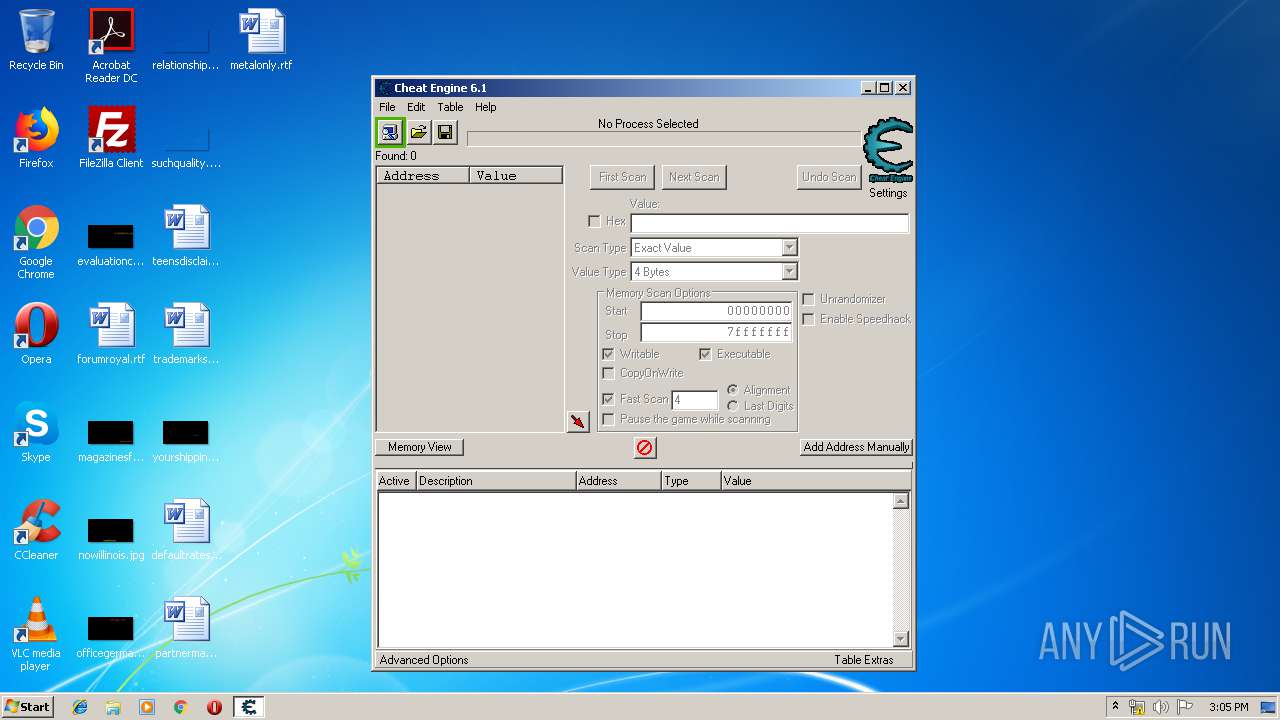
| File name: | Cheat Engine 6.1 Portable.exe |
| Full analysis: | https://app.any.run/tasks/a215bfcb-b799-43d3-ab64-76534ff94640 |
| Verdict: | No threats detected |
| Analysis date: | July 27, 2019, 14:04:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8481768B3E16D25E994497542E1AA706 |
| SHA1: | 2548DCAECC11593984B2D97CDE95A01ED6CDC331 |
| SHA256: | 45DA2F687B0063F592D5FBD1E99E566240D4186CBBEB032C2C9395ED7F787A65 |
| SSDEEP: | 196608:nM+iUz1joJwOx7g7bTC9MBF5eKWwDCQPqFR:M+f0U3CupZD0H |
MALICIOUS
Application was dropped or rewritten from another process
- cheatengine-i386.exe (PID: 540)
- Cheat Engine.exe (PID: 1940)
Loads dropped or rewritten executable
- cheatengine-i386.exe (PID: 540)
SUSPICIOUS
Executable content was dropped or overwritten
- Cheat Engine 6.1 Portable.exe (PID: 2160)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (87.9) |
|---|---|---|
| .exe | | | InstallShield setup (7.3) |
| .scr | | | Windows screen saver (2.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:03:28 21:23:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 84480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 28-Mar-2006 19:23:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 28-Mar-2006 19:23:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44972 |
.data | 0x00014000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.73184 |
.idata | 0x0001B000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05399 |
.rsrc | 0x0001C000 | 0x00012FE0 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.54437 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
7 | 3.24143 | 556 | Latin 1 / Western European | Russian - Russia | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | Russian - Russia | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | Russian - Russia | RT_STRING |
100 | 1.98048 | 20 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
101 | 4.19099 | 2998 | Latin 1 / Western European | Russian - Russia | RT_BITMAP |
ASKNEXTVOL | 3.42532 | 642 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
GETPASSWORD1 | 3.29928 | 314 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
LICENSEDLG | 3.17045 | 232 | Latin 1 / Western European | Russian - Russia | RT_DIALOG |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
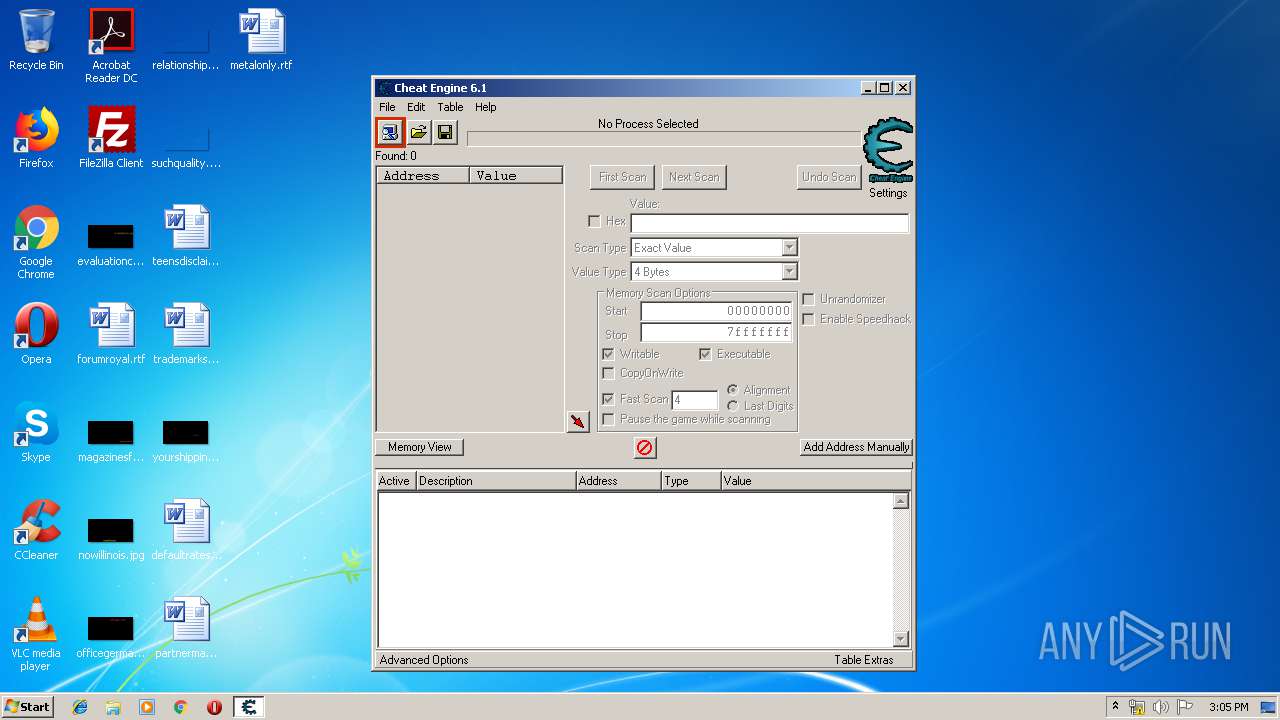
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
1
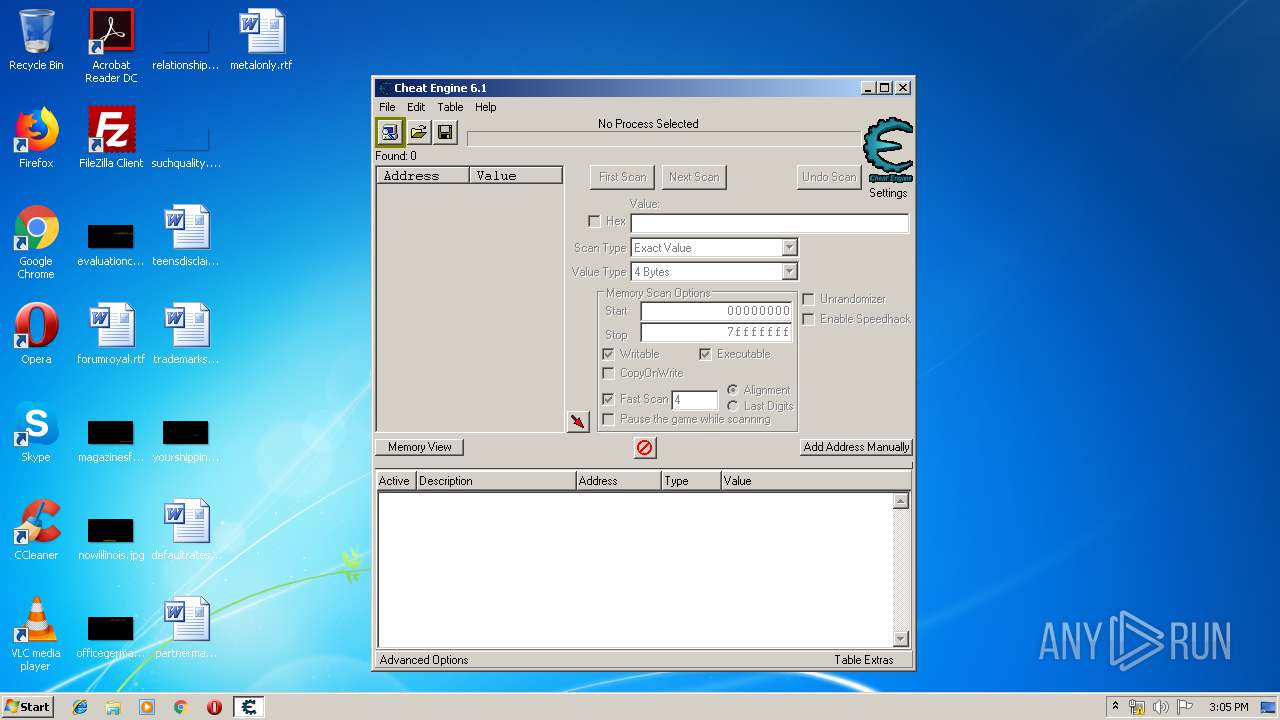
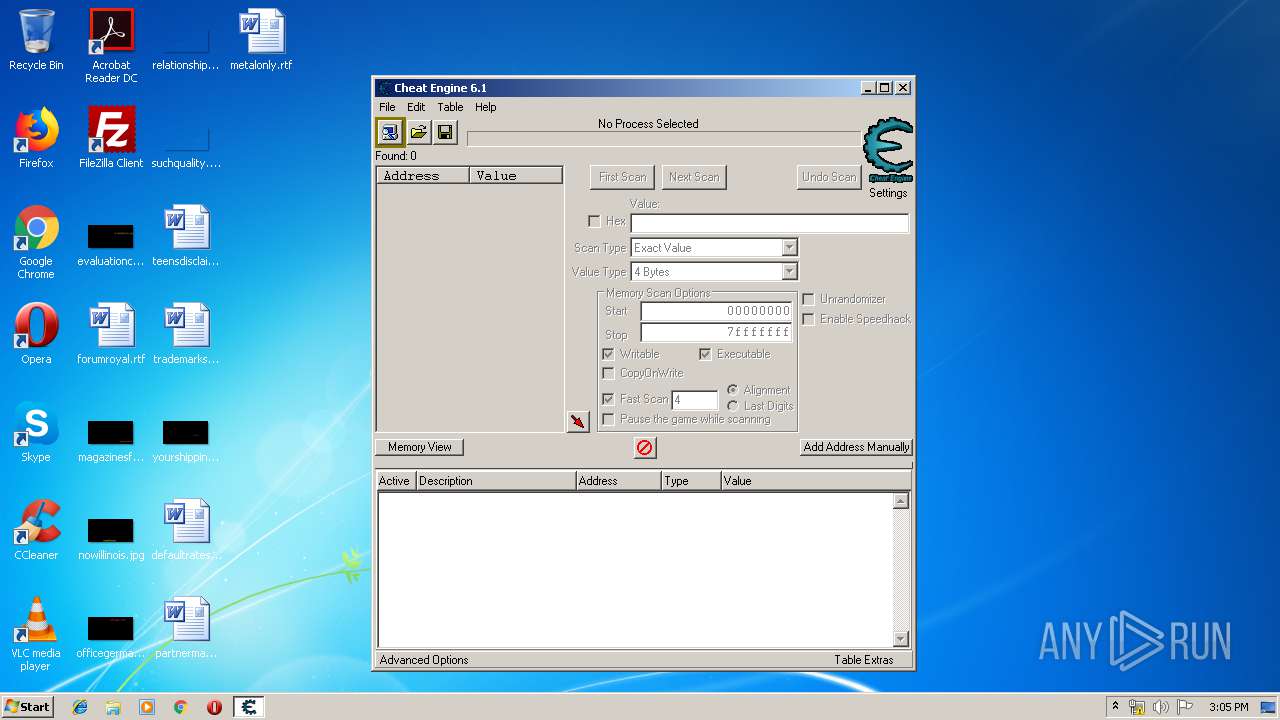
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\cheatengine-i386.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\cheatengine-i386.exe | Cheat Engine.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Exit code: 0 Version: 6.1.0.1561 Modules
| |||||||||||||||
| 1940 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Cheat Engine.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Cheat Engine.exe | — | Cheat Engine 6.1 Portable.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\Cheat Engine 6.1 Portable.exe" | C:\Users\admin\AppData\Local\Temp\Cheat Engine 6.1 Portable.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\AppData\Local\Temp\Cheat Engine 6.1 Portable.exe" | C:\Users\admin\AppData\Local\Temp\Cheat Engine 6.1 Portable.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
745
Read events
733
Write events
12
Delete events
0
Modification events
| (PID) Process: | (1940) Cheat Engine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1940) Cheat Engine.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2160) Cheat Engine 6.1 Portable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2160) Cheat Engine 6.1 Portable.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (540) cheatengine-i386.exe | Key: | HKEY_CURRENT_USER\Software\Cheat Engine |
| Operation: | write | Name: | Undo |
Value: 1 | |||
| (PID) Process: | (540) cheatengine-i386.exe | Key: | HKEY_CURRENT_USER\Software\Cheat Engine |
| Operation: | write | Name: | Advanced |
Value: 1 | |||
| (PID) Process: | (540) cheatengine-i386.exe | Key: | HKEY_CURRENT_USER\Software\Cheat Engine |
| Operation: | write | Name: | ScanThreadpriority |
Value: 4 | |||
| (PID) Process: | (540) cheatengine-i386.exe | Key: | HKEY_CURRENT_USER\Software\Cheat Engine |
| Operation: | write | Name: | First Time User |
Value: 0 | |||
Executable files
24
Suspicious files
0
Text files
21
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dbk32.sys | executable | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dbk64.sys | executable | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\main.lua | text | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lua5.1-64.dll | executable | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\standalonephase1.dat | executable | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\CheatEngine.chm | chm | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\cheatengine-x86_64.exe | executable | |
MD5:— | SHA256:— | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\cheatengine-i386.exe | executable | |
MD5:AB9983B19AE94F47CC870E1914955370 | SHA256:CE481709C585D0EFEEBABCE7DA99ED338D0FAA80556EAC6FD150FD44ED1F0B48 | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\commonmodulelist.txt | text | |
MD5:9FA5FDFEAAC678D34B4348851C13D08F | SHA256:20D482EE7A13AAB6299B1197B67F303488BB0BB96B698D31D1A57857D989B75D | |||
| 2160 | Cheat Engine 6.1 Portable.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Kernelmoduleunloader.exe | executable | |
MD5:591D309FC8A2EE10A1D09E4D0113C88F | SHA256:697616AEEC9A06070282F6DBA0983E91182F6DB7B02BAA6DE7DA5375165FB0AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
cheatengine-i386.exe | Offset of LBR_Count=760 |
cheatengine-i386.exe | sizeof fxstate = 512 |