| File name: | ChangeWallpaper.bat |
| Full analysis: | https://app.any.run/tasks/262677a3-7a73-4cc9-914c-6eab7e1fcf06 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 22:28:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with very long lines (539), with CRLF line terminators |
| MD5: | 2C3055301D180BC8749D1726742C3BEE |
| SHA1: | F14AD5DF0DA6E3899F36AACF006C96508BC739FF |
| SHA256: | 459F82F0495BD8943C3FC58C64F9CE5EC6D60D0D469EF82C7FAF0D7243C257B8 |
| SSDEEP: | 24:wqRk3tWW7kVtXWc8sjVqJUF9+hM9QbSvVjhiMEFnH/SZYeV+XAI9mXbNP0gAG:G3t6XhgaF9Euhi32DEQI9mXZsgAG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Imports DLL using pinvoke
- powershell.exe (PID: 5428)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 5800)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5392)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4988)
- csc.exe (PID: 4008)
Executable content was dropped or overwritten
- csc.exe (PID: 4988)
- csc.exe (PID: 4008)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5392)
INFO
Create files in a temporary directory
- cvtres.exe (PID: 1244)
- csc.exe (PID: 4988)
- csc.exe (PID: 4008)
- cvtres.exe (PID: 4120)
Reads the machine GUID from the registry
- csc.exe (PID: 4988)
- csc.exe (PID: 4008)
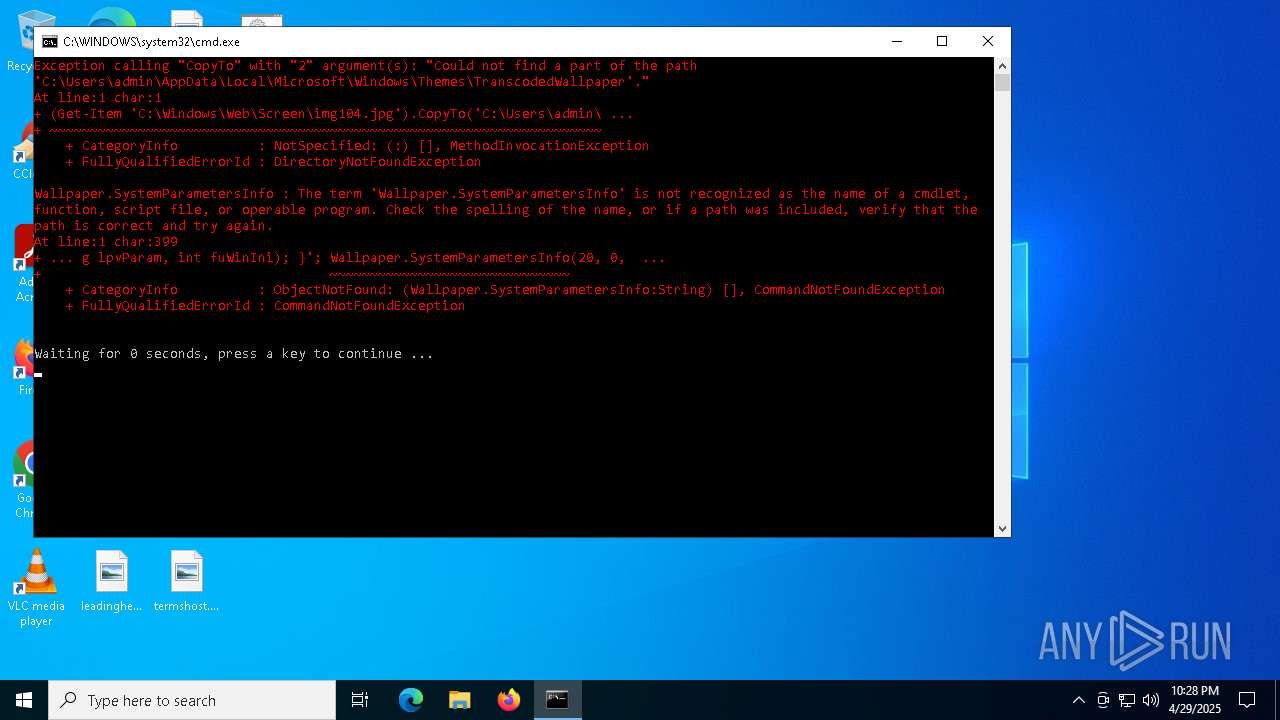
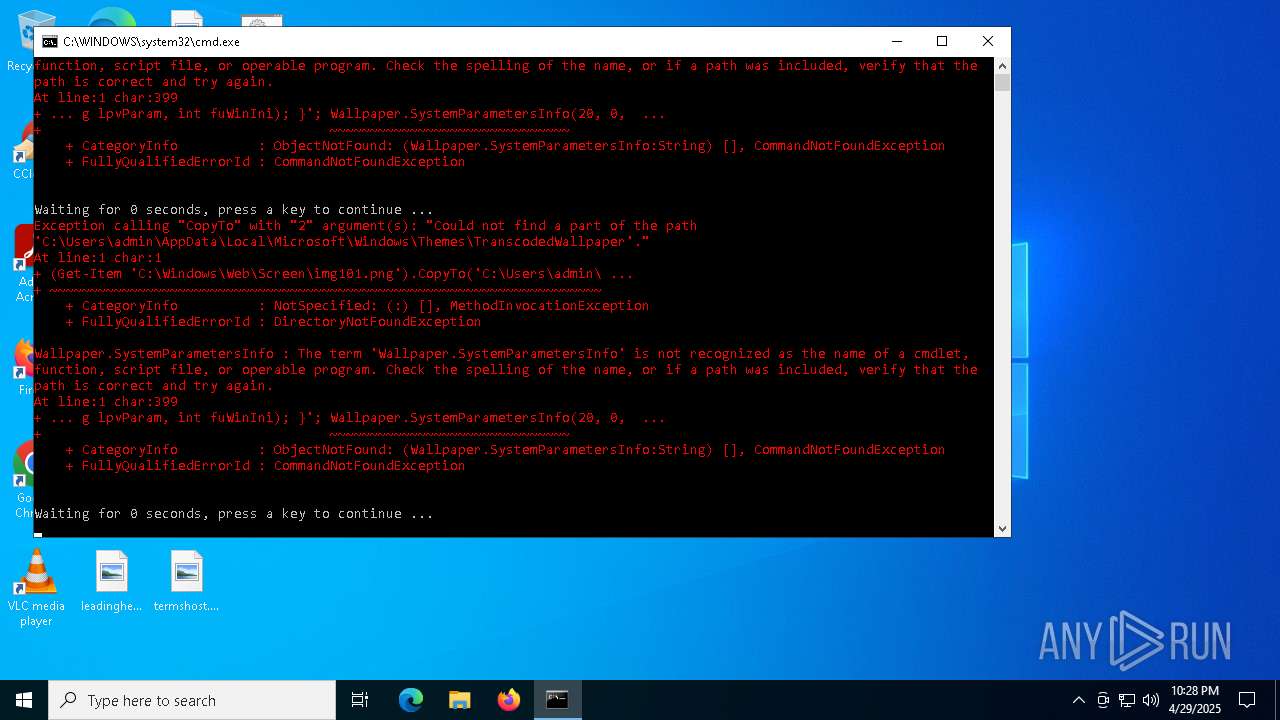
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5428)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 5800)
Checks supported languages
- csc.exe (PID: 4988)
- cvtres.exe (PID: 1244)
- csc.exe (PID: 4008)
- cvtres.exe (PID: 4120)
Reads the software policy settings
- slui.exe (PID: 6248)
Checks proxy server information
- slui.exe (PID: 6248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESCCF6.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFA5D1812216D402C8D70C8A47951A5E.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | powershell -command "(Get-Item 'C:\Windows\Web\Screen\img101.png').CopyTo('C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\TranscodedWallpaper', $true); Add-Type -TypeDefinition 'using System; using System.Runtime.InteropServices; public class Wallpaper { [DllImport(\"user32.dll\", CharSet = CharSet.Auto)] public static extern int SystemParametersInfo(int uAction, int uParam, string lpvParam, int fuWinIni); }'; Wallpaper.SystemParametersInfo(20, 0, 'C:\\Users\\admin\\AppData\\Local\\Microsoft\\Windows\\Themes\\TranscodedWallpaper', 3)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | timeout /t 0 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\keeqy5ta.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4120 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESDB1F.tmp" "c:\Users\admin\AppData\Local\Temp\CSC8EEDB06E117F4F4DAA4A1BA12A772F44.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4988 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\tkorm2rd.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5392 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\ChangeWallpaper.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | timeout /t 0 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5428 | powershell -command "(Get-Item 'C:\Windows\Web\Screen\img104.jpg').CopyTo('C:\Users\admin\AppData\Local\Microsoft\Windows\Themes\TranscodedWallpaper', $true); Add-Type -TypeDefinition 'using System; using System.Runtime.InteropServices; public class Wallpaper { [DllImport(\"user32.dll\", CharSet = CharSet.Auto)] public static extern int SystemParametersInfo(int uAction, int uParam, string lpvParam, int fuWinIni); }'; Wallpaper.SystemParametersInfo(20, 0, 'C:\\Users\\admin\\AppData\\Local\\Microsoft\\Windows\\Themes\\TranscodedWallpaper', 3)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
20 175
Read events
20 175
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
5
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tkorm2rd.cmdline | text | |
MD5:2A71B91DB13DDB12A4D2EDE42CE995E7 | SHA256:C0393303A9806579EFAD2E2004EE6A4DFEC8A79E24766A41EFE9594D7279B28E | |||
| 5428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r0oe5re4.m2r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hw0bnkpc.jpy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4988 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCFA5D1812216D402C8D70C8A47951A5E.TMP | binary | |
MD5:C9C0BEA9F5BD9254053BD65443239B68 | SHA256:6C0486A3B6E66D68809E1E90C40DE2AAE530DC74A110710029C83951E5D70FA9 | |||
| 5428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tkorm2rd.0.cs | text | |
MD5:B5BC6F9136DCE704041D49AEBB0B4FA1 | SHA256:D17A04B258A3F4D6C07A25E77CA59C310F7030062ECEEC328EEA1F0D2047F024 | |||
| 1764 | powershell.exe | C:\Users\admin\AppData\Local\Temp\keeqy5ta.cmdline | text | |
MD5:2D414D010D12C5BB1EB9B84387D3421E | SHA256:5E1015C227B3A9D911F9BFAC53662B21DA398589EA5F97A6133BDF080B3758A7 | |||
| 4988 | csc.exe | C:\Users\admin\AppData\Local\Temp\tkorm2rd.out | text | |
MD5:252DFBFDA11633E85BBD805BC2627BB2 | SHA256:7D6A02E6B84E5F8217FA46E9FC54083541C38ED854A1D66D5852AF9FD56E791D | |||
| 1764 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dezvo33l.ttt.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1764 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2f4eeubj.5bi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1x2qja0i.wrx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
22
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6708 | RUXIMICS.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6708 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6708 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6708 | RUXIMICS.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6708 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6048 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6248 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |