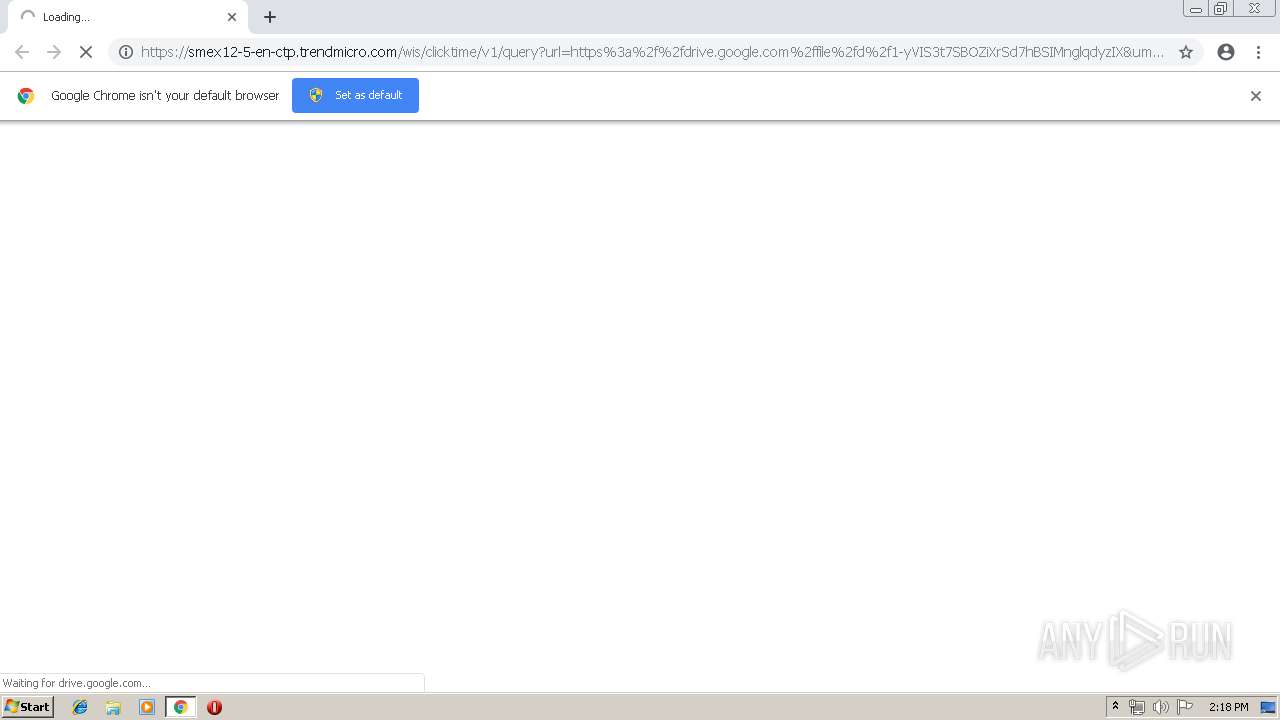
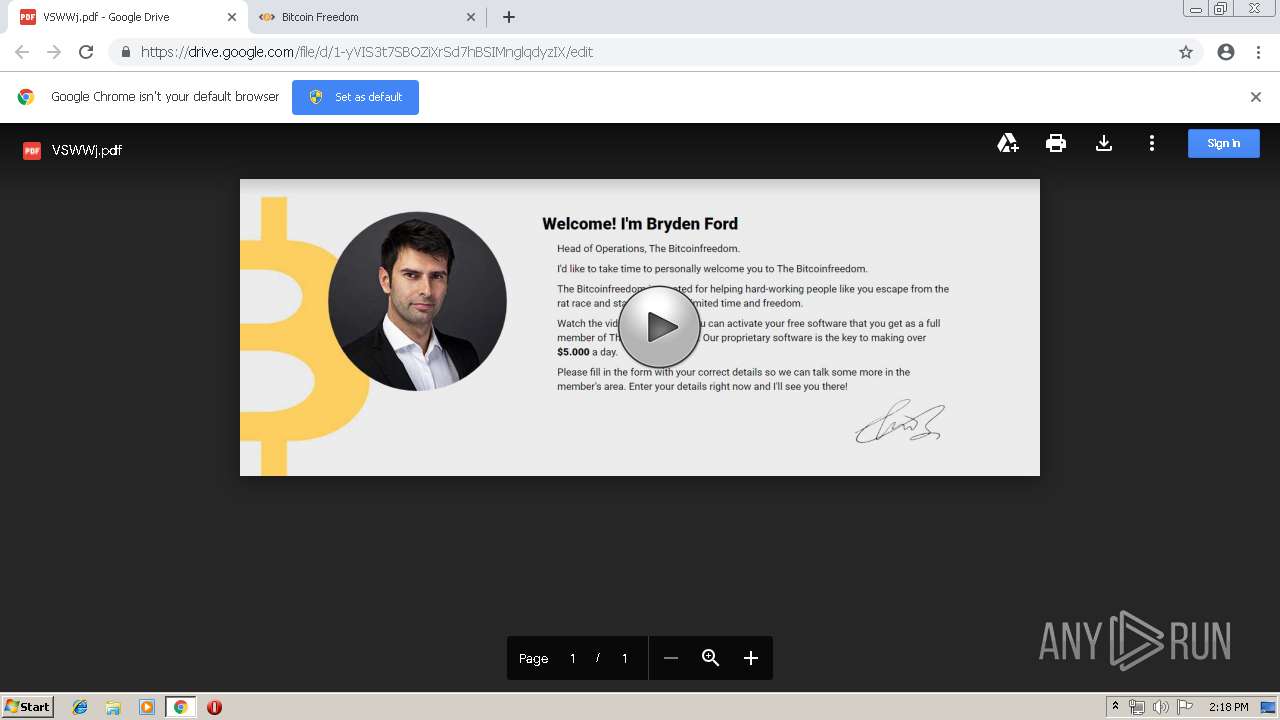
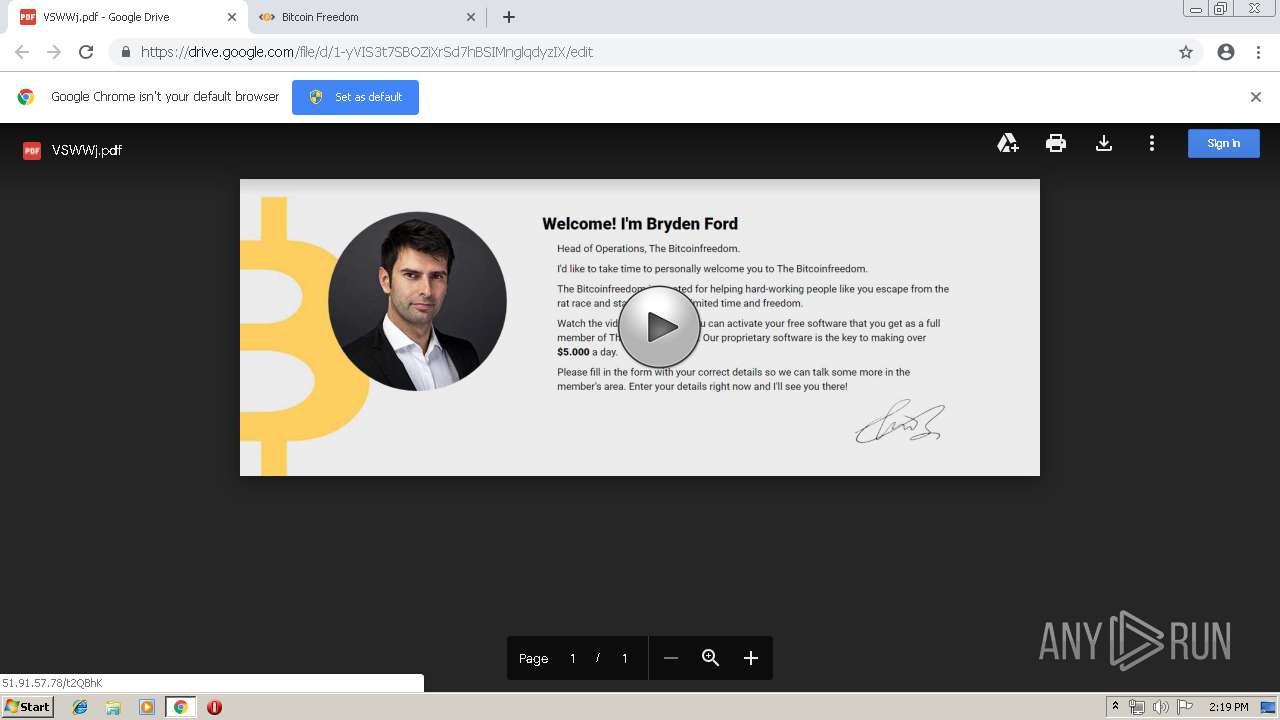
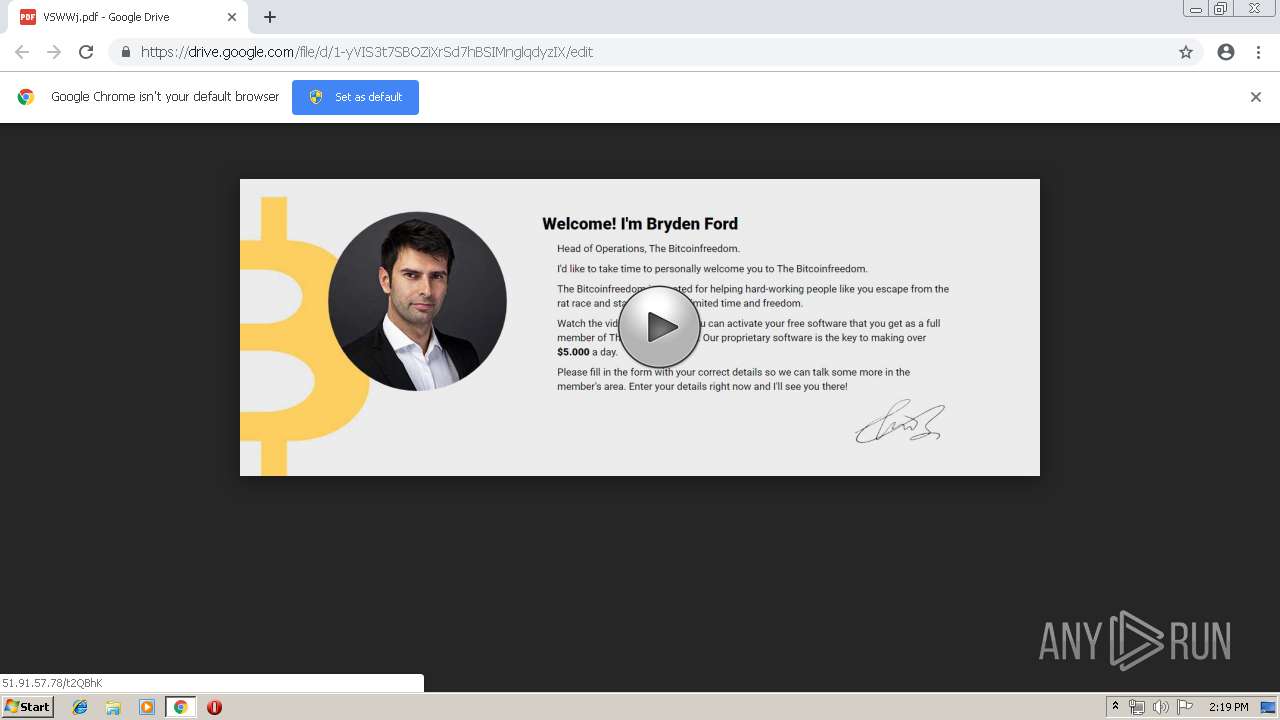
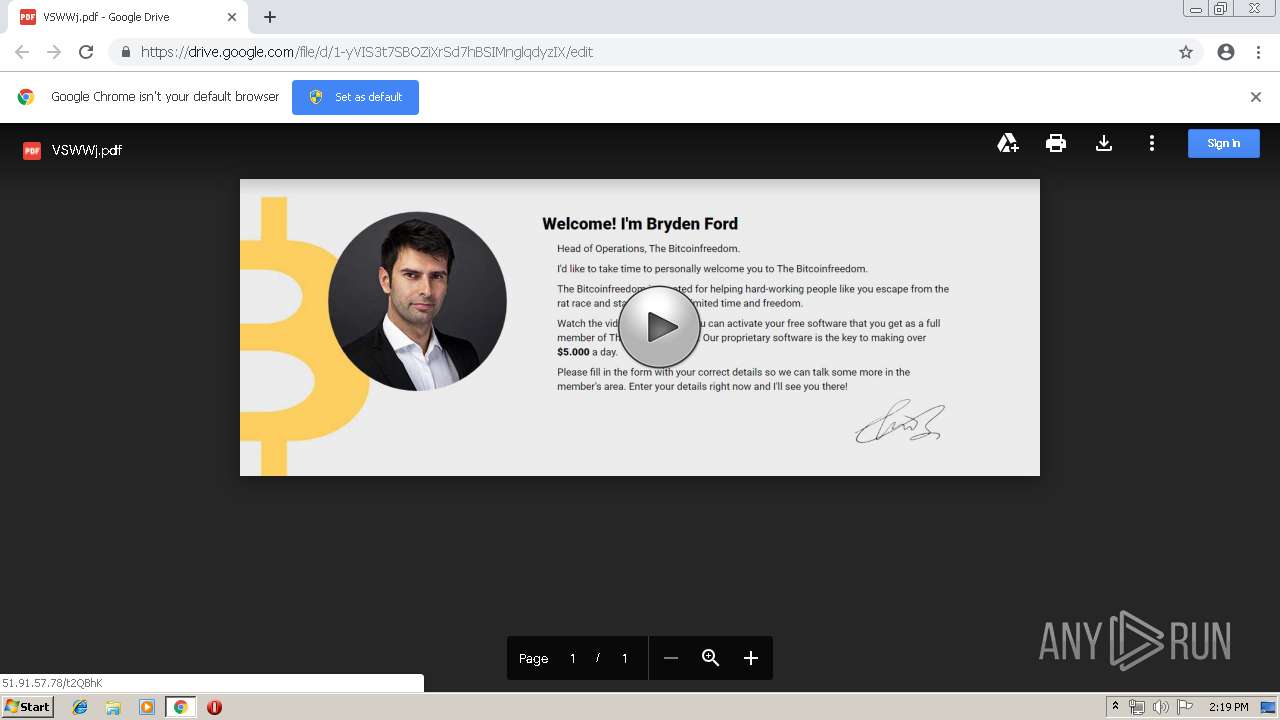
| URL: | https://smex12-5-en-ctp.trendmicro.com/wis/clicktime/v1/query?url=https%3a%2f%2fdrive.google.com%2ffile%2fd%2f1%2dyVIS3t7SBOZiXrSd7hBSIMnglqdyzIX&umid=4a545049-b034-4d11-8220-2e0a86108834&auth=6a5c03d6fef9a99a2201a70979af732a0a6d5ebb-aebf332ef70eee9e9c5f2a0a4933b5b390716ff6 |
| Full analysis: | https://app.any.run/tasks/8332a1bd-912b-444f-9759-a494c4255324 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 13:18:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 69C8DC0998D527942955FB3DD4C56118 |
| SHA1: | 08346A2C1723CFFE757712861CD308AA558C3A5B |
| SHA256: | 45AAED46E9BC8DA598CACFBCFDFB257B3DC97690975C93AAD6B58FDB1603564E |
| SSDEEP: | 6:2zibKMZsdnGMTBjcoqkBbaskXiVEASINHcAEoLPlyAj+h07T:2ziDKGMN4rk0skXQSINcox7T |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3392)
INFO
Application launched itself
- chrome.exe (PID: 3392)
Creates files in the user directory
- chrome.exe (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13735516597398512855 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13735516597398512855 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16693529552238319585 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16693529552238319585 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5440004613124697601 --mojo-platform-channel-handle=5328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=744312224226239905 --mojo-platform-channel-handle=5704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6459706936079101654 --mojo-platform-channel-handle=5204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16681152473493934808 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16681152473493934808 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13757712096839986545 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11488560162387774047 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11488560162387774047 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9216223043595848091 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9216223043595848091 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,17188909726604746557,11164848659531028005,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1289531059631958367 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1289531059631958367 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
592
Read events
488
Write events
99
Delete events
5
Modification events
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3392-13205423927450125 |
Value: 259 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
143
Text files
191
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\056370cd-be7c-415d-add7-bee206944222.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
88
TCP/UDP connections
75
DNS requests
41
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
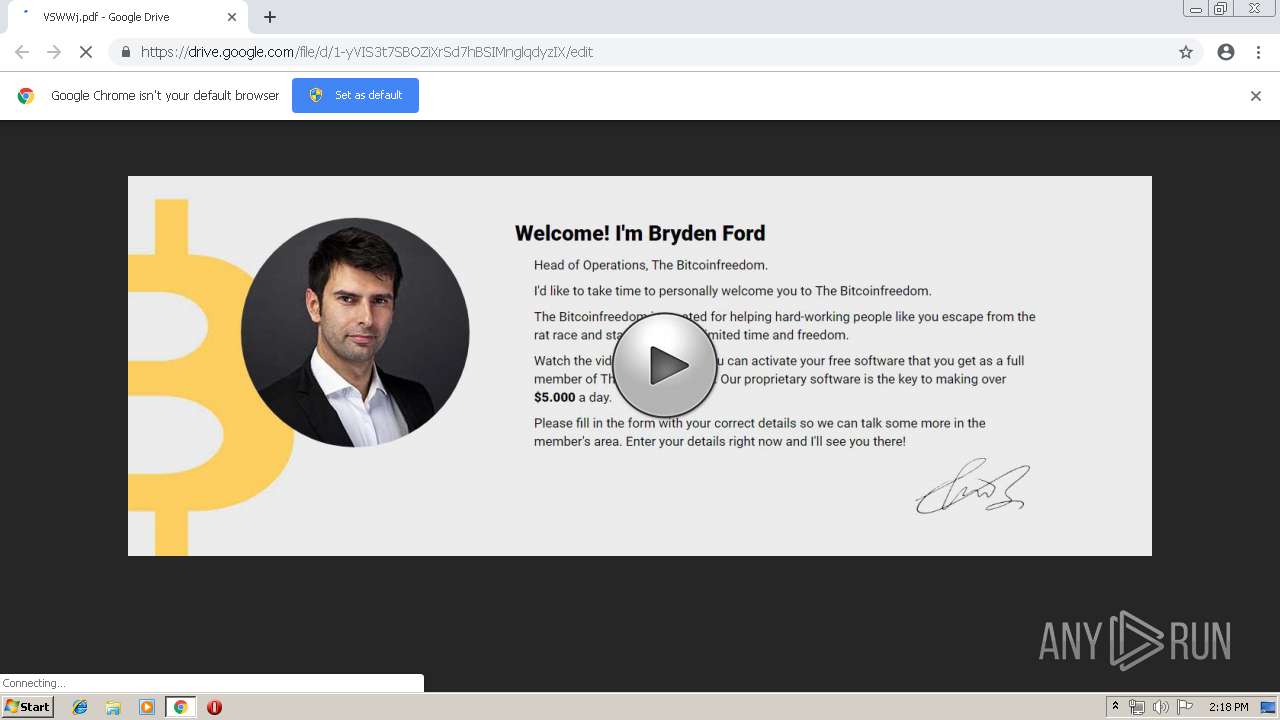
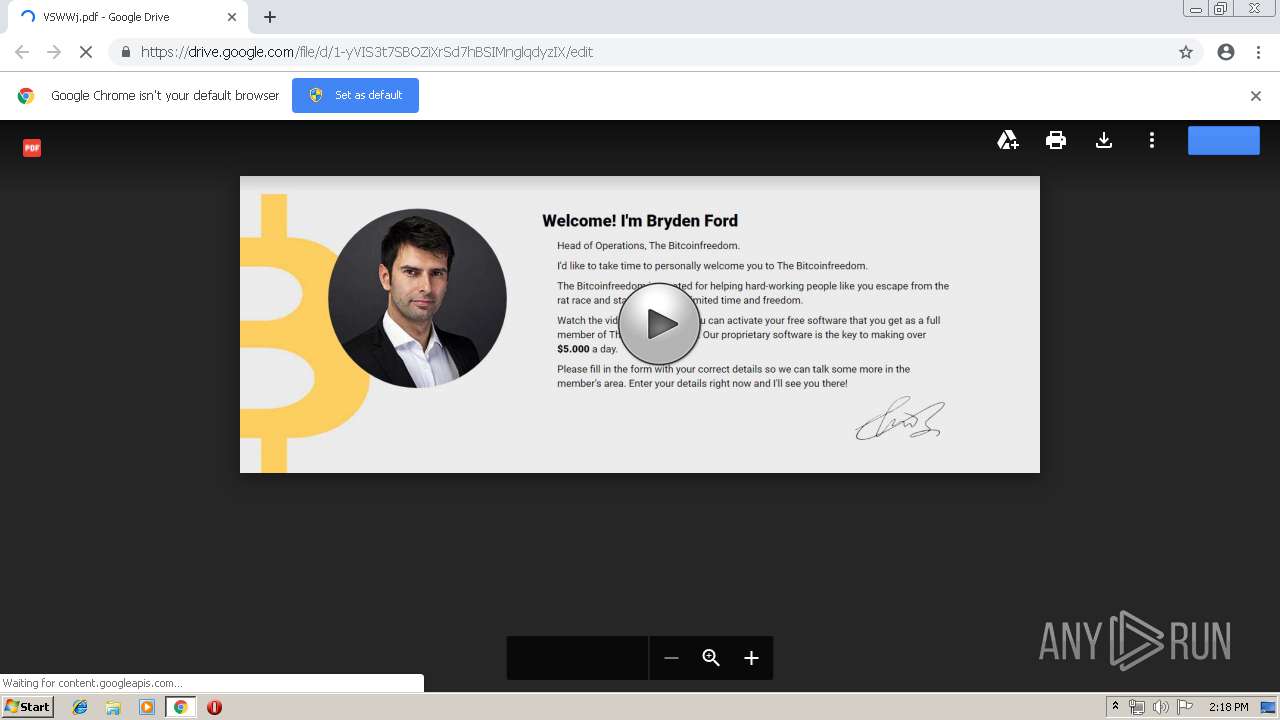
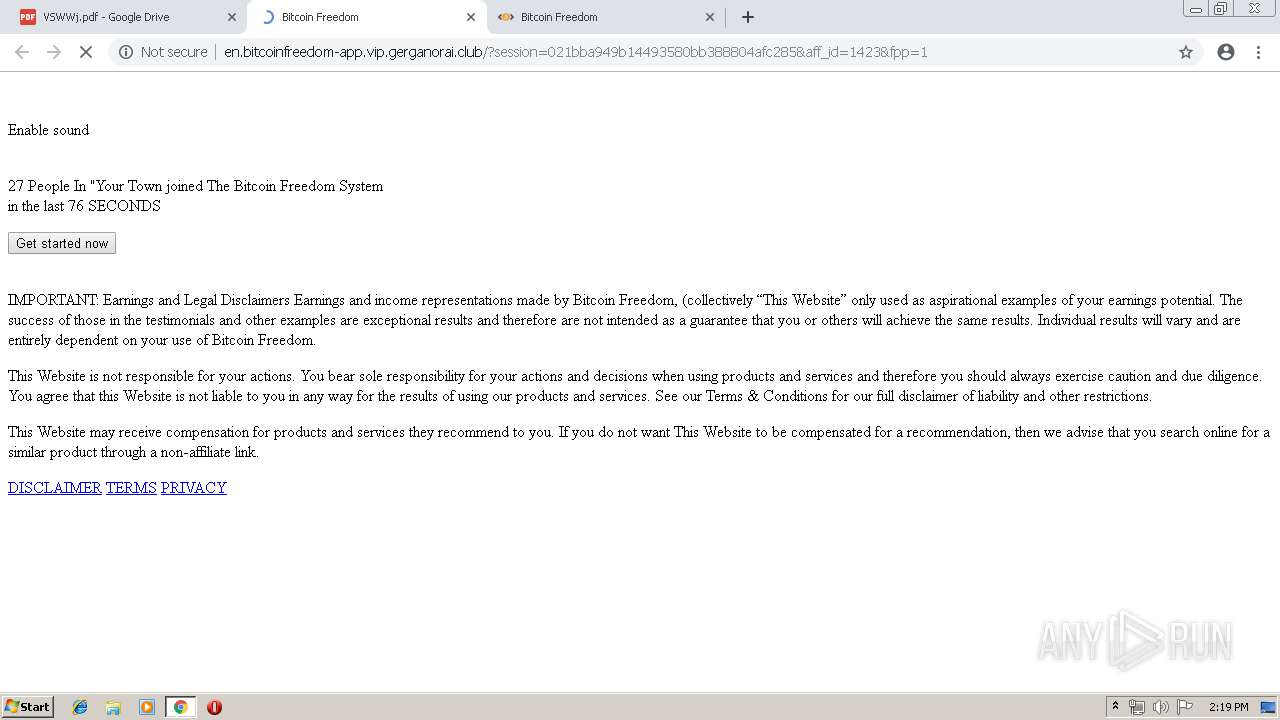
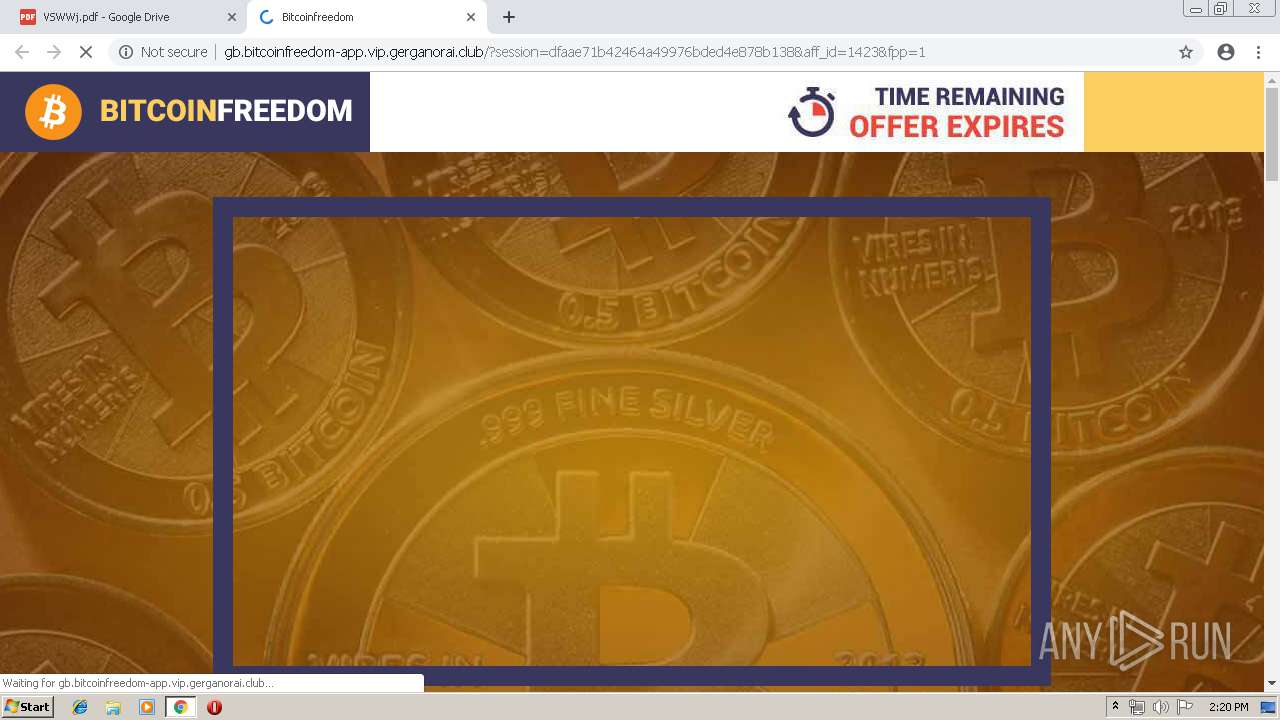
3392 | chrome.exe | GET | 302 | 104.18.49.221:80 | http://vip.gerganorai.club/tracker?offer_id=3441&aff_id=1423&u=0:50,1140:50&gl=off | US | — | — | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/img/logoText.png | US | image | 8.09 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/css/style_pop_up.css | US | text | 979 b | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/css/font-awesome.css | US | text | 5.60 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/css/css1.css | US | text | 5.89 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/img/securStripe.png | US | image | 19.9 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/?session=a7b10fd392714beaa2182260ff8a014e&aff_id=1423&fpp=1 | US | html | 3.78 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/css/include_fonts.css | US | text | 105 b | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/img/volume.png | US | image | 6.10 Kb | suspicious |
3392 | chrome.exe | GET | 200 | 104.18.48.221:80 | http://en.bitcoinfreedom-app.vip.gerganorai.club/js/watch.js | US | text | 29.5 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 34.213.201.171:443 | smex12-5-en-ctp.trendmicro.com | Amazon.com, Inc. | US | unknown |
3392 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 173.194.76.194:443 | drive.google.com | Google Inc. | US | unknown |
3392 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 172.217.23.138:443 | content.googleapis.com | Google Inc. | US | whitelisted |
3392 | chrome.exe | 51.91.57.78:80 | — | — | GB | unknown |
3392 | chrome.exe | 104.18.49.221:80 | vip.gerganorai.club | Cloudflare Inc | US | shared |
3392 | chrome.exe | 173.194.76.198:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
smex12-5-en-ctp.trendmicro.com |
| whitelisted |
accounts.google.com |
| shared |
drive.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
lh4.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |