| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/daa96908-7e72-4e0f-a2b7-c221b7375c4c |
| Verdict: | Suspicious activity |
| Analysis date: | November 09, 2018, 19:24:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8B9EF2AA30DACDD8BDA125DE95415038 |
| SHA1: | 6572EAEEA44198937994C06E77DE947E8087D02E |
| SHA256: | 45D413CD160EA0E41EC40A4AB9E6E206263F7608AF4C15D979645199FDE86805 |
| SSDEEP: | 98304:VZ1hCFd+mS9C+WxoM8CtkskTNfNZ2ynS9KGqpS0vYW:VZrCFda9CZx0vZ2y/HSzW |
MALICIOUS
Application was dropped or rewritten from another process
- unins000.exe (PID: 4052)
- _iu14D2N.tmp (PID: 2664)
Loads dropped or rewritten executable
- _iu14D2N.tmp (PID: 2664)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 1440)
- unins000.exe (PID: 4052)
- setup.tmp (PID: 352)
- _iu14D2N.tmp (PID: 2664)
Reads the Windows organization settings
- setup.tmp (PID: 352)
- _iu14D2N.tmp (PID: 2664)
Starts application with an unusual extension
- unins000.exe (PID: 4052)
Reads Windows owner or organization settings
- setup.tmp (PID: 352)
- _iu14D2N.tmp (PID: 2664)
Starts itself from another location
- unins000.exe (PID: 4052)
INFO
Loads dropped or rewritten executable
- setup.tmp (PID: 352)
Application was dropped or rewritten from another process
- setup.tmp (PID: 352)
Creates files in the program directory
- setup.tmp (PID: 352)
Creates a software uninstall entry
- setup.tmp (PID: 352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 81408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
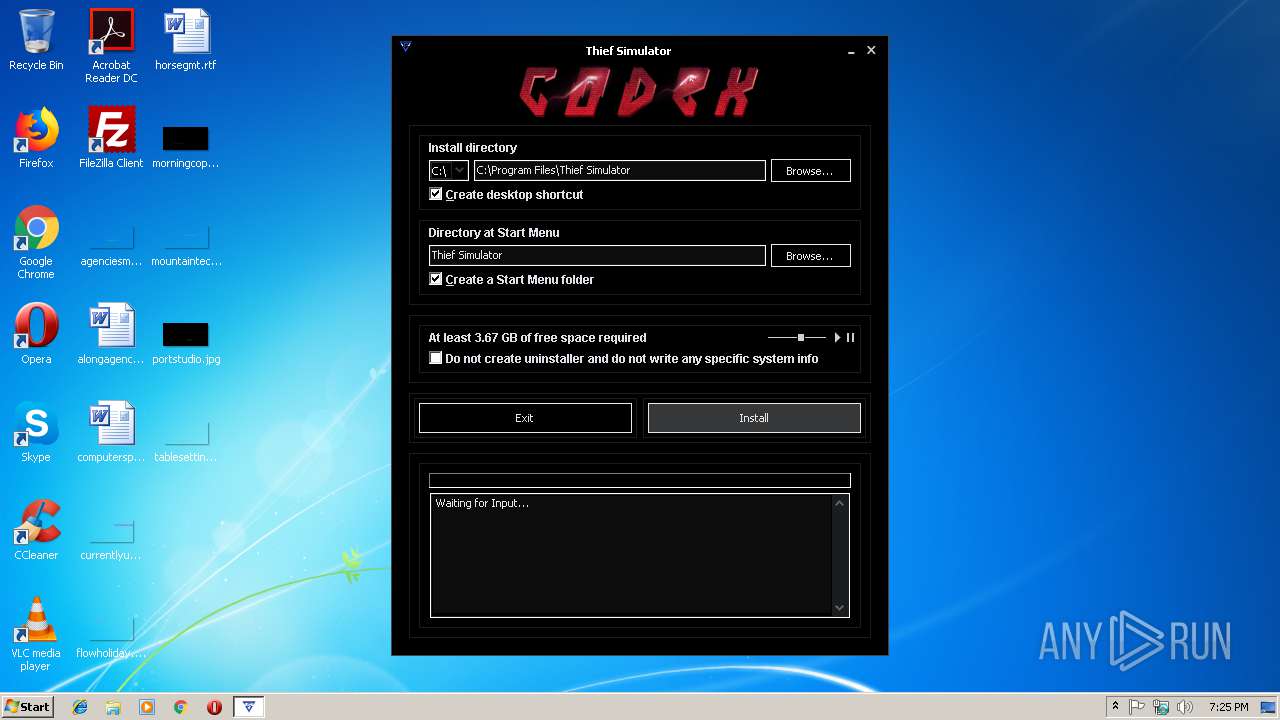
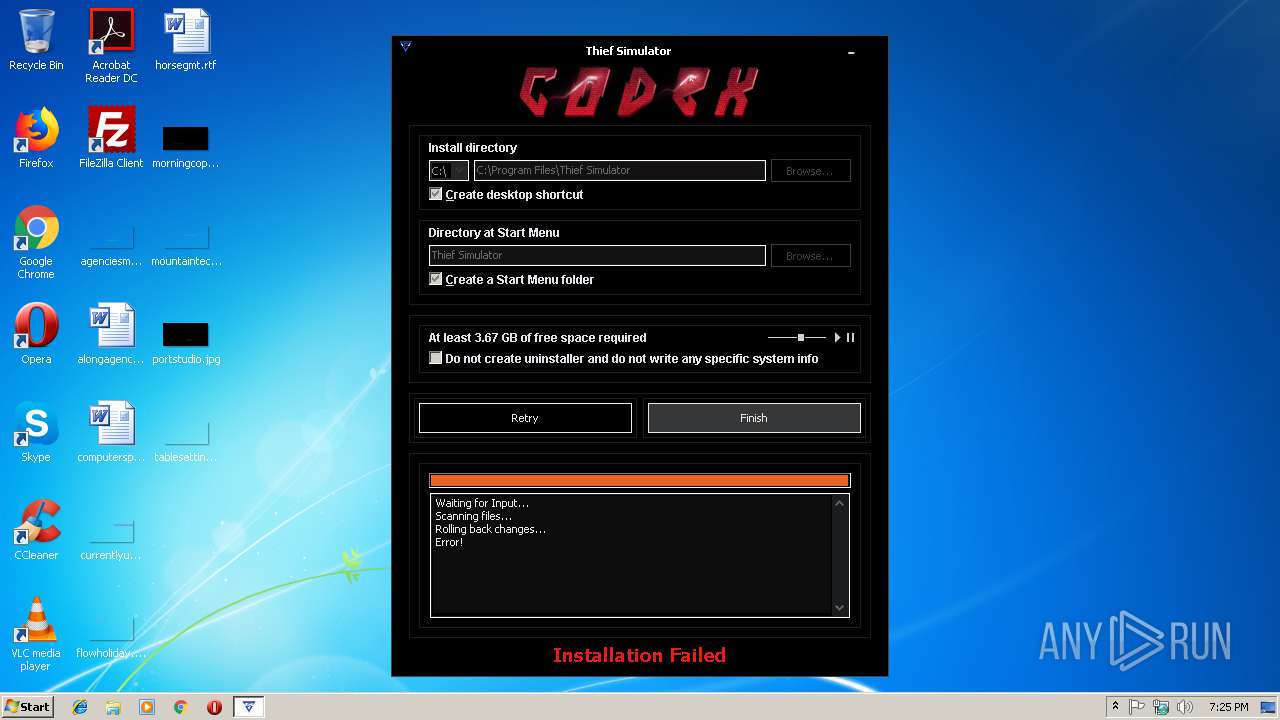
| FileDescription: | Thief Simulator Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Thief Simulator |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Thief Simulator Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Thief Simulator |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x00011CA8 | 0x00011E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.35376 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06505 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.28769 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.31584 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.78688 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 3.13038 | 196 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
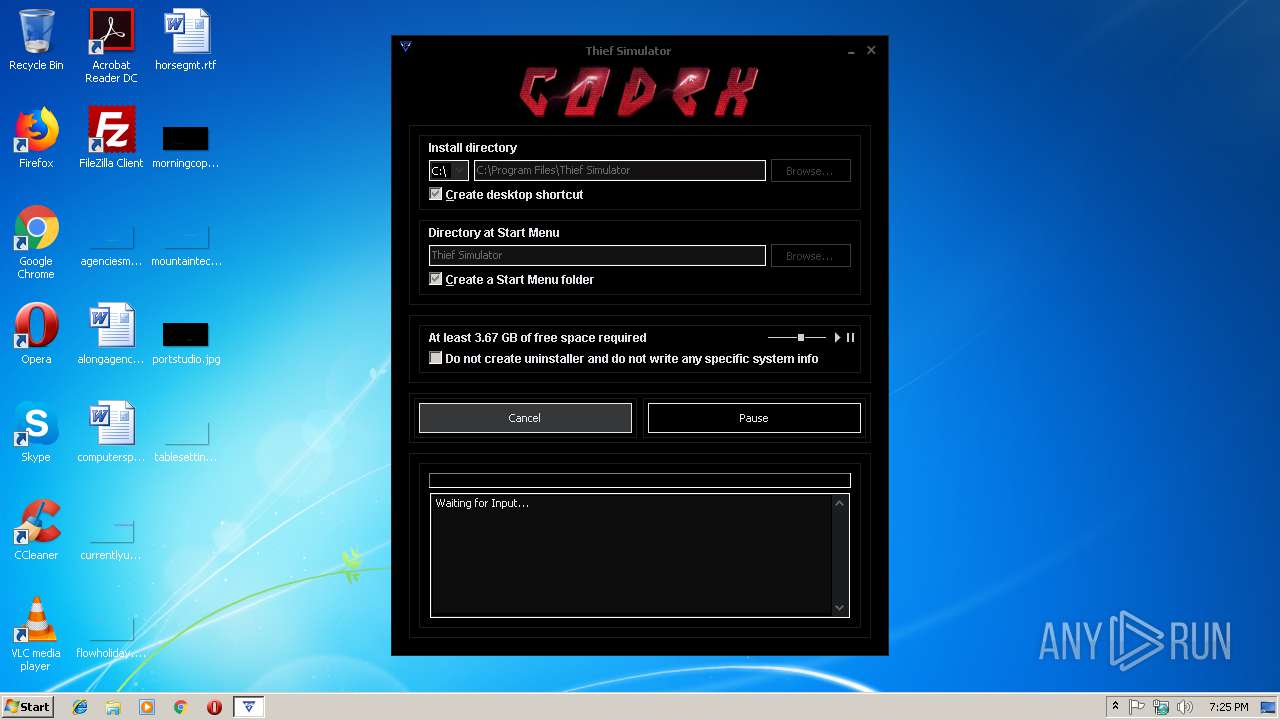
| 352 | "C:\Users\admin\AppData\Local\Temp\is-DPTSG.tmp\setup.tmp" /SL5="$50224,3687301,168448,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-DPTSG.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Thief Simulator Setup Exit code: 0 Version: Modules
| |||||||||||||||
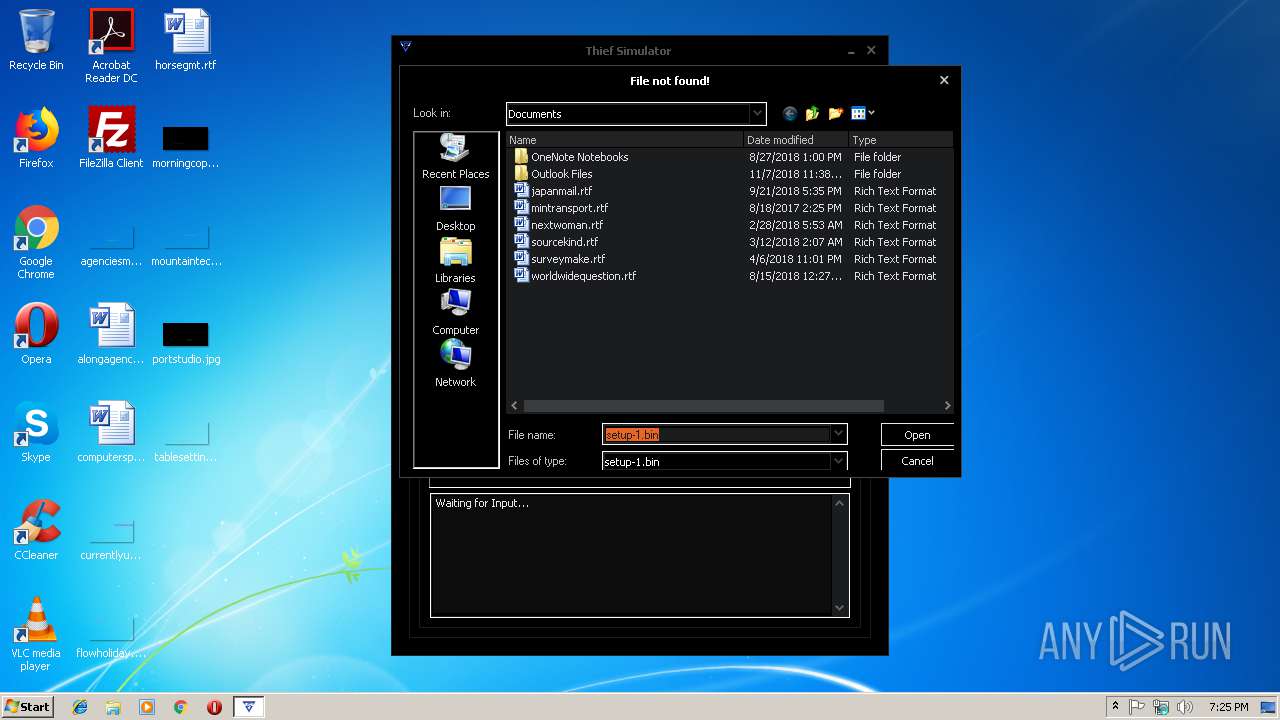
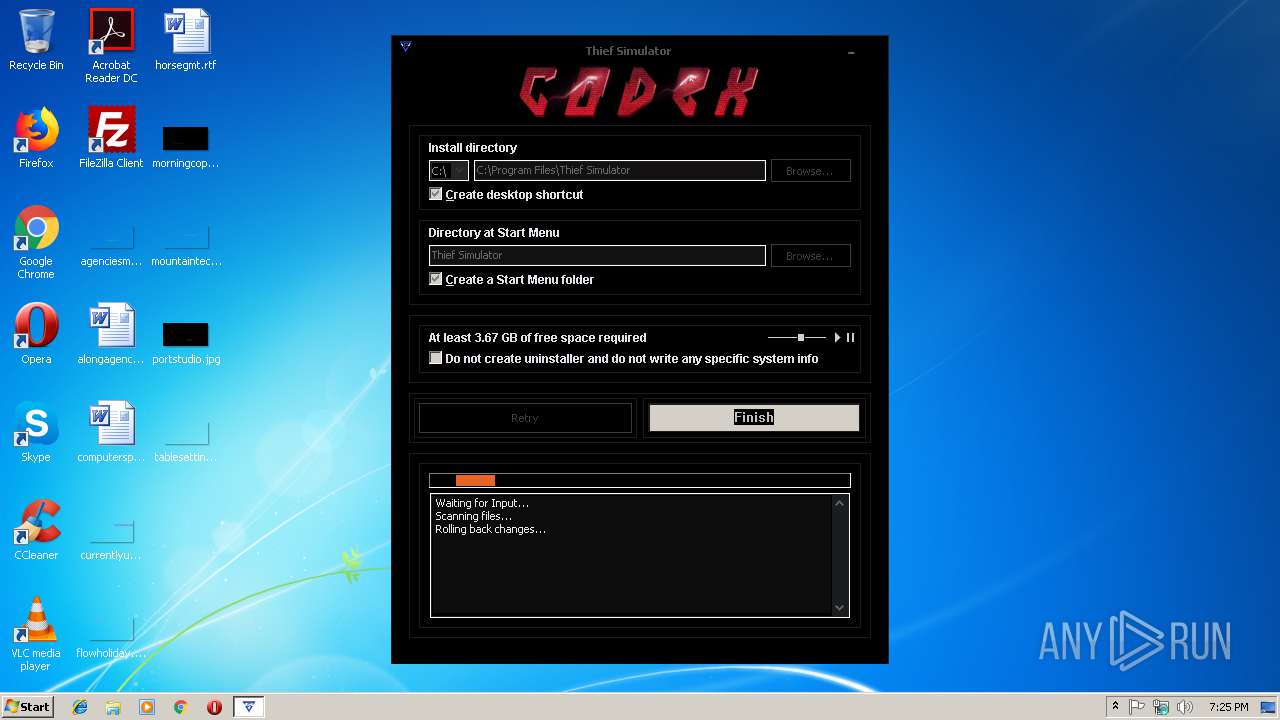
| 2664 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files\Thief Simulator\unins000.exe" /FIRSTPHASEWND=$B01D0 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3940 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Thief Simulator Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Thief Simulator\unins000.exe" /VERYSILENT | C:\Program Files\Thief Simulator\unins000.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
521
Read events
464
Write events
51
Delete events
6
Modification events
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 60010000BC1B85F26178D401 | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 15145EC39451C37122CA5E65FAC420860D3B25E027CF5205A4A1960AF8AA8783 | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
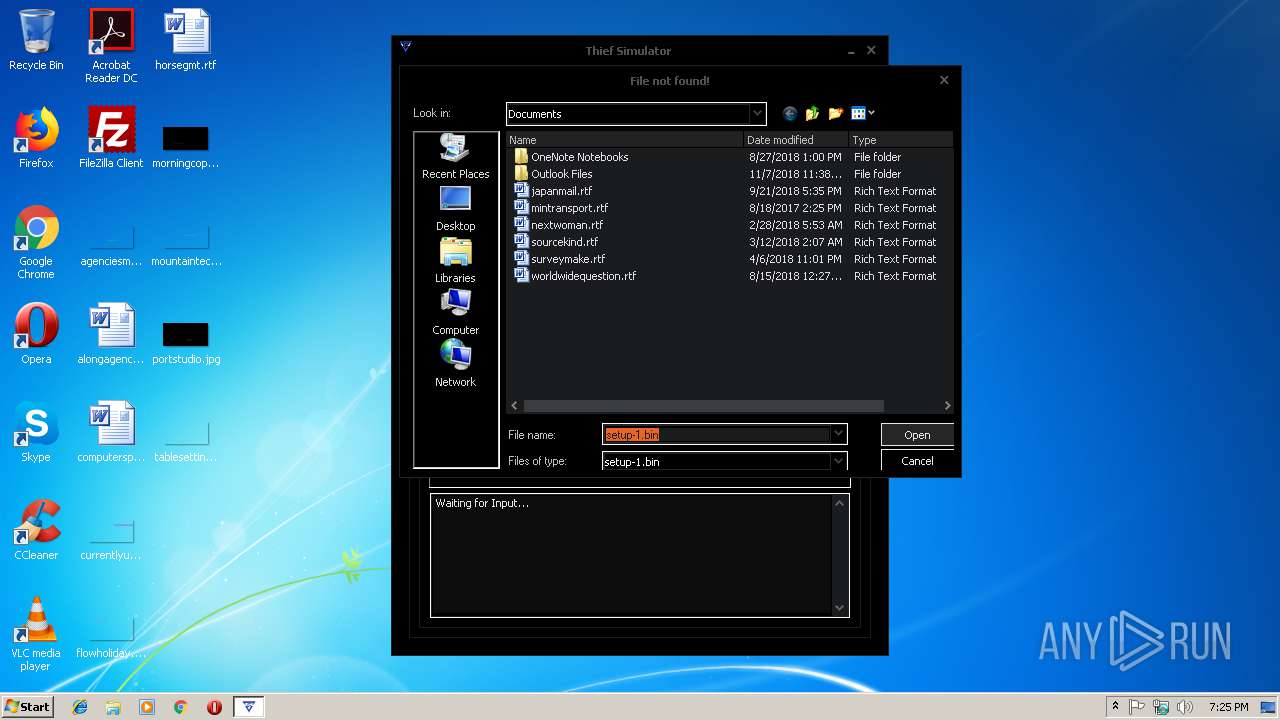
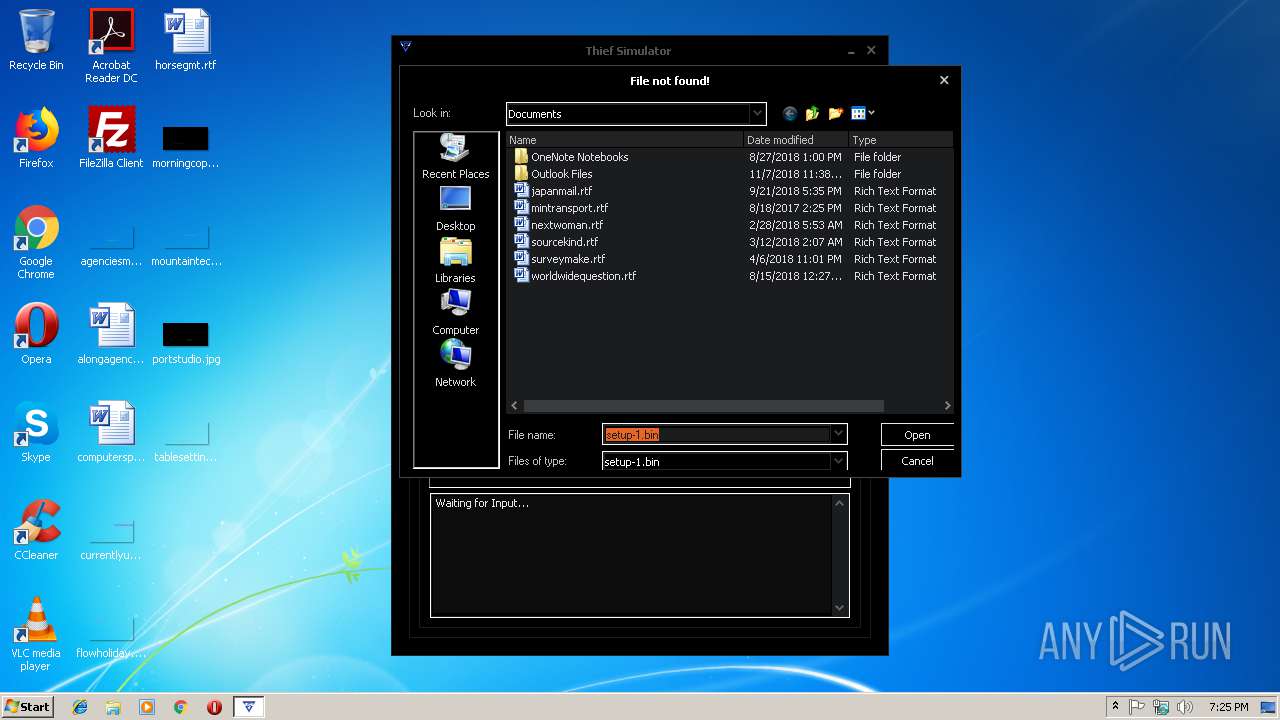
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000000000000010000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (352) setup.tmp | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlgLegacy |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
Executable files
11
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 352 | setup.tmp | C:\Program Files\Thief Simulator\is-LC4NQ.tmp | — | |
MD5:— | SHA256:— | |||
| 352 | setup.tmp | C:\Program Files\Thief Simulator\unins000.dat | — | |
MD5:— | SHA256:— | |||
| 2664 | _iu14D2N.tmp | C:\Program Files\Thief Simulator\unins000.dat | — | |
MD5:— | SHA256:— | |||
| 352 | setup.tmp | C:\Program Files\Thief Simulator\unins000.exe | executable | |
MD5:— | SHA256:— | |||
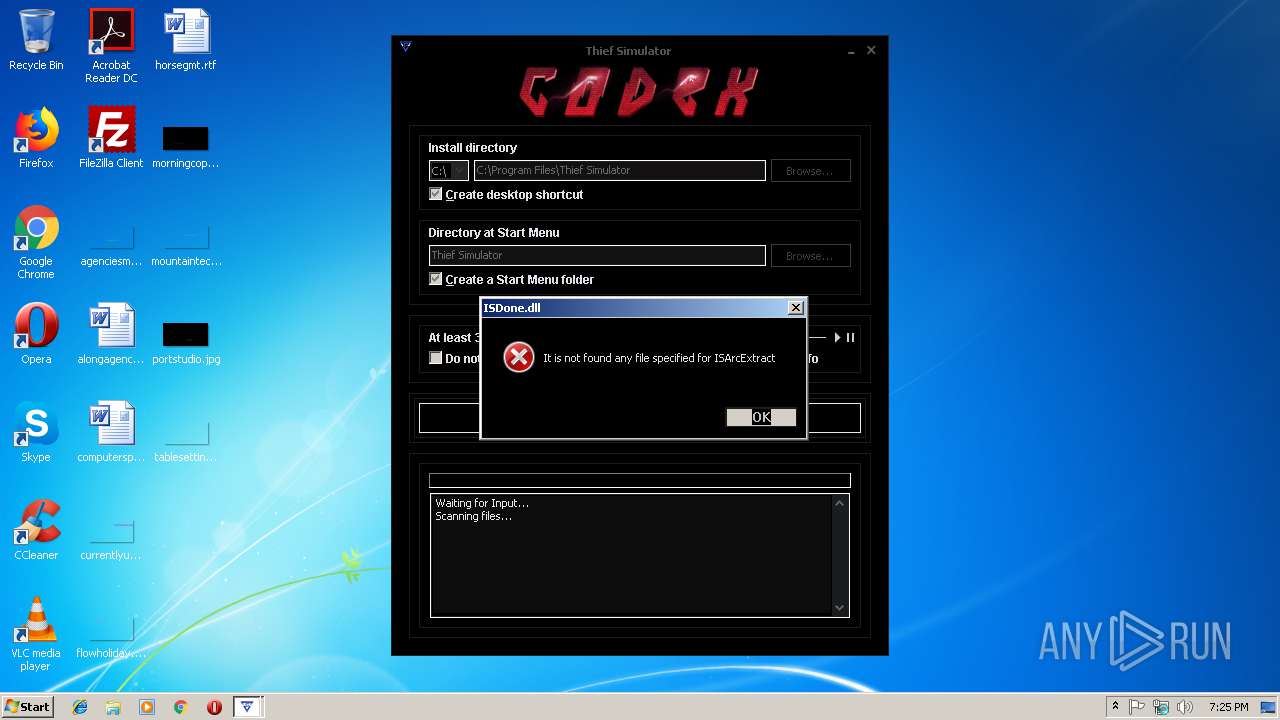
| 352 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-Q9PNN.tmp\ISDone.dll | executable | |
MD5:DCE6D68DA86F44BA0CB70FA7718E2E84 | SHA256:B9BDC4A0309AA47613A7B5A680C55839AA7BA28E28F96E6B9316D4D5FE1DBE9D | |||
| 352 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-Q9PNN.tmp\unarc.dll | executable | |
MD5:06A9571FF4789CF4AEC6FDA08992A9DC | SHA256:461E262189717C32EF0D7B559137B4F37D0EEA1F7010A564ADB11A06927938C4 | |||
| 352 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-Q9PNN.tmp\BASS.dll | executable | |
MD5:C0B11A7E60F69241DDCB278722AB962F | SHA256:A8D979460E970E84EACCE36B8A68AE5F6B9CC0FE16E05A6209B4EAD52B81B021 | |||
| 4052 | unins000.exe | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | executable | |
MD5:— | SHA256:— | |||
| 352 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-Q9PNN.tmp\wintb.dll | executable | |
MD5:39A339E9C9ECC529202508C9C89A9956 | SHA256:88160915CD065E25BC0B9B89099663CCBCCA606A5707A28A5DF12E9C118D4F16 | |||
| 2664 | _iu14D2N.tmp | C:\Users\admin\AppData\Local\Temp\is-AUOGM.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
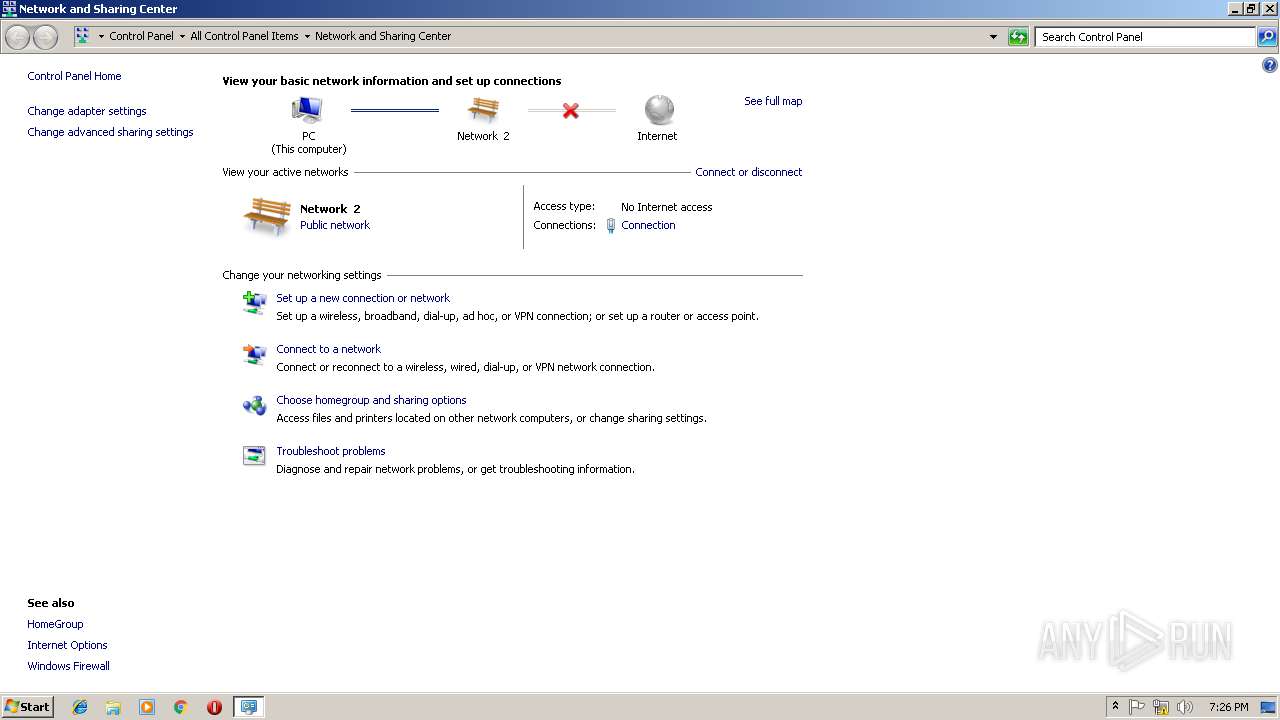
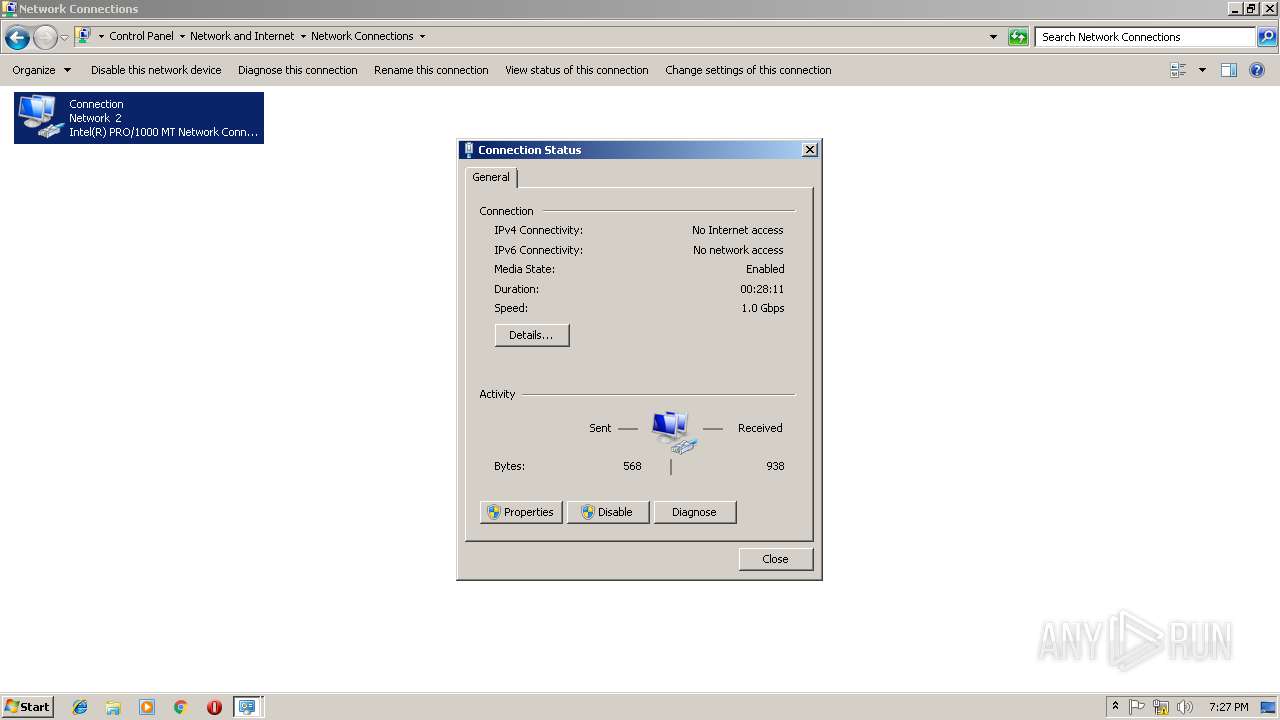
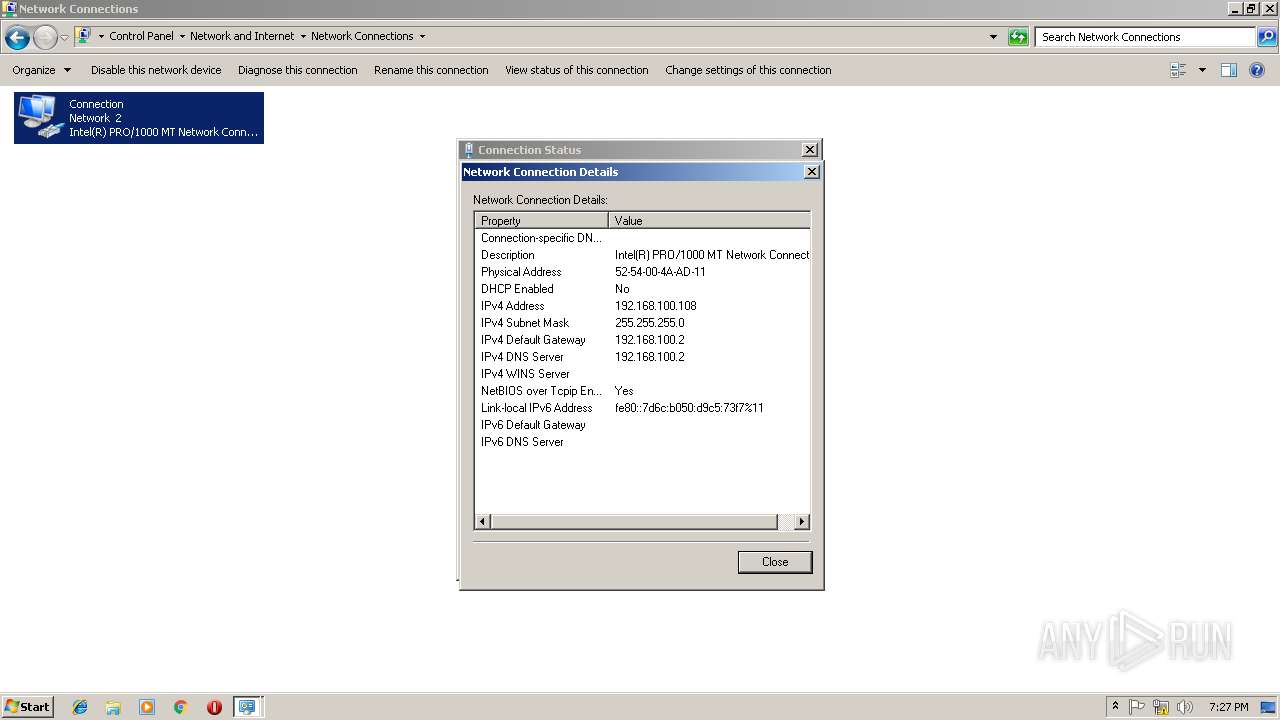
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report