| File name: | rufus-4.7.exe |
| Full analysis: | https://app.any.run/tasks/67395150-3c34-44ea-b4e3-1fb90f684cdb |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2025, 20:50:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 3 sections |
| MD5: | F052ACD38A010B6A1FFA26FDC229A229 |
| SHA1: | CA1D781015AB17E7B912A7B57A559E66654ED2BF |
| SHA256: | 45777D818FC9BA187BCC7B930583764130EA71100FD9E3C66D4A7143BDBCE4C5 |
| SSDEEP: | 49152:FmEbbn9IKmqiuIlrDWqectImMaj5nY78CdrD4f7a0pPhfJEsgy8GZBLvHhPSJB9M:FHb5IK44qDtzMaBY7Vo7pJlgmBj5SgsA |
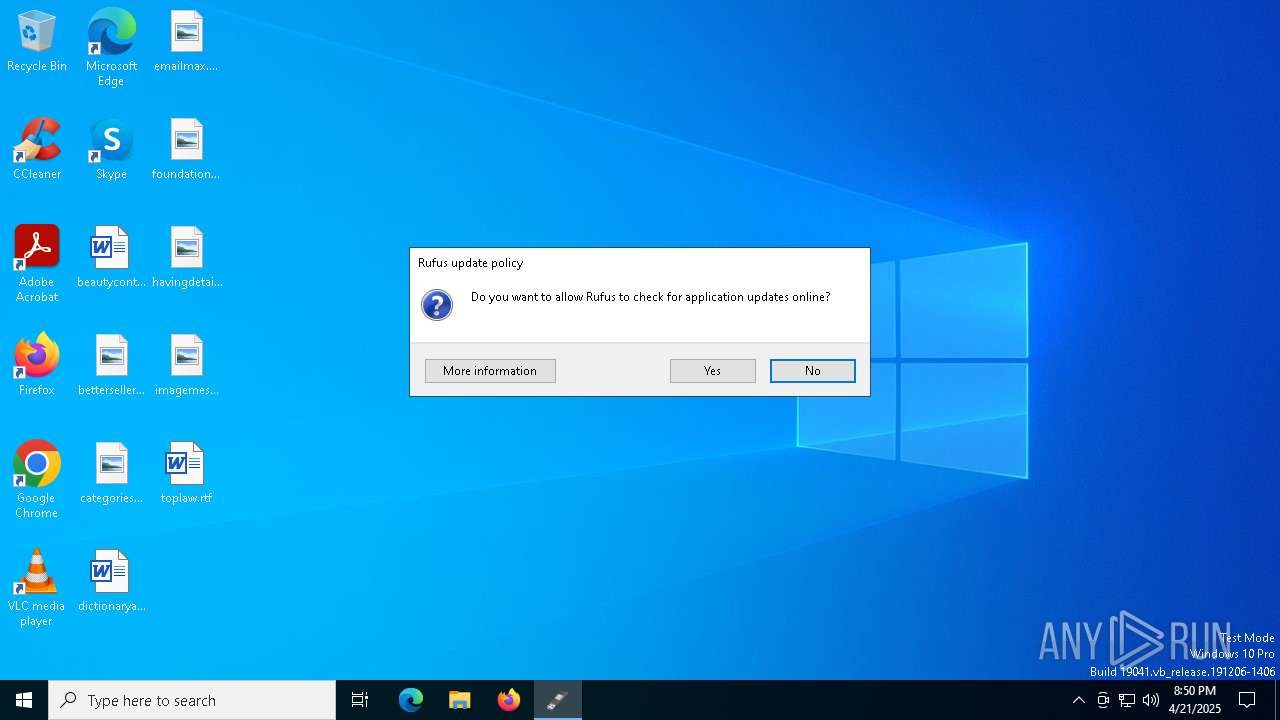
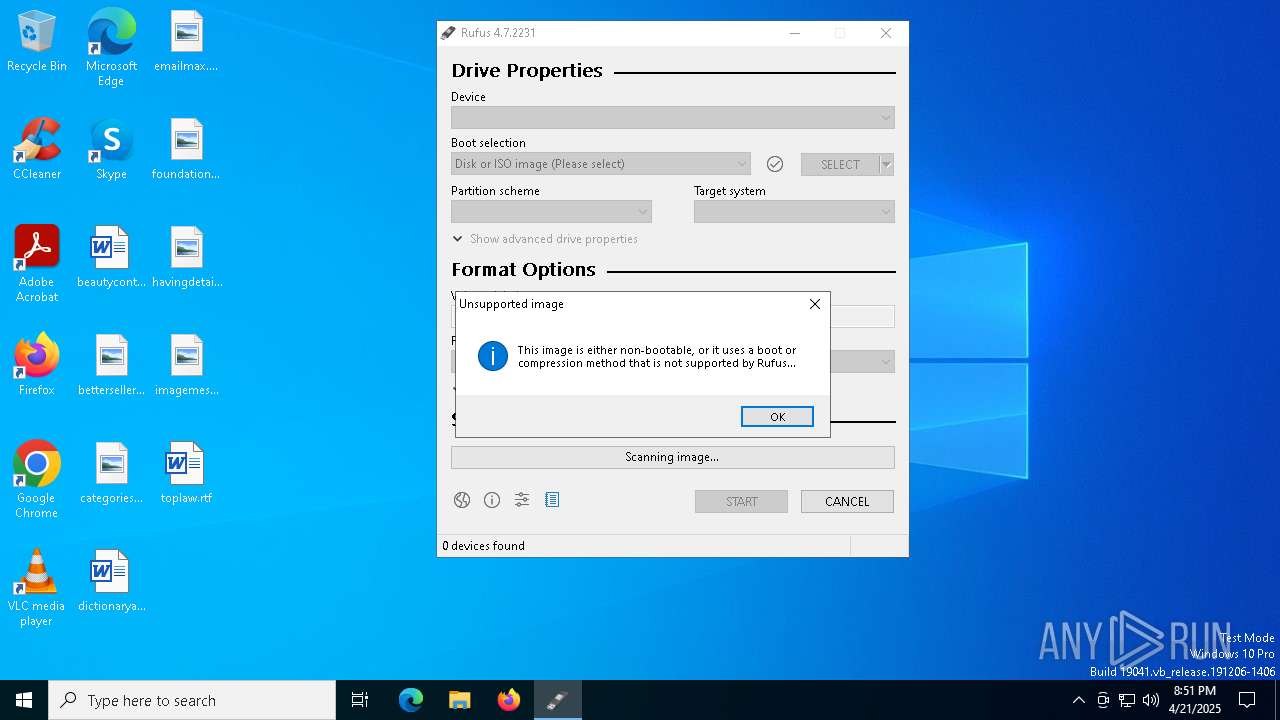
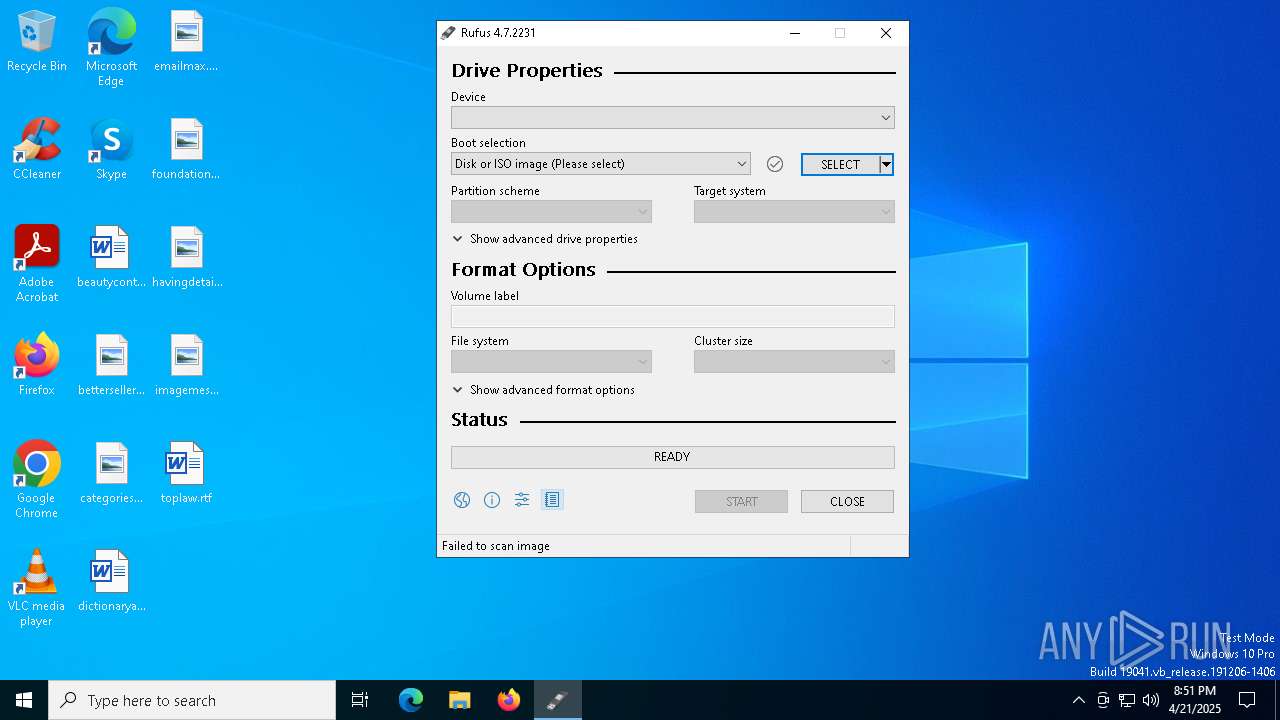
MALICIOUS
Changes the Windows auto-update feature
- rufus-4.7.exe (PID: 6964)
SUSPICIOUS
Executes as Windows Service
- vds.exe (PID: 5280)
- vds.exe (PID: 7844)
Reads security settings of Internet Explorer
- rufus-4.7.exe (PID: 6964)
Creates file in the systems drive root
- rufus-4.7.exe (PID: 6964)
INFO
Checks supported languages
- rufus-4.7.exe (PID: 6964)
Reads the computer name
- rufus-4.7.exe (PID: 6964)
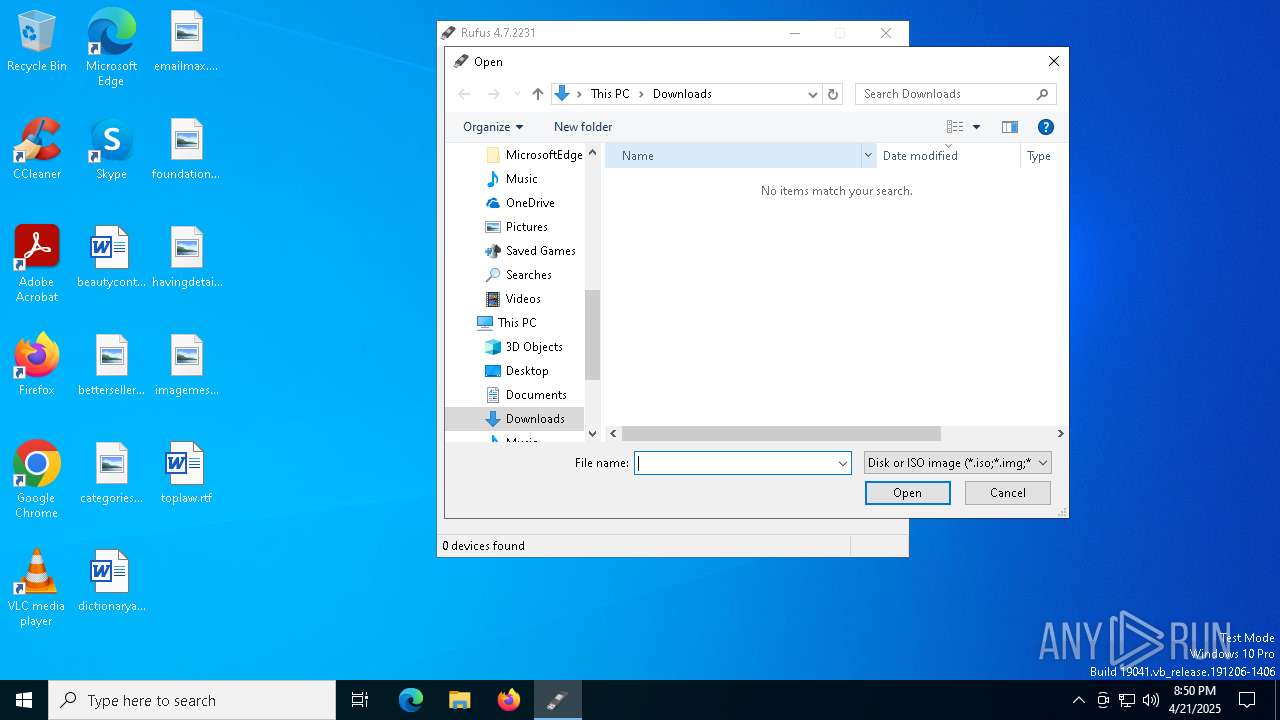
Process checks whether UAC notifications are on
- rufus-4.7.exe (PID: 6964)
Create files in a temporary directory
- rufus-4.7.exe (PID: 6964)
Reads the machine GUID from the registry
- rufus-4.7.exe (PID: 6964)
Checks proxy server information
- rufus-4.7.exe (PID: 6964)
- slui.exe (PID: 7792)
Creates files or folders in the user directory
- rufus-4.7.exe (PID: 6964)
Reads the software policy settings
- rufus-4.7.exe (PID: 6964)
- slui.exe (PID: 4620)
- slui.exe (PID: 7792)
UPX packer has been detected
- rufus-4.7.exe (PID: 6964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (87.1) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.4) |
| .exe | | | DOS Executable Generic (6.4) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:09 10:15:32+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.44 |
| CodeSize: | 1634304 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 3145728 |
| EntryPoint: | 0x48ea30 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
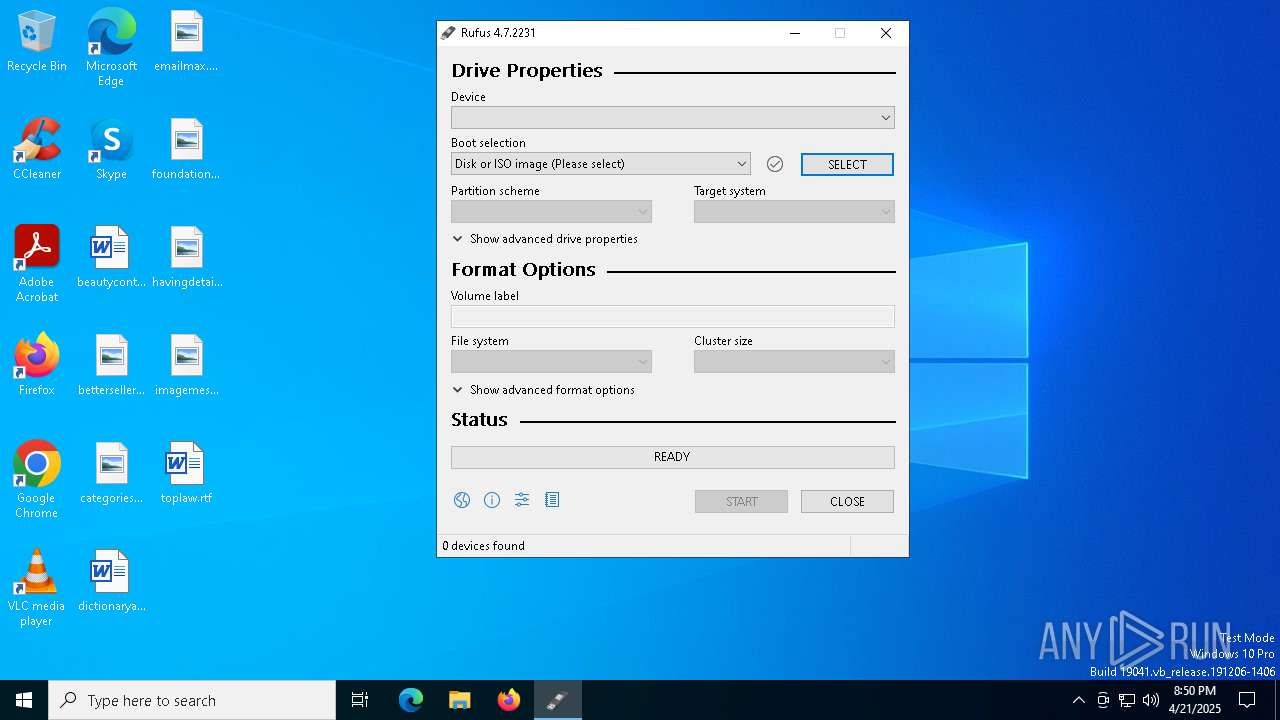
| FileVersionNumber: | 4.7.2231.0 |
| ProductVersionNumber: | 4.7.2231.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | https://rufus.ie |
| CompanyName: | Akeo Consulting |
| FileDescription: | Rufus |
| FileVersion: | 4.7.2231 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2025 Pete Batard (GPL v3) |
| LegalTrademarks: | https://www.gnu.org/licenses/gpl-3.0.html |
| OriginalFileName: | rufus-4.7.exe |
| ProductName: | Rufus |
| ProductVersion: | 4.7.2231 |
Total processes
144
Monitored processes
8
Malicious processes
0
Suspicious processes
1
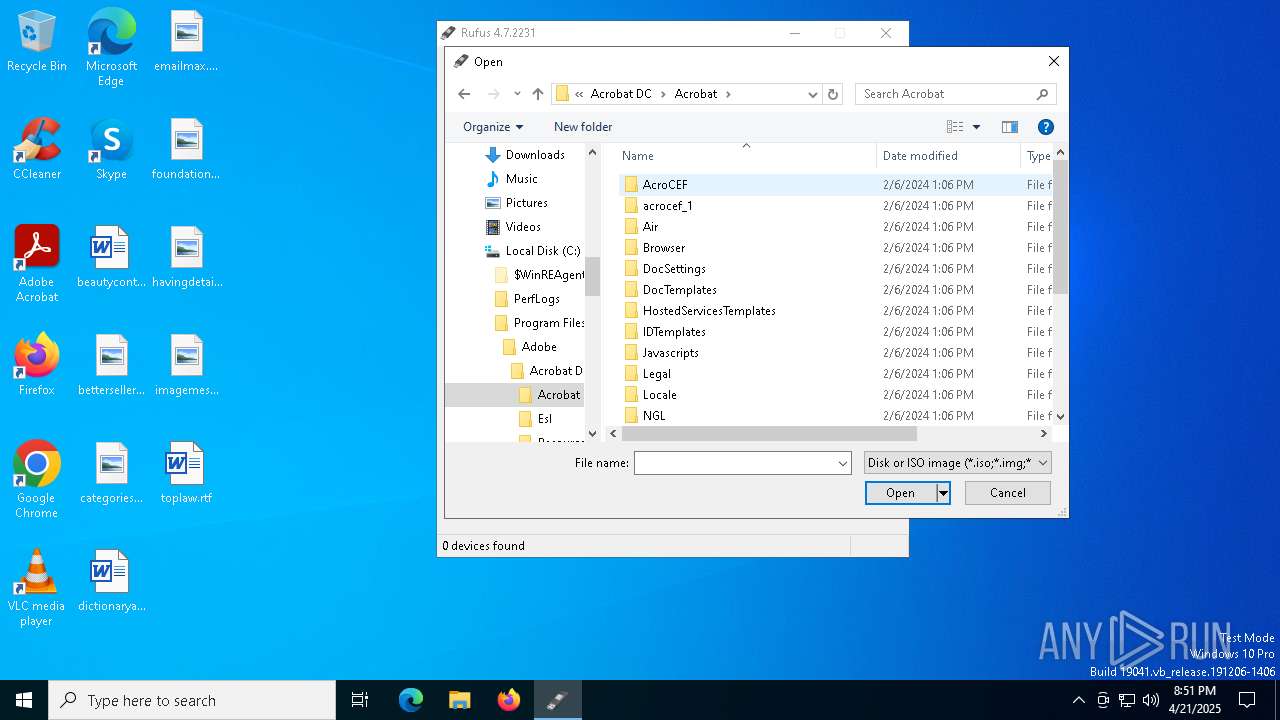
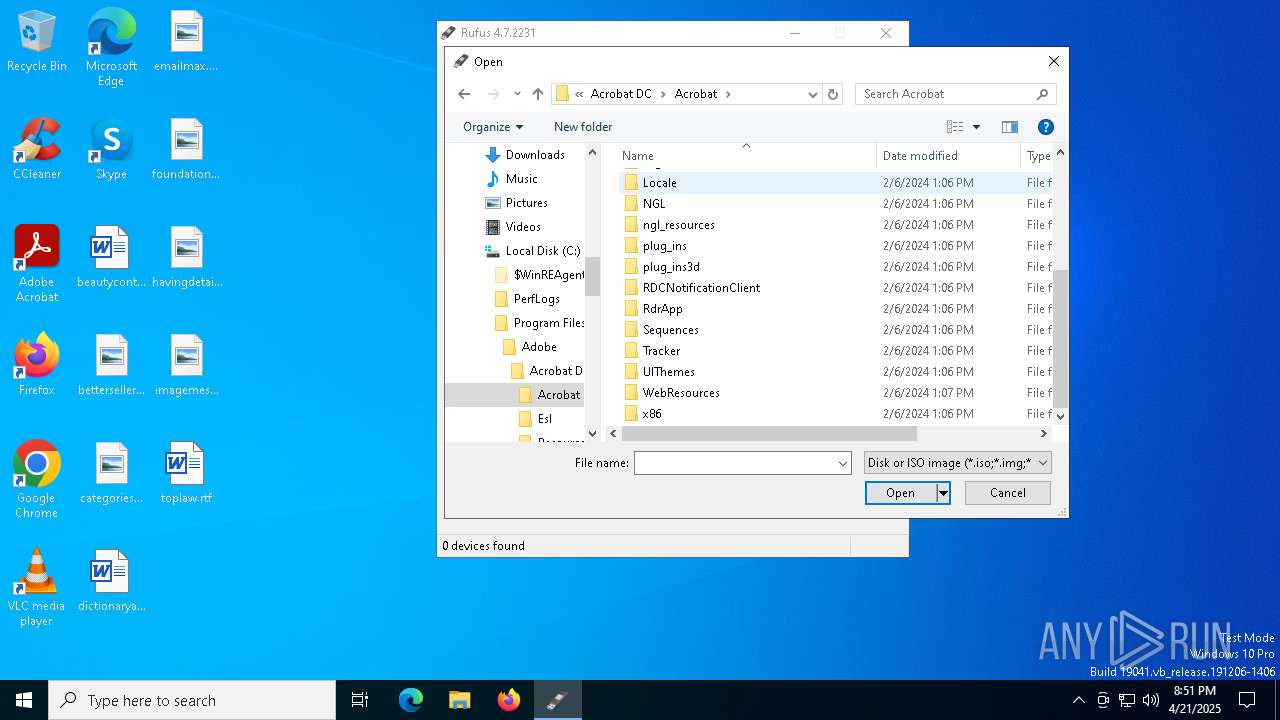
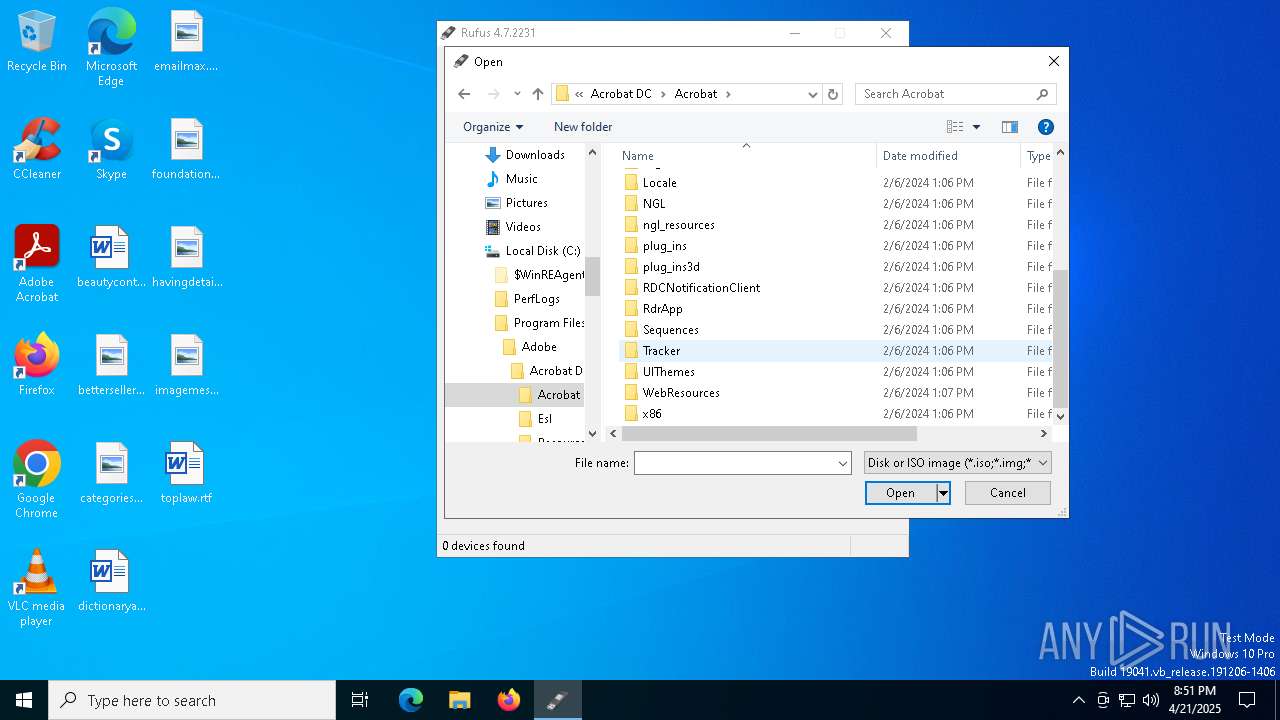
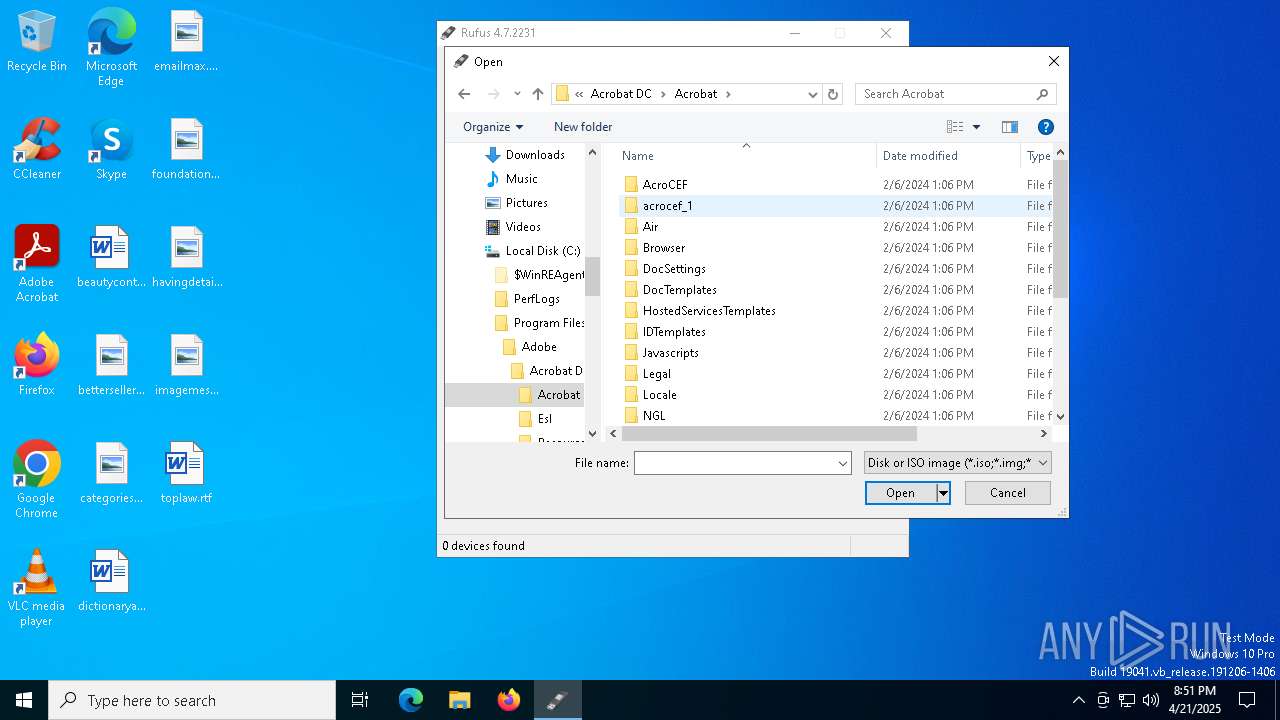
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1676 | "C:\Users\admin\AppData\Local\Temp\rufus-4.7.exe" | C:\Users\admin\AppData\Local\Temp\rufus-4.7.exe | — | explorer.exe | |||||||||||
User: admin Company: Akeo Consulting Integrity Level: MEDIUM Description: Rufus Exit code: 3221226540 Version: 4.7.2231 Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5280 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 258 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6644 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6964 | "C:\Users\admin\AppData\Local\Temp\rufus-4.7.exe" | C:\Users\admin\AppData\Local\Temp\rufus-4.7.exe | explorer.exe | ||||||||||||
User: admin Company: Akeo Consulting Integrity Level: HIGH Description: Rufus Version: 4.7.2231 Modules
| |||||||||||||||
| 7792 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7844 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 929
Read events
15 071
Write events
784
Delete events
74
Modification events
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\AppHVSI |
| Operation: | write | Name: | AllowAppHVSI_ProviderSet |
Value: 0 | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UpdateDefault |
Value: 0 | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\Network Connections |
| Operation: | write | Name: | NC_DoNotShowLocalOnlyIcon |
Value: 1 | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\Windows Feeds |
| Operation: | write | Name: | EnableFeeds |
Value: 0 | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUStatusServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | UpdateServiceUrlAlternate |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | **del.FillEmptyContentUrls |
Value: | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | UseWUServer |
Value: 1 | |||
| (PID) Process: | (6964) rufus-4.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{8390C8B5-4D4A-44CC-9CEB-24182BB8AAC0}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | NoAutoUpdate |
Value: 0 | |||
Executable files
4
Suspicious files
16
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 6964 | rufus-4.7.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:3D89F23265C9E30A0CF055C3EB4D637C | SHA256:806582F6221C79BD4C7EACDC4B63E937CE247EEE2BA159F55C545CDFB2B1C25B | |||
| 6964 | rufus-4.7.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:0C014C71A70DC7758BFDC822E974F1F3 | SHA256:8EBD915268E16B55A3ABDE6F612363576FAB5DF656F955D672CCE8889C5FF9CA | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:31136A233AA66949135DD17C28FAF8AD | SHA256:30EF1E4C166AB0C17D389D7A6A2CF8CA4441C2E6AF29E0F00C73CF2CF1C5EDC5 | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:D06E4D85C8C9D9D1EA0CFA6BEDBDD7AF | SHA256:0B6F62FB10638C8EC2EF069D9421CAFEF677D0418306FA9ABED18A7AB06A83B5 | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8CFF94A6502E24DC82E1FBEB7044EEA | binary | |
MD5:DEE3802BFD448EB422486D8CF01902C0 | SHA256:B84331DFDD49F20D175F6ACA23881AD5A35AE9C1124930A20B712F63F9B91881 | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:3090DB690943884B914951284AD8579D | SHA256:CAB887218D5F8384712DAF711151D232065A0B97F6190BED3139E44515728C94 | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:212661907056573B8C64BB3A162119D6 | SHA256:7C776F77142D2E25E4CB2BD4239F80AEB64E2F37C8537C4BAC59C1CCEE82BC8B | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:8E9F8A68DEA2BB51D6DC782004628C01 | SHA256:C998A53AA905554A41D125DF38593A17575FD2762DFAAEDBC5DD4978731593DC | |||
| 6964 | rufus-4.7.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\commits[1].json | text | |
MD5:7FCC9BB1BBBD63FFECD87193D0DC07E3 | SHA256:E7C7B317E8AD88F4C8FC3C9CED1F9CFBCAB19B806A959AB7C6EB5CF53550219D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
34
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6964 | rufus-4.7.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
7536 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7536 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6964 | rufus-4.7.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CECoW9cIBGAf3CpJj3Tw5qfI%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6964 | rufus-4.7.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2196 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
rufus.ie |
| unknown |
x1.c.lencr.org |
| whitelisted |
github.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |