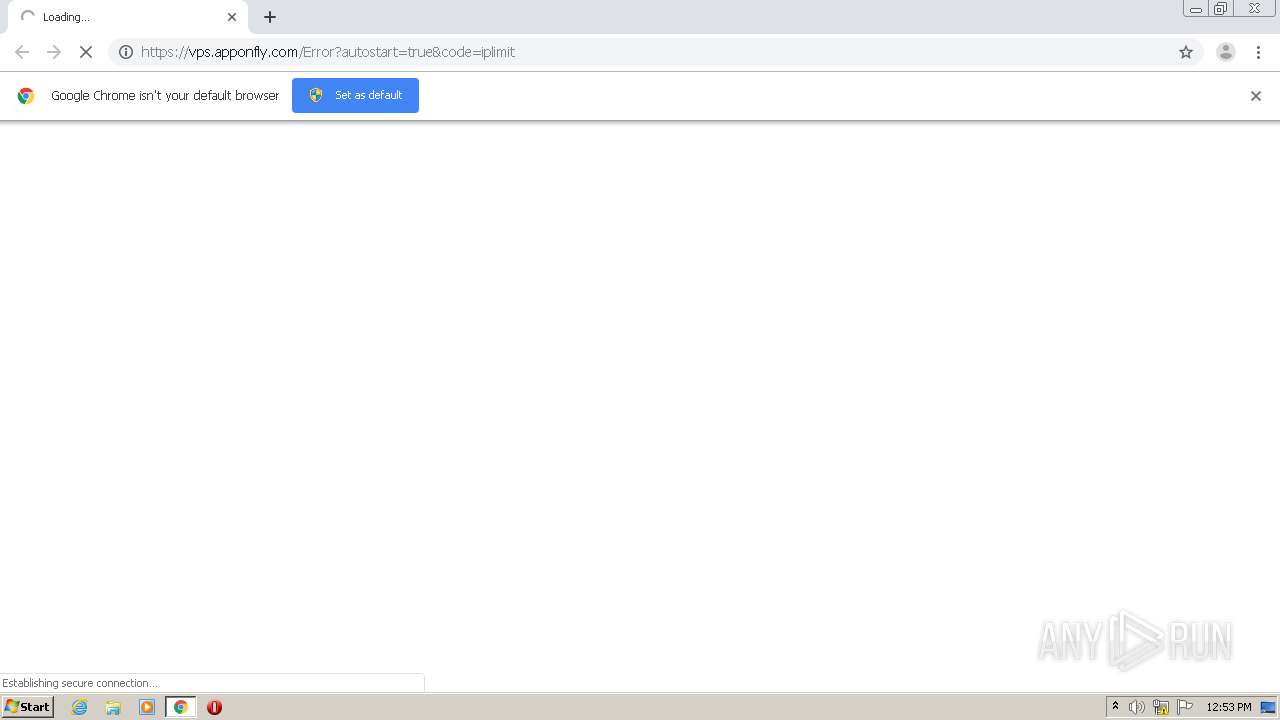
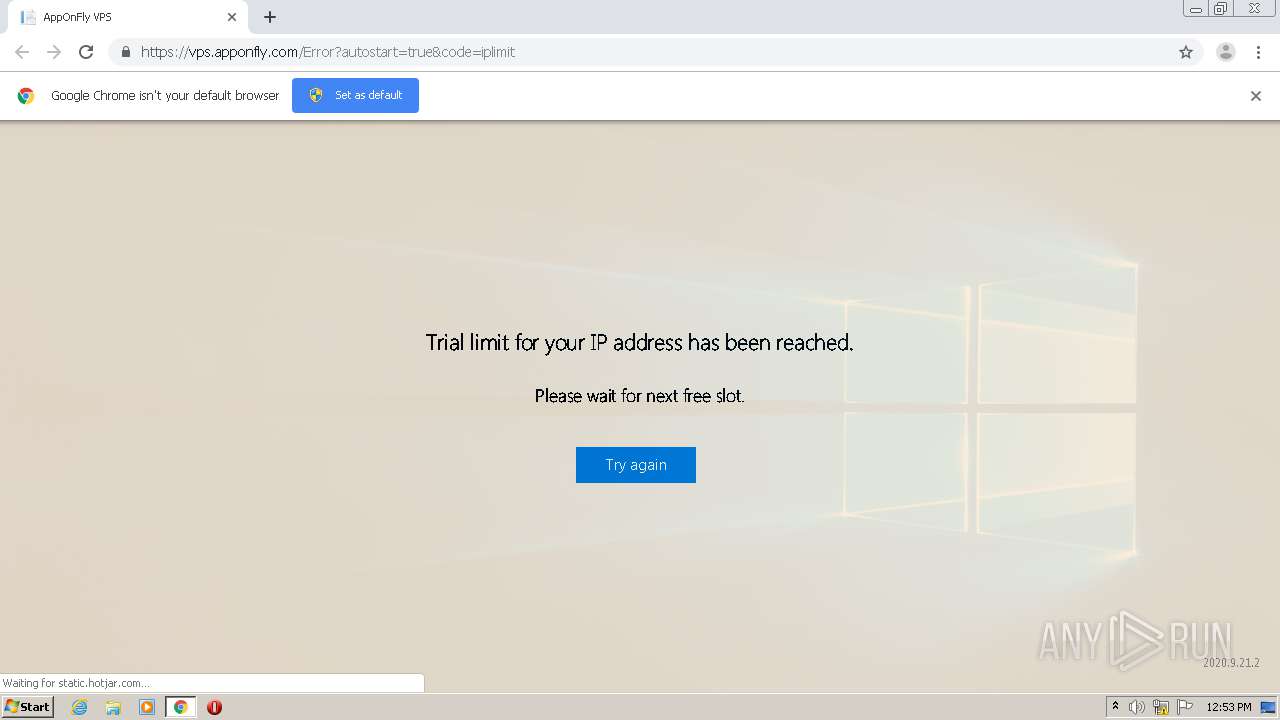
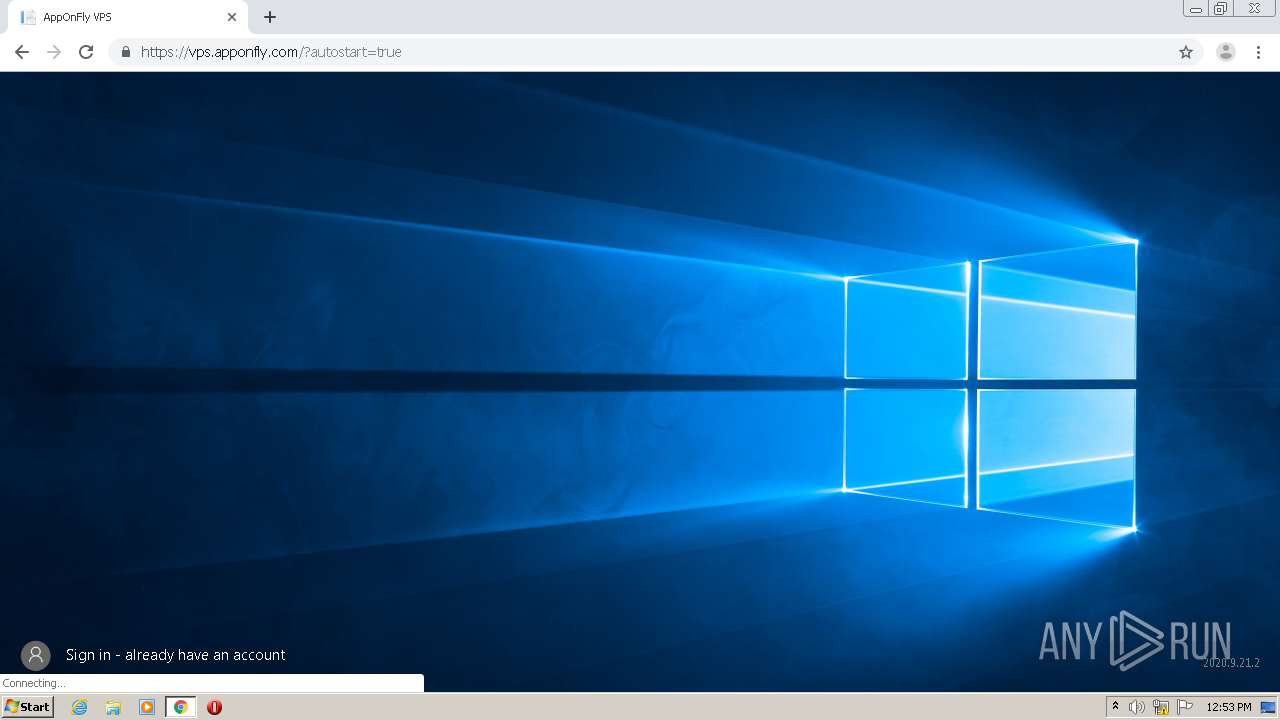
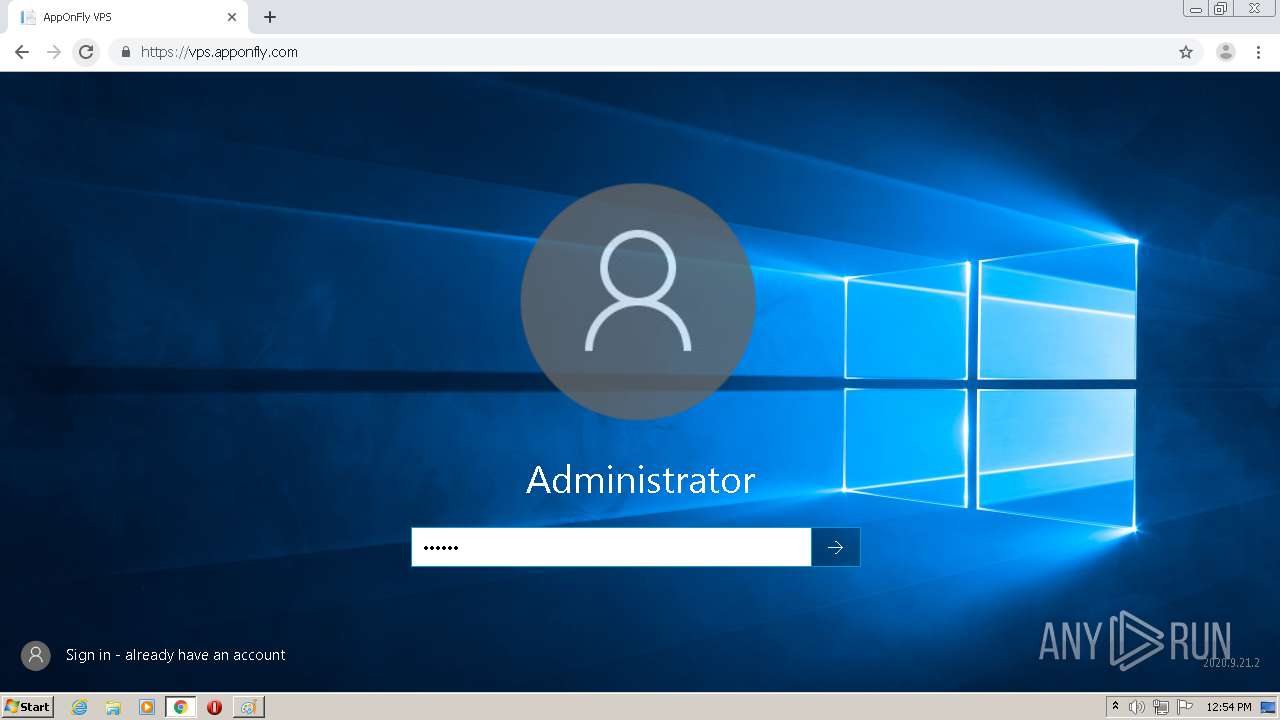
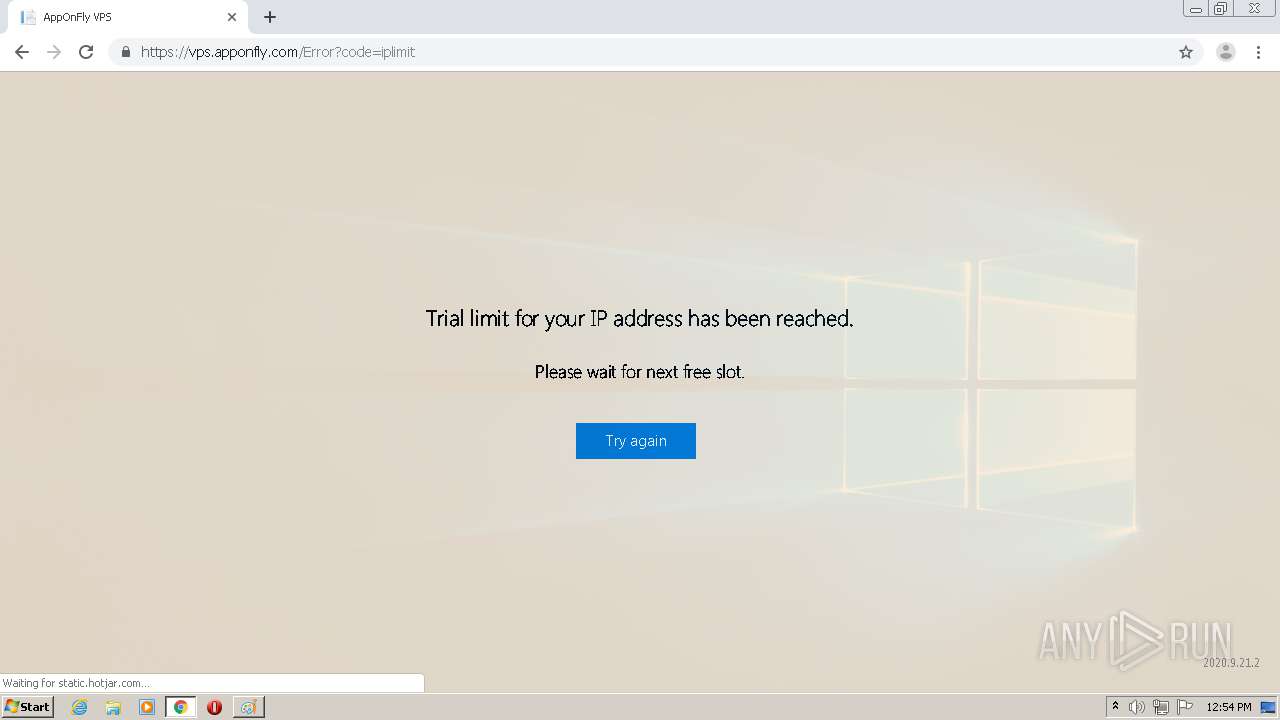
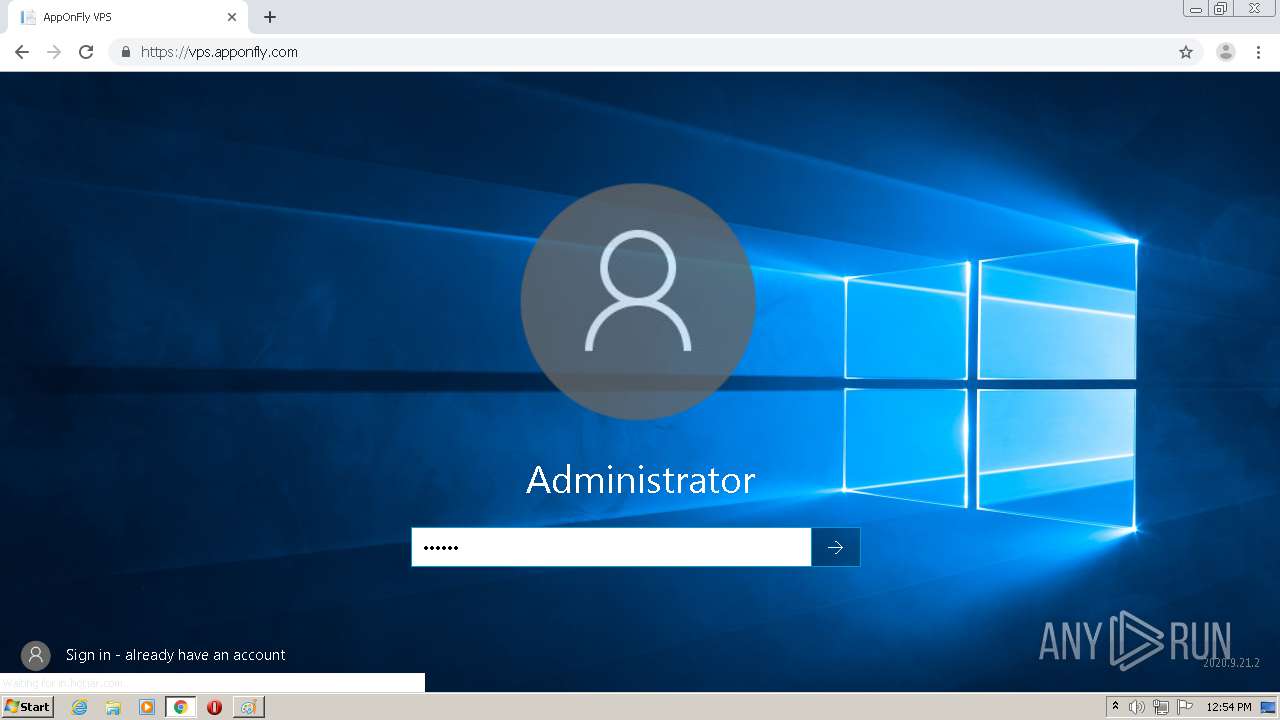
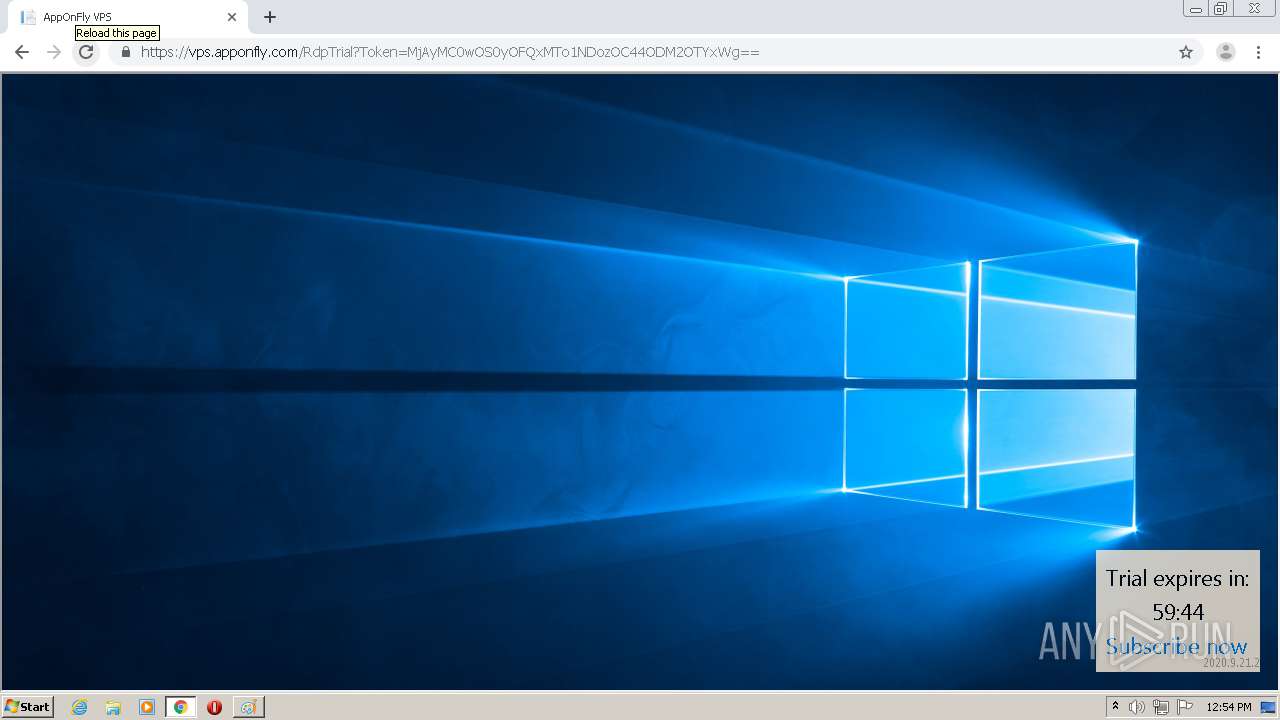
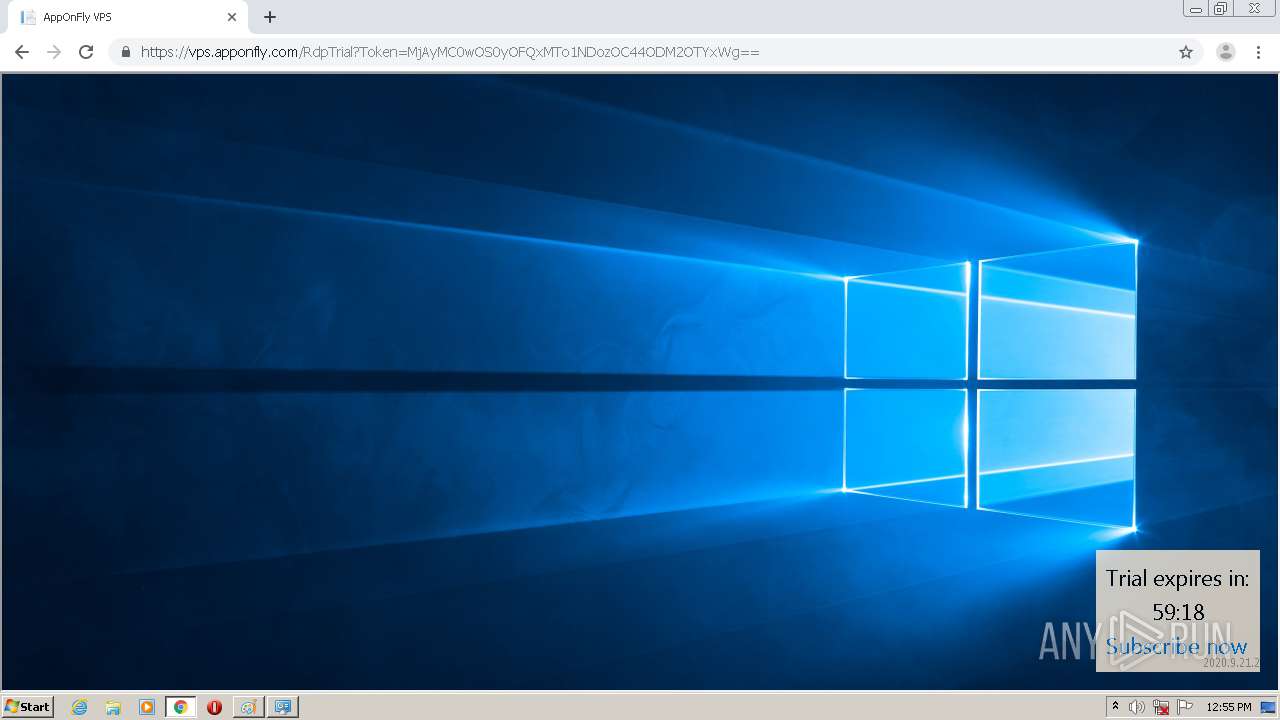
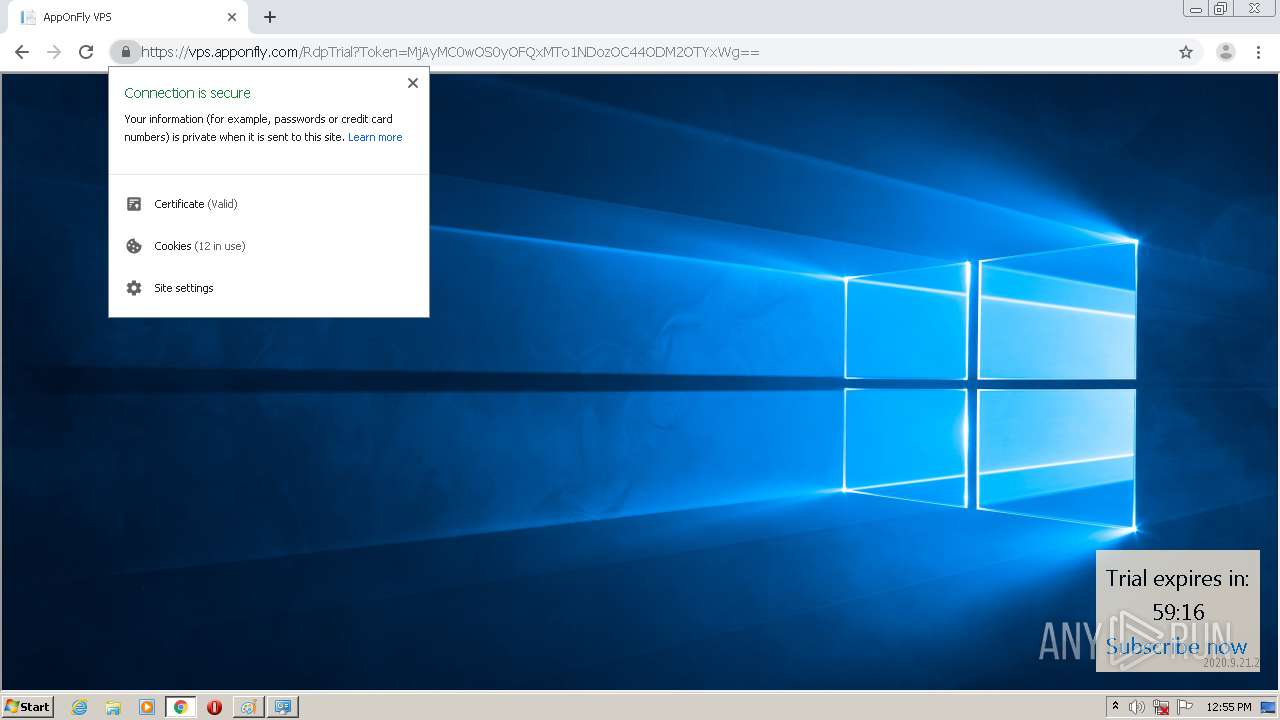
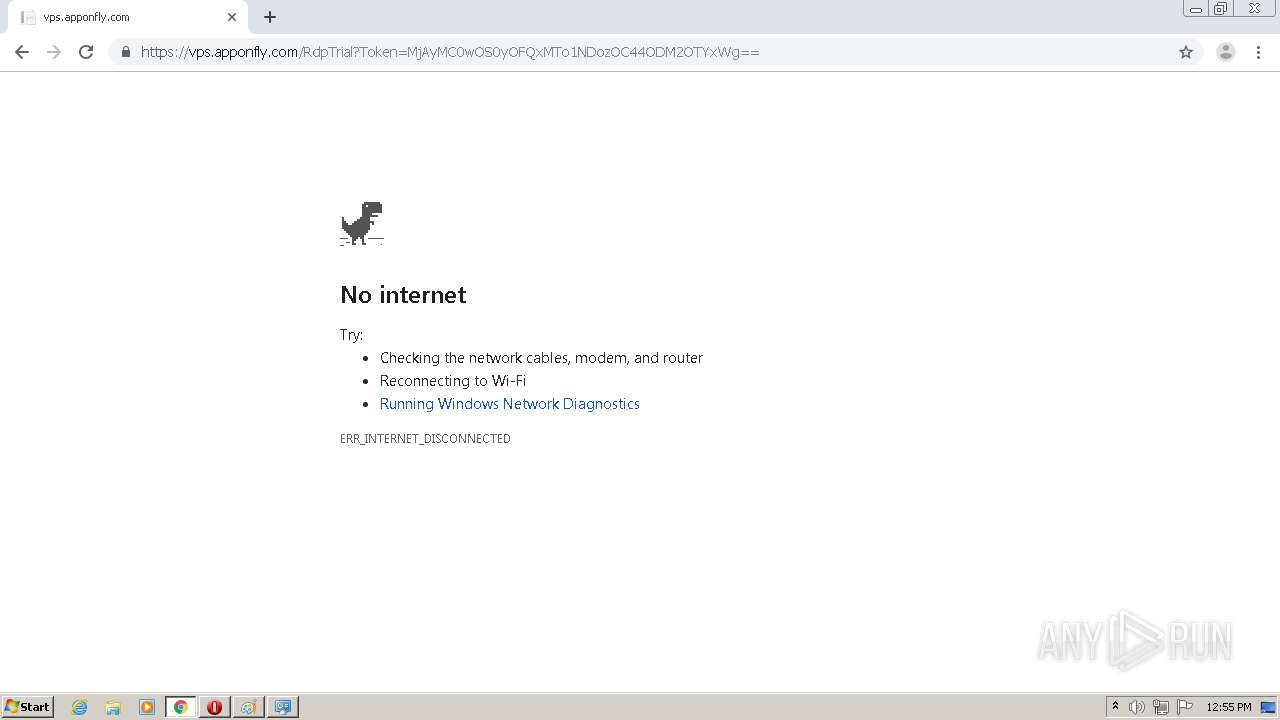
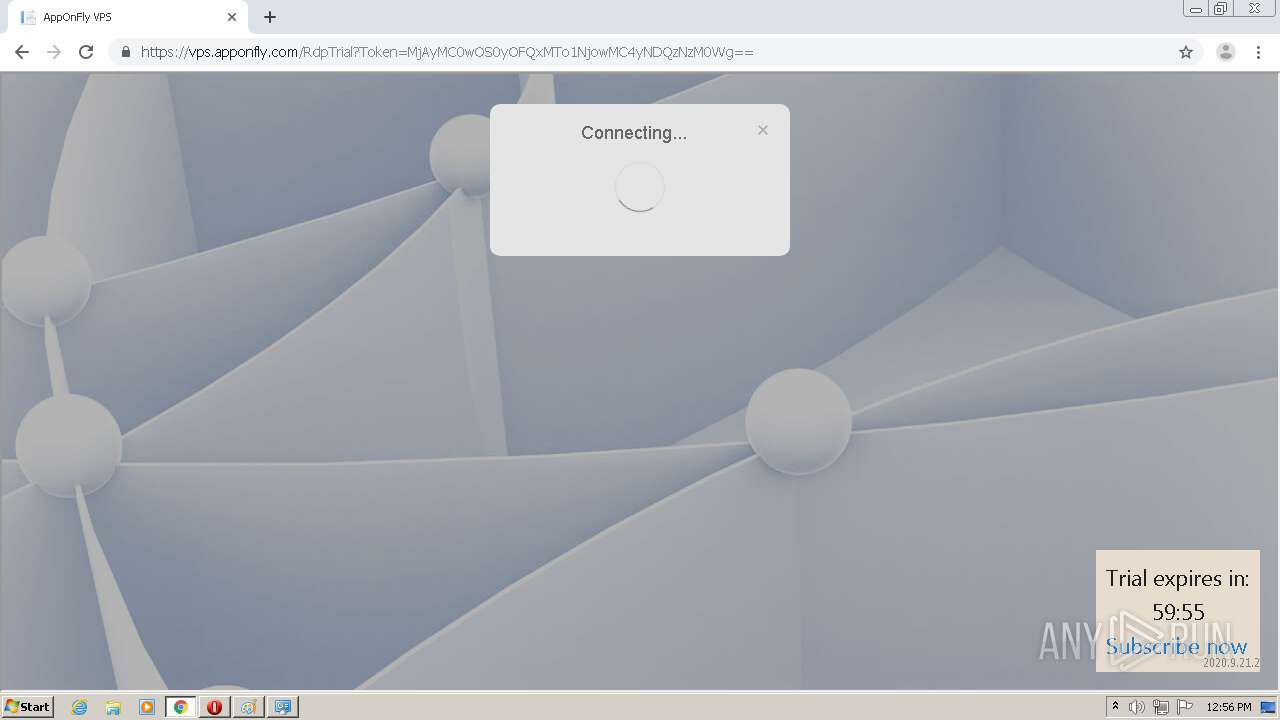
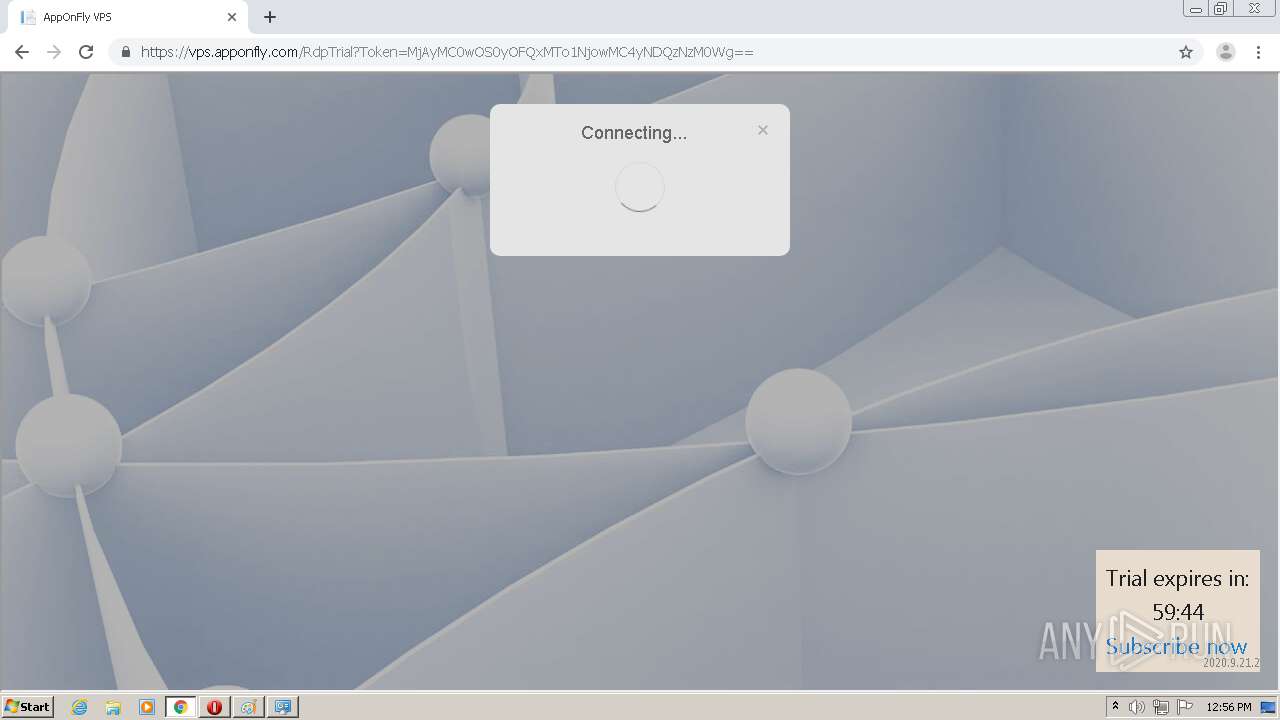
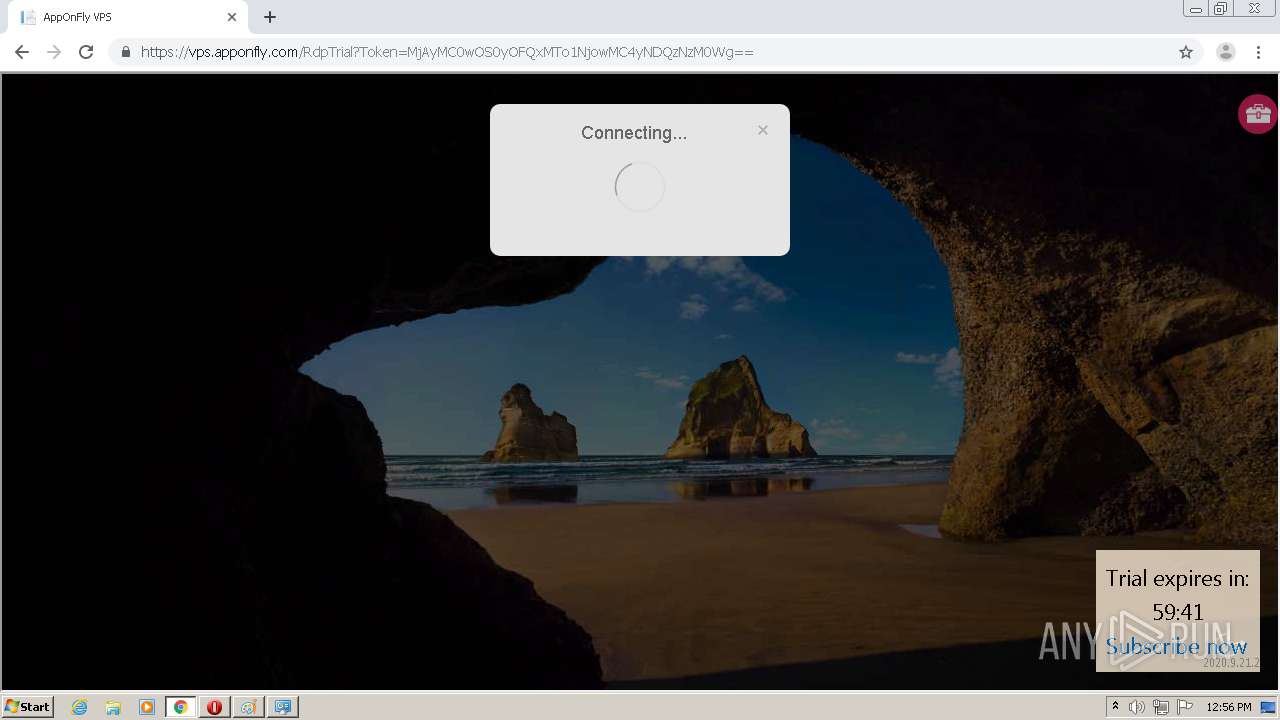
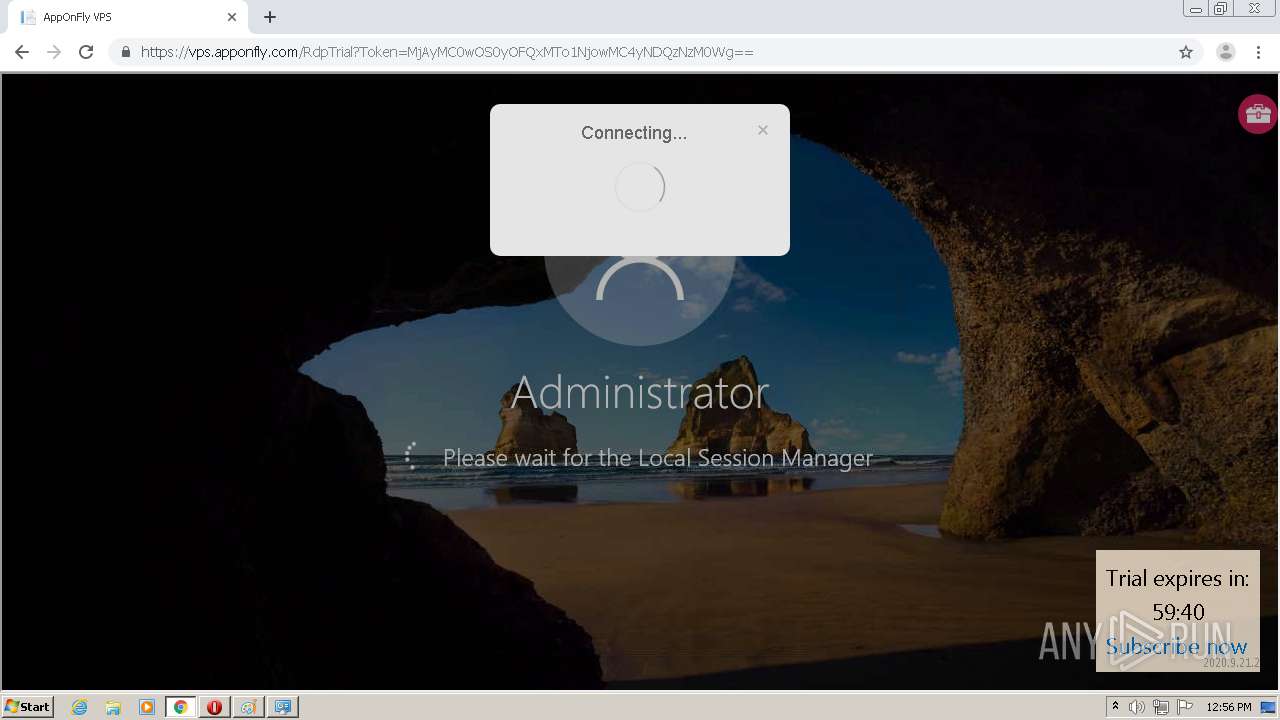
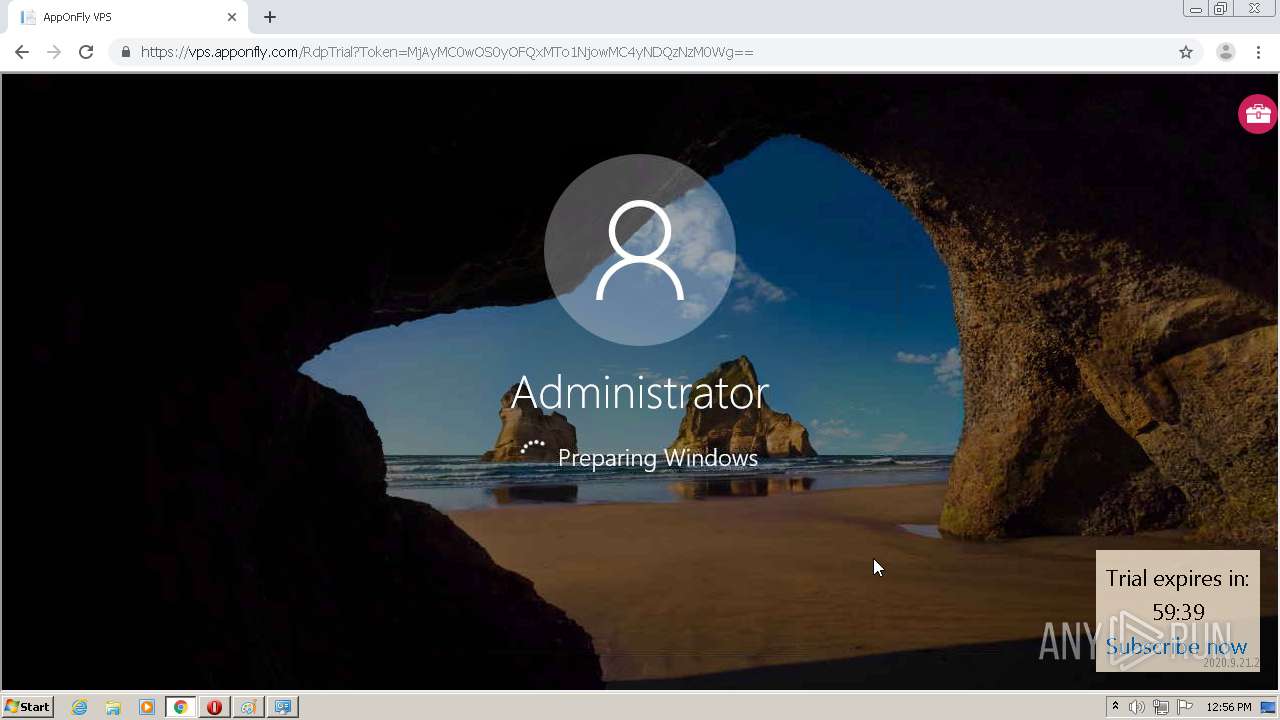
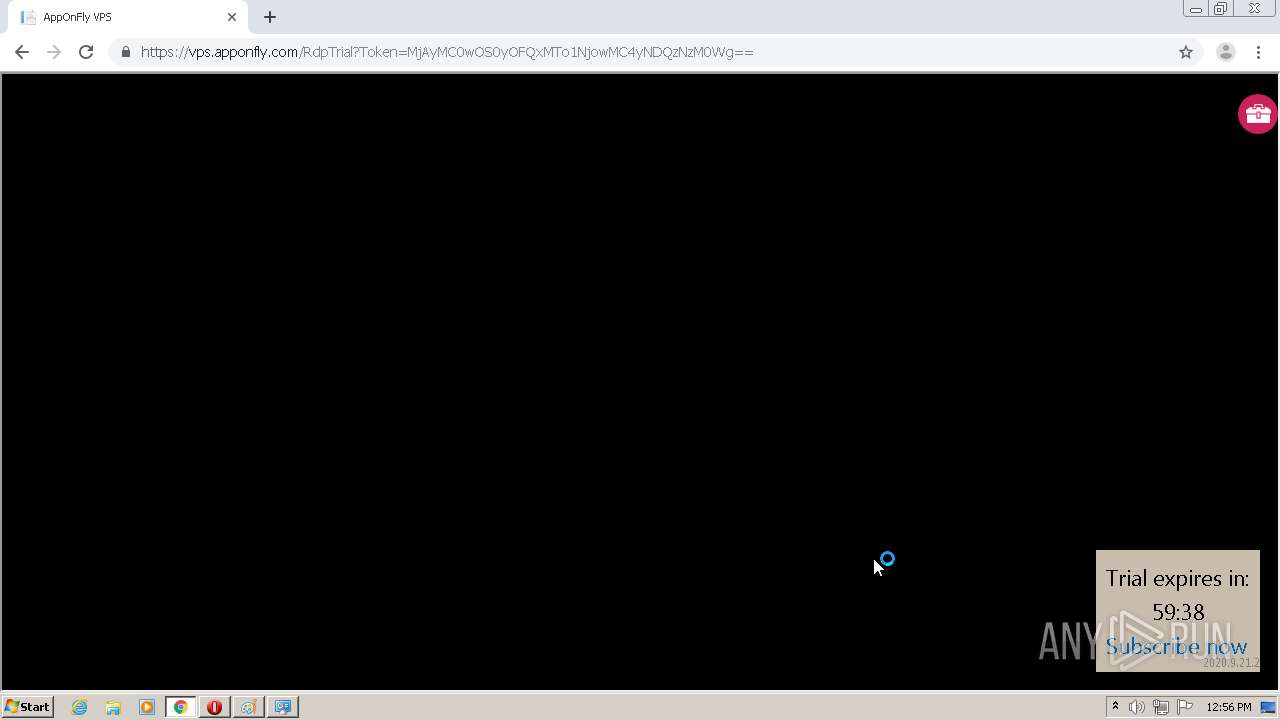
| URL: | https://vps.apponfly.com/Error?autostart=true&code=iplimit |
| Full analysis: | https://app.any.run/tasks/101a268d-e166-47d0-a8ab-5c93af36a2e5 |
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2020, 11:53:05 |
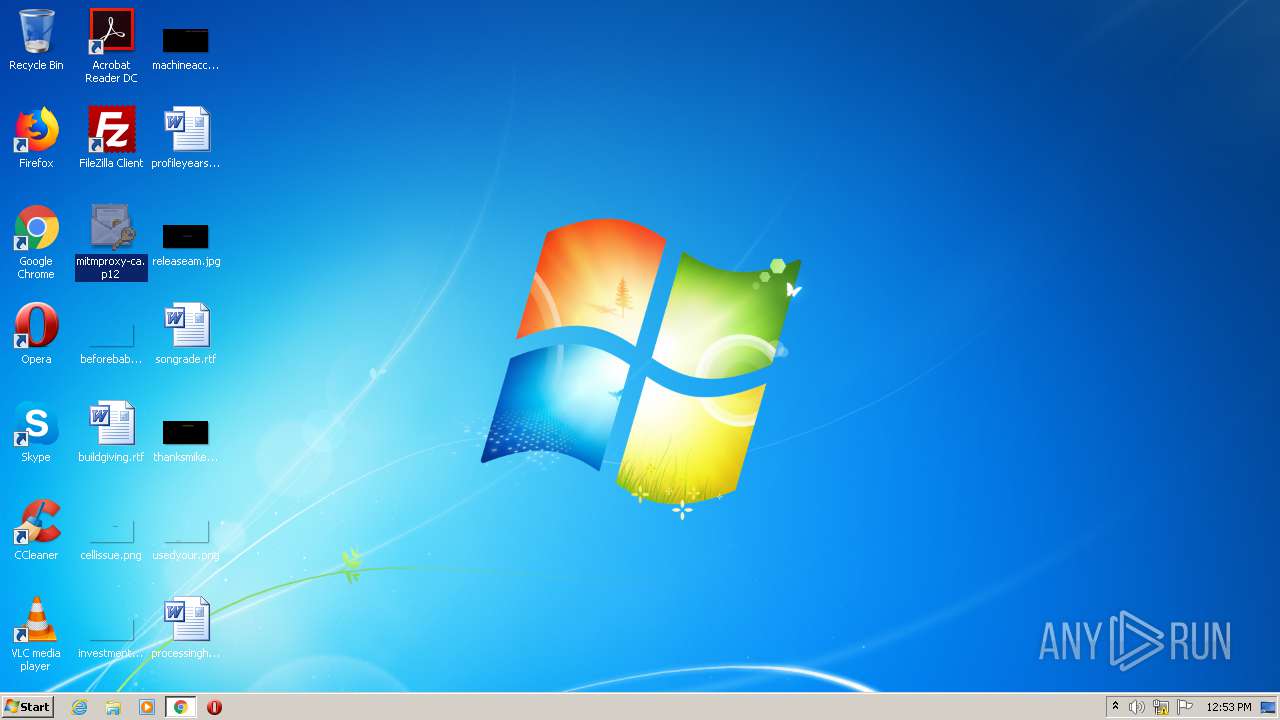
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C843A65DE304556F2BC6DBFB7485F25C |
| SHA1: | E355AF0499E50AFA63A9B05BE37568C5B1501A0A |
| SHA256: | 459D9719889C59C6C30F7C337CAD718BD15EC3F461EC64EB937592620B654D0D |
| SSDEEP: | 3:N8VVgLD4ybEEYXRYRXVBBAYMjMIMR:2ILDEEYBYRXX2YMjMIMR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- rundll32.exe (PID: 2716)
- DllHost.exe (PID: 4044)
- DllHost.exe (PID: 1516)
INFO
Reads the hosts file
- chrome.exe (PID: 2096)
- chrome.exe (PID: 760)
Reads settings of System Certificates
- chrome.exe (PID: 2096)
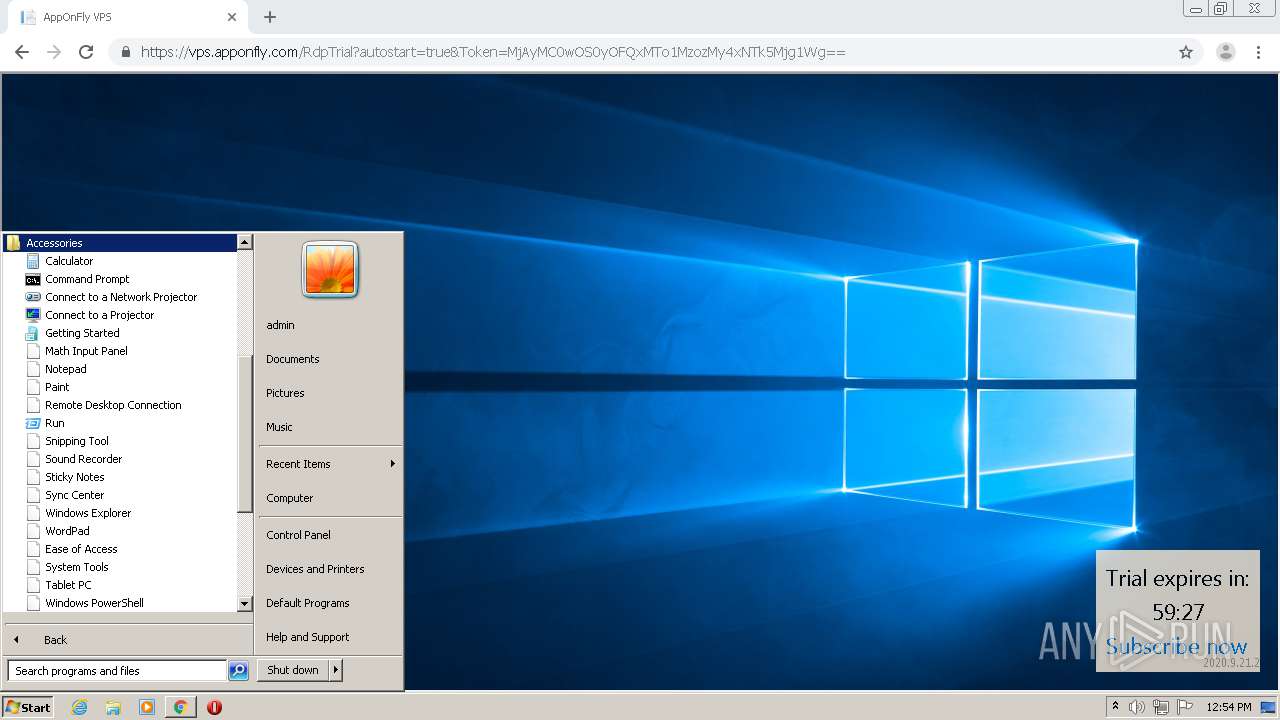
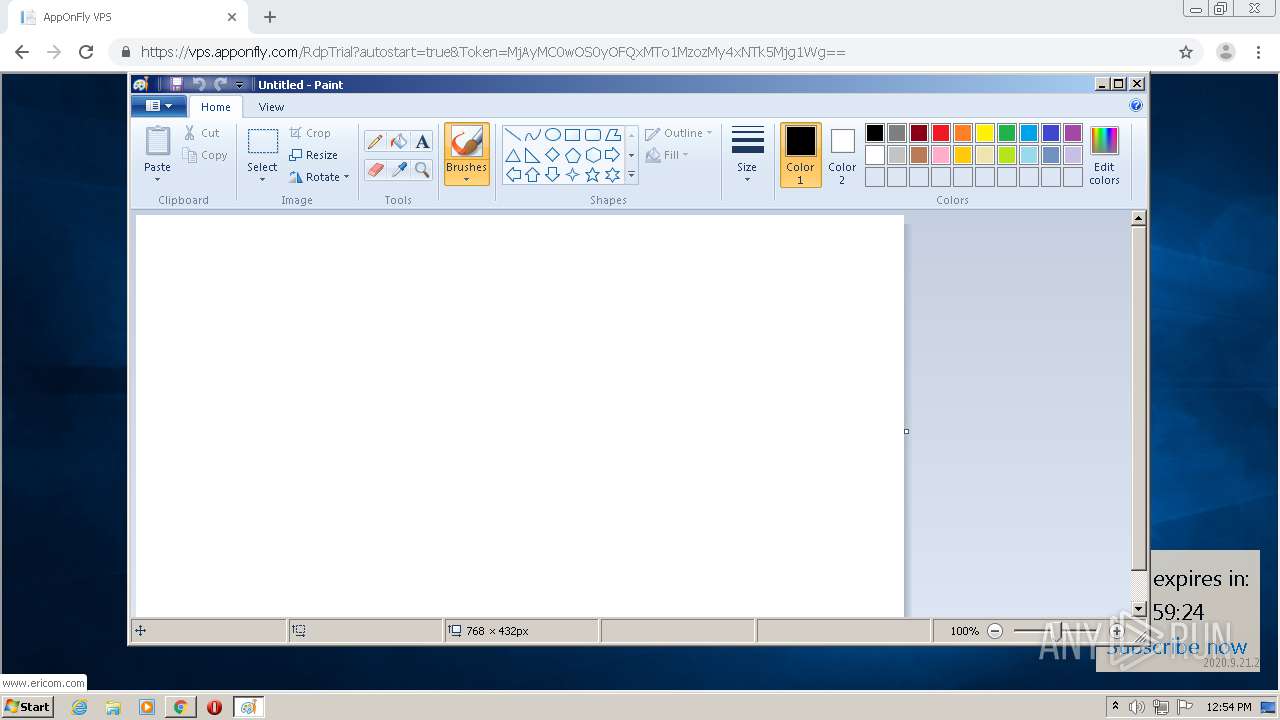
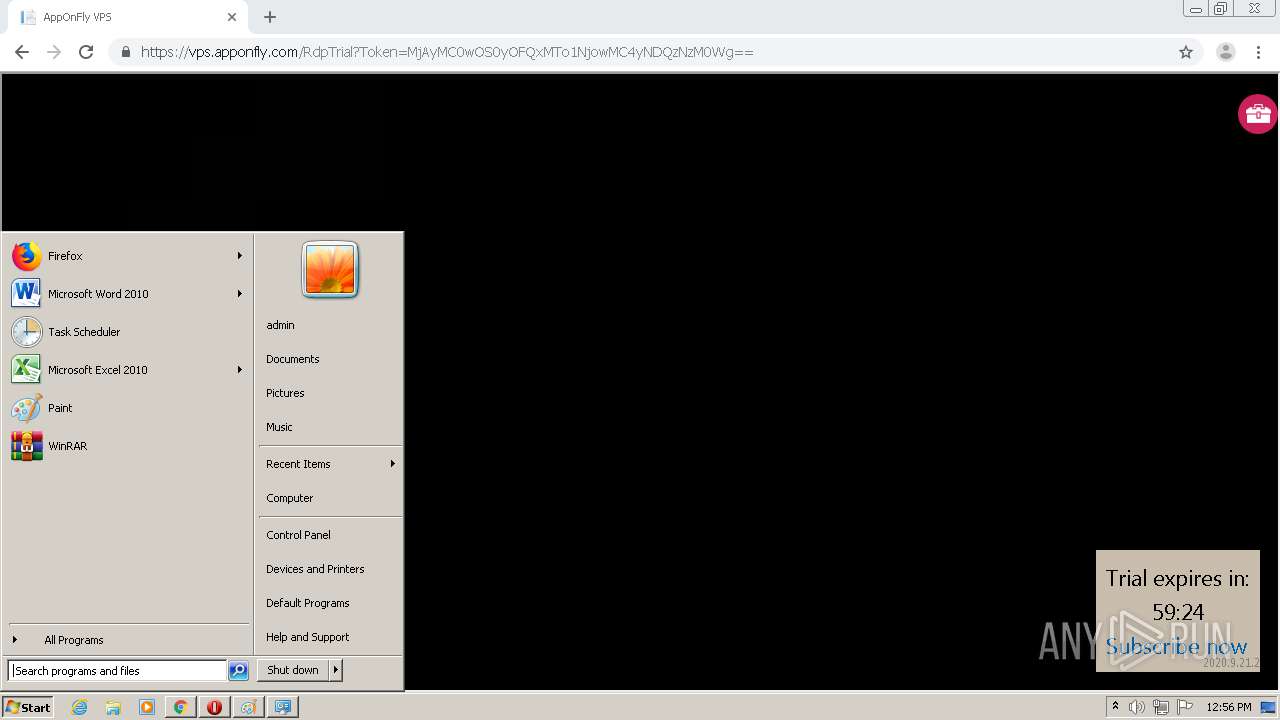
Manual execution by user
- mspaint.exe (PID: 624)
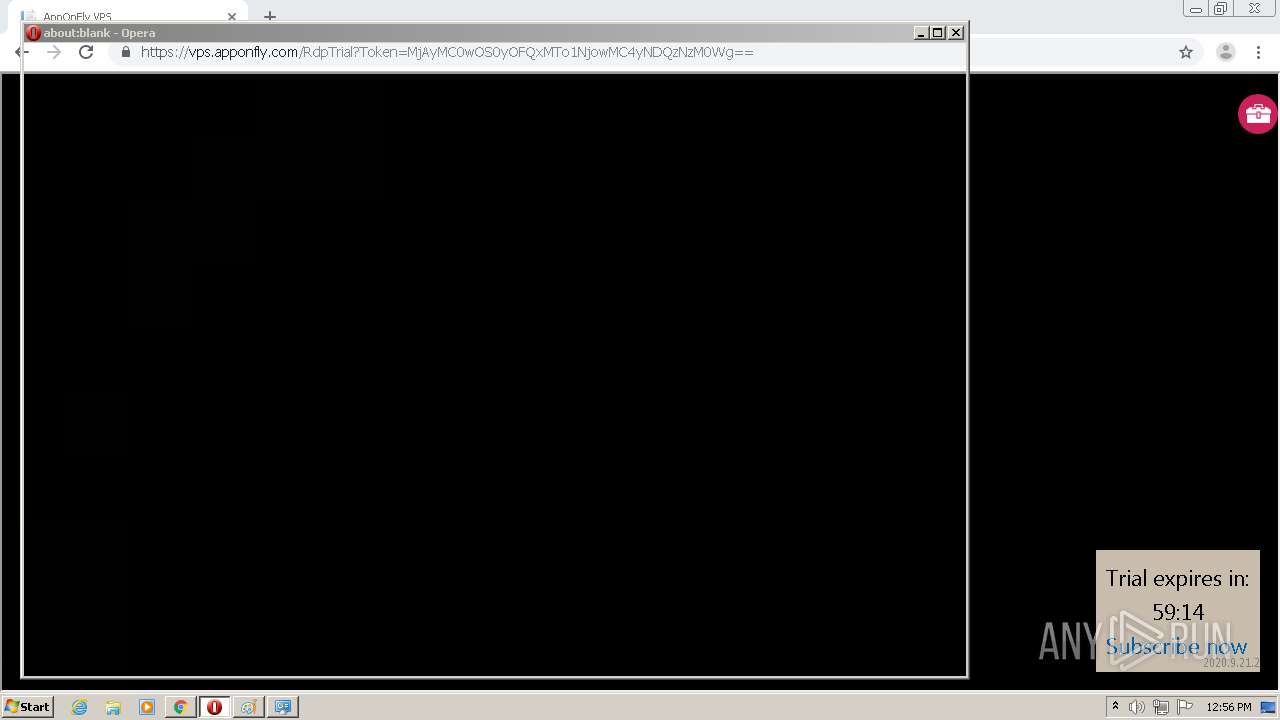
- opera.exe (PID: 1512)
Application launched itself
- chrome.exe (PID: 760)
Creates files in the user directory
- opera.exe (PID: 1512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
33
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3688 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 624 | "C:\Windows\system32\mspaint.exe" | C:\Windows\system32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1176649709232681165,8192383499028277585,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12884782432085293019 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2636 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
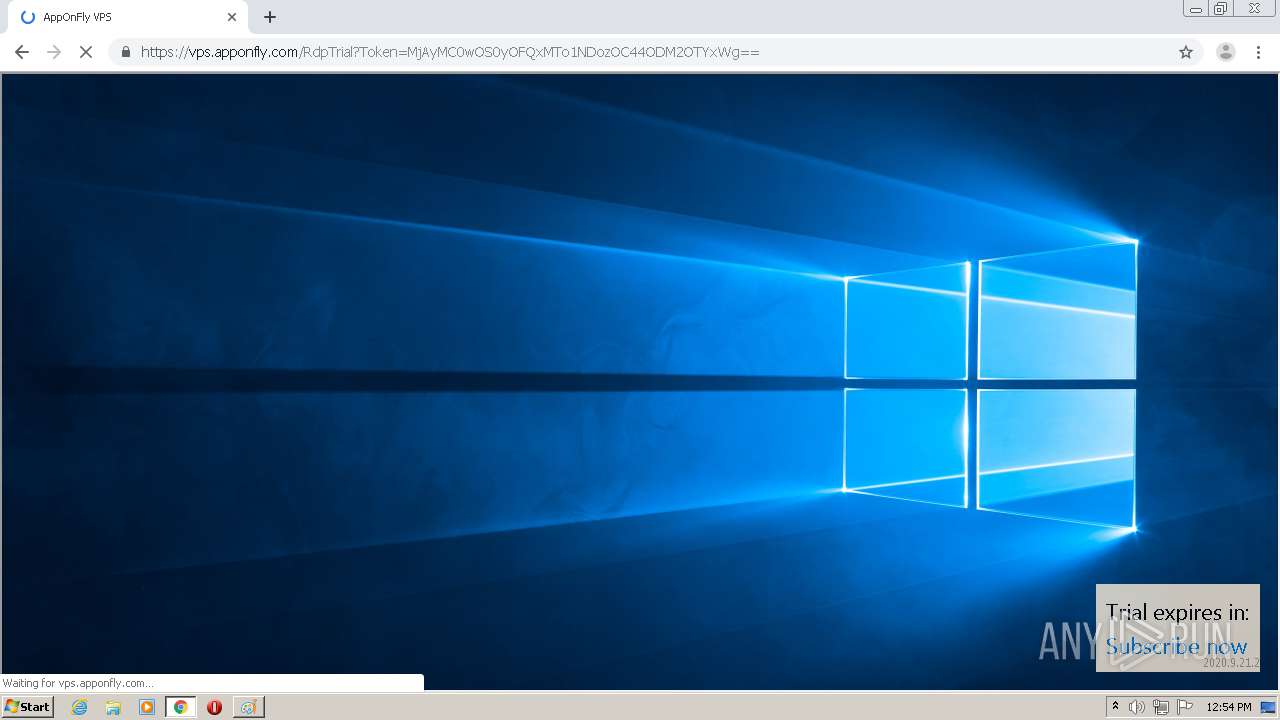
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://vps.apponfly.com/Error?autostart=true&code=iplimit" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1176649709232681165,8192383499028277585,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13718991814006305124 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1176649709232681165,8192383499028277585,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18397267806993994733 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
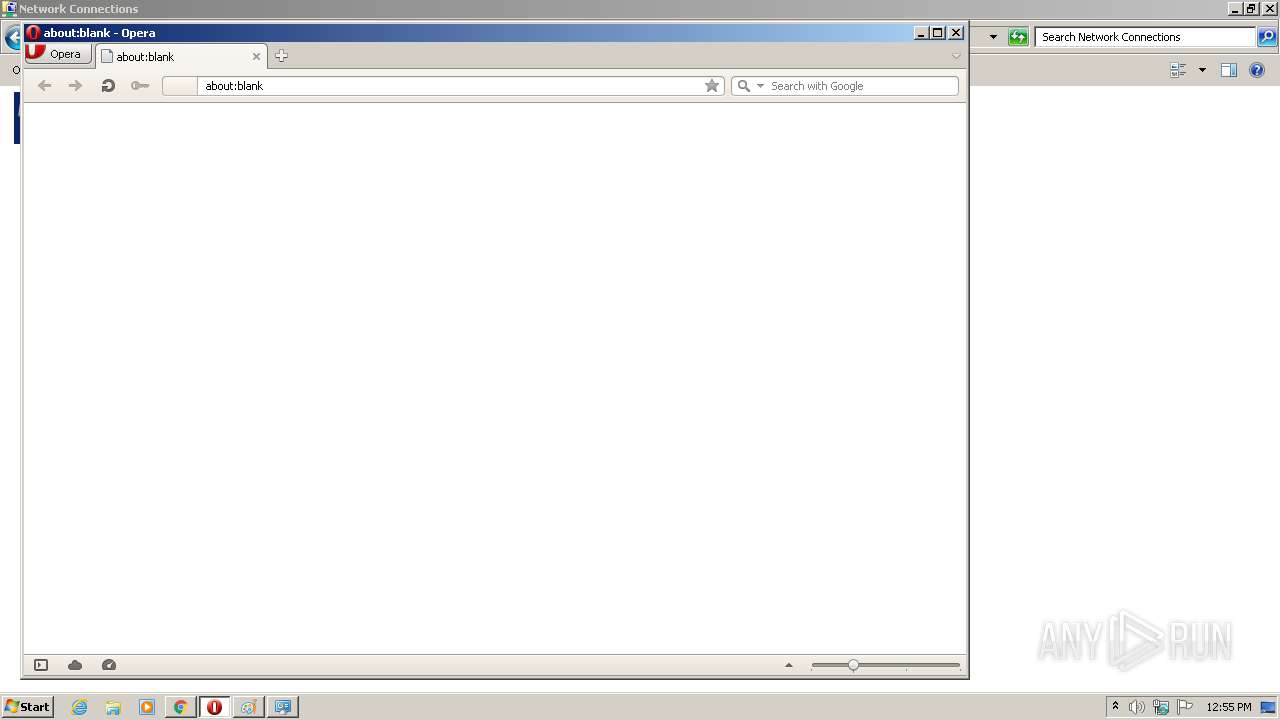
| 1512 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | — | explorer.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1516 | C:\Windows\system32\DllHost.exe /Processid:{BA126F01-2166-11D1-B1D0-00805FC1270E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1176649709232681165,8192383499028277585,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17805486995509079549 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,1176649709232681165,8192383499028277585,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17994593062299735024 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 117
Read events
890
Write events
223
Delete events
4
Modification events
| (PID) Process: | (312) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 760-13245767600324375 |
Value: 259 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (760) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
105
Text files
141
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F71CEB0-2F8.pma | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fe797e7f-39a9-4783-abb7-5561587ca471.tmp | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3b57f4.TMP | text | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3b5813.TMP | text | |
MD5:— | SHA256:— | |||
| 760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
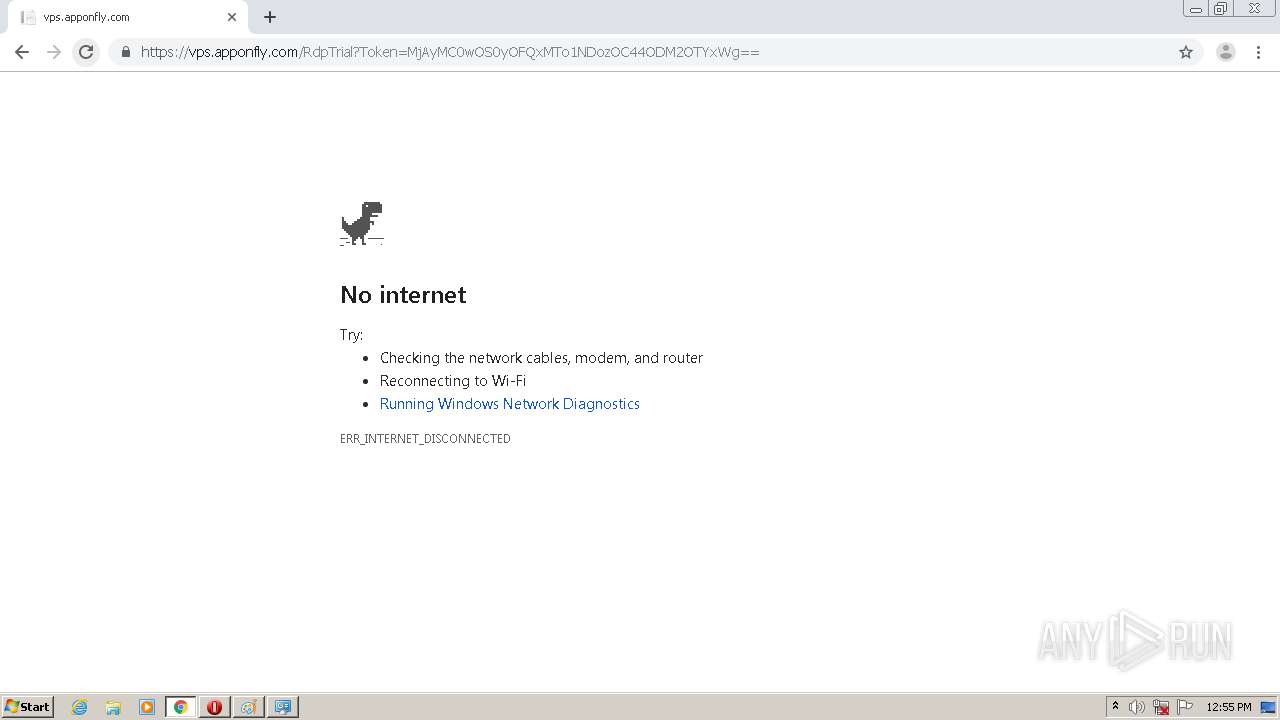
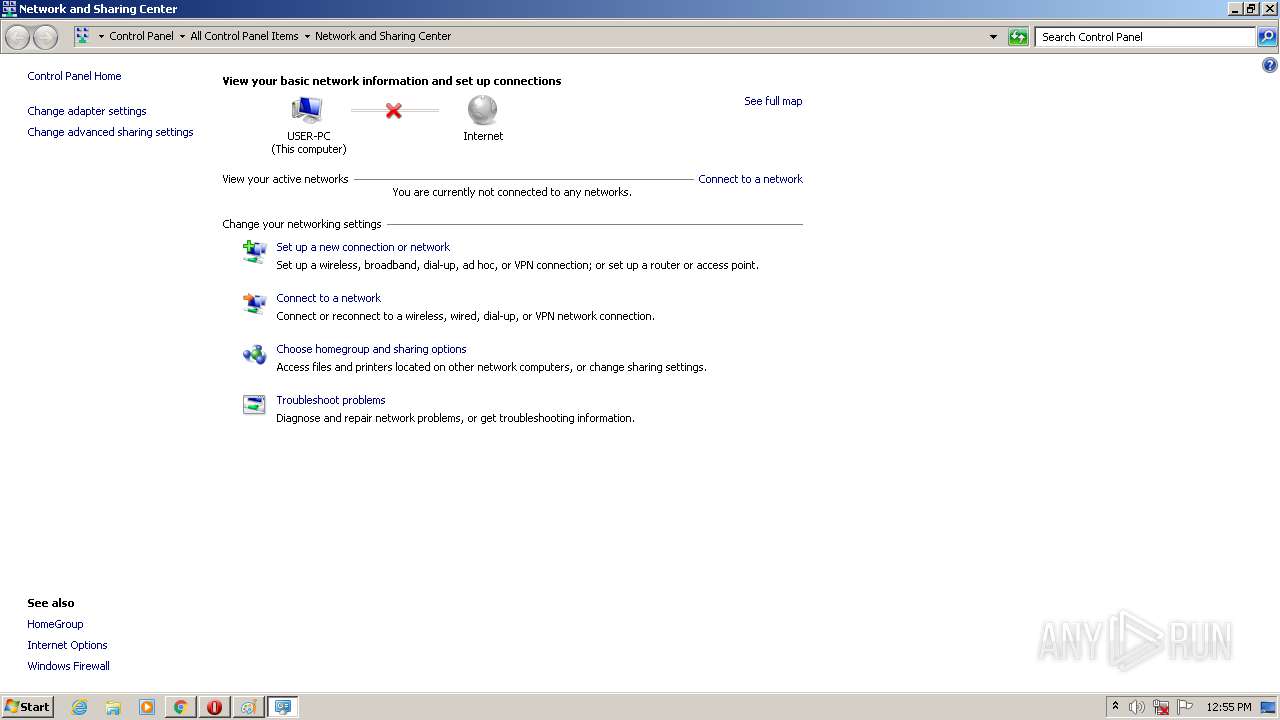
HTTP(S) requests
0
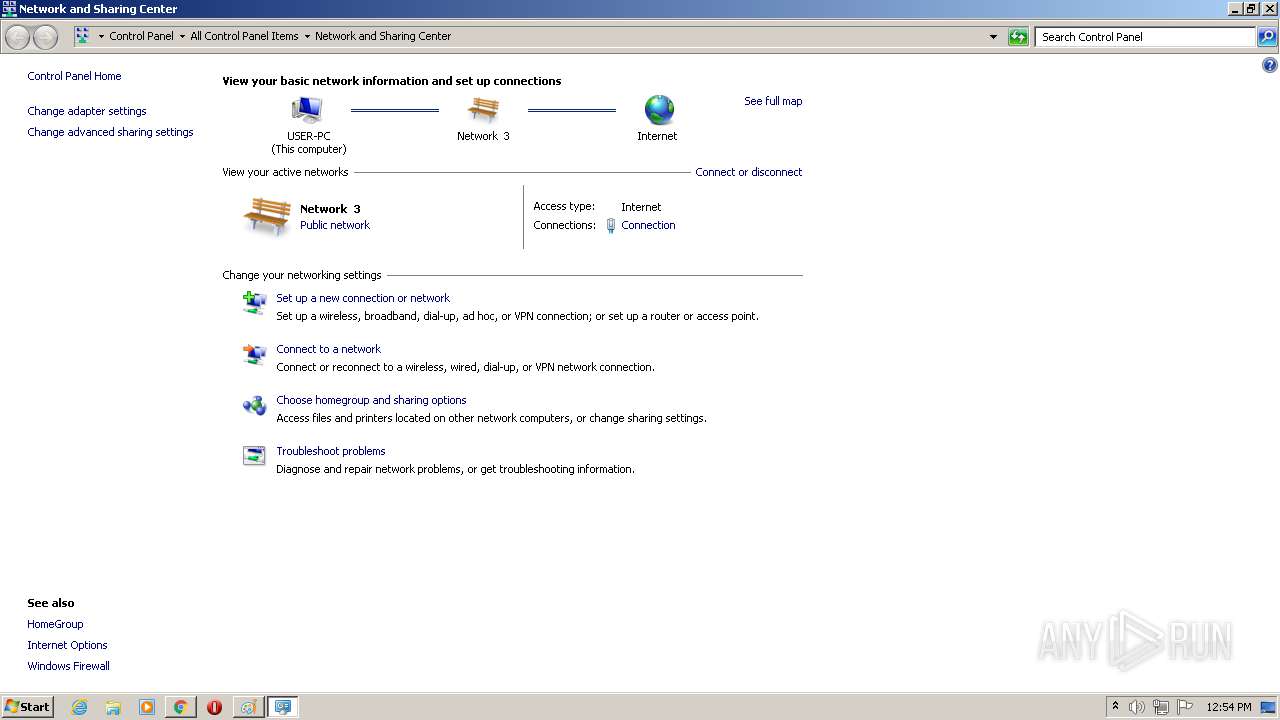
TCP/UDP connections
54
DNS requests
31
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
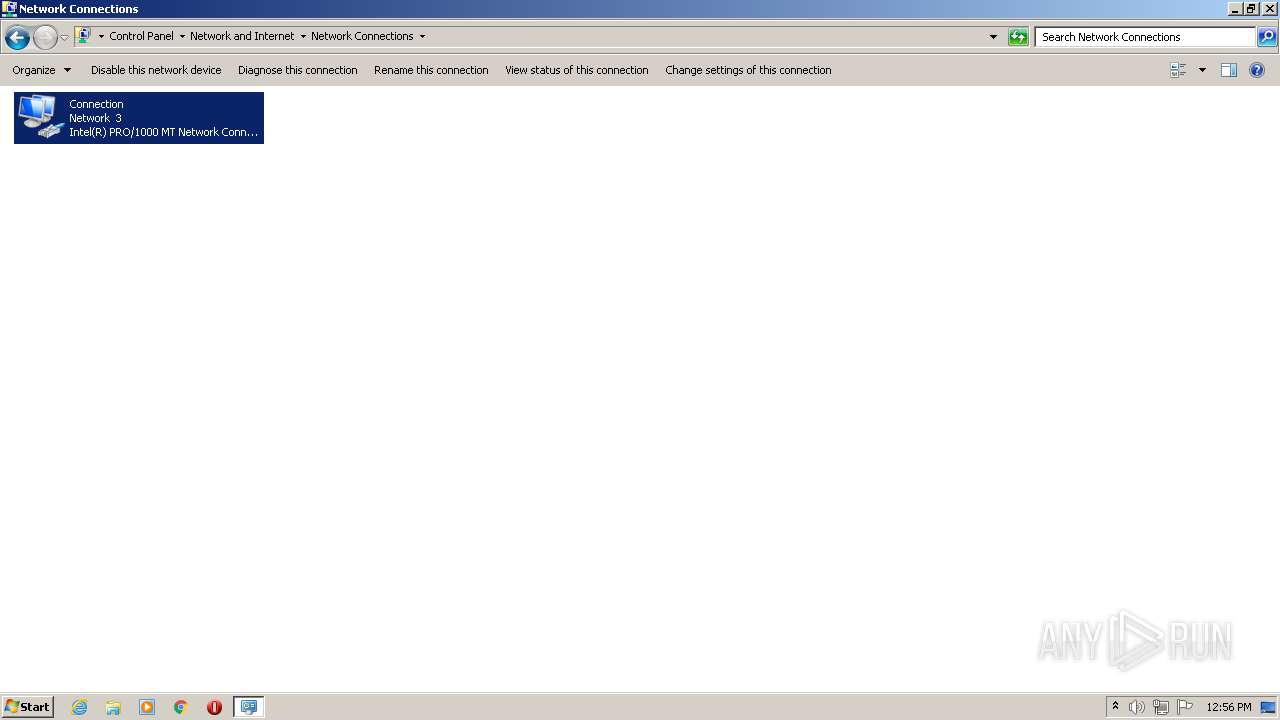
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
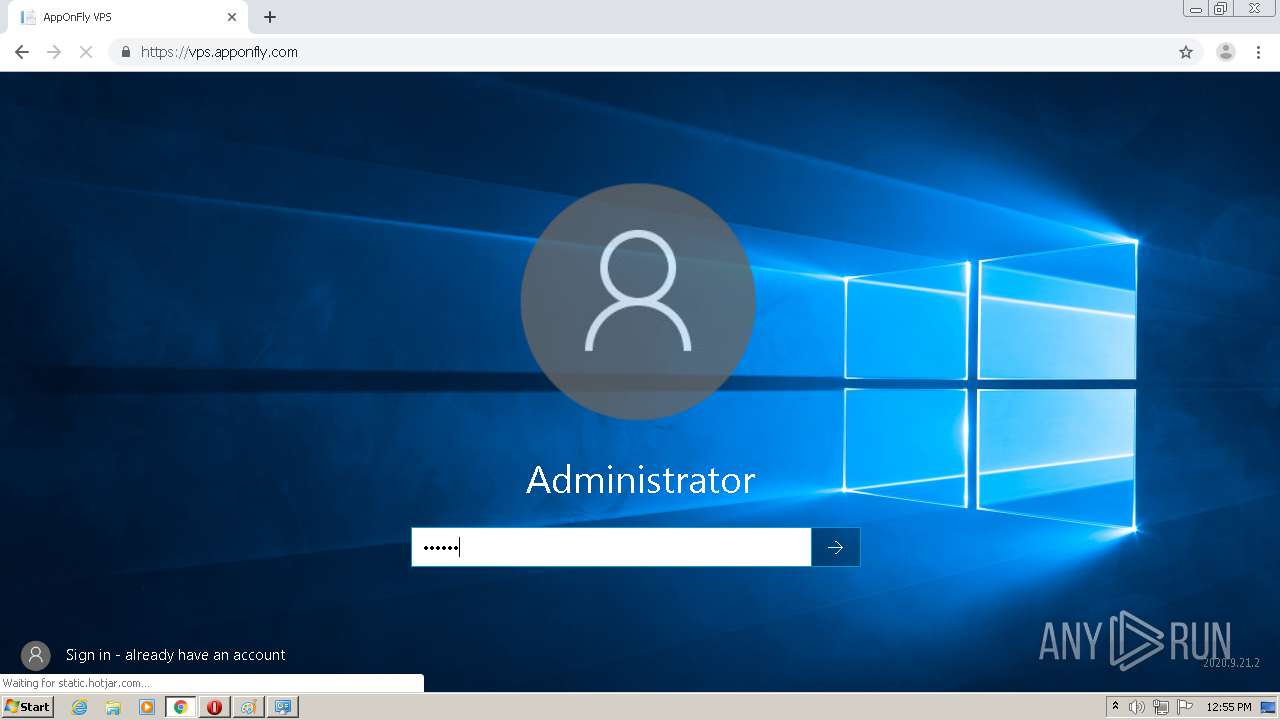
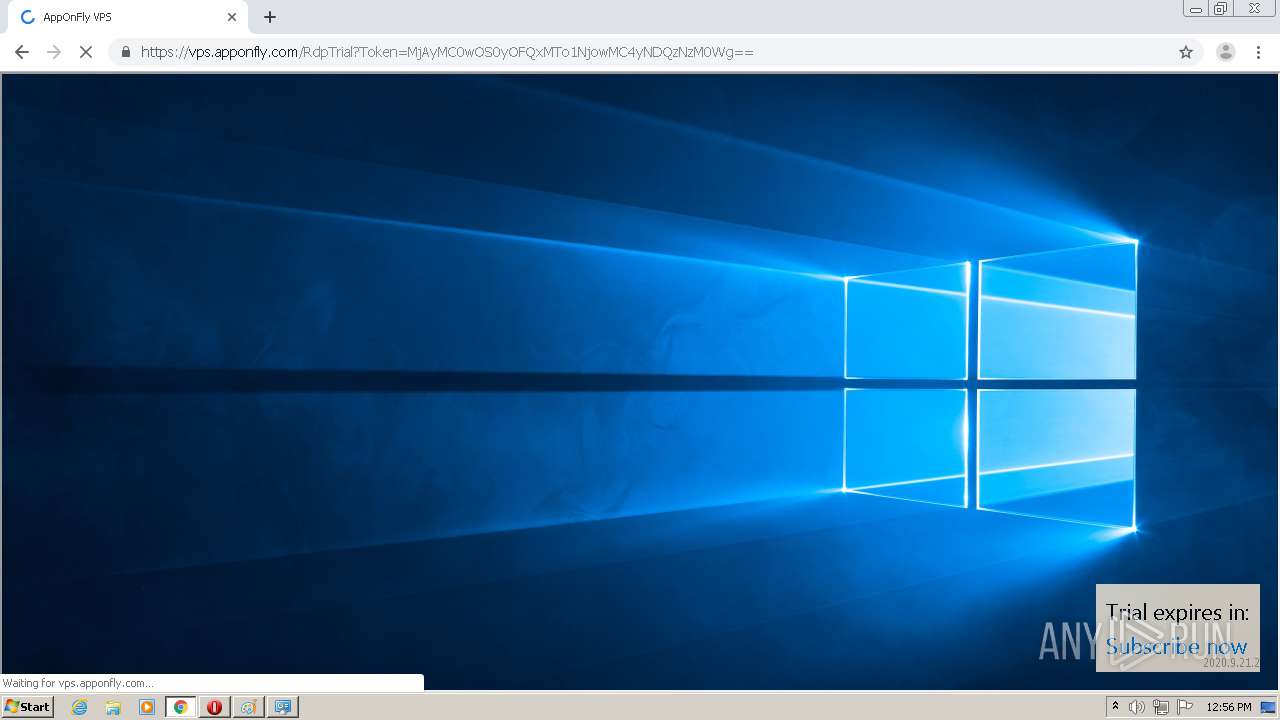
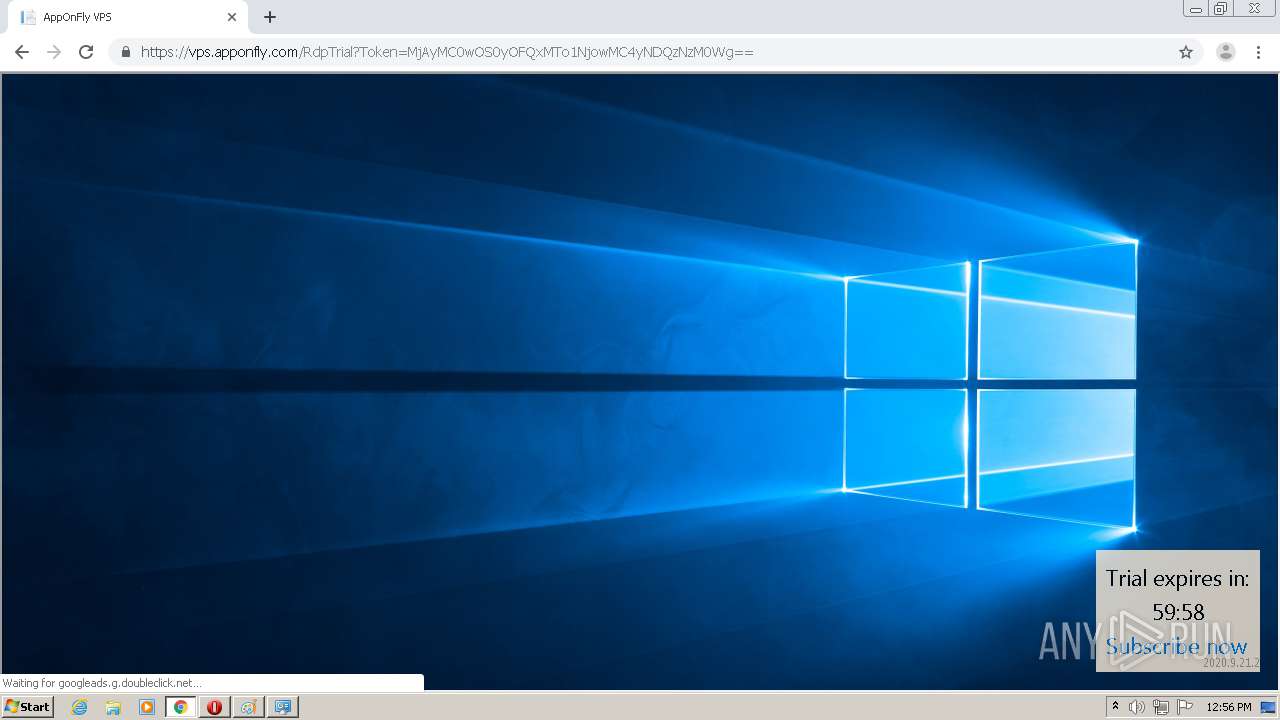
2096 | chrome.exe | 172.217.16.162:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2096 | chrome.exe | 185.219.169.22:443 | vps.apponfly.com | — | — | unknown |
2096 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 172.217.22.67:443 | www.google.lv | Google Inc. | US | whitelisted |
2096 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 52.17.9.66:443 | in.hotjar.com | Amazon.com, Inc. | IE | unknown |
2096 | chrome.exe | 185.219.169.21:4443 | htmlgw2.apponfly.com | — | — | unknown |
2096 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 147.75.33.131:443 | static.hotjar.com | Packet Host, Inc. | US | unknown |
2096 | chrome.exe | 172.217.21.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
vps.apponfly.com |
| malicious |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
static.hotjar.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
script.hotjar.com |
| whitelisted |
vars.hotjar.com |
| shared |
www.google.com |
| malicious |