| File name: | wsaprov.dll |
| Full analysis: | https://app.any.run/tasks/6697aa7c-df3d-41a6-846e-fba88ab876b1 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 14:54:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 9191D165F4F103067E3A42D879CCFEEB |
| SHA1: | 09875C0626801C371FF26613082285FE43C2E82A |
| SHA256: | 460446DB6EBE7A159BE2535C2C1C6738B6C552B64420312F55C25F2530BE7AC1 |
| SSDEEP: | 6144:Kz9CDwTssne5buWRFTXn4b1o+U6pijPZcTlp:K5QxsehuWPLn4o+UNjxcT |
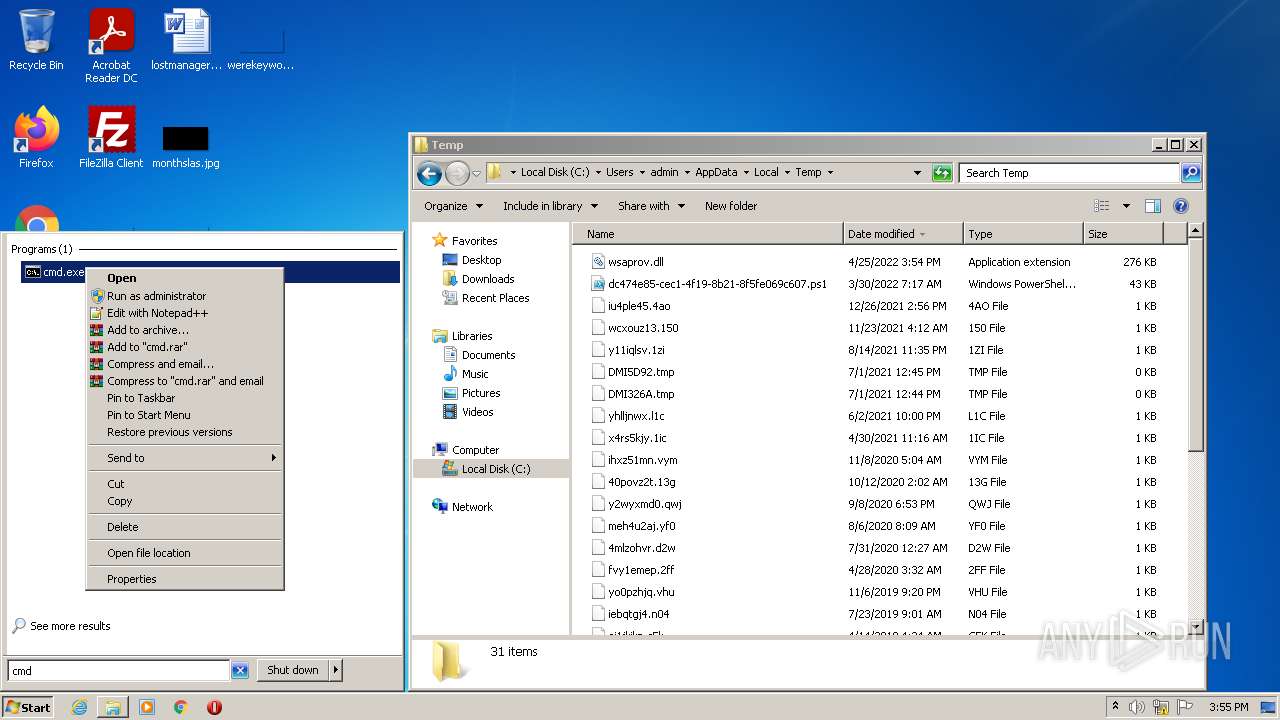
MALICIOUS
Loads dropped or rewritten executable
- Explorer.EXE (PID: 1464)
Drops executable file immediately after starts
- Explorer.EXE (PID: 1464)
Runs app for hidden code execution
- Explorer.EXE (PID: 1464)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 2788)
- cmd.exe (PID: 3532)
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 1464)
- cmd.exe (PID: 2788)
- cmd.exe (PID: 3532)
Executable content was dropped or overwritten
- Explorer.EXE (PID: 1464)
Drops a file with a compile date too recent
- Explorer.EXE (PID: 1464)
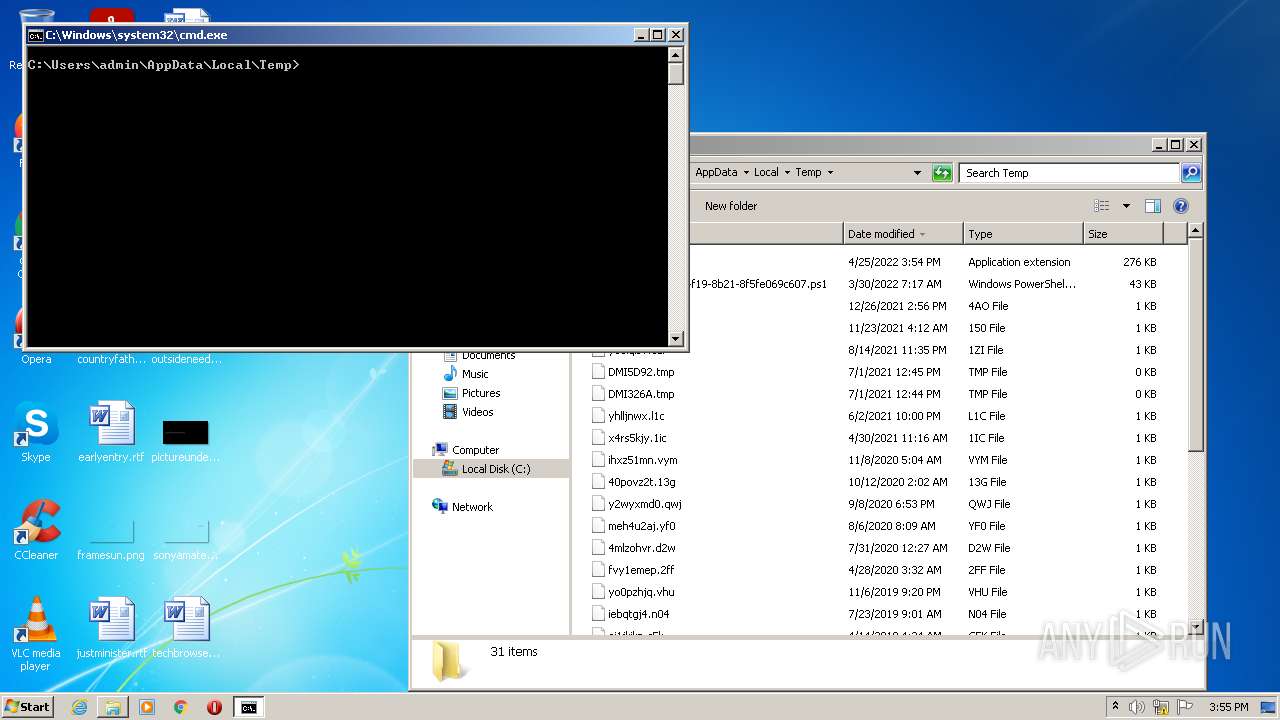
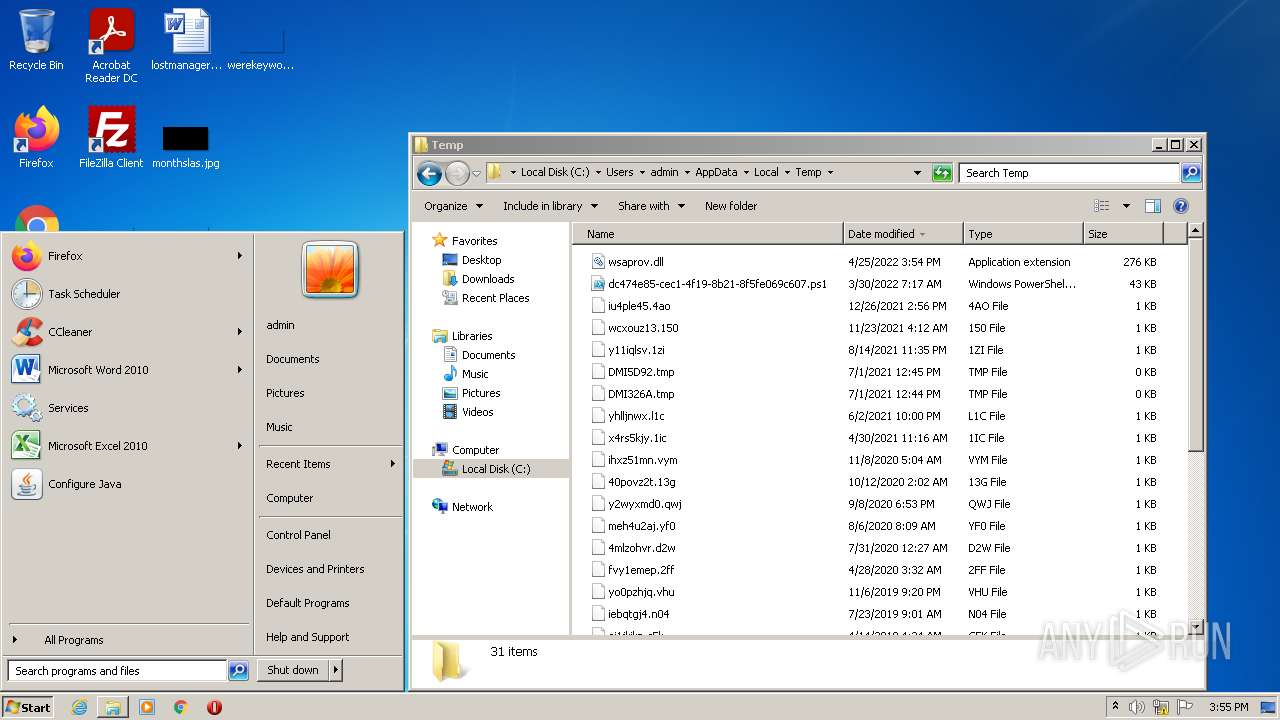
Starts CMD.EXE for commands execution
- Explorer.EXE (PID: 1464)
INFO
Loads main object executable
- rundll32.exe (PID: 1928)
Reads CPU info
- Explorer.EXE (PID: 1464)
Checks supported languages
- rundll32.exe (PID: 1928)
- rundll32.exe (PID: 1856)
- Explorer.EXE (PID: 1464)
- rundll32.exe (PID: 2436)
Reads the computer name
- rundll32.exe (PID: 1928)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 1464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x13b0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 23040 |
| CodeSize: | 258048 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:12:30 10:04:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Dec-2021 09:04:46 |
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Dec-2021 09:04:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003EE20 | 0x0003F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49035 |
.rdata | 0x00040000 | 0x000015B8 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.69703 |
.data | 0x00042000 | 0x00002F58 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.48625 |
.tls | 0x00045000 | 0x00000008 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.reloc | 0x00046000 | 0x0000145C | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.3929 |
Imports
KERNEL32.dll |
WS2_32.dll |
msvcrt.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
0 | 0x00000000 | |
Main@16 | 1 | 0x0003FBB0 |
ServiceMain@8 | 2 | 0x0003D4B0 |
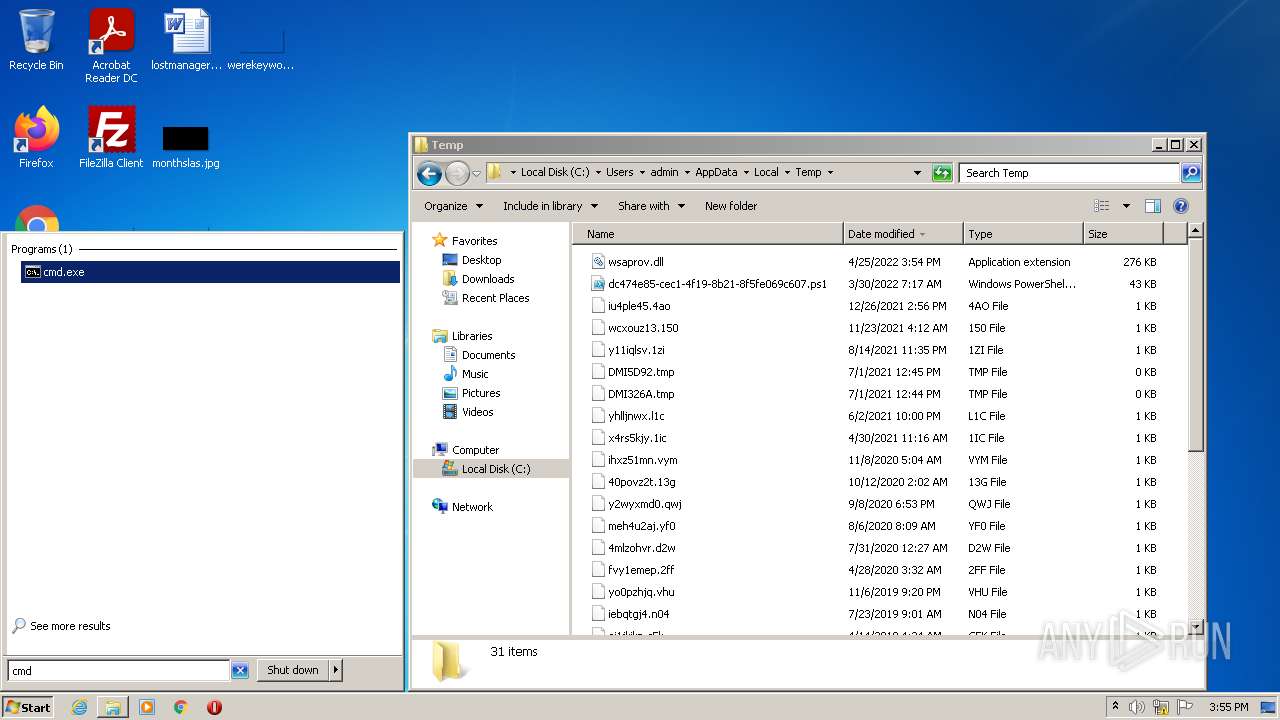
Total processes
46
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
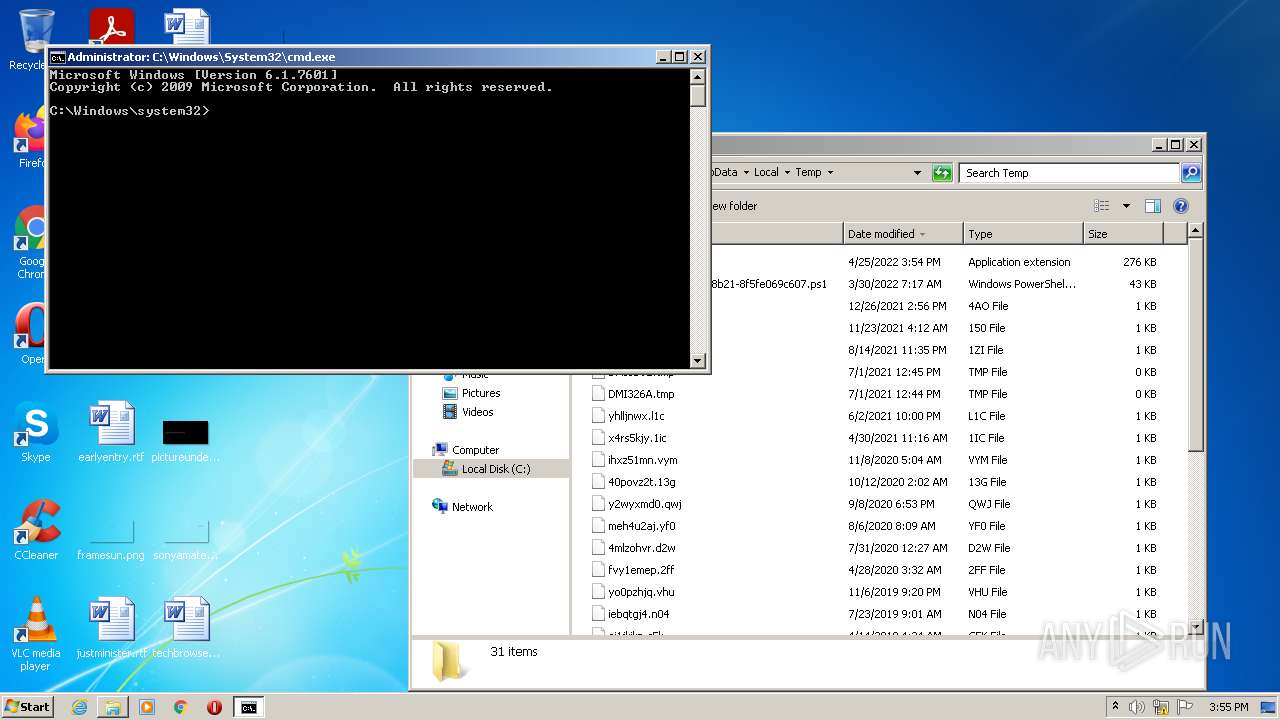
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1464 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1856 | rundll32.exe wsaprov.dll | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
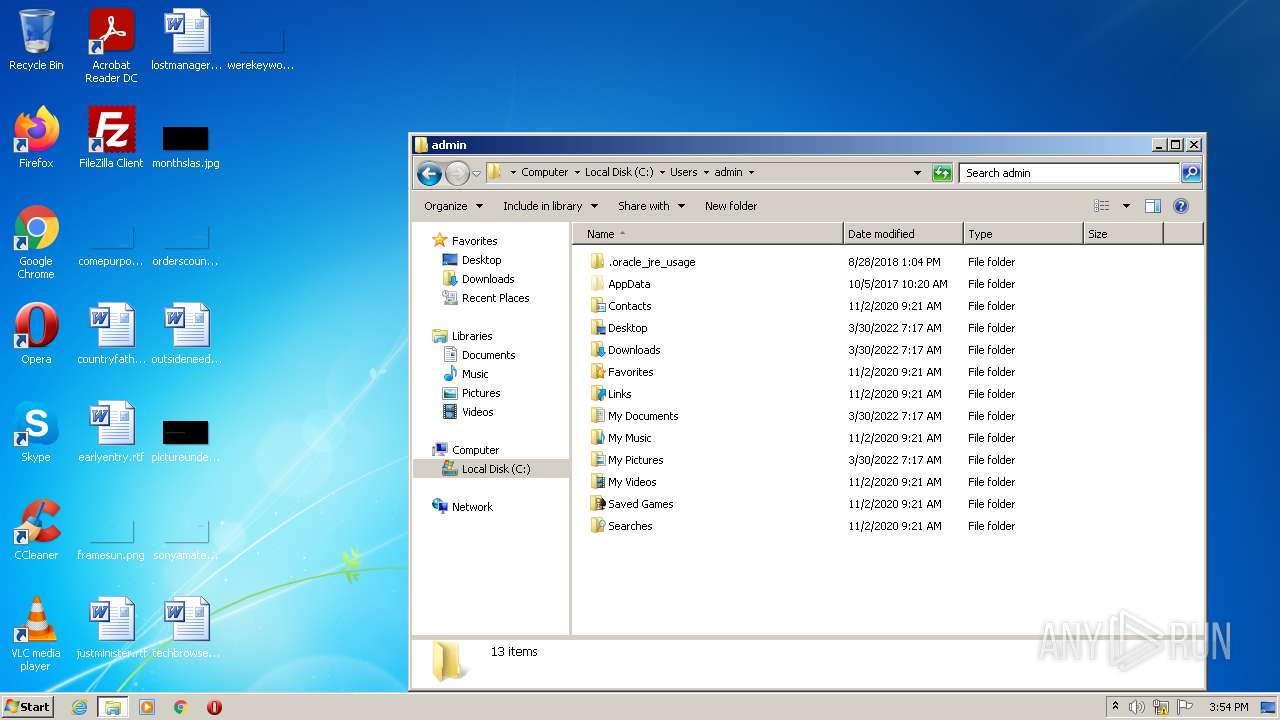
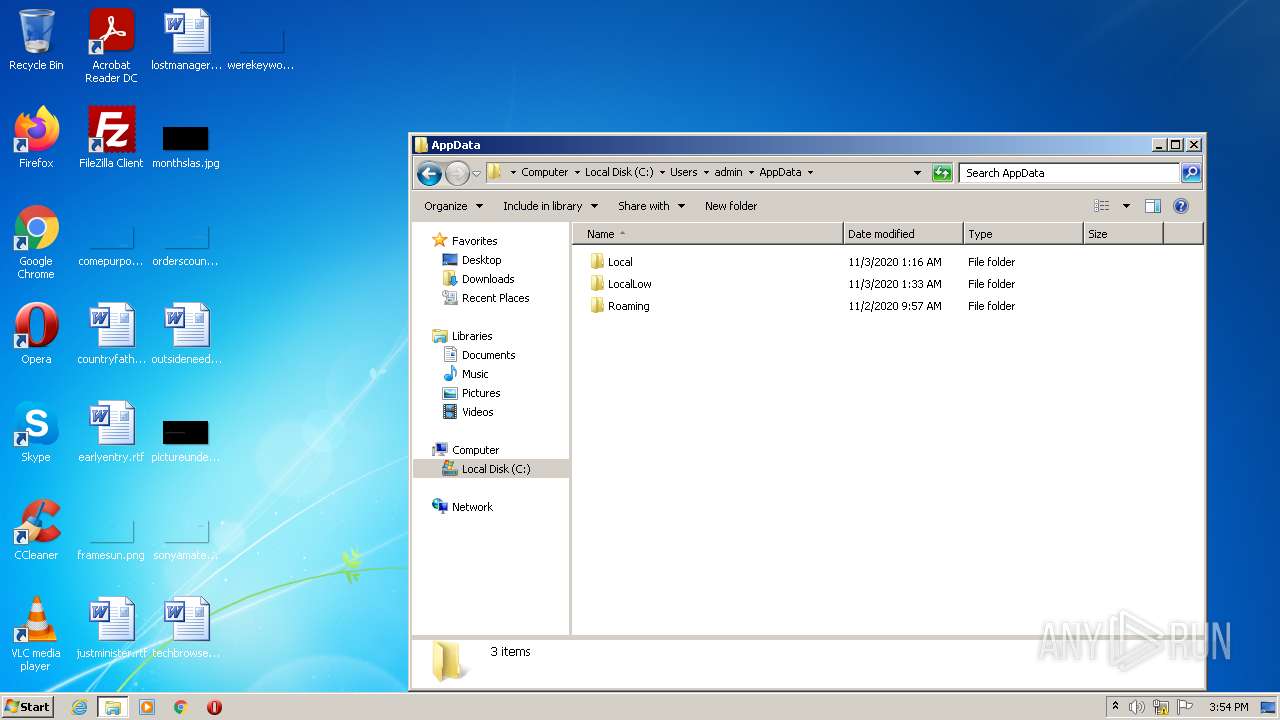
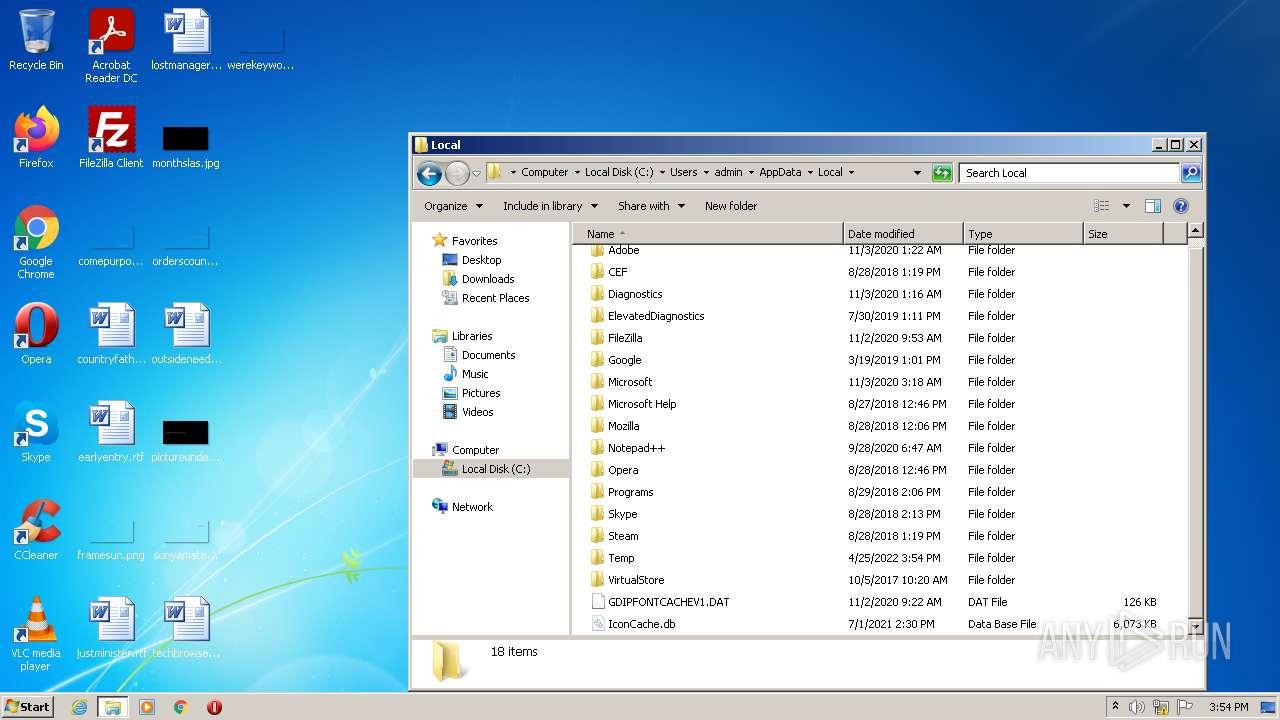
| 1928 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\wsaprov.dll.exe", Main@16 | C:\Windows\System32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | rundll32.exe wsaprov.dll | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
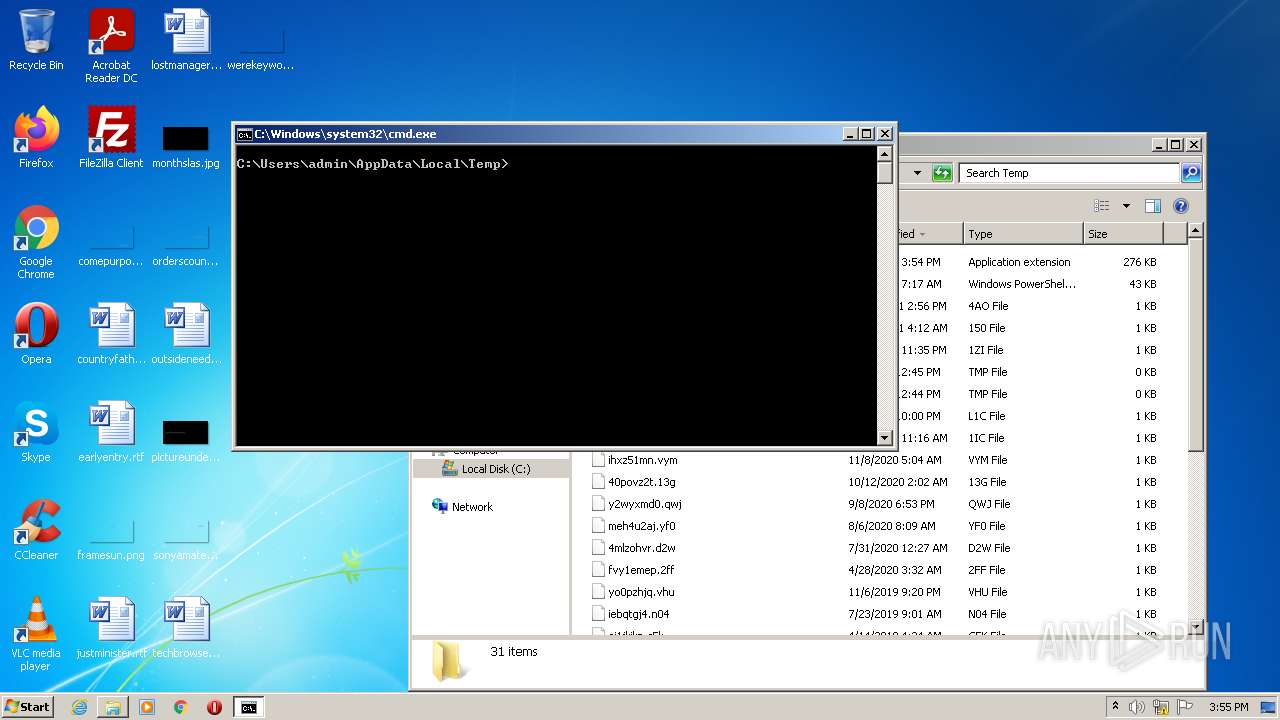
| 2788 | "cmd.exe" /s /k pushd "C:\Users\admin\AppData\Local\Temp" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3532 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
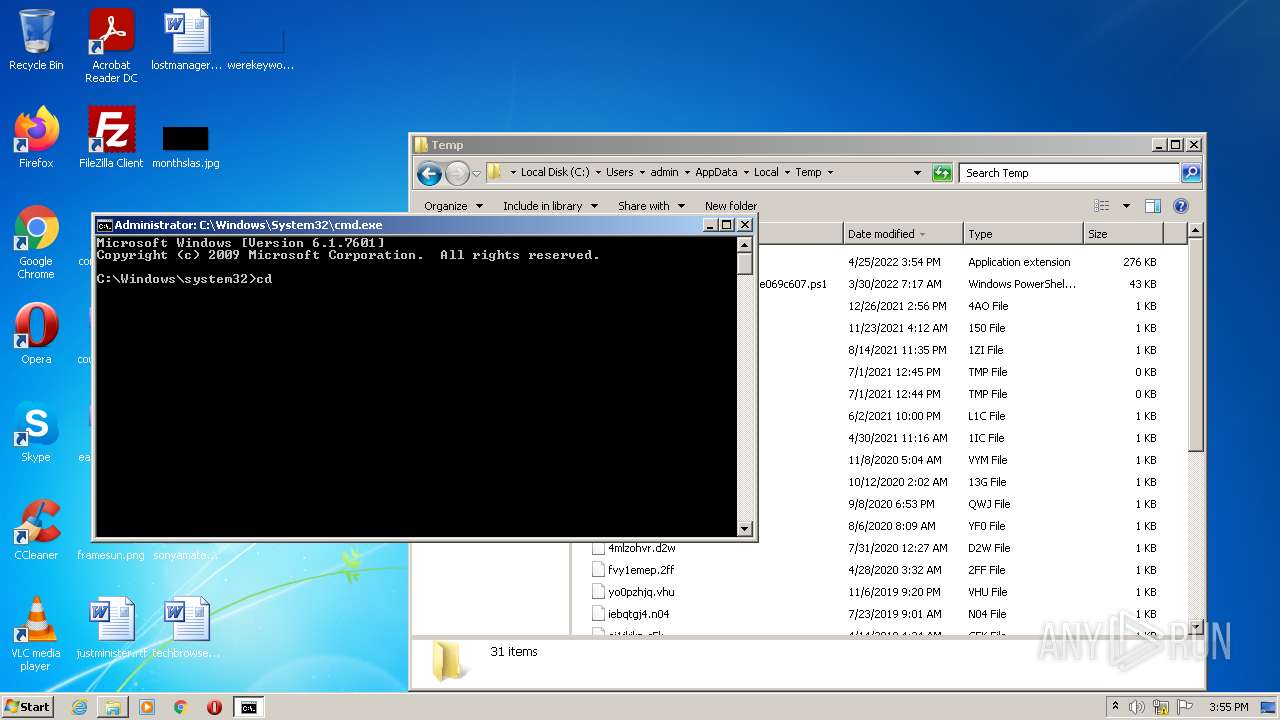
Total events
10 032
Read events
9 389
Write events
643
Delete events
0
Modification events
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\mycomput.dll,-400 |
Value: Mana&ge | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\BdeUnlockWizard.exe,-100 |
Value: &Unlock Drive... | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Rev |
Value: 0 | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (1464) Explorer.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\27\Shell\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Vid |
Value: {65F125E5-7BE1-4810-BA9D-D271C8432CE3} | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
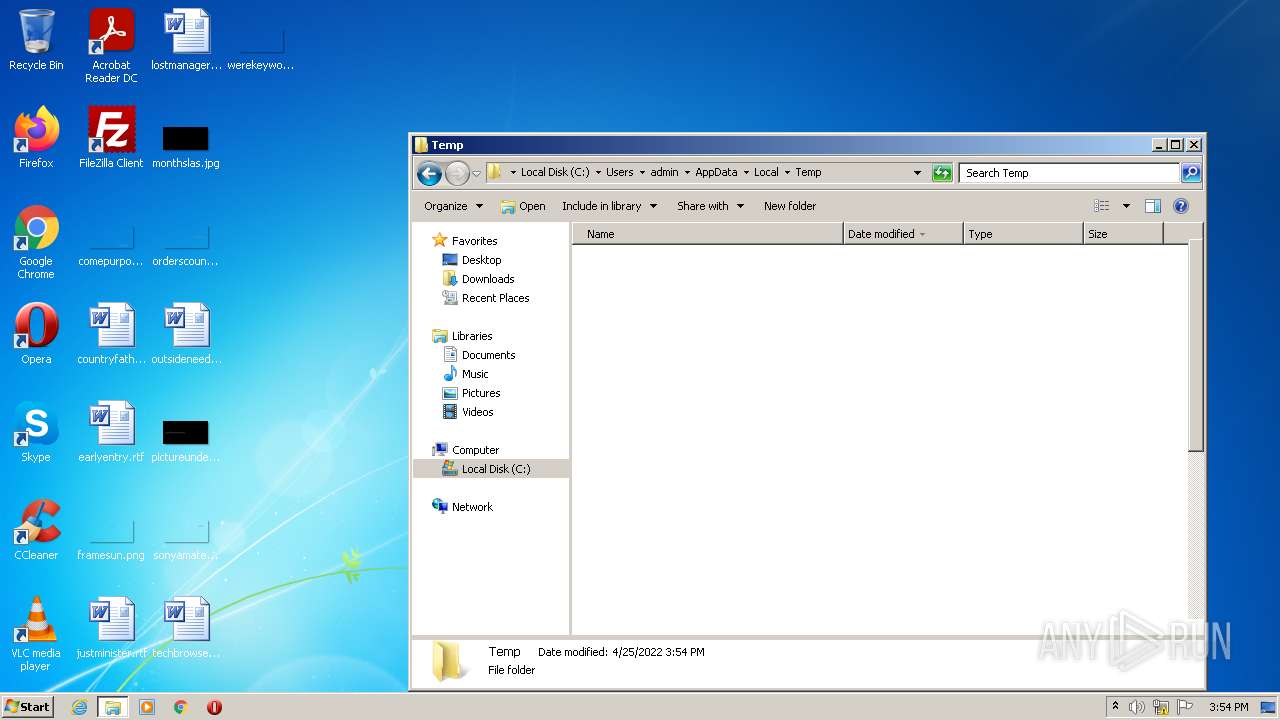
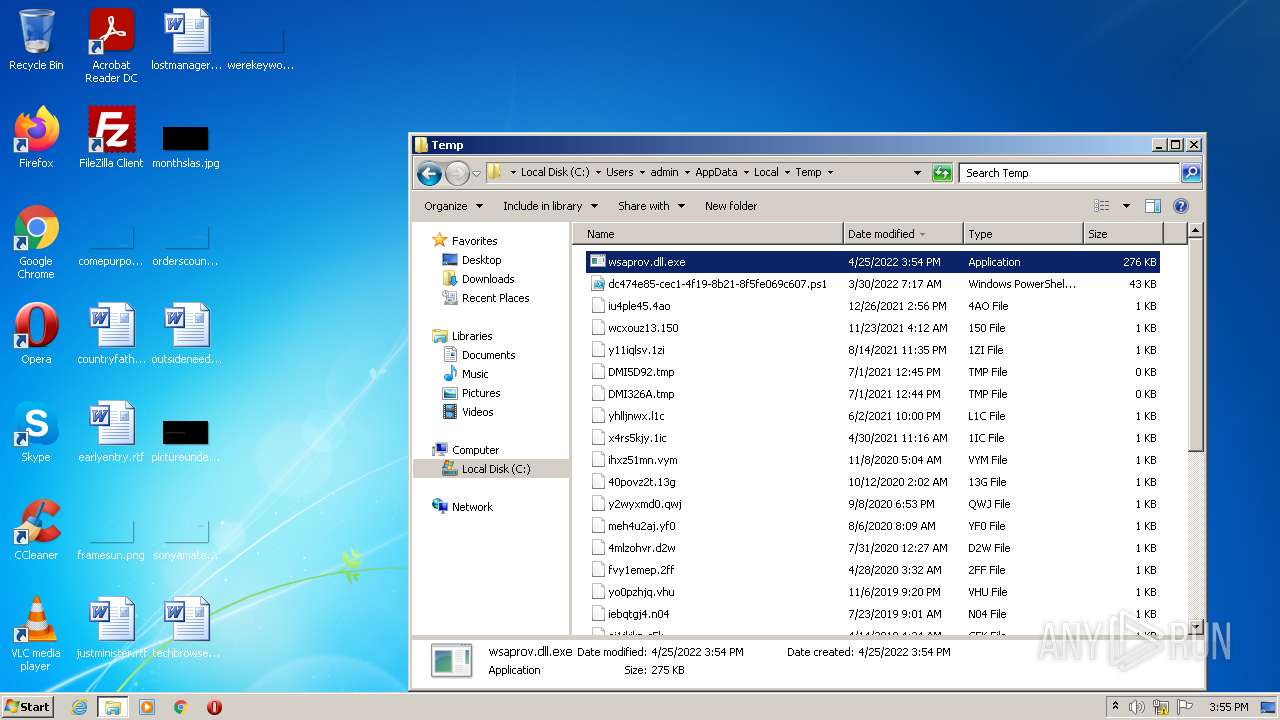
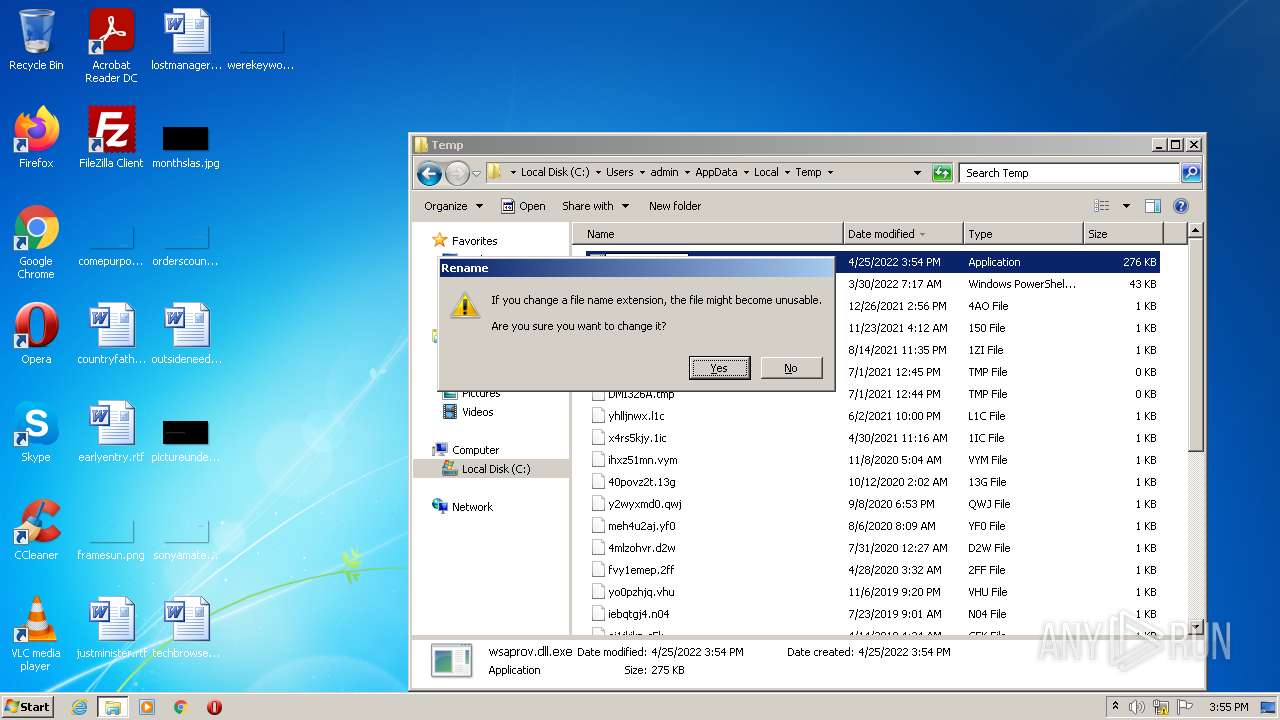
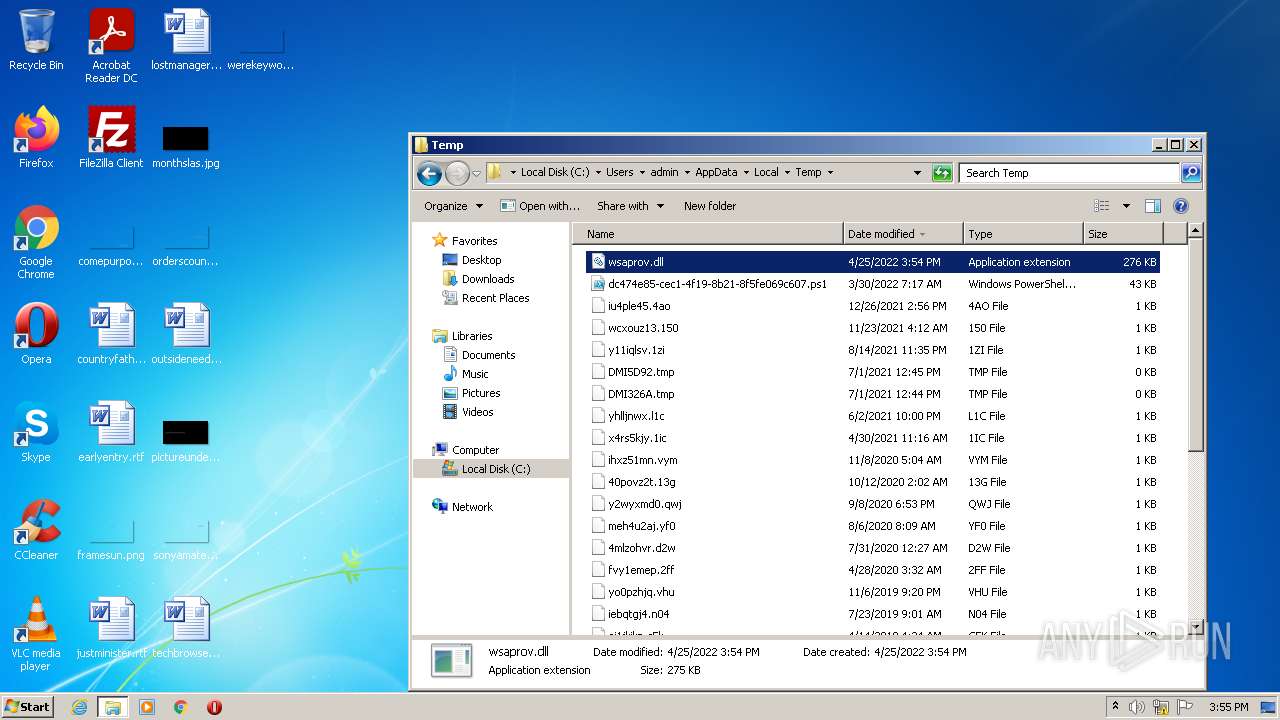
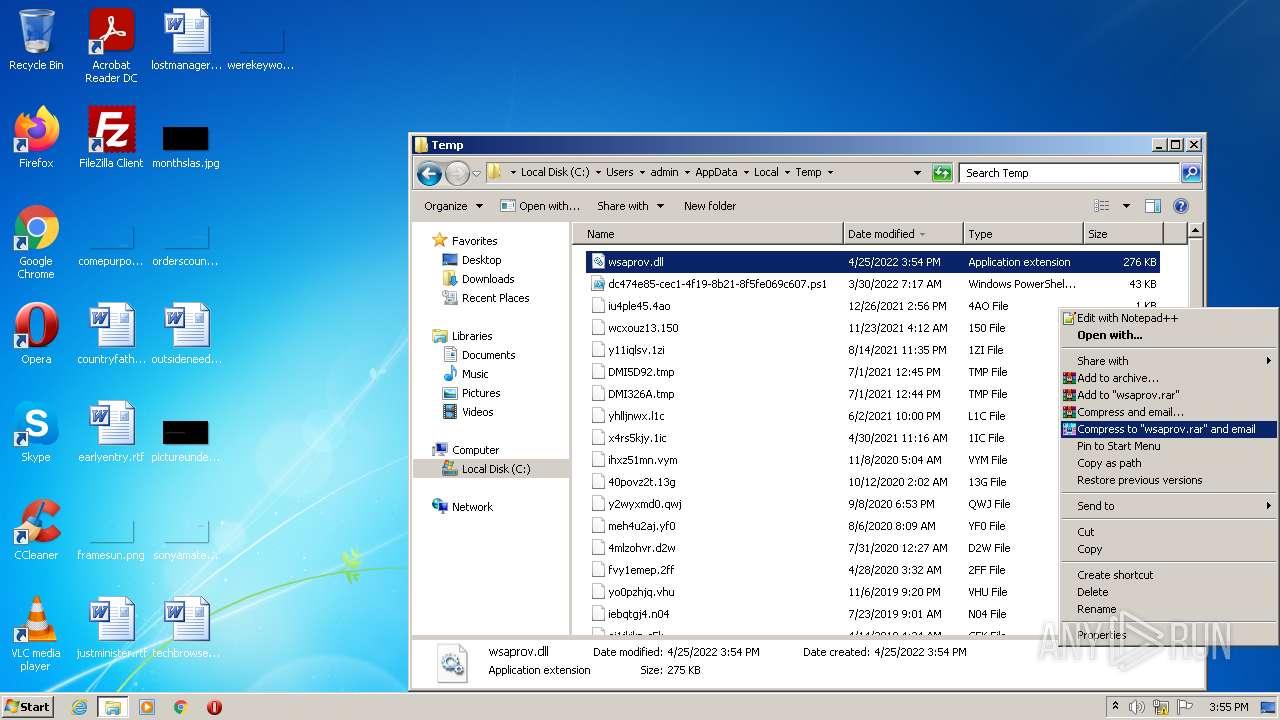
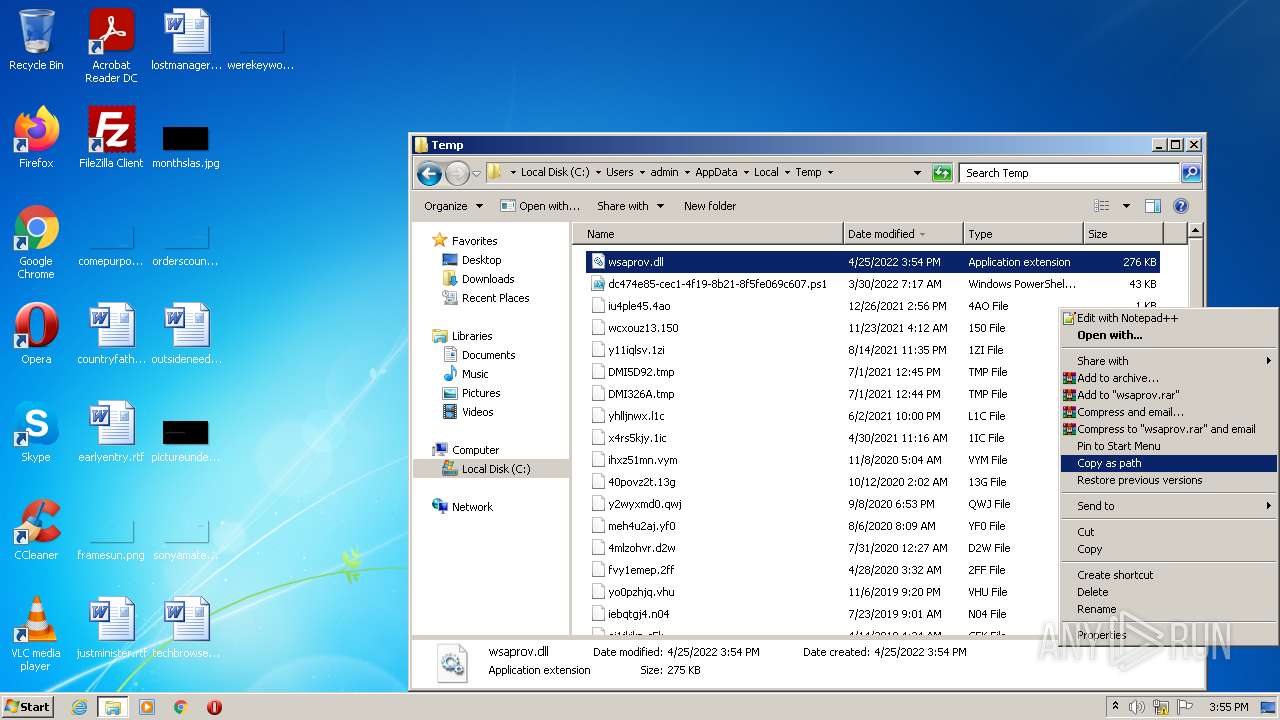
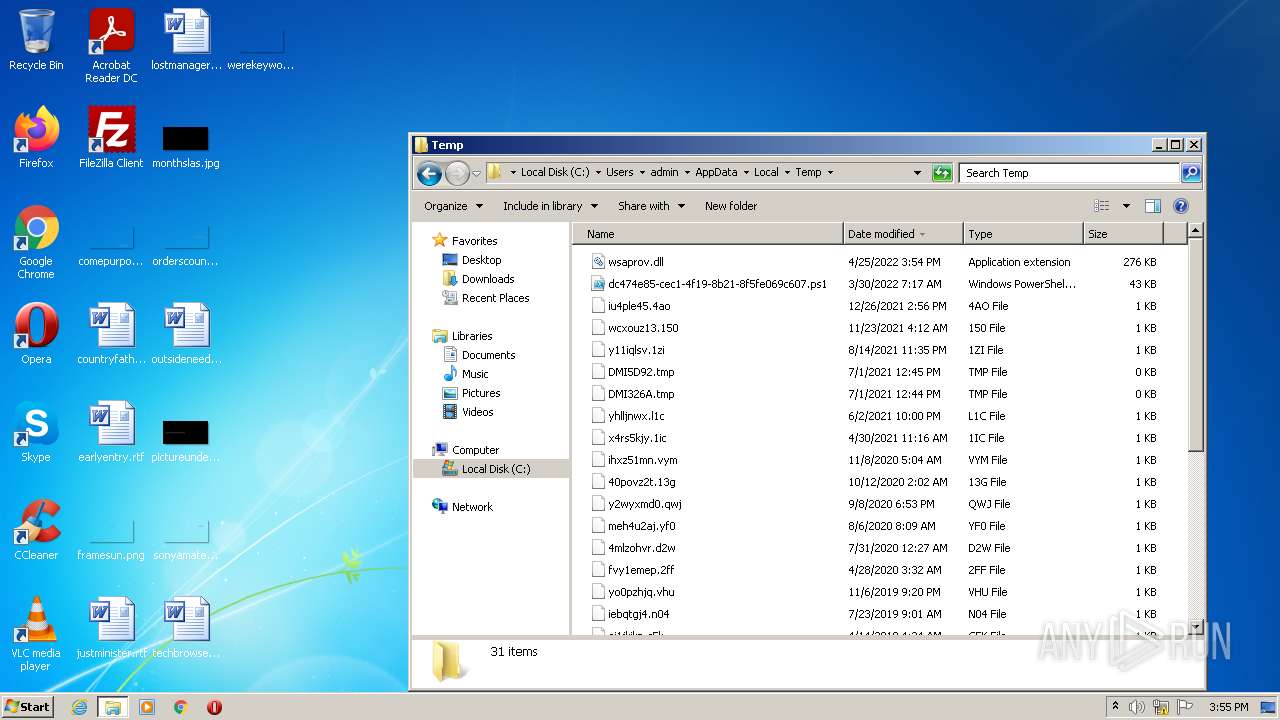
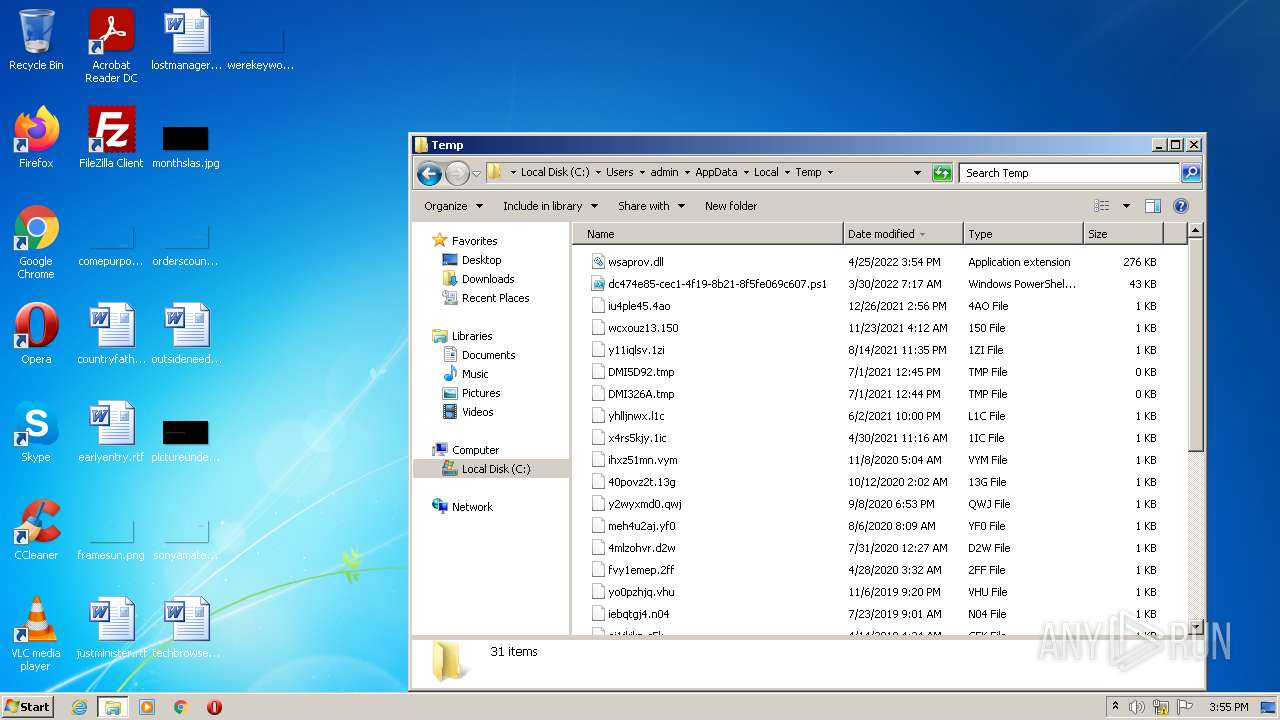
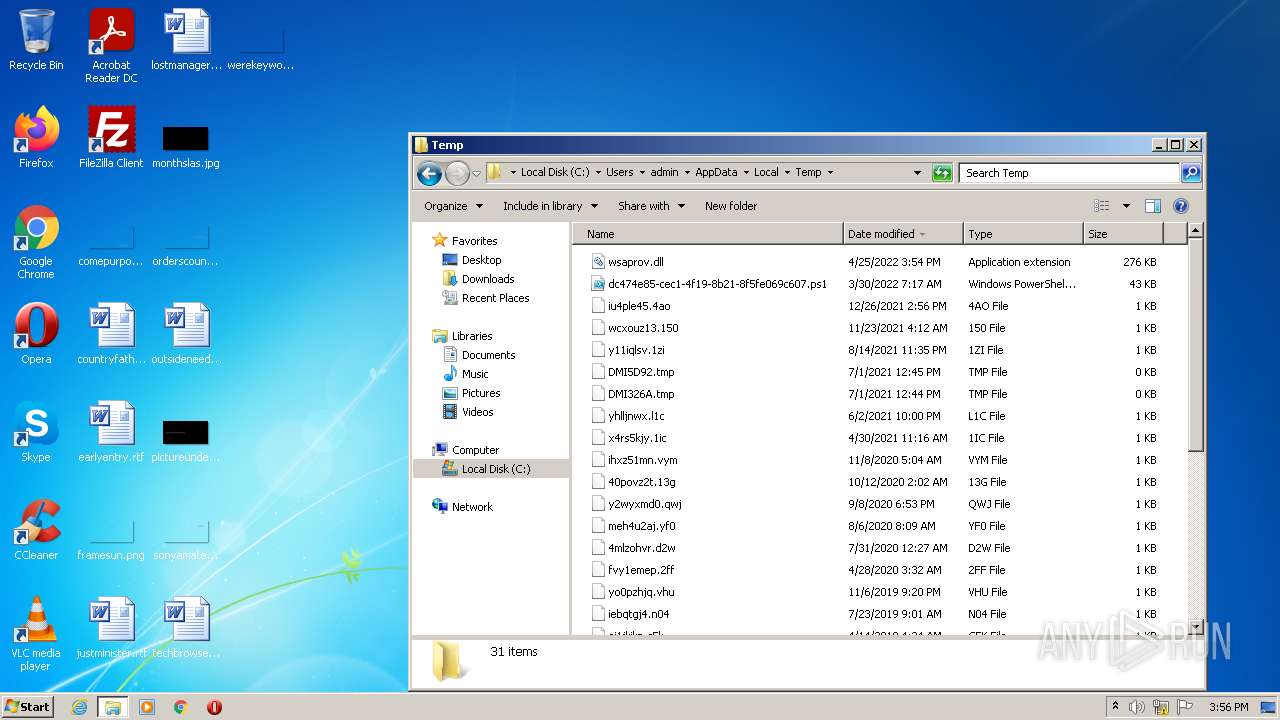
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
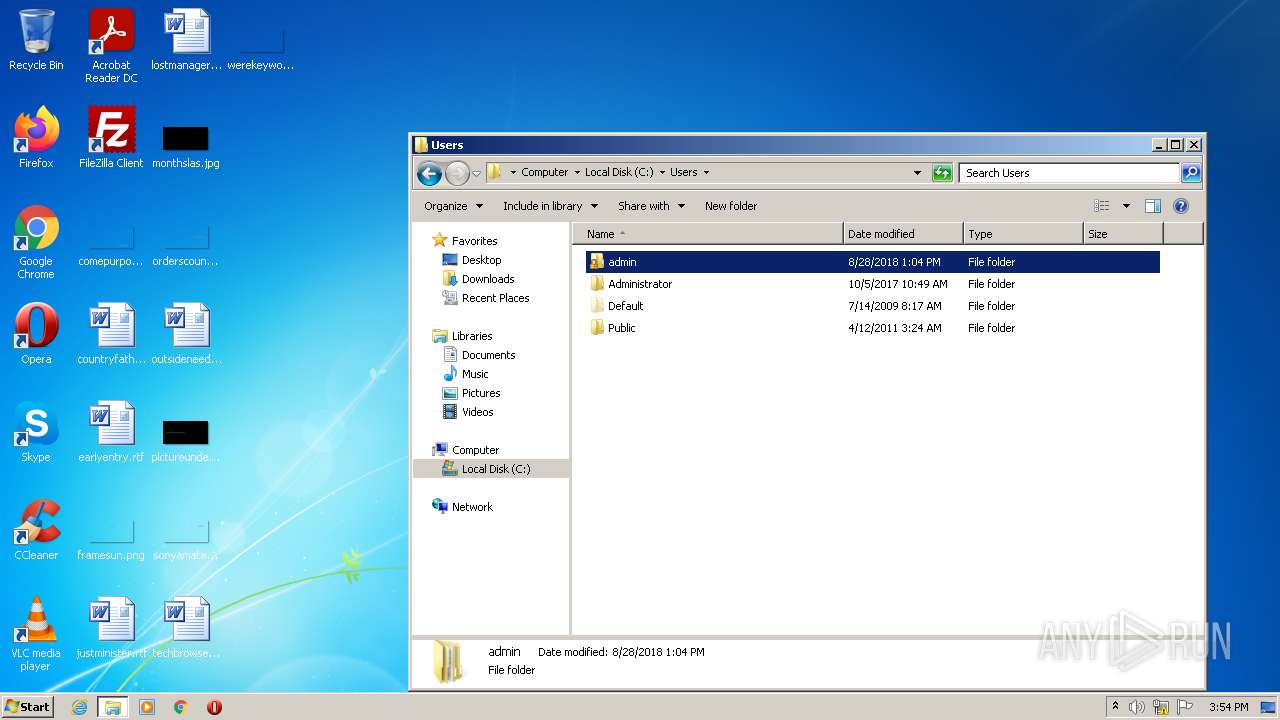
| 1464 | Explorer.EXE | C:\Users\admin\AppData\Local\Temp\wsaprov.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report