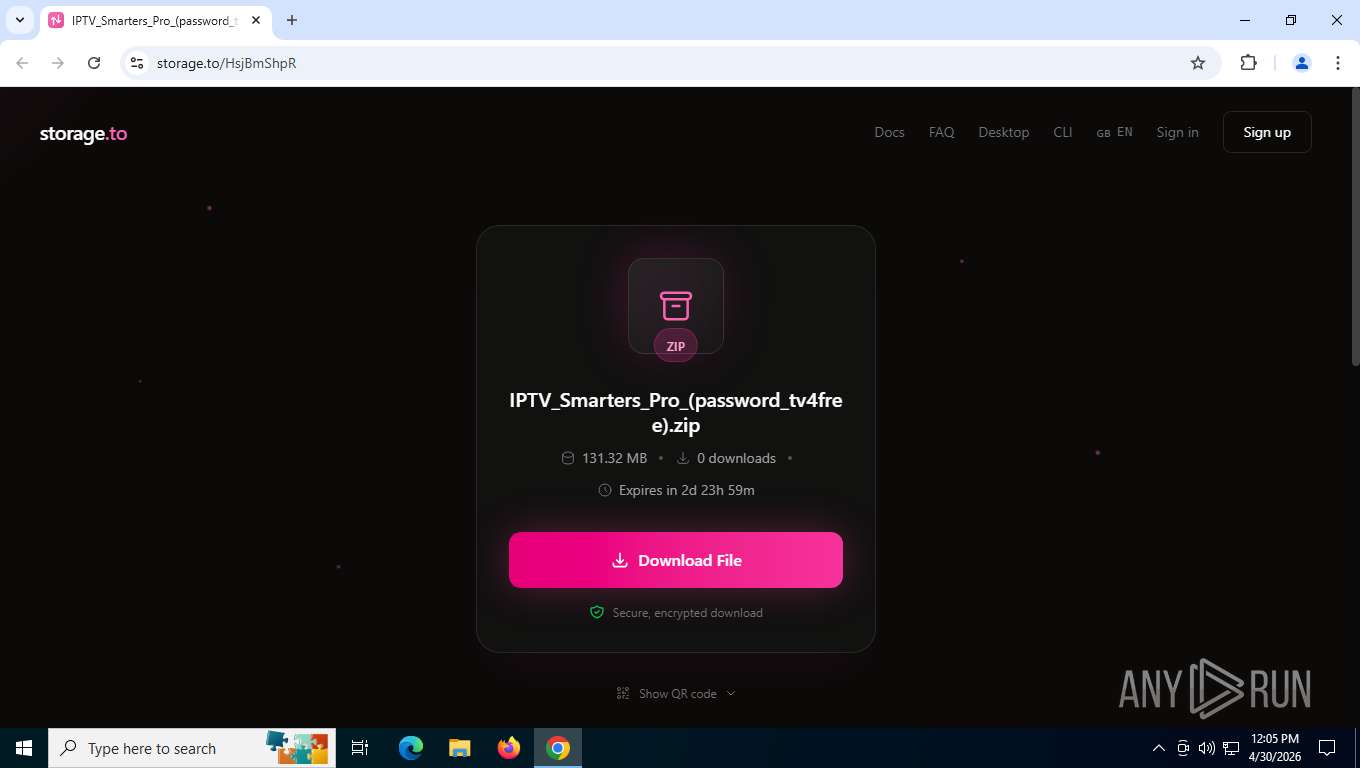
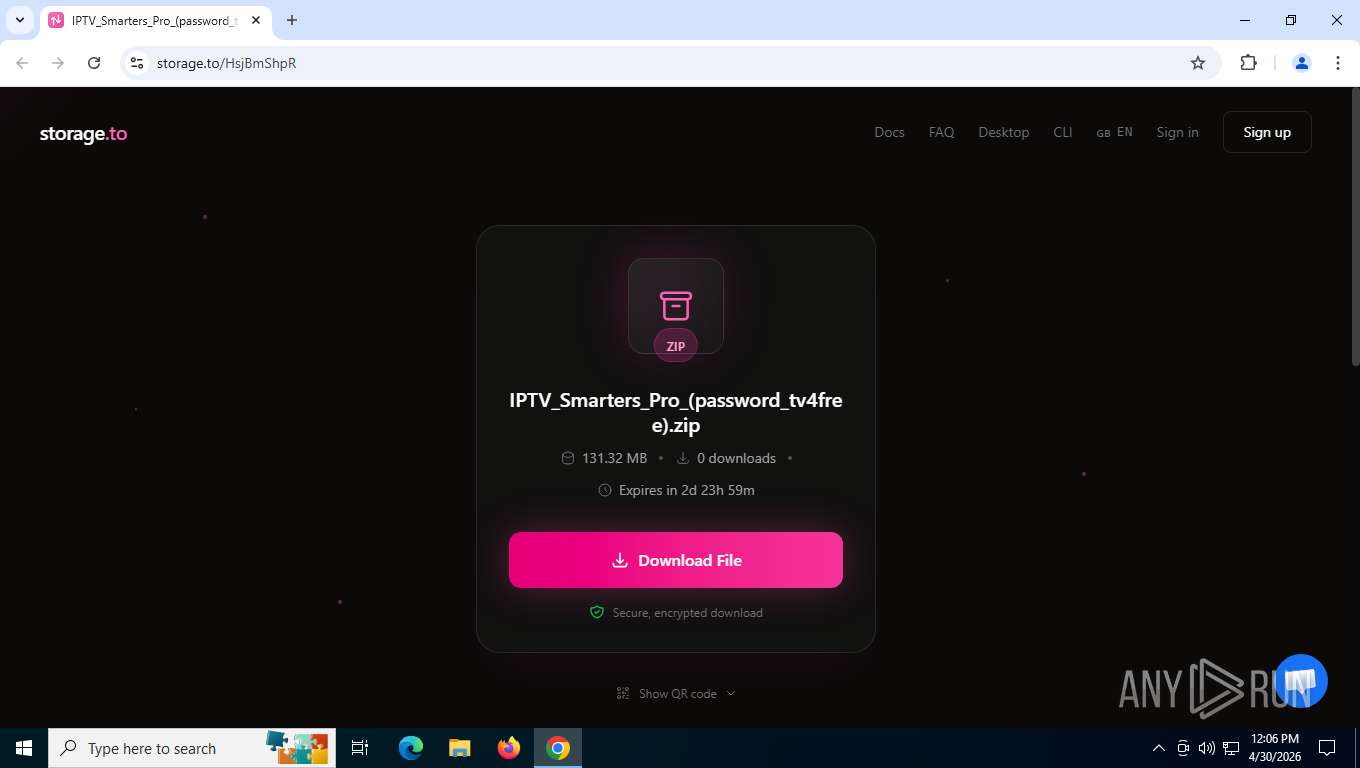
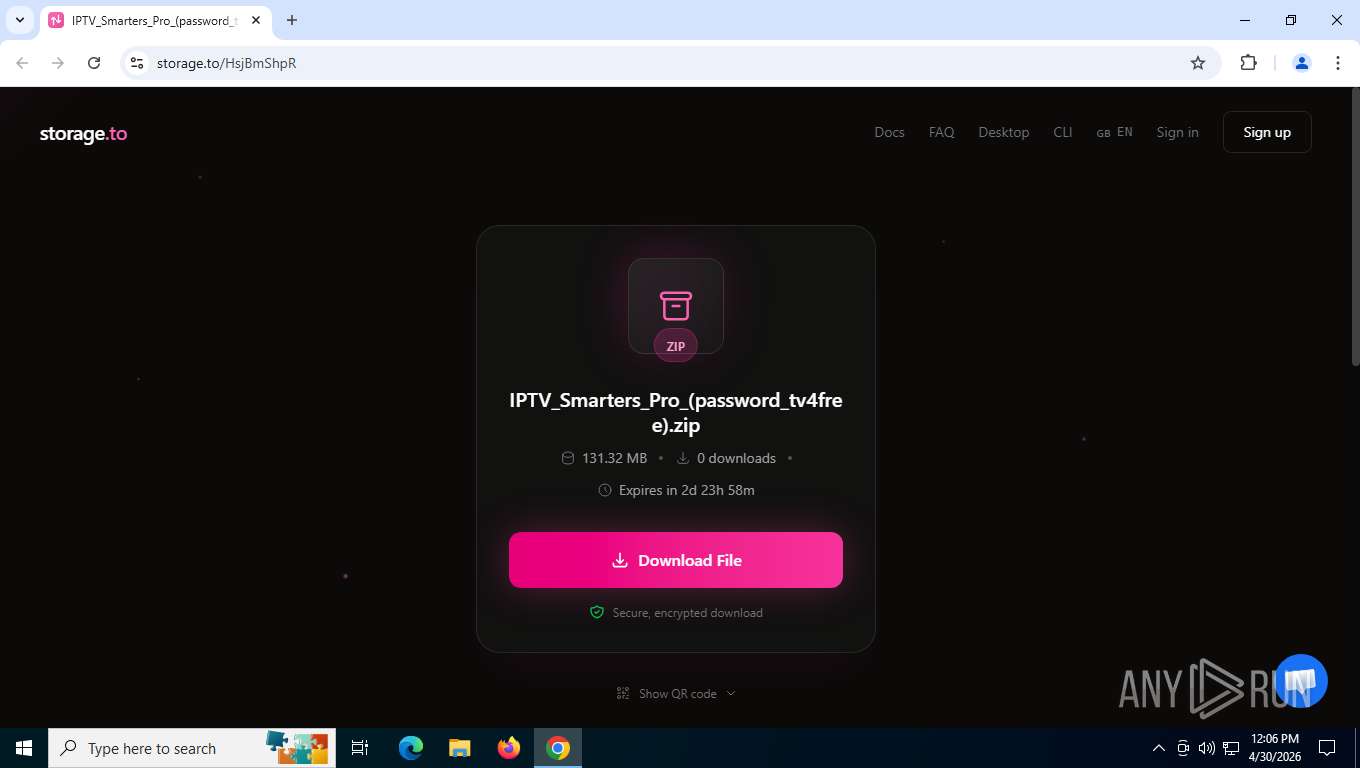
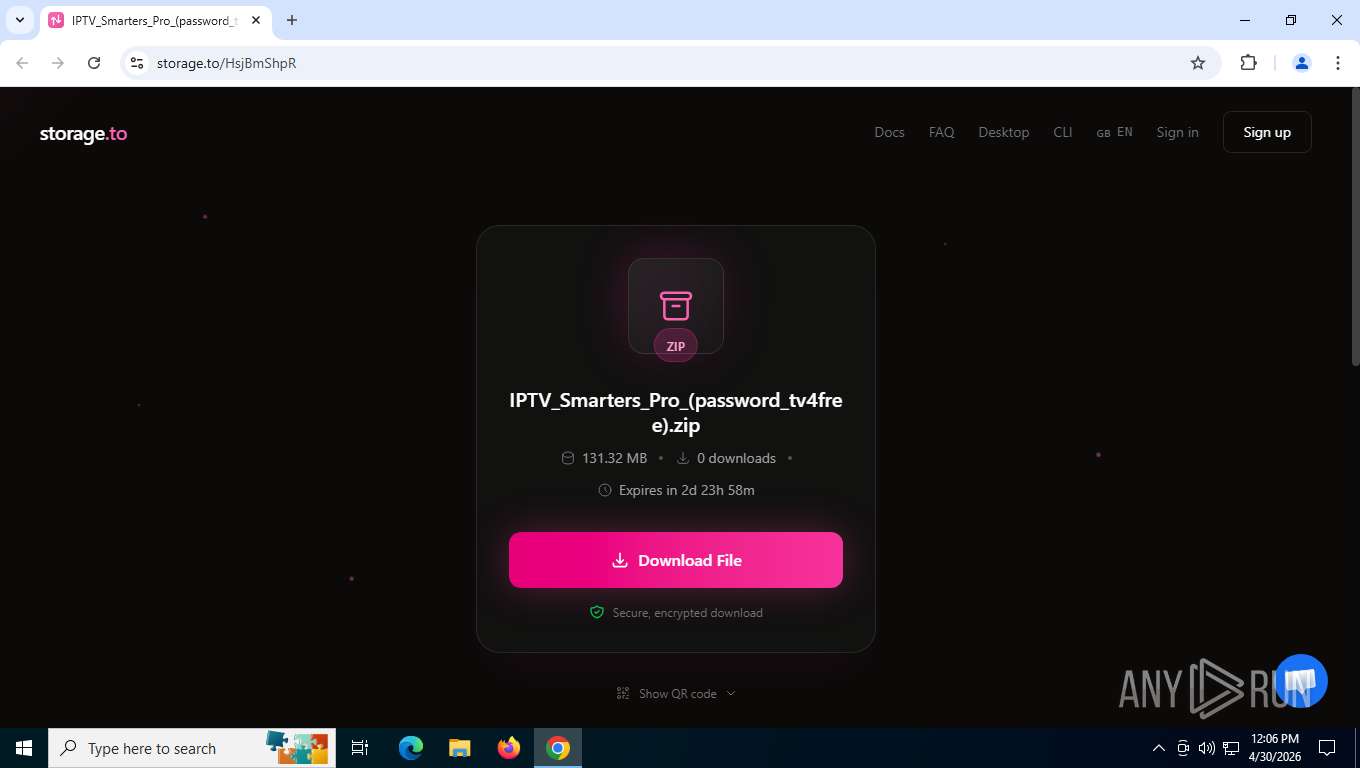
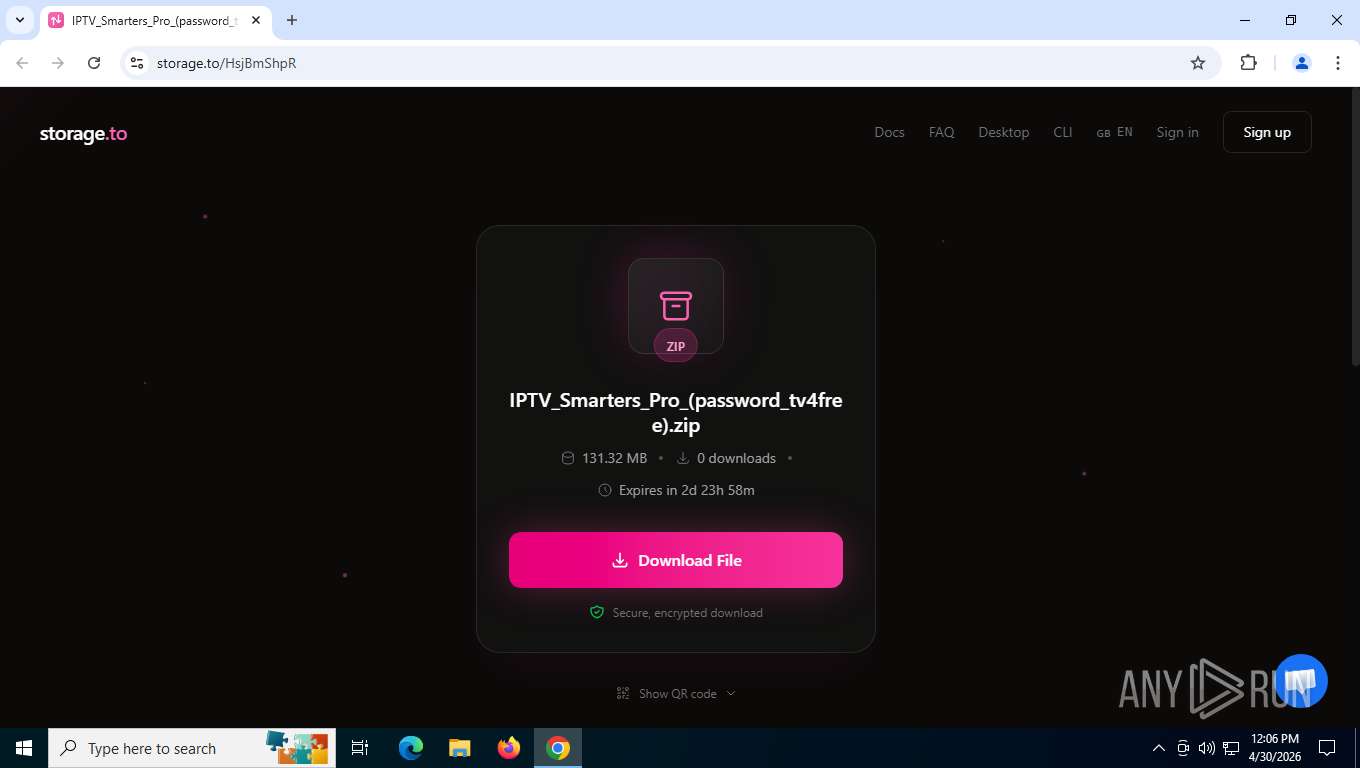
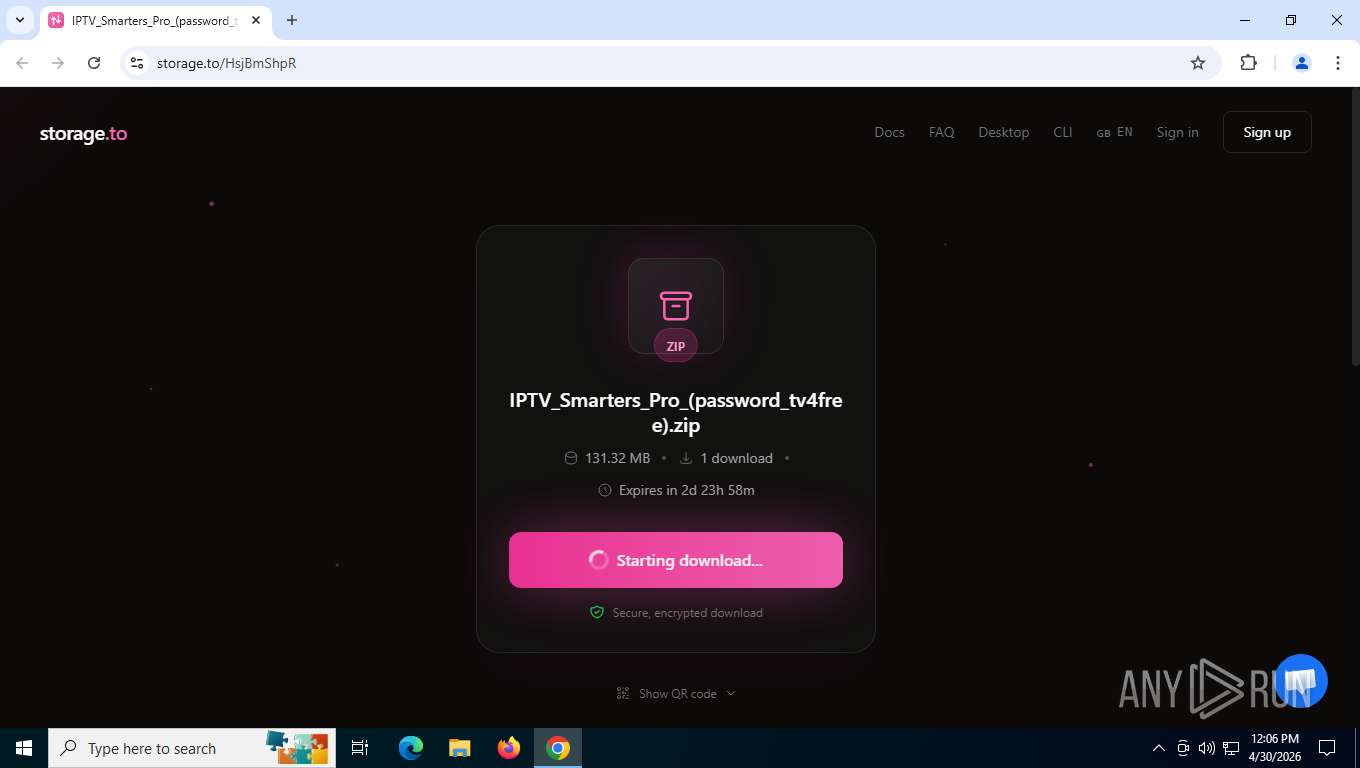
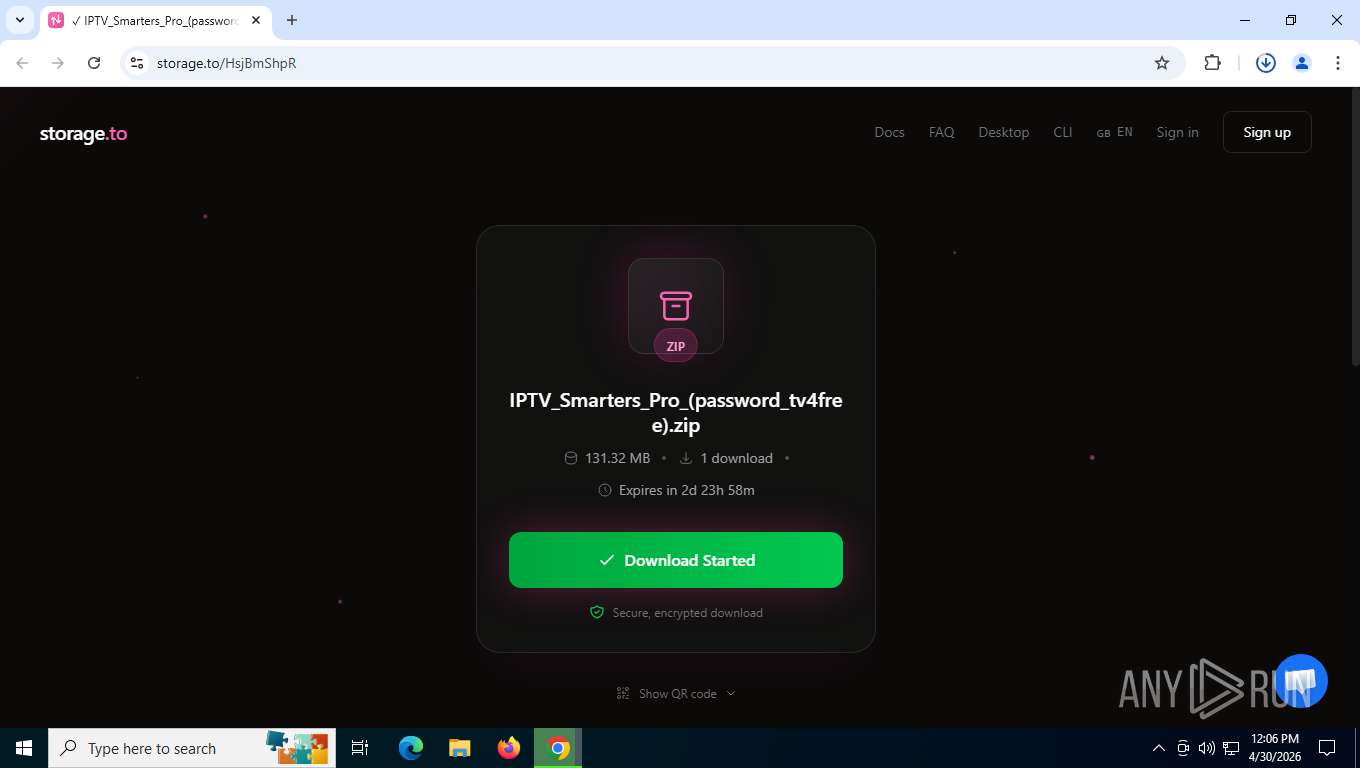
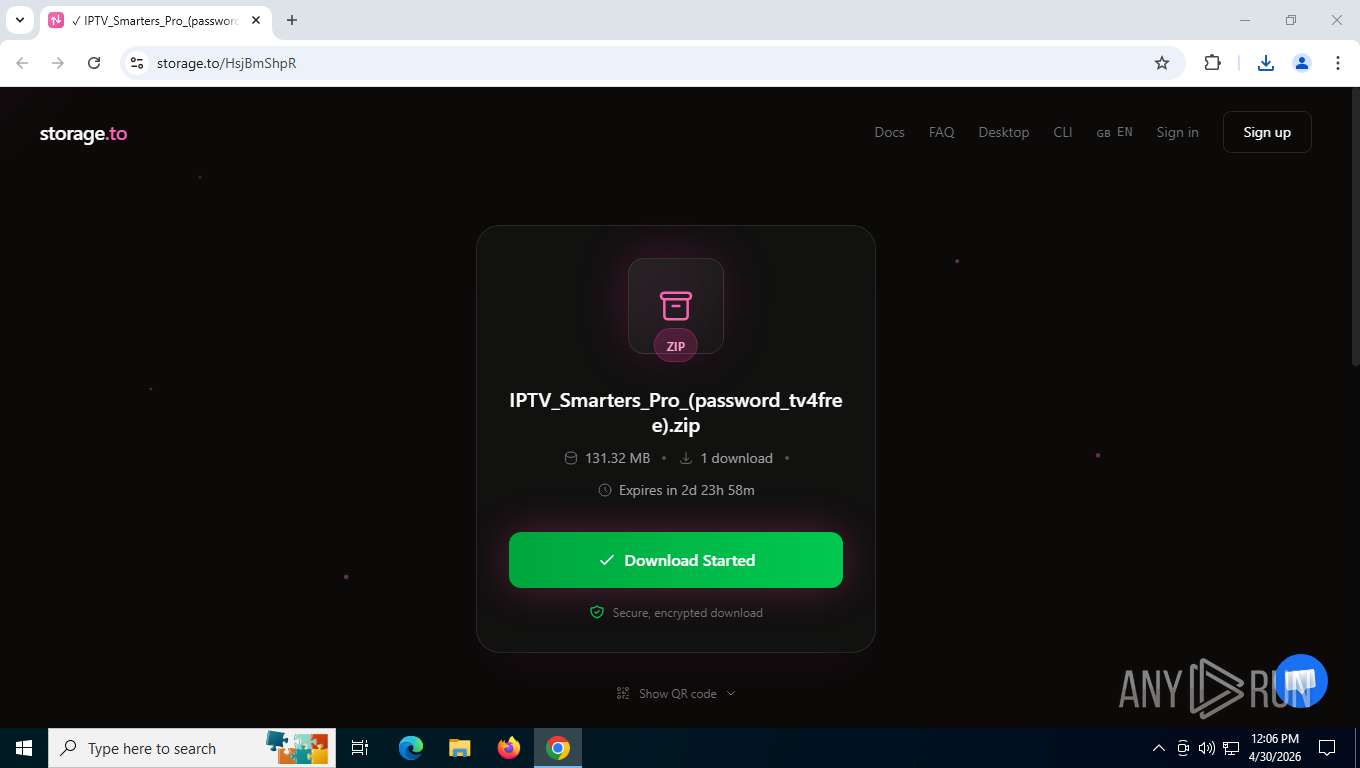
| URL: | https://storage.to/HsjBmShpR |
| Full analysis: | https://app.any.run/tasks/8088553b-dd31-4471-94d1-cafa05aeb457 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2026, 16:05:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BE571A45E956F478CA0C3DE757451FD7 |
| SHA1: | 1AE173F1753E7892A96EE086F2A115BBCB01B05B |
| SHA256: | 455A0753AEA8DD5BE0BB6BEE752B58B21BDE3D2357158BA34D302460C85D8965 |
| SSDEEP: | 3:N8cMECVKGnIqd:2cMpKwI4 |
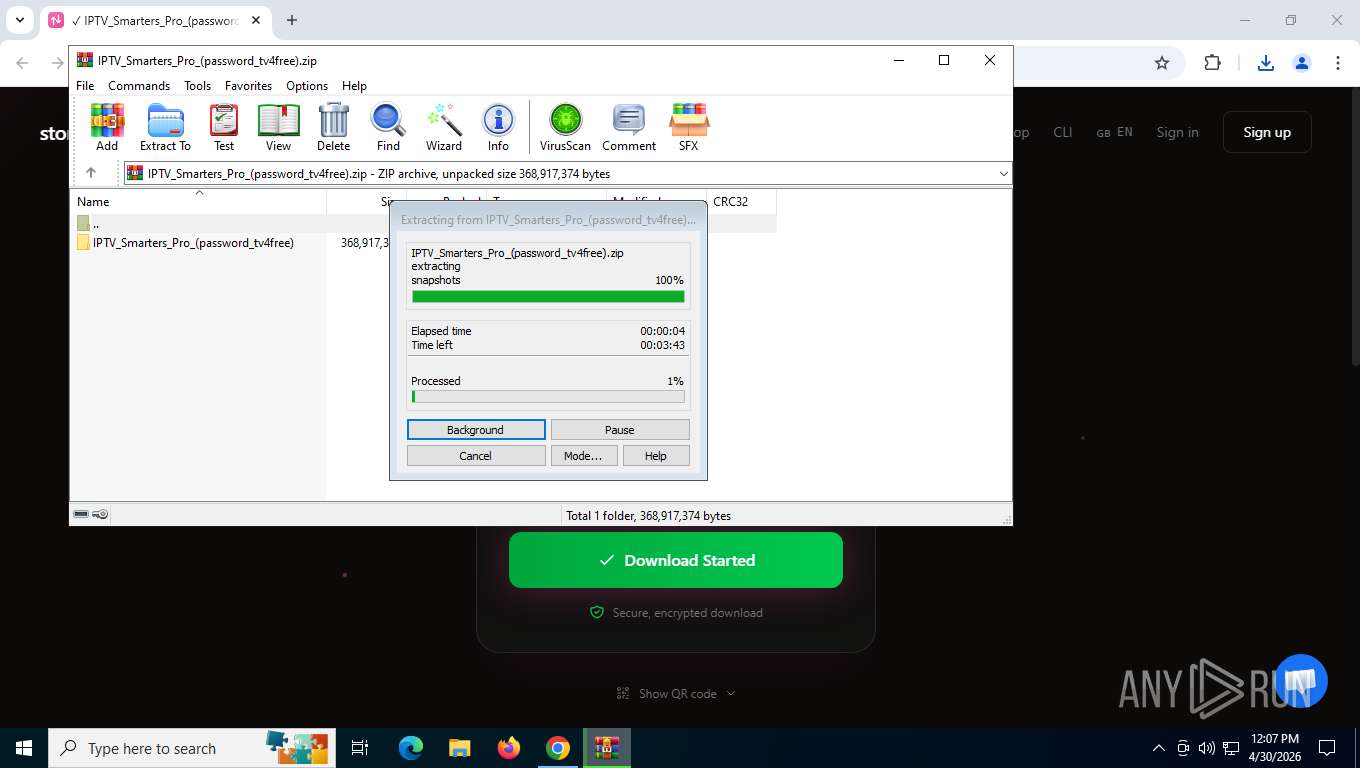
MALICIOUS
Executing a file with an untrusted certificate
- IPTVSmartersProSetup.exe (PID: 5548)
- IPTVSmartersProSetup.exe (PID: 7388)
- DismHost.exe (PID: 8932)
Loads dropped or rewritten executable
- MigRegDB.exe (PID: 6448)
- FileCoAuth.exe (PID: 8344)
- FileCoAuth.exe (PID: 8052)
- FileCoAuth.exe (PID: 9460)
SUSPICIOUS
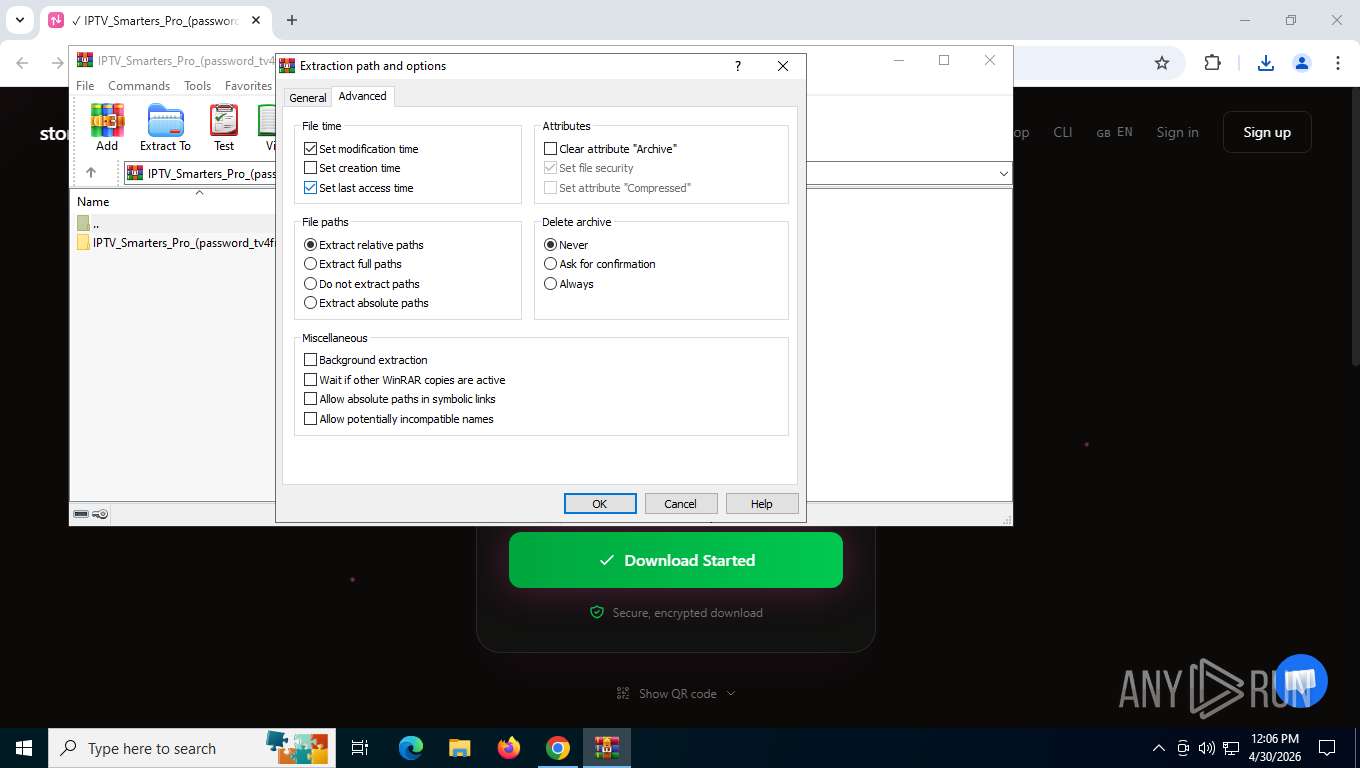
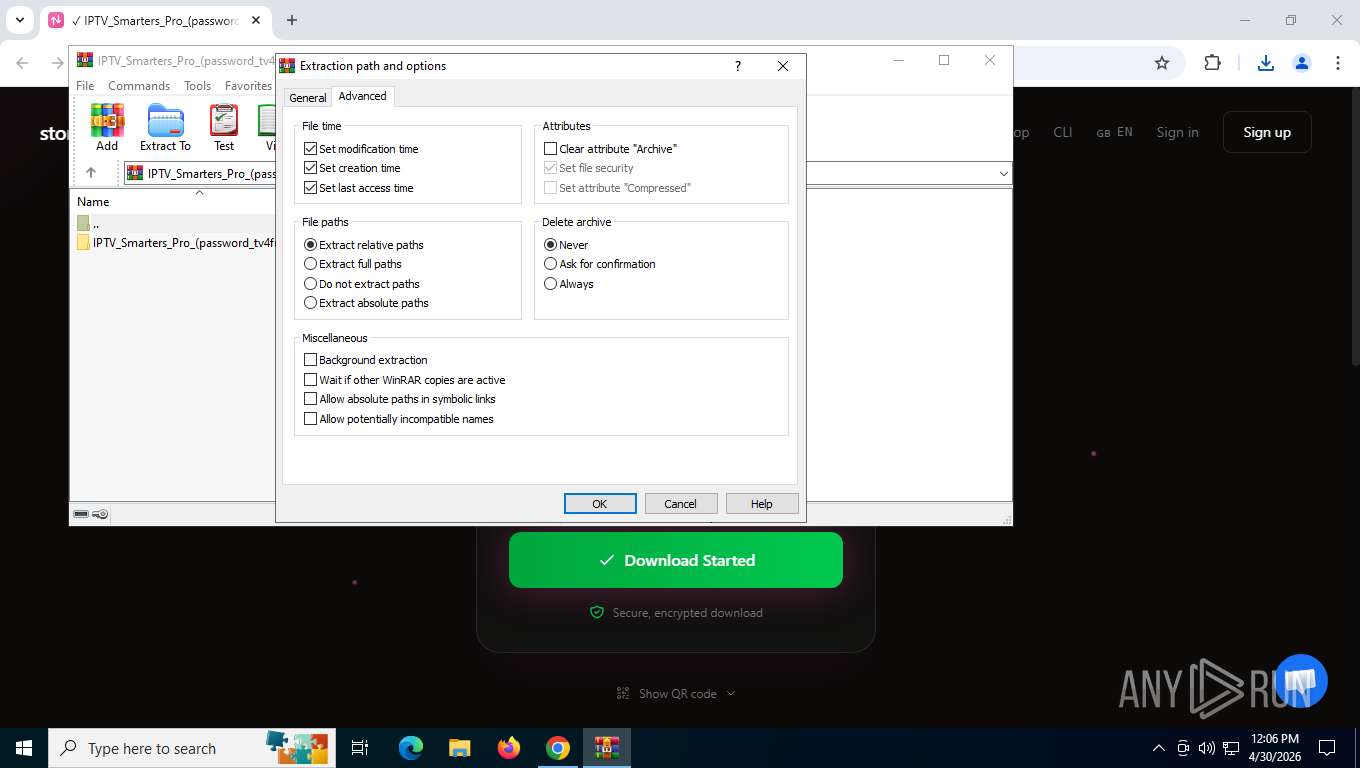
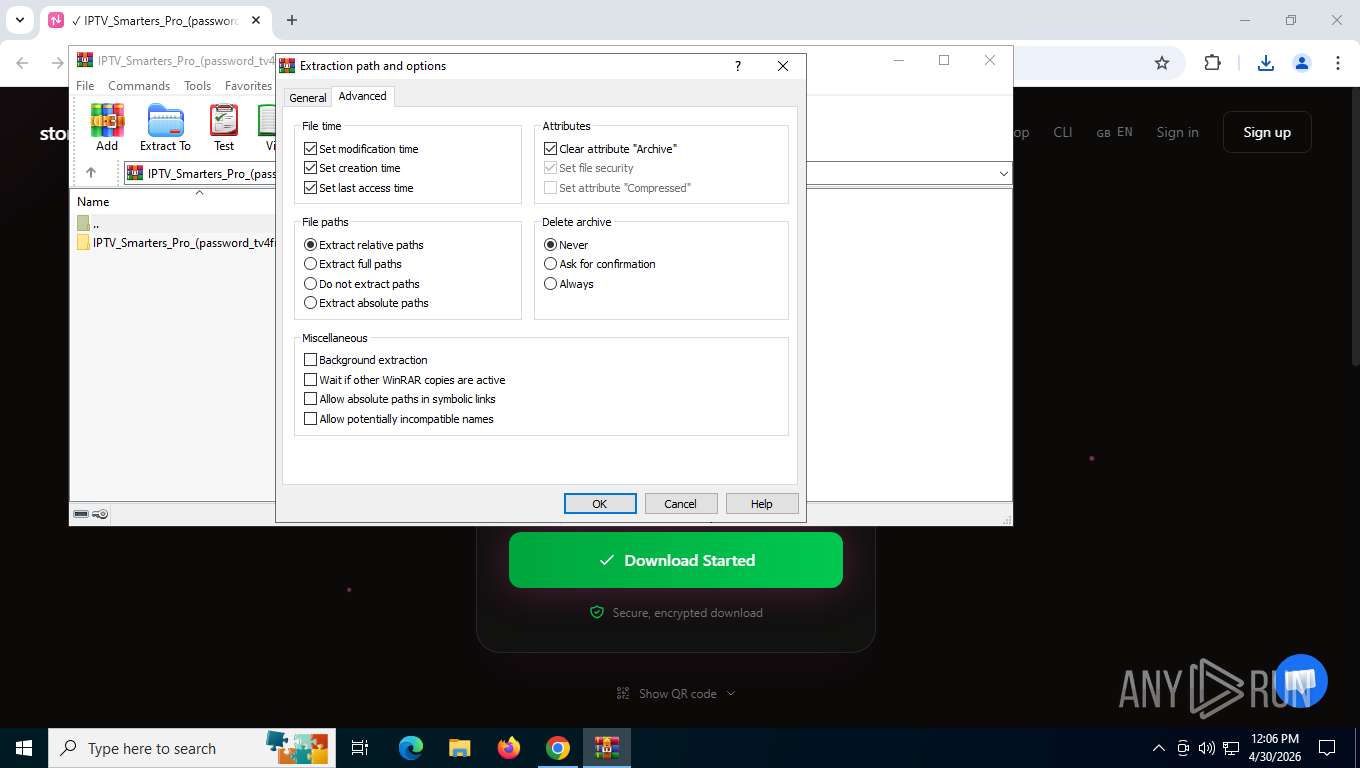
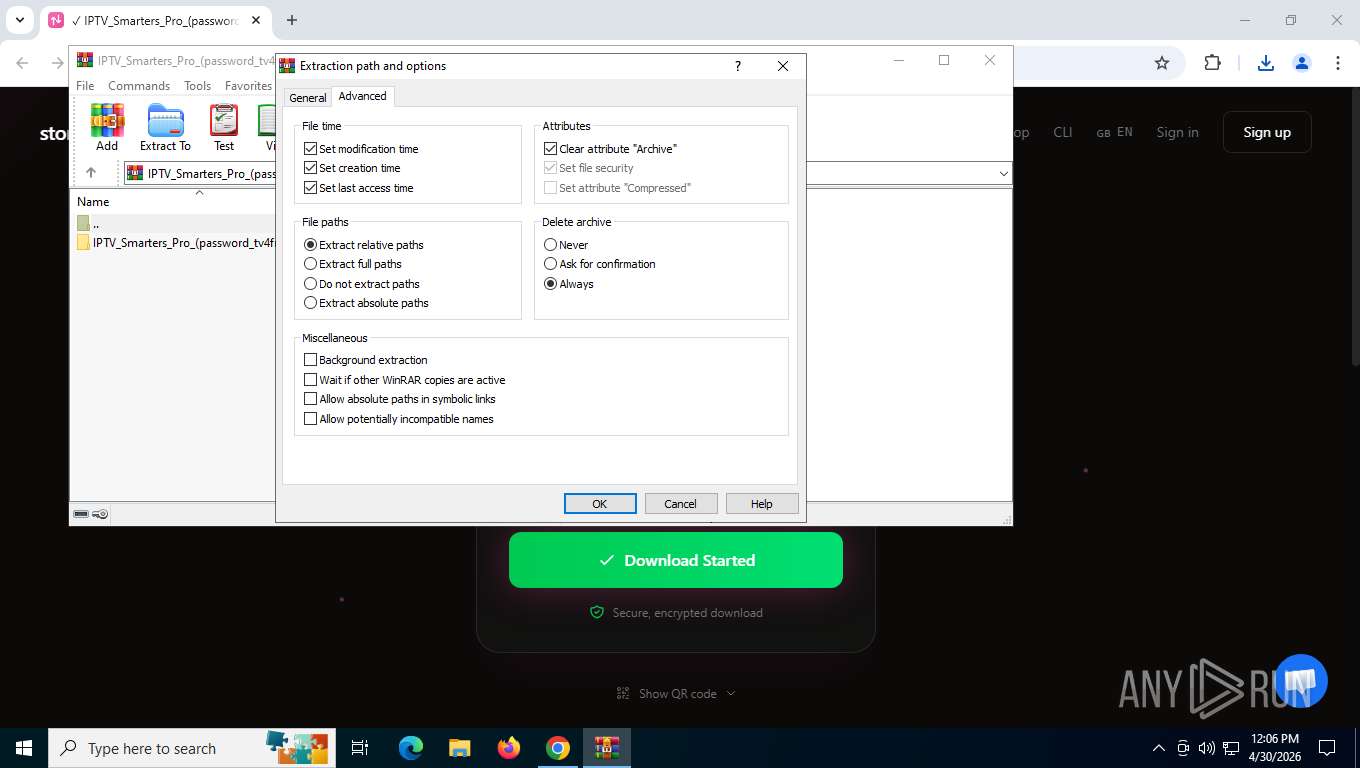
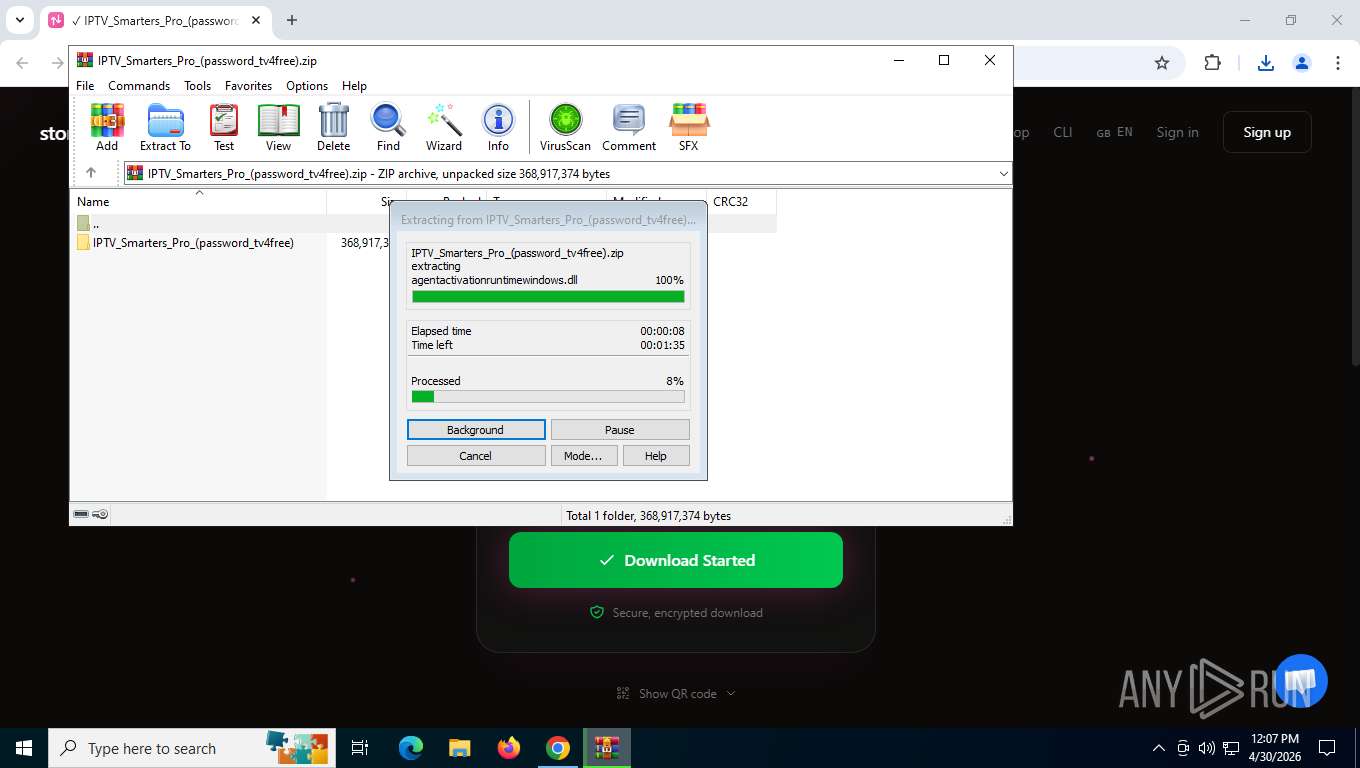
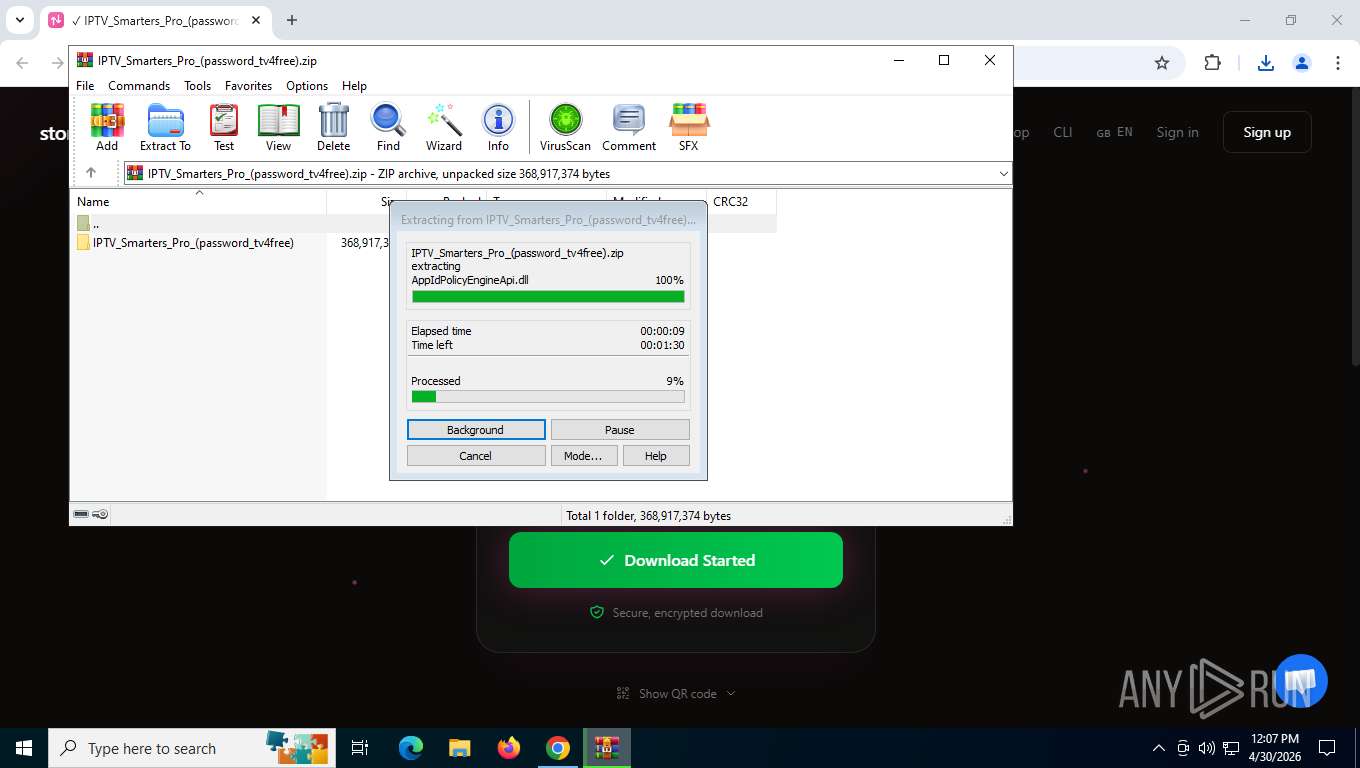
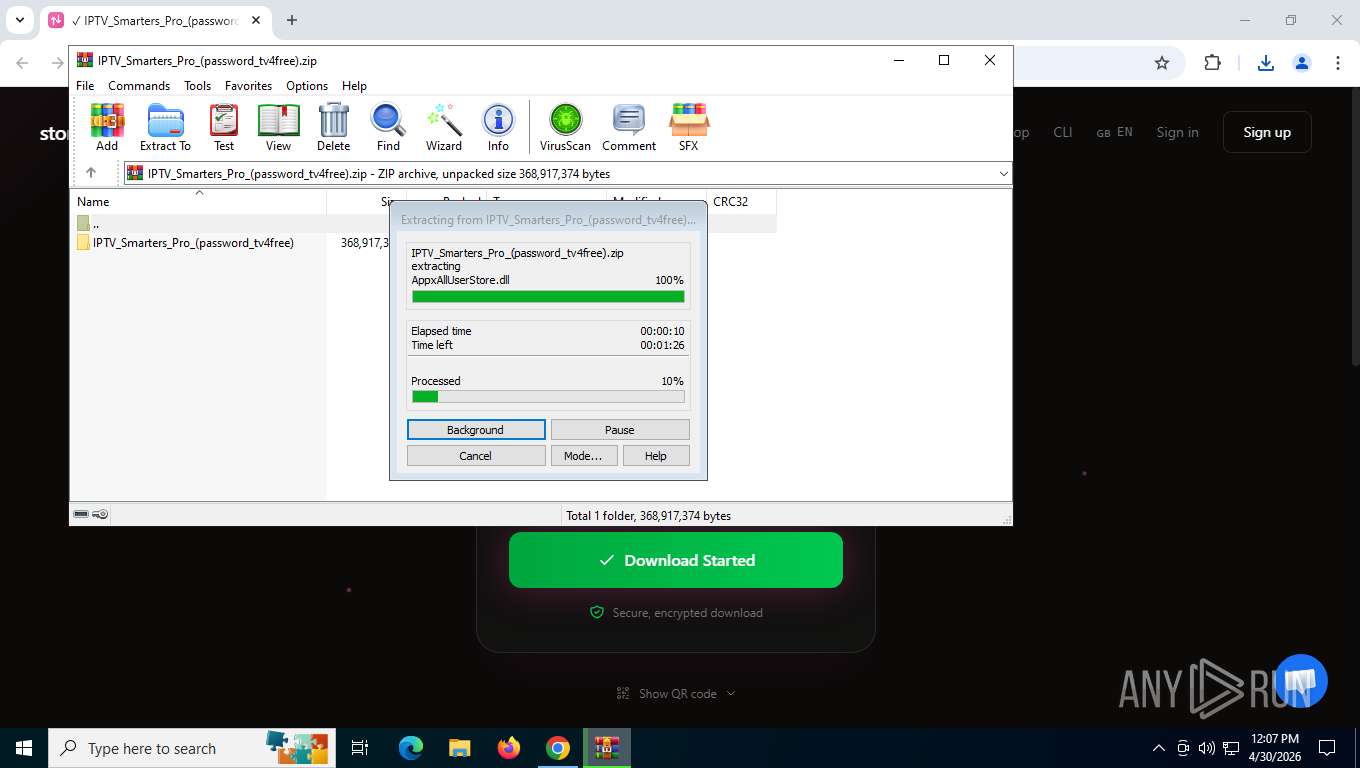
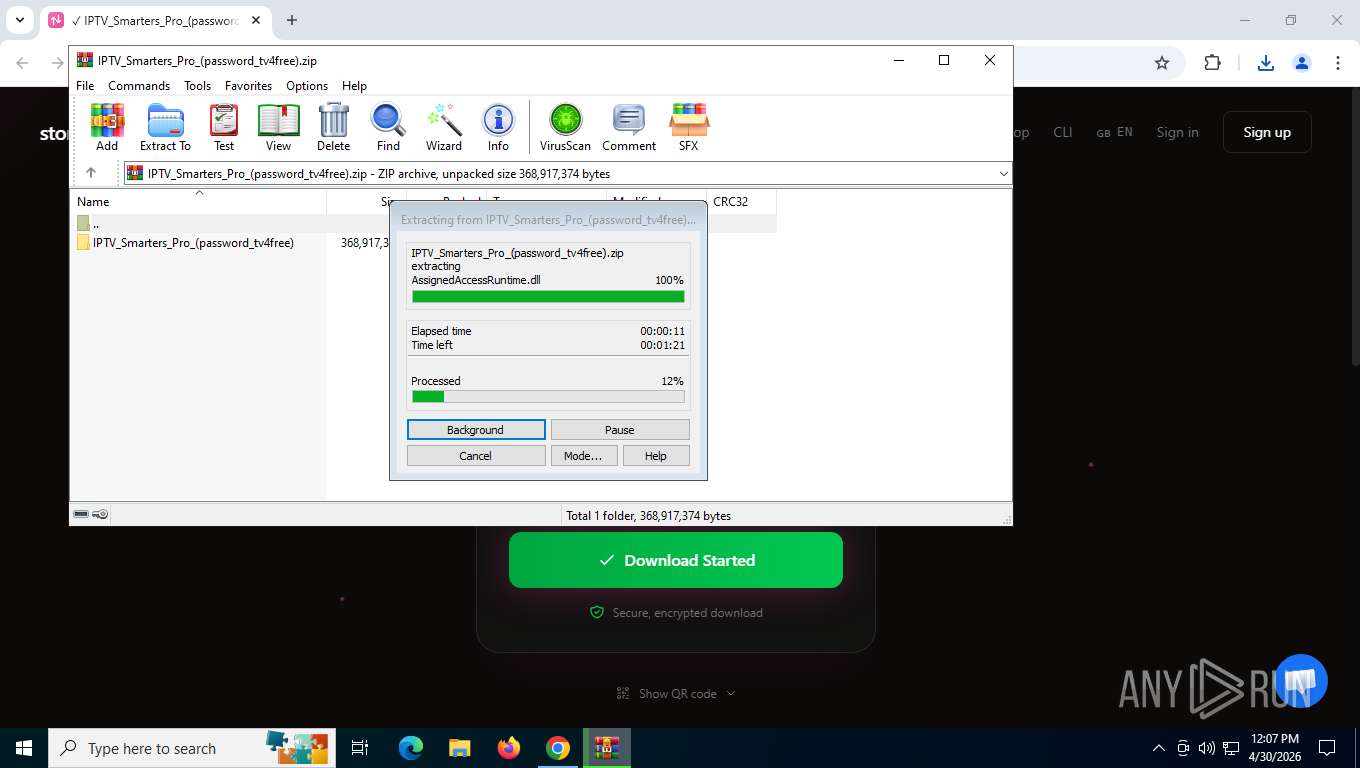
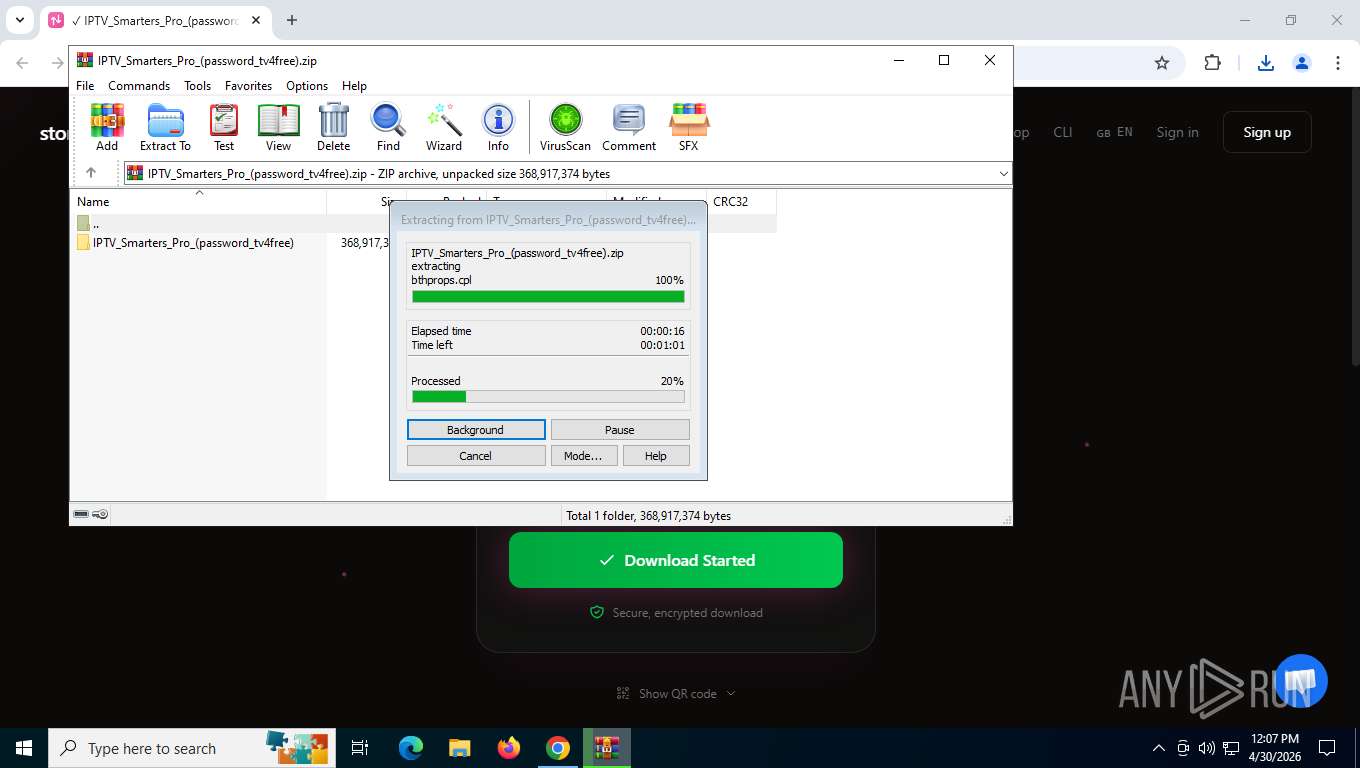
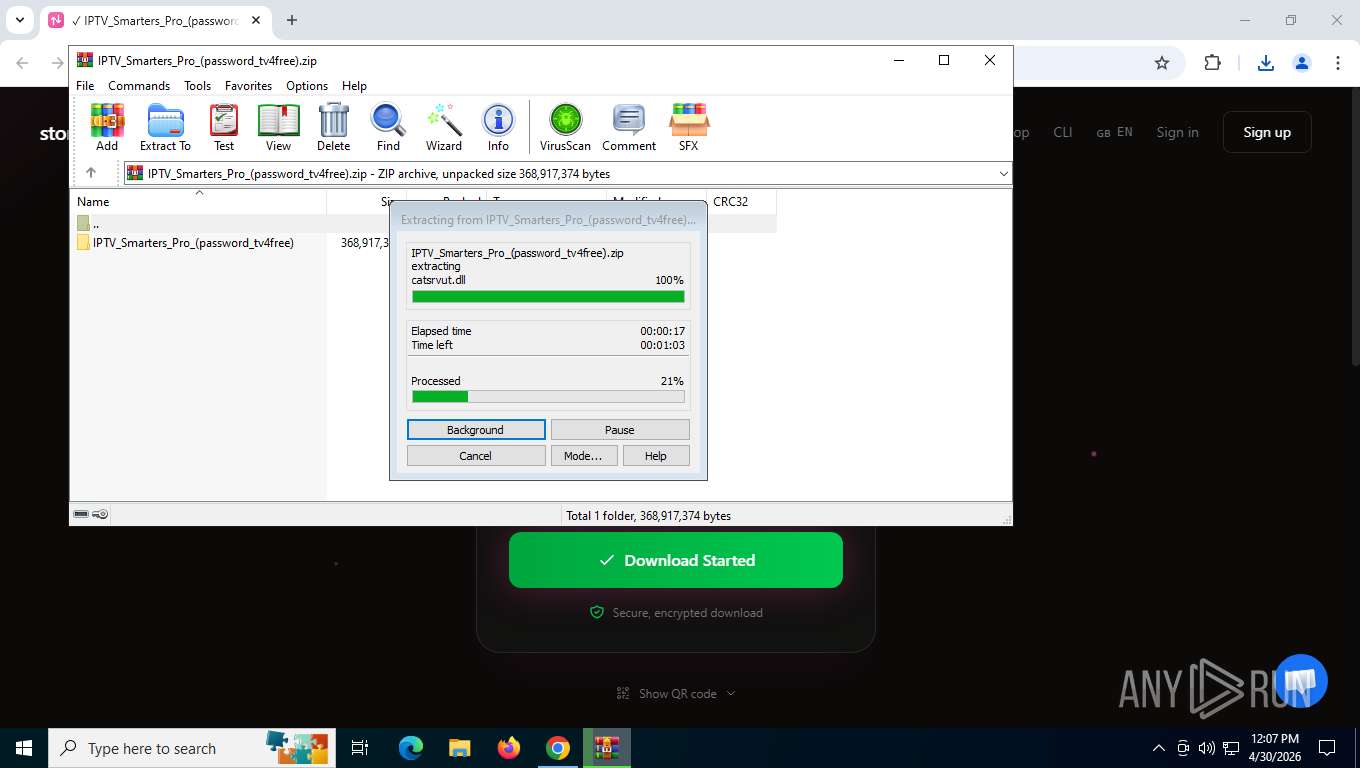
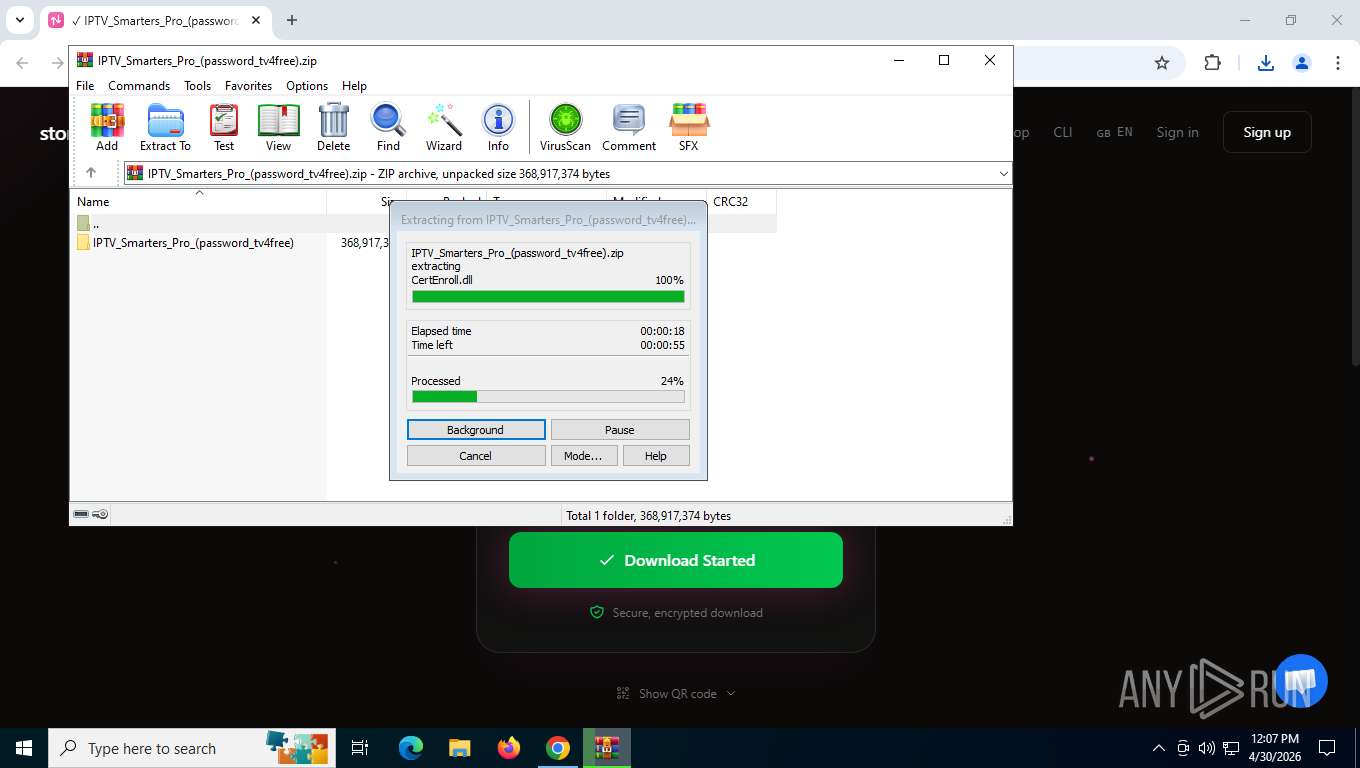
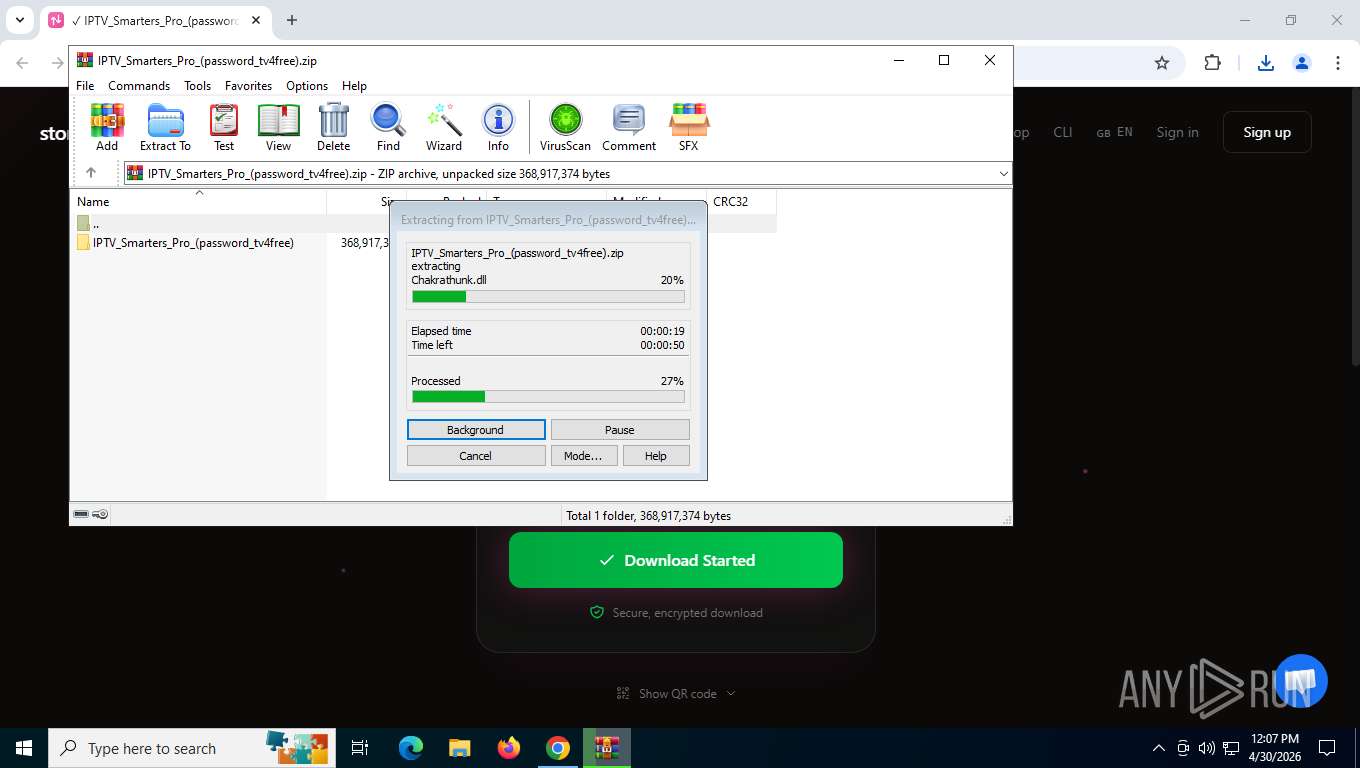
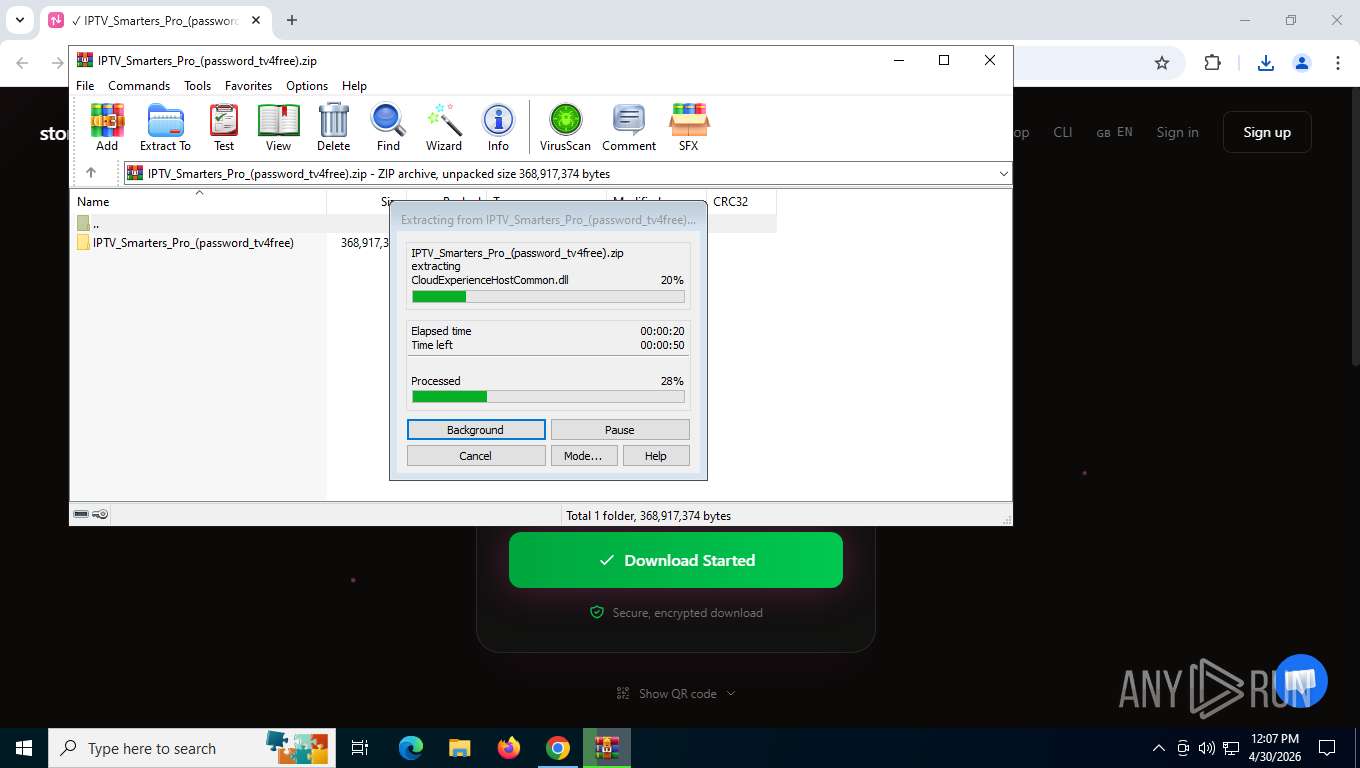
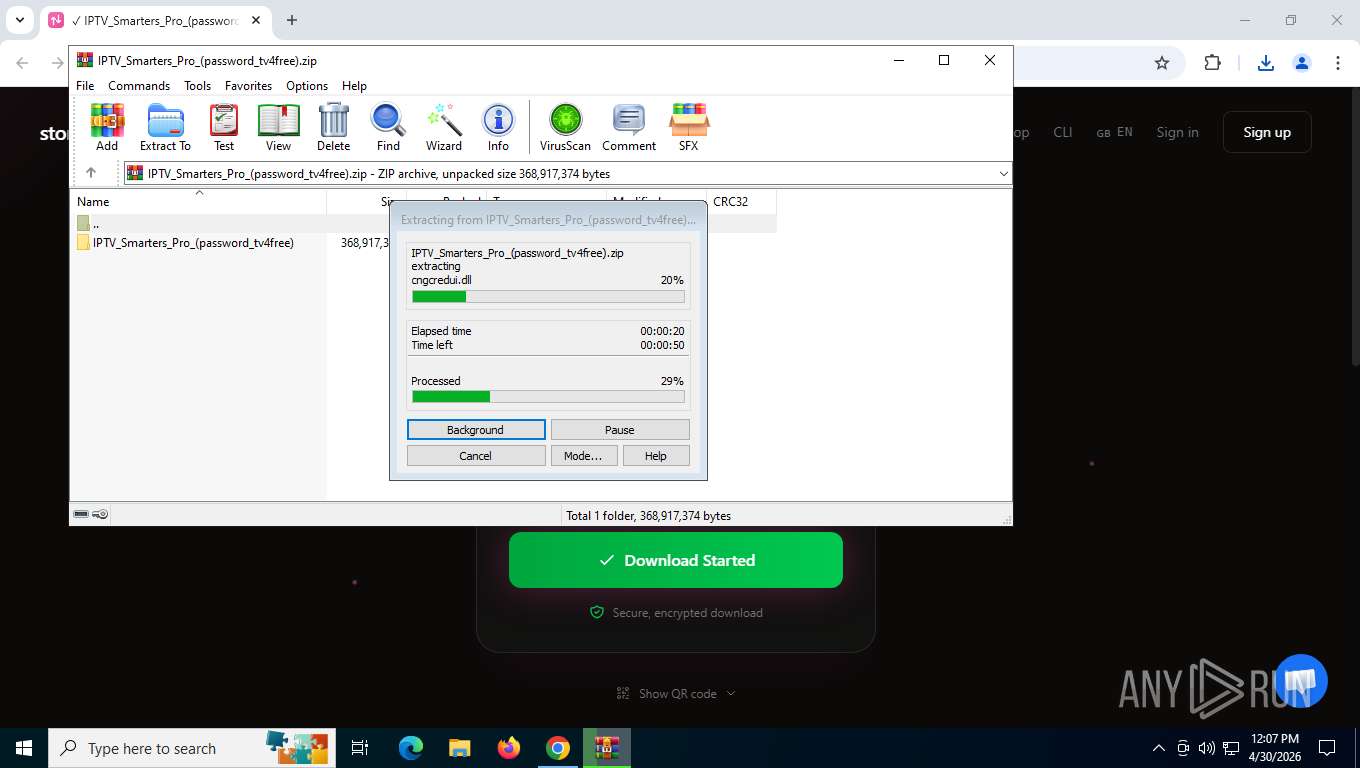
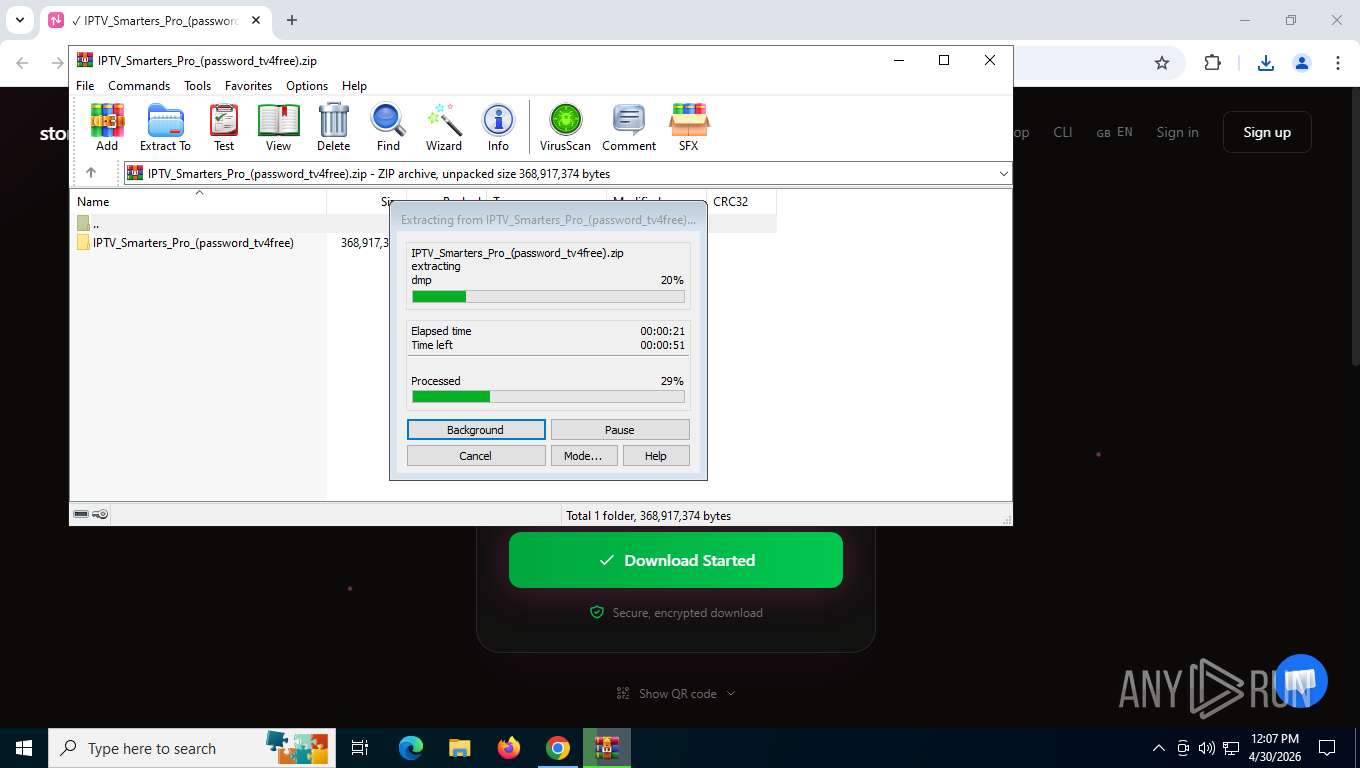
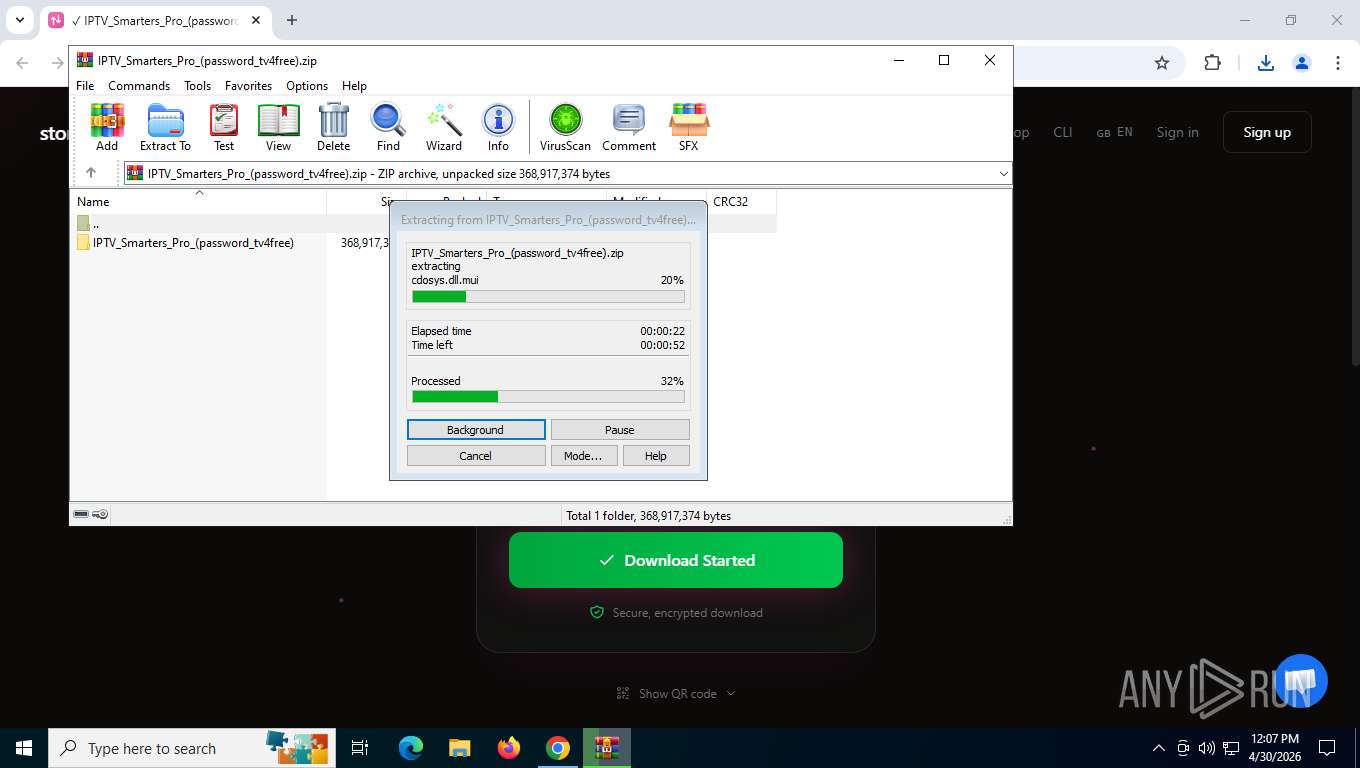
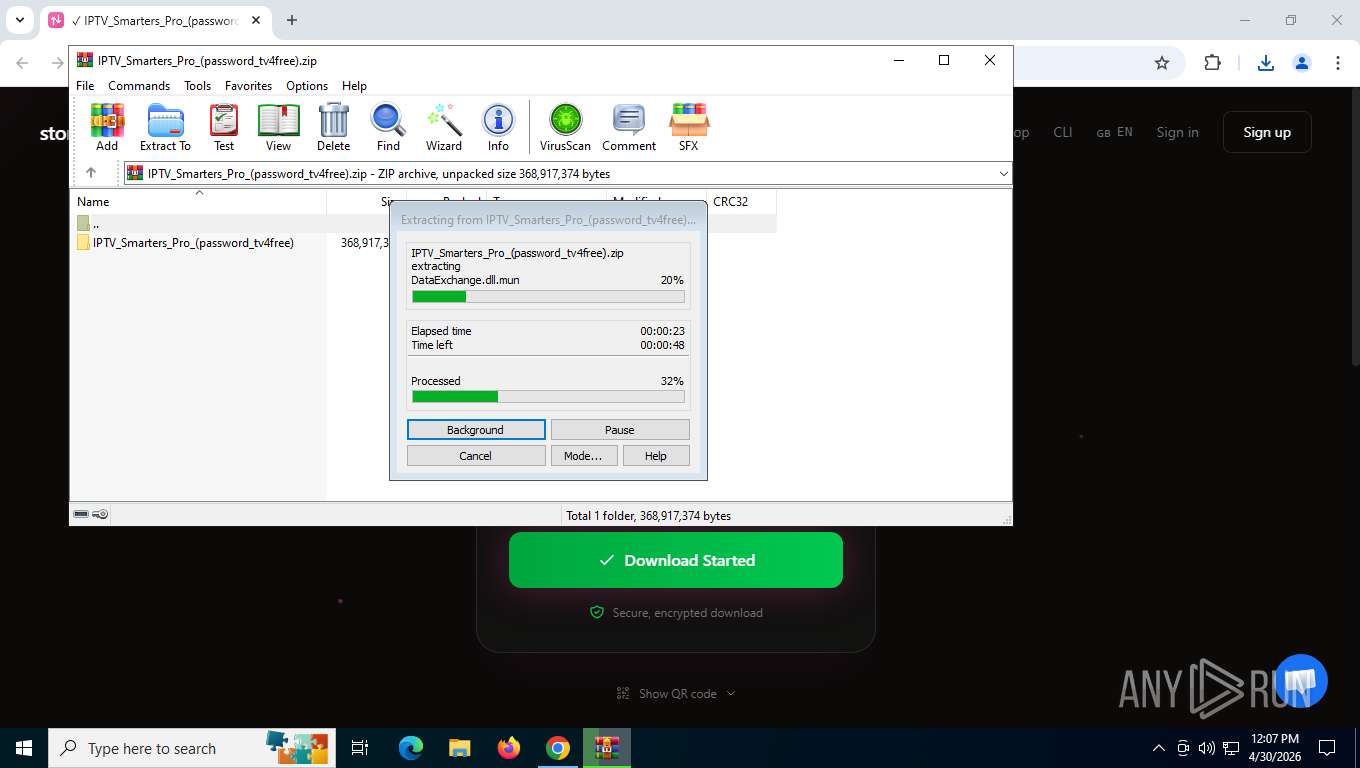
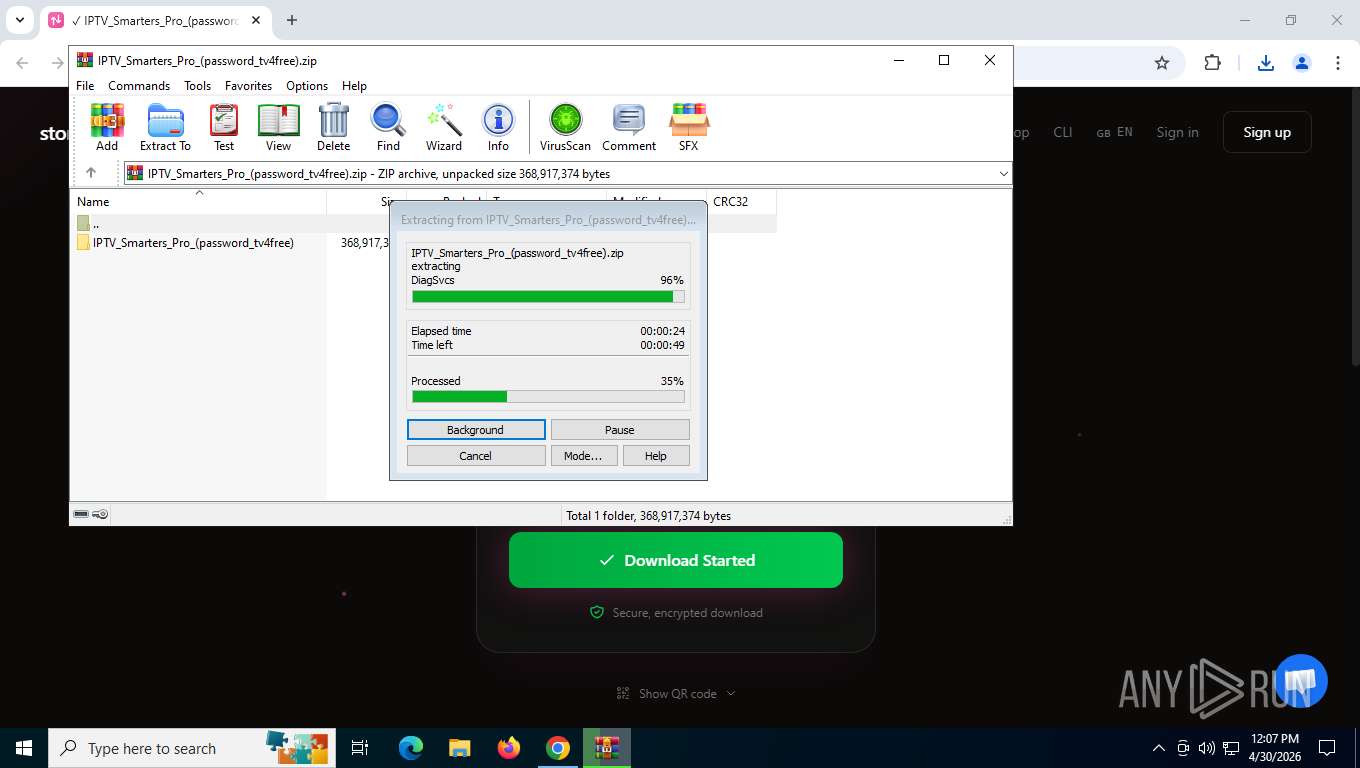
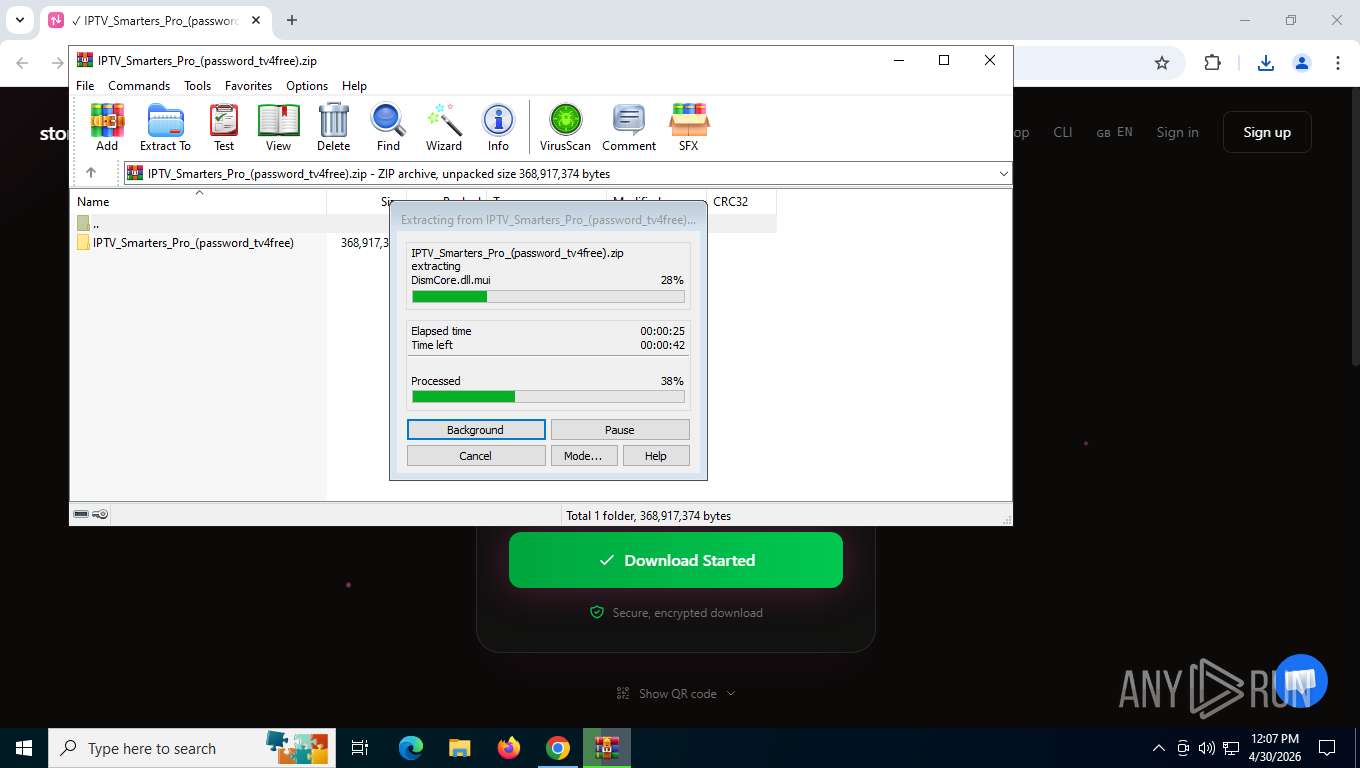
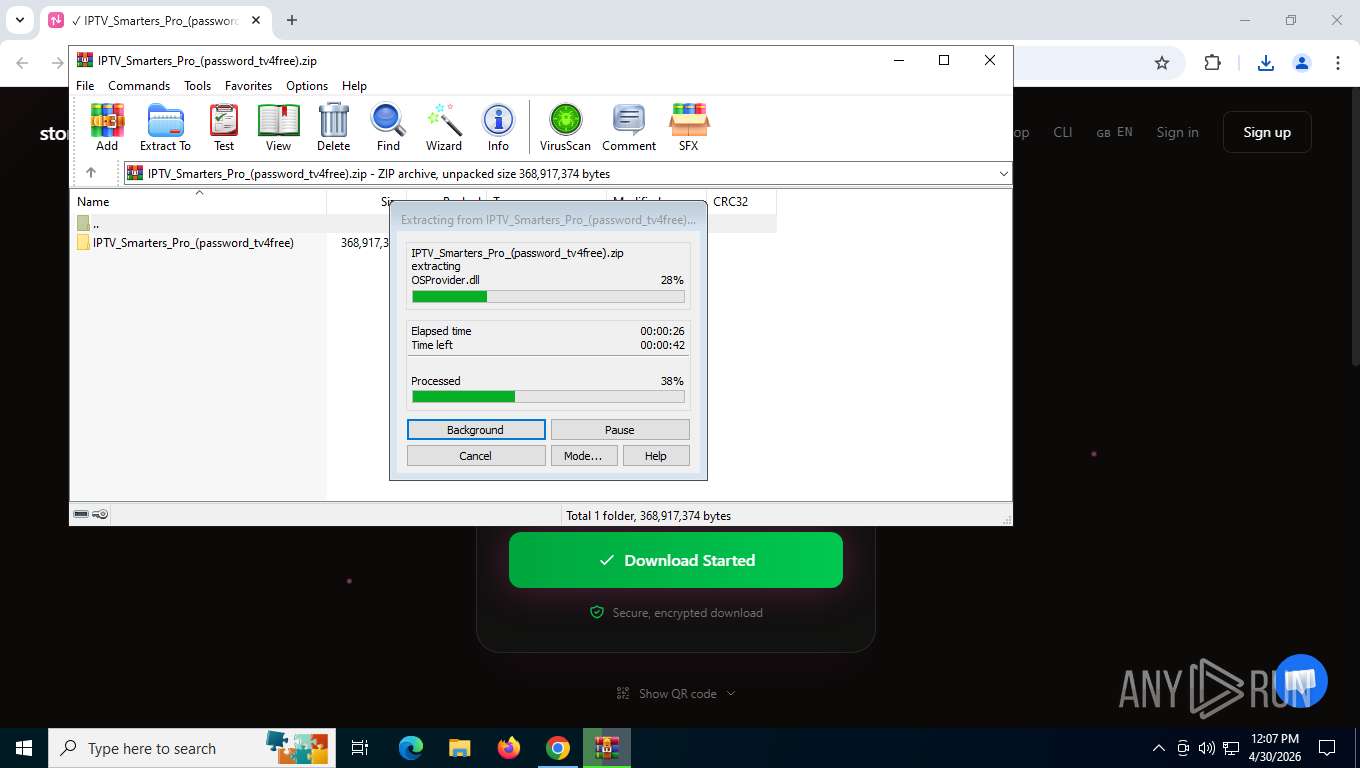
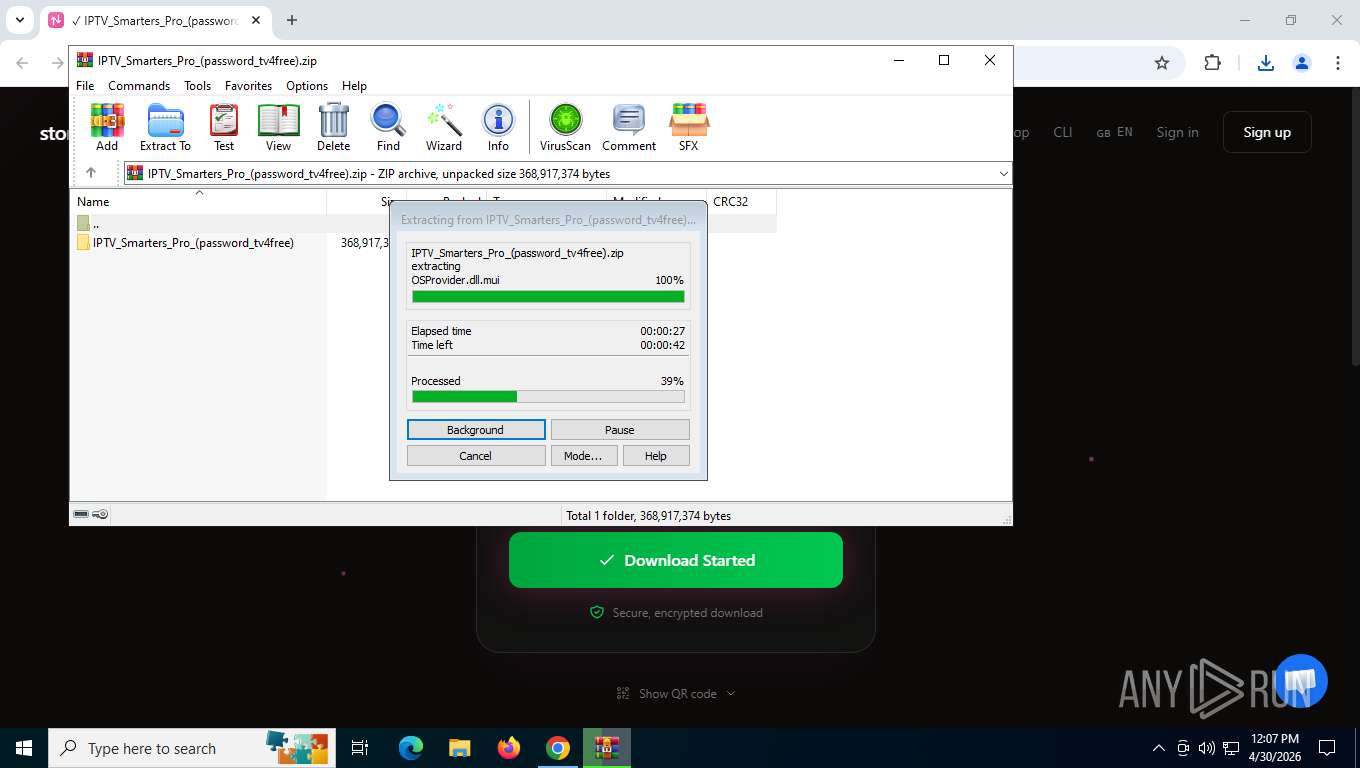
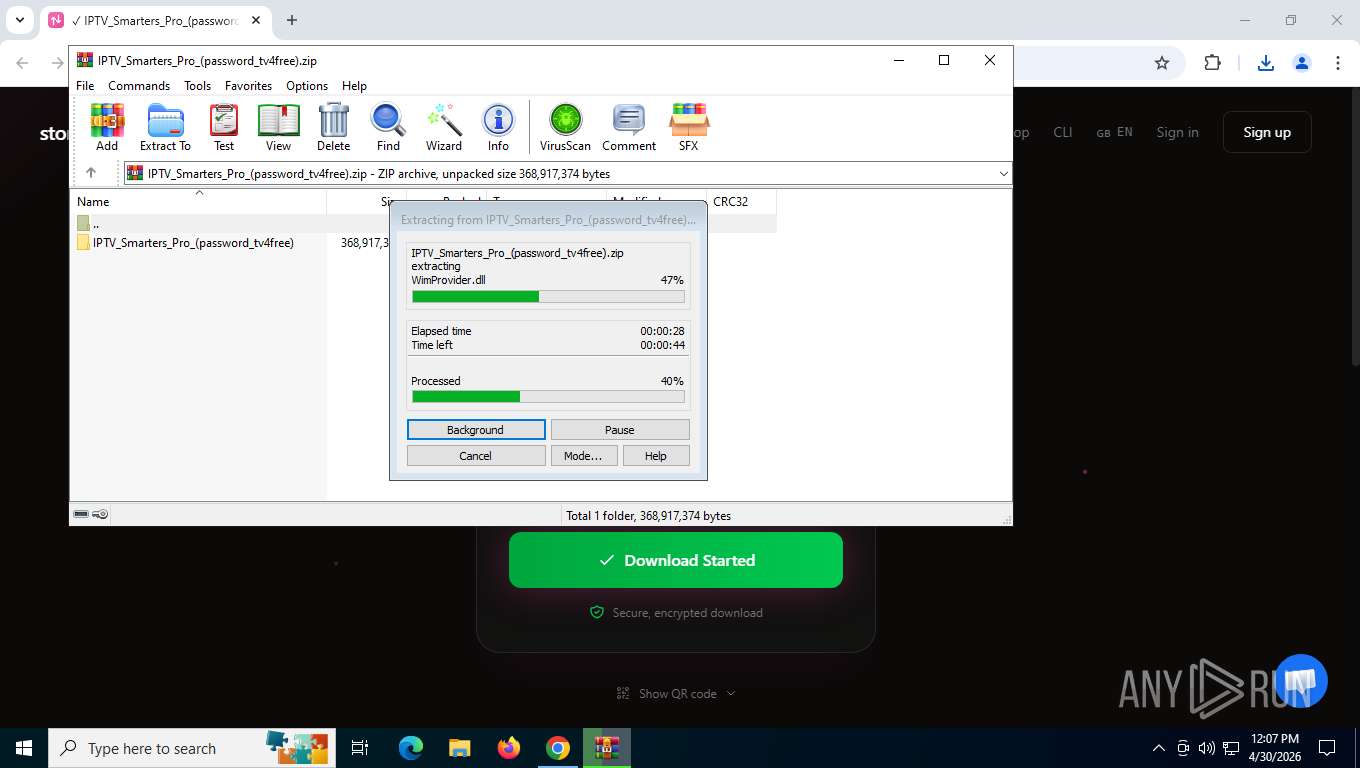
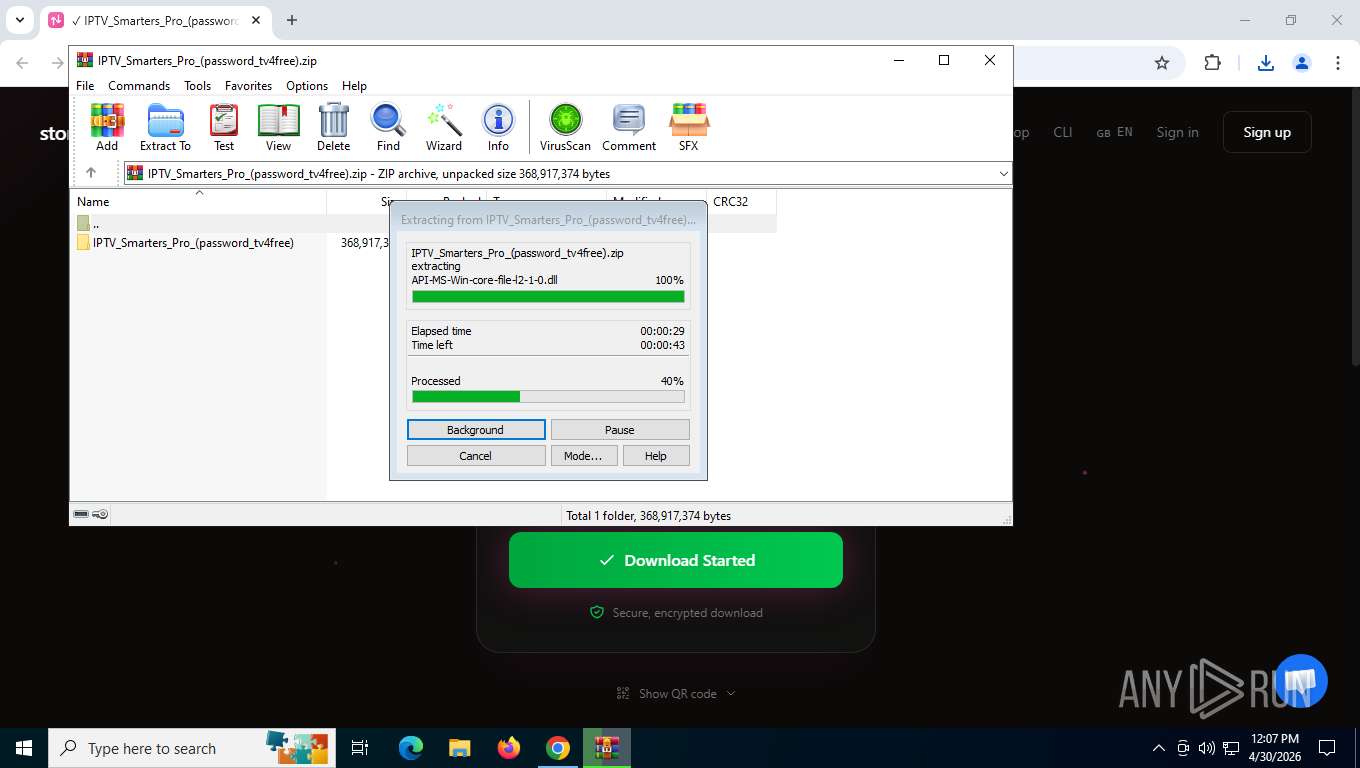
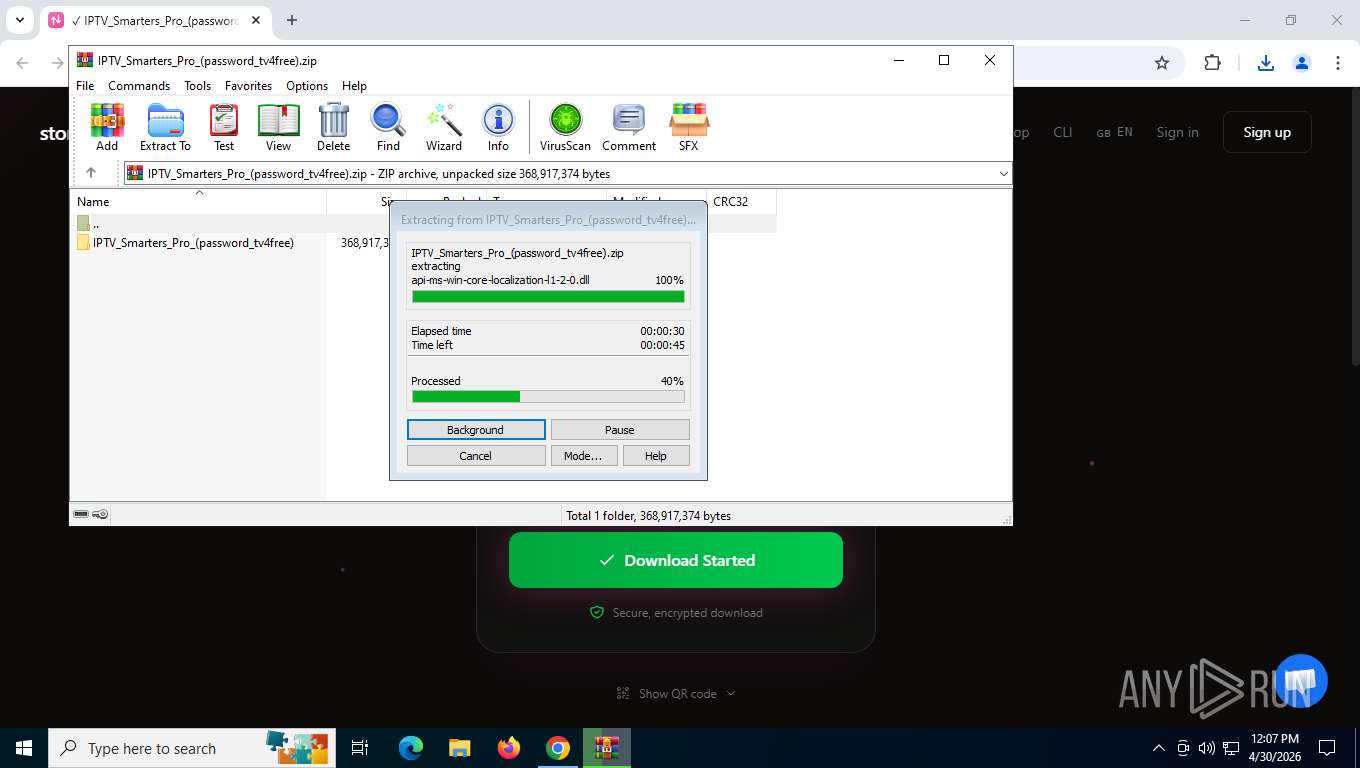
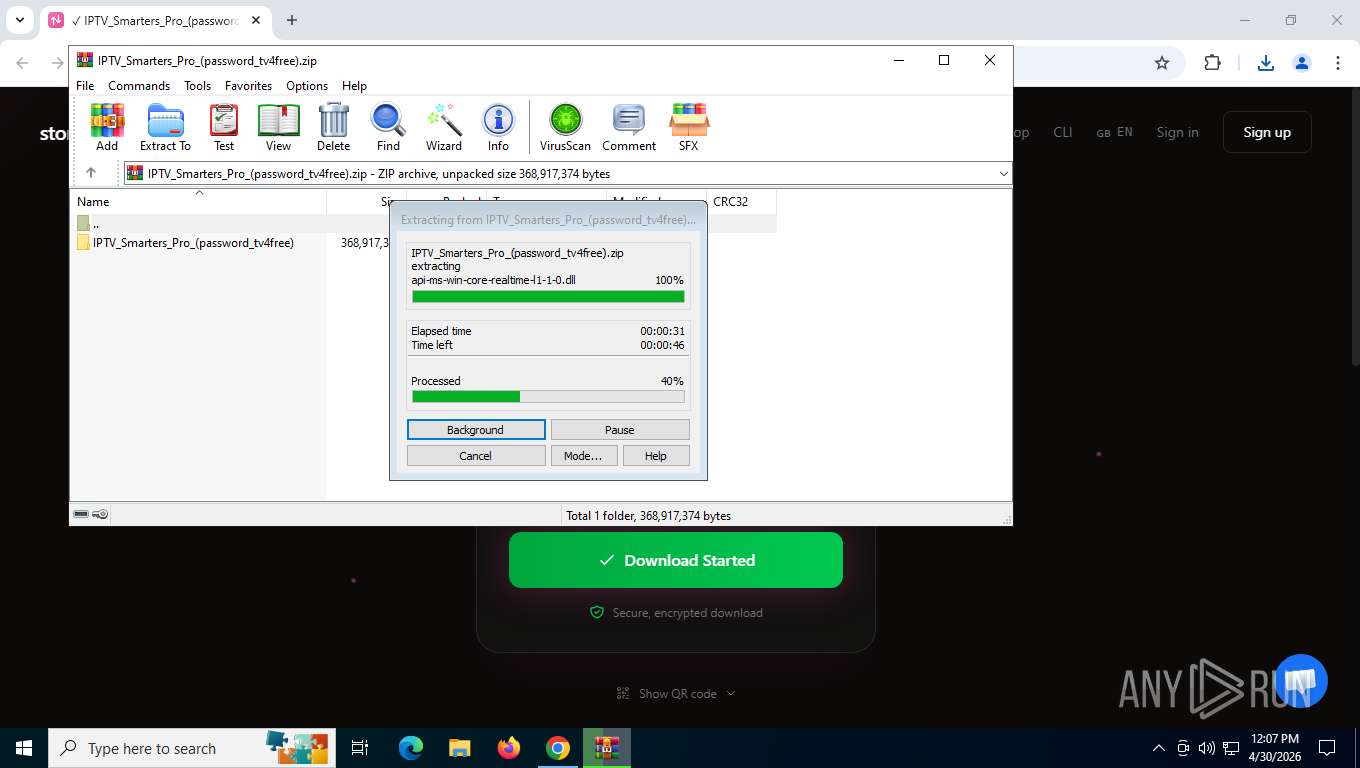
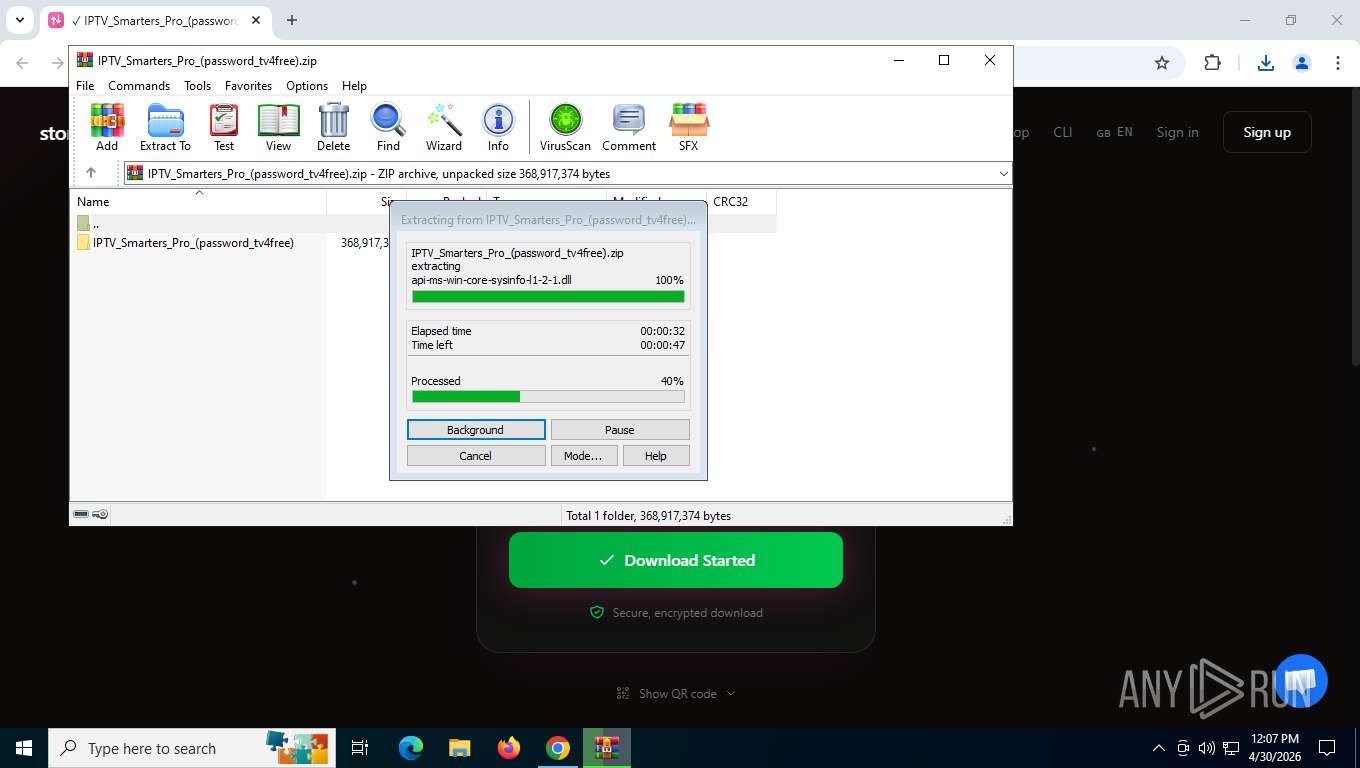
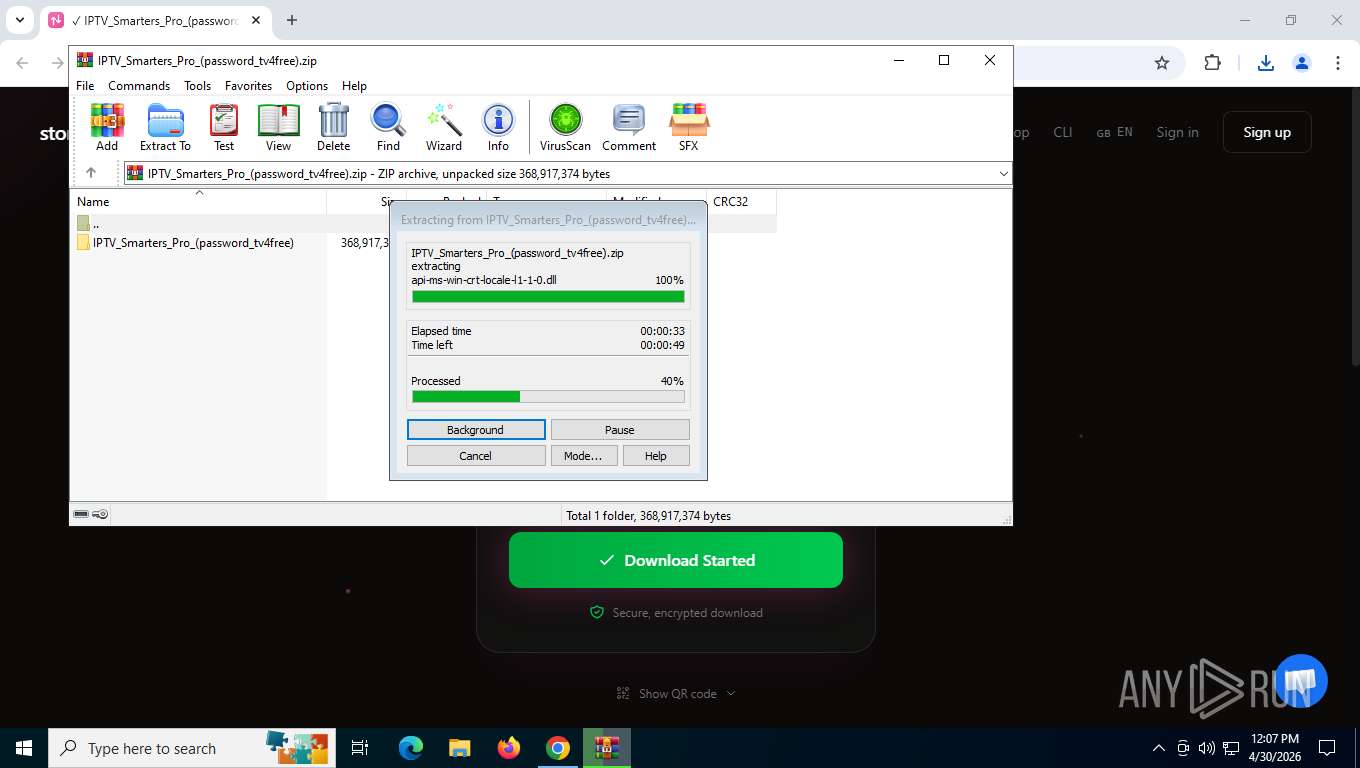
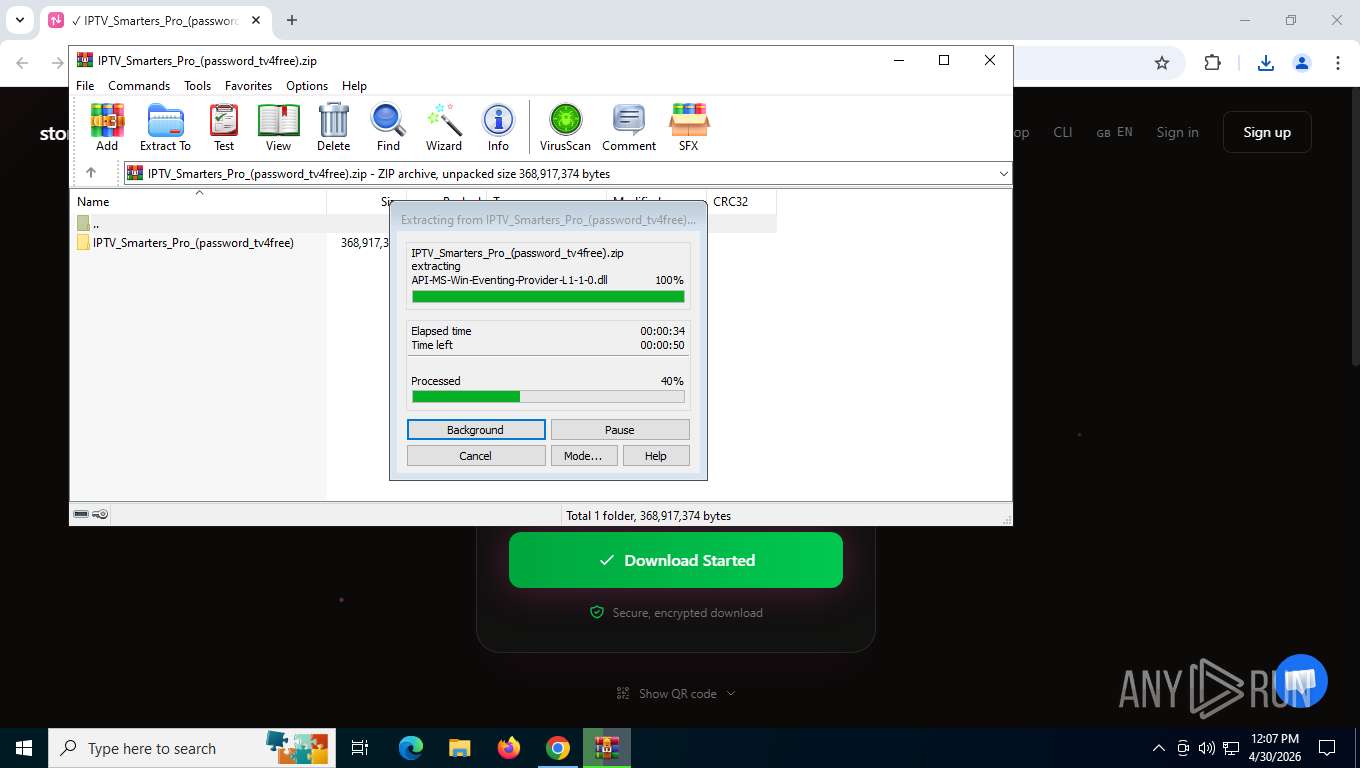
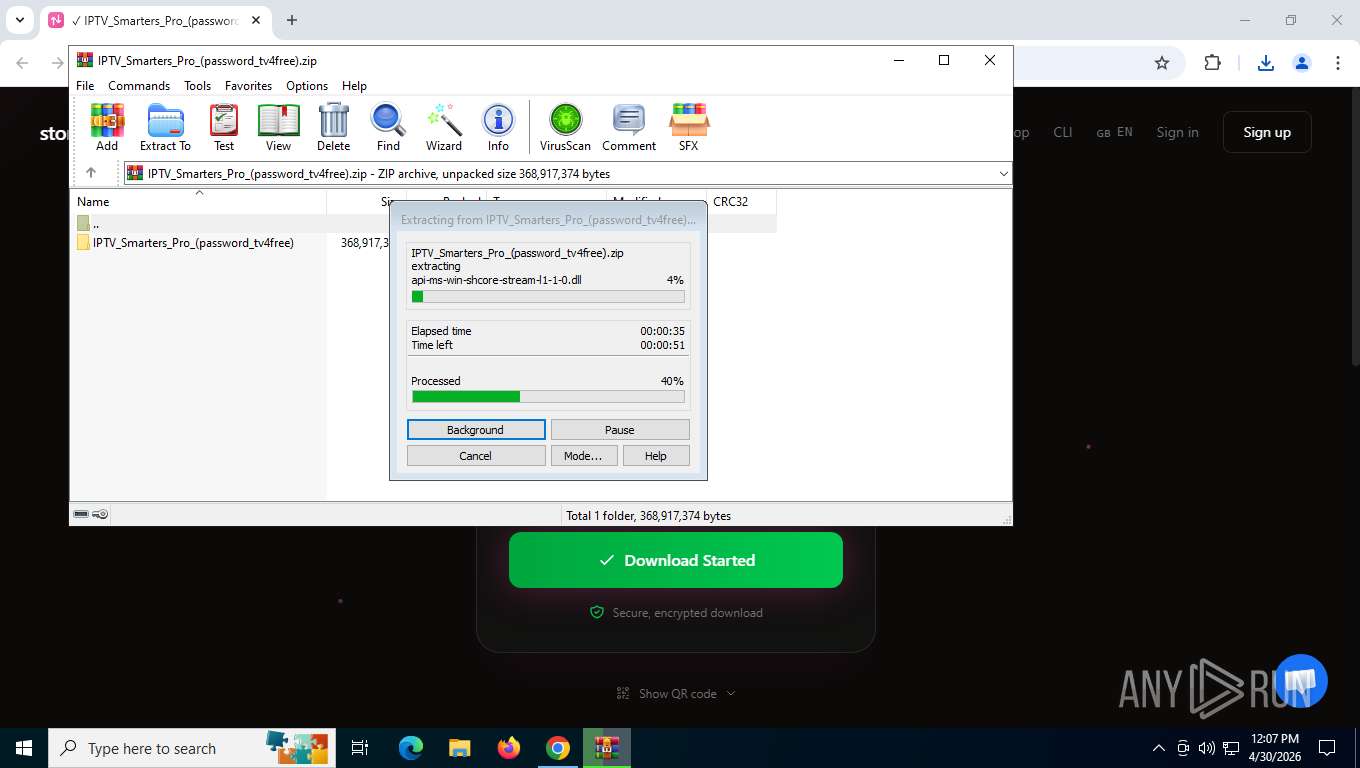
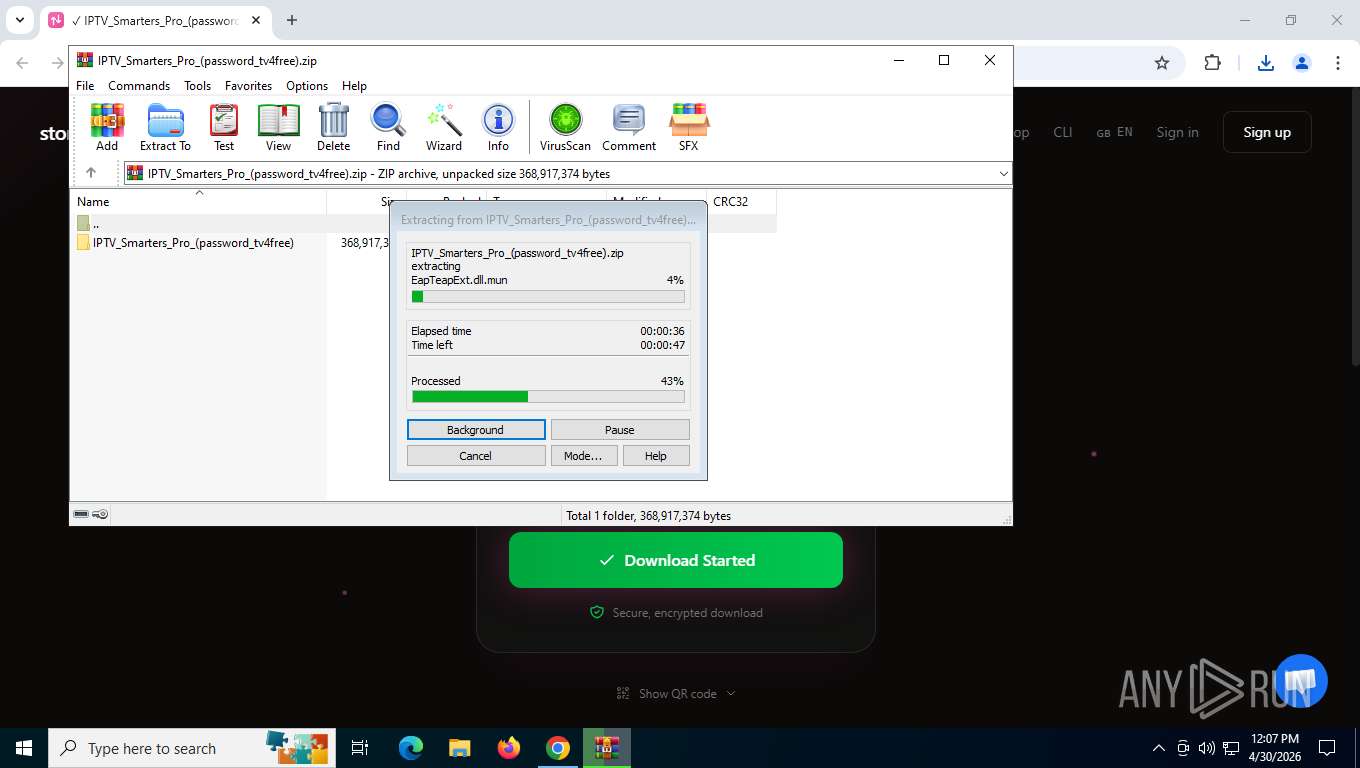
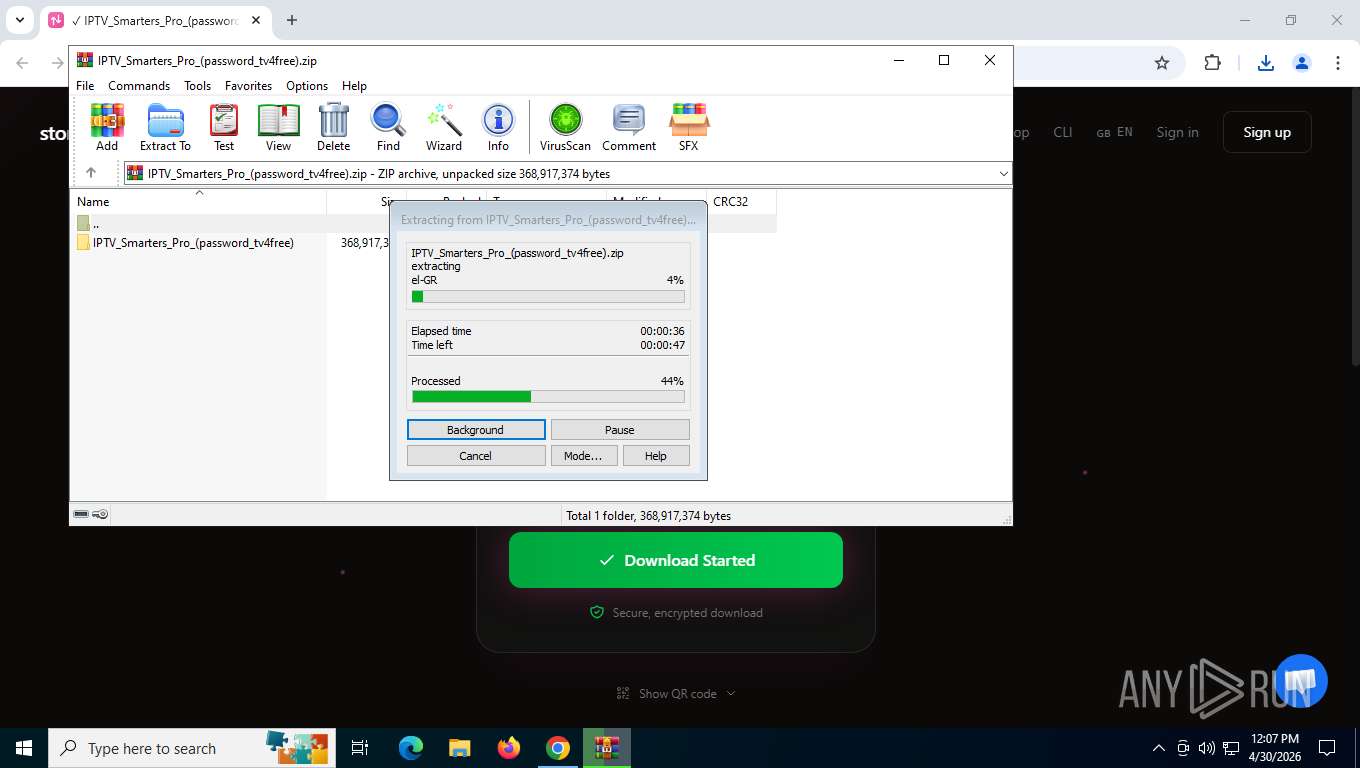
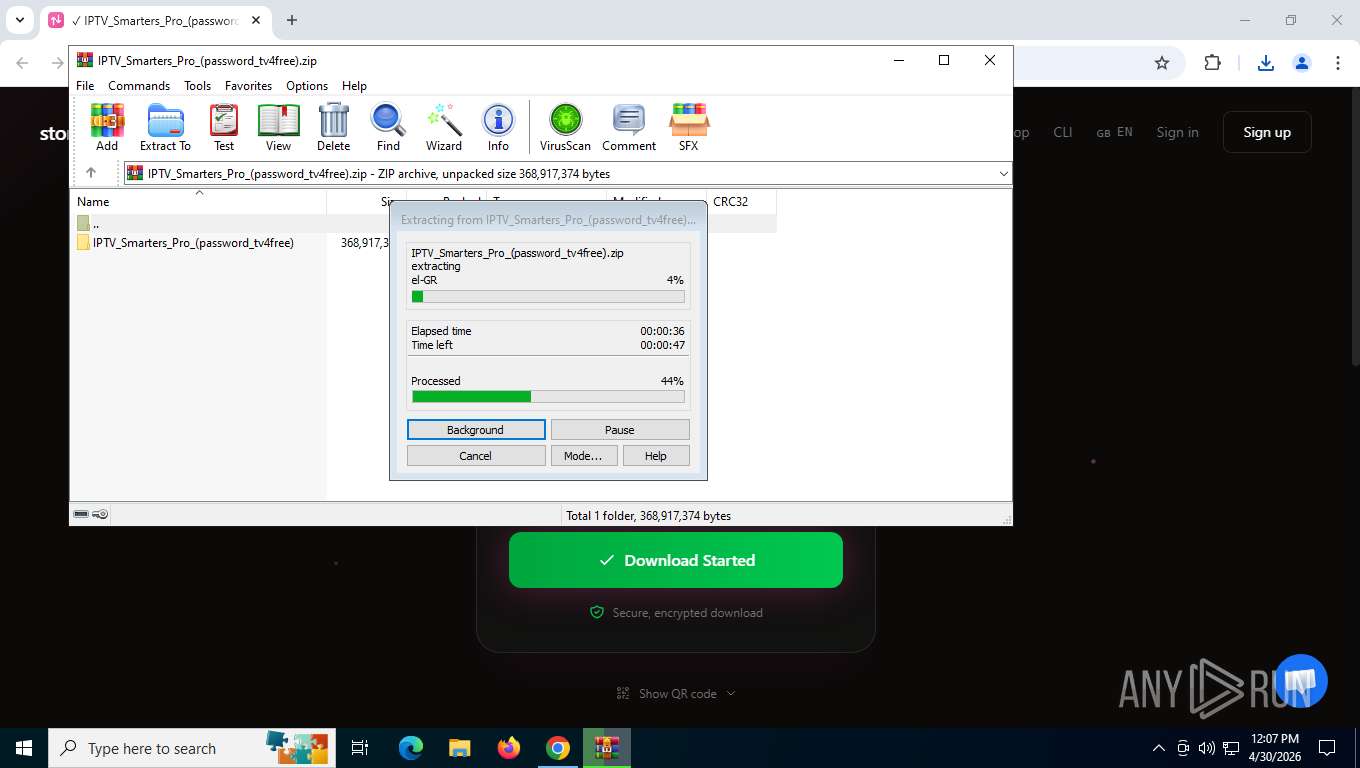
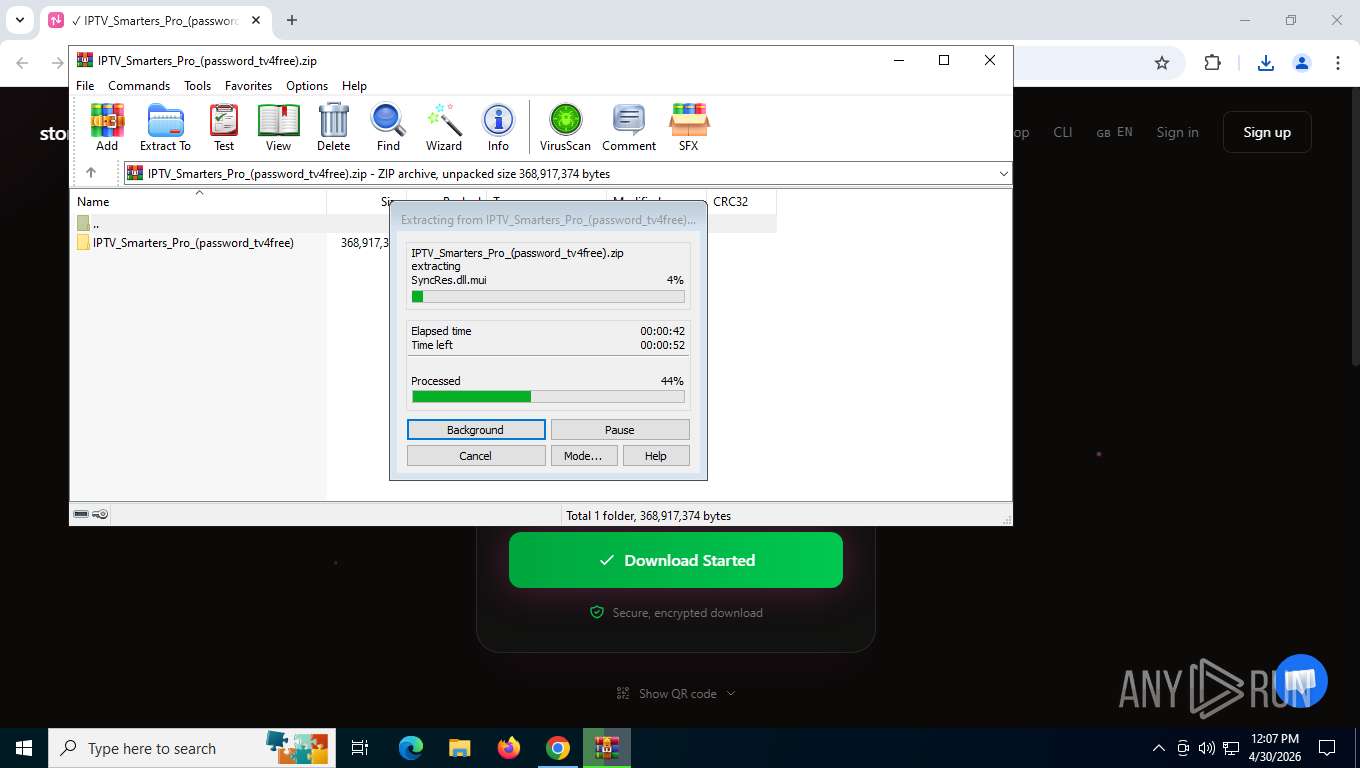
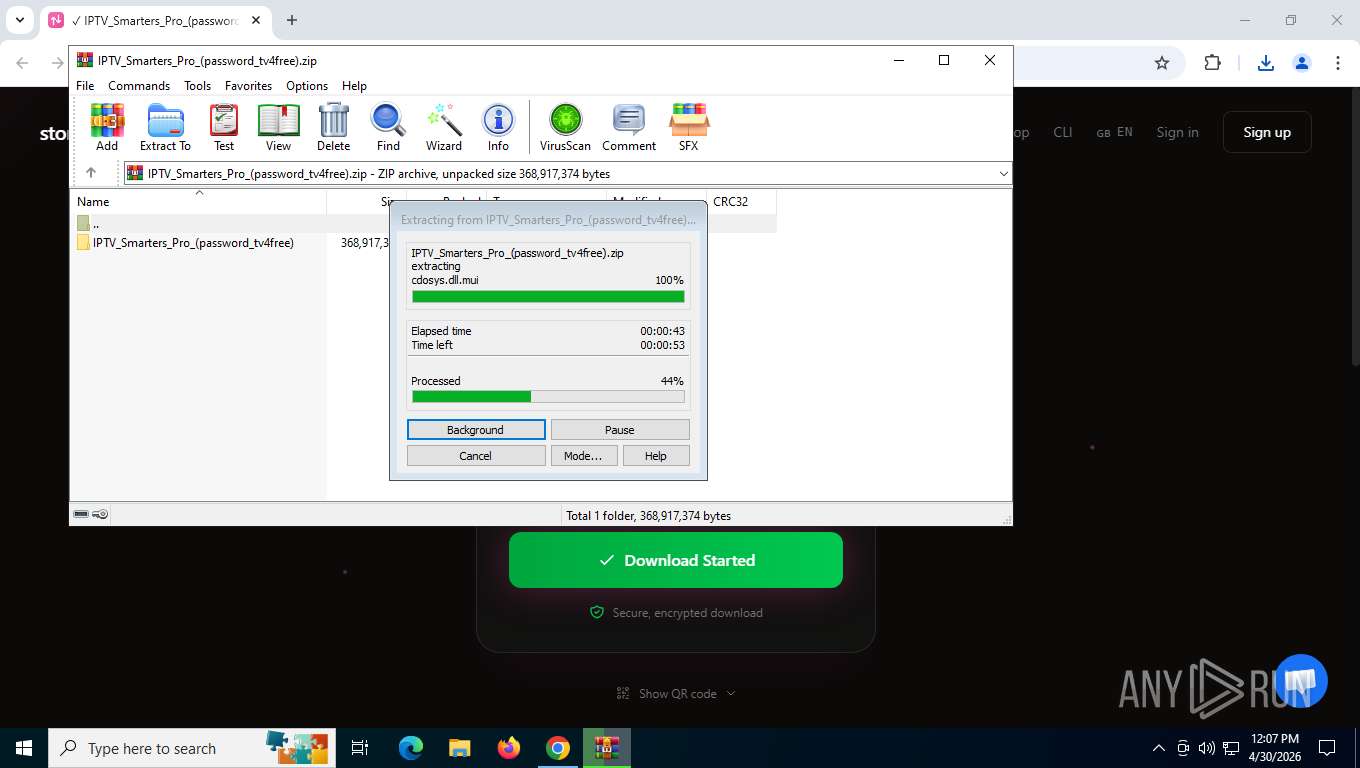
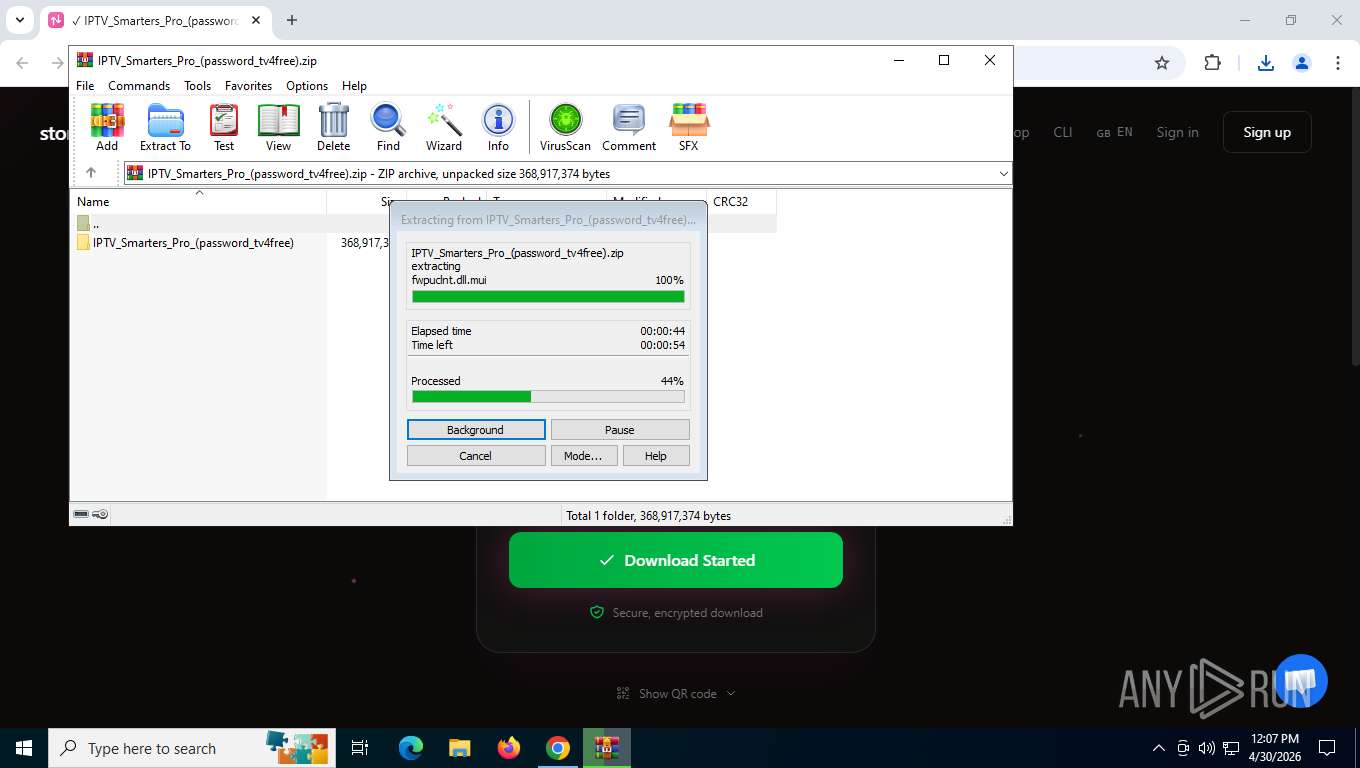
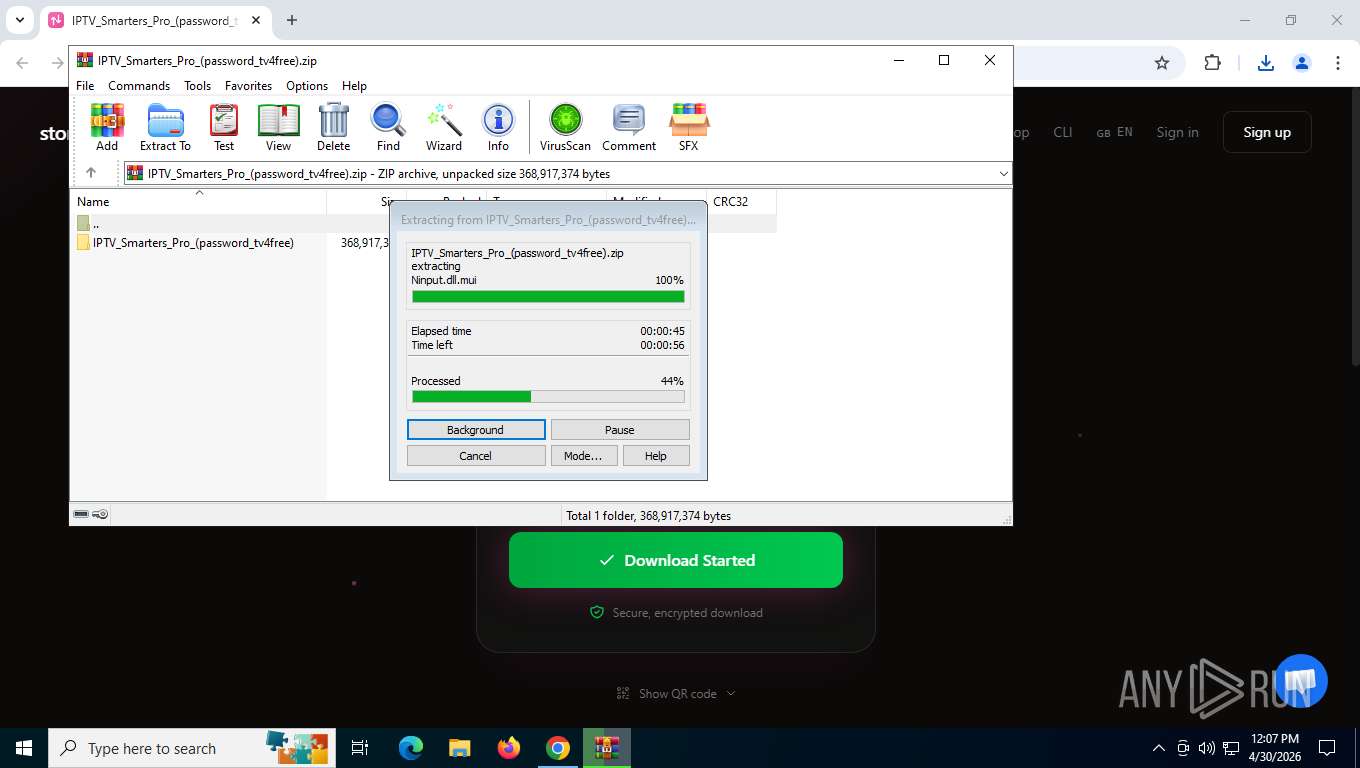
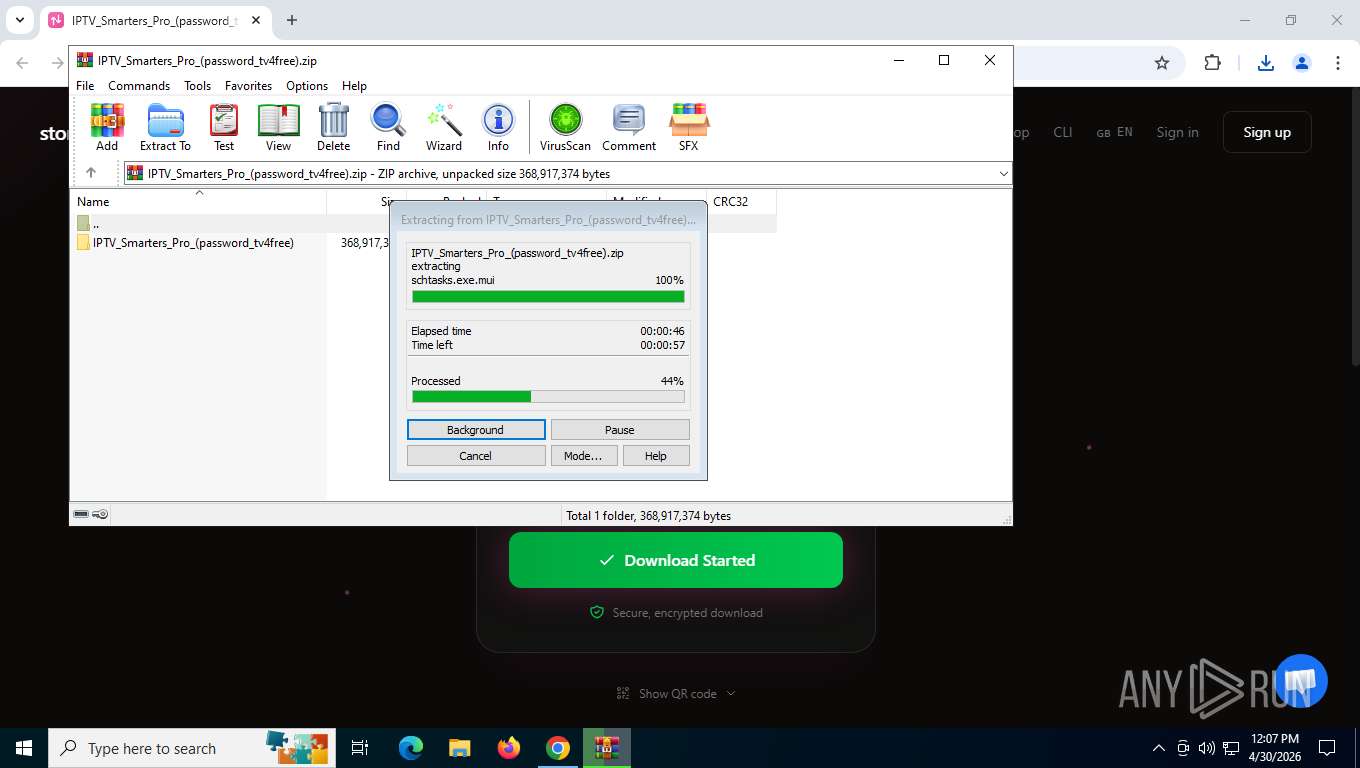
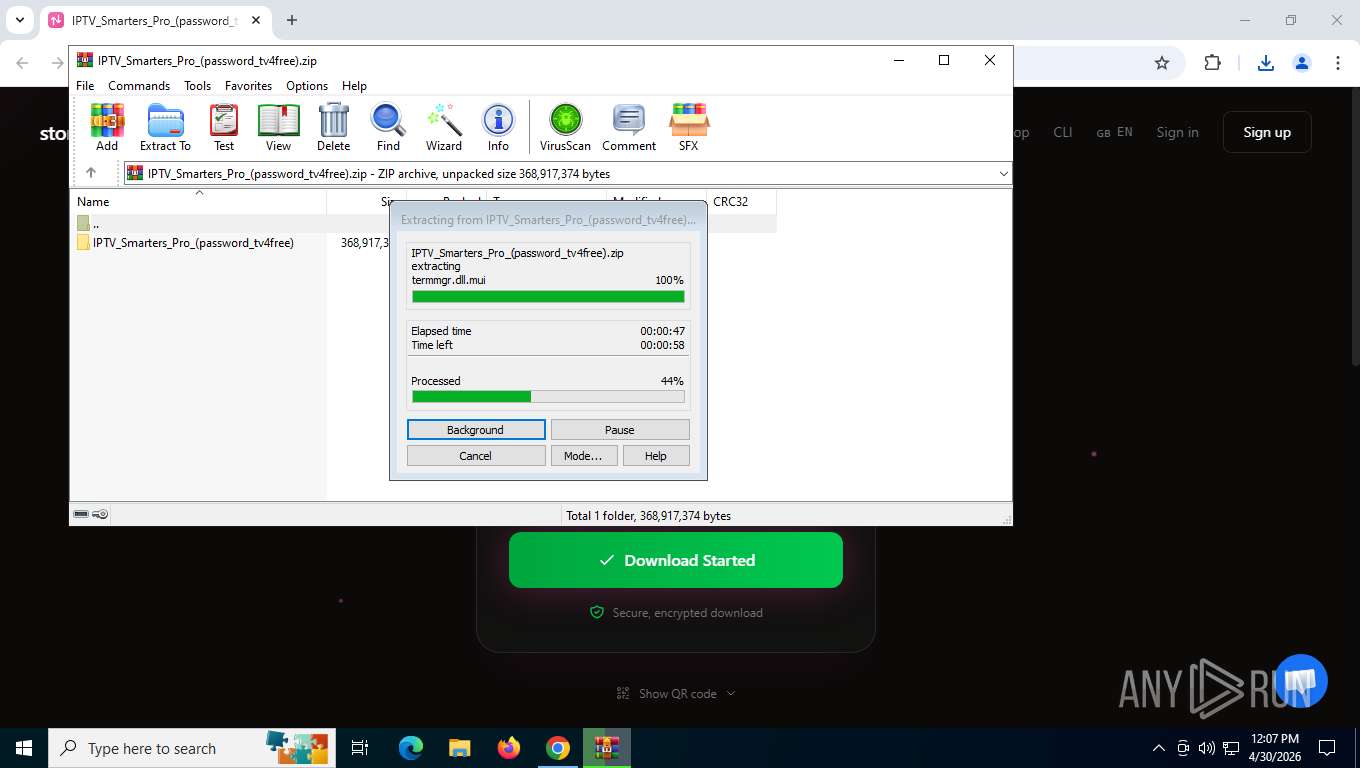
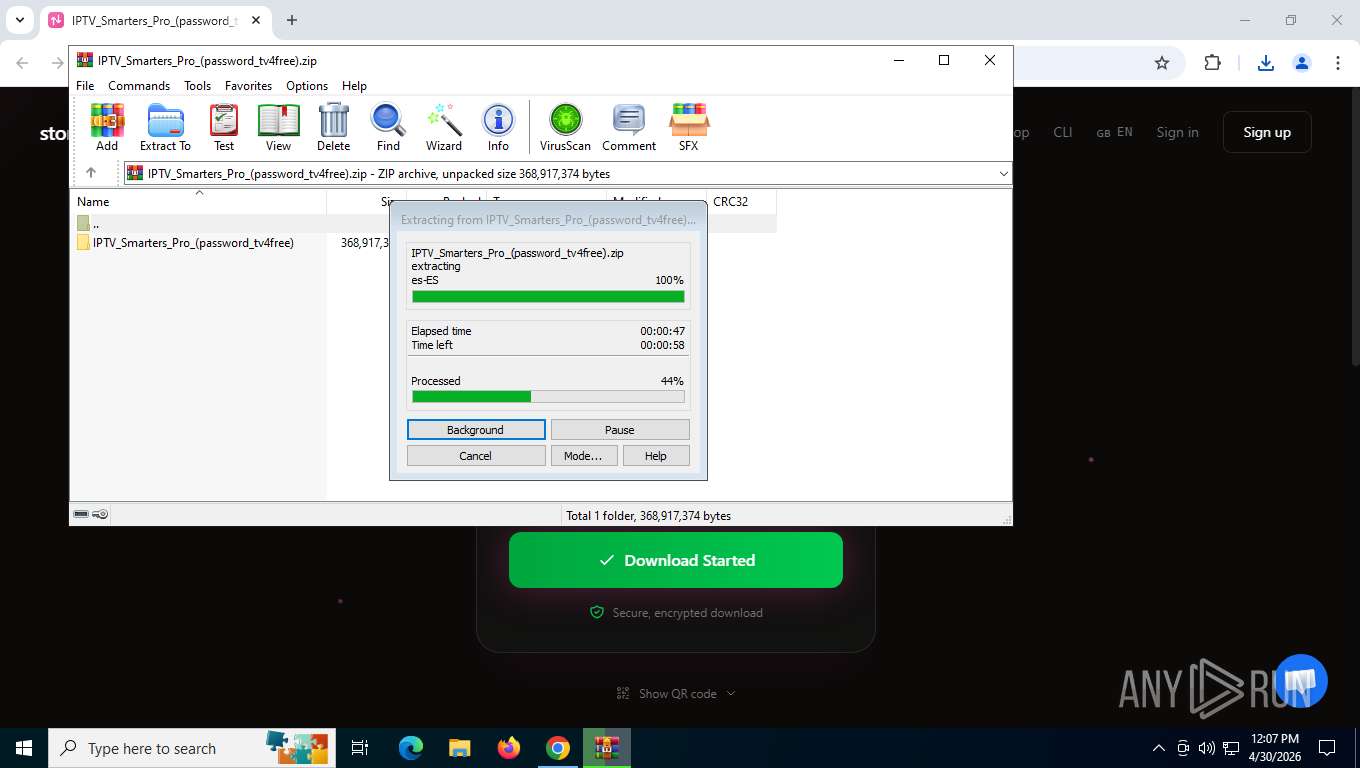
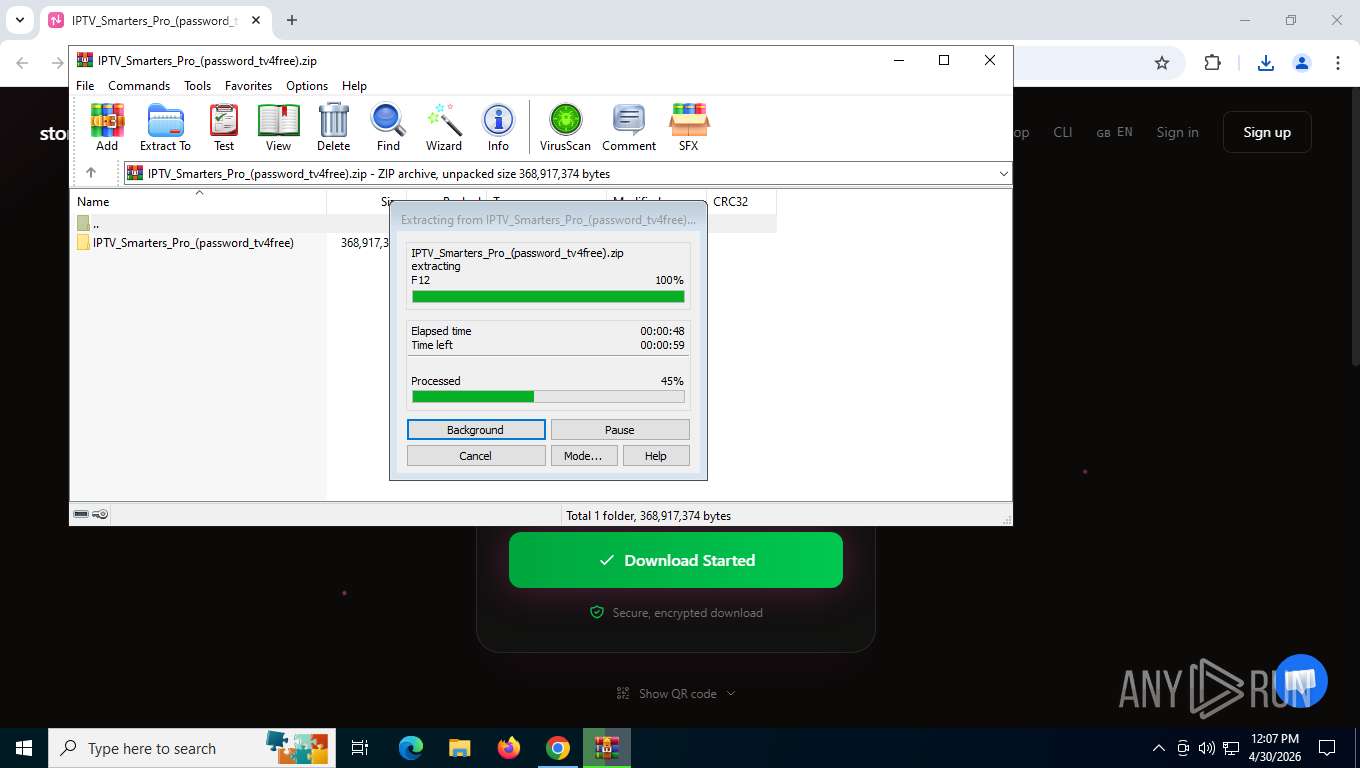
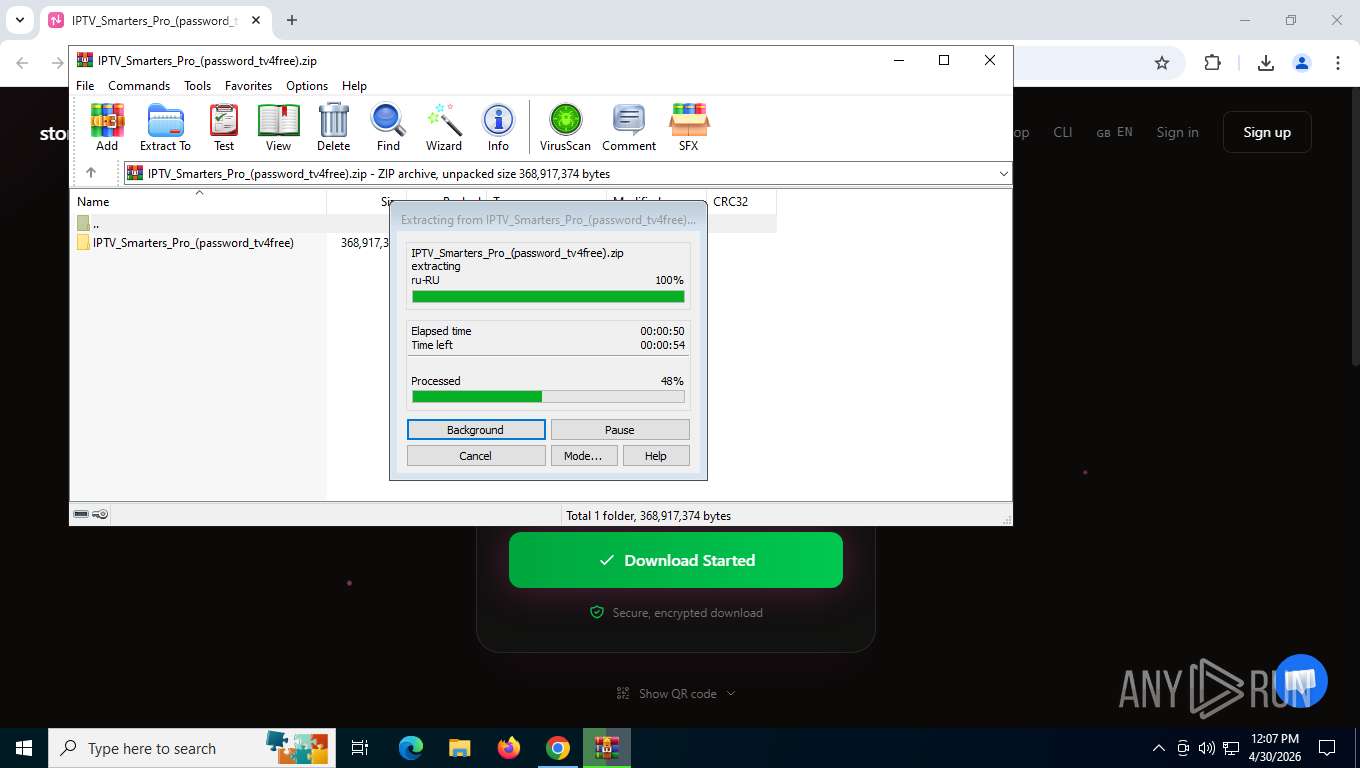
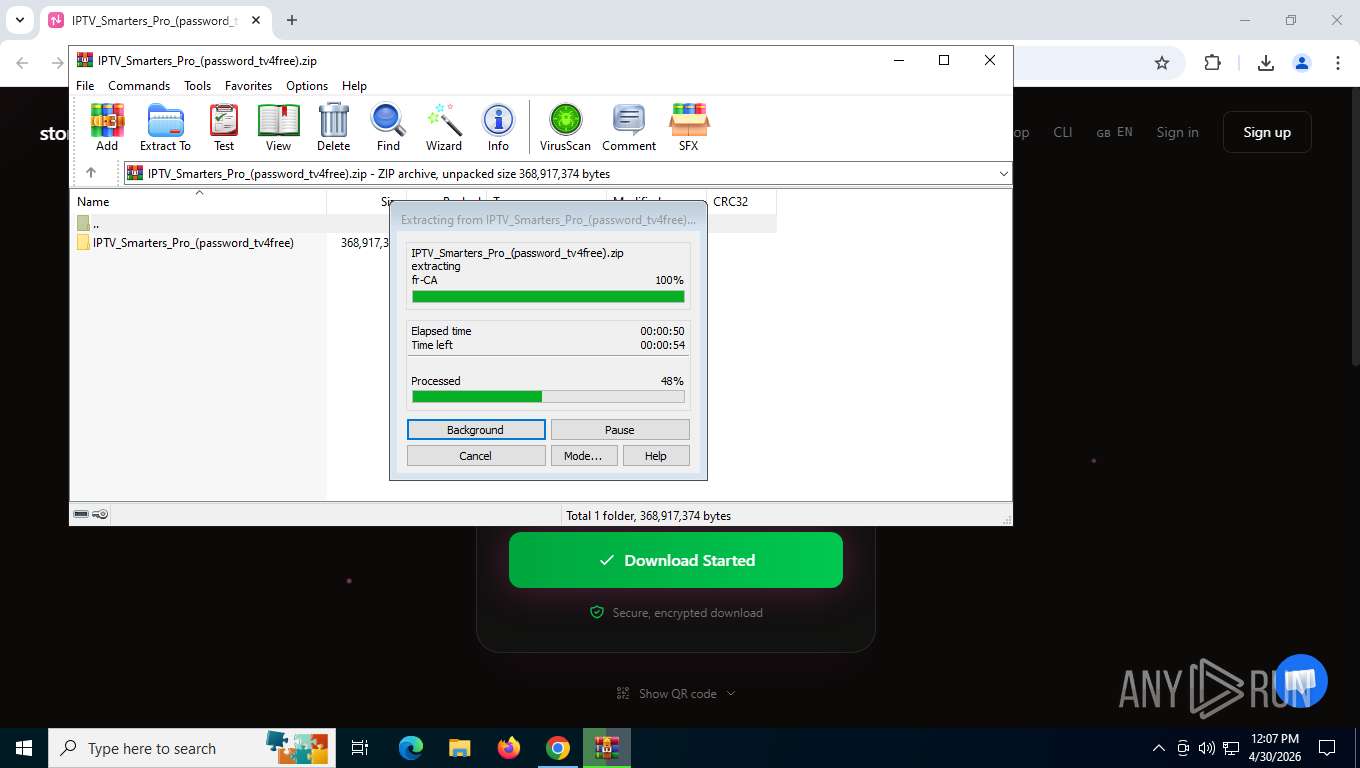
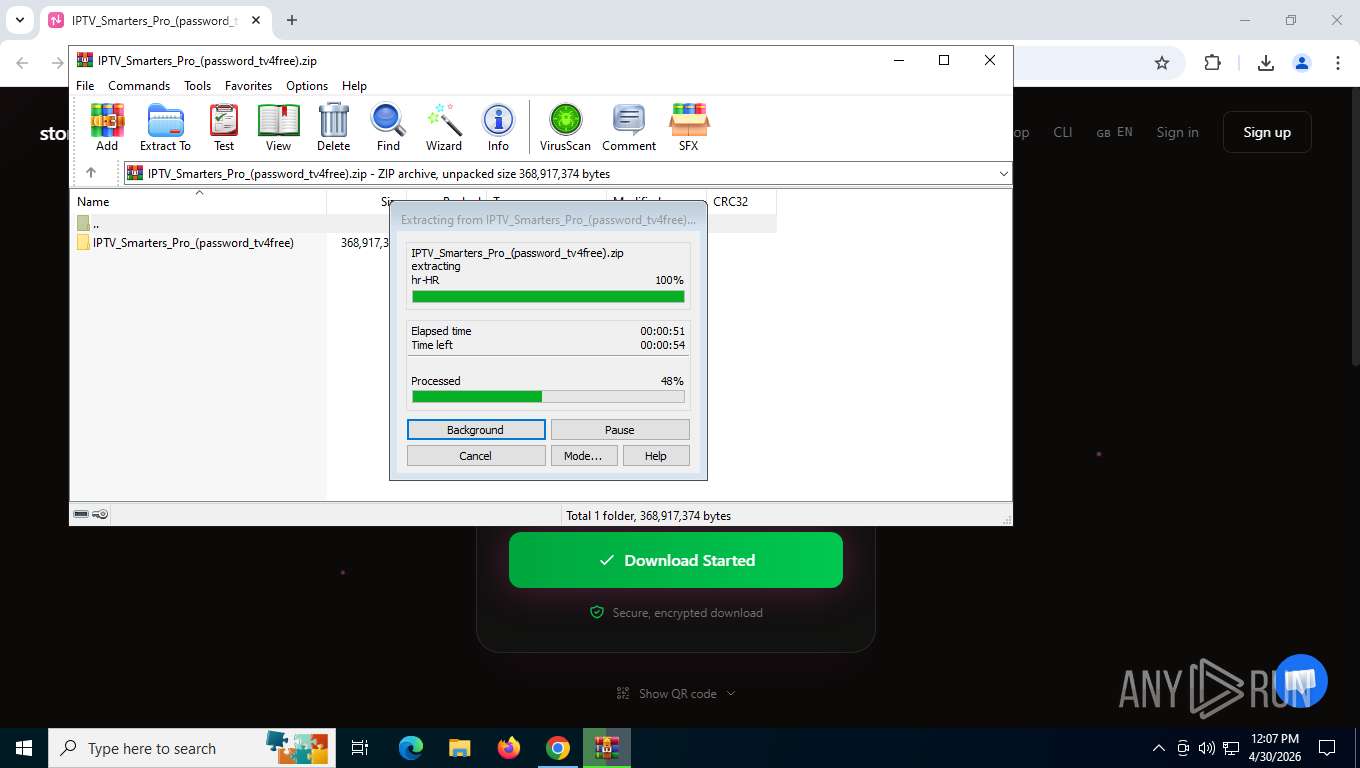
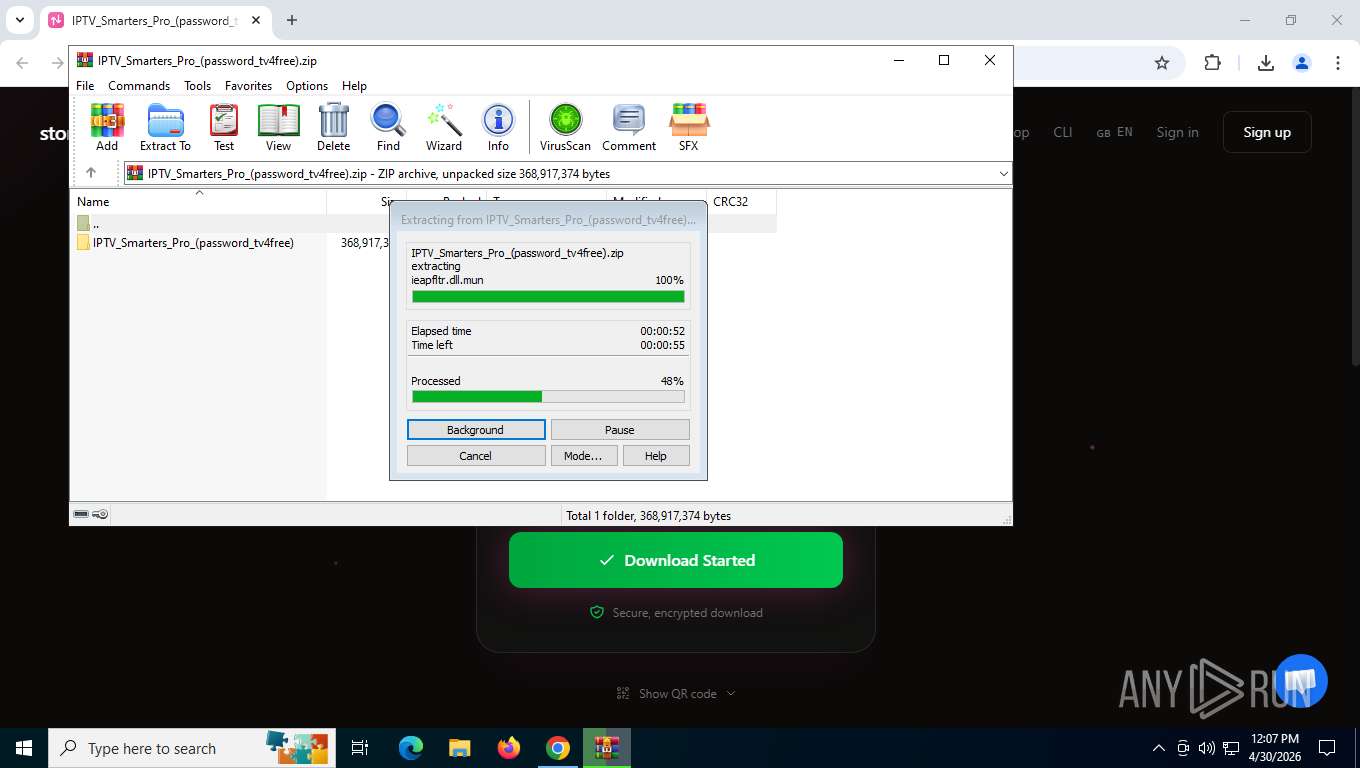
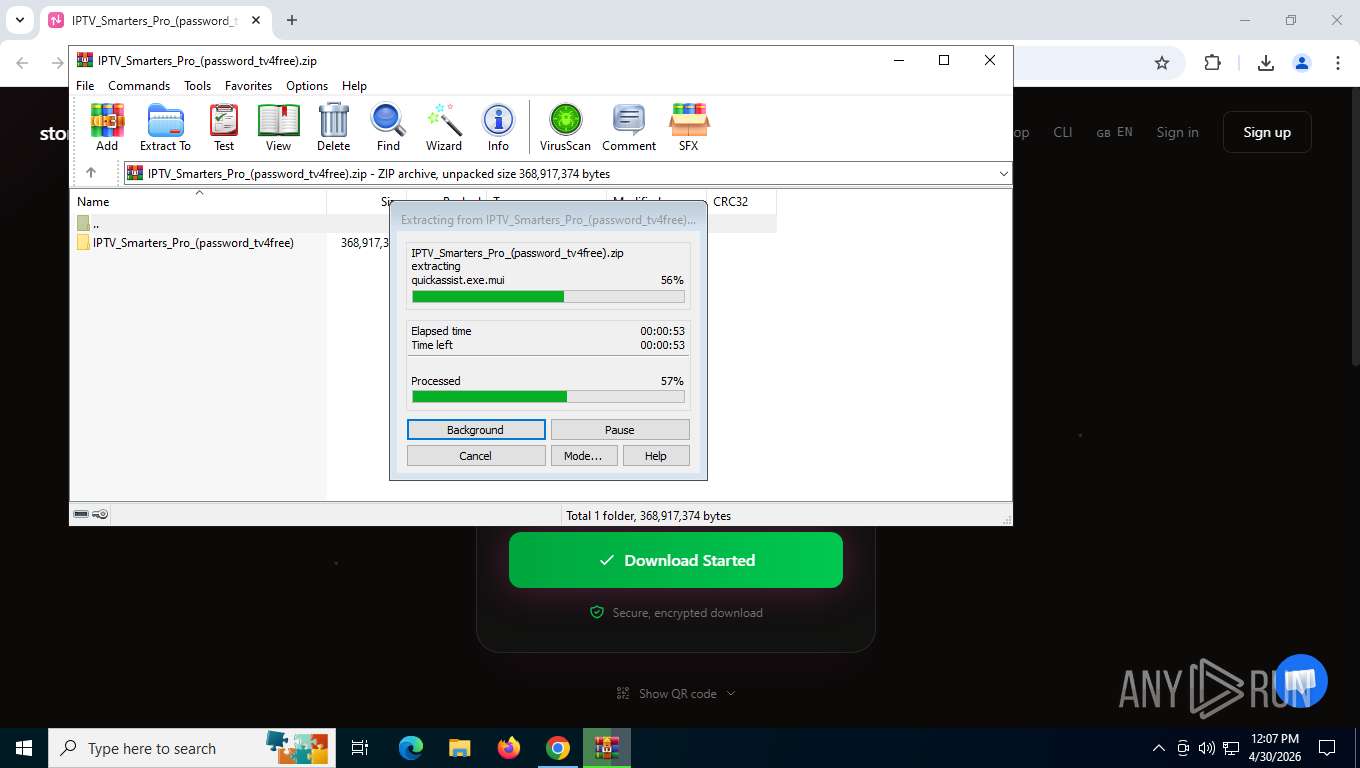
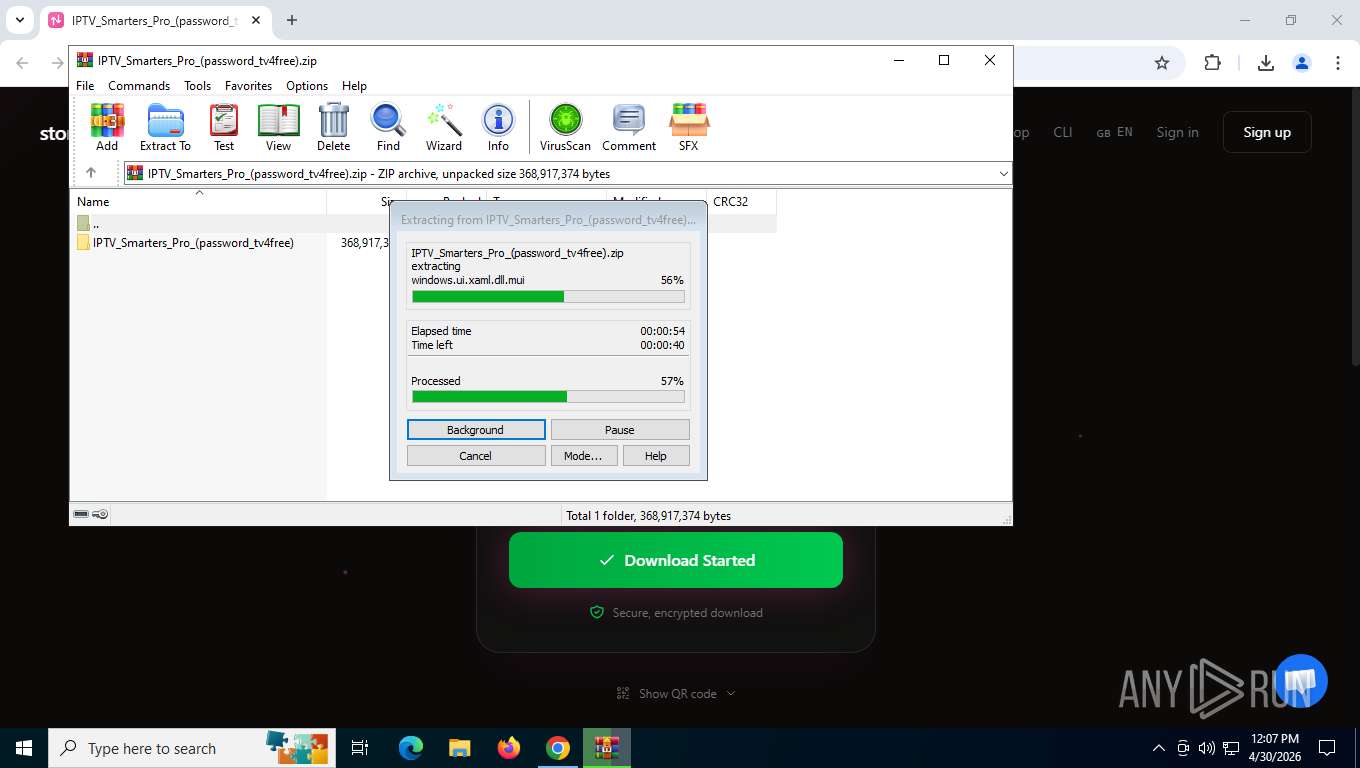
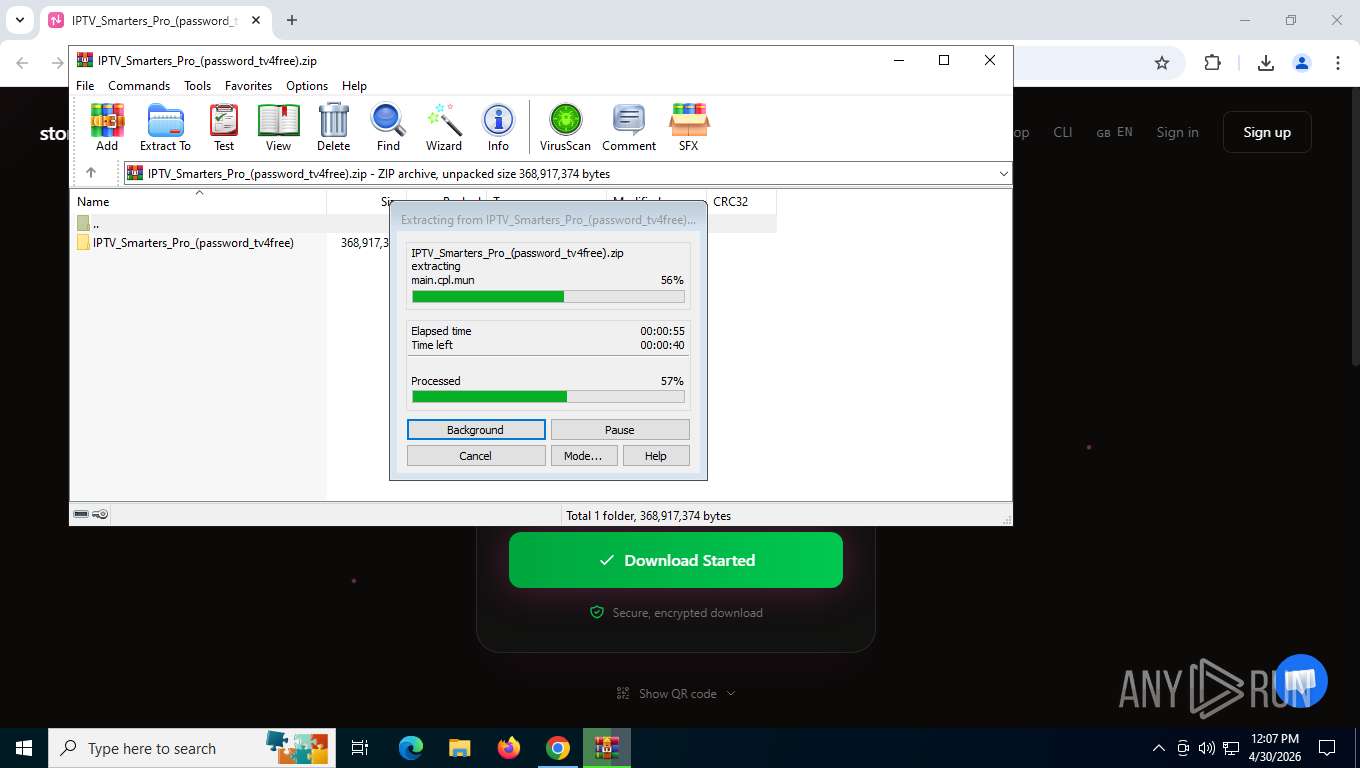
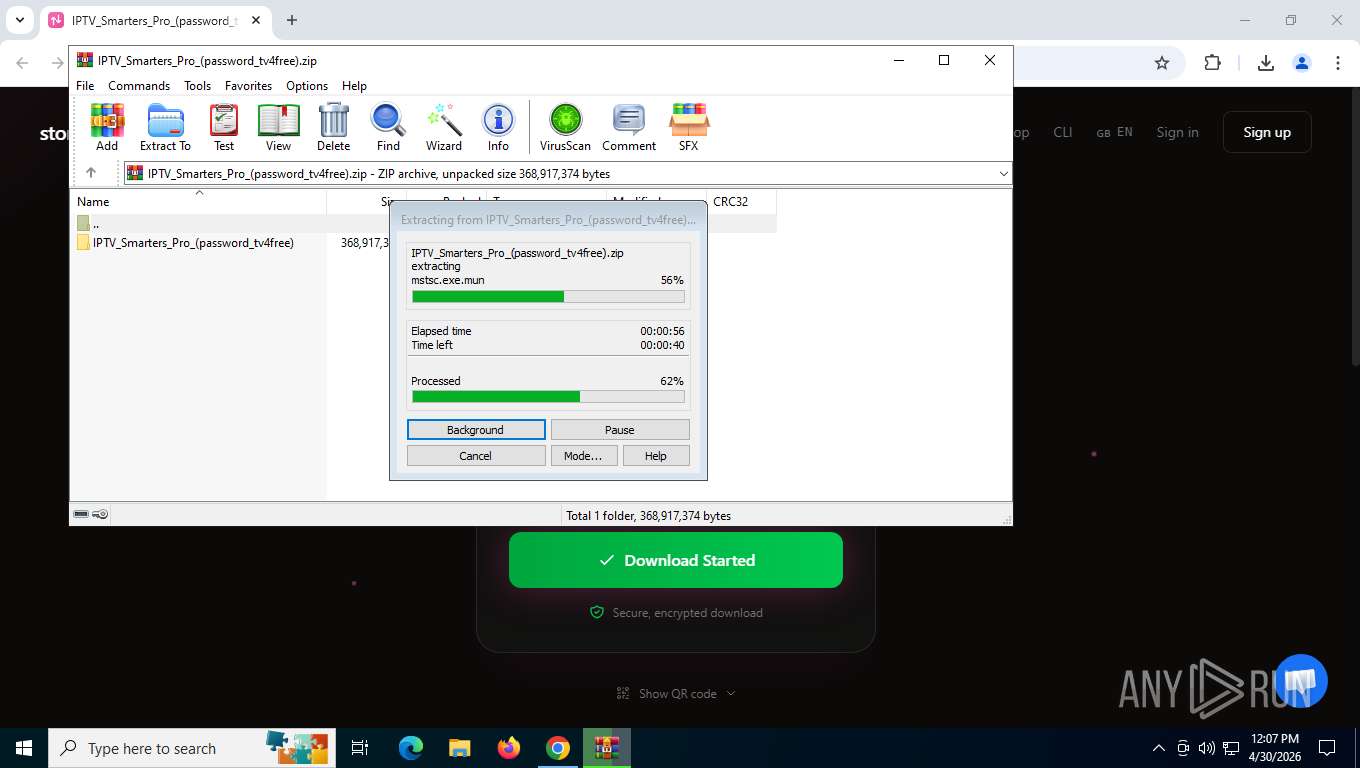
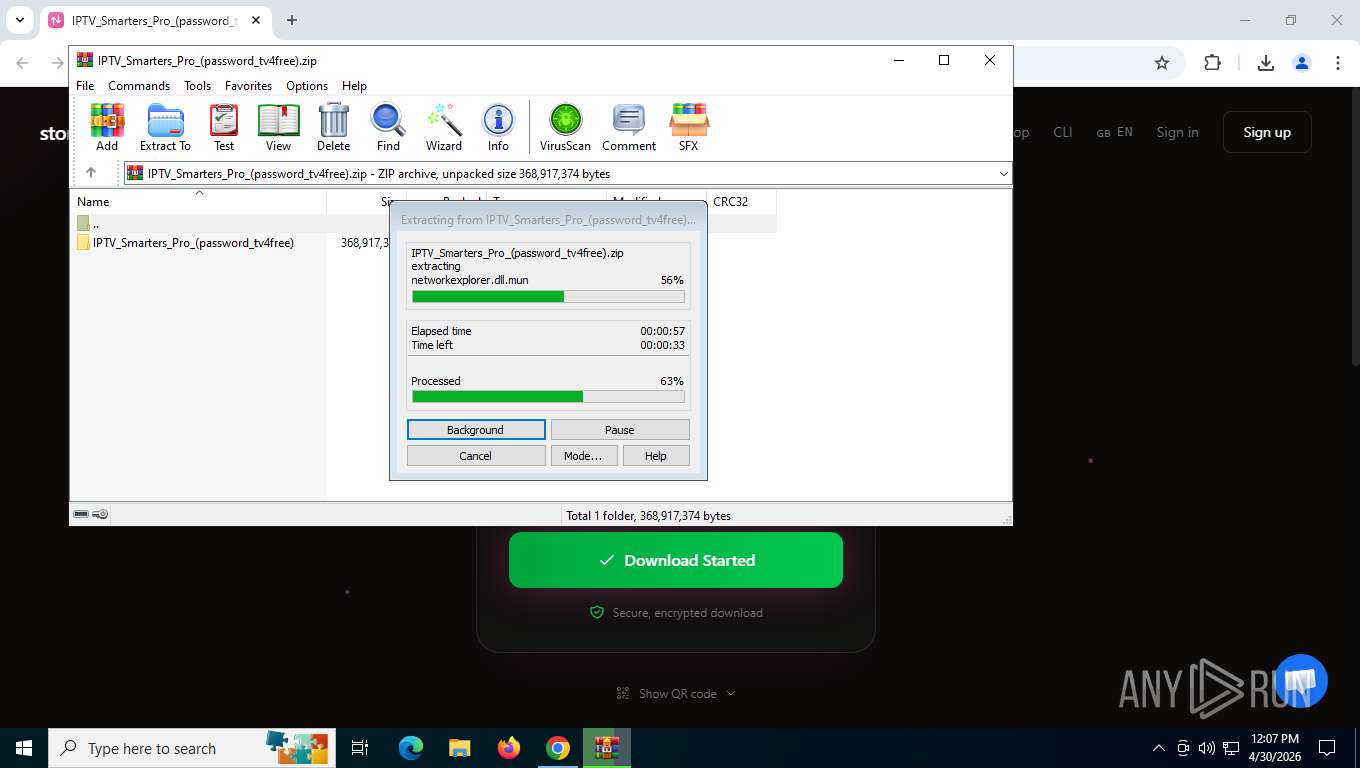
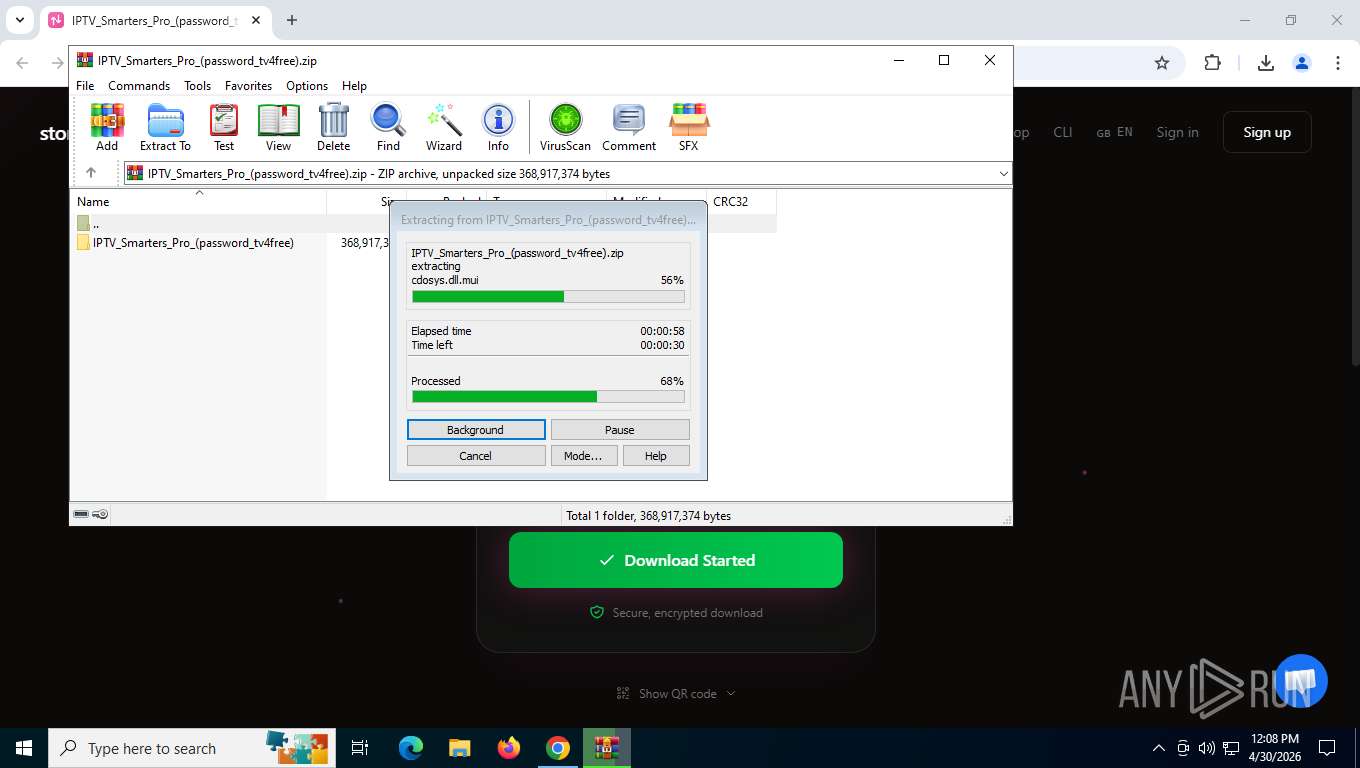
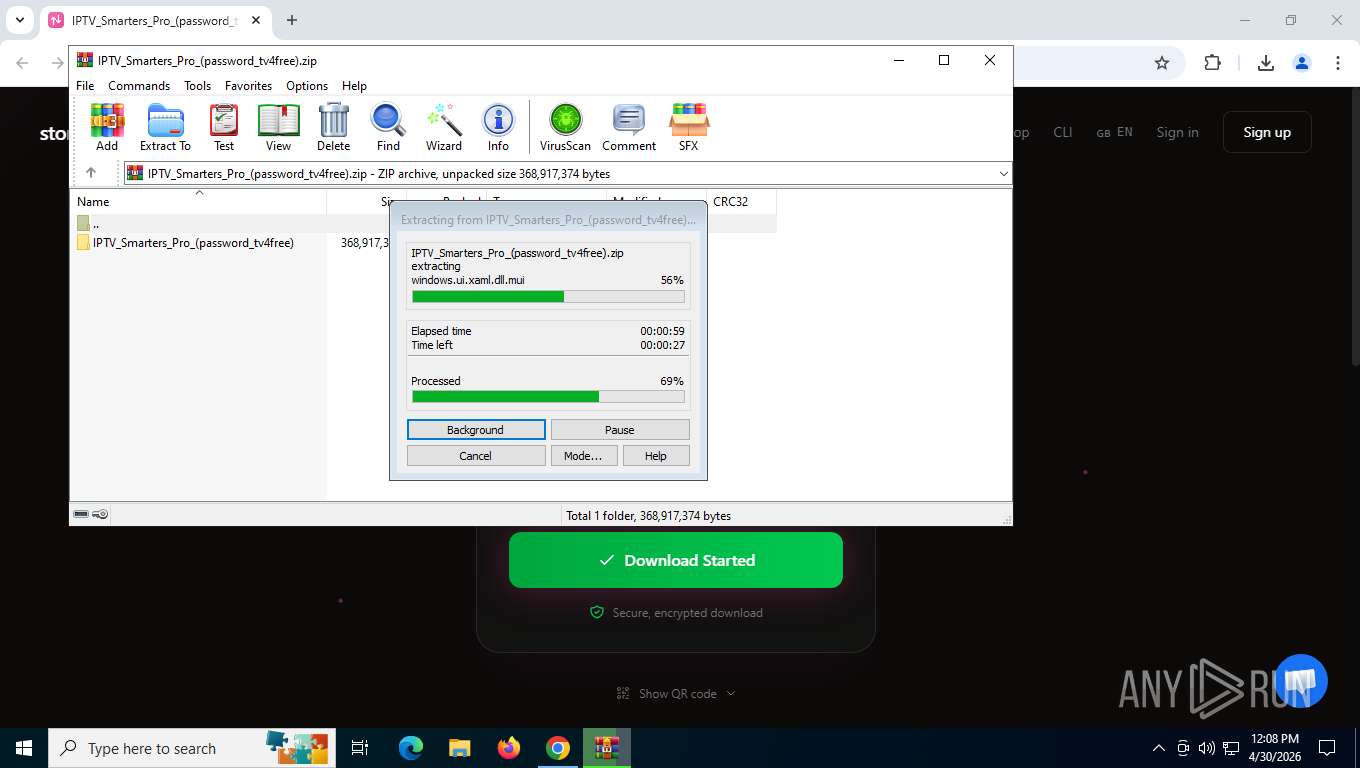
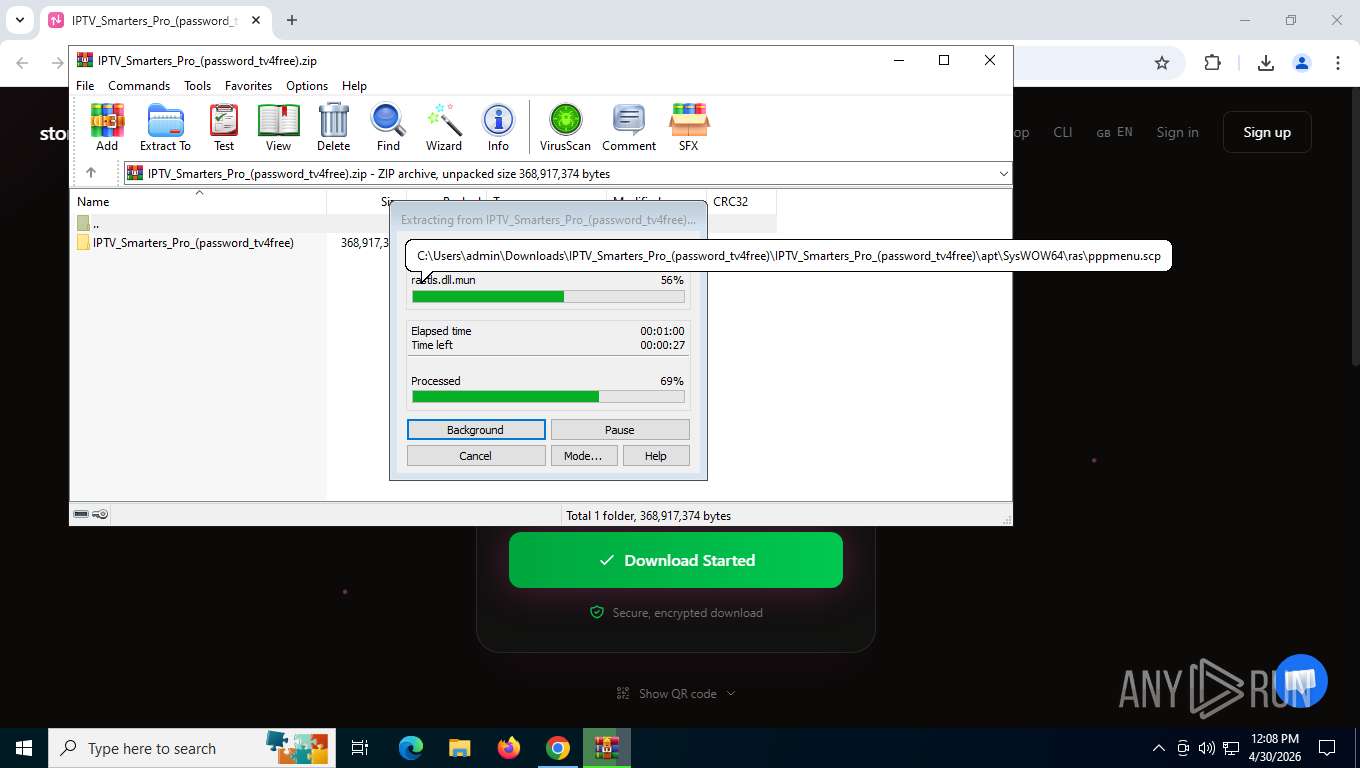
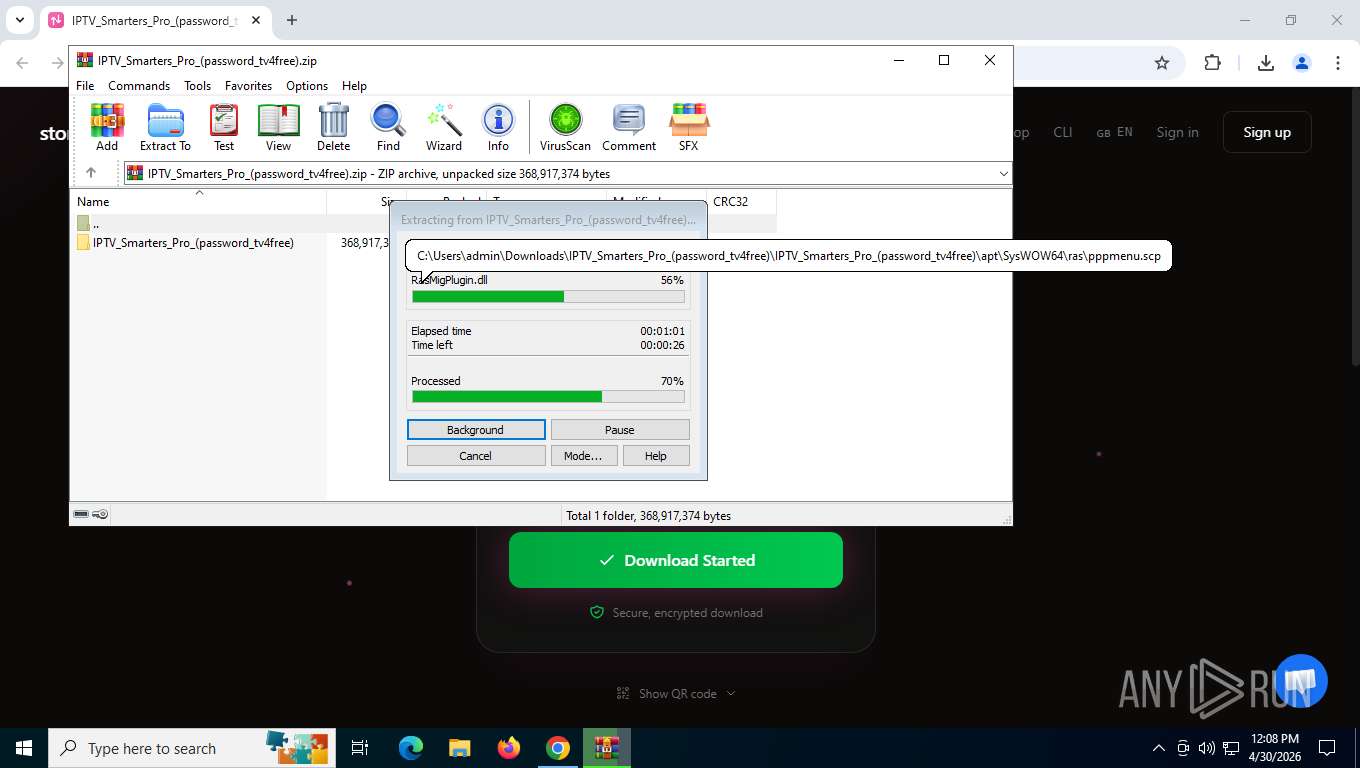
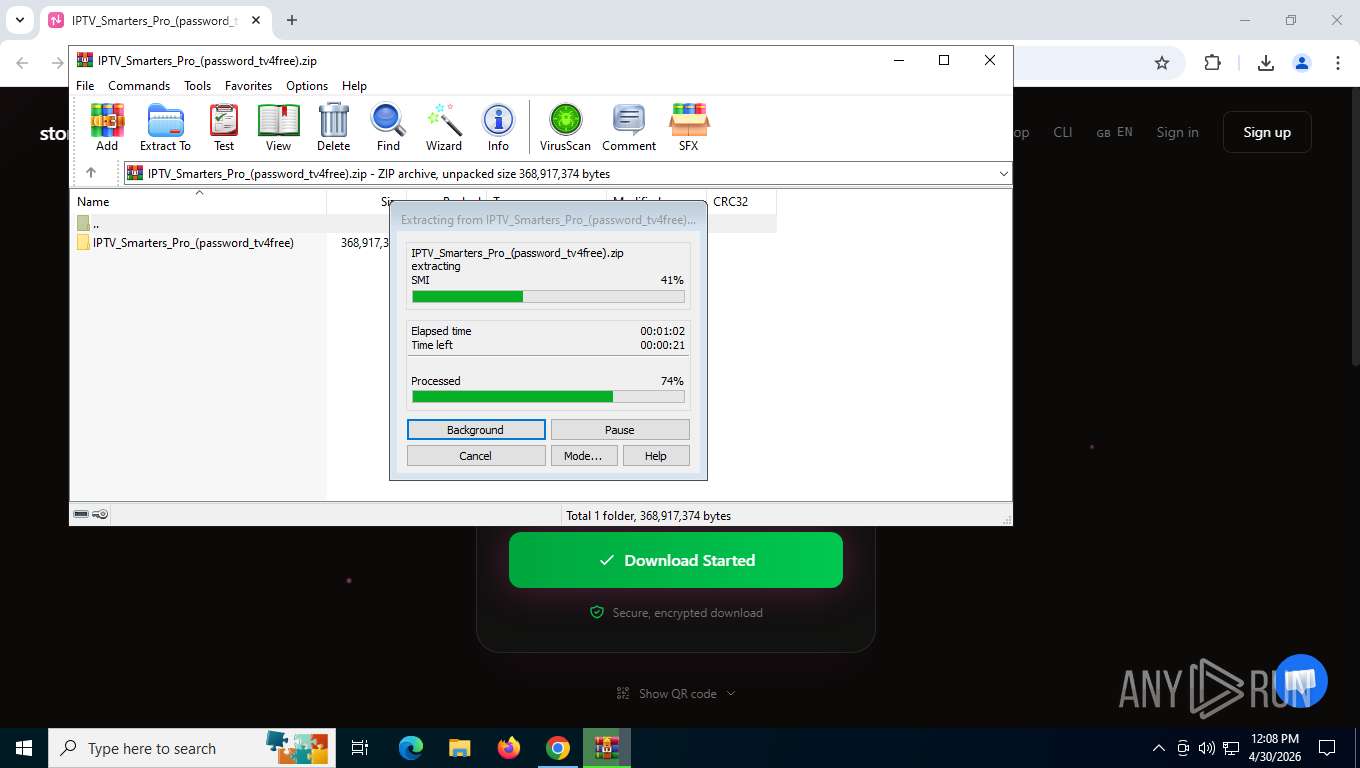
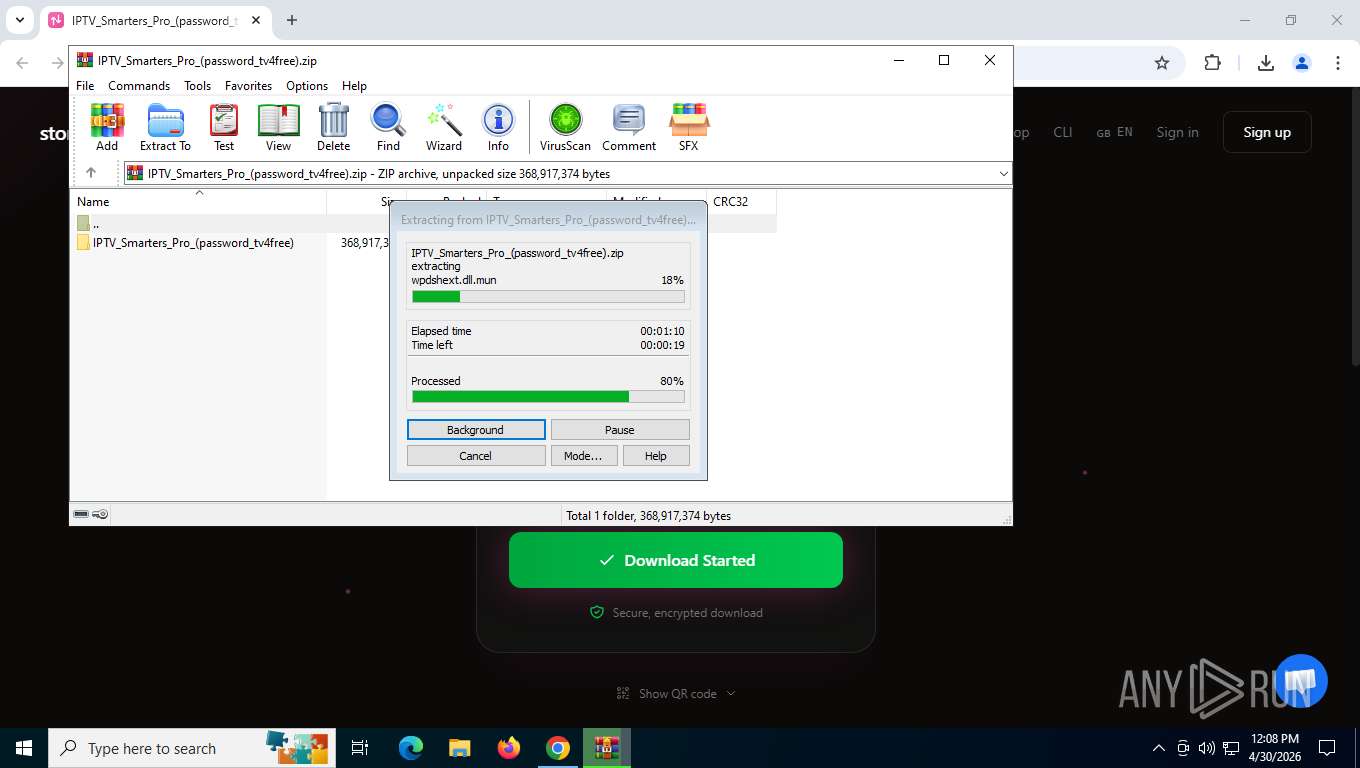
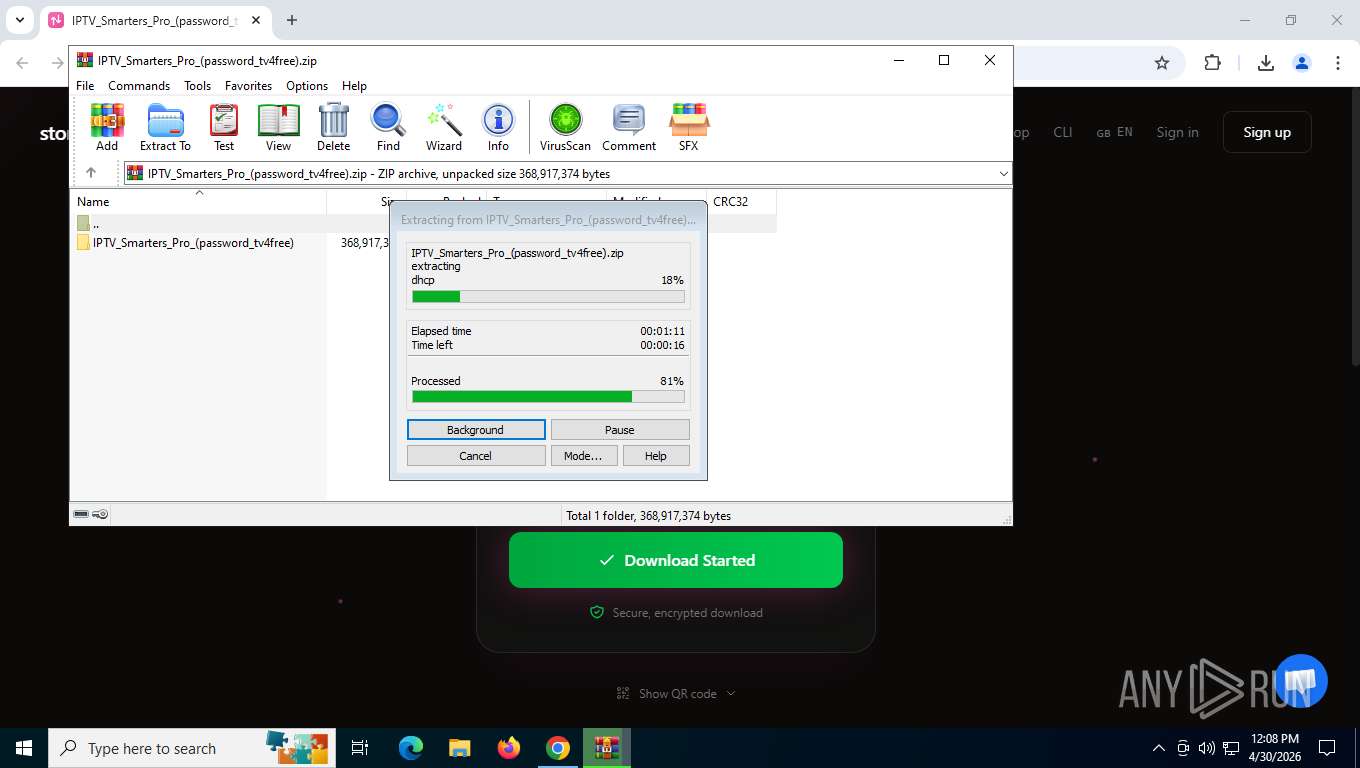
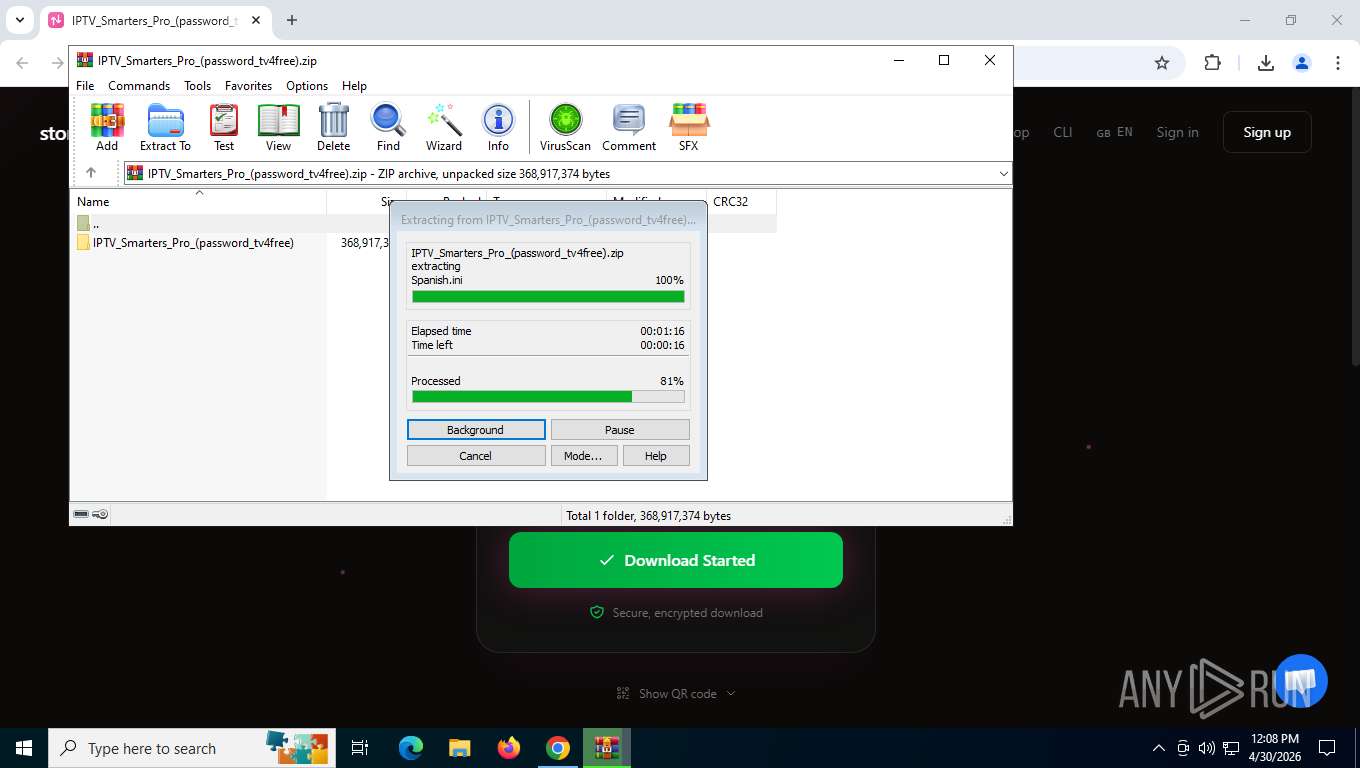
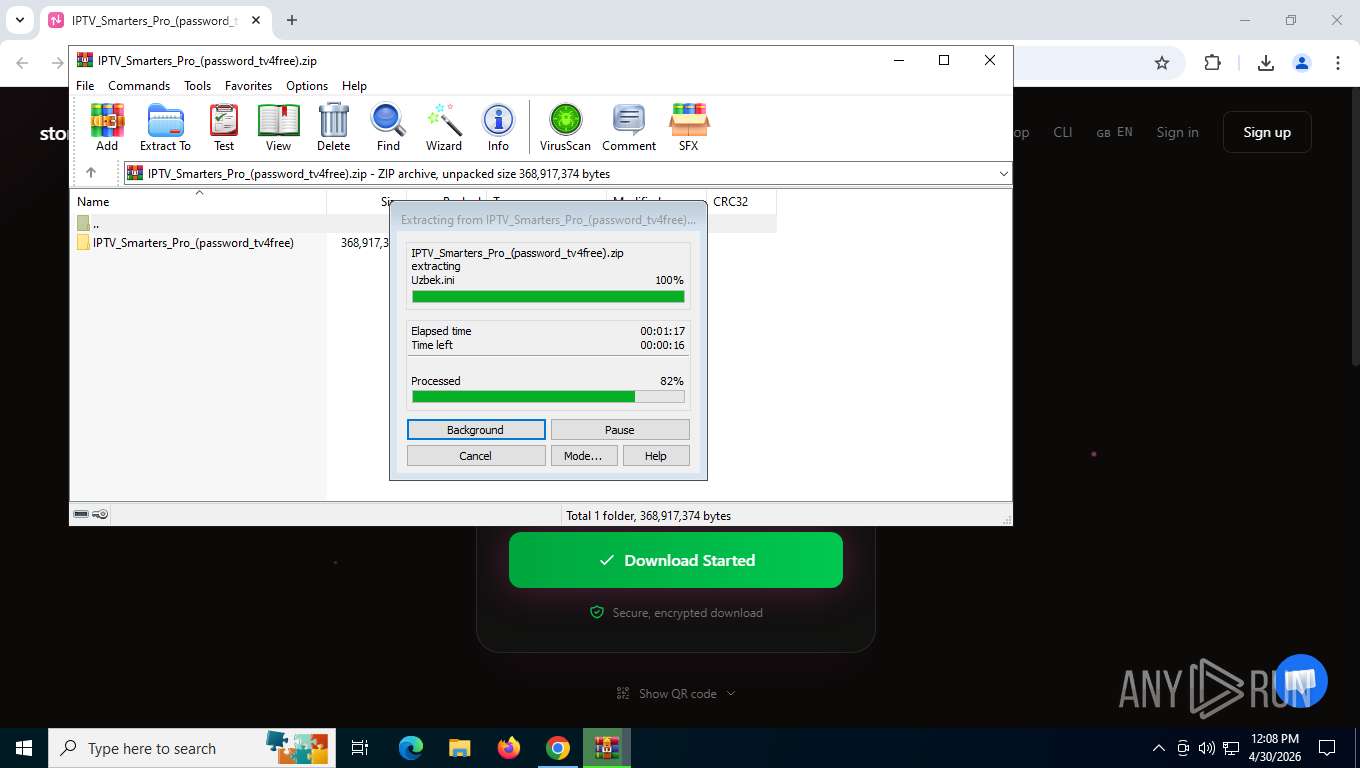
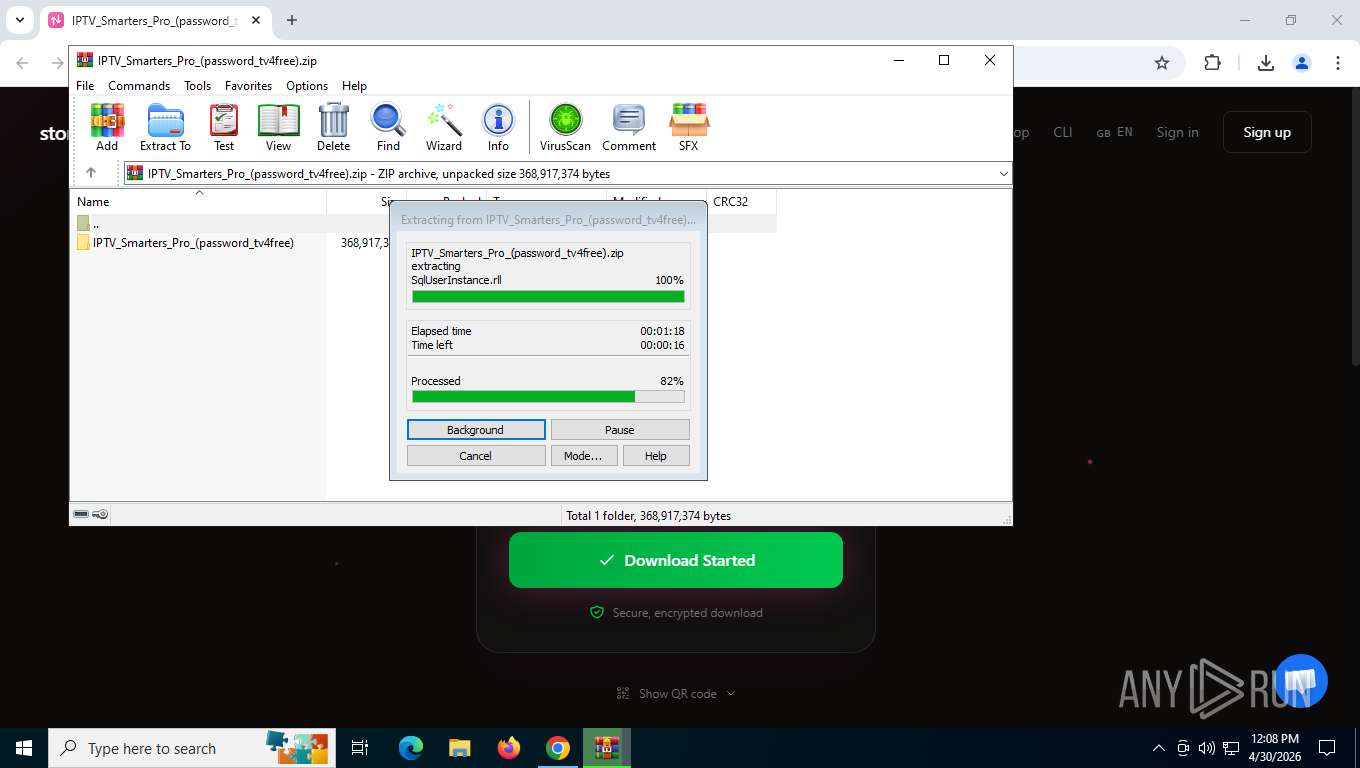
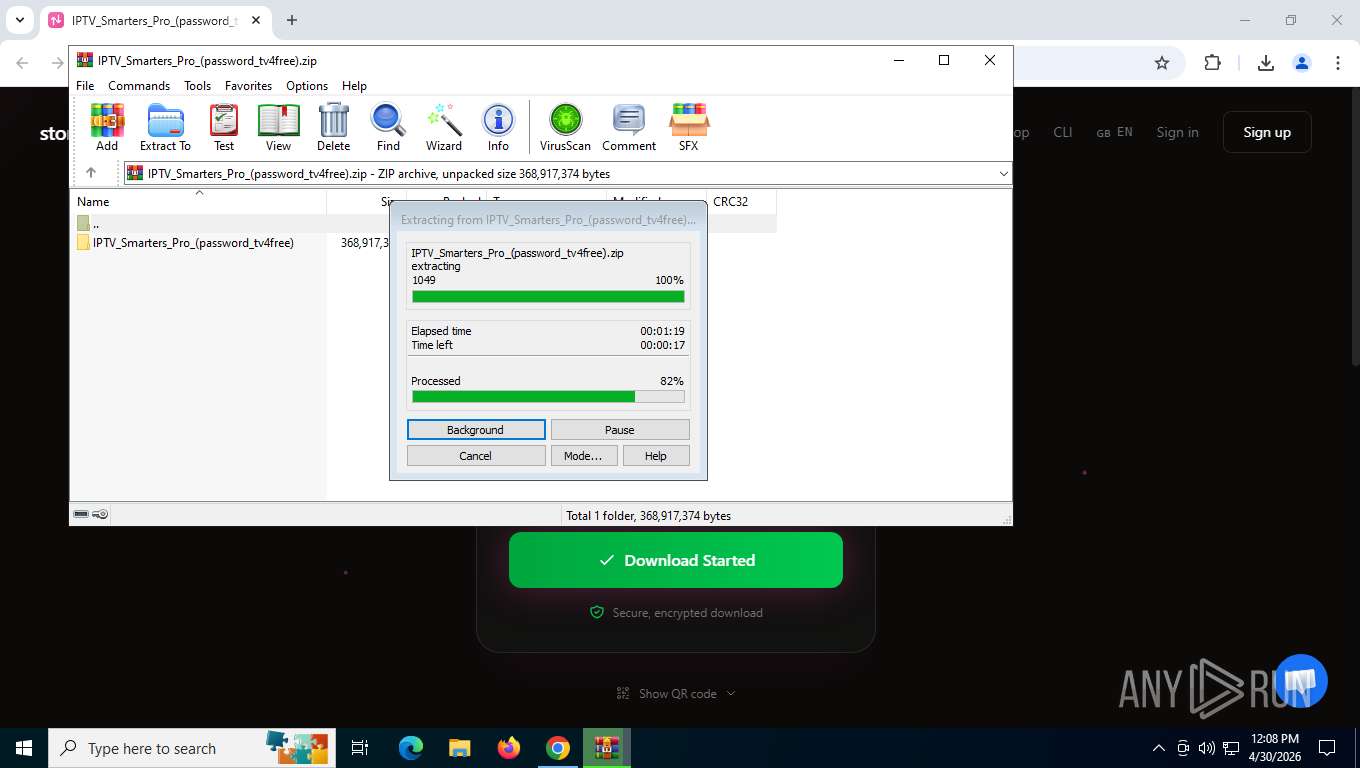
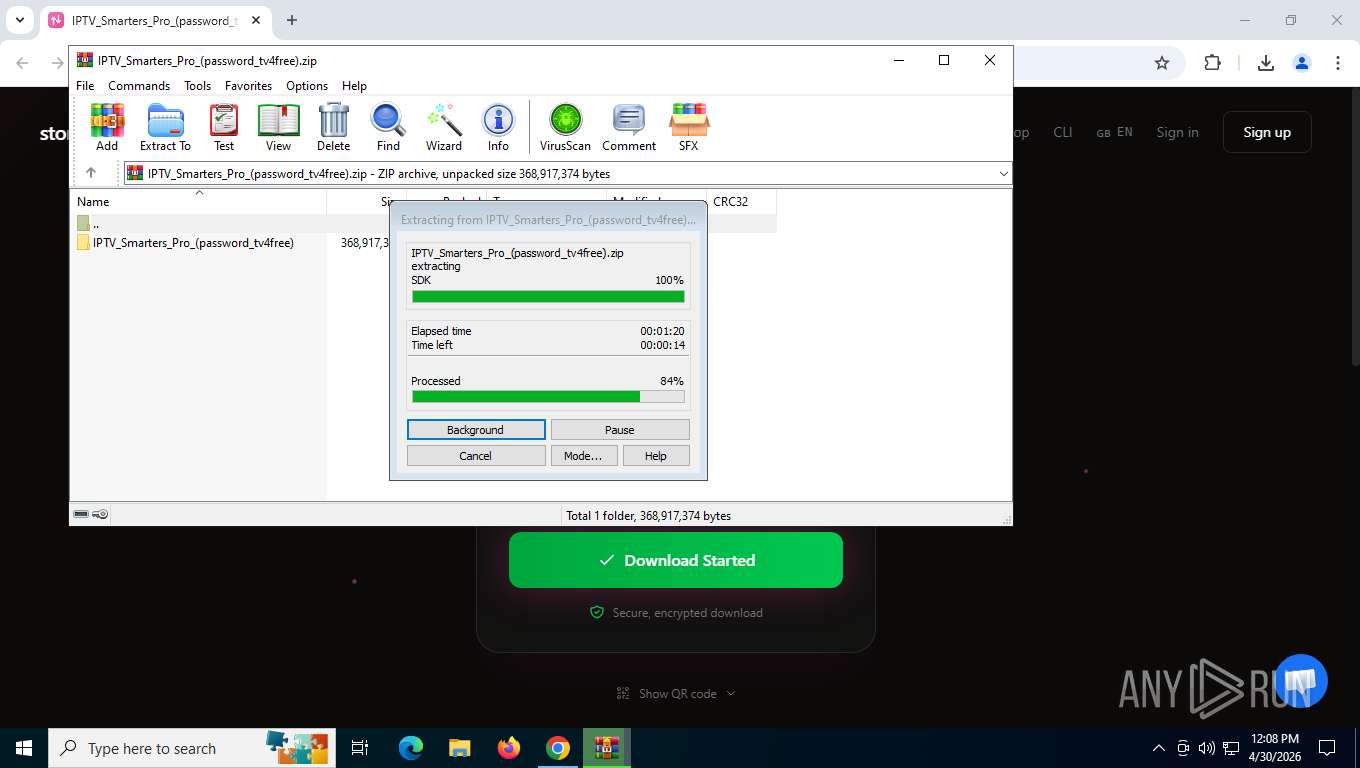
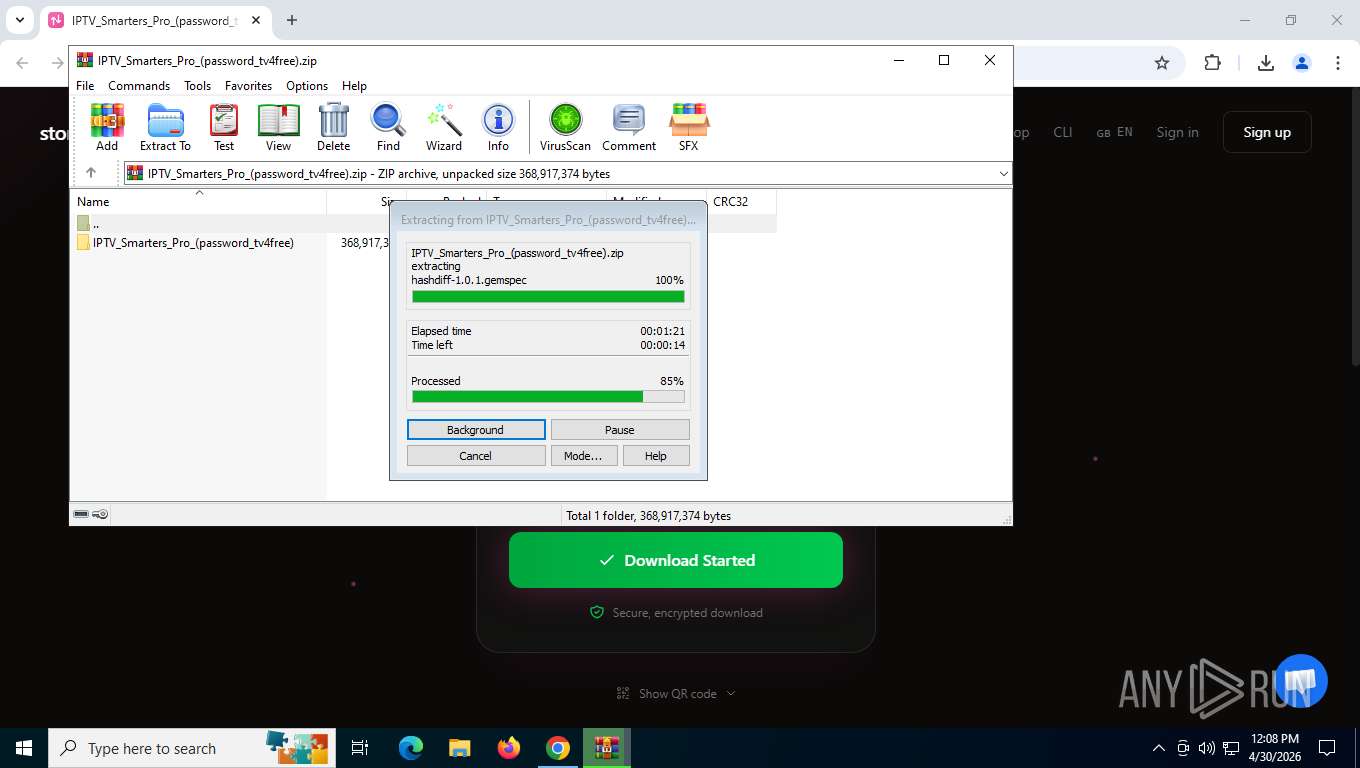
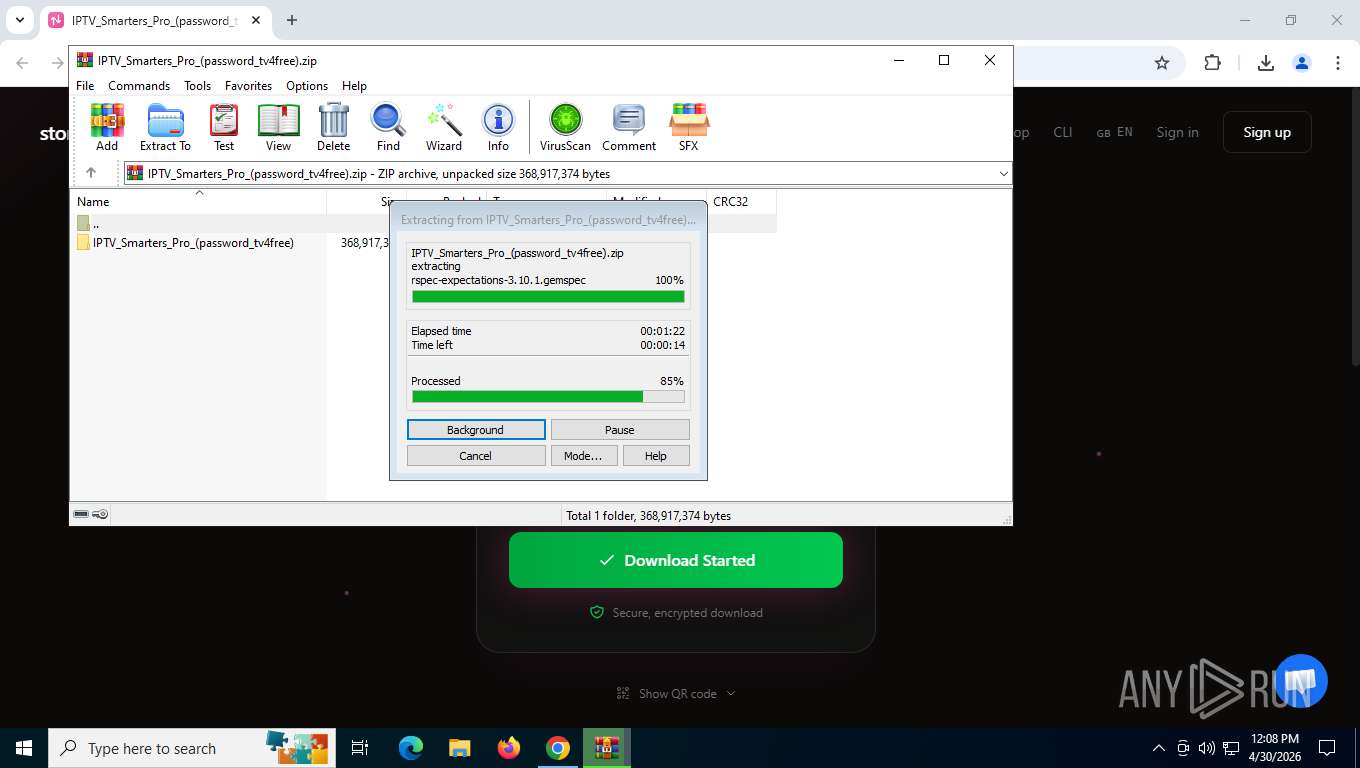
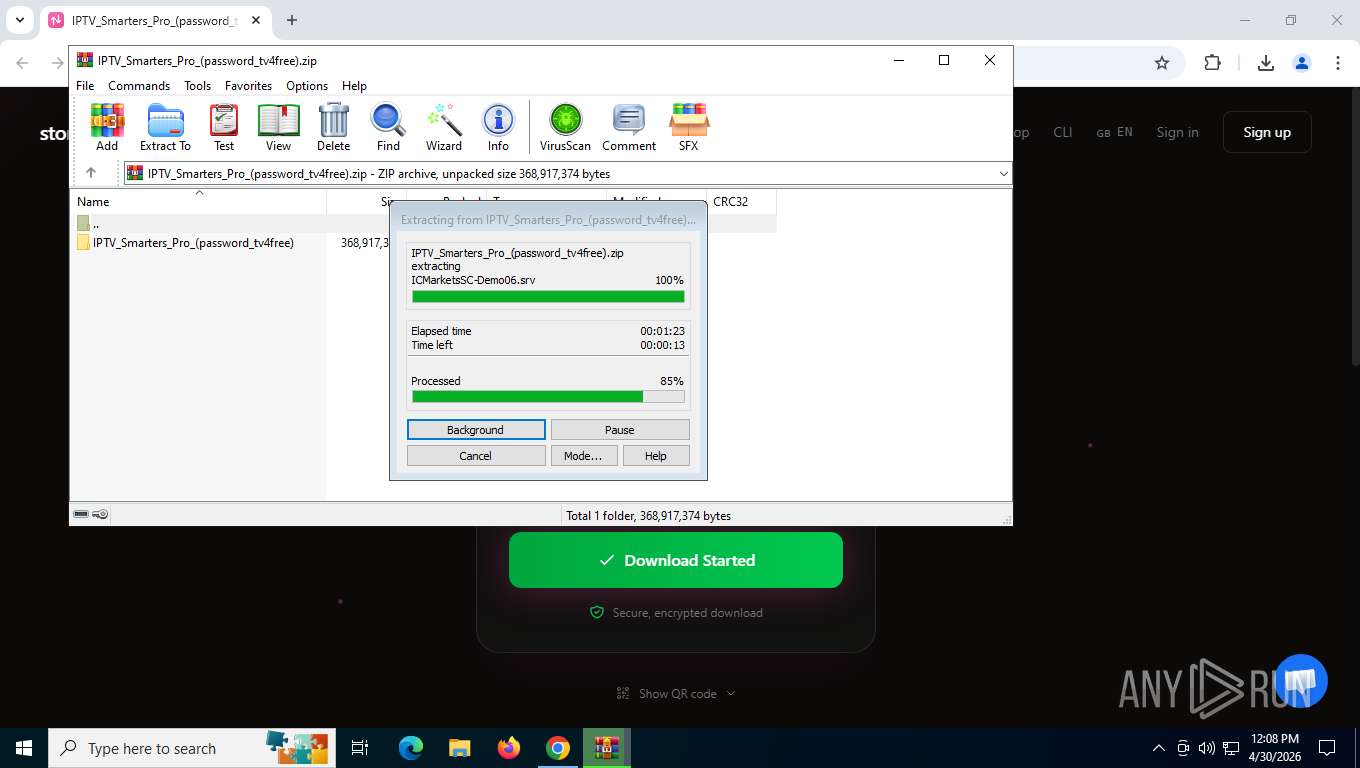
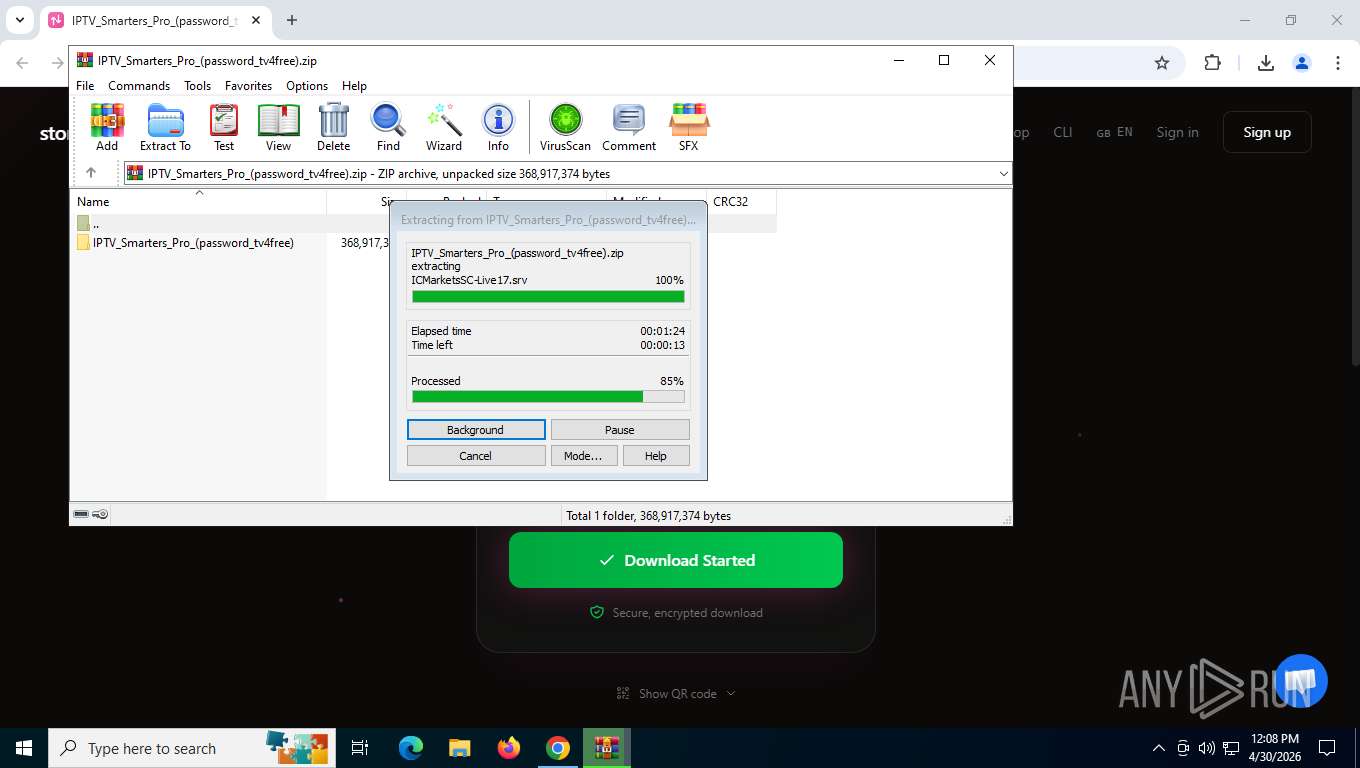
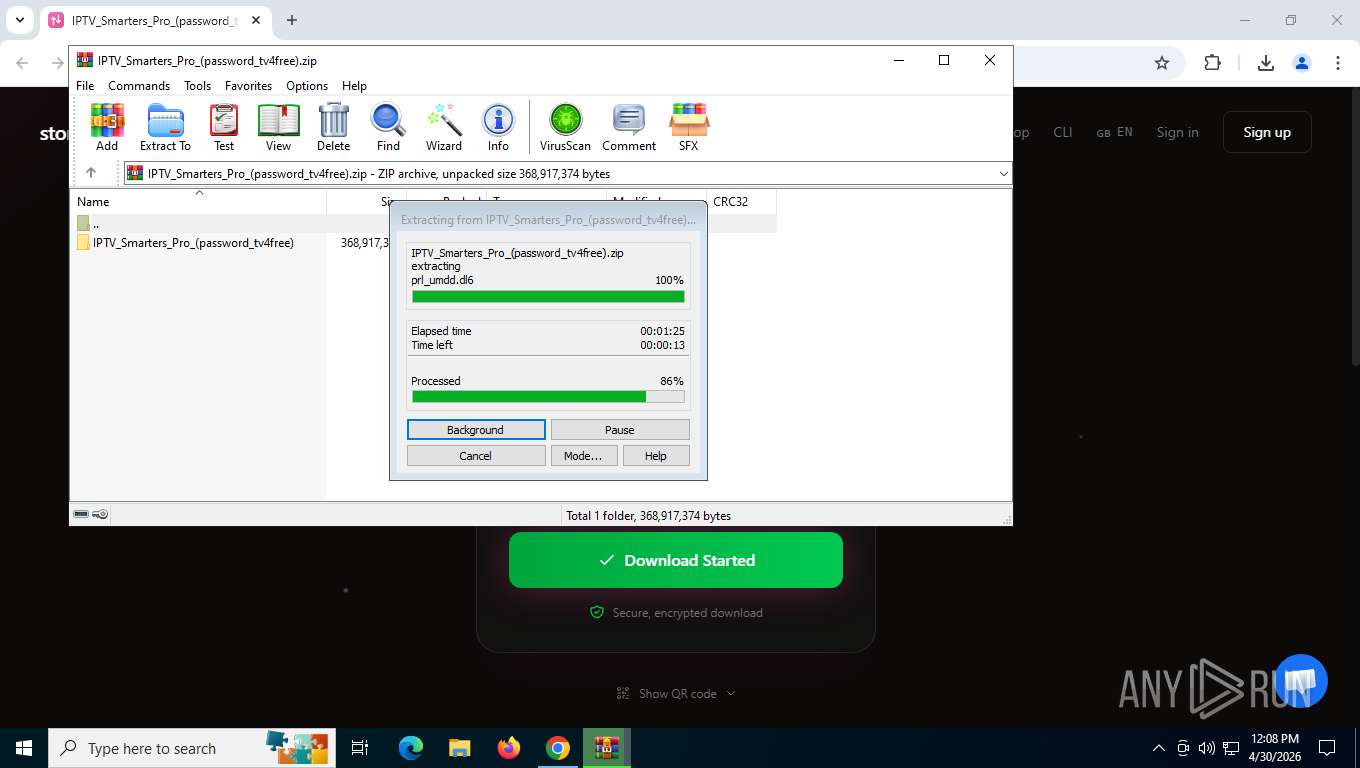
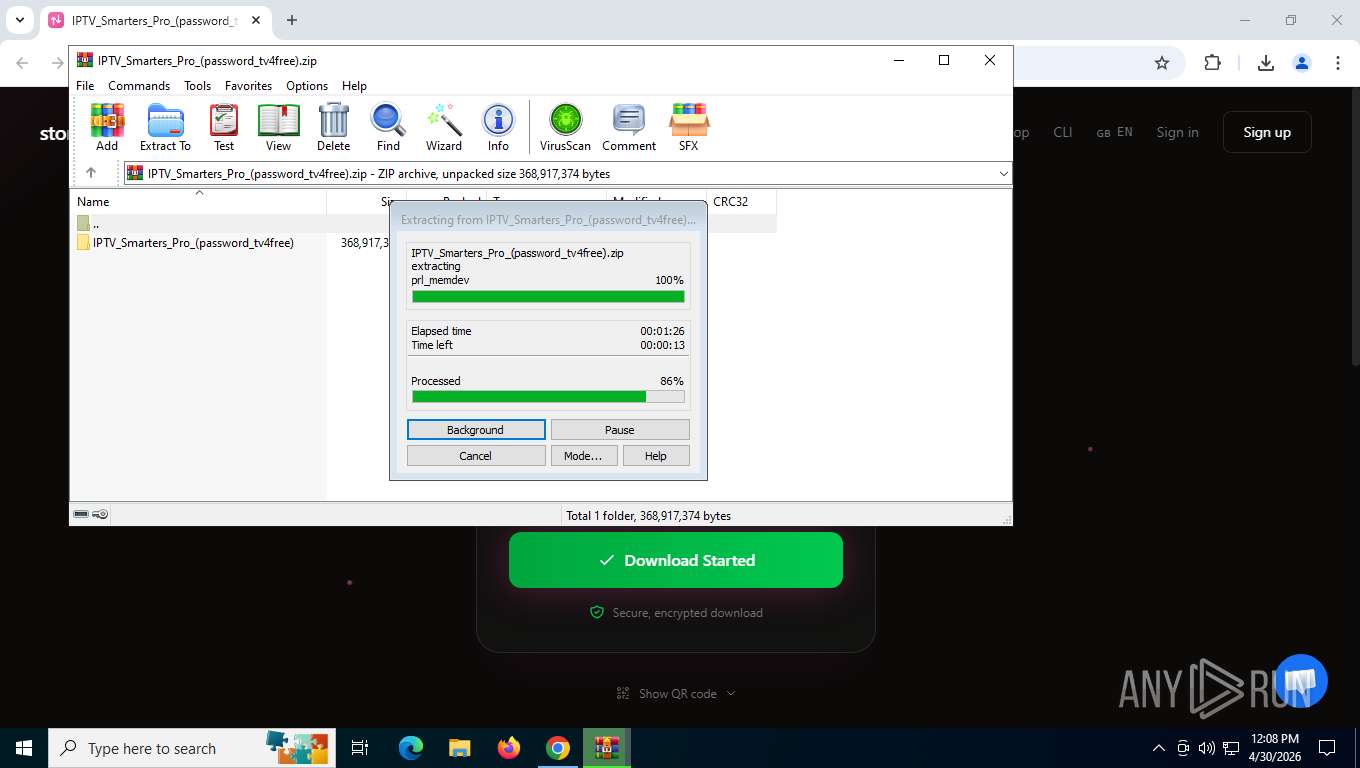
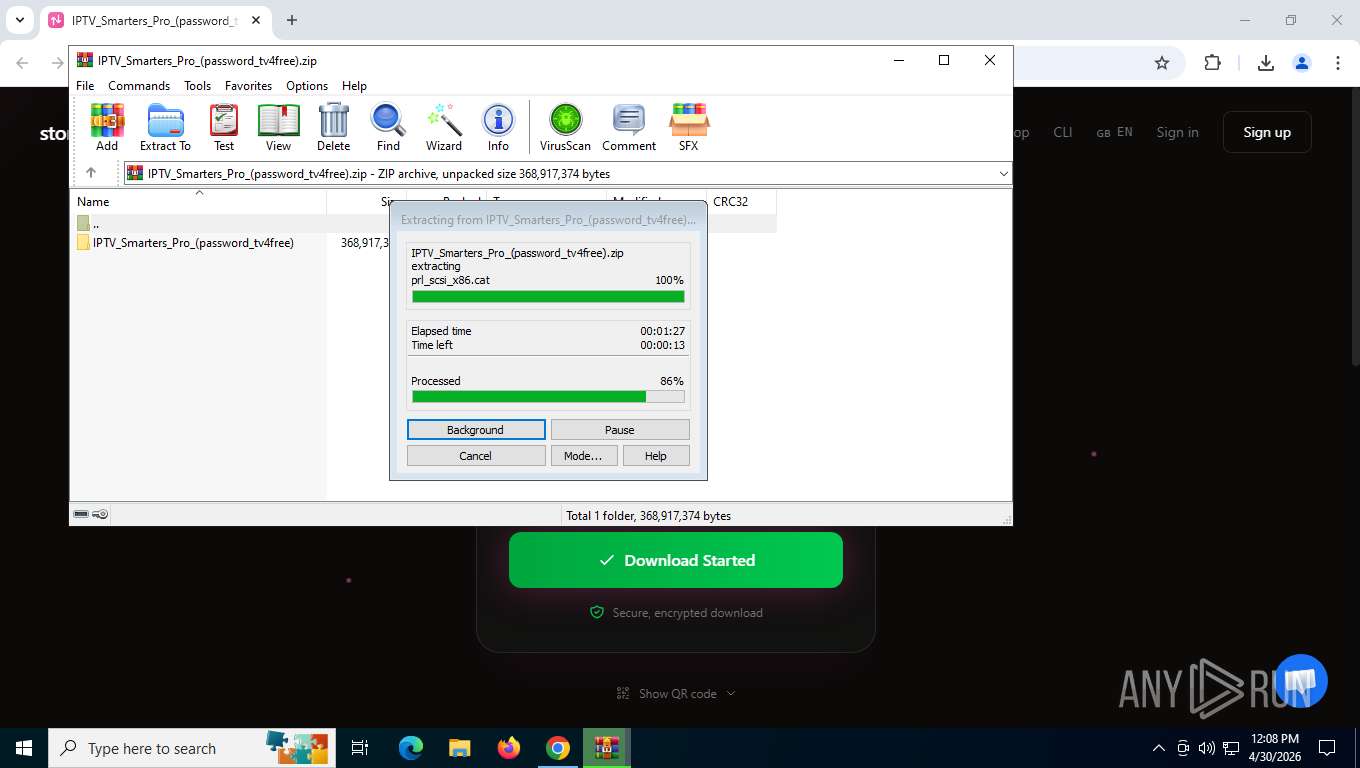
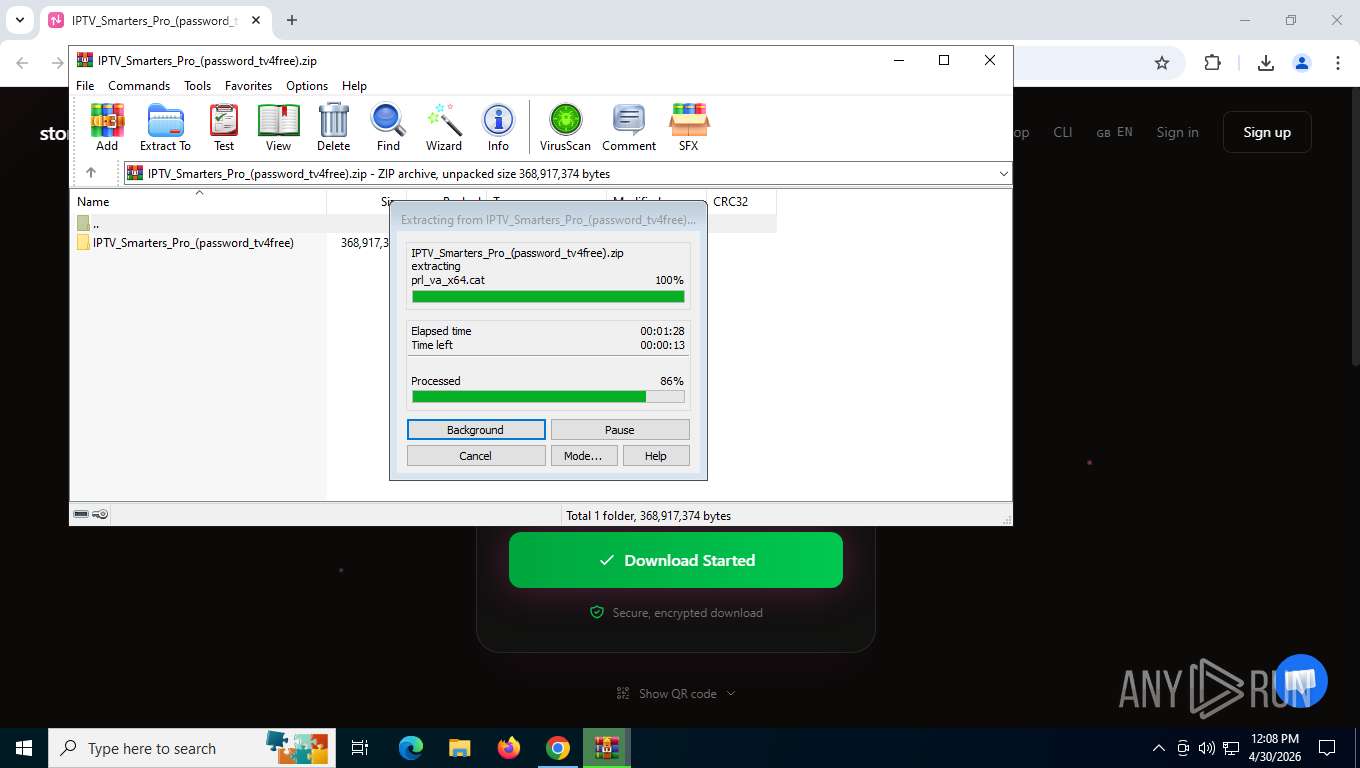
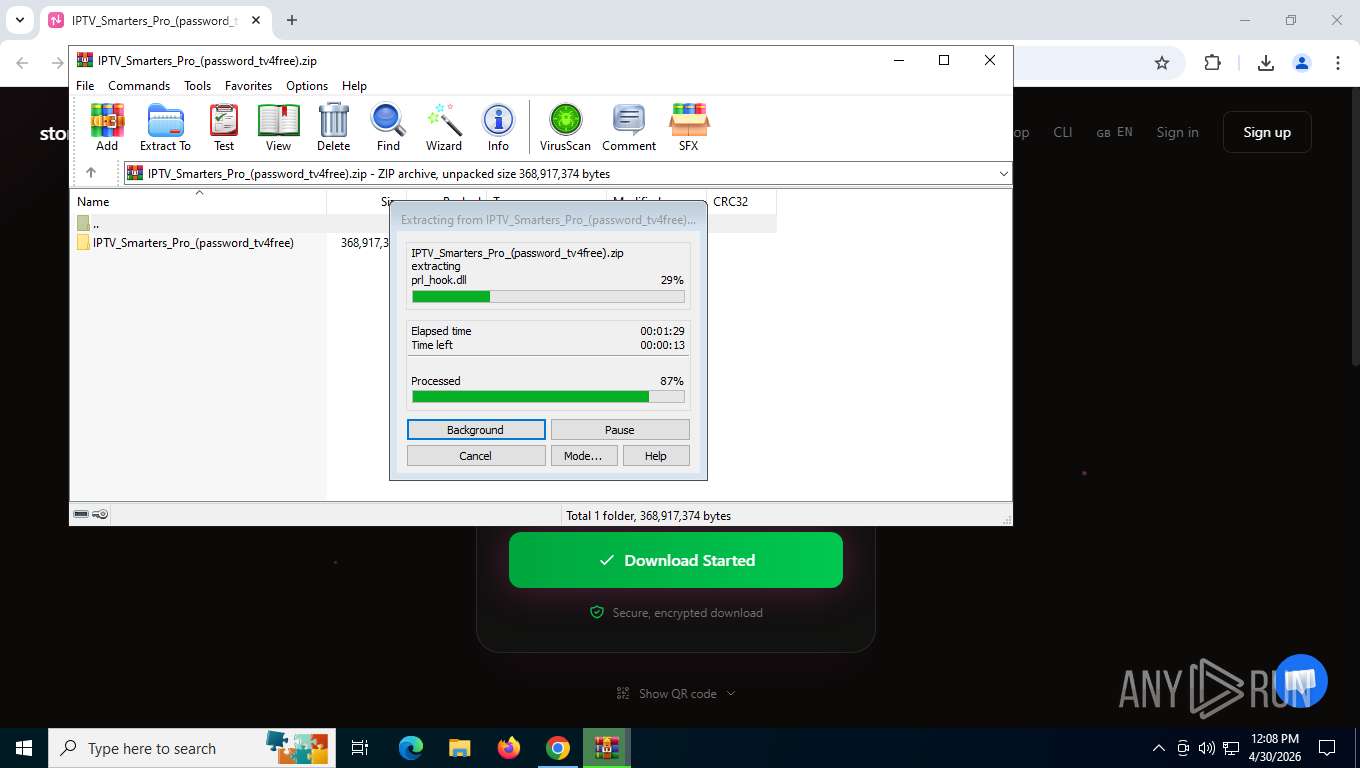
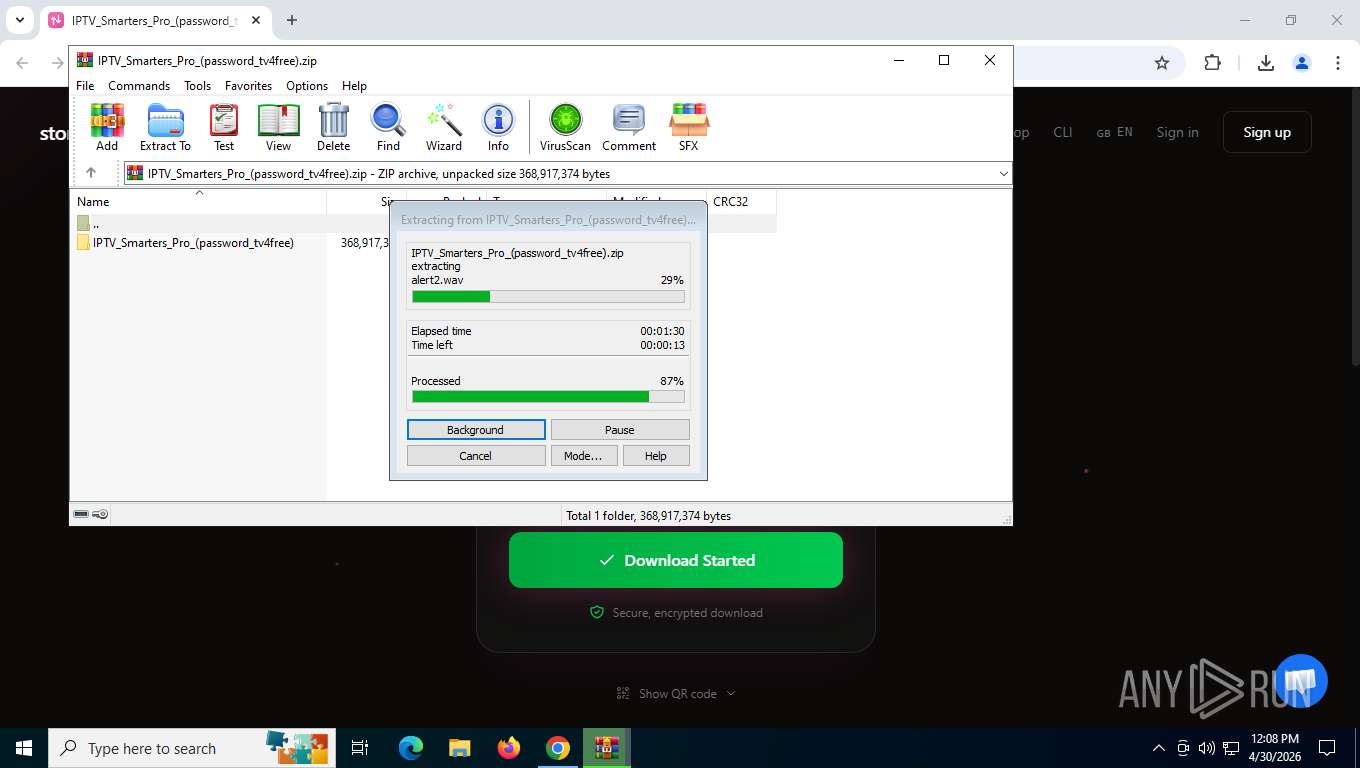
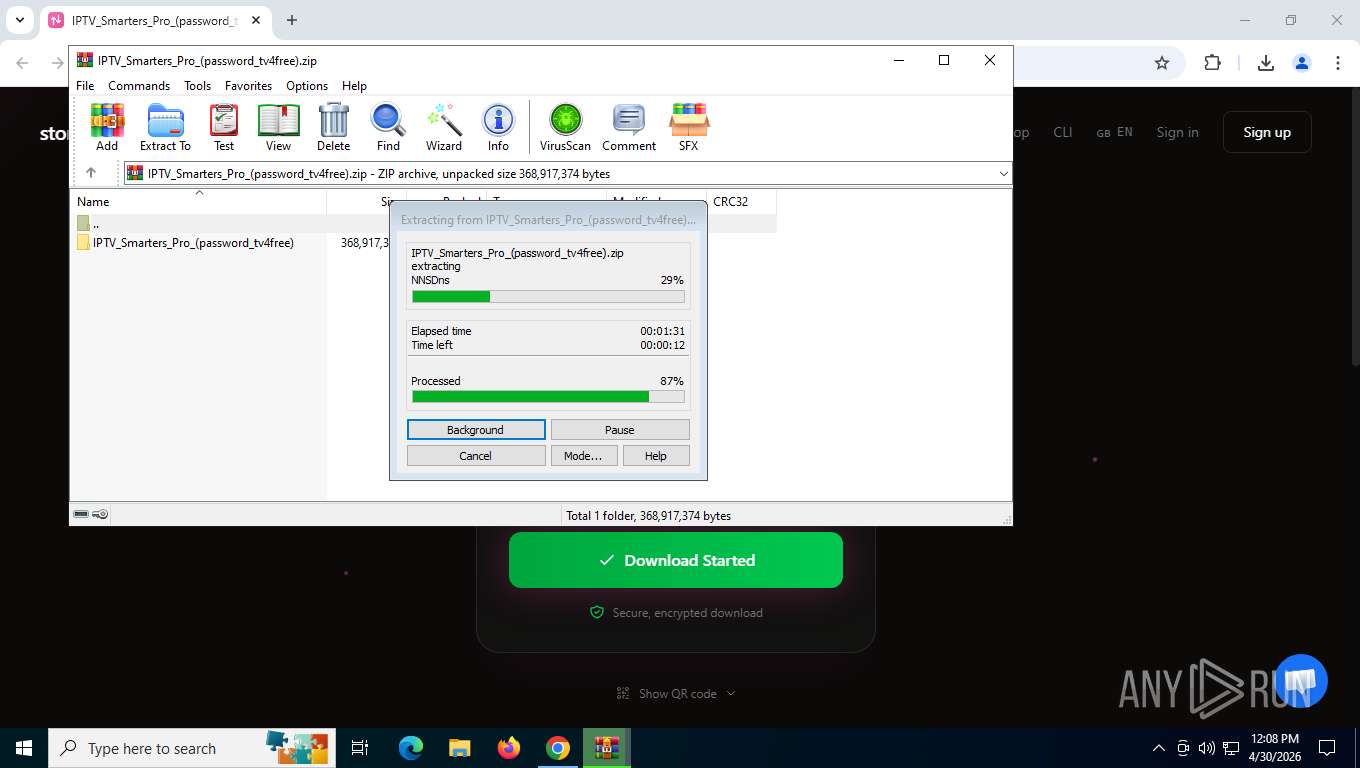
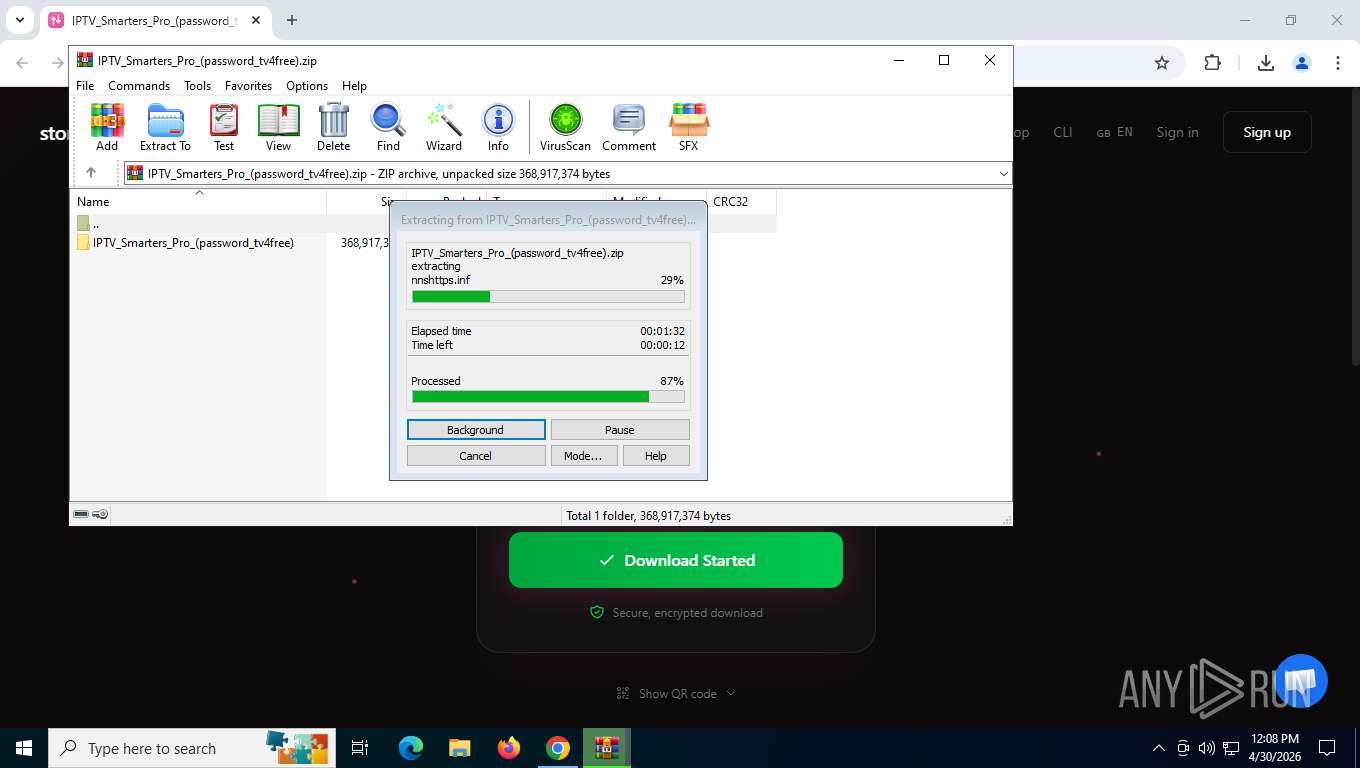
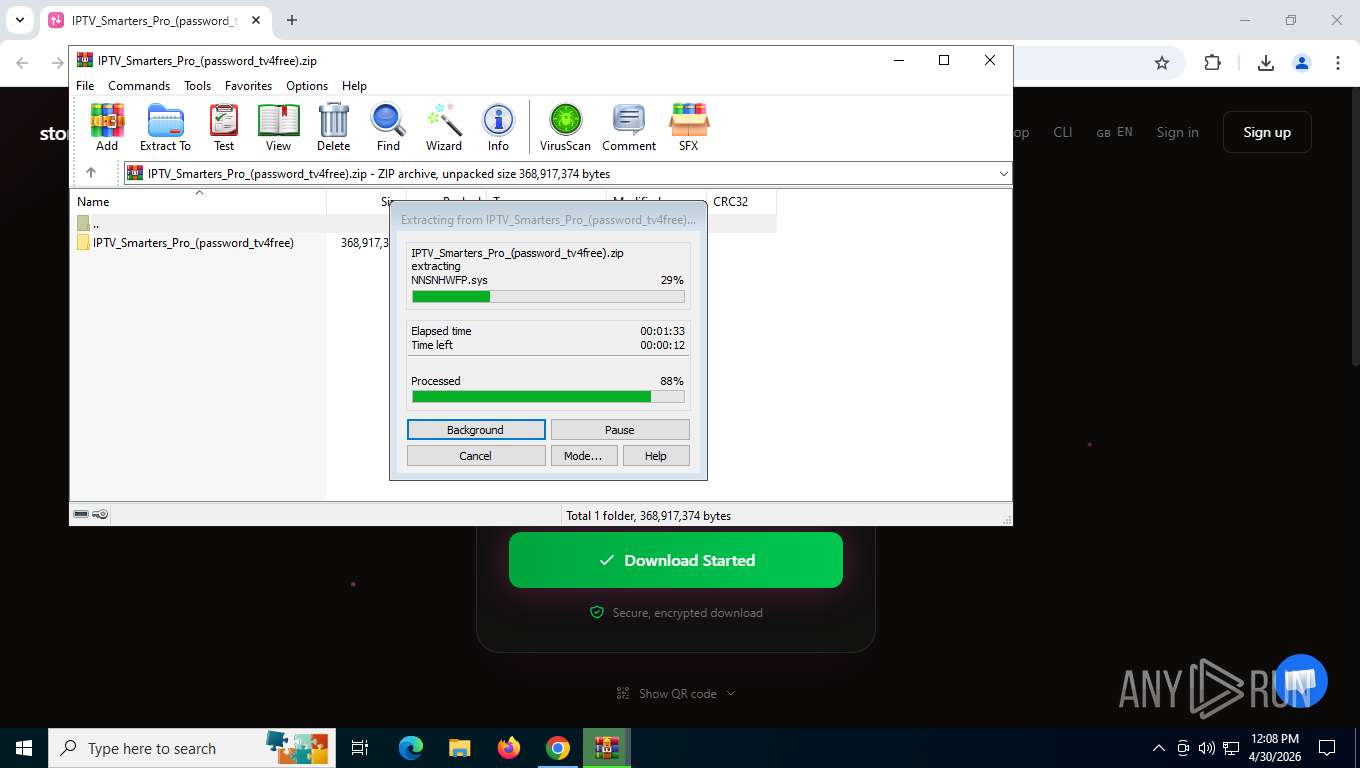
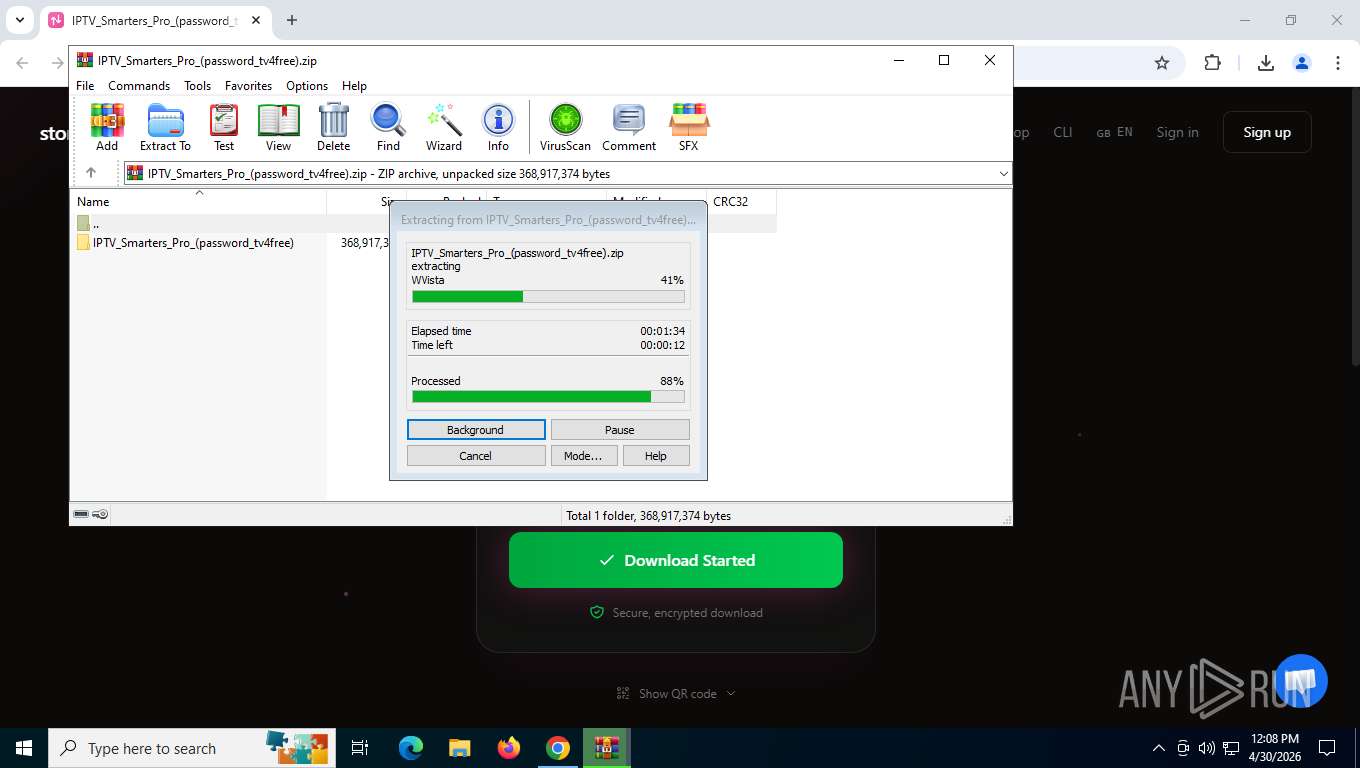
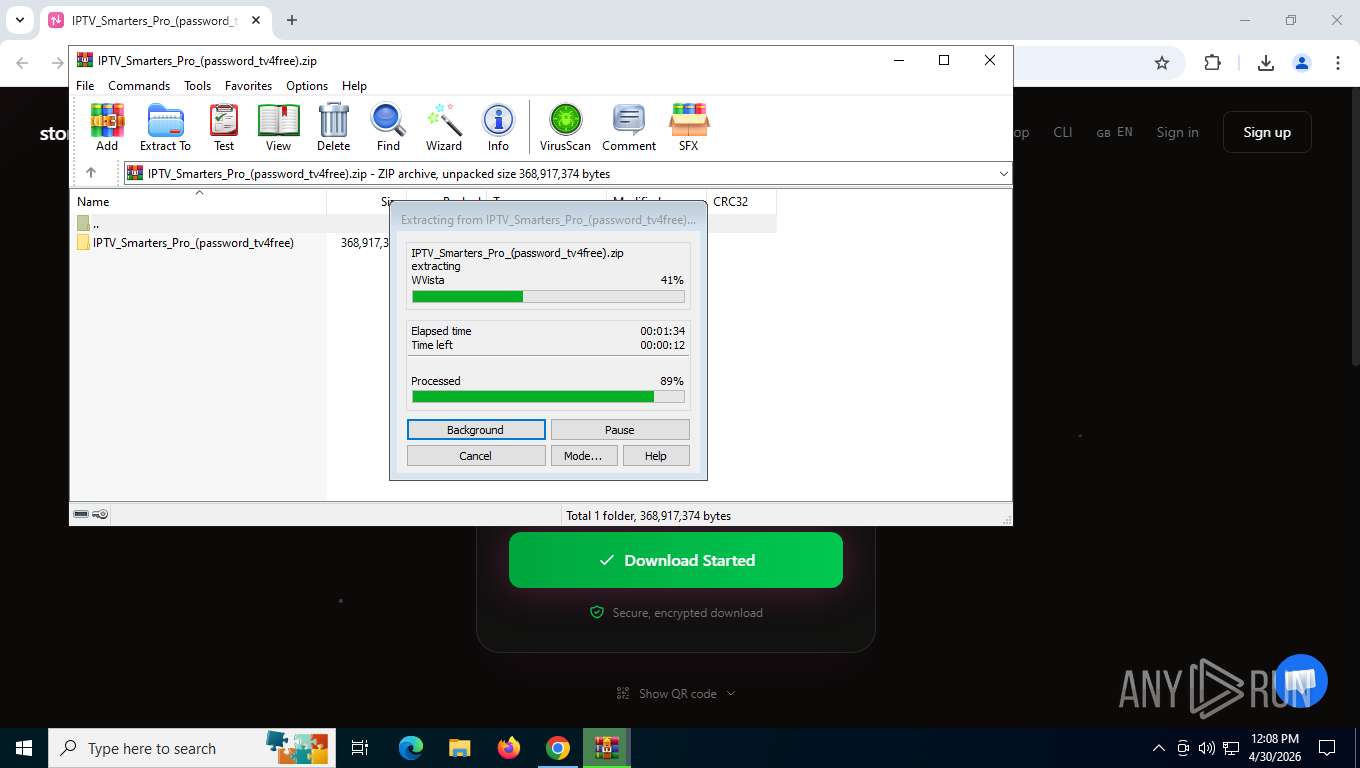
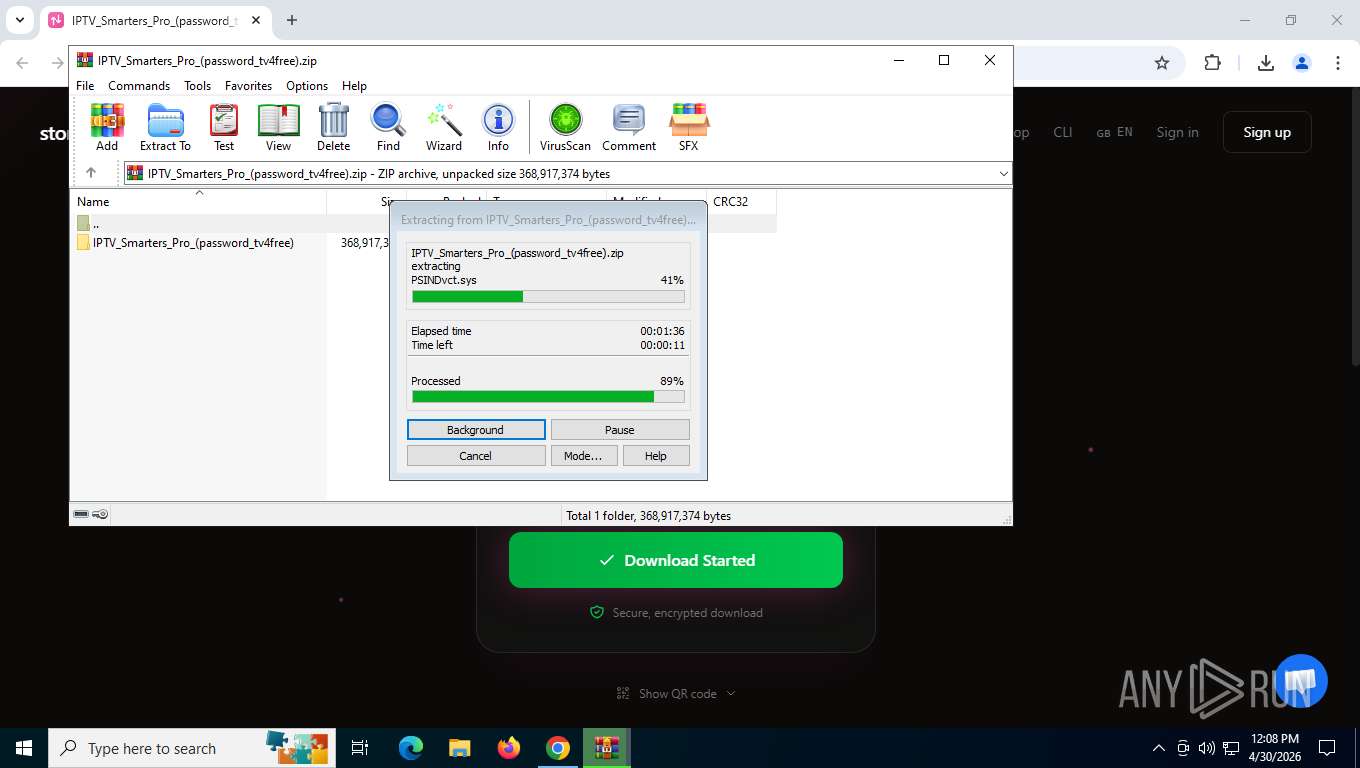
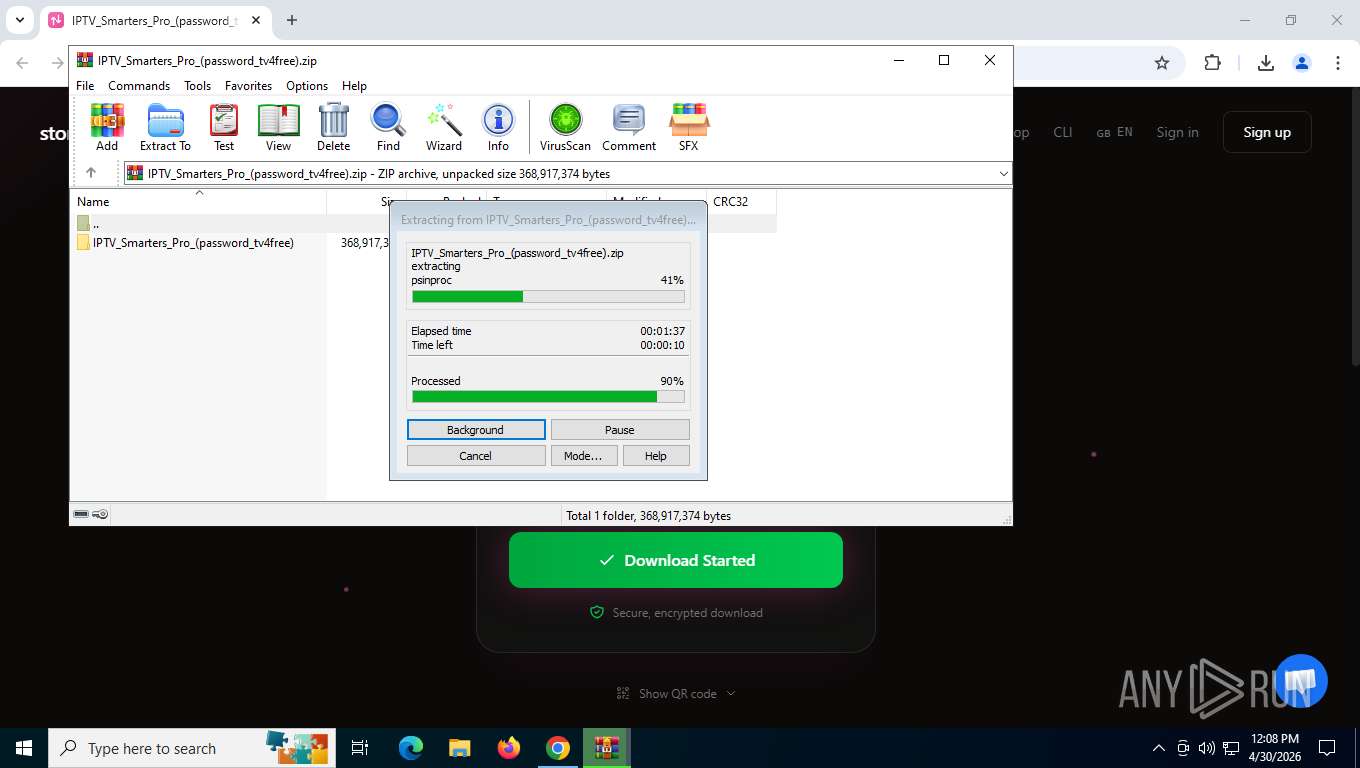
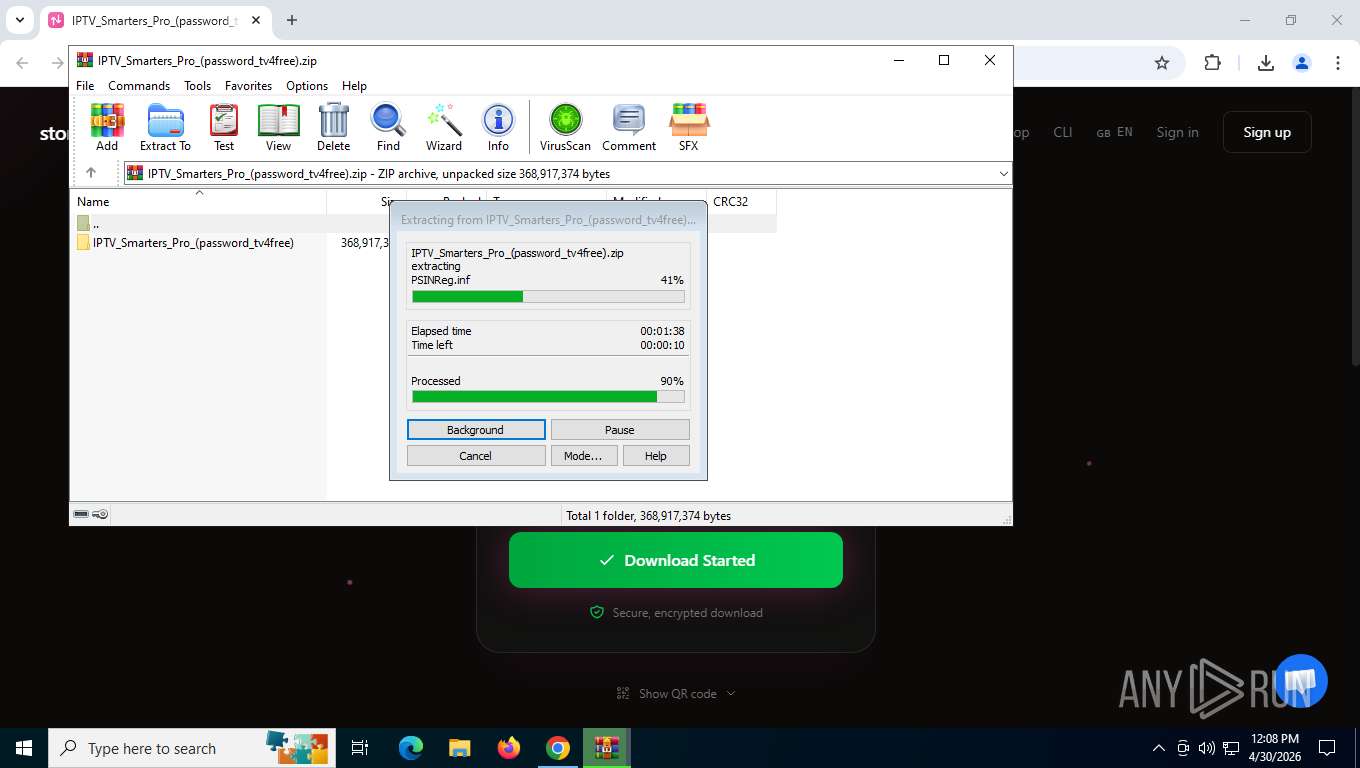
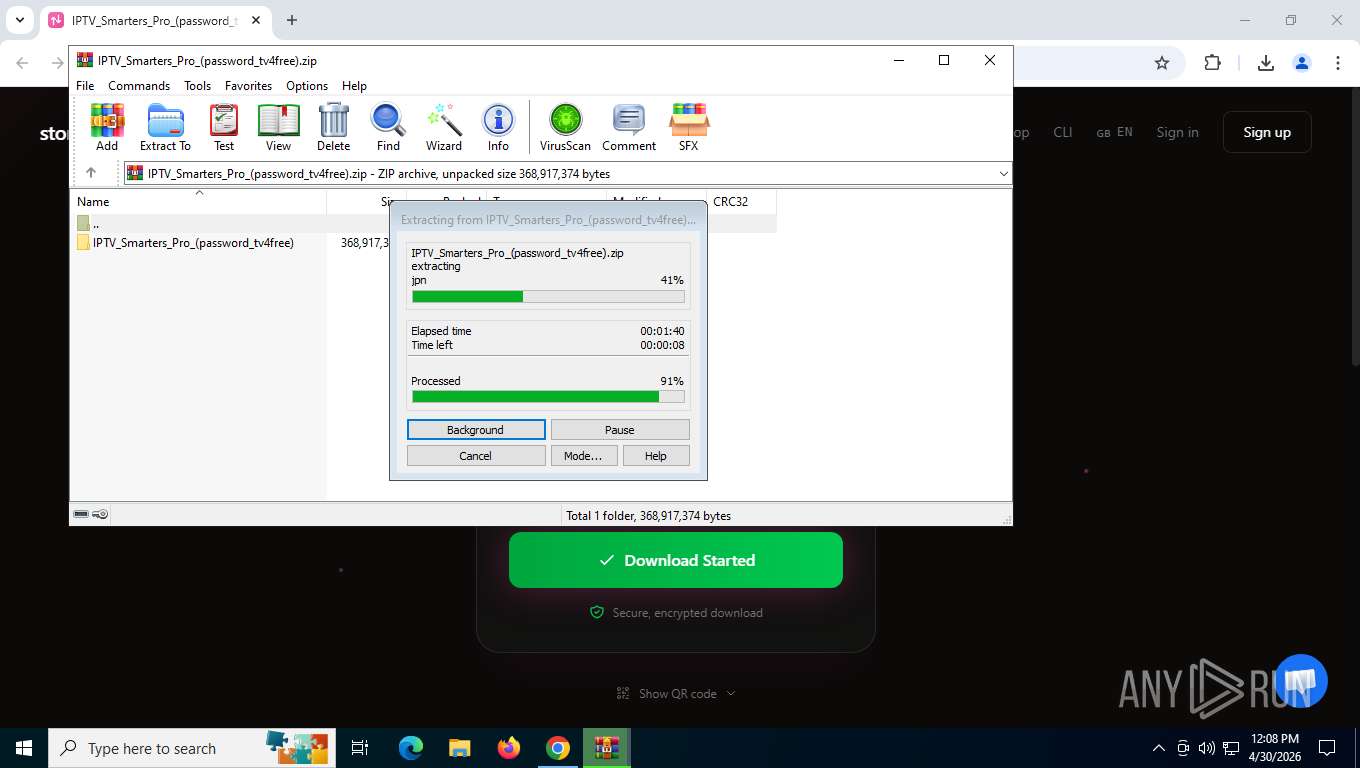
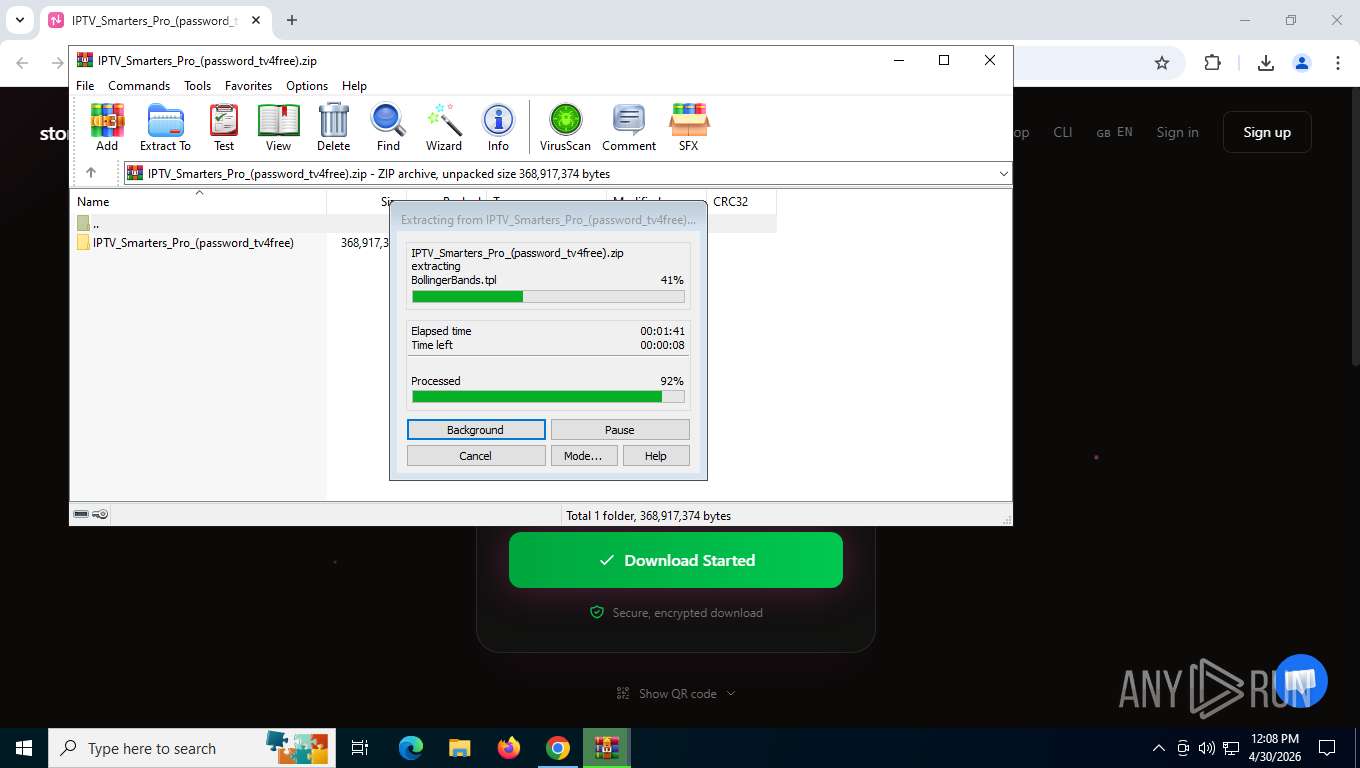
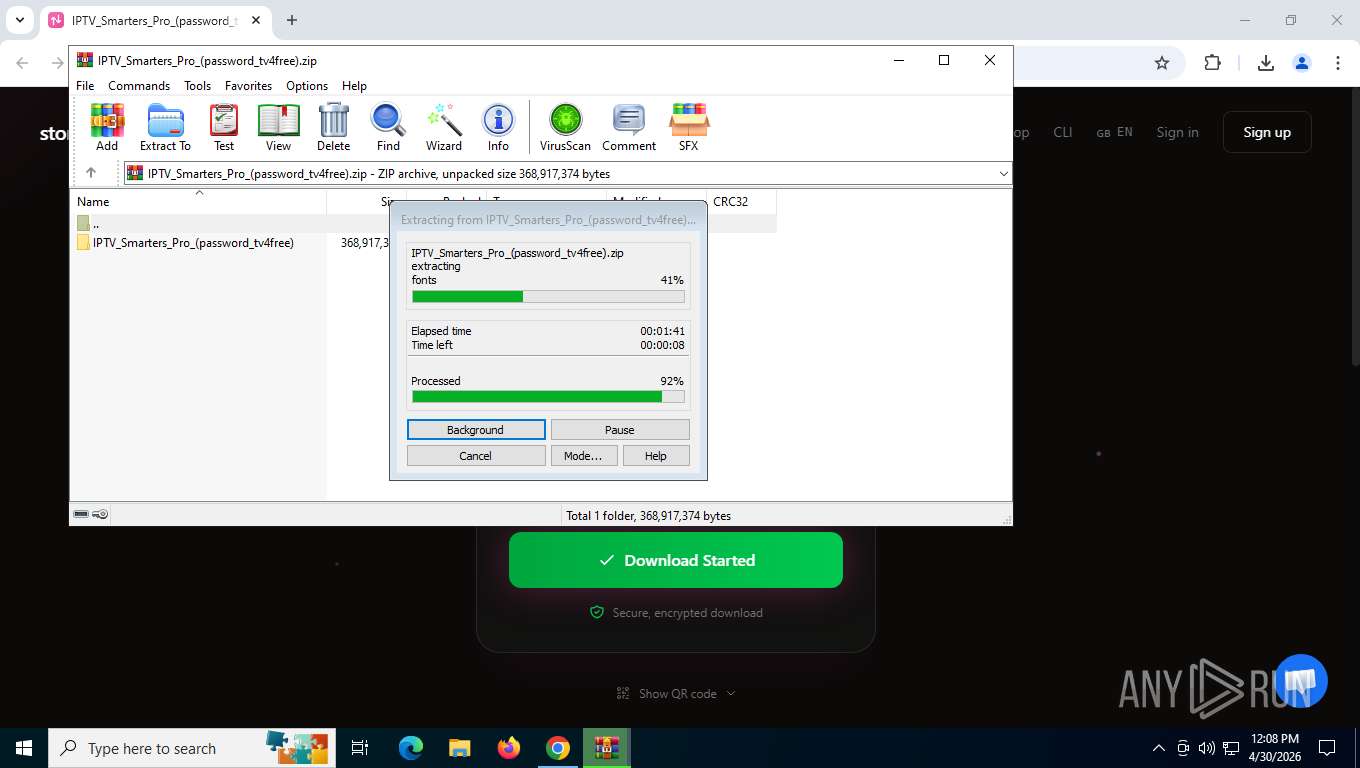
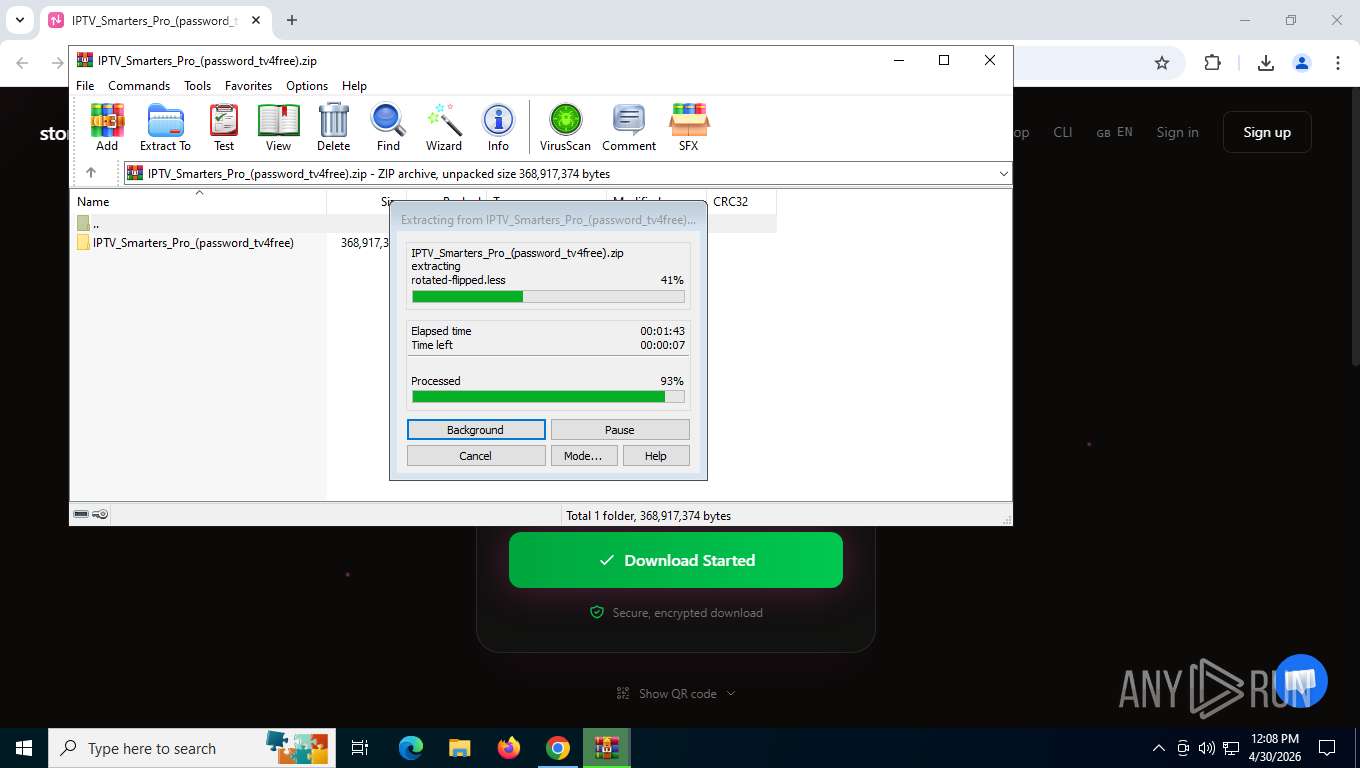
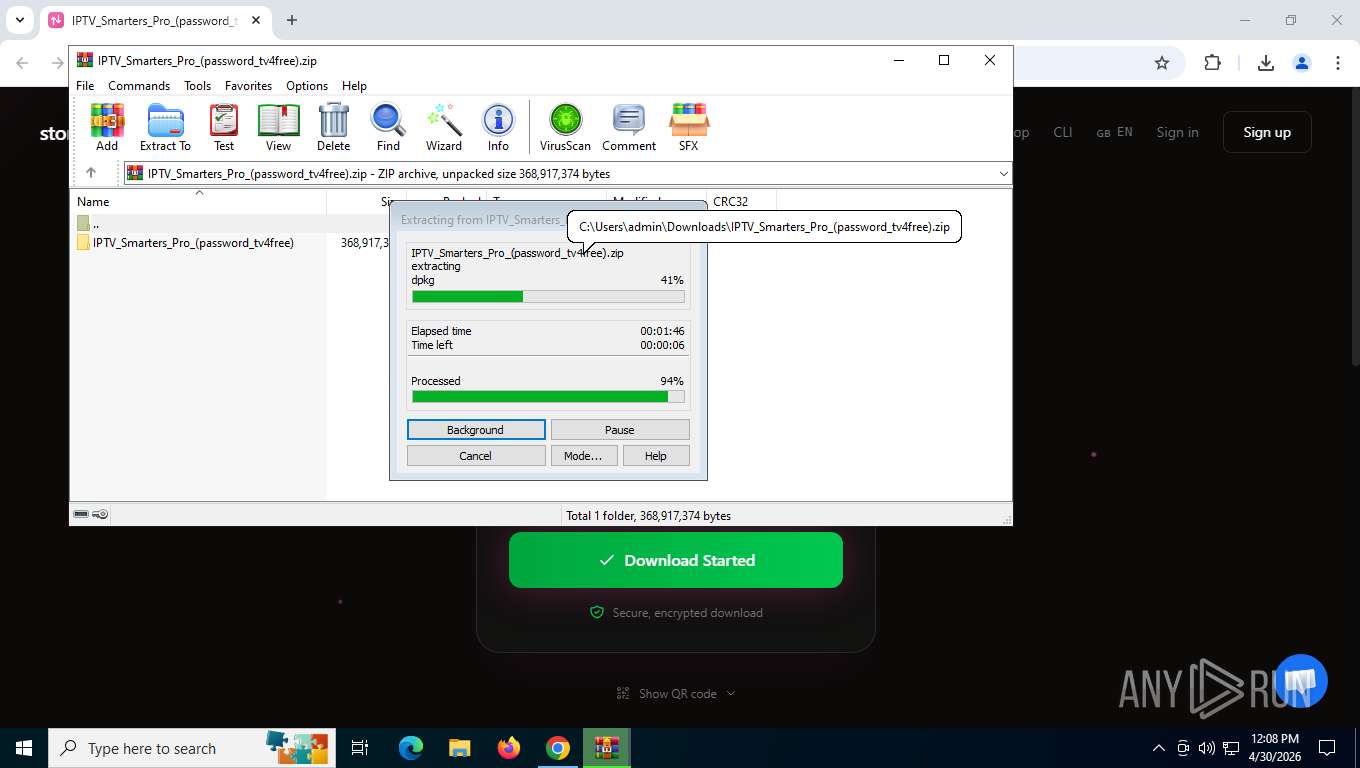
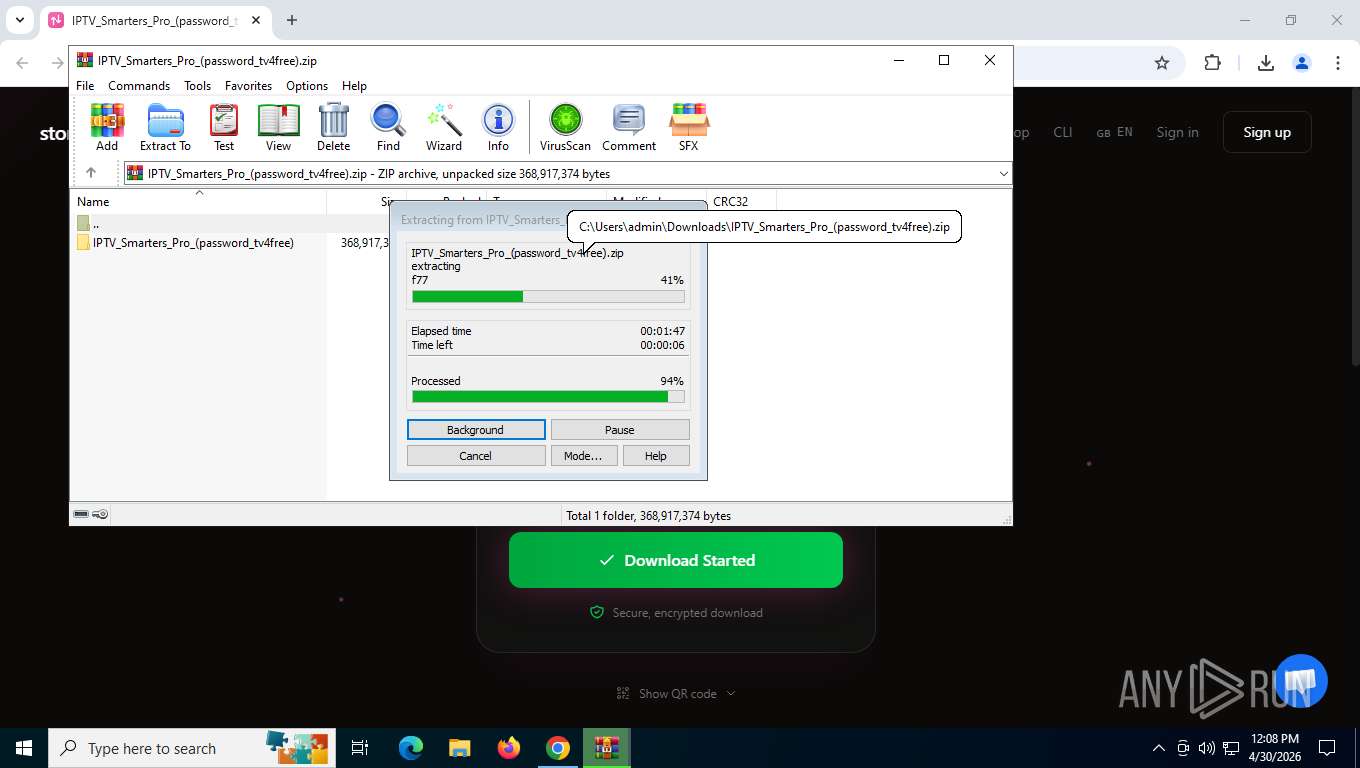
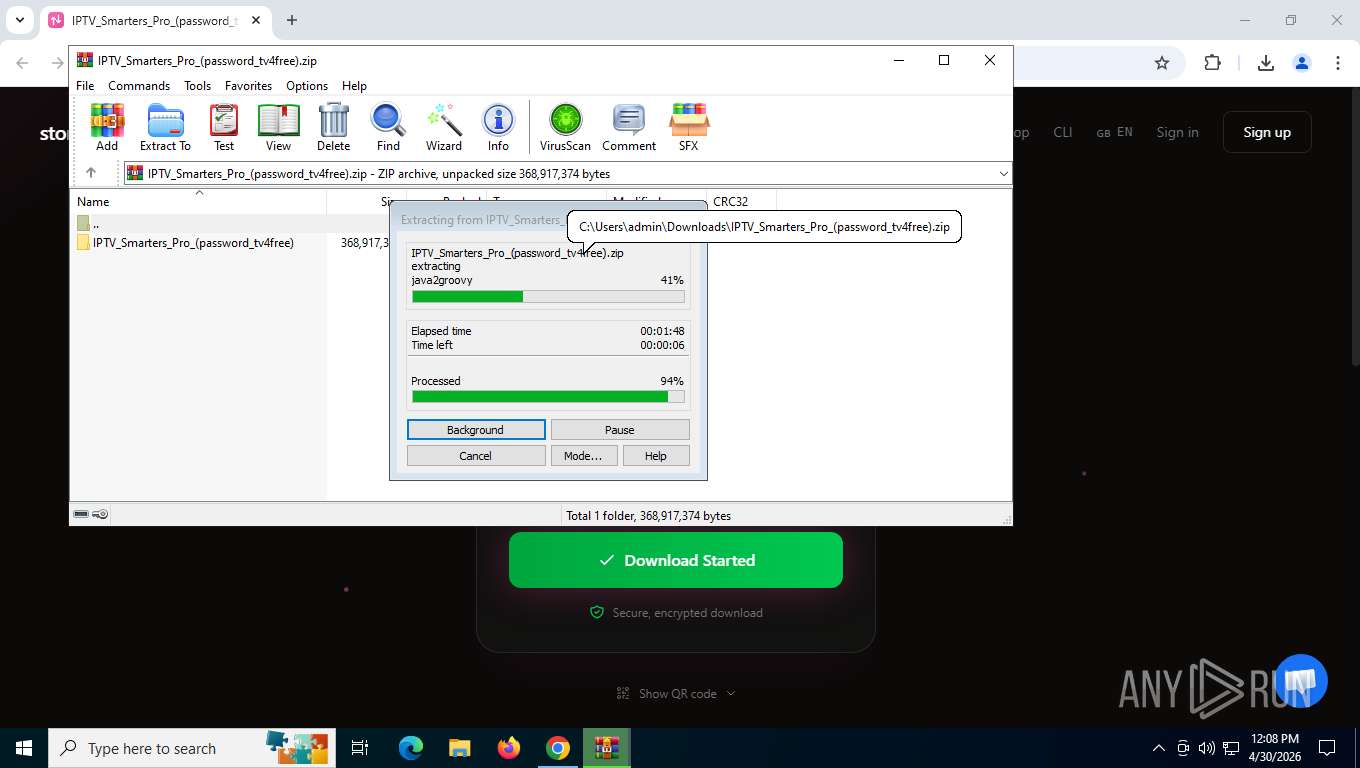
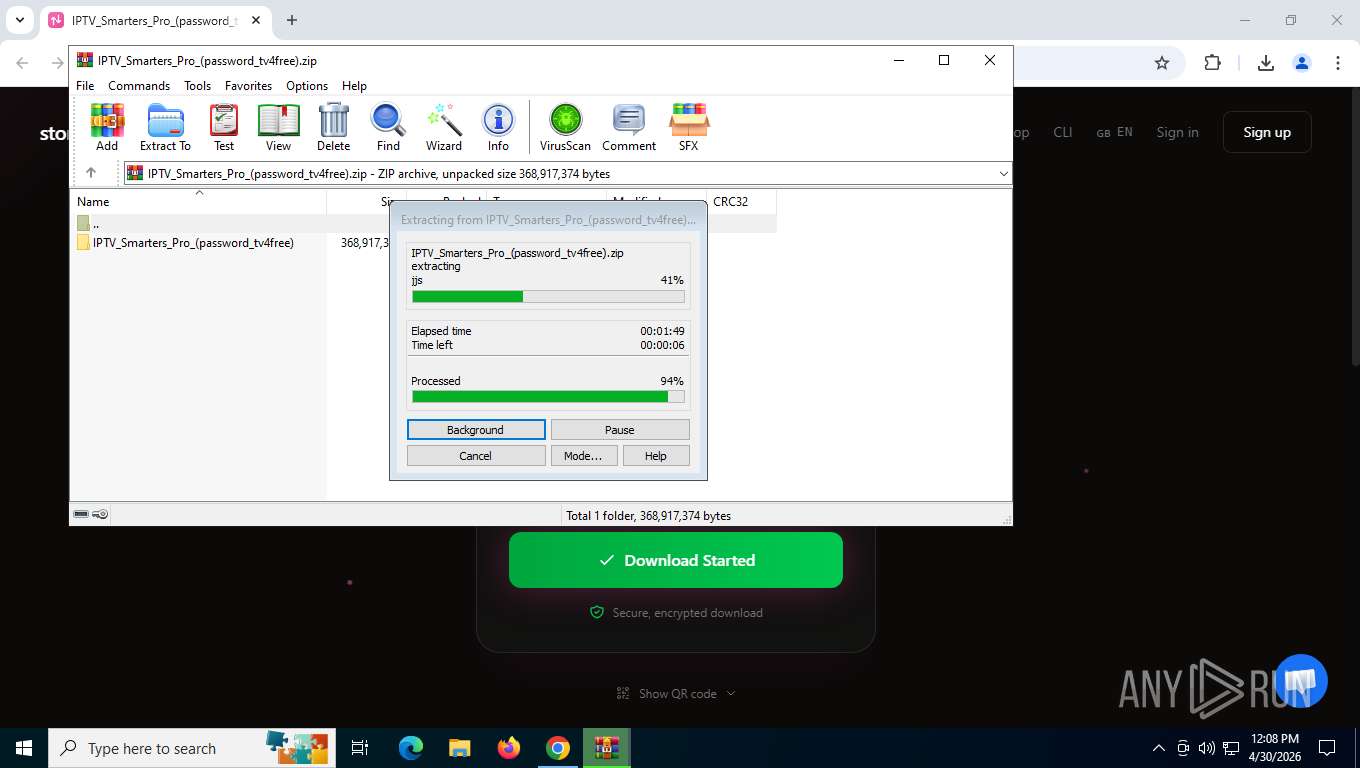
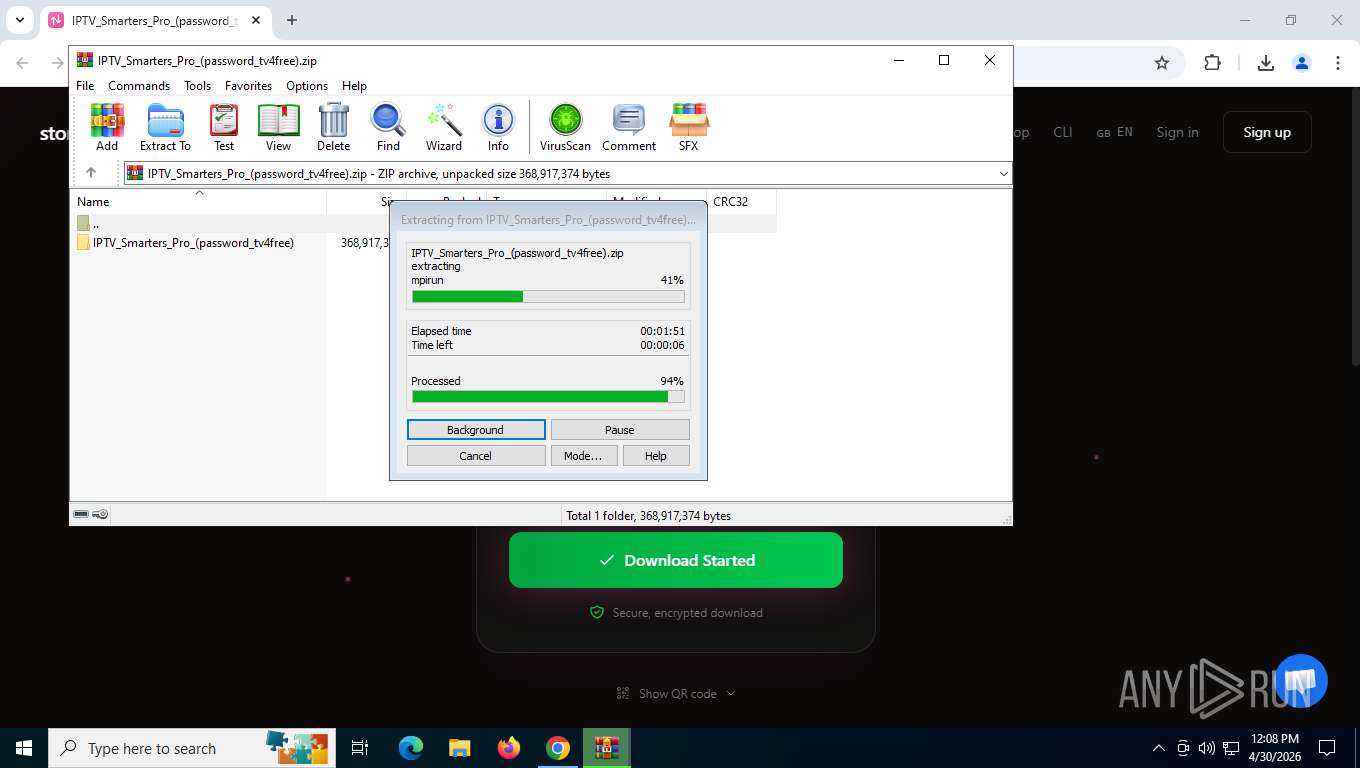
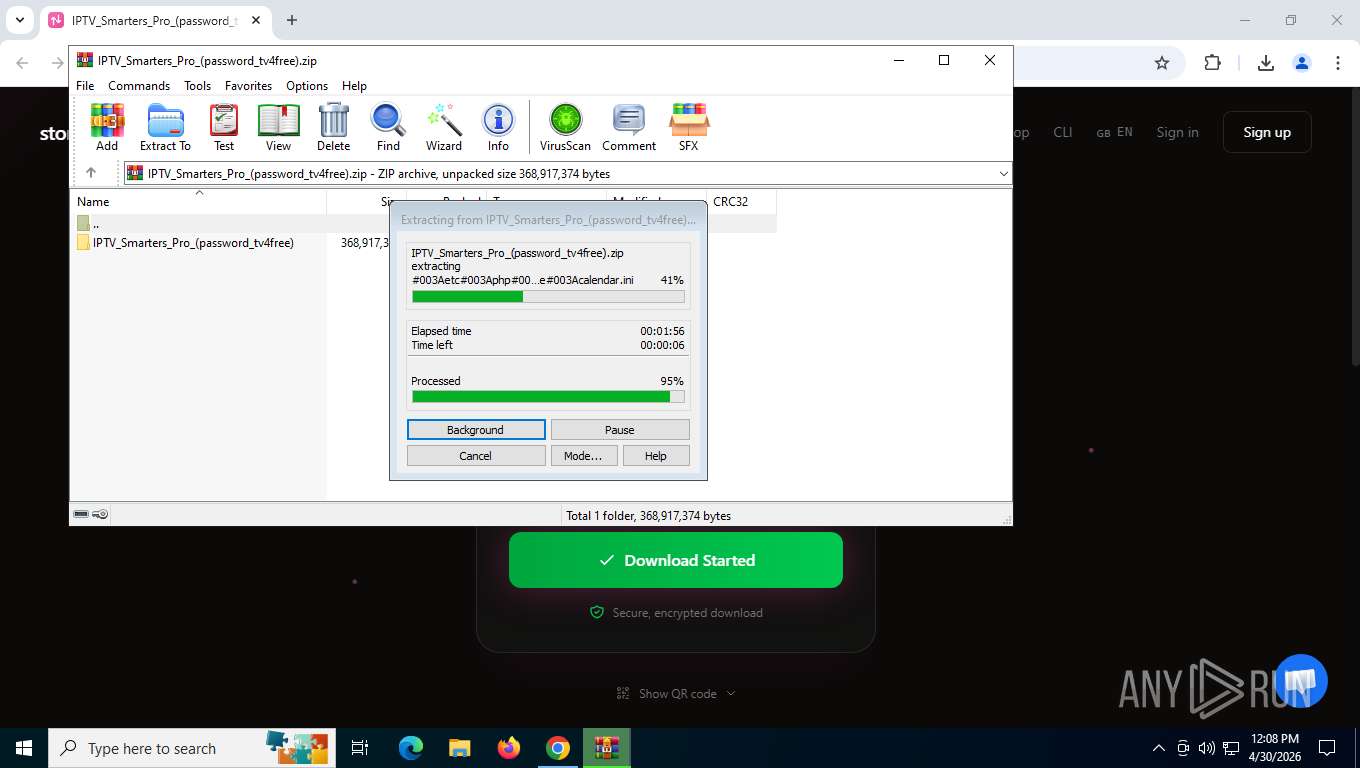
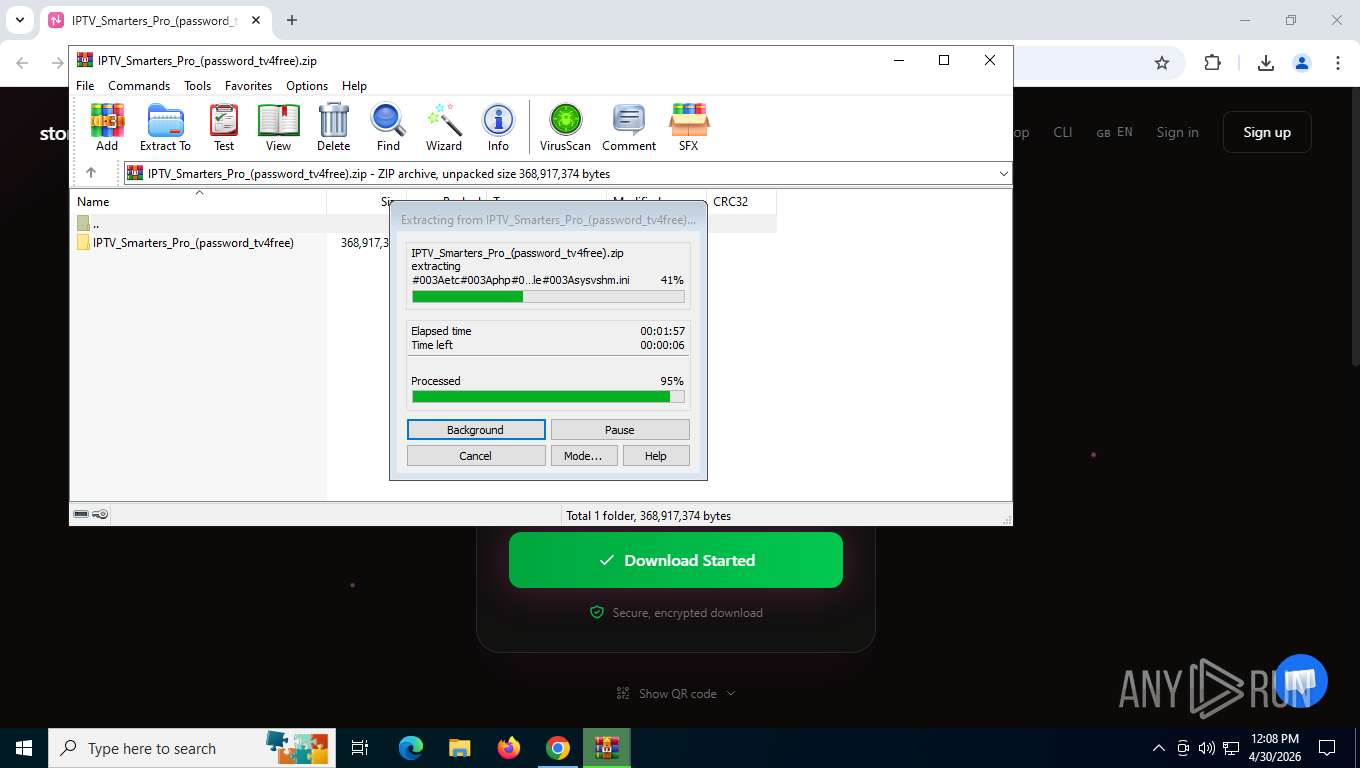
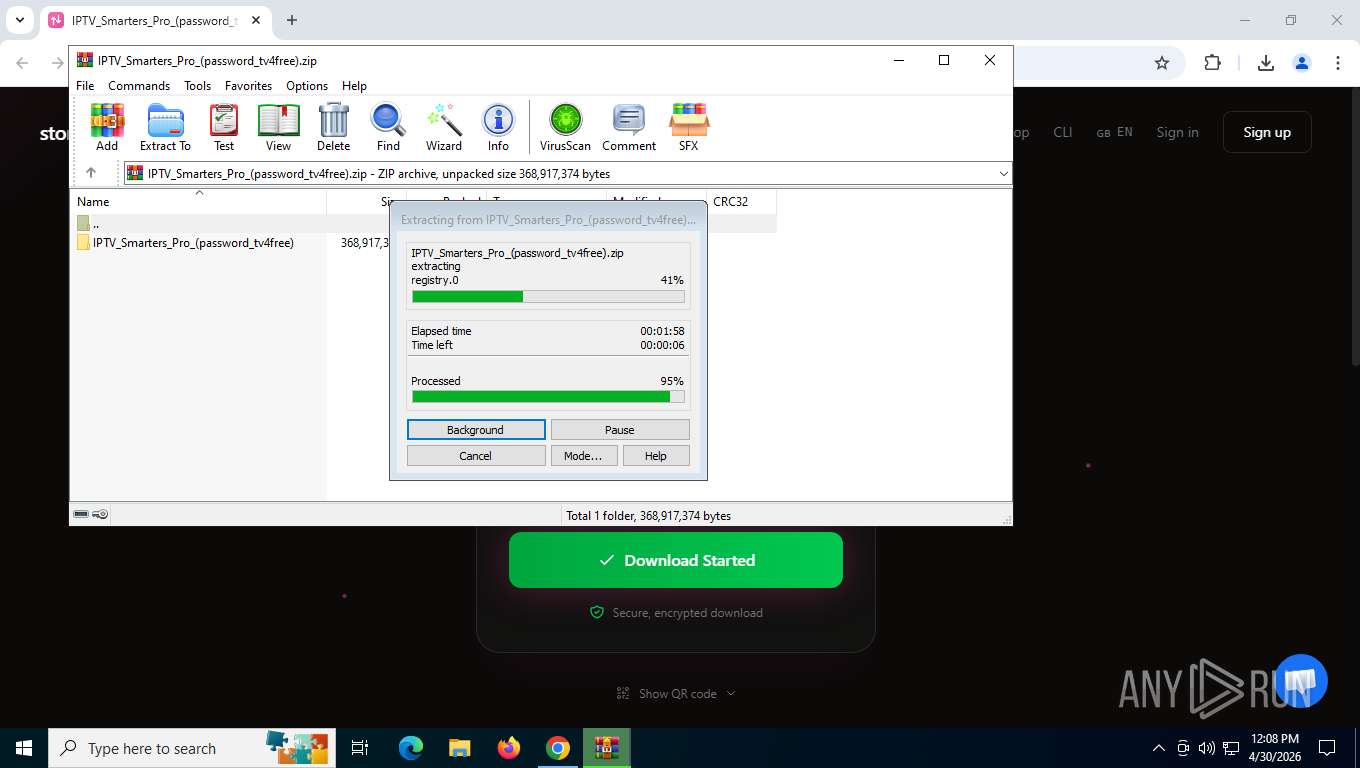
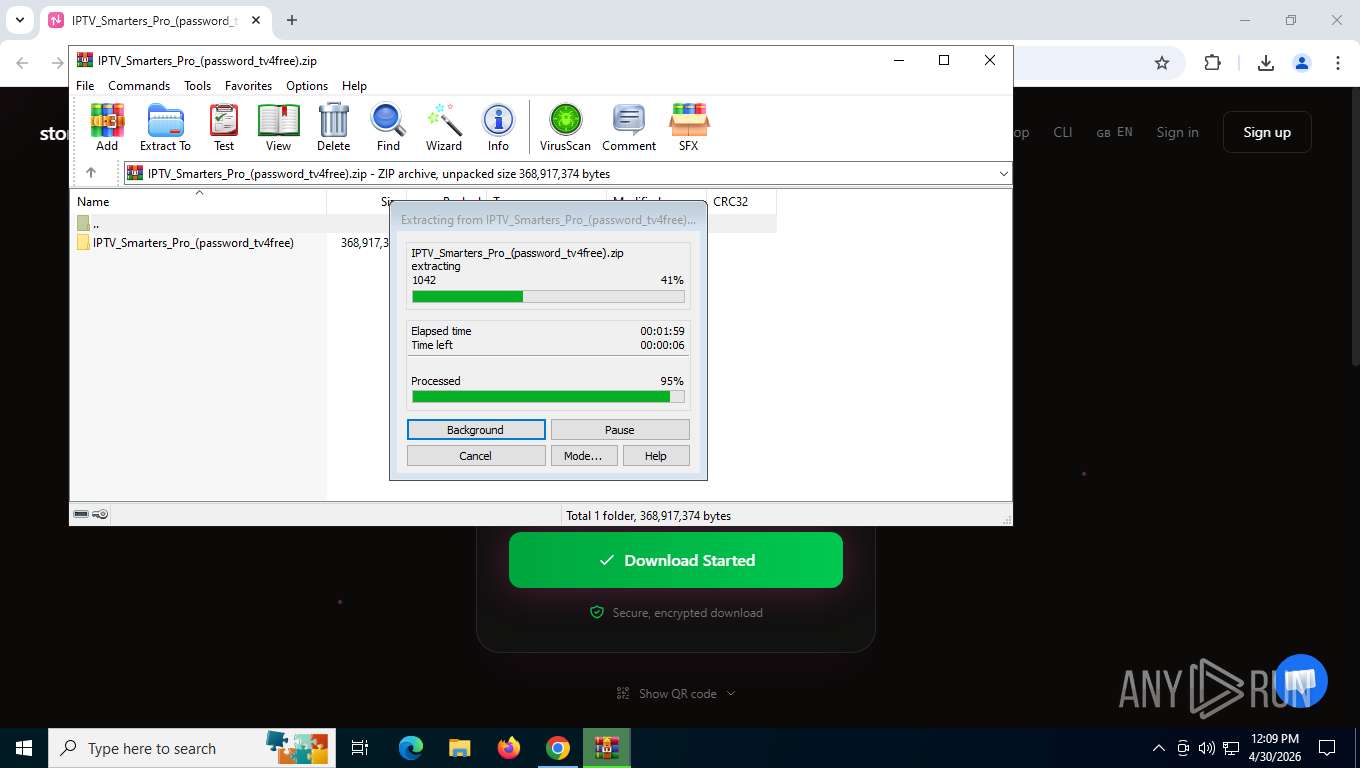
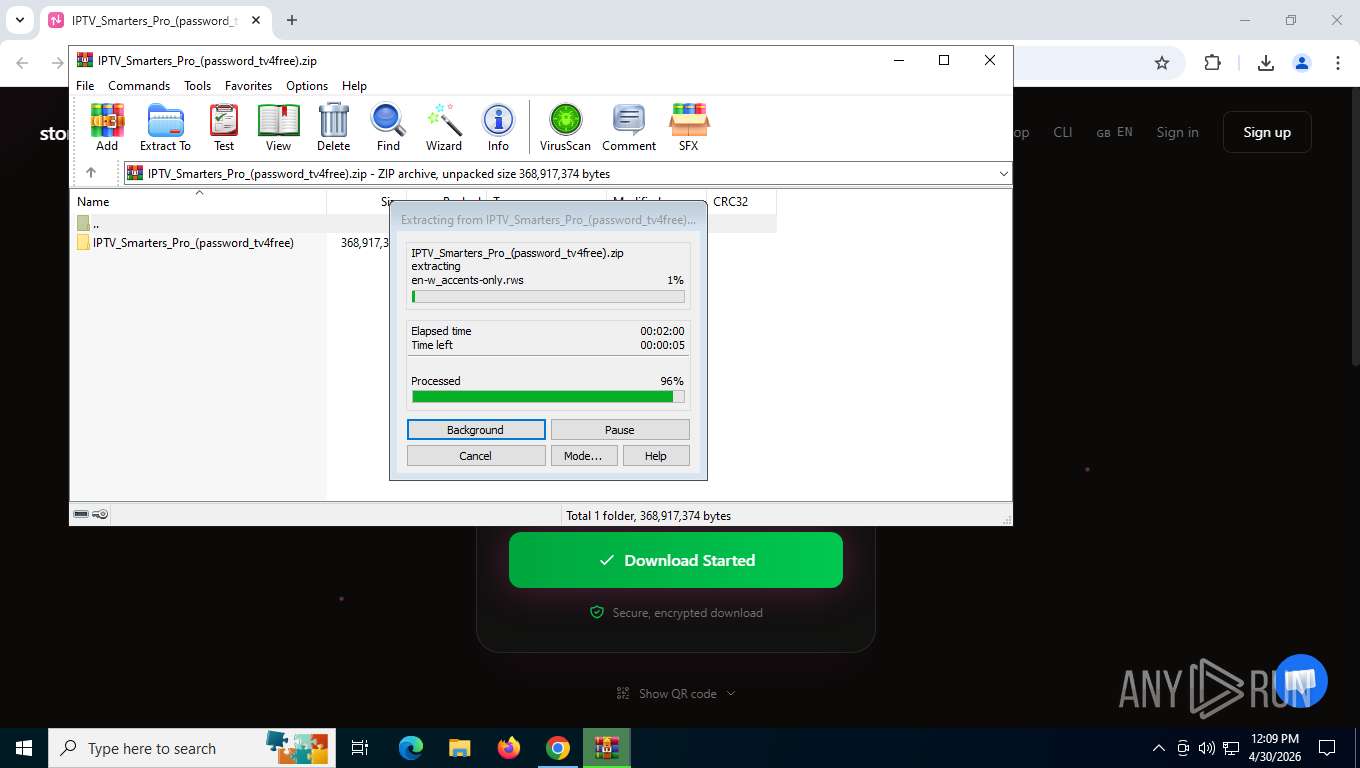
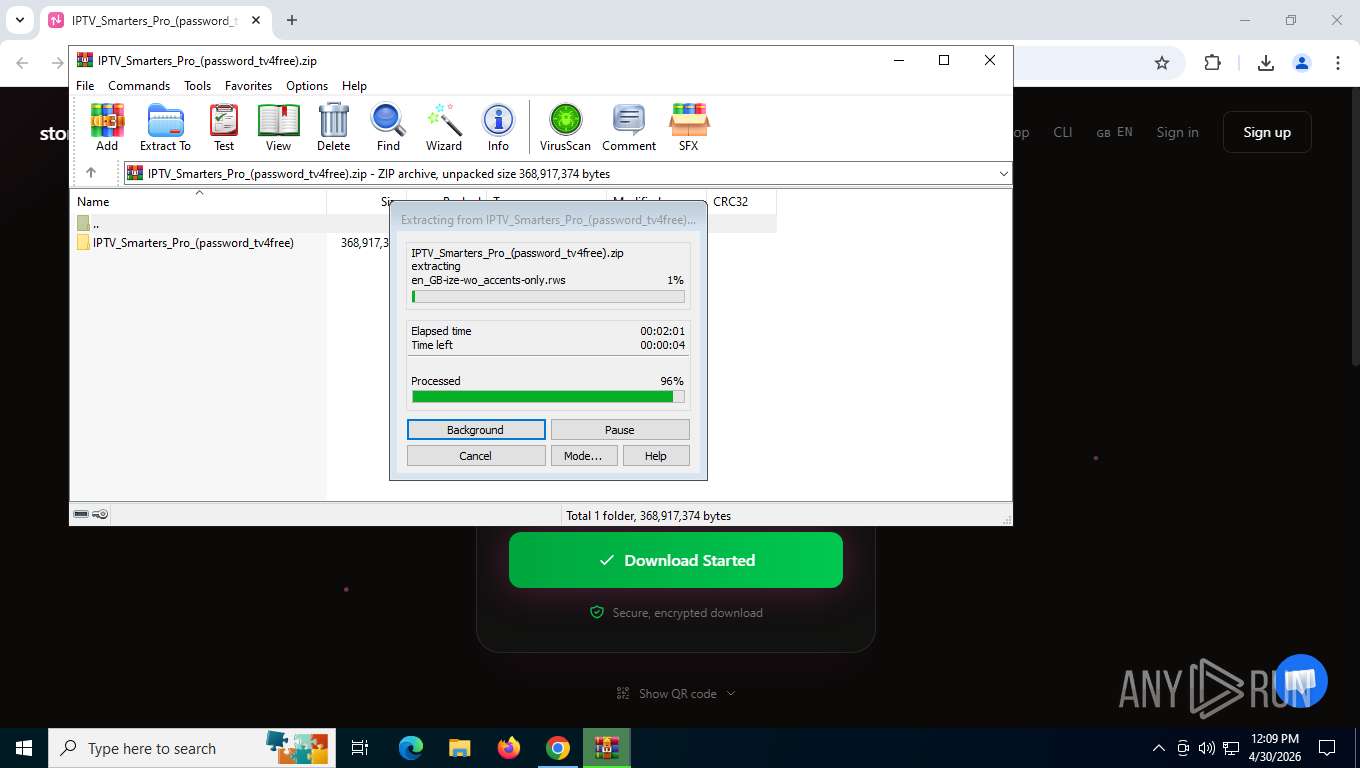
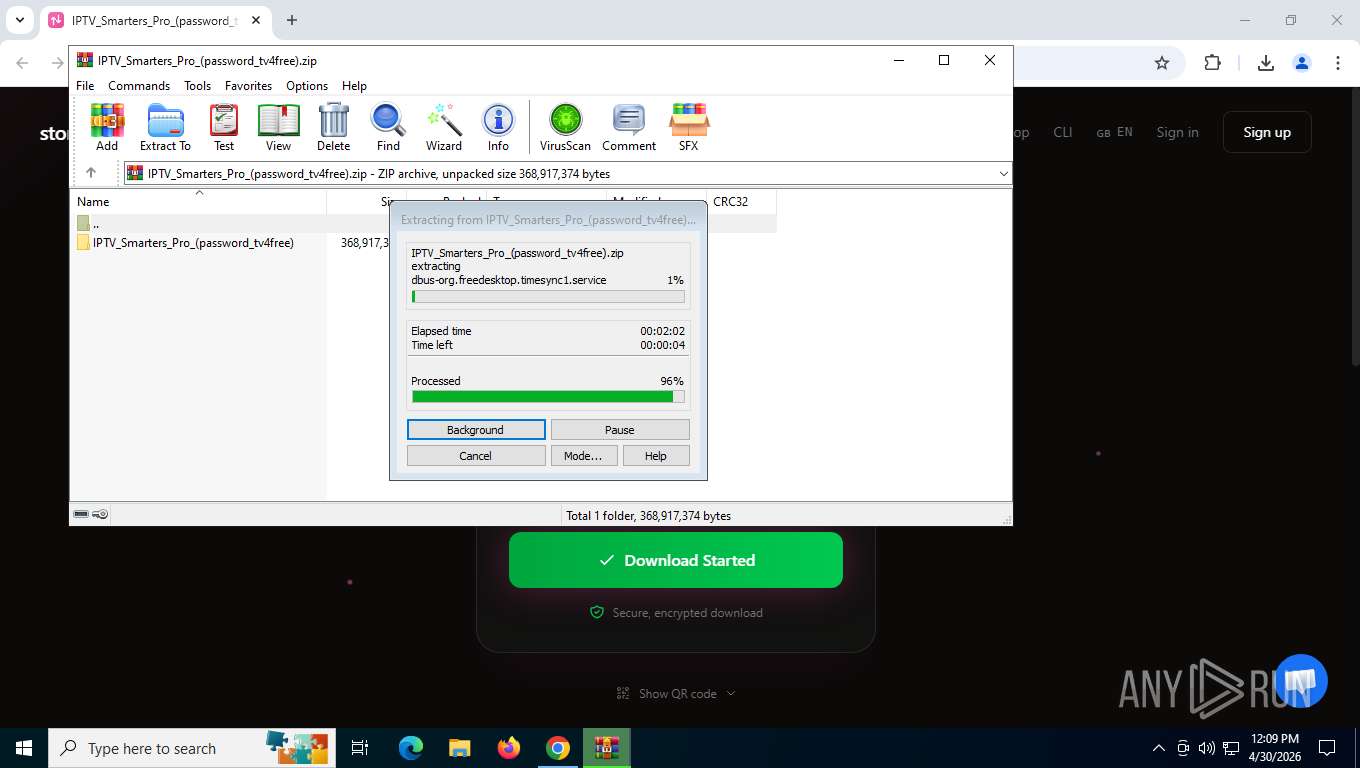
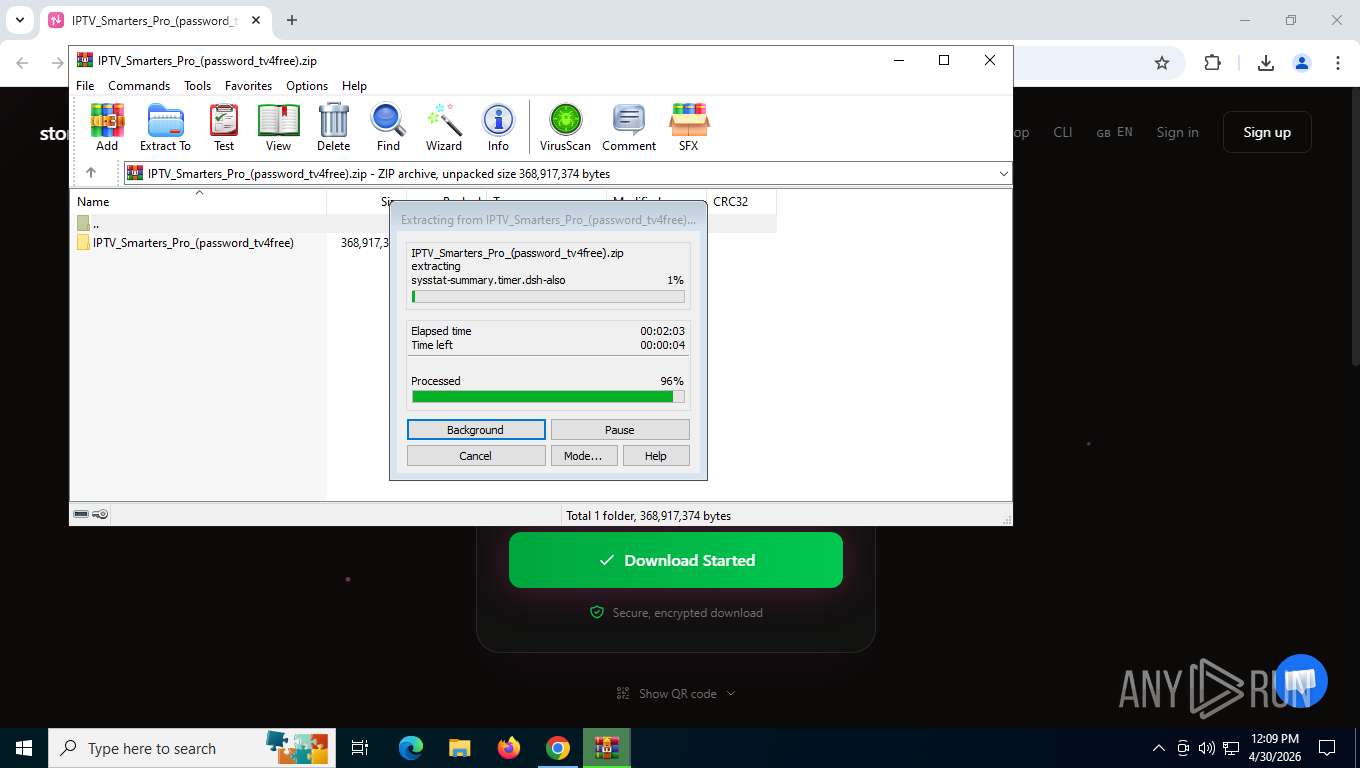
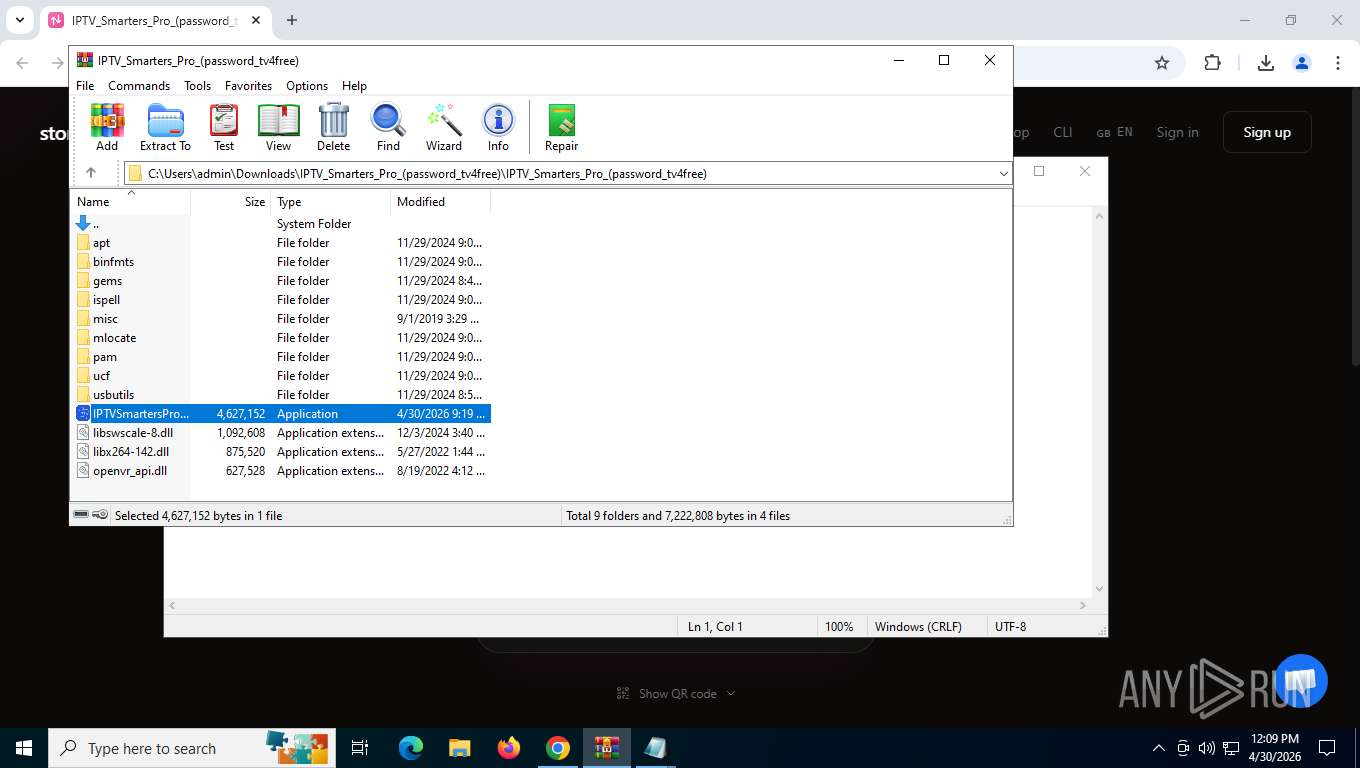
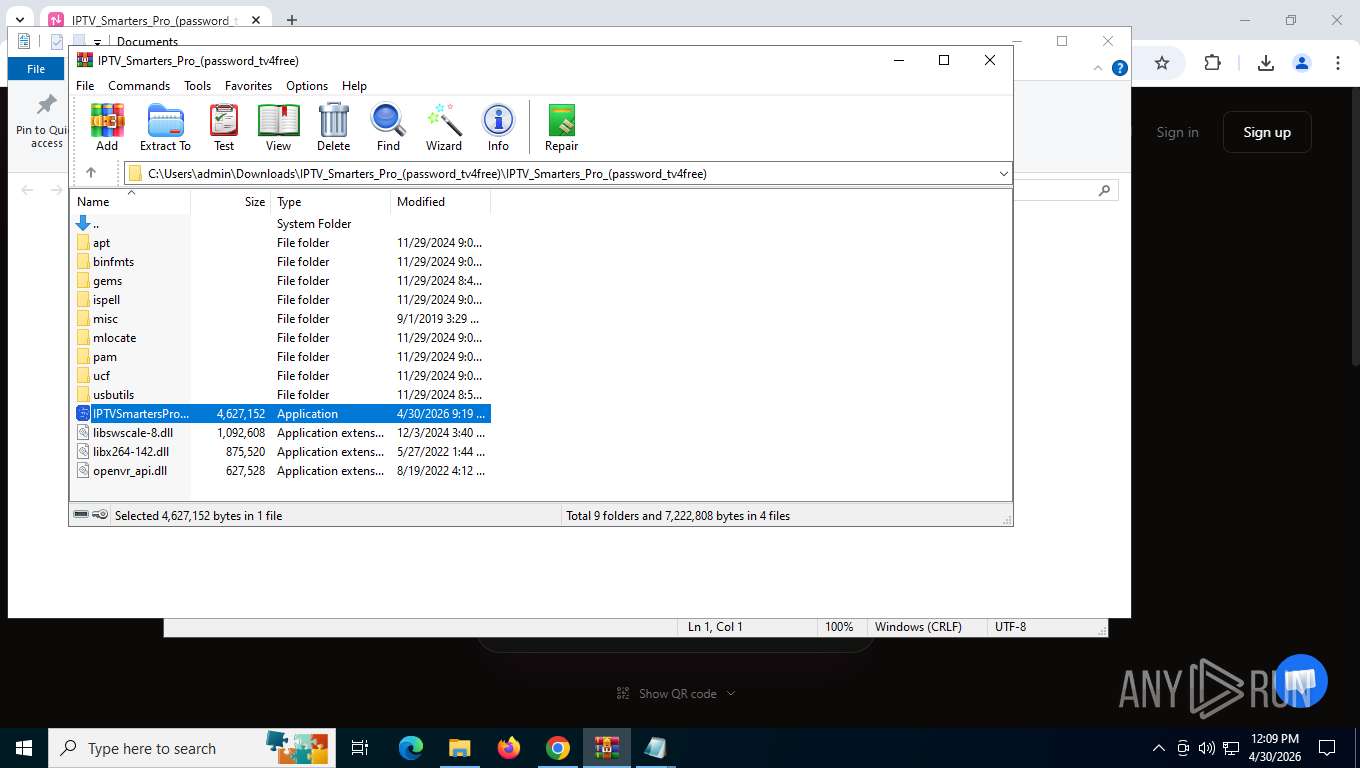
The process creates files with name similar to system file names
- WinRAR.exe (PID: 8184)
- wermgr.exe (PID: 8492)
- wermgr.exe (PID: 3320)
- wermgr.exe (PID: 8292)
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8184)
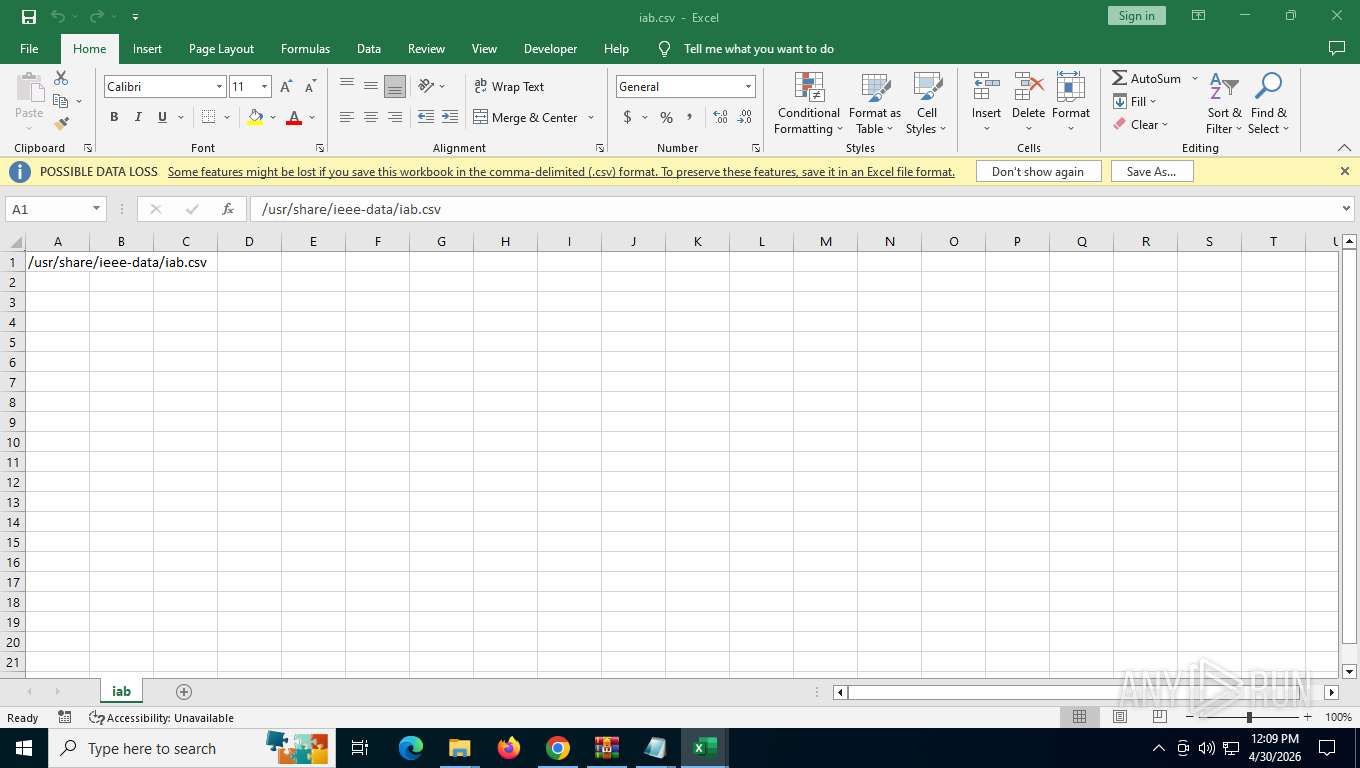
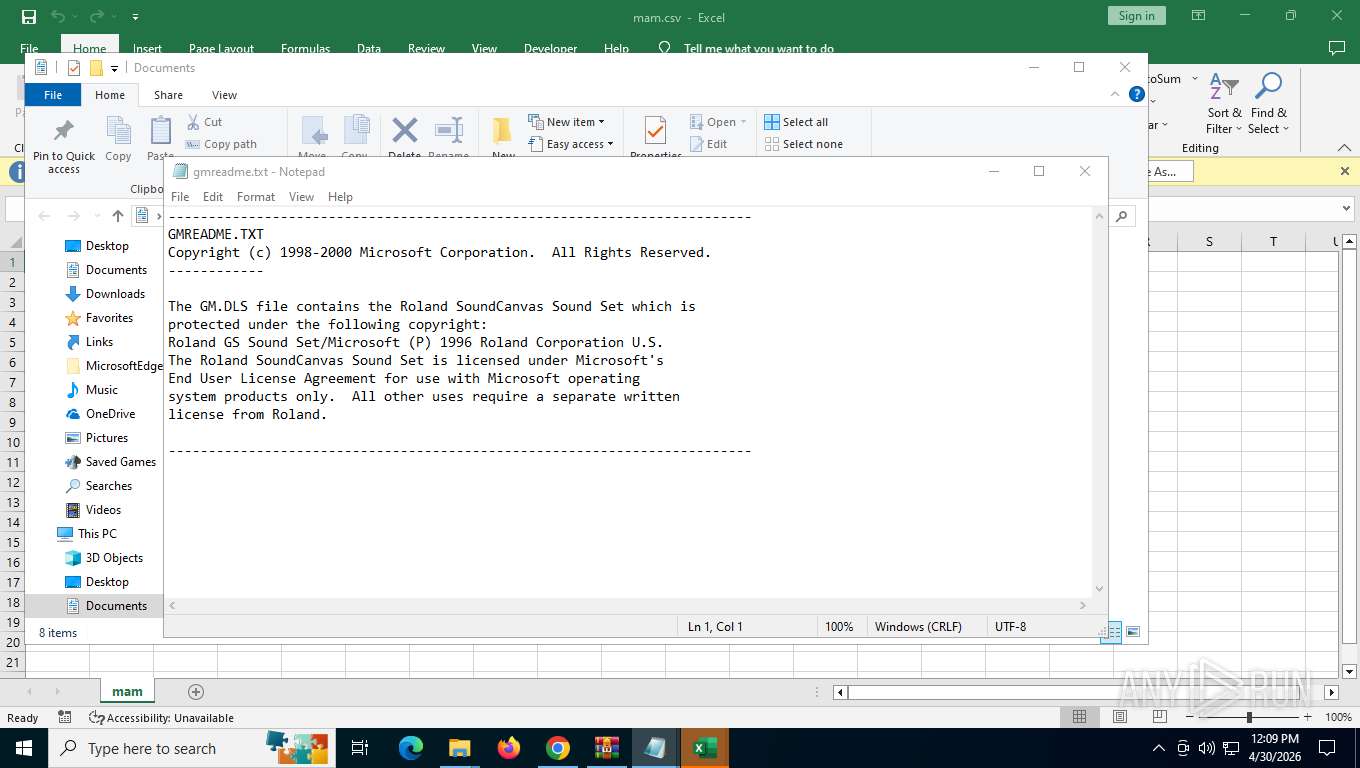
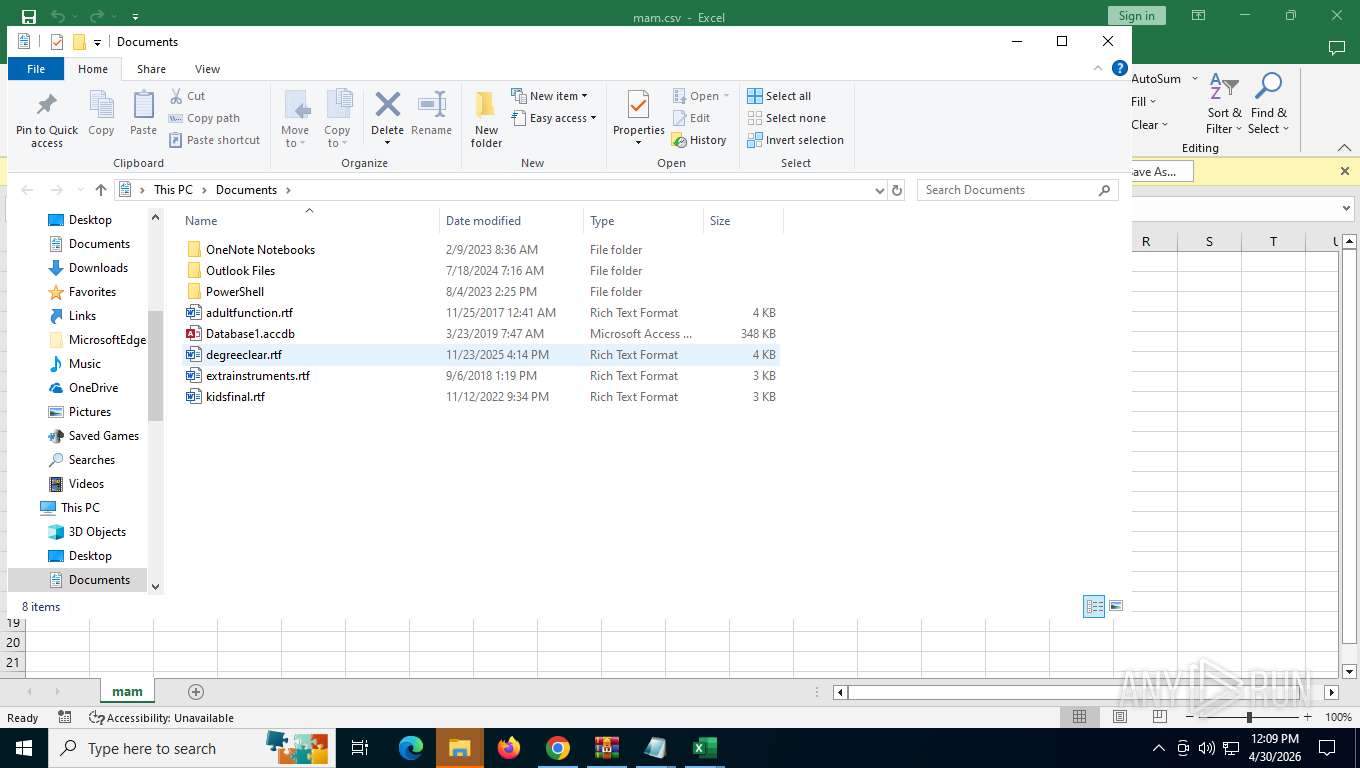
Opens a file (MACROS)
- EXCEL.EXE (PID: 7352)
Reads data from a file (MACROS)
- EXCEL.EXE (PID: 7352)
Reads Microsoft Outlook installation path
- IEChooser.exe (PID: 8272)
INFO
Application launched itself
- chrome.exe (PID: 7776)
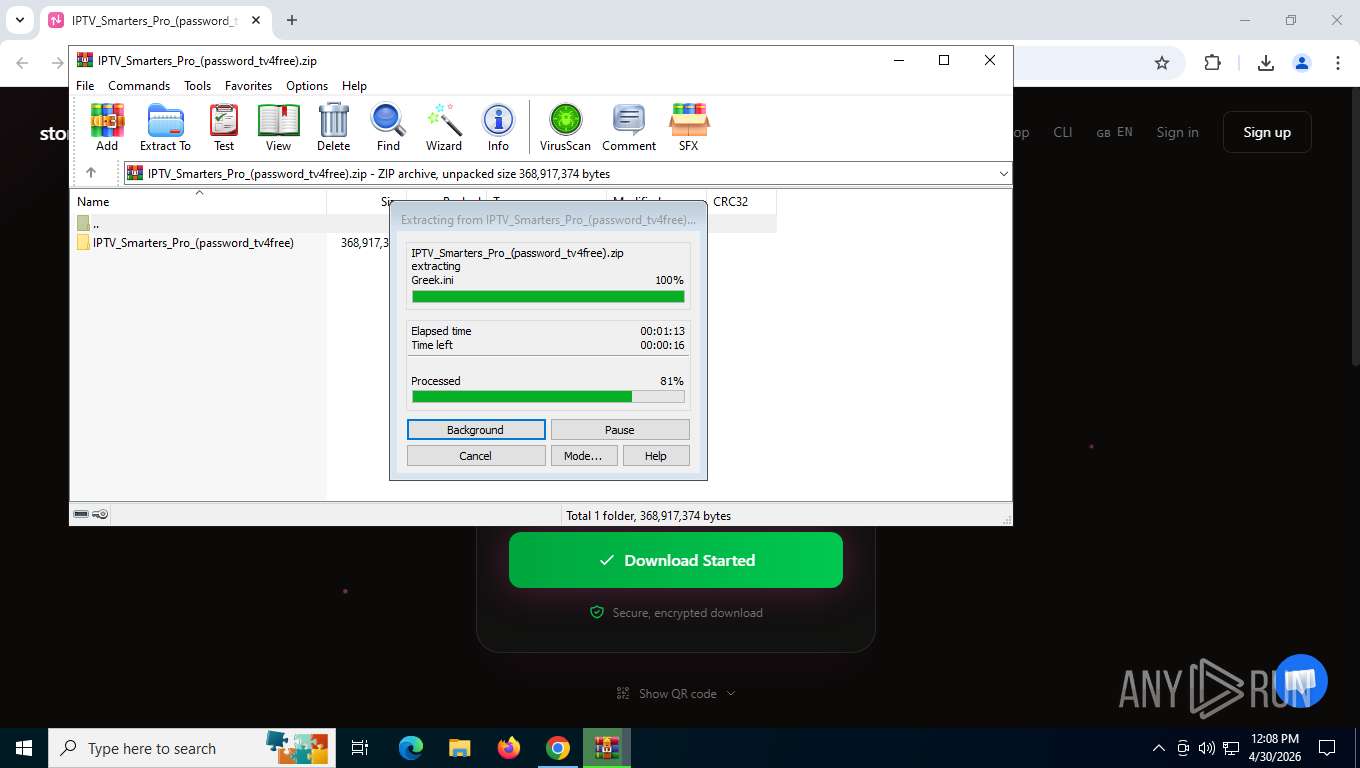
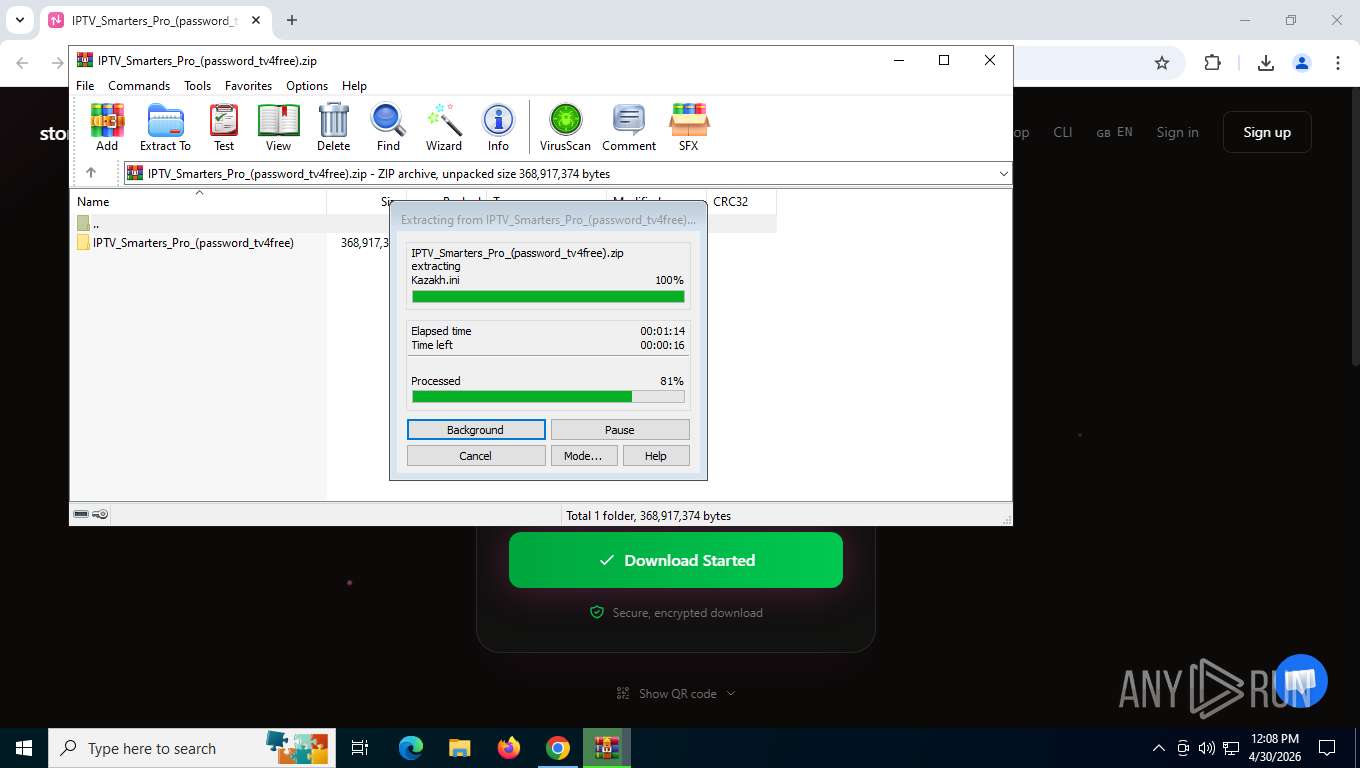
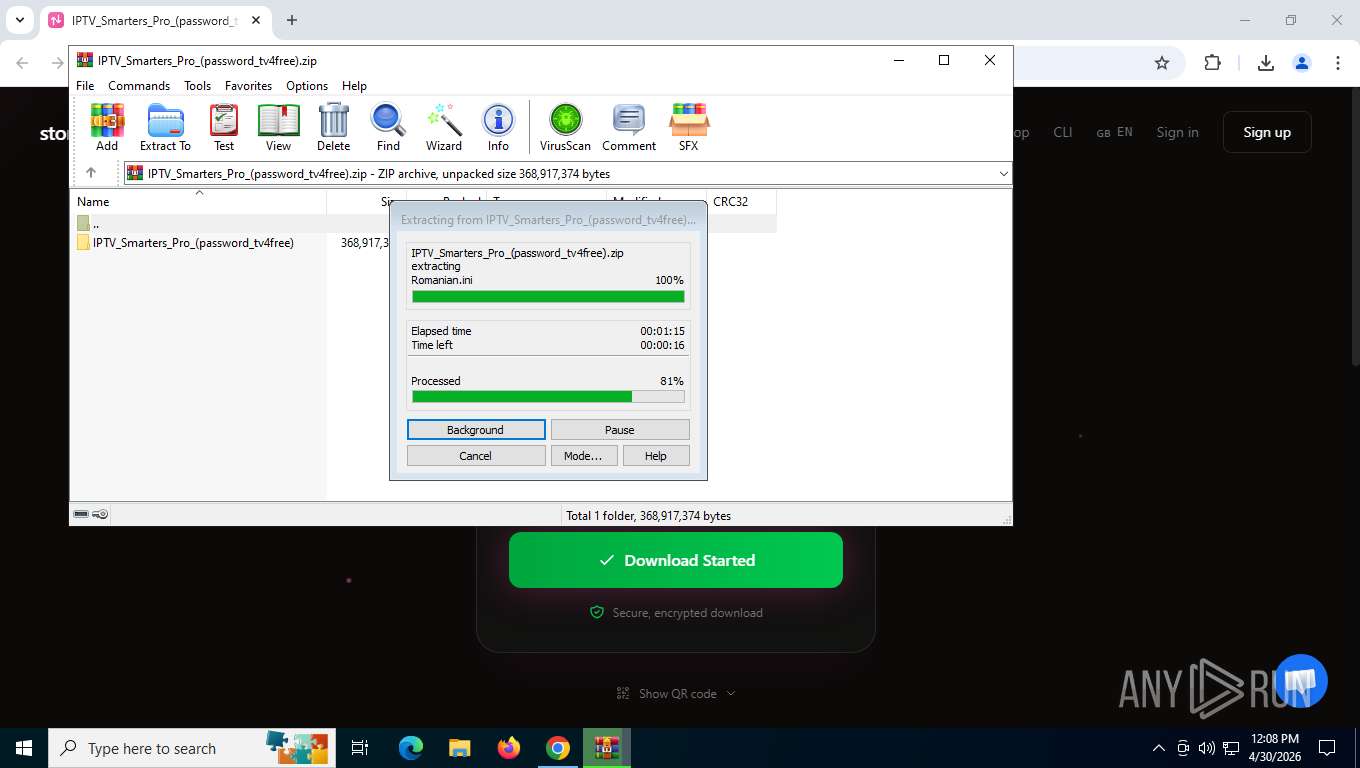
The sample compiled with english language support
- WinRAR.exe (PID: 8184)
Attempting to connect via WebSocket
- chrome.exe (PID: 5920)
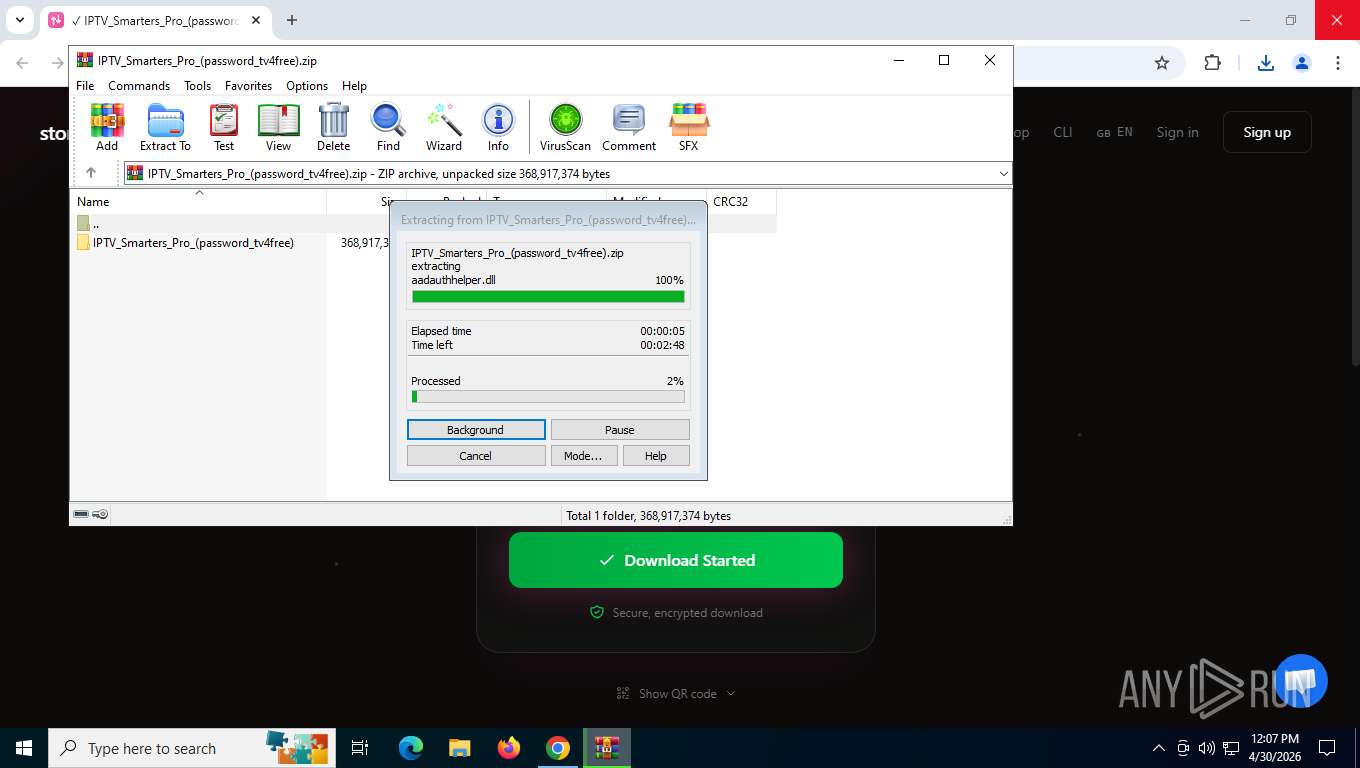
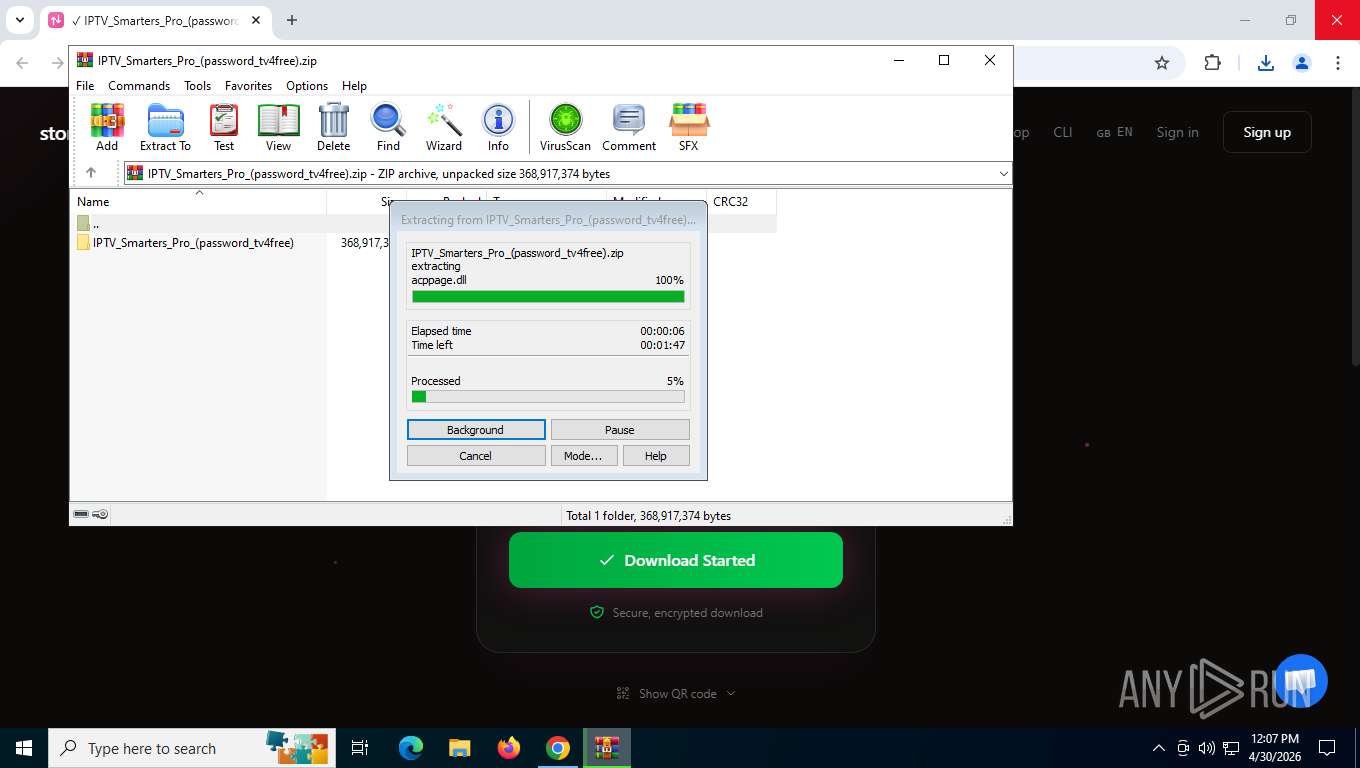
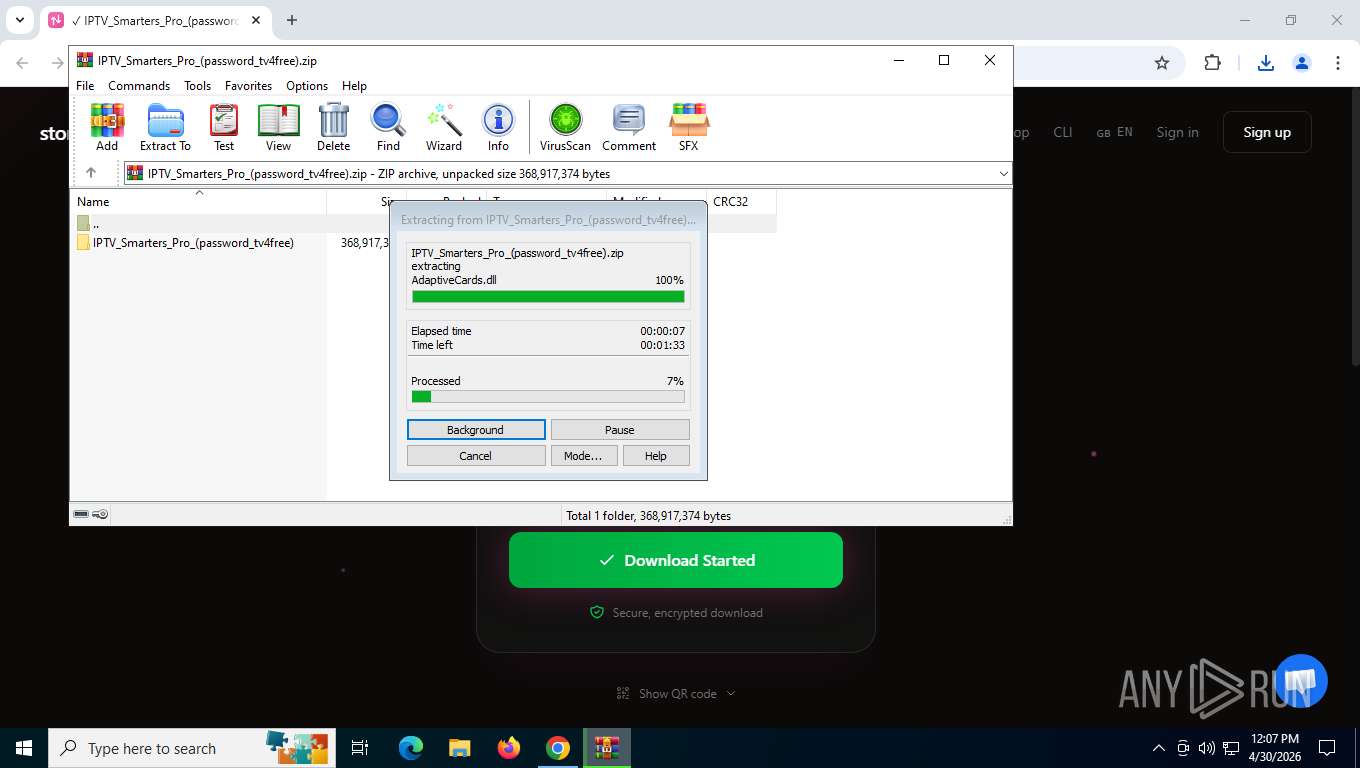
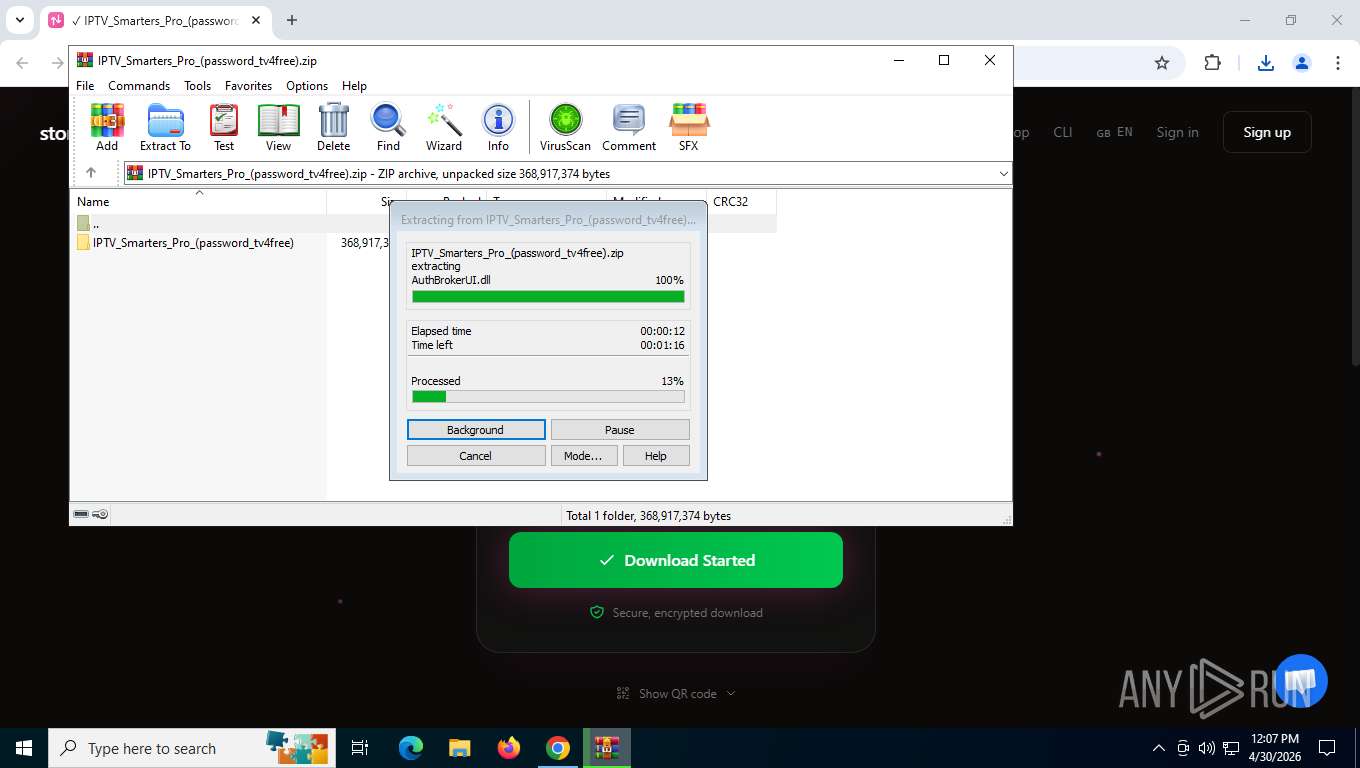
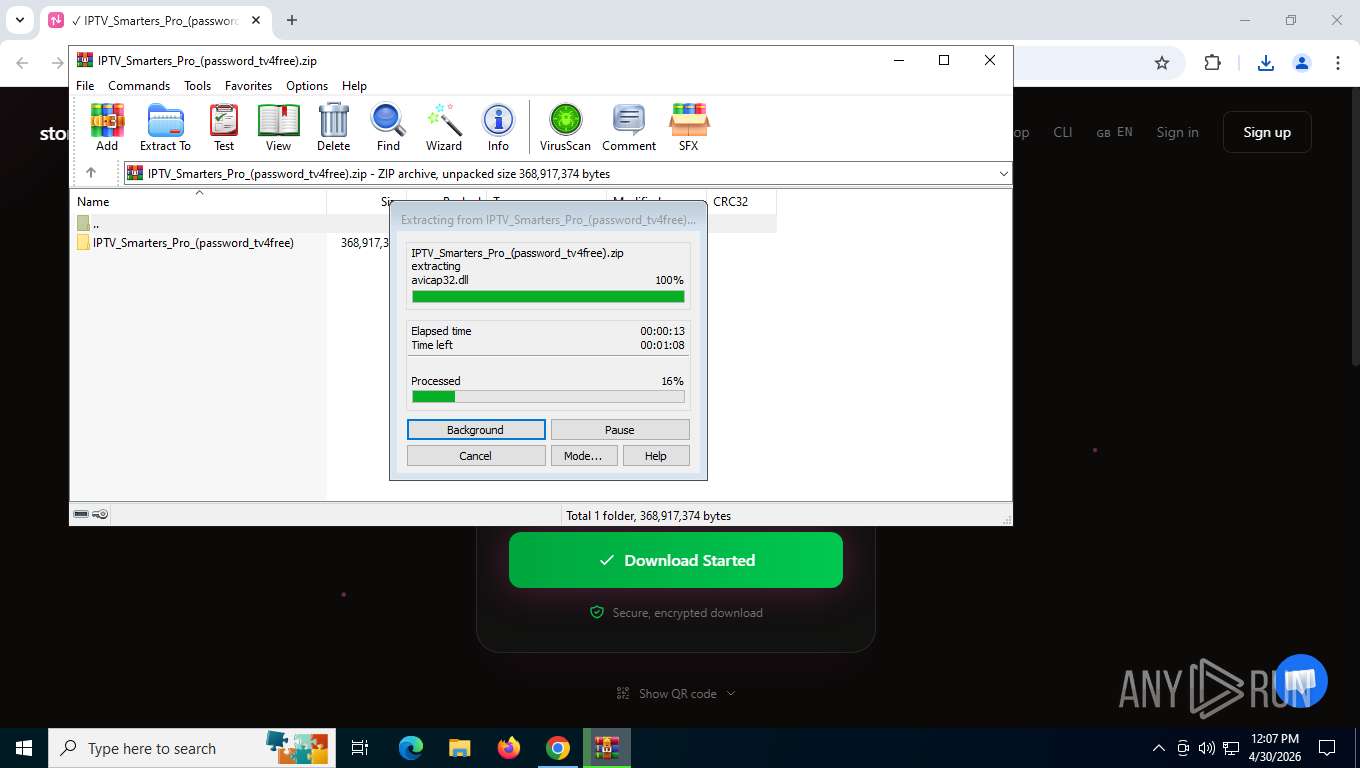
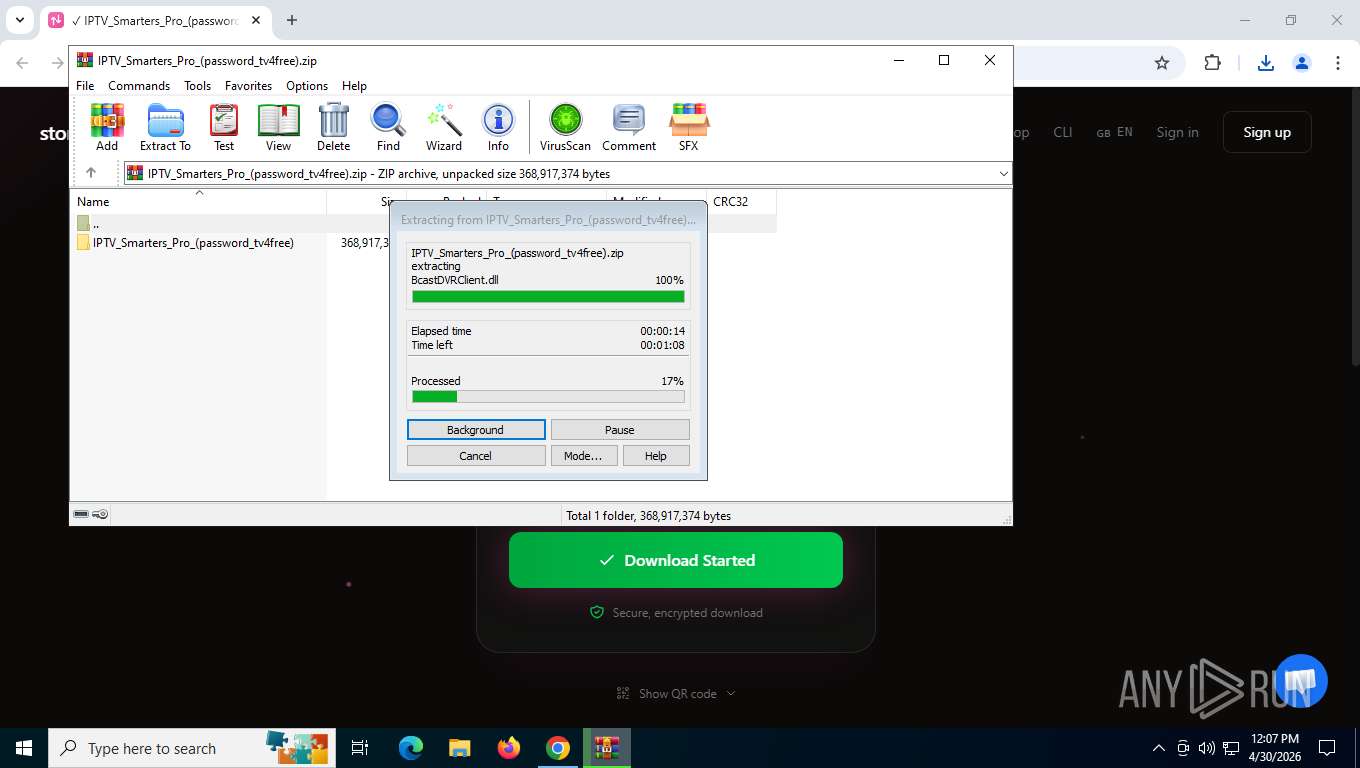
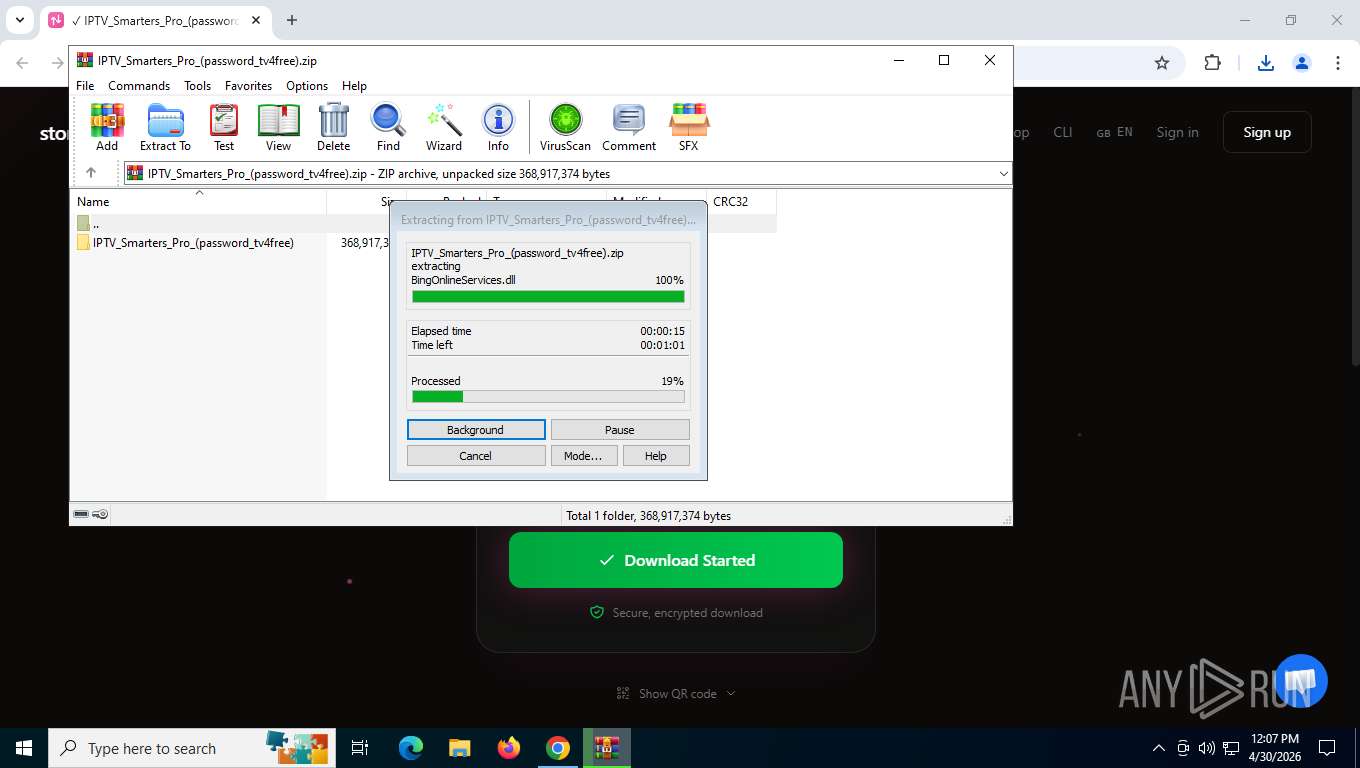
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8184)
The sample compiled with arabic language support
- WinRAR.exe (PID: 8184)
The sample compiled with turkish language support
- WinRAR.exe (PID: 8184)
The sample compiled with bulgarian language support
- WinRAR.exe (PID: 8184)
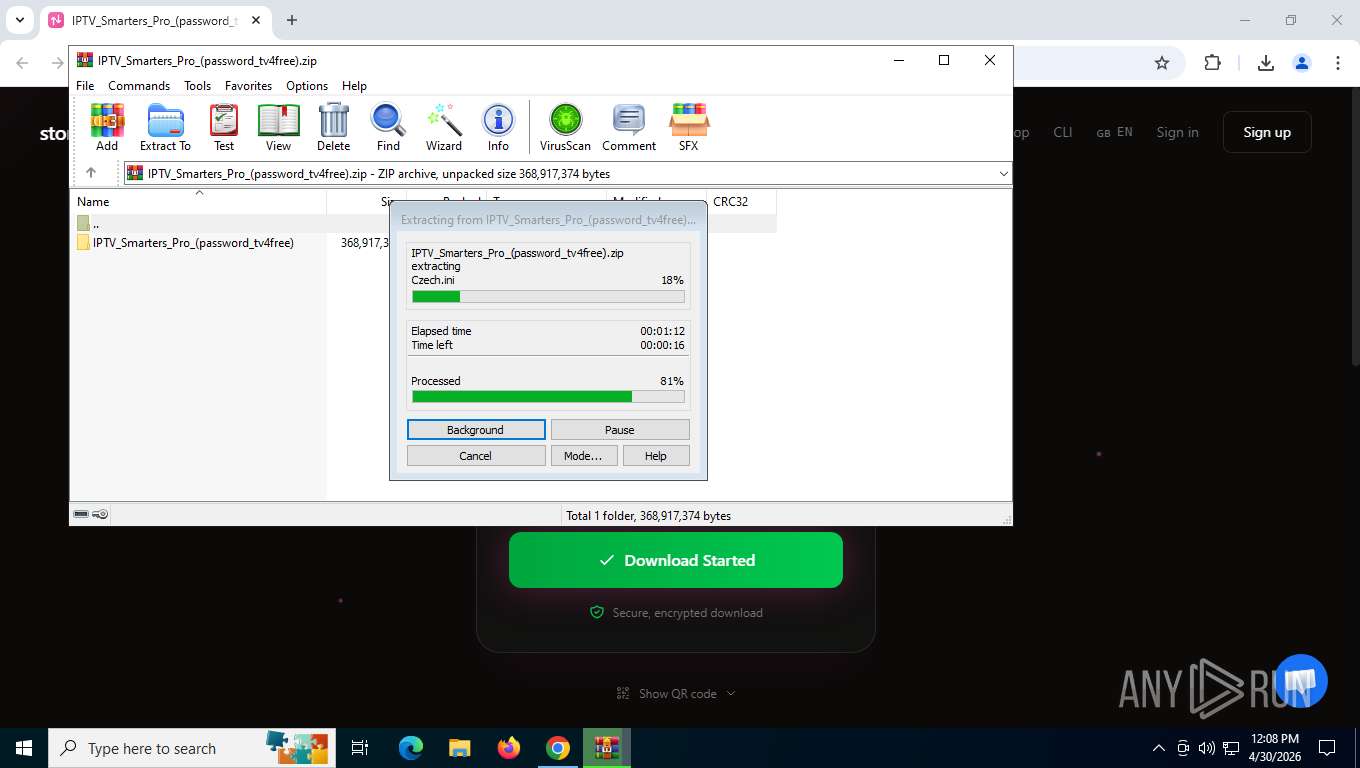
The sample compiled with czech language support
- WinRAR.exe (PID: 8184)
The sample compiled with german language support
- WinRAR.exe (PID: 8184)
The sample compiled with russian language support
- WinRAR.exe (PID: 8184)
The sample compiled with french language support
- WinRAR.exe (PID: 8184)
The sample compiled with spanish language support
- WinRAR.exe (PID: 8184)
The sample compiled with Italian language support
- WinRAR.exe (PID: 8184)
The sample compiled with japanese language support
- WinRAR.exe (PID: 8184)
The sample compiled with korean language support
- WinRAR.exe (PID: 8184)
The sample compiled with polish language support
- WinRAR.exe (PID: 8184)
The sample compiled with slovak language support
- WinRAR.exe (PID: 8184)
The sample compiled with portuguese language support
- WinRAR.exe (PID: 8184)
The sample compiled with swedish language support
- WinRAR.exe (PID: 8184)
The sample compiled with chinese language support
- WinRAR.exe (PID: 8184)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8184)
- notepad.exe (PID: 2420)
- notepad.exe (PID: 7320)
- notepad.exe (PID: 3120)
- notepad.exe (PID: 3160)
- notepad.exe (PID: 7884)
- notepad.exe (PID: 1108)
- notepad.exe (PID: 5304)
- notepad.exe (PID: 8756)
- notepad.exe (PID: 8388)
- IEChooser.exe (PID: 8272)
Checks supported languages
- IPTVSmartersProSetup.exe (PID: 5548)
- IPTVSmartersProSetup.exe (PID: 7388)
- MigRegDB.exe (PID: 6448)
- DismHost.exe (PID: 8932)
- comrepl.exe (PID: 9076)
- IEChooser.exe (PID: 8272)
Application based on Golang
- IPTVSmartersProSetup.exe (PID: 5548)
- IPTVSmartersProSetup.exe (PID: 7388)
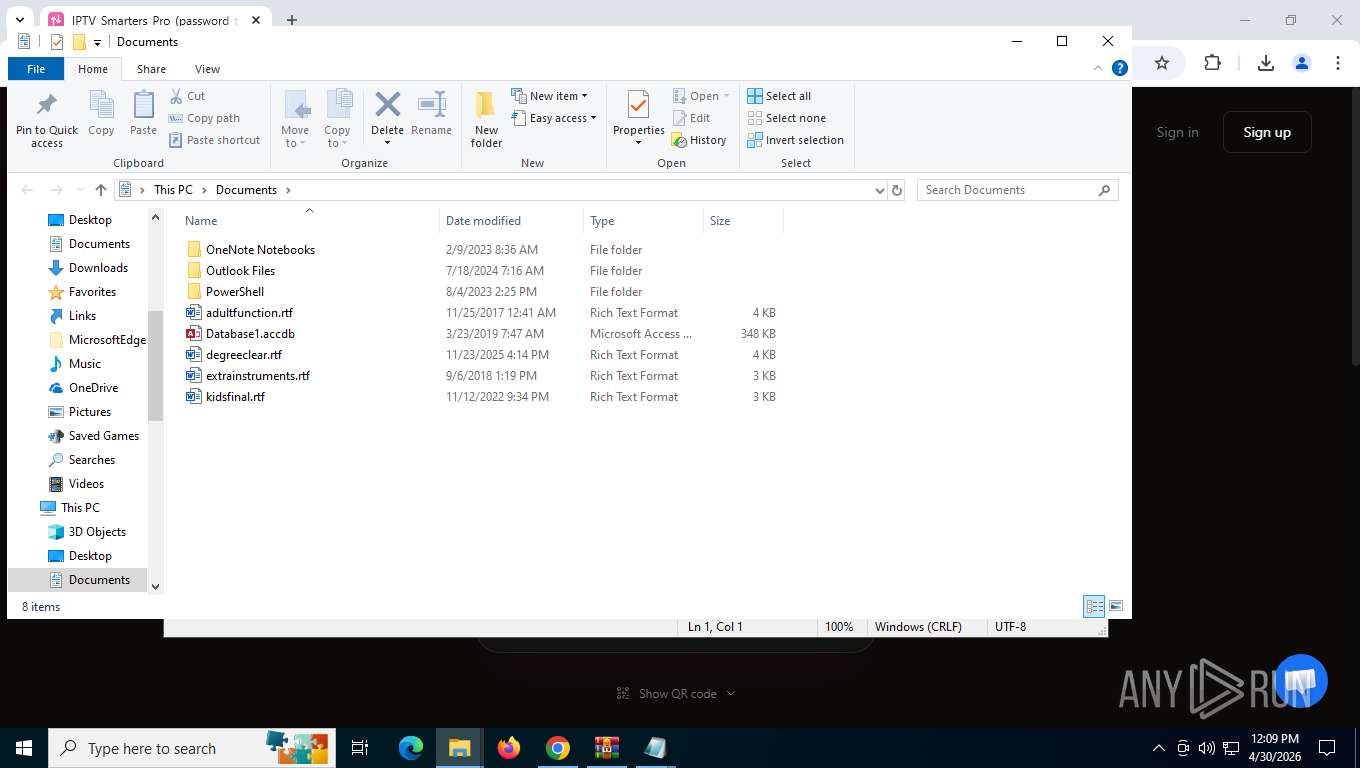
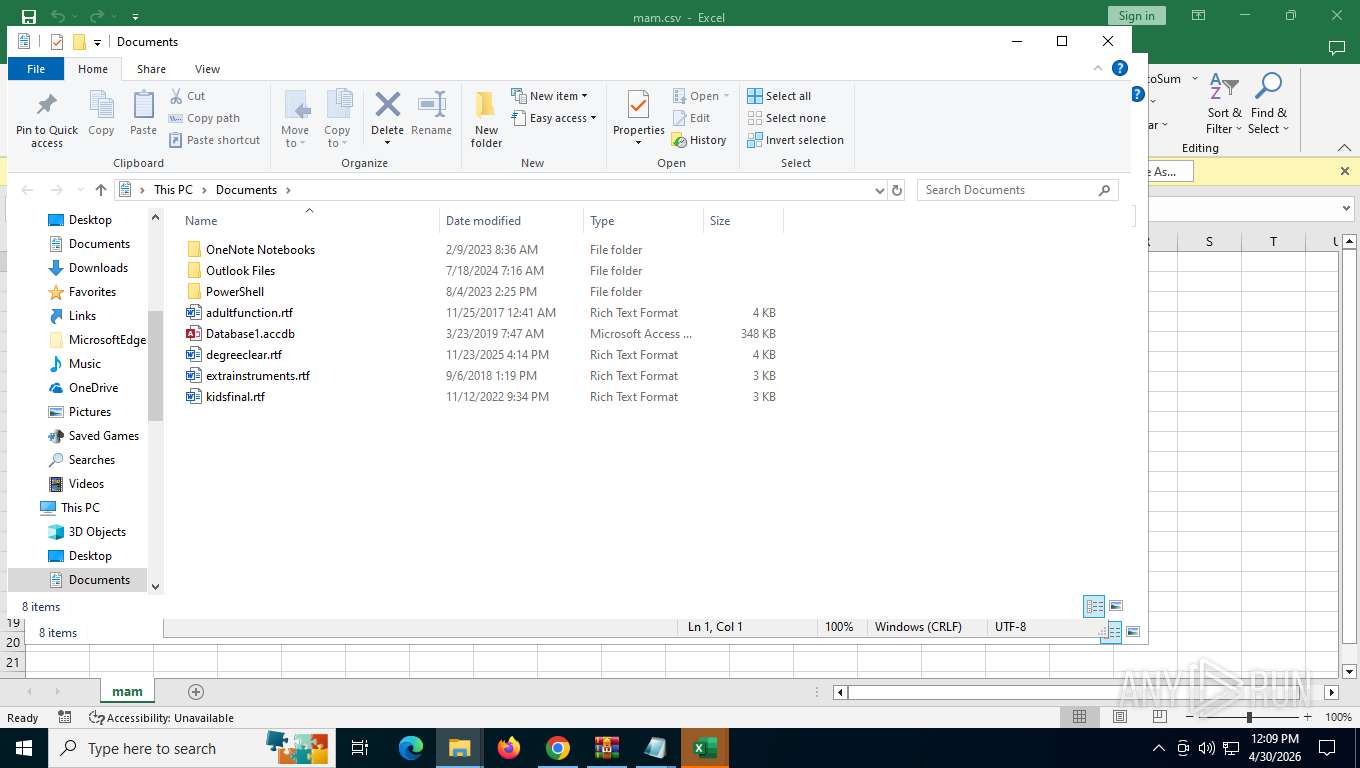
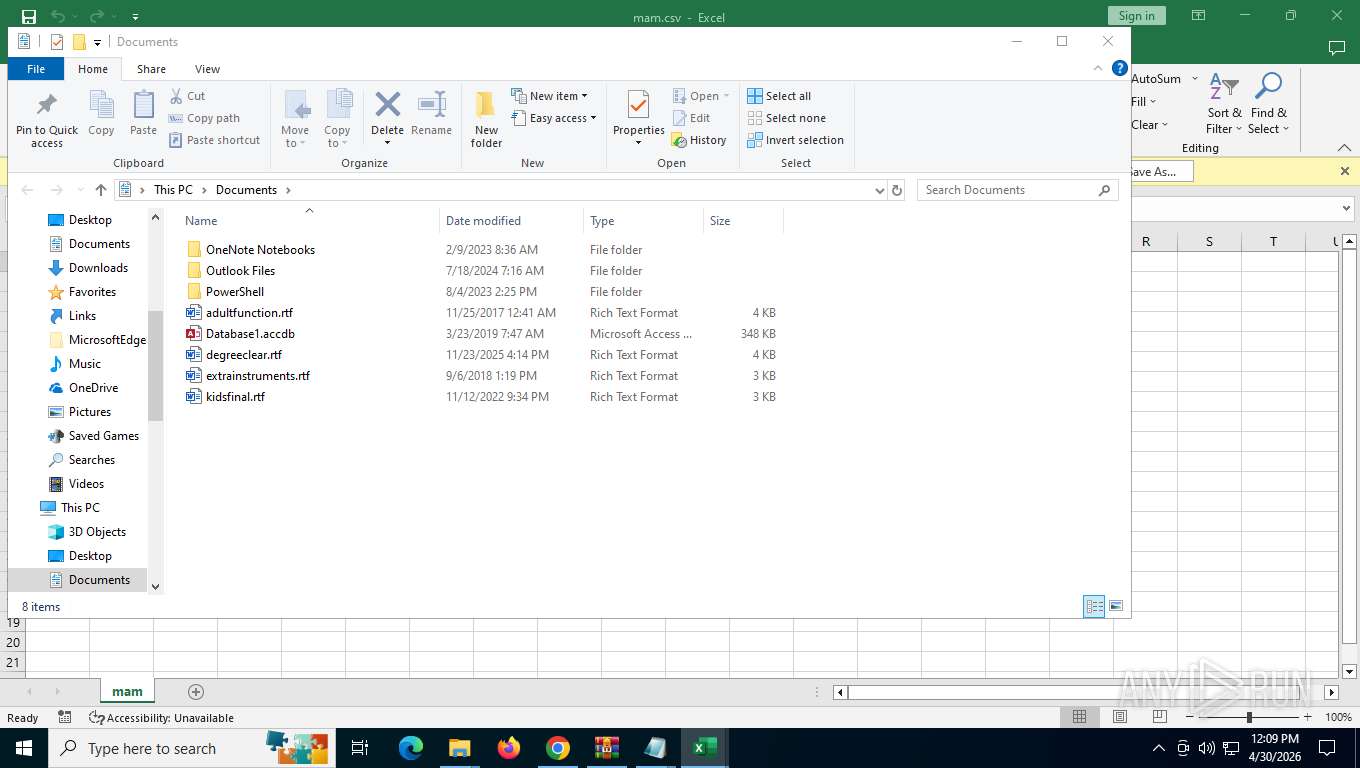
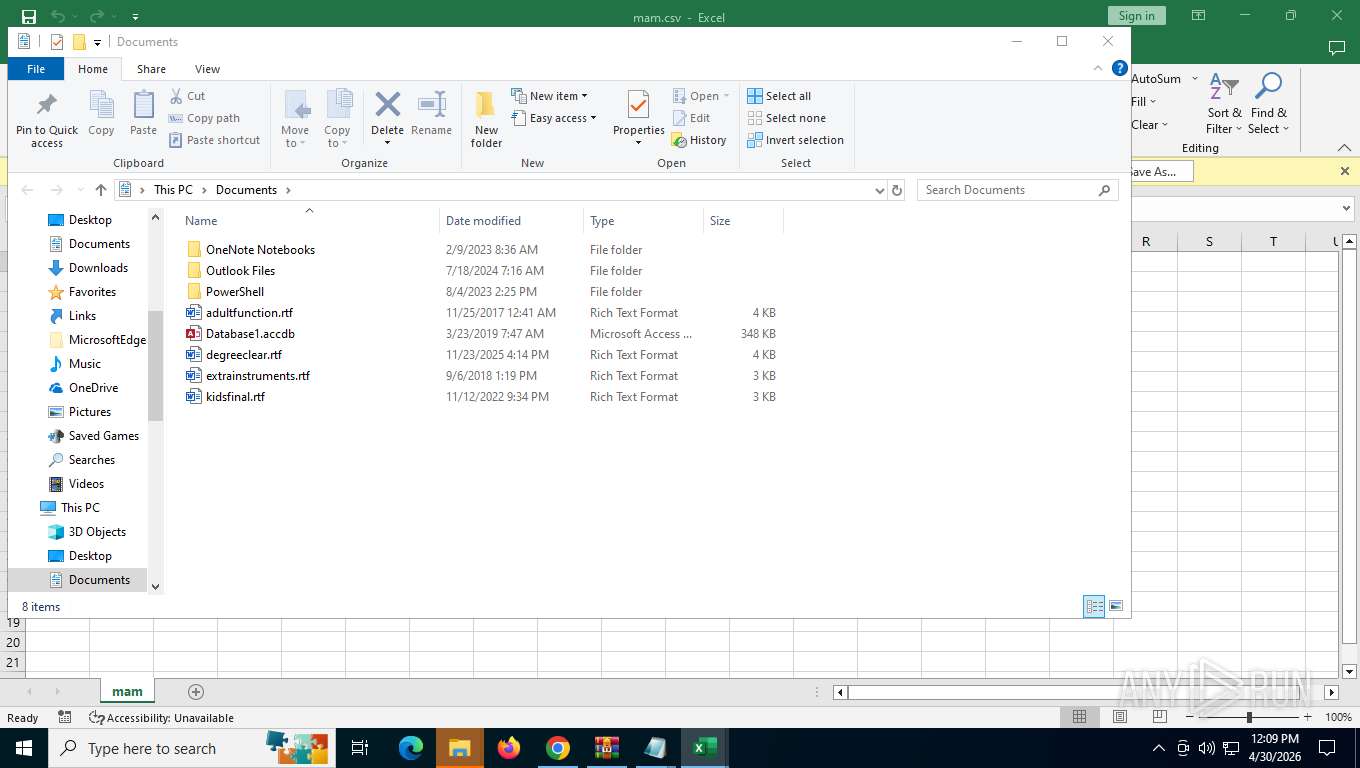
Manual execution by a user
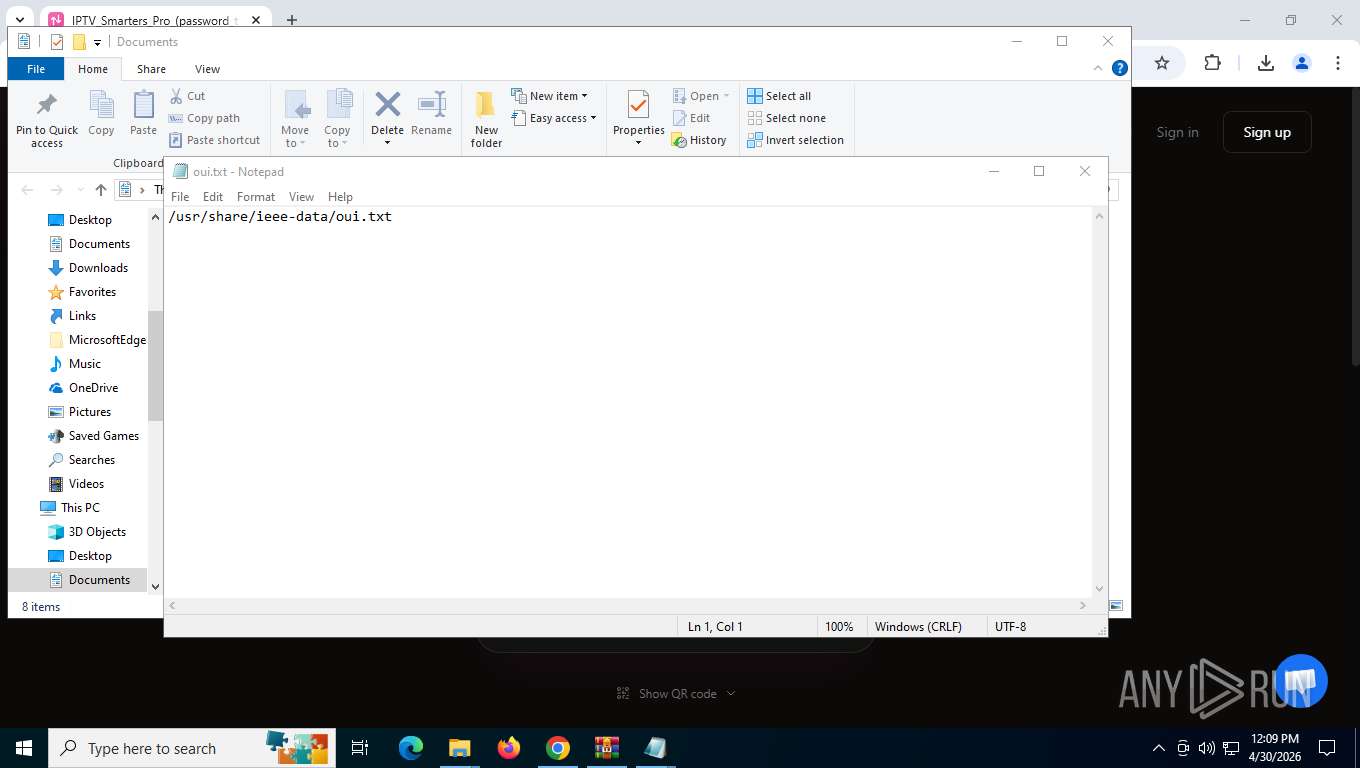
- notepad.exe (PID: 2420)
- notepad.exe (PID: 7884)
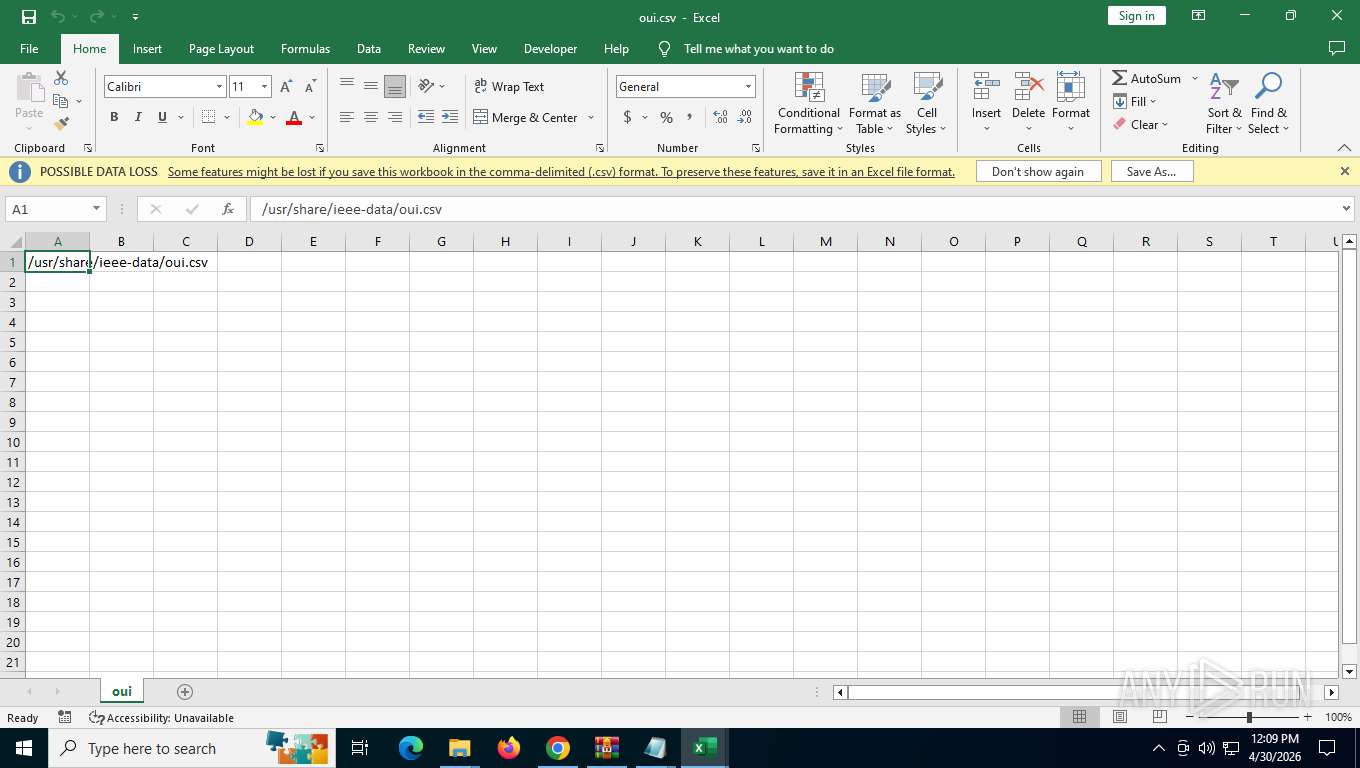
- EXCEL.EXE (PID: 7352)
- EXCEL.EXE (PID: 5888)
- notepad.exe (PID: 7320)
- EXCEL.EXE (PID: 7876)
- EXCEL.EXE (PID: 2532)
- notepad.exe (PID: 3120)
- EXCEL.EXE (PID: 7288)
- EXCEL.EXE (PID: 5764)
- EXCEL.EXE (PID: 2916)
- notepad.exe (PID: 3160)
- notepad.exe (PID: 1108)
- MigRegDB.exe (PID: 6448)
- notepad.exe (PID: 5304)
- notepad.exe (PID: 8756)
- DismHost.exe (PID: 8932)
- EXCEL.EXE (PID: 9192)
- notepad.exe (PID: 8388)
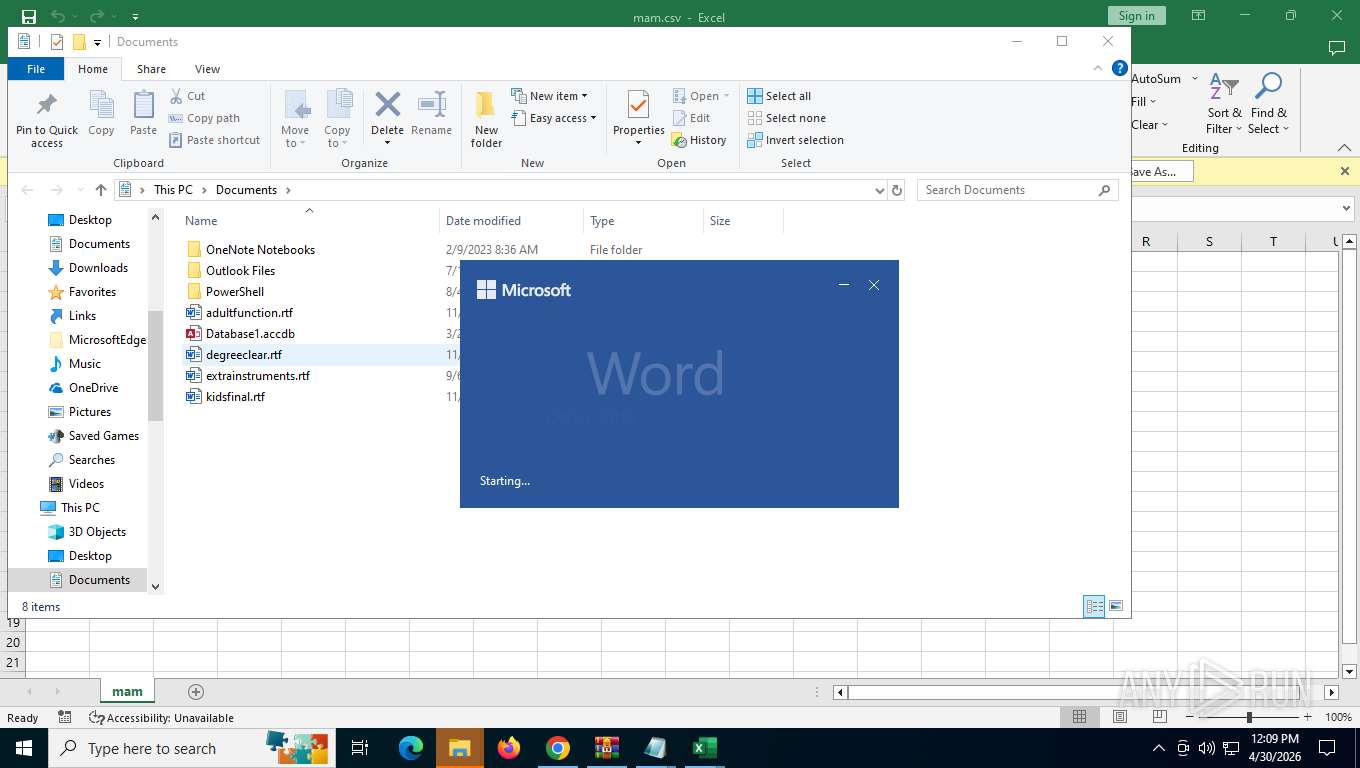
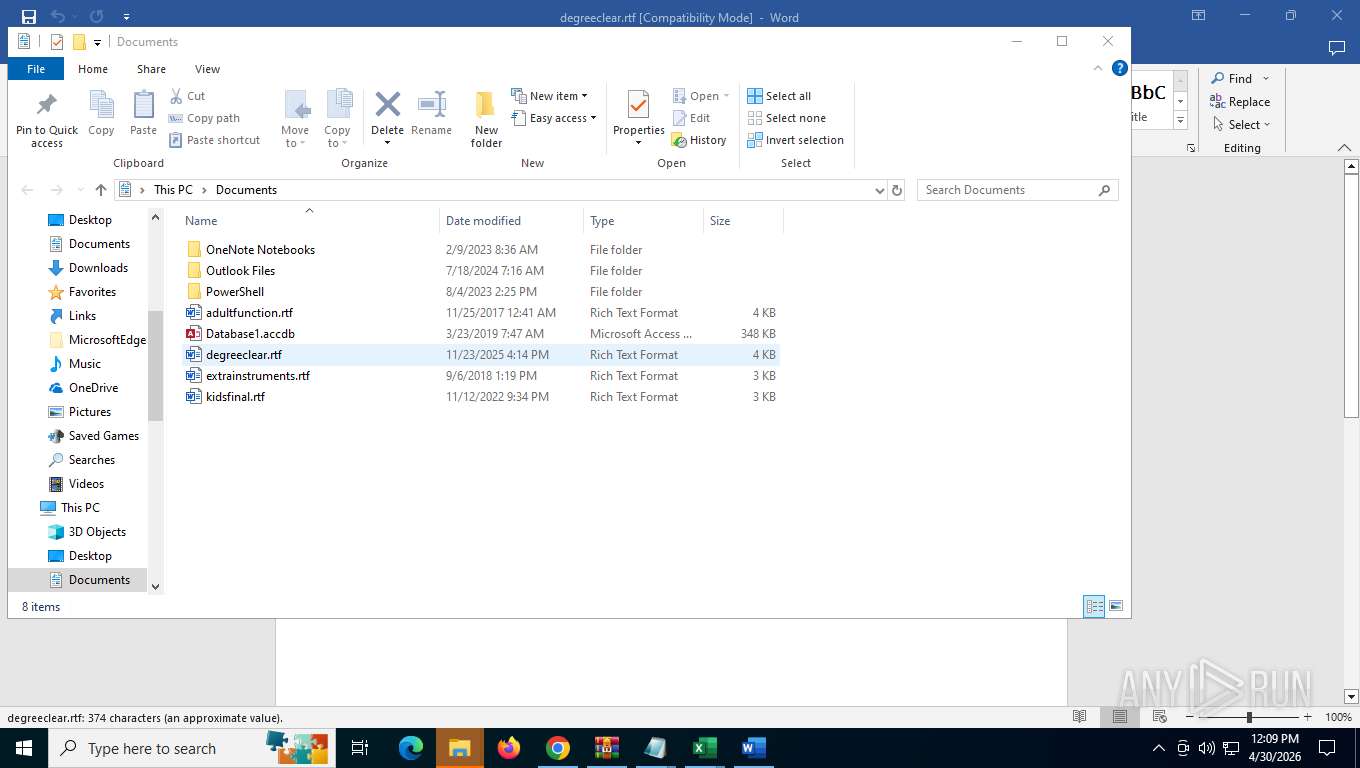
- WINWORD.EXE (PID: 9096)
- wermgr.exe (PID: 8292)
- IEChooser.exe (PID: 8272)
- wermgr.exe (PID: 8492)
- wermgr.exe (PID: 3320)
- WINWORD.EXE (PID: 9516)
- WINWORD.EXE (PID: 9596)
- comrepl.exe (PID: 9076)
There is functionality for taking screenshot (YARA)
- IPTVSmartersProSetup.exe (PID: 5548)
- IPTVSmartersProSetup.exe (PID: 7388)
Reads the computer name
- IPTVSmartersProSetup.exe (PID: 5548)
- DismHost.exe (PID: 8932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
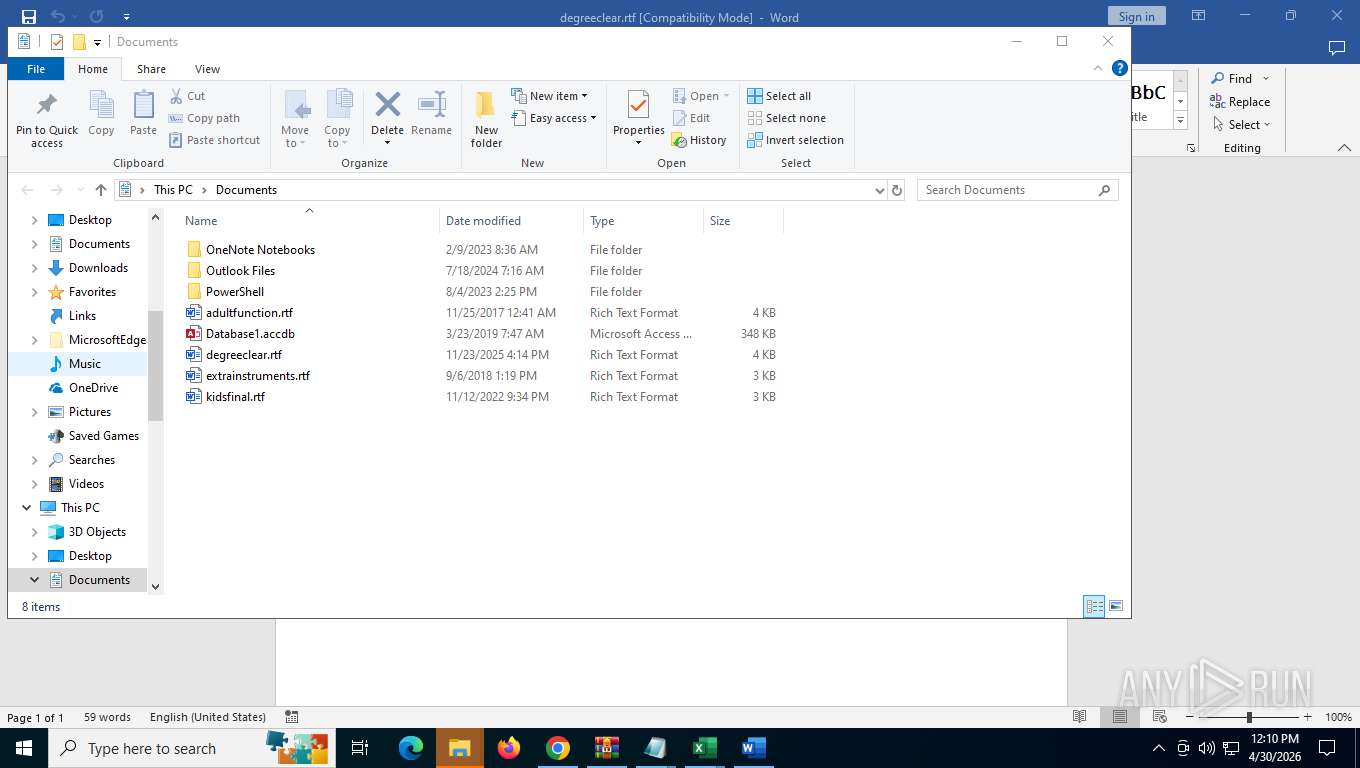
Total processes
214
Monitored processes
70
Malicious processes
1
Suspicious processes
4
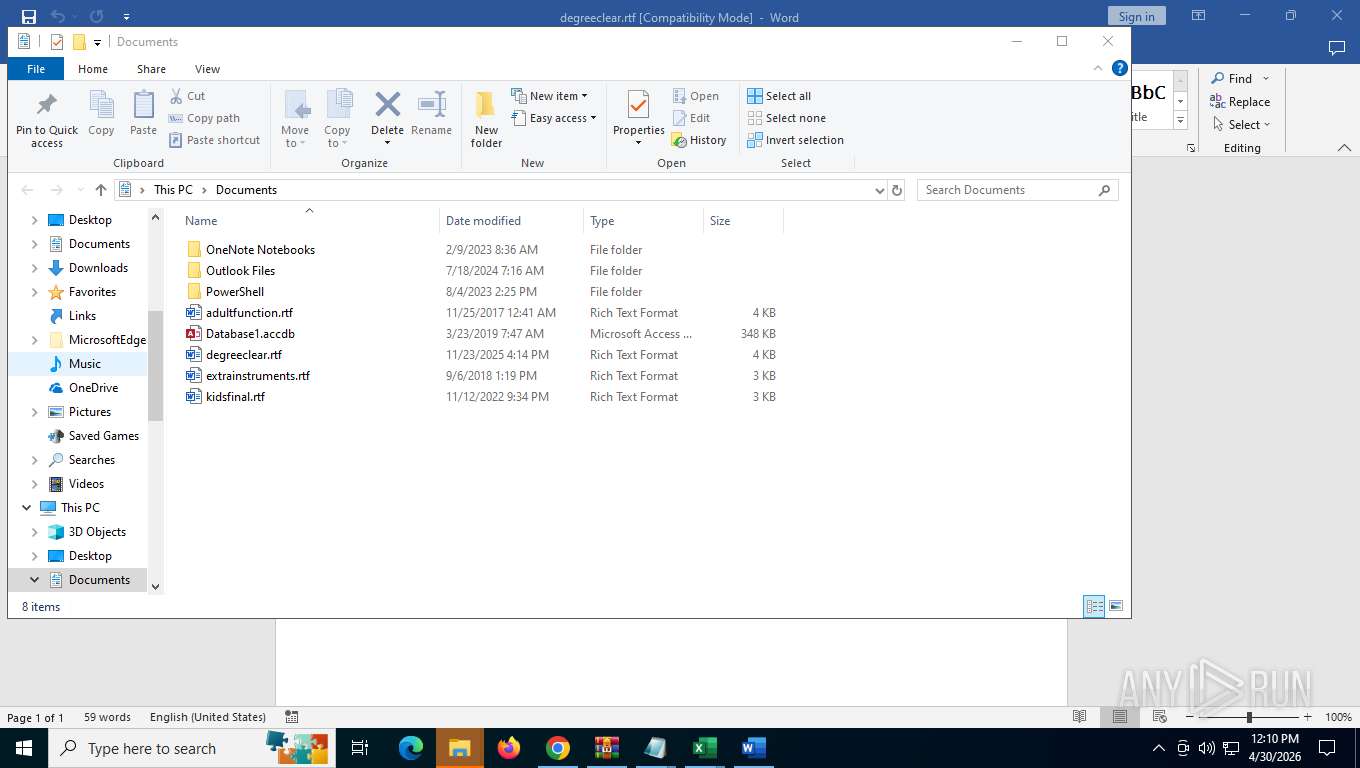
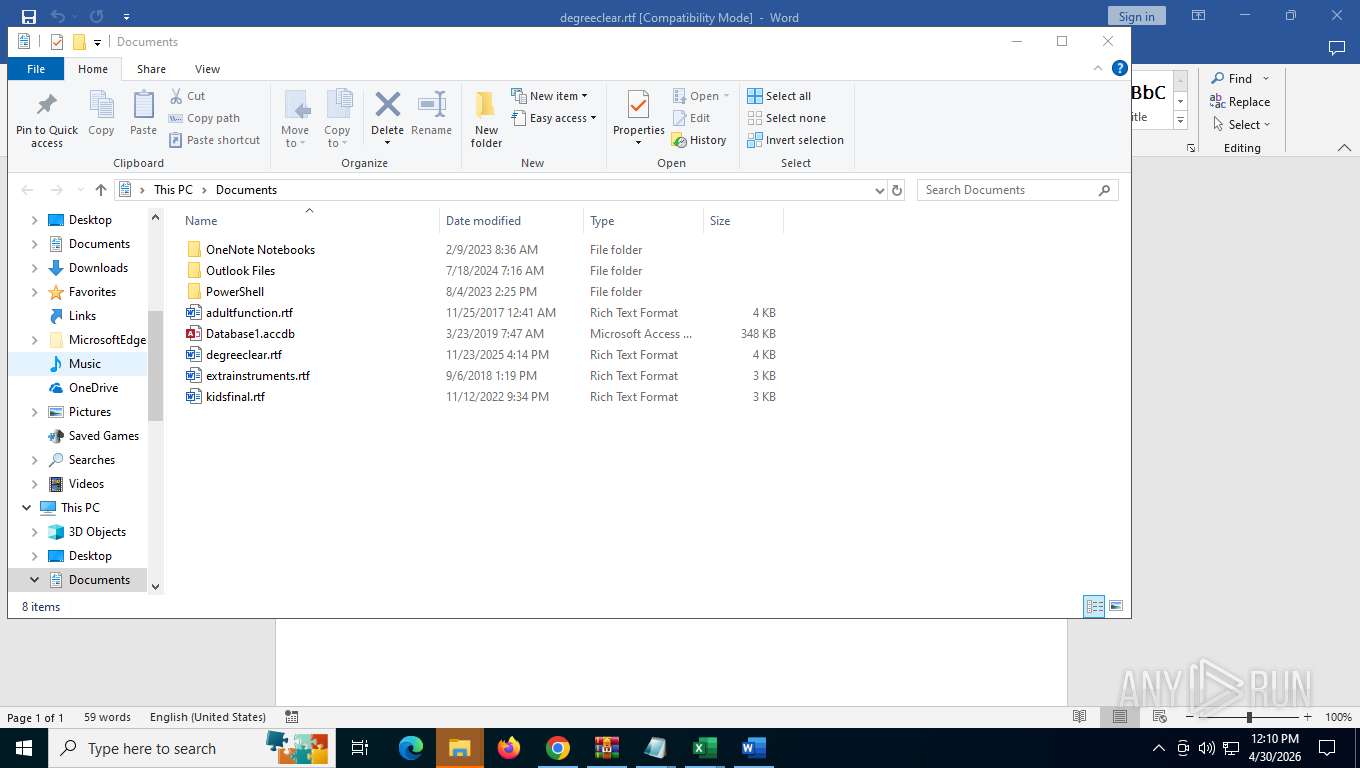
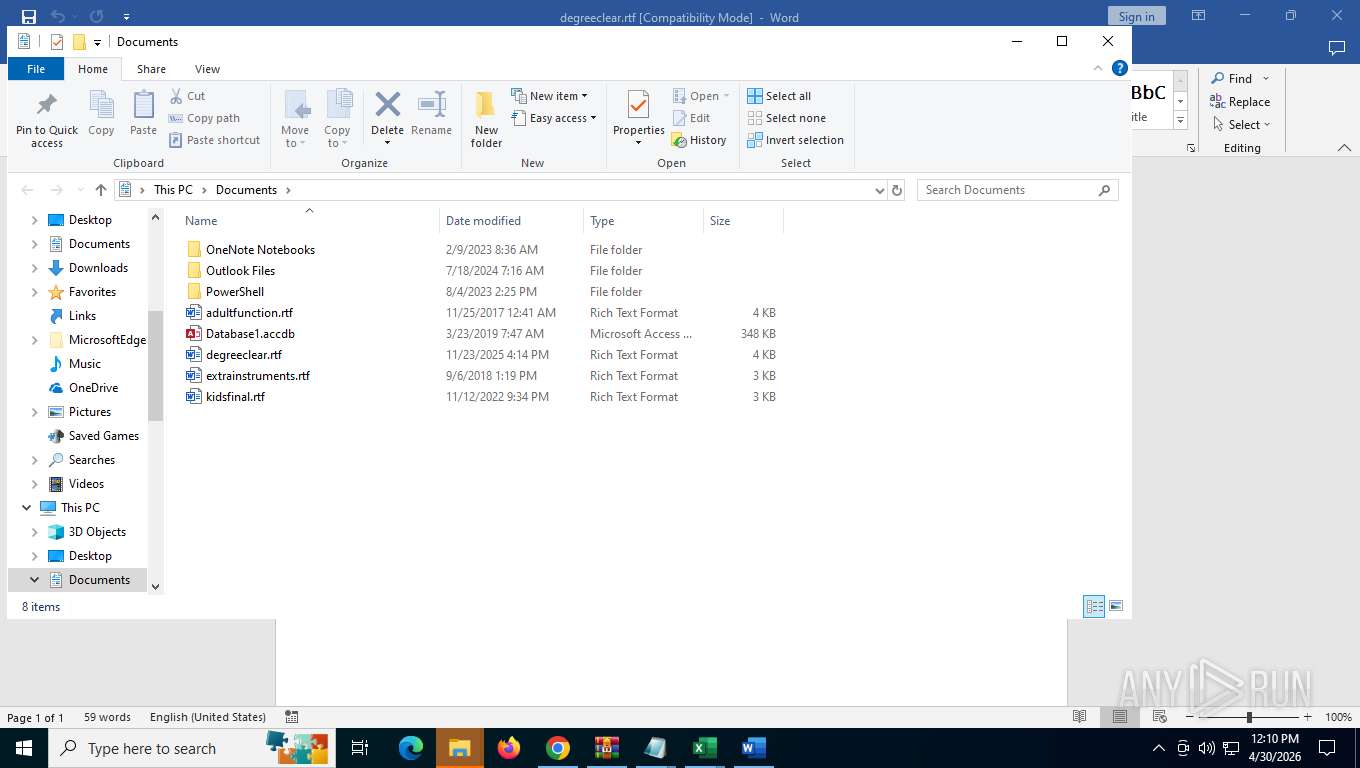
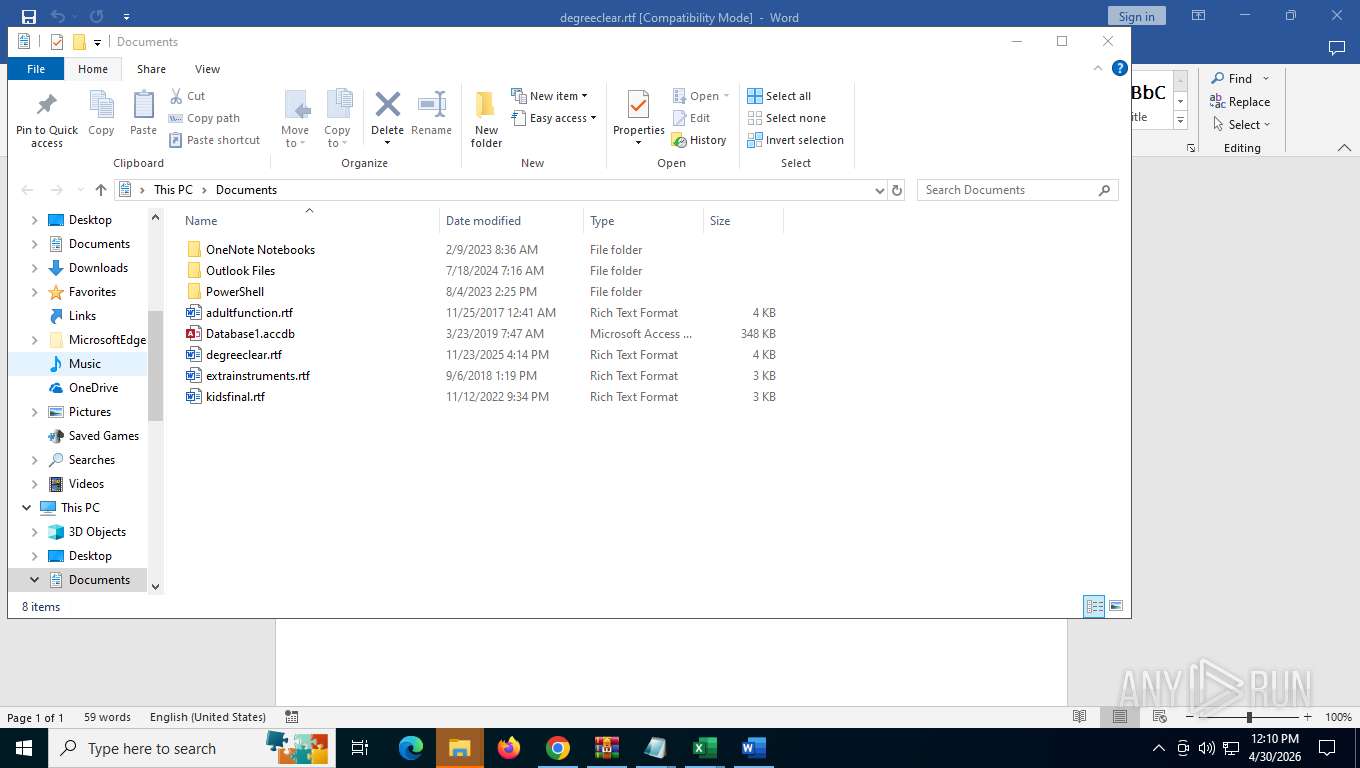
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5812,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4820,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1108 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\IPTV_Smarters_Pro_(password_tv4free)/apt/ieee-data/oui.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffe234afff8,0x7ffe234b0004,0x7ffe234b0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=32 --field-trial-handle=6680,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6140 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3228,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6720,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6128,i,825079554830692783,10870594093092113120,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
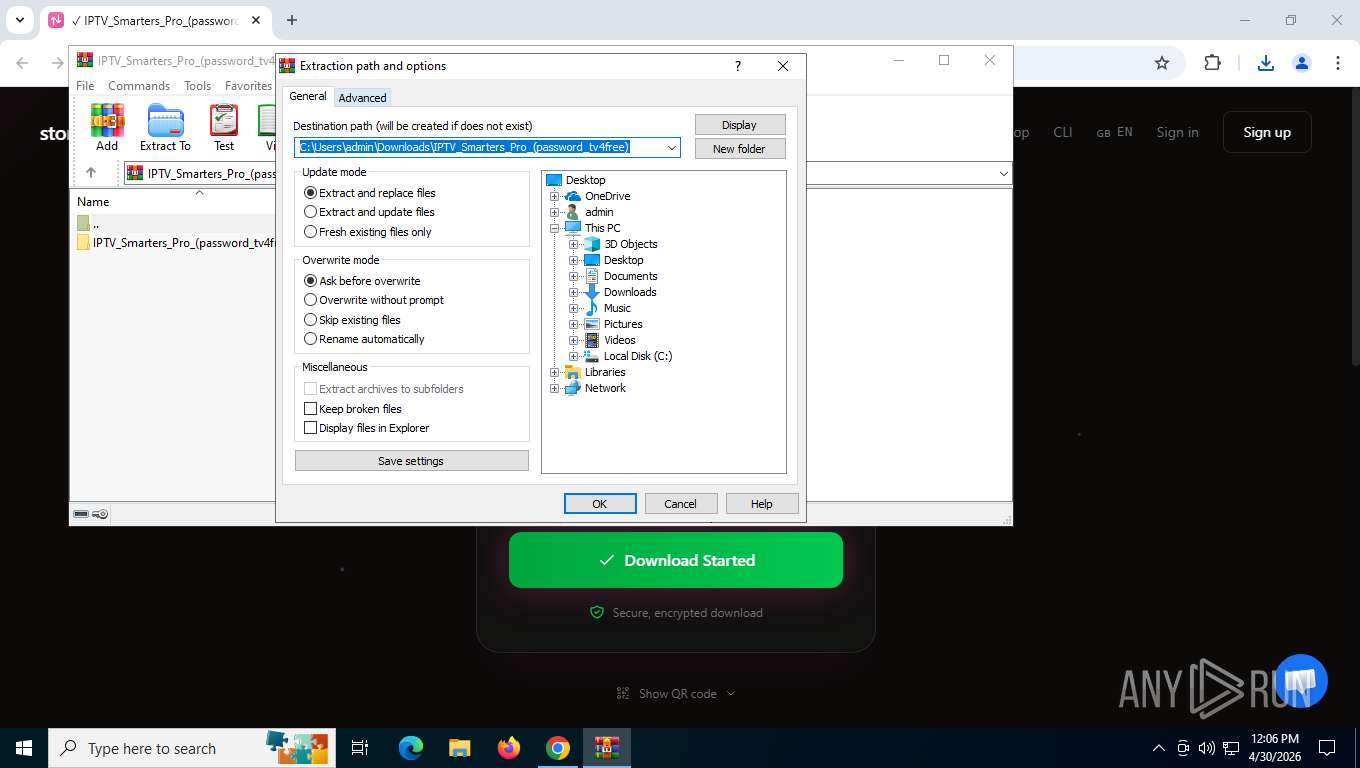
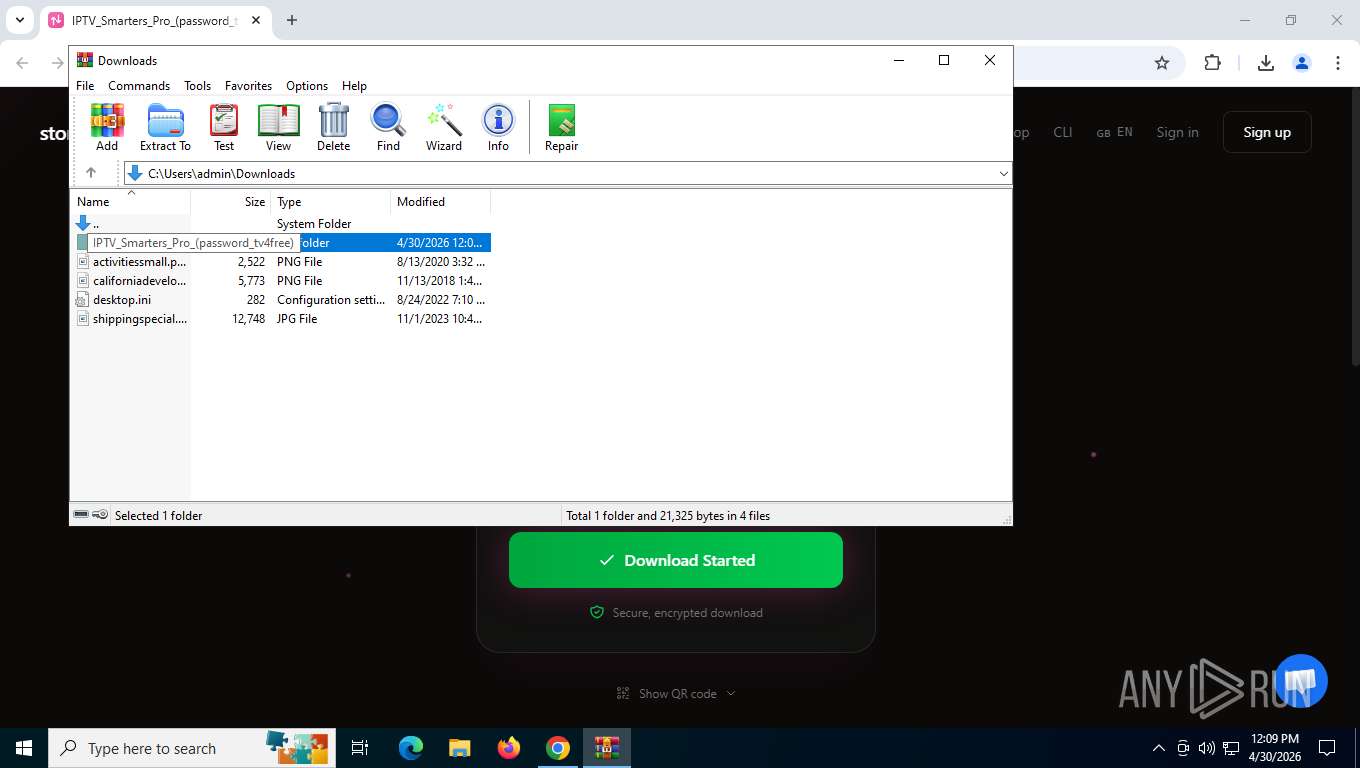
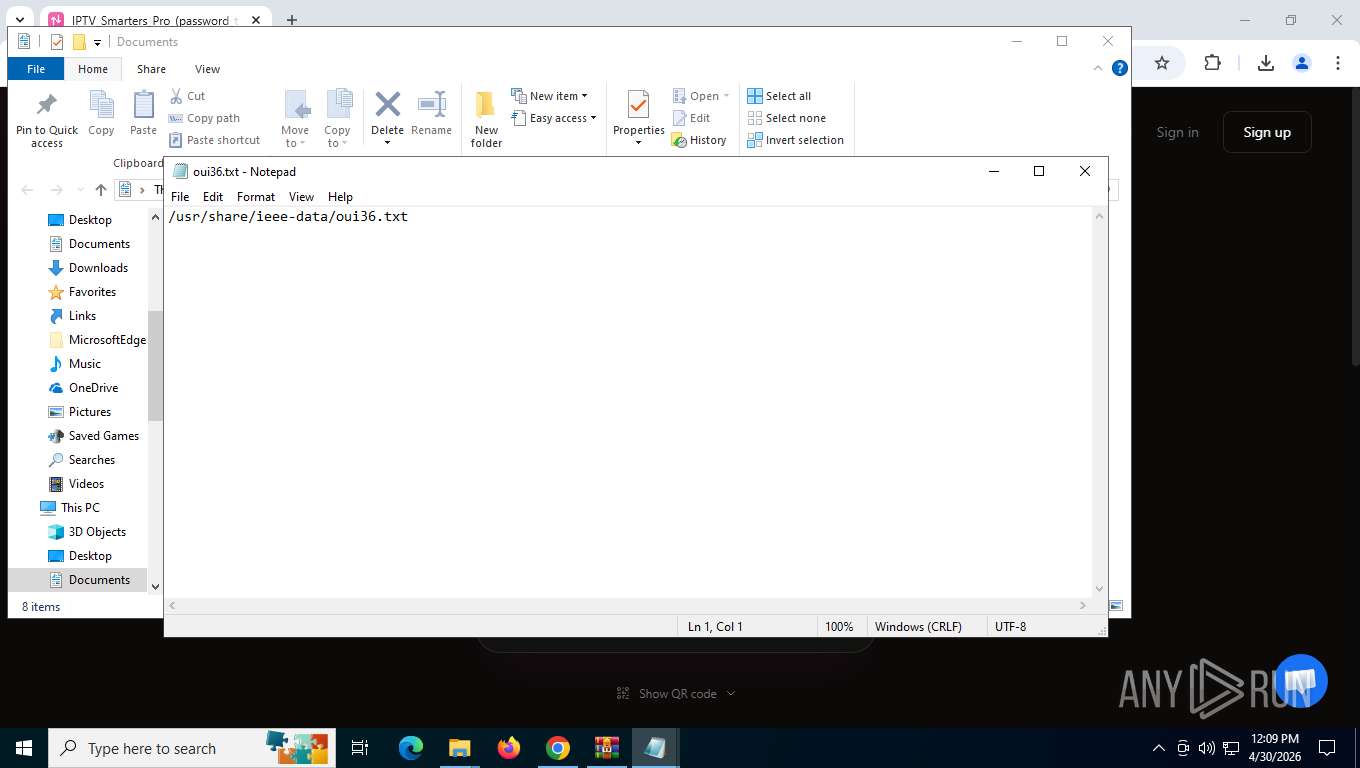
| 2420 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\IPTV_Smarters_Pro_(password_tv4free)\IPTV_Smarters_Pro_(password_tv4free)\apt\ieee-data\iab.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
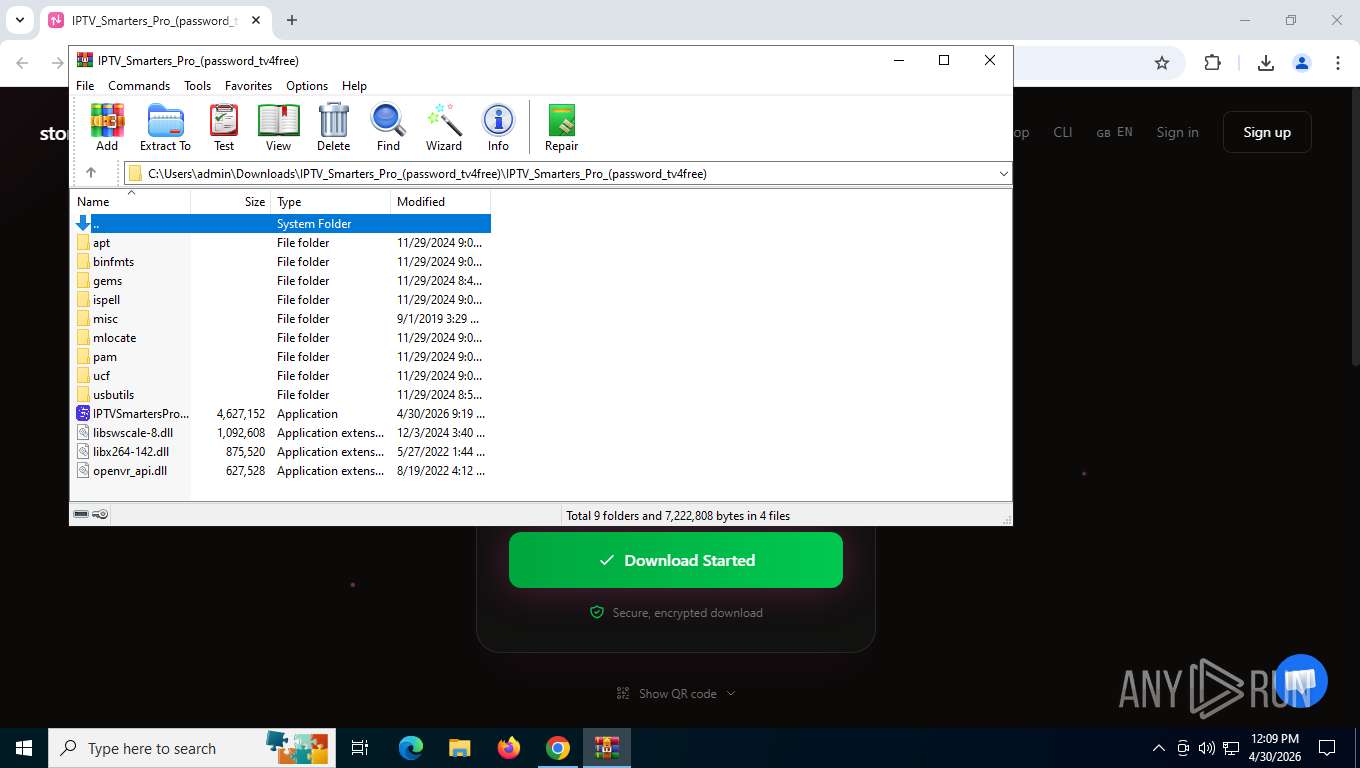
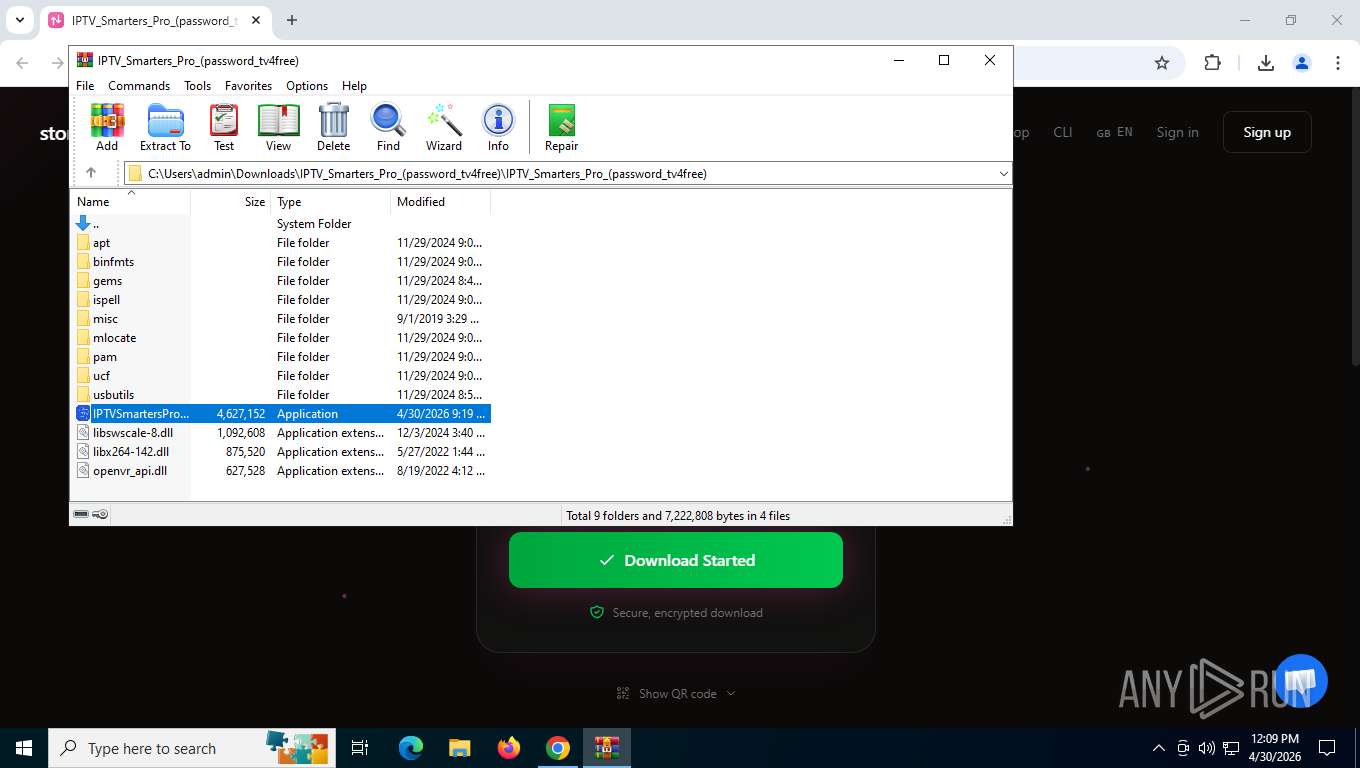
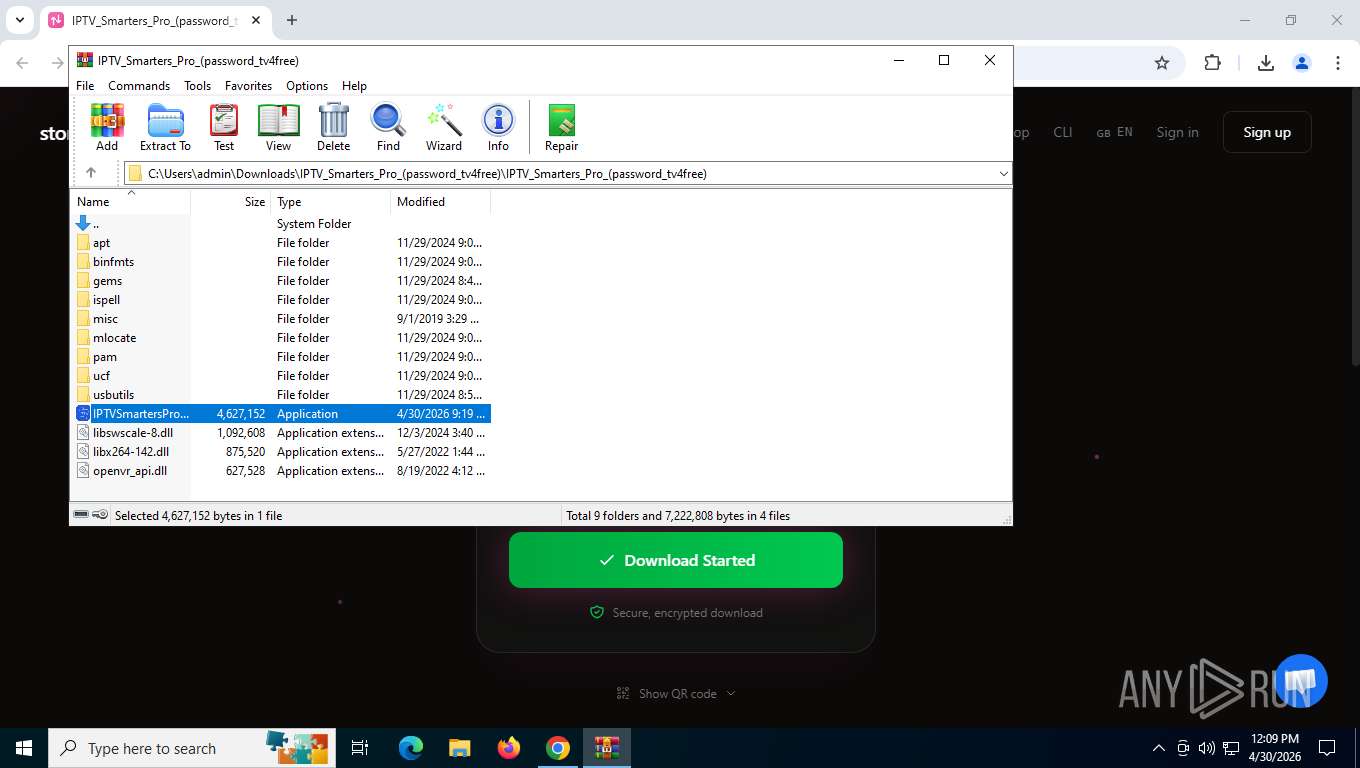
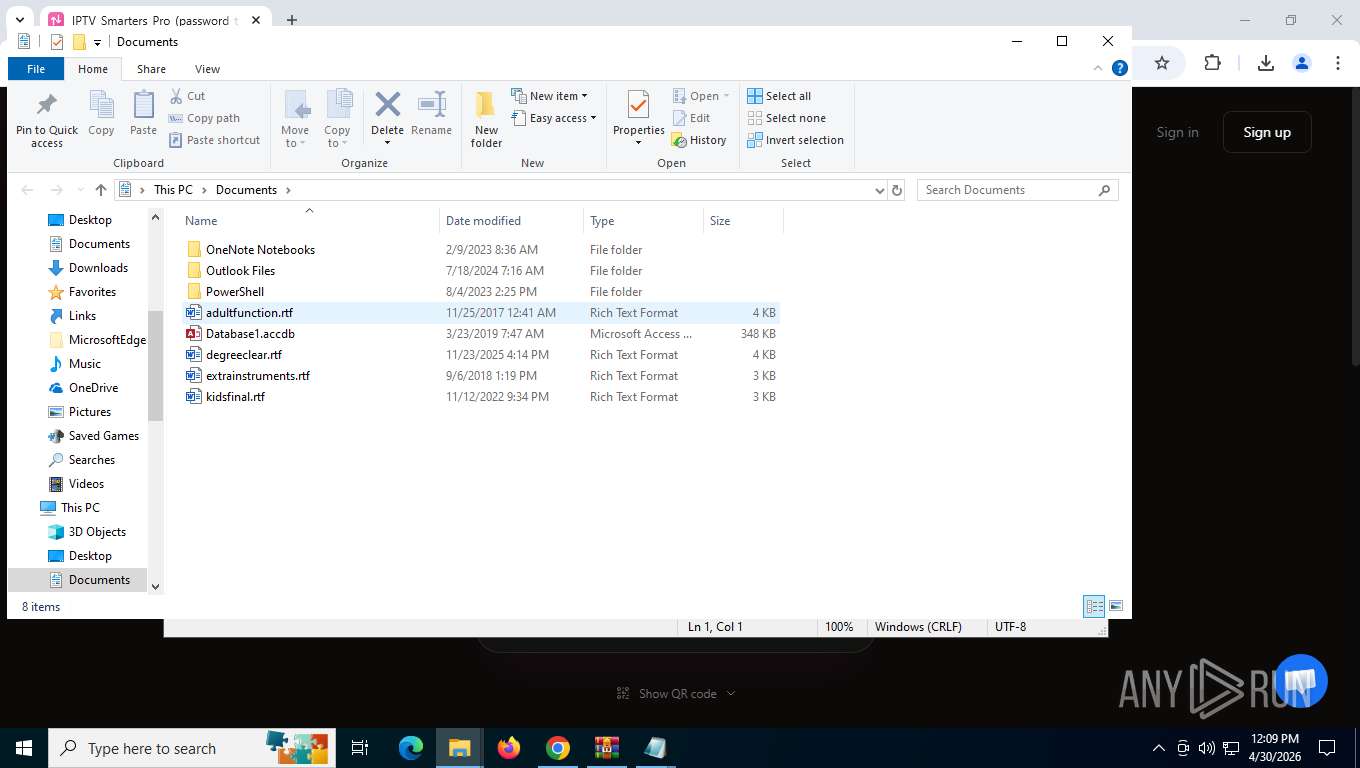
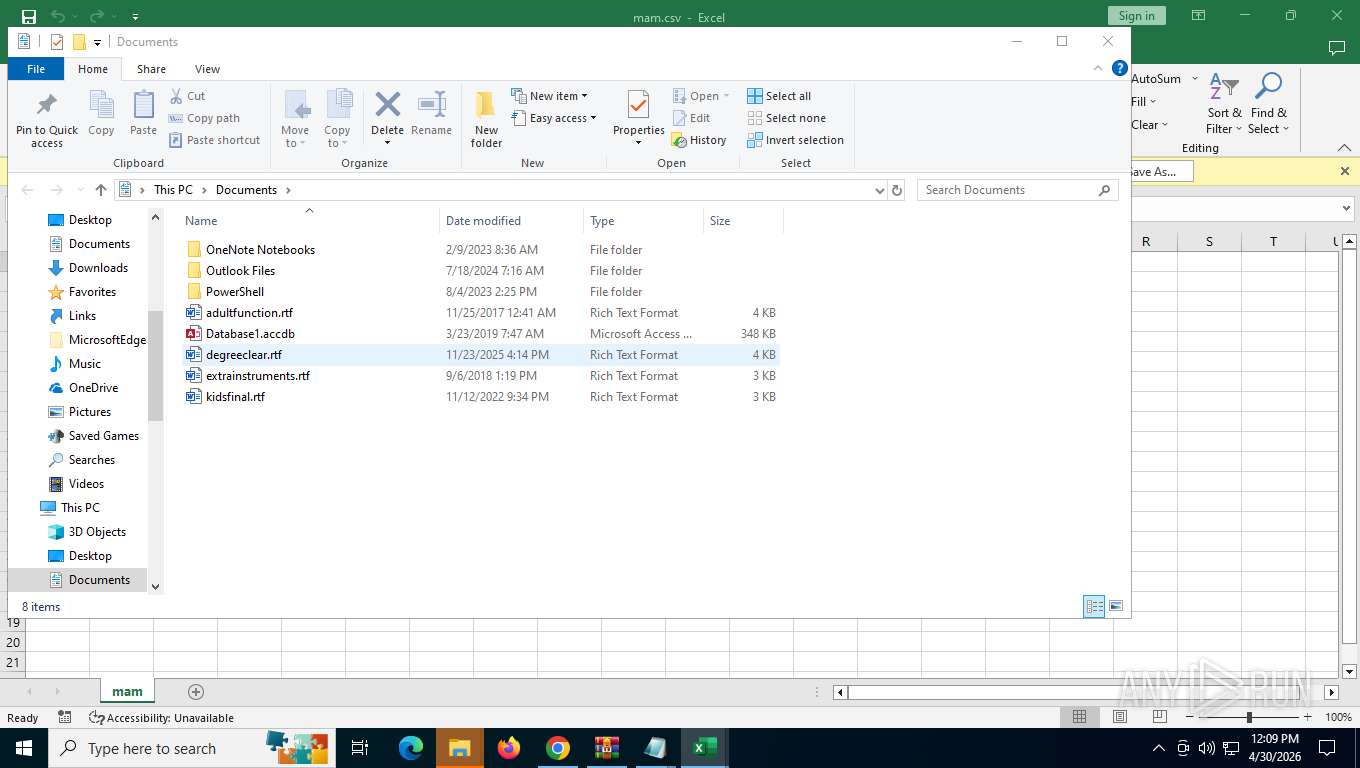
| 2532 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" C:\Users\admin\Downloads\IPTV_Smarters_Pro_(password_tv4free)\IPTV_Smarters_Pro_(password_tv4free)\apt\ieee-data\mam.csv | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
47 962
Read events
46 806
Write events
999
Delete events
157
Modification events
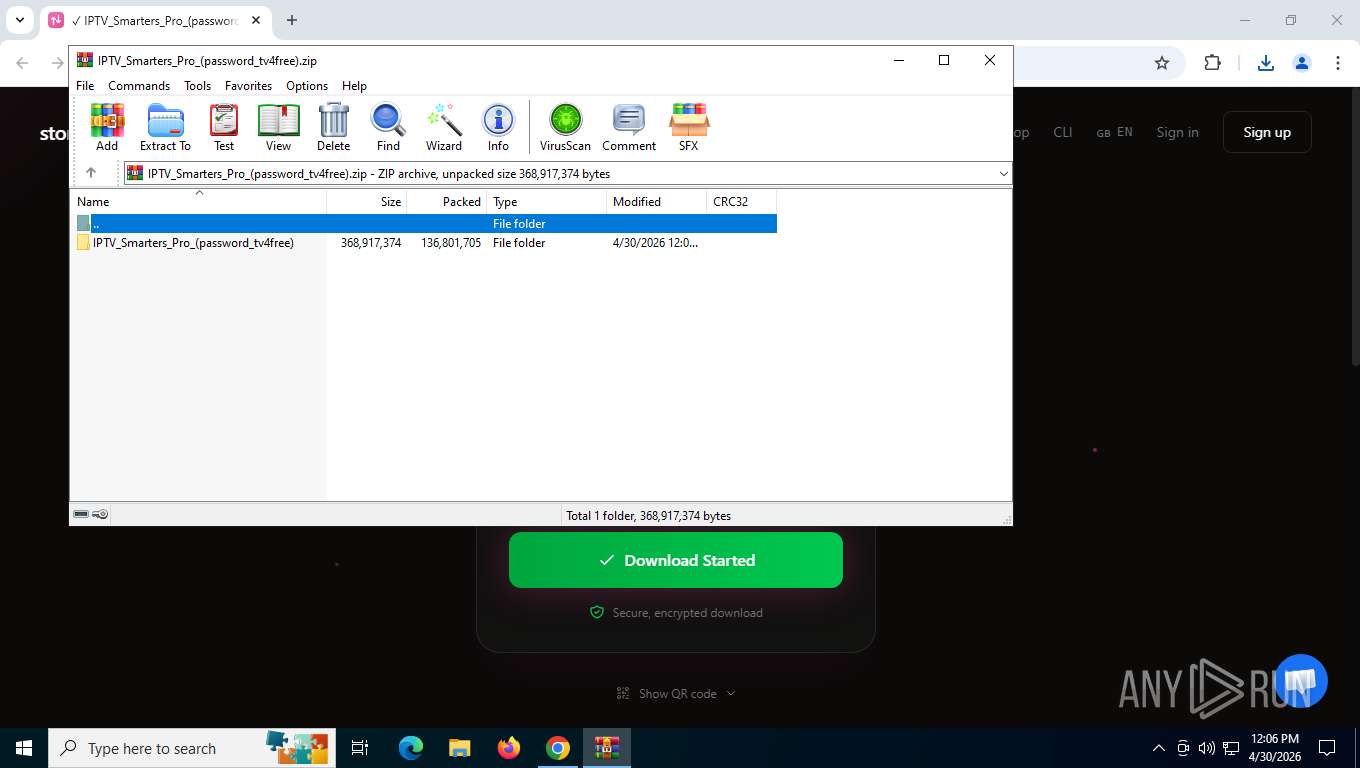
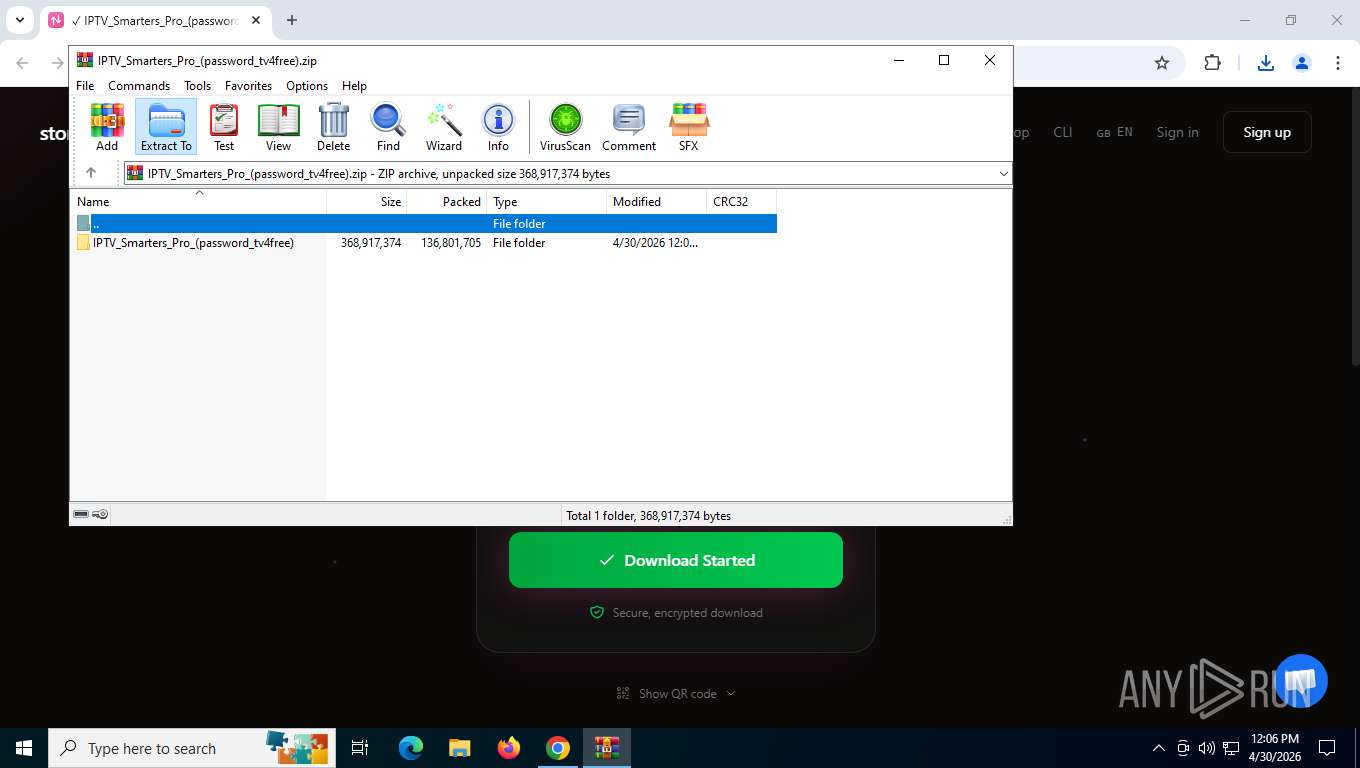
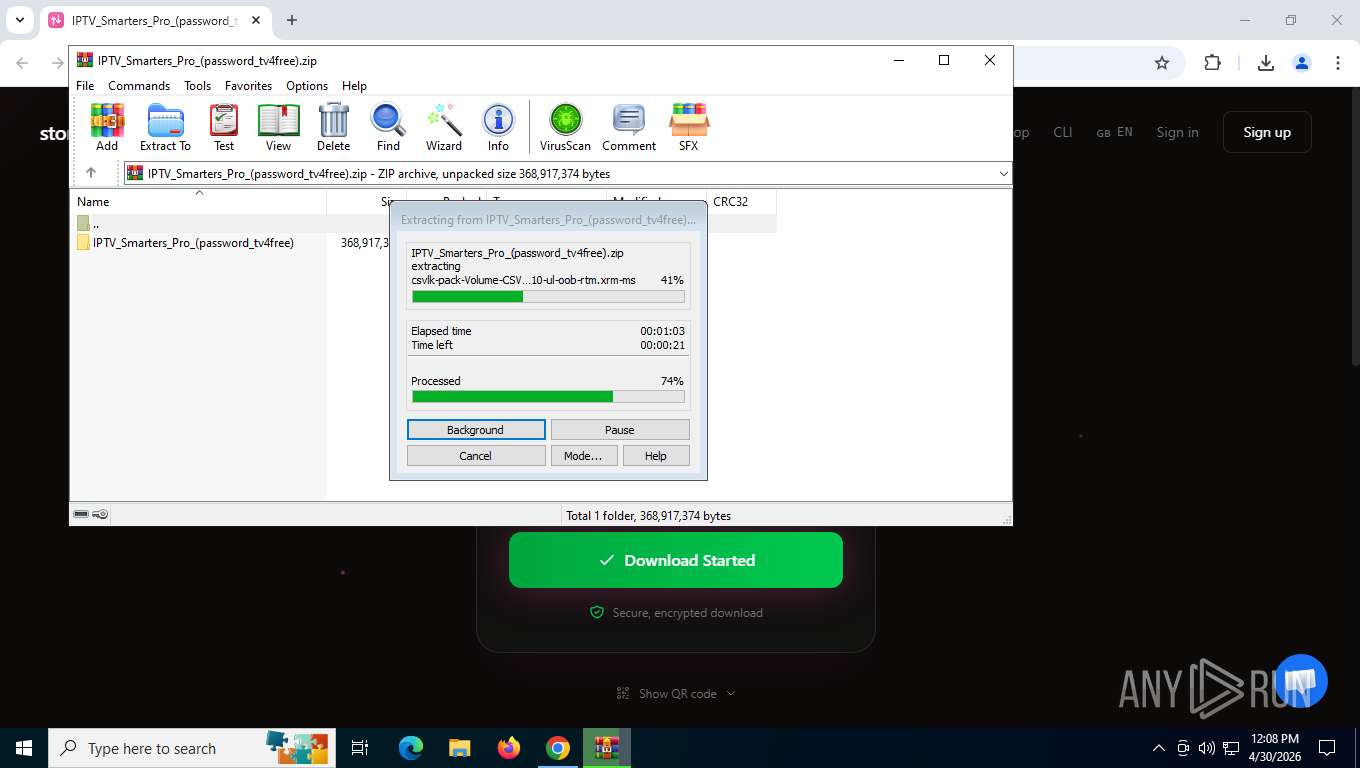
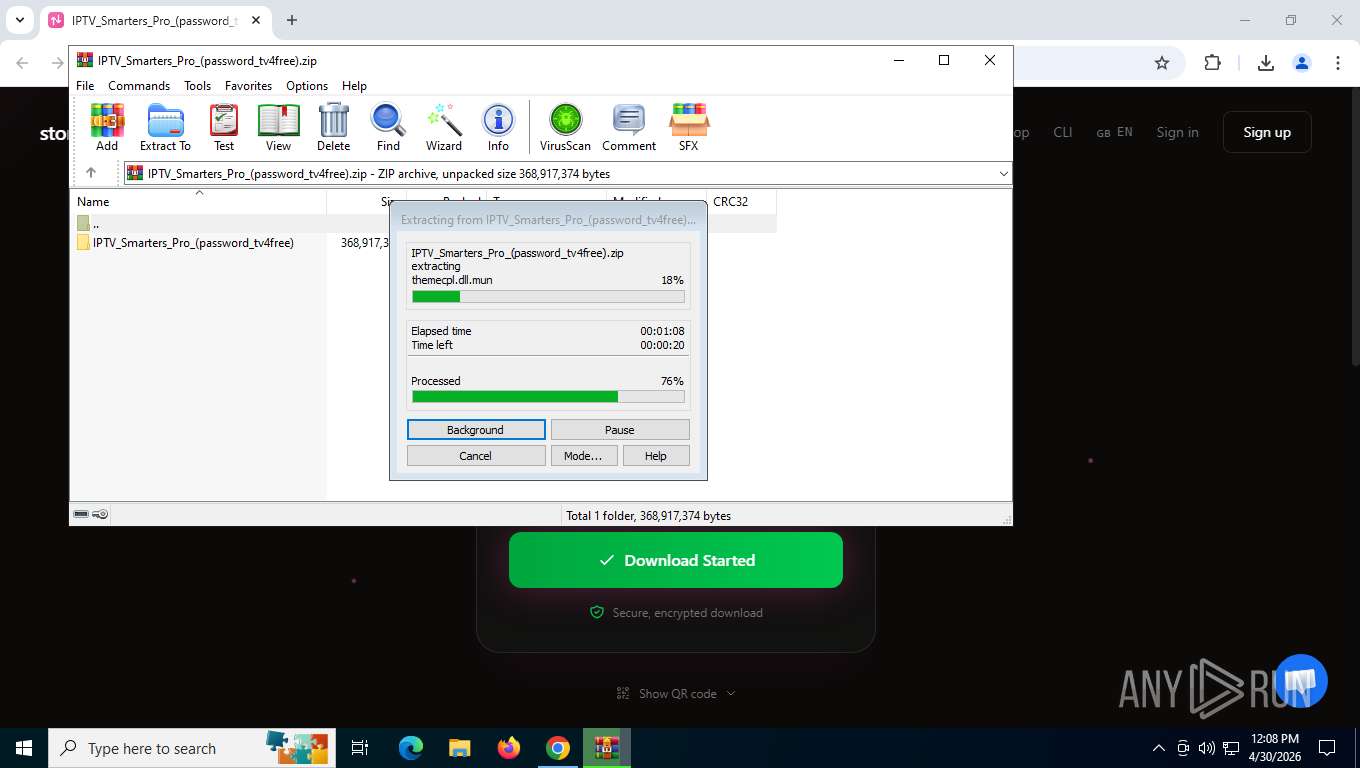
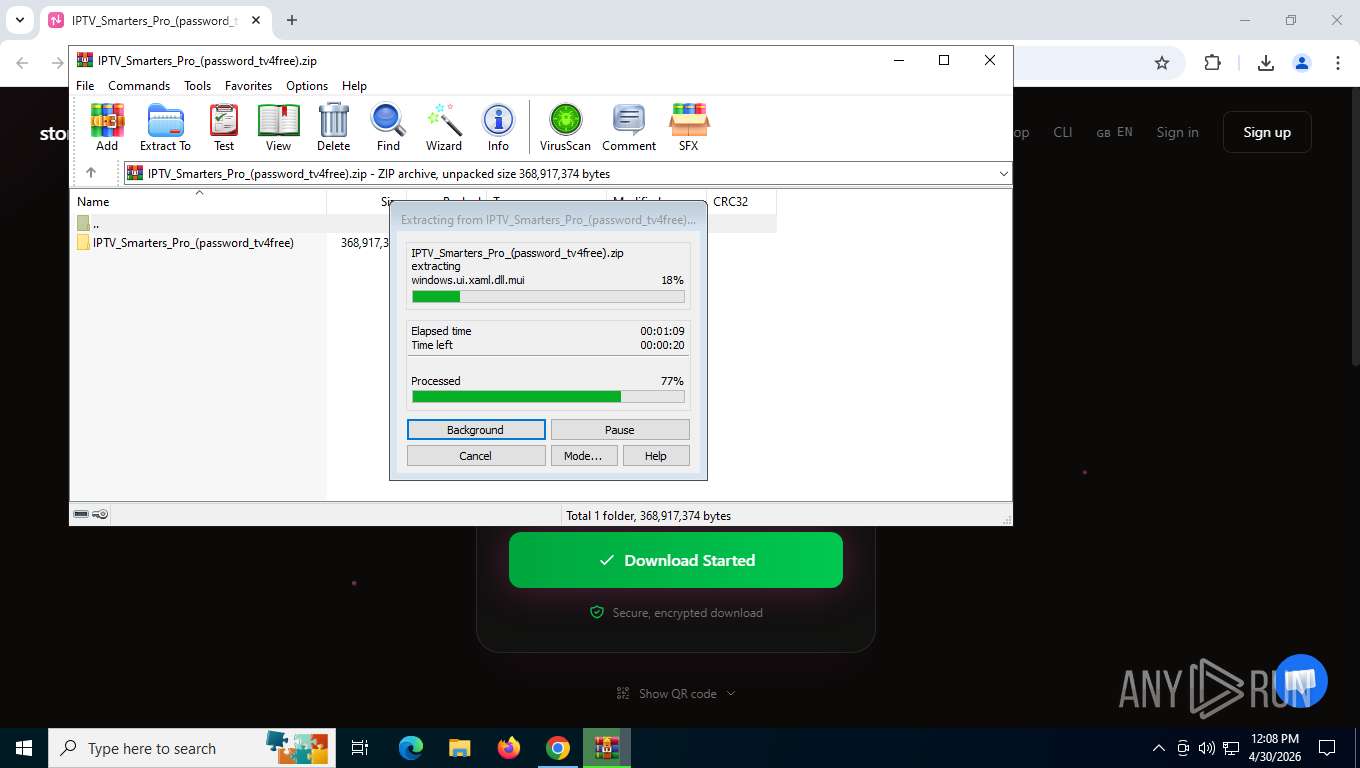
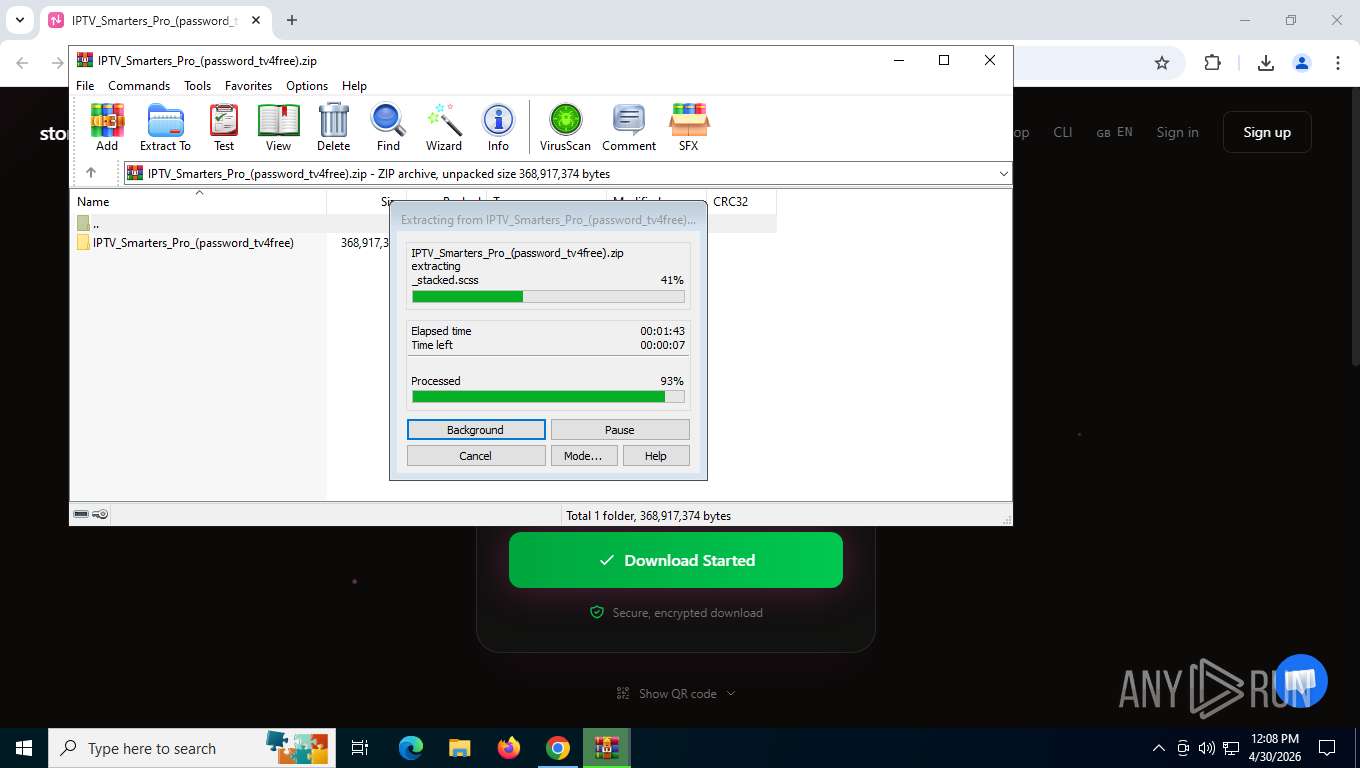
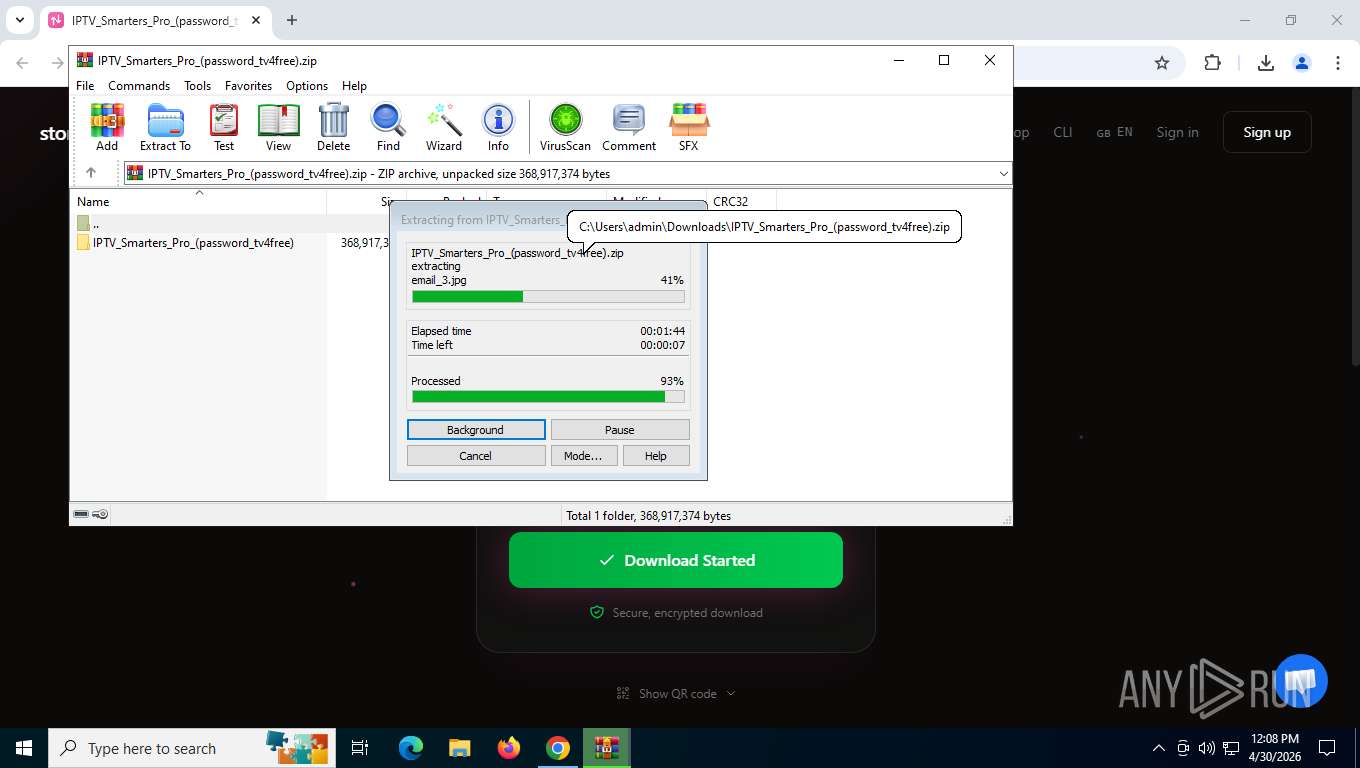
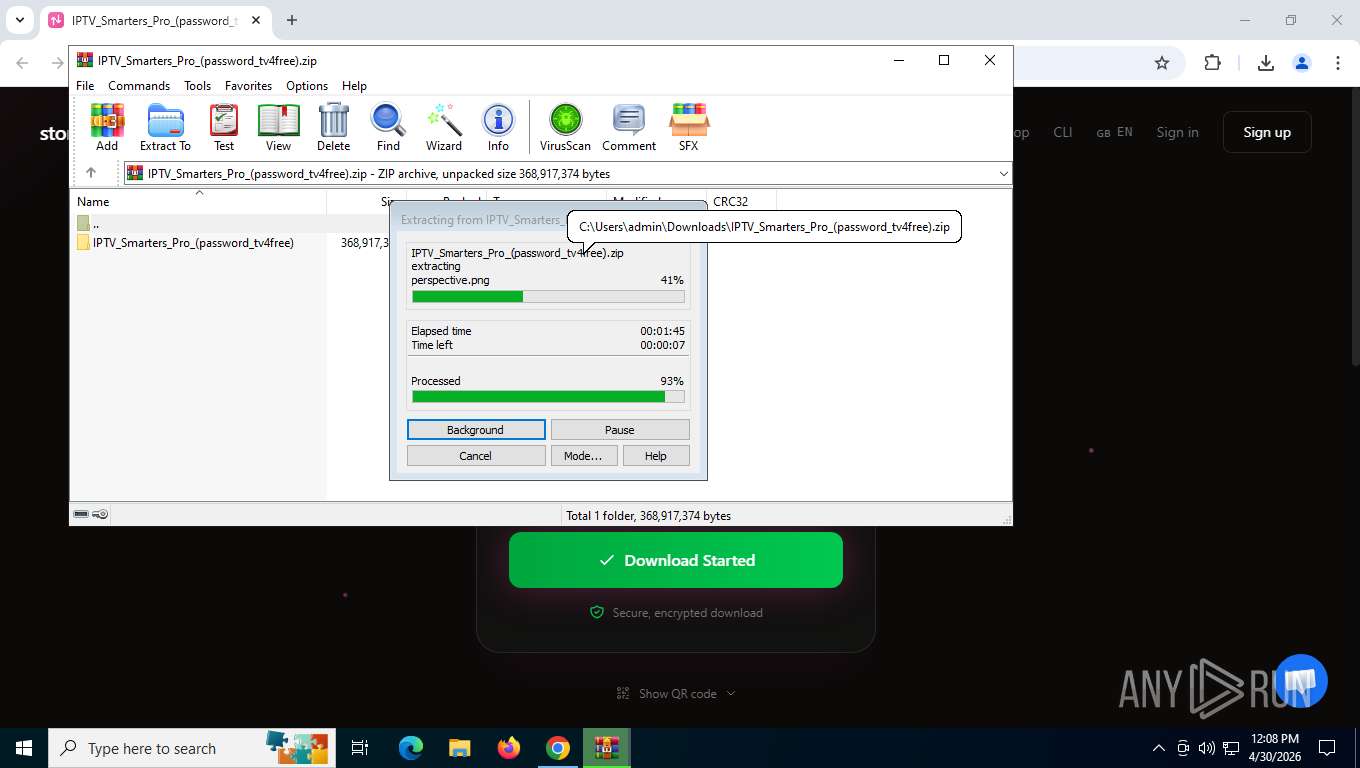
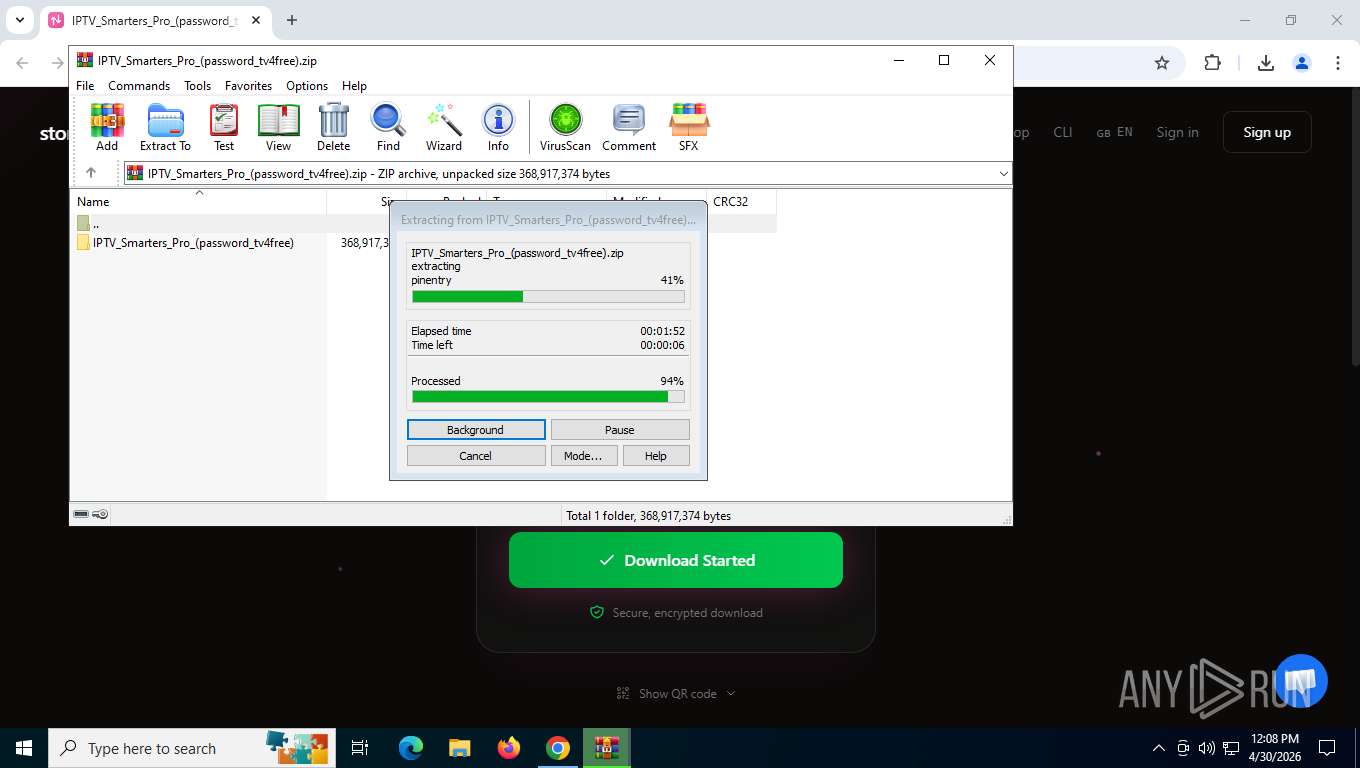
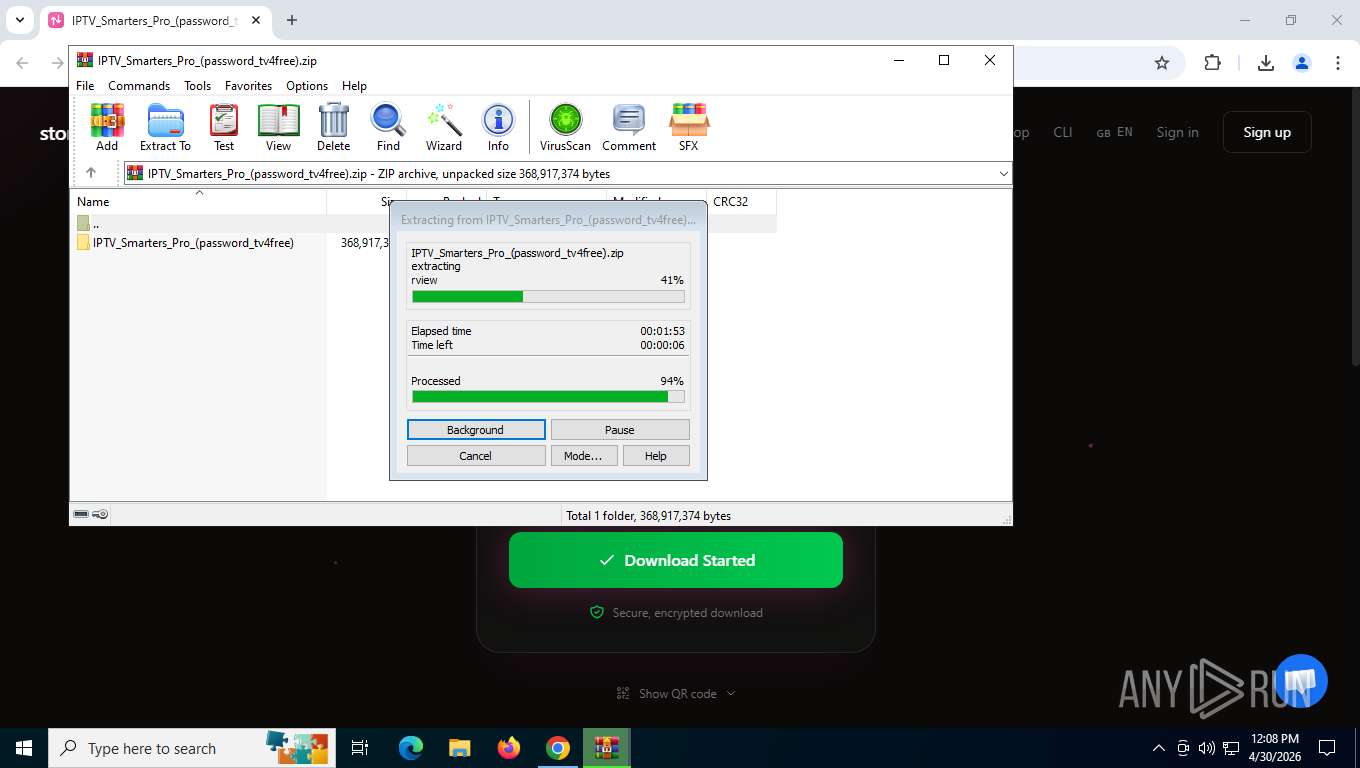
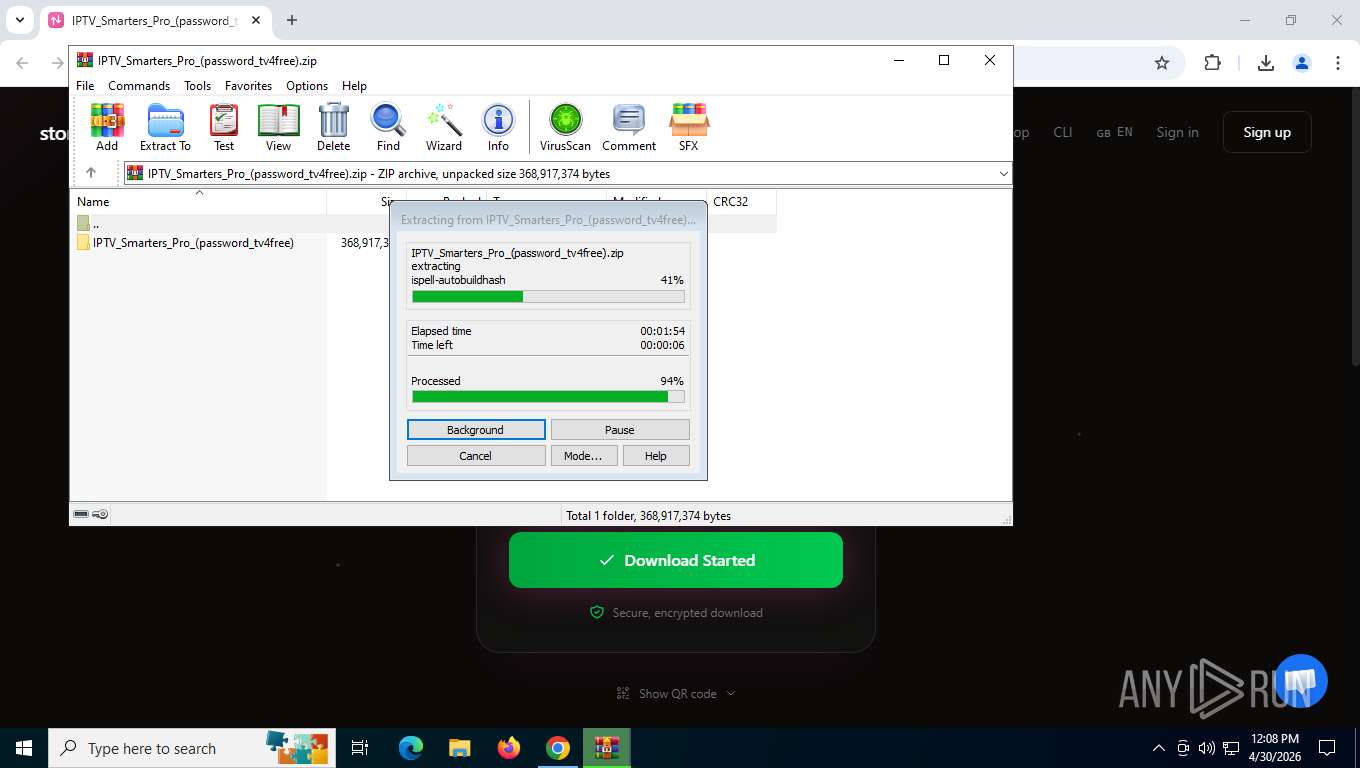
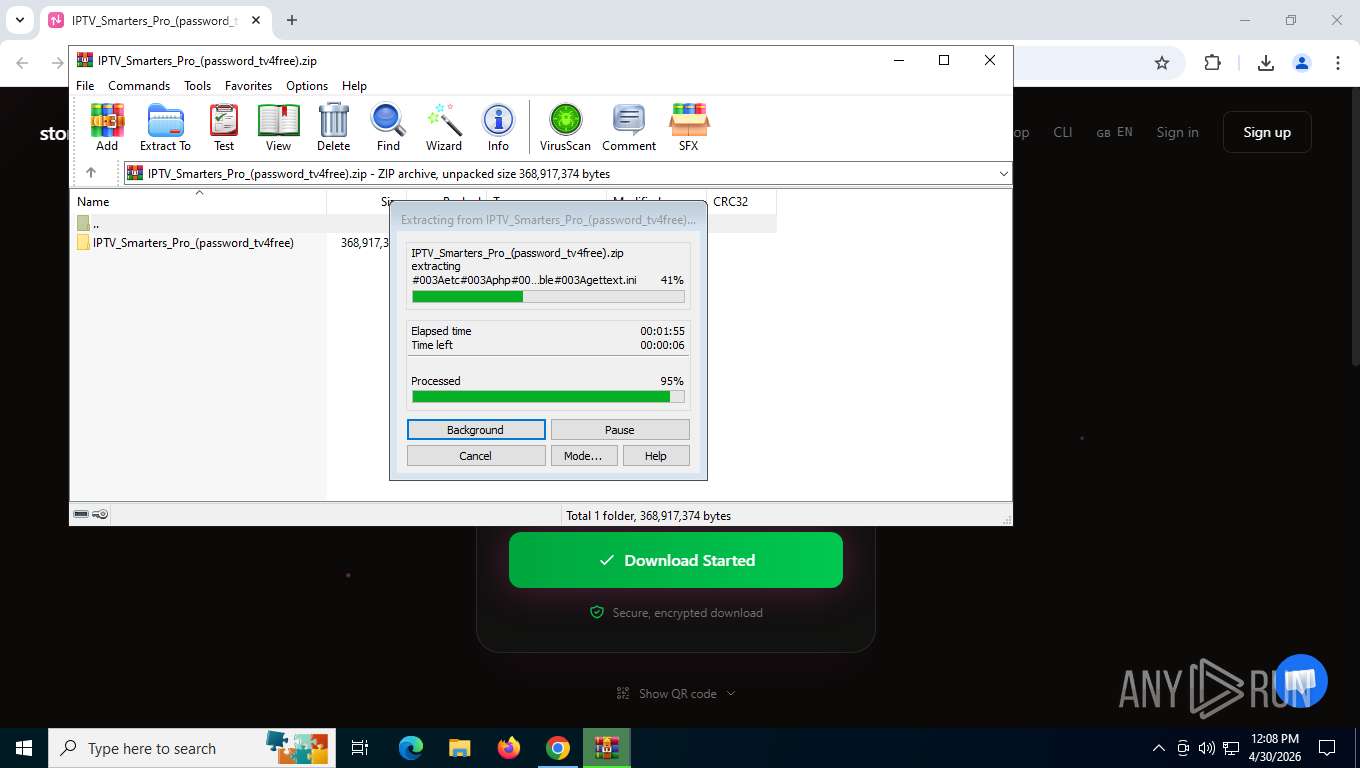
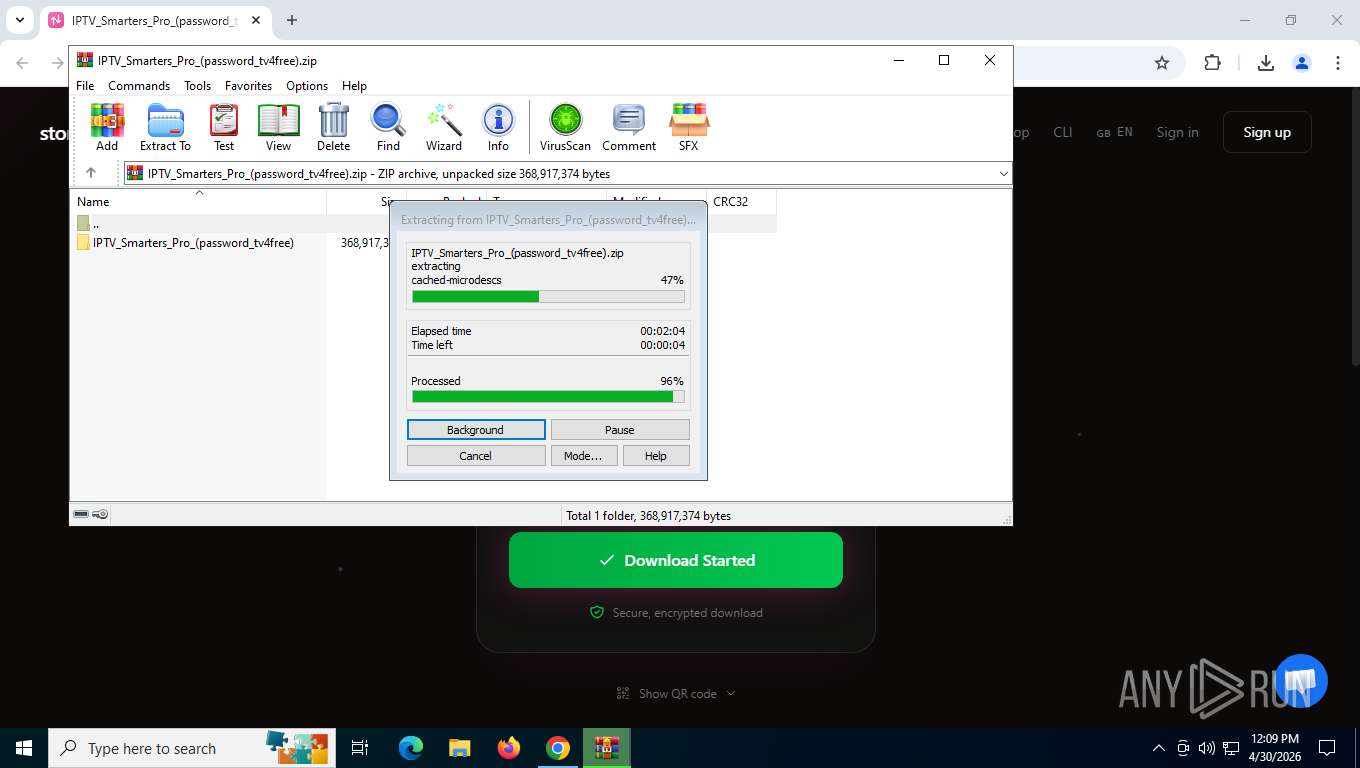
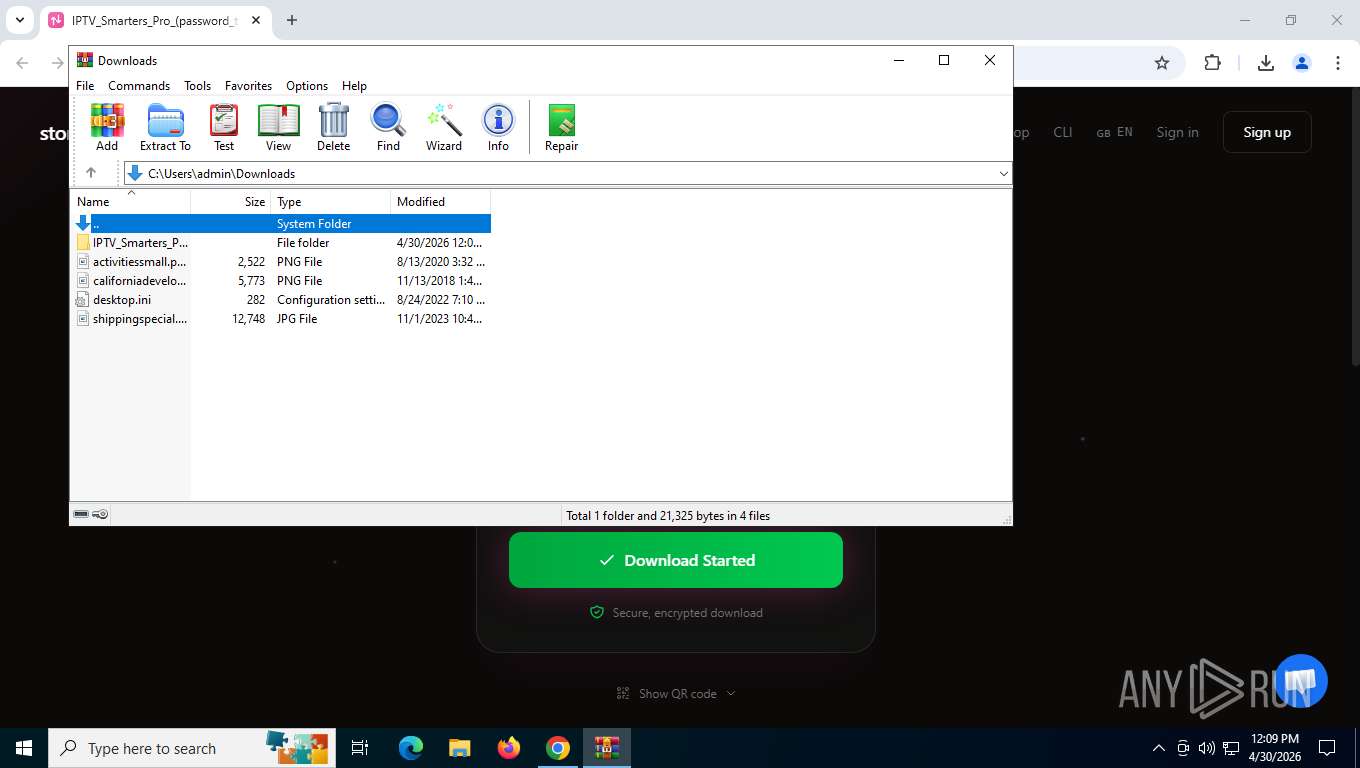
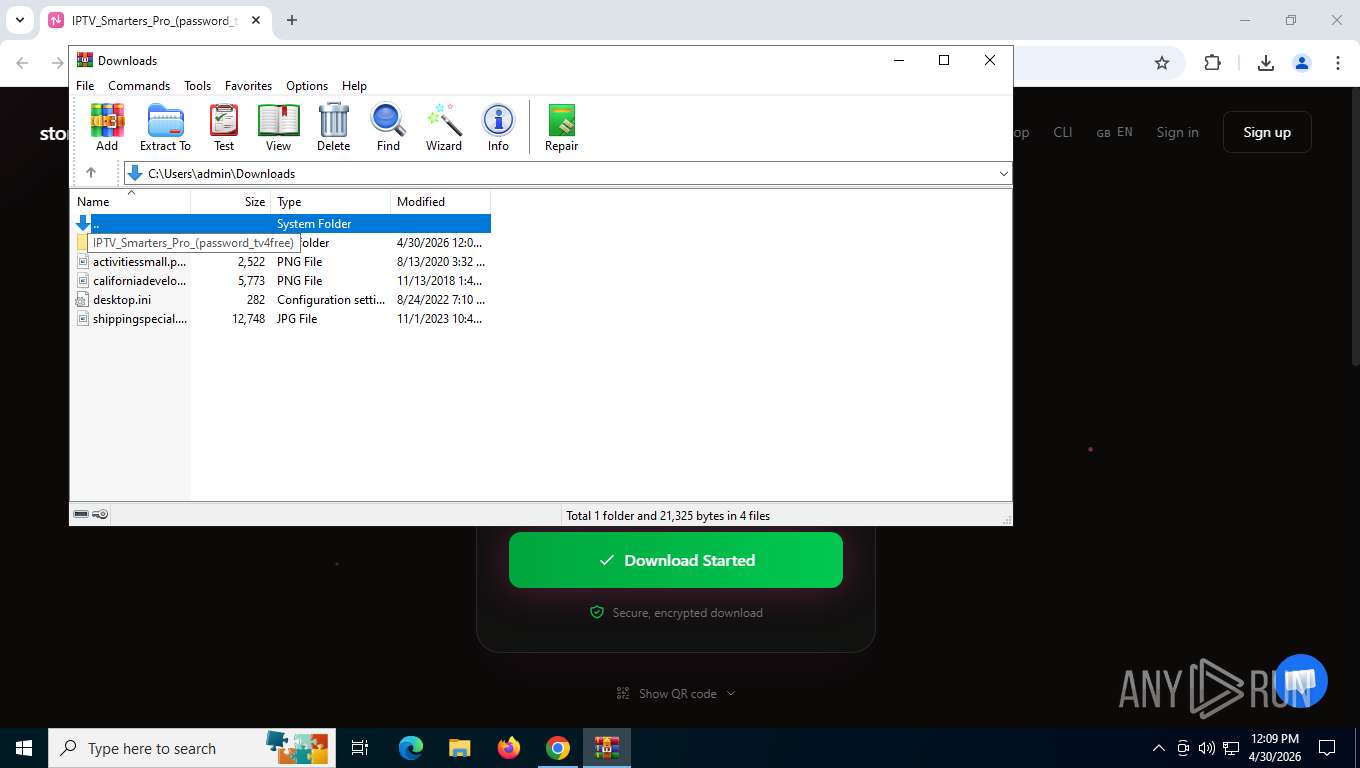
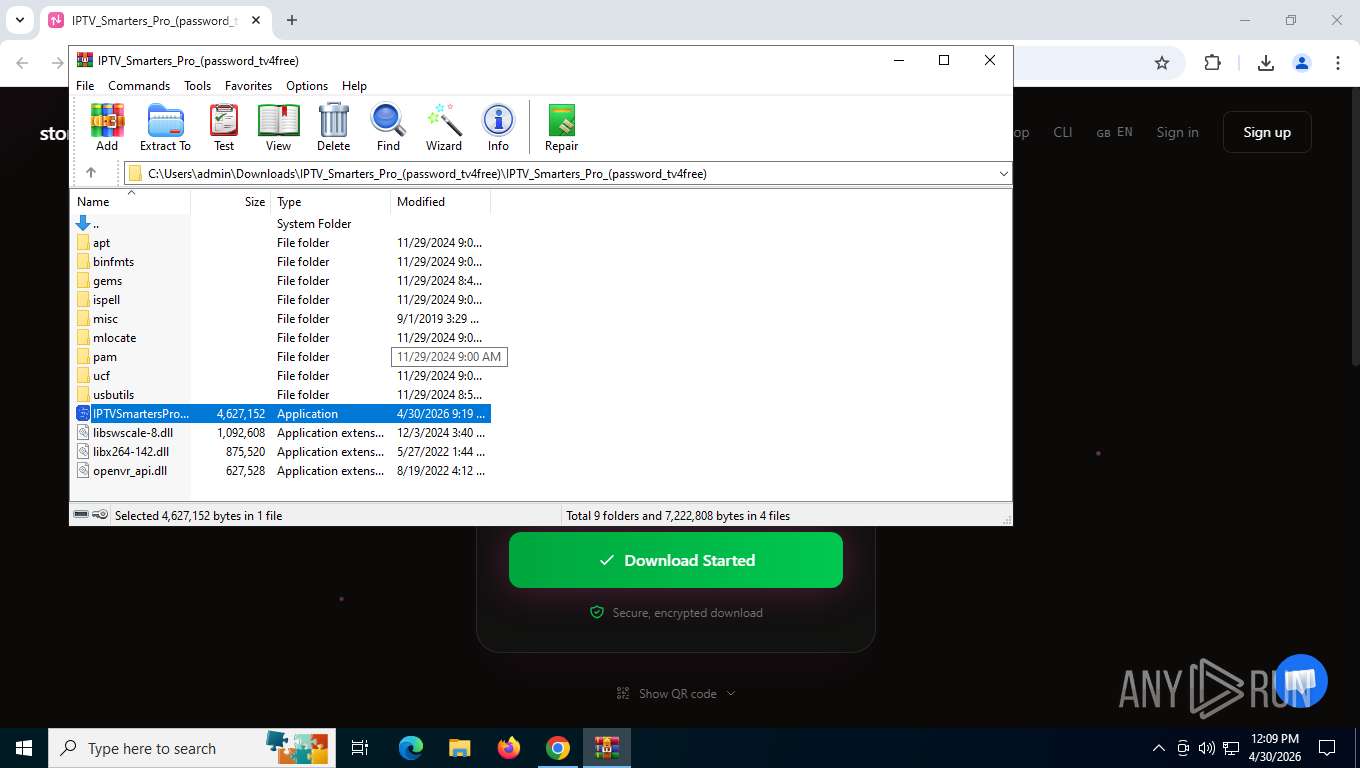
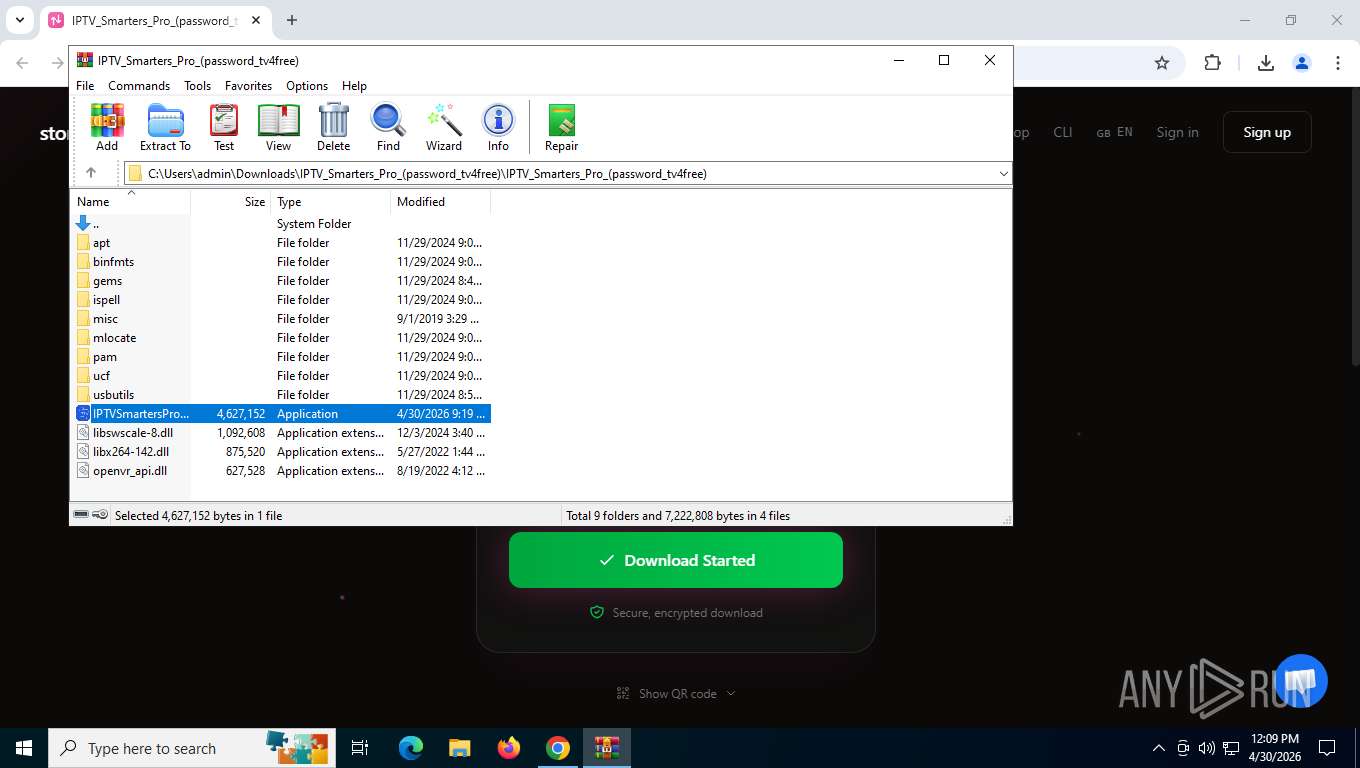
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
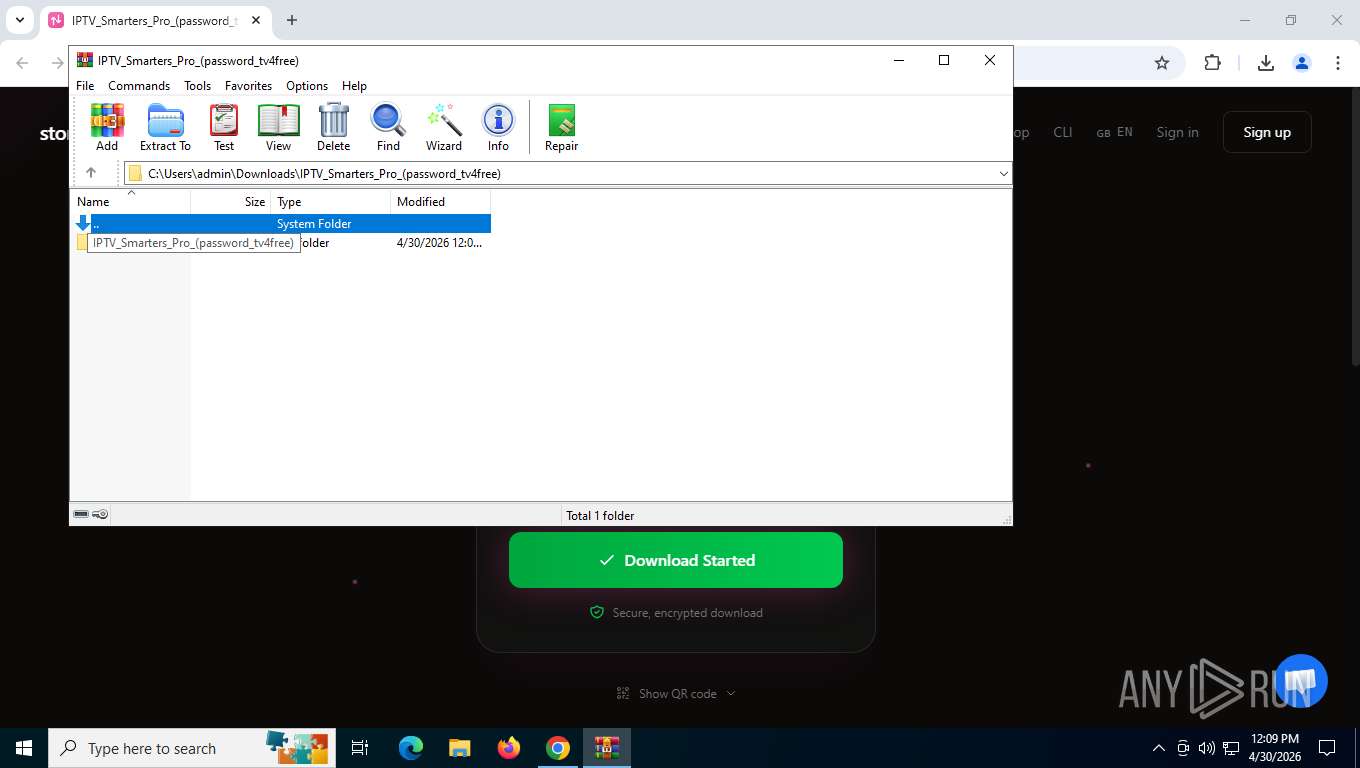
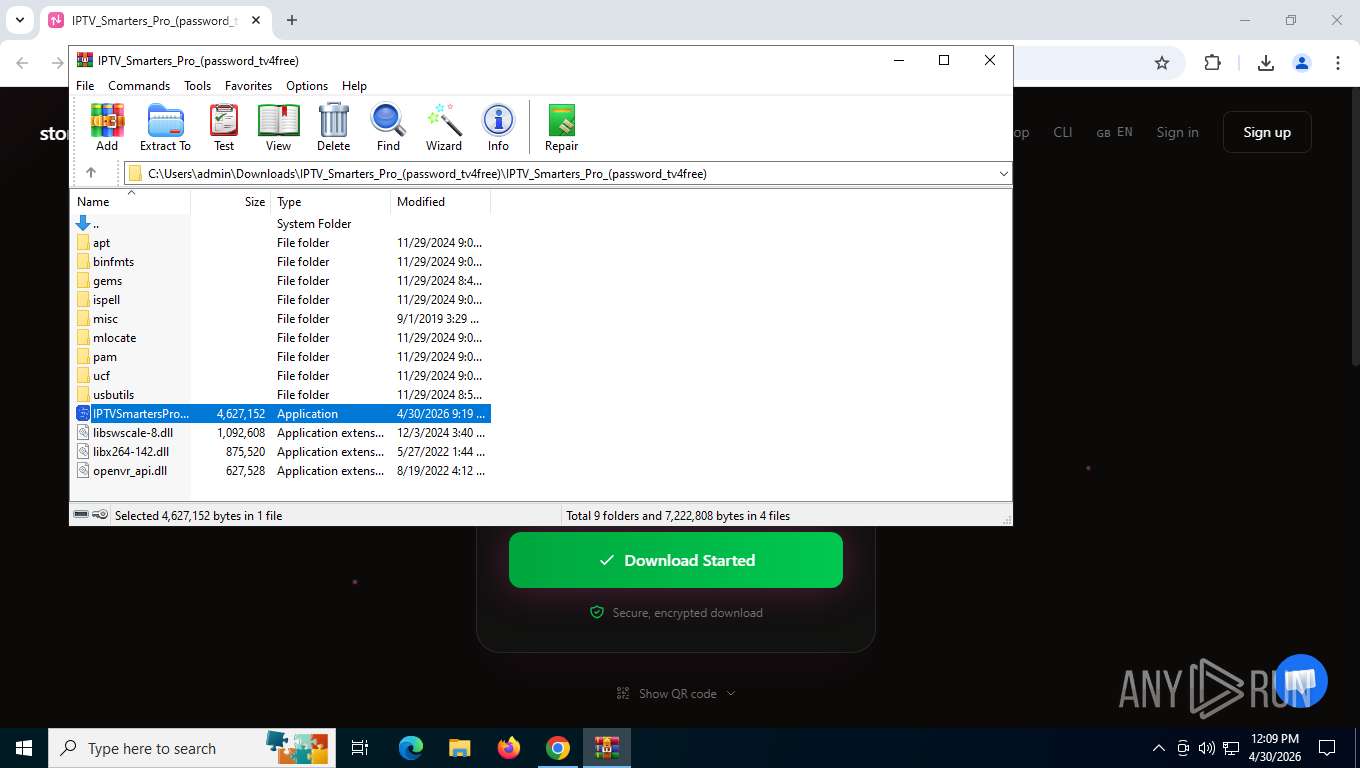
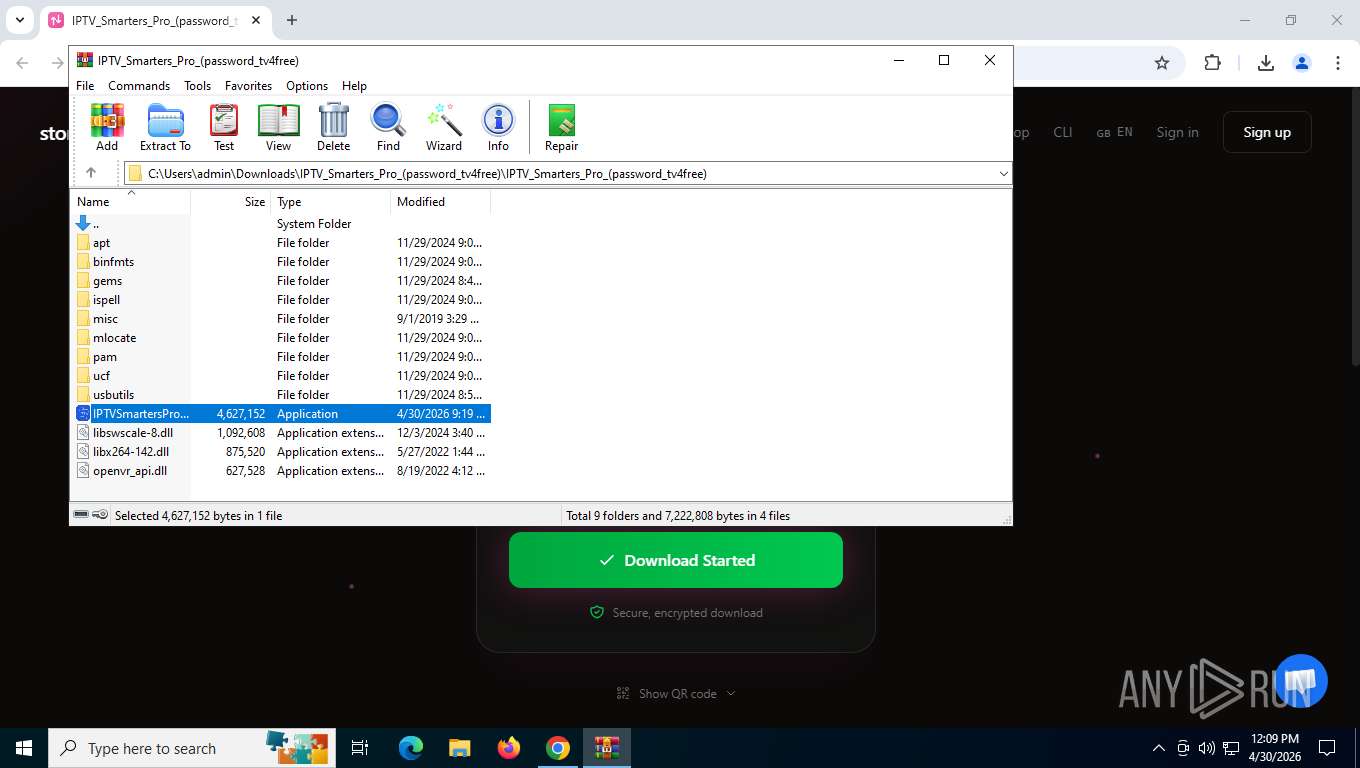
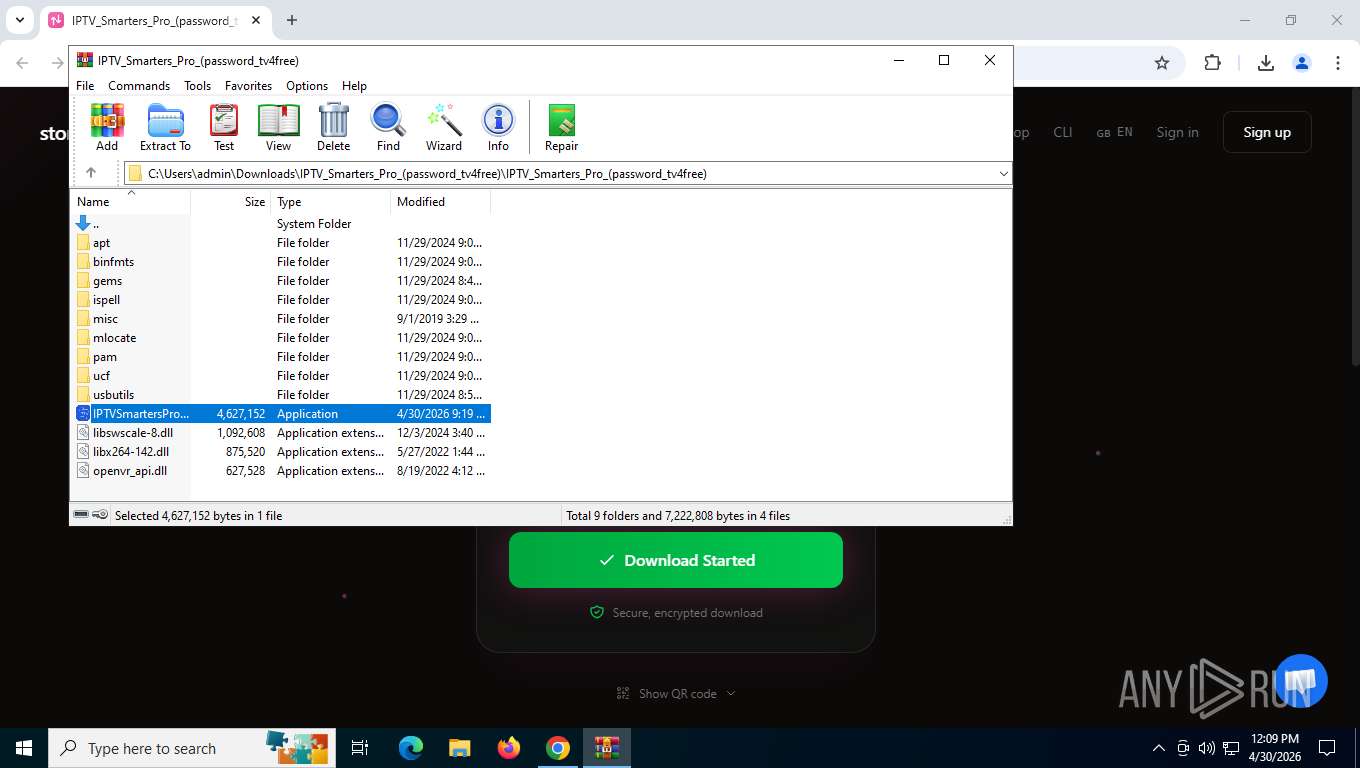
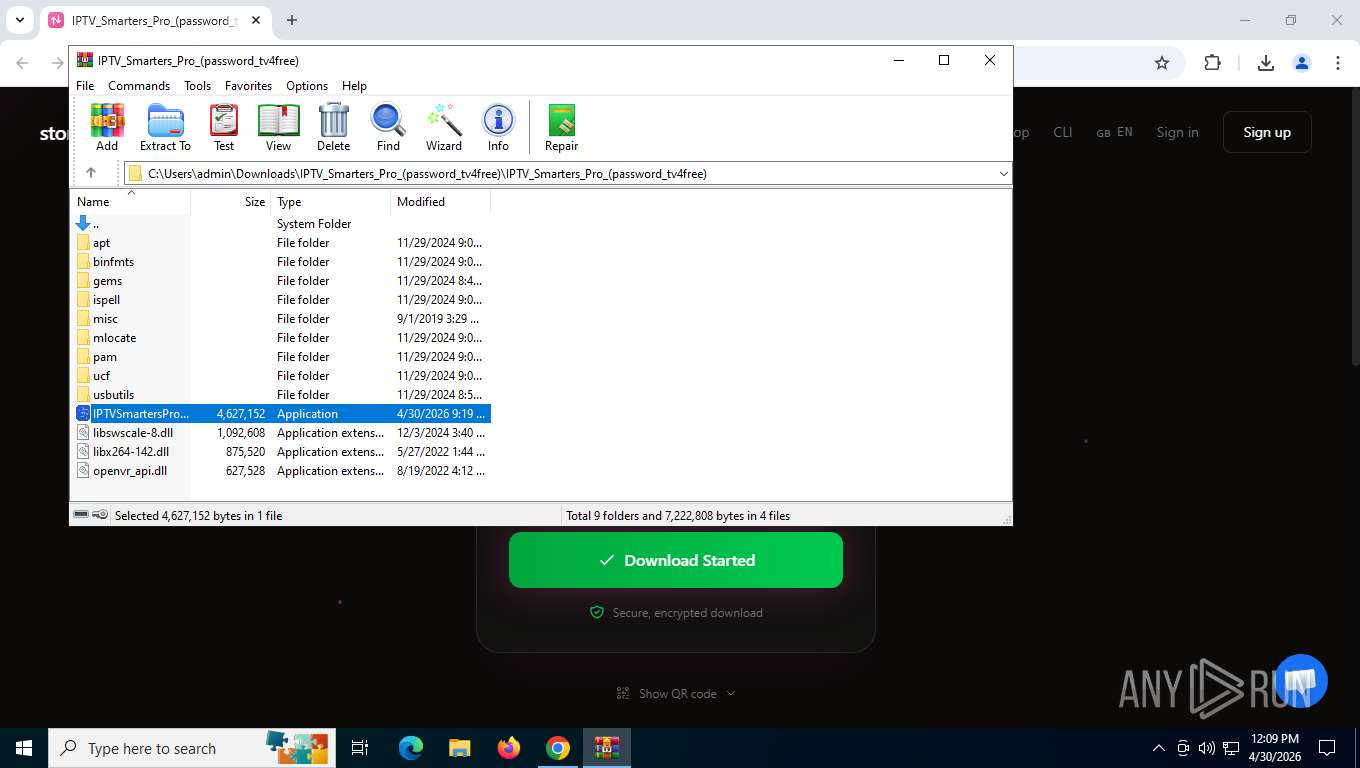
Value: C:\Users\admin\Downloads\IPTV_Smarters_Pro_(password_tv4free).zip | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8184) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
956
Suspicious files
1 031
Text files
641
Unknown types
117
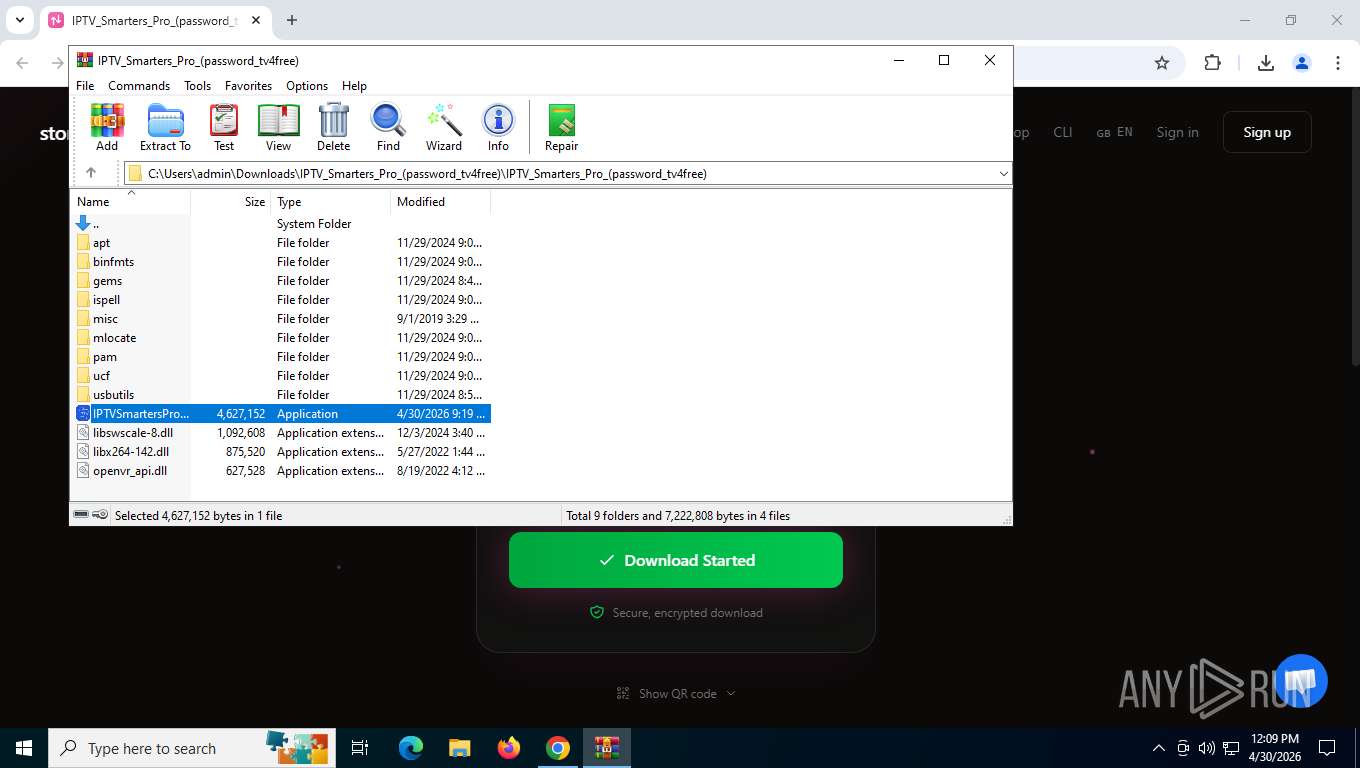
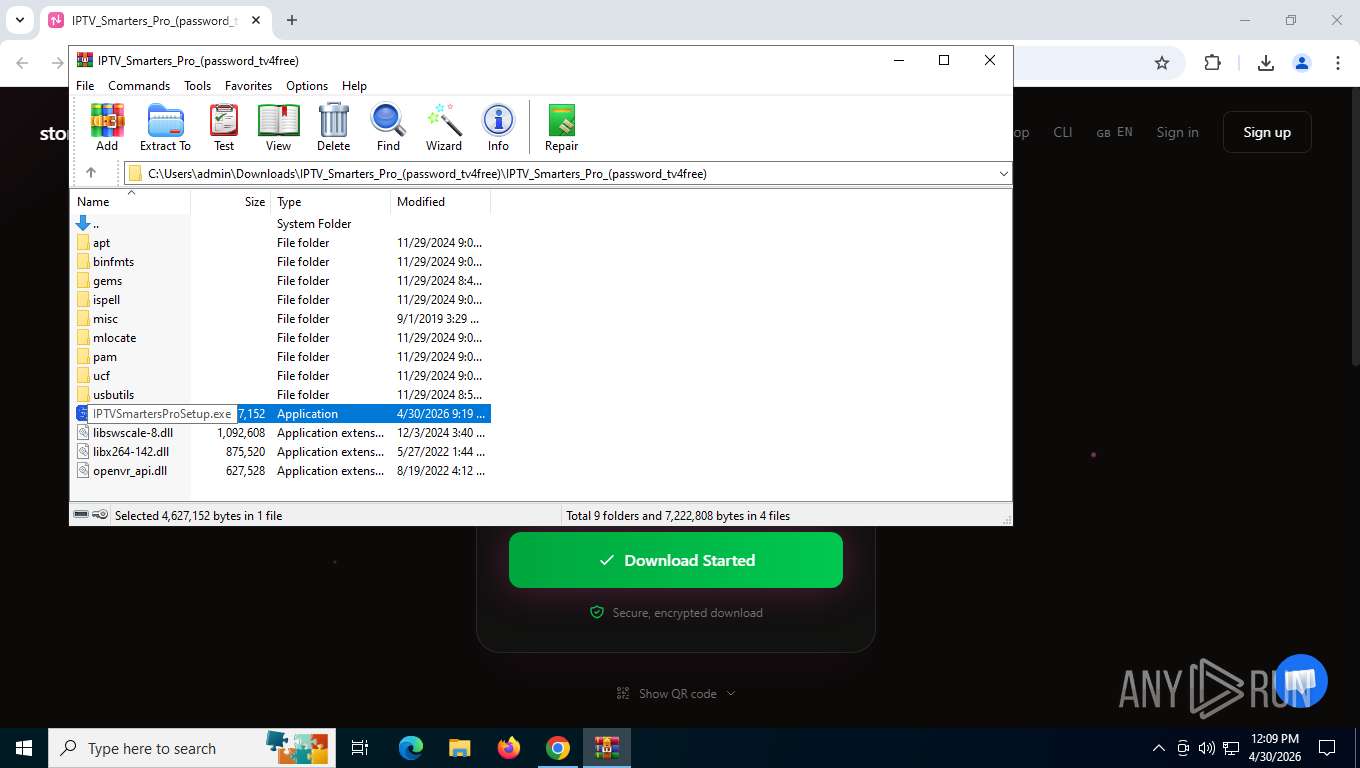
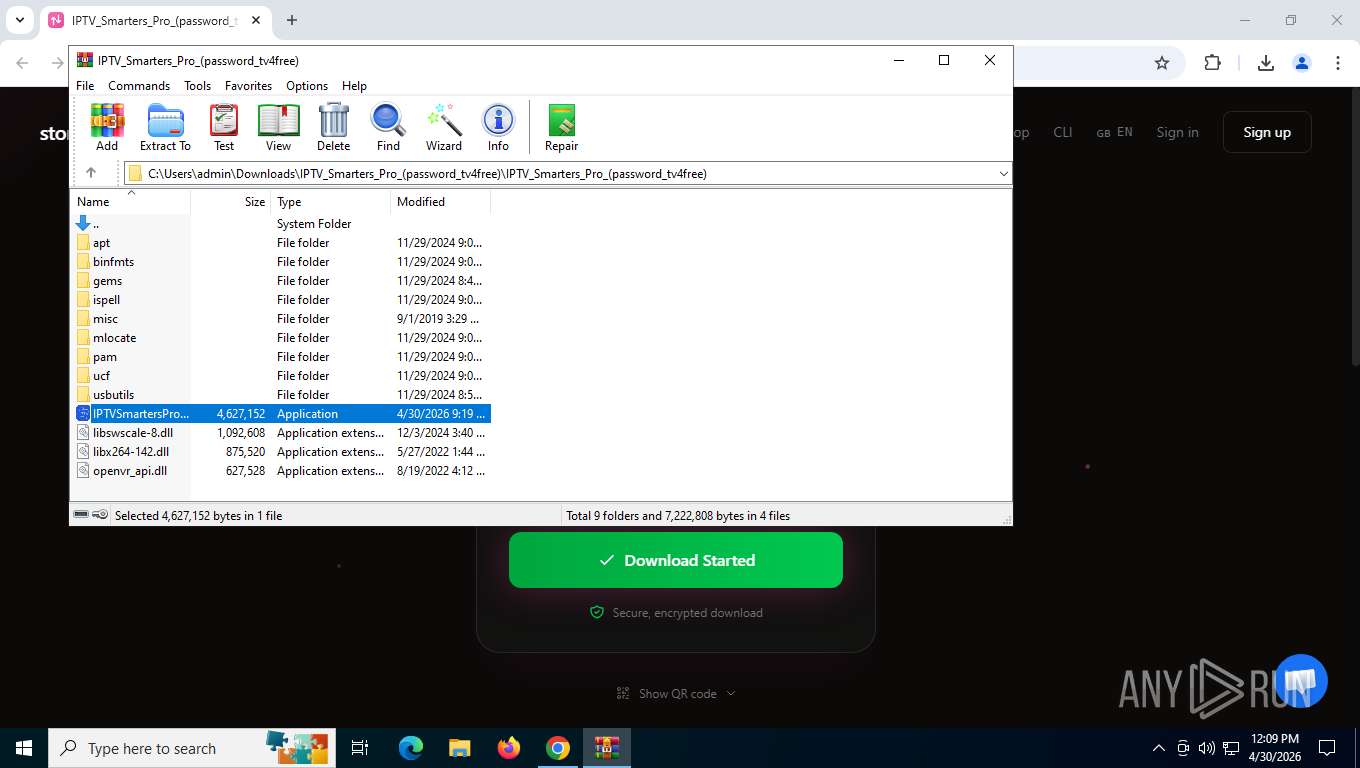
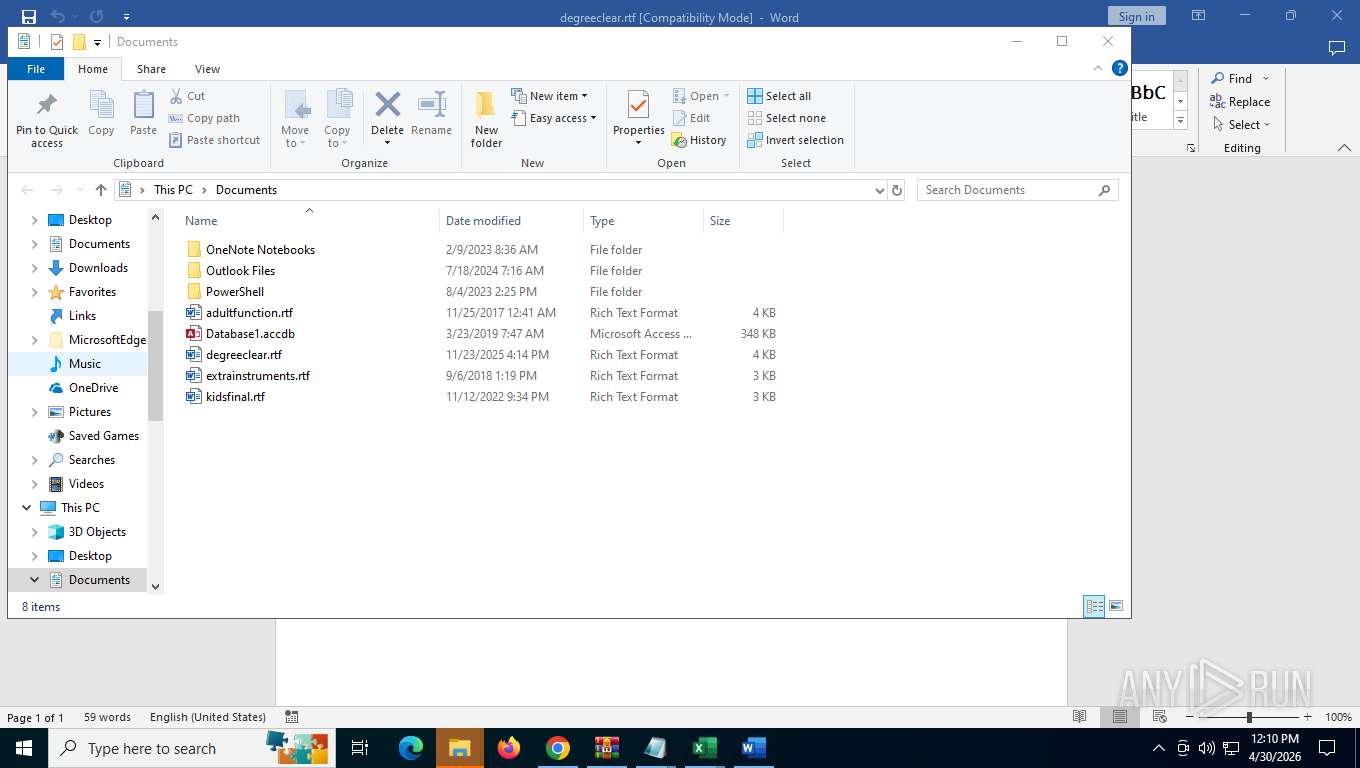
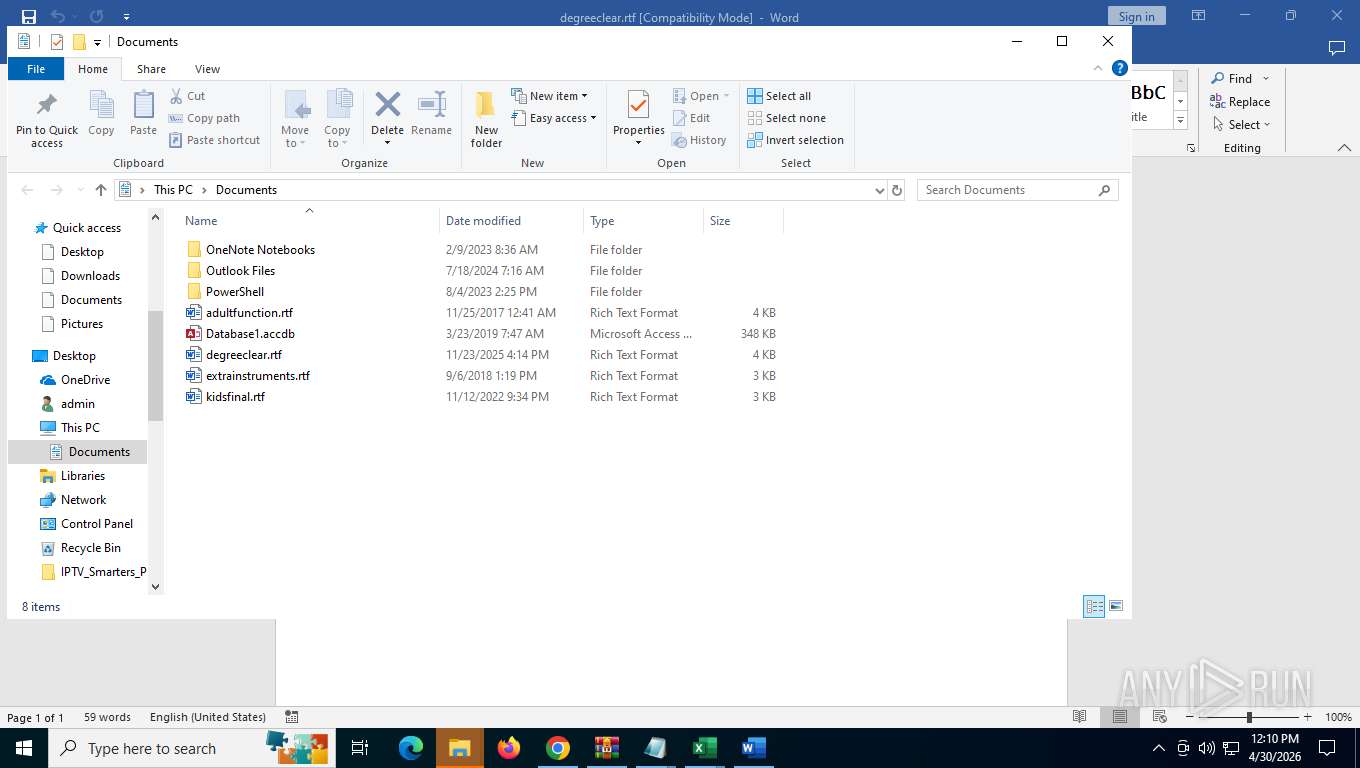
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFdfe36.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFdfe36.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFdfe46.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFdfe46.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdfe56.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFdfe56.TMP | — | |
MD5:— | SHA256:— | |||
| 7776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
191
TCP/UDP connections
132
DNS requests
92
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5920 | chrome.exe | GET | 200 | 142.251.20.97:443 | https://www.googletagmanager.com/gtag/js?id=G-2X4HHTTKKH | US | text | 438 Kb | whitelisted |
5920 | chrome.exe | GET | 200 | 104.26.11.35:443 | https://storage.to/build/assets/app-BHH8rdGj.css | US | text | 1.38 Kb | unknown |
5920 | chrome.exe | POST | 204 | 216.239.32.36:443 | https://region1.google-analytics.com/g/collect?v=2&tid=G-2X4HHTTKKH>m=45je64t0h2v892321847za200zd892321847&_p=1777565153075&gcd=13l3l3l2l1l1&npa=1&dma_cps=a&dma=1&are=1&cid=738810044.1777565153&frm=0&pscdl=noapi&rcb=3&sr=1360x768&uaa=x86&uab=64&uafvl=Not(A%253ABrand%3B99.0.0.0%7CGoogle%2520Chrome%3B133.0.6943.127%7CChromium%3B133.0.6943.127&uam=&uamb=0&uap=Windows&uapv=10.0.0&uaw=0&ul=en-us&_s=1&tag_exp=0~115938465~115938469~116363097~117266400~117512542~117884344~118463261&sid=1777565153&sct=1&seg=0&dl=https%3A%2F%2Fstorage.to%2FHsjBmShpR&dt=IPTV_Smarters_Pro_(password_tv4free).zip%20-%20storage.to&en=page_view&_fv=1&_nsi=1&_ss=1&_ee=1&tfd=888 | US | — | — | whitelisted |
5920 | chrome.exe | GET | 200 | 104.26.11.35:443 | https://storage.to/build/assets/app-DKpdJGZQ.js | US | text | 186 Kb | unknown |
5920 | chrome.exe | GET | 200 | 142.251.13.113:80 | http://clients2.google.com/time/1/current?cup2key=8:58zAr7Ky40woigrjCzPpyOsHkGEIV8oTHdmubXOETYk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 107 b | whitelisted |
5920 | chrome.exe | POST | 204 | 104.26.11.35:443 | https://storage.to/cdn-cgi/rum? | US | — | — | unknown |
5920 | chrome.exe | GET | 200 | 104.26.11.35:443 | https://storage.to/build/assets/module.esm-B2nUsvHo.js | US | text | 44.2 Kb | unknown |
5920 | chrome.exe | GET | 200 | 104.26.11.35:443 | https://storage.to/favicon/favicon-96x96.png | US | image | 10.2 Kb | unknown |
5920 | chrome.exe | GET | 200 | 104.26.11.35:443 | https://storage.to/favicon/favicon.ico | US | image | 14.7 Kb | unknown |
5920 | chrome.exe | GET | 101 | 64.227.36.222:443 | https://client.relay.crisp.chat/w/45f/?EIO=4&transport=websocket | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8140 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5920 | chrome.exe | 142.251.13.113:80 | clients2.google.com | GOOGLE | US | whitelisted |
5920 | chrome.exe | 142.250.154.95:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5920 | chrome.exe | 142.251.14.101:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
5920 | chrome.exe | 104.26.11.35:443 | storage.to | CLOUDFLARENET | US | whitelisted |
5920 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
storage.to |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
client.crisp.chat |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5920 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5920 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5920 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5920 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
8140 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5920 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|