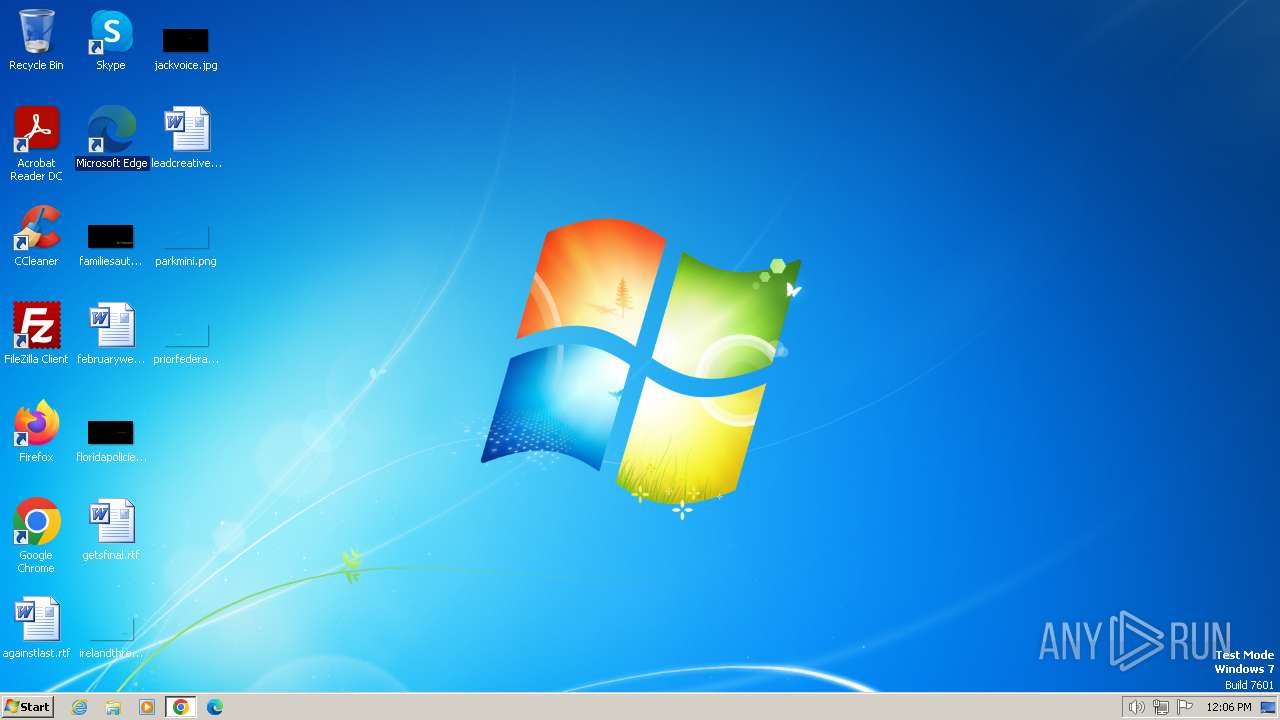
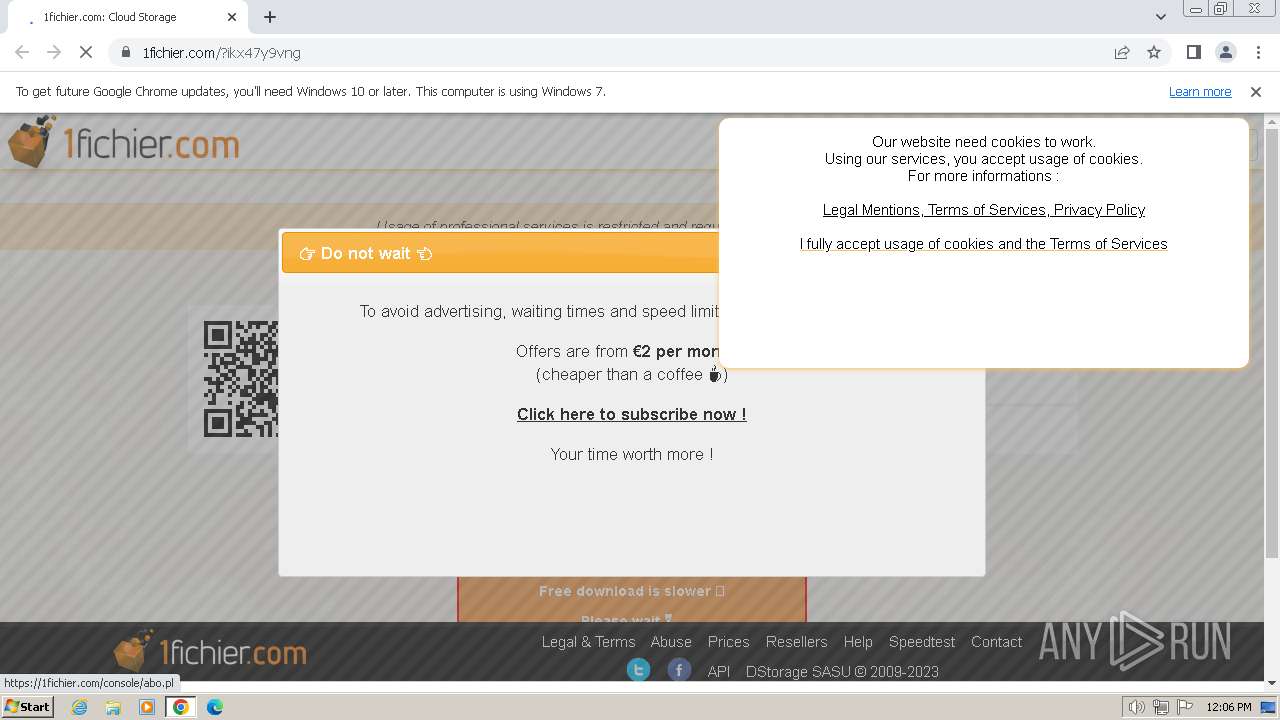
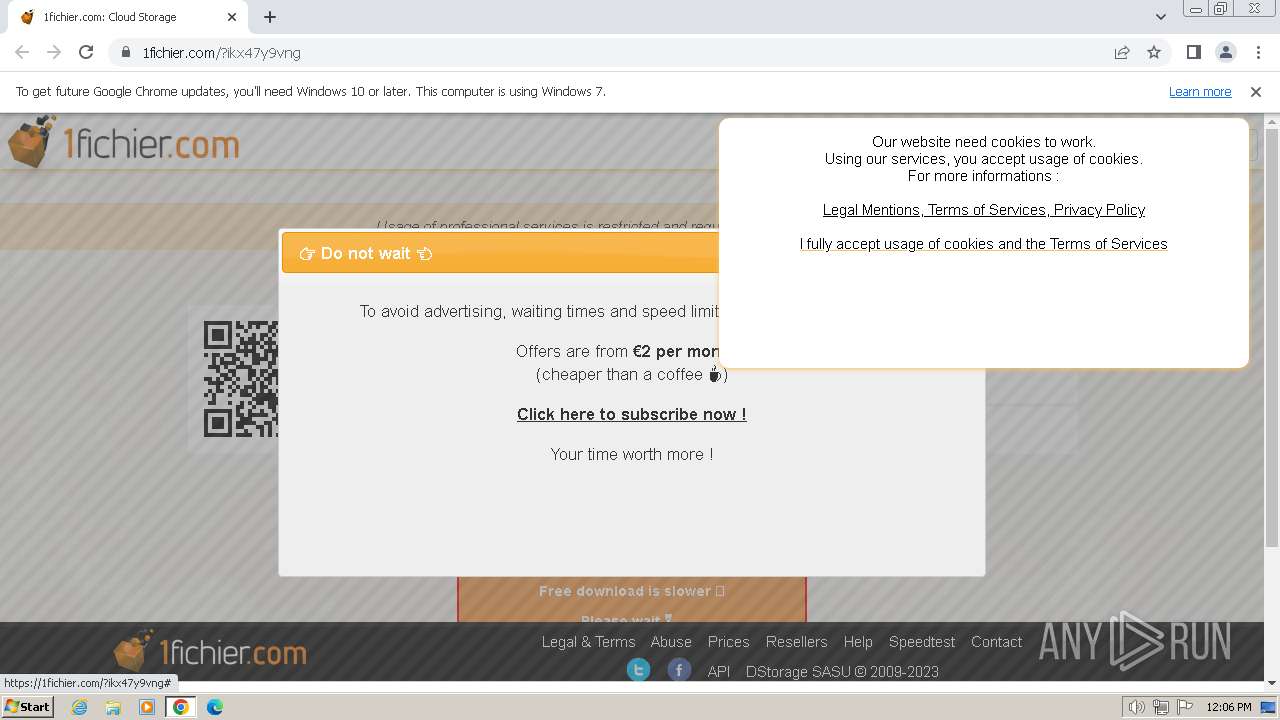
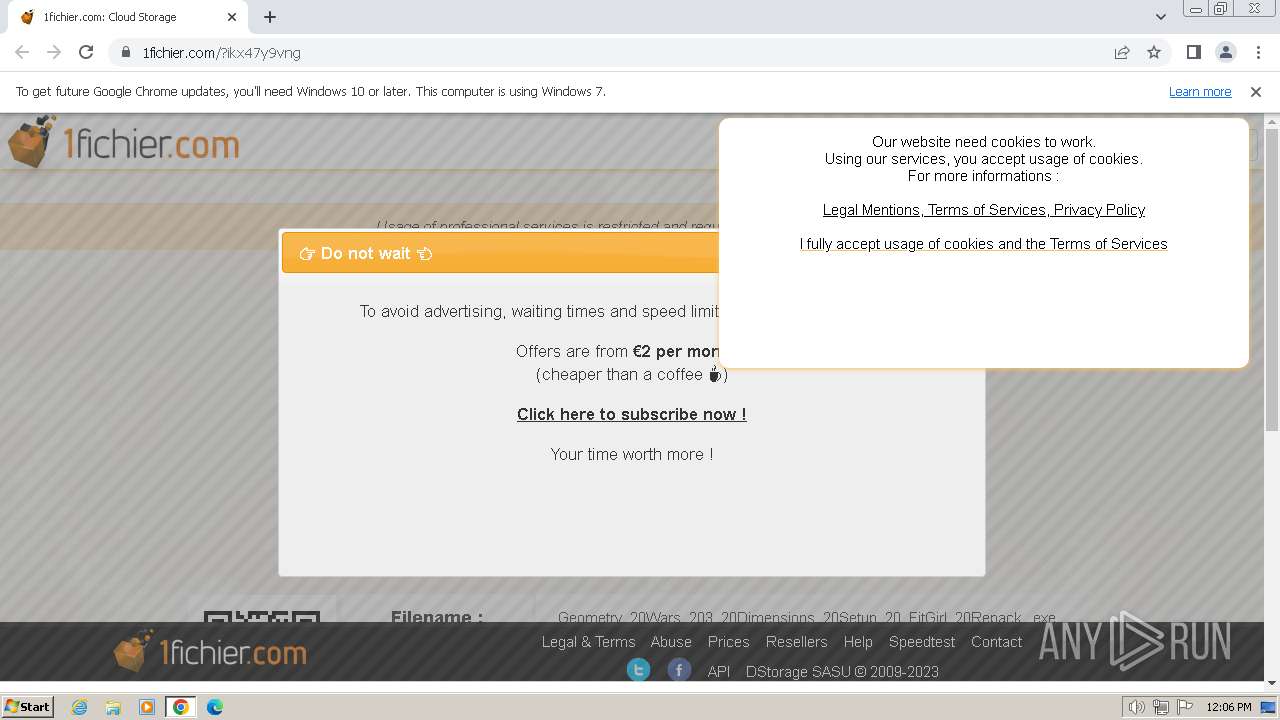
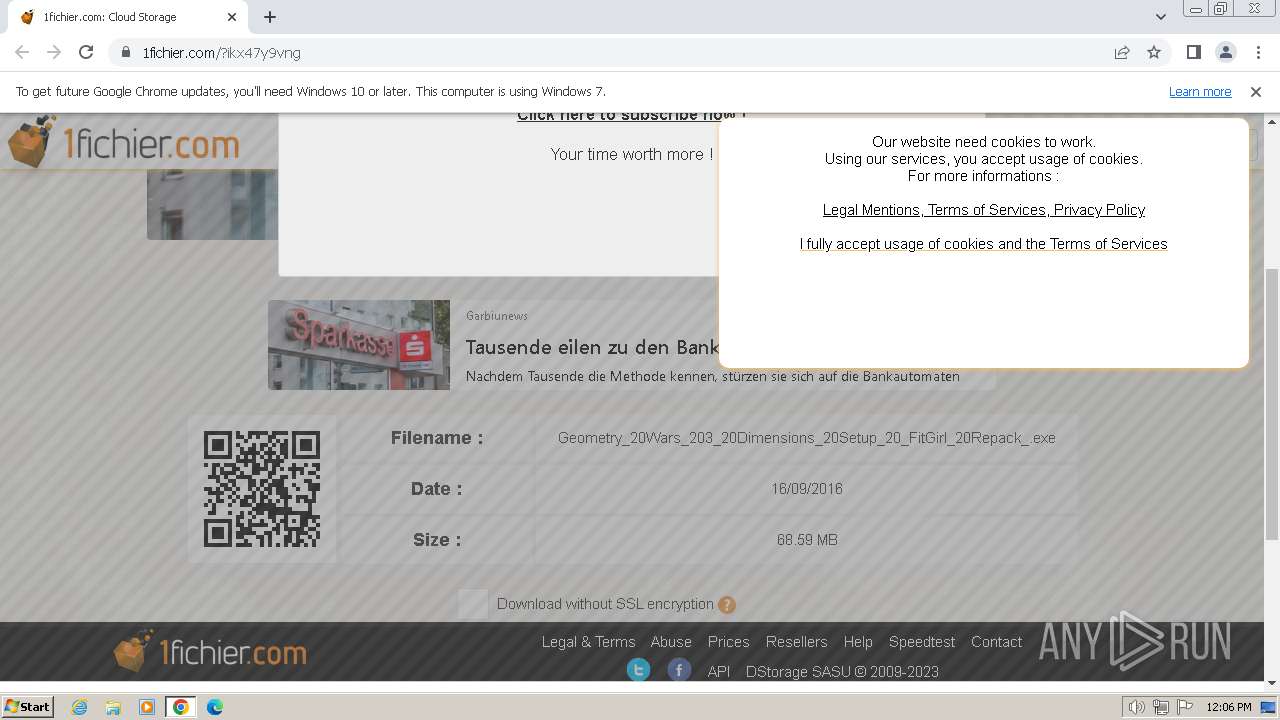
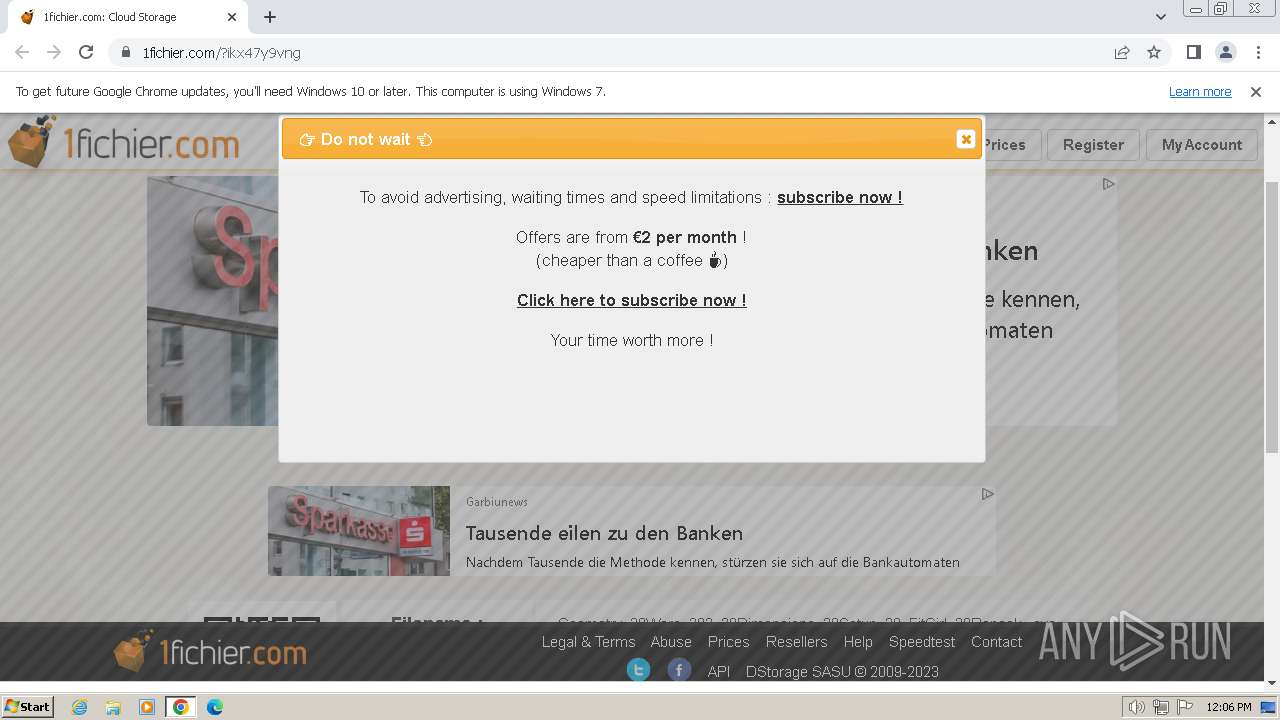
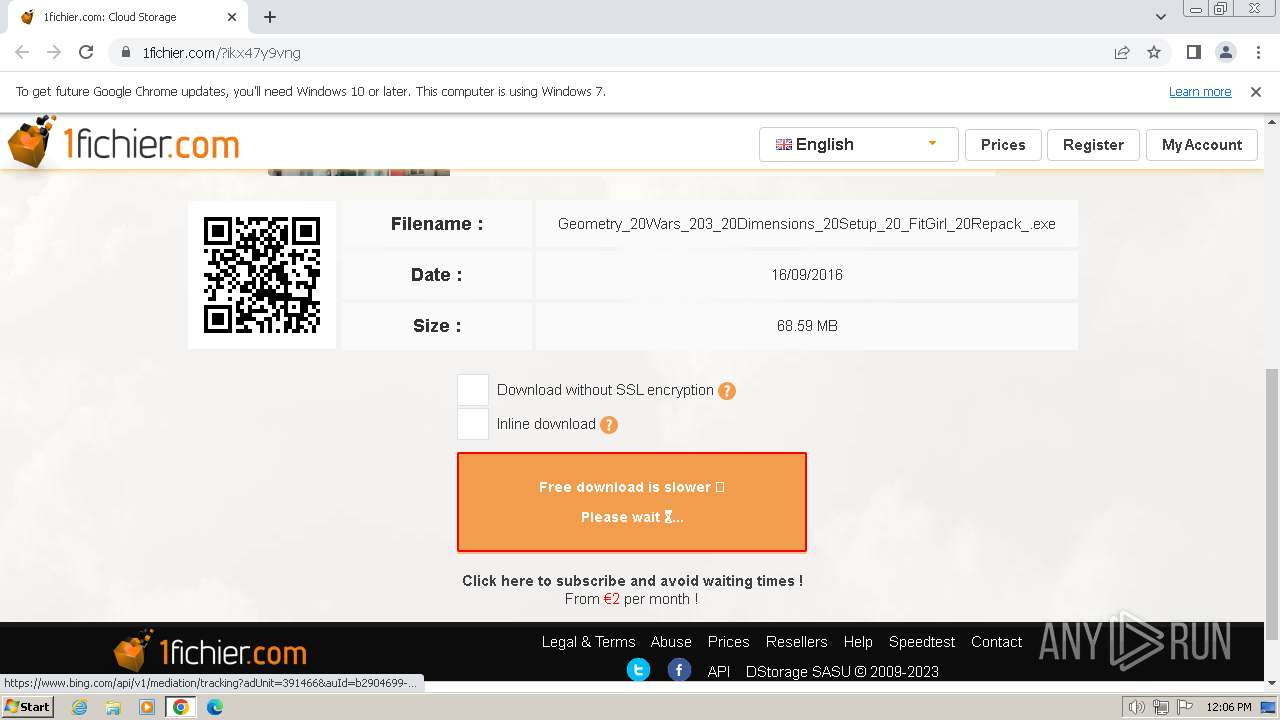
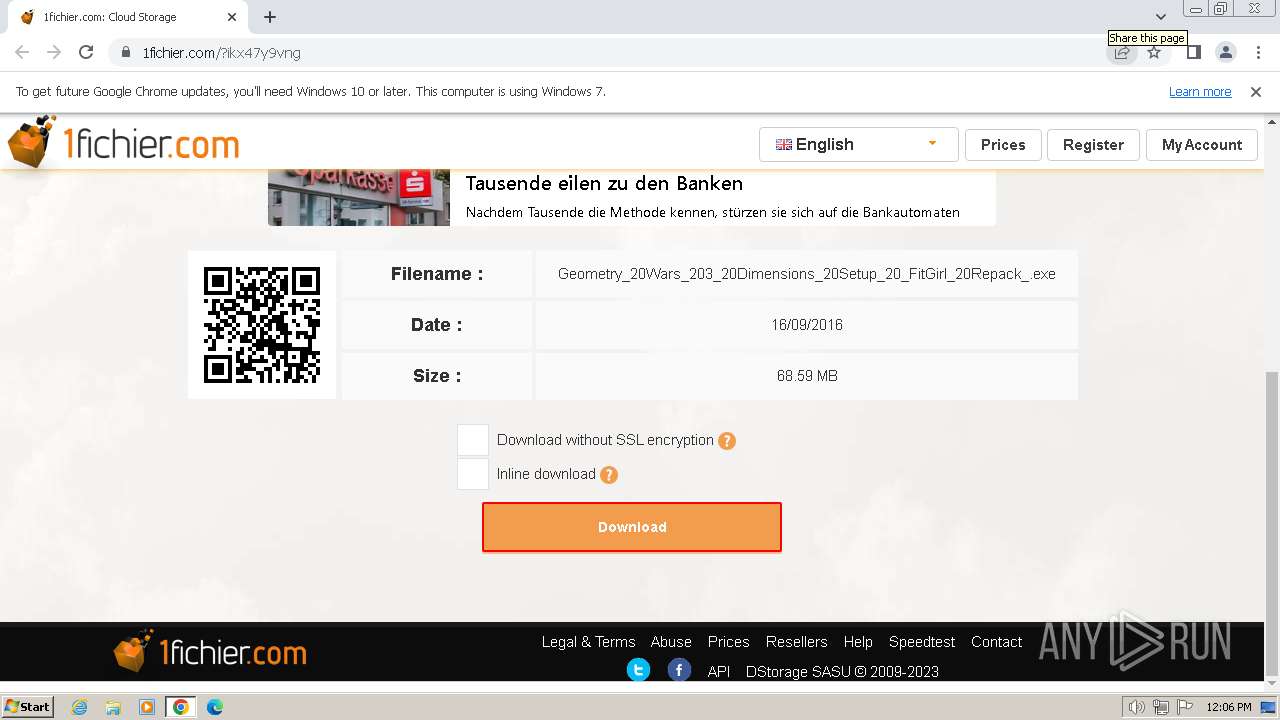
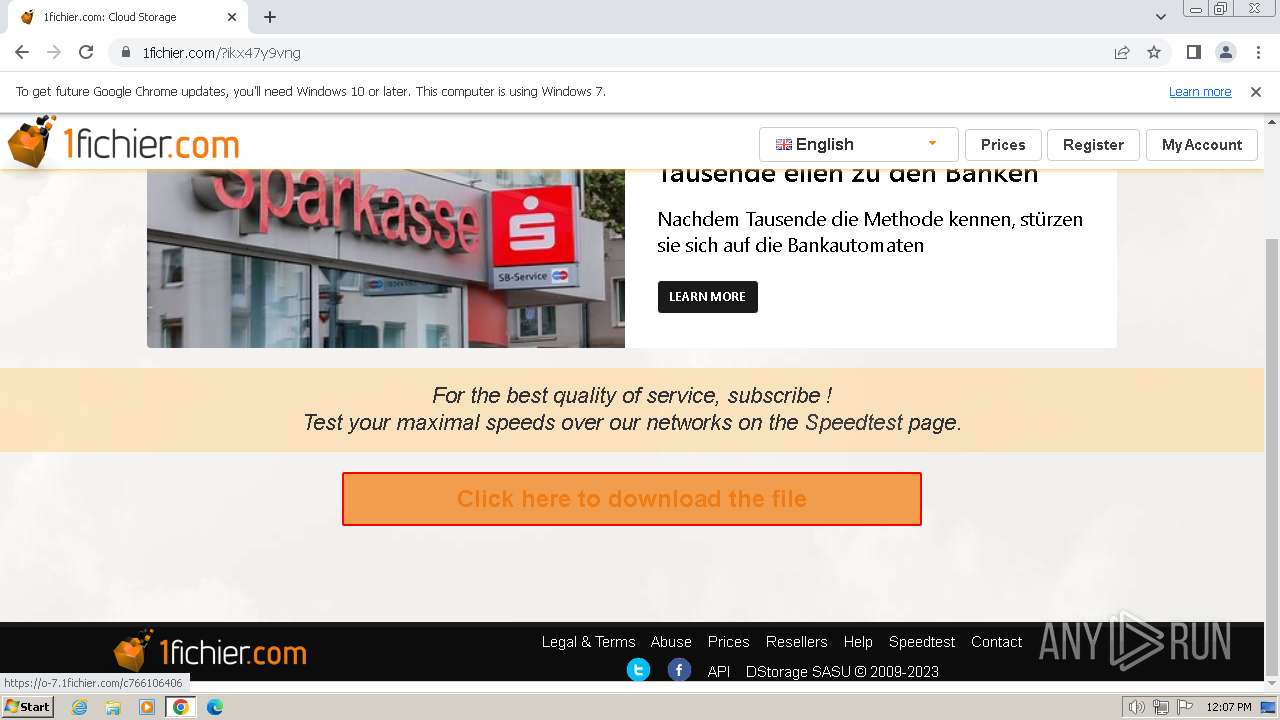
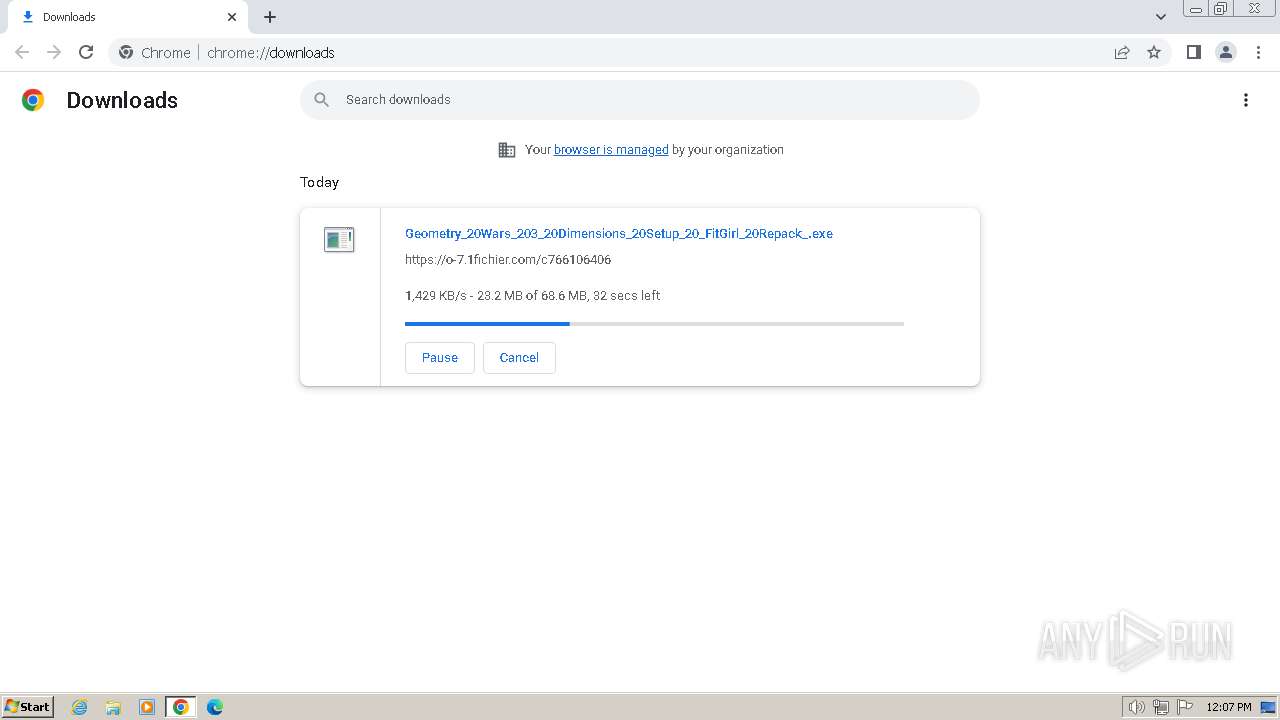
| URL: | https://1fichier.com/?ikx47y9vng |
| Full analysis: | https://app.any.run/tasks/43a92c1a-e34d-499e-9fb8-470746d2d862 |
| Verdict: | Malicious activity |
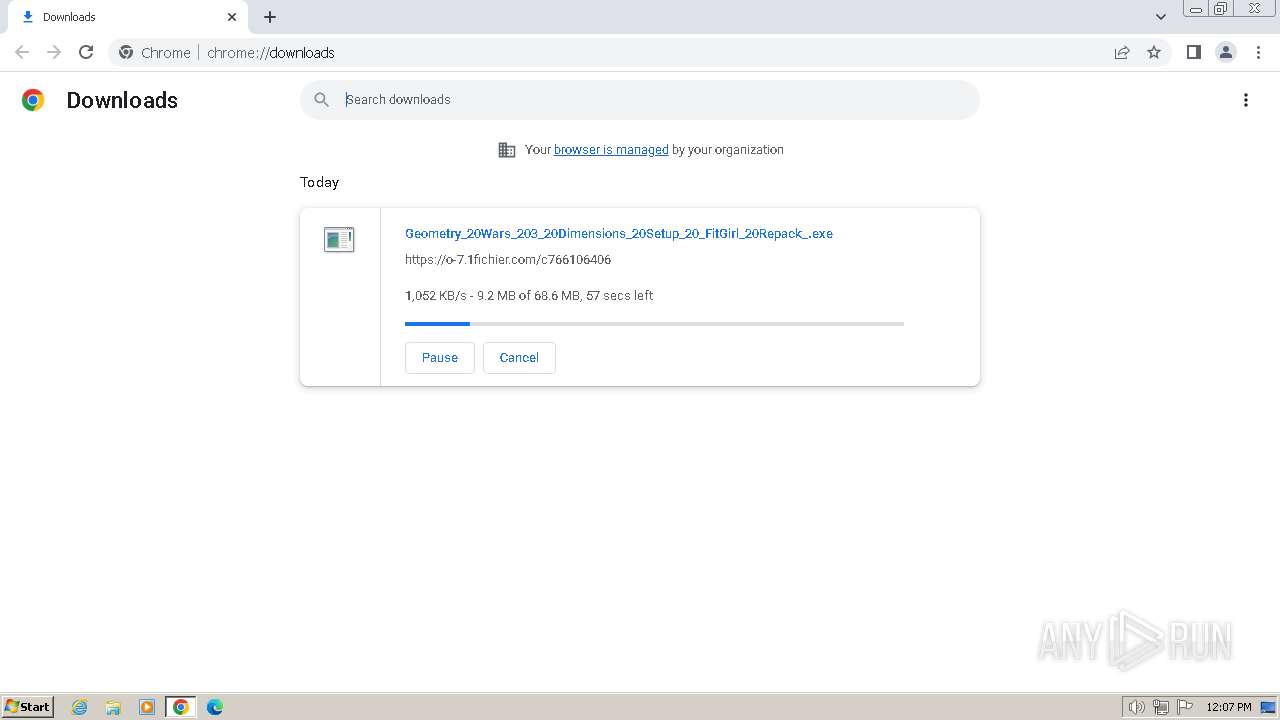
| Analysis date: | January 31, 2024, 12:06:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | ADAE4EE1A3F754D88656D1CE5761CFD7 |
| SHA1: | 7419C38D71B8696456686E8C3CF67DC5F75D03DA |
| SHA256: | 460DEEC1B4BE7C550339F2AA832DD698D5246F28EE829196092C84738EDA98BB |
| SSDEEP: | 3:N8oMSLdySh2:2ohBA |
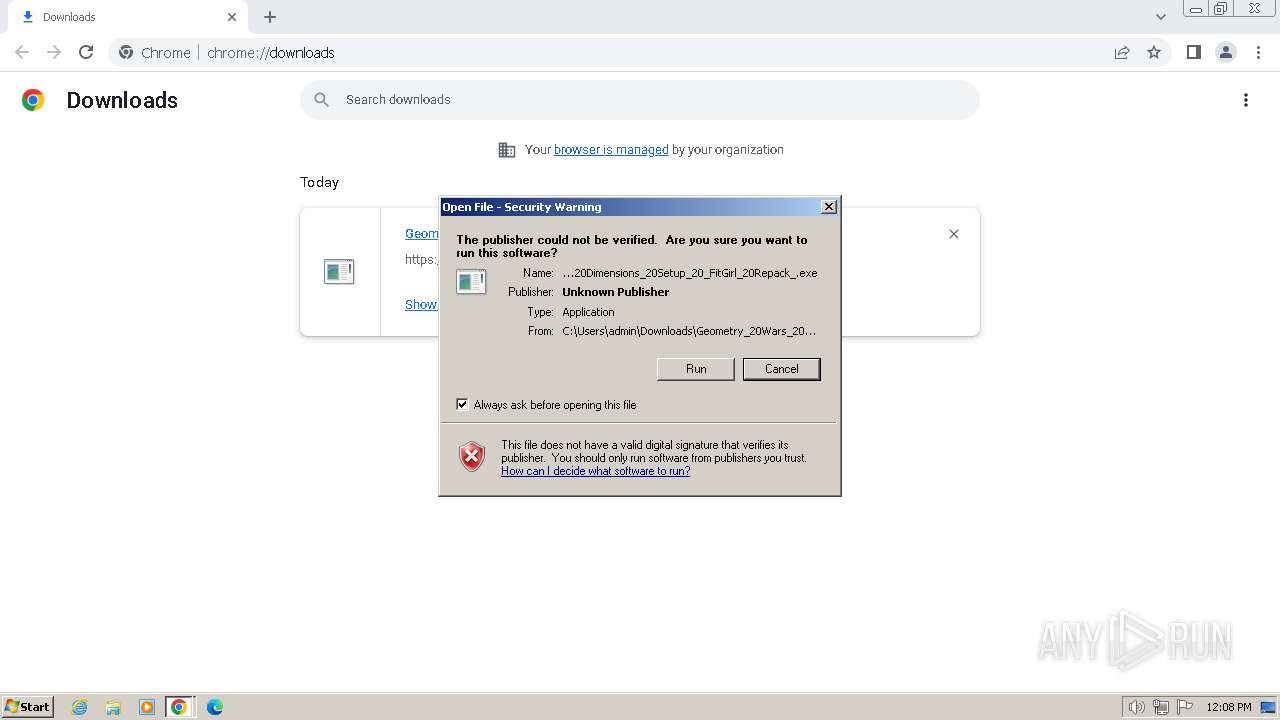
MALICIOUS
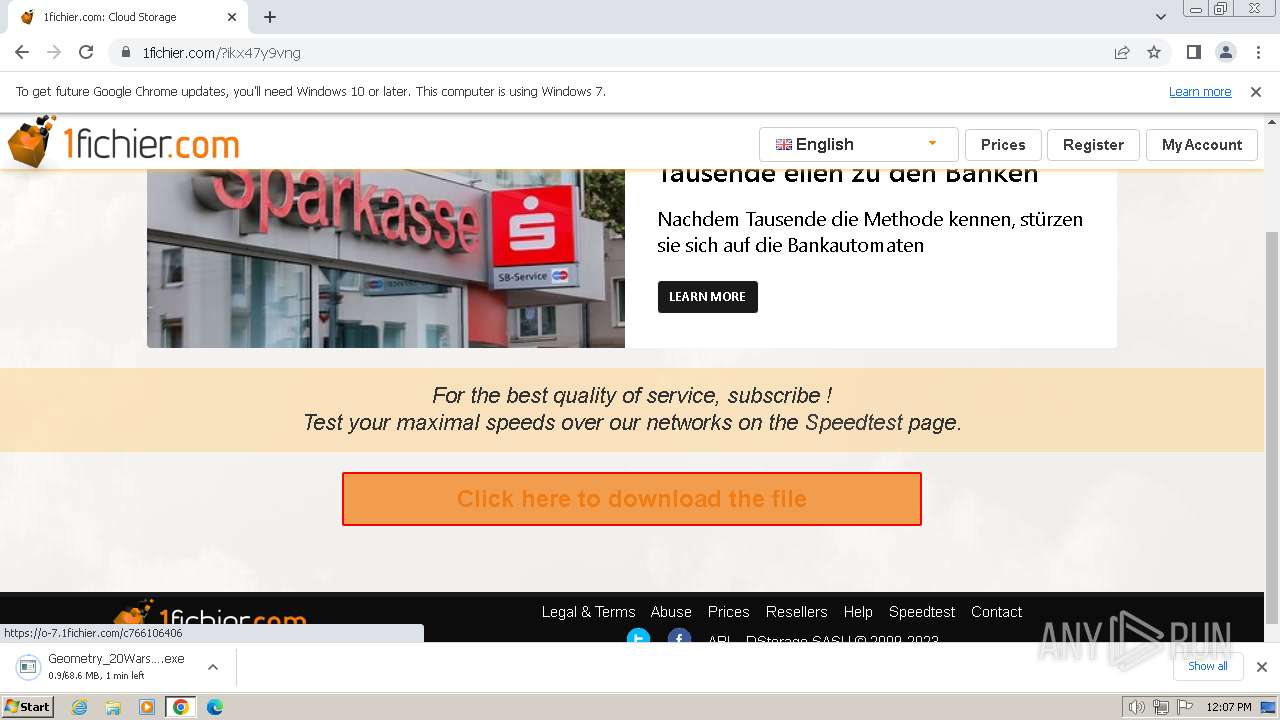
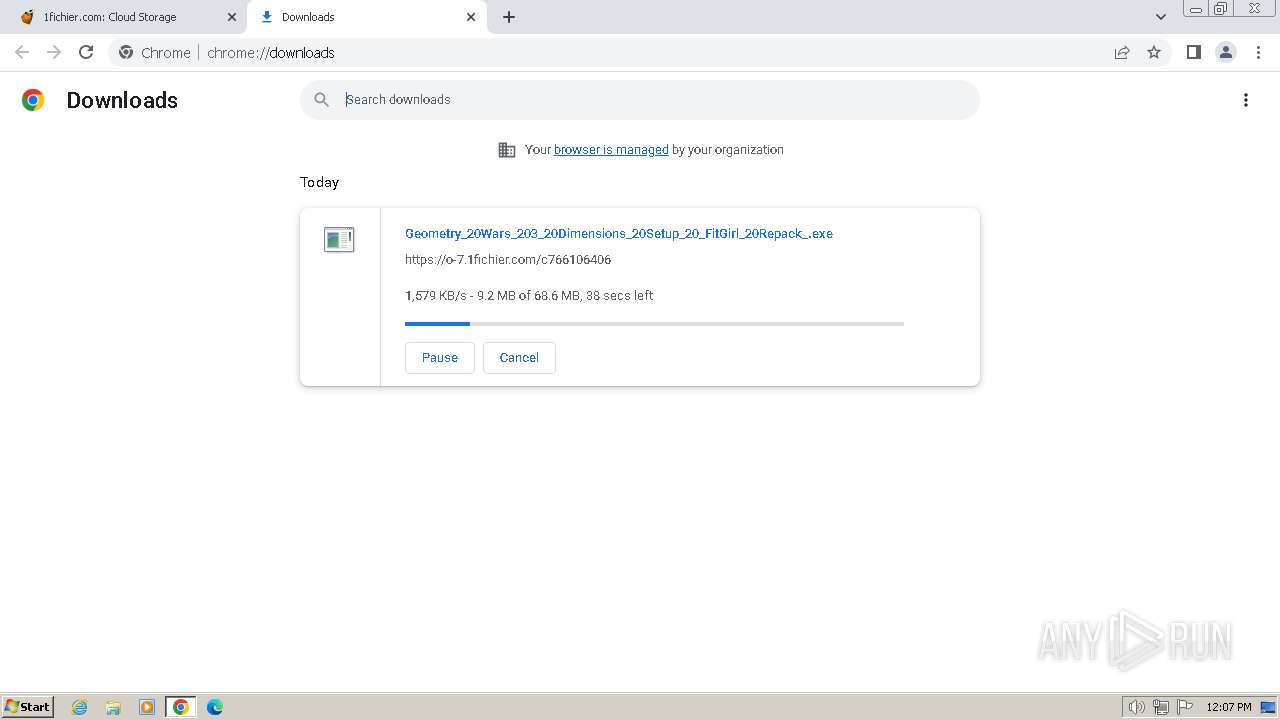
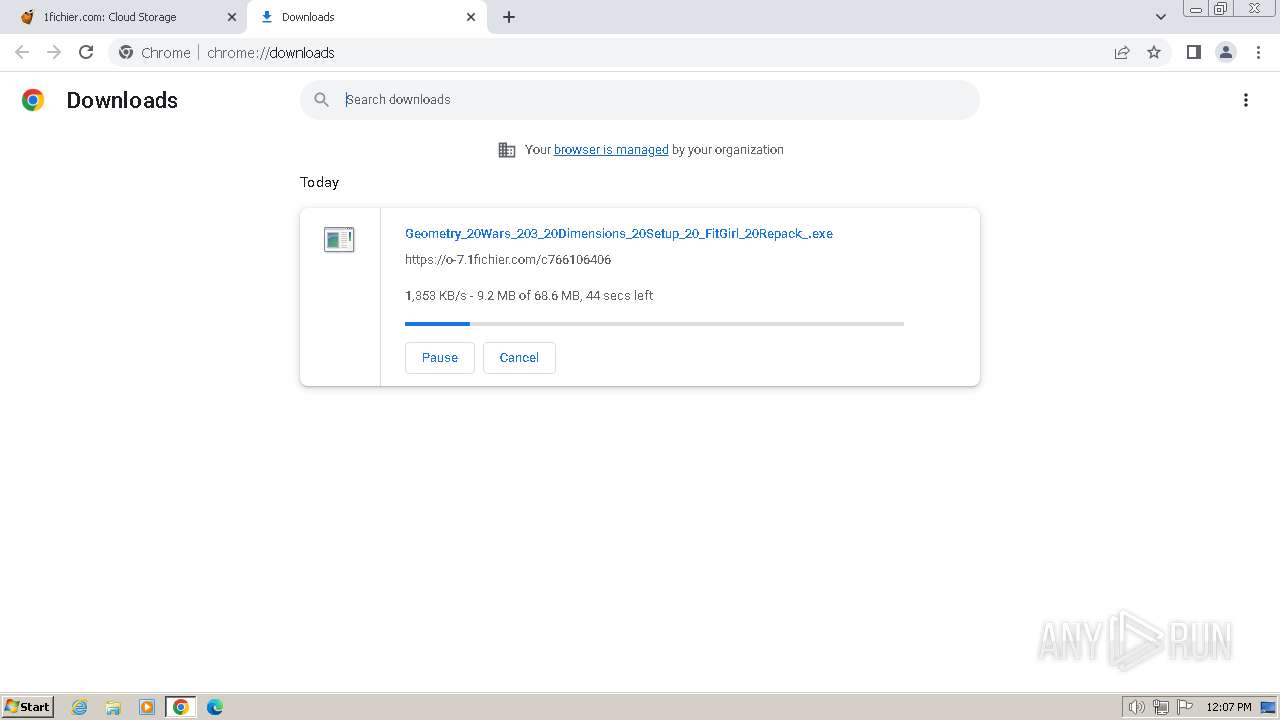
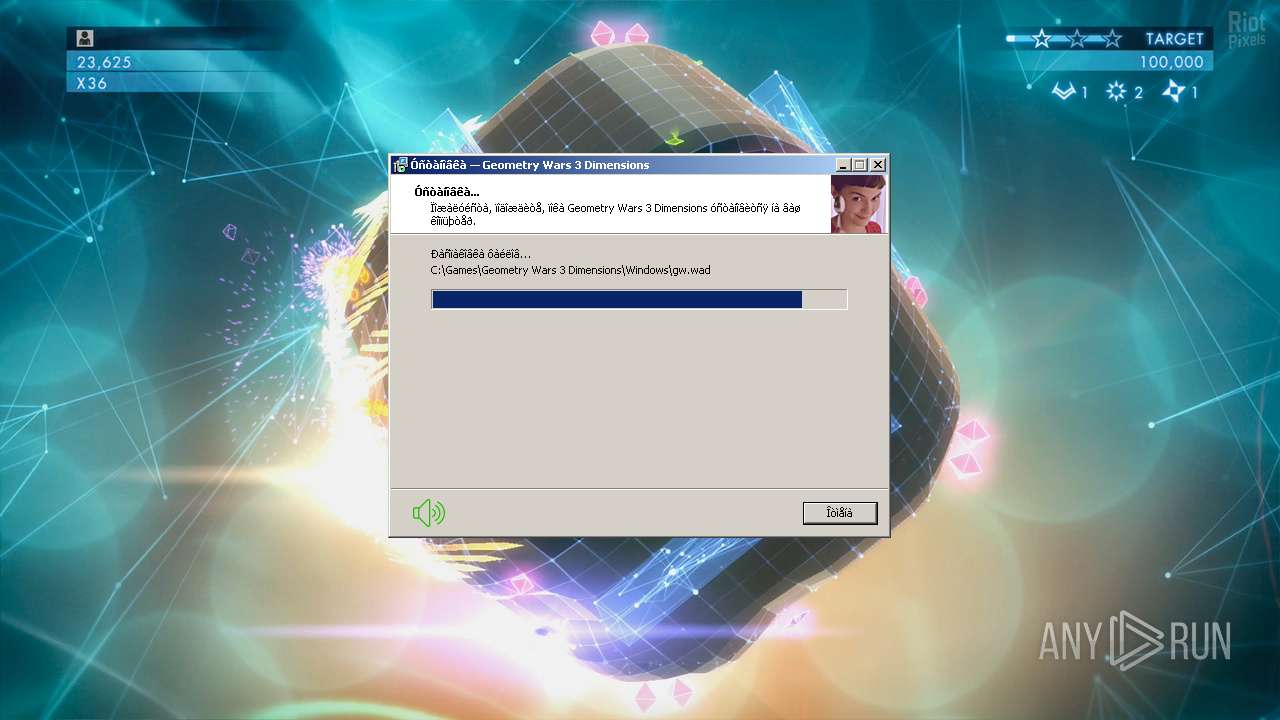
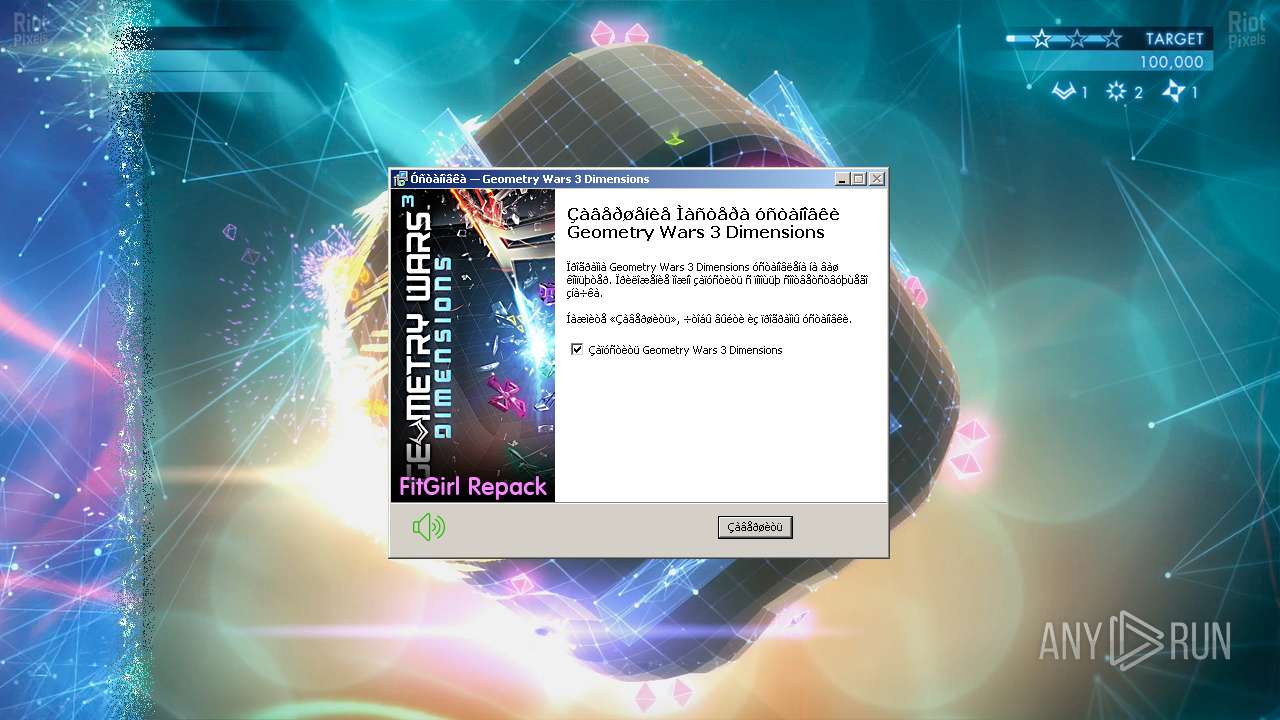
Drops the executable file immediately after the start
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 3824)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 1432)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
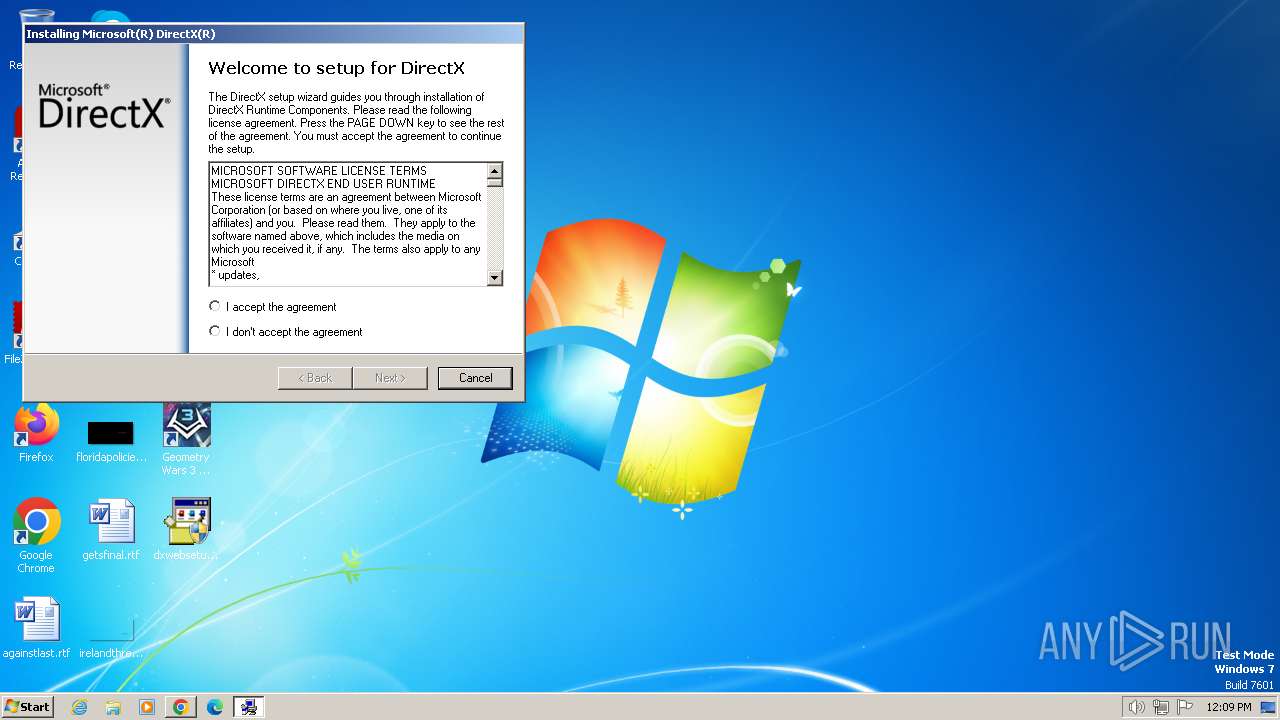
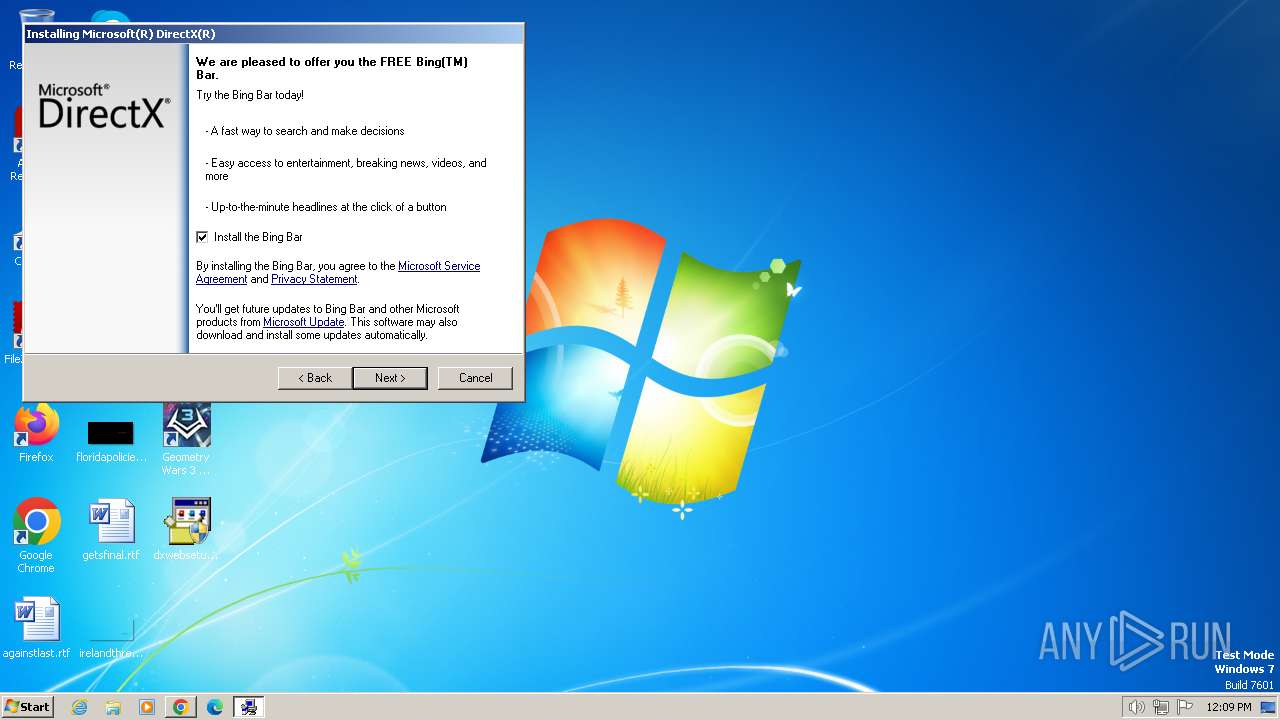
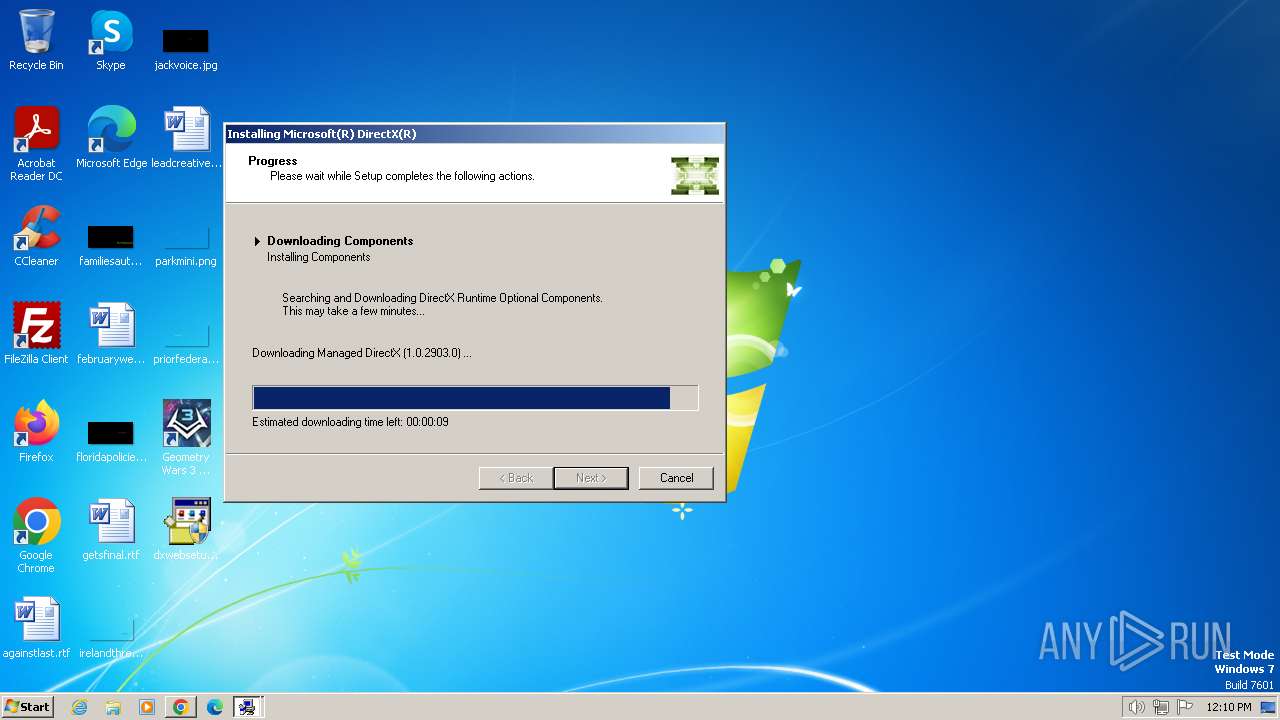
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
Creates a writable file in the system directory
- dxwsetup.exe (PID: 996)
SUSPICIOUS
Executable content was dropped or overwritten
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 3824)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 1432)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
Reads the Windows owner or organization settings
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
Process drops legitimate windows executable
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
Starts a Microsoft application from unusual location
- dxwebsetup.exe (PID: 2760)
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
Reads the Internet Settings
- dxwsetup.exe (PID: 996)
Reads security settings of Internet Explorer
- dxwsetup.exe (PID: 996)
Executes as Windows Service
- VSSVC.exe (PID: 3584)
Reads settings of System Certificates
- dxwsetup.exe (PID: 996)
Checks Windows Trust Settings
- dxwsetup.exe (PID: 996)
Searches for installed software
- dllhost.exe (PID: 3716)
- dxwsetup.exe (PID: 996)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 1380)
Reads the computer name
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3768)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
- wmpnscfg.exe (PID: 3976)
- Launcher.exe (PID: 3732)
- dxwsetup.exe (PID: 996)
Checks supported languages
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3768)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 3824)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 1432)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
- wmpnscfg.exe (PID: 3976)
- Launcher.exe (PID: 3732)
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
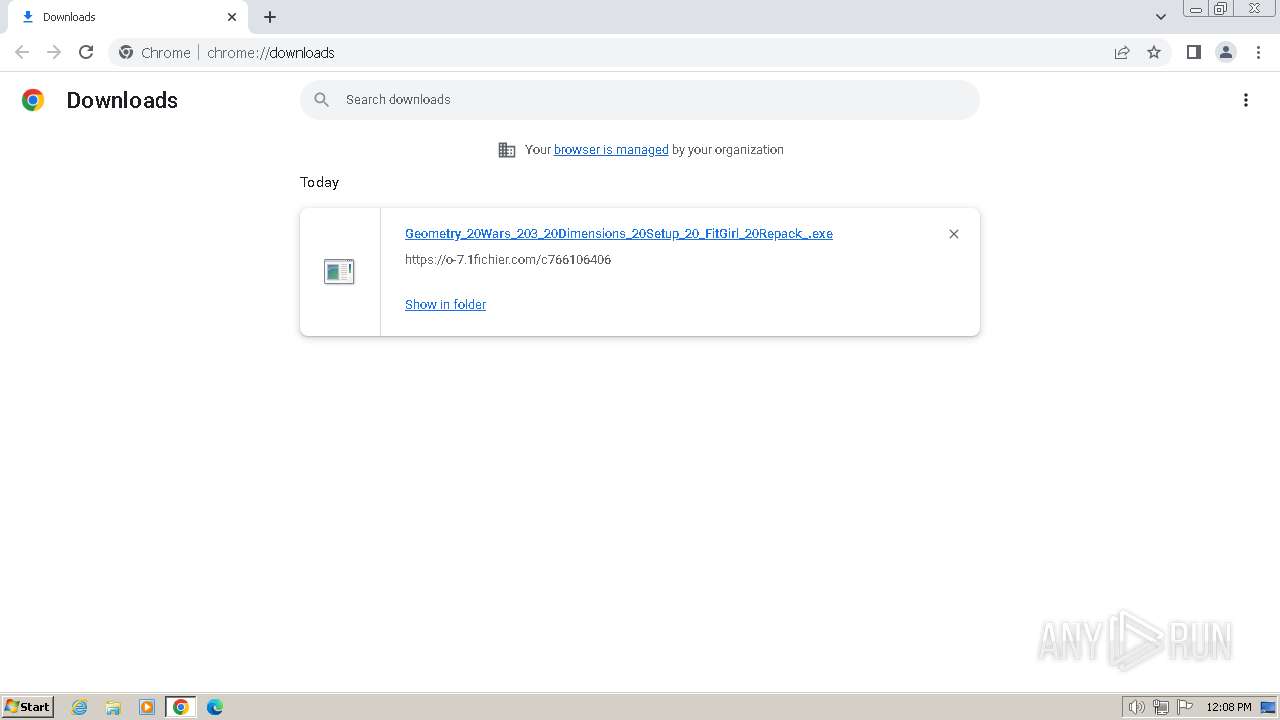
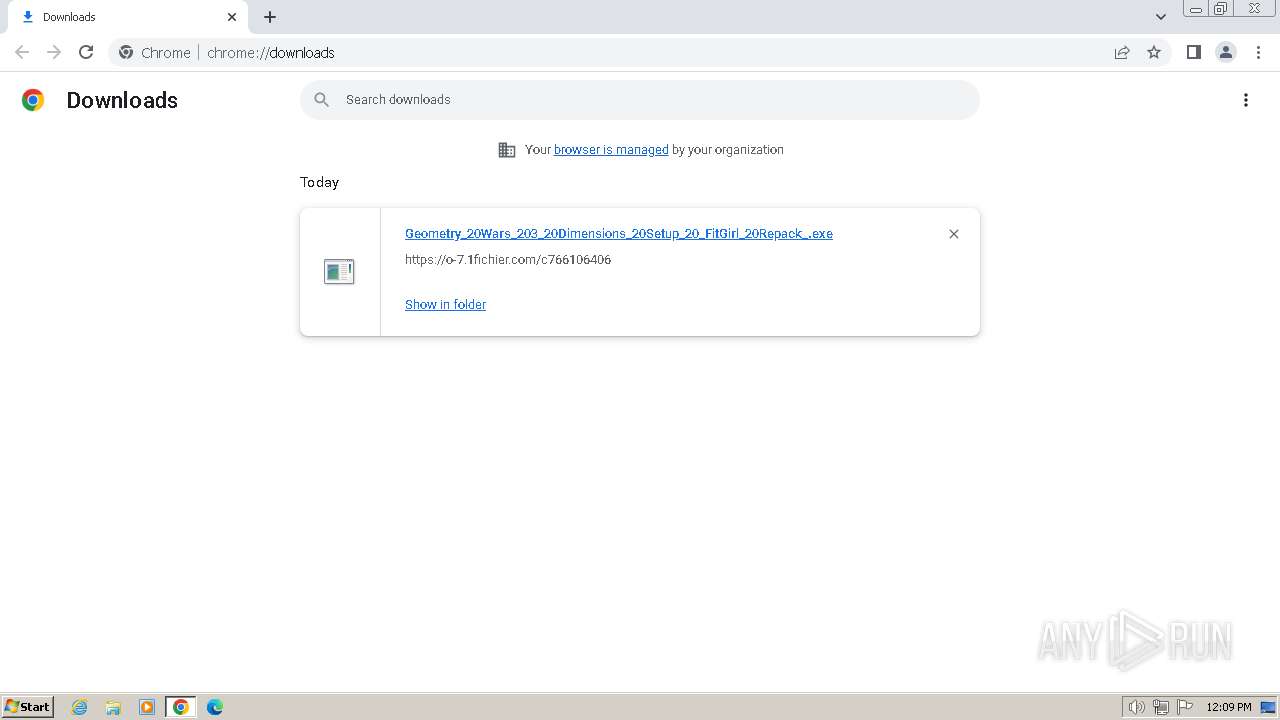
The process uses the downloaded file
- chrome.exe (PID: 1380)
- chrome.exe (PID: 1816)
Drops the executable file immediately after the start
- chrome.exe (PID: 1380)
Create files in a temporary directory
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 3824)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe (PID: 1432)
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
- dxwebsetup.exe (PID: 3020)
- dxwsetup.exe (PID: 996)
Application launched itself
- chrome.exe (PID: 1380)
Manual execution by a user
- dxwebsetup.exe (PID: 3020)
- wmpnscfg.exe (PID: 3976)
- dxwebsetup.exe (PID: 2760)
Creates files in the program directory
- Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp (PID: 3096)
Checks proxy server information
- dxwsetup.exe (PID: 996)
Reads the machine GUID from the registry
- dxwsetup.exe (PID: 996)
Creates files or folders in the user directory
- dxwsetup.exe (PID: 996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
36
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=3736 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 996 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | dxwebsetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1840 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://1fichier.com/?ikx47y9vng" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\Downloads\Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe" /SPAWNWND=$17014C /NOTIFYWND=$D0162 | C:\Users\admin\Downloads\Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.exe | Geometry_20Wars_203_20Dimensions_20Setup_20_FitGirl_20Repack_.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Geometry Wars 3 Dimensions Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=2112 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1524 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3348 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1300 --field-trial-handle=860,i,11523477776586508599,13250136904640288745,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
12 694
Read events
12 403
Write events
284
Delete events
7
Modification events
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
77
Suspicious files
449
Text files
55
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF163676.TMP | — | |
MD5:— | SHA256:— | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF163686.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF163cee.TMP | — | |
MD5:— | SHA256:— | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 1380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1649cf.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
103
TCP/UDP connections
83
DNS requests
94
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
996 | dxwsetup.exe | GET | 302 | 23.53.232.166:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxupdate.cab | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 5.34 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.84 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.82 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 9.22 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpbursl4n2ooxdpheelb266ngrq_847/efniojlnjndmcbiieegkicadnoecjjef_847_all_acyb3rjoplcedax3agimuwrqlxrq.crx3 | unknown | binary | 9.22 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpbursl4n2ooxdpheelb266ngrq_847/efniojlnjndmcbiieegkicadnoecjjef_847_all_acyb3rjoplcedax3agimuwrqlxrq.crx3 | unknown | binary | 17.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpbursl4n2ooxdpheelb266ngrq_847/efniojlnjndmcbiieegkicadnoecjjef_847_all_acyb3rjoplcedax3agimuwrqlxrq.crx3 | unknown | binary | 87.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpbursl4n2ooxdpheelb266ngrq_847/efniojlnjndmcbiieegkicadnoecjjef_847_all_acyb3rjoplcedax3agimuwrqlxrq.crx3 | unknown | binary | 44.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2380 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
1380 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2380 | chrome.exe | 5.39.224.140:443 | 1fichier.com | DSTORAGE s.a.s. | FR | unknown |
2380 | chrome.exe | 5.39.224.141:443 | img.1fichier.com | DSTORAGE s.a.s. | FR | unknown |
2380 | chrome.exe | 18.154.84.67:443 | tags.refinery89.com | — | US | unknown |
2380 | chrome.exe | 104.16.96.121:443 | t.seedtag.com | CLOUDFLARENET | — | unknown |
2380 | chrome.exe | 195.181.170.18:443 | cdn.consentmanager.net | Datacamp Limited | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
1fichier.com |
| whitelisted |
img.1fichier.com |
| unknown |
tags.refinery89.com |
| whitelisted |
t.seedtag.com |
| unknown |
cdn.consentmanager.net |
| malicious |
a.delivery.consentmanager.net |
| unknown |
ib.adnxs.com |
| whitelisted |
onetag-sys.com |
| whitelisted |
shb.richaudience.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |