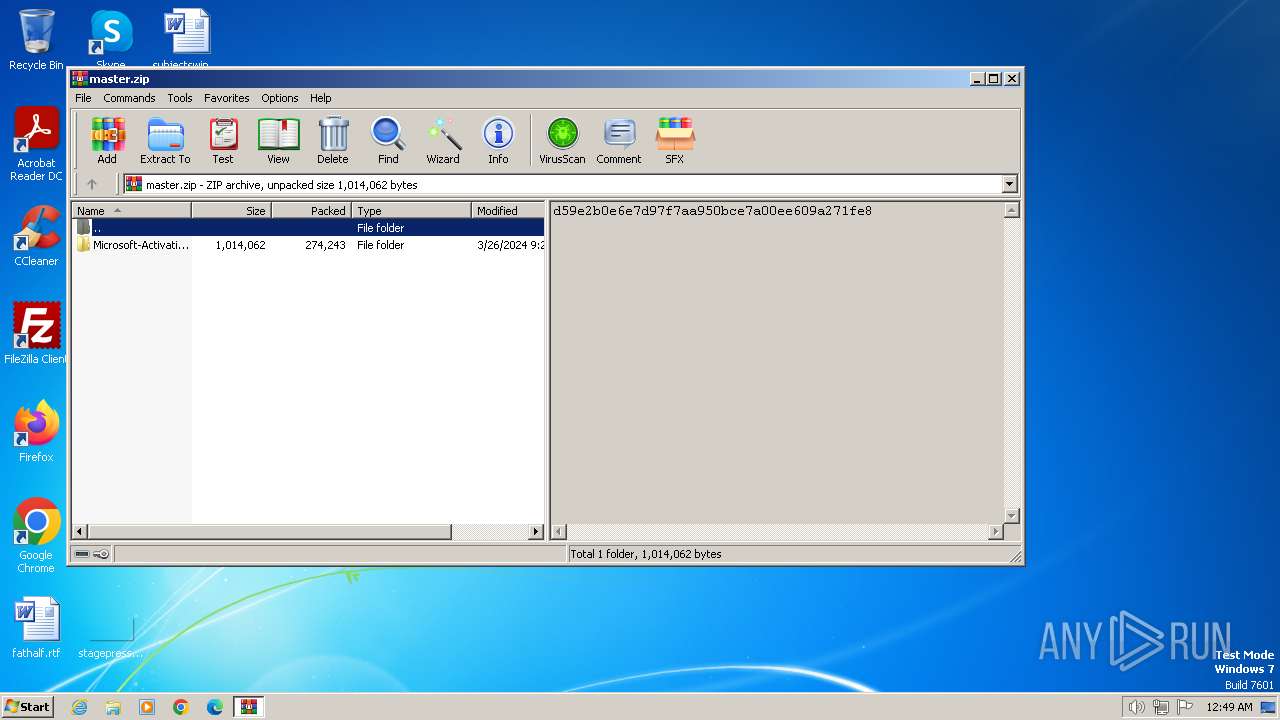
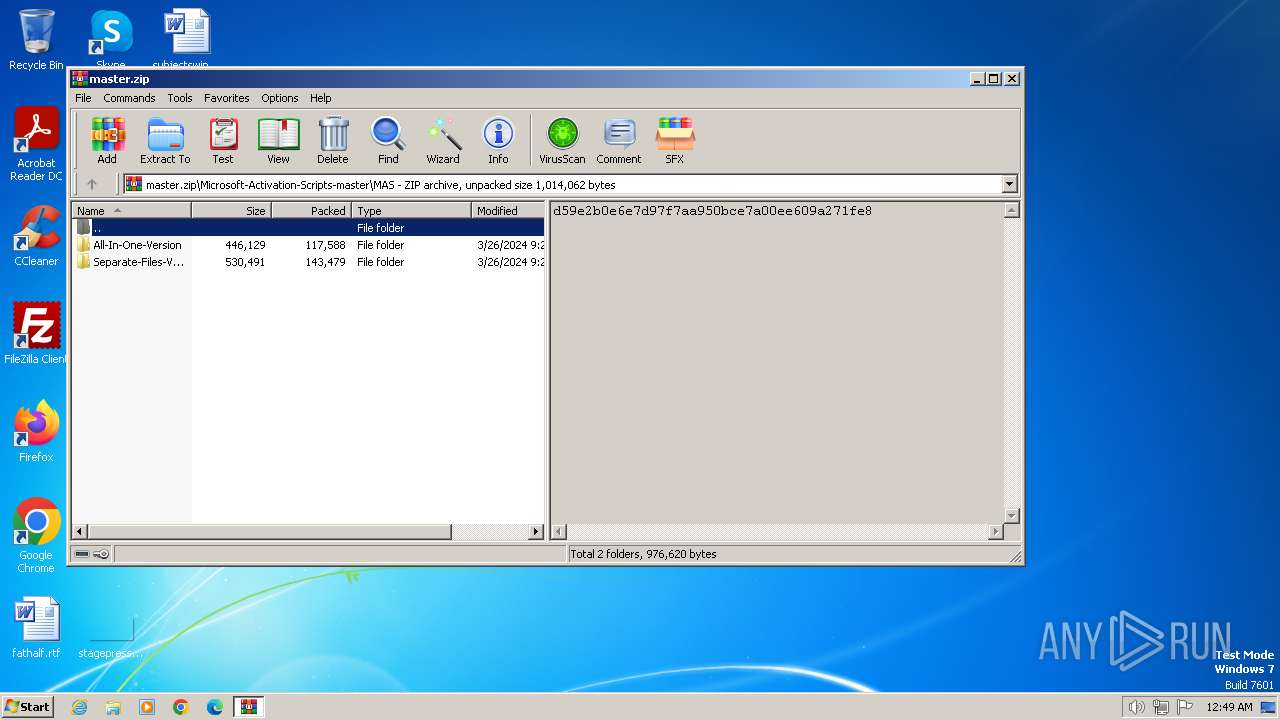
| download: | /massgravel/Microsoft-Activation-Scripts/archive/refs/heads/master.zip |
| Full analysis: | https://app.any.run/tasks/ff918050-6511-431d-a4e5-d6ea0a7151e7 |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2024, 23:49:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 2884D68734CEA34F329A4A1BC0975AD1 |
| SHA1: | 291086E7B7EF47DDE5B32995751F1C8865A3C103 |
| SHA256: | 4556DC4E916D98AAD9EF66B47F81E81F15A974352A6D3A92CA19750954235550 |
| SSDEEP: | 6144:saT2t2LanGAs/yOhrraJi8FPxKGwDeXh8Qu9G+cJUNQx2pqgg3o2Vz:saK4LaGAs/kjZhwDeX9t+cJUuxwg4Iz |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2336)
- net.exe (PID: 2424)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3936)
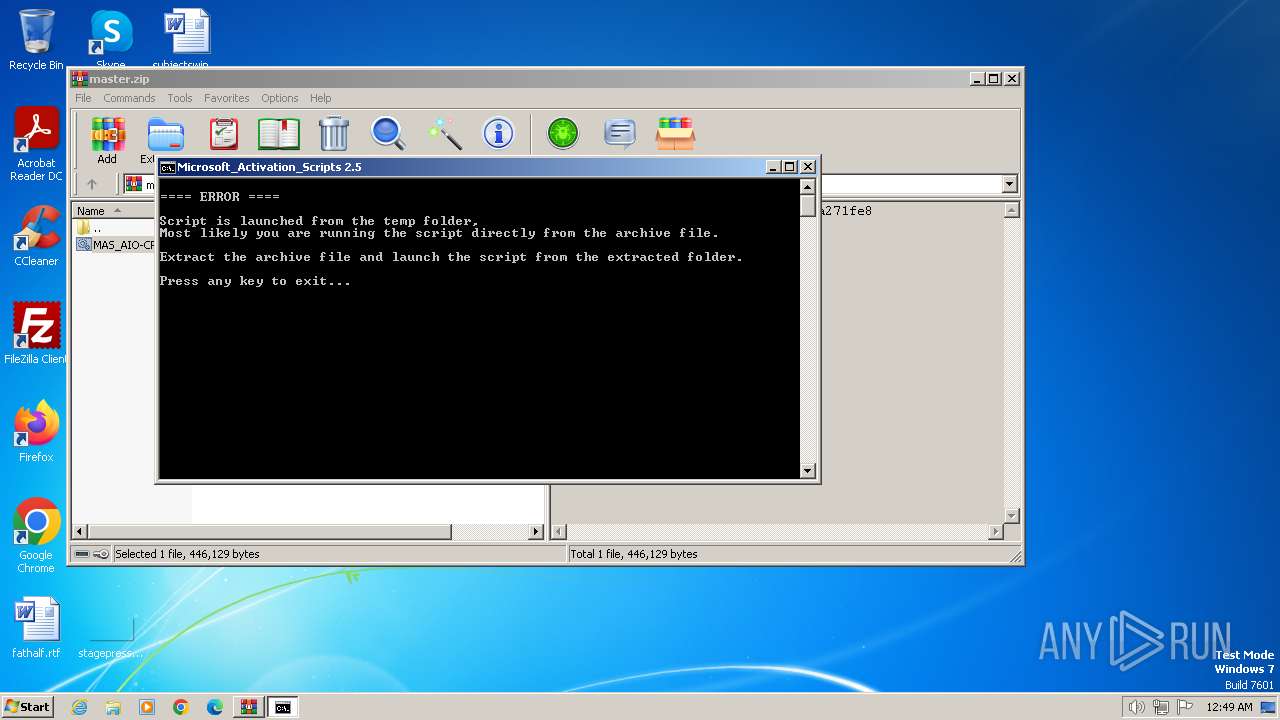
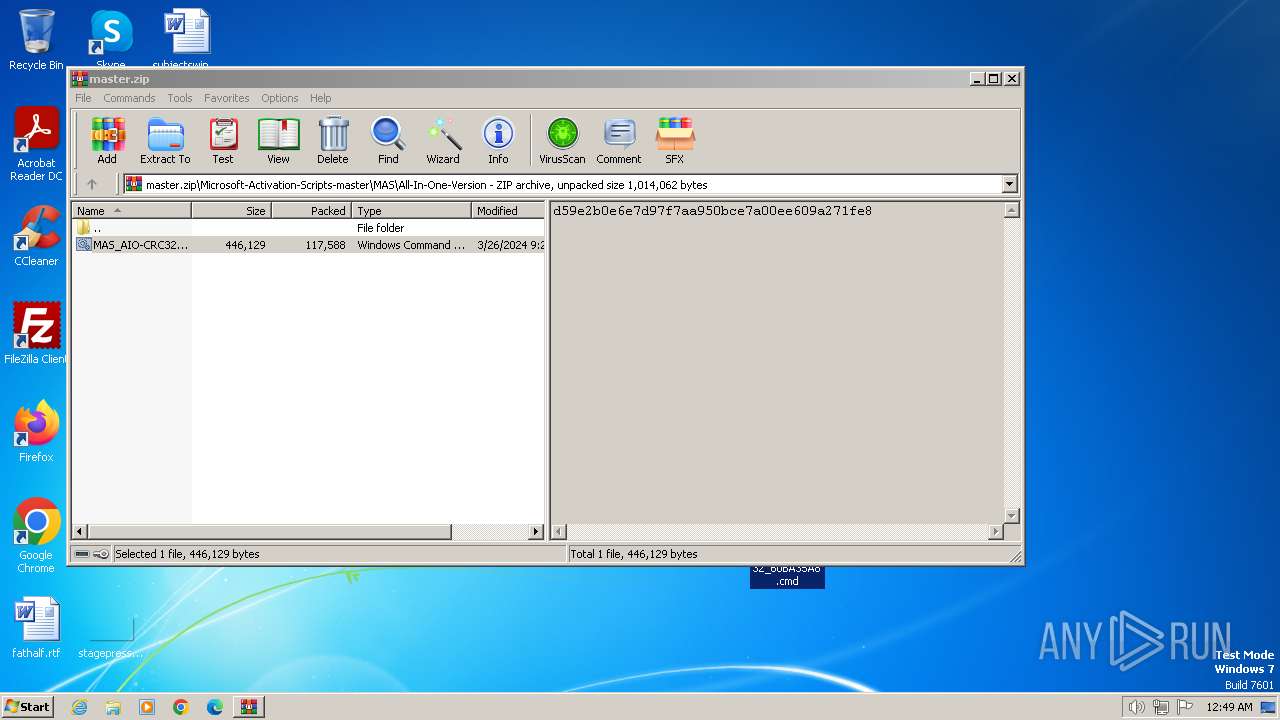
Executing commands from ".cmd" file
- WinRAR.exe (PID: 3936)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2168)
- powershell.exe (PID: 2564)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2232)
- WinRAR.exe (PID: 3936)
- cmd.exe (PID: 2168)
- powershell.exe (PID: 2564)
- cmd.exe (PID: 2336)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2168)
Application launched itself
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2168)
- cmd.exe (PID: 2336)
Starts SC.EXE for service management
- cmd.exe (PID: 2168)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2336)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2336)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2168)
- cmd.exe (PID: 2336)
Reads the Internet Settings
- powershell.exe (PID: 2564)
- WMIC.exe (PID: 3336)
- WMIC.exe (PID: 3600)
- WMIC.exe (PID: 1928)
- WMIC.exe (PID: 3444)
- WMIC.exe (PID: 2060)
- WMIC.exe (PID: 712)
- WMIC.exe (PID: 3088)
- WMIC.exe (PID: 3616)
- WMIC.exe (PID: 552)
- WMIC.exe (PID: 3036)
Starts NET.EXE to map network drives
- cmd.exe (PID: 2336)
Hides command output
- cmd.exe (PID: 4056)
- cmd.exe (PID: 748)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 796)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 1644)
- cmd.exe (PID: 240)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2336)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 2404)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2744)
INFO
Checks operating system version
- cmd.exe (PID: 2232)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2168)
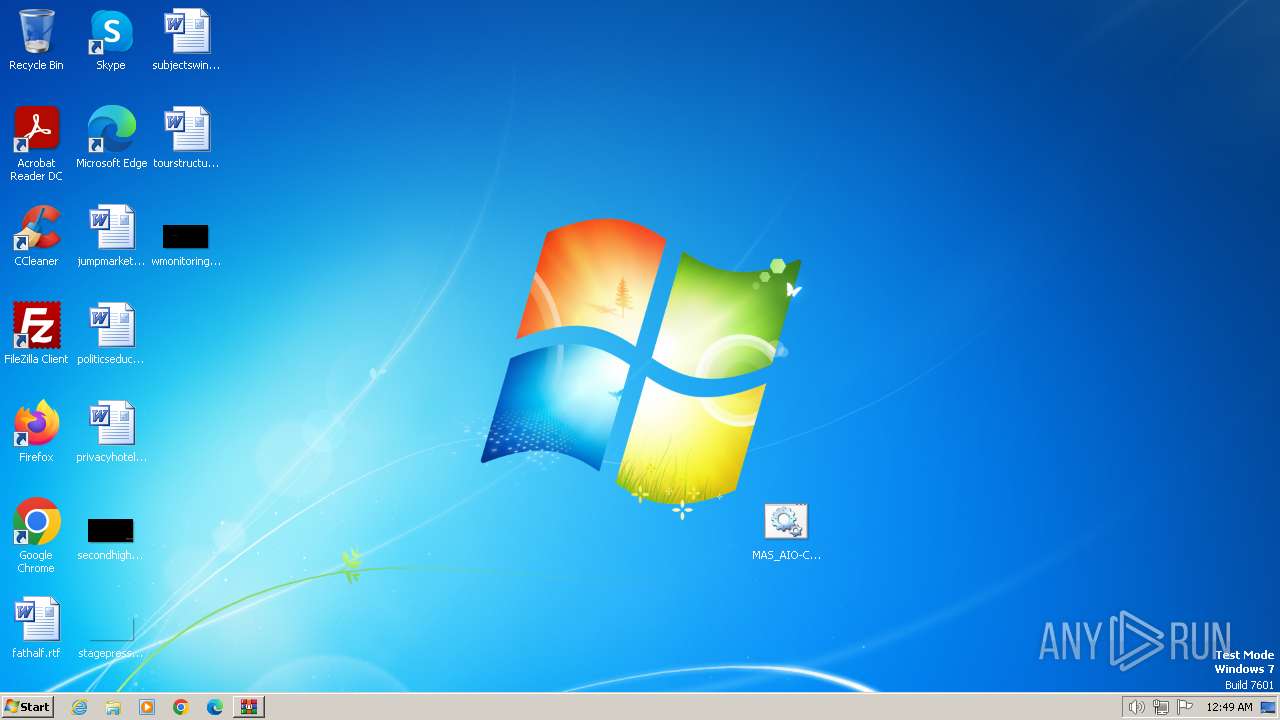
Manual execution by a user
- cmd.exe (PID: 2168)
Checks supported languages
- mode.com (PID: 3504)
- mode.com (PID: 3236)
- mode.com (PID: 3880)
Reads Microsoft Office registry keys
- reg.exe (PID: 2892)
- reg.exe (PID: 2420)
- reg.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:03:26 14:27:28 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Microsoft-Activation-Scripts-master/ |
Total processes
217
Monitored processes
172
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v DisableKeyManagementServiceHostCaching | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | C:\Windows\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\15.0\Common\InstallRoot /v Path" 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 268 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v KeyManagementServiceName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and LicenseStatus='1' ) get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform" /f /v DisableDnsPublishing | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 668 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and Description like '%KMSCLIENT%' ) get ID /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 592
Read events
13 542
Write events
32
Delete events
18
Modification events
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\master.zip | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
1
Text files
5
Unknown types
5
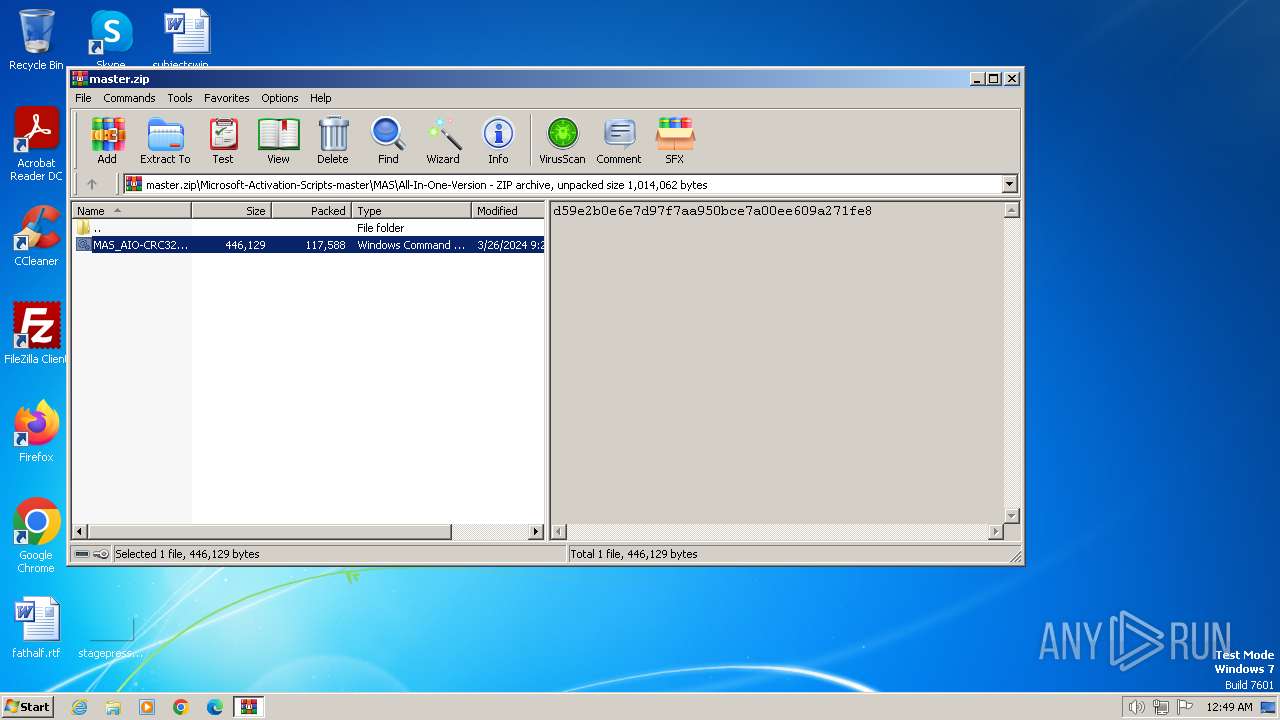
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
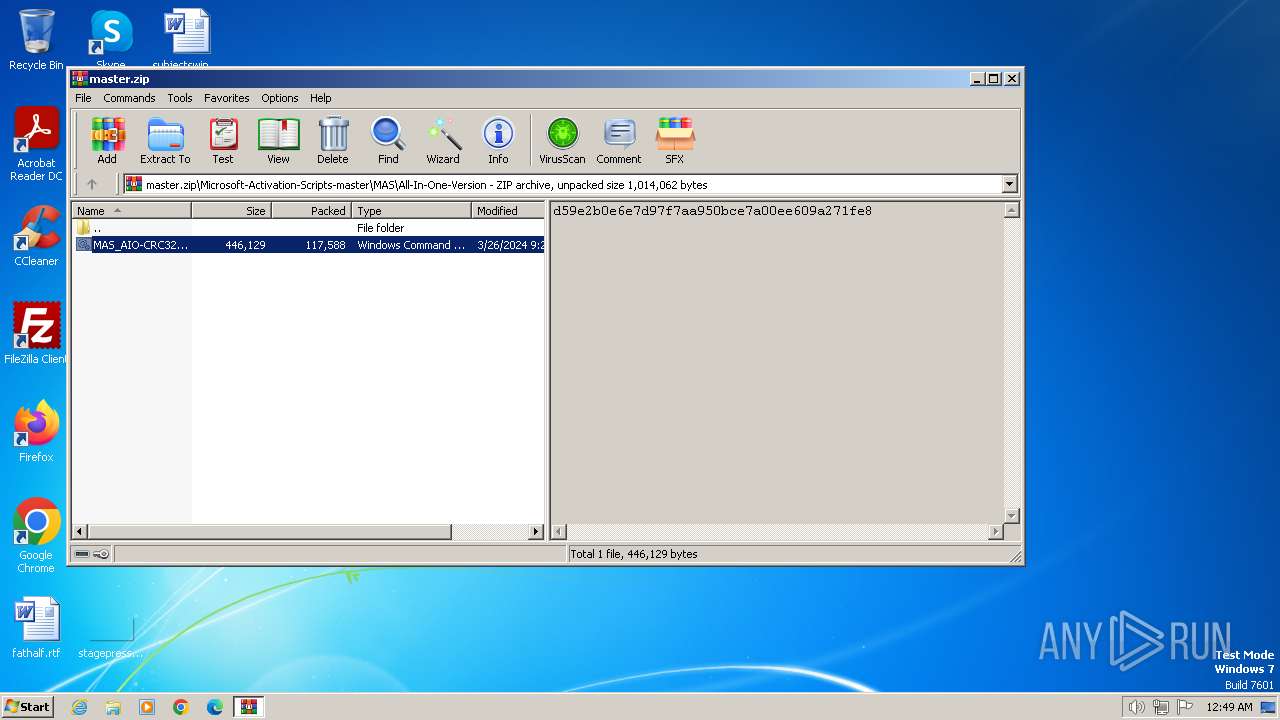
| 3936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3936.15882\MAS_AIO-CRC32_60BA35A8.cmd | text | |
MD5:— | SHA256:— | |||
| 3936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3936.16572\Microsoft-Activation-Scripts-master\MAS\All-In-One-Version\MAS_AIO-CRC32_60BA35A8.cmd | text | |
MD5:— | SHA256:— | |||
| 2564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rw4a0zde.n2j.ps1 | binary | |
MD5:— | SHA256:— | |||
| 2564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1uslsfy0.s2p.psm1 | binary | |
MD5:— | SHA256:— | |||
| 2564 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 2336 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:— | SHA256:— | |||
| 2336 | cmd.exe | C:\Windows\Temp\`.txt | text | |
MD5:— | SHA256:— | |||
| 3872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\gkkl2nsg.nsk.ps1 | binary | |
MD5:— | SHA256:— | |||
| 3872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\heea5ojz.ido.psm1 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updatecheck.massgrave.dev |
| unknown |
kms.zhuxiaole.org |
| unknown |
kms.wxlost.com |
| unknown |