| File name: | rufus-3.3.exe |
| Full analysis: | https://app.any.run/tasks/949beedd-a1d6-49a6-93d3-7e9e831278e7 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 08:42:11 |
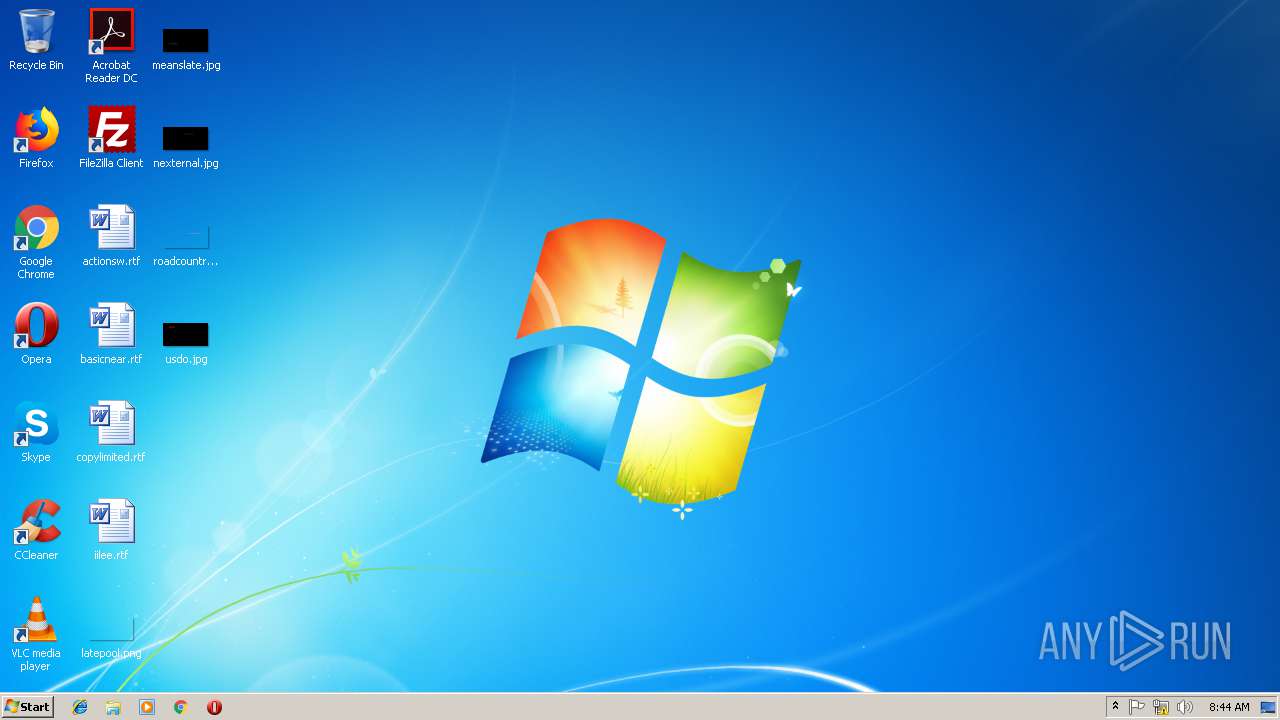
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | E32A70B9BC326099A42945389CE5A253 |
| SHA1: | 03A5E4E873BDEB2A8C17ABC41DED592654F89E35 |
| SHA256: | 45BD13CA54F037A5BA70A60BFC4A72E65E42A45445AB092B1A712C3169A2D93E |
| SSDEEP: | 24576:TYNYvhlkERiIk7bNc+KE5U2vew9kyb+rREmoKWNYZNKtXaoGifw:2YvhLQnbFjmw9k24to3eZ9/ |
MALICIOUS
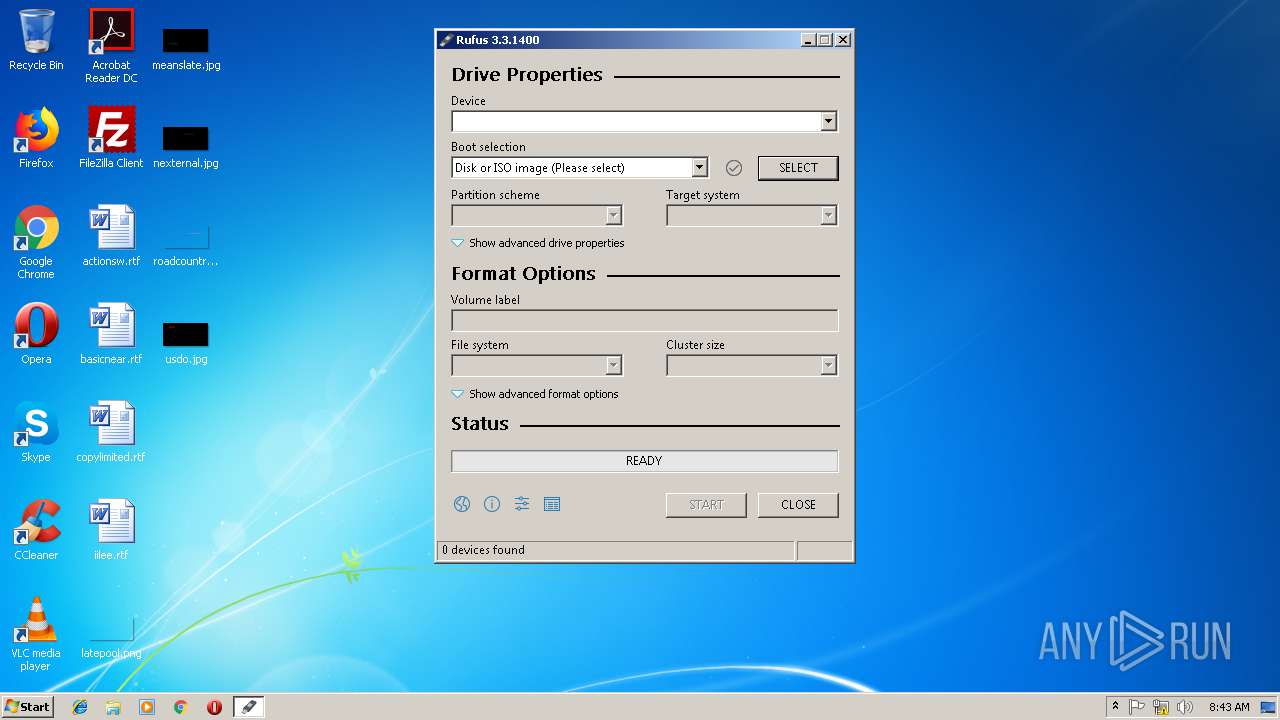
Changes Windows auto-update feature
- rufus-3.3.exe (PID: 764)
SUSPICIOUS
No suspicious indicators.INFO
Reads CPU info
- firefox.exe (PID: 3460)
- firefox.exe (PID: 1328)
- firefox.exe (PID: 3056)
- firefox.exe (PID: 2772)
Creates files in the user directory
- firefox.exe (PID: 3460)
Application launched itself
- firefox.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.31 |
| CodeSize: | 978944 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 1994752 |
| EntryPoint: | 0x2d5e00 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.1400.0 |
| ProductVersionNumber: | 3.3.1400.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://akeo.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 3.3.1400 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2018 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/copyleft/gpl.html |
| OriginalFileName: | rufus-3.3.exe |
| ProductName: | Rufus |
| ProductVersion: | 3.3.1400 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| TLS Callbacks: | 1 callback(s) detected. |
| Comments: | https://akeo.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 3.3.1400 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2018 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/copyleft/gpl.html |
| OriginalFilename: | rufus-3.3.exe |
| ProductName: | Rufus |
| ProductVersion: | 3.3.1400 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x001E7000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x001E8000 | 0x000EF000 | 0x000EEA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99975 |
.rsrc | 0x002D7000 | 0x0000B000 | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.93357 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17938 | 1895 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.68423 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.77127 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.98144 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.04318 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 7.9242 | 2386 | UNKNOWN | UNKNOWN | RT_DIALOG |
102 | 7.38422 | 316 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 7.4132 | 366 | UNKNOWN | UNKNOWN | RT_DIALOG |
104 | 7.82589 | 1268 | UNKNOWN | UNKNOWN | RT_DIALOG |
105 | 6.88676 | 172 | UNKNOWN | UNKNOWN | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
COMDLG32.DLL |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
41
Monitored processes
6
Malicious processes
0
Suspicious processes
1
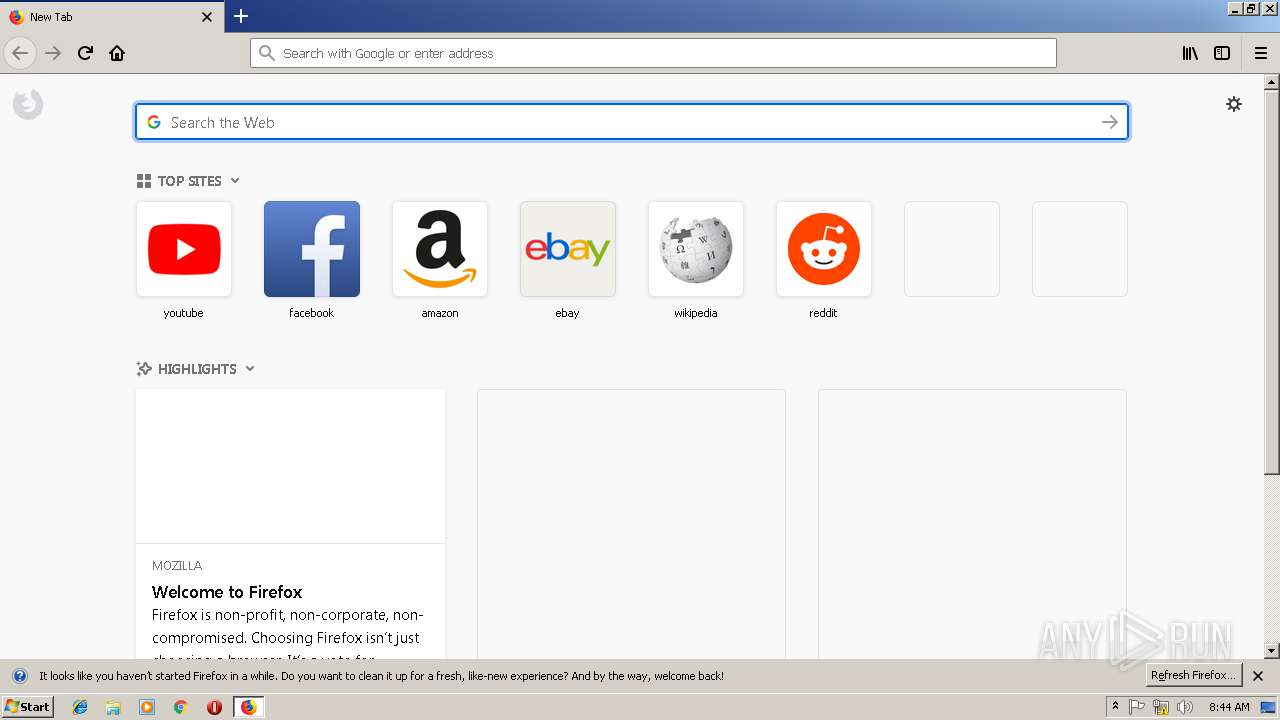
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Users\admin\AppData\Local\Temp\rufus-3.3.exe" | C:\Users\admin\AppData\Local\Temp\rufus-3.3.exe | explorer.exe | ||||||||||||
User: admin Company: Akeo Consulting Integrity Level: HIGH Description: Rufus Exit code: 0 Version: 3.3.1400 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3460.0.1913816572\267219909" -childID 1 -isForBrowser -prefsHandle 708 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3460 "\\.\pipe\gecko-crash-server-pipe.3460" 1424 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3460.12.1810083646\1790768481" -childID 3 -isForBrowser -prefsHandle 2964 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3460 "\\.\pipe\gecko-crash-server-pipe.3460" 2968 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3460.6.1002851602\150400053" -childID 2 -isForBrowser -prefsHandle 2248 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3460 "\\.\pipe\gecko-crash-server-pipe.3460" 2432 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\rufus-3.3.exe" | C:\Users\admin\AppData\Local\Temp\rufus-3.3.exe | — | explorer.exe | |||||||||||
User: admin Company: Akeo Consulting Integrity Level: MEDIUM Description: Rufus Exit code: 3221226540 Version: 3.3.1400 Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
Total events
660
Read events
564
Write events
39
Delete events
57
Modification events
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | IncludeRecommendedUpdates |
Value: 0 | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | AutoInstallMinorUpdates |
Value: 0 | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoDriveTypeAutorun |
Value: 158 | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}User |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (764) rufus-3.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Group Policy Objects\{F32403BC-E15F-4BE1-9AC4-F3FB0EEB9801}Machine\Software |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
79
Text files
25
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3460 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\doomed\3319 | binary | |
MD5:— | SHA256:— | |||
| 764 | rufus-3.3.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:— | SHA256:— | |||
| 764 | rufus-3.3.exe | C:\Windows\System32\GroupPolicy\GPT.INI | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
27
DNS requests
76
Threats
0
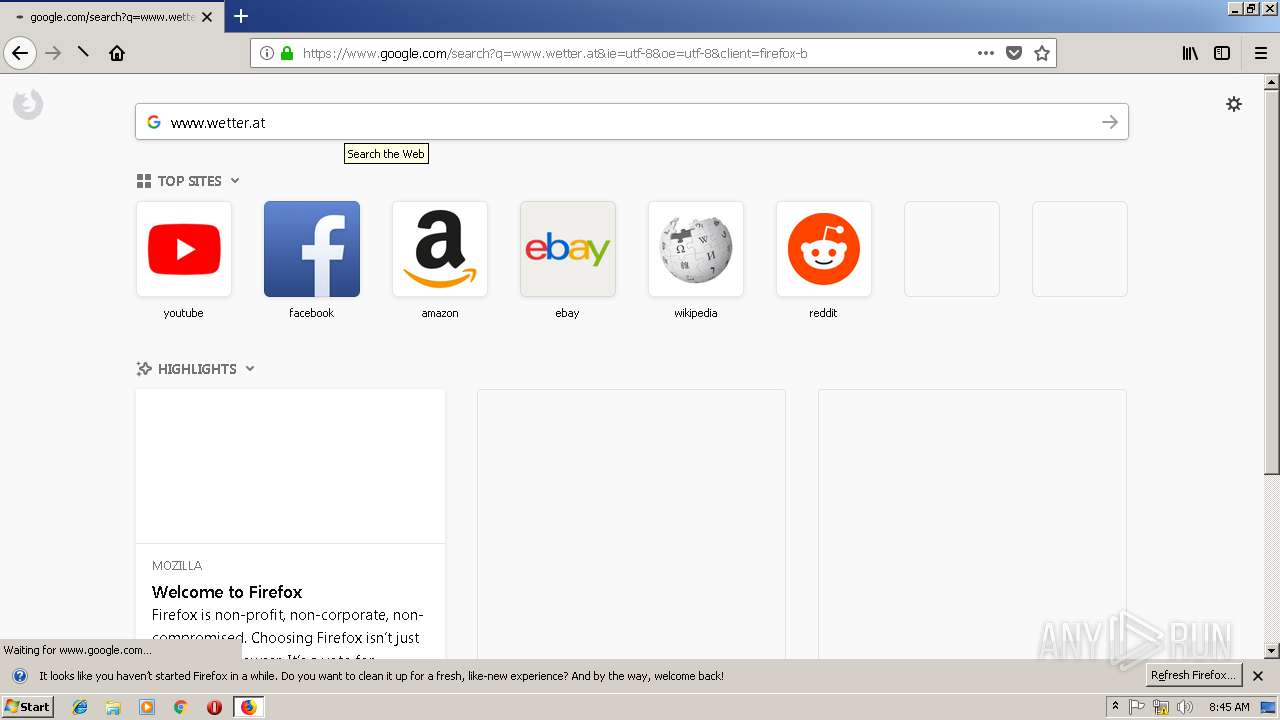
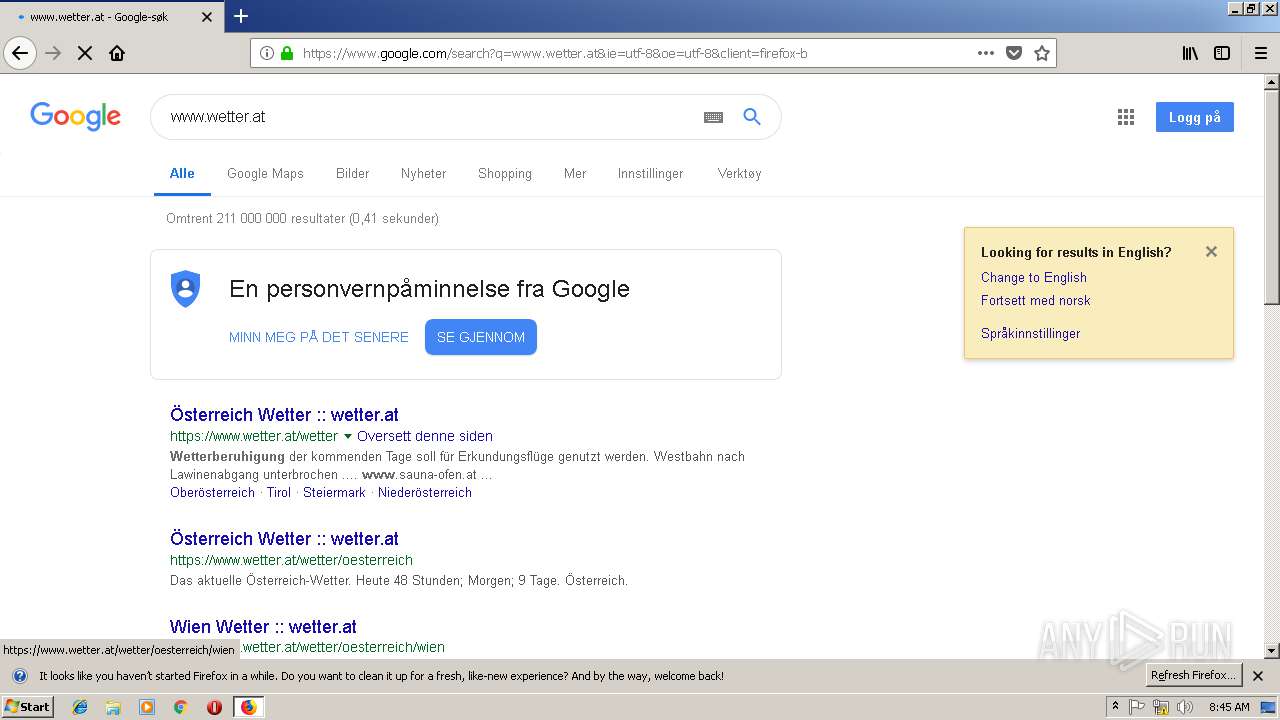
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3460 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | POST | 200 | 216.58.210.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3460 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3460 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3460 | firefox.exe | 52.222.173.79:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3460 | firefox.exe | 34.252.164.43:443 | location.services.mozilla.com | Amazon.com, Inc. | IE | unknown |
3460 | firefox.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3460 | firefox.exe | 52.222.161.21:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | whitelisted |
3460 | firefox.exe | 216.58.210.14:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3460 | firefox.exe | 54.187.144.104:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3460 | firefox.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3460 | firefox.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
3460 | firefox.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
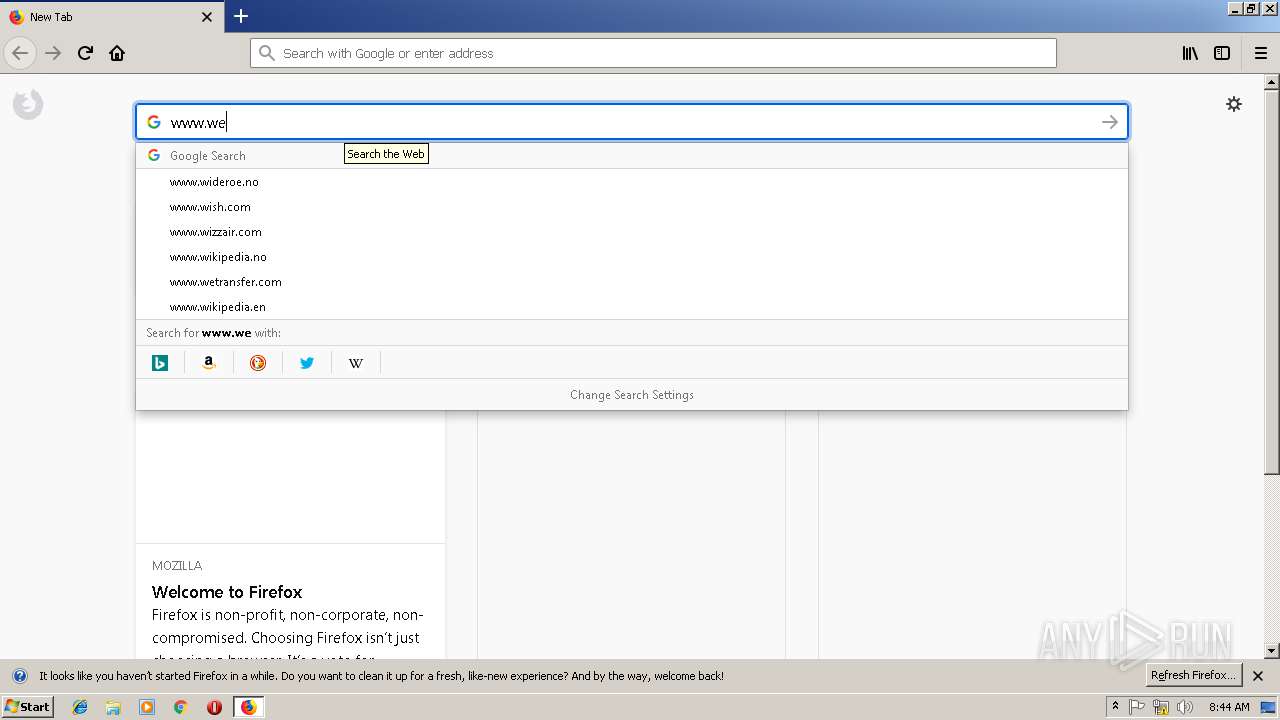
DNS requests
Domain | IP | Reputation |
|---|---|---|
rufus.ie |
| suspicious |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
tiles.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
Threats
Process | Message |
|---|---|
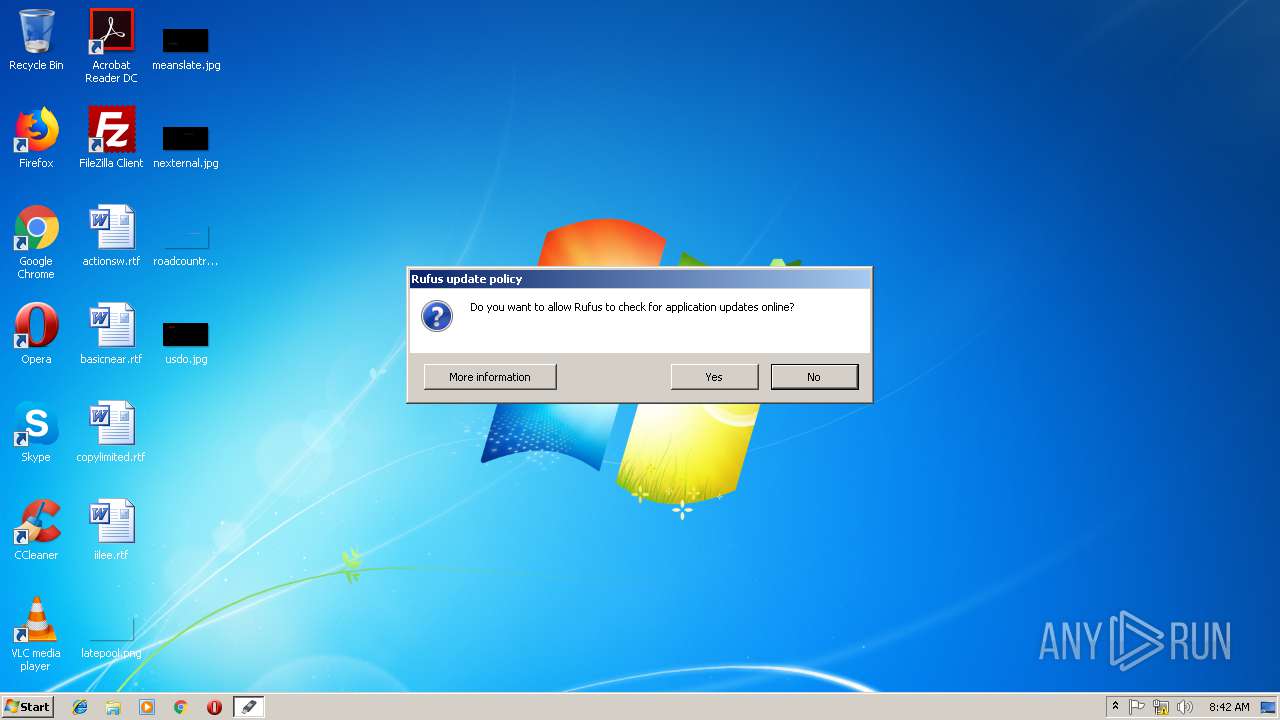
rufus-3.3.exe | *** Rufus init ***
|
rufus-3.3.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-3.3.exe | Will use settings from registry
|
rufus-3.3.exe | Will use settings from registry
|
rufus-3.3.exe | loc file not found in current directory - embedded one will be used
|
rufus-3.3.exe | localization: extracted data to 'C:\Users\admin\AppData\Local\Temp\RufEF55.tmp'
|
rufus-3.3.exe | localization: found locale 'en-US'
|
rufus-3.3.exe | localization: found locale 'ar-SA'
|
rufus-3.3.exe | embedded.loc(691): the version of this translation is older than the base one and may result in some messages not being properly translated.
If you are the translator, please update your translation with the changes that intervened between v3.0 and v3.2.
See https://github.com/pbatard/rufus/blob/master/res/loc/ChangeLog.txt
|
rufus-3.3.exe | embedded.loc(691): the version of this translation is older than the base one and may result in some messages not being properly translated.
If you are the translator, please update your translation with the changes that intervened between v3.0 and v3.2.
See https://github.com/pbatard/rufus/blob/master/res/loc/ChangeLog.txt
|