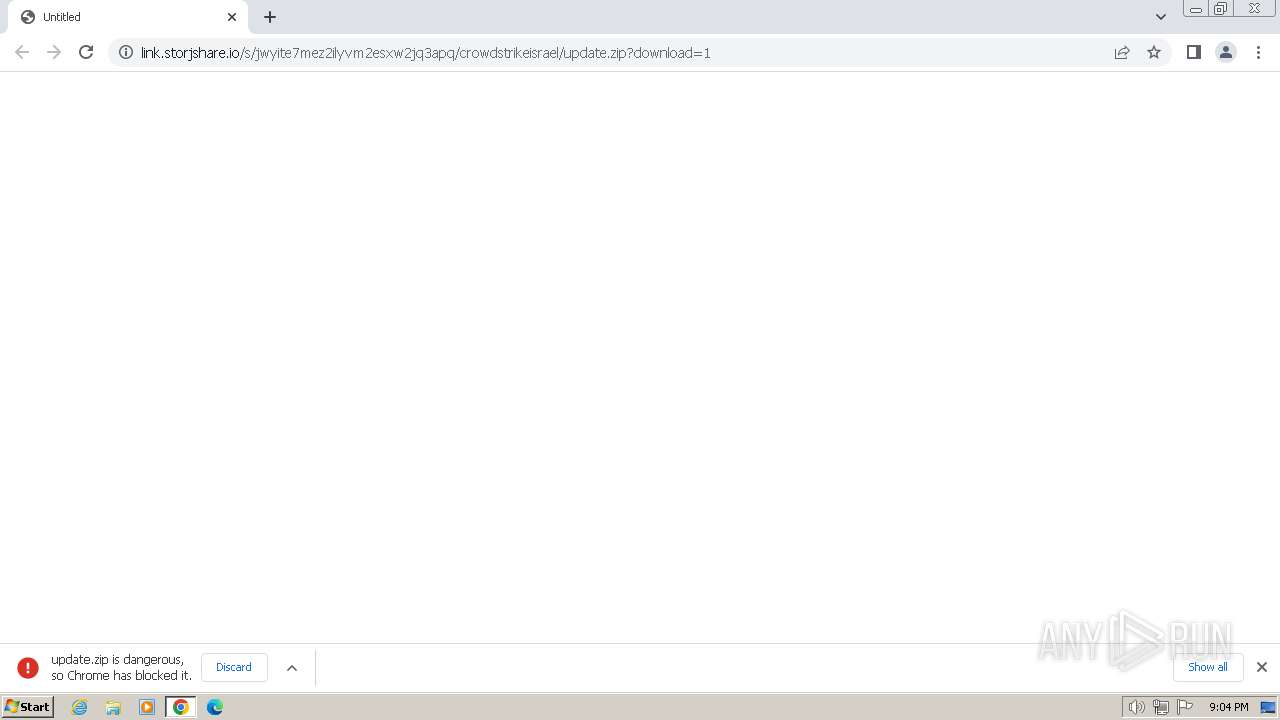
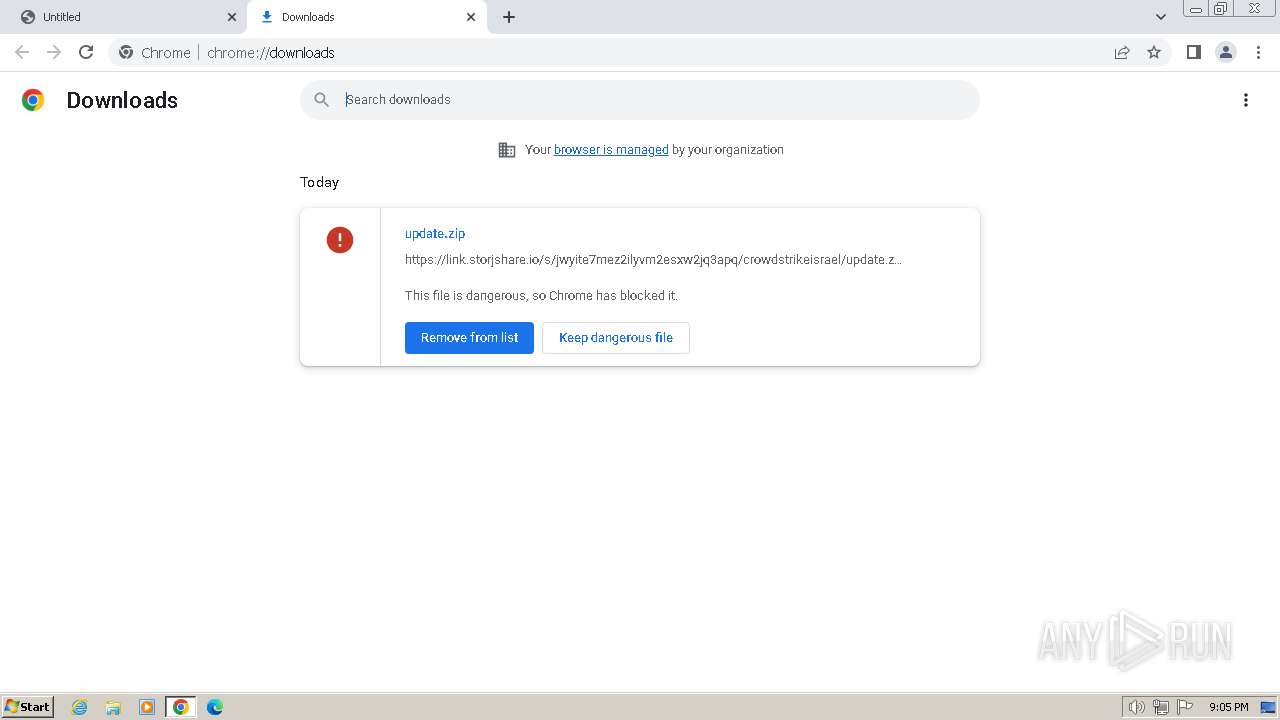
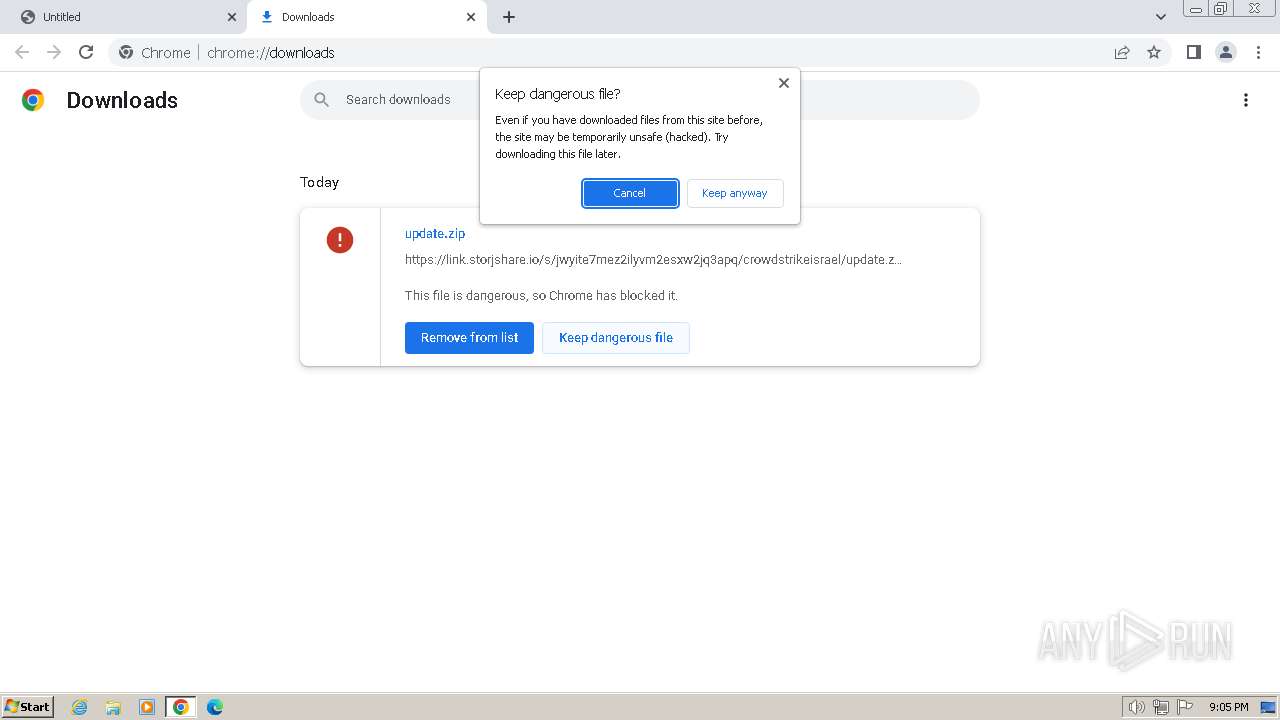
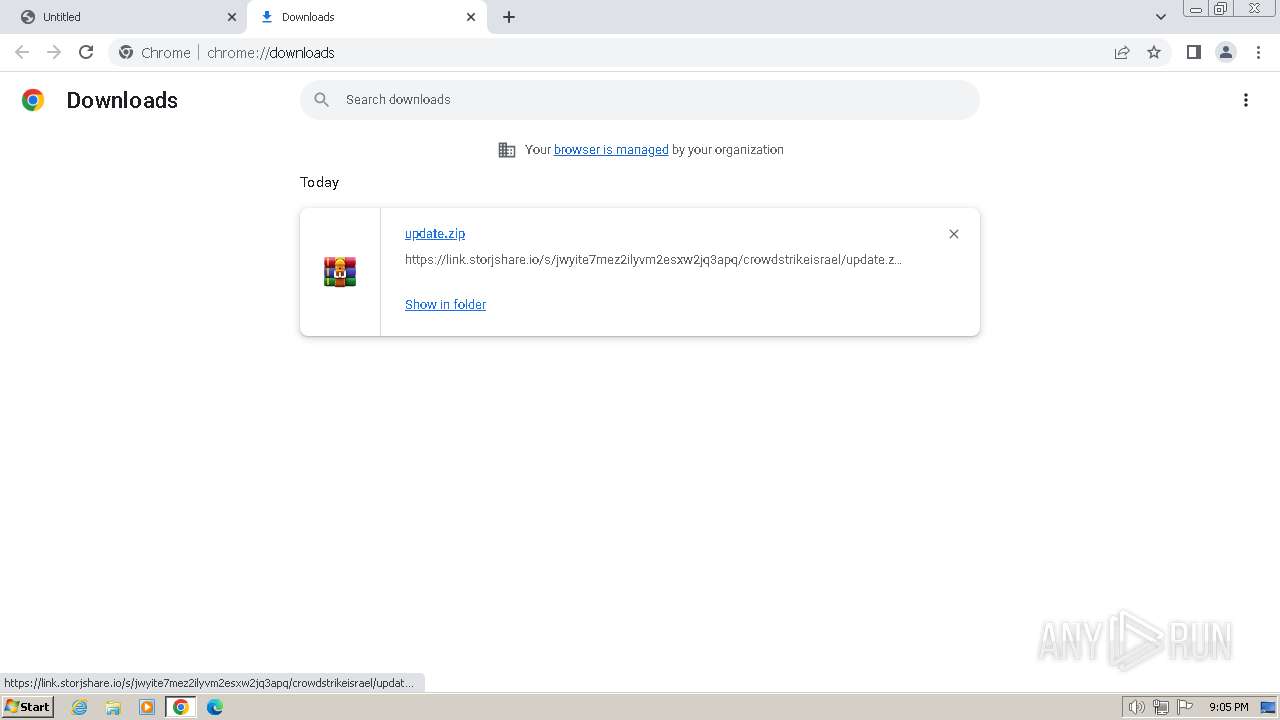
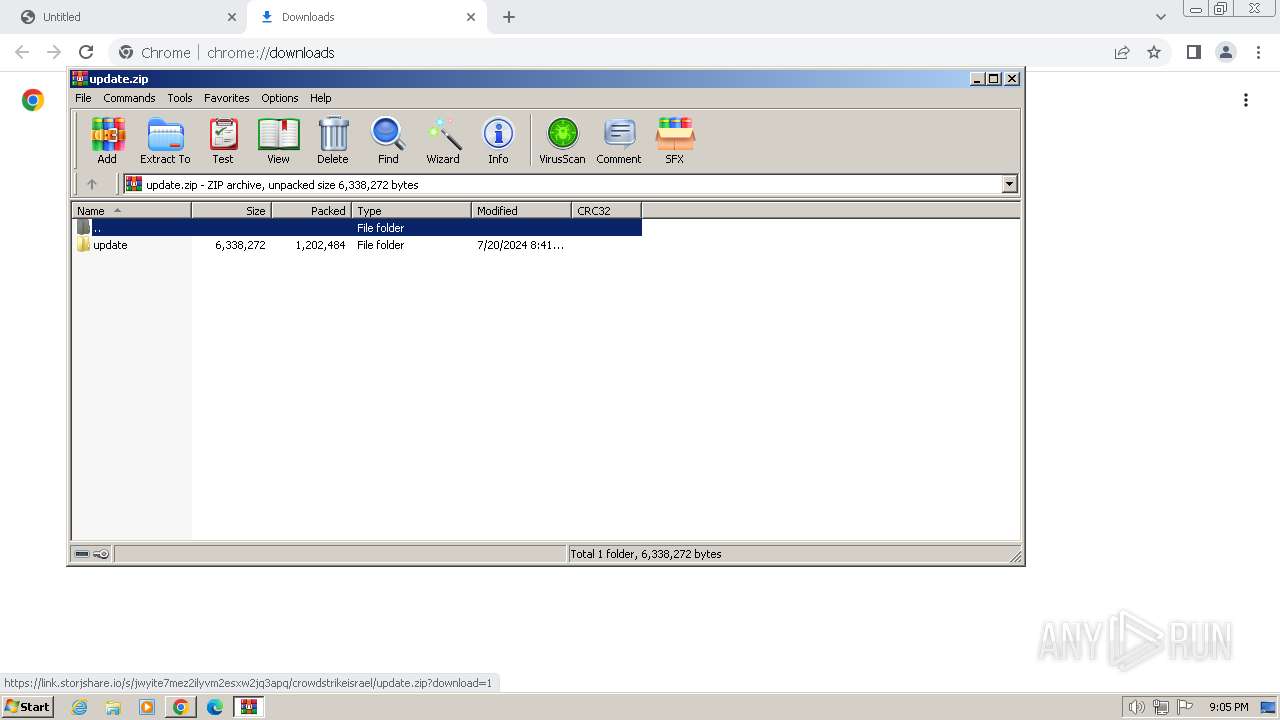
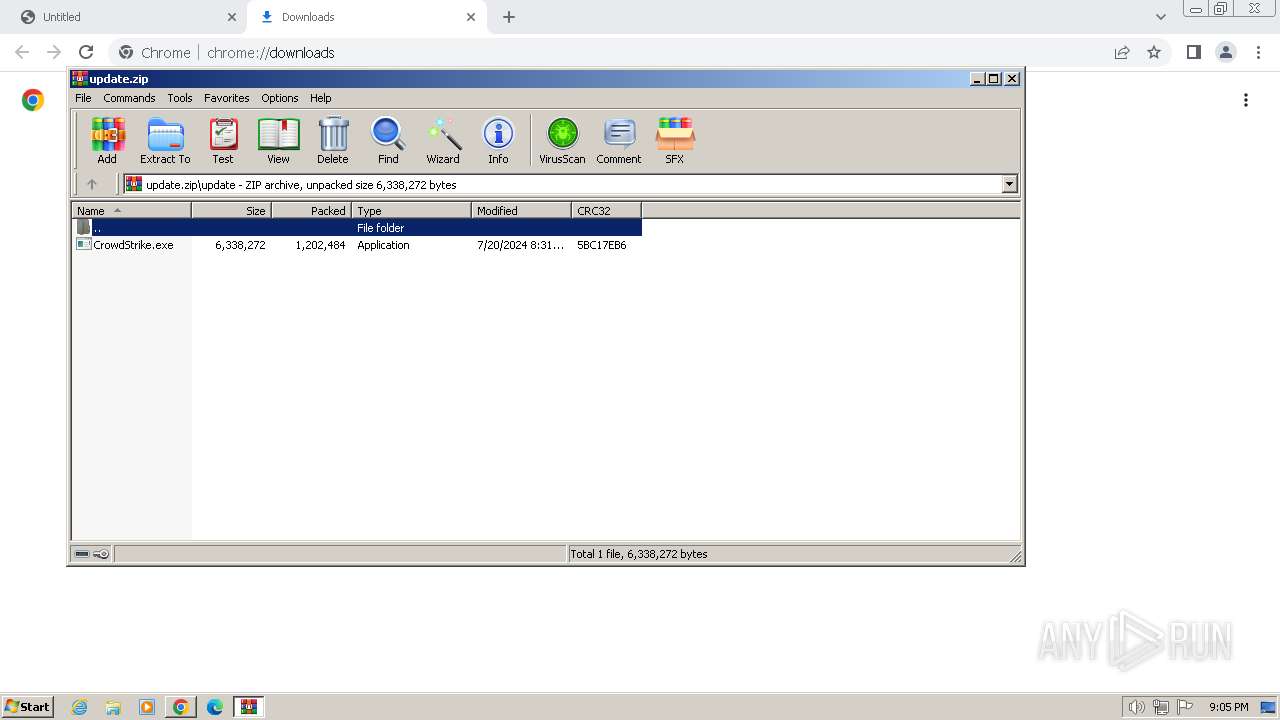
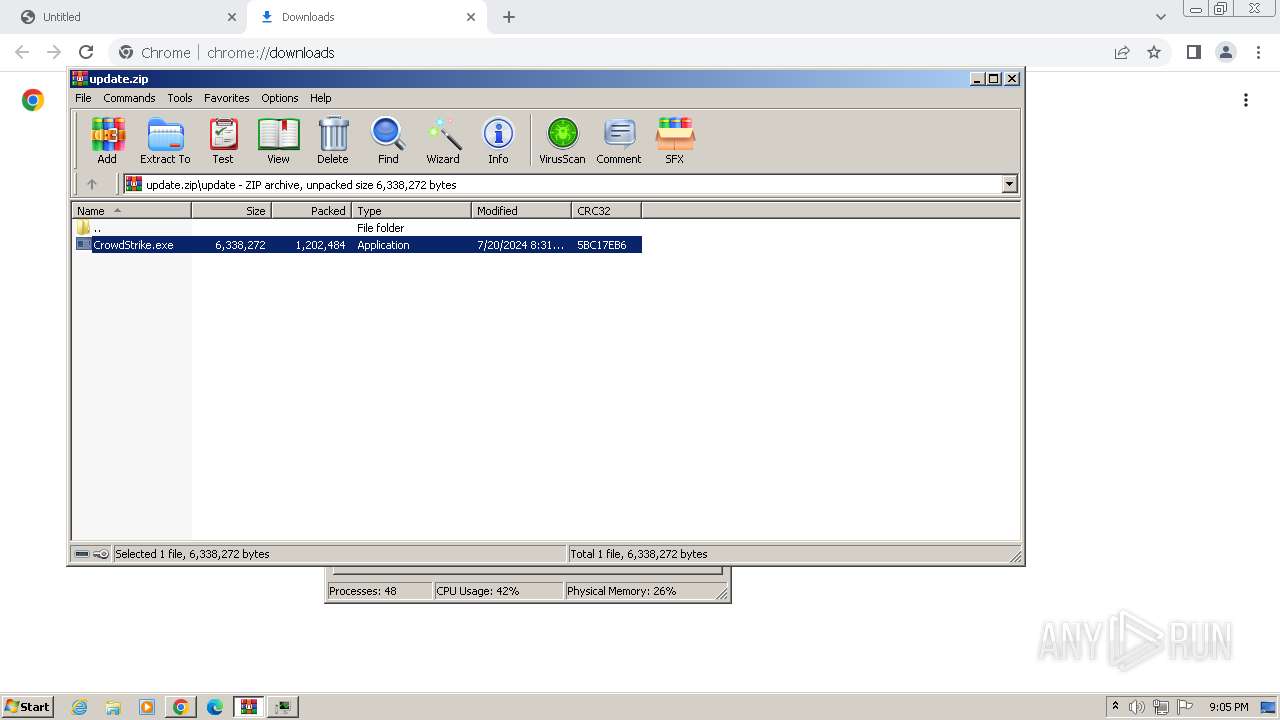
| URL: | https://link.storjshare.io/s/jwyite7mez2ilyvm2esxw2jq3apq/crowdstrikeisrael/update.zip?download=1 |
| Full analysis: | https://app.any.run/tasks/7f2b6509-e1e6-4922-b78a-fca215f63b2e |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2024, 20:04:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 60C49AD134730AEF6DFEBBAC375D8F3D |
| SHA1: | 8F6FF5909F3DD8B138687DCE4D51572B4CE4E516 |
| SHA256: | 45E184F6AC949610F0A36BD6F81E449618EE9F370F3484673263B0F0AEE30887 |
| SSDEEP: | 3:N8MLki4wLz4AtSCPUDVLSBWVpeDnEFUn:2Mgi4yz4QUDf3Etn |
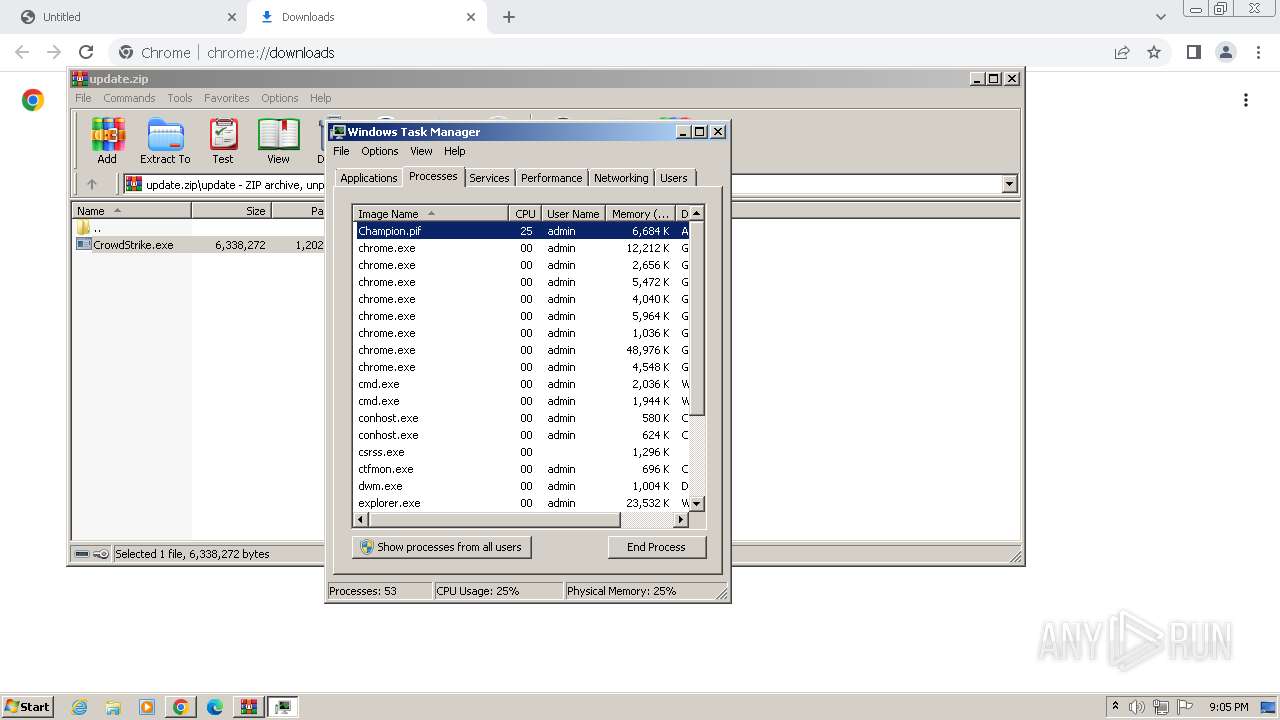
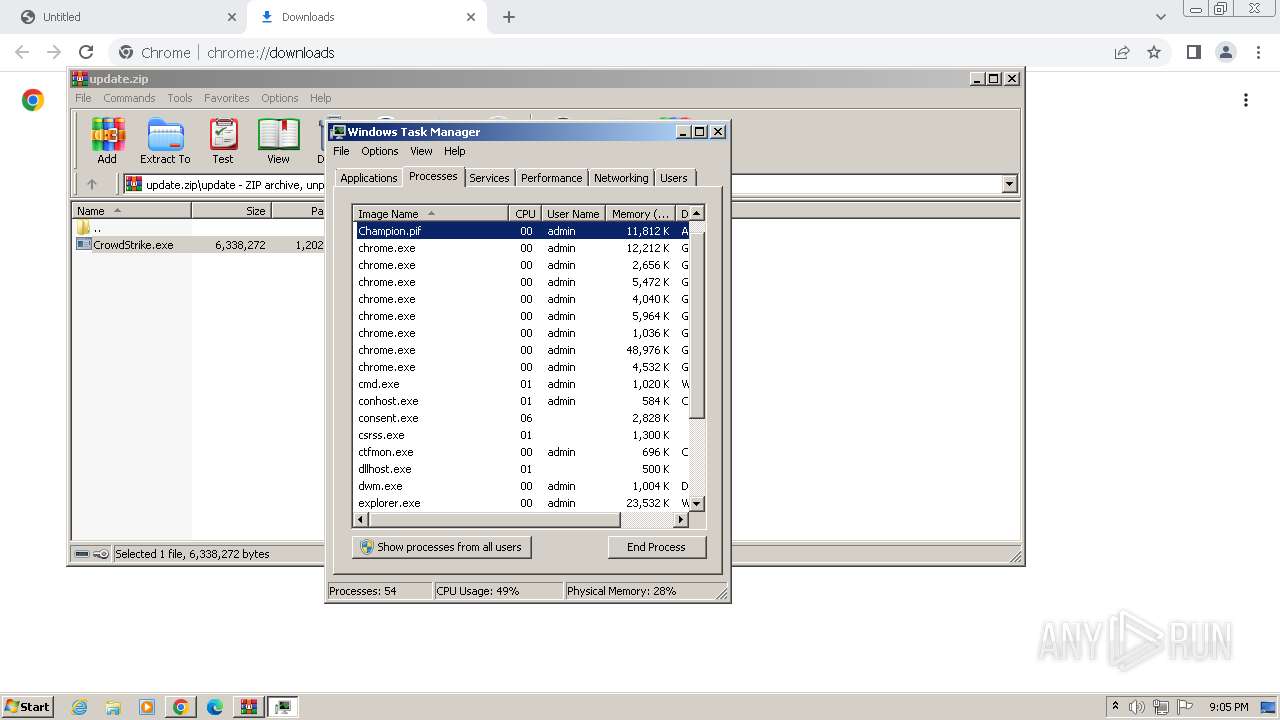
MALICIOUS
Drops the executable file immediately after the start
- CrowdStrike.exe (PID: 3408)
- Champion.pif (PID: 3028)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
- cmd.exe (PID: 2756)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 2032)
- findstr.exe (PID: 1876)
- findstr.exe (PID: 1488)
- findstr.exe (PID: 328)
- findstr.exe (PID: 3300)
- findstr.exe (PID: 3204)
- findstr.exe (PID: 4092)
- findstr.exe (PID: 2328)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Create files in the Startup directory
- RegAsm.exe (PID: 2684)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2588)
- CrowdStrike.exe (PID: 3408)
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- CrowdStrike.exe (PID: 1132)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
Reads the Internet Settings
- CrowdStrike.exe (PID: 3408)
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- CrowdStrike.exe (PID: 1132)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Executing commands from ".cmd" file
- CrowdStrike.exe (PID: 3408)
- CrowdStrike.exe (PID: 2828)
- CrowdStrike.exe (PID: 1132)
- CrowdStrike.exe (PID: 2724)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3316)
Get information on the list of running processes
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3316)
Starts CMD.EXE for commands execution
- CrowdStrike.exe (PID: 3408)
- cmd.exe (PID: 2756)
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- cmd.exe (PID: 3076)
- CrowdStrike.exe (PID: 1132)
- cmd.exe (PID: 2656)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
- cmd.exe (PID: 3316)
Application launched itself
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3316)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 2756)
Executable content was dropped or overwritten
- cmd.exe (PID: 2756)
- Champion.pif (PID: 3028)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Suspicious file concatenation
- cmd.exe (PID: 1280)
- cmd.exe (PID: 2780)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 1832)
Starts application with an unusual extension
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3316)
The executable file from the user directory is run by the CMD process
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- Champion.pif (PID: 3028)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
- Champion.pif (PID: 2032)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2756)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 3316)
Process drops legitimate windows executable
- Champion.pif (PID: 3028)
The process creates files with name similar to system file names
- Champion.pif (PID: 3028)
Starts a Microsoft application from unusual location
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Drops a system driver (possible attempt to evade defenses)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Checks for external IP
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads settings of System Certificates
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Creates file in the systems drive root
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Write to the desktop.ini file (may be used to cloak folders)
- RegAsm.exe (PID: 2684)
- RegAsm.exe (PID: 2688)
INFO
Application launched itself
- chrome.exe (PID: 3380)
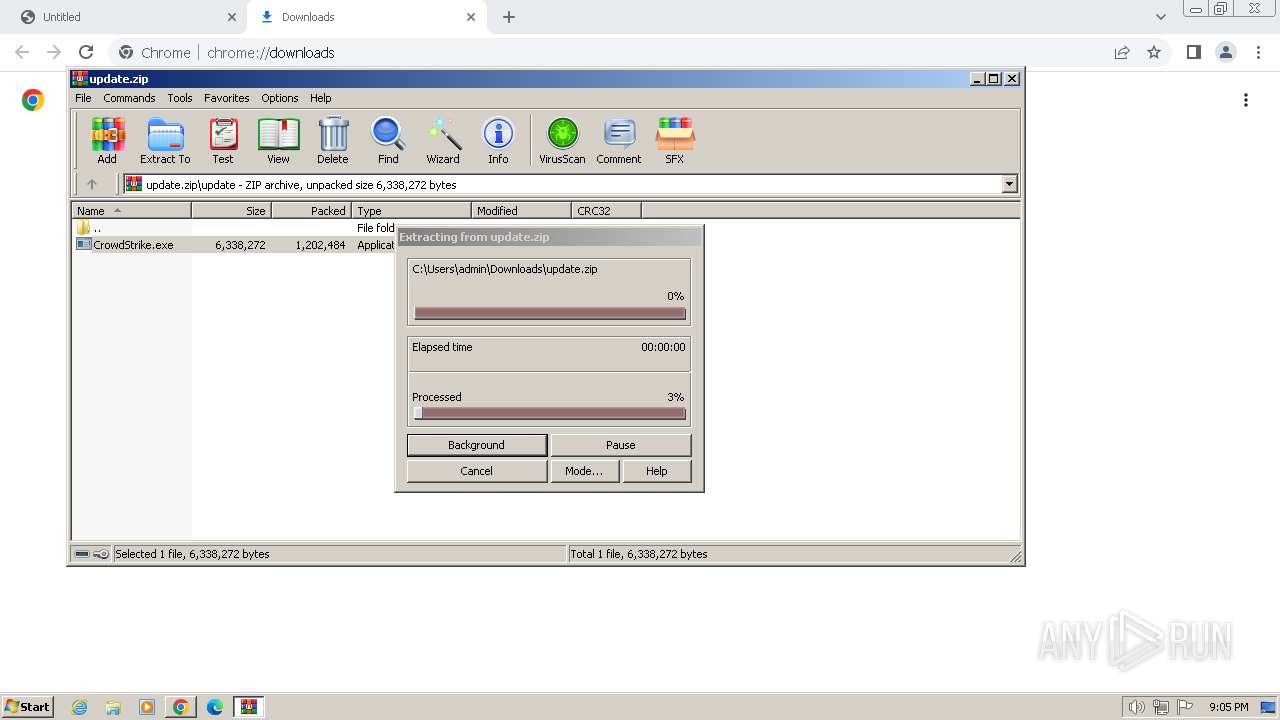
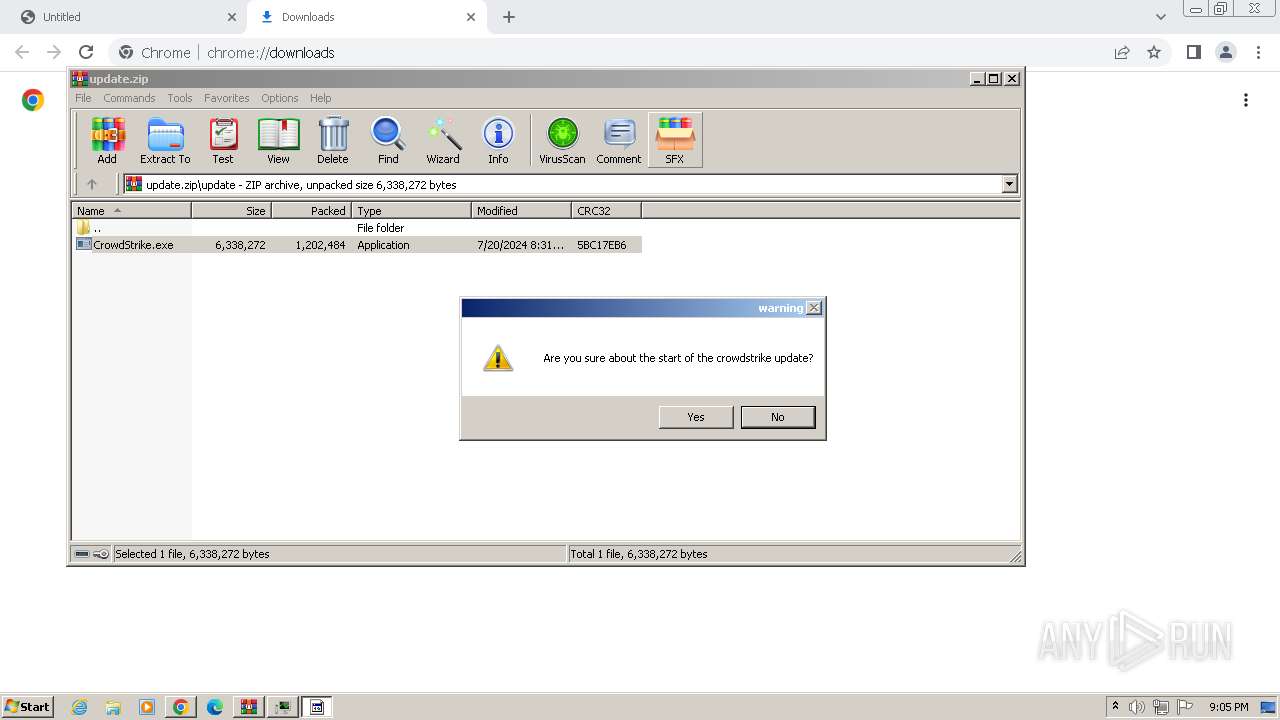
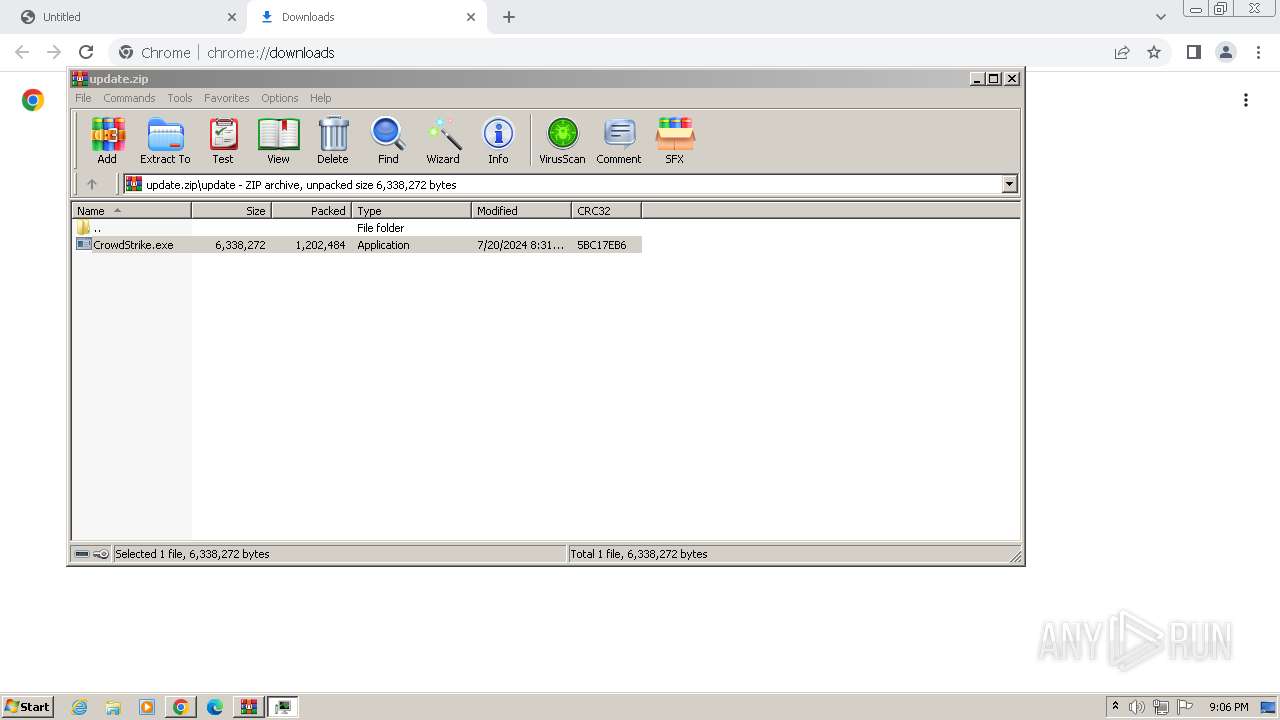
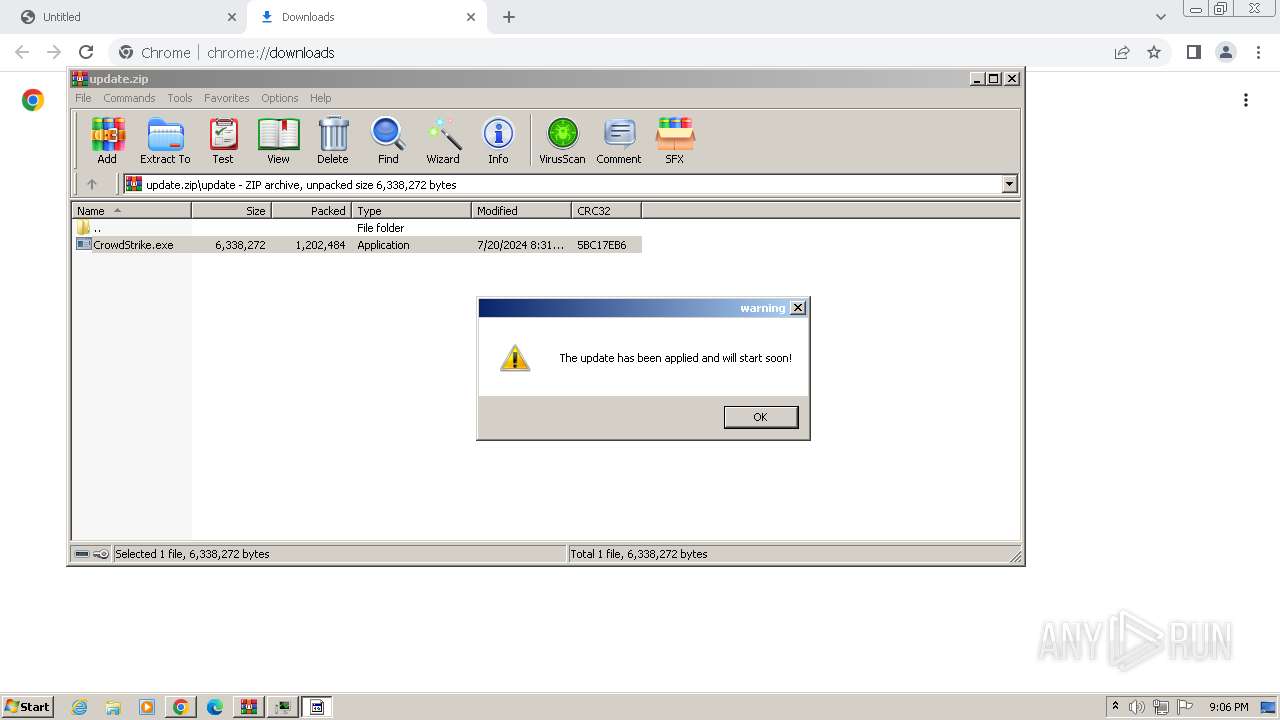
Drops the executable file immediately after the start
- chrome.exe (PID: 3380)
- chrome.exe (PID: 3936)
- WinRAR.exe (PID: 2588)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2248)
Executable content was dropped or overwritten
- chrome.exe (PID: 3936)
- WinRAR.exe (PID: 2588)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 2248)
The process uses the downloaded file
- chrome.exe (PID: 3552)
- WinRAR.exe (PID: 2588)
Create files in a temporary directory
- CrowdStrike.exe (PID: 3408)
- CrowdStrike.exe (PID: 2828)
- Champion.pif (PID: 3028)
- CrowdStrike.exe (PID: 1132)
- CrowdStrike.exe (PID: 2724)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads the computer name
- CrowdStrike.exe (PID: 3408)
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- Champion.pif (PID: 3028)
- CrowdStrike.exe (PID: 1132)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
- Champion.pif (PID: 2032)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Checks supported languages
- CrowdStrike.exe (PID: 3408)
- Champion.pif (PID: 2860)
- CrowdStrike.exe (PID: 2828)
- Champion.pif (PID: 3028)
- CrowdStrike.exe (PID: 1132)
- Champion.pif (PID: 2108)
- CrowdStrike.exe (PID: 2724)
- Champion.pif (PID: 2032)
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads mouse settings
- Champion.pif (PID: 2860)
- Champion.pif (PID: 3028)
- Champion.pif (PID: 2108)
- Champion.pif (PID: 2032)
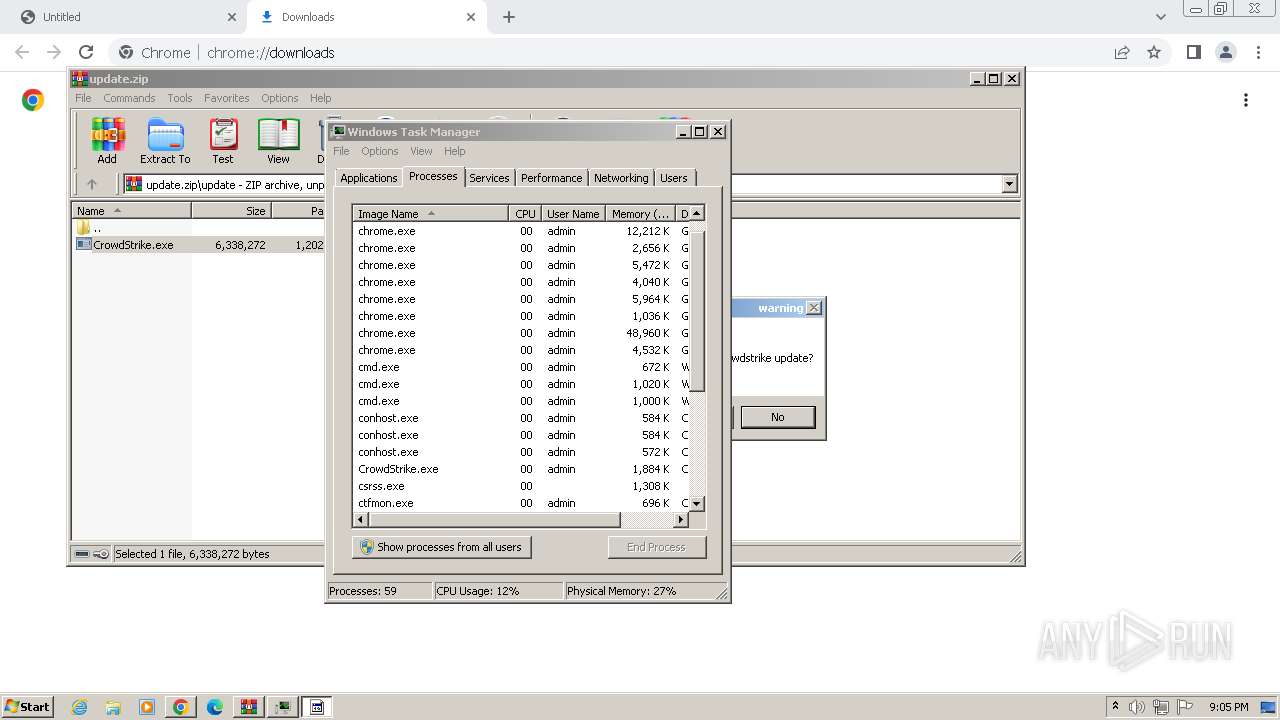
Manual execution by a user
- taskmgr.exe (PID: 3020)
Disables trace logs
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads Environment values
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads the machine GUID from the registry
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Reads the software policy settings
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Attempting to use instant messaging service
- RegAsm.exe (PID: 2688)
- RegAsm.exe (PID: 2684)
Executes as Windows Service
- SearchIndexer.exe (PID: 3044)
Creates files in the program directory
- SearchIndexer.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
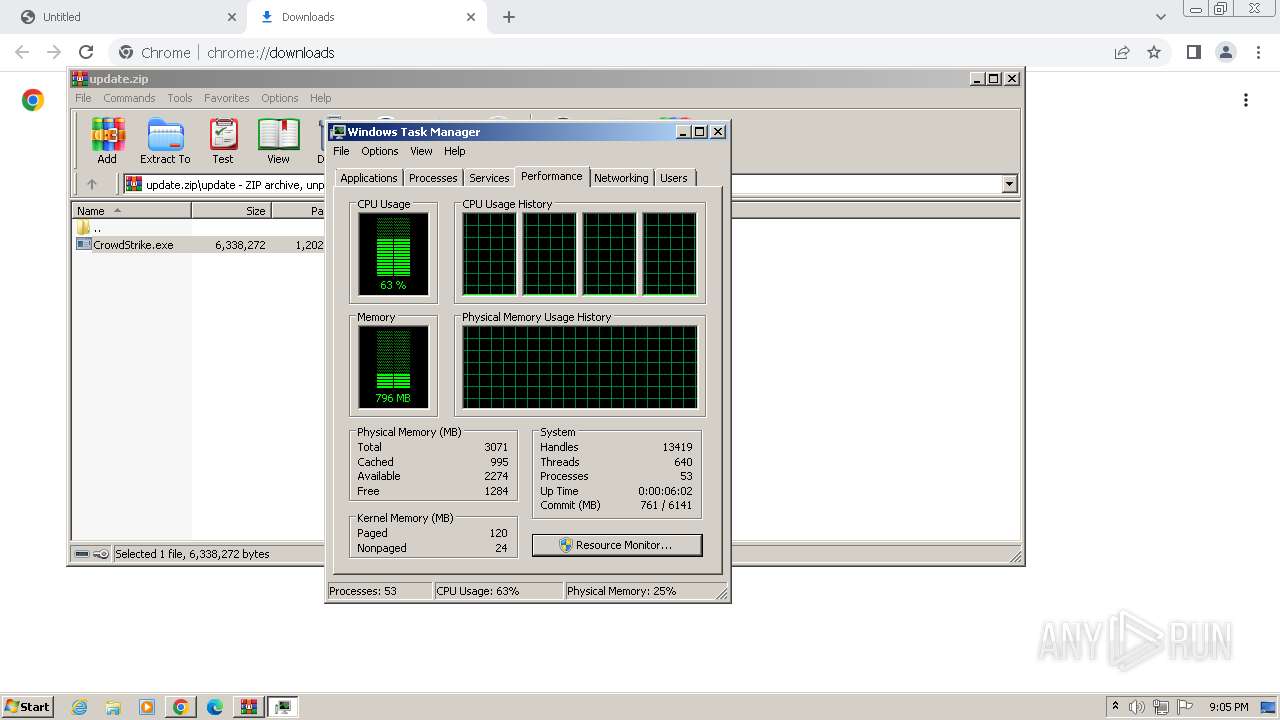
Total processes
123
Monitored processes
71
Malicious processes
14
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | findstr /I "avastui.exe avgui.exe bdservicehost.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2988 --field-trial-handle=1148,i,15622628059887020416,5612690600550771515,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
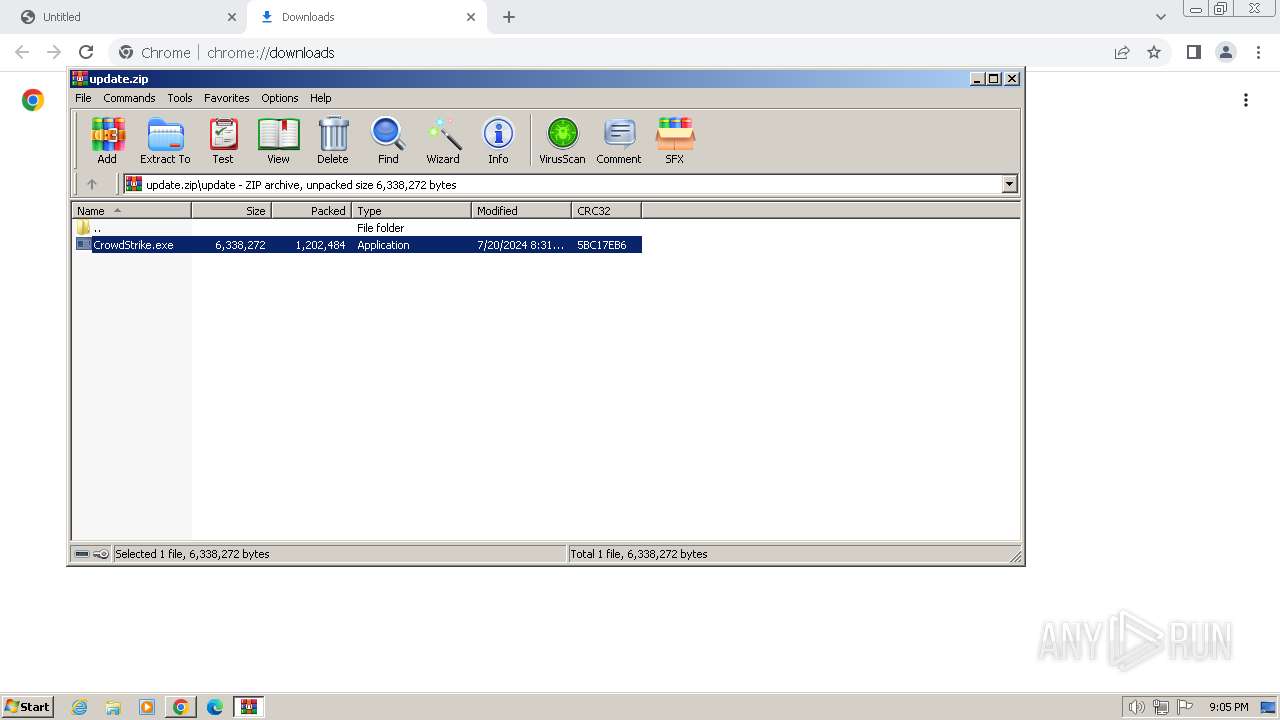
| 1132 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2588.24997\update\CrowdStrike.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2588.24997\update\CrowdStrike.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CrowdStrike Updater Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1164 | cmd /c md 564784 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1280 | cmd /c copy /b Treating + Viagra + Vision + Jul + Str 564784\L | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1284 | findstr /V "locatedflatrendsoperating" Ukraine | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | findstr /I "wrsa.exe opssvc.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | cmd /c md 564784 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1652 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
32 540
Read events
32 313
Write events
210
Delete events
17
Modification events
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
17
Suspicious files
1 494
Text files
42
Unknown types
306
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4ed79.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:FF6BABA737D50E515029C3F3A1305BBC | SHA256:670EED15EAA8E3F1A4F8612B229654EB0C64107AEAF0B1017E4BD45E3F7EED83 | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF4efea.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF4f113.TMP | — | |
MD5:— | SHA256:— | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3380 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF4ed89.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
33
DNS requests
25
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | whitelisted |
2688 | RegAsm.exe | GET | 200 | 104.16.185.241:80 | http://icanhazip.com/ | unknown | — | — | shared |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2960 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
3380 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2960 | chrome.exe | 136.0.77.2:443 | link.storjshare.io | EGIHOSTING | US | unknown |
3380 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2960 | chrome.exe | 216.58.212.174:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
link.storjshare.io |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2960 | chrome.exe | Potentially Bad Traffic | ET INFO File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
2960 | chrome.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
1060 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
2688 | RegAsm.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
1060 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
2688 | RegAsm.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2688 | RegAsm.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2688 | RegAsm.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
2684 | RegAsm.exe | Attempted Information Leak | ET POLICY IP Check Domain (icanhazip. com in HTTP Host) |
Process | Message |
|---|---|
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |
RegAsm.exe | GetDrive failed |