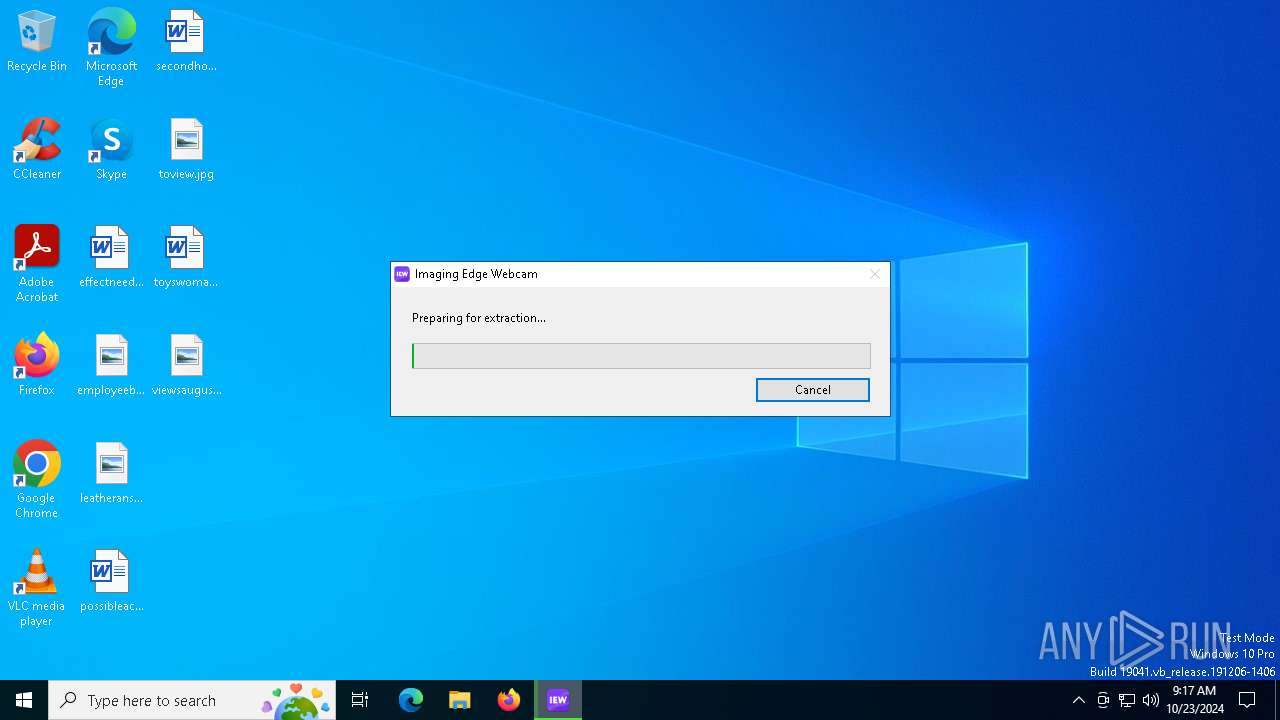
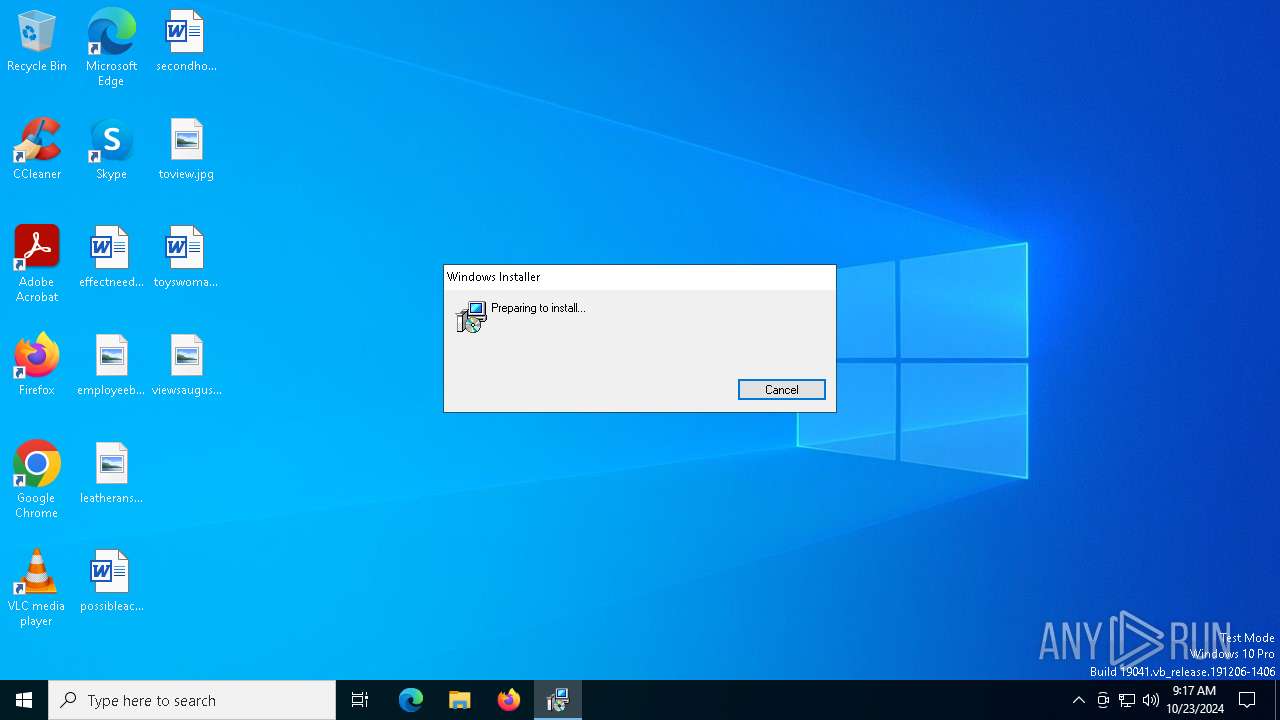
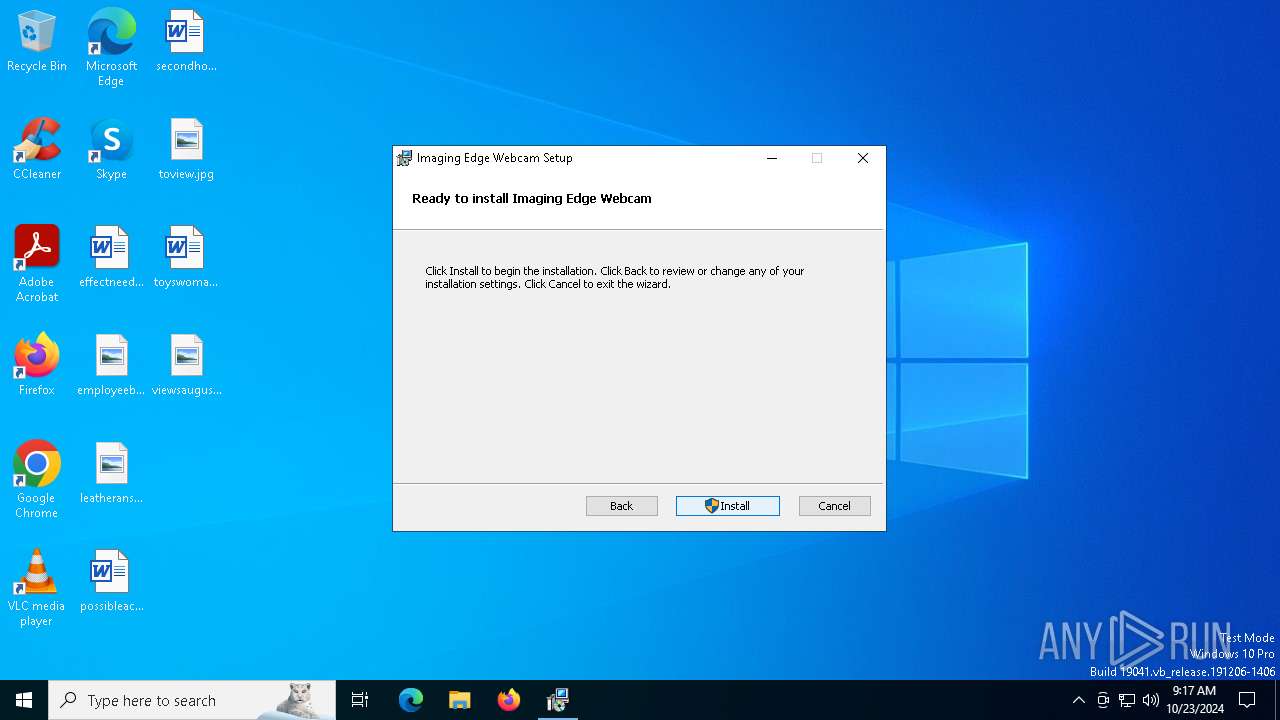
| File name: | IEW113_2311a.exe |
| Full analysis: | https://app.any.run/tasks/cce1ab78-b4b0-4094-b75b-e7329ae82ba0 |
| Verdict: | Malicious activity |
| Analysis date: | October 23, 2024, 09:17:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1BB2447F9AE84781BCFA73EDA1606D72 |
| SHA1: | 6C875DD5404A67CEB1D3AEE207BE4286CBD8DD93 |
| SHA256: | 45F839521BDF4EBFEB32D8DD17EA33133E3C7AE67C6859380BEA02CF56CF30F6 |
| SSDEEP: | 98304:7amWue98jYfCPKrZHuPUspTACYaFyYzaulVO0dWvqJN1+3G8K9d6FMSMLtZwXEXb:BteKD2JIRh |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- IEW113_2311a.exe (PID: 7156)
- IEW113_2311a.exe (PID: 6864)
Application launched itself
- IEW113_2311a.exe (PID: 7156)
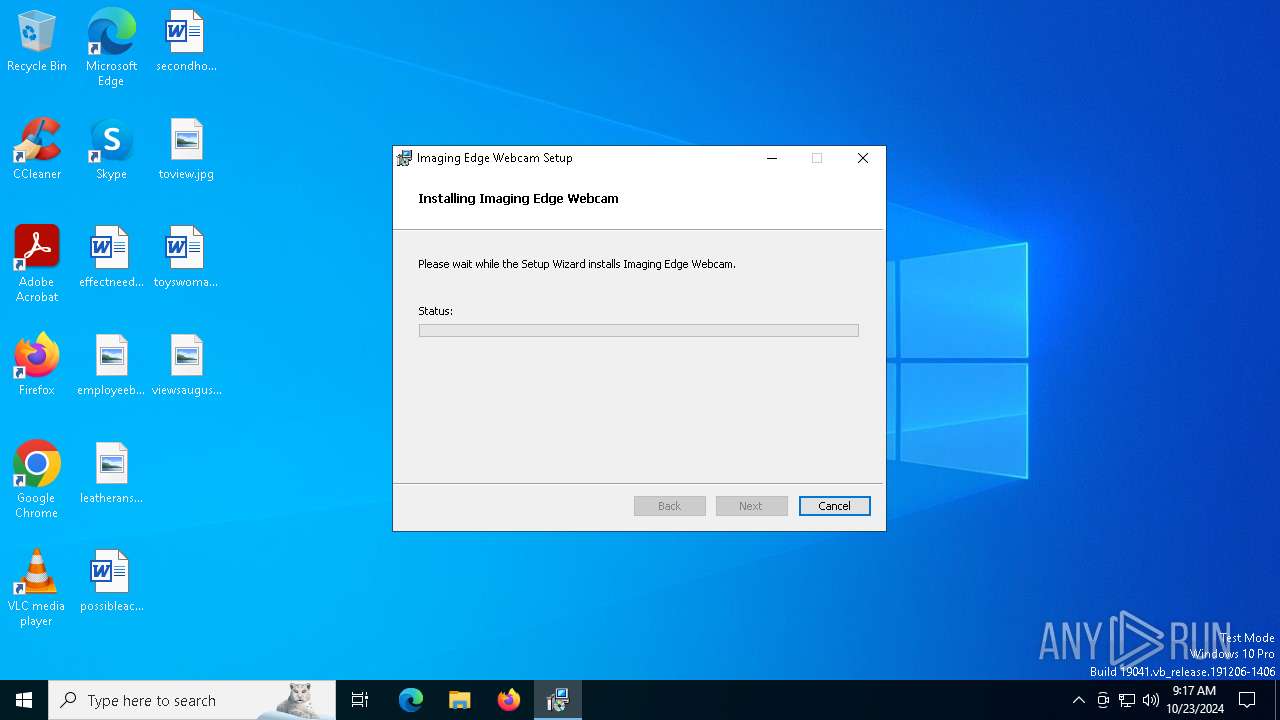
Searches for installed software
- msiexec.exe (PID: 4348)
Executes as Windows Service
- WUDFHost.exe (PID: 1008)
- VSSVC.exe (PID: 3700)
- WUDFHost.exe (PID: 2416)
- ImagingEdgeWebcamLauncher.exe (PID: 7380)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 3276)
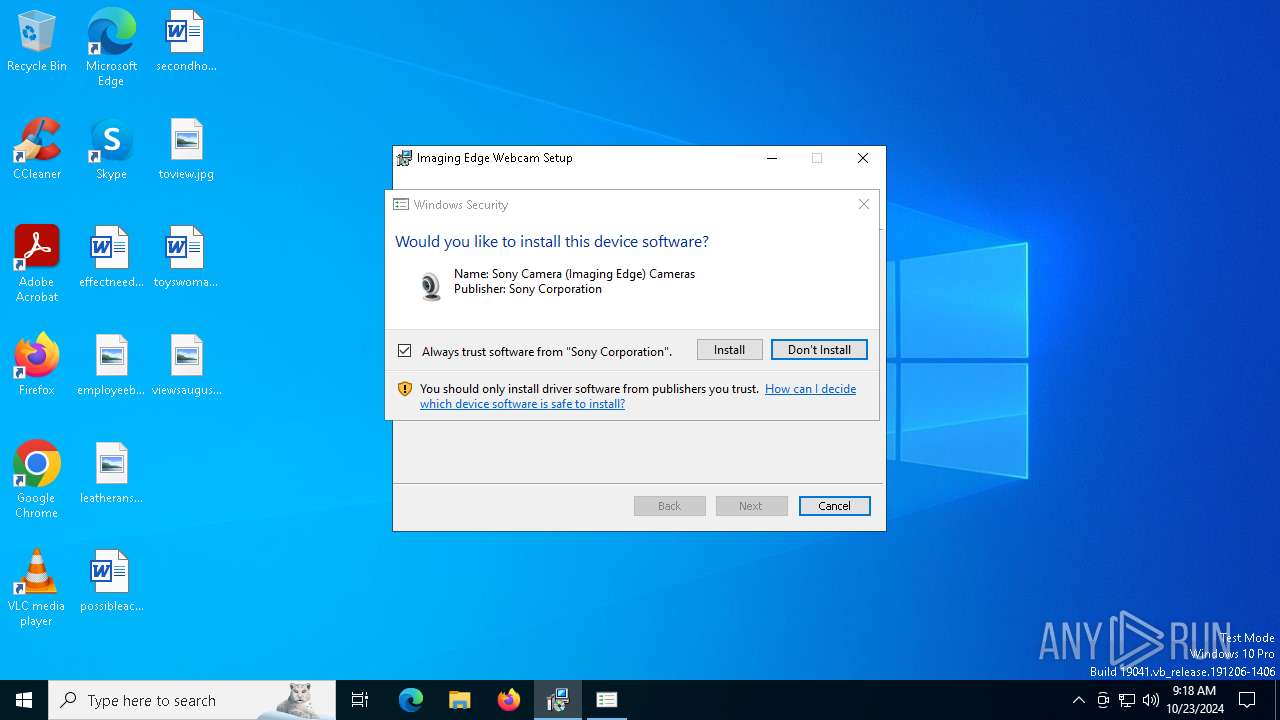
Process drops legitimate windows executable
- msiexec.exe (PID: 948)
The process drops C-runtime libraries
- msiexec.exe (PID: 948)
Executable content was dropped or overwritten
- pnputil.exe (PID: 6772)
- drvinst.exe (PID: 6420)
Starts SC.EXE for service management
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 7436)
INFO
Checks supported languages
- IEW113_2311a.exe (PID: 7156)
- IEW113_2311a.exe (PID: 6864)
- msiexec.exe (PID: 948)
- msiexec.exe (PID: 6952)
Create files in a temporary directory
- IEW113_2311a.exe (PID: 7156)
Reads the computer name
- IEW113_2311a.exe (PID: 7156)
- IEW113_2311a.exe (PID: 6864)
- msiexec.exe (PID: 948)
- msiexec.exe (PID: 6952)
The process uses the downloaded file
- IEW113_2311a.exe (PID: 7156)
- IEW113_2311a.exe (PID: 6864)
Process checks computer location settings
- IEW113_2311a.exe (PID: 7156)
- IEW113_2311a.exe (PID: 6864)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4348)
Creates files or folders in the user directory
- msiexec.exe (PID: 4348)
Reads the software policy settings
- msiexec.exe (PID: 4348)
Checks proxy server information
- msiexec.exe (PID: 4348)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4348)
- msiexec.exe (PID: 948)
Manages system restore points
- SrTasks.exe (PID: 5236)
Application launched itself
- msiexec.exe (PID: 948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:07:07 03:01:39+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 219136 |
| InitializedDataSize: | 241664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16600 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.3.10061 |
| ProductVersionNumber: | 1.1.3.10061 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
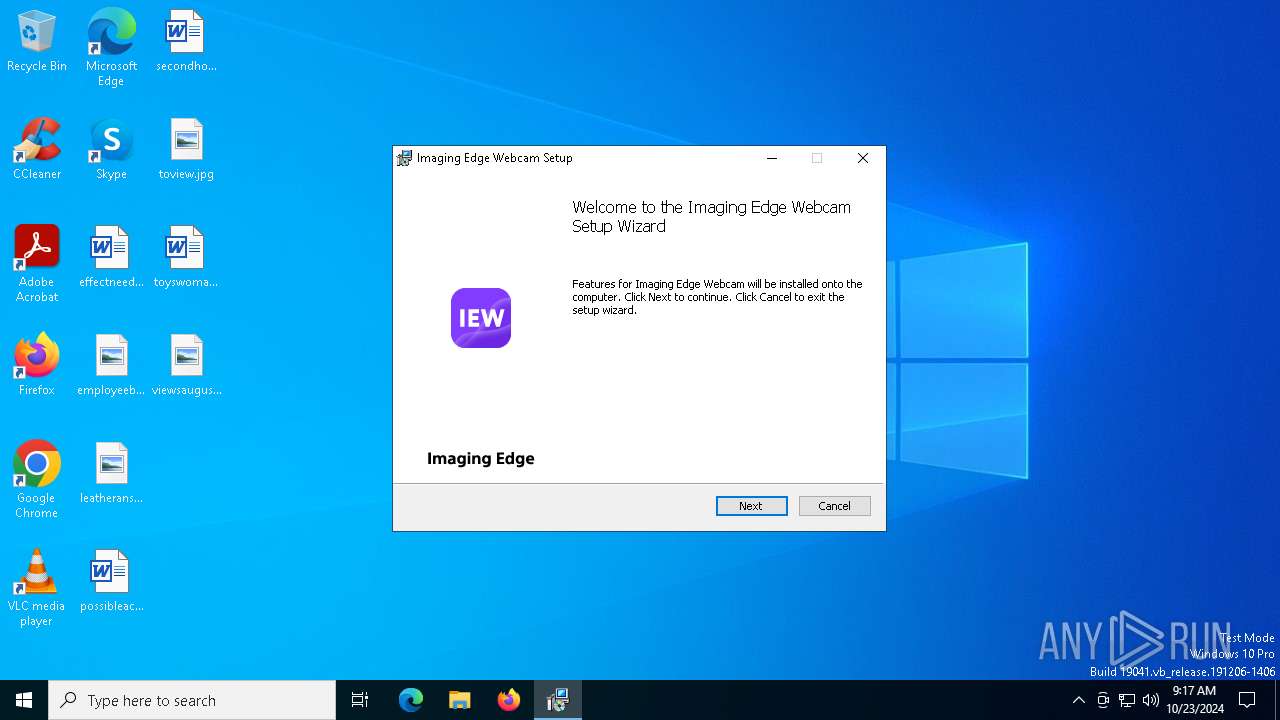
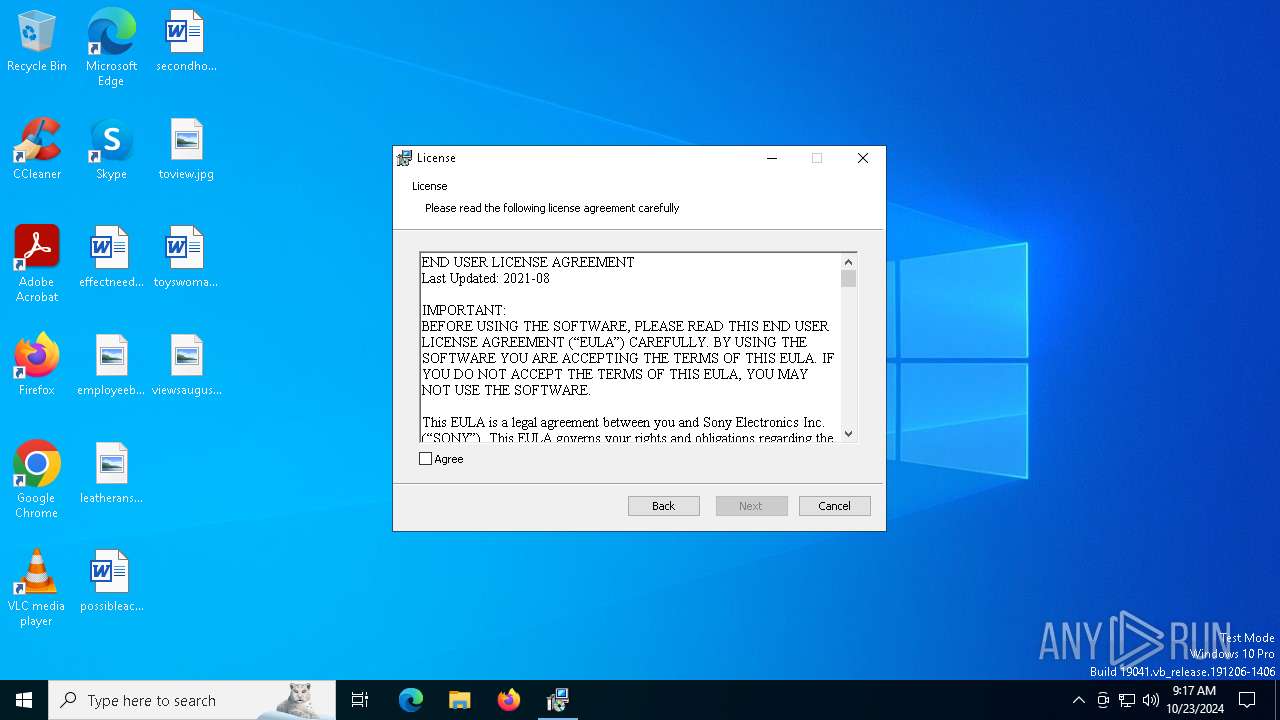
| CompanyName: | Sony Corporation |
| ExtractorVersion: | 5.0.0.06151 |
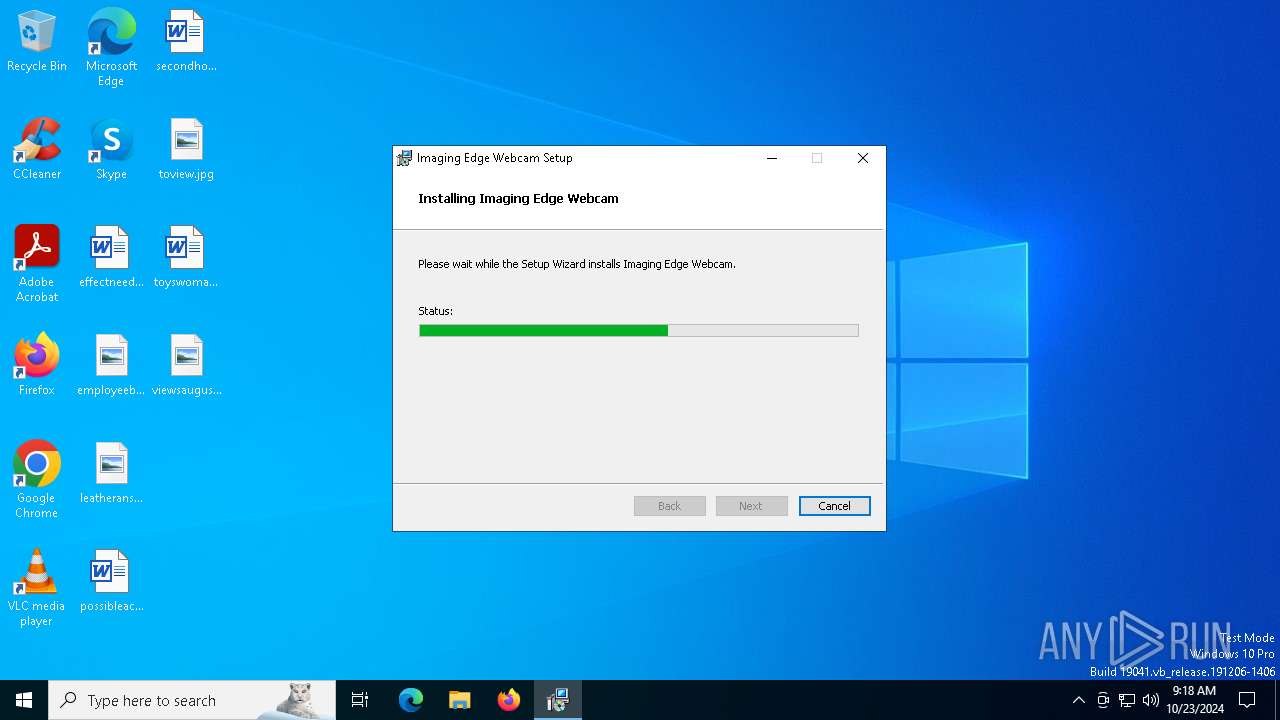
| FileDescription: | Imaging Edge Webcam Installer |
| FileVersion: | 1.1.3.10061 |
| InternalName: | Sony Packaging Tool |
| LegalCopyright: | Copyright 2020, 2021, 2022, 2023 Sony Corporation |
| OriginalFileName: | PackmanExtractor.exe |
| PackagerCID: | C00022 |
| PackagerLID: | M00059 |
| PackagerName: | Sony Packaging Tool |
| PackagerVersion: | 5.0.0.06150 |
| ProductName: | Imaging Edge Webcam |
| ProductVersion: | 1.1.03.10061 |
Total processes
162
Monitored processes
33
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1008 | "C:\Windows\System32\WUDFHost.exe" -HostGUID:{193a1820-d9ac-4997-8c55-be817523f6aa} -IoEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-2b923890-909b-429e-bf4a-134d2b5e9729 -SystemEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-92a0f774-a3e0-4243-a97a-bd74d51d4eaa -IoCancelEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-b9539cf1-4e68-4c5f-98c8-92ec106992b9 -NonStateChangingEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-386a710c-68c8-4be8-b9f5-d4852b7df86f -LifetimeId:108520c5-01b1-4bdc-8659-c5d9e67971ff -DeviceGroupId:WudfDefaultDevicePool -HostArg:0 | C:\Windows\System32\WUDFHost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Driver Foundation - User-mode Driver Framework Host Process Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2416 | DrvInst.exe "1" "0" "root\ImagingEdgeWebcam\0000" "" "" "4c7041fbf" "0000000000000000" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 2416 | "C:\Windows\System32\WUDFHost.exe" -HostGUID:{193a1820-d9ac-4997-8c55-be817523f6aa} -IoEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-7b905ac5-b1c0-4e64-a8ed-185923e9dd7c -SystemEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-33a5f8fb-20c6-4fd6-ae7e-8130d0277c30 -IoCancelEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-c13050ed-c4ac-4a98-a7e8-e230d7f0cb14 -NonStateChangingEventPortName:\UMDFCommunicationPorts\WUDF\HostProcess-b7881f16-3124-4d3d-b490-1b8ba73b0090 -LifetimeId:54bfce08-a80e-4b92-b43e-d47ea899cbbb -DeviceGroupId:WudfDefaultDevicePool -HostArg:0 | C:\Windows\System32\WUDFHost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Driver Foundation - User-mode Driver Framework Host Process Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2692 | cmd /c pnputil /add-driver "C:\Program Files\Sony\Imaging Edge Webcam\Driver\*.inf" /install | C:\Windows\System32\cmd.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3276 | C:\Windows\System32\MsiExec.exe -Embedding 3F4C0289D334A15F35433FD87184AF14 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3648 | rundll32.exe C:\WINDOWS\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{e850b849-f81f-6d4f-beb9-8507f677ccf1} Global\{cd4cc517-378c-0544-b062-69f45f588c63} C:\WINDOWS\System32\DriverStore\Temp\{be44c7b4-be8a-314e-ac19-ae6318c0d5de}\ImagingEdgeWebcam_Driver.inf C:\WINDOWS\System32\DriverStore\Temp\{be44c7b4-be8a-314e-ac19-ae6318c0d5de}\ImagingEdgeWebcam.cat | C:\Windows\System32\rundll32.exe | — | drvinst.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 3700 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4348 | "C:\WINDOWS\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\SPackTool\{B4EDEE18-E910-4A0A-AD9D-10404BC97088}\Package\SetupIEW.msi | C:\Windows\System32\msiexec.exe | IEW113_2311a.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 401
Read events
5 367
Write events
25
Delete events
9
Modification events
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000042DADD712C25DB01B40300003C090000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000042DADD712C25DB01B40300003C090000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000143F31722C25DB01B40300003C090000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000004BA633722C25DB01B40300003C090000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000001E0E36722C25DB01B40300003C090000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000009AF141722C25DB01B40300003C090000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000058DAC9722C25DB01B40300003C090000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A1A4CE722C25DB01B40300001C0A0000E8030000010000000000000000000000CC6CB5B50514F74C8CE104C868EE08BF00000000000000000000000000000000 | |||
| (PID) Process: | (3700) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000008056DF722C25DB01740E0000F8150000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
32
Suspicious files
46
Text files
9
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7156 | IEW113_2311a.exe | C:\Users\admin\AppData\Local\Temp\SPackTool\{B4EDEE18-E910-4A0A-AD9D-10404BC97088}\Support\E8FF0748-2339-49f9-9A79-824D7561736C.cab | — | |
MD5:— | SHA256:— | |||
| 7156 | IEW113_2311a.exe | C:\Users\admin\AppData\Local\Temp\SPackTool\{B4EDEE18-E910-4A0A-AD9D-10404BC97088}\Package\SetupIEW.msi | — | |
MD5:— | SHA256:— | |||
| 948 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 948 | msiexec.exe | C:\Windows\Installer\9644c.msi | — | |
MD5:— | SHA256:— | |||
| 7156 | IEW113_2311a.exe | C:\Users\admin\AppData\Local\Temp\SPackTool\{B4EDEE18-E910-4A0A-AD9D-10404BC97088}\Support\Settings.ini | text | |
MD5:EAAC4B67F55D7363993F1AC326172141 | SHA256:882F197D5002FF35873C2CAF5169B61137E0BB12642AA05B930C26A2D8EA019F | |||
| 948 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{b5b56ccc-1405-4cf7-8ce1-04c868ee08bf}_OnDiskSnapshotProp | binary | |
MD5:712049A781604EFB575294C7948E97B7 | SHA256:FAEE19A32D441E8186B4976D34E2210E2B4D1EF6E6CA84A877BC4D7169B54895 | |||
| 948 | msiexec.exe | C:\Windows\Installer\MSI6806.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 948 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:712049A781604EFB575294C7948E97B7 | SHA256:FAEE19A32D441E8186B4976D34E2210E2B4D1EF6E6CA84A877BC4D7169B54895 | |||
| 4348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_2EEC40BBAAC97AB65B891C8D2BF5DE36 | binary | |
MD5:5A3A03ADCC34CE77671BEAE15B2B8DF2 | SHA256:BDA8F5712C629869C819D5FDE109BD8A3E3FA675893269E181AAC4792F1359C9 | |||
| 948 | msiexec.exe | C:\Windows\Installer\MSI6778.tmp | executable | |
MD5:DE475943D21409F1372093D37FC0A0C8 | SHA256:EB6100F6194060C59C979B470795336F1ECD59757F131A7B7EBA9A6B3B829677 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
44
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4348 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
4348 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4376 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |