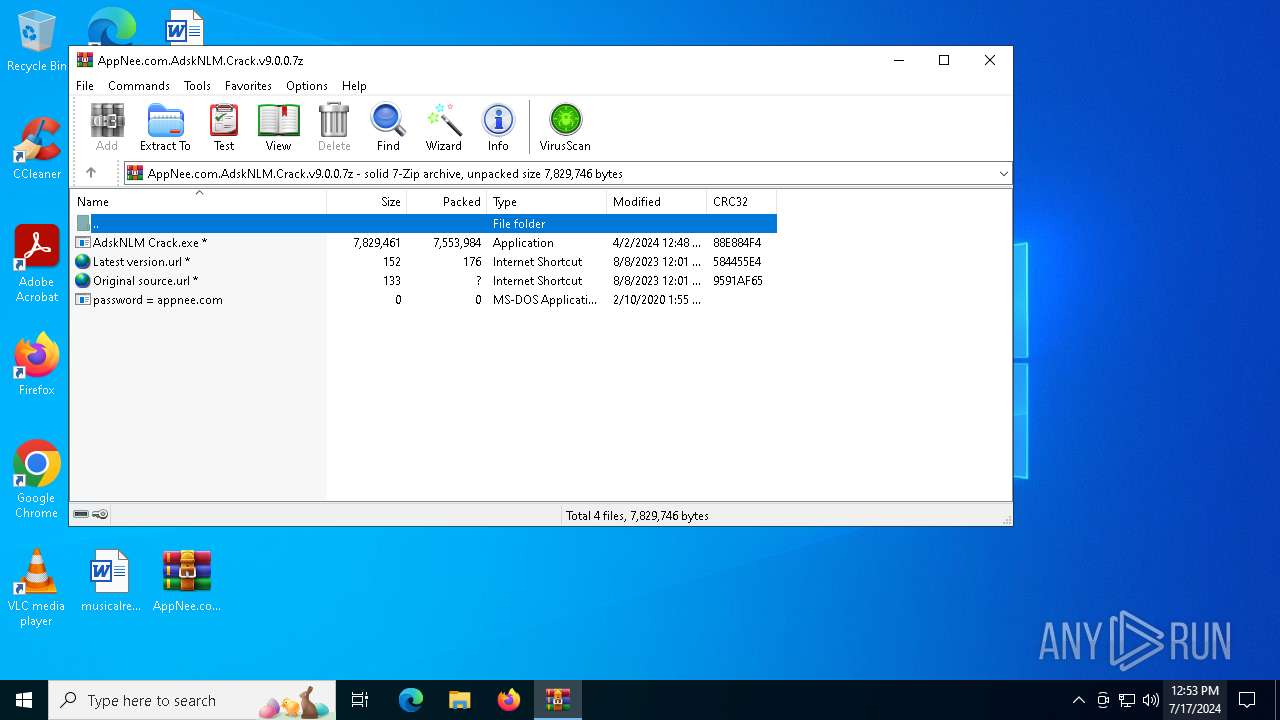
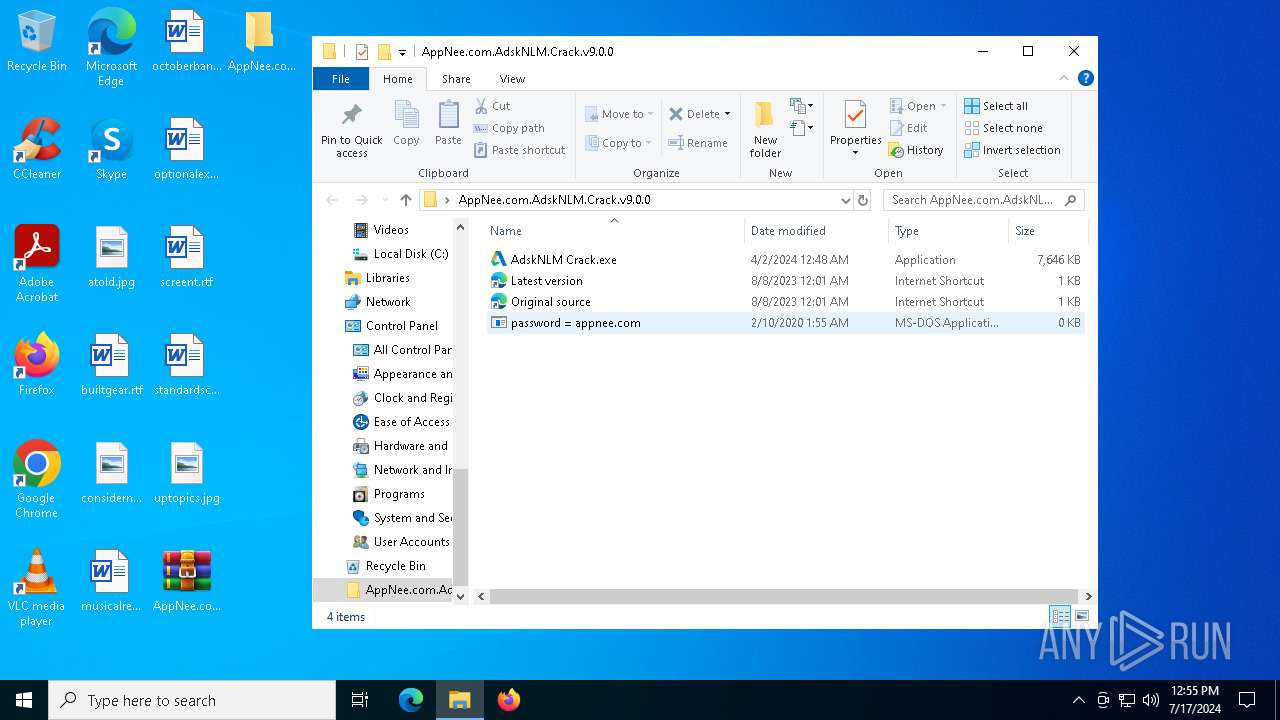
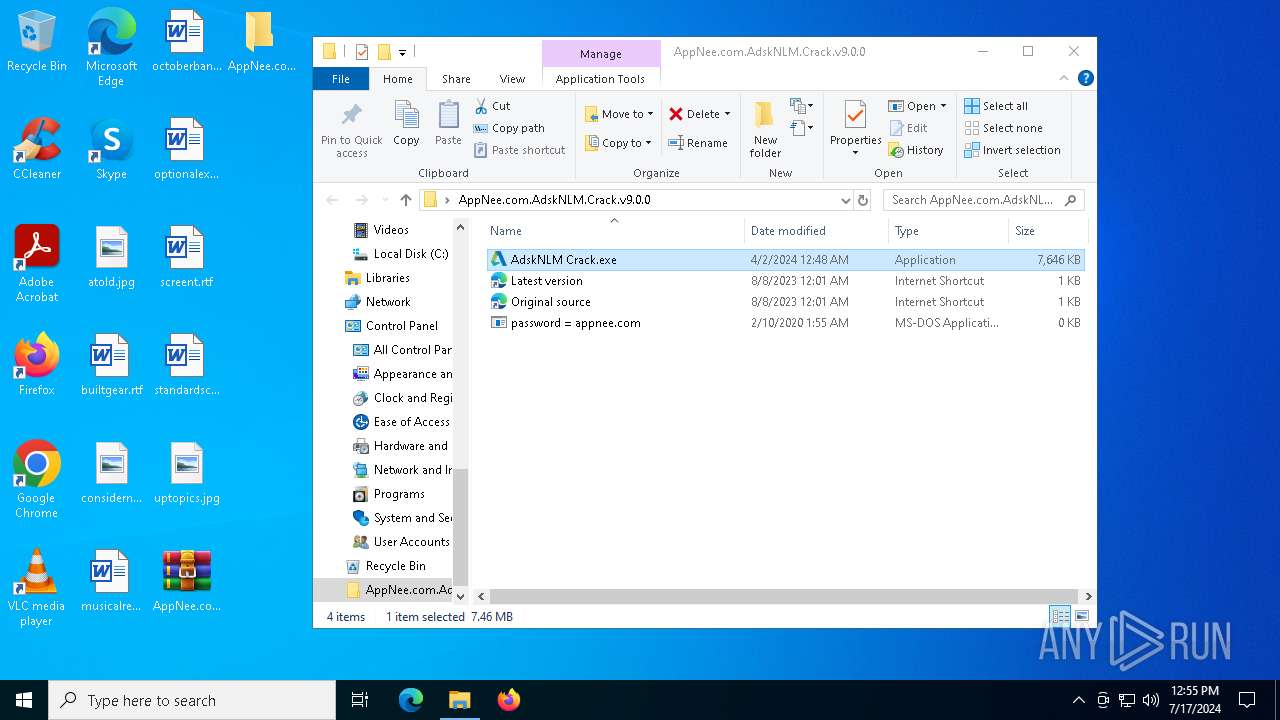
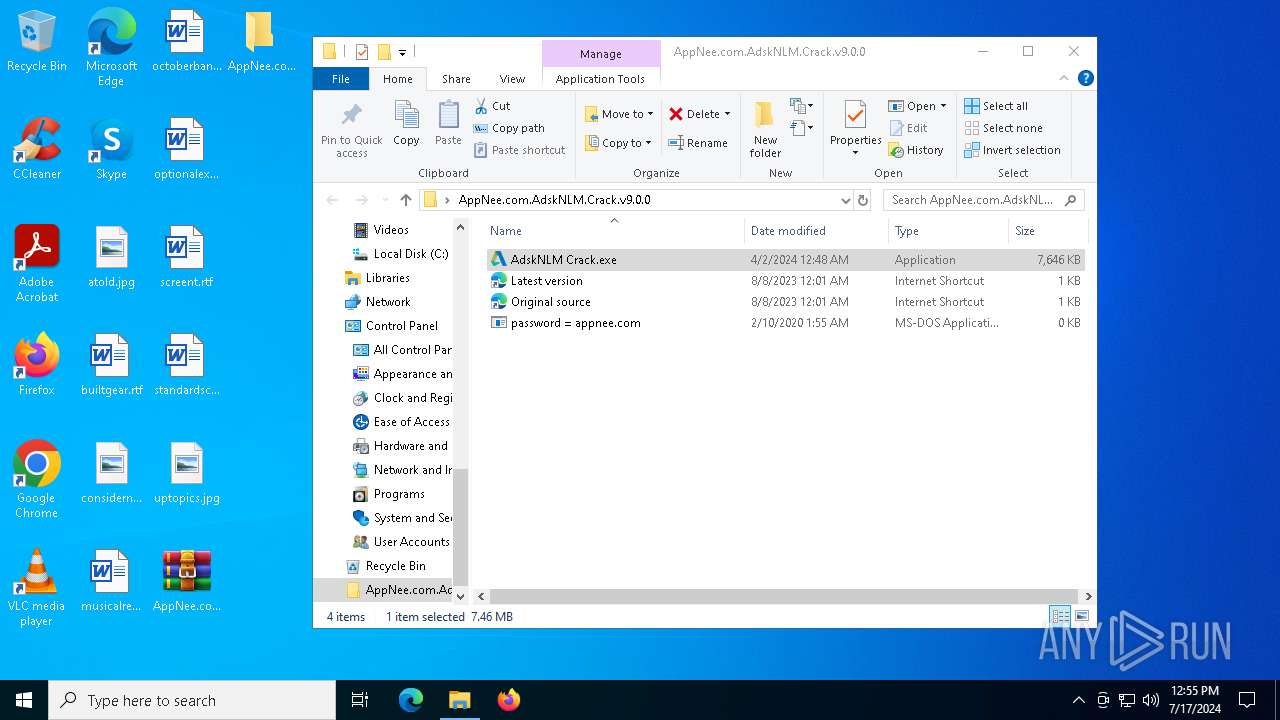
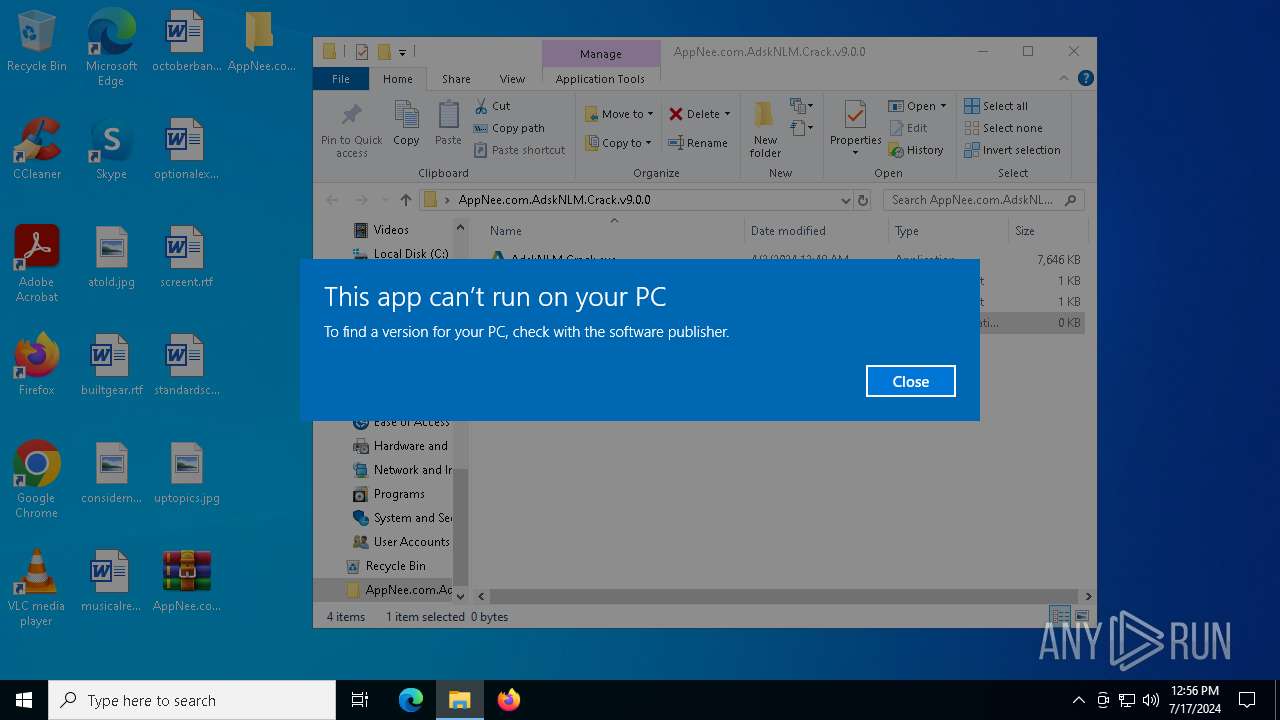
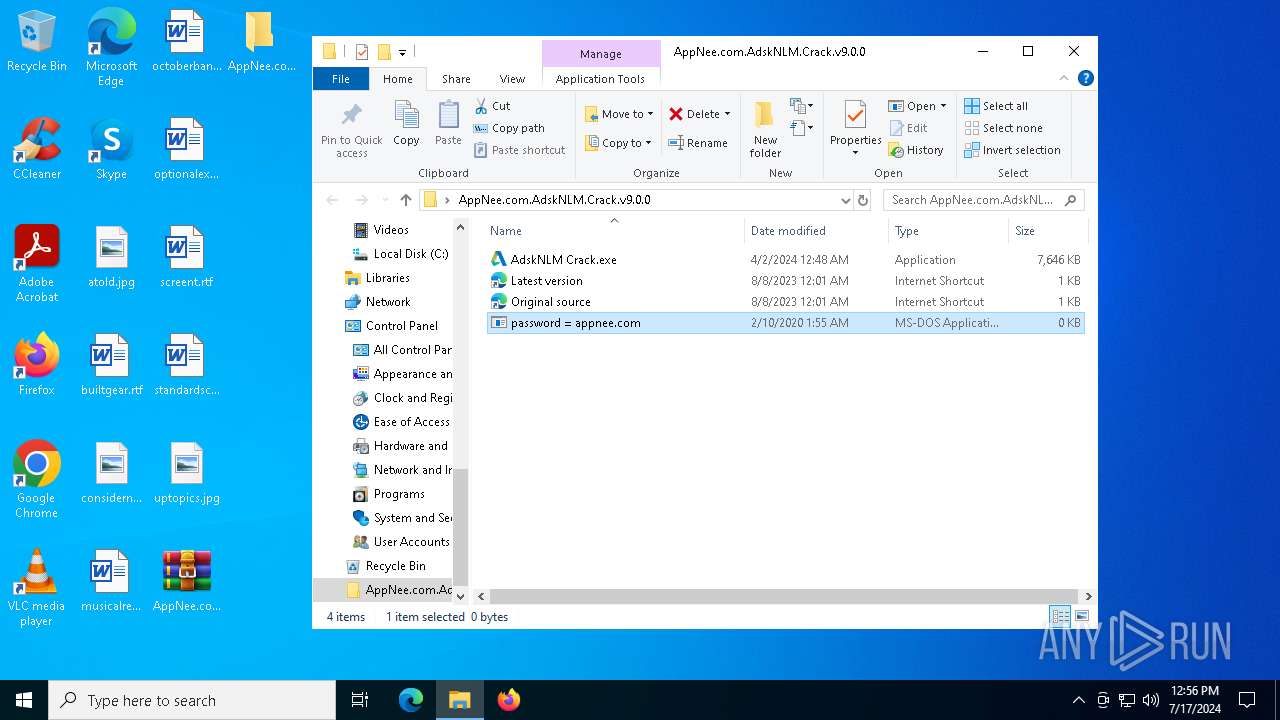
| File name: | AppNee.com.AdskNLM.Crack.v9.0.0.7z |
| Full analysis: | https://app.any.run/tasks/fccc36bf-9483-4b1e-9ccf-460a26bfcd38 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2024, 12:53:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | A86E33CEBD22B6D767B180C0AF07AF9F |
| SHA1: | 866CD4412A1669248B948E5855ACF485FE7CECFE |
| SHA256: | 454195E13D33057D9EFAA1ED13BB691805441C437D666AB6186F97BBBBED73DD |
| SSDEEP: | 98304:9cnXtCGhxZupLMAFDHd3/lUPn8kdpbqTCR9wWlUqKgTzWlGTxgpZNF73o5/GUeS/:MbEc23a8+bfONCwD5DeWc |
MALICIOUS
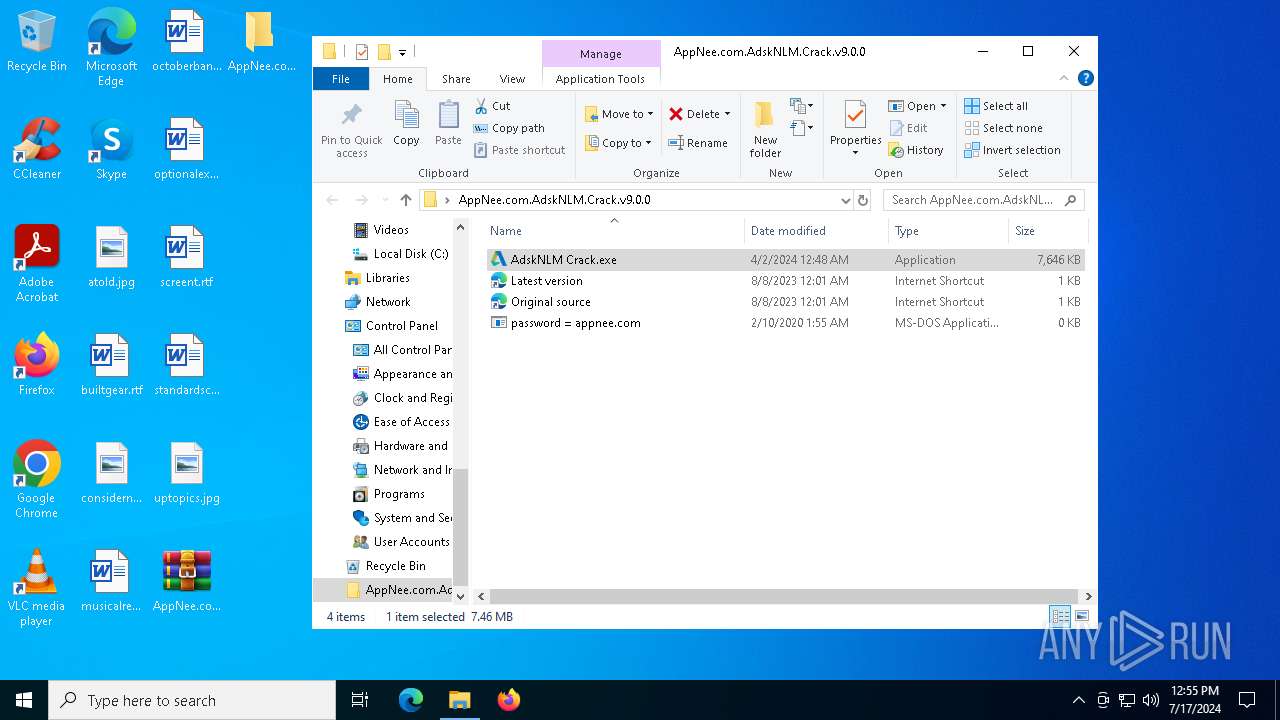
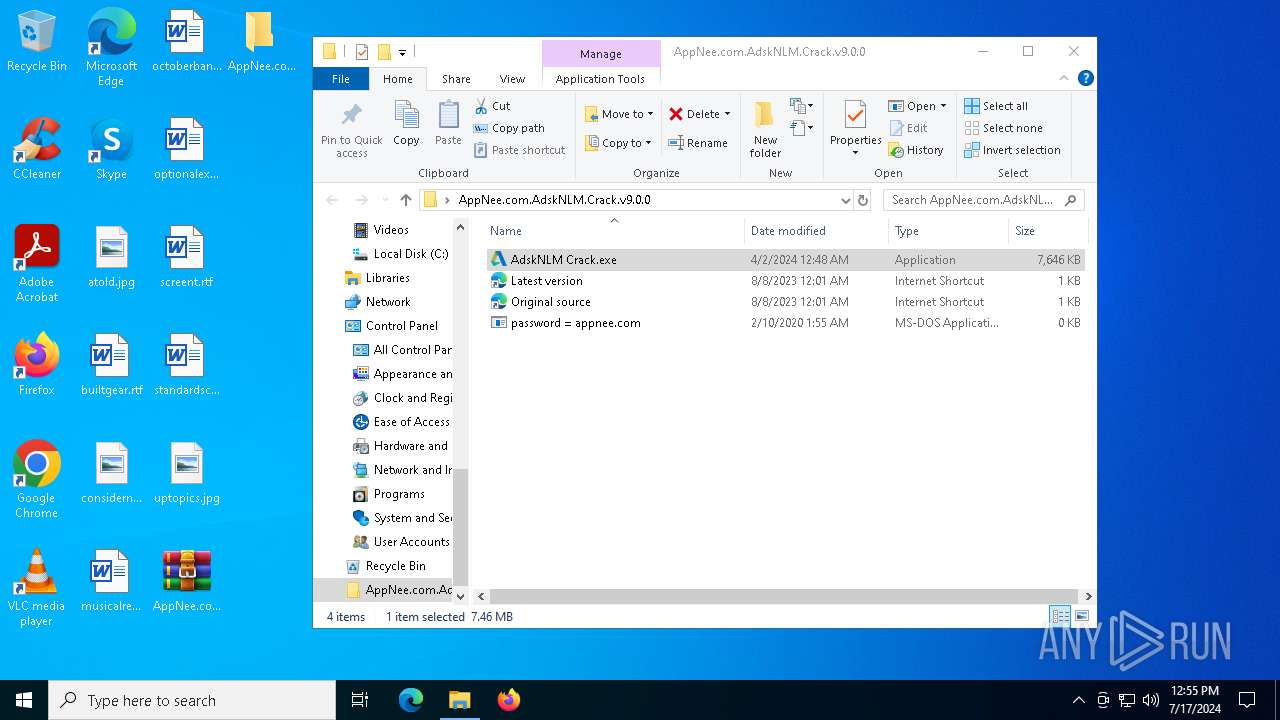
Drops the executable file immediately after the start
- AdskNLM Crack.exe (PID: 6784)
- msiexec.exe (PID: 1832)
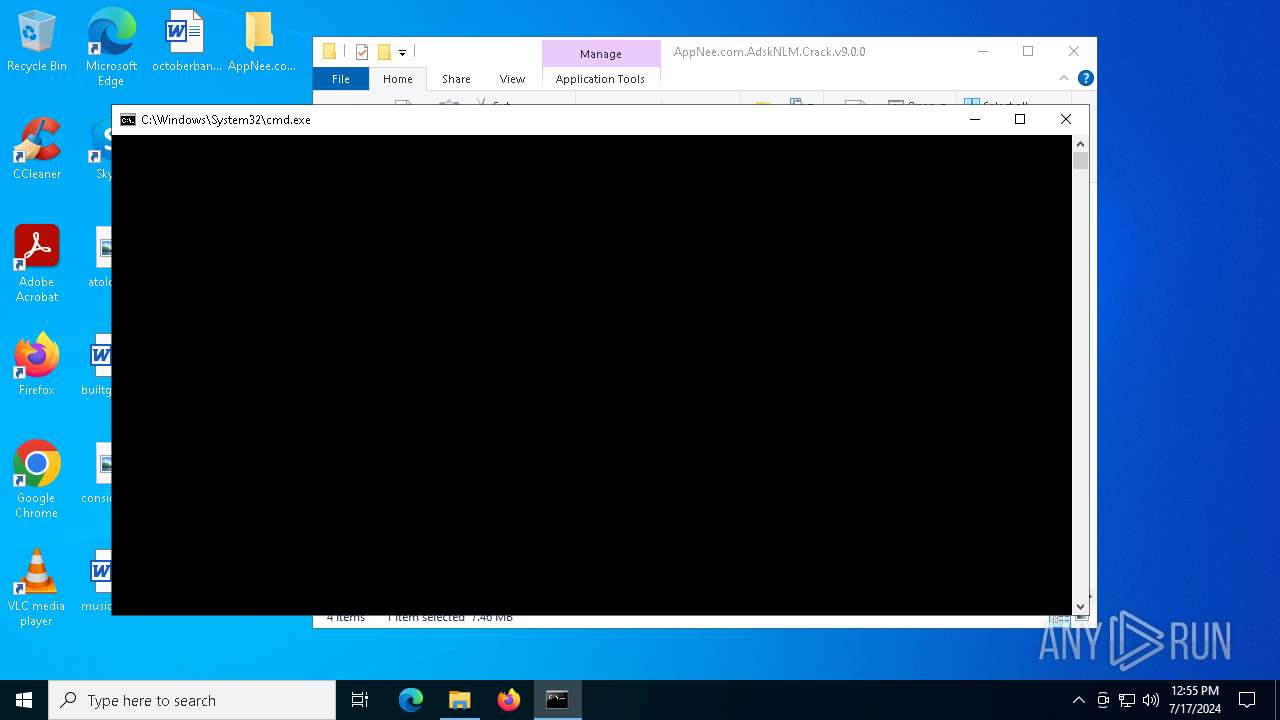
Modifies hosts file to block updates
- cmd.exe (PID: 6788)
SUSPICIOUS
Reads security settings of Internet Explorer
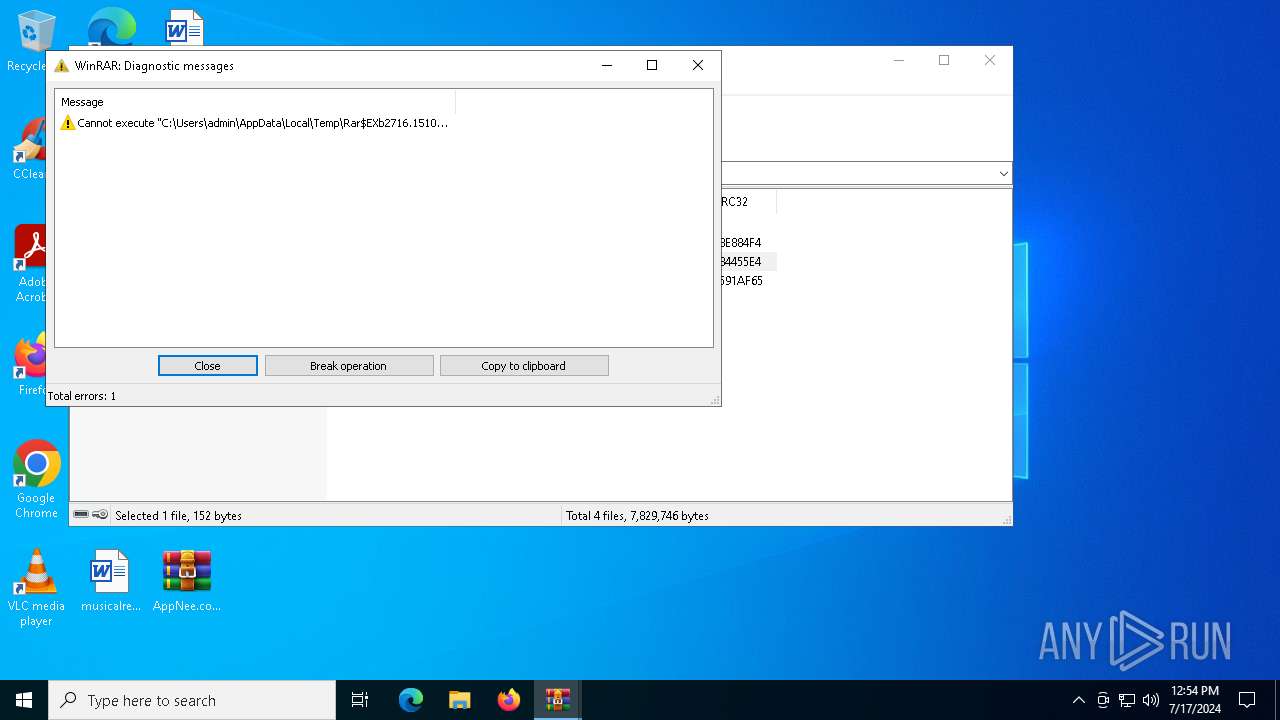
- WinRAR.exe (PID: 2716)
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 5224)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 5636)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 764)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 5284)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 3996)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 6672)
- AdskNLM Crack.exe (PID: 6740)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 4556)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 6616)
- AdskNLM Crack.exe (PID: 992)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 3392)
Application launched itself
- AdskNLM Crack.exe (PID: 6784)
- cmd.exe (PID: 6328)
- AdskNLM Crack.exe (PID: 5636)
- cmd.exe (PID: 5004)
- cmd.exe (PID: 5248)
- cmd.exe (PID: 6380)
- lmgrd.exe (PID: 6672)
Reads the date of Windows installation
- AdskNLM Crack.exe (PID: 5636)
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 5224)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 764)
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 5284)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 3996)
- AdskNLM Crack.exe (PID: 6672)
- AdskNLM Crack.exe (PID: 6740)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 4556)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 6616)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 992)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 3392)
Starts SC.EXE for service management
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 5284)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 3392)
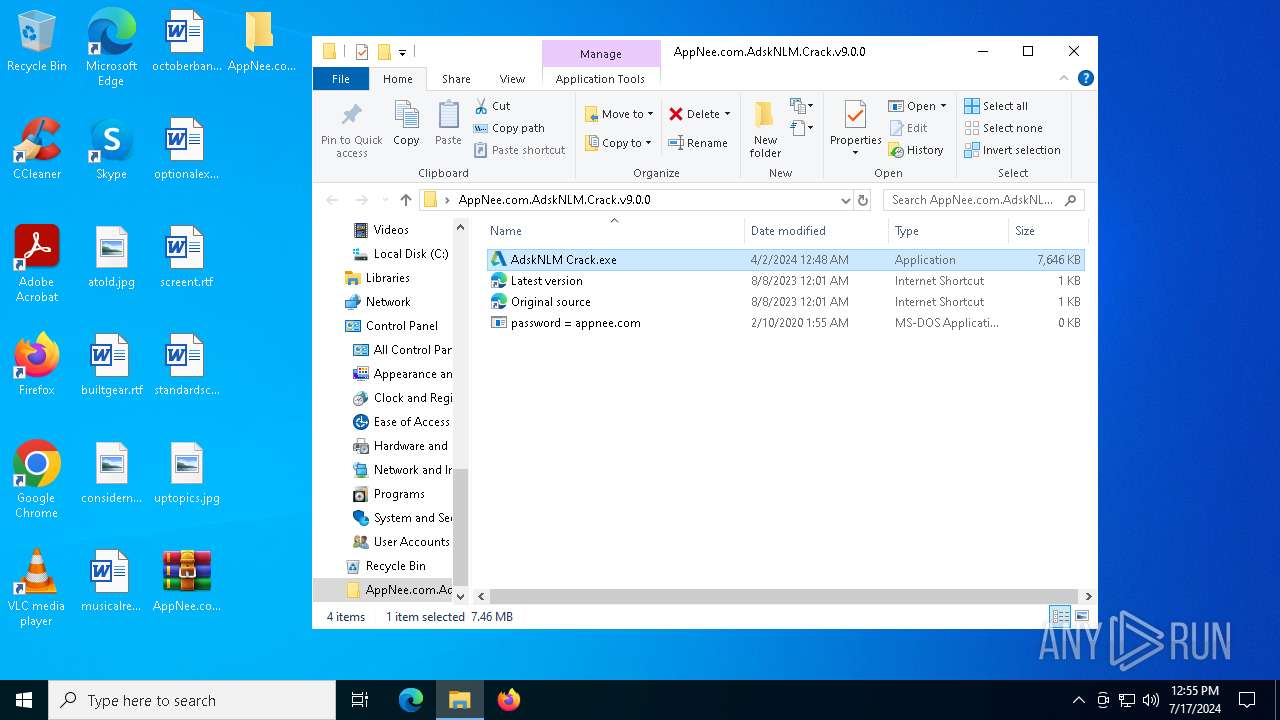
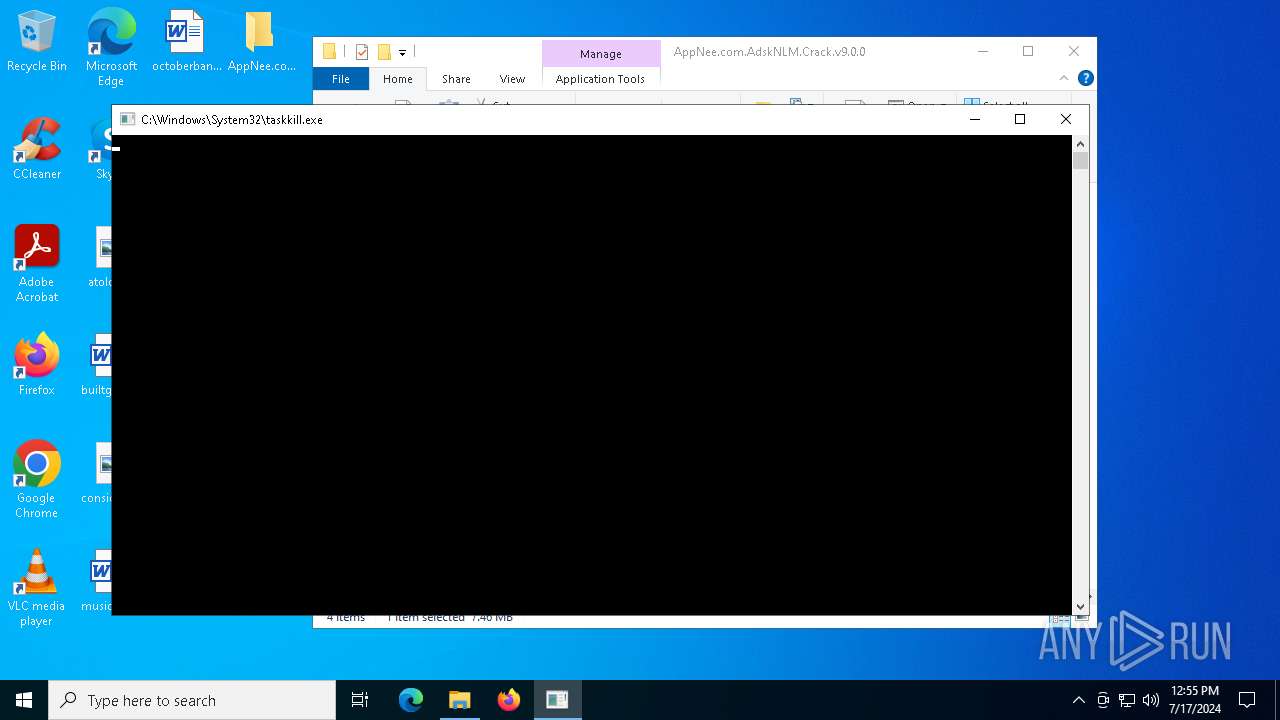
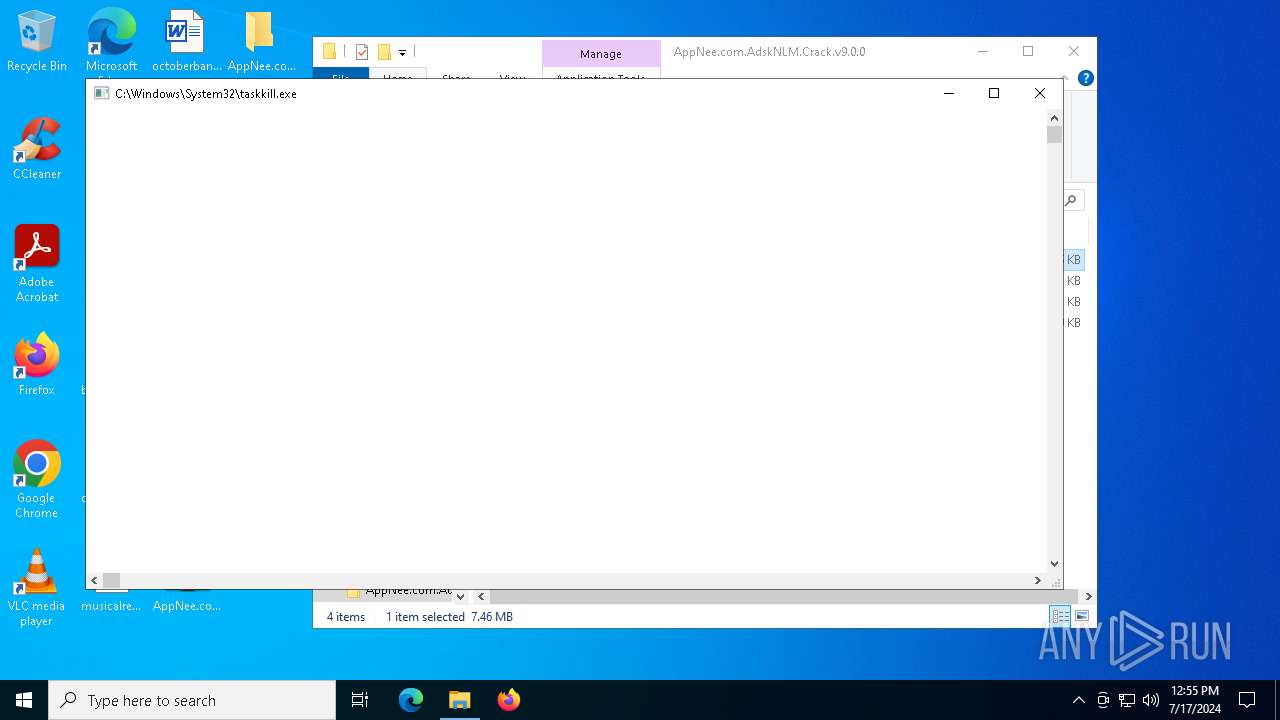
Uses TASKKILL.EXE to kill process
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 764)
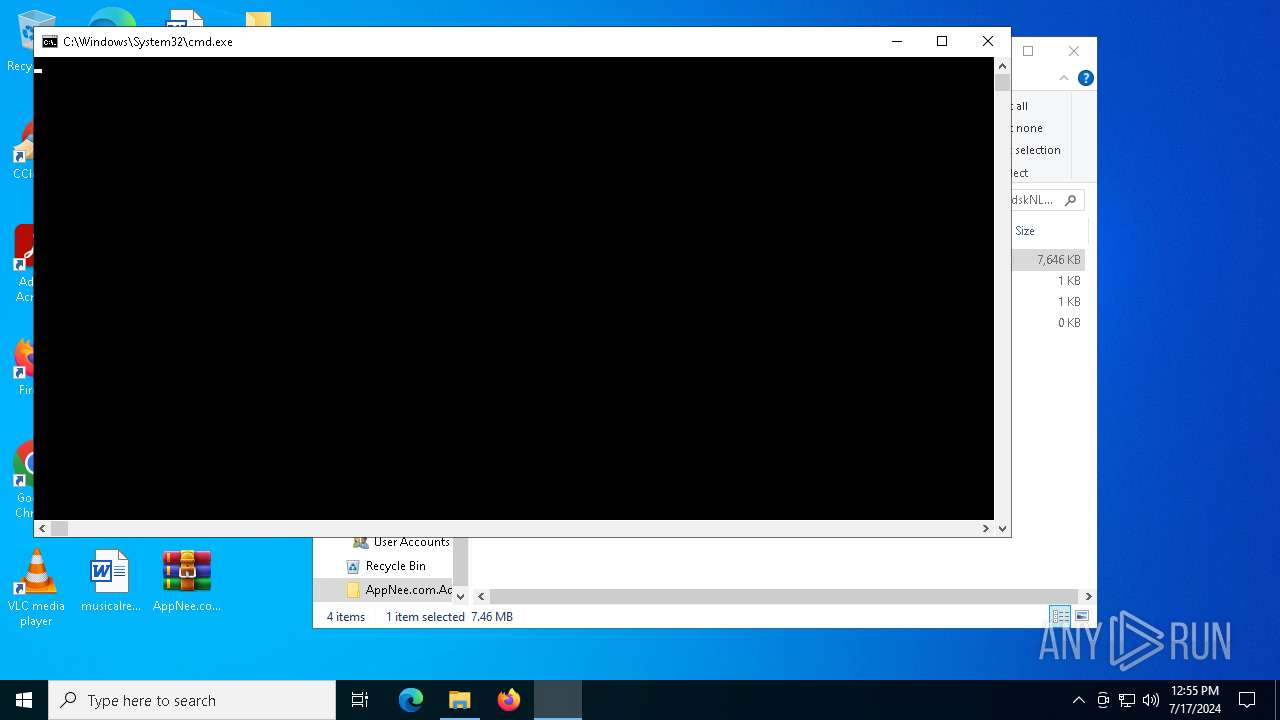
Starts CMD.EXE for commands execution
- AdskNLM Crack.exe (PID: 5224)
- cmd.exe (PID: 6328)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 3996)
- AdskNLM Crack.exe (PID: 6740)
- cmd.exe (PID: 5004)
- AdskNLM Crack.exe (PID: 4556)
- cmd.exe (PID: 5248)
- AdskNLM Crack.exe (PID: 6616)
- cmd.exe (PID: 6380)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 992)
Executable content was dropped or overwritten
- xcopy.exe (PID: 5324)
- AdskNLM Crack.exe (PID: 6784)
Process copies executable file
- cmd.exe (PID: 6328)
- cmd.exe (PID: 5004)
Uses REG/REGEDIT.EXE to modify registry
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 1272)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4728)
- cmd.exe (PID: 6700)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 6180)
Checks Windows Trust Settings
- msiexec.exe (PID: 1832)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1832)
Executes as Windows Service
- lmgrd.exe (PID: 6672)
There is functionality for VM detection (VMWare)
- adskflex.exe (PID: 6916)
- lmgrd.exe (PID: 6672)
- lmgrd.exe (PID: 7032)
There is functionality for VM detection (VirtualBox)
- lmgrd.exe (PID: 6672)
- lmgrd.exe (PID: 7032)
- adskflex.exe (PID: 6916)
There is functionality for VM detection (antiVM strings)
- lmgrd.exe (PID: 6672)
- lmgrd.exe (PID: 7032)
- adskflex.exe (PID: 6916)
INFO
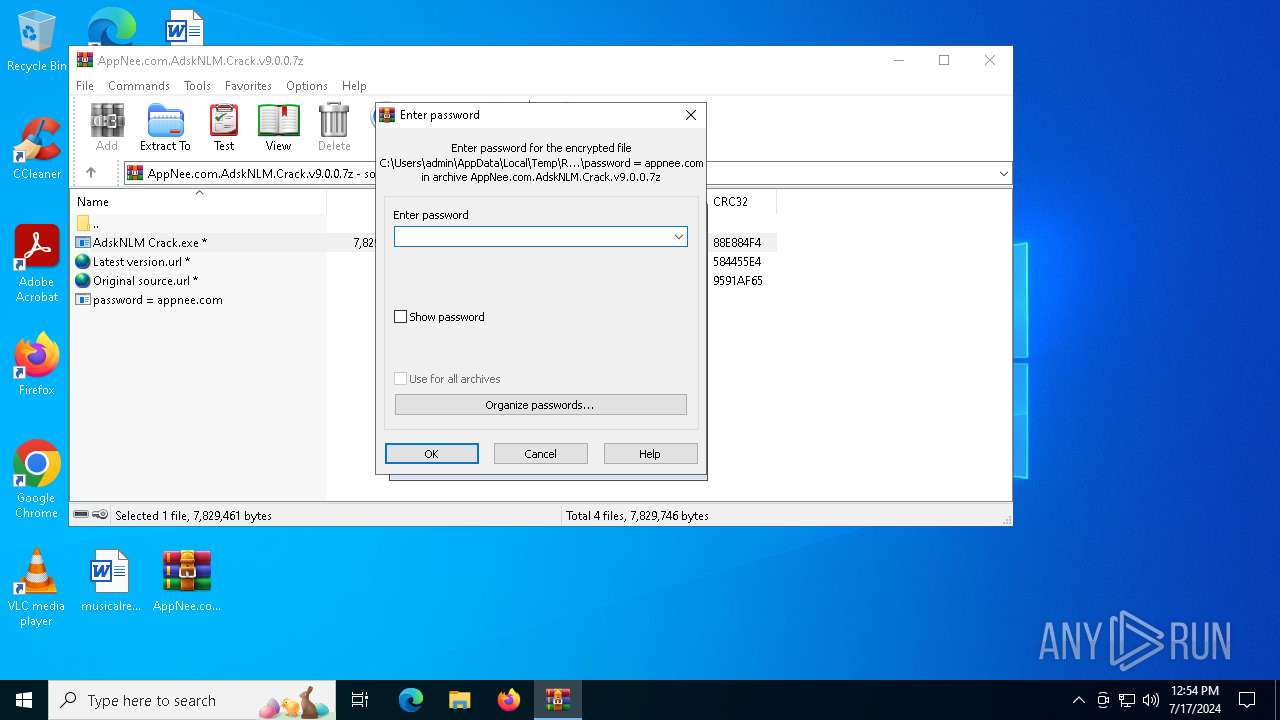
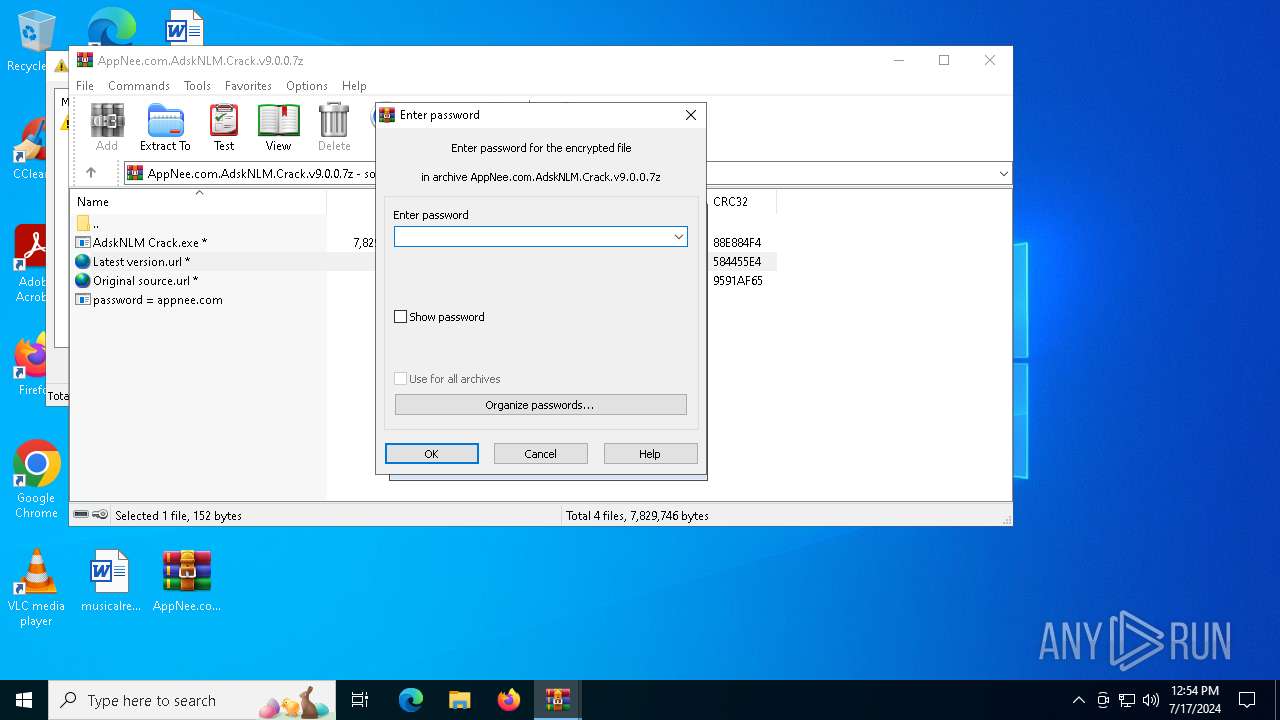
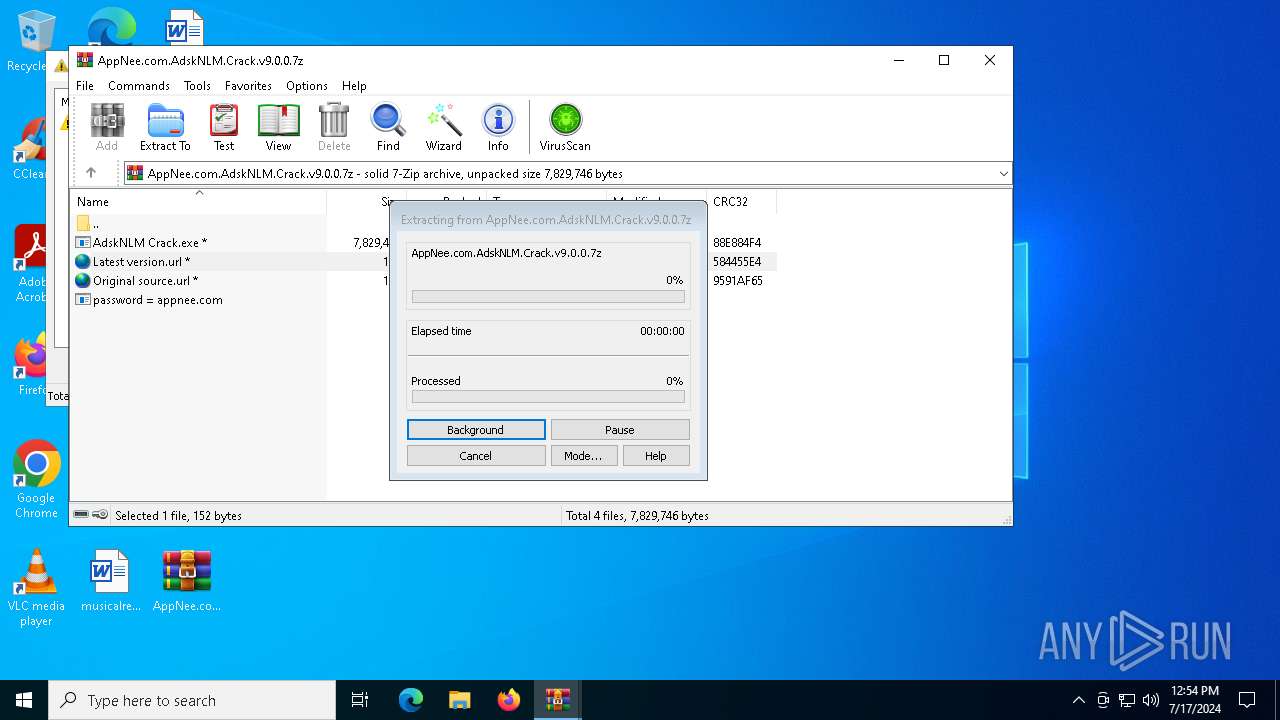
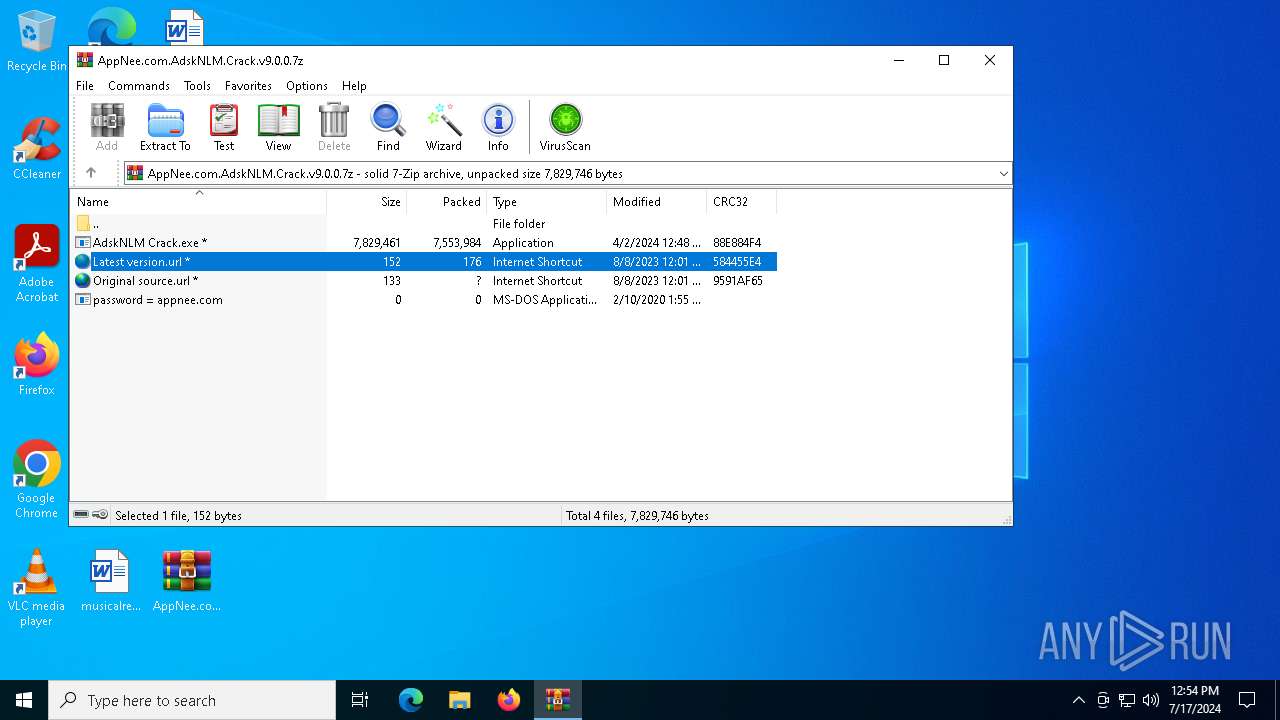
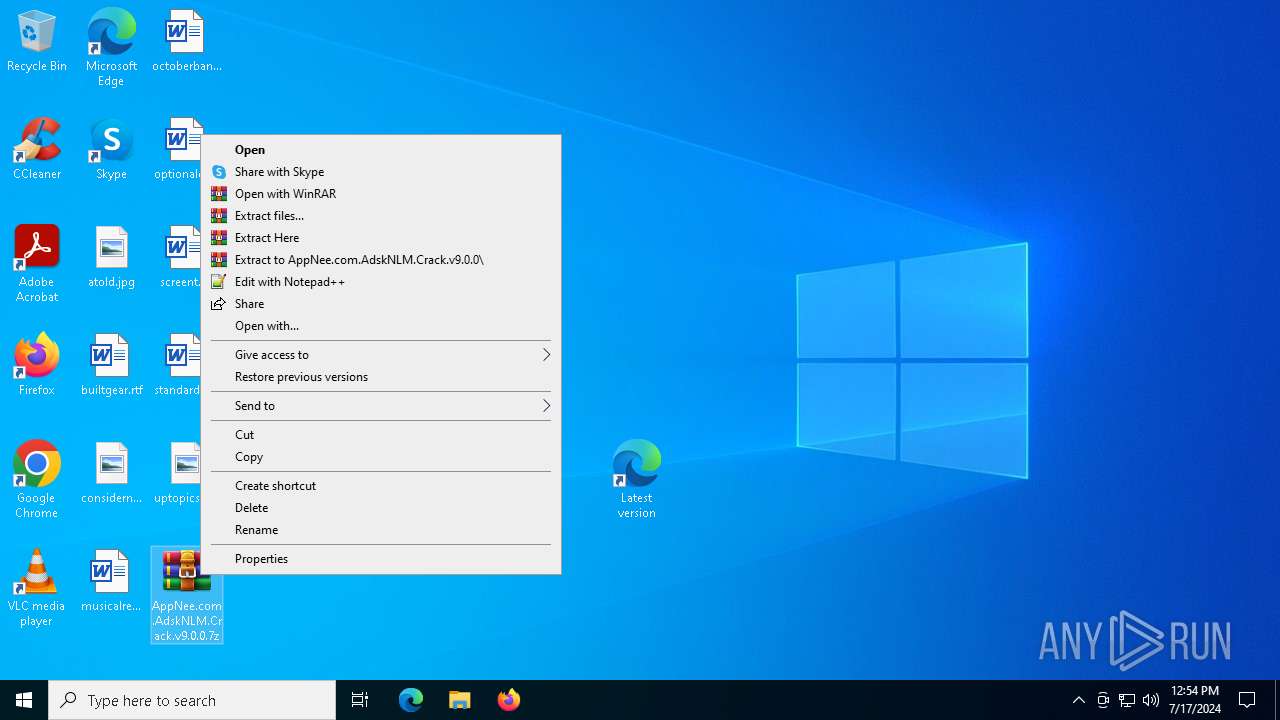
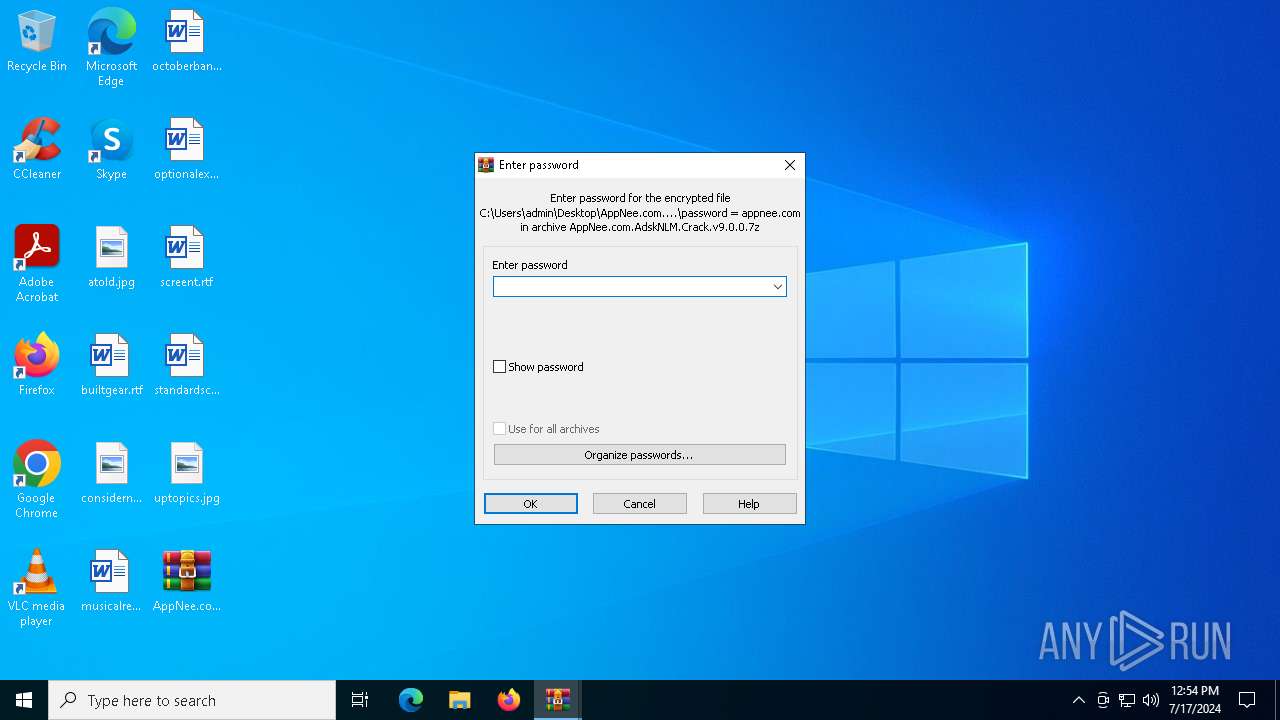
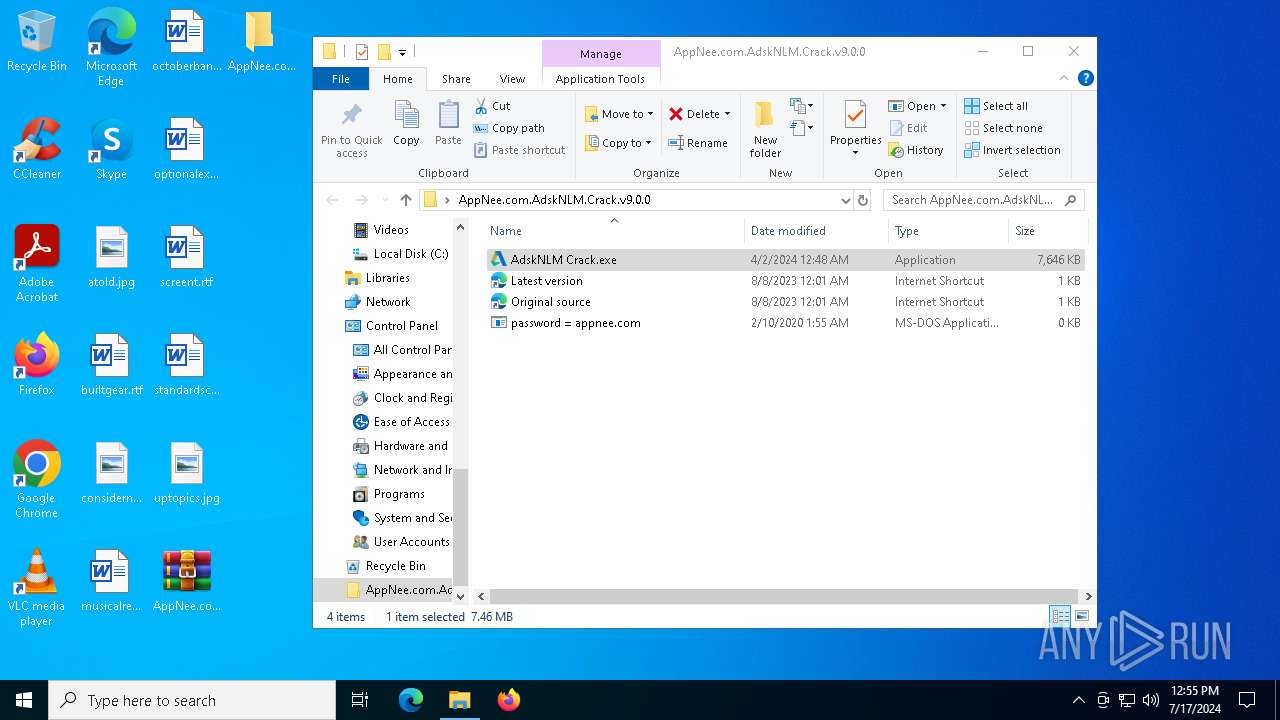
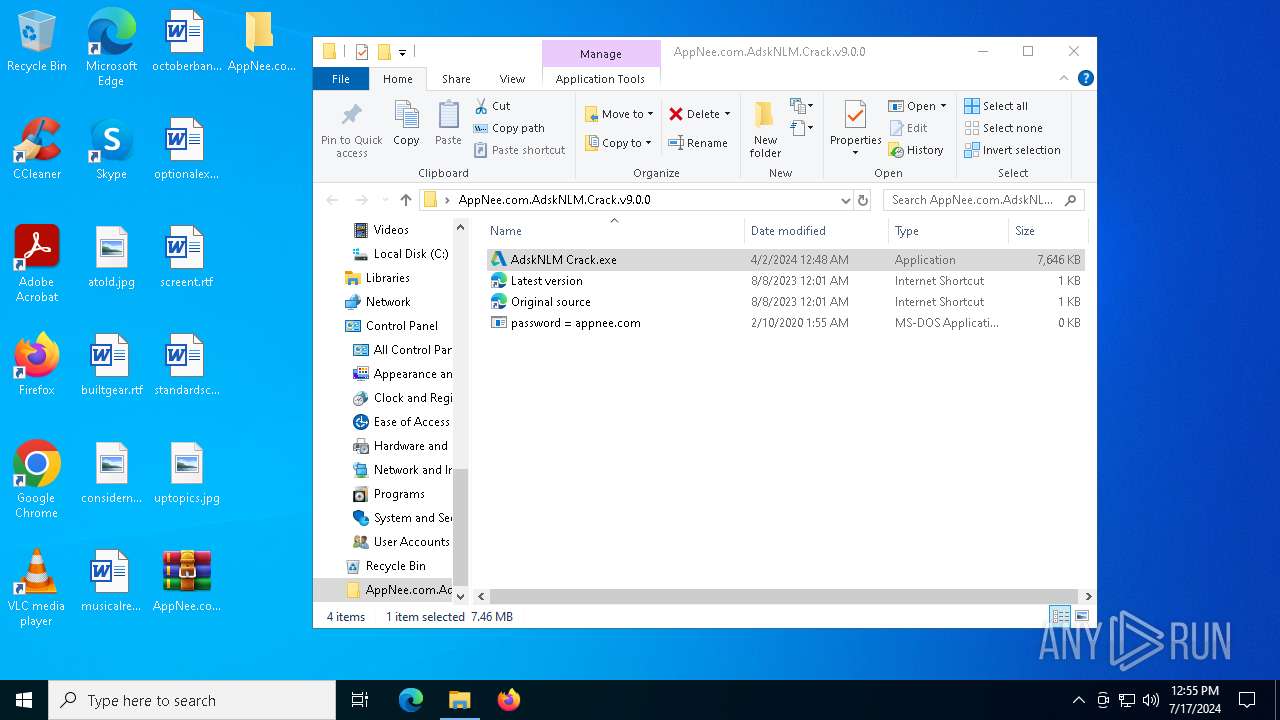
Manual execution by a user
- WinRAR.exe (PID: 6492)
- AdskNLM Crack.exe (PID: 5636)
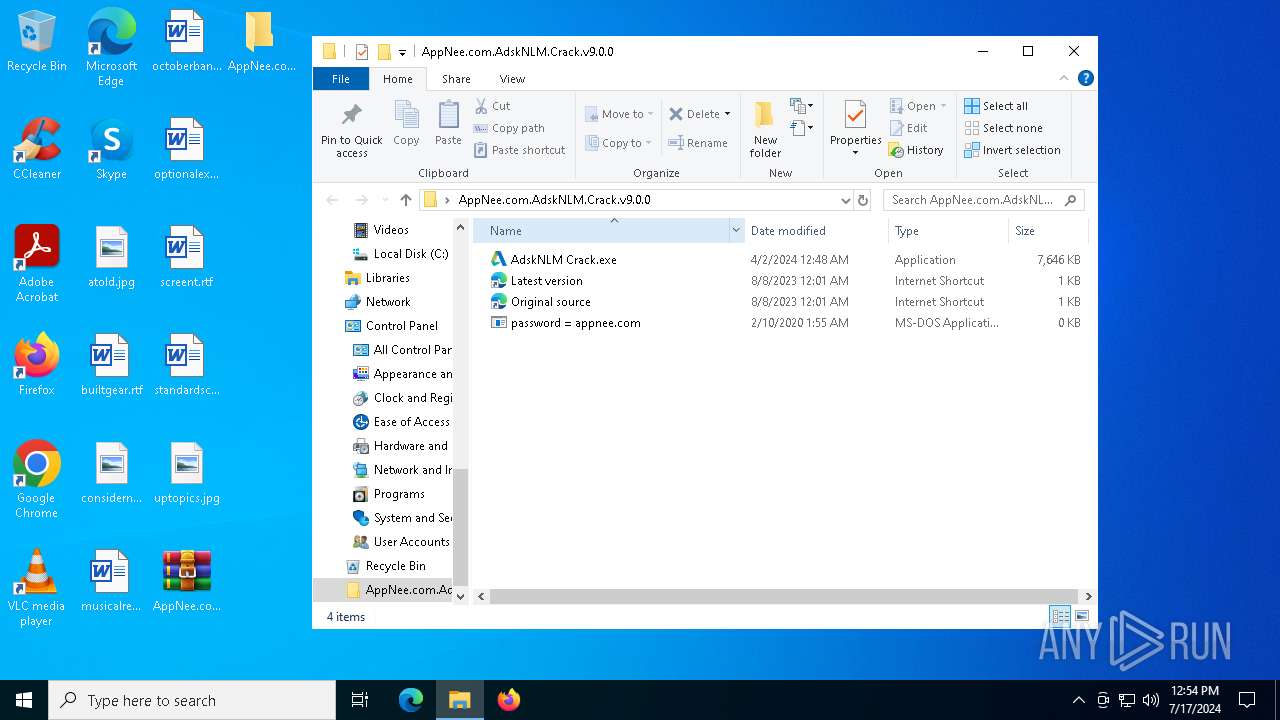
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6492)
- xcopy.exe (PID: 5324)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6492)
- msiexec.exe (PID: 1832)
Checks supported languages
- AdskNLM Crack.exe (PID: 5636)
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 5224)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 764)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 5284)
- msiexec.exe (PID: 1832)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 3996)
- msiexec.exe (PID: 3936)
- AdskNLM Crack.exe (PID: 6672)
- AdskNLM Crack.exe (PID: 6740)
- msiexec.exe (PID: 4800)
- msiexec.exe (PID: 884)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 4556)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 6616)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 3392)
- AdskNLM Crack.exe (PID: 992)
- lmgrd.exe (PID: 6672)
- lmgrd.exe (PID: 7032)
- adskflex.exe (PID: 6916)
Reads the computer name
- AdskNLM Crack.exe (PID: 5636)
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 5224)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 764)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 5284)
- msiexec.exe (PID: 1832)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 3996)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 6672)
- msiexec.exe (PID: 884)
- AdskNLM Crack.exe (PID: 6740)
- msiexec.exe (PID: 3936)
- msiexec.exe (PID: 4800)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 4556)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 6616)
- AdskNLM Crack.exe (PID: 992)
- AdskNLM Crack.exe (PID: 2108)
- lmgrd.exe (PID: 6672)
- lmgrd.exe (PID: 7032)
- AdskNLM Crack.exe (PID: 3392)
- adskflex.exe (PID: 6916)
Process checks computer location settings
- AdskNLM Crack.exe (PID: 4316)
- AdskNLM Crack.exe (PID: 3164)
- AdskNLM Crack.exe (PID: 5224)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 4944)
- AdskNLM Crack.exe (PID: 6036)
- AdskNLM Crack.exe (PID: 6572)
- AdskNLM Crack.exe (PID: 5636)
- AdskNLM Crack.exe (PID: 6272)
- AdskNLM Crack.exe (PID: 6588)
- AdskNLM Crack.exe (PID: 6736)
- AdskNLM Crack.exe (PID: 1052)
- AdskNLM Crack.exe (PID: 3128)
- AdskNLM Crack.exe (PID: 6832)
- AdskNLM Crack.exe (PID: 5516)
- AdskNLM Crack.exe (PID: 448)
- AdskNLM Crack.exe (PID: 4456)
- AdskNLM Crack.exe (PID: 6100)
- AdskNLM Crack.exe (PID: 764)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 452)
- AdskNLM Crack.exe (PID: 6784)
- AdskNLM Crack.exe (PID: 3108)
- AdskNLM Crack.exe (PID: 5284)
- AdskNLM Crack.exe (PID: 5532)
- AdskNLM Crack.exe (PID: 1280)
- AdskNLM Crack.exe (PID: 2252)
- AdskNLM Crack.exe (PID: 6224)
- AdskNLM Crack.exe (PID: 6192)
- AdskNLM Crack.exe (PID: 4308)
- AdskNLM Crack.exe (PID: 7068)
- AdskNLM Crack.exe (PID: 6744)
- AdskNLM Crack.exe (PID: 6672)
- AdskNLM Crack.exe (PID: 3996)
- AdskNLM Crack.exe (PID: 6740)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 4556)
- AdskNLM Crack.exe (PID: 6856)
- AdskNLM Crack.exe (PID: 6364)
- AdskNLM Crack.exe (PID: 2272)
- AdskNLM Crack.exe (PID: 6520)
- AdskNLM Crack.exe (PID: 376)
- AdskNLM Crack.exe (PID: 7132)
- AdskNLM Crack.exe (PID: 6980)
- AdskNLM Crack.exe (PID: 7016)
- AdskNLM Crack.exe (PID: 2472)
- AdskNLM Crack.exe (PID: 6188)
- AdskNLM Crack.exe (PID: 3596)
- AdskNLM Crack.exe (PID: 6616)
- AdskNLM Crack.exe (PID: 6372)
- AdskNLM Crack.exe (PID: 1272)
- AdskNLM Crack.exe (PID: 992)
- AdskNLM Crack.exe (PID: 2108)
- AdskNLM Crack.exe (PID: 3392)
Creates files in the program directory
- xcopy.exe (PID: 5324)
- xcopy.exe (PID: 7088)
- adskflex.exe (PID: 6916)
Create files in a temporary directory
- AdskNLM Crack.exe (PID: 6784)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 2336)
- WMIC.exe (PID: 2012)
- WMIC.exe (PID: 3156)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1832)
Reads the software policy settings
- msiexec.exe (PID: 1832)
Application launched itself
- msiexec.exe (PID: 1832)
Creates files or folders in the user directory
- msiexec.exe (PID: 1832)
- xcopy.exe (PID: 6240)
Creates a software uninstall entry
- msiexec.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
328
Monitored processes
184
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | "C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe" -sfxwaitall:0 "reg" add "HKLM\SOFTWARE\WOW6432Node\FLEXlm License Manager\AdskNLM" /v "Lmgrd" /d "C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe" /f | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe | — | AdskNLM Crack.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 448 | "C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe" -sfxwaitall:0 "sc" start AdskLicensingService | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe | — | AdskNLM Crack.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 452 | "C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe" -sfxwaitall:0 "taskkill" /f /im "AdskAccessCore.exe" | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe | — | AdskNLM Crack.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | "C:\Windows\System32\reg.exe" add "HKCU\SOFTWARE\Autodesk\MC3" /v "ADARePrompted" /t "REG_DWORD" /d "1" /f | C:\Windows\System32\reg.exe | — | AdskNLM Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 764 | "C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe" -sfxwaitall:0 "taskkill" /f /im "Autodesk Access UI Host.exe" | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe | — | AdskNLM Crack.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 884 | C:\Windows\syswow64\MsiExec.exe -Embedding 29EDA0528D24364559EBBE3F0CAD69D3 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) | |||||||||||||||
Total events
73 185
Read events
72 844
Write events
332
Delete events
9
Modification events
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0.7z | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-10046 |
Value: Internet Shortcut | |||
| (PID) Process: | (2716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
16
Suspicious files
27
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm11-19-4-1-ipv4-ipv6-win64.msi | — | |
MD5:— | SHA256:— | |||
| 1832 | msiexec.exe | C:\WINDOWS\Installer\1e6417.msi | — | |
MD5:— | SHA256:— | |||
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\adskflex.exe | executable | |
MD5:E974687B0135A662623056078A8E58E1 | SHA256:82BE4EC8BA546EBF1E3448976D06E163E9C4E258301CFCEB9CE8A2D76ECBD6AE | |||
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\UnNamed.json | binary | |
MD5:BA3088F87EDFCCEB1E084C971DB40601 | SHA256:E0371582686D18B48EDB9E956057B52AA97DE8C034EE79AAB10FFB5331711651 | |||
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm.mst | binary | |
MD5:29810BAB1EF69A3D26872093EF09372B | SHA256:90E413CD675EE085C441DF6327F6661A3459F4E109E0684B1A361C050D672BDB | |||
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version.dll | executable | |
MD5:44774FAFD716FA45C7A0CCB3B14D59A6 | SHA256:4739ABFF4DA13A27F2421452007C9D2340BF4F9E9A601EF0EC9F1B9D64D1D365 | |||
| 6492 | WinRAR.exe | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\AdskNLM Crack.exe | executable | |
MD5:7C43835AAC7F366CE2075A0D8DB8C334 | SHA256:982EC5CDEA22801121C7FA31D23FB69CCA07167928DB33540594F6ACBCD79883 | |||
| 6492 | WinRAR.exe | C:\Users\admin\Desktop\AppNee.com.AdskNLM.Crack.v9.0.0\Latest version.url | url | |
MD5:5CAD3BBBEBA4E12BA41B4318EC2BA8A4 | SHA256:B89F4933A6303178B3ED5A59890F39FC0EB7C61FCE2BF6C10369D81675164196 | |||
| 6784 | AdskNLM Crack.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\delnowmic.ps1 | text | |
MD5:67924FF023F149E8B467A8905FF1B4FC | SHA256:4B5EF379990A4663A3341913B0BD4FEDF906B9F6AF8D8FA0CB8BEE4A09FF92F9 | |||
| 2716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2716.16396\Latest version.url | url | |
MD5:5CAD3BBBEBA4E12BA41B4318EC2BA8A4 | SHA256:B89F4933A6303178B3ED5A59890F39FC0EB7C61FCE2BF6C10369D81675164196 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
78
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4004 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4092 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4092 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6916 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5132 | WmiPrvSE.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6844 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5132 | WmiPrvSE.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1888 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1292 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2072 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1888 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1888 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1888 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2072 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |