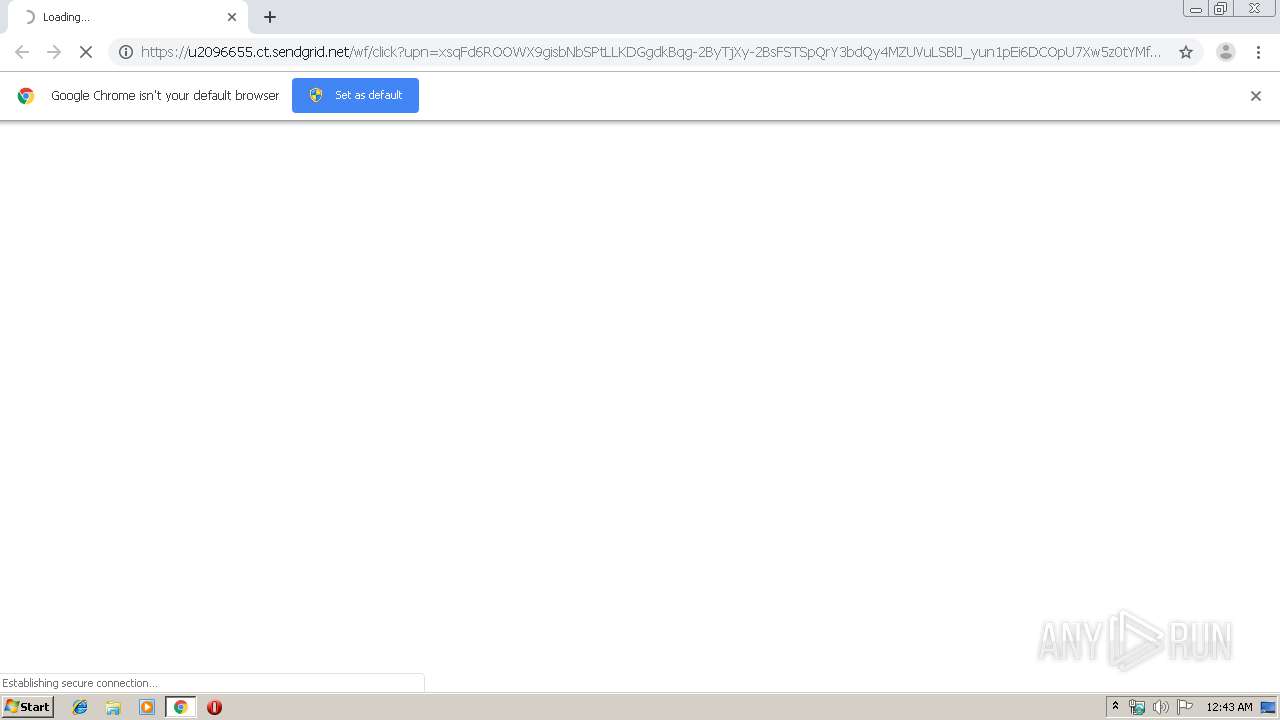
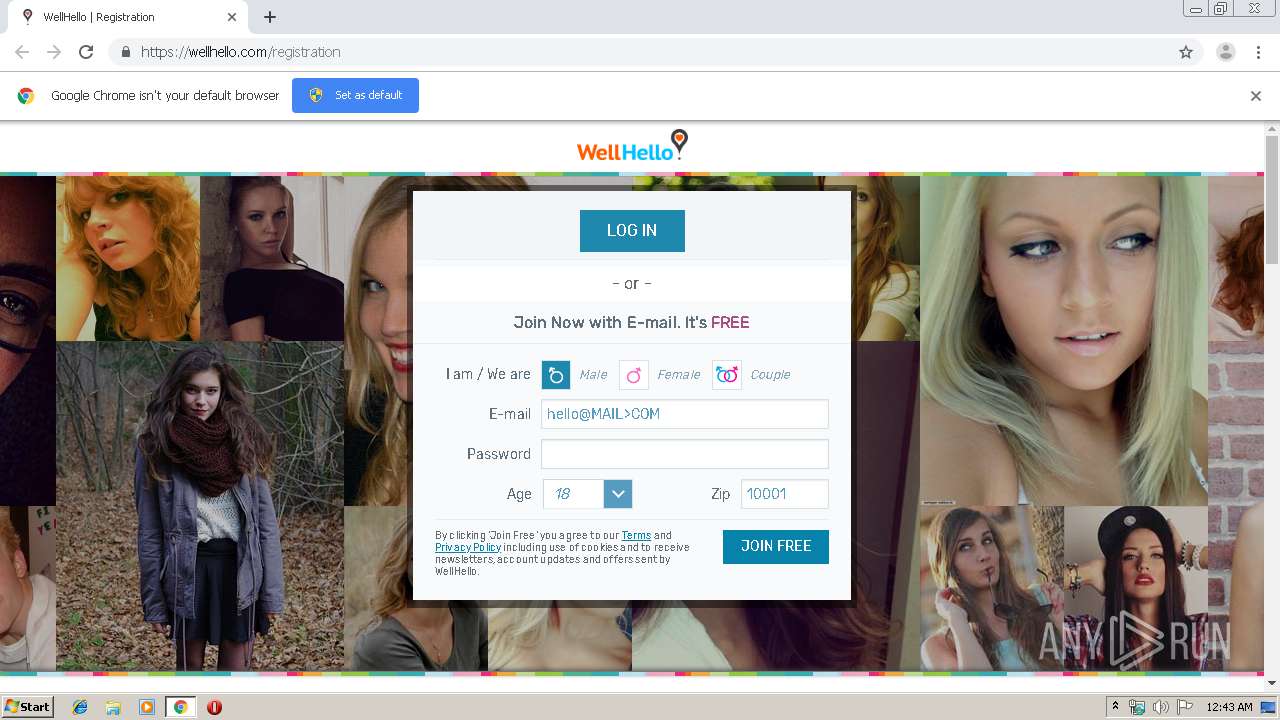
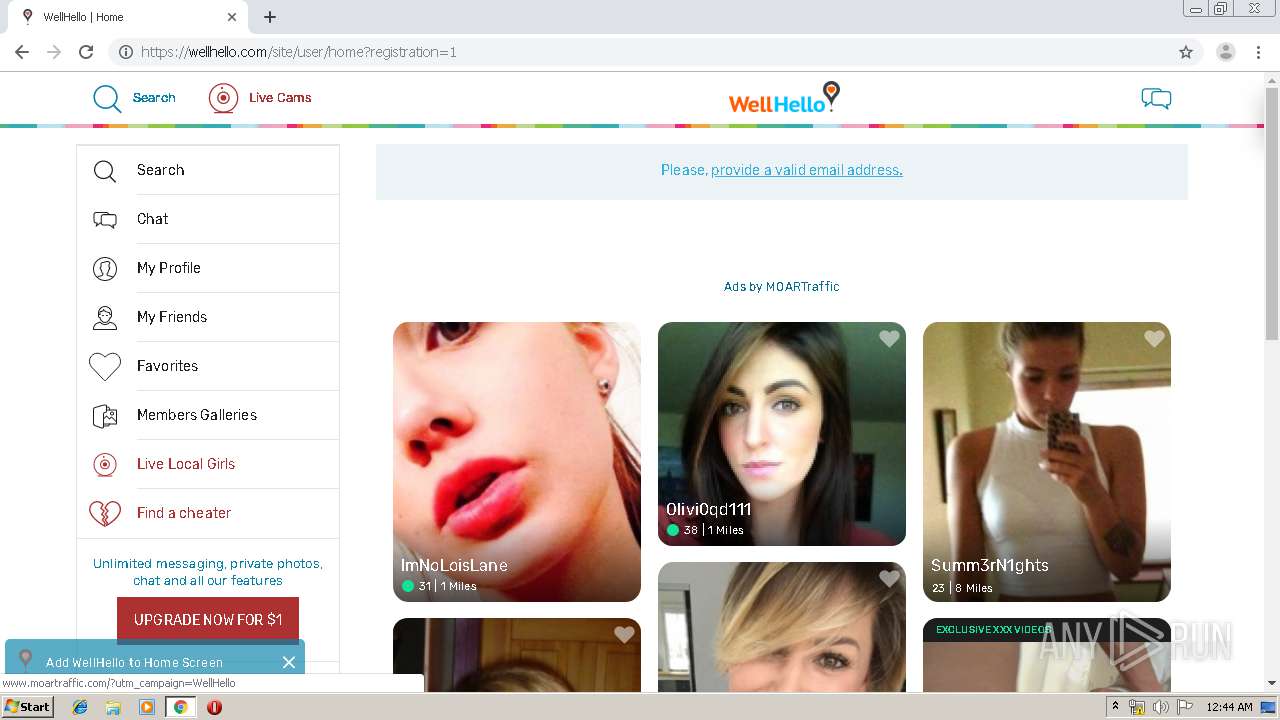
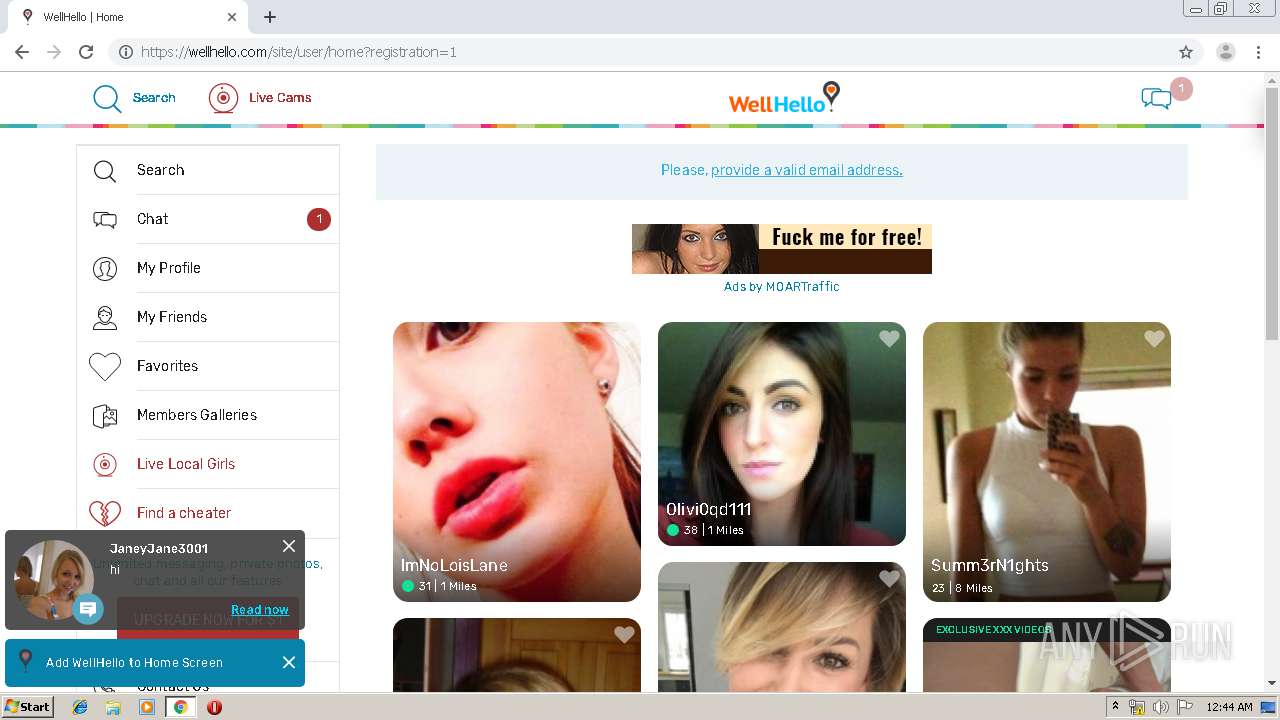
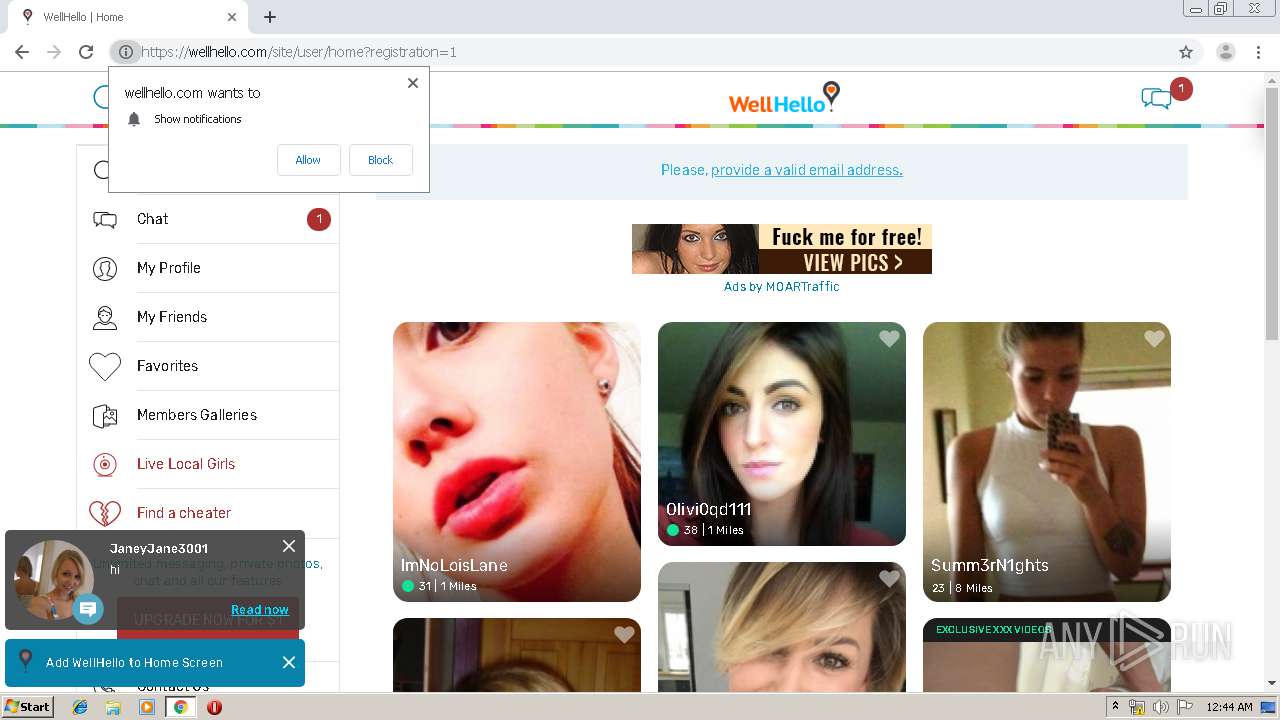
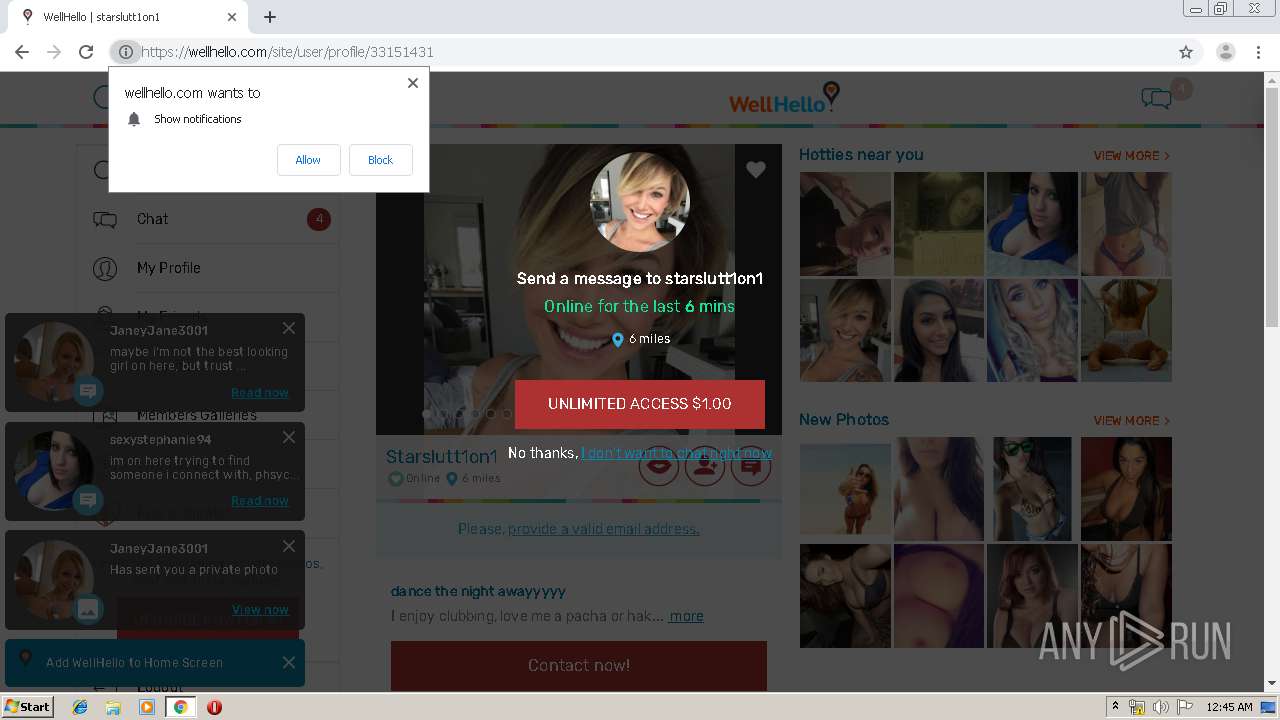
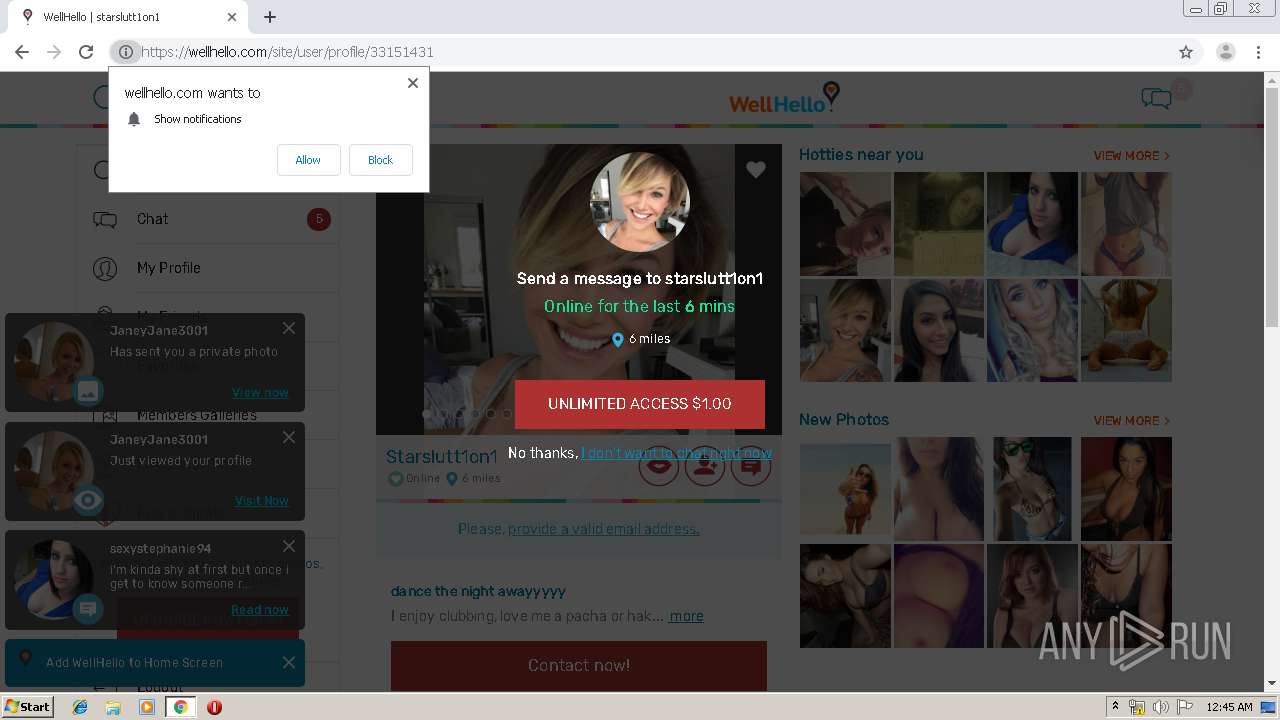
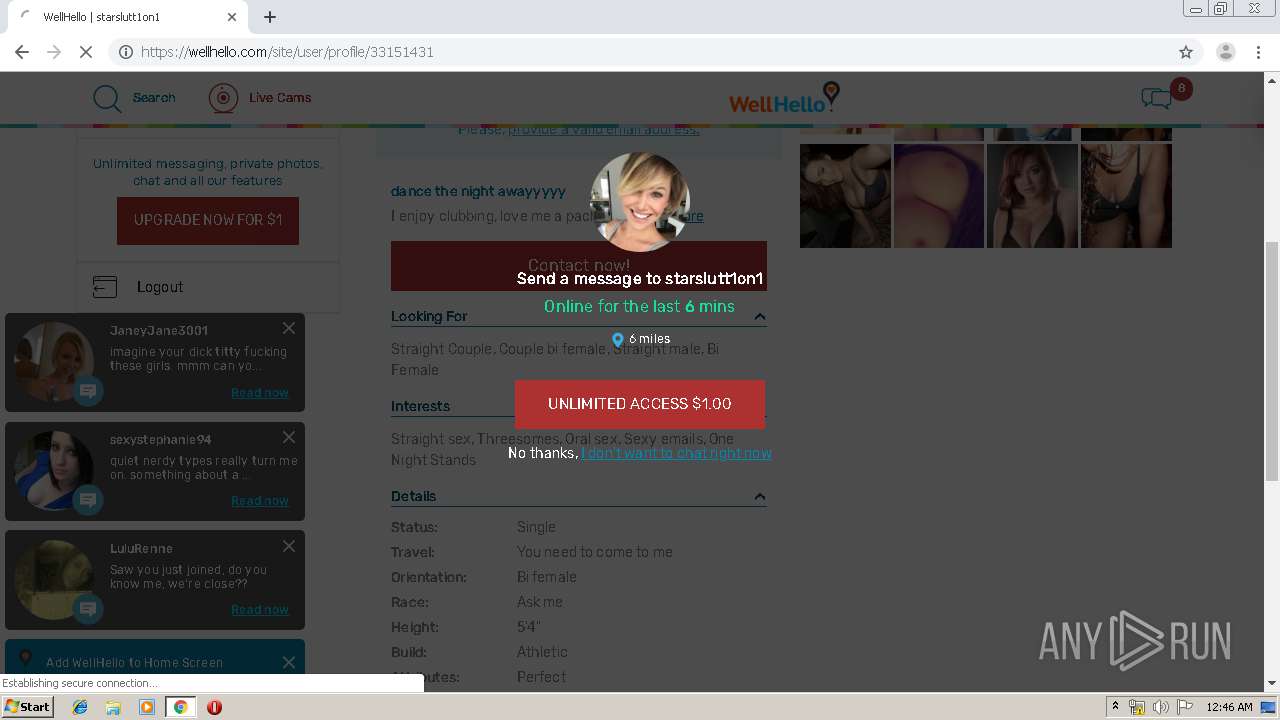
| URL: | https://u2096655.ct.sendgrid.net/wf/click?upn=xsqFd6ROOWX9gisbNbSPtLLKDGgdkBqg-2ByTjXy-2BsFSTSpQrY3bdQy4MZUVuLSBlJ_yun1pEi6DCOpU7Xw5z0tYMfw-2BPHVnmmo6ERpRSWLU8Wz8NspzMeQCC3pSccsMNWDtwryyRFRgzKcsbfPLqrDuTDDjd9pMMH0lABpyExTEBv6lQbVEqsvElDuBrpqZ0W0U2sj1bvtUaFbEmCQZRm2ZQfdOm4CqxI1PrOYr61crIJkv2ciKsWIVZrolt-2B-2BZ6ebWshjkOK9yQIALZvyHSChDPCXcqN07n6rvWj-2BuabsUdH-2BAA-2FVVElR0CIqGA74T6n3pYF9VAkY4XGg-2B70wTQByucsxODKKV-2FROzG3kKgJ-2BcIACu-2FmpdlquFziy6ODZOH3BwrHojhoT9ApBwlYfOnIYTwhDsJMGD2V-2FlT1c3b9Gtt2unaR-2BNLQ5N1KgHi-2BPAdollxRZ9x4sqS1GVX1TqgS8vJPHclkvvDzFH94p51FM4eWIZhduKQ3kBUfY1lPA9z4sUv9C-2FRn2T6P9WLh5818lvpCUWp3lMwVAQN7zyiHnb-2FGX3g-2Fk-2BNqjk83SpoK4zGIh |
| Full analysis: | https://app.any.run/tasks/648350c7-35d2-4a5c-9c48-9b78a02fbb6d |
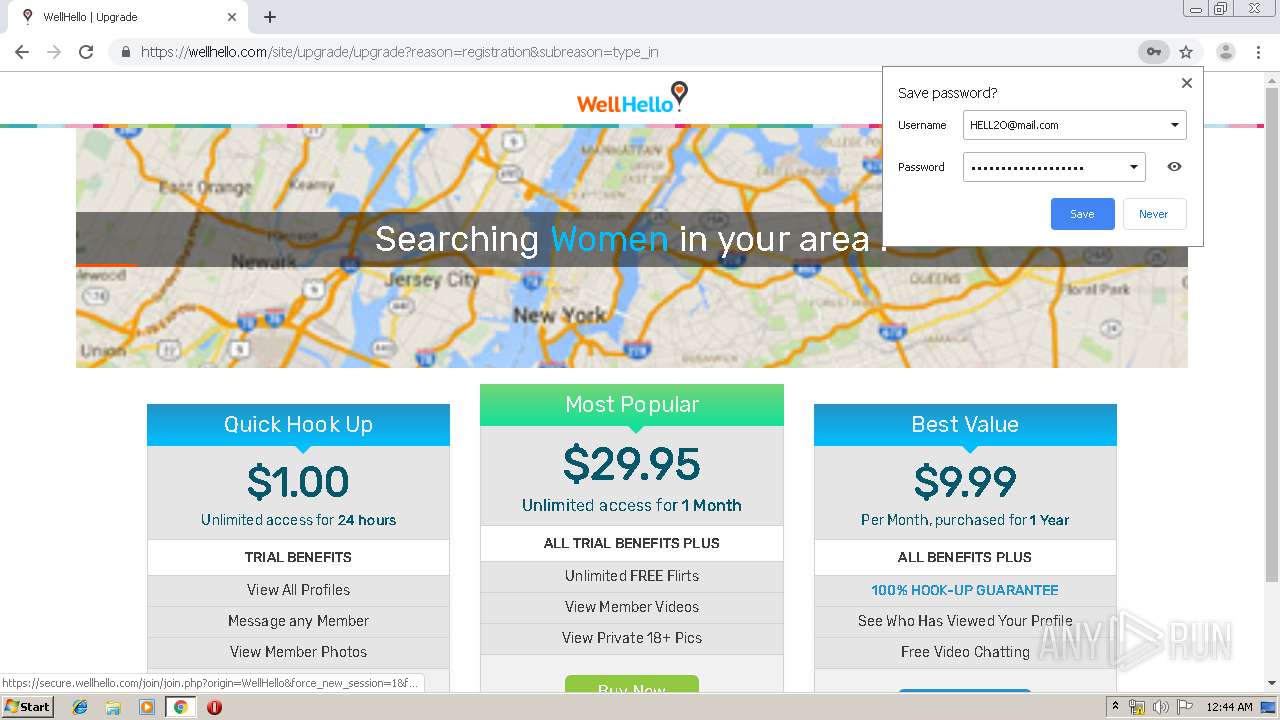
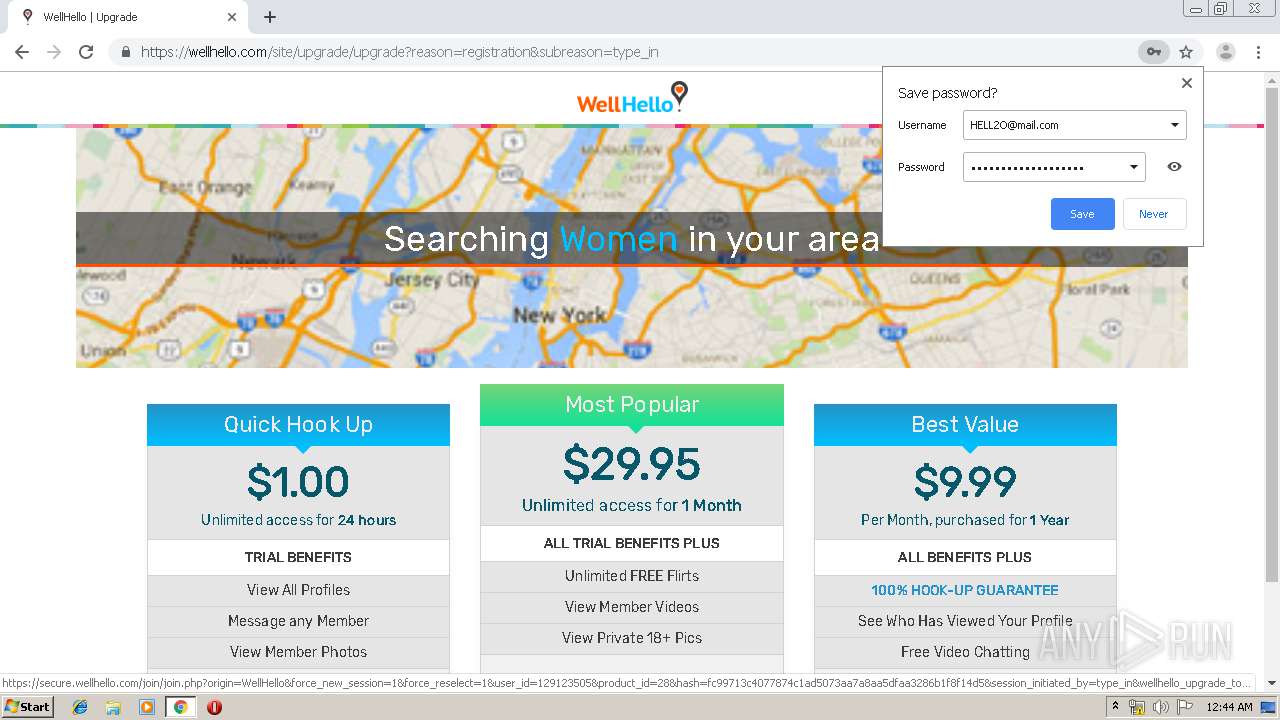
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2019, 23:43:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C9C6AB99464C4A7220236497E85827D1 |
| SHA1: | 2761DCED47688DECAE36101ED4A28972E3CFCF8F |
| SHA256: | 454CDA1E89BF1F6F5F46EBADF2E6C6FDAC3D2F2DCCC24E4199A4030E19A500C4 |
| SSDEEP: | 12:2pVDSCuhQzc8nRrT6c7zU2lNa8cdWNkWuz9hRXngmQXKG/bK8lafZ:2vLJw8RT7vlNmLRXgm6KGTflax |
MALICIOUS
No malicious indicators.SUSPICIOUS
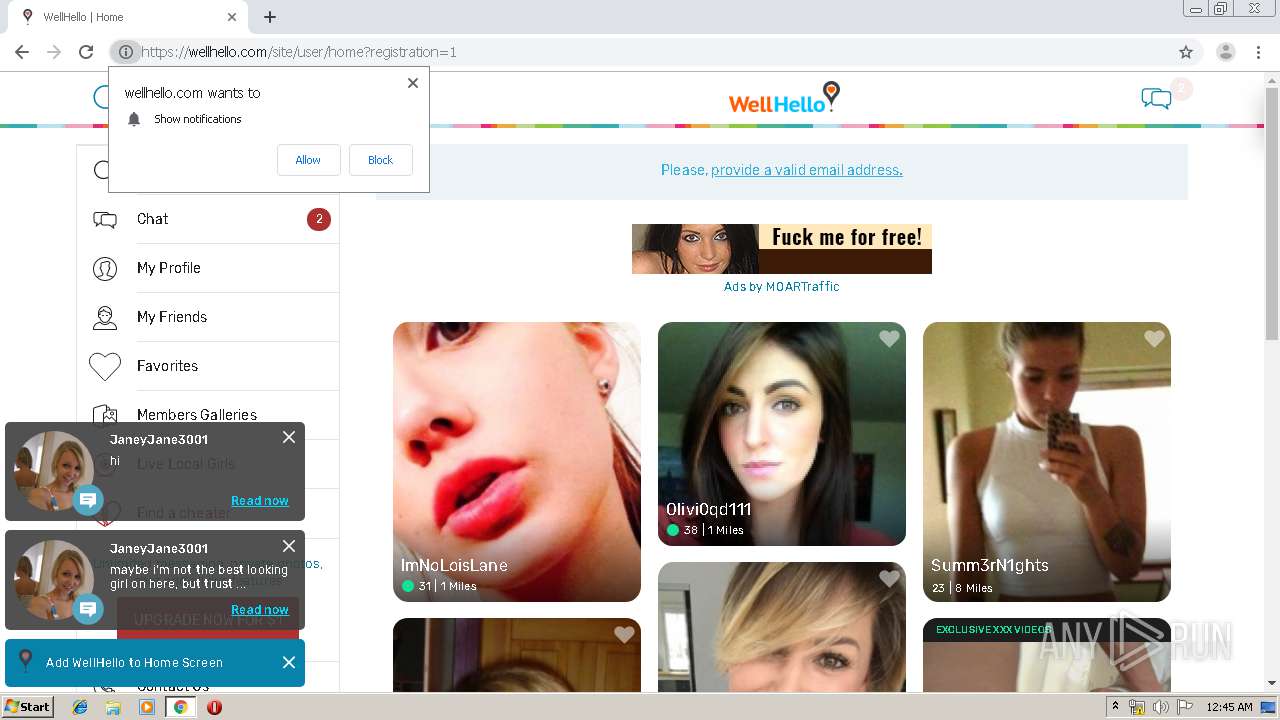
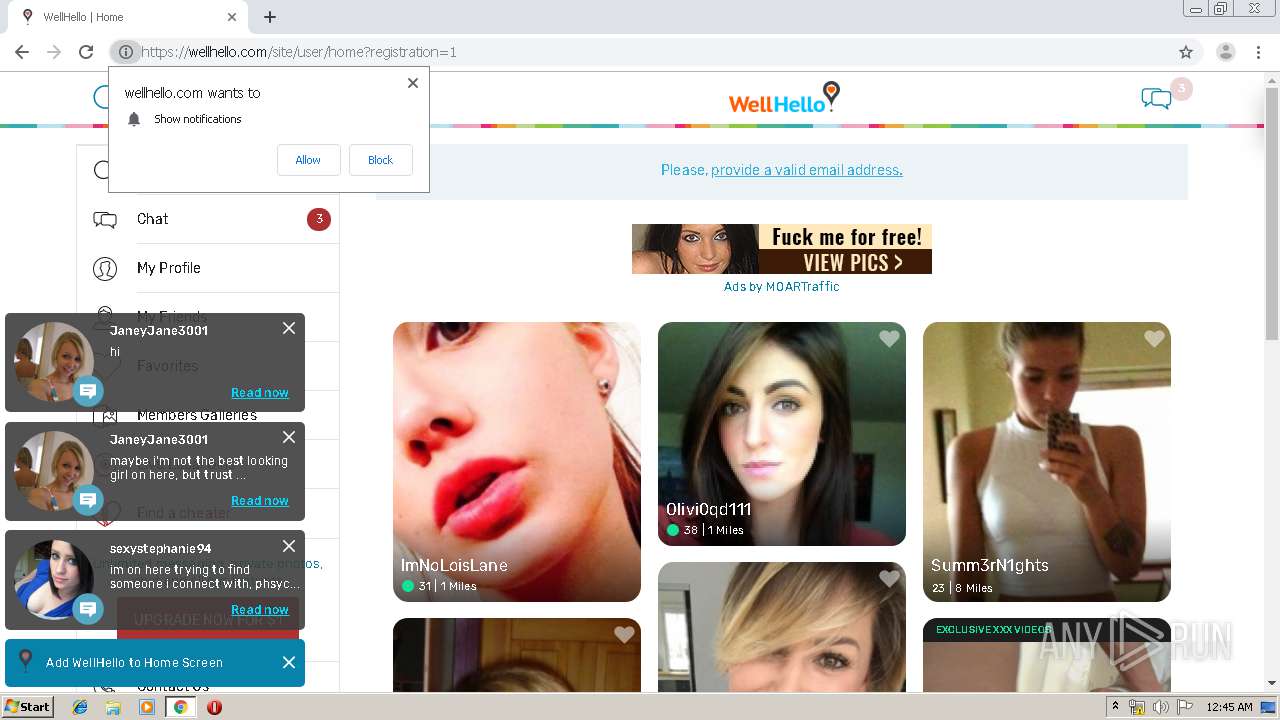
Modifies files in Chrome extension folder
- chrome.exe (PID: 2512)
INFO
Reads the hosts file
- chrome.exe (PID: 2512)
- chrome.exe (PID: 456)
Application launched itself
- chrome.exe (PID: 2512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17521591800484253121 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2480 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11930069081126590193 --mojo-platform-channel-handle=1576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12909276390744119865 --mojo-platform-channel-handle=3600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5690789269027562393 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17397399891771899834 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11219602724212905086 --mojo-platform-channel-handle=3696 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11309455374633492948 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12605918703641612105 --mojo-platform-channel-handle=572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15672175576696993218,1638629920728067037,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4397050003159440055 --mojo-platform-channel-handle=3480 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
643
Read events
550
Write events
88
Delete events
5
Modification events
| (PID) Process: | (344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2512-13213669398947875 |
Value: 259 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2512) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
74
Text files
241
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\70b48c31-abf4-41f3-b9d1-800b0b4245f9.tmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe686a.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFe68d7.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 2512 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:0ACECCA4CF9ADE756DA7CC9DCDF02D50 | SHA256:18F910775132B4FEE014EA0FAB836D857F367E76232FAB4AE6A86A92E4C3EBEE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
75
DNS requests
42
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
456 | chrome.exe | GET | 200 | 74.125.104.104:80 | http://r2---sn-2gb7sn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.52&mm=28&mn=sn-2gb7sn7k&ms=nvh&mt=1569195736&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
456 | chrome.exe | GET | 200 | 92.122.213.217:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
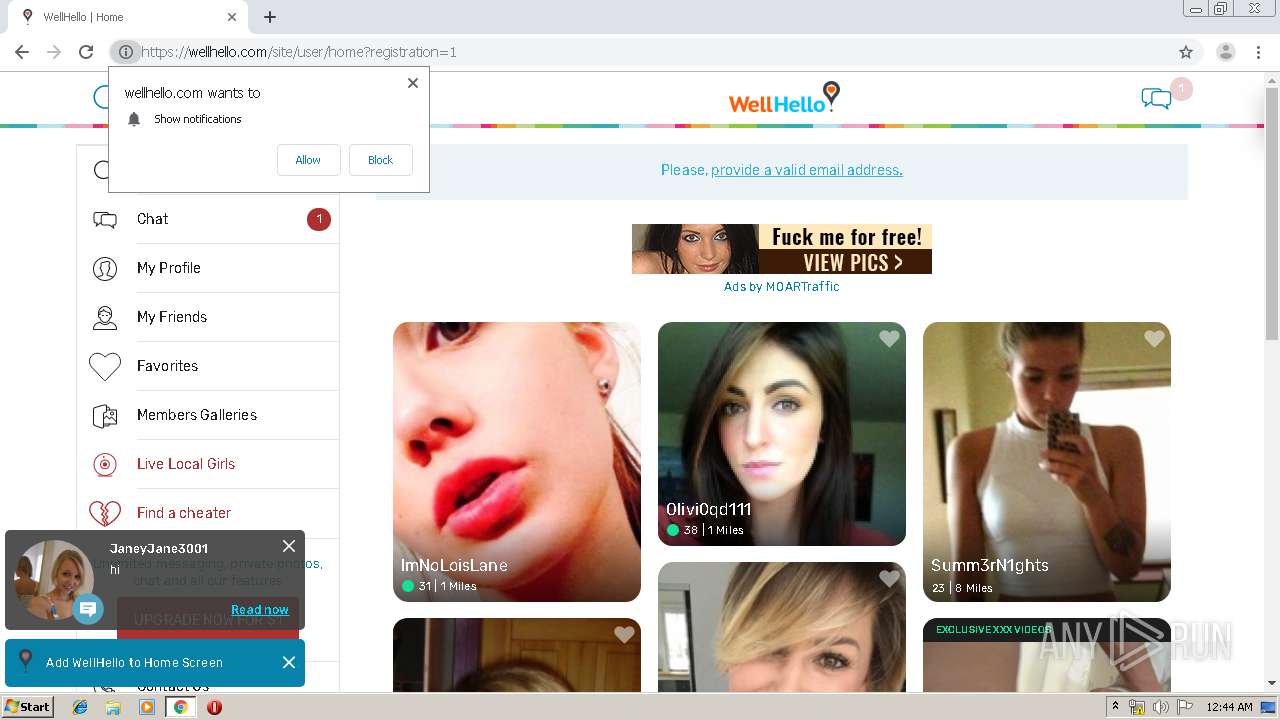
456 | chrome.exe | GET | 200 | 78.140.186.199:80 | http://img-ams-5-edge.thumbdn.com/wc-thumb/210fd4ab4ea854696506432a7e2673f4_w400.jpg | NL | image | 9.17 Kb | unknown |
456 | chrome.exe | GET | 200 | 13.32.222.153:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
456 | chrome.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | unknown | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | chrome.exe | 68.169.80.226:443 | secure.authbill.com | ISPrime, Inc. | US | unknown |
456 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 216.58.205.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 162.247.242.19:443 | bam.nr-data.net | New Relic | US | whitelisted |
456 | chrome.exe | 172.217.22.110:80 | clients2.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 151.101.66.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
456 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
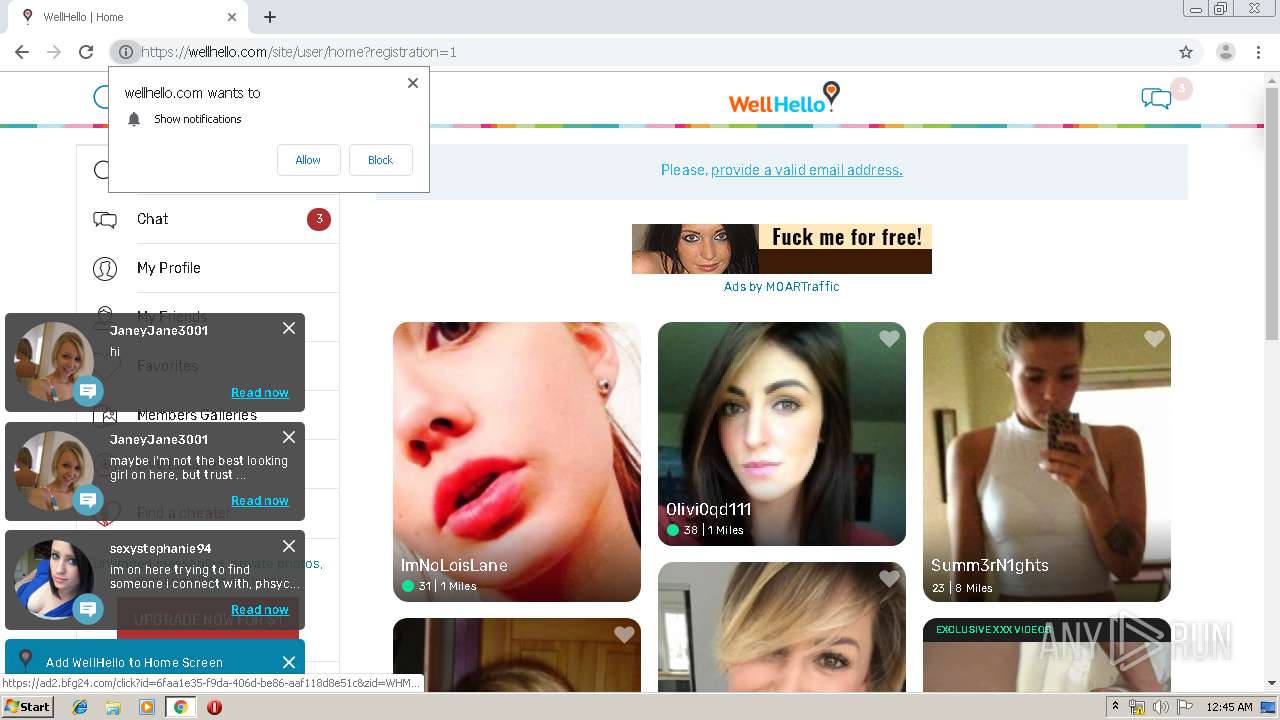
456 | chrome.exe | 167.89.118.35:443 | u2096655.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u2096655.ct.sendgrid.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
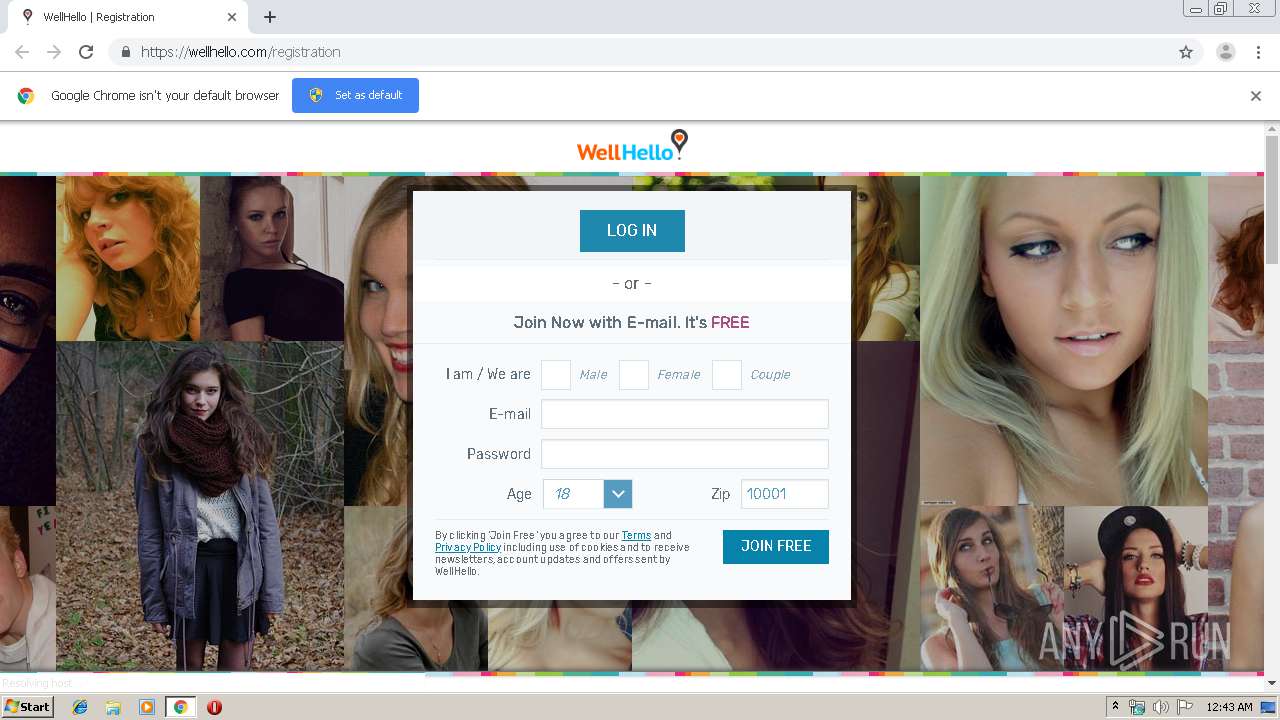
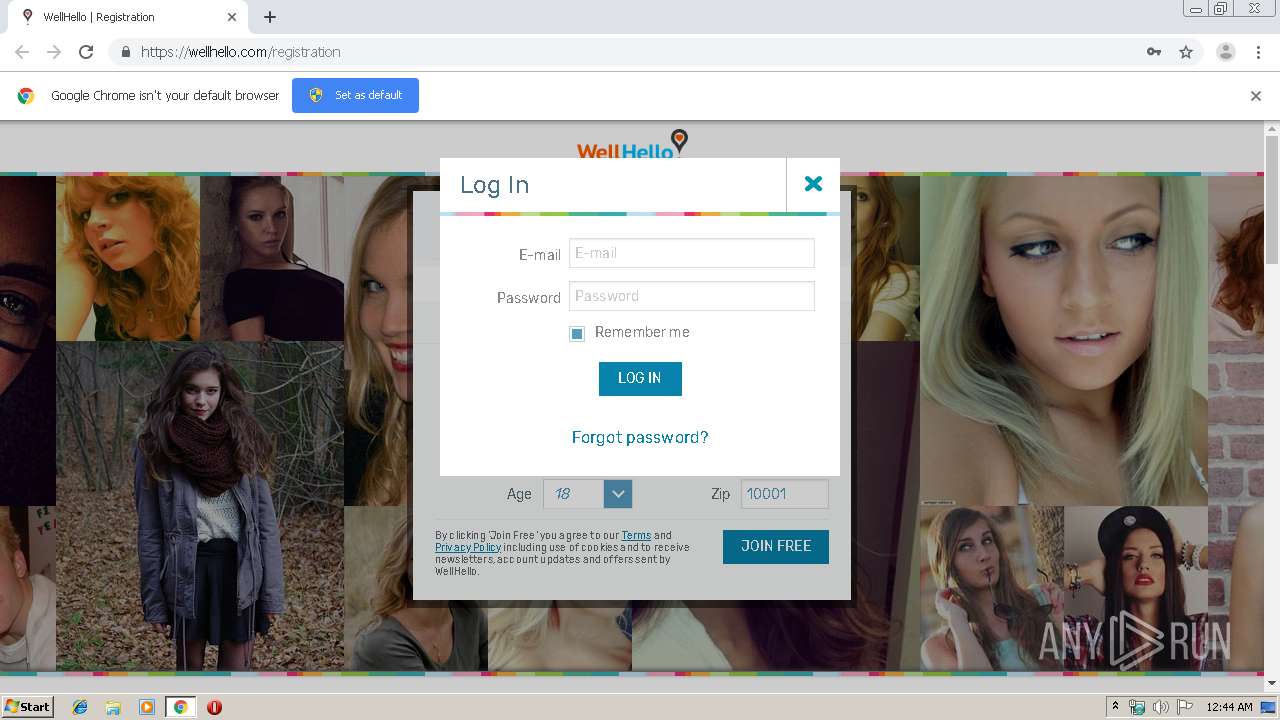
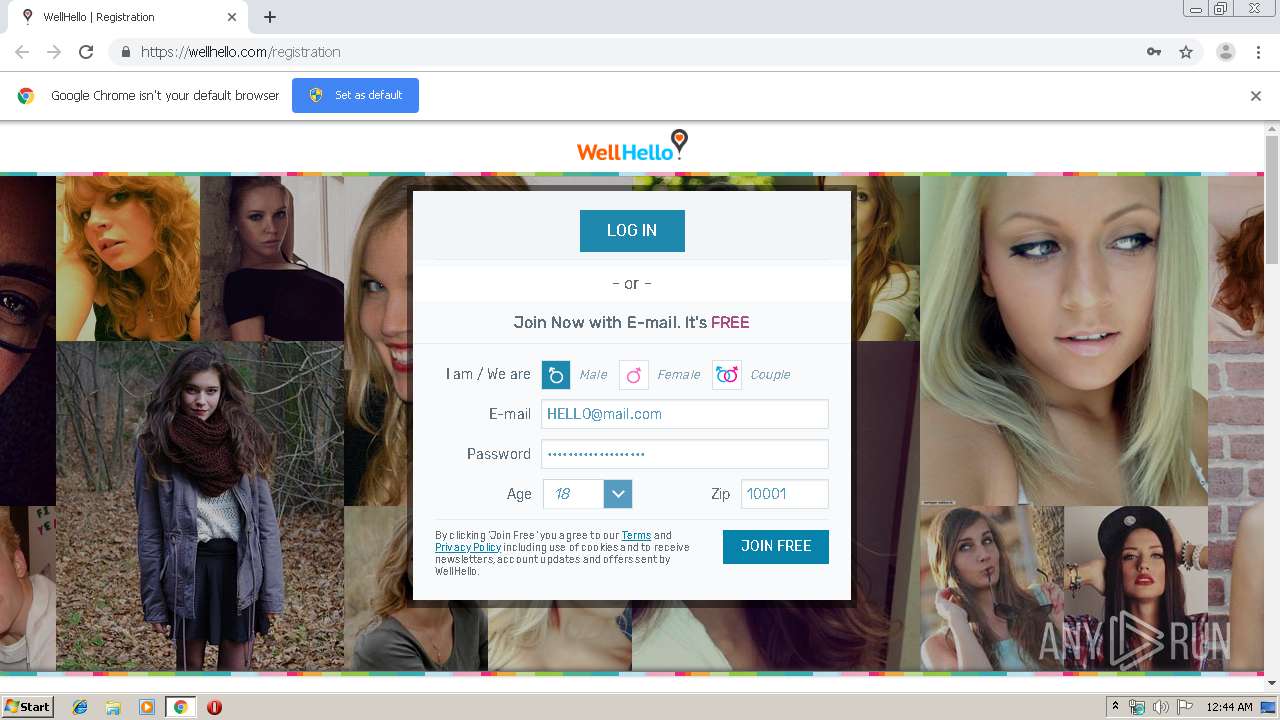
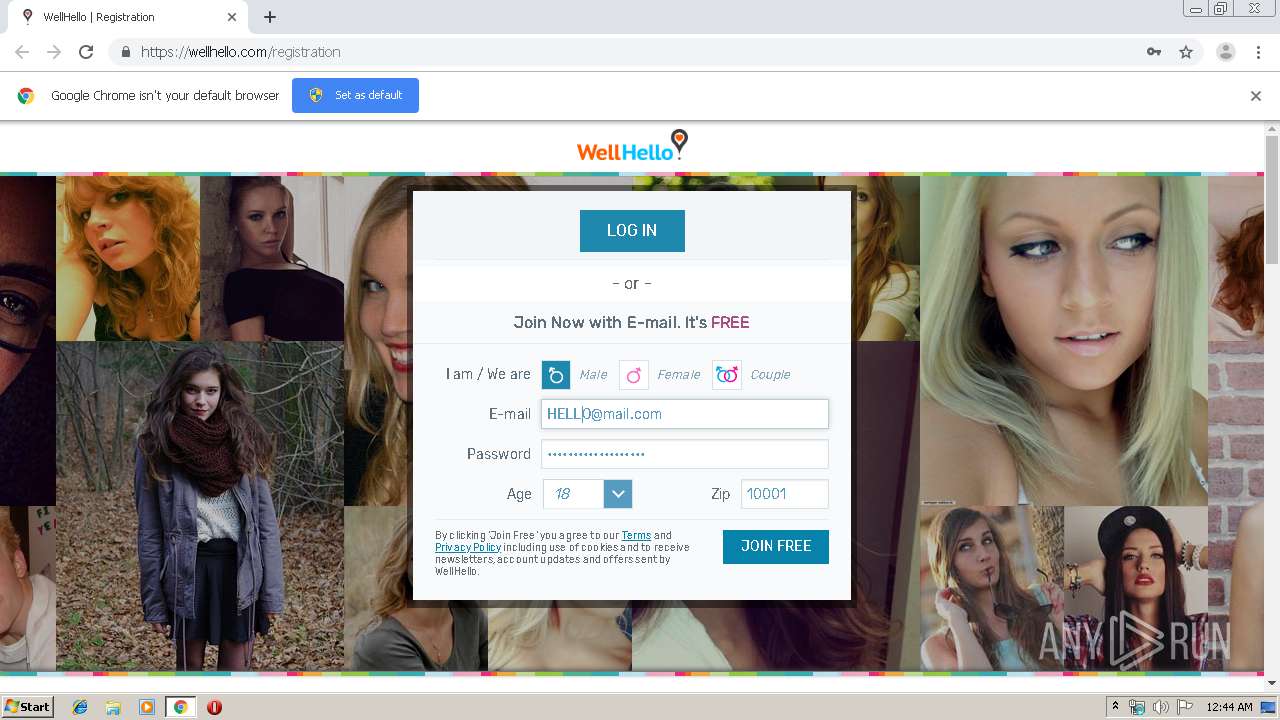
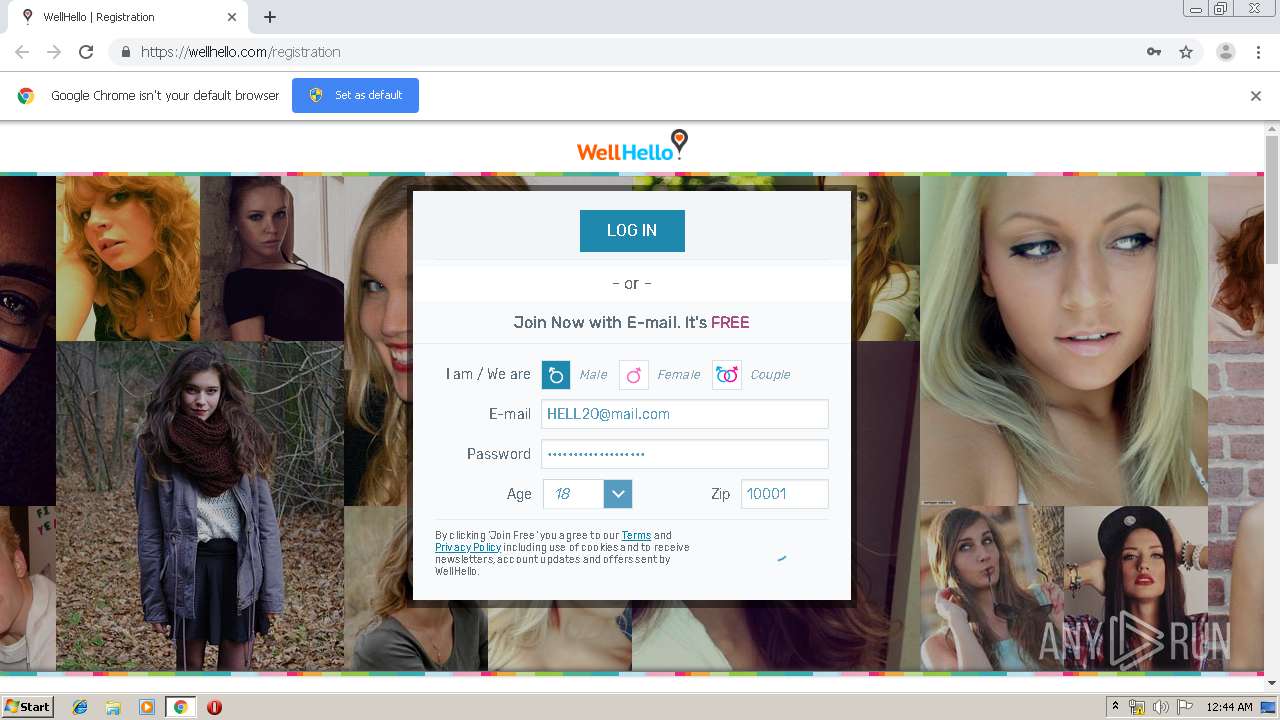
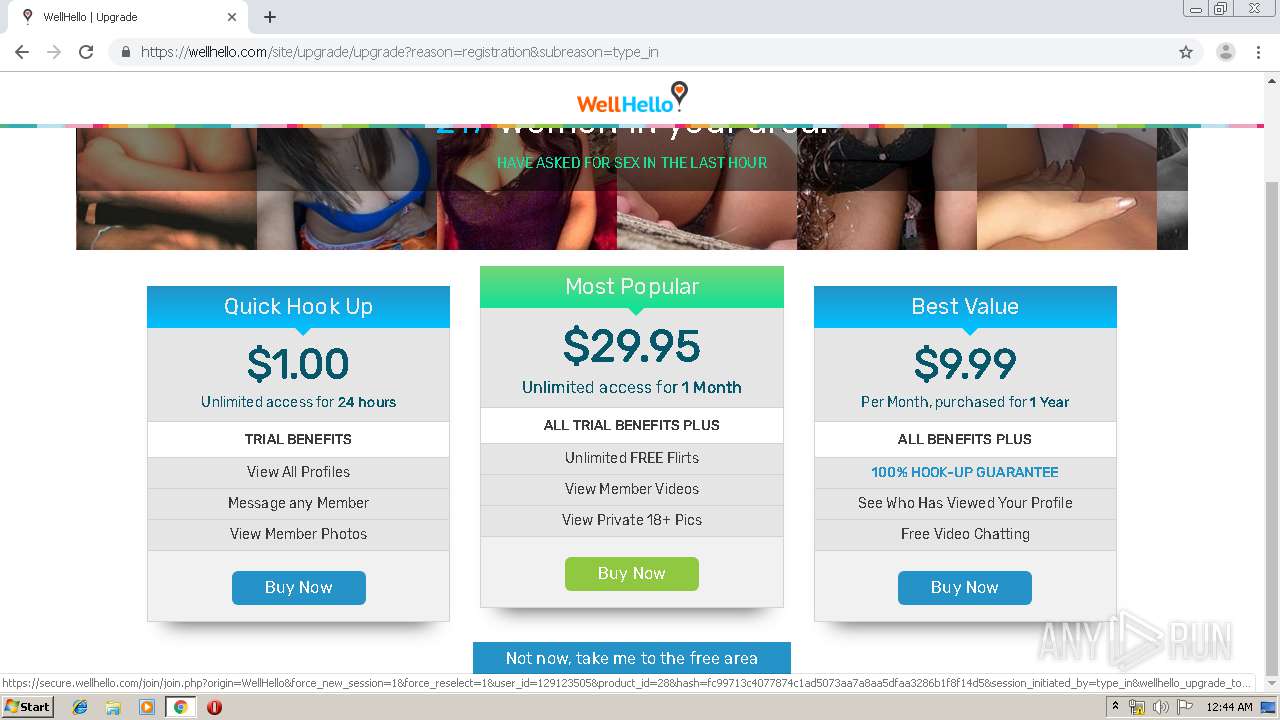
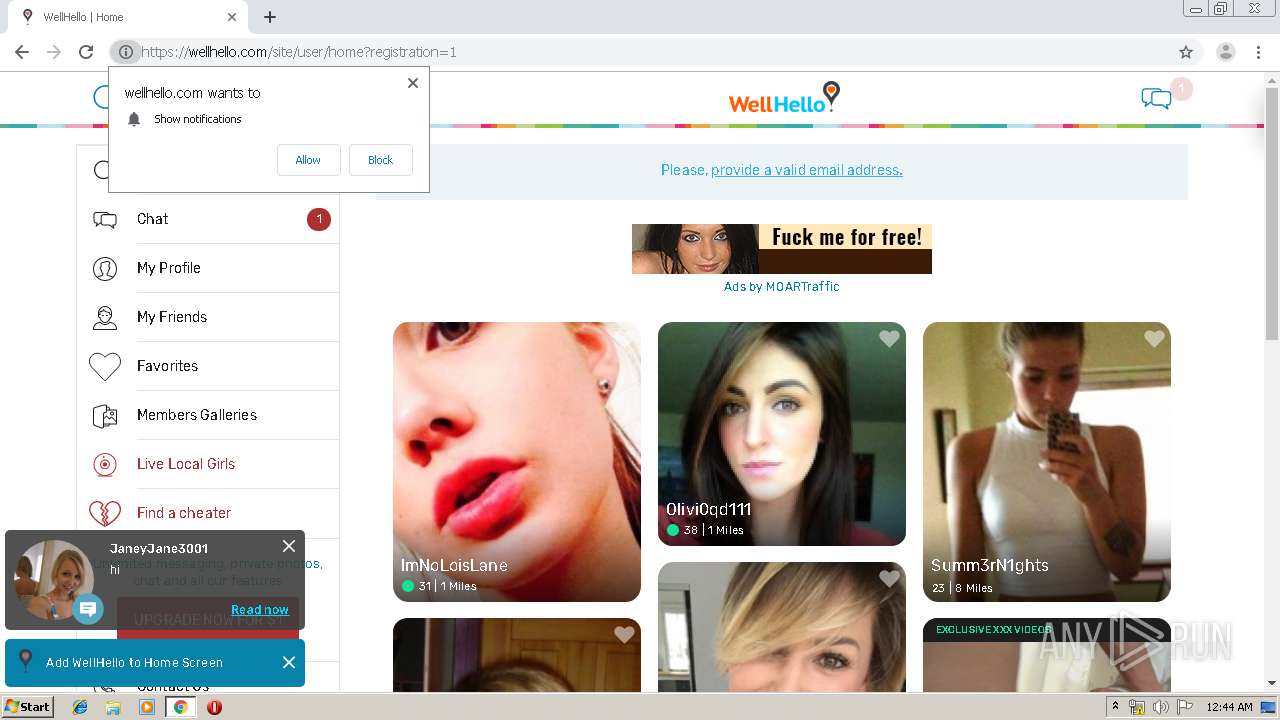
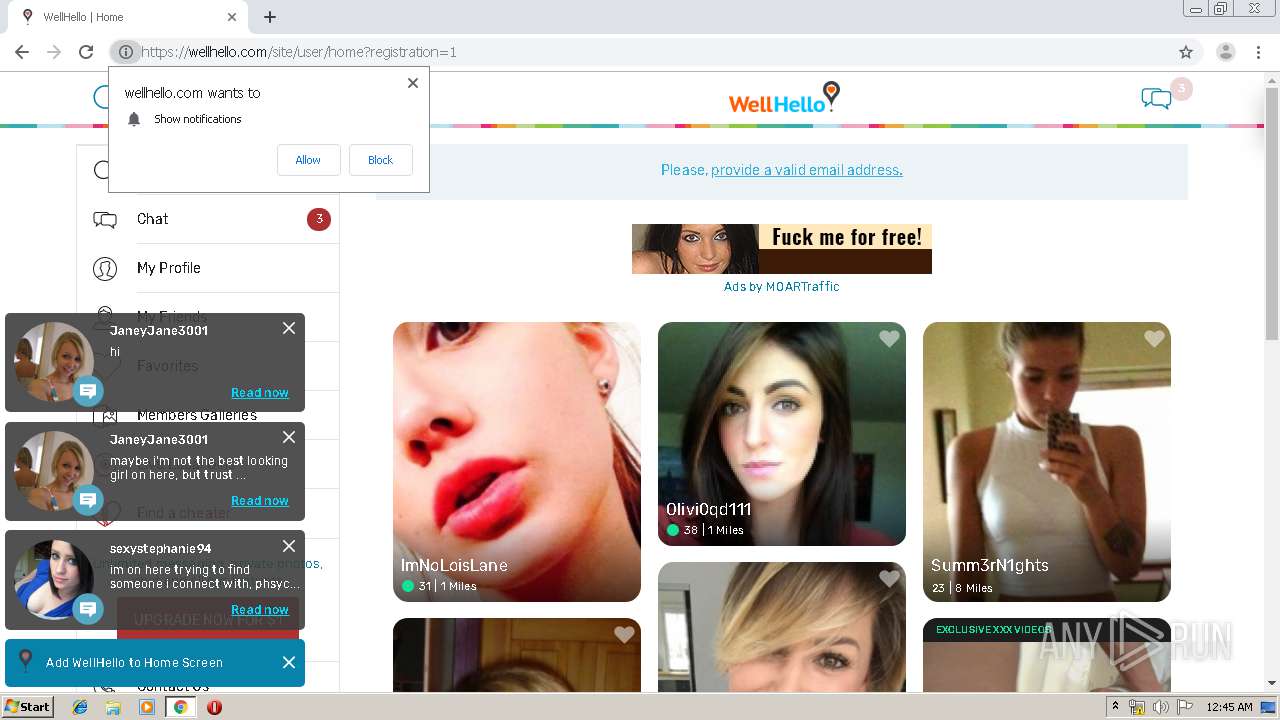
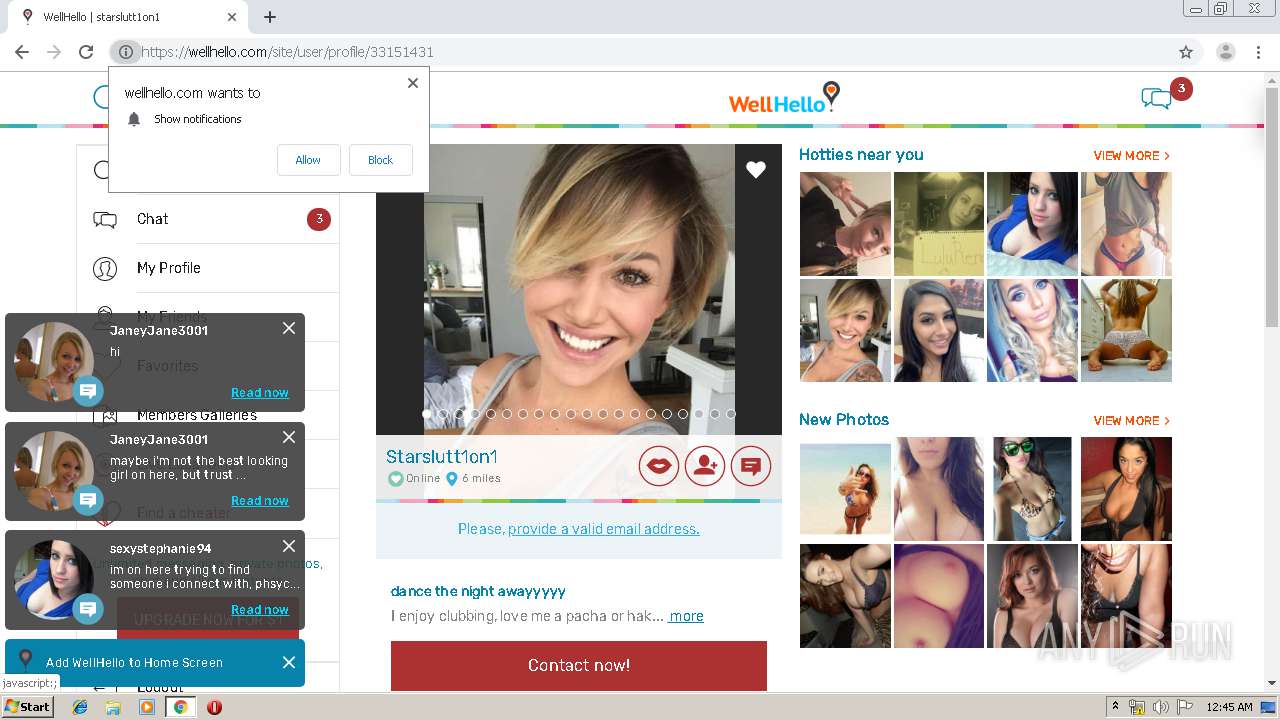
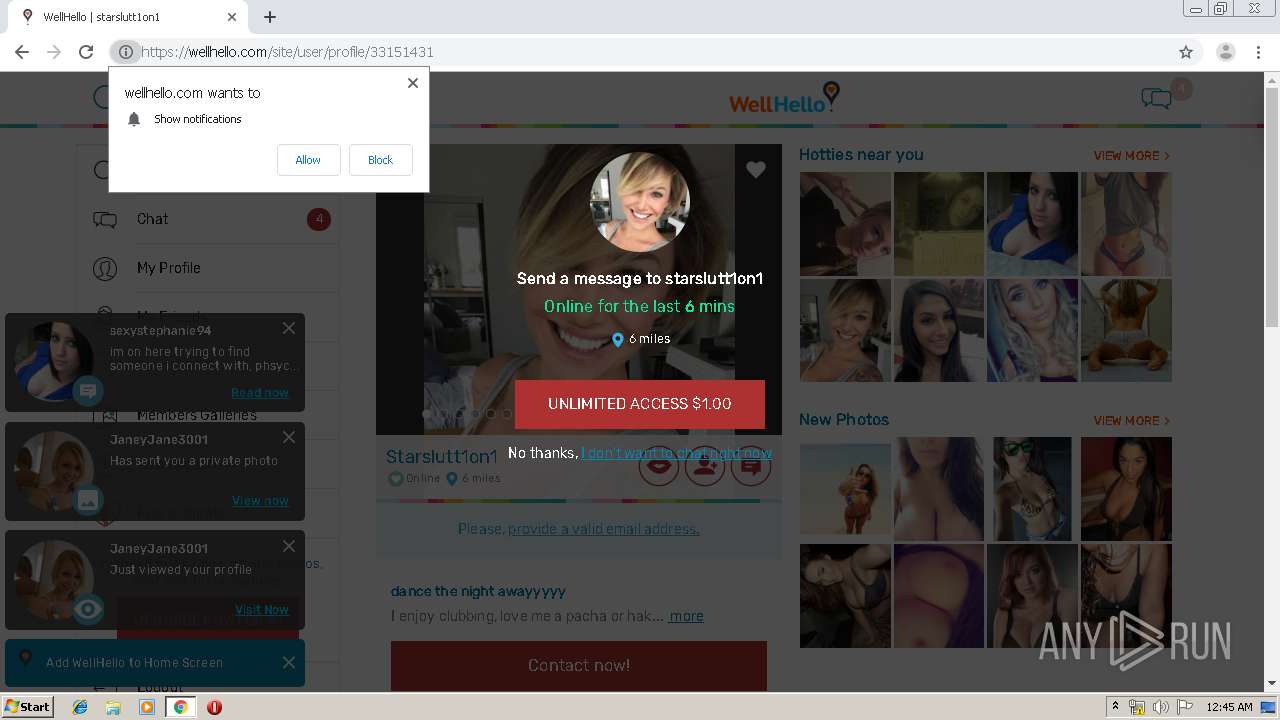
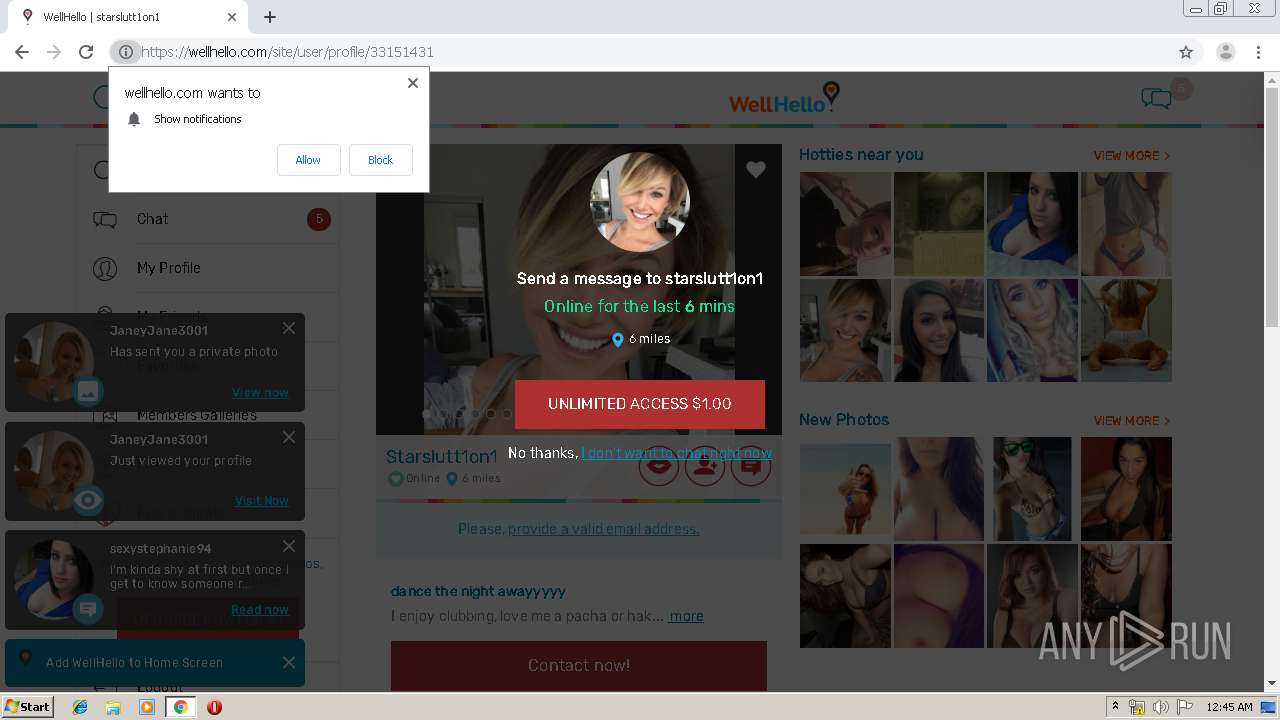
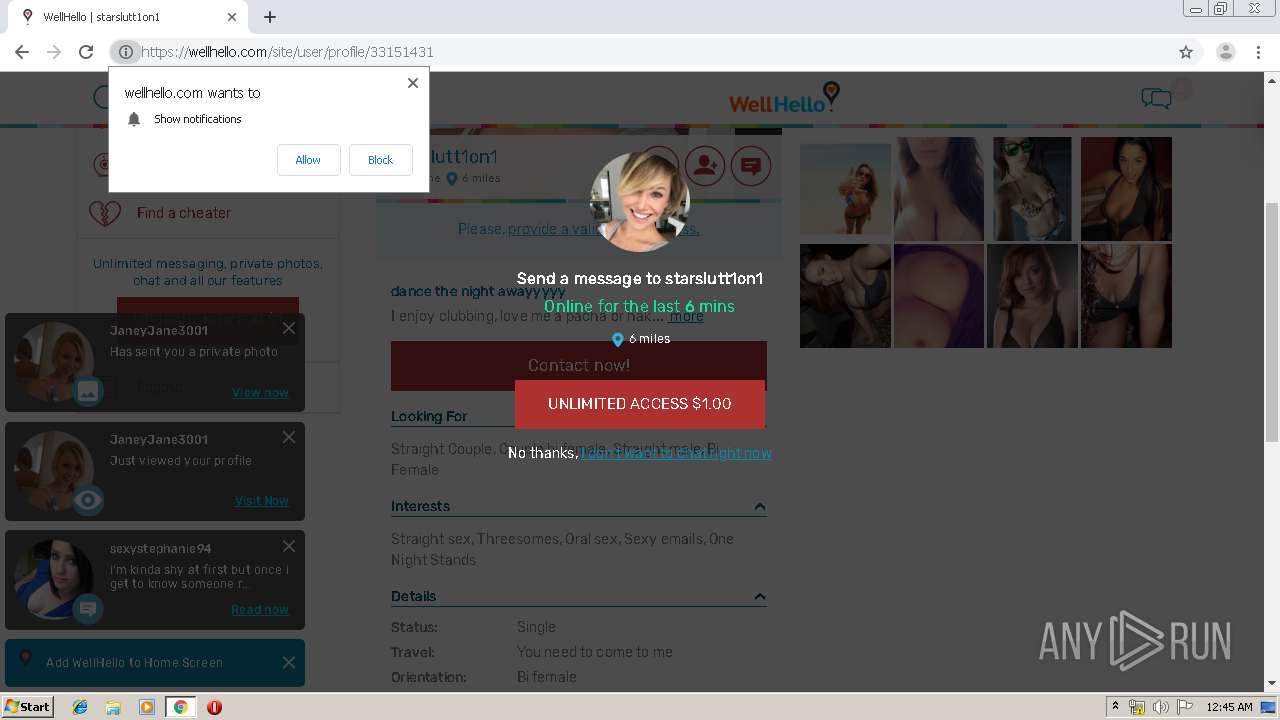
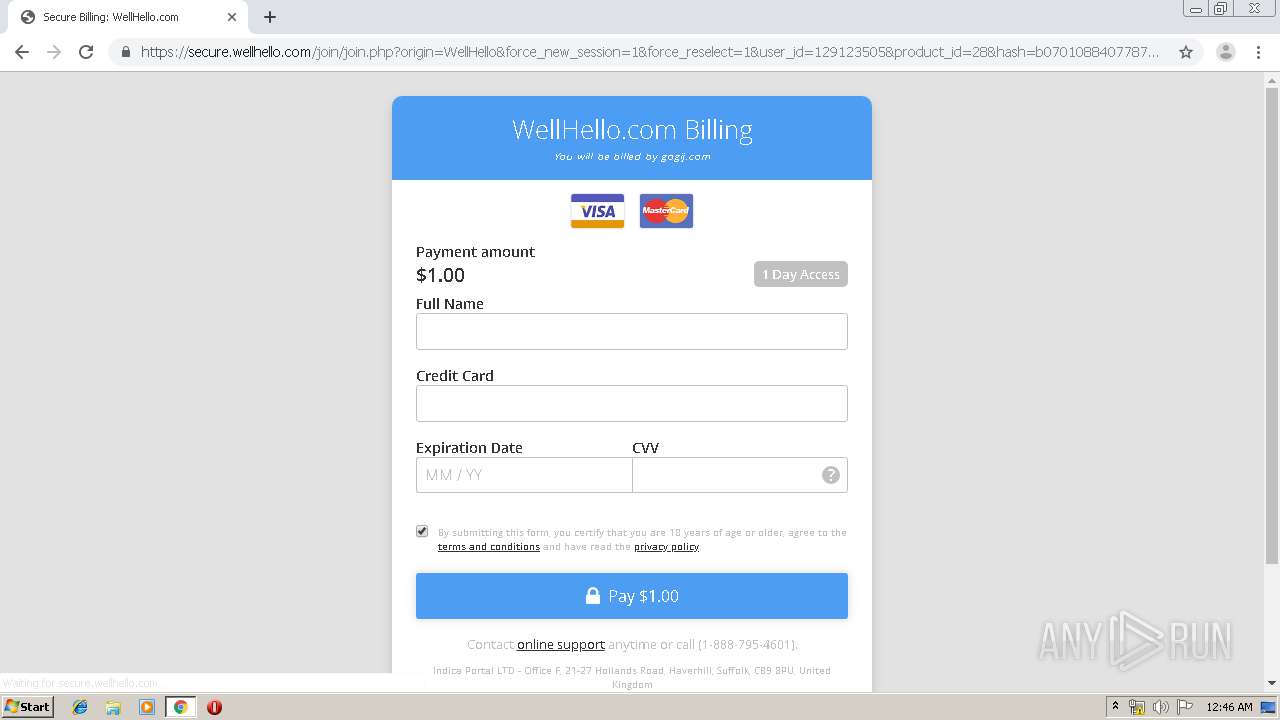
www.wellhello.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
wellhello.com |
| whitelisted |
static.wellhello.com |
| whitelisted |
js-agent.newrelic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
456 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |