| File name: | PSCExploit.exe |
| Full analysis: | https://app.any.run/tasks/942b75f7-aa87-4835-8150-4f19cf0ed11f |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 17:43:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 96AAD4A54C0608690F0494CD48137B90 |
| SHA1: | BA84C4E0A67D7C4345085671943108BFA26C514B |
| SHA256: | 45332B4FEB9F5582F41733476055D78B112A1A30C3D3EE2914EA979832F6124A |
| SSDEEP: | 24576:cny/f9upaae95PDWpK+bp8N61dvoBhwNxIa4b8luSG2hwZ:9FgS5+W6Du8xlE8luS7o |
MALICIOUS
Writes to a start menu file
- javaw.exe (PID: 3884)
Changes the autorun value in the registry
- REG.exe (PID: 4080)
Application was dropped or rewritten from another process
- pscgen.exe (PID: 2356)
Loads dropped or rewritten executable
- javaw.exe (PID: 3884)
SUSPICIOUS
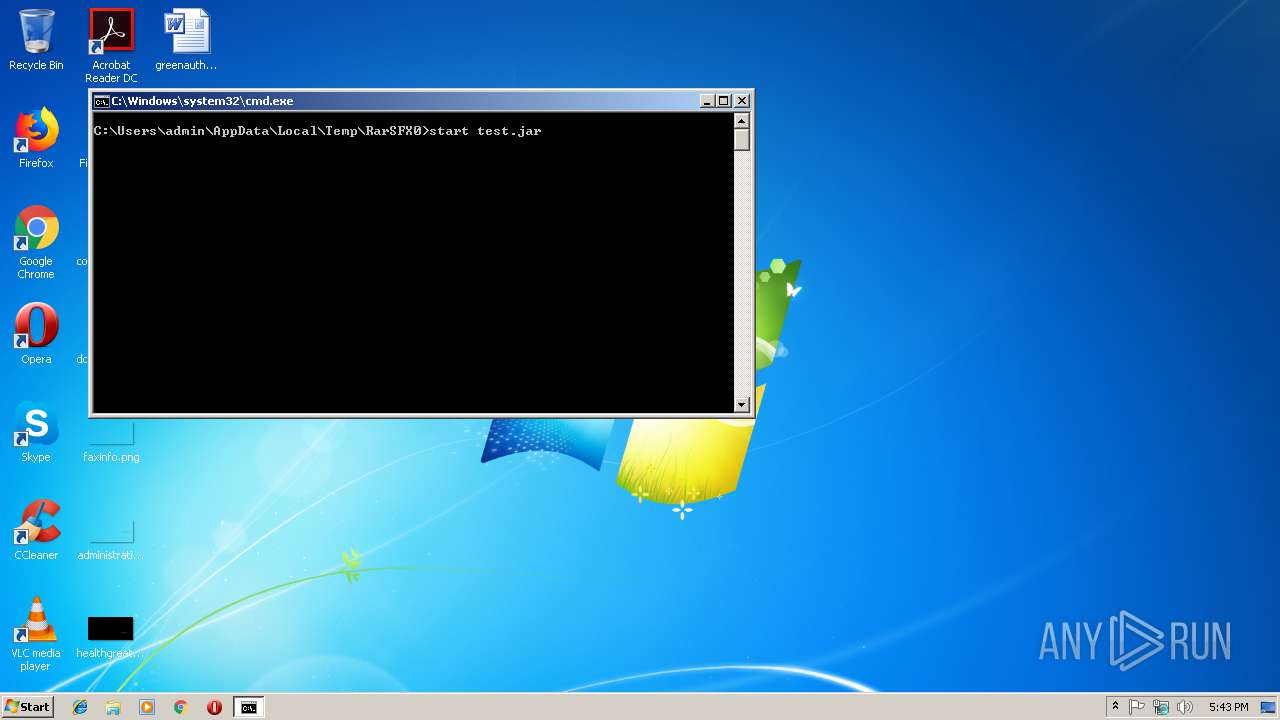
Executes JAVA applets
- cmd.exe (PID: 2404)
Starts CMD.EXE for commands execution
- PSCExploit.exe (PID: 2960)
Executable content was dropped or overwritten
- PSCExploit.exe (PID: 2960)
- javaw.exe (PID: 3884)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 3884)
Creates files in the user directory
- javaw.exe (PID: 3884)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3884)
Connects to unusual port
- javaw.exe (PID: 3884)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:15 09:00:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165888 |
| InitializedDataSize: | 176128 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d7cb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Feb-2015 08:00:31 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Feb-2015 08:00:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002878A | 0x00028800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71935 |
.rdata | 0x0002A000 | 0x00004FD3 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38998 |
.data | 0x0002F000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46555 |
.rsrc | 0x00051000 | 0x0000498A | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.64782 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24822 | 1738 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.23498 | 564 | UNKNOWN | German - Germany | RT_STRING |
8 | 3.21532 | 616 | UNKNOWN | German - Germany | RT_STRING |
9 | 3.20126 | 604 | UNKNOWN | German - Germany | RT_STRING |
10 | 3.20175 | 416 | UNKNOWN | German - Germany | RT_STRING |
11 | 3.27003 | 1412 | UNKNOWN | German - Germany | RT_STRING |
12 | 3.18751 | 424 | UNKNOWN | German - Germany | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
39
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | attrib +H C:\Users\admin\AppData\Roaming\test.jar | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
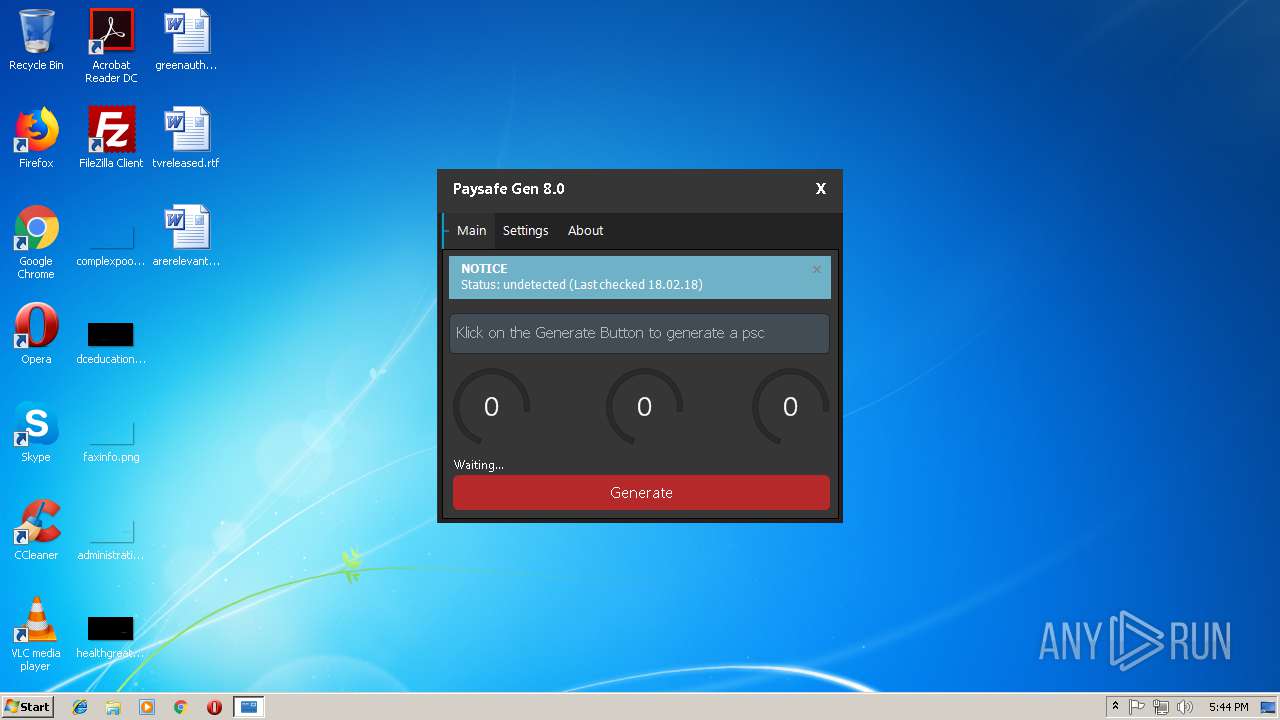
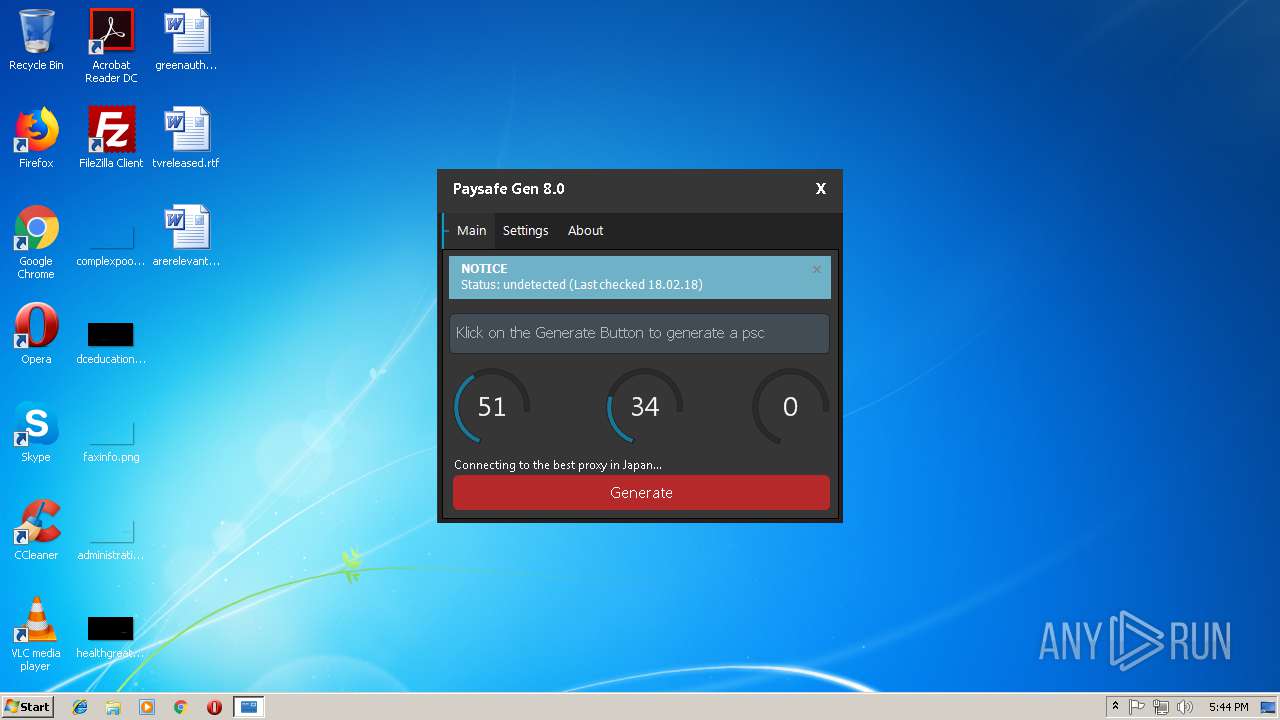
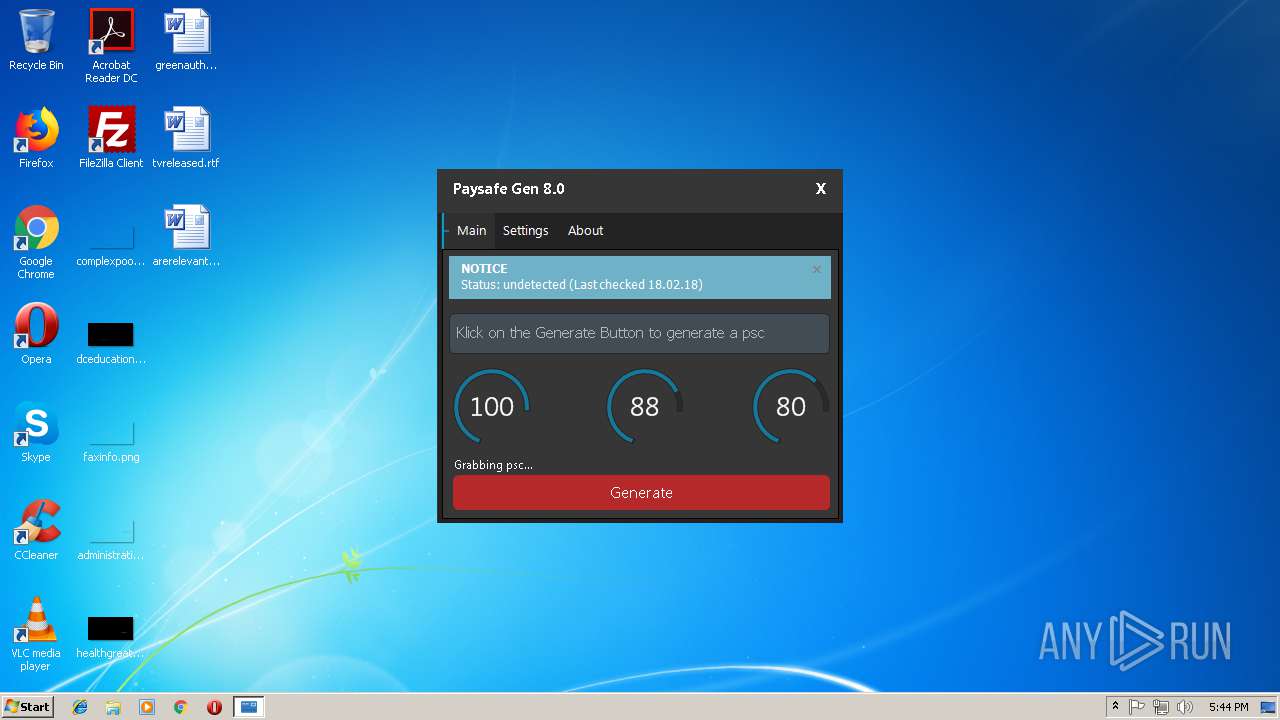
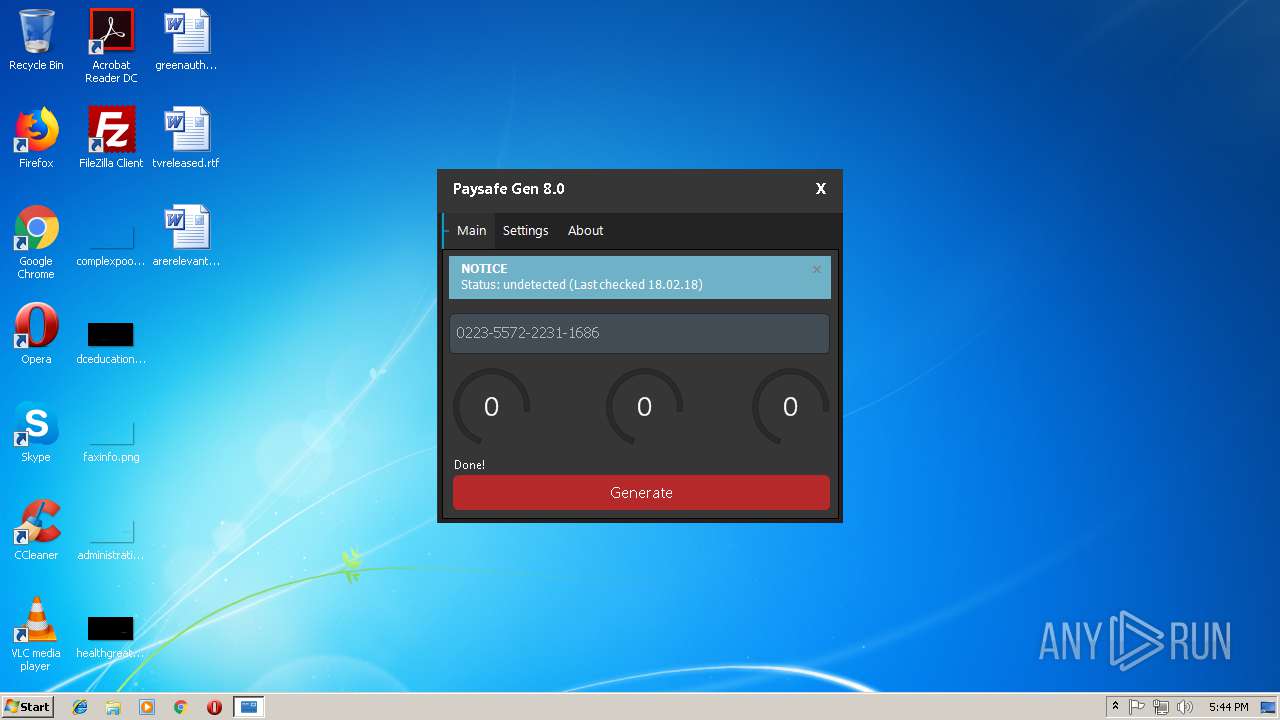
| 2356 | pscgen.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\pscgen.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PSc Gen 2018 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2404 | cmd /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\lnch.bat" " | C:\Windows\system32\cmd.exe | — | PSCExploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2432 | attrib +H C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\test.jar | C:\Windows\system32\attrib.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\PSCExploit.exe" | C:\Users\admin\AppData\Local\Temp\PSCExploit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3884 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\RarSFX0\test.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | cmd.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 4080 | REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "test.jar" /d "C:\Users\admin\AppData\Roaming\test.jar" /f | C:\Windows\system32\REG.exe | javaw.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
707
Read events
702
Write events
5
Delete events
0
Modification events
| (PID) Process: | (2960) PSCExploit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2960) PSCExploit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4080) REG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | test.jar |
Value: C:\Users\admin\AppData\Roaming\test.jar | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3884 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JNativeHook-1074147969084934013.dll | — | |
MD5:— | SHA256:— | |||
| 2960 | PSCExploit.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\pscgen.exe | executable | |
MD5:— | SHA256:— | |||
| 2960 | PSCExploit.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\test.jar | compressed | |
MD5:— | SHA256:— | |||
| 3884 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\test.jar | compressed | |
MD5:— | SHA256:— | |||
| 2960 | PSCExploit.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\lnch.bat | text | |
MD5:— | SHA256:— | |||
| 3884 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3884 | javaw.exe | C:\Users\admin\AppData\Roaming\test.jar | compressed | |
MD5:— | SHA256:— | |||
| 3884 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JNativeHook-FCBC1DC5993F3B7C153159E29CD4364927BC9517.dll | executable | |
MD5:B4CE035F926531D6B4DFA8477C6477E4 | SHA256:F6FFEAD3B5F3DB5A7A00D1FEF874C3D3ED7ECF095DA2D981EBD691FDFA685716 | |||
| 3884 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3884 | javaw.exe | 193.161.193.99:44587 | — | OOO Bitree Networks | RU | malicious |