| File name: | calc.exe |
| Full analysis: | https://app.any.run/tasks/a88758dd-c67d-474f-9ae5-5911899119e5 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 14:50:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3DB905BAEC59FE849D1EE4226C75B81B |
| SHA1: | 553447C9FCC445170B7878F059B3851DB3AEDF9B |
| SHA256: | 4535F1CD7C2FEA55AEA3B352DB5C3C98370BCF3492AAE5A76015185B7B905145 |
| SSDEEP: | 1536:h3d66NC1fy7yEy/5+fX6hDVUdbmARMiMtY7JSvbAgL4HhqlBsWW1N69liBKwAyt:Tw+CIaDWKAeI7QbLL4Hhn71ugB5N |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- azplsot.exe (PID: 3588)
Application was dropped or rewritten from another process
- azplsot.exe (PID: 3588)
SUSPICIOUS
Executable content was dropped or overwritten
- calc.exe (PID: 1476)
- cmd.exe (PID: 3844)
Starts CMD.EXE for commands execution
- calc.exe (PID: 1476)
Starts SC.EXE for service management
- calc.exe (PID: 1476)
Uses NETSH.EXE for network configuration
- calc.exe (PID: 1476)
Creates or modifies windows services
- svchost.exe (PID: 3380)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:09:18 01:06:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 95744 |
| InitializedDataSize: | 12800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2014 23:06:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Sep-2014 23:06:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00017472 | 0x00017600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.69358 |
idata | 0x00019000 | 0x00000360 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.22631 |
.ldata | 0x0001A000 | 0x000006CC | 0x00000800 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.551507 |
.rsrc | 0x0001B000 | 0x00001680 | 0x00001800 | IMAGE_SCN_MEM_READ | 6.80913 |
.rlc | 0x0001D000 | 0x00000CAC | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.54858 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.08943 | 768 | UNKNOWN | English - United States | RT_RCDATA |
Imports
advapi32.dll |
authz.DLL |
kernel32.dll |
Total processes
51
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
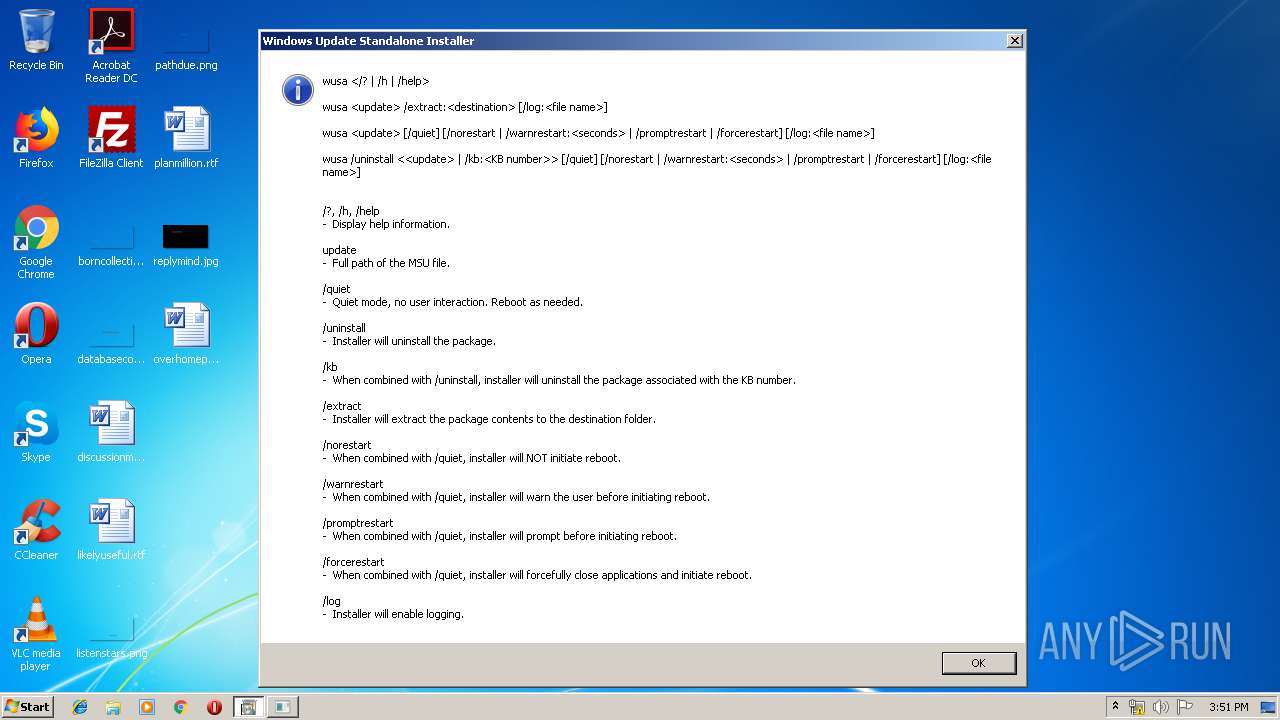
| 964 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | calc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\Temp\calc.exe" | C:\Users\admin\AppData\Local\Temp\calc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1492 | sc create arunlsjt binPath= "C:\Windows\system32\arunlsjt\azplsot.exe /d\"C:\Users\admin\AppData\Local\Temp\calc.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\system32\sc.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | cmd /C mkdir C:\Windows\system32\arunlsjt\ | C:\Windows\system32\cmd.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3252 | sc description arunlsjt "wifi internet conection" | C:\Windows\system32\sc.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | svchost.exe | C:\Windows\system32\svchost.exe | azplsot.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | netsh advfirewall firewall add rule name="Host-process for services of Windows" dir=in action=allow program="C:\Windows\system32\svchost.exe" enable=yes>nul | C:\Windows\system32\netsh.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | C:\Windows\system32\arunlsjt\azplsot.exe /d"C:\Users\admin\AppData\Local\Temp\calc.exe" | C:\Windows\system32\arunlsjt\azplsot.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3748 | sc start arunlsjt | C:\Windows\system32\sc.exe | calc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
138
Read events
75
Write events
63
Delete events
0
Modification events
| (PID) Process: | (1476) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1476) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3384) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | calc.exe | C:\Users\admin\AppData\Local\Temp\azplsot.exe | executable | |
MD5:— | SHA256:— | |||
| 3844 | cmd.exe | C:\Windows\system32\arunlsjt\azplsot.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | svchost.exe | 40.76.4.15:80 | microsoft.com | Microsoft Corporation | US | whitelisted |
3380 | svchost.exe | 104.47.54.36:25 | microsoft-com.mail.protection.outlook.com | Microsoft Corporation | US | unknown |
3380 | svchost.exe | 43.231.4.7:443 | — | Gigabit Hosting Sdn Bhd | MY | malicious |
3380 | svchost.exe | 98.137.159.26:25 | mta5.am0.yahoodns.net | Yahoo | US | unknown |
3380 | svchost.exe | 74.125.131.26:25 | alt1.aspmx.l.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta5.am0.yahoodns.net |
| unknown |
google.com |
| malicious |
alt1.aspmx.l.google.com |
| whitelisted |