| File name: | UserBenchMark.exe |
| Full analysis: | https://app.any.run/tasks/8cefa5a8-37ac-4261-bc51-101e7ff40ff7 |
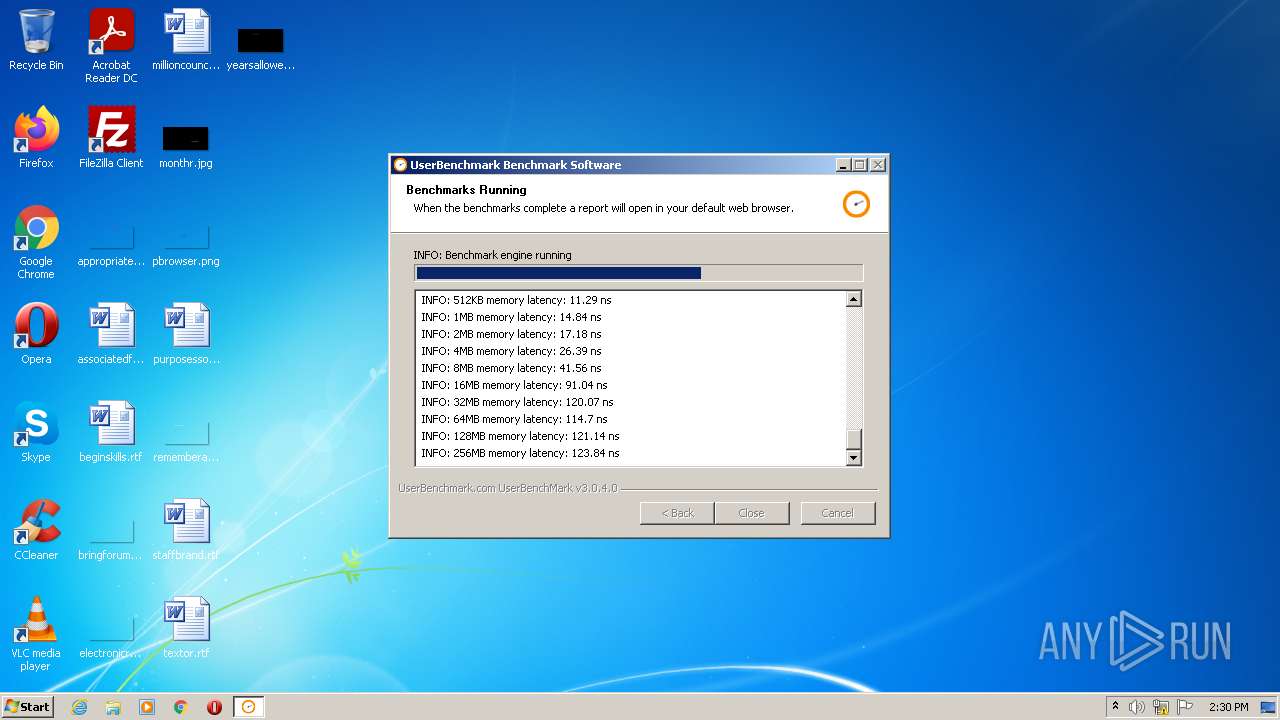
| Verdict: | Malicious activity |
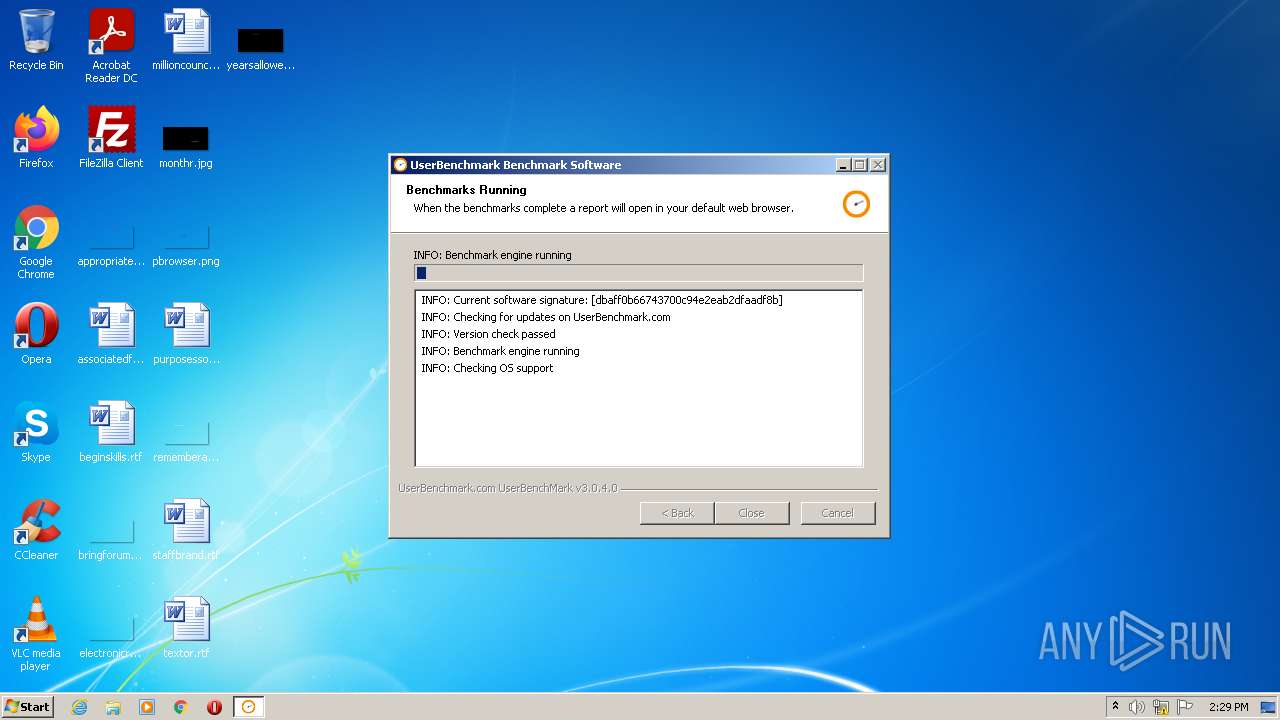
| Analysis date: | January 06, 2022, 14:29:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | DBAFF0B66743700C94E2EAB2DFAADF8B |
| SHA1: | 6B2574856A92FD127F710801EA1D15A6BC314AC5 |
| SHA256: | 460445595E1F4D6E4B2EFC8FB950C16AE737852189EA4363627784E865C17DA9 |
| SSDEEP: | 196608:/f7bbt7AxzTTc5ROkdwOC5k8CnaydsQTjQ6:n7/t09c7OkiZe8Cp5TU6 |
MALICIOUS
Drops executable file immediately after starts
- UserBenchMark.exe (PID: 2176)
Loads dropped or rewritten executable
- UserBenchMark.exe (PID: 2176)
Application was dropped or rewritten from another process
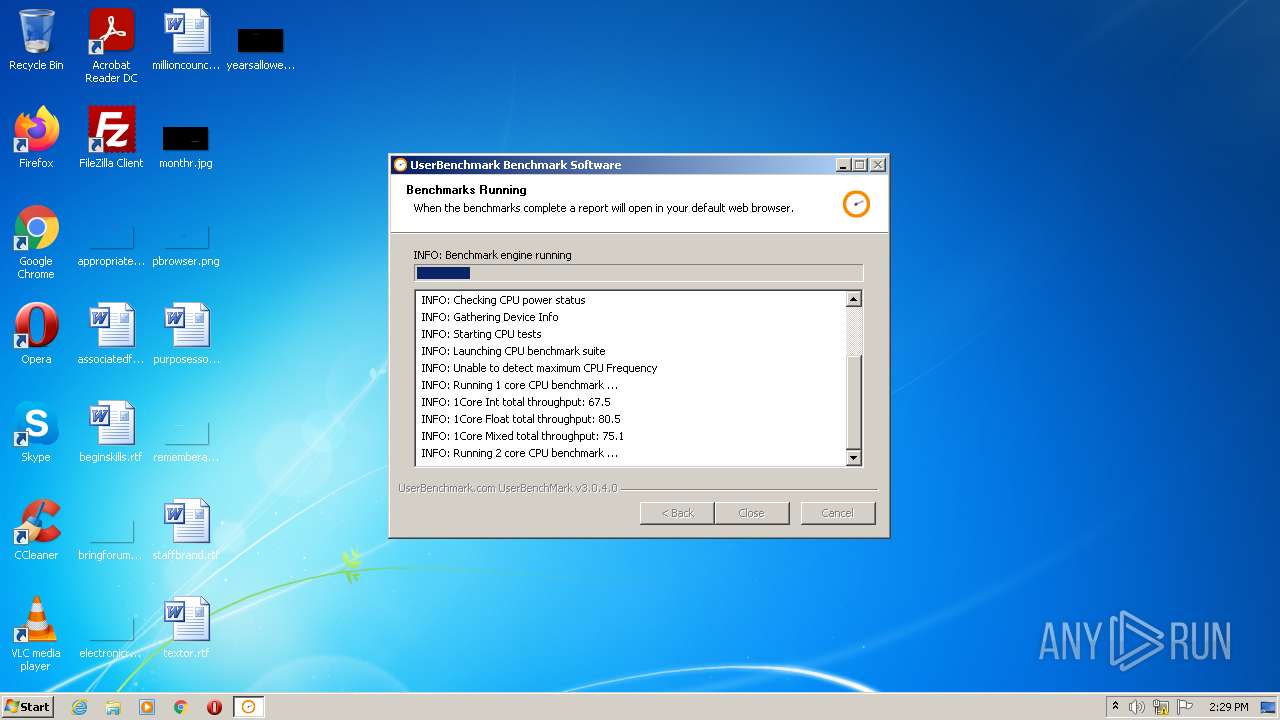
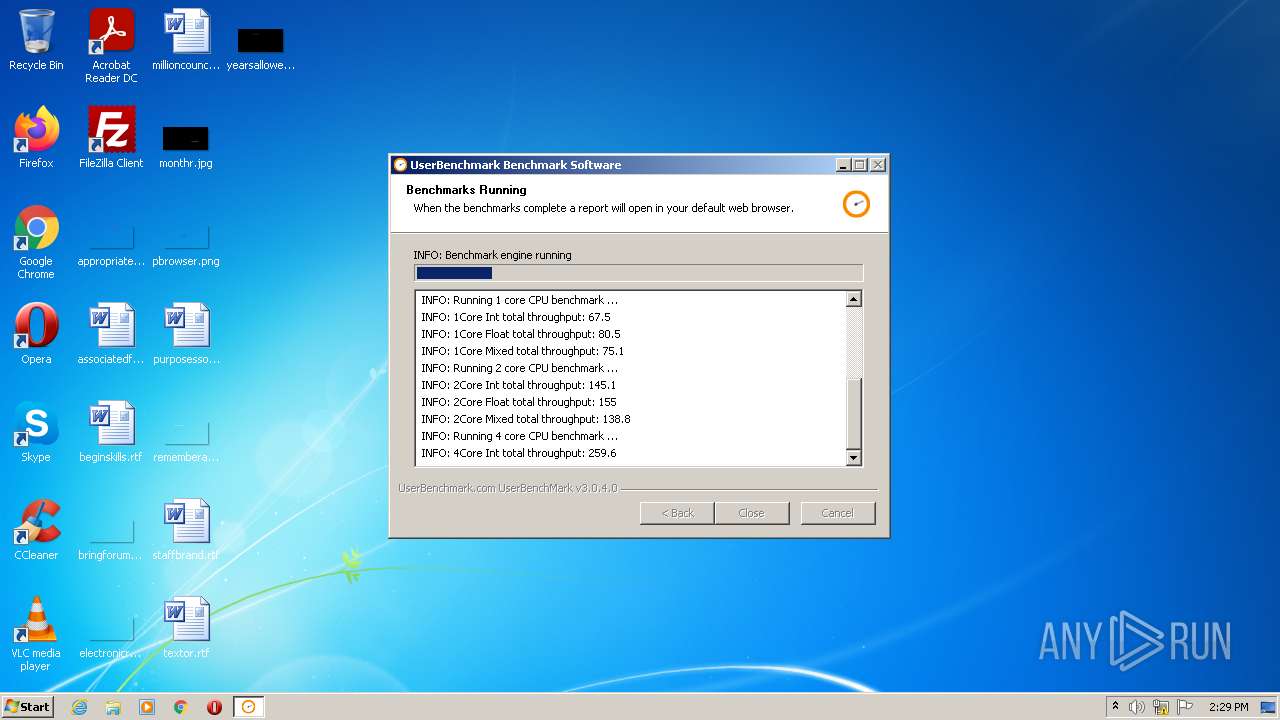
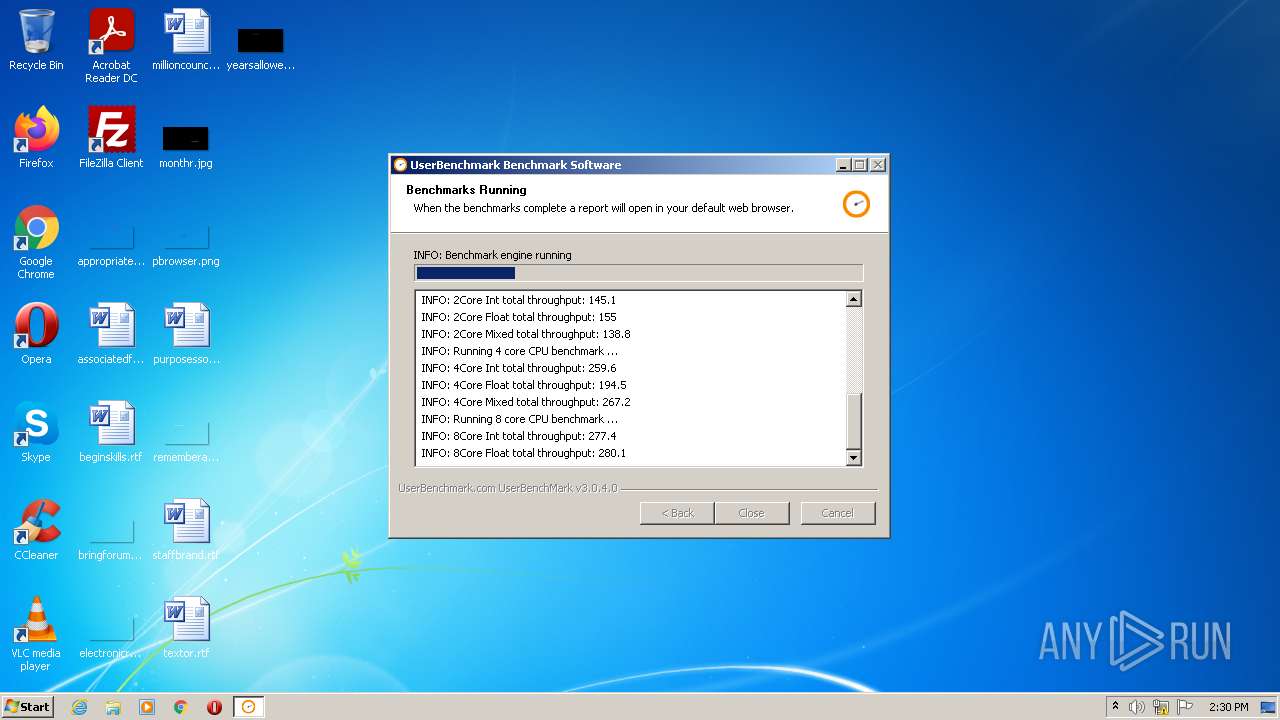
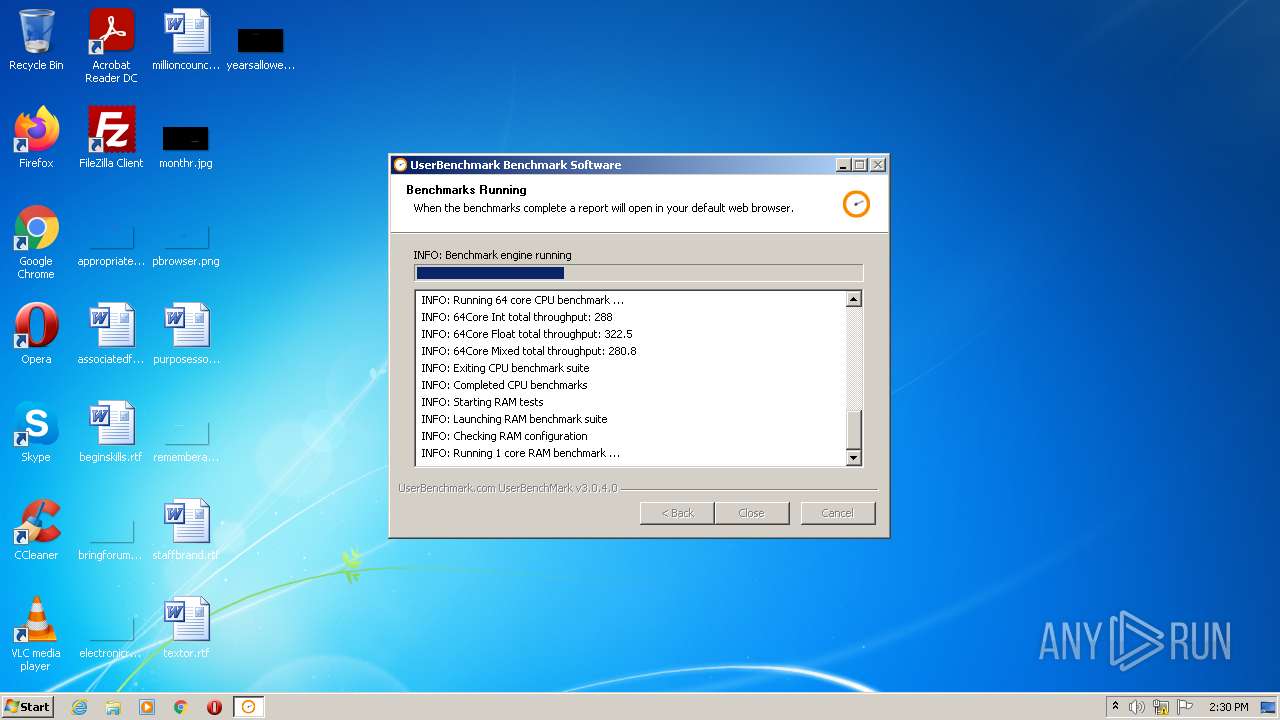
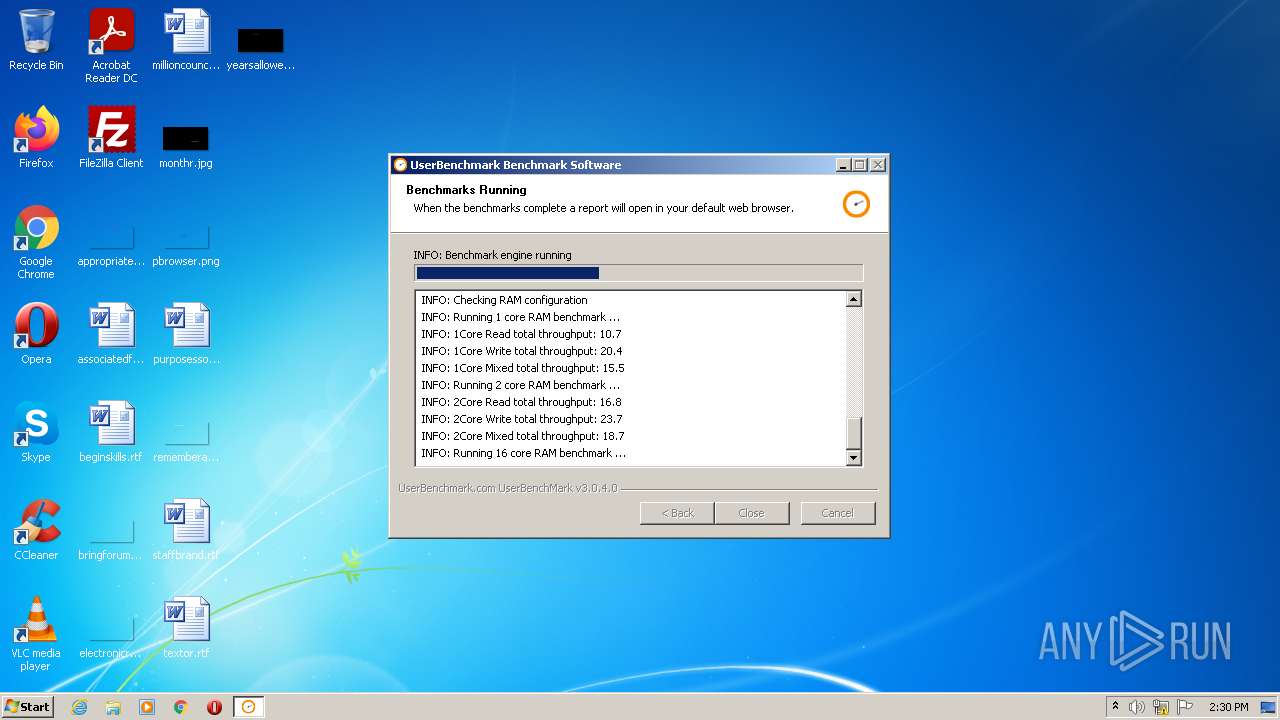
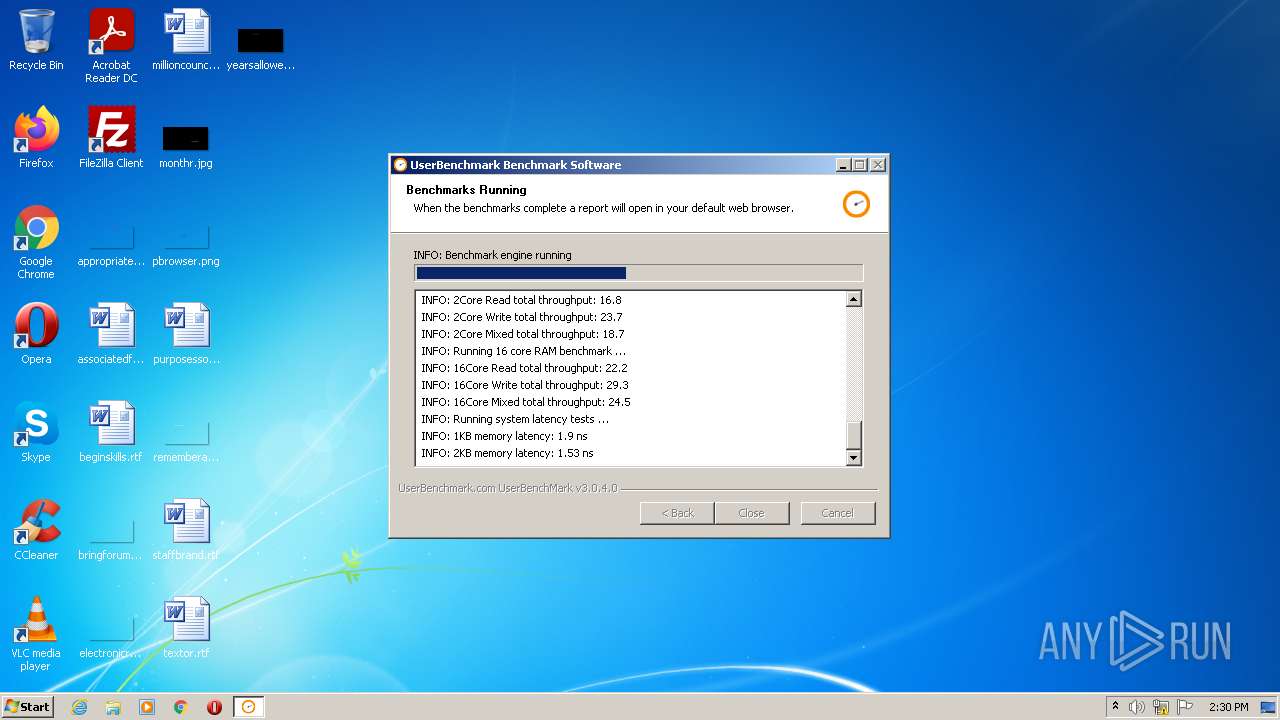
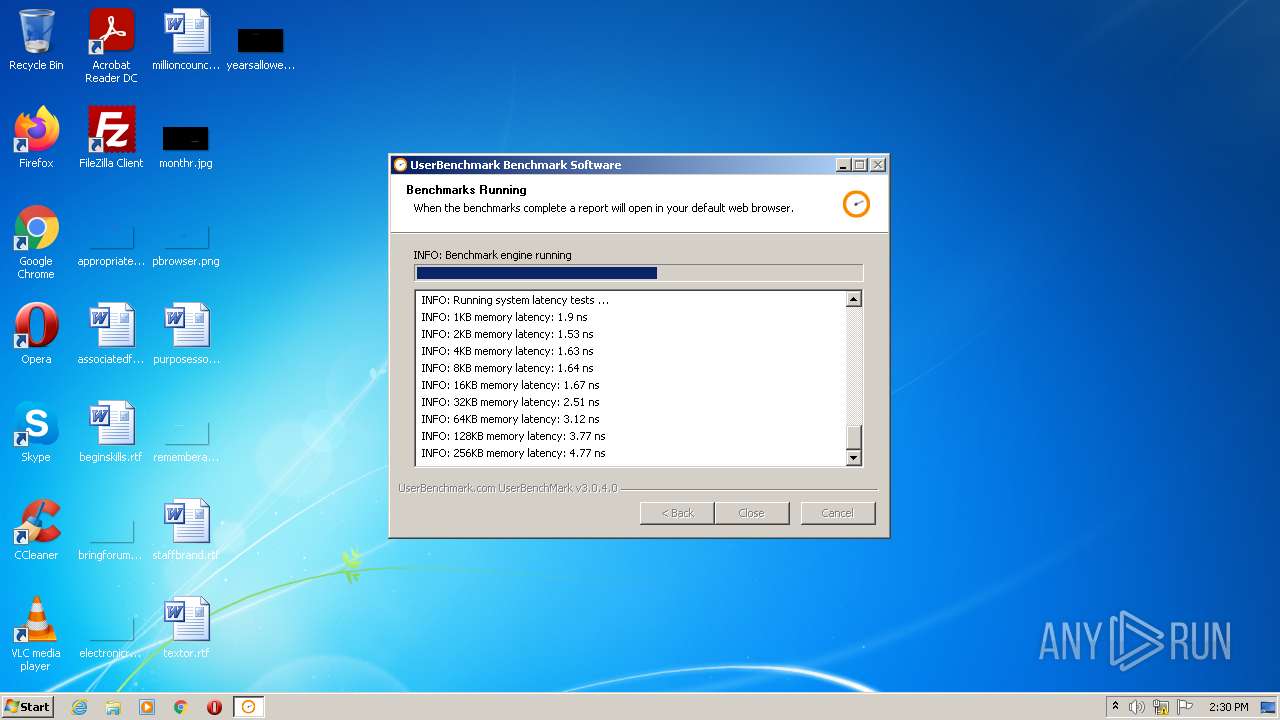
- UserBenchMarkRunEngine.exe (PID: 3844)
- UBMCPUBench.exe (PID: 1644)
- UBMRAMBench.exe (PID: 1124)
- UBMDriveBench.exe (PID: 1088)
SUSPICIOUS
Checks supported languages
- UserBenchMark.exe (PID: 2176)
- UBMDriveBench.exe (PID: 1088)
- ns4CBA.tmp (PID: 2588)
- UserBenchMarkRunEngine.exe (PID: 3844)
- UBMCPUBench.exe (PID: 1644)
- UBMRAMBench.exe (PID: 1124)
Reads the computer name
- UserBenchMark.exe (PID: 2176)
- UserBenchMarkRunEngine.exe (PID: 3844)
- UBMCPUBench.exe (PID: 1644)
- UBMDriveBench.exe (PID: 1088)
Drops a file that was compiled in debug mode
- UserBenchMark.exe (PID: 2176)
Drops a file with too old compile date
- UserBenchMark.exe (PID: 2176)
Executable content was dropped or overwritten
- UserBenchMark.exe (PID: 2176)
Starts application with an unusual extension
- UserBenchMark.exe (PID: 2176)
INFO
Checks Windows Trust Settings
- UserBenchMark.exe (PID: 2176)
Reads settings of System Certificates
- UserBenchMark.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
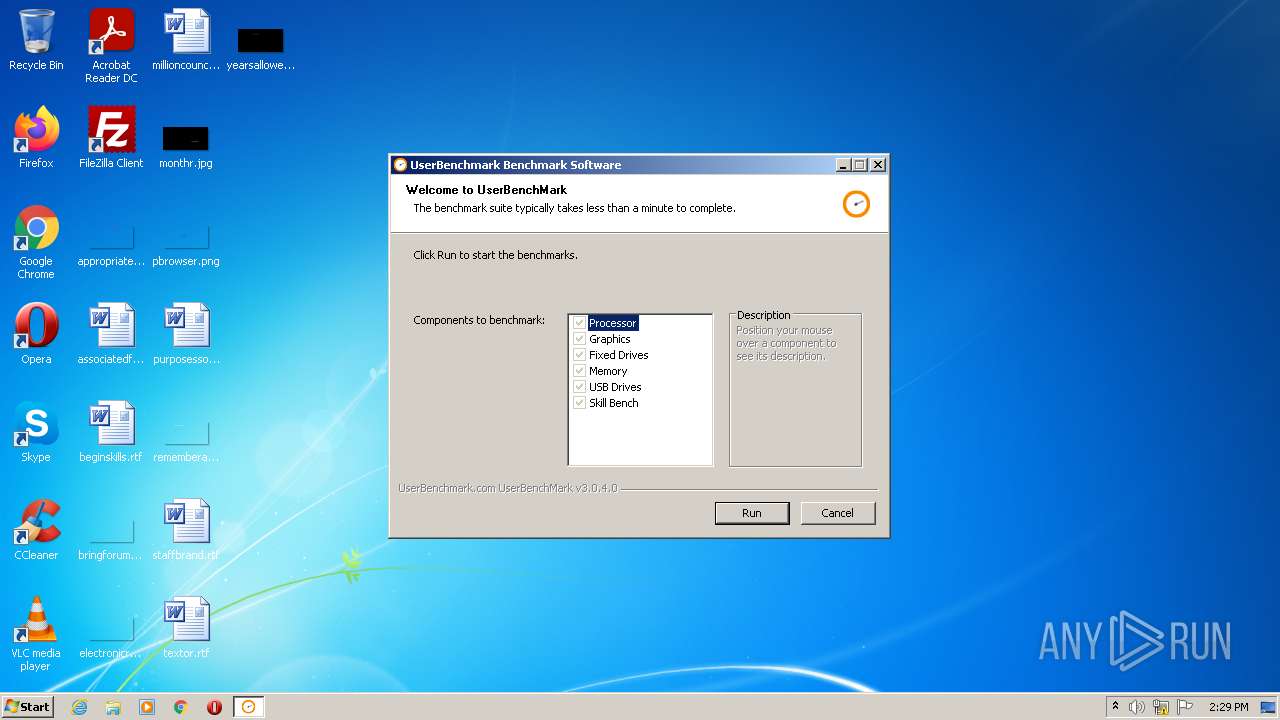
| ProductName: | UserBenchMark |
|---|---|
| LegalTrademarks: | UserBenchmark |
| LegalCopyright: | UserBenchmark.com |
| FileVersion: | 3.0.4.0 |
| FileDescription: | Benchmark Software |
| CompanyName: | UserBenchmark.com |
| Comments: | hello |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.0.4.0 |
| FileVersionNumber: | 3.0.4.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| Comments: | hello |
| CompanyName: | UserBenchmark.com |
| FileDescription: | Benchmark Software |
| FileVersion: | 3.0.4.0 |
| LegalCopyright: | UserBenchmark.com |
| LegalTrademarks: | UserBenchmark |
| ProductName: | UserBenchMark |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00034000 | 0x00004BB0 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.31301 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22452 | 954 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.82836 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70992 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
46
Monitored processes
7
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | UBMDriveBench.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMDriveBench.exe | — | UserBenchMarkRunEngine.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1124 | UBMRAMBench.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMRAMBench.exe | — | UserBenchMarkRunEngine.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1644 | UBMCPUBench.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMCPUBench.exe | — | UserBenchMarkRunEngine.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\UserBenchMark.exe" | C:\Users\admin\AppData\Local\Temp\UserBenchMark.exe | Explorer.EXE | ||||||||||||
User: admin Company: UserBenchmark.com Integrity Level: HIGH Description: Benchmark Software Exit code: 0 Version: 3.0.4.0 Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\AppData\Local\Temp\nsaEFD4.tmp\ns4CBA.tmp" "C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UserBenchMarkRunEngine.exe" start | C:\Users\admin\AppData\Local\Temp\nsaEFD4.tmp\ns4CBA.tmp | — | UserBenchMark.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\UserBenchMark.exe" | C:\Users\admin\AppData\Local\Temp\UserBenchMark.exe | — | Explorer.EXE | |||||||||||
User: admin Company: UserBenchmark.com Integrity Level: MEDIUM Description: Benchmark Software Exit code: 3221226540 Version: 3.0.4.0 Modules
| |||||||||||||||
| 3844 | "C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UserBenchMarkRunEngine.exe" start | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UserBenchMarkRunEngine.exe | — | ns4CBA.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 163
Read events
4 128
Write events
35
Delete events
0
Modification events
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2176) UserBenchMark.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
21
Suspicious files
14
Text files
23
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMGPUStats.exe | executable | |
MD5:1719F06537CF366DB9EFF2E8DC99B797 | SHA256:655BEFB1E4671B2099DC8B520CBB2CFC80B8B5CD43BF544F38E6F83A32BC4678 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMCPUBench.exe | executable | |
MD5:04D9805E7736F6270569E024BDC2F79B | SHA256:5B24E7314CA659133BC09CB6763602E8FFF10717A7F1AC3E05C8DB4BA6C8F87A | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\SHADOW.exe | executable | |
MD5:C28DD3A78947FC2E9365D009ACFD4FC9 | SHA256:FAE12BD8C460E77E84FB50466C11703B2AF78C60767B16632682373FD1A425F6 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UBMDriveBench.exe | executable | |
MD5:376DCB606346D8F1FADDEA056CEE0CFC | SHA256:BB7F2C6F85C0F527D78AE90A86B10ECB1F46DC7C36BAC7E4B2B254BD4A91C6B4 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\UserBenchMarkRunEngine.exe | executable | |
MD5:905A8867C63855C58791B1ACD3EA2CC1 | SHA256:0435FE9A826CBAB08250D98F9AD65D0425C6F2E7C398F4E74ED3FDCBEA747EED | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\Media\Airplane\bihull.bmp | image | |
MD5:164949EB5C125010817E69540FC72640 | SHA256:B89AD345C81A871FCDD7D7A4923813DD9E57EC0C6AE9BAD6A8A7E58FE9A402A8 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\Media\SHADOW.fx | text | |
MD5:80056F7CB34D026188761FF788FE4CBB | SHA256:F5B7EFE9DACEA606DEF5DCE7164E64E89B7D24BEA472862E257D41AB54257013 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\Media\ring.x | text | |
MD5:6E6CC828BE6740F61339600F69DD6B1B | SHA256:7E9519C38EE1D48210C0EC794208EF70F483C34980788A8ED45511C09C511BEF | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\Media\Misc\sphere.x | text | |
MD5:5218417690005DDFB56F6CD81873BD2B | SHA256:1A05F397897AD7CAB362D215B62CFFF613A9CE06D357B549D69B70A701C7C3C9 | |||
| 2176 | UserBenchMark.exe | C:\Users\admin\AppData\Local\Temp\UserBenchMarkTemp\Media\spotlight.x | text | |
MD5:07E205E90539F031C639F0AD152E3037 | SHA256:0CB19A3256B88F5DCE62E760A532EB7B953440C0DAA48160D51BEF3E27E053CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
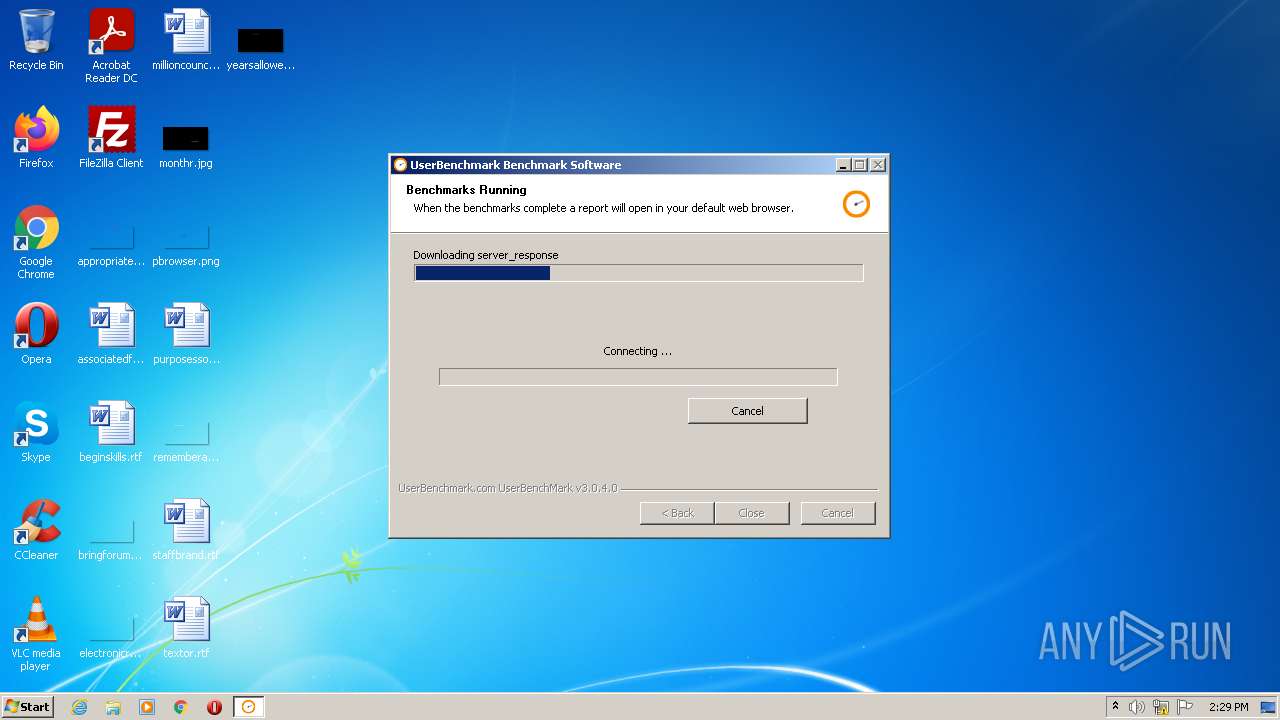
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | UserBenchMark.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2176 | UserBenchMark.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2176 | UserBenchMark.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCHvO3kYCVNP3 | US | der | 1.74 Kb | whitelisted |
2176 | UserBenchMark.exe | GET | 200 | 67.27.157.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cbd9d1351b76d011 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2176 | UserBenchMark.exe | 54.39.161.167:443 | www.userbenchmark.com | OVH SAS | FR | suspicious |
2176 | UserBenchMark.exe | 67.27.157.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
— | — | 8.253.204.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2176 | UserBenchMark.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.userbenchmark.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |