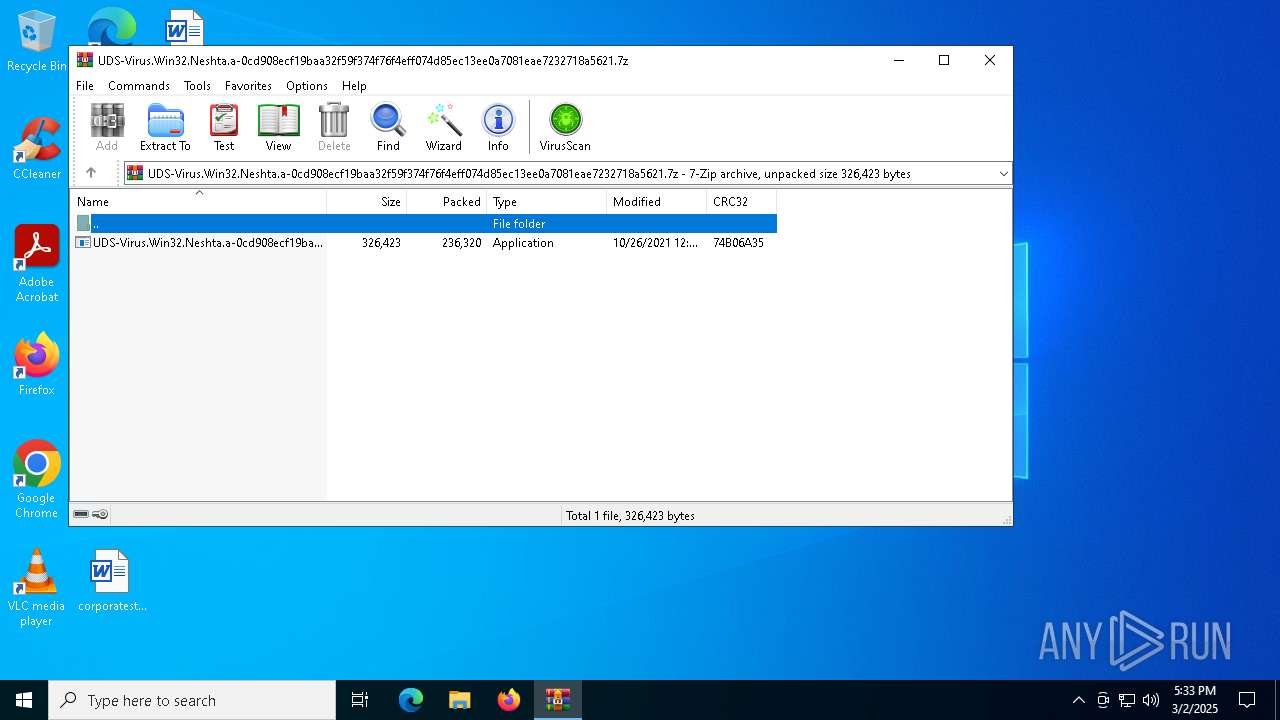
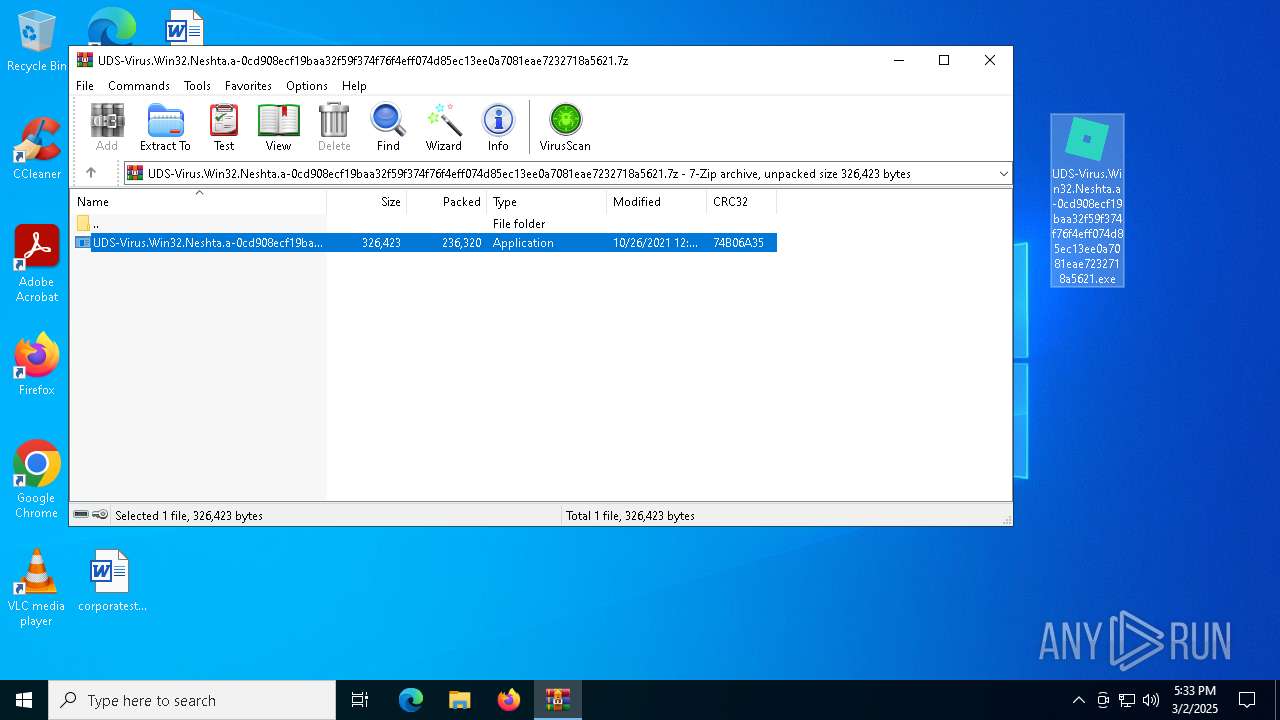
| File name: | UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.7z |
| Full analysis: | https://app.any.run/tasks/5adf68cf-b6b6-4c99-912d-fb4ee59a5bb1 |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2025, 17:33:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 2AC3F2D4C4C07517A605EC8E0CD57AC3 |
| SHA1: | E191FA8E25F210FCF1E06608E34A462D7C018BD9 |
| SHA256: | 45BA3FD5990DBCF4D1FAA3C06D521EAFC618EF5B21CFB31BDC5105EF9AE54B89 |
| SSDEEP: | 12288:UnPvfDlbFZW0dd0yMxzxdW8iJiShM+KoLMkYgIgqP:YPvLlbFZWWdezxd3iJiShM+KoLMngIgK |
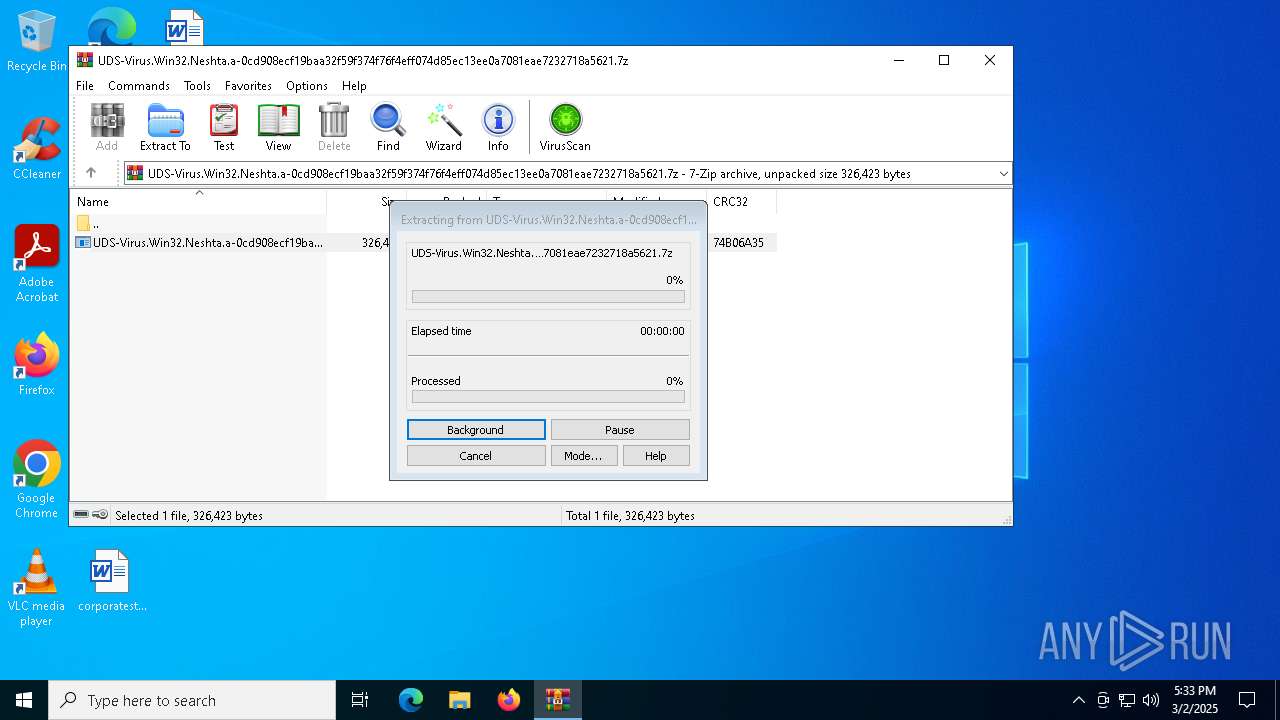
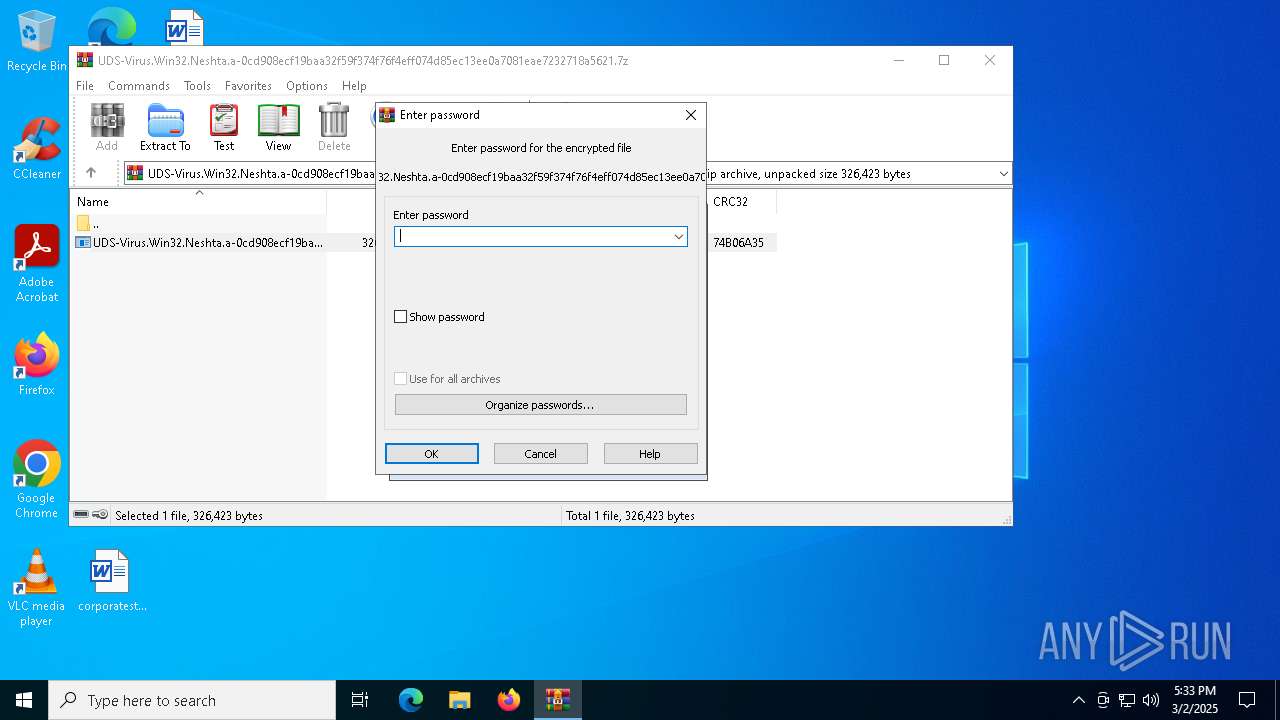
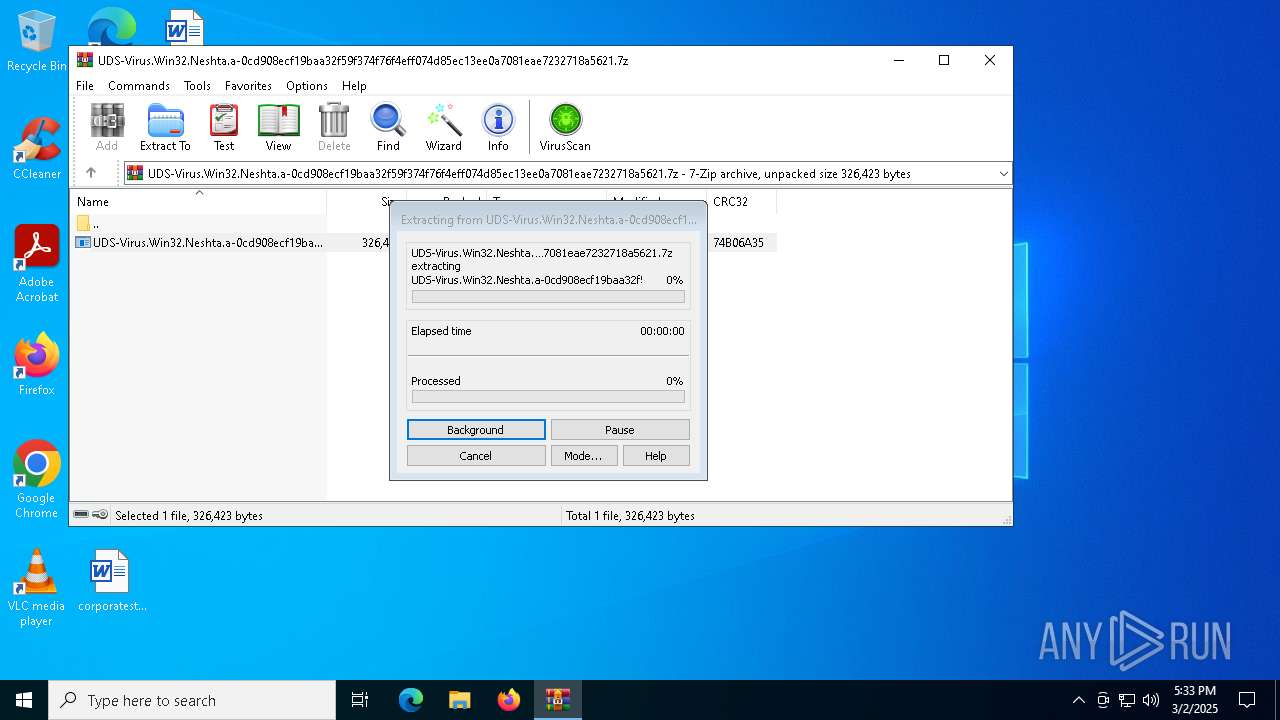
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2320)
SUSPICIOUS
Executable content was dropped or overwritten
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- Un_A.exe (PID: 6576)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
- Un_A.exe (PID: 4944)
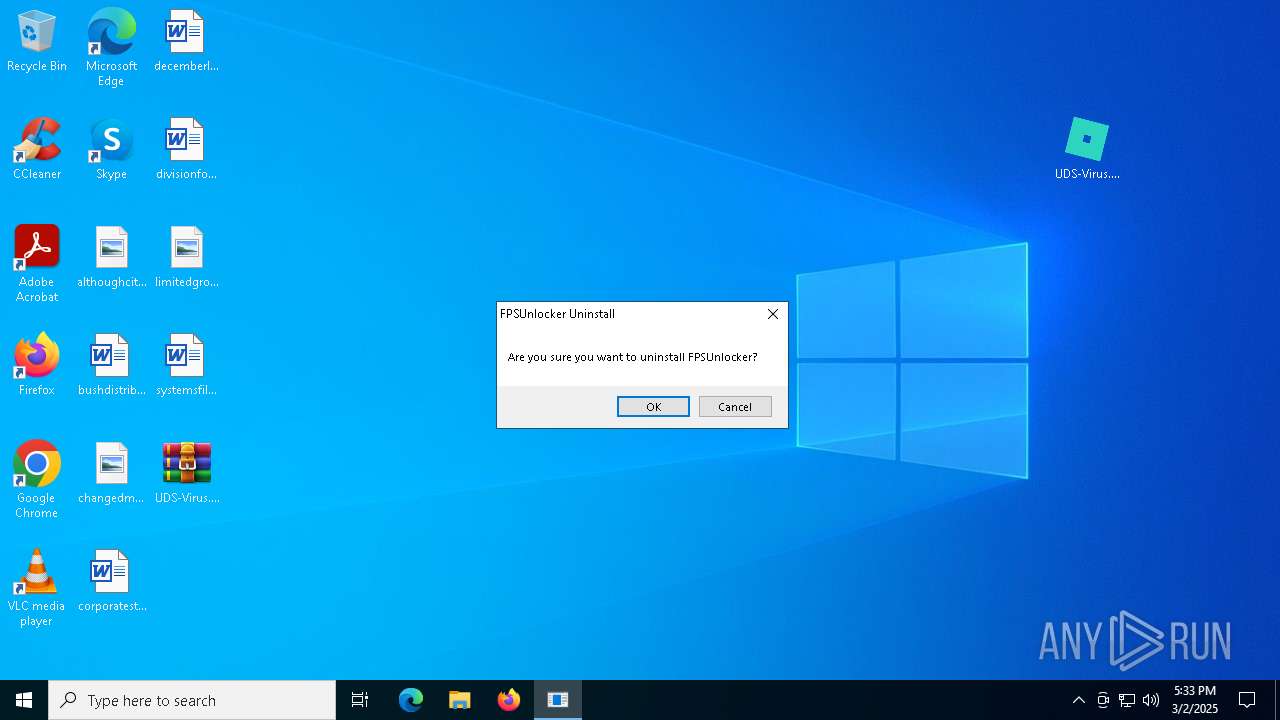
Starts itself from another location
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
The process creates files with name similar to system file names
- Un_A.exe (PID: 6576)
- Un_A.exe (PID: 4944)
Malware-specific behavior (creating "System.dll" in Temp)
- Un_A.exe (PID: 6576)
- Un_A.exe (PID: 4944)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4608)
INFO
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1072)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1072)
The sample compiled with english language support
- WinRAR.exe (PID: 2320)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
- Un_A.exe (PID: 6576)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1072)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2320)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5548)
- BackgroundTransferHost.exe (PID: 4428)
- BackgroundTransferHost.exe (PID: 5332)
- BackgroundTransferHost.exe (PID: 1072)
- BackgroundTransferHost.exe (PID: 6132)
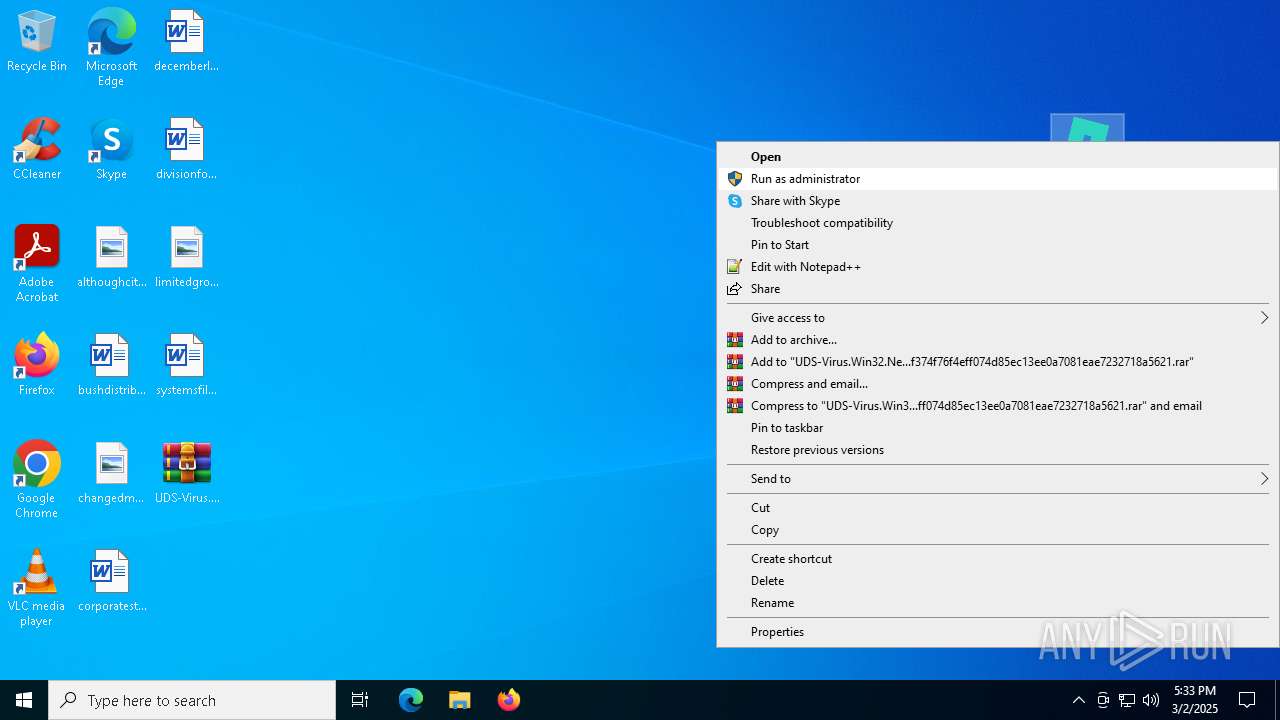
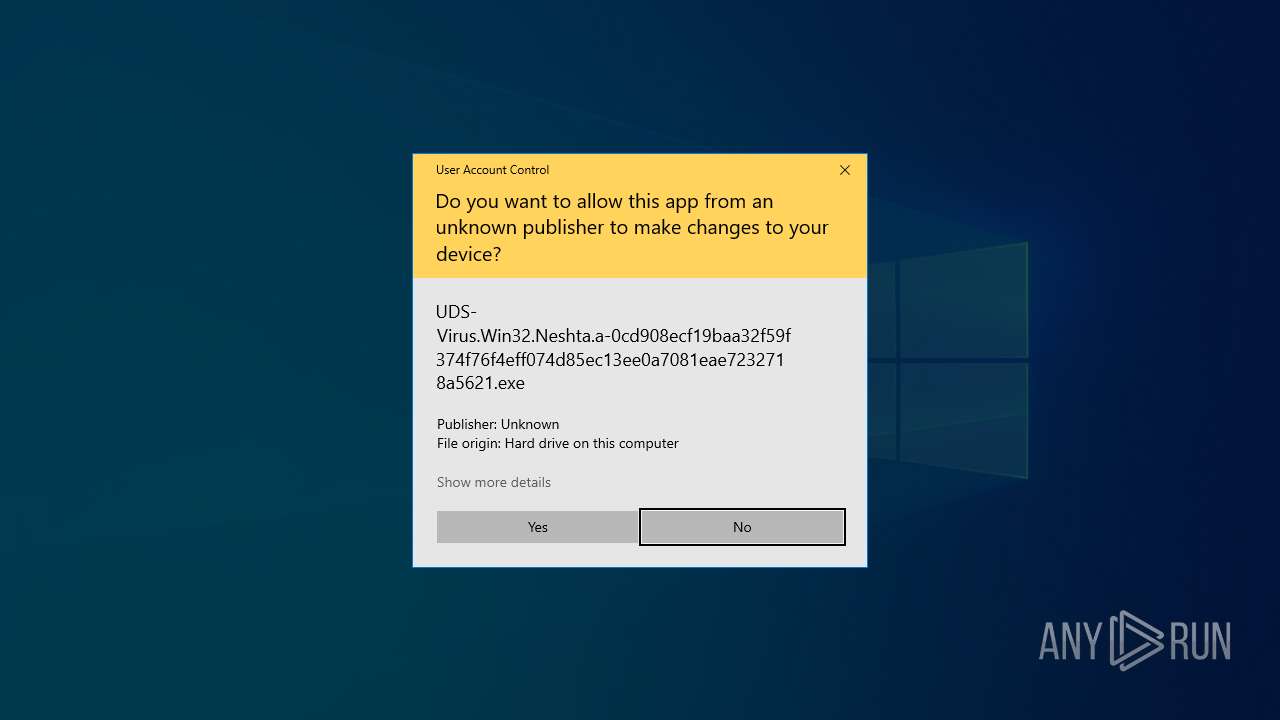
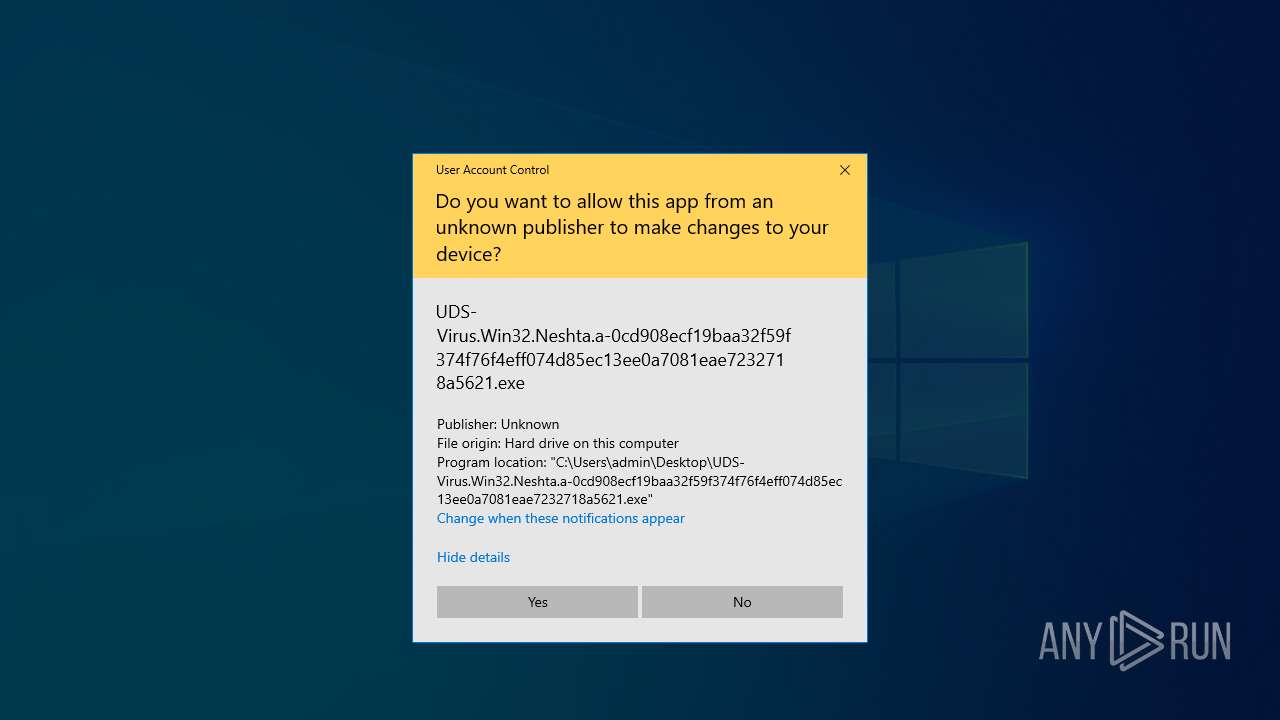
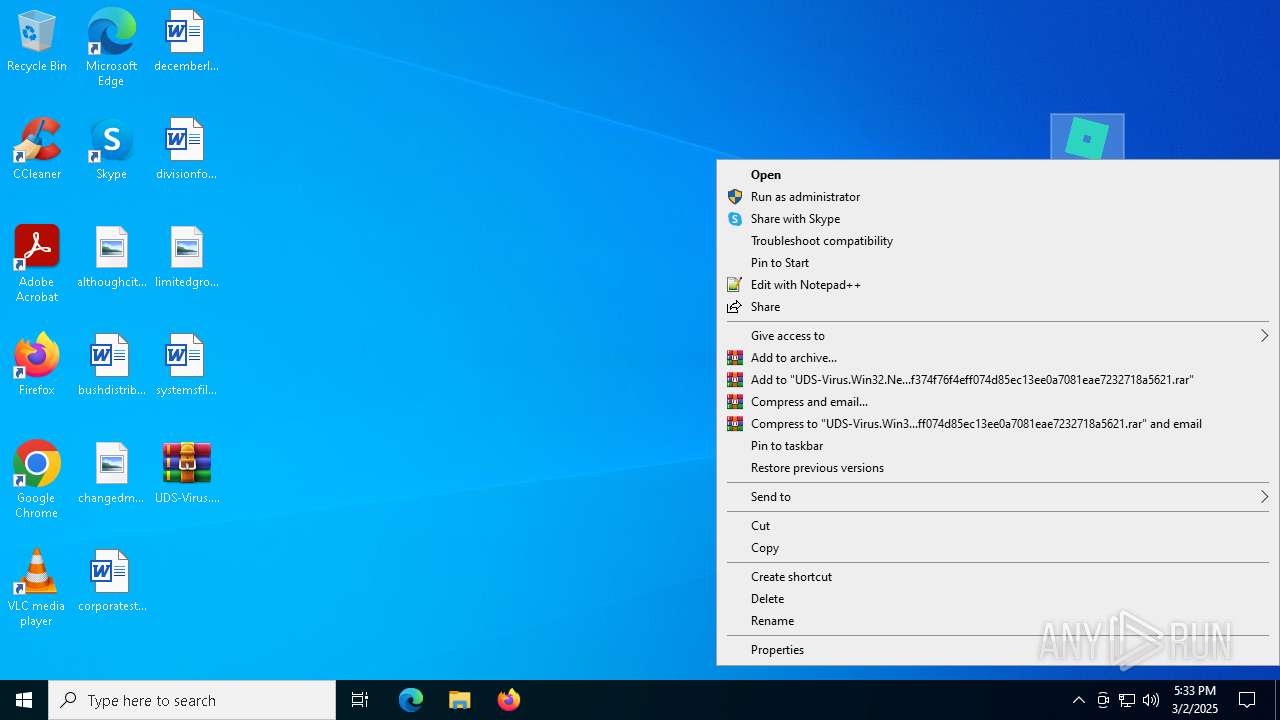
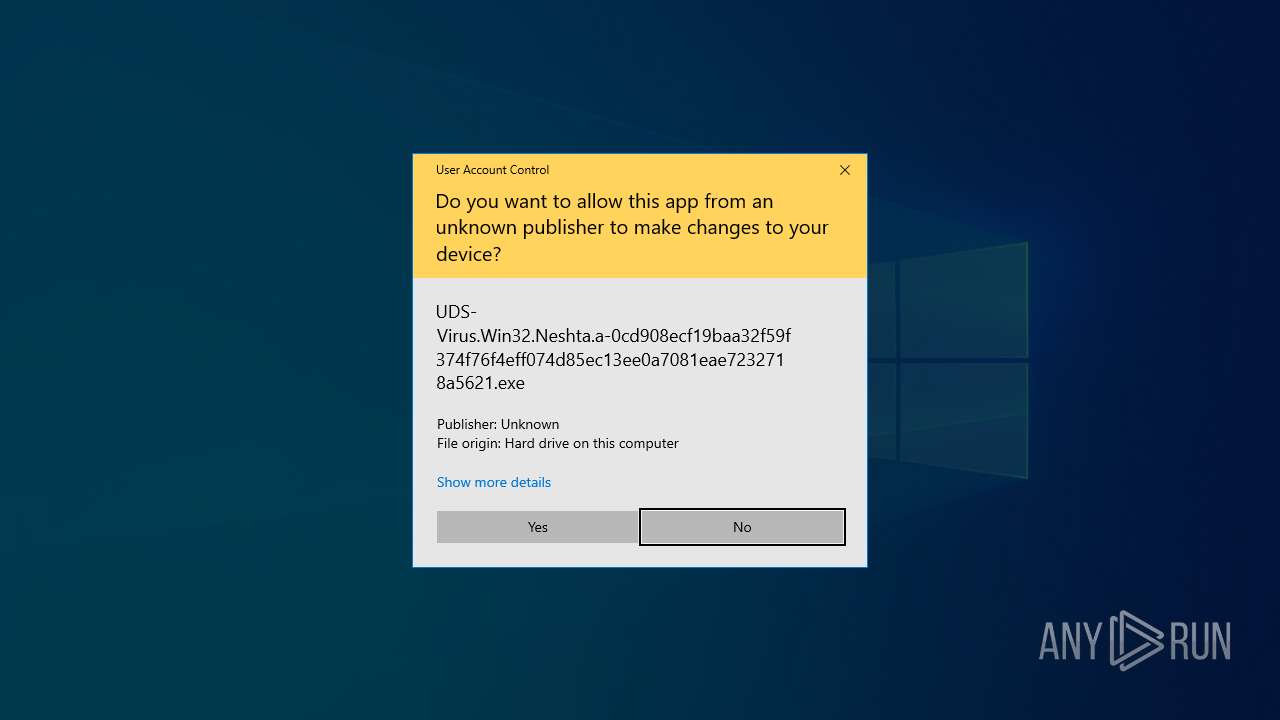
Manual execution by a user
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
Checks supported languages
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- Un_A.exe (PID: 6576)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
- Un_A.exe (PID: 4944)
- ShellExperienceHost.exe (PID: 4608)
Create files in a temporary directory
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 4188)
- Un_A.exe (PID: 6576)
- UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe (PID: 6972)
- Un_A.exe (PID: 4944)
Reads the computer name
- Un_A.exe (PID: 4944)
- Un_A.exe (PID: 6576)
- ShellExperienceHost.exe (PID: 4608)
Process checks computer location settings
- Un_A.exe (PID: 6576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:10:26 12:22:30+00:00 |
| ArchivedFileName: | UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe |
Total processes
150
Monitored processes
13
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4180 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | "C:\Users\admin\Desktop\UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe" | C:\Users\admin\Desktop\UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe | explorer.exe | ||||||||||||
User: admin Company: fpsunlocker.net Integrity Level: HIGH Description: Free Roblox FPS Unlocker software helps the user to increase the FPS. Roblox has limited the frame rate to 60 FPS, and if you got frustrated because of the restricted frame rate, then here is a solut Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
| 4428 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4608 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4944 | "C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe" _?=C:\Users\admin\Desktop\ | C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe | UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe | ||||||||||||
User: admin Company: fpsunlocker.net Integrity Level: HIGH Description: Free Roblox FPS Unlocker software helps the user to increase the FPS. Roblox has limited the frame rate to 60 FPS, and if you got frustrated because of the restricted frame rate, then here is a solut Exit code: 2 Version: 1.1.1 Modules
| |||||||||||||||
| 5332 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5968 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 696
Read events
4 660
Write events
36
Delete events
0
Modification events
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.7z | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6132) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
8
Suspicious files
7
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\87a9420a-959a-48f8-8c9b-8fbafba4f1db.down_data | — | |
MD5:— | SHA256:— | |||
| 4944 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsz2672.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 1072 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\a78ff2e2-e23e-4b9f-b495-1514d1246898.0c1cdafe-c887-44f5-9e98-0e751e509040.down_meta | binary | |
MD5:387AAF92292BD82E308A9F8D9BF05E38 | SHA256:848F51B72F61A9EA18DDEDE0BB834A3AA636F08613FC6D6426491E45231A6BC4 | |||
| 1072 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\87a9420a-959a-48f8-8c9b-8fbafba4f1db.0c1cdafe-c887-44f5-9e98-0e751e509040.down_meta | binary | |
MD5:387AAF92292BD82E308A9F8D9BF05E38 | SHA256:848F51B72F61A9EA18DDEDE0BB834A3AA636F08613FC6D6426491E45231A6BC4 | |||
| 6576 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsrEE0C.tmp\StdUtils.dll | executable | |
MD5:C6A6E03F77C313B267498515488C5740 | SHA256:B72E9013A6204E9F01076DC38DABBF30870D44DFC66962ADBF73619D4331601E | |||
| 6576 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsrEE0C.tmp\nsProcess.dll | executable | |
MD5:F0438A894F3A7E01A4AAE8D1B5DD0289 | SHA256:30C6C3DD3CC7FCEA6E6081CE821ADC7B2888542DAE30BF00E881C0A105EB4D11 | |||
| 1072 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\a78ff2e2-e23e-4b9f-b495-1514d1246898.up_meta_secure | binary | |
MD5:96B795E18931F74B28FB126E3E9A376F | SHA256:E78139A502212EA46908FA2CB470AD2DB98351B18D025BB442775485E7F0AD4A | |||
| 1072 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:CA6173FC5E87CAB1BEF55DAC3B19CB8F | SHA256:2784FA484E6E373A9A1451396BA9BF7E52CB1D3208E446A62EE6FC9E9D3D73D1 | |||
| 4188 | UDS-Virus.Win32.Neshta.a-0cd908ecf19baa32f59f374f76f4eff074d85ec13ee0a7081eae7232718a5621.exe | C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe | executable | |
MD5:D1DE04534FF3457BFB7EFD36A9F6FB1A | SHA256:0CD908ECF19BAA32F59F374F76F4EFF074D85EC13EE0A7081EAE7232718A5621 | |||
| 6576 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsrEE0C.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
20
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1072 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5400 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5960 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1072 | BackgroundTransferHost.exe | 92.123.104.62:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |