| File name: | javapolicy.exe |
| Full analysis: | https://app.any.run/tasks/0c48b03a-717f-4fbb-80c7-467ea453ca4a |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2019, 19:35:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D1C0384374E1AEDBFD59ADB5BF9EC8EF |
| SHA1: | 1FED5879AB2B6B5BF018A6F5FC29DA1A3789ED85 |
| SHA256: | 45AB98266E828D2E8625F095D61800086EE5FAB577E54FACBF8DD843FBF8591E |
| SSDEEP: | 1536:6CsUGH3oIsW7HknHJC5+DSnwFvmmjsgjMA6YM7iaPAEa8YjM5FIMH3kA:6ZtXoIXHUJCtnw8mQg8Ga8LgvIMXT |
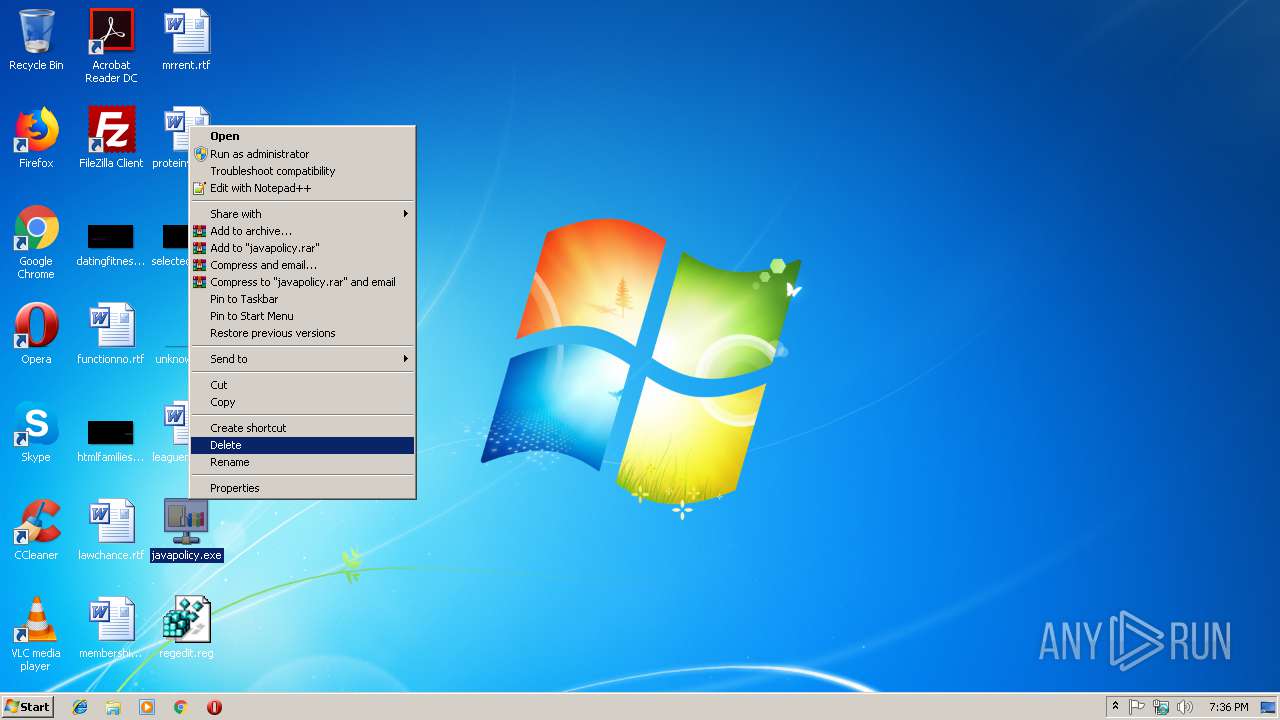
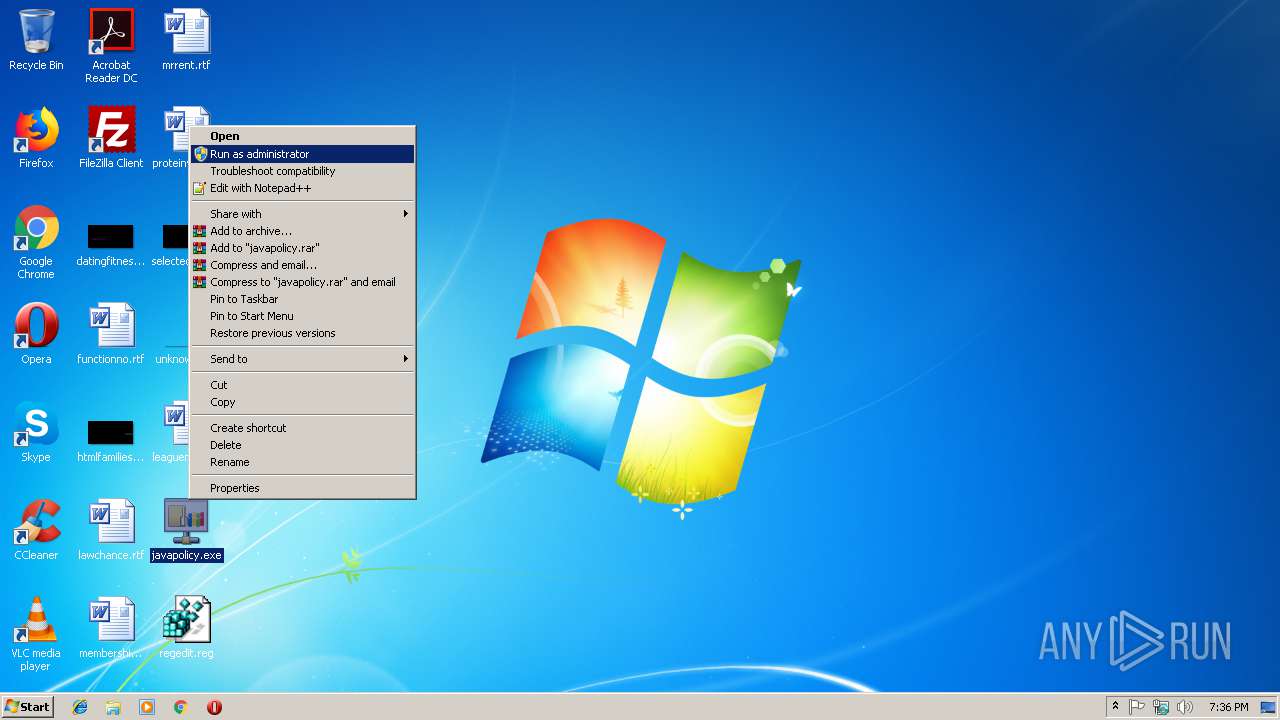
MALICIOUS
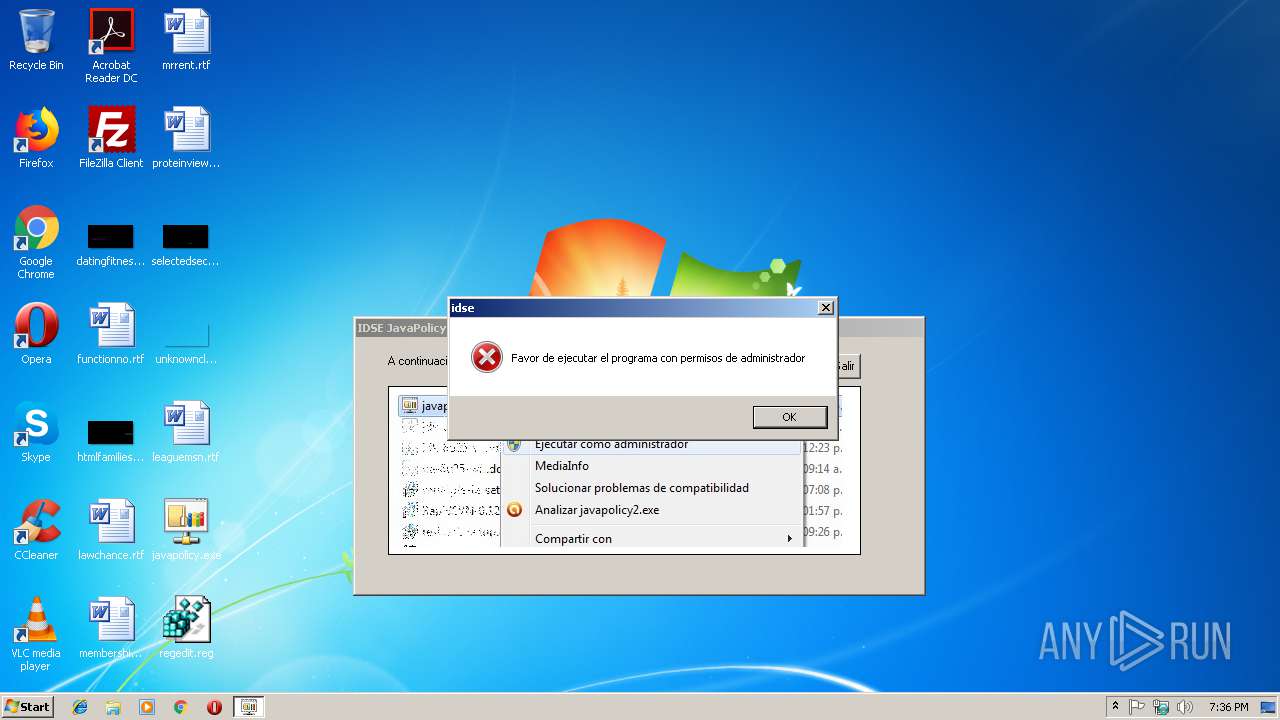
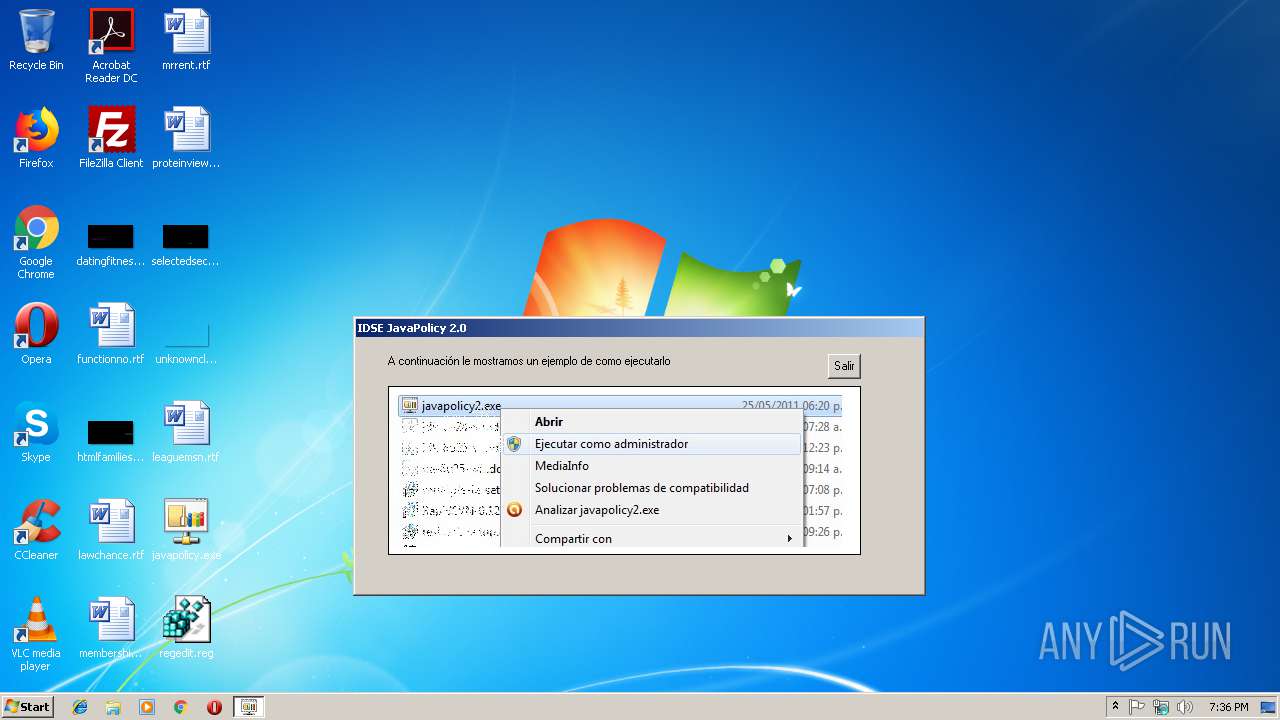
Actions looks like stealing of personal data
- javapolicy.exe (PID: 3316)
SUSPICIOUS
Creates files in the program directory
- javapolicy.exe (PID: 3316)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:06:02 20:44:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 98304 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1858 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
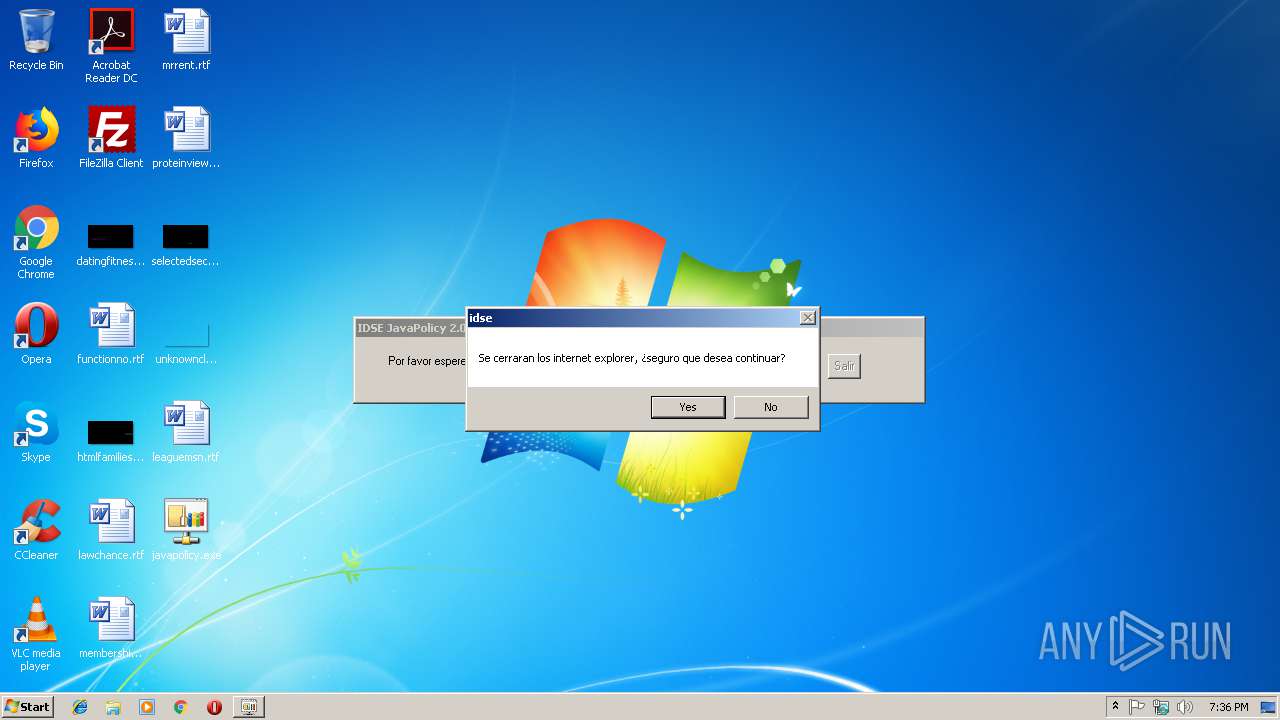
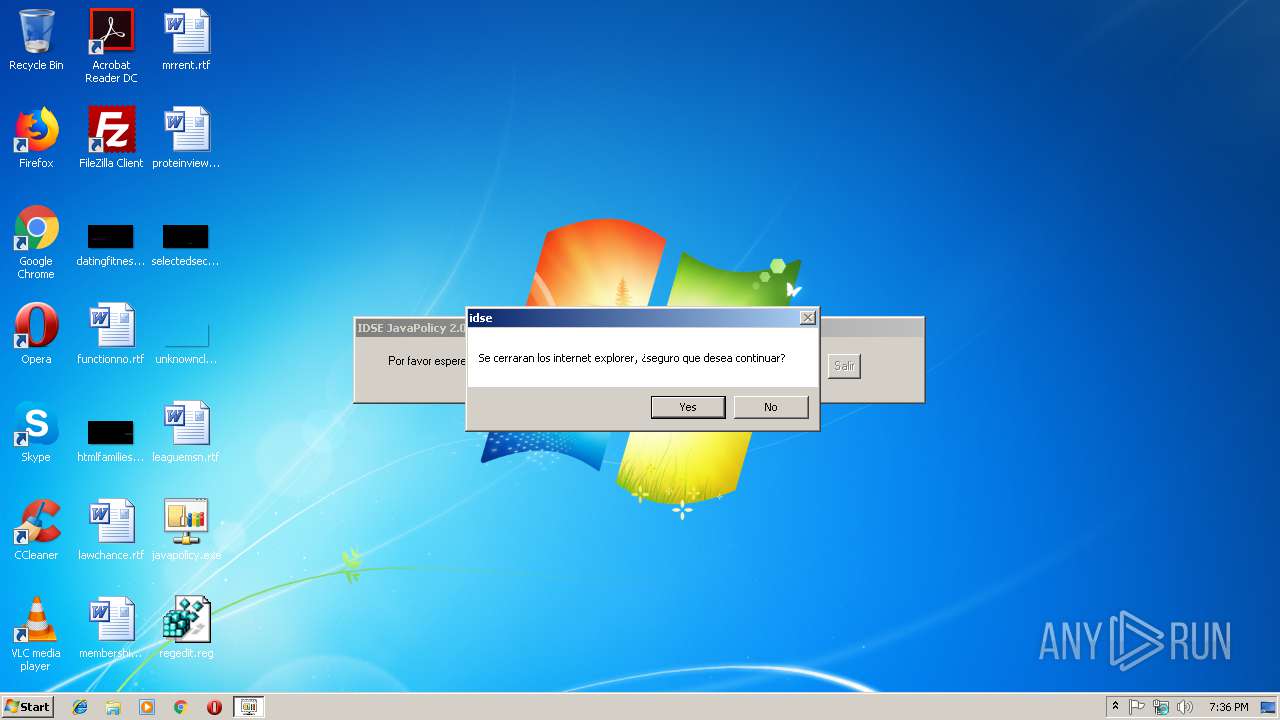
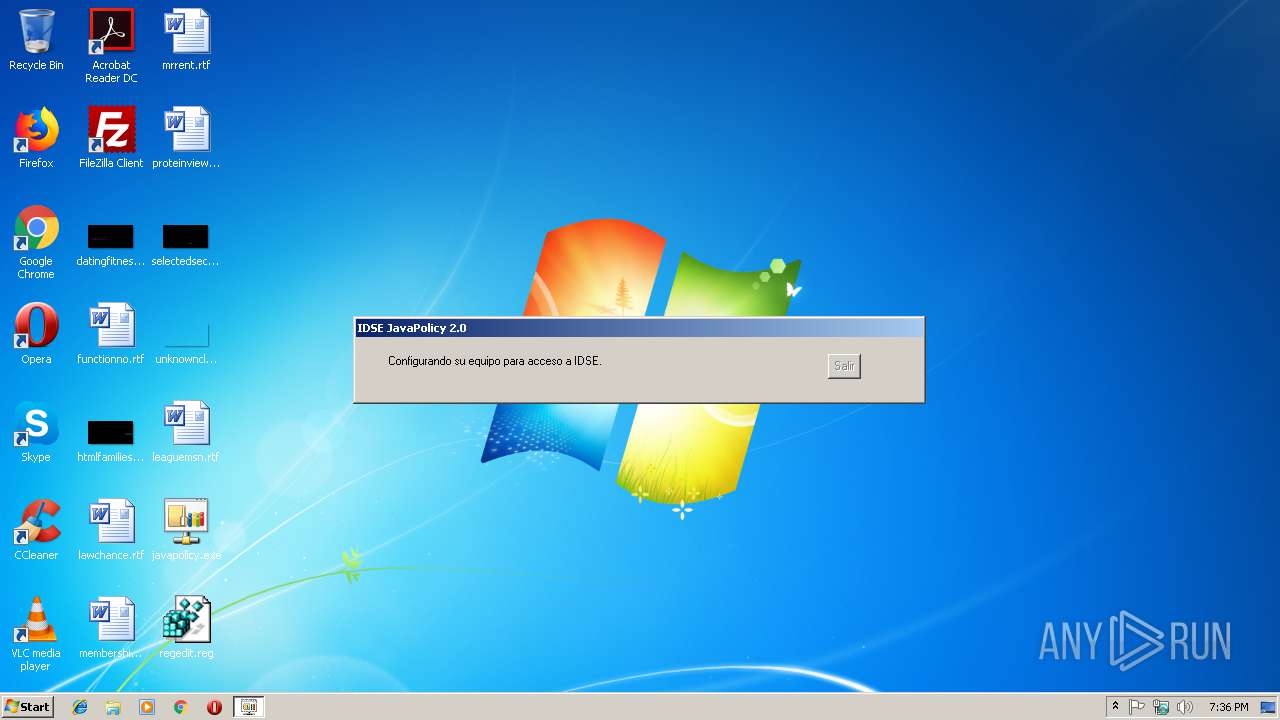
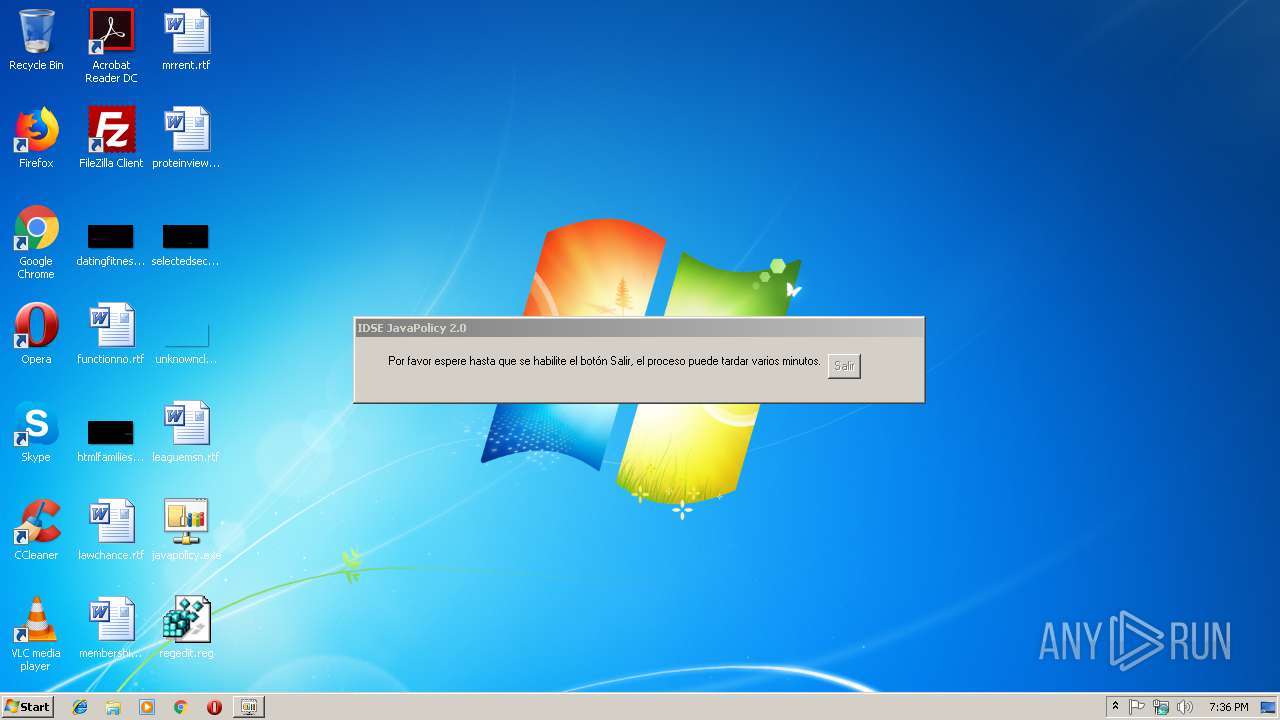
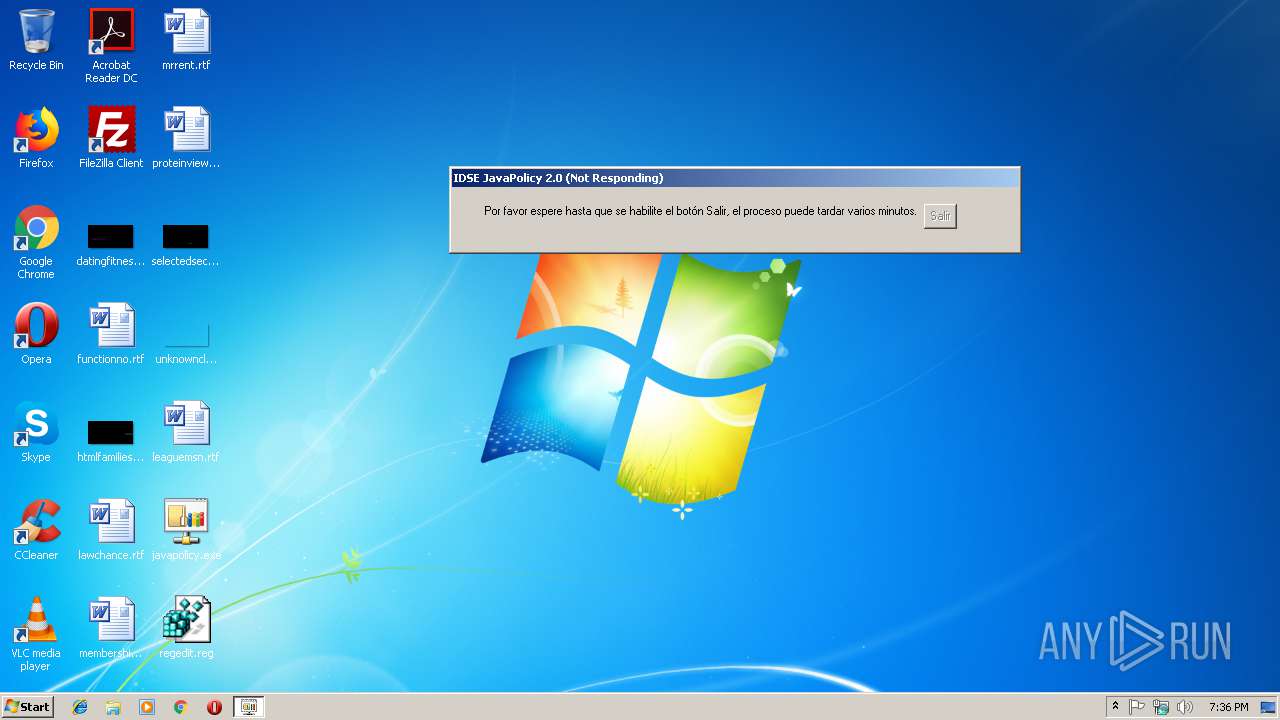
| ProductName: | idse |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | javapolicy |
| OriginalFileName: | javapolicy.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Jun-2011 18:44:54 |
| Detected languages: |
|
| ProductName: | idse |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | javapolicy |
| OriginalFilename: | javapolicy.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Jun-2011 18:44:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00017E44 | 0x00018000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.79936 |
.data | 0x00019000 | 0x00000AF8 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0001A000 | 0x000066C0 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00076 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.11688 | 484 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.76835 | 1640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 3.7926 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 3.21416 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30004 | 5.53404 | 3752 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30005 | 5.64781 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30006 | 2.55471 | 1384 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30007 | 4.93581 | 9640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30008 | 5.12189 | 4264 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30009 | 4.77859 | 1128 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2716 | regedit /s "C:\Users\admin\Desktop\regedit.reg" | C:\Windows\regedit.exe | — | javapolicy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\Desktop\javapolicy.exe" | C:\Users\admin\Desktop\javapolicy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3316 | "C:\Users\admin\Desktop\javapolicy.exe" | C:\Users\admin\Desktop\javapolicy.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 4088 | regedit /s "C:\Users\admin\Desktop\regedit.reg" | C:\Windows\regedit.exe | — | javapolicy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
14
Read events
12
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2716) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (2716) regedit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\gob.mx\*.imss |
| Operation: | write | Name: | http |
Value: 2 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | javapolicy.exe | C:\Users\admin\AppData\Local\Temp\~DF08E0435C2296532F.TMP | — | |
MD5:— | SHA256:— | |||
| 3144 | javapolicy.exe | C:\Users\admin\Desktop\regedit.reg | text | |
MD5:695E5BCDEC5E778FE17667C5898A4D34 | SHA256:DDF7FC8A8BE7EC52A4B72EAC624859A604B30AB94D02B5BDE93B6BCFEEDC1A09 | |||
| 3316 | javapolicy.exe | C:\Program Files\Java\jre1.8.0_92\lib\security\java.policy.2019030770588.27.bak | text | |
MD5:11340CD598A8517A0FD315A319716A08 | SHA256:B8582889B0DF36065093C642ED0F9FA2A94CC0DC6FDE366980CFD818EC957250 | |||
| 3316 | javapolicy.exe | C:\Users\admin\Desktop\regedit.reg | text | |
MD5:695E5BCDEC5E778FE17667C5898A4D34 | SHA256:DDF7FC8A8BE7EC52A4B72EAC624859A604B30AB94D02B5BDE93B6BCFEEDC1A09 | |||
| 3316 | javapolicy.exe | C:\Program Files\Java\jre1.8.0_92\lib\security\java.policy | text | |
MD5:CE7F5EF7FFA6DB930CCFC6CA0A817AE3 | SHA256:B5C5583D5412A24519F6CC2E9982E7B866027EFA5BF0DE474EE52EFD572E0D07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report