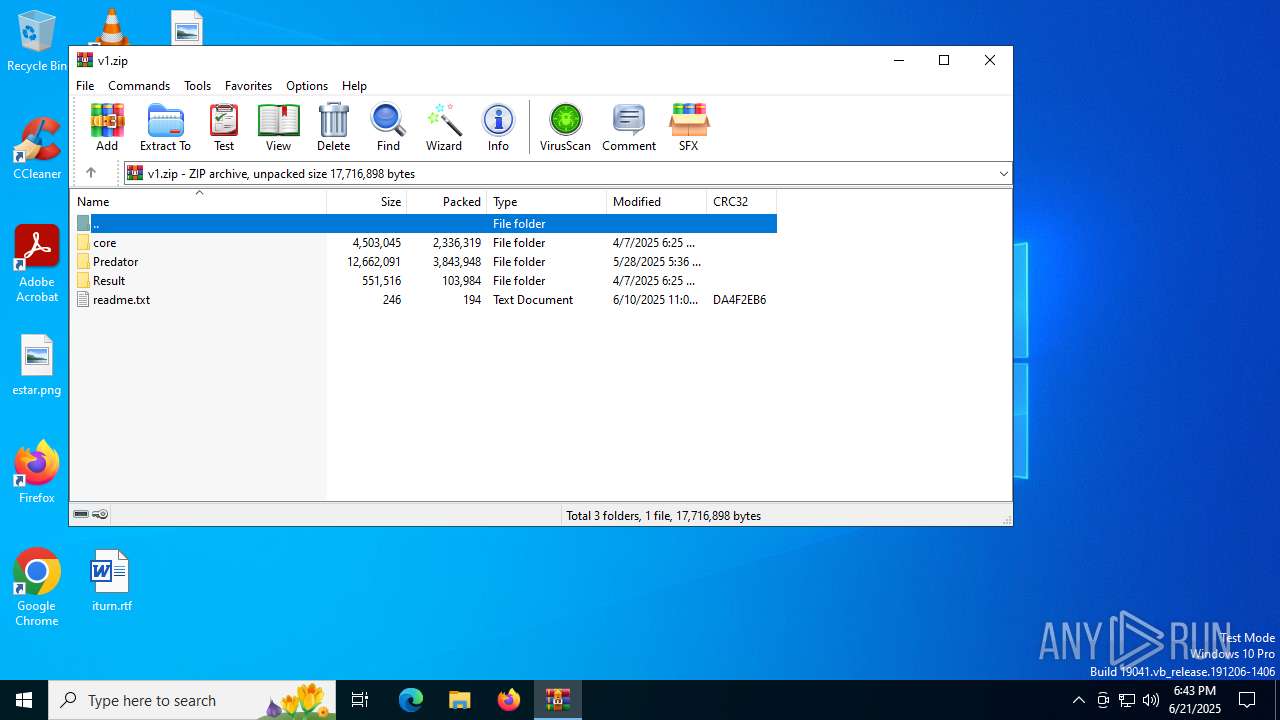
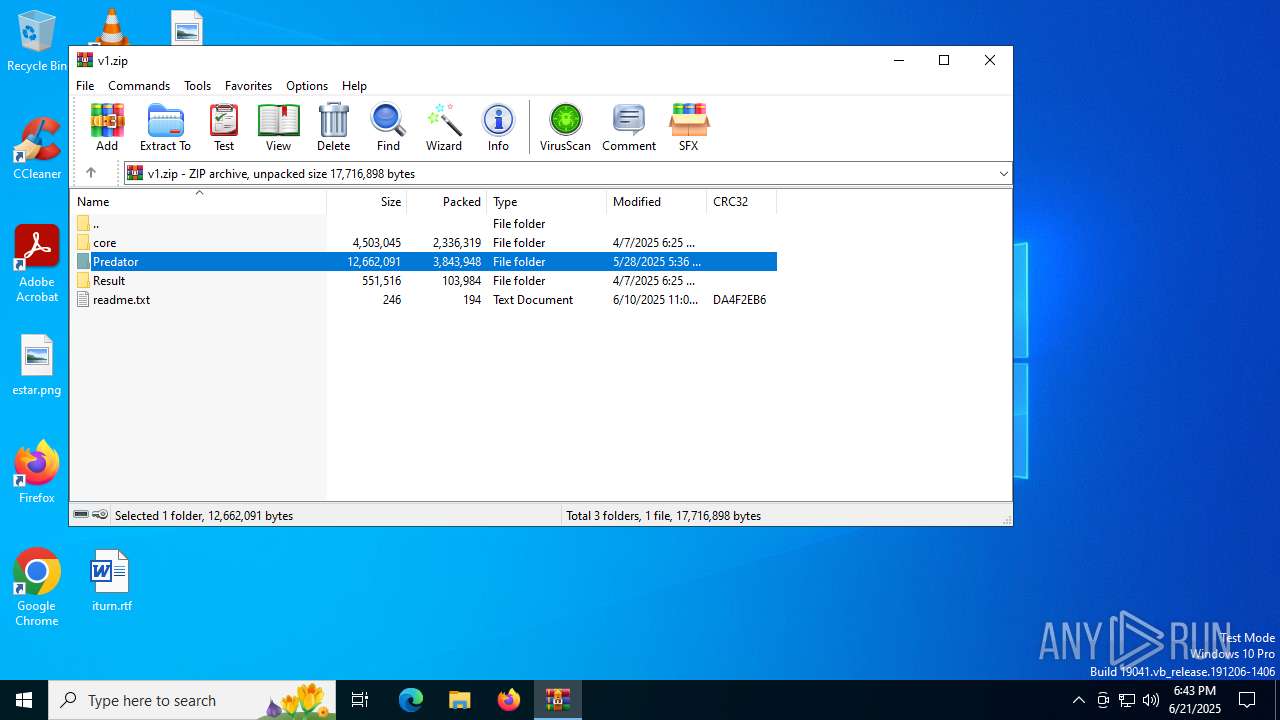
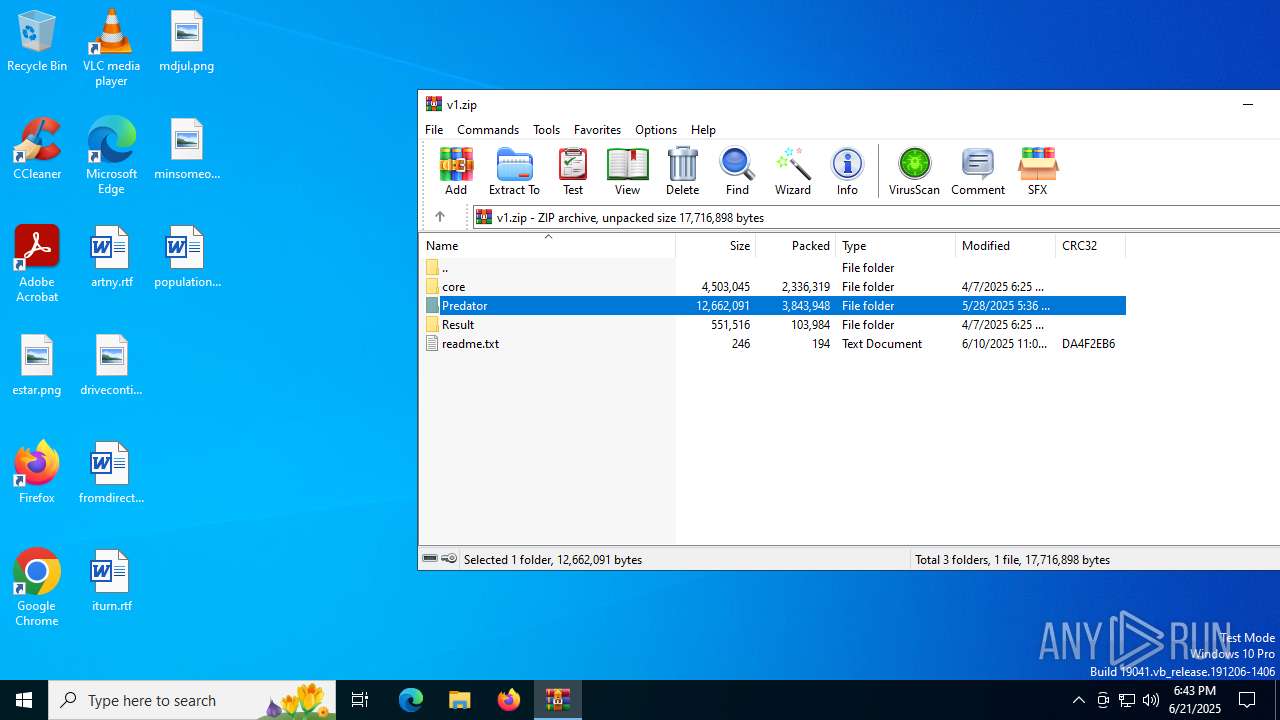
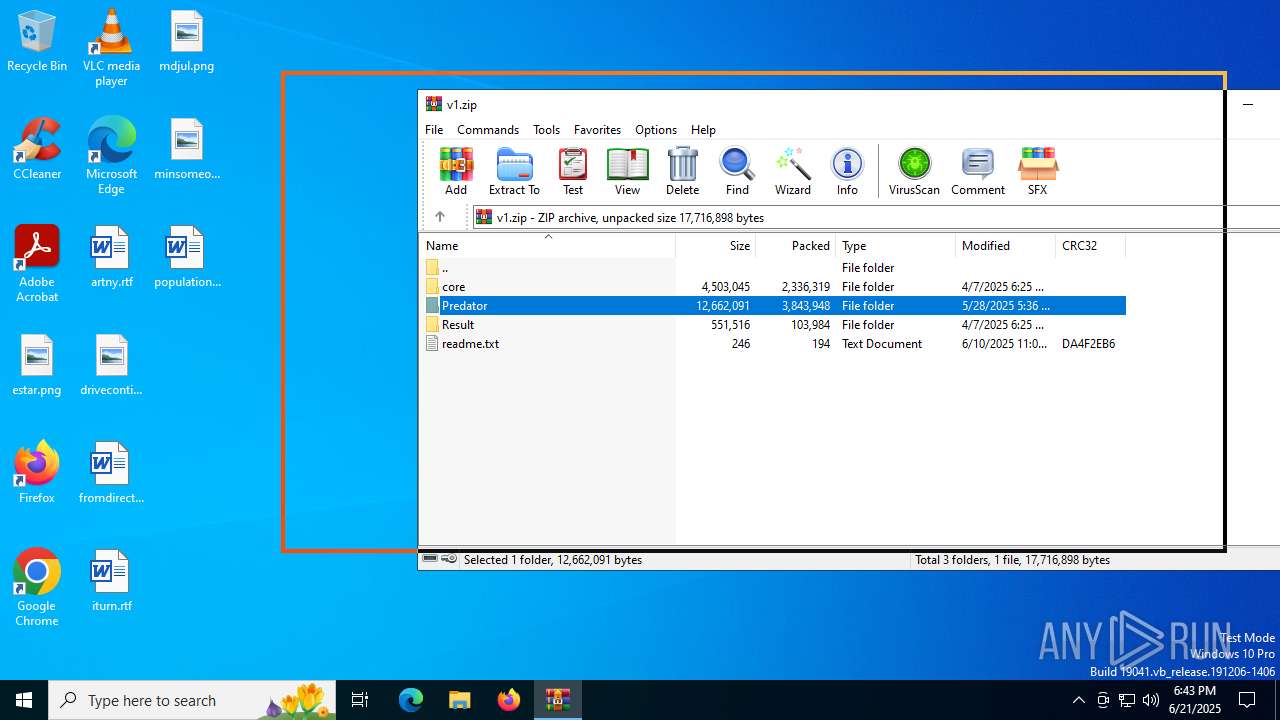
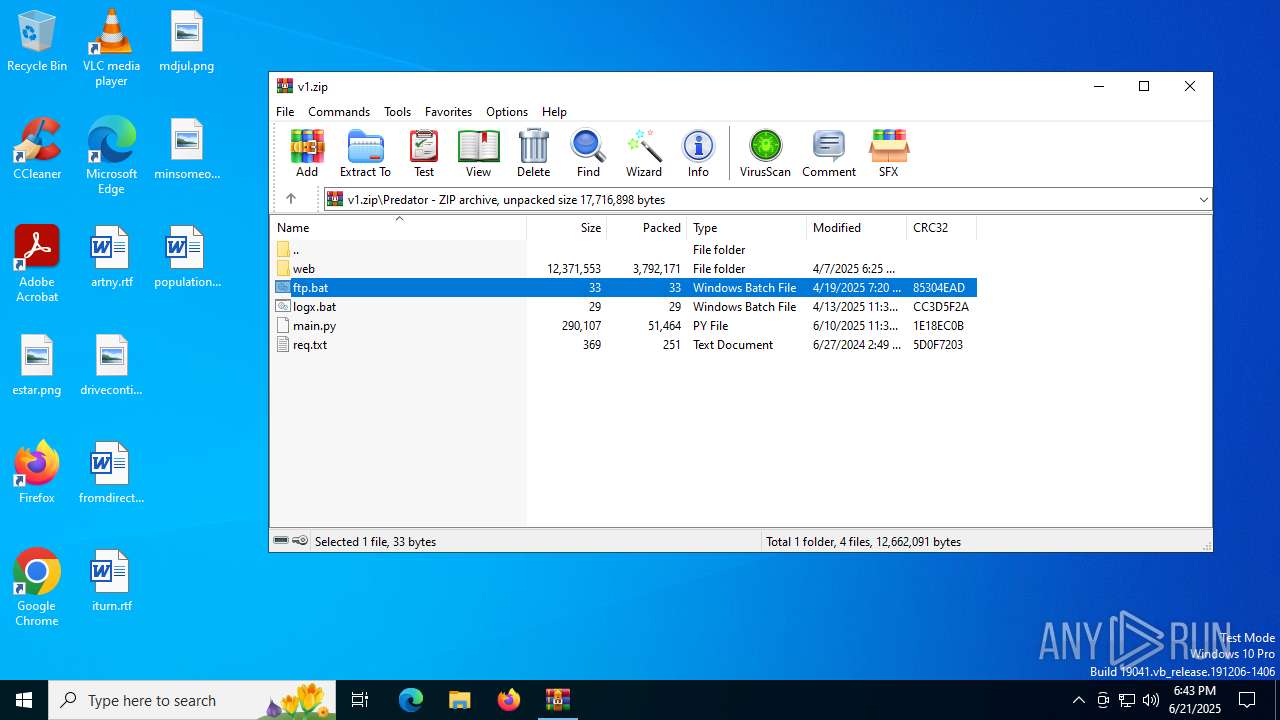
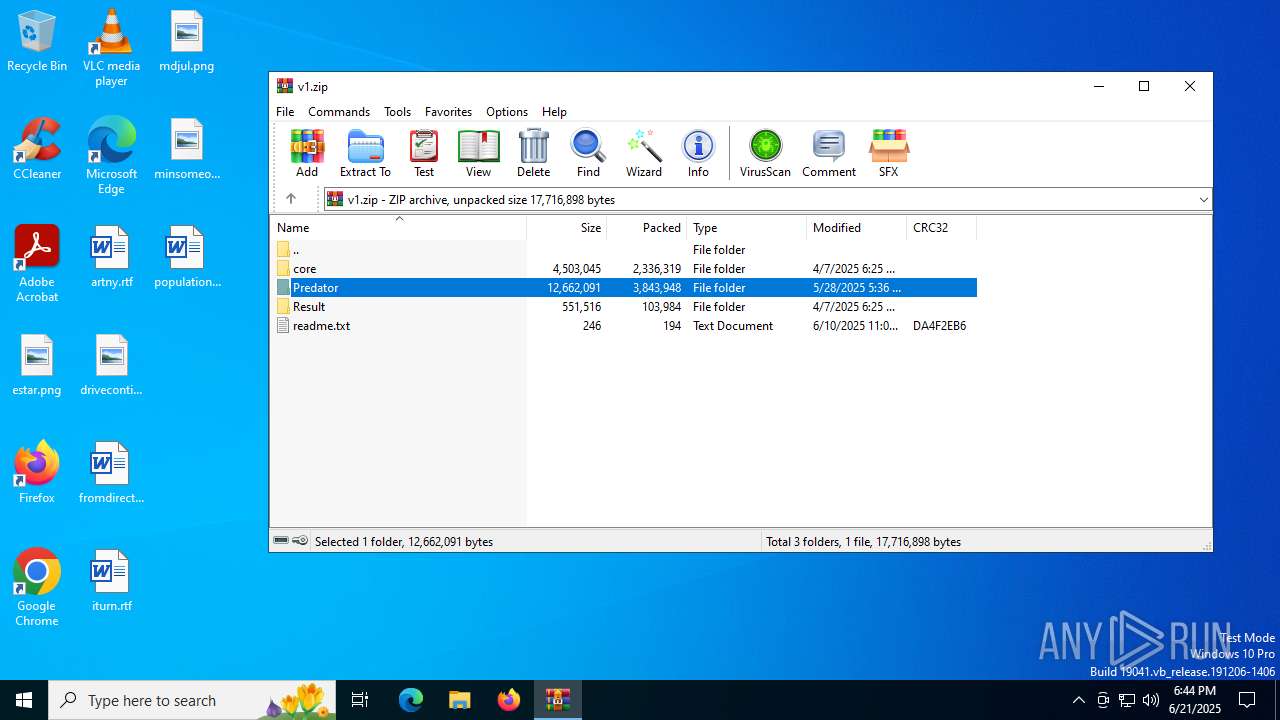
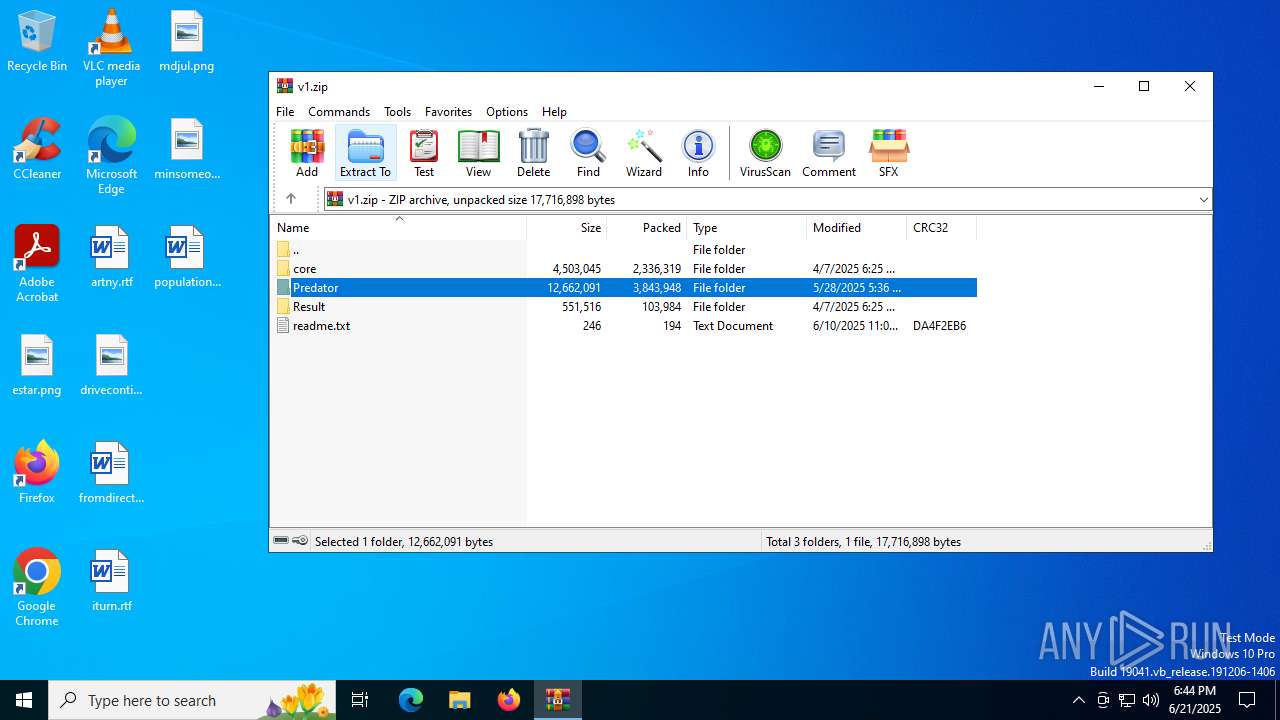
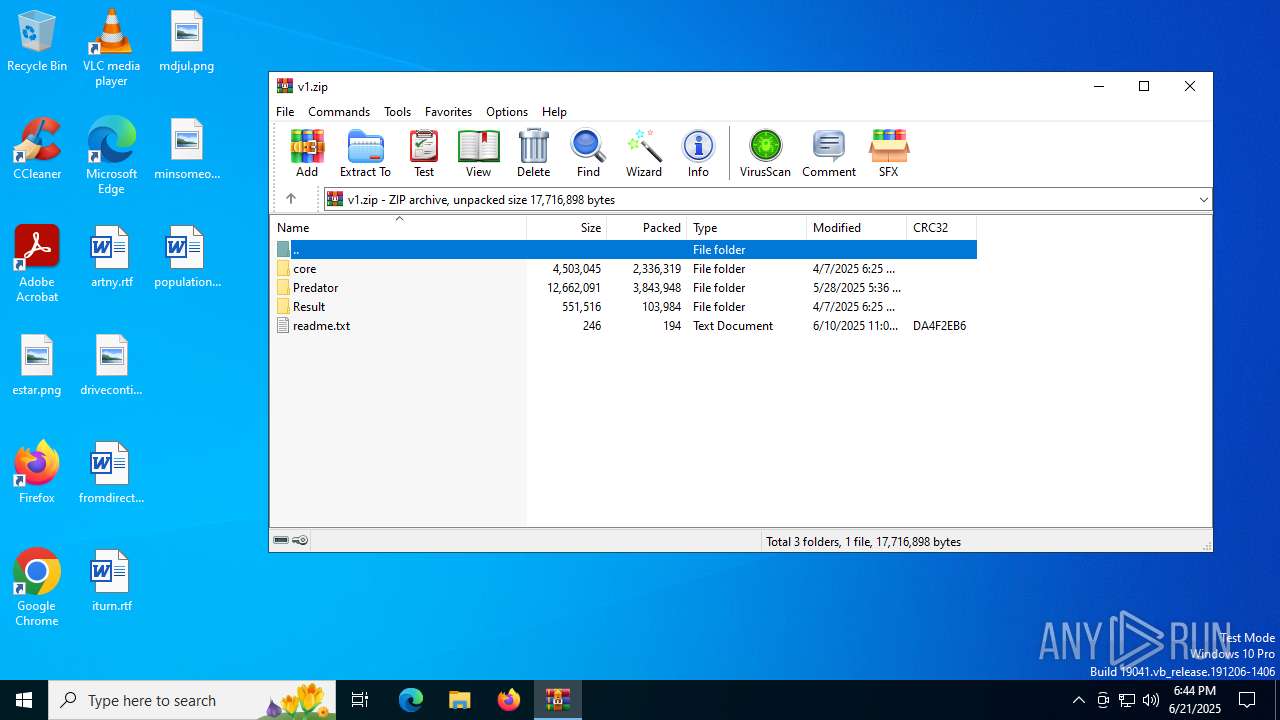
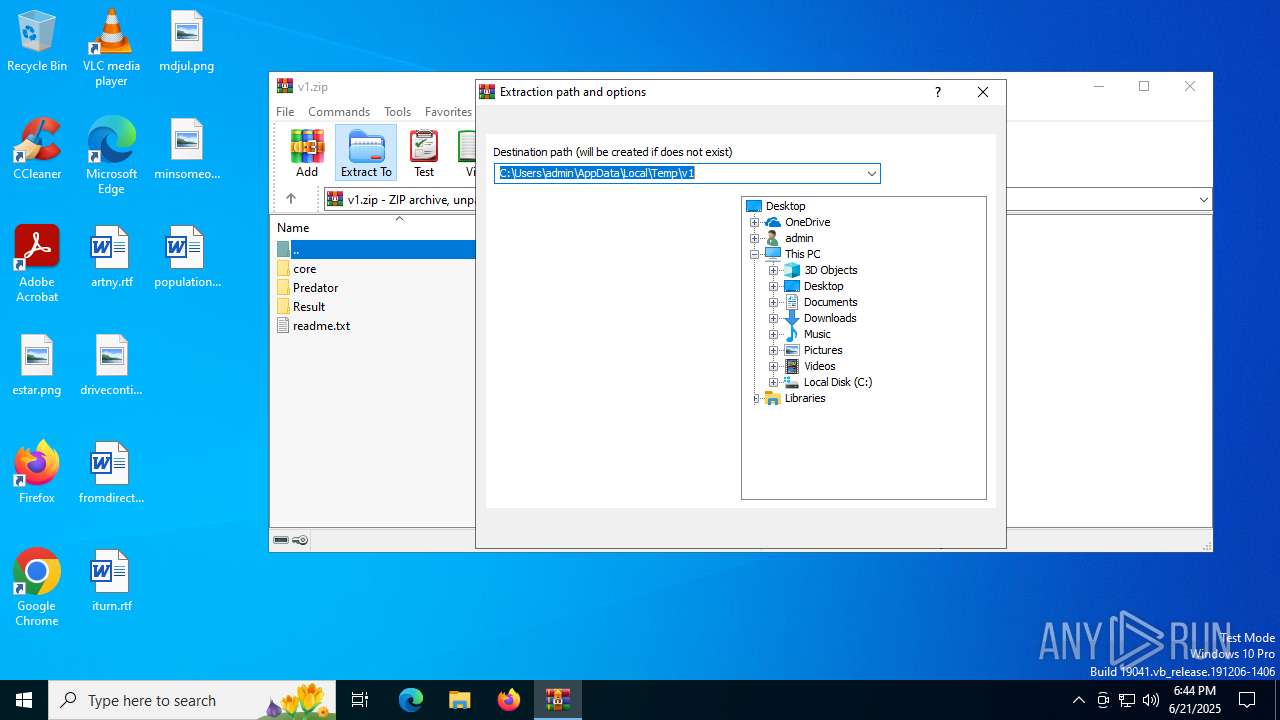
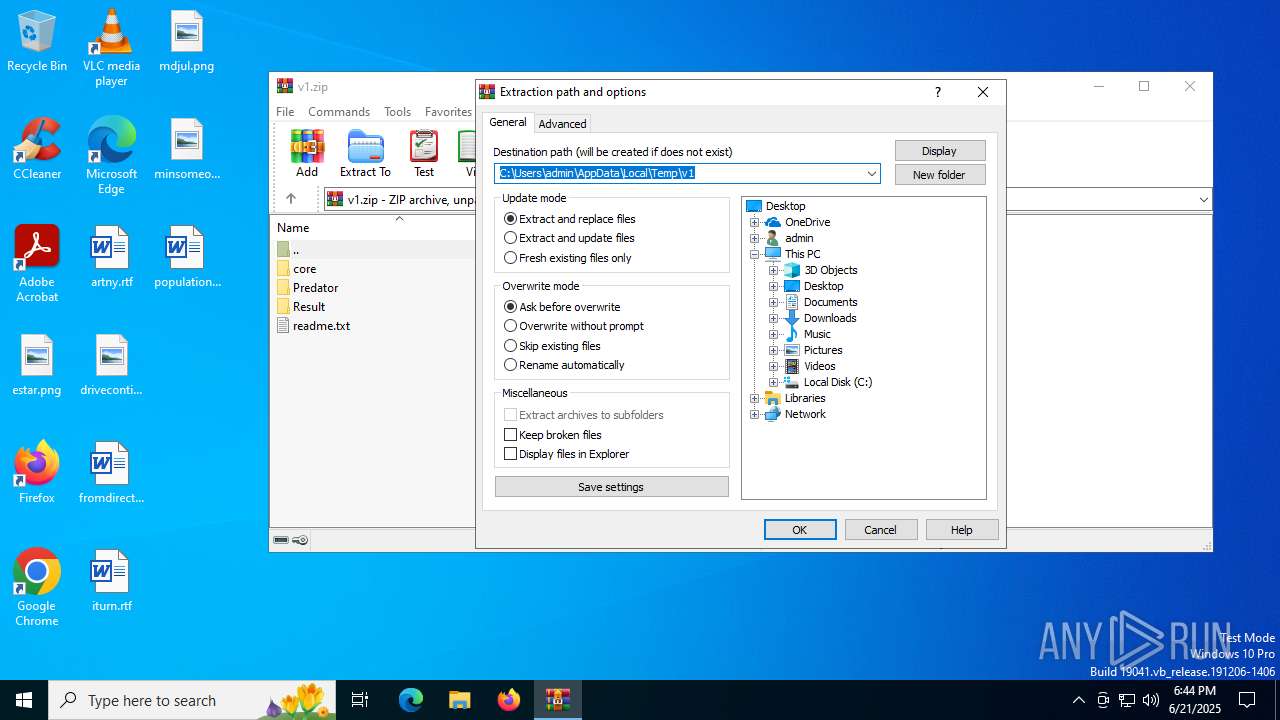
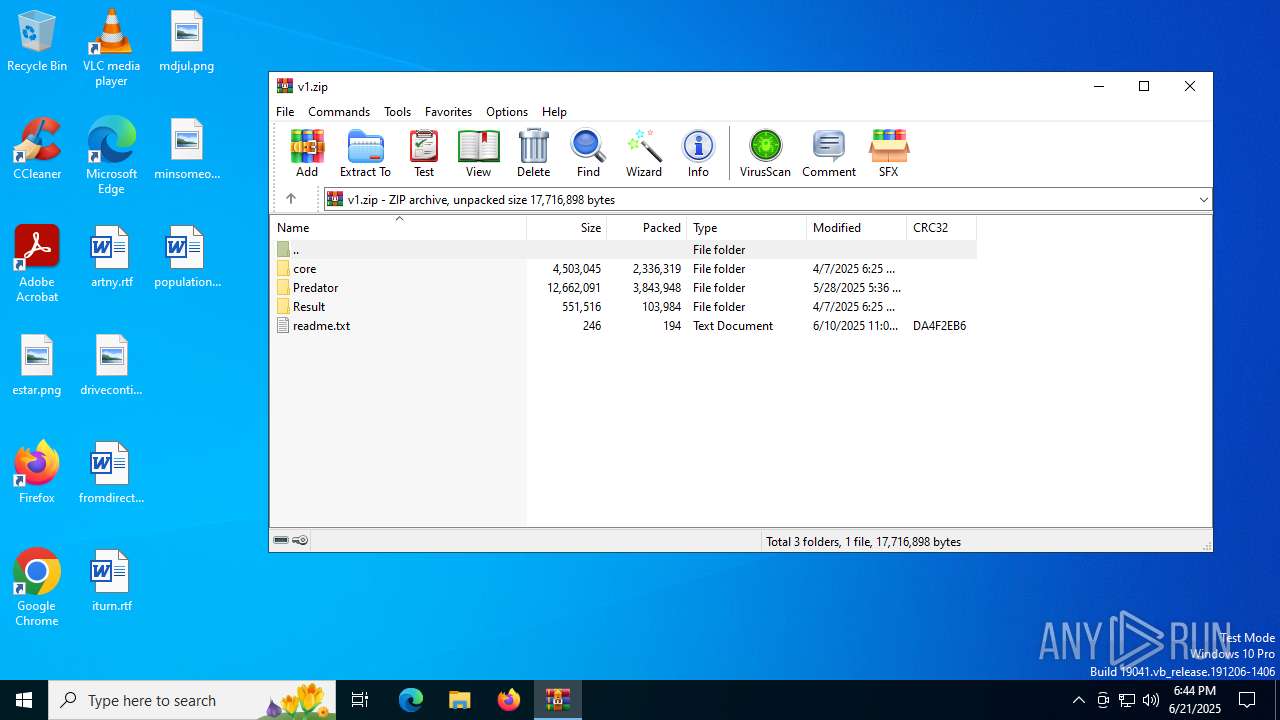
| File name: | v1.zip |
| Full analysis: | https://app.any.run/tasks/ed083b7f-0ef6-4b48-9053-0788ede3ae0d |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 18:43:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 5BA89ED828F225CF503C4827BE8056B2 |
| SHA1: | 0504946CD4F18D70AF491D8EA9076ECAD2F006E2 |
| SHA256: | 4530C182A935C14BC2A2DA2FFE878E8D8B868A89DD97B08362A18181BFFF2D60 |
| SSDEEP: | 98304:2Sb+M1Y4+AjAeRI41q8yjMR2UoCr4ngwEwR+YEiGtS/mHWJvo58RpF3tqL8WYUhv:9s9Lv9Yr2mdsK |
MALICIOUS
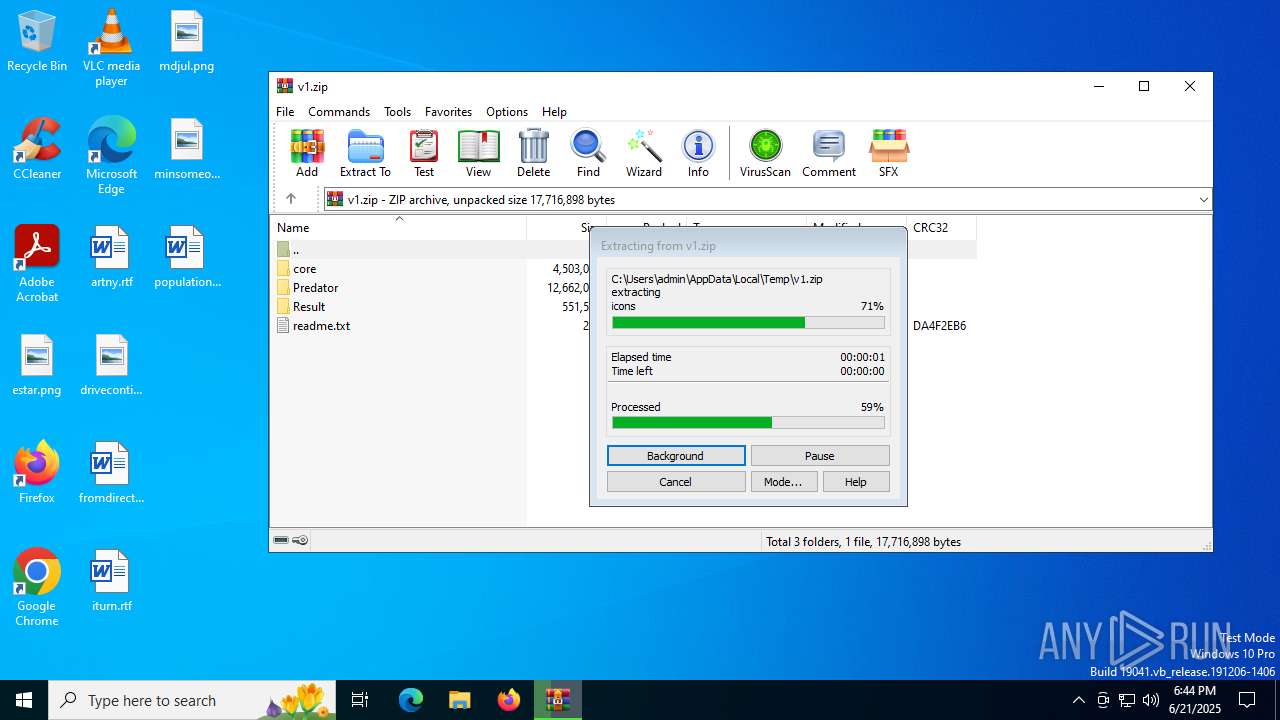
Generic archive extractor
- WinRAR.exe (PID: 2996)
SUSPICIOUS
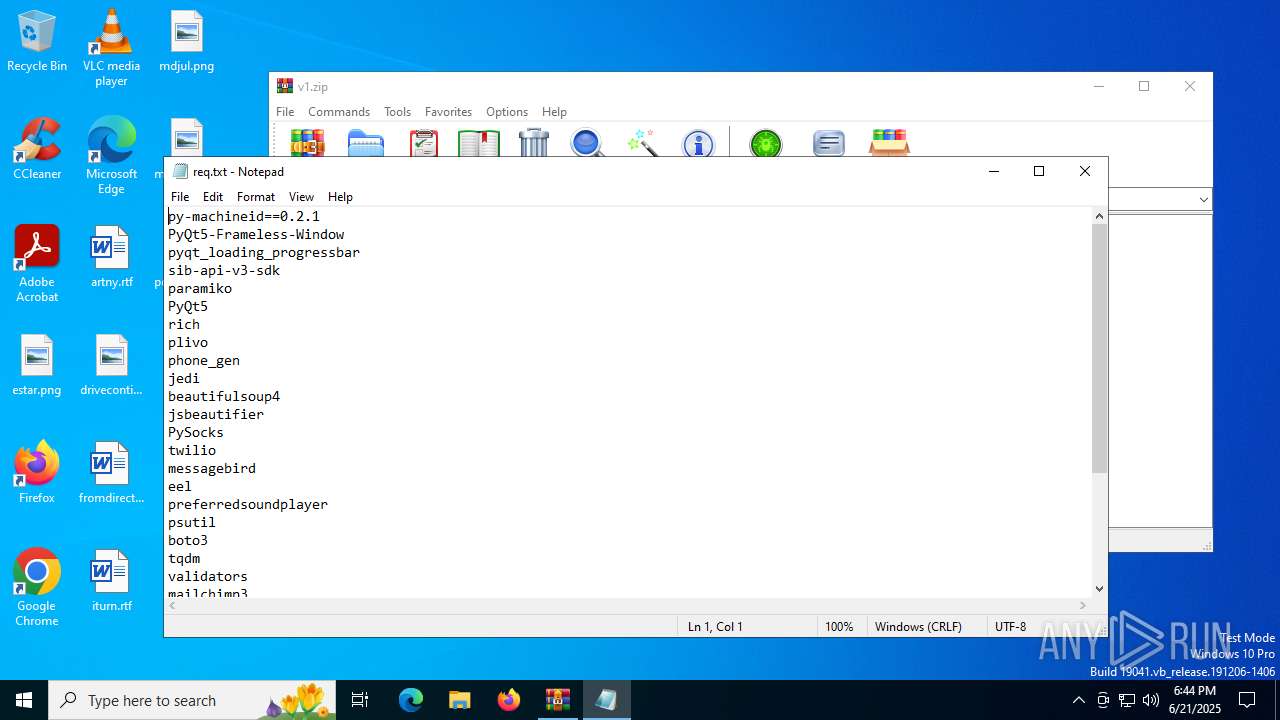
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 2996)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2996)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2996)
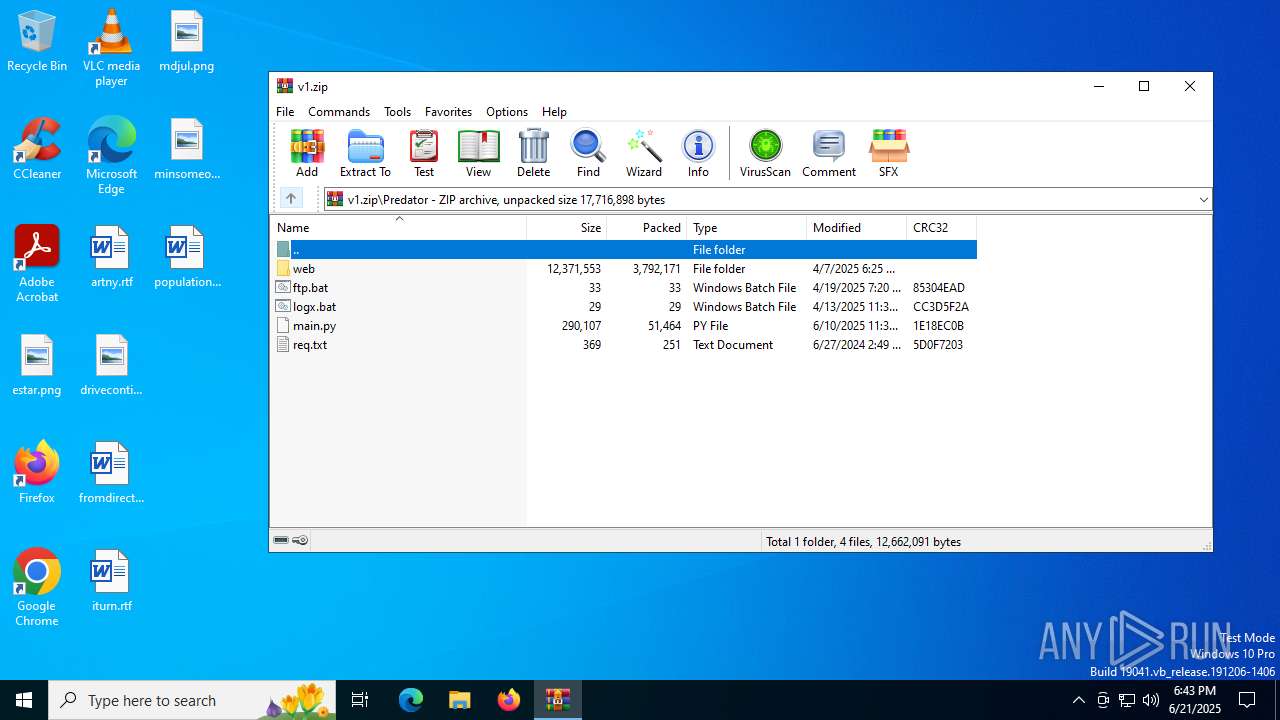
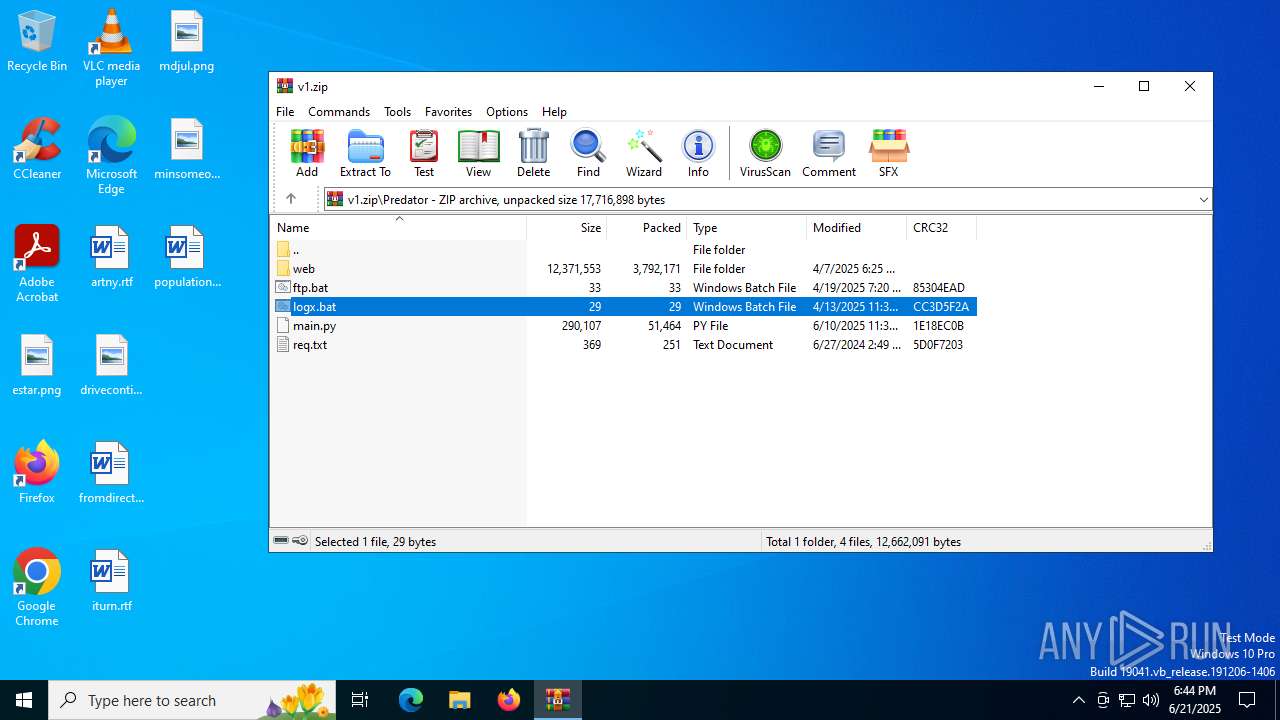
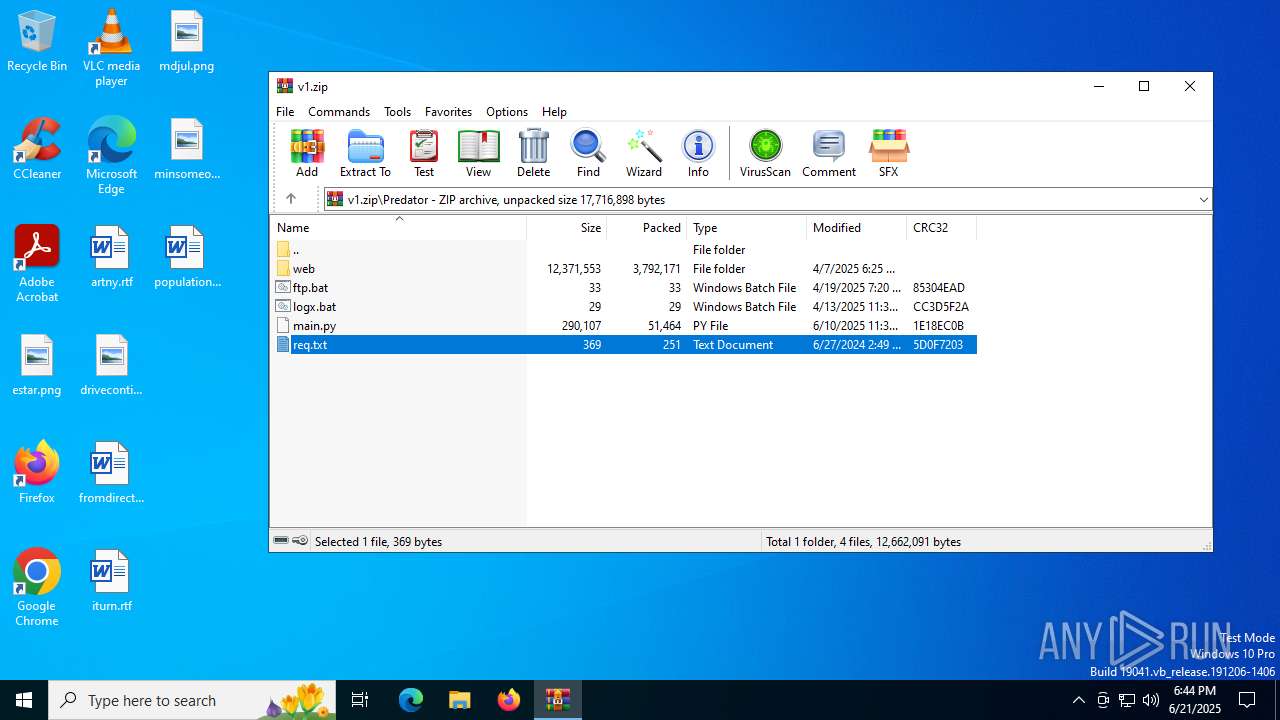
Executing commands from a ".bat" file
- WinRAR.exe (PID: 2996)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2996)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (42.1) |
|---|---|---|
| .zip | | | ZIP compressed archive (21) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:04:07 19:25:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | core/ |
Total processes
140
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
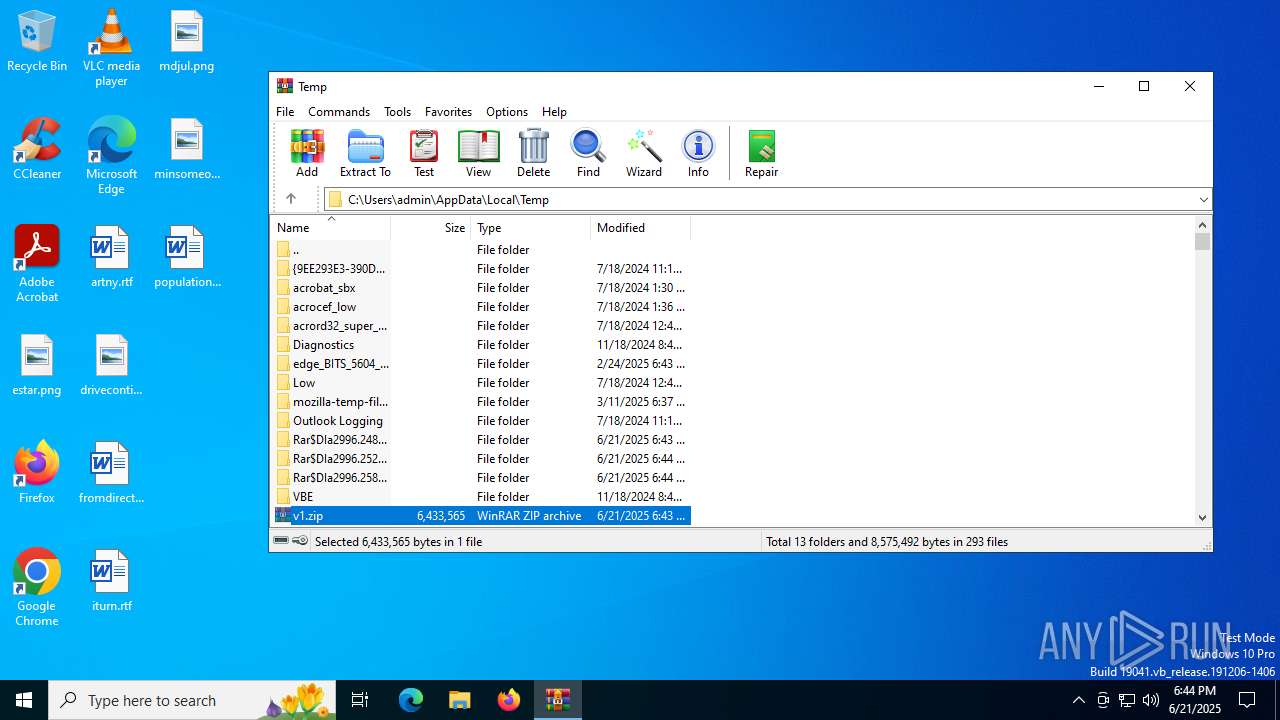
| 1212 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2996.25251\logx.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\v1.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 3396 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3724 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa2996.24807\ftp.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6504 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2996.25814\req.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 615
Read events
5 579
Write events
23
Delete events
13
Modification events
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\v1.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
190
Text files
408
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2996.25814\req.txt | text | |
MD5:D83CDFC5574C34AEC238521C118A3C3B | SHA256:94341AAE6A1C5DC8533BE65CF906A8DCE8716ECF7EABC40E5D111AB966E7EE18 | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\EditorApp.py | text | |
MD5:C59C6037A5CE7C6552156B9830C49F77 | SHA256:F8E7DD6035EB82681E232D3A0DAA4AA987CECF0BC89101EC6D0DE69D82919073 | |||
| 2996 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2996.25251\logx.bat | text | |
MD5:7BD85CE2AD0180EDB894BE7B9B67EF4E | SHA256:9E9CE7772638DC3A98043B4BD73783869E19328F5F2F7CD55C4DB00B694D1C5C | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\editor.cpython-311.pyc | binary | |
MD5:B0970E0D4CD1198CD6C37E13BFF3D692 | SHA256:16893EBD0623B7E17E756B2F82C49727E3DA0D1362DEA157F3241B6F4E0B64CD | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\EditorApp.cpython-311.pyc | binary | |
MD5:618AE82B1D4495E59319942ACE24F32C | SHA256:3310448BCAA462CACE3B16CCB2A3612EC04043E6BA88F17FE1A6D0843CB8BD46 | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\theme.json | binary | |
MD5:1A0A09483332570A31449A48E604E74E | SHA256:7D13952D95EF7965F53120791D2DF3031B9405F0BA85A03C8F4201DBD0F62BAE | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\autocompleter.cpython-311.pyc | binary | |
MD5:F5BA885F1AC53FD5A47B1EB29446E138 | SHA256:7DD149B6A6D71042F5BCF29F5537C20D31E3696D9BE35A69C8E66E10EB4CD4C7 | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\FileManager.cpython-311.pyc | binary | |
MD5:45232D6B42359FCB81F04422C416D67D | SHA256:EB9A994F6A2F452EABF7B3160D1BC3AF2A6A5BF92A588561AD827A9CDF767631 | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\file_manager.cpython-311.pyc | binary | |
MD5:0E7C1671CB2DDAD45C8B44E90BF9C047 | SHA256:EEA77D55B8B488C78F82246D92C406A1DC839D34BB8E3538BEA0908535894201 | |||
| 2996 | WinRAR.exe | C:\Users\admin\Desktop\core\Editor\__pycache__\file_types.cpython-311.pyc | binary | |
MD5:2733FF8088B1F3B7237CF3A9EF2D8123 | SHA256:19992CD4082BB07E3D5CDB02F2D92CDDADC6C1683E4BBFBF326223398A1DF928 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6368 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.192.18.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2348 | SIHClient.exe | GET | 200 | 23.192.18.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2348 | SIHClient.exe | GET | 200 | 23.192.18.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.77.197.149:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2028 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 98.66.133.184:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6368 | svchost.exe | 20.231.128.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6368 | svchost.exe | 23.51.98.7:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.77.197.149:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |