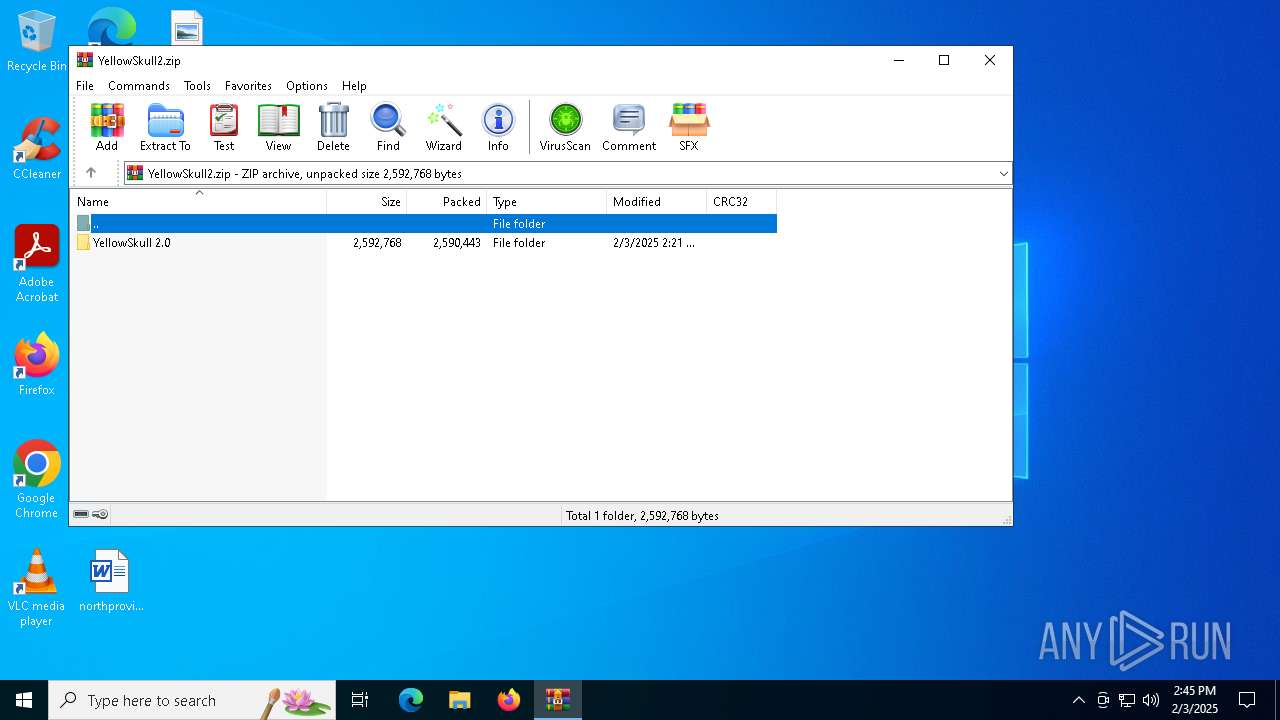
| File name: | YellowSkull2.zip |
| Full analysis: | https://app.any.run/tasks/6d887d5f-282d-4741-a0bb-9c1ffadccac4 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2025, 14:45:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 8A85654BE6EB915D8CF216E946315F84 |
| SHA1: | 3776F5B56F9B016C377B8C45DBDD04A952E03D12 |
| SHA256: | 454D0890672420EEF79D7A674A27F91E2B25B551E2DBC72751DC8F95944EE5E0 |
| SSDEEP: | 98304:vtd6+HJCbbEV+nM5VesnqjIyxuQ9zk677FVzagcLs86fONe3Tcd66kTli9lYN2xQ:okSnAucLq+DG |
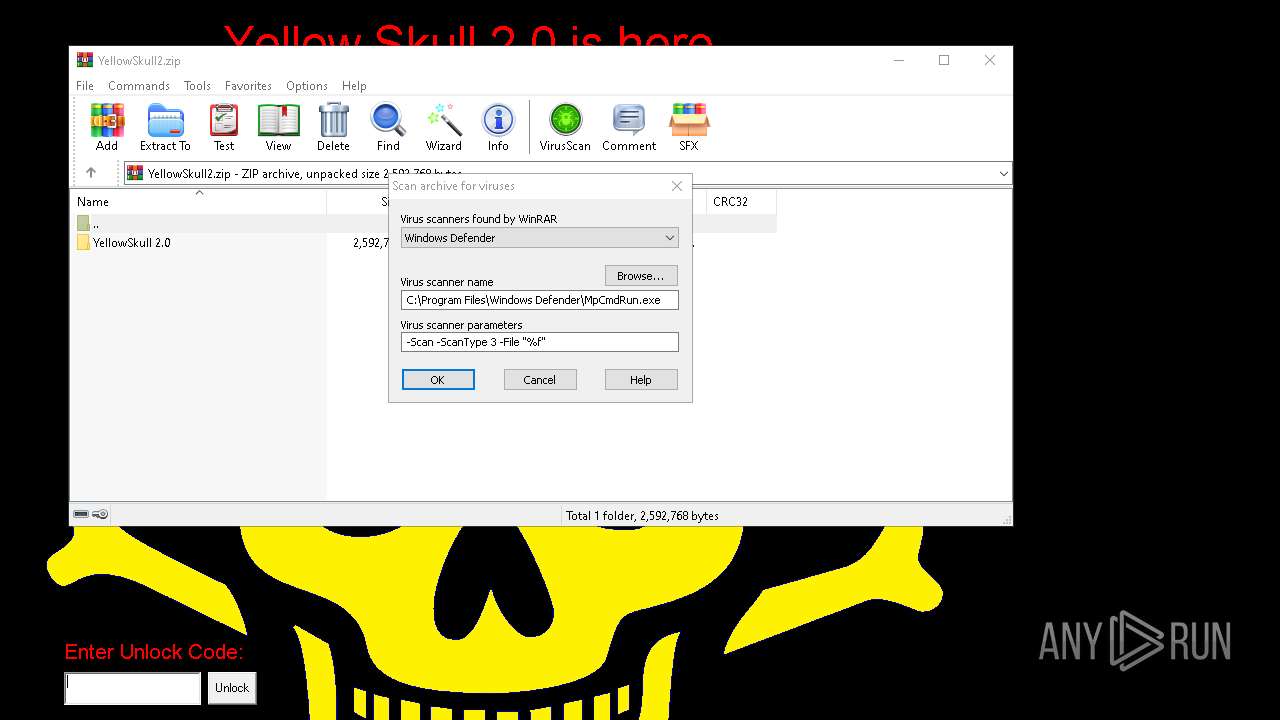
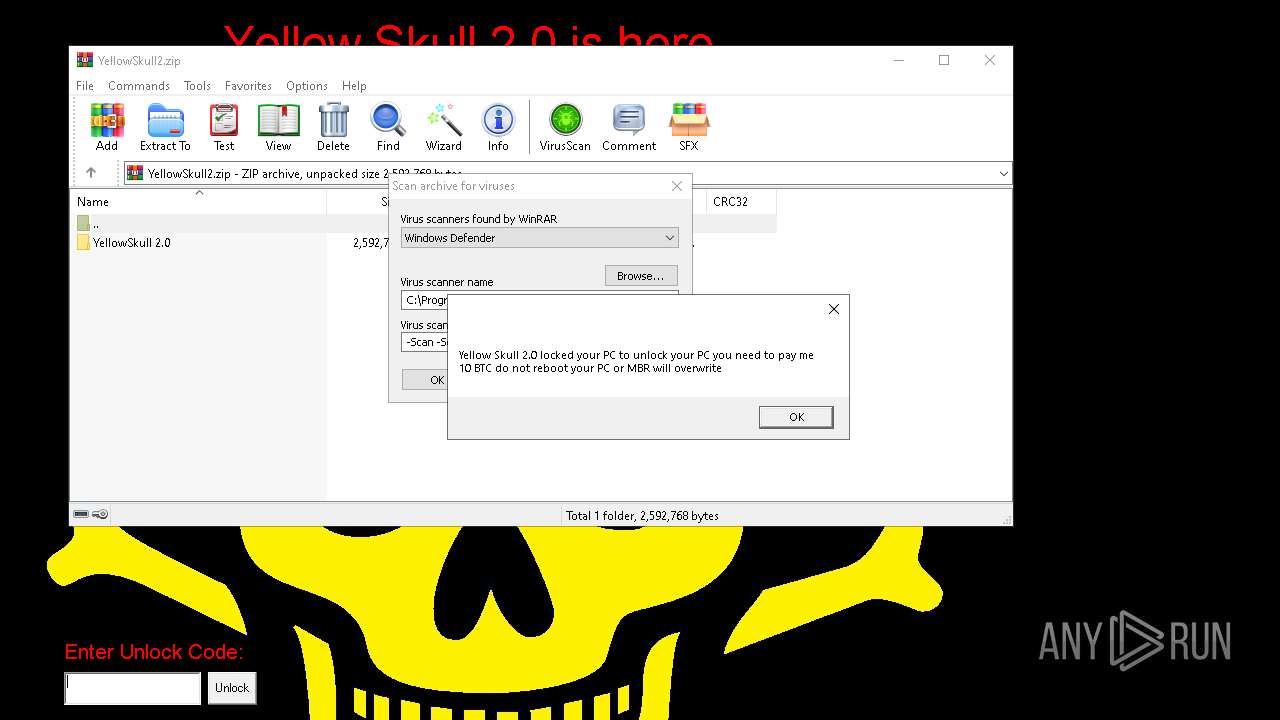
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5432)
Disables the LogOff the Start menu
- reg.exe (PID: 4652)
UAC/LUA settings modification
- reg.exe (PID: 5388)
Changes the autorun value in the registry
- reg.exe (PID: 2736)
SUSPICIOUS
Executable content was dropped or overwritten
- YellowSkull 2.0.exe (PID: 836)
- cmd.exe (PID: 2928)
Reads security settings of Internet Explorer
- YellowSkull 2.0.exe (PID: 836)
Executing commands from a ".bat" file
- YellowSkull 2.0.exe (PID: 836)
Starts CMD.EXE for commands execution
- YellowSkull 2.0.exe (PID: 836)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2928)
Changes the desktop background image
- reg.exe (PID: 1328)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2928)
The executable file from the user directory is run by the CMD process
- bg.exe (PID: 3260)
- YSkullLock.exe (PID: 4308)
The process executes VB scripts
- cmd.exe (PID: 2928)
INFO
Manual execution by a user
- YellowSkull 2.0.exe (PID: 836)
- YellowSkull 2.0.exe (PID: 2092)
Checks supported languages
- YellowSkull 2.0.exe (PID: 836)
- bg.exe (PID: 3260)
- YSkullLock.exe (PID: 4308)
Reads the computer name
- YellowSkull 2.0.exe (PID: 836)
- bg.exe (PID: 3260)
- YSkullLock.exe (PID: 4308)
The sample compiled with english language support
- YellowSkull 2.0.exe (PID: 836)
Process checks computer location settings
- YellowSkull 2.0.exe (PID: 836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:02:03 14:21:16 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | YellowSkull 2.0/ |
Total processes
171
Monitored processes
53
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | "C:\Users\admin\Desktop\YellowSkull 2.0.exe" | C:\Users\admin\Desktop\YellowSkull 2.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1224 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | reg add "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d c:\yellowskull.bmp /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1864 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2072 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\SysWOW64\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\Desktop\YellowSkull 2.0.exe" | C:\Users\admin\Desktop\YellowSkull 2.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
5 295
Read events
5 277
Write events
18
Delete events
0
Modification events
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\YellowSkull2.zip | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5432) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2928) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (1328) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: c:\yellowskull.bmp | |||
Executable files
4
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | cmd.exe | C:\YellowSkull.bmp | image | |
MD5:11BCDA64D254AD8DC591B41F8FCEB04D | SHA256:84C5DAD2D4CEC5B636C1FAE6F1E1482ADA9F62363DCF269B4A86F6070D5B50FC | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\YellowSkull.bmp | image | |
MD5:11BCDA64D254AD8DC591B41F8FCEB04D | SHA256:84C5DAD2D4CEC5B636C1FAE6F1E1482ADA9F62363DCF269B4A86F6070D5B50FC | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\YSkullLock.exe | executable | |
MD5:2191C3A14B53531E82726B17DD331CEF | SHA256:3B2ABD3773E4678100F197F53A886EC833FD2E26AA9A94D780A2D22BEFDF7D44 | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\bg.cpp | text | |
MD5:A4F885352ED45CF37331BD01EC5B838A | SHA256:7032FD15B3B95CC3F0637BB8F8463E0848B5C2767C1CF4109EC34D7E2861322C | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\bg.wav | binary | |
MD5:832B350B50A07906C630A2B8819FD209 | SHA256:94E1CECF8ED740EA45C87927DE31005C3B2F9DB261AAE04FE56A81E337D1E8DA | |||
| 2928 | cmd.exe | C:\YSkullMBRSetup.exe | executable | |
MD5:220303EB72EBDE4605116640FB719B26 | SHA256:F081C913488C3F22B62F906DAC2A82A38D085EBE1D28701F0059DFDFBF1CCF42 | |||
| 2928 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\k.vbs | text | |
MD5:08121EA7E3B2EB7EDFC85252B937AAEB | SHA256:31CD4463ECC62DC846DBAEE0A5446D4BF11100BEFF1B01AE88E234B6C29329C2 | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\YellowSkull2.bat | text | |
MD5:4671D5895D88BC19645CAB0FC7CA398A | SHA256:DD8AA9F7955674A7A1B5B222D7C1809C583C705DAE8BF476CDD42EFCC0AFABB5 | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\bg.exe | executable | |
MD5:12CF508E9058E3E67CF8A736557C2749 | SHA256:B3670EC42931E2DEA3E03053EDA32240D8B6DB15BF89D0C74E23E99ECB0AAF49 | |||
| 836 | YellowSkull 2.0.exe | C:\Users\admin\AppData\Local\Temp\7850.tmp\YSkullMBRSetup.exe | executable | |
MD5:220303EB72EBDE4605116640FB719B26 | SHA256:F081C913488C3F22B62F906DAC2A82A38D085EBE1D28701F0059DFDFBF1CCF42 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3564 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3564 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3564 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3564 | svchost.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3564 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3976 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |