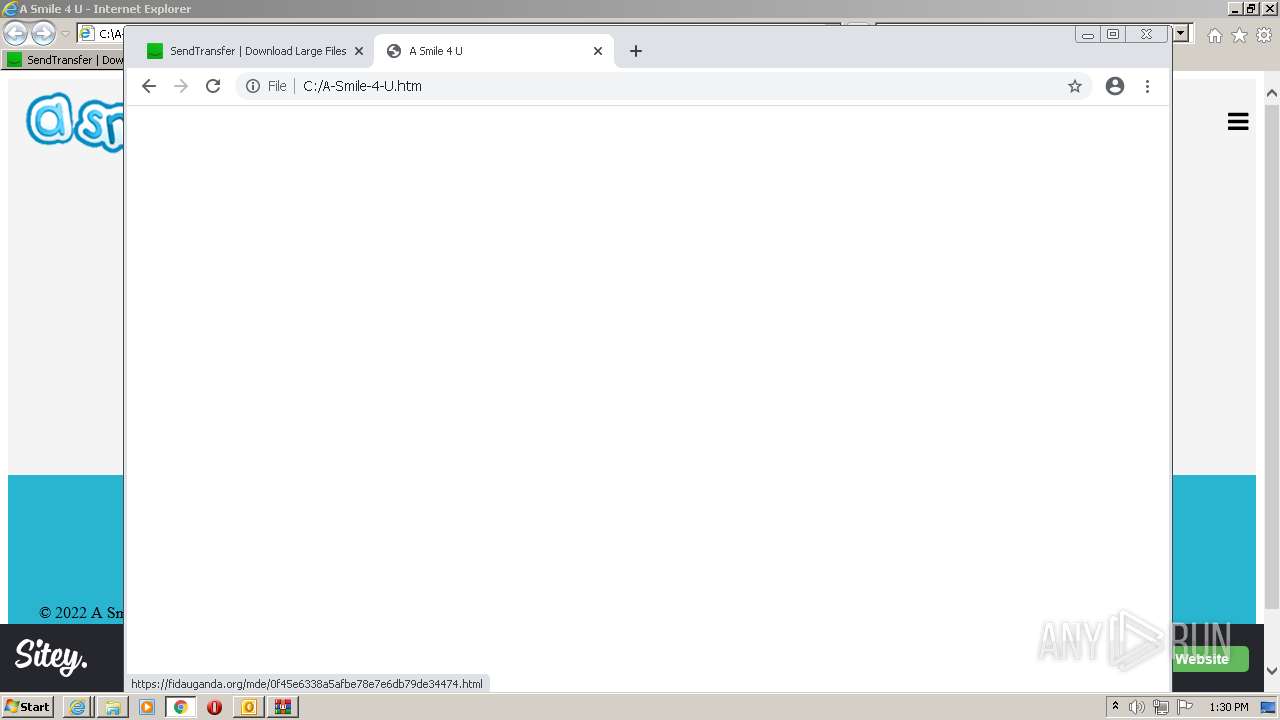
2628 | iexplore.exe | 78.110.213.85:443 | www.sendtransfer.com | METRONET s.r.o. | CZ | unknown |
2628 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
— | — | 8.252.191.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2628 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
2432 | chrome.exe | 142.251.36.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2432 | chrome.exe | 142.251.37.109:443 | accounts.google.com | Google Inc. | US | unknown |
2432 | chrome.exe | 142.251.36.65:443 | clients2.googleusercontent.com | Google Inc. | US | unknown |
2432 | chrome.exe | 142.250.185.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.sendtransfer.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |