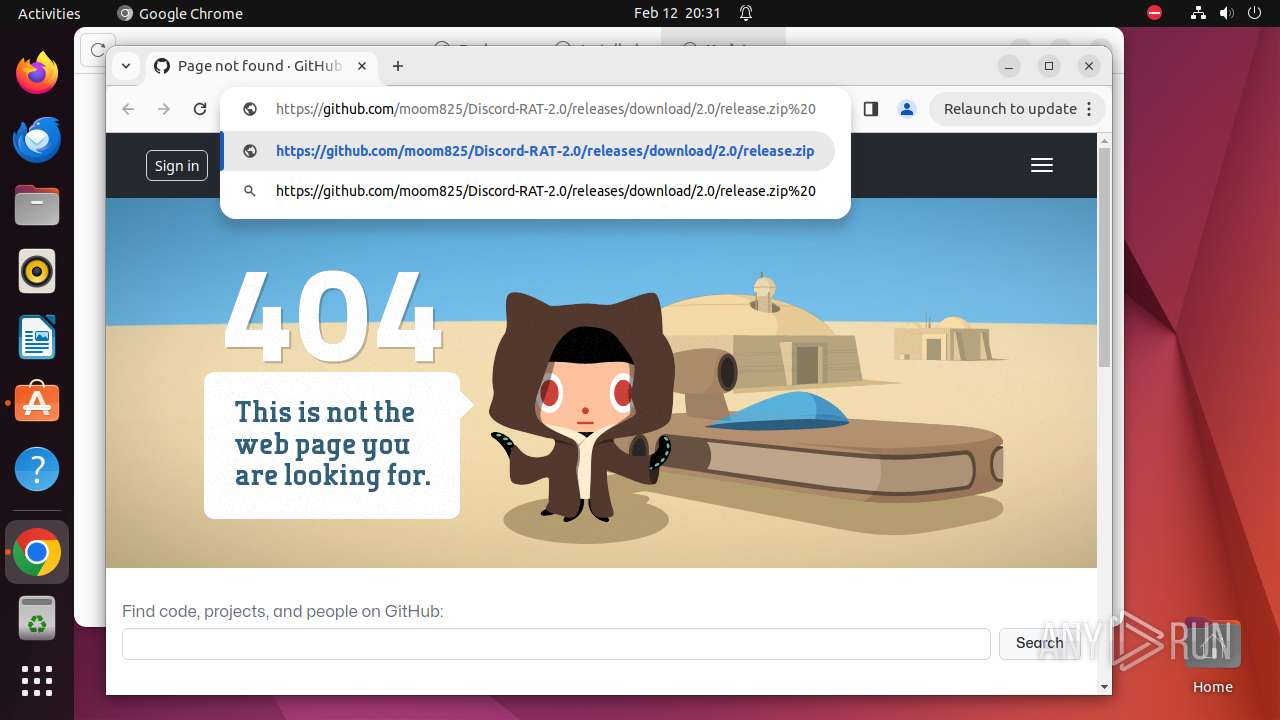
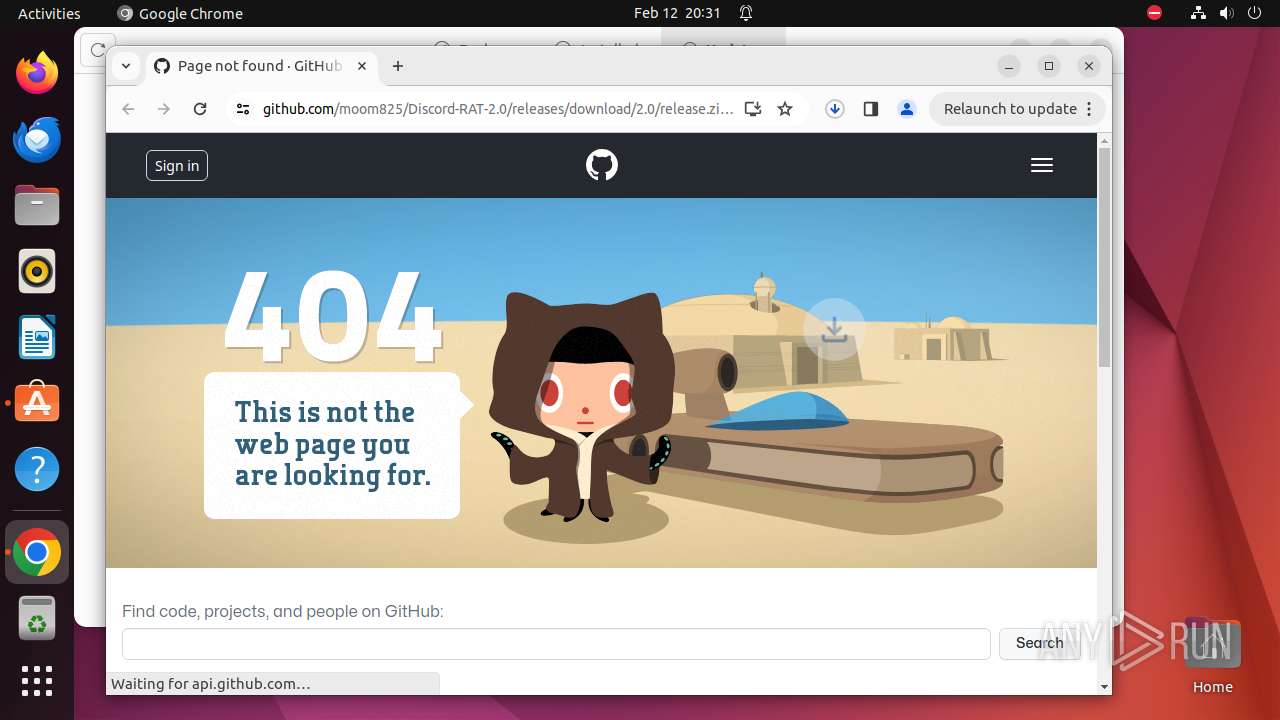
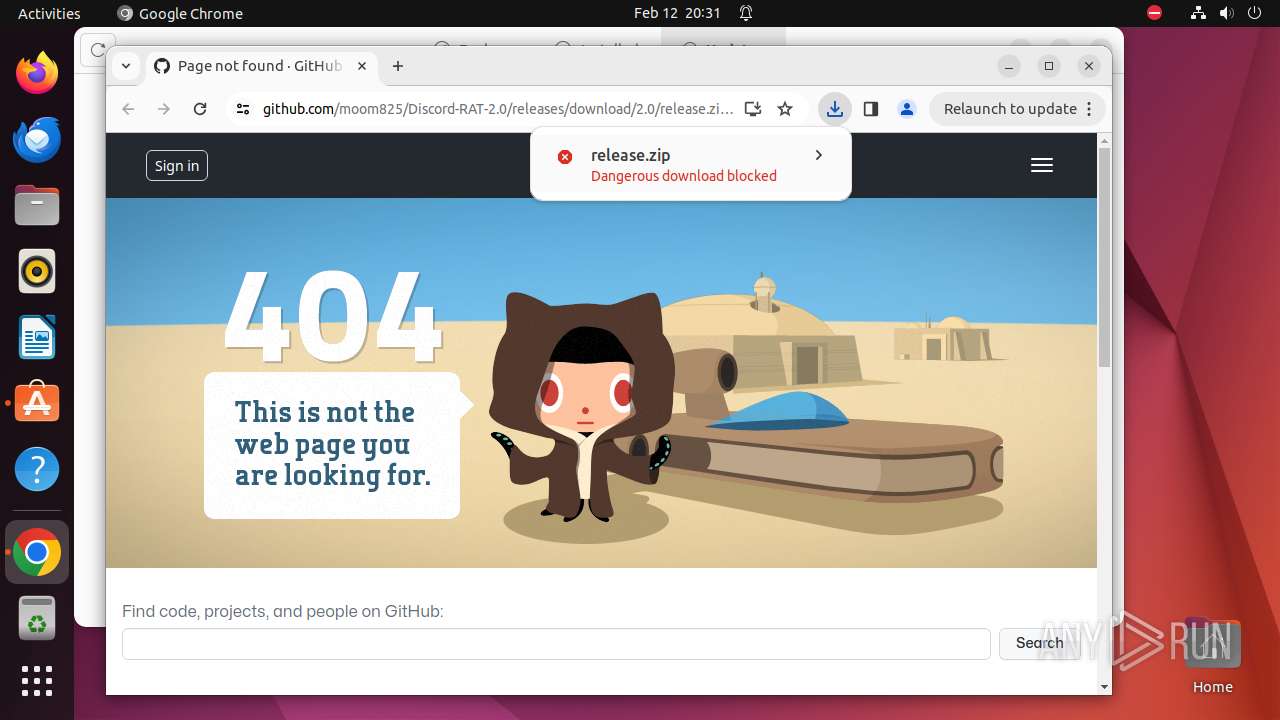
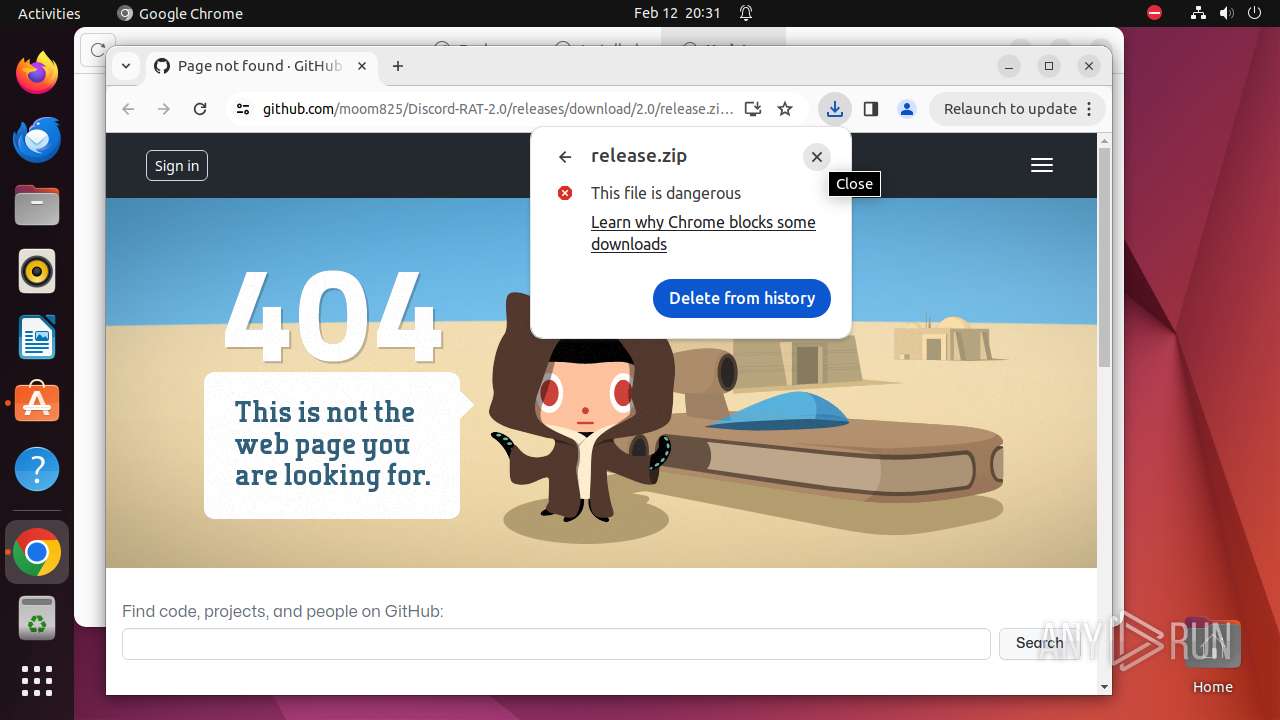
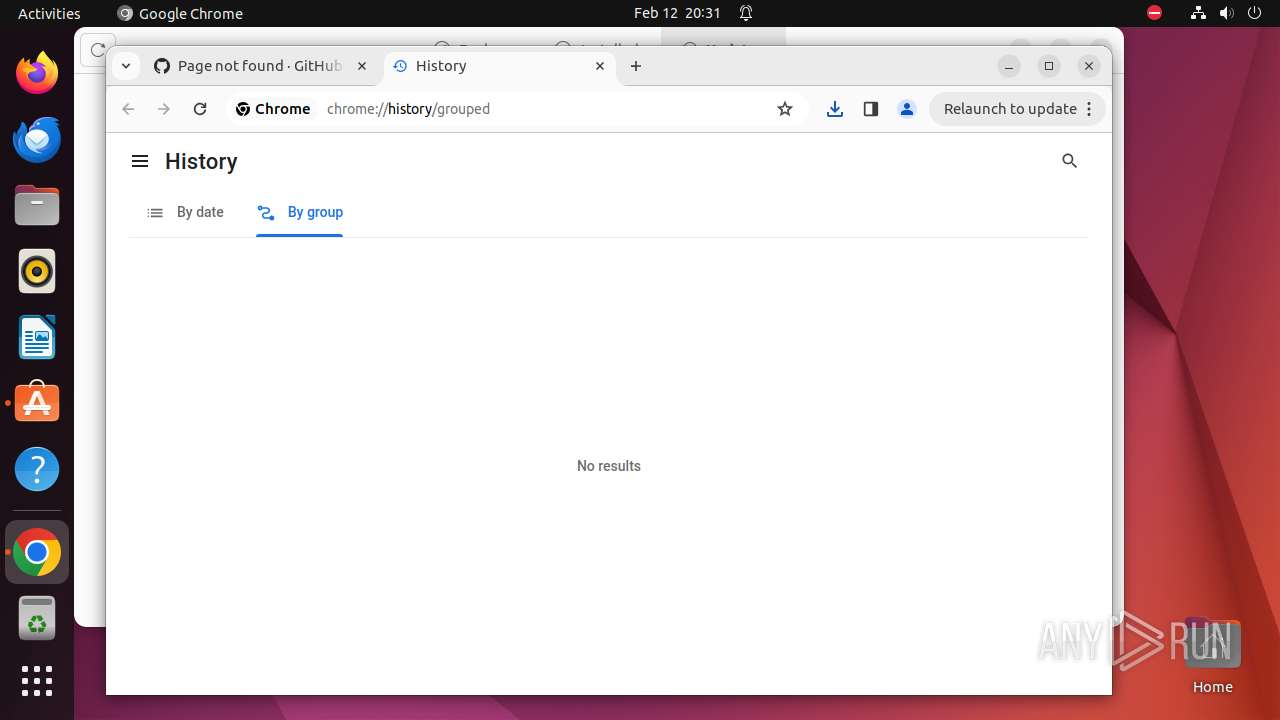
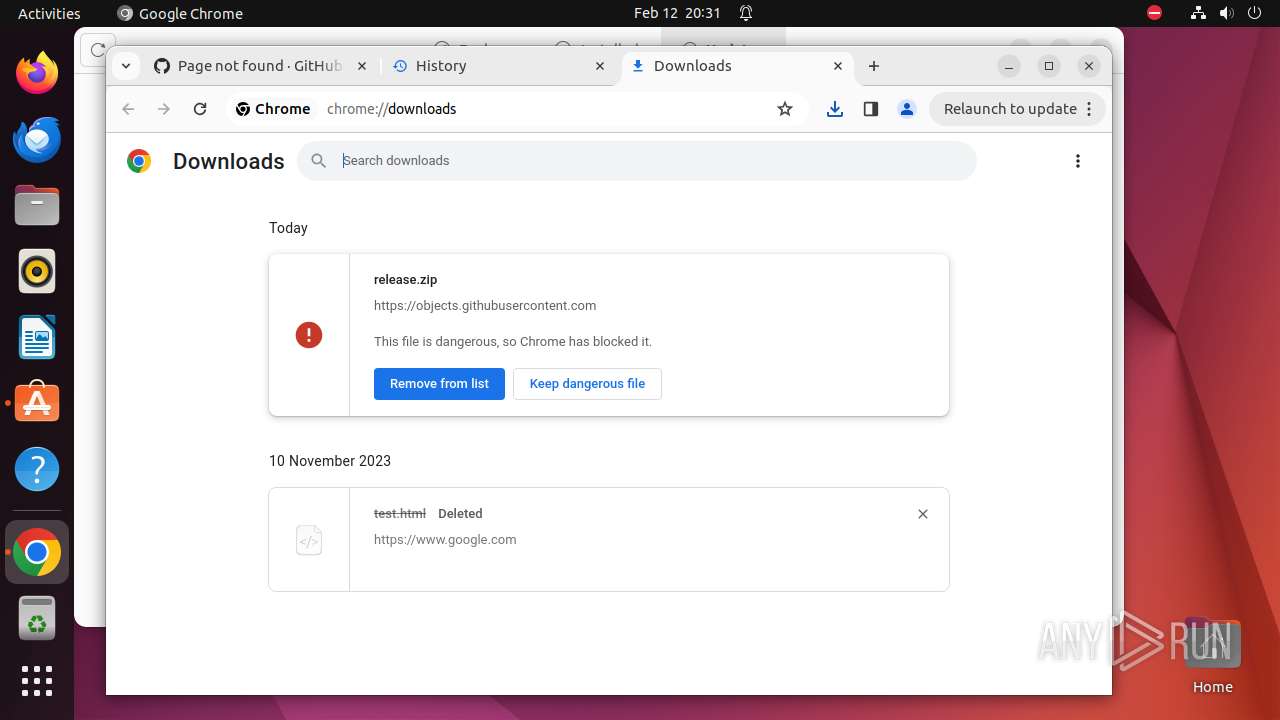
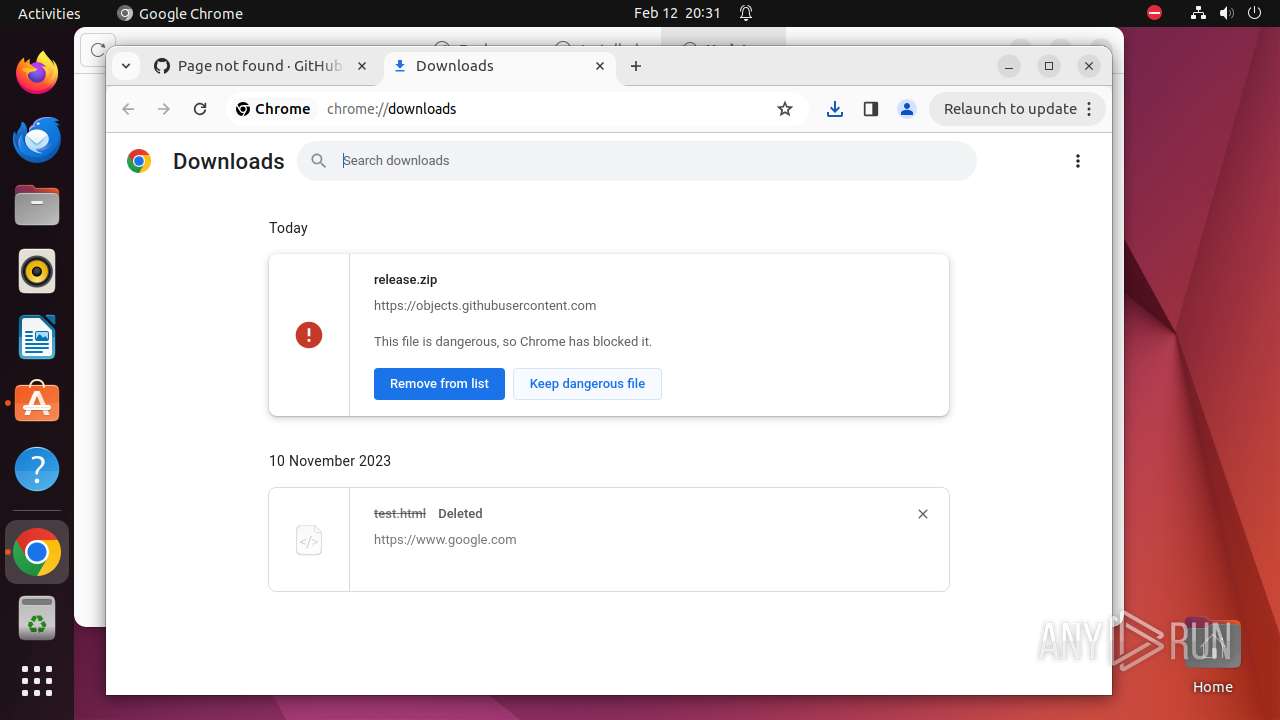
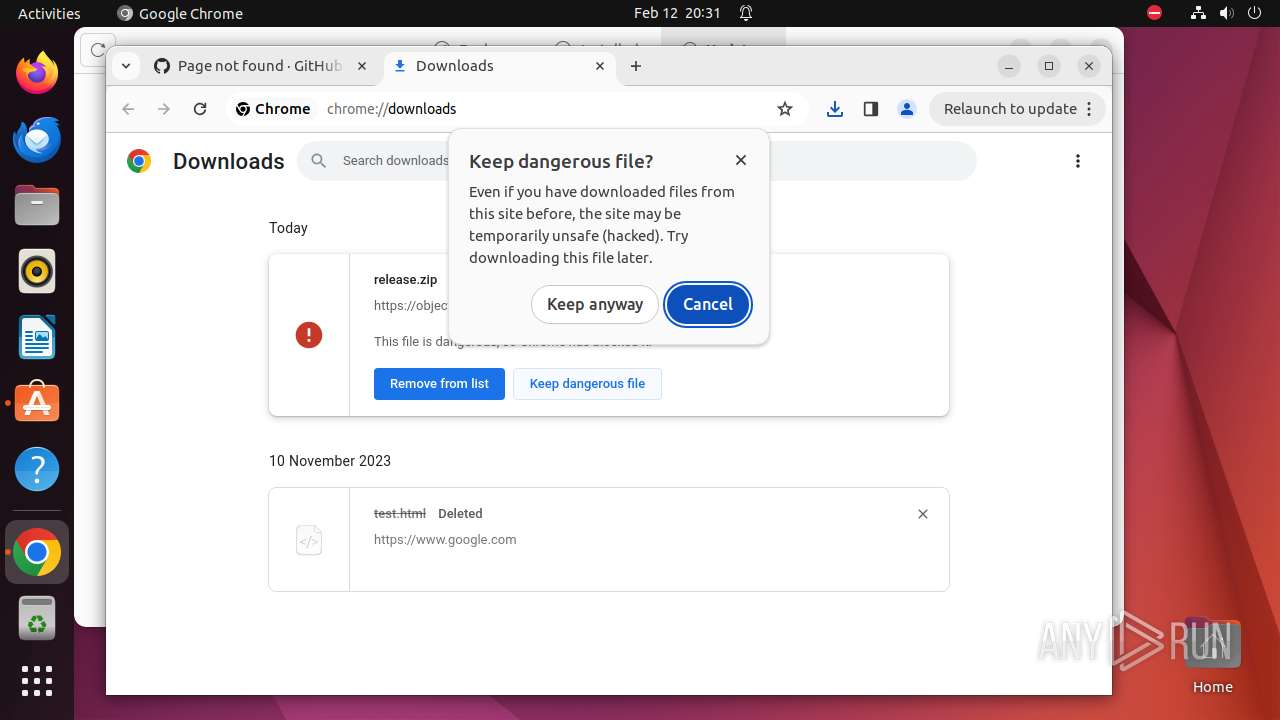
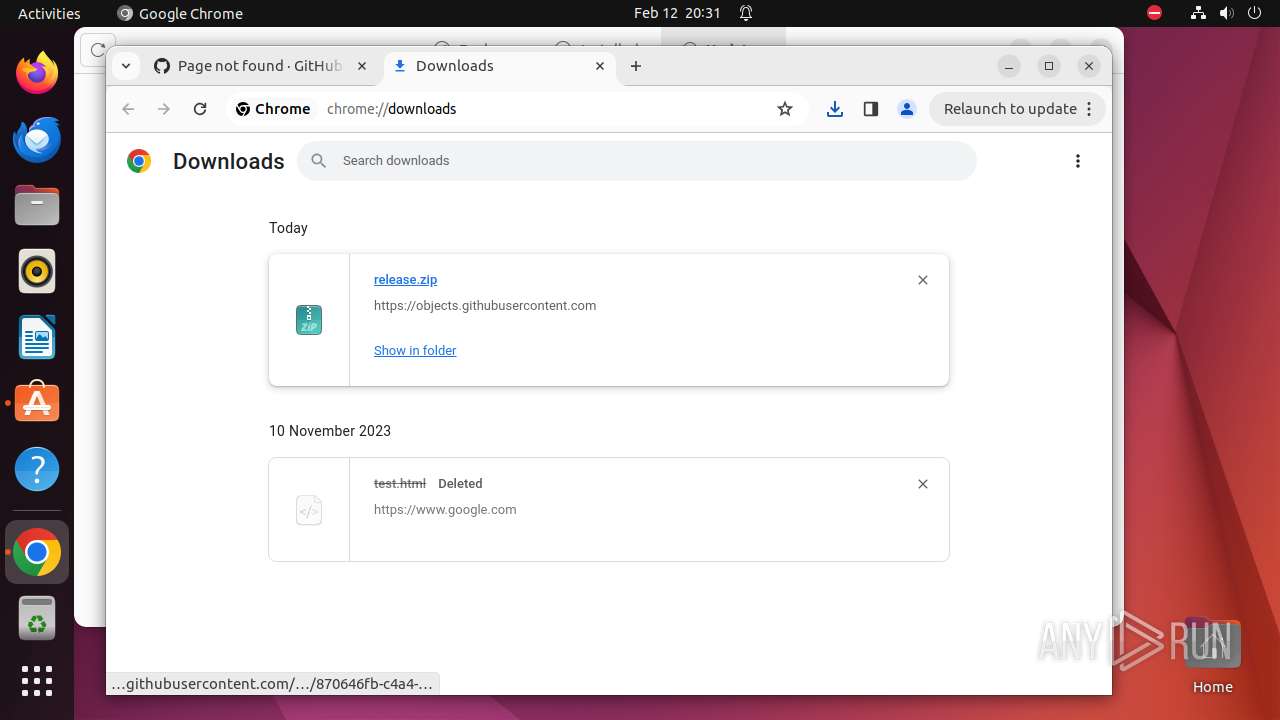
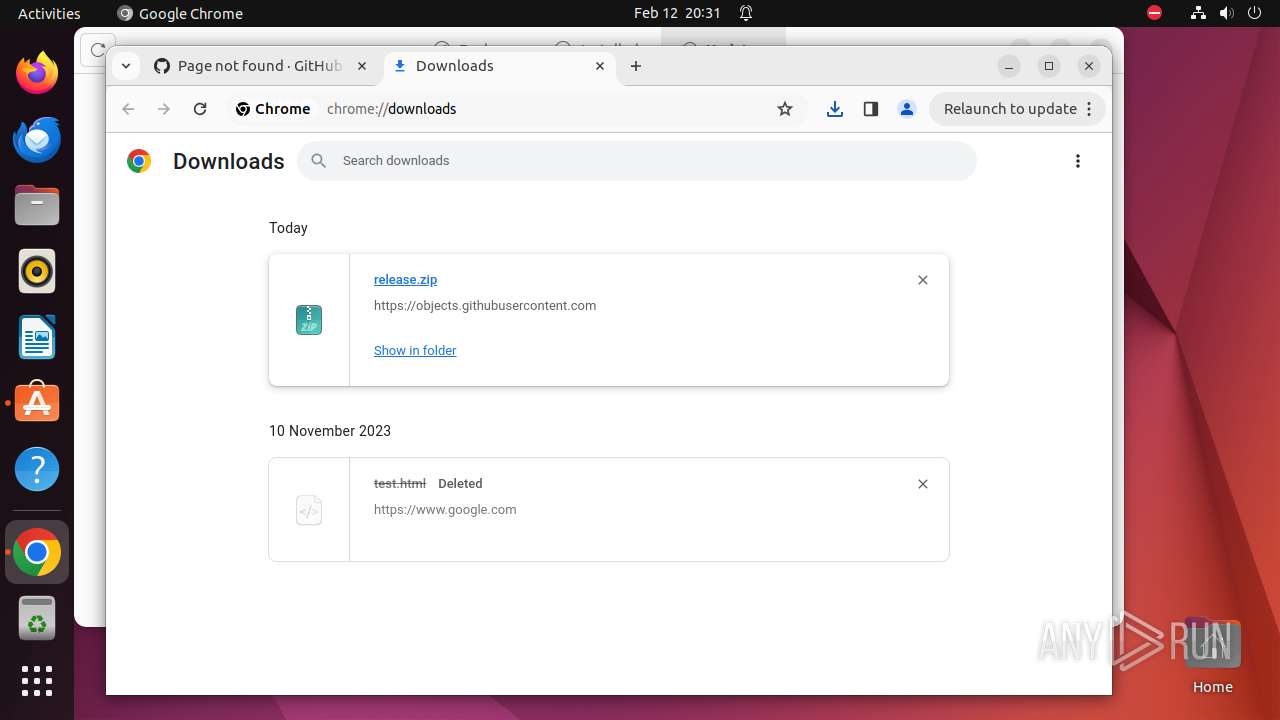
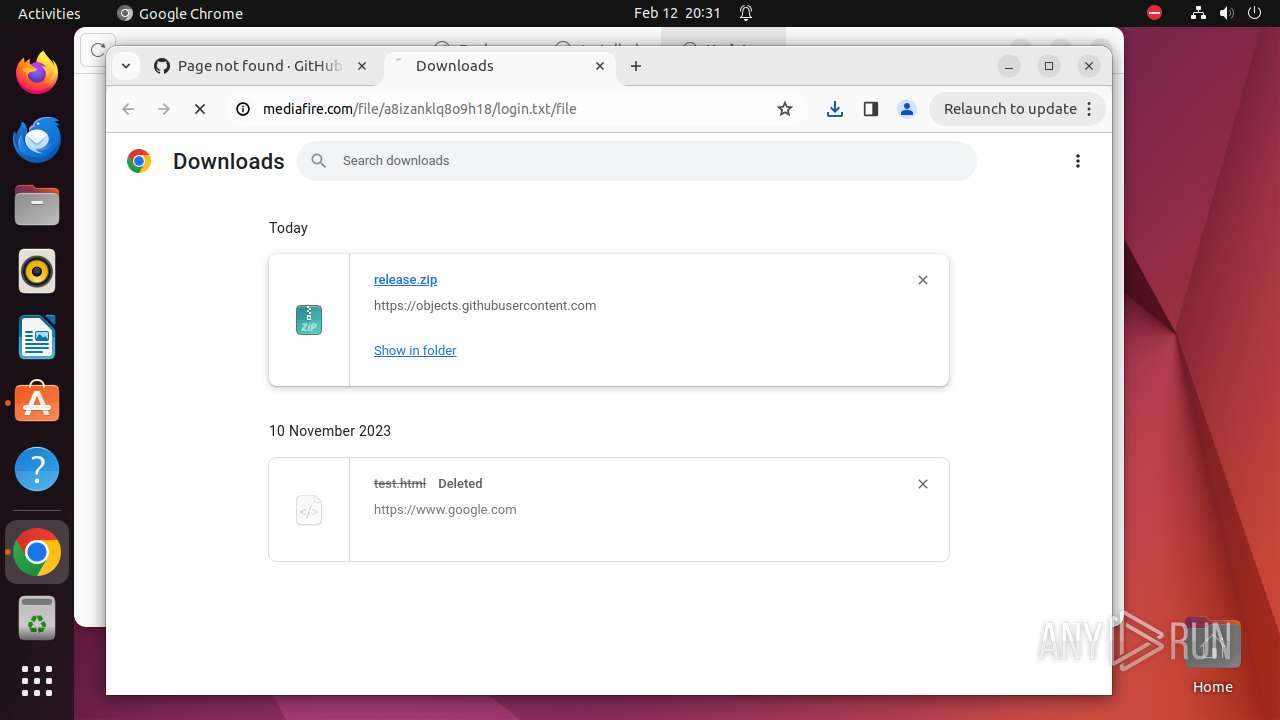
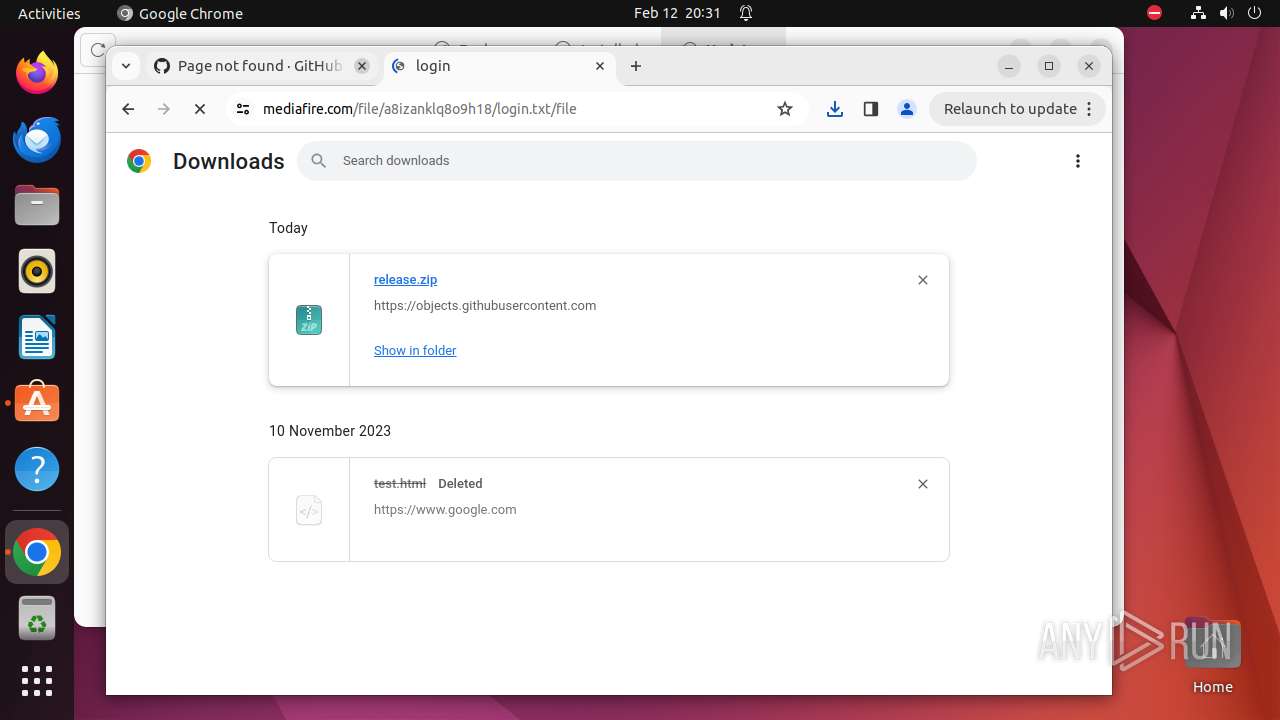
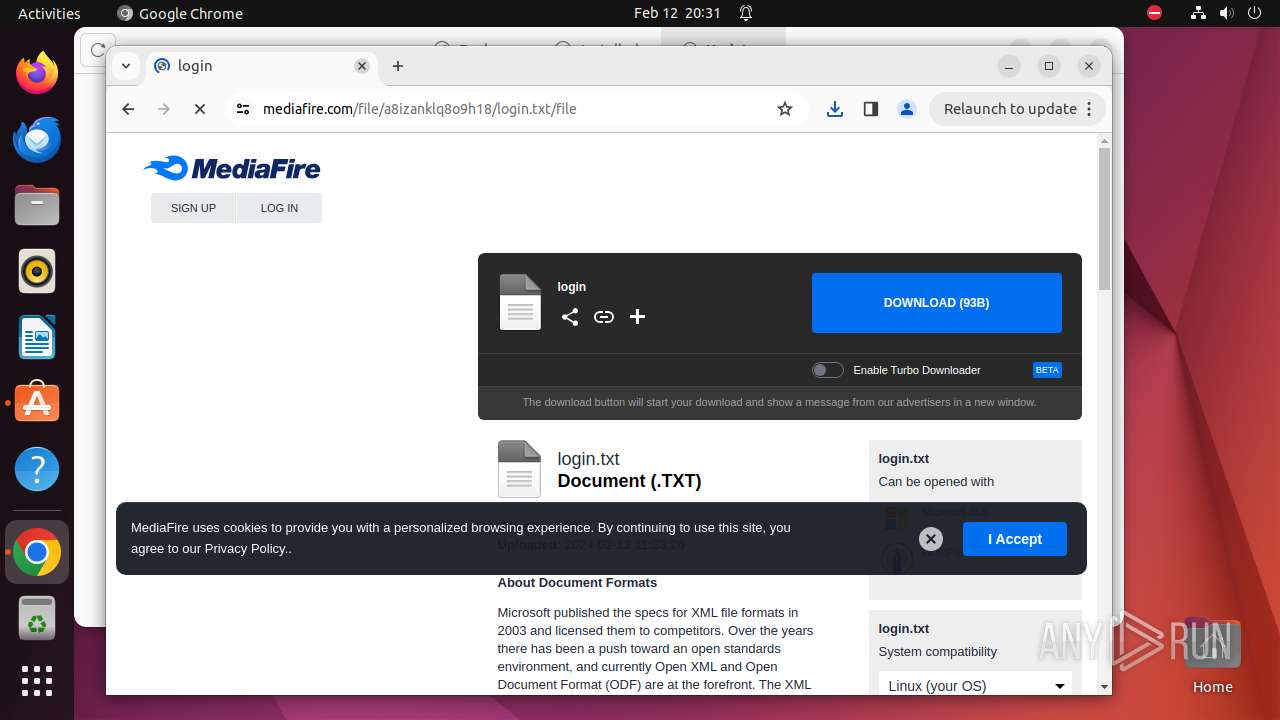
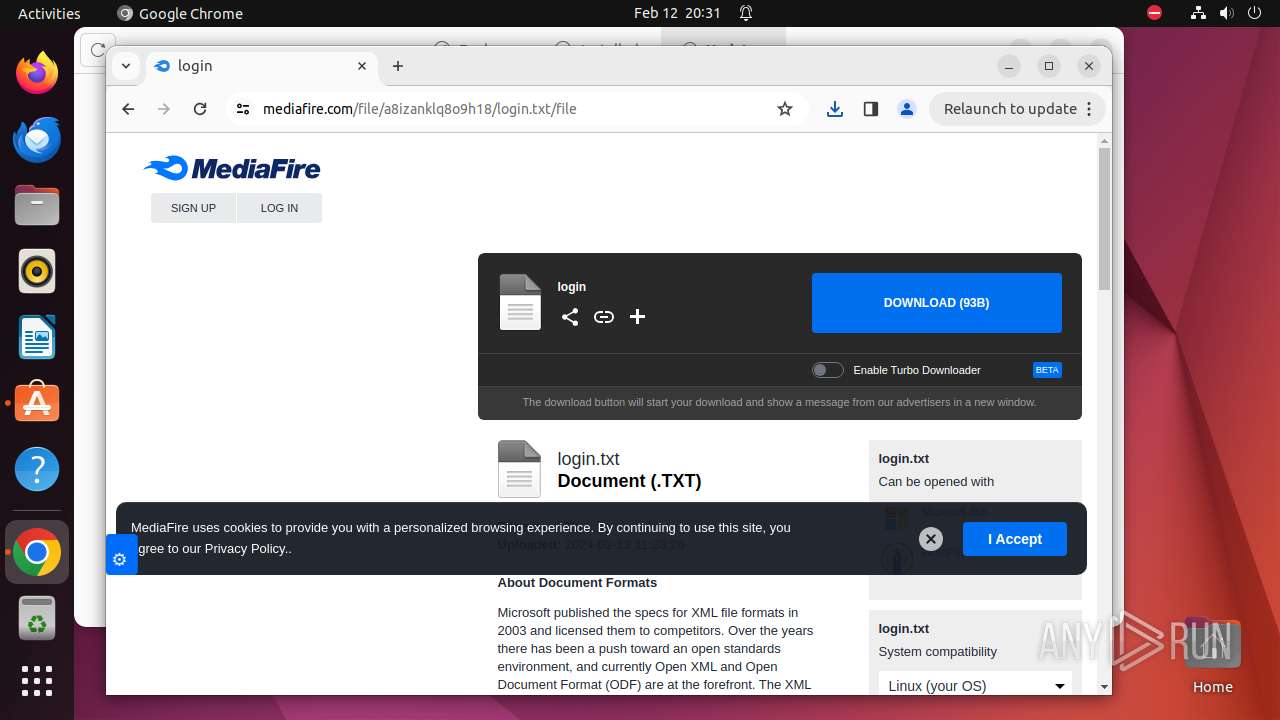
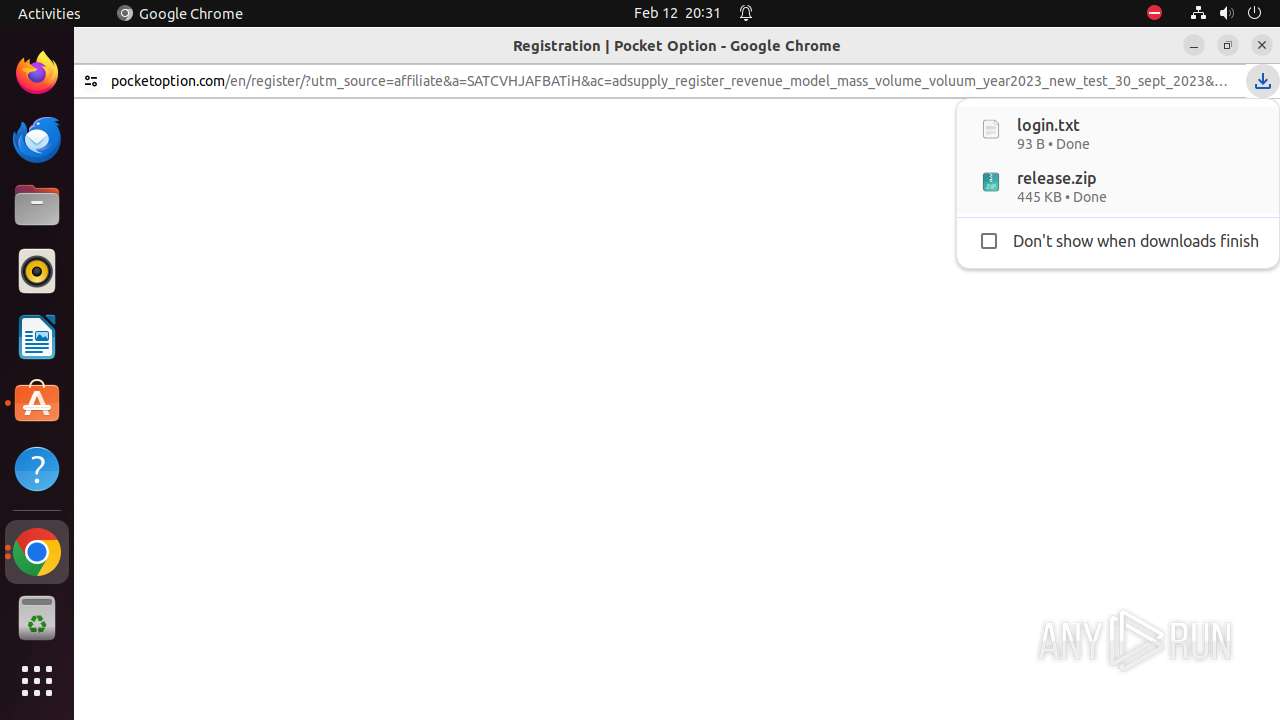
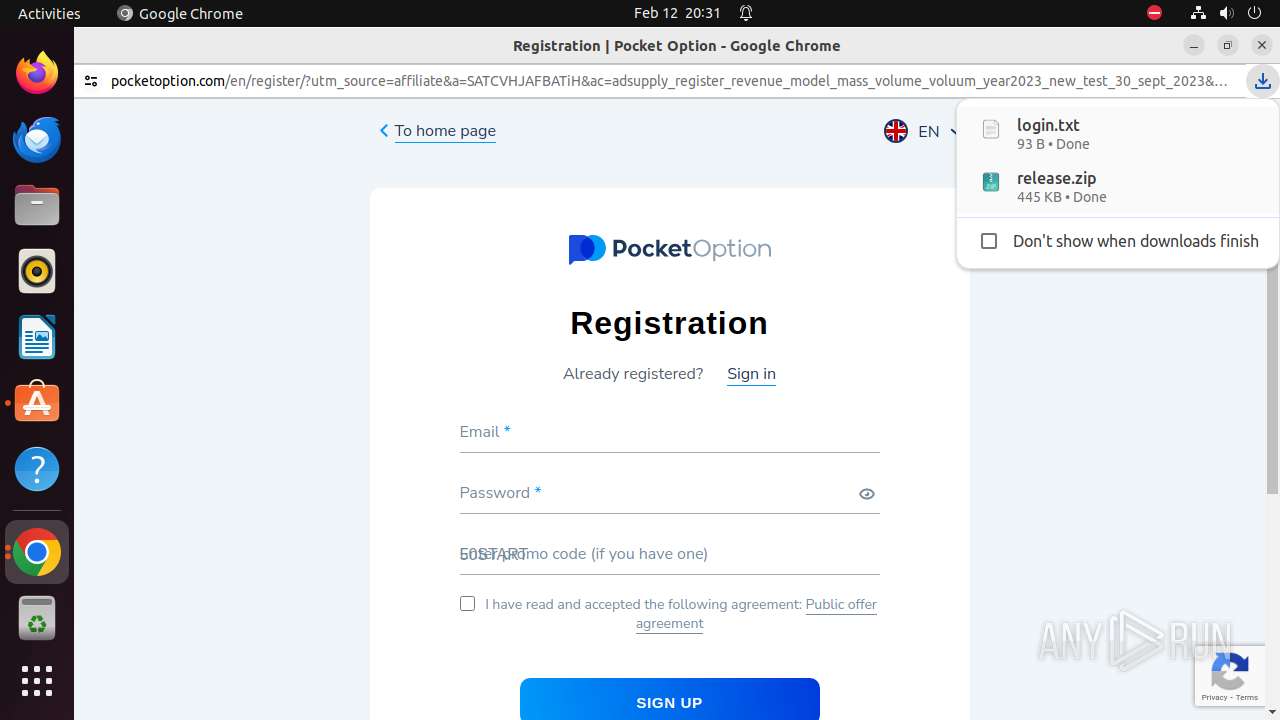
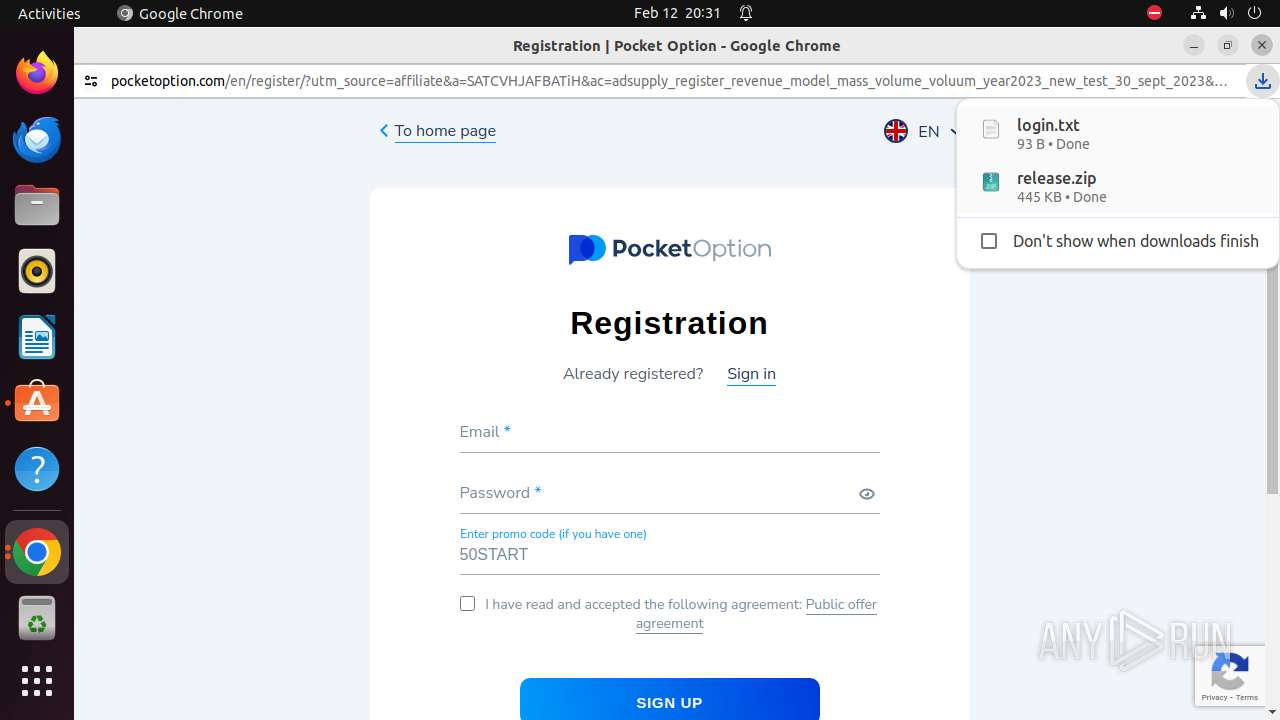
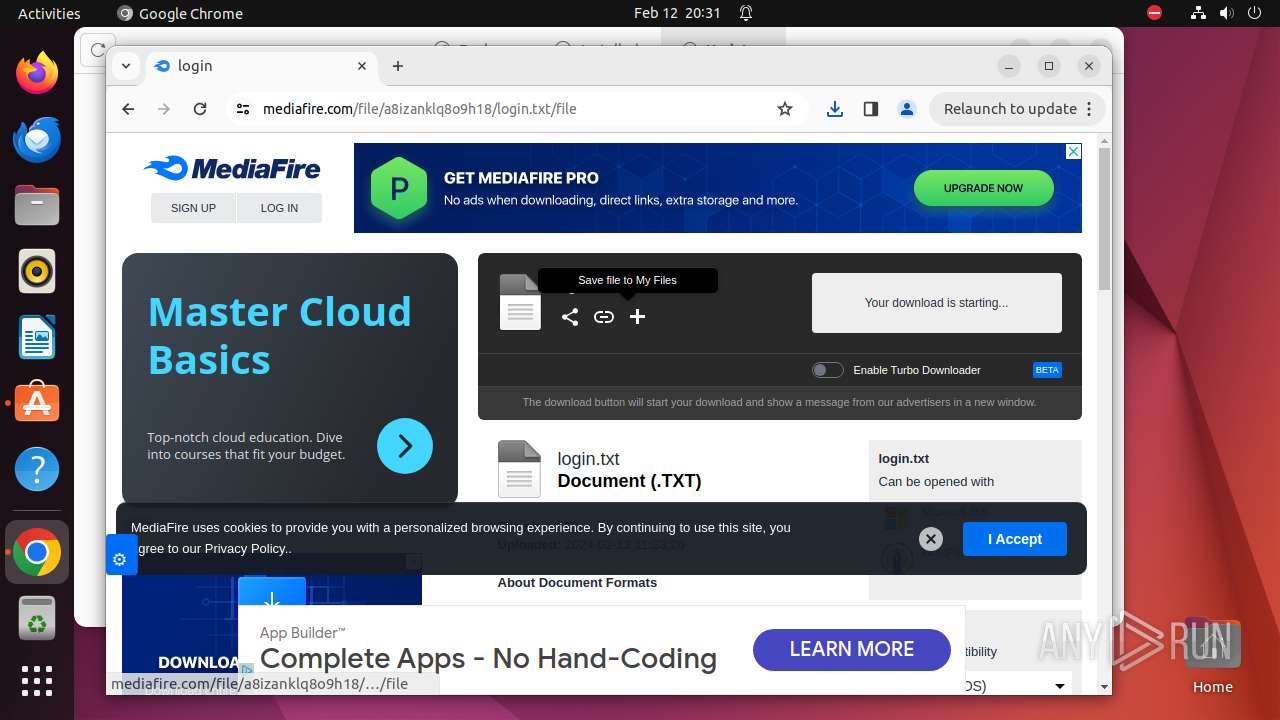
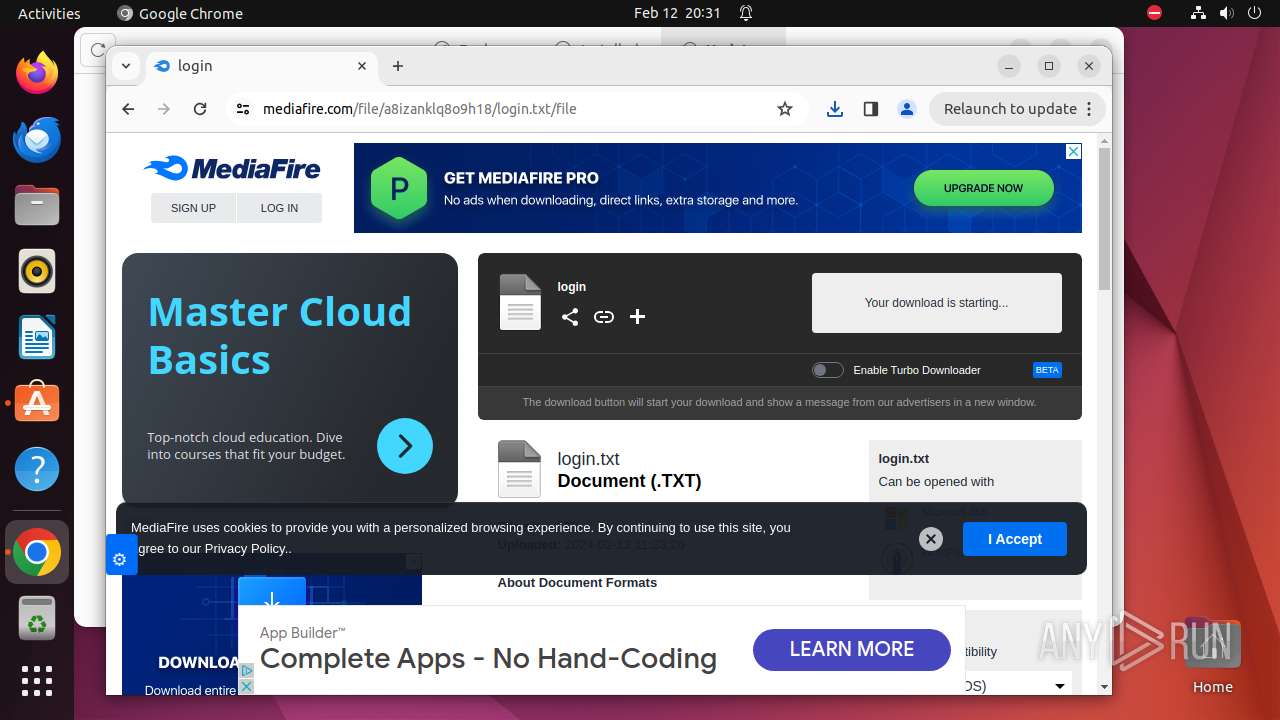
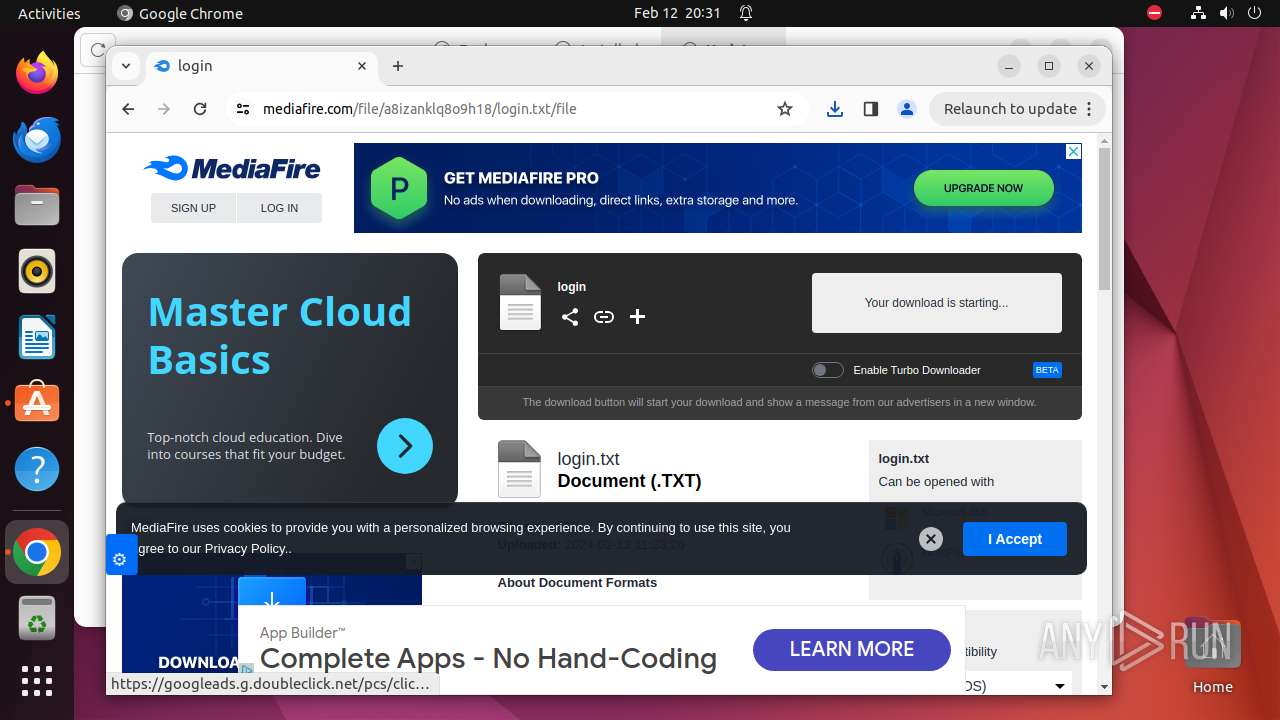
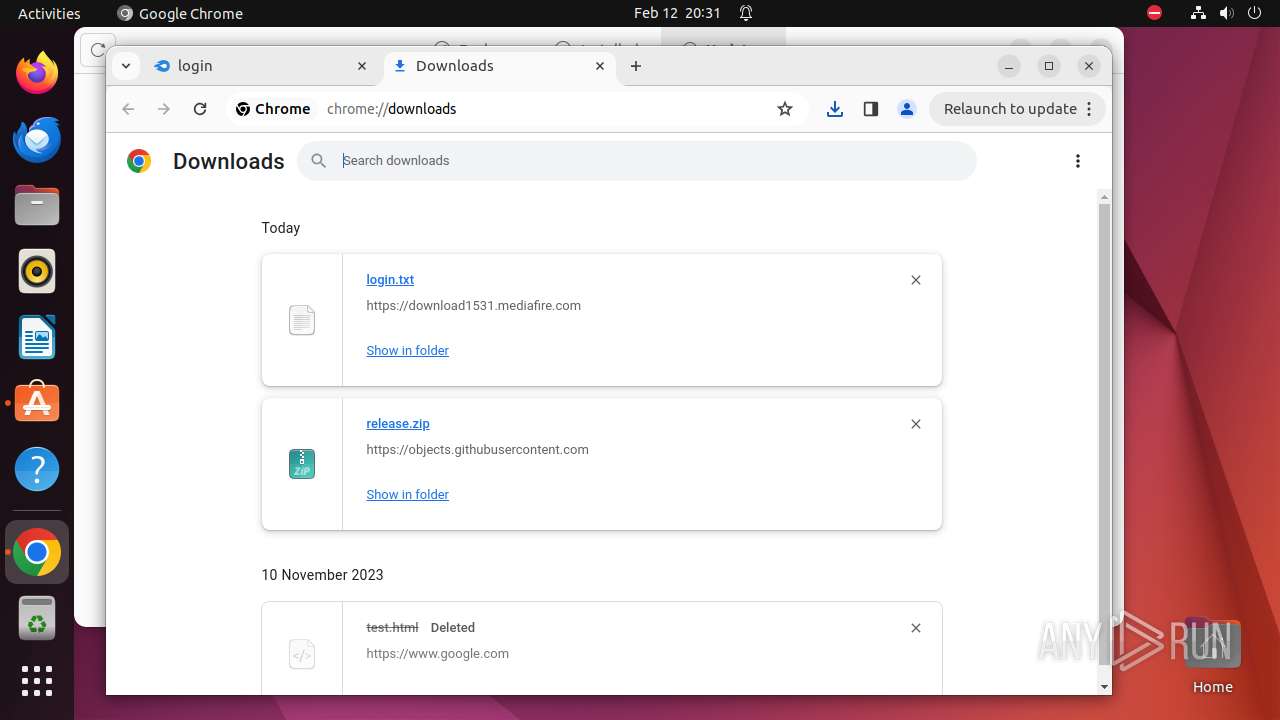
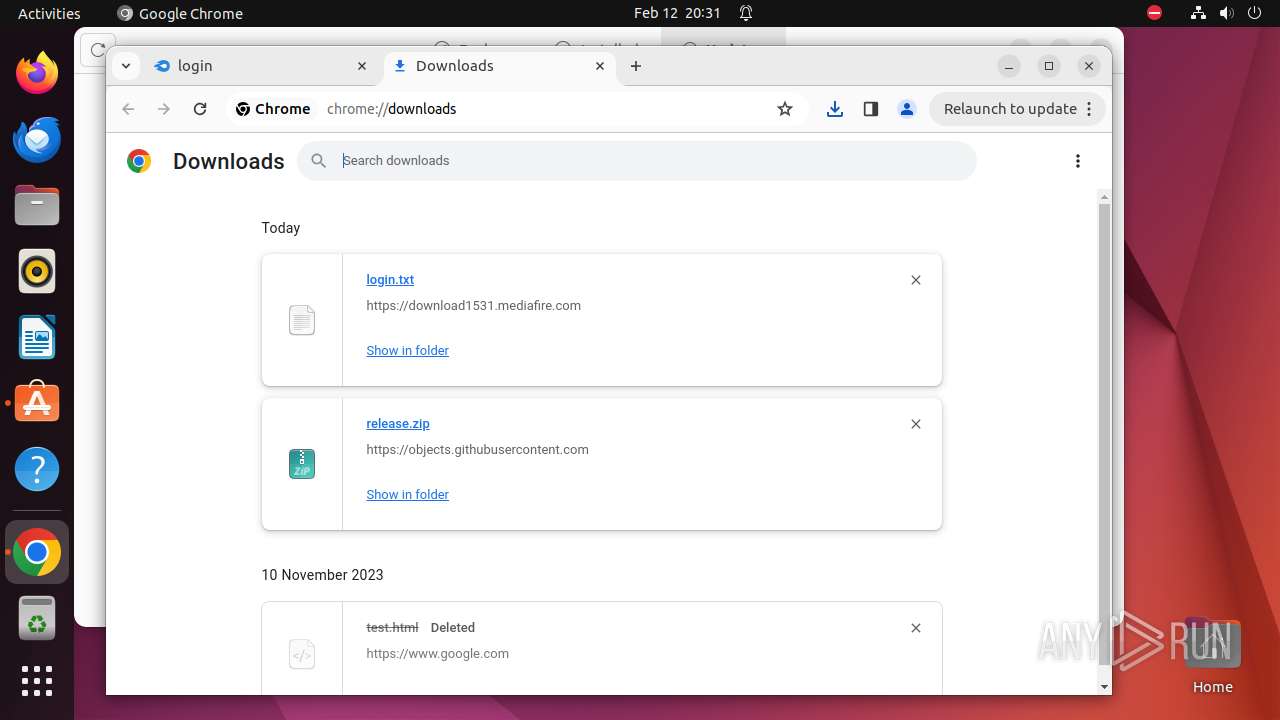
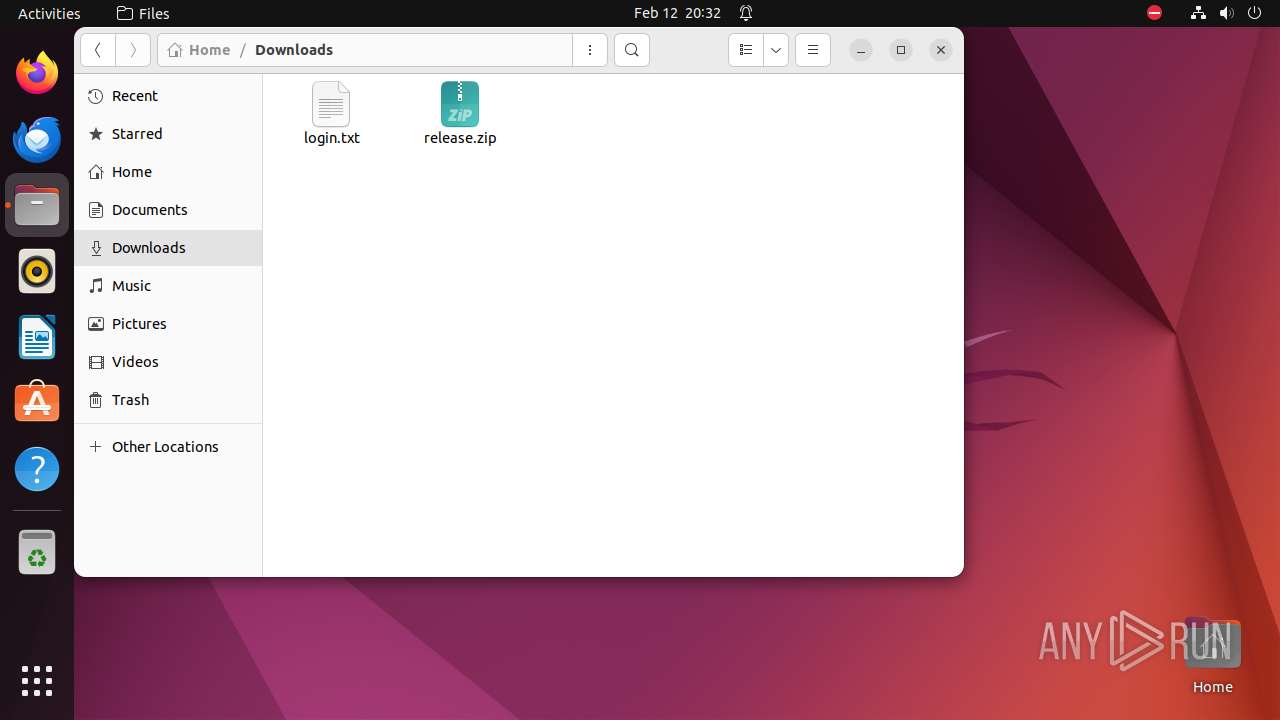
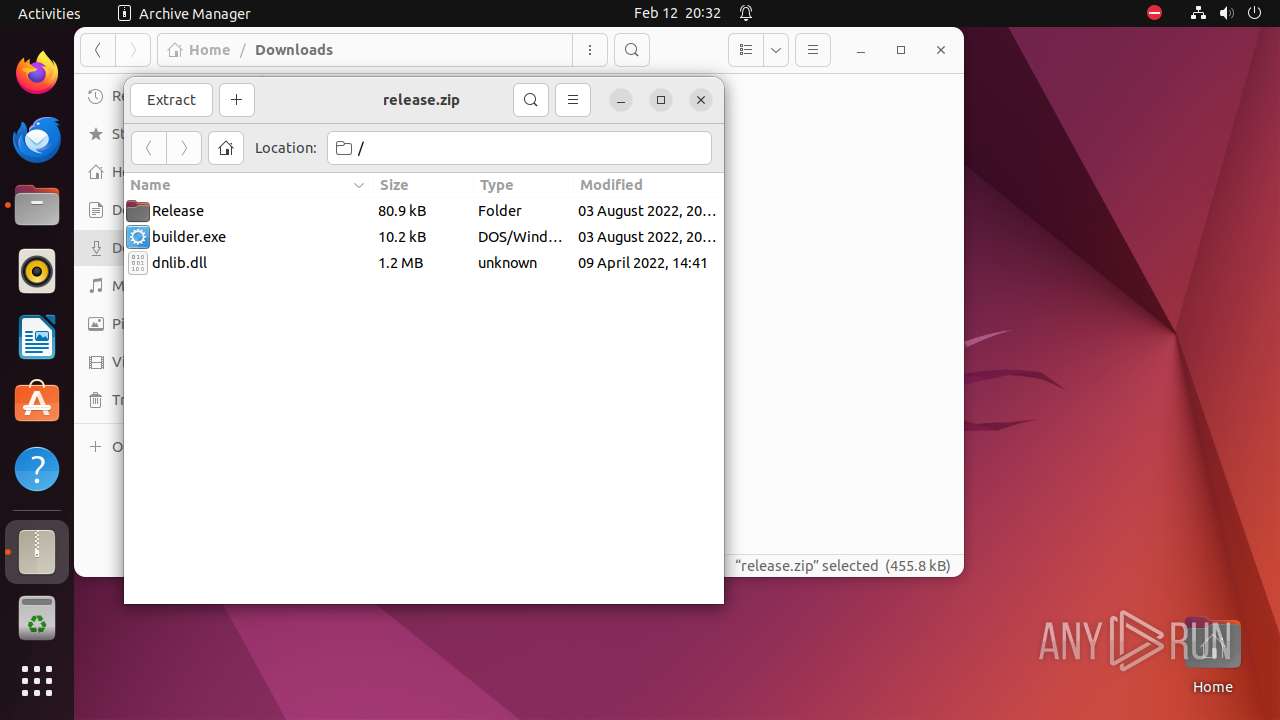
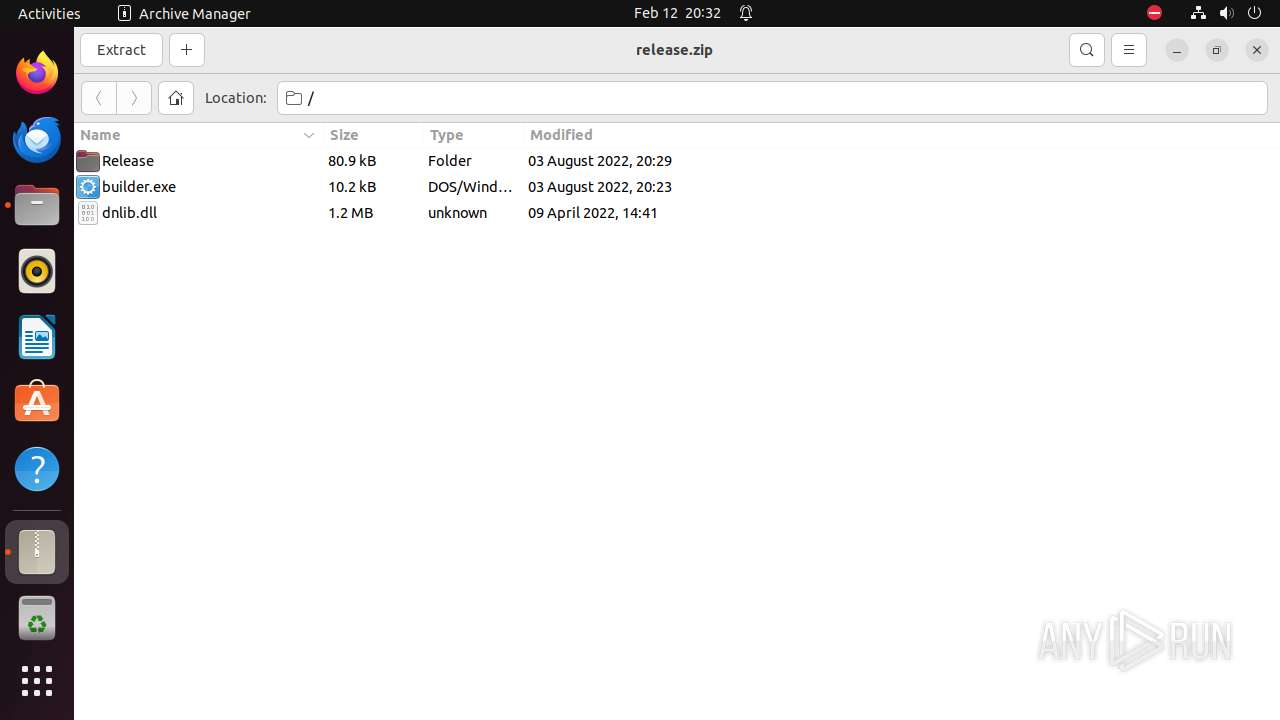
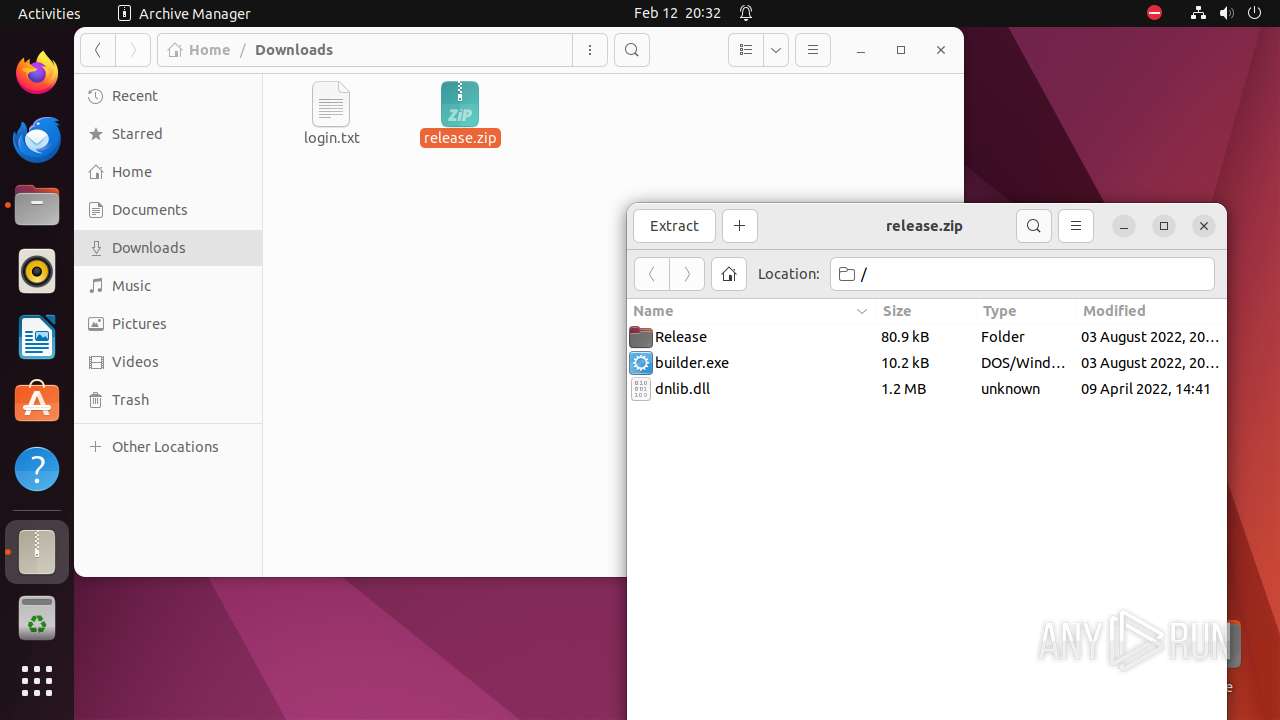
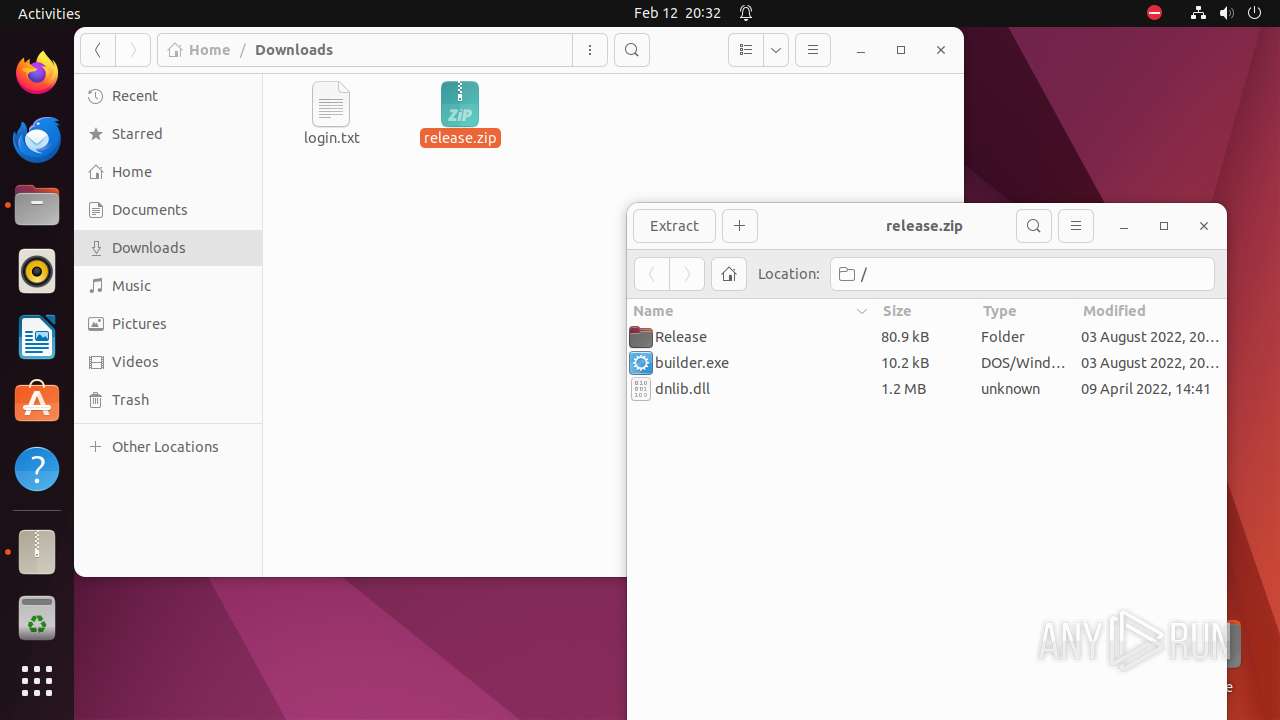
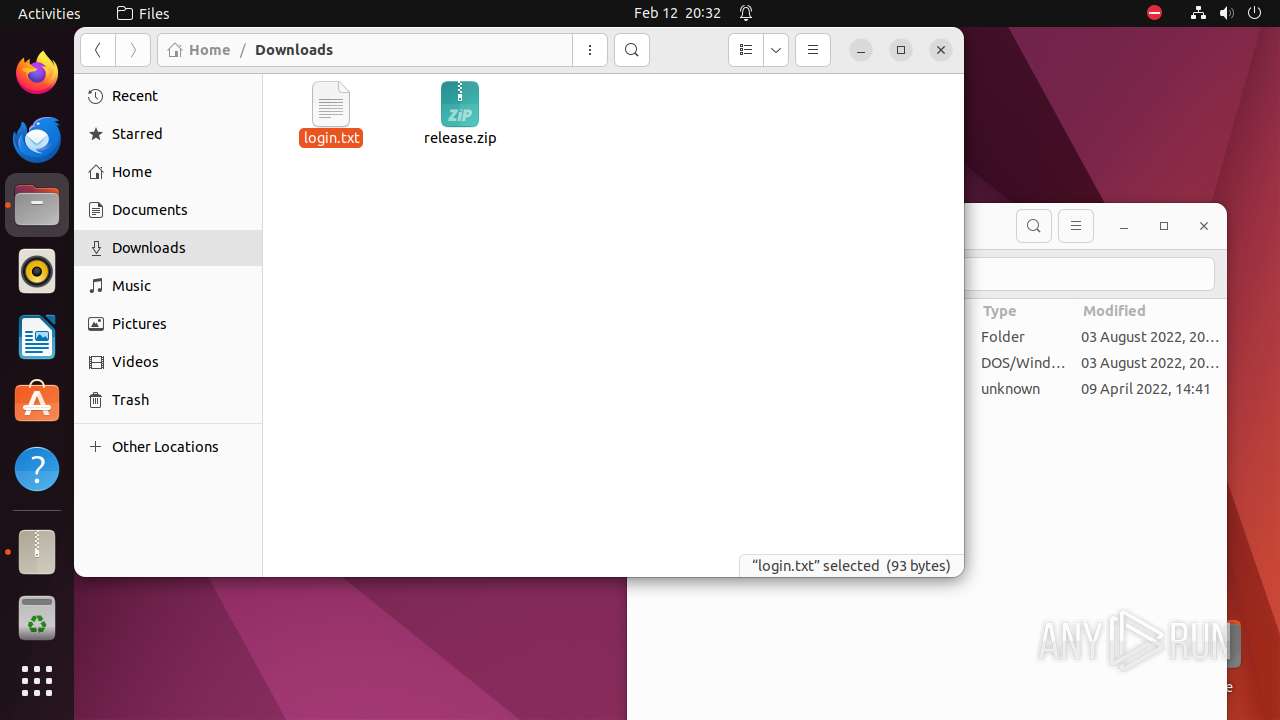
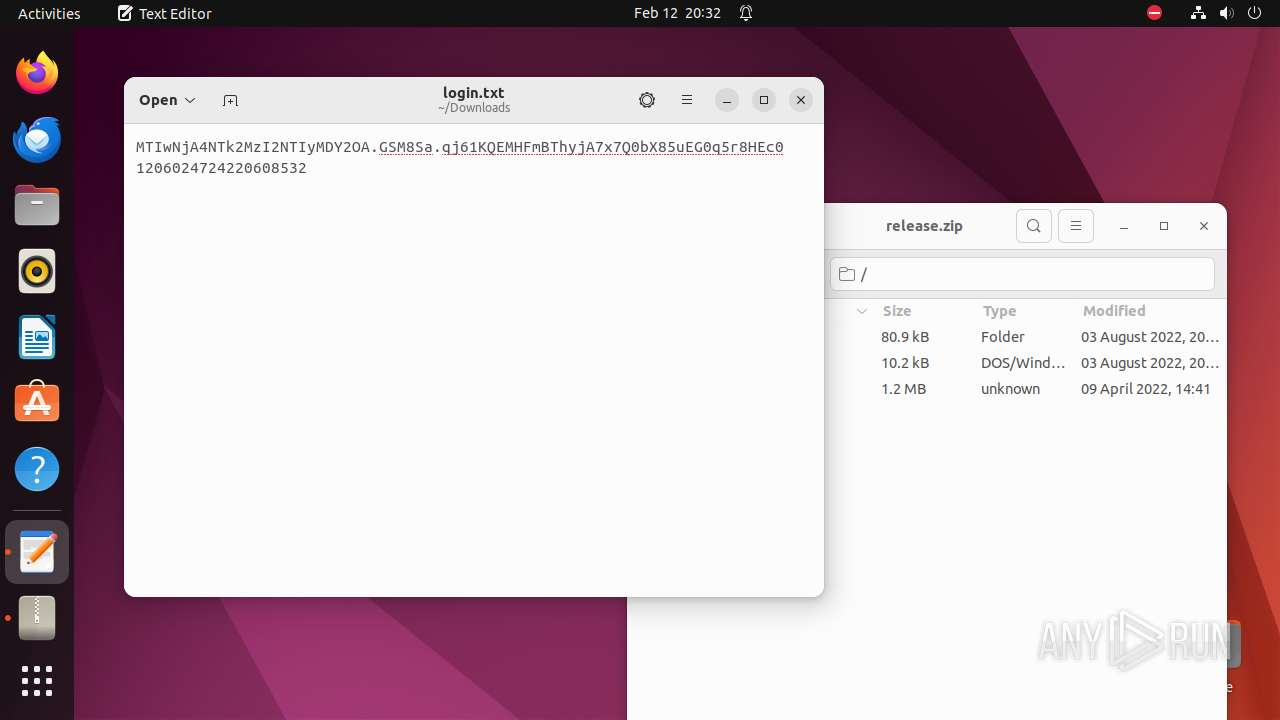
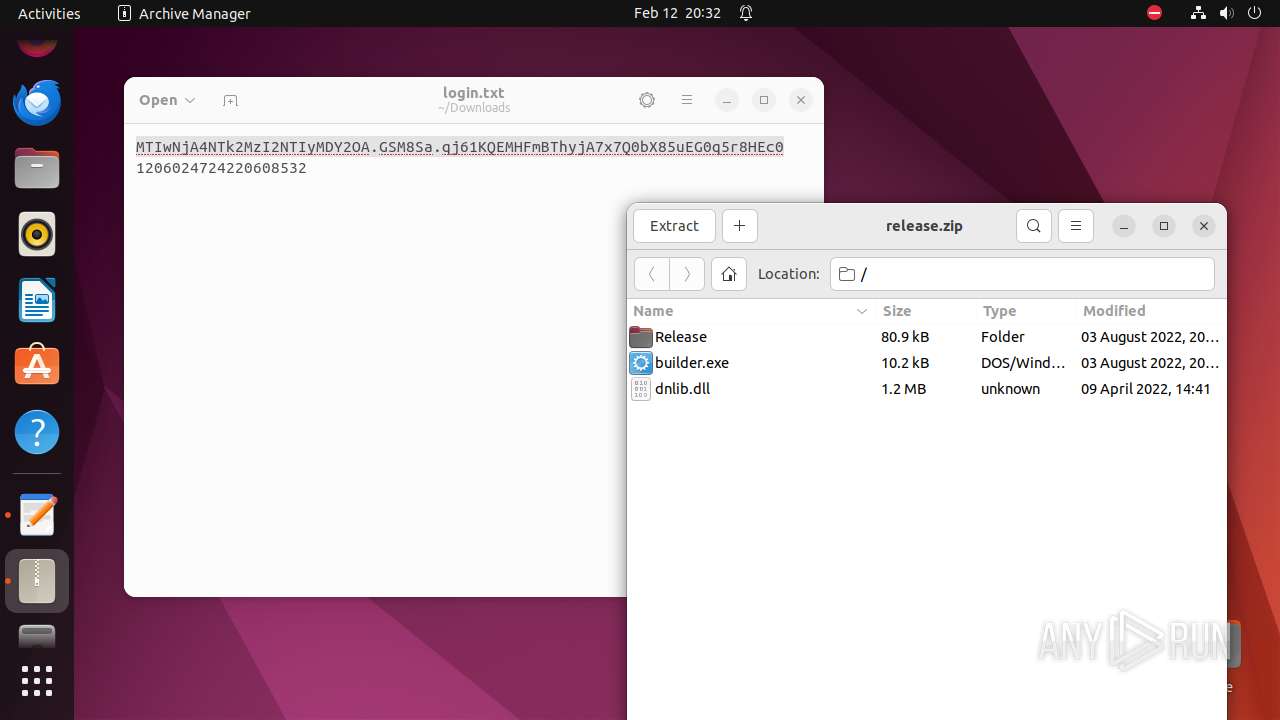
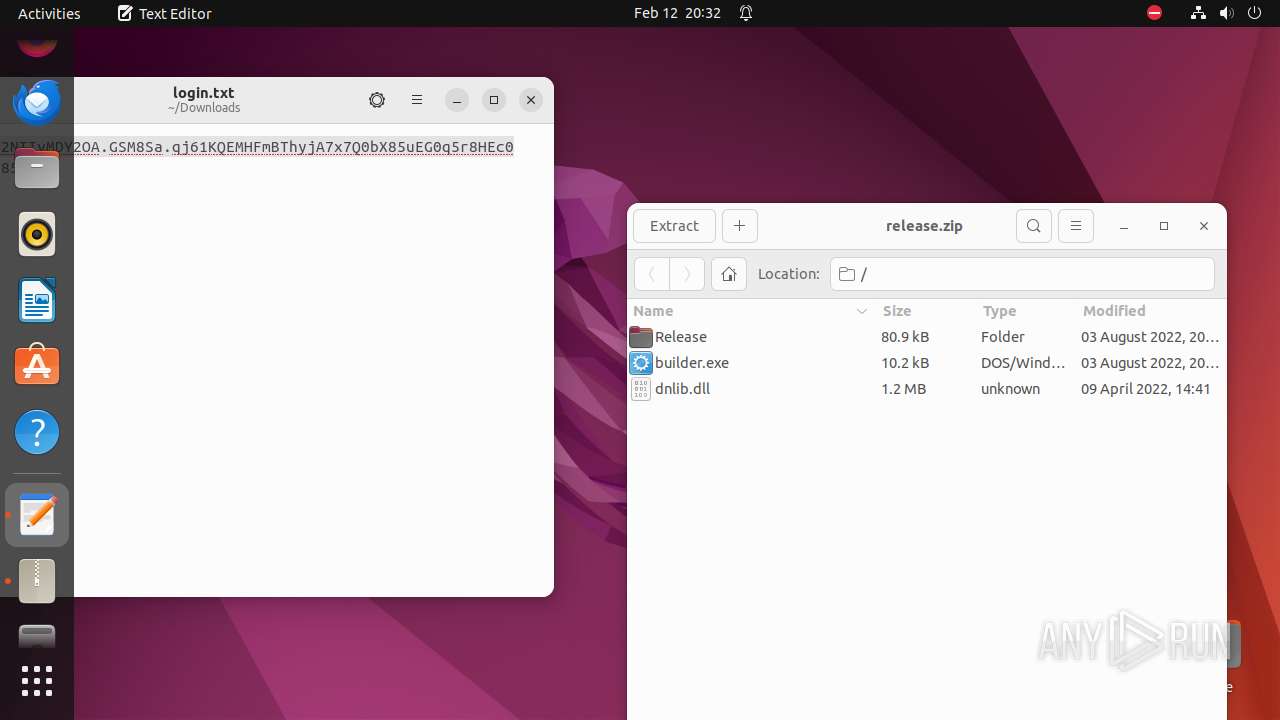
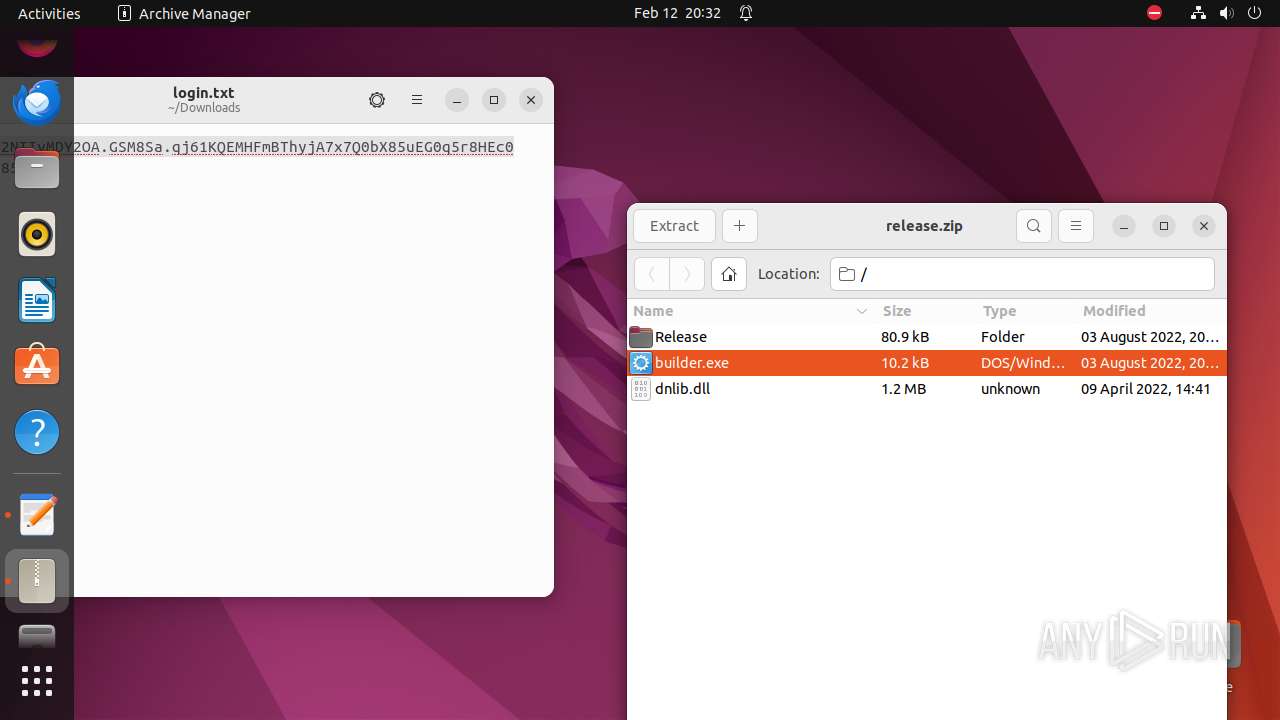
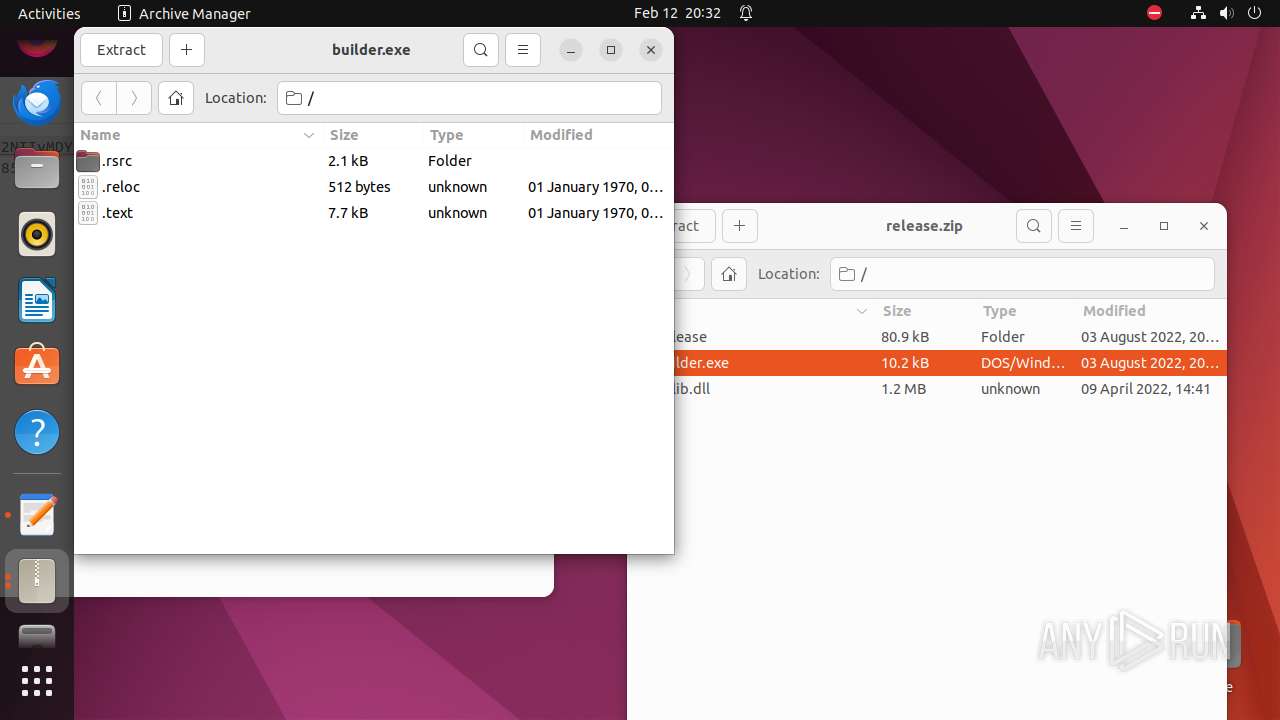
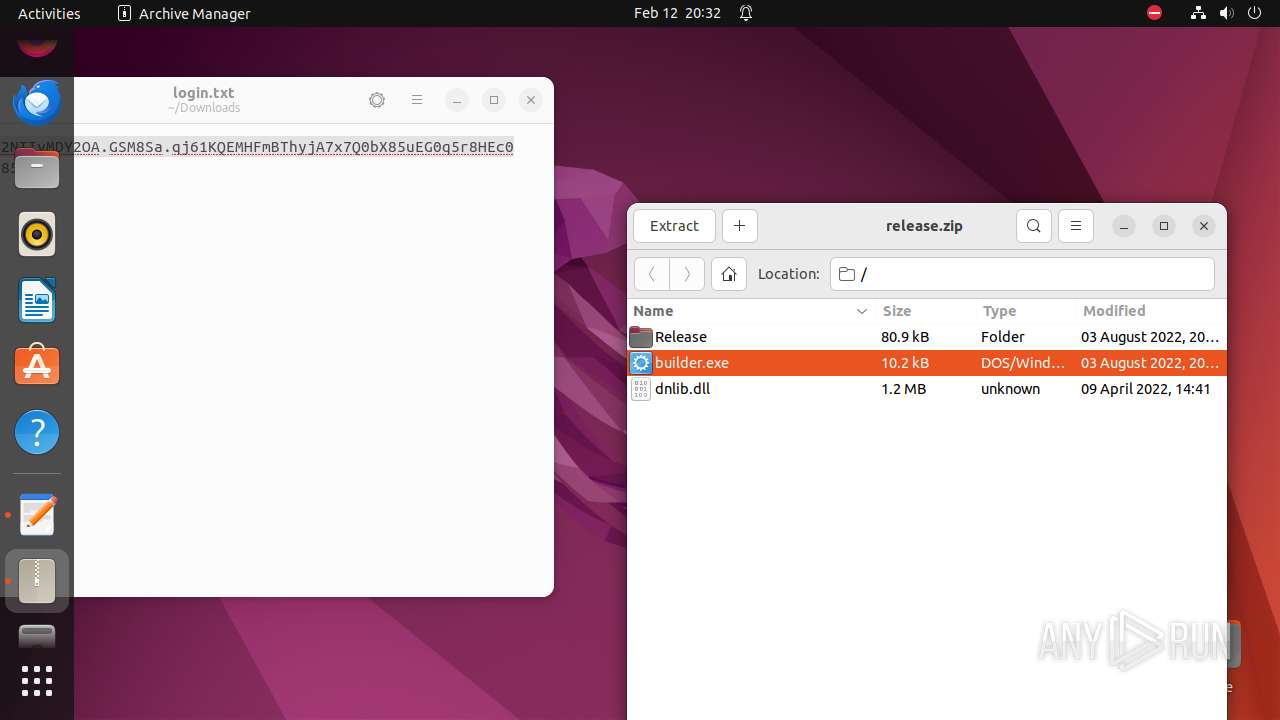
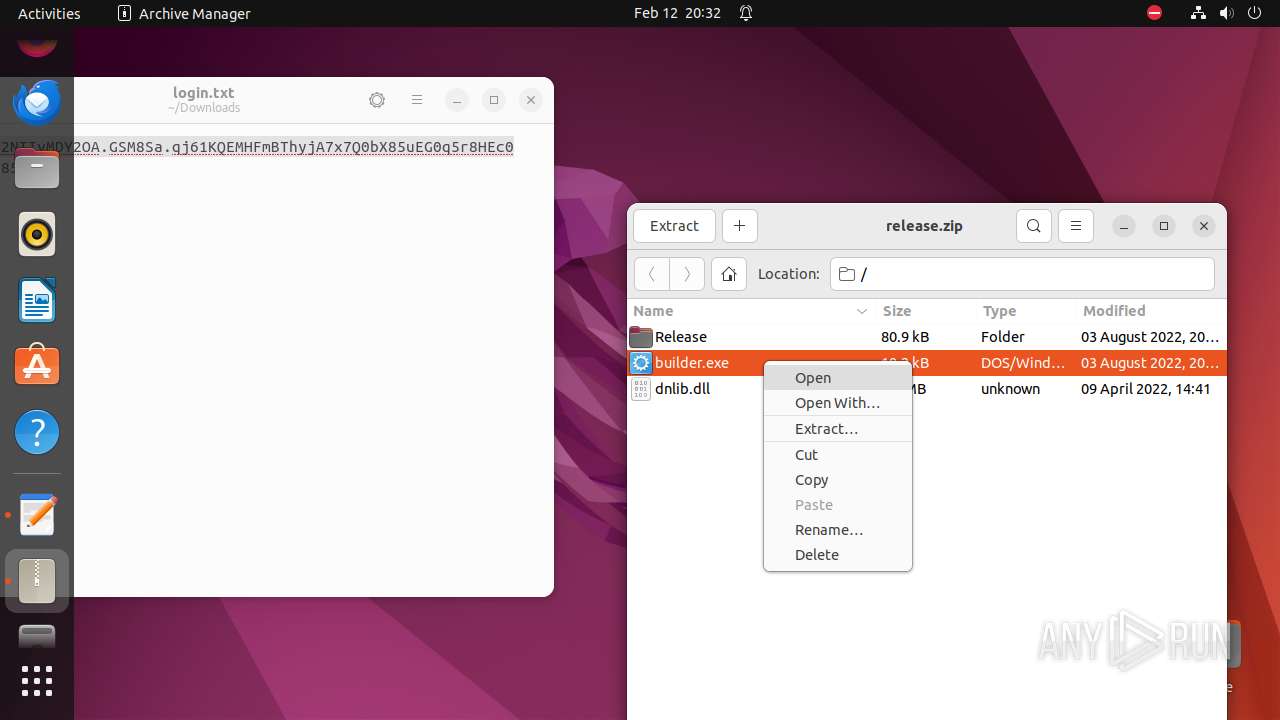
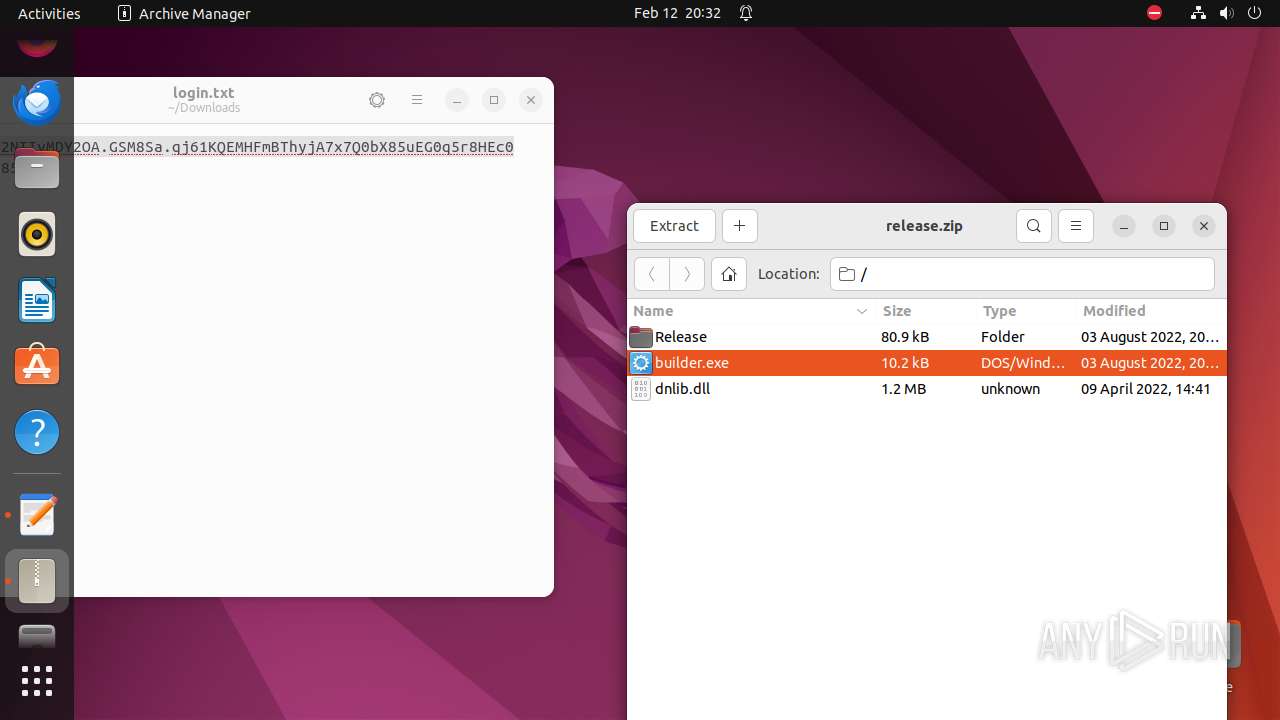
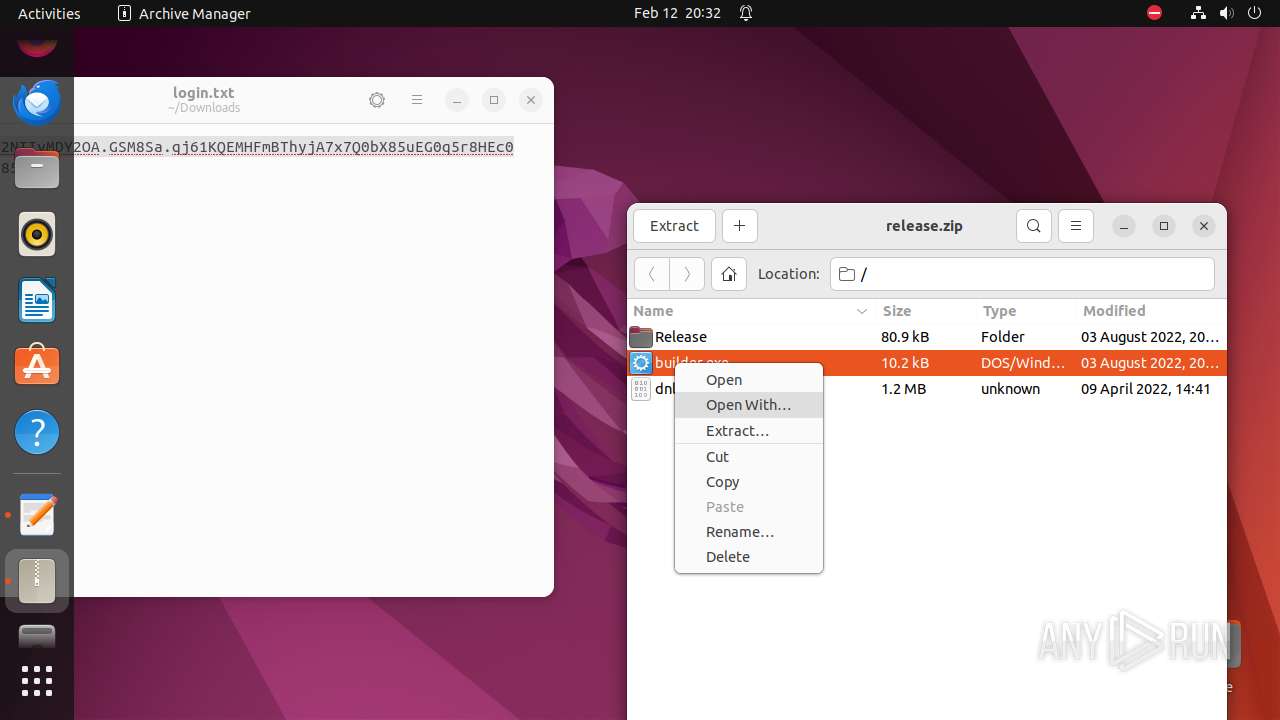
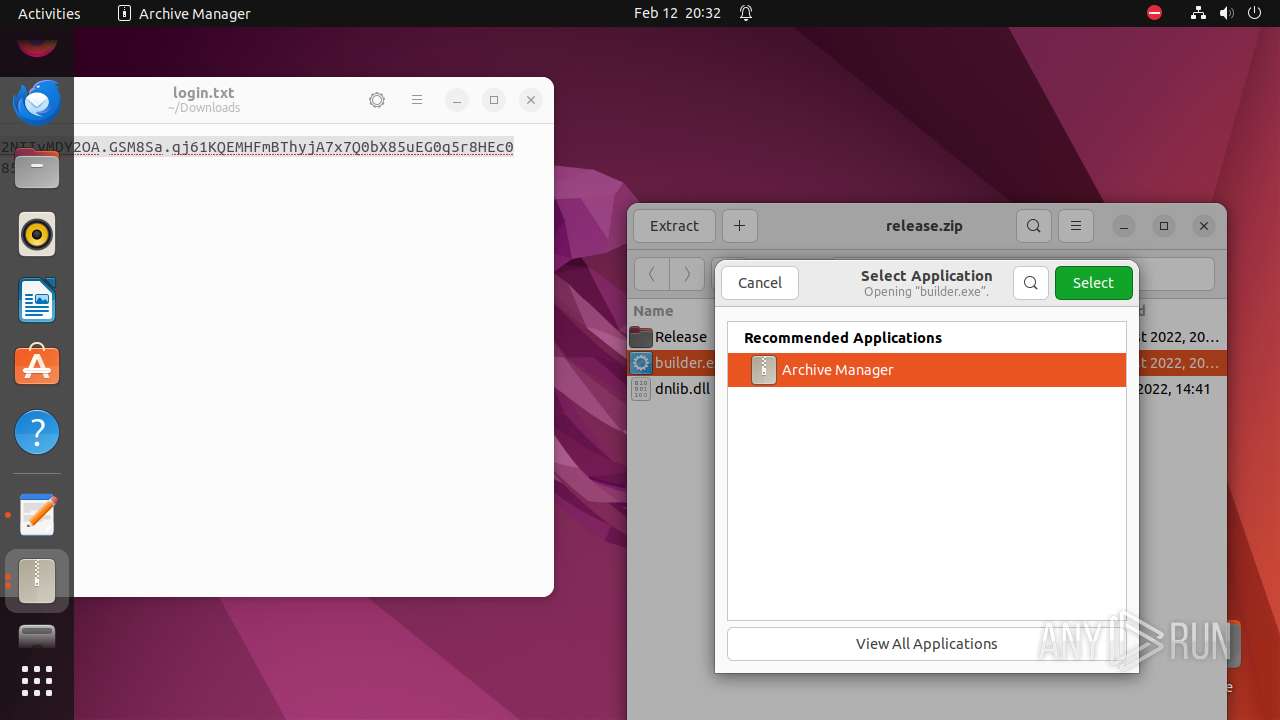
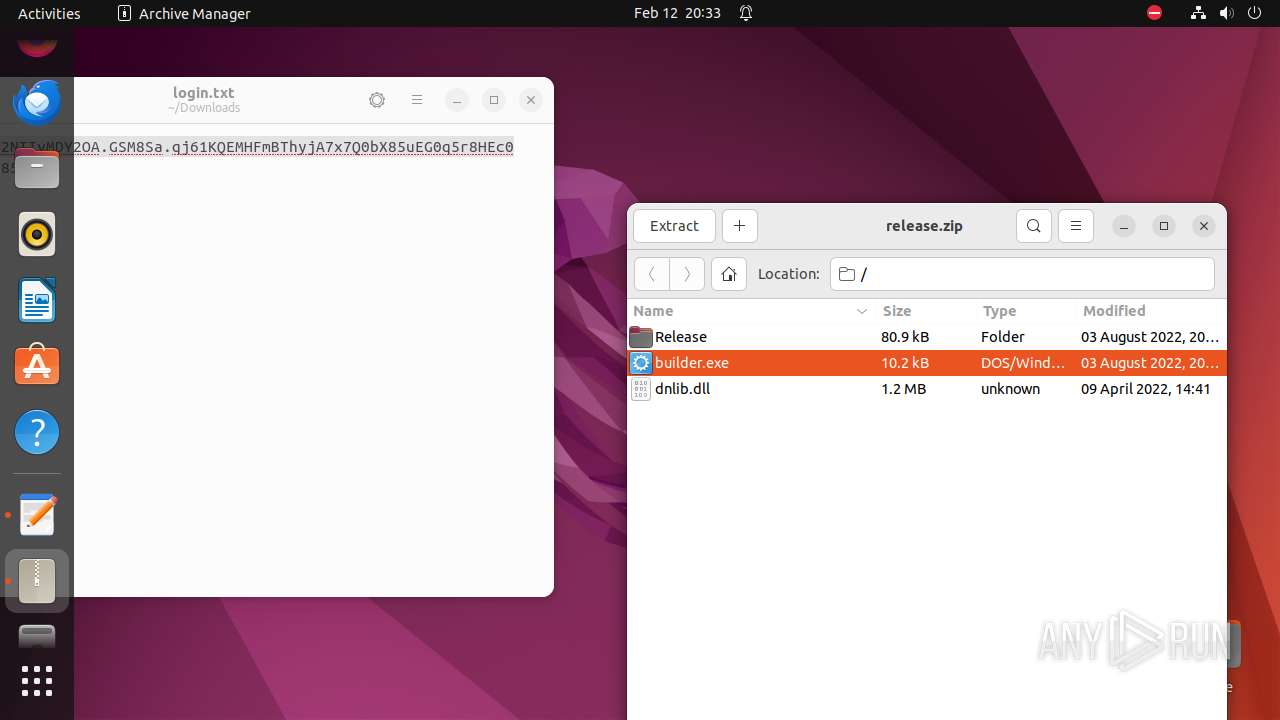
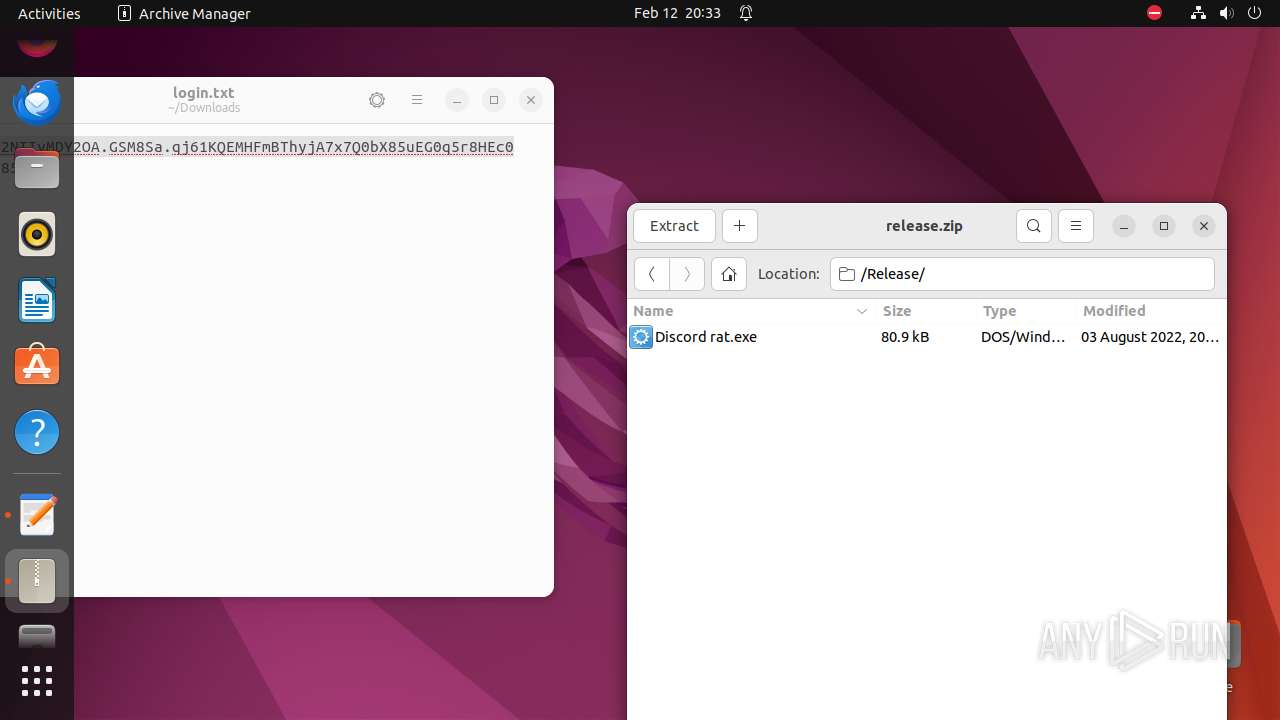
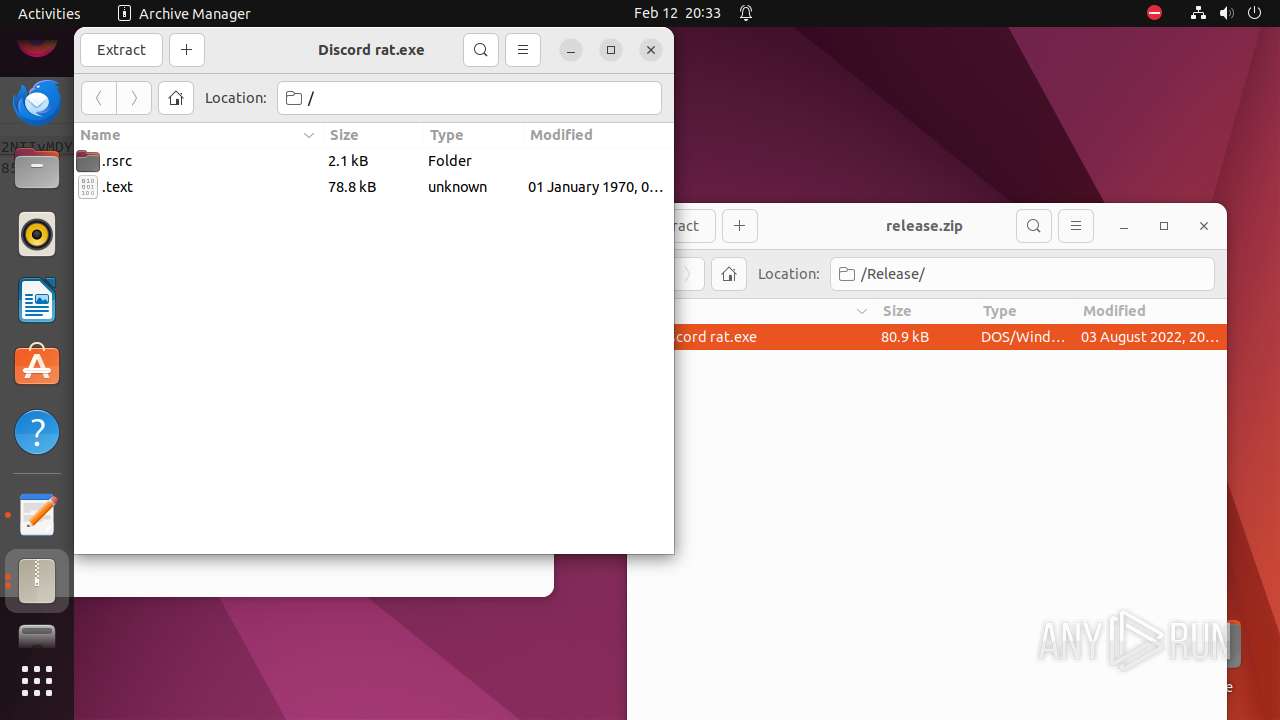
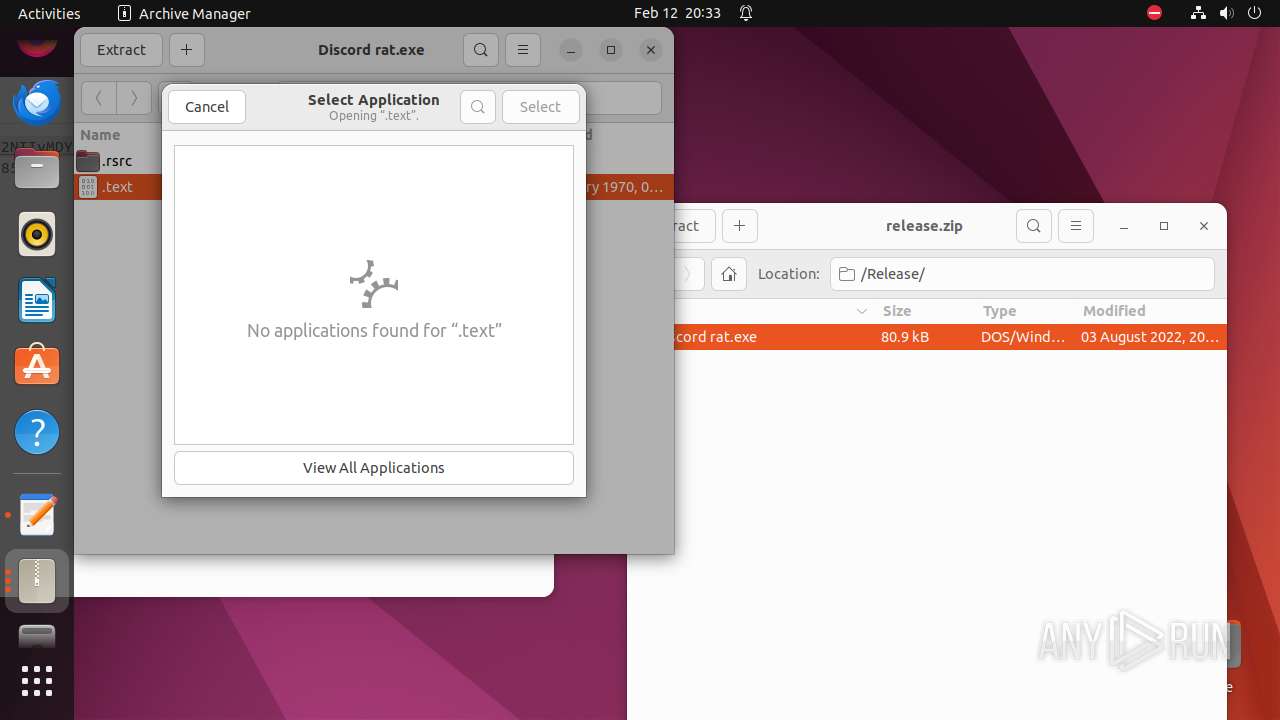
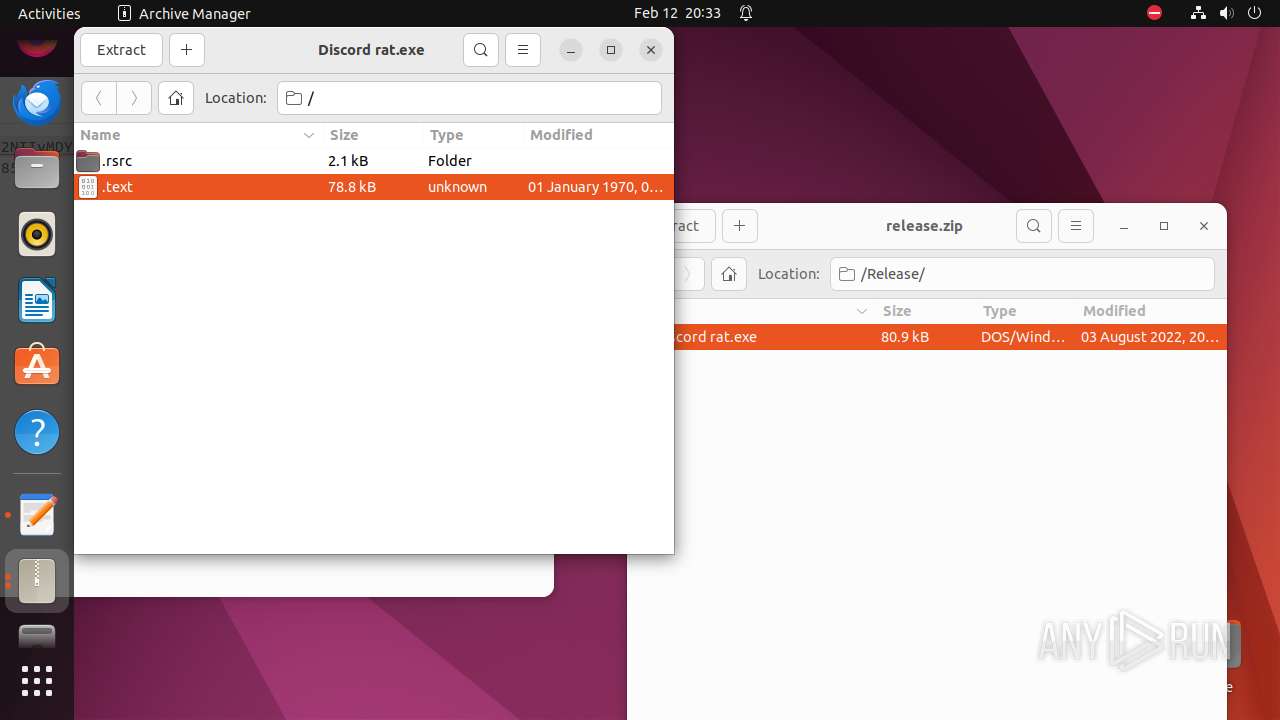
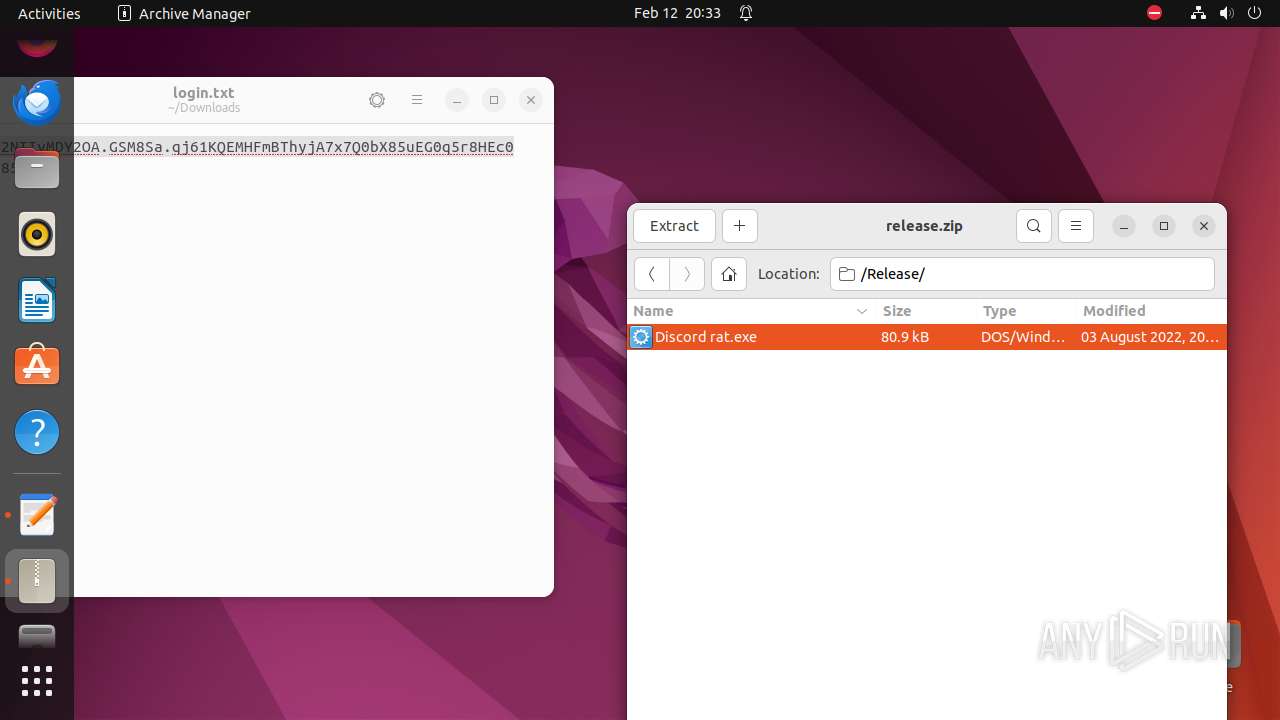
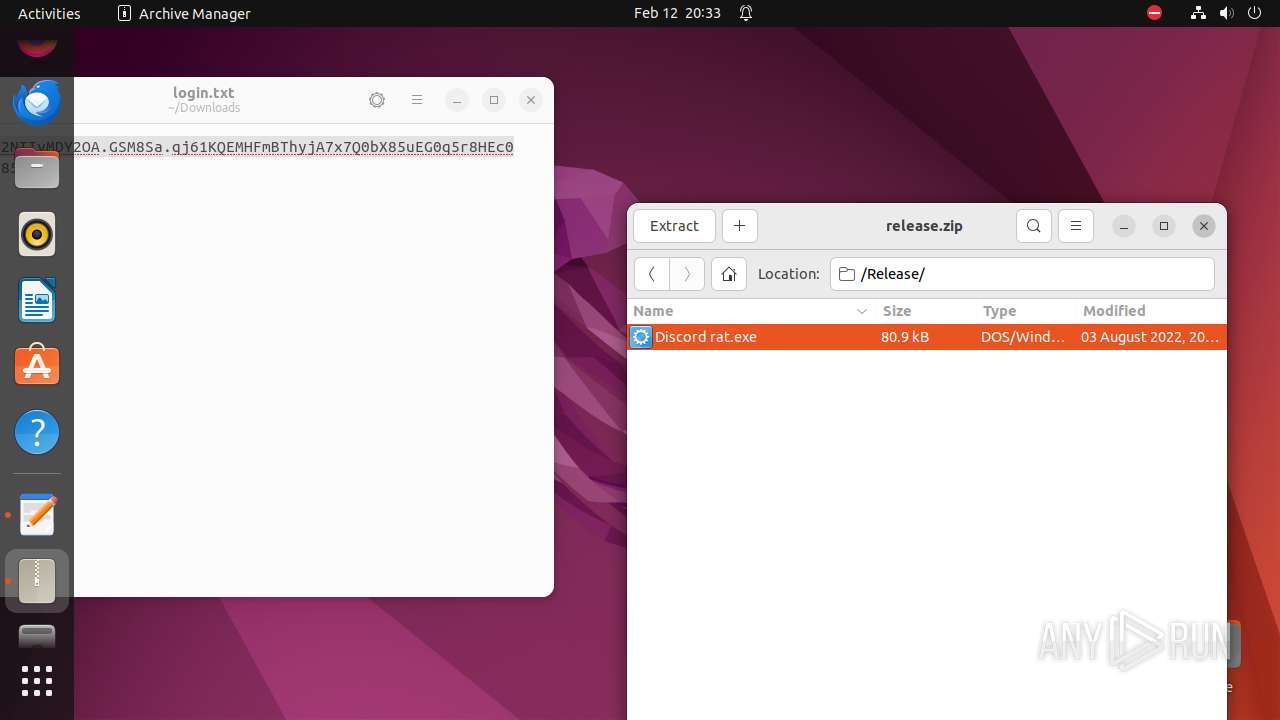
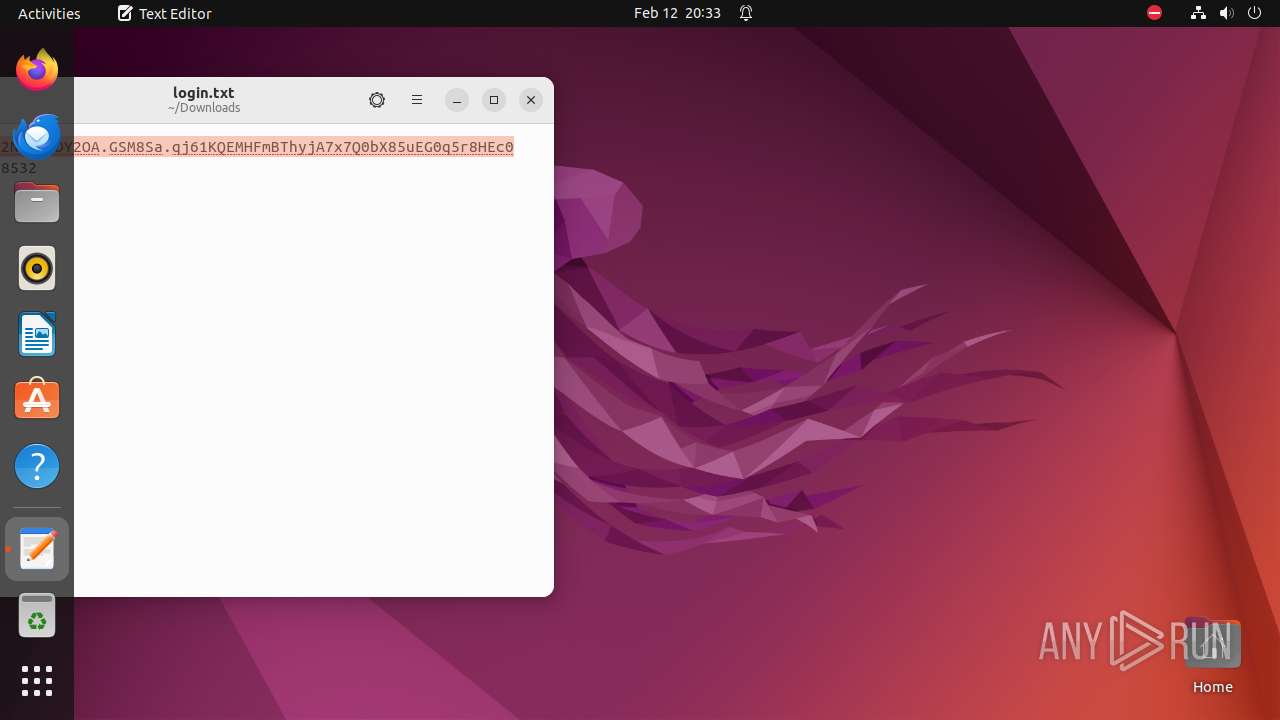
| URL: | https://github.com/moom825/Discord-RAT-2.0/releases/download/2.0/release.zip%20https://www.mediafire.com/file/a8izanklq8o9h18/login.txt/file |
| Full analysis: | https://app.any.run/tasks/5b34bb0b-0b5a-4366-94ea-f49561ee777f |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2024, 20:30:48 |
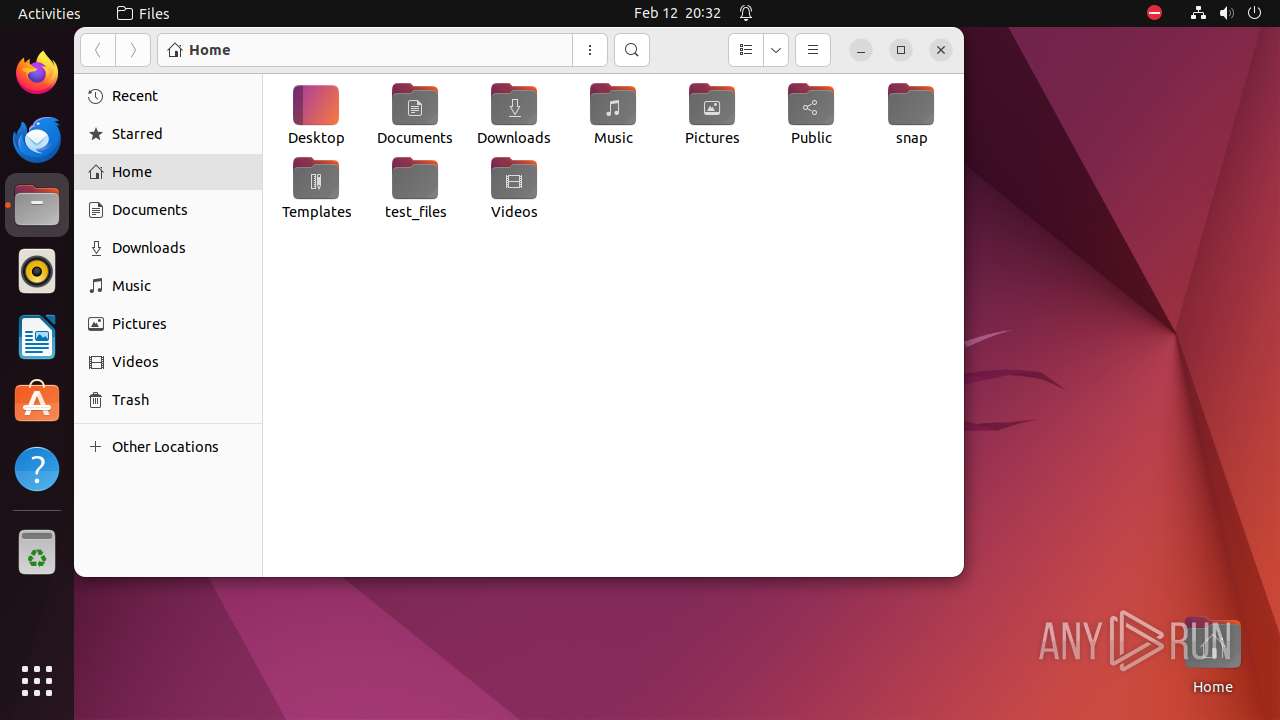
| OS: | Ubuntu 22.04.2 |
| MD5: | 1554F3FC3022F454F25987B446EDB8ED |
| SHA1: | 0BB587C15203B0AC6ABEF16200AC7A2F99BC45EB |
| SHA256: | 45B9F650E5549C114B7DA4DD14F37397B85090A6ED0F6EACA4FB2ABCA12A2025 |
| SSDEEP: | 3:N8tEd4u3MWOBJMkCXcQJRfMsnMDSLw3eGUo0MfELtNEKrKHRA:2uuASKCQ0POLw3eGYei/KHm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 8504)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
355
Monitored processes
134
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7938 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"https://github\.com/moom825/Discord-RAT-2\.0/releases/download/2\.0/release\.zip%20https://www\.mediafire\.com/file/a8izanklq8o9h18/login\.txt/file\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 7984 | ||||
| 7939 | sudo -iu user google-chrome https://github.com/moom825/Discord-RAT-2.0/releases/download/2.0/release.zip%20https://www.mediafire.com/file/a8izanklq8o9h18/login.txt/file | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 7940 | ||||
| 7940 | /usr/bin/google-chrome https://github.com/moom825/Discord-RAT-2.0/releases/download/2.0/release.zip%20https://www.mediafire.com/file/a8izanklq8o9h18/login.txt/file | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 7940 | ||||
| 7941 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7942 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7943 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7944 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7945 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 7940 | ||||
| 7946 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 7984 | ||||
| 7947 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7940 | chrome | /7940/fd/63 | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65CA7FFD-1F04.pma | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.MsptRj | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.g8T6nC | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.phP7eO | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.BwCgIc | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.etBmUp | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.UvLWaY | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /.com.google.Chrome.luKqK3 | — | |
MD5:— | SHA256:— | |||
| 7940 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
174
DNS requests
206
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ev3edpafxbygoeuy76lfg2ezli_2024.2.11.1/jflhchccmppkfebkiaminageehmchikm_2024.02.11.01_all_addz6wke6z5tl2vogzlsabpxd73a.crx3 | unknown | binary | 7.65 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/efniojlnjndmcbiieegkicadnoecjjef/1.9324e37832b4647cfe6dd5c305addbd1aebad06a25acf8cab9423efe9424cbf2/1.6fcc02a365d39485c49c9da8679a9fd979832315b2d47ff7f0ab395b10e303bd/04aec90660ca209151b66b2ff3d7c7e7c402fe8f78436469699d5e4971bf74d6.puff | unknown | binary | 11.3 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gonpemdgkjcecdgbnaabipppbmgfggbe/1.06e71f675912f15e683ea65e2a1ec902ff07d67953b8dbf4542f93baf98a29bc/1.48fecfa3c6f59eb6c34fdd5e8f19e0678699e2f27dc8ebfa7025c246d4575c68/c67e12b46a2316837ac3d7cc7035823f1e378f081e47b11a14890378f9808c6f.puff | unknown | binary | 2.60 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac4f3somx23o64dmkbjhcjiarbaa_2024.2.7.0/niikhdgajlphfehepabhhblakbdgeefj_2024.02.07.00_all_aday4y2elpq75abbq5dcch3j5mra.crx3 | unknown | binary | 5.61 Kb | unknown |
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/addz6q6bz6tk3vsstidrivmno3xq_8543/hfnkpimlhhgieaddgfemjhofmfblmnib_8543_all_acqfgv64tayldgynuci62usitjzq.crx3 | unknown | binary | 26.4 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.363351f0d0ca05b48f43d4adac95ad01d955bb2988c015733e70e09625d47065/1.ab8da5b849ba36382f26992fe1b52d72aa457549f31246a0c386d6880fca8afc/7d154c7442d14a8b229549ff84d2ee16f1b087332b3d00cd990023f1966e5935.puff | unknown | binary | 40.3 Kb | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/1.d714e27bbcdedab3f9f9ca92462ee6dc8ca779849aefdd27af92009a9d55a38f/1.1c9ef13b7a63abd8f89d0cbad98858b9e8f54fc3951160950403c72b45812d07/7c4973aa28b0c59d92cc9ebf075fcdccab6008b049c66388f079107ba6184551.puff | unknown | binary | 2.28 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 91.189.91.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
— | — | 195.181.175.41:443 | — | Datacamp Limited | DE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 142.250.184.227:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
— | — | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
github.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
s3-w.us-east-1.amazonaws.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
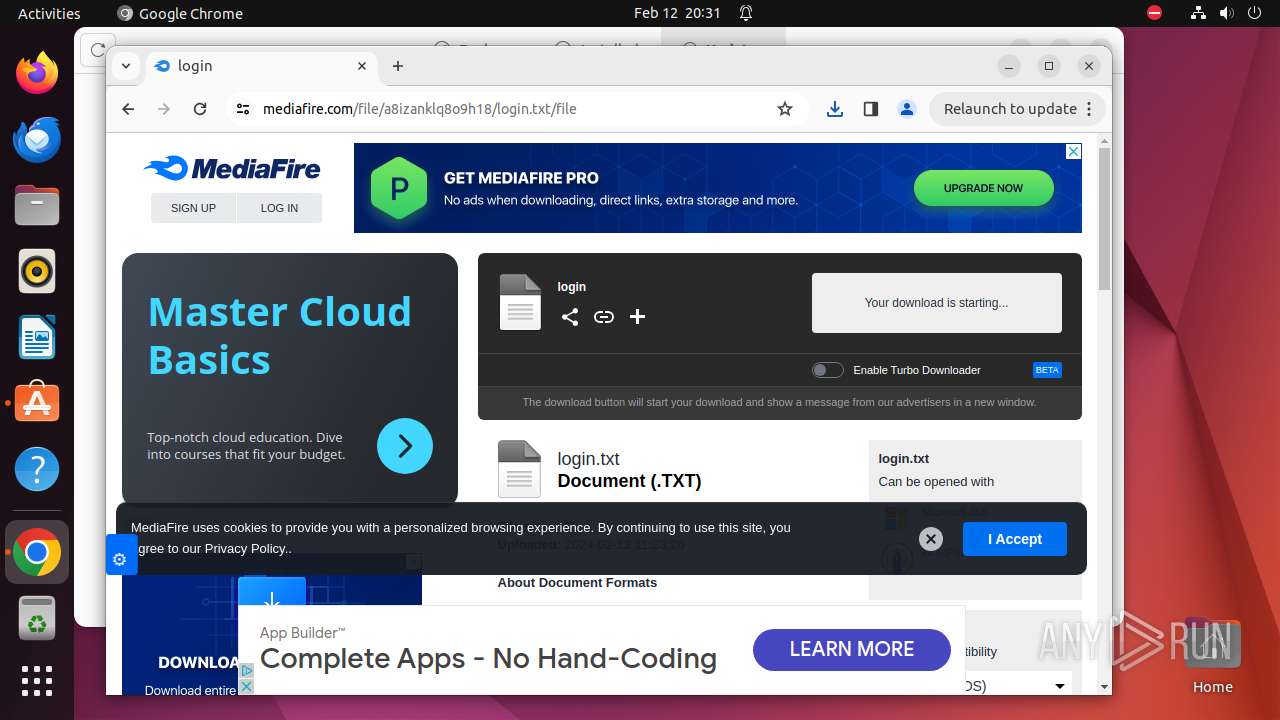
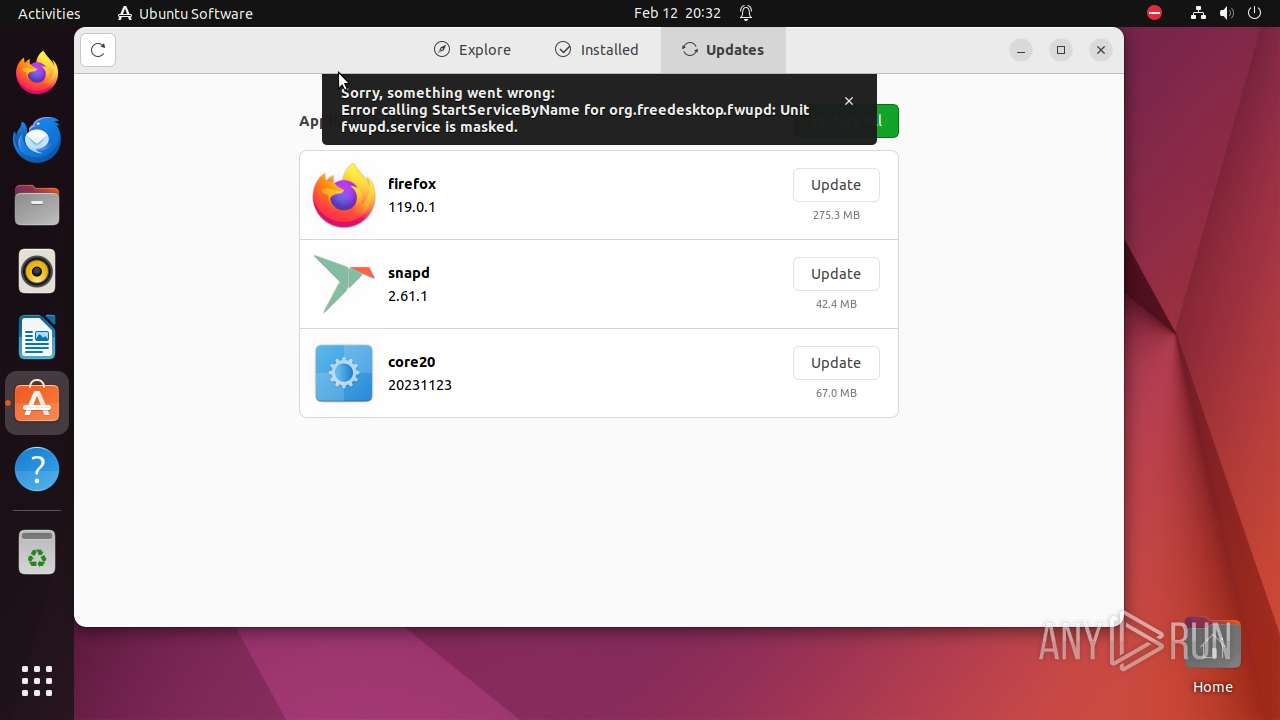
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |