| File name: | Archivo_c.cmd |
| Full analysis: | https://app.any.run/tasks/4e8c1a47-892d-4ed8-96da-b8e80a1b6041 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 21:33:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 7C49FF9A353343D96815757771A0E84D |
| SHA1: | ACF150F95354BC95BCEA006BBF7798A0F9739E93 |
| SHA256: | 4587E1A9C5ECFCF8C961E003BC36C672857FC5A1C998BE789C4BA414994D4B0E |
| SSDEEP: | 96:WTxrjlQeBjCdFoHPt6FoH8zjGvahlpjfiPk2pCj7fj6jXhLJ4puP2:WFlQ2jwFoHPUFoH8z6va2N4vi9/2 |
MALICIOUS
Changes settings of System certificates
- wscript.exe (PID: 2064)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2908)
Application was dropped or rewritten from another process
- hAY_fgk.exe (PID: 3124)
- hAY_fgk.exe (PID: 3500)
Loads dropped or rewritten executable
- hAY_fgk.exe (PID: 3124)
- SearchProtocolHost.exe (PID: 1724)
- hAY_fgk.exe (PID: 3500)
SUSPICIOUS
Creates files in the user directory
- wscript.exe (PID: 2064)
Executes scripts
- cmd.exe (PID: 2908)
Adds / modifies Windows certificates
- wscript.exe (PID: 2064)
Executable content was dropped or overwritten
- wscript.exe (PID: 2064)
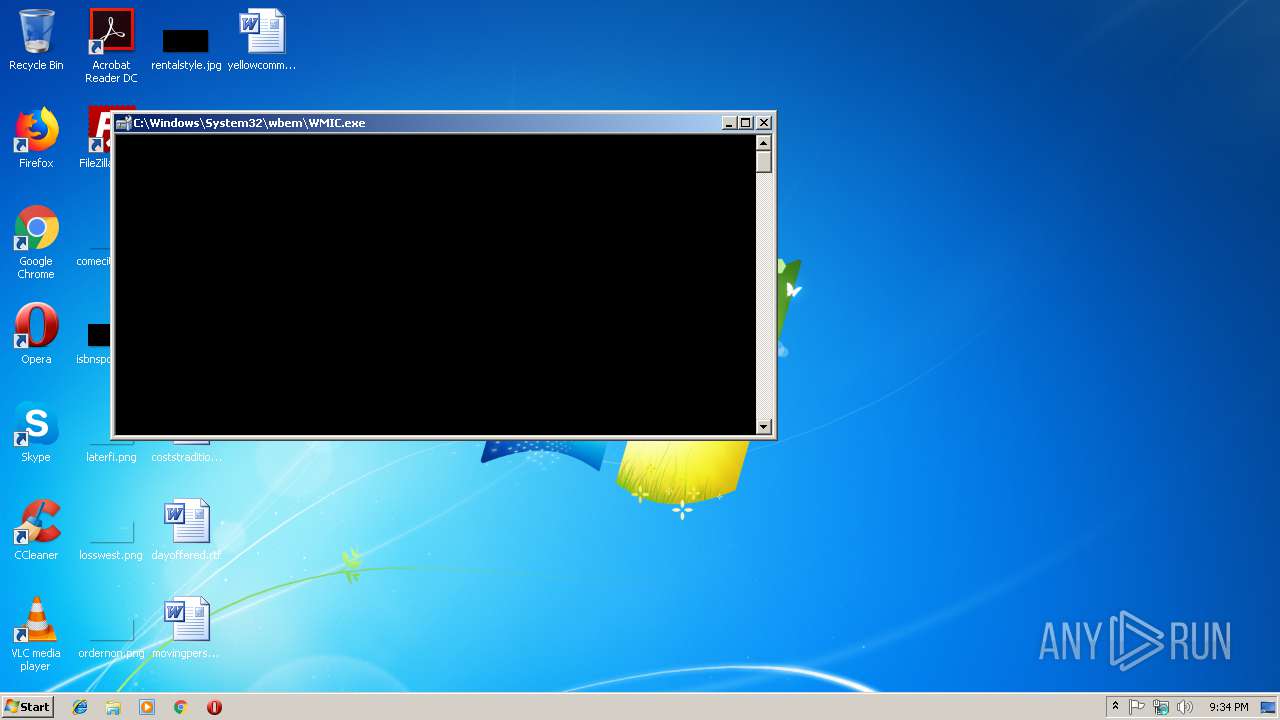
Uses WMIC.EXE to create a new process
- wscript.exe (PID: 2064)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2064)
INFO
Dropped object may contain Bitcoin addresses
- wscript.exe (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1724 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | wscript //Nologo "C:\Users\admin\admin\admin.vbs" t6LevwOojGHcGSntDM7EI9cvnd0wo3FjR3h8yq | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2732 | "C:\Windows\System32\wbem\WMIC.exe" process call create C:\Users\admin\hAY_fgk\hAY_fgk.exe | C:\Windows\System32\wbem\WMIC.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Archivo_c.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3124 | C:\Users\admin\hAY_fgk\hAY_fgk.exe | C:\Users\admin\hAY_fgk\hAY_fgk.exe | — | wmiprvse.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: NVIDIA Smart Maximise Helper Host Exit code: 0 Version: 6.14.10.100.03 Modules
| |||||||||||||||
| 3360 | "C:\Windows\system32\cmd.exe" /c start C:\Users\admin\hAY_fgk\hAY_fgk.exe | C:\Windows\system32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3500 | C:\Users\admin\hAY_fgk\hAY_fgk.exe | C:\Users\admin\hAY_fgk\hAY_fgk.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: NVIDIA Smart Maximise Helper Host Exit code: 0 Version: 6.14.10.100.03 Modules
| |||||||||||||||
| 3728 | ping 127.0.0.1 -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
876
Read events
836
Write events
37
Delete events
3
Modification events
| (PID) Process: | (1724) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1724) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2064) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
6
Text files
68
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\CabEF09.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\TarEF0A.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\CabEF2B.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\TarEF2C.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\CabEFD8.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Temp\TarEFD9.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\hAY_fgk\WPA4V0CPZ8OET10ZIM0WKC1PLARGFQZKJKUZTDA | — | |
MD5:— | SHA256:— | |||
| 2908 | cmd.exe | C:\Users\admin\admin\admin.vbs | text | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 2064 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\y169[1].zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | wscript.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2064 | wscript.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | wscript.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2064 | wscript.exe | 132.148.244.194:443 | politecnicointernacional.edu.co | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
politecnicointernacional.edu.co |
| unknown |
www.download.windowsupdate.com |
| whitelisted |