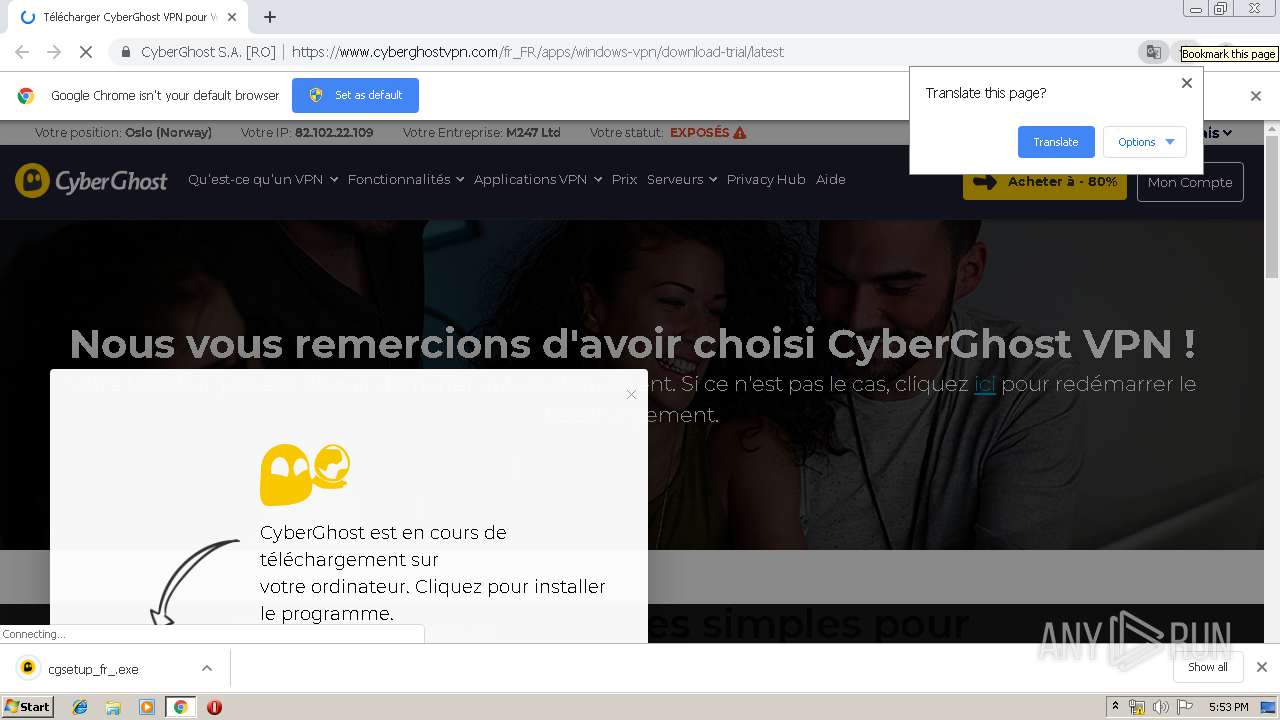
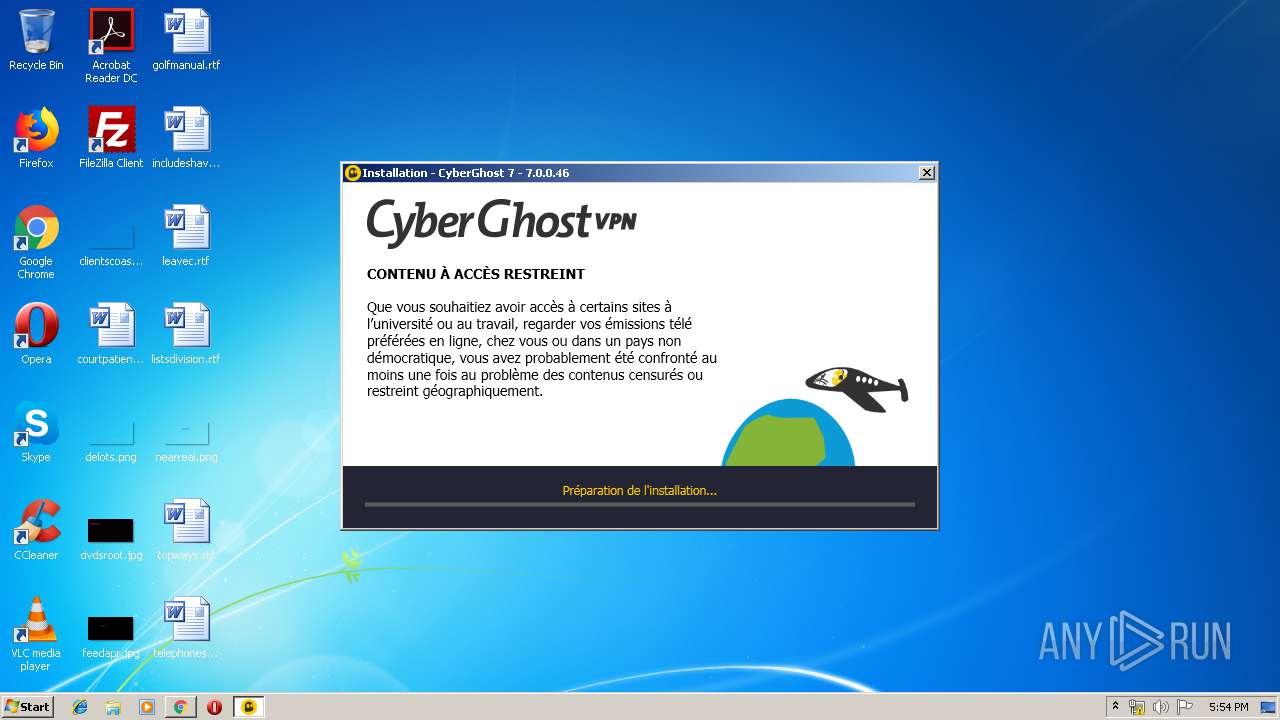
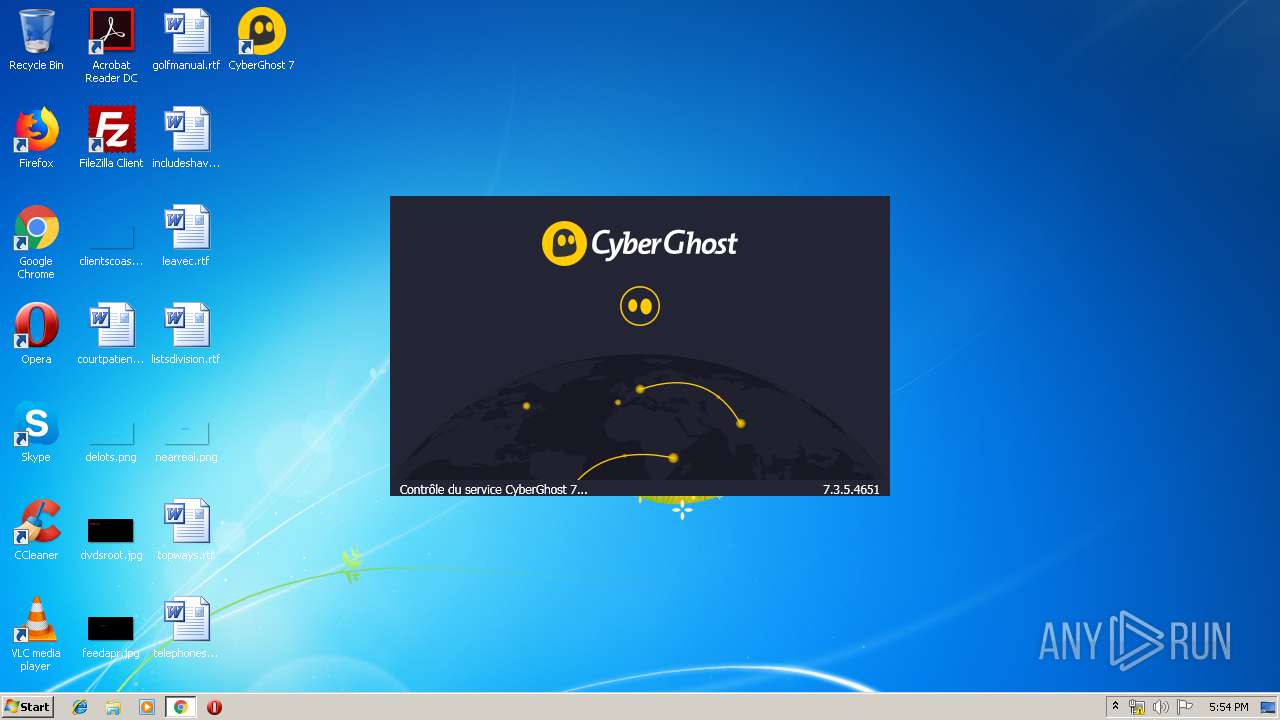
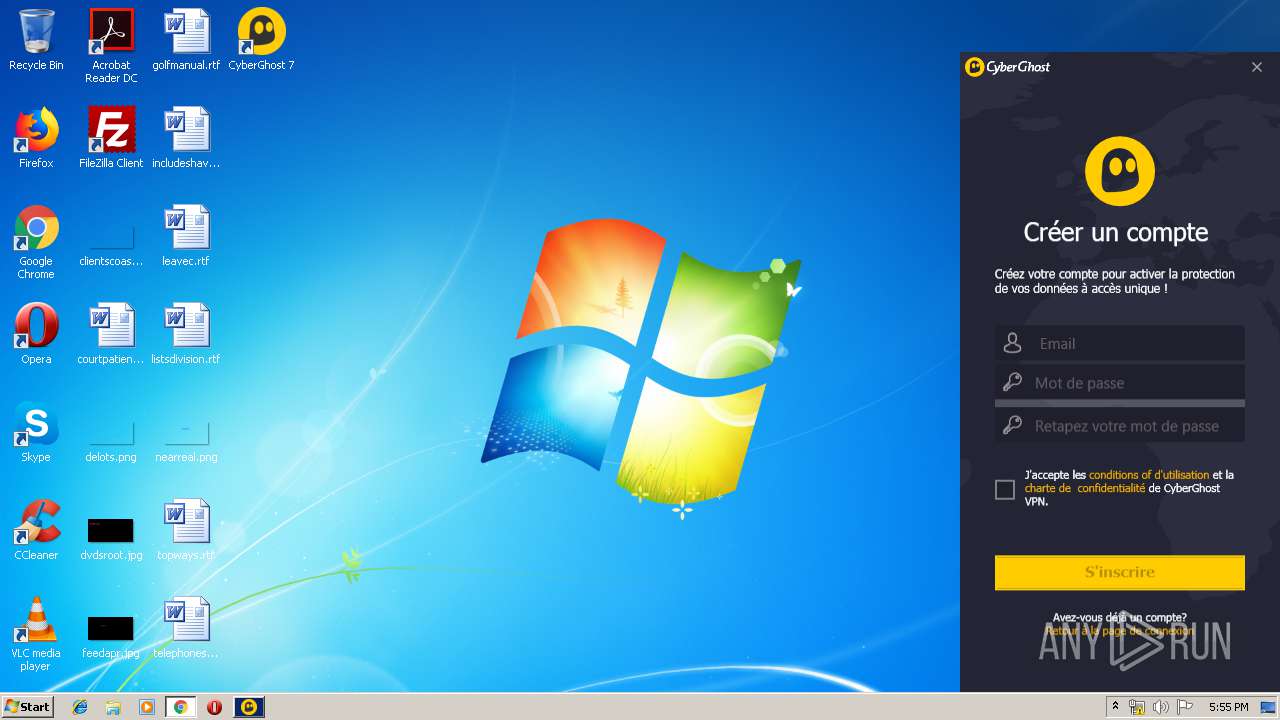
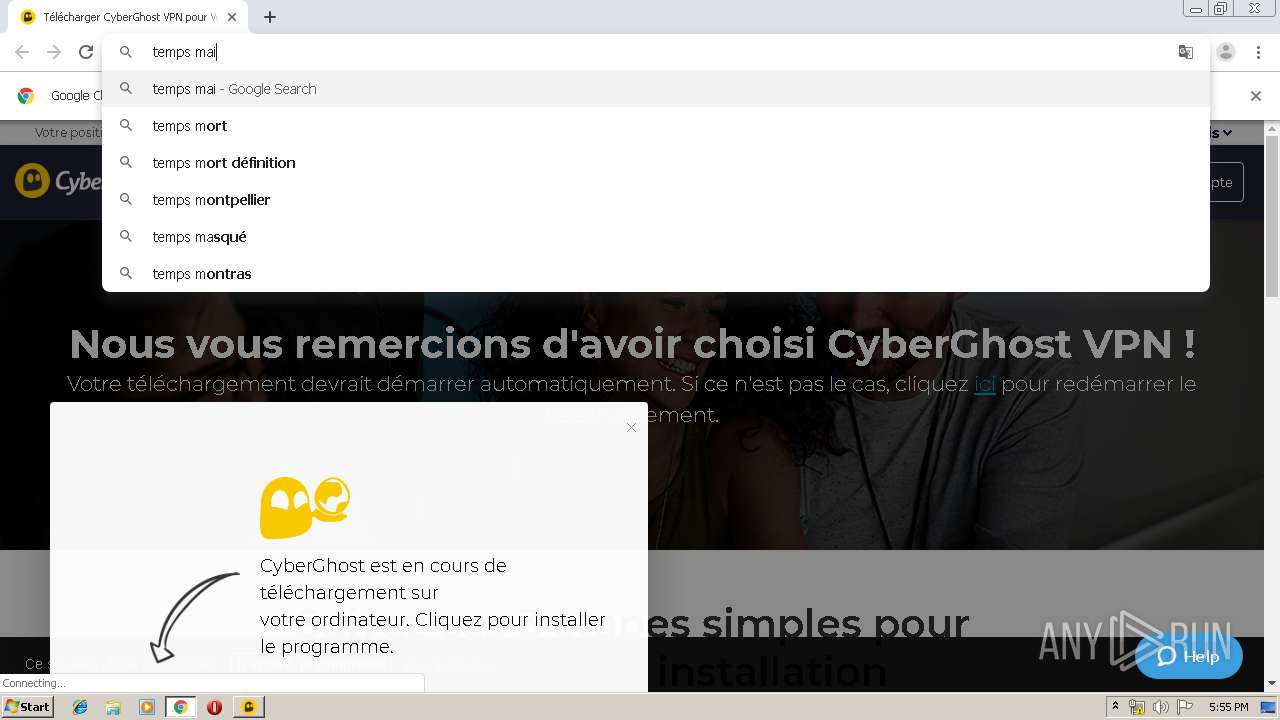
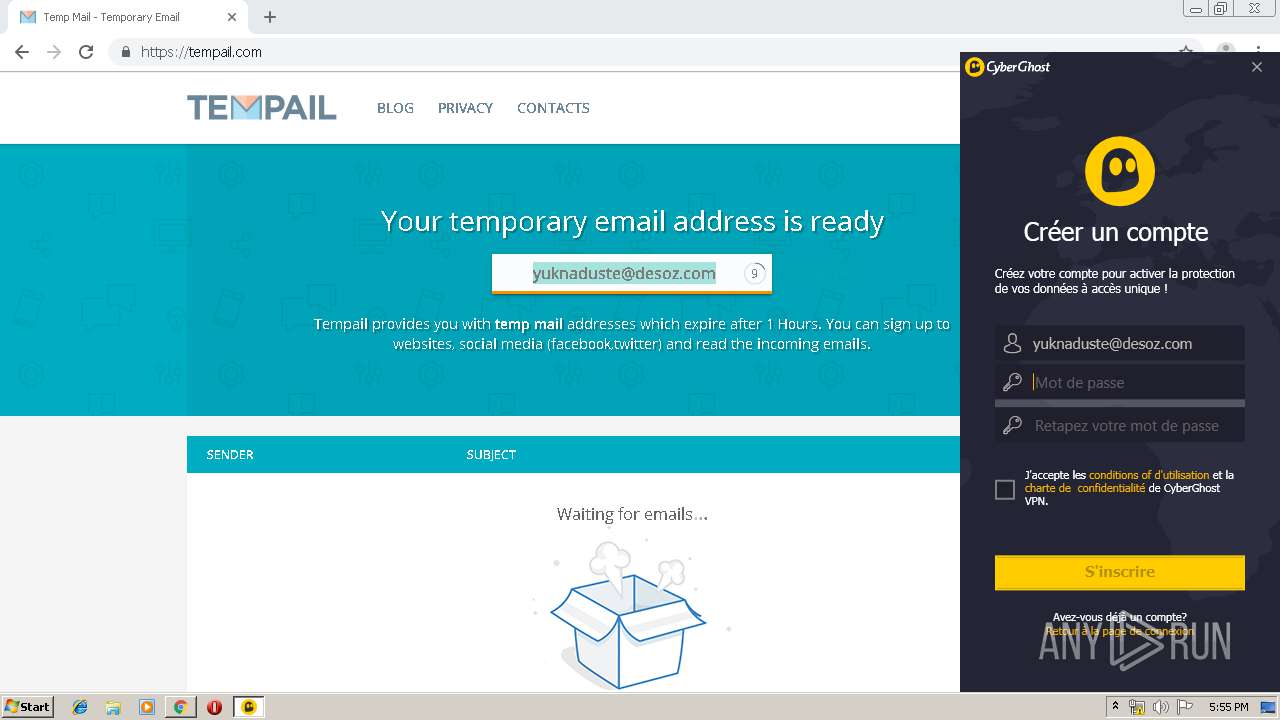
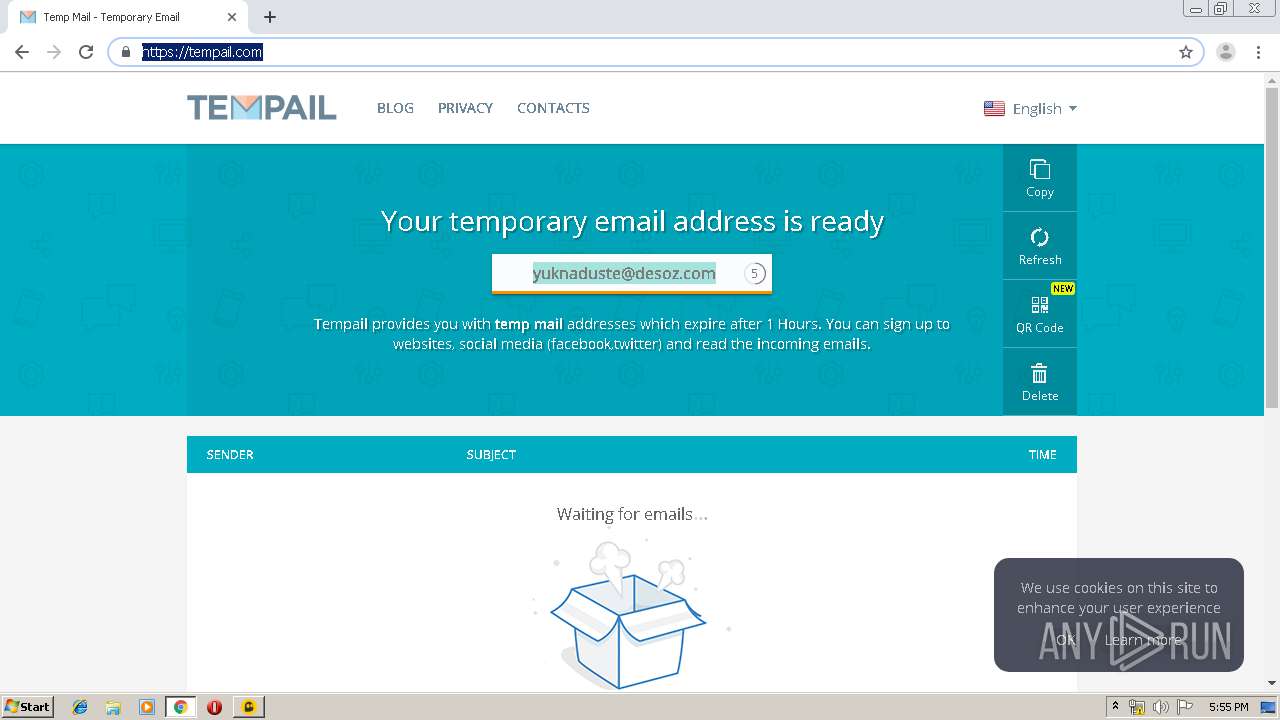
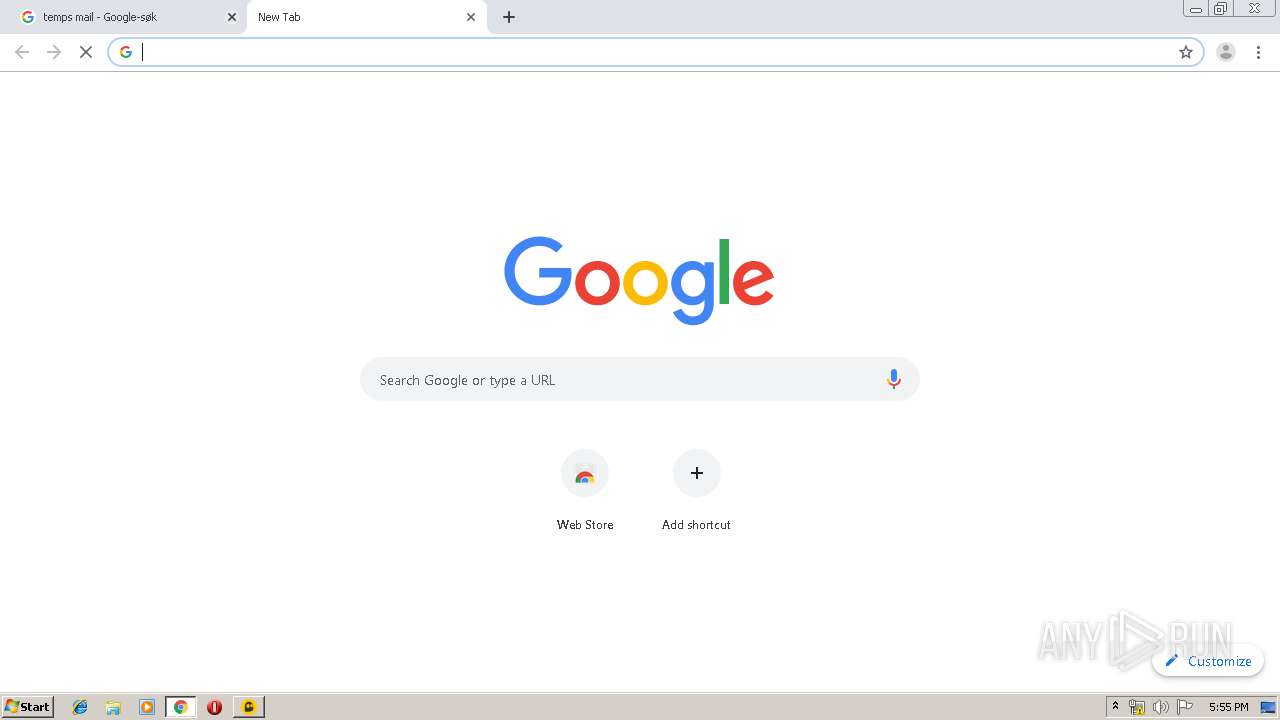
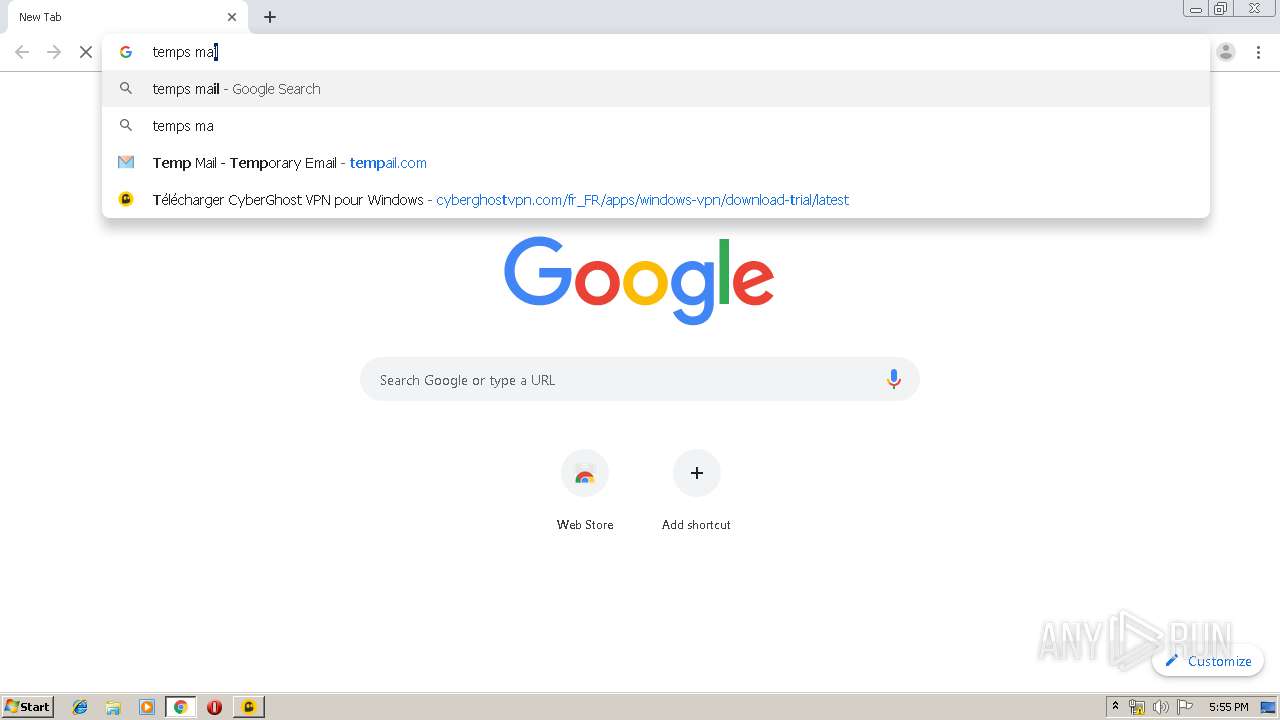
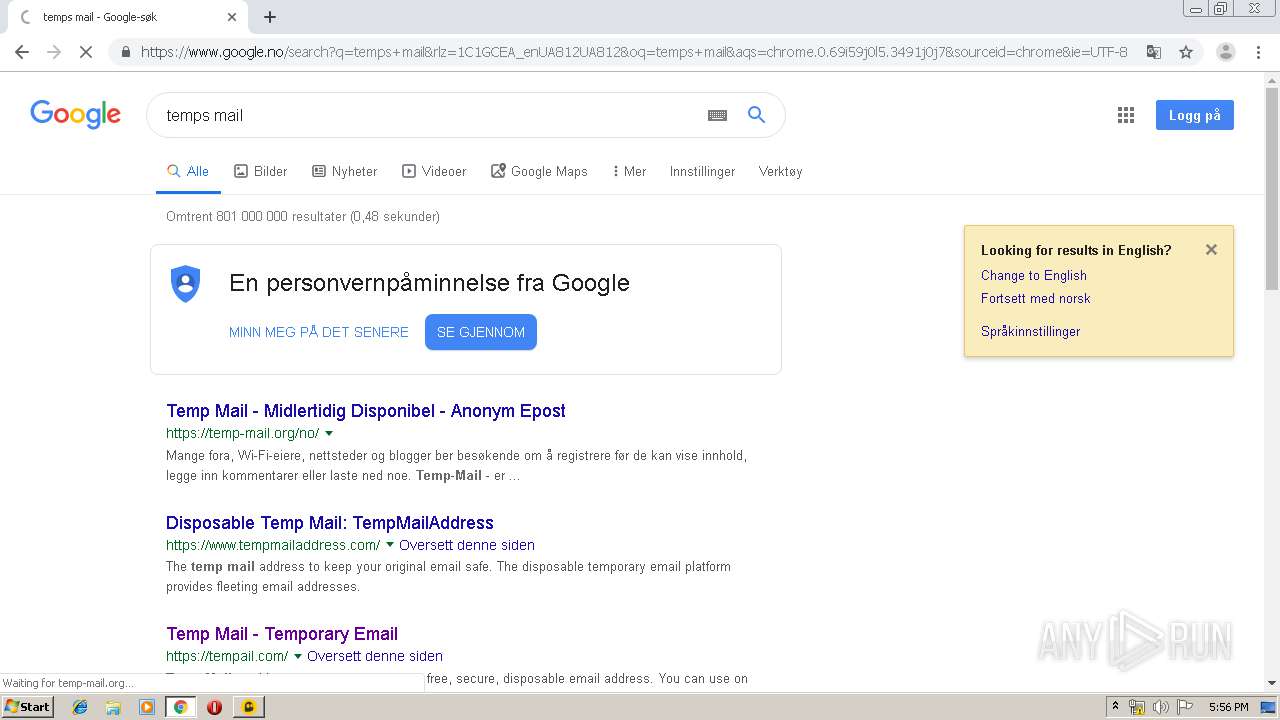
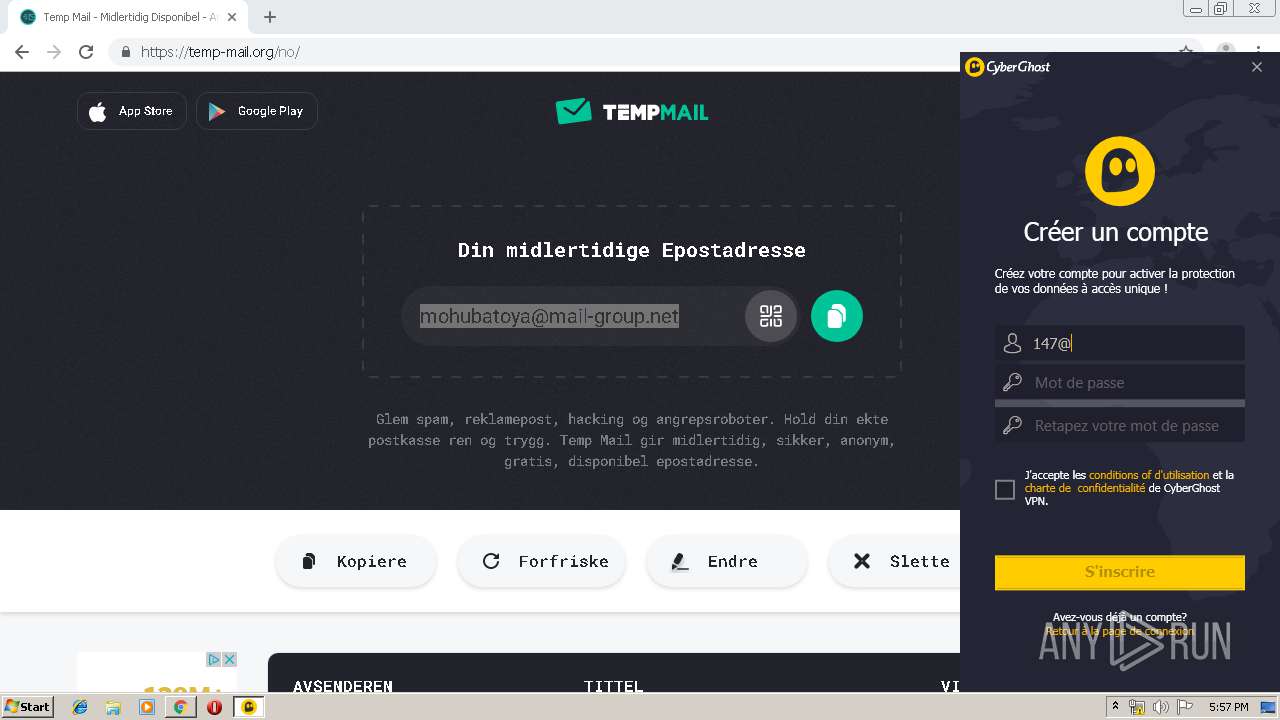
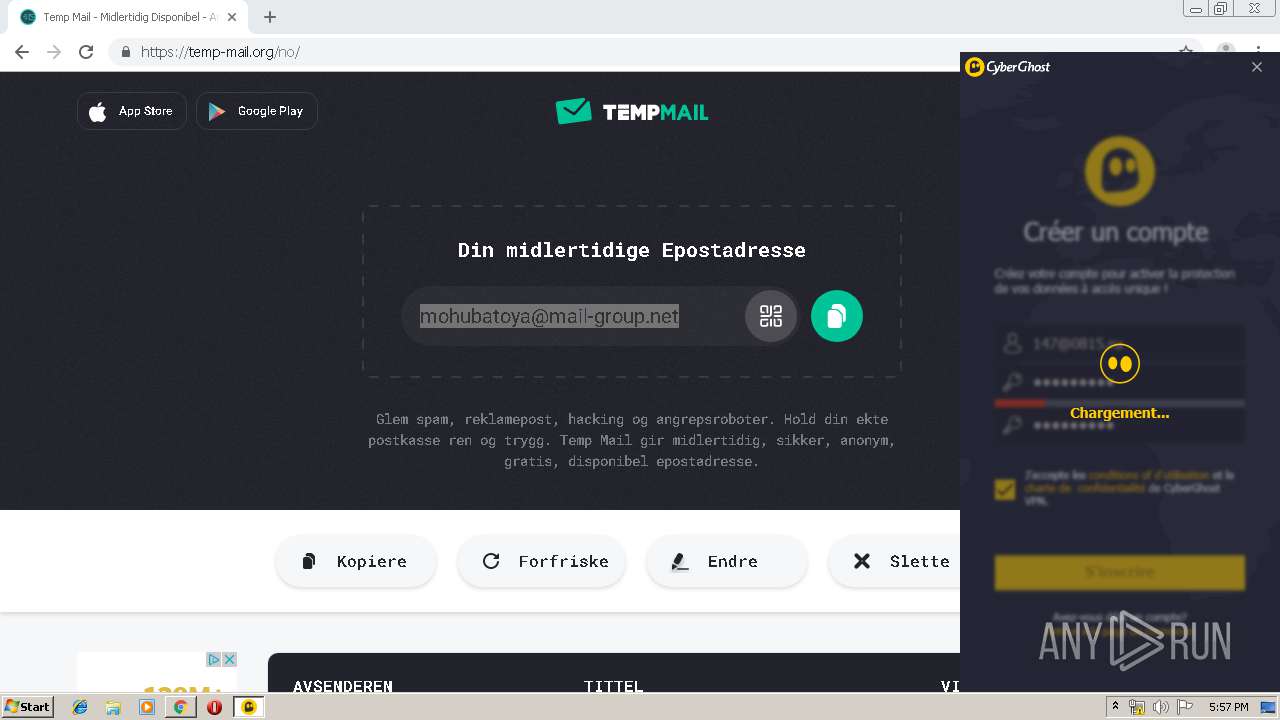
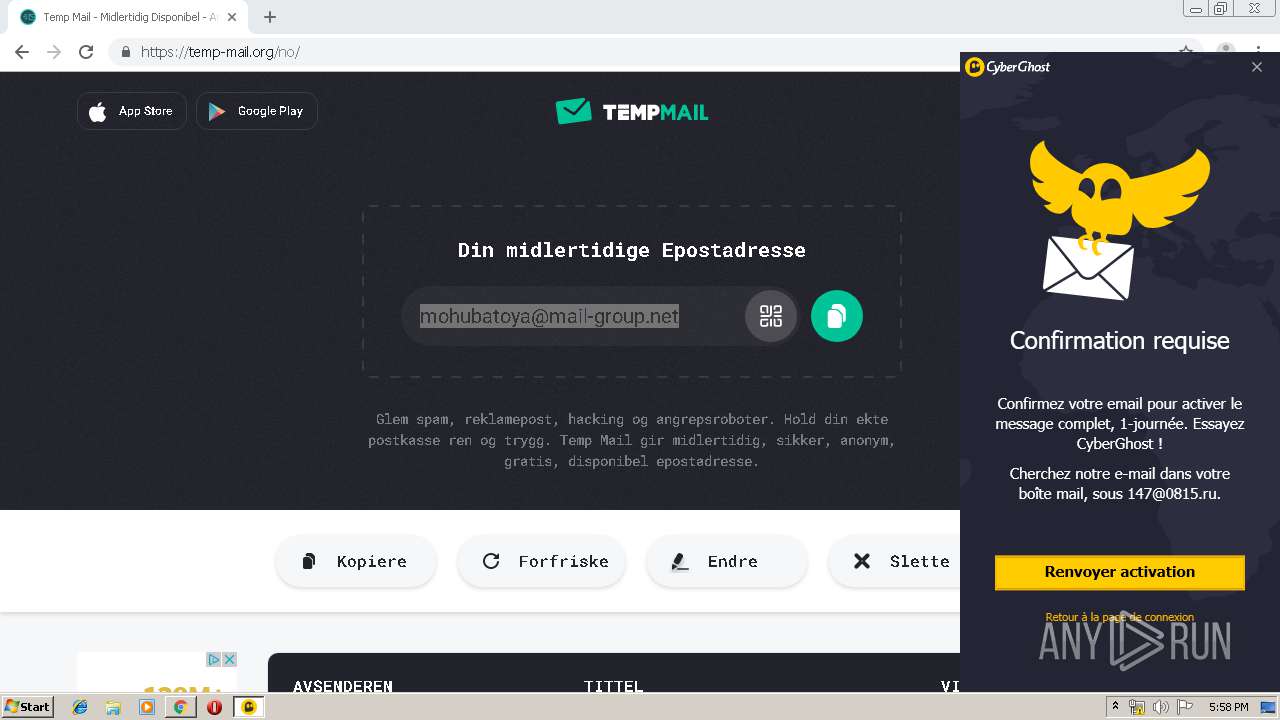
| URL: | https://www.cyberghostvpn.com/fr_FR/download-trial |
| Full analysis: | https://app.any.run/tasks/be15024b-f46c-4a74-8b6d-cba59e722d1b |
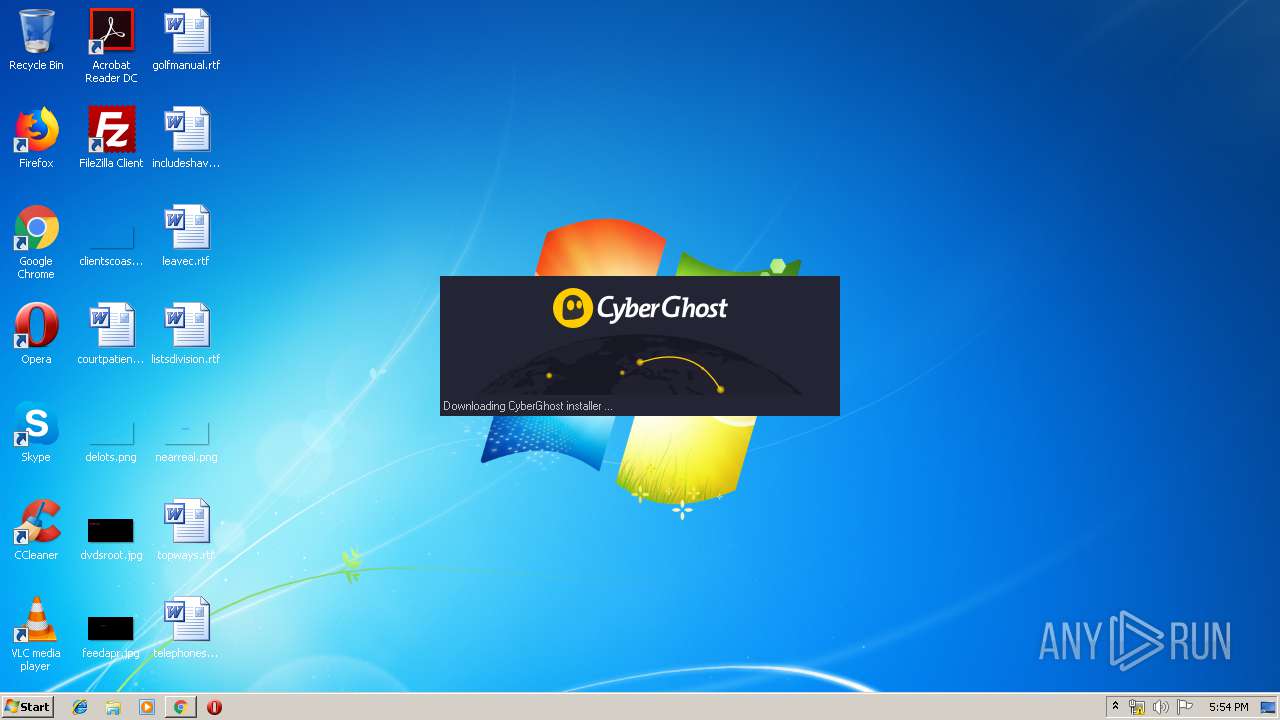
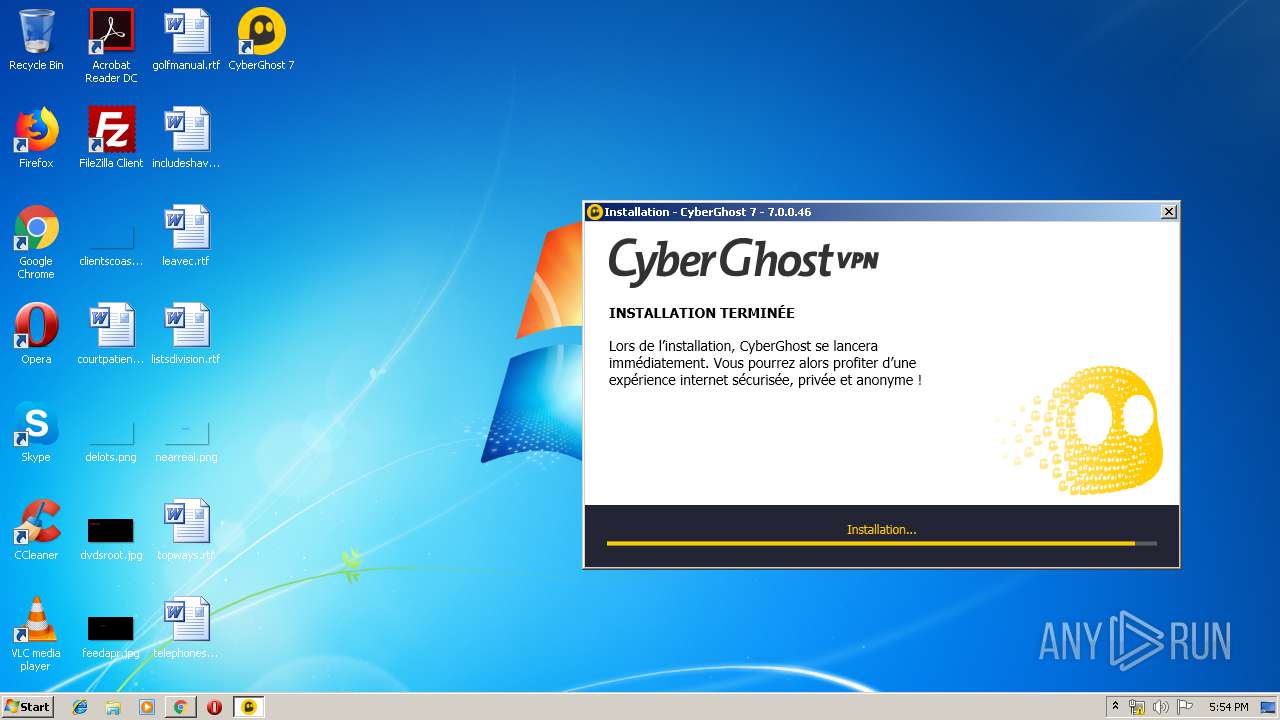
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2019, 16:53:33 |
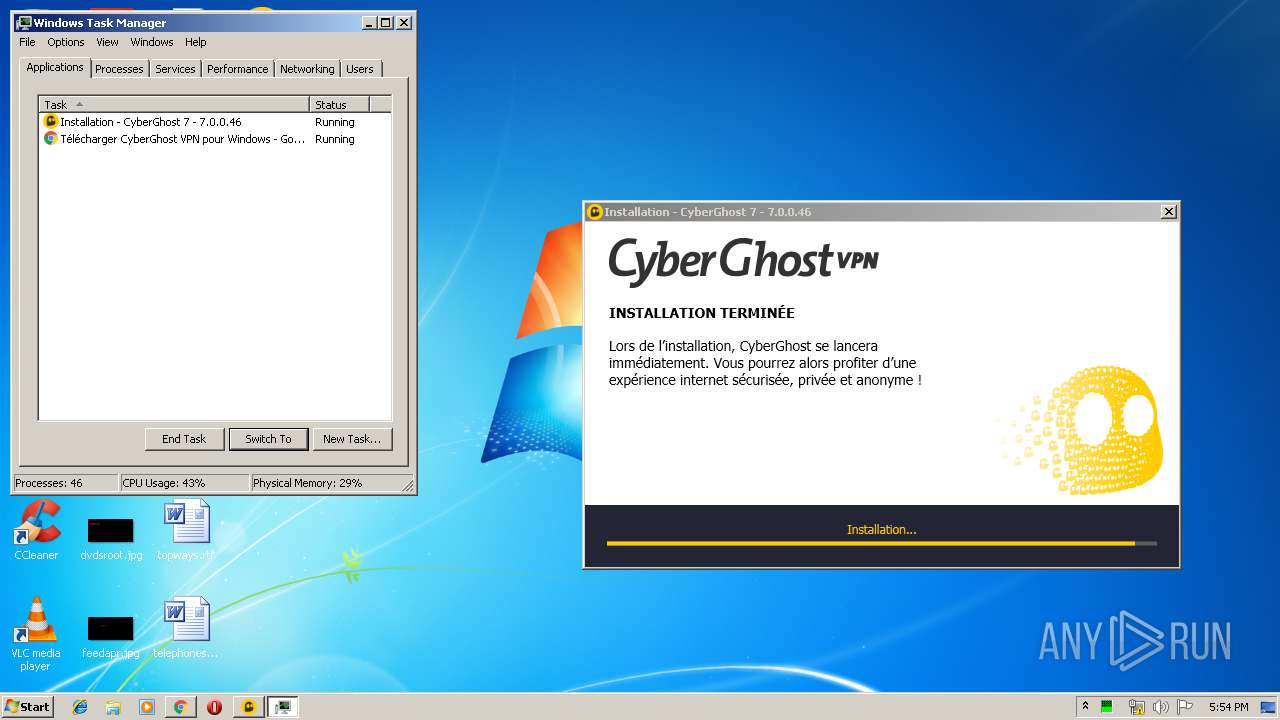
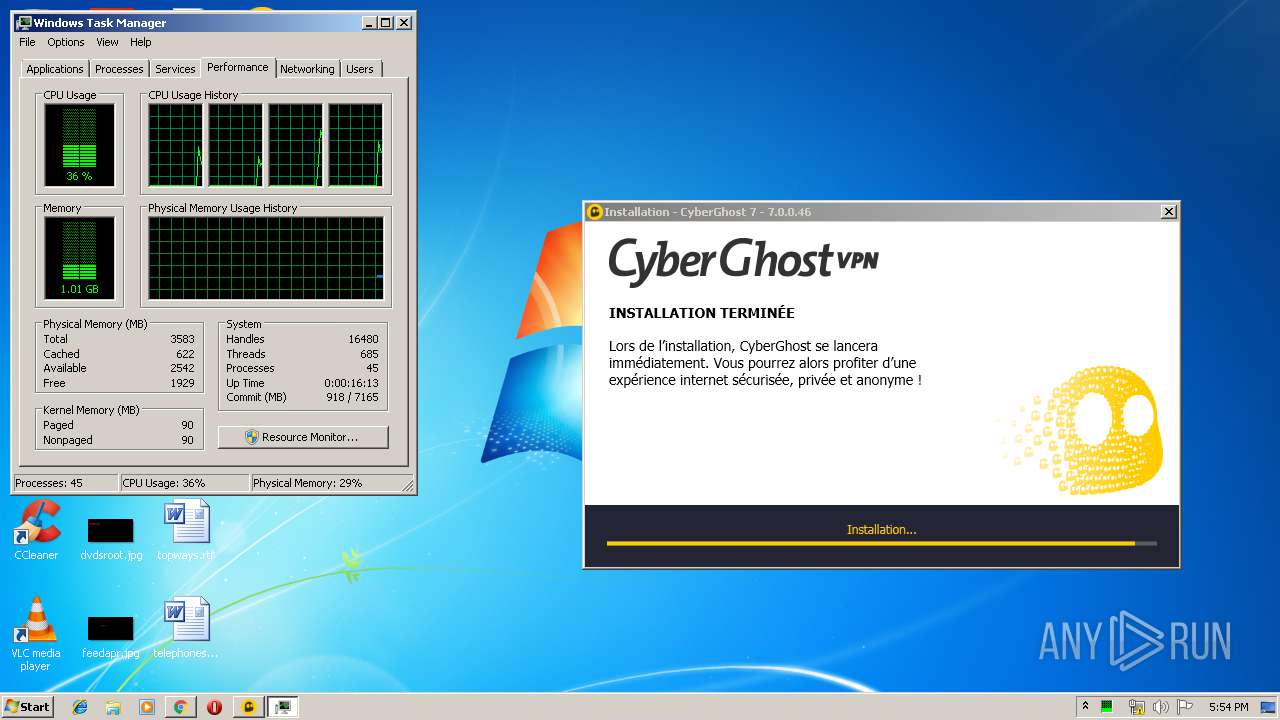
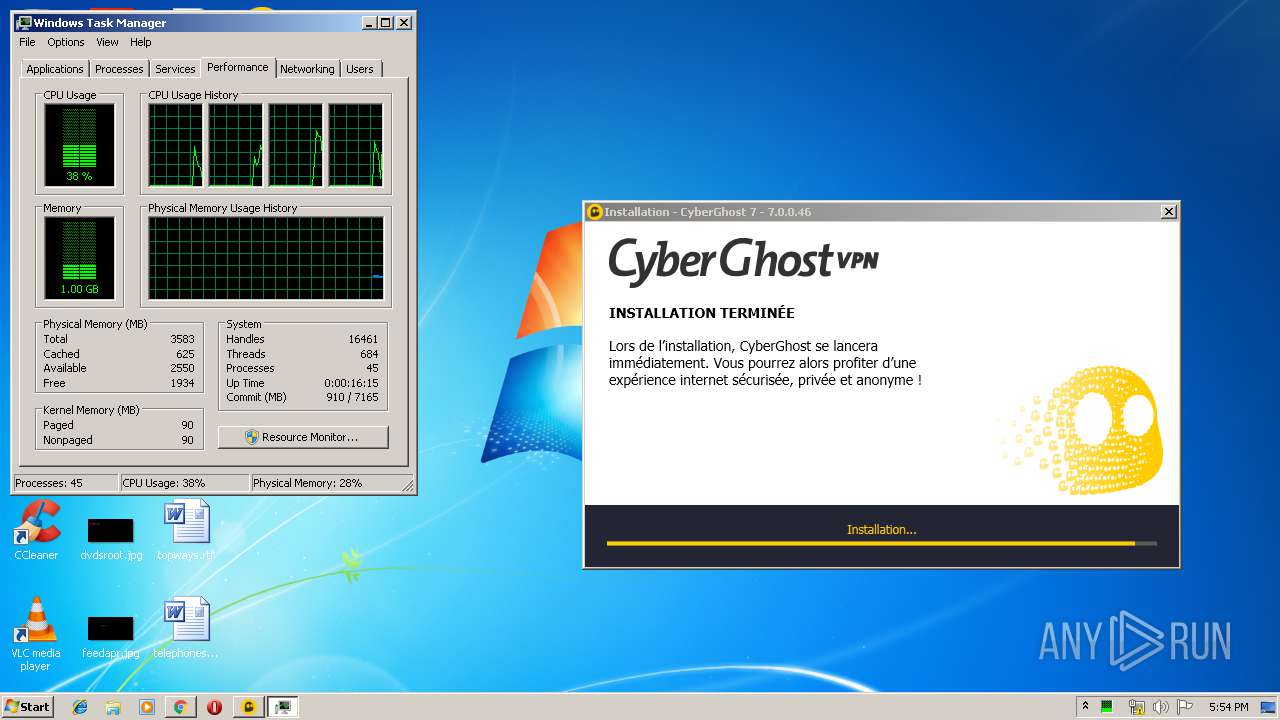
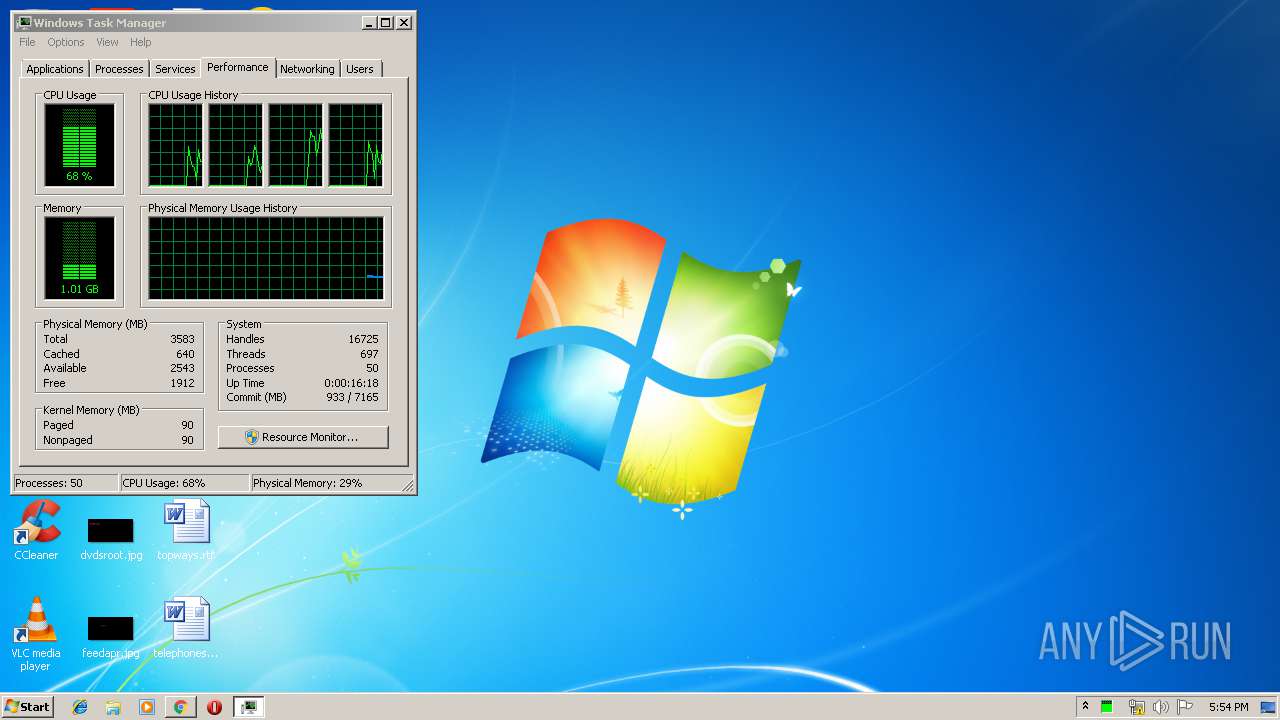
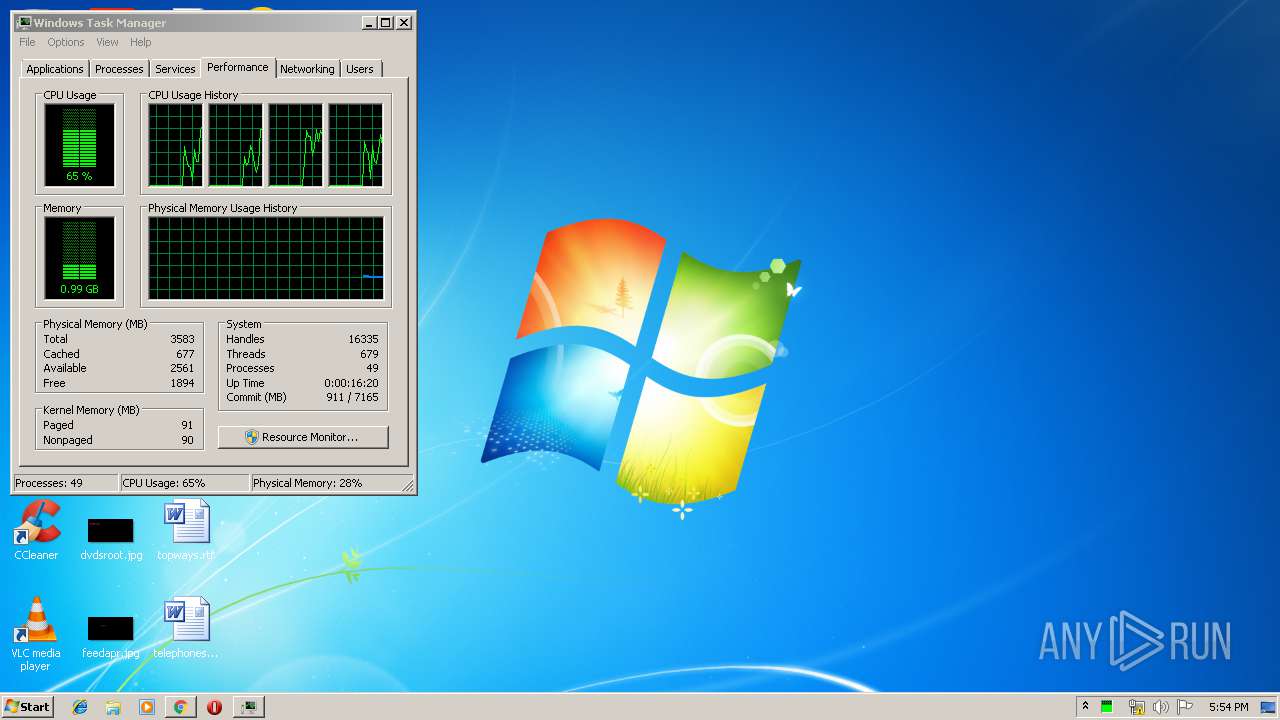
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D012F66228EDA080E491184ECE93A004 |
| SHA1: | 9CBCA9B69DBACAD46C955493DE2D0D1BCFA13DCE |
| SHA256: | 451AF2D20A682AD4DE64880800A7608B3DF9B90D069499DB15442EA04BC8C350 |
| SSDEEP: | 3:N8DSLzAXQThyKIYq+JARXMg:2OLsg1yV+JuMg |
MALICIOUS
Application was dropped or rewritten from another process
- cgsetup_fr_.exe (PID: 3532)
- cgsetup_fr_.exe (PID: 3708)
- tmp3498.tmp.exe (PID: 3144)
- CyberGhost.Service.exe (PID: 3096)
- CyberGhost.exe (PID: 3804)
- CyberGhost.Service.exe (PID: 3180)
- wyUpdate.exe (PID: 4012)
- CyberGhost.exe (PID: 3252)
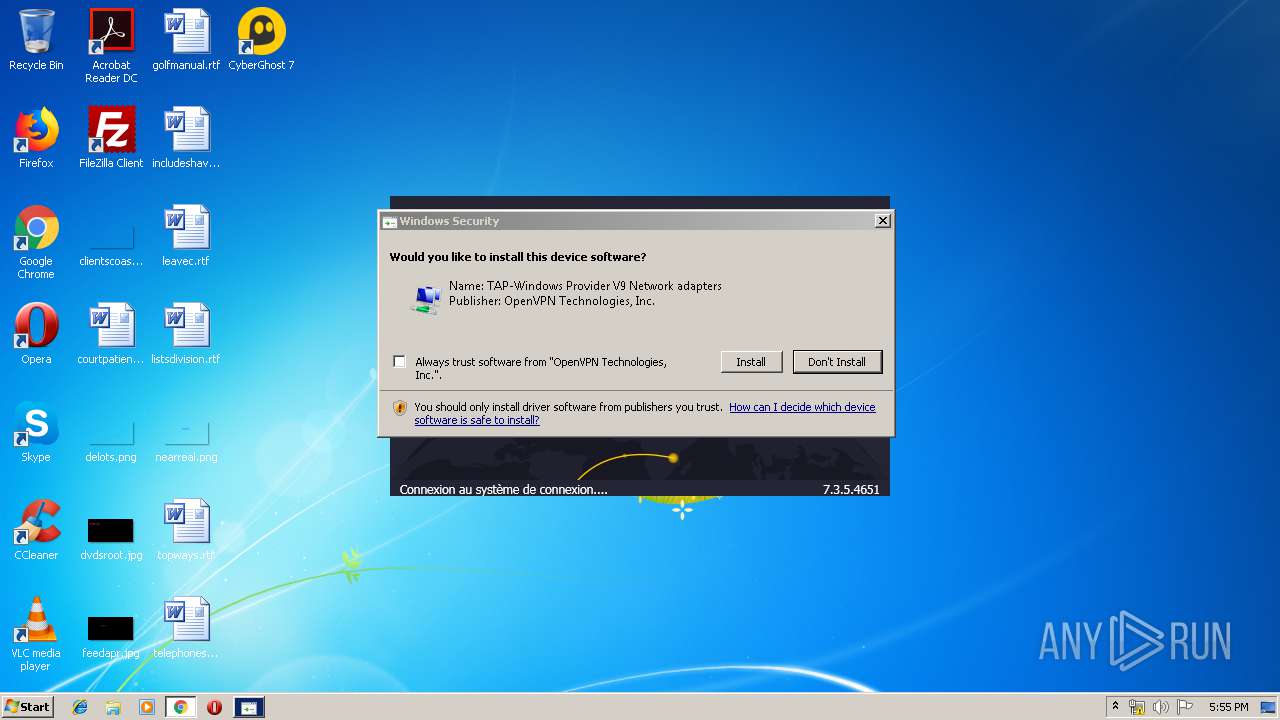
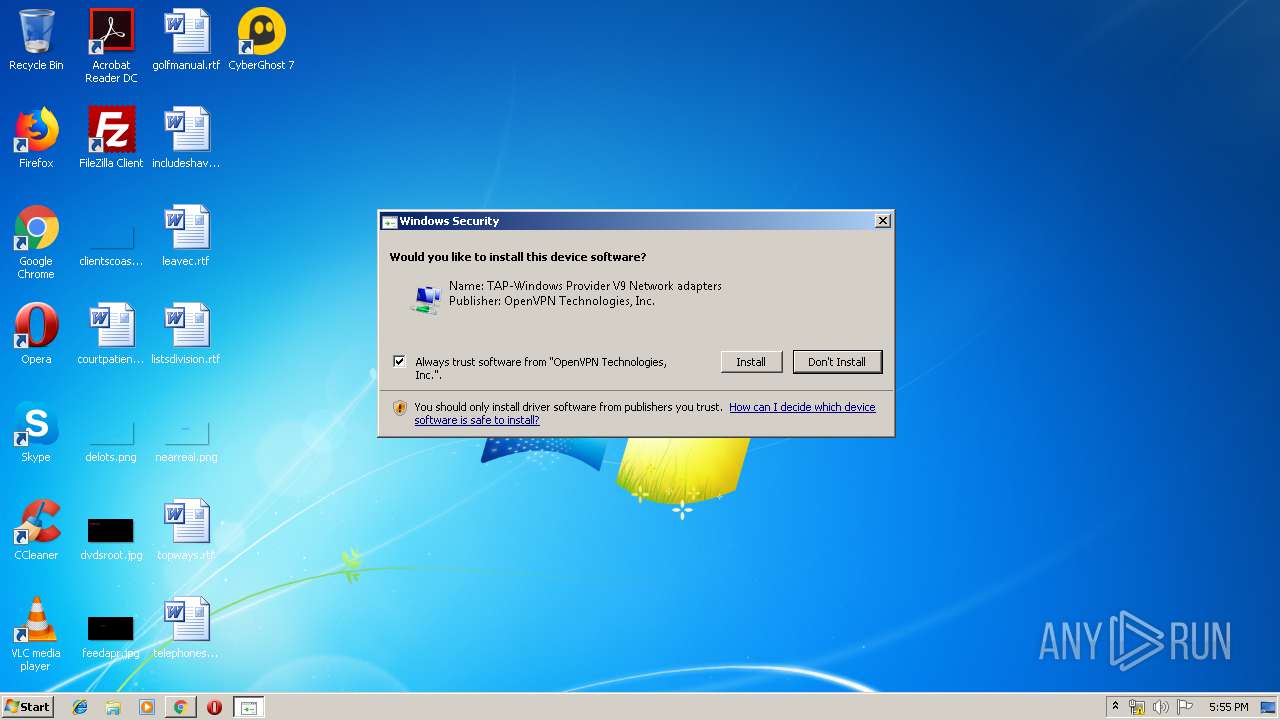
- tap-windows-9.21.2.exe (PID: 2656)
- nsF3A6.tmp (PID: 3240)
- nsF078.tmp (PID: 2912)
- tapinstall.exe (PID: 3352)
- tapinstall.exe (PID: 2120)
- nvspbind.exe (PID: 2180)
- nvspbind.exe (PID: 3228)
- nvspbind.exe (PID: 3536)
- wyUpdate.exe (PID: 3796)
- openssl.exe (PID: 2024)
Changes settings of System certificates
- cgsetup_fr_.exe (PID: 3708)
Loads dropped or rewritten executable
- CyberGhost.exe (PID: 3804)
- CyberGhost.Service.exe (PID: 3096)
- CyberGhost.Service.exe (PID: 3180)
- CyberGhost.exe (PID: 3252)
- tap-windows-9.21.2.exe (PID: 2656)
- openssl.exe (PID: 2024)
Changes the autorun value in the registry
- CyberGhost.exe (PID: 3252)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3716)
- tmp3498.tmp.exe (PID: 3144)
- cgsetup_fr_.exe (PID: 3708)
- tap-windows-9.21.2.exe (PID: 2656)
- tapinstall.exe (PID: 2120)
- DrvInst.exe (PID: 3836)
- DrvInst.exe (PID: 2152)
Adds / modifies Windows certificates
- cgsetup_fr_.exe (PID: 3708)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3716)
Reads Environment values
- tmp3498.tmp.exe (PID: 3144)
- CyberGhost.exe (PID: 3804)
- CyberGhost.Service.exe (PID: 3180)
- CyberGhost.exe (PID: 3252)
Creates a software uninstall entry
- tmp3498.tmp.exe (PID: 3144)
- tap-windows-9.21.2.exe (PID: 2656)
Creates files in the program directory
- CyberGhost.Service.exe (PID: 3096)
- tap-windows-9.21.2.exe (PID: 2656)
- tmp3498.tmp.exe (PID: 3144)
- openssl.exe (PID: 2024)
Modifies the open verb of a shell class
- CyberGhost.Service.exe (PID: 3180)
Executed as Windows Service
- CyberGhost.Service.exe (PID: 3180)
- vssvc.exe (PID: 2692)
Creates files in the Windows directory
- wyUpdate.exe (PID: 4012)
- DrvInst.exe (PID: 3836)
- wyUpdate.exe (PID: 3796)
- DrvInst.exe (PID: 2152)
Changes IE settings (feature browser emulation)
- CyberGhost.exe (PID: 3804)
Starts application with an unusual extension
- tap-windows-9.21.2.exe (PID: 2656)
Executed via COM
- DrvInst.exe (PID: 3836)
- DrvInst.exe (PID: 2936)
- DrvInst.exe (PID: 2152)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3836)
Creates files in the driver directory
- DrvInst.exe (PID: 3836)
- DrvInst.exe (PID: 2152)
Removes files from Windows directory
- DrvInst.exe (PID: 3836)
- wyUpdate.exe (PID: 4012)
- wyUpdate.exe (PID: 3796)
- DrvInst.exe (PID: 2152)
Reads Internet Cache Settings
- CyberGhost.exe (PID: 3252)
Creates files in the user directory
- CyberGhost.exe (PID: 3252)
Reads internet explorer settings
- CyberGhost.exe (PID: 3252)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 3716)
Reads settings of System Certificates
- tmp3498.tmp.exe (PID: 3144)
- CyberGhost.exe (PID: 3252)
Application launched itself
- chrome.exe (PID: 3716)
Changes settings of System certificates
- chrome.exe (PID: 3016)
- DrvInst.exe (PID: 3836)
Dropped object may contain Bitcoin addresses
- tmp3498.tmp.exe (PID: 3144)
Manual execution by user
- taskmgr.exe (PID: 3372)
Searches for installed software
- DrvInst.exe (PID: 3836)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
58
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5508887290613321166 --mojo-platform-channel-handle=2908 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=597061702632338115 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2596 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=91695122788461382 --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12607807700917980708 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4195936992888362070 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6318735419290656974 --mojo-platform-channel-handle=4444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18154124327850865829 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14274974558874241922 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,6326749828871123424,9505727835561297477,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16207656336398937580 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{2d0dee5c-dcac-6afc-8bab-f440fc951650} Global\{03104f54-eb1c-4dca-d50e-0c284c56466f} C:\Windows\System32\DriverStore\Temp\{7474a829-85e0-3470-e79d-a03e2790a11a}\oemvista.inf C:\Windows\System32\DriverStore\Temp\{7474a829-85e0-3470-e79d-a03e2790a11a}\tap0901.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 175
Read events
2 848
Write events
1 267
Delete events
60
Modification events
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3716-13207683228922875 |
Value: 259 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3716) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
71
Suspicious files
228
Text files
978
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2b7466e1-5d3a-4d9c-a29a-c9ead202b158.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFdf686.TMP | text | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFdf6f3.TMP | text | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdf676.TMP | text | |
MD5:— | SHA256:— | |||
| 3716 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
183
DNS requests
109
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3016 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEChOOcFLOG2InHKZ5YzQWlc%3D | US | der | 727 b | whitelisted |
3016 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3016 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBS83pEmglYTXfyF78OS%2BRiTRWadkgQULGn%2FgMmHkK404bTnTJOFmUDpp7ICEQDDbF%2Fu1THHEl%2B%2BZyPPnmDQ | US | der | 472 b | whitelisted |
3016 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.3 Kb | whitelisted |
3016 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
3708 | cgsetup_fr_.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3016 | chrome.exe | GET | 200 | 52.222.149.30:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3016 | chrome.exe | GET | 200 | 74.125.110.137:80 | http://r4---sn-5goeen7y.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.22.109&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1563209540&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3016 | chrome.exe | 52.222.149.30:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
3016 | chrome.exe | 172.217.23.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3016 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3016 | chrome.exe | 104.20.175.46:443 | www.cyberghostvpn.com | Cloudflare Inc | US | shared |
3016 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3016 | chrome.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3016 | chrome.exe | 23.111.9.35:443 | use.fontawesome.com | netDNA | US | suspicious |
3016 | chrome.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3016 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3016 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cyberghostvpn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdn.trustpilot.net |
| whitelisted |
Threats
Process | Message |
|---|---|
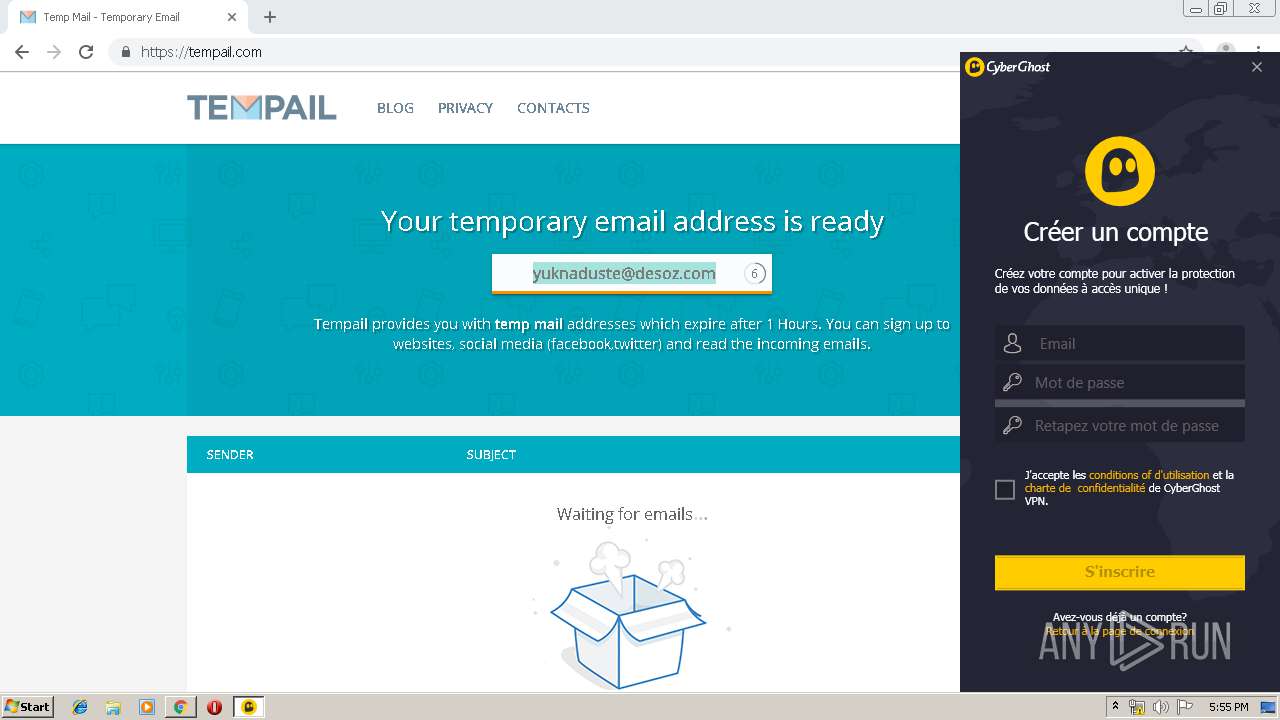
CyberGhost.Service.exe | Checking for Update on https://download.cyberghostvpn.com/windows/updates/7/
|
CyberGhost.Service.exe | STORING SETTINGS DUE TO CHANGE ON: ClickId
|
CyberGhost.exe | STORING SETTINGS DUE TO CHANGE ON: AutoStart
|
CyberGhost.Service.exe | Checking for Update on https://download.cyberghostvpn.com/windows/updates/7/
|
CyberGhost.Service.exe | STORING SETTINGS DUE TO CHANGE ON: Challenge
|
CyberGhost.exe | STORING SETTINGS DUE TO CHANGE ON: IsResetted
|
CyberGhost.exe | STORING SETTINGS DUE TO CHANGE ON: LastProductId
|