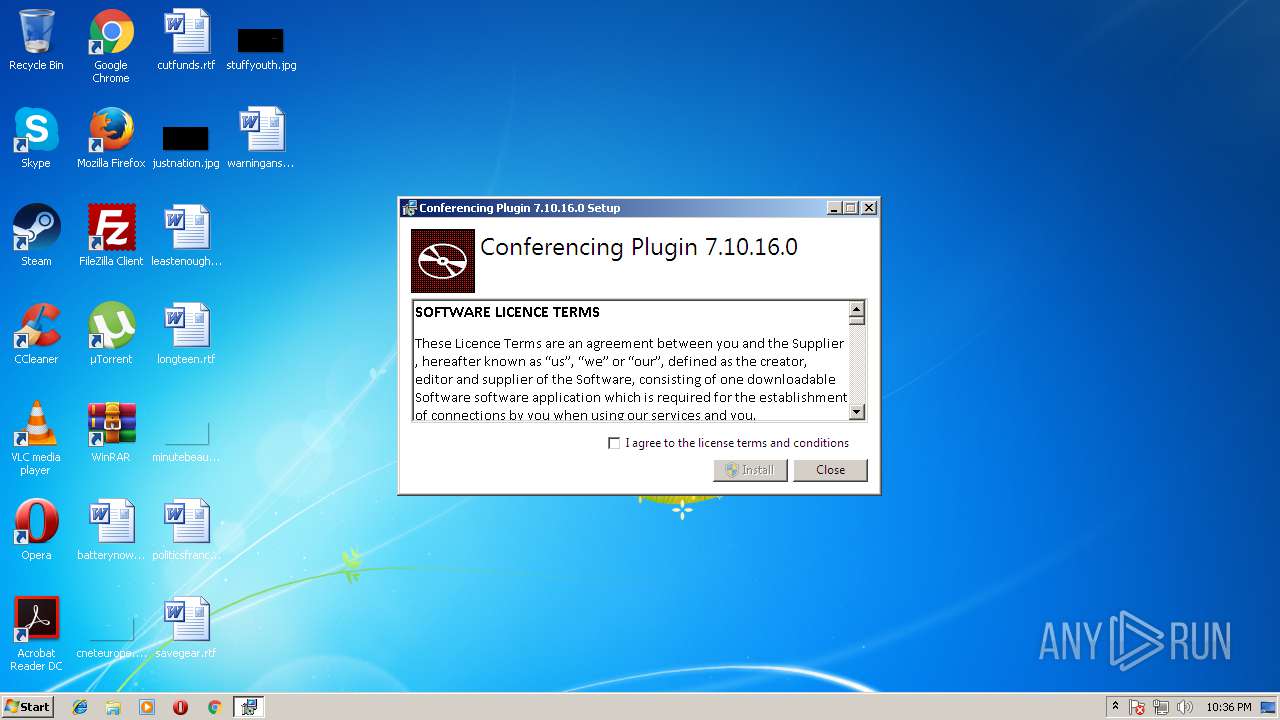
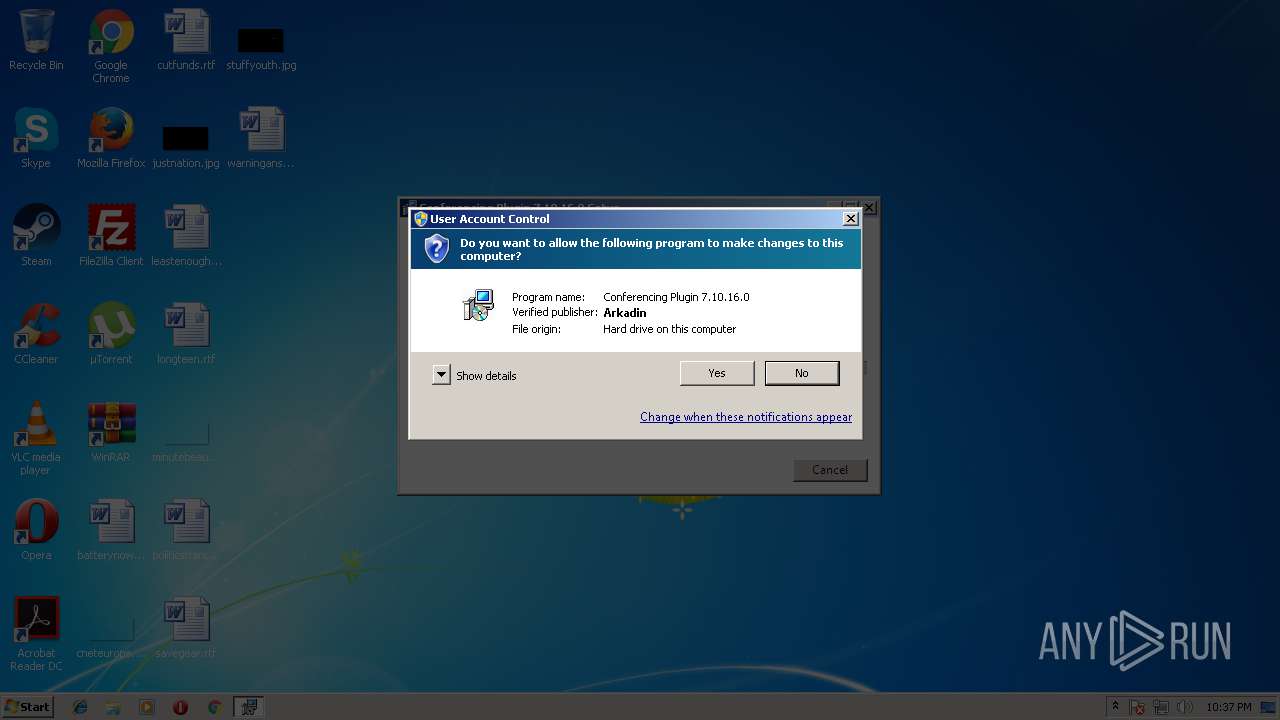
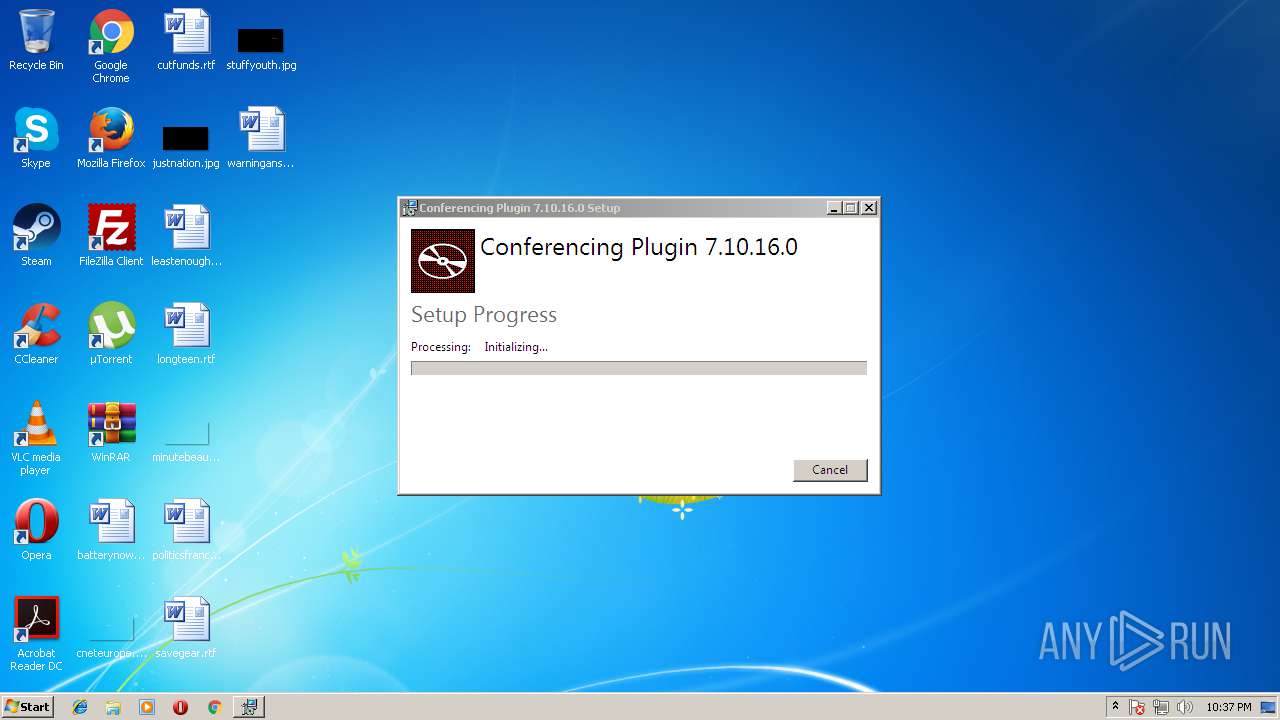
| File name: | ConferencingPluginSetup.exe |
| Full analysis: | https://app.any.run/tasks/19ab4fb0-8167-415c-a555-ad3879fcff3b |
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2018, 21:36:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A3DD684CD732DAC1EA8B6E10204CA586 |
| SHA1: | 8513B1AA75598C4989658147AEE2321A9BFE153E |
| SHA256: | 4577E317825460908FBC5556B54C1F69DC9716620B7D604123E3444970A8E28F |
| SSDEEP: | 393216:sZiLNMJkgDF1WVlnzjx9EJBGqMBlwXysaS+lXbeBPV:sZsNq6TzV9ED4wirllXylV |
MALICIOUS
Application was dropped or rewritten from another process
- ConferencingPluginSetup.exe (PID: 2936)
- ConferencingPluginSetup.exe (PID: 3564)
Changes the autorun value in the registry
- ConferencingPluginSetup.exe (PID: 3564)
- regsvr32.exe (PID: 3704)
Loads dropped or rewritten executable
- ConferencingPluginSetup.exe (PID: 2936)
- regsvr32.exe (PID: 2568)
- regsvr32.exe (PID: 3704)
Registers / Runs the DLL via REGSVR32.EXE
- msiexec.exe (PID: 1088)
SUSPICIOUS
Executable content was dropped or overwritten
- ConferencingPluginSetup.exe (PID: 2936)
- ConferencingPluginSetup.exe (PID: 1336)
- ConferencingPluginSetup.exe (PID: 3564)
- msiexec.exe (PID: 1088)
Starts itself from another location
- ConferencingPluginSetup.exe (PID: 2936)
Creates or modifies windows services
- ConferencingPluginSetup.exe (PID: 3564)
Creates a software uninstall entry
- ConferencingPluginSetup.exe (PID: 3564)
Creates files in the program directory
- ConferencingPluginSetup.exe (PID: 3564)
Creates COM task schedule object
- regsvr32.exe (PID: 3704)
- regsvr32.exe (PID: 2568)
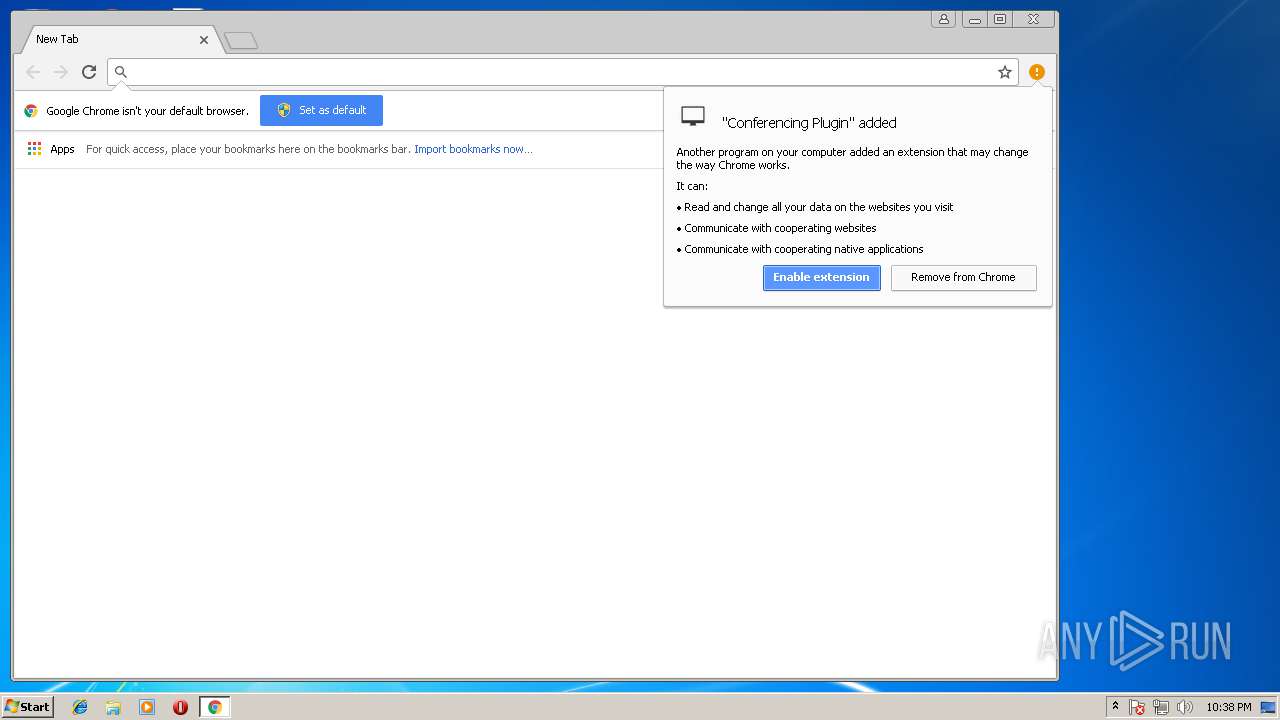
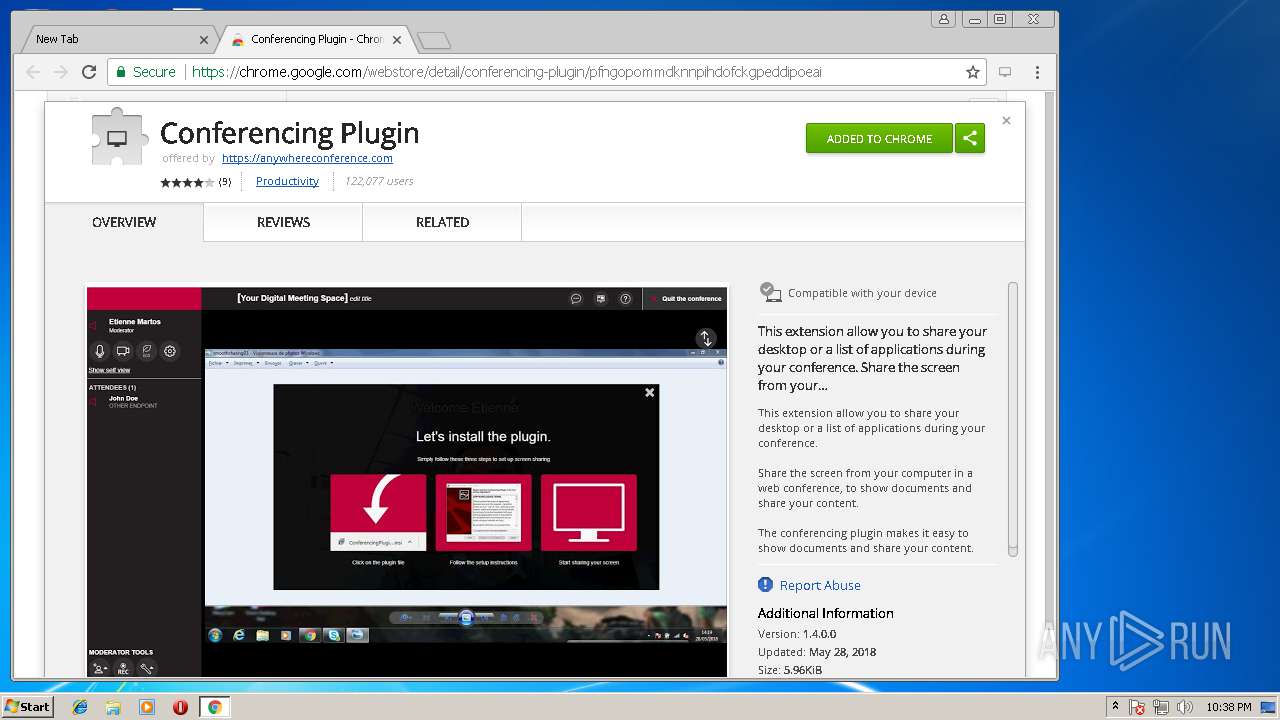
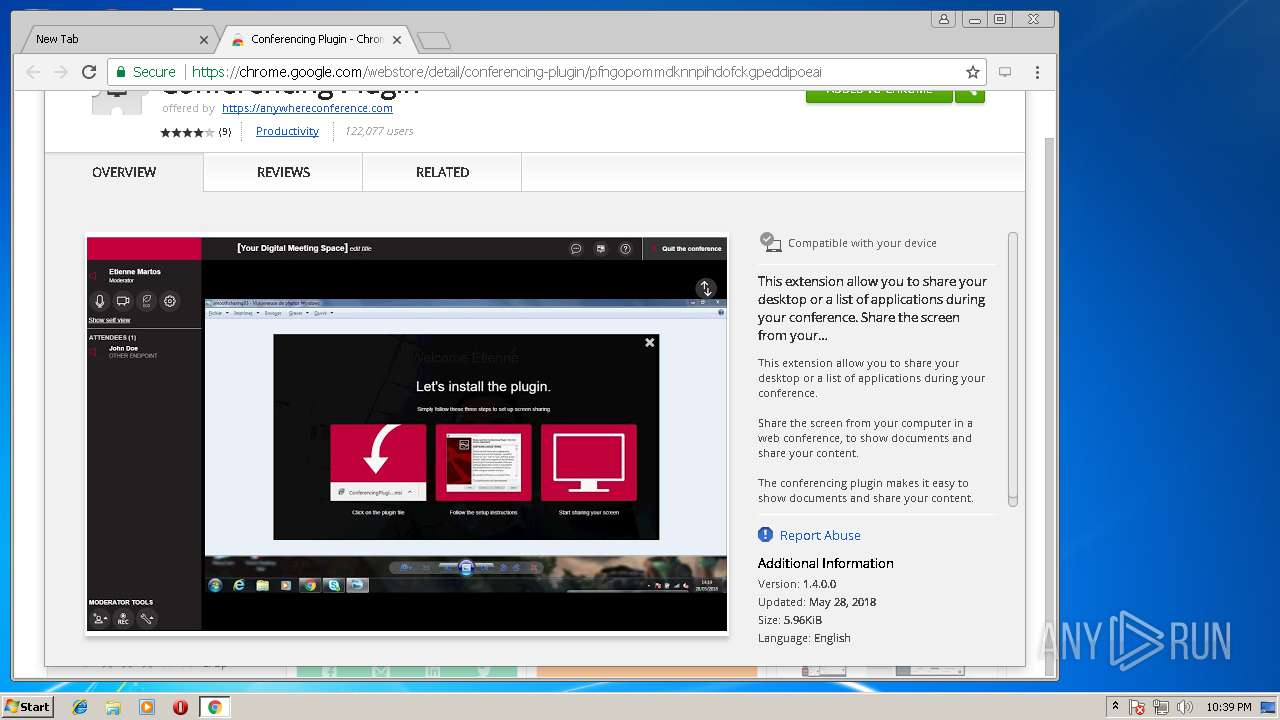
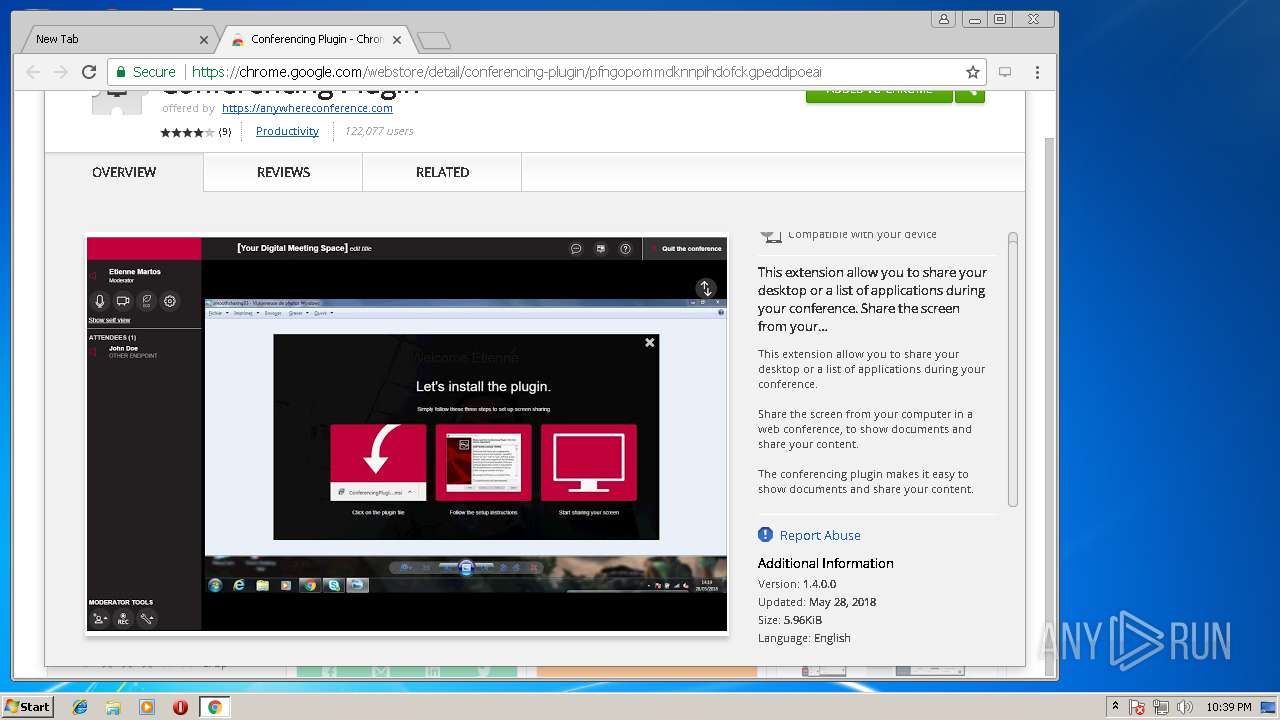
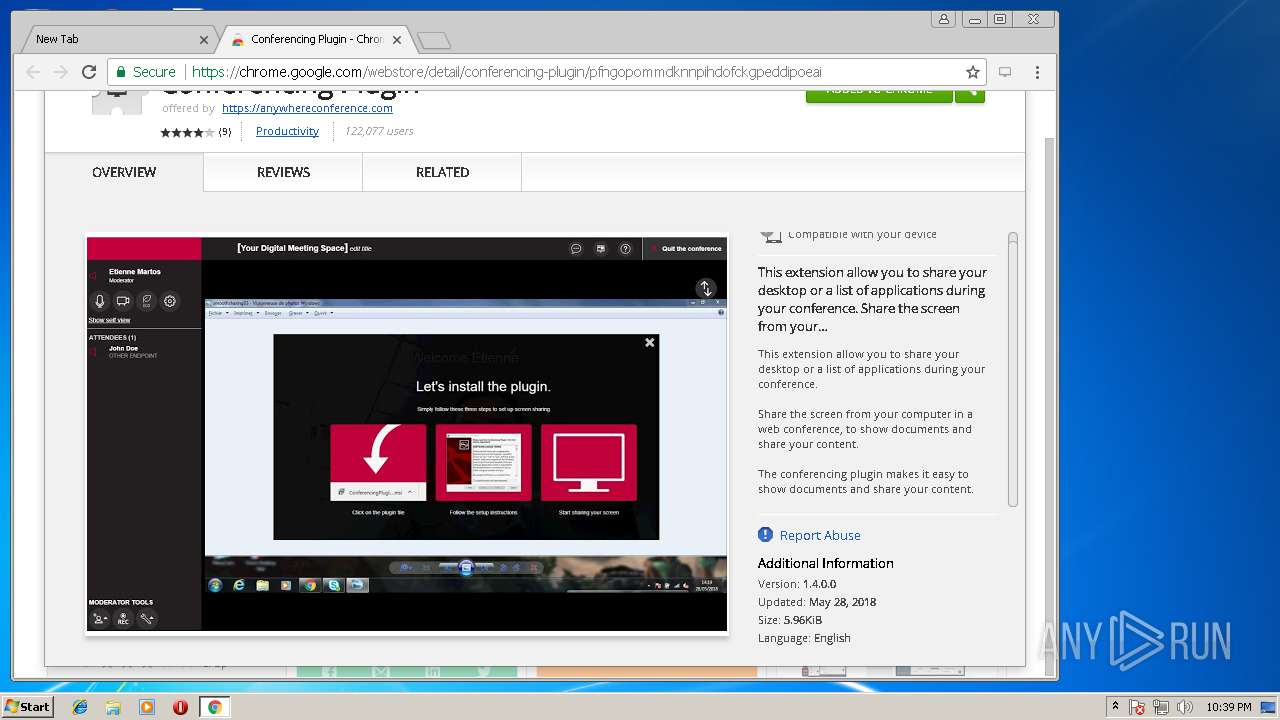
Modifies files in Chrome extension folder
- chrome.exe (PID: 784)
INFO
Dropped object may contain URL's
- ConferencingPluginSetup.exe (PID: 2936)
- ConferencingPluginSetup.exe (PID: 3564)
- ConferencingPluginSetup.exe (PID: 1336)
- chrome.exe (PID: 784)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 776)
- msiexec.exe (PID: 1088)
Low-level read access rights to disk partition
- vssvc.exe (PID: 960)
Creates a software uninstall entry
- msiexec.exe (PID: 1088)
Reads settings of System Certificates
- chrome.exe (PID: 784)
Application launched itself
- chrome.exe (PID: 784)
Creates files in the program directory
- msiexec.exe (PID: 1088)
Creates or modifies windows services
- vssvc.exe (PID: 960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:18 23:00:38+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.11 |
| CodeSize: | 301568 |
| InitializedDataSize: | 160768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e2a6 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.10.16.0 |
| ProductVersionNumber: | 7.10.16.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Conferencing Plugin |
| FileDescription: | Conferencing Plugin 7.10.16.0 |
| FileVersion: | 7.10.16.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Conferencing Plugin. All rights reserved. |
| OriginalFileName: | ConferencingPluginSetup.exe |
| ProductName: | Conferencing Plugin 7.10.16.0 |
| ProductVersion: | 7.10.16.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2017 22:00:38 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Conferencing Plugin |
| FileDescription: | Conferencing Plugin 7.10.16.0 |
| FileVersion: | 7.10.16.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Conferencing Plugin. All rights reserved. |
| OriginalFilename: | ConferencingPluginSetup.exe |
| ProductName: | Conferencing Plugin 7.10.16.0 |
| ProductVersion: | 7.10.16.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Nov-2017 22:00:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049937 | 0x00049A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57001 |
.rdata | 0x0004B000 | 0x0001ED60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11423 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15266 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.714974 |
.rsrc | 0x0006D000 | 0x00003AB8 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.5193 |
.reloc | 0x00071000 | 0x00003DFC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79434 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
64
Monitored processes
27
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot19" "" "" "61530dda3" "00000000" "000005B4" "000005C0" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1736,4420818745170170607,8564856934100663672,131072 --lang=en-US --utility-allowed-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir784_29559" --service-request-channel-token=D8026015AA3560272CBA03E85DEC1E0C --mojo-platform-channel-handle=2712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1736,4420818745170170607,8564856934100663672,131072 --lang=en-US --utility-allowed-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir784_8568" --service-request-channel-token=28A4871EB7D756A1A455C27595752CC0 --mojo-platform-channel-handle=2712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 960 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\AppData\Local\Temp\ConferencingPluginSetup.exe" | C:\Users\admin\AppData\Local\Temp\ConferencingPluginSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Conferencing Plugin Integrity Level: MEDIUM Description: Conferencing Plugin 7.10.16.0 Exit code: 0 Version: 7.10.16.0 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1736,4420818745170170607,8564856934100663672,131072 --service-pipe-token=76A61BB4FF933D889C0EFC91F8CBC1A7 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=76A61BB4FF933D889C0EFC91F8CBC1A7 --renderer-client-id=15 --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1736,4420818745170170607,8564856934100663672,131072 --lang=en-US --service-request-channel-token=03260349694D3514DDFCD41781C9AD0C --mojo-platform-channel-handle=2464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.91 Modules
| |||||||||||||||
| 2568 | regsvr32.exe /s "C:\Program Files\Conferencing Appshare Plugin\Internet Explorer\32\VersionChecker.dll" | C:\Windows\system32\regsvr32.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 863
Read events
1 133
Write events
704
Delete events
26
Modification events
| (PID) Process: | (2936) ConferencingPluginSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2936) ConferencingPluginSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (960) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AEF304AFF23BD401C003000018090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AEF304AFF23BD401C003000090090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AEF304AFF23BD401C0030000A8040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (960) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AEF304AFF23BD401C003000068030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3564) ConferencingPluginSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000007CCFBFAEF23BD401EC0D0000740C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3564) ConferencingPluginSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000007CCFBFAEF23BD401EC0D0000740C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3564) ConferencingPluginSetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 21 | |||
| (PID) Process: | (3564) ConferencingPluginSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000D0B9EAAEF23BD401EC0D0000740C0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
153
Suspicious files
54
Text files
312
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | ConferencingPluginSetup.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2936 | ConferencingPluginSetup.exe | C:\Users\admin\AppData\Local\Temp\{A037E680-5534-4CC8-9BC7-3643A8FBA018}\ConferencingPluginSetup.msi | — | |
MD5:— | SHA256:— | |||
| 3564 | ConferencingPluginSetup.exe | C:\ProgramData\Package Cache\.unverified\ConferencingPluginSetup.msi | — | |
MD5:— | SHA256:— | |||
| 3564 | ConferencingPluginSetup.exe | C:\ProgramData\Package Cache\{36404130-FC4C-4131-ABE2-1AE0A3CEE4F5}v7.10.16.0\ConferencingPluginSetup.msi | — | |
MD5:— | SHA256:— | |||
| 1088 | msiexec.exe | C:\Windows\Installer\4d4000.msi | — | |
MD5:— | SHA256:— | |||
| 960 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1088 | msiexec.exe | C:\Windows\Installer\MSI43A9.tmp | — | |
MD5:— | SHA256:— | |||
| 1088 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF5D6A25B99626CF73.TMP | — | |
MD5:— | SHA256:— | |||
| 2936 | ConferencingPluginSetup.exe | C:\Users\admin\AppData\Local\Temp\{A037E680-5534-4CC8-9BC7-3643A8FBA018}\.be\ConferencingPluginSetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3564 | ConferencingPluginSetup.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
35
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
784 | chrome.exe | GET | 200 | 74.125.97.76:80 | http://r7---sn-q0c7dn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGZmQUFWZDVabUx2XzNSUmJXZUVFZWhQQQ/6317.1002.0.5_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=81.17.242.229&mm=28&mn=sn-q0c7dn7s&ms=nvh&mt=1535145839&mv=u&pl=20&shardbypass=yes | US | crx | 877 Kb | whitelisted |
784 | chrome.exe | GET | 200 | 172.217.168.46:80 | http://clients1.google.com/tools/pso/ping?as=chrome&brand=GCEA&pid=&hl=en&events=C1I,C2I,C7I,C1S,C7S&rep=2&rlz=C1:,C2:,C7:&id=4E3014F88A1776A95D57E2AE3211A742FF35E455C4BA364784 | US | text | 132 b | whitelisted |
784 | chrome.exe | GET | 302 | 216.58.215.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGZmQUFWZDVabUx2XzNSUmJXZUVFZWhQQQ/6317.1002.0.5_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 505 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
784 | chrome.exe | 172.217.168.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 172.217.168.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 216.58.215.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 216.58.215.238:80 | clients2.google.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 216.58.214.42:443 | www.googleapis.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 74.125.97.76:80 | r7---sn-q0c7dn7s.gvt1.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 216.58.215.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 172.217.168.36:443 | www.google.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 172.217.168.8:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
784 | chrome.exe | 108.177.126.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
www.google.de |
| whitelisted |
apis.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
www.googleapis.com |
| whitelisted |