| File name: | MYset1234.exe |
| Full analysis: | https://app.any.run/tasks/f86fd0b0-b000-4b54-b9a4-55cc92368bf2 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 11:49:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 478C61042CF2E405634CD28465332CE8 |
| SHA1: | 4468ECFC493930CCA285E23EAF87D2DA1D7CAA94 |
| SHA256: | 45DB9D9D372EC43413597450D7A888E4AE195E7AE12E1FB9709524469E42ADBA |
| SSDEEP: | 12288:Dgeh+QxEID1Rgf4tQnPkTFhpviFrXsmnztHf5lRpde4acO3qZjXfaGcU9lt/:rhzGIJ5yPYgtXsKfnRX5/O/GcU9l1 |
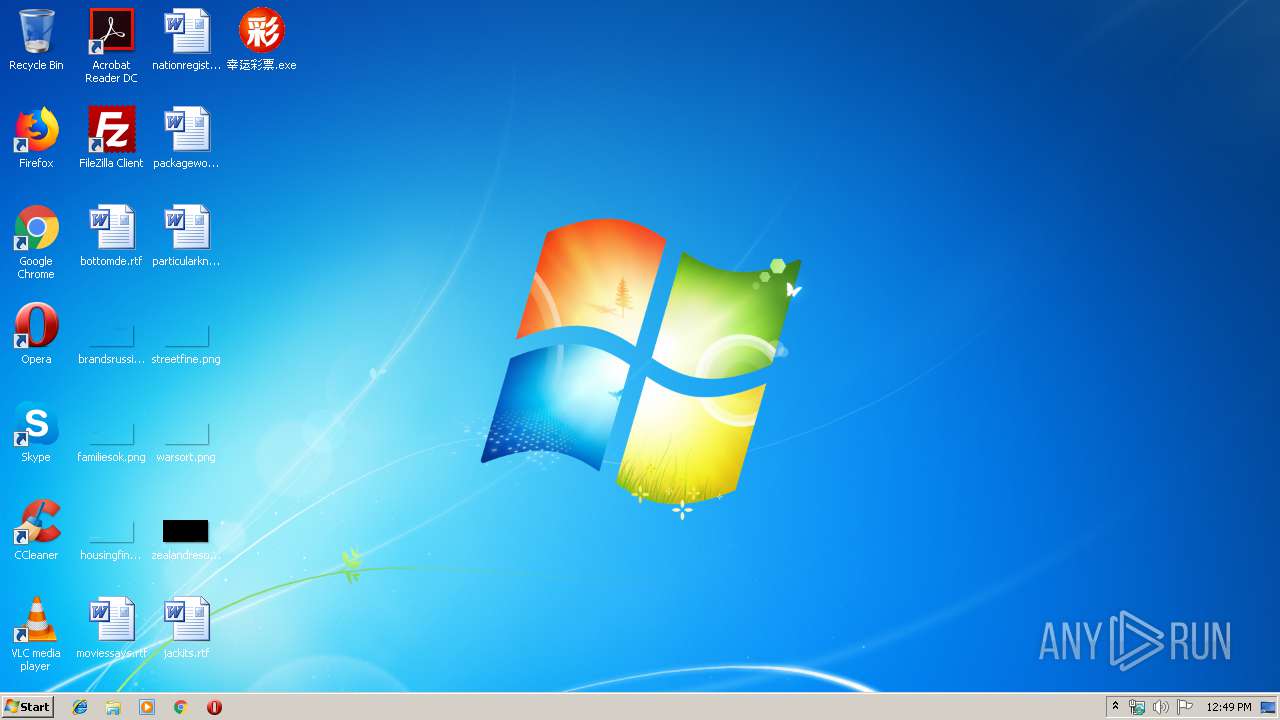
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2328)
- cmd.exe (PID: 3480)
SUSPICIOUS
Starts application with an unusual extension
- MYset1234.exe (PID: 4060)
- cmd.exe (PID: 2212)
Executable content was dropped or overwritten
- MYset1234.exe (PID: 4060)
Starts CMD.EXE for commands execution
- MYset1234.exe (PID: 4060)
Changes the started page of IE
- MYset1234.exe (PID: 4060)
- reg.exe (PID: 3920)
Writes to a desktop.ini file (may be used to cloak folders)
- Fav~Url.tmp (PID: 3332)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3480)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Clipper DOS Executable (19.1) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:04:10 02:11:21+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 286720 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 512000 |
| EntryPoint: | 0xc7304 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.13.710 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 5.0.13.710 |
| LegalCopyright: | Copyright (C) 2010-2013 DaBaiCai.Com |
| ProductVersion: | 5 |
| CompanyName: | DaBaiCai.Com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Apr-2012 00:11:21 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Apr-2012 00:11:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.textbss | 0x00001000 | 0x000C6000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.text | 0x000C7000 | 0x00002000 | 0x00001600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.99667 |
.data | 0x000C9000 | 0x0006F000 | 0x0006F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.79644 |
.idata | 0x00138000 | 0x00001000 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.63289 |
.rsrc | 0x00139000 | 0x00001000 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.24509 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09117 | 791 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 0 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 0 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 2.67657 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 2.32506 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 0 | 542 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 0 | 720 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 0 | 542 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 0 | 760 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 0 | 764 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
USERENV.dll |
Total processes
48
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2212 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\fbinst.dll "C:\Windows\dbcOnce\SUPPORT.IM_" output IMG/* %~nx | C:\Windows\system32\cmd.exe | — | MYset1234.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2328 | C:\Windows\system32\cmd.exe /c ping 127.0.0.1 -n 3&del /q "C:\Users\admin\AppData\Local\Temp\MYset1234.exe" | C:\Windows\system32\cmd.exe | — | MYset1234.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2684 | C:\Users\admin\AppData\Local\Temp\fbinst.dll "C:\Windows\dbcOnce\SUPPORT.IM_" output IMG/* %~nx | C:\Users\admin\AppData\Local\Temp\fbinst.dll | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3016 | ping 127.0.0.1 -n 3 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | C:\Users\admin\AppData\Local\dbcTMP\Fav~Url.tmp -y -o"C:\Users\admin\Favorites" | C:\Users\admin\AppData\Local\dbcTMP\Fav~Url.tmp | — | MYset1234.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3480 | C:\Windows\system32\cmd.exe /c ping 127.0.0.1 -n 50® add "HKCU\Software\Microsoft\Internet Explorer\Main" /v "Start Page" /d "www.hao123.com.bz" /f | C:\Windows\system32\cmd.exe | — | MYset1234.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\AppData\Local\Temp\MYset1234.exe" | C:\Users\admin\AppData\Local\Temp\MYset1234.exe | — | explorer.exe | |||||||||||
User: admin Company: DaBaiCai.Com Integrity Level: MEDIUM Exit code: 3221226540 Version: 5.0.13.710 Modules
| |||||||||||||||
| 3920 | reg add "HKCU\Software\Microsoft\Internet Explorer\Main" /v "Start Page" /d "www.hao123.com.bz" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4044 | ping 127.0.0.1 -n 50 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Users\admin\AppData\Local\Temp\MYset1234.exe" | C:\Users\admin\AppData\Local\Temp\MYset1234.exe | explorer.exe | ||||||||||||
User: admin Company: DaBaiCai.Com Integrity Level: HIGH Exit code: 0 Version: 5.0.13.710 Modules
| |||||||||||||||
Total events
52
Read events
50
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4060) MYset1234.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: www.hao123.com.bz | |||
| (PID) Process: | (3920) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: www.hao123.com.bz | |||
Executable files
1
Suspicious files
0
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\aut9FCF.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\gtofspg | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\aut9FFF.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\dbcTMP\Fav~Url.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\autA06D.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\autA06E.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | MYset1234.exe | C:\Users\admin\AppData\Local\Temp\fbinst.dll | — | |
MD5:— | SHA256:— | |||
| 3332 | Fav~Url.tmp | C:\Users\admin\Favorites\淘宝购物\淘宝网 - 电器城.URL | text | |
MD5:— | SHA256:— | |||
| 3332 | Fav~Url.tmp | C:\Users\admin\Favorites\站台网-中国第一家分类信息网.url | text | |
MD5:— | SHA256:— | |||
| 3332 | Fav~Url.tmp | C:\Users\admin\Favorites\4466网页游戏平台.url | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report