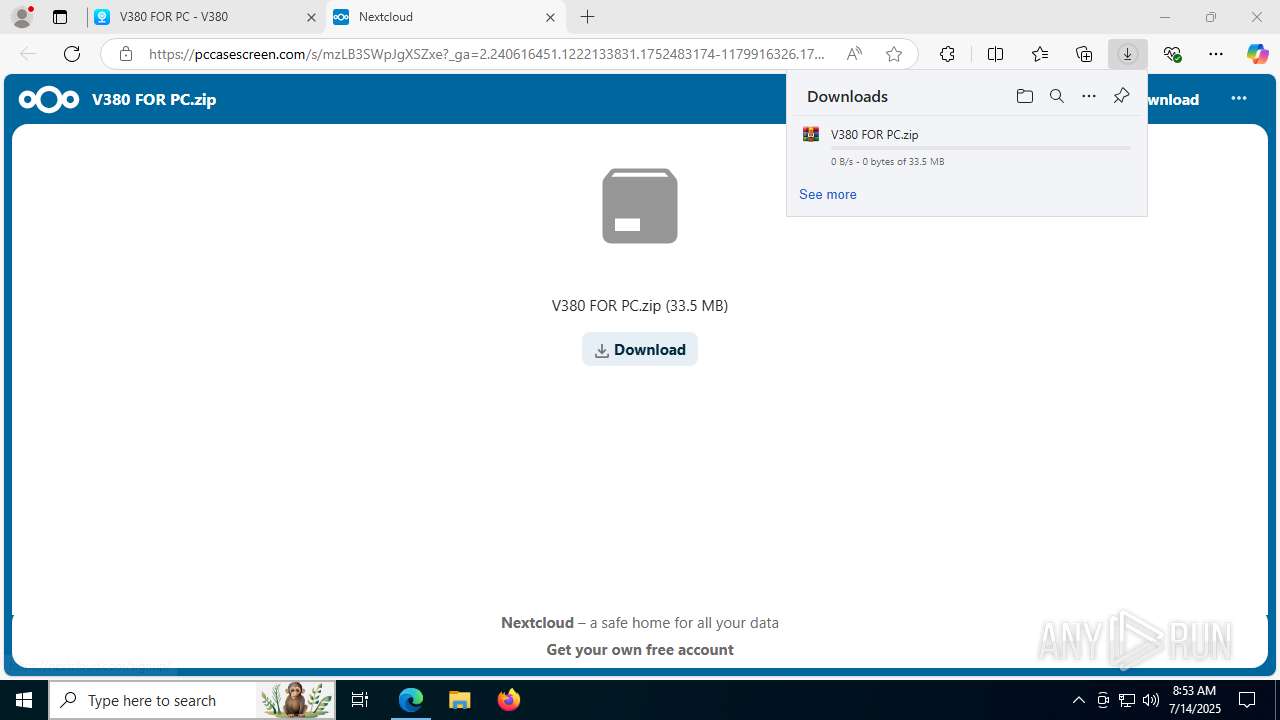
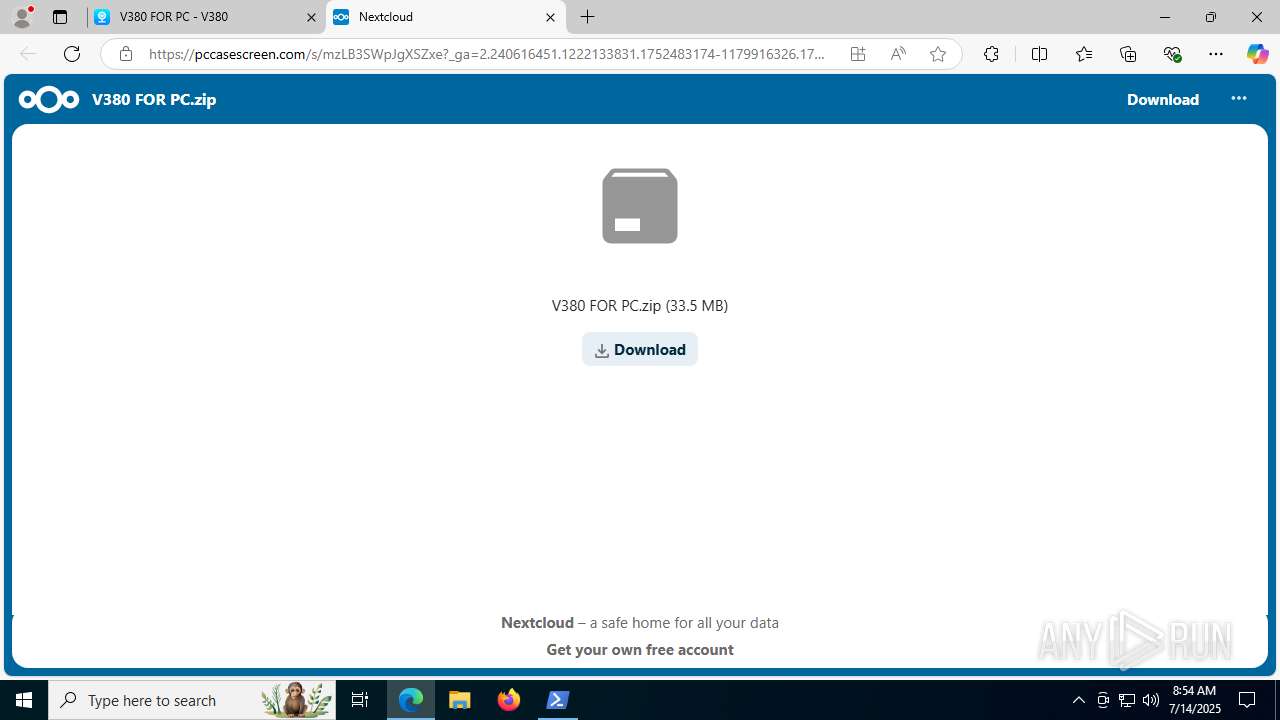
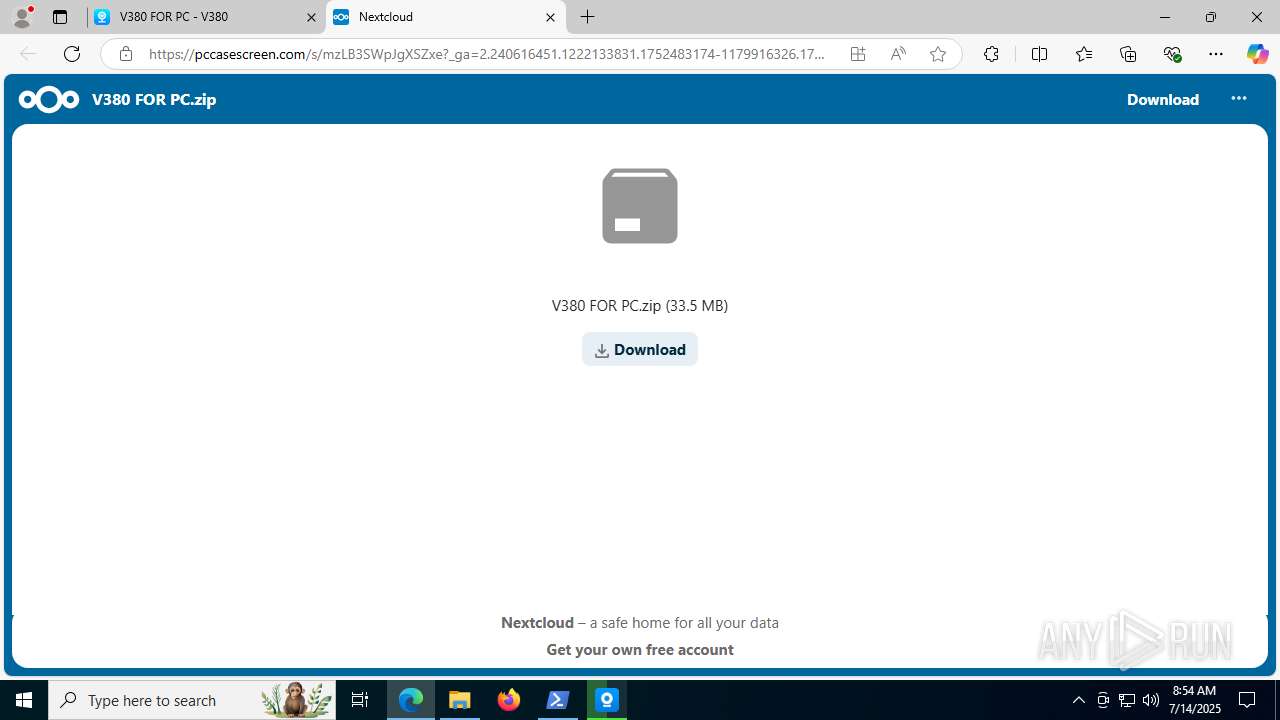
| URL: | https://eur02.safelinks.protection.outlook.com/?url=https%3A%2F%2Fv380.org%2Fv380-for-pc%2F&data=05%7C02%7CSOCMonitoring%40sterling.ng%7C9fbf2ad3177148deebe108ddc2aca50f%7C4c8a9f7a11fc4fc290990b68f72a197e%7C0%7C0%7C638880771065498976%7CUnknown%7CTWFpbGZsb3d8eyJFbXB0eU1hcGkiOnRydWUsIlYiOiIwLjAuMDAwMCIsIlAiOiJXaW4zMiIsIkFOIjoiTWFpbCIsIldUIjoyfQ%3D%3D%7C0%7C%7C%7C&sdata=3cqSleue2yKDUyByB8X9blGQiSc1Pz4AD3x66wgl8og%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/cf0ffb71-286c-4a0f-b02c-895f0f7a68f7 |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2025, 08:52:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
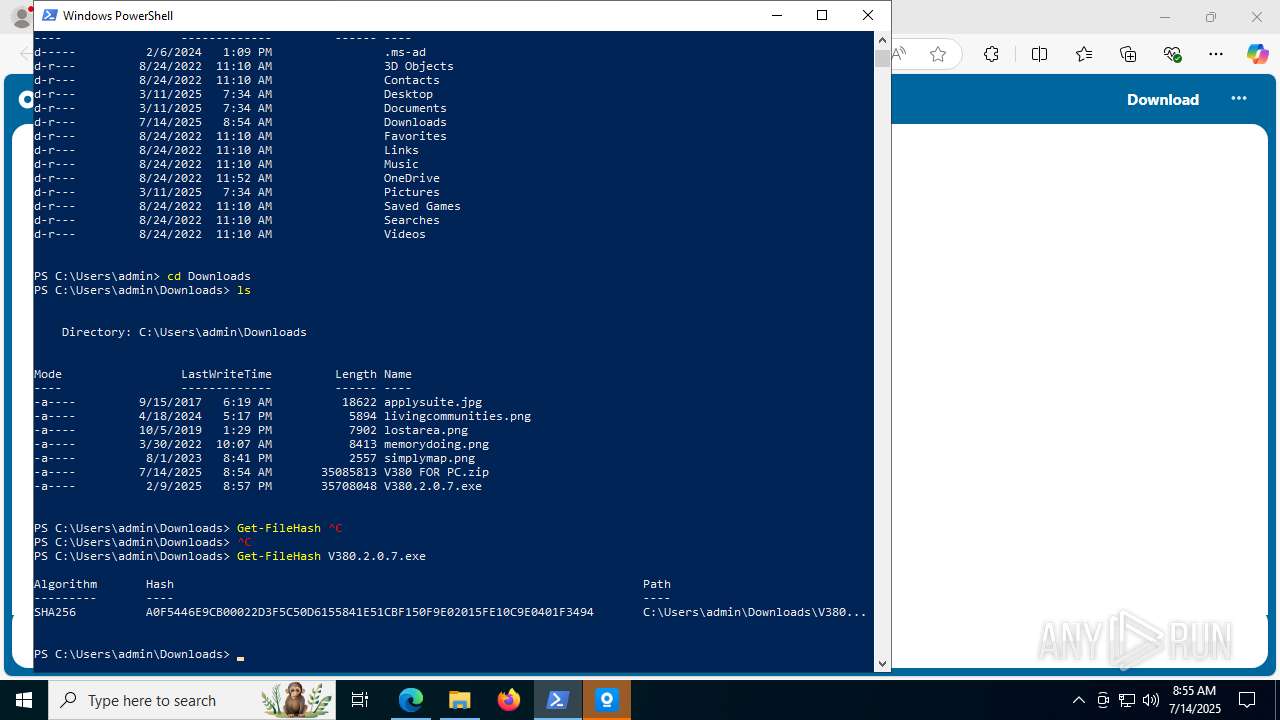
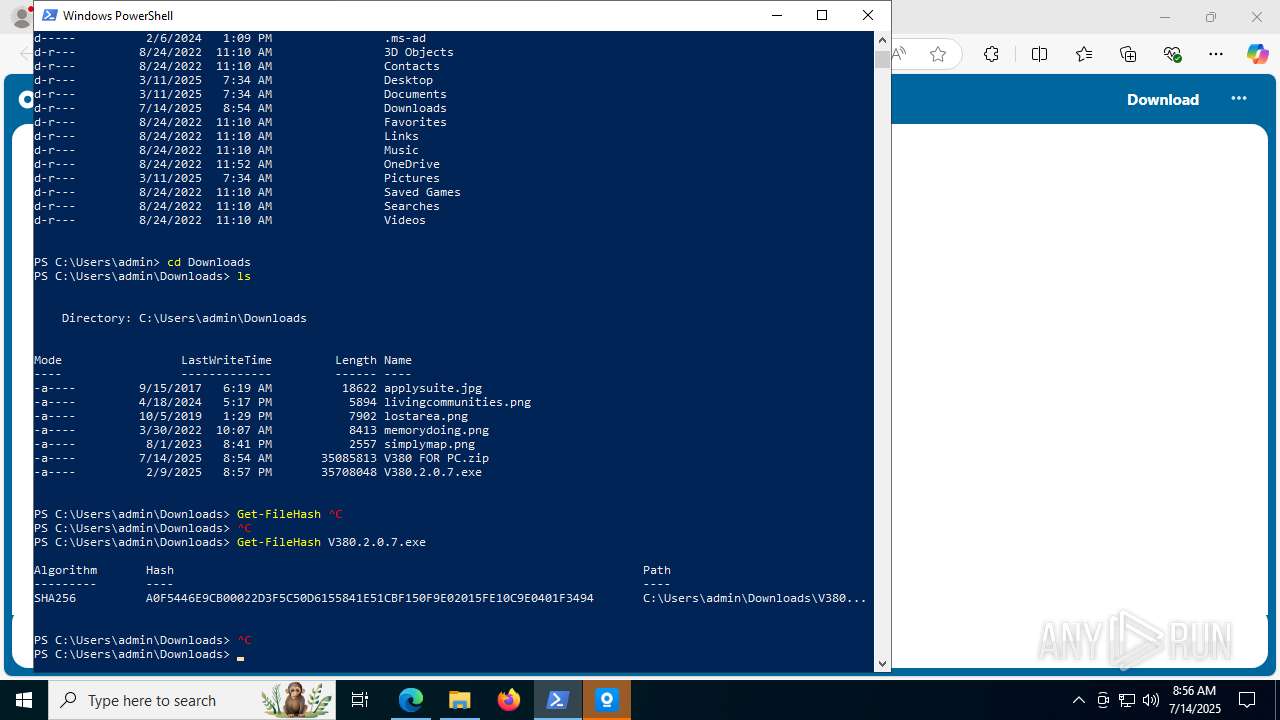
| MD5: | 17DD486F920A6C0FA16B50066A081FCF |
| SHA1: | AF15B168B4C91CC06B4509BCF9B224D4EA47FB56 |
| SHA256: | 451AC322822619C2B498DA51974C083620A52B0475EA2BC8CEA1D54B90683192 |
| SSDEEP: | 6:2hf5V9iRXPN3z4DyvKqSBNZbLUCRx7S7XKdOXLEOFVaVbWFZLsfhdtqHNwAmSSie:2hhqxMDyvbMbfSTKEEOauN1Si5Plh77U |
MALICIOUS
No malicious indicators.SUSPICIOUS
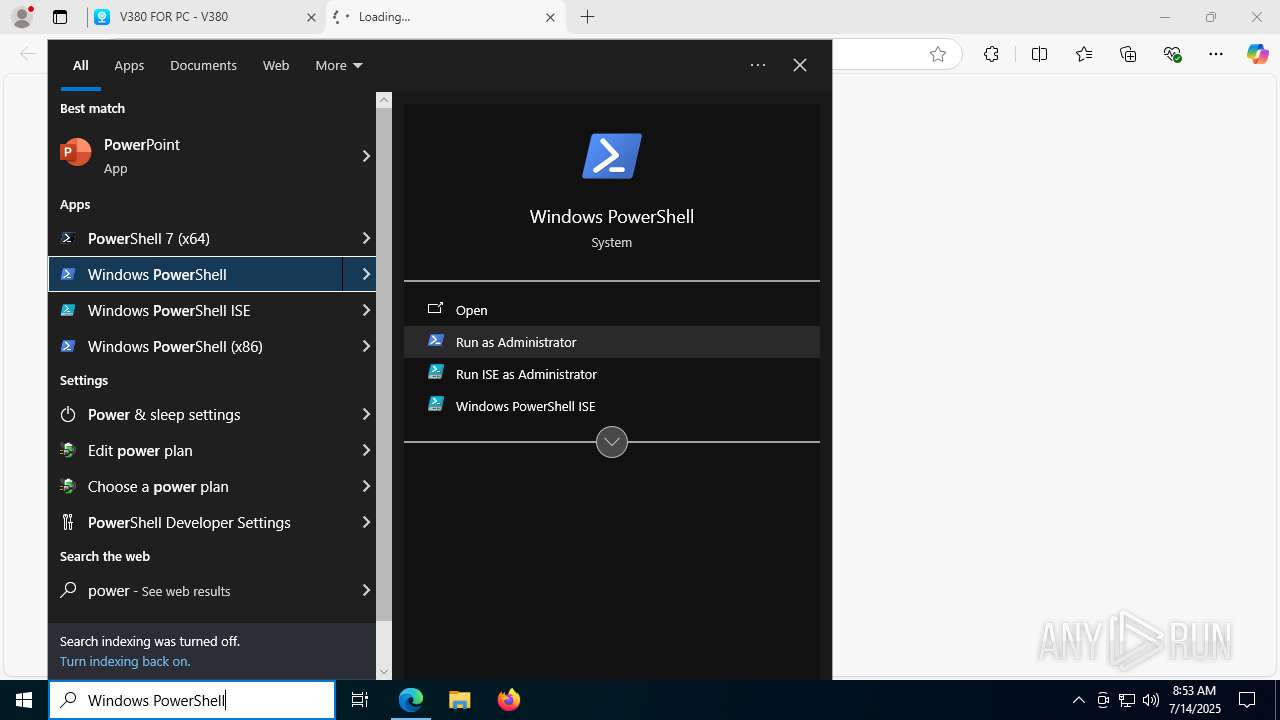
The process executes via Task Scheduler
- powershell.exe (PID: 7640)
Reads security settings of Internet Explorer
- V380.2.0.7.tmp (PID: 7236)
- ShellExperienceHost.exe (PID: 8096)
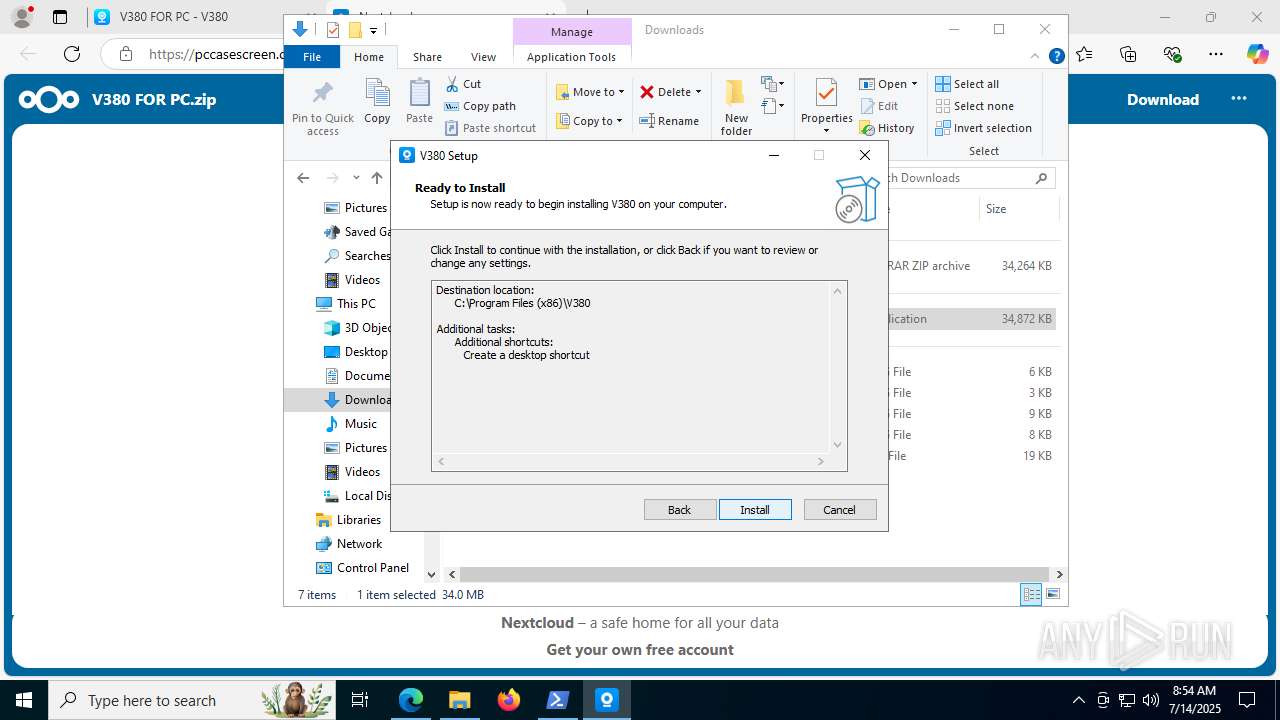
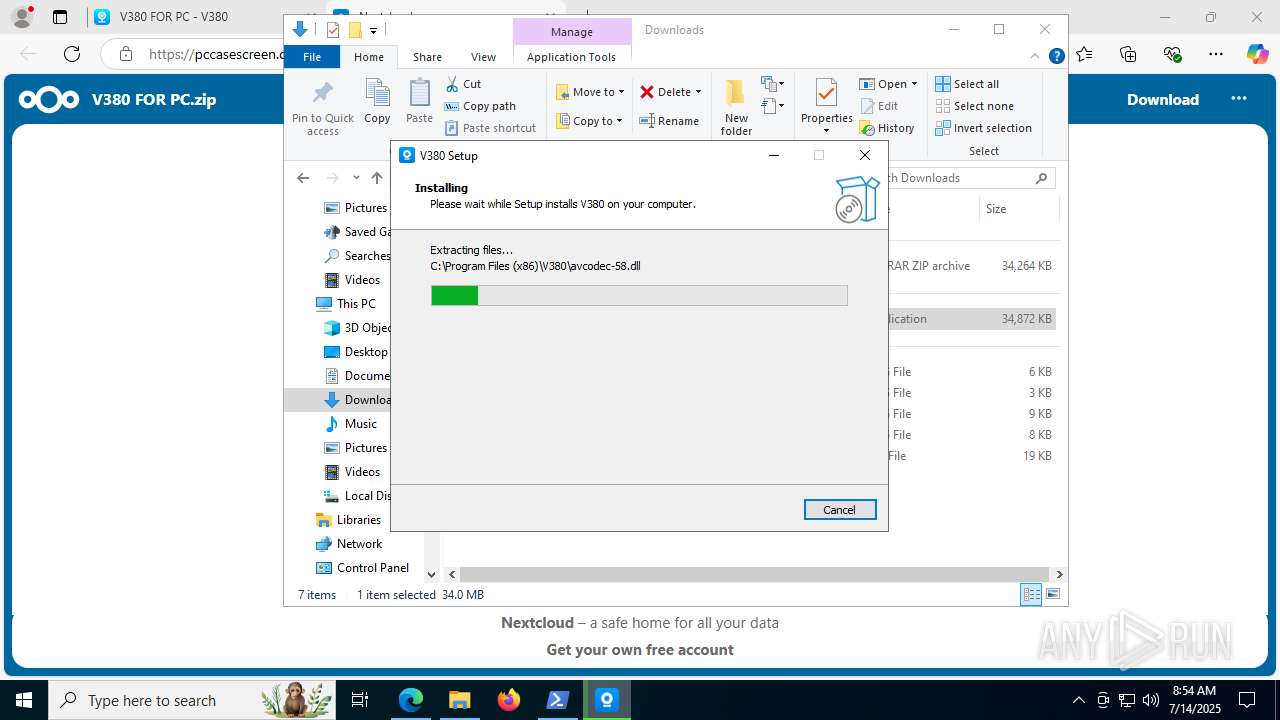
Executable content was dropped or overwritten
- V380.2.0.7.exe (PID: 7244)
- V380.2.0.7.tmp (PID: 1932)
- V380.2.0.7.exe (PID: 4324)
Reads the Windows owner or organization settings
- V380.2.0.7.tmp (PID: 1932)
Process drops legitimate windows executable
- V380.2.0.7.tmp (PID: 1932)
The process drops C-runtime libraries
- V380.2.0.7.tmp (PID: 1932)
Connects to unusual port
- V380Login.exe (PID: 4816)
There is functionality for taking screenshot (YARA)
- V380Login.exe (PID: 4816)
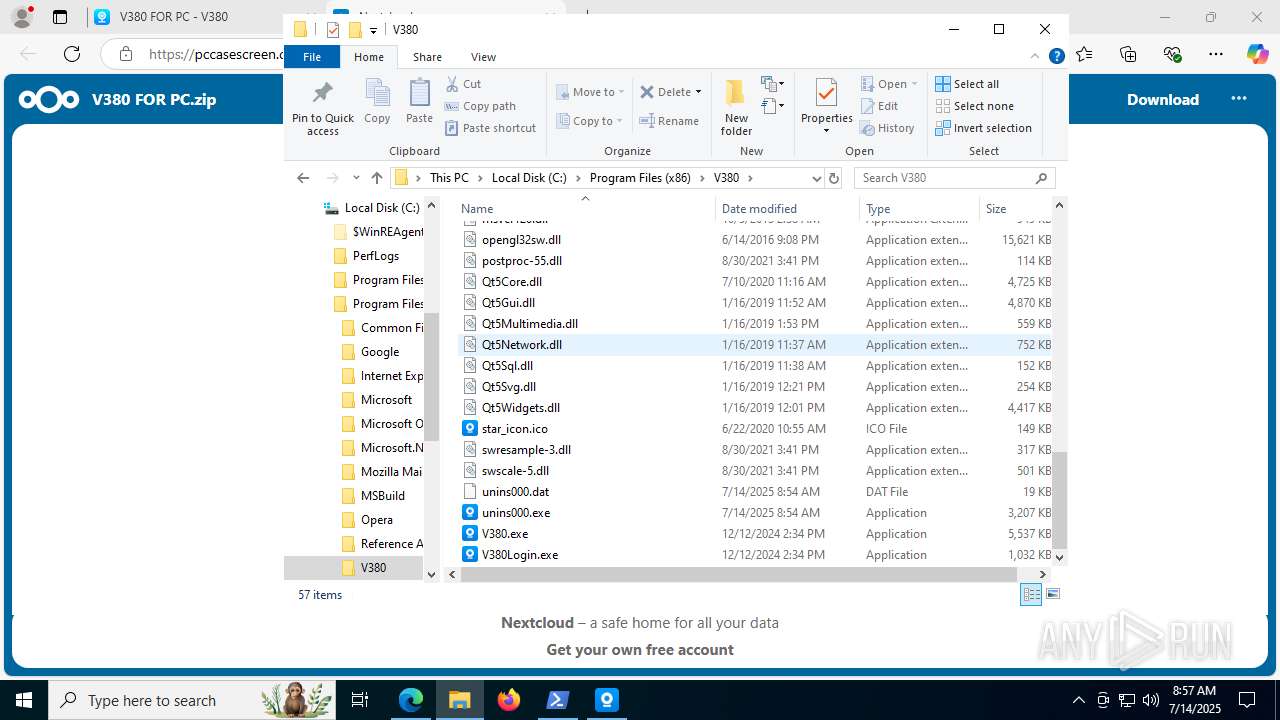
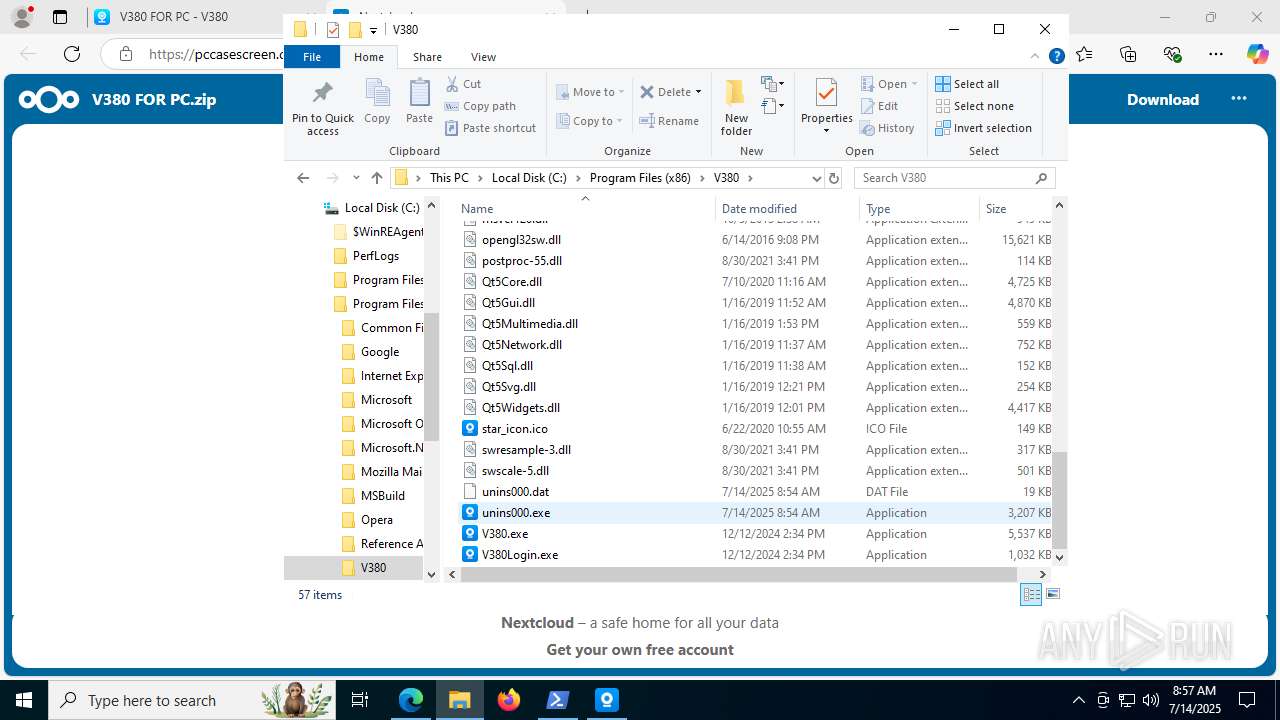
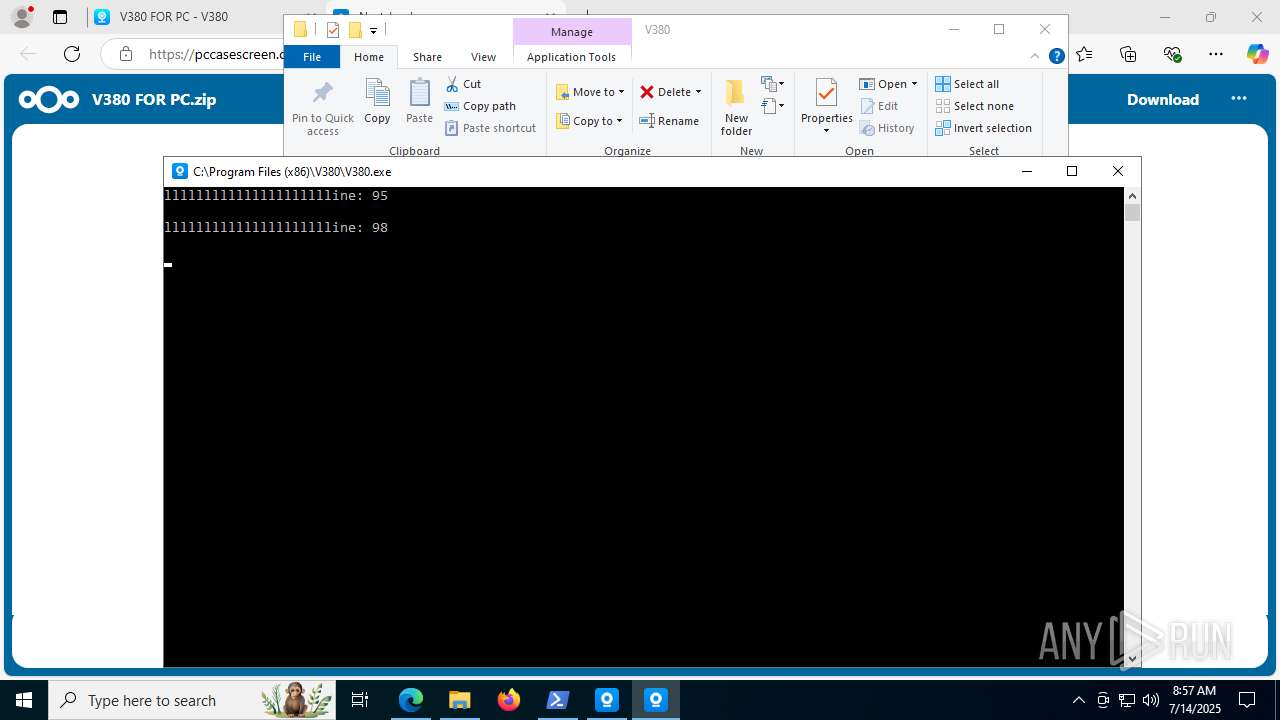
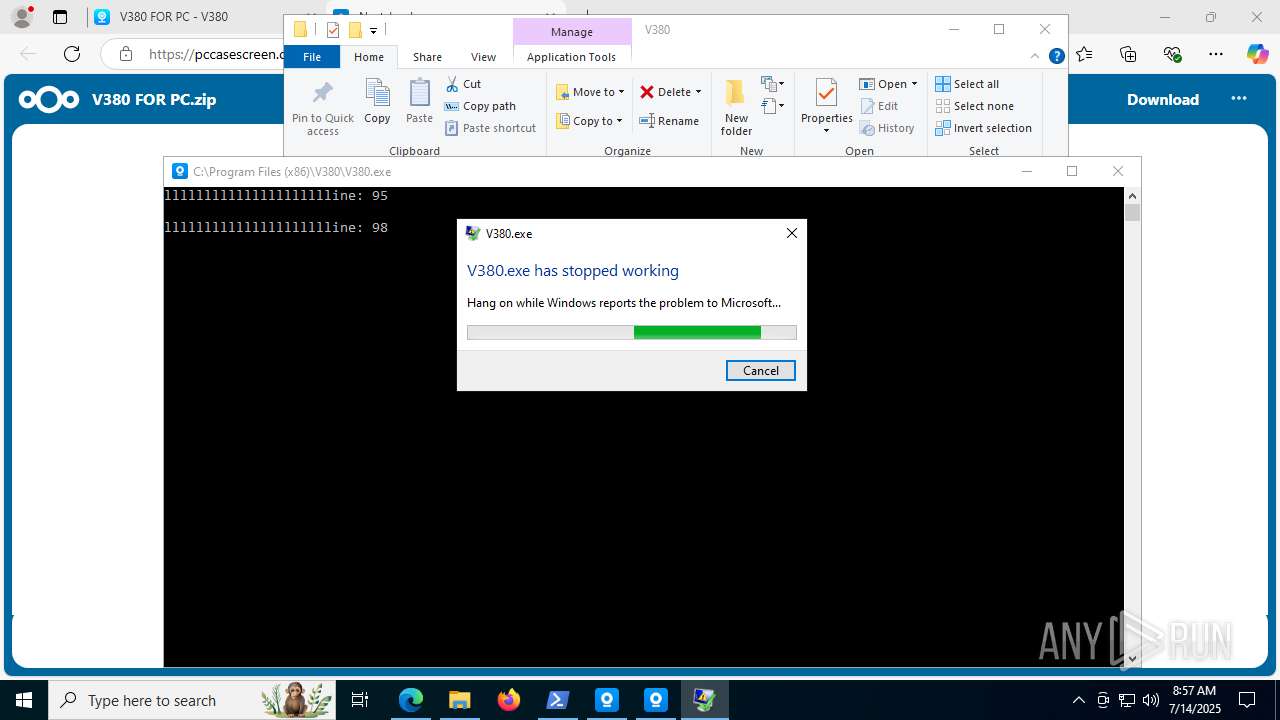
Executes application which crashes
- V380.exe (PID: 8112)
INFO
Application launched itself
- msedge.exe (PID: 7080)
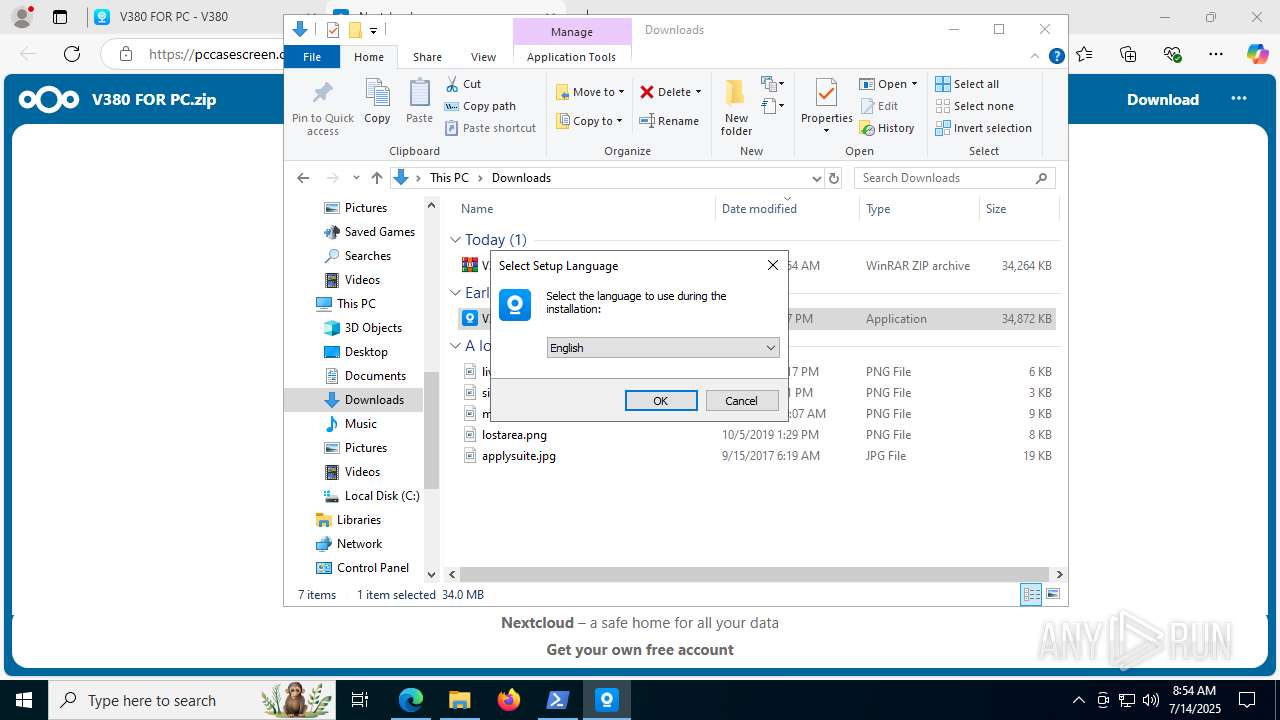
Checks supported languages
- identity_helper.exe (PID: 7556)
- V380.2.0.7.exe (PID: 7244)
- V380.2.0.7.tmp (PID: 7236)
- V380.2.0.7.exe (PID: 4324)
- V380.2.0.7.tmp (PID: 1932)
- ShellExperienceHost.exe (PID: 8096)
- V380Login.exe (PID: 4816)
- V380.exe (PID: 8112)
Reads the computer name
- identity_helper.exe (PID: 7556)
- V380.2.0.7.tmp (PID: 7236)
- V380.2.0.7.tmp (PID: 1932)
- V380Login.exe (PID: 4816)
- ShellExperienceHost.exe (PID: 8096)
Reads Environment values
- identity_helper.exe (PID: 7556)
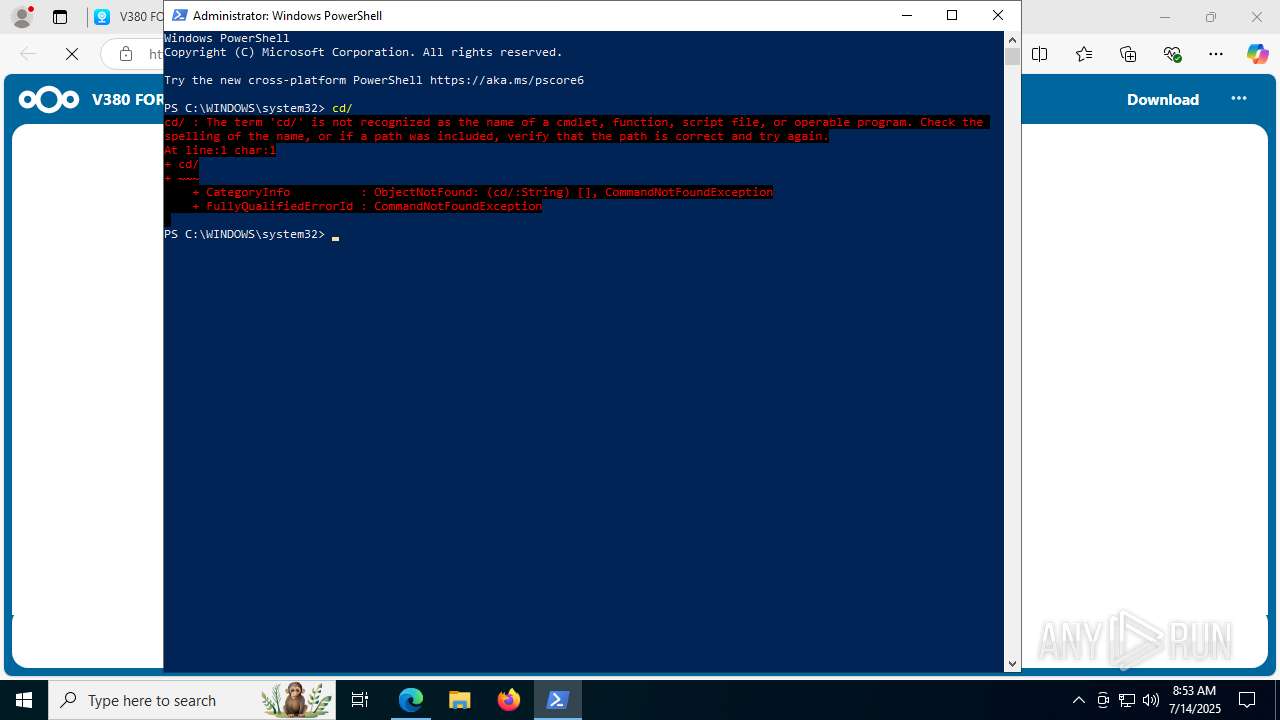
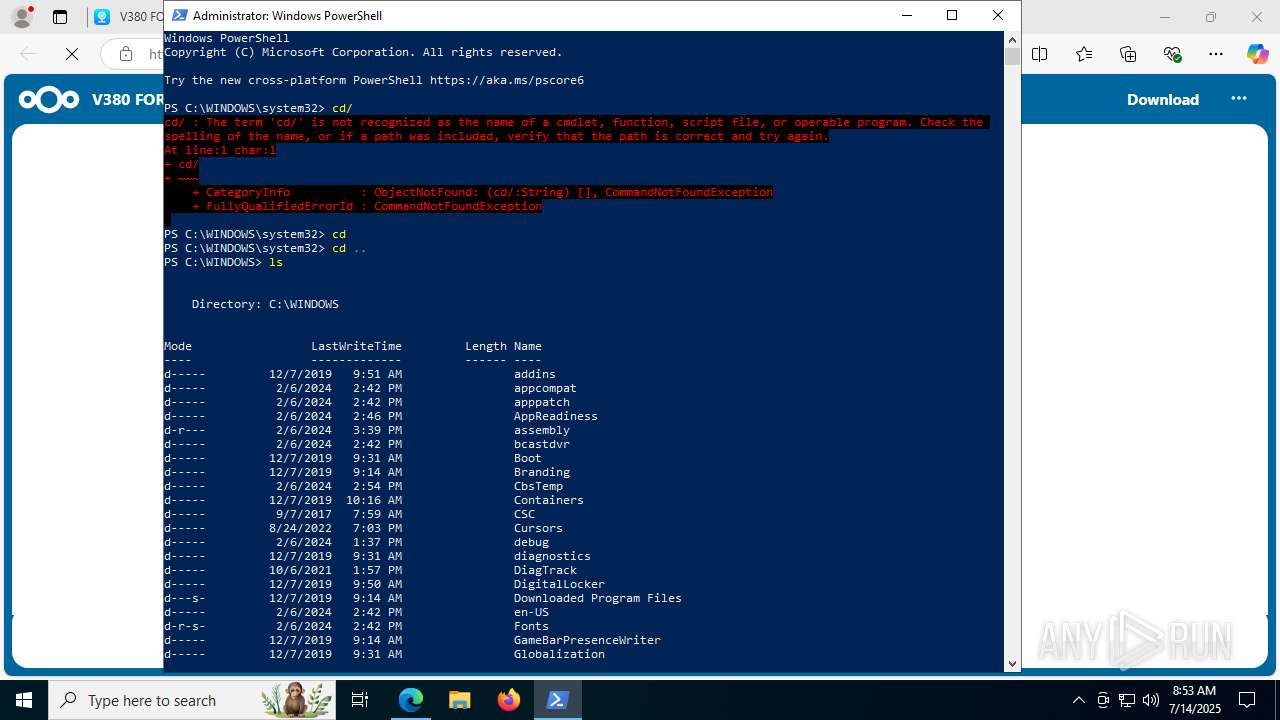
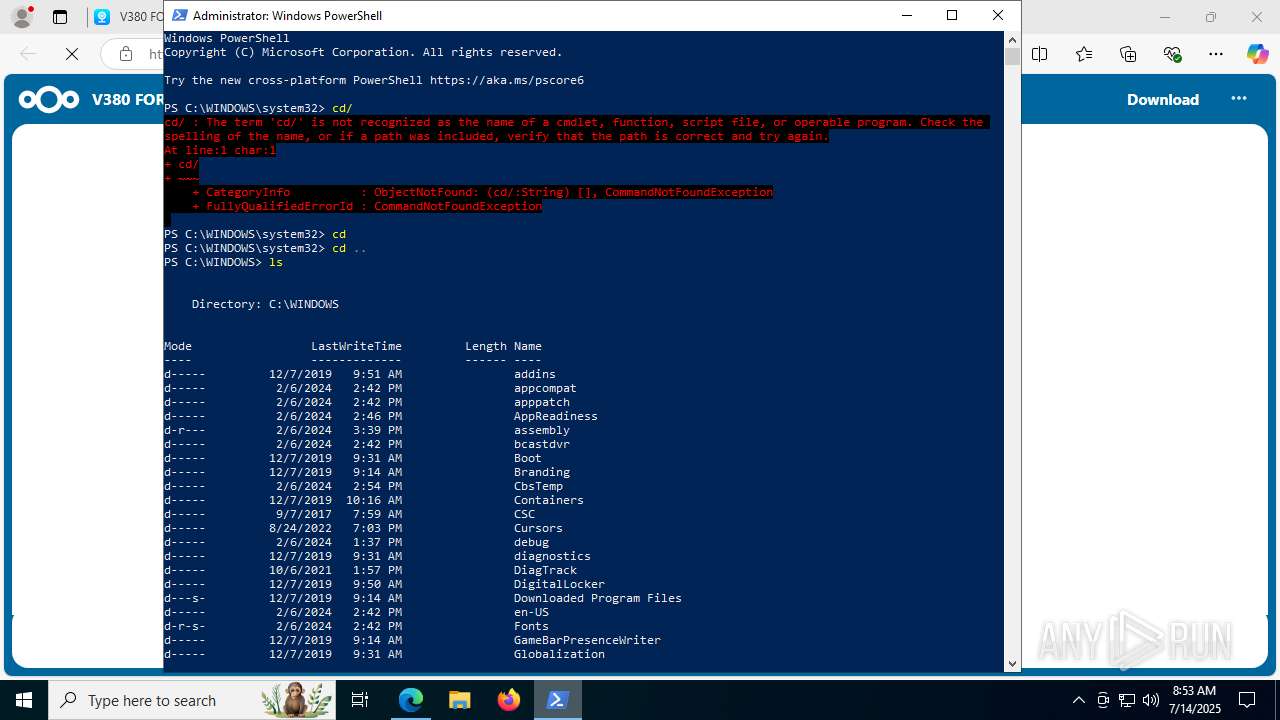
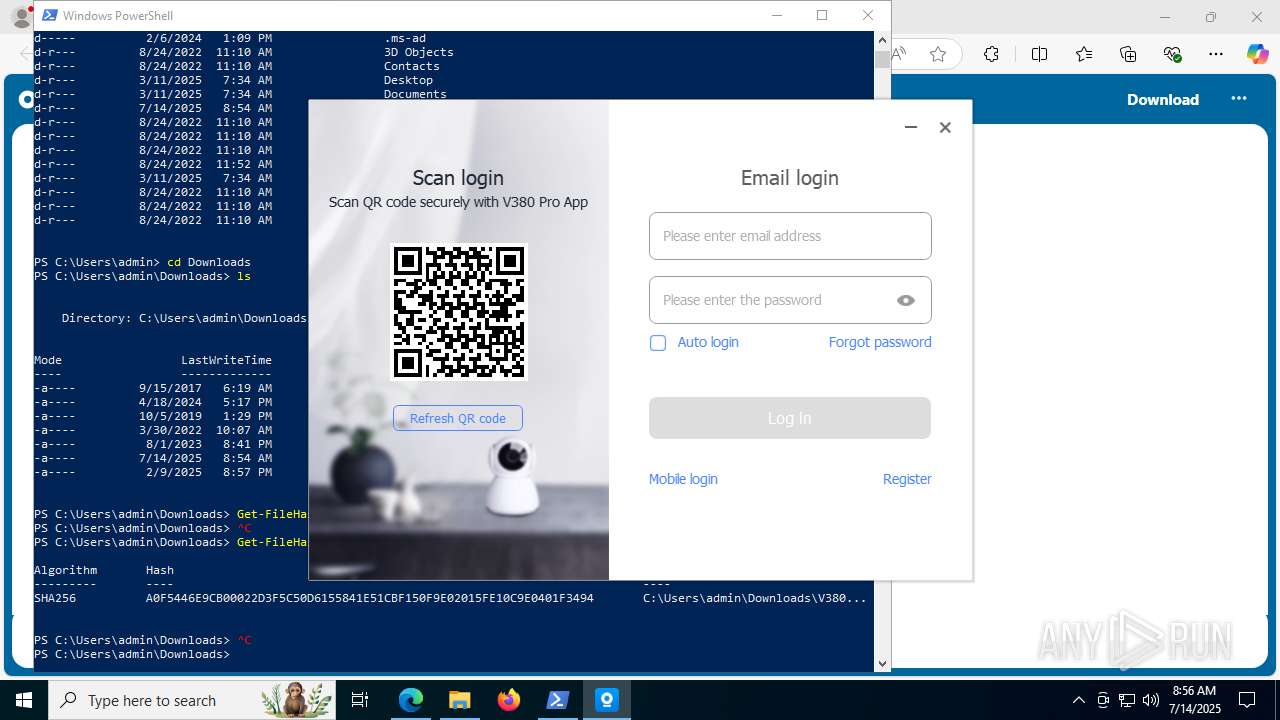
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7640)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 5884)
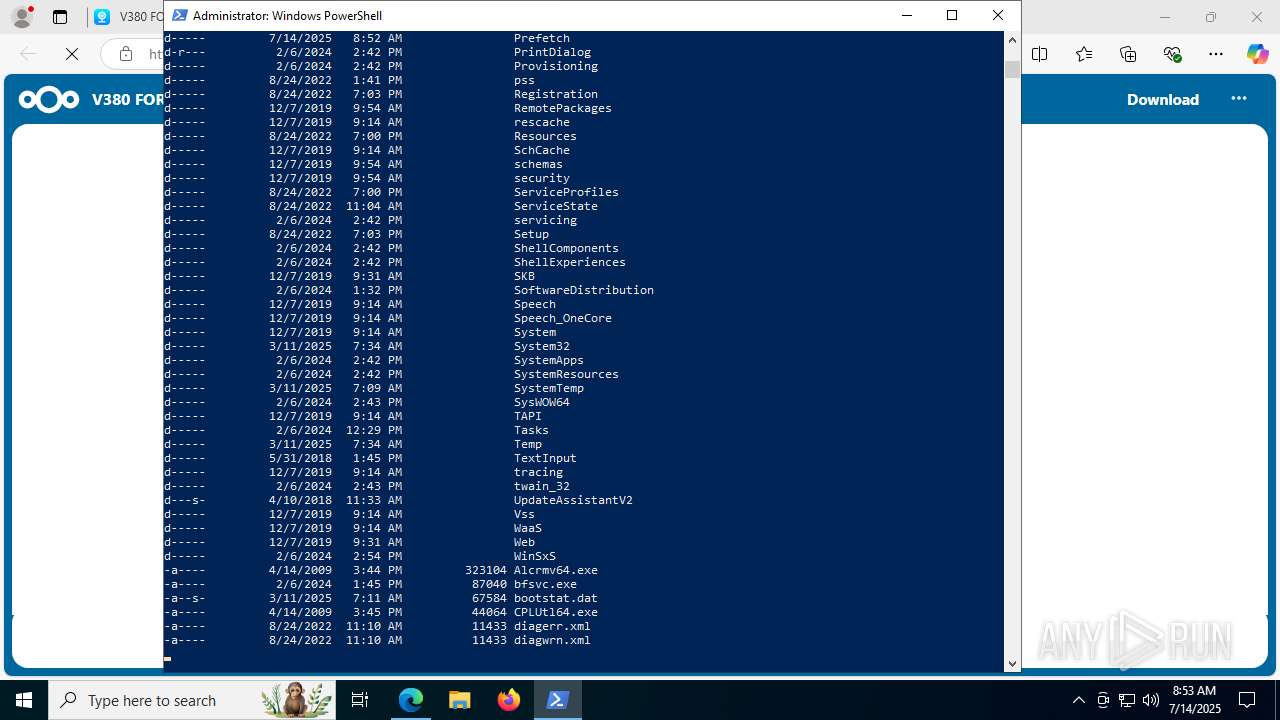
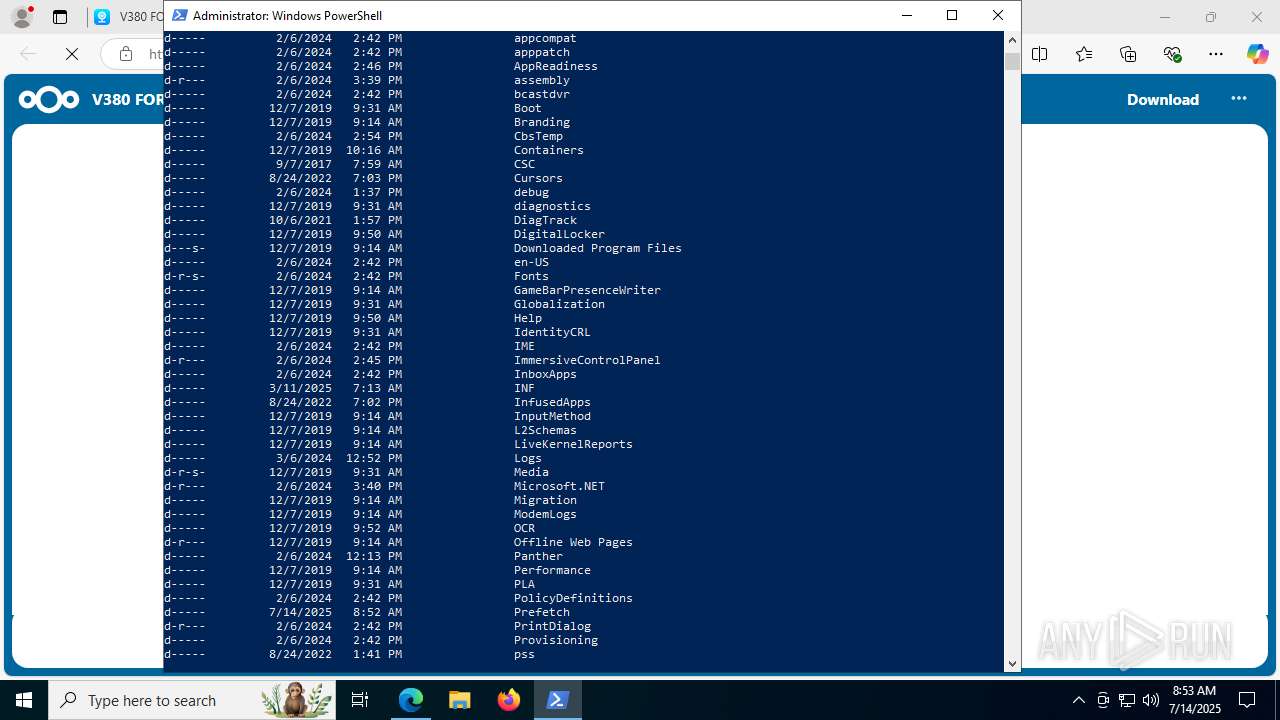
Checks current location (POWERSHELL)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 5884)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 5884)
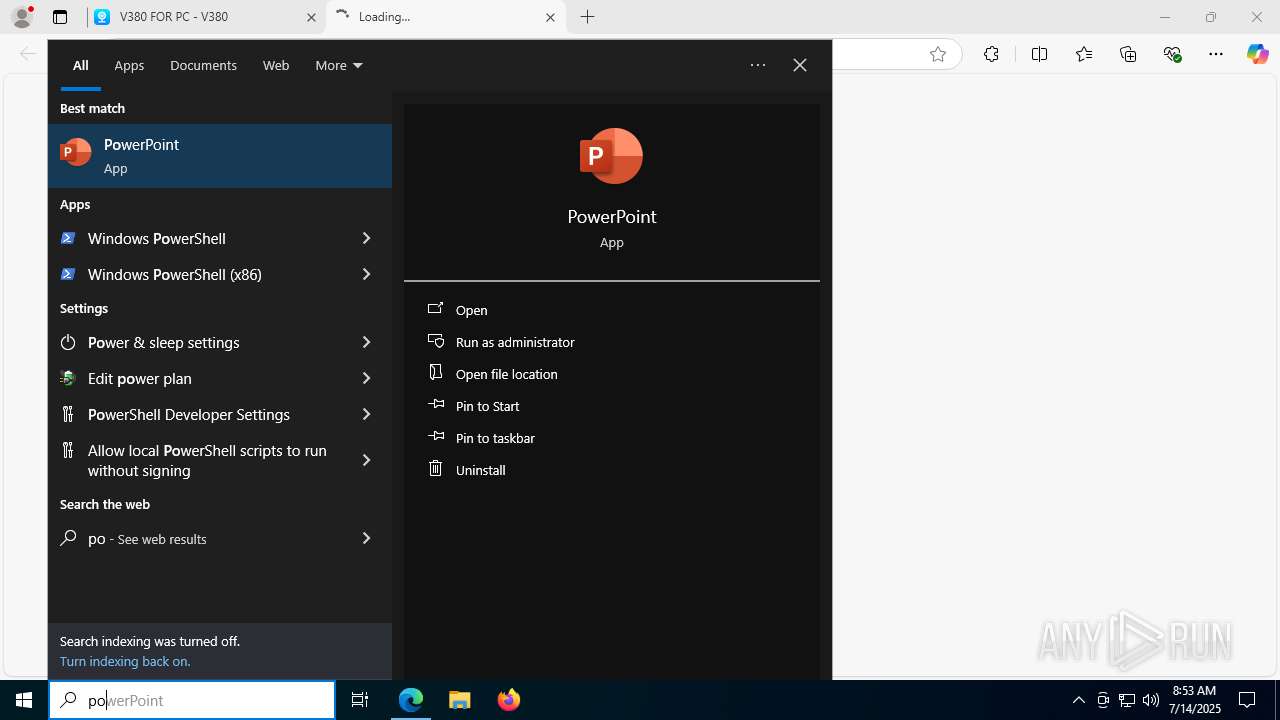
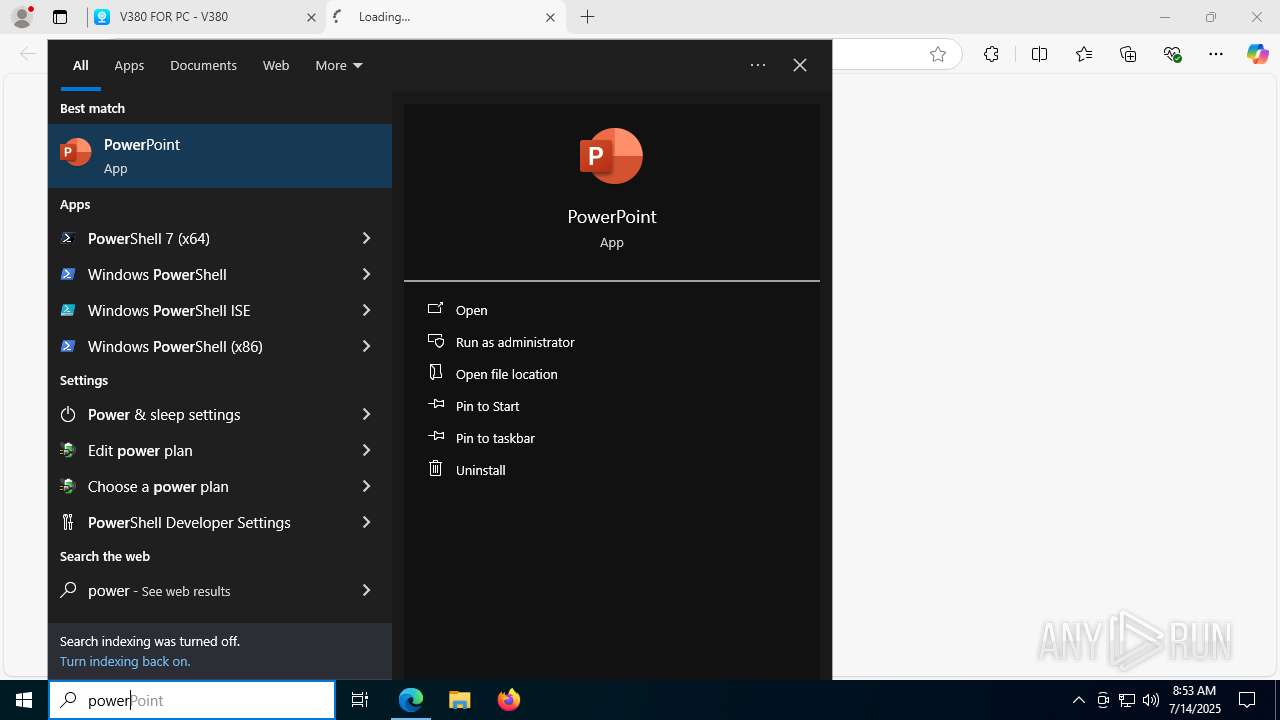
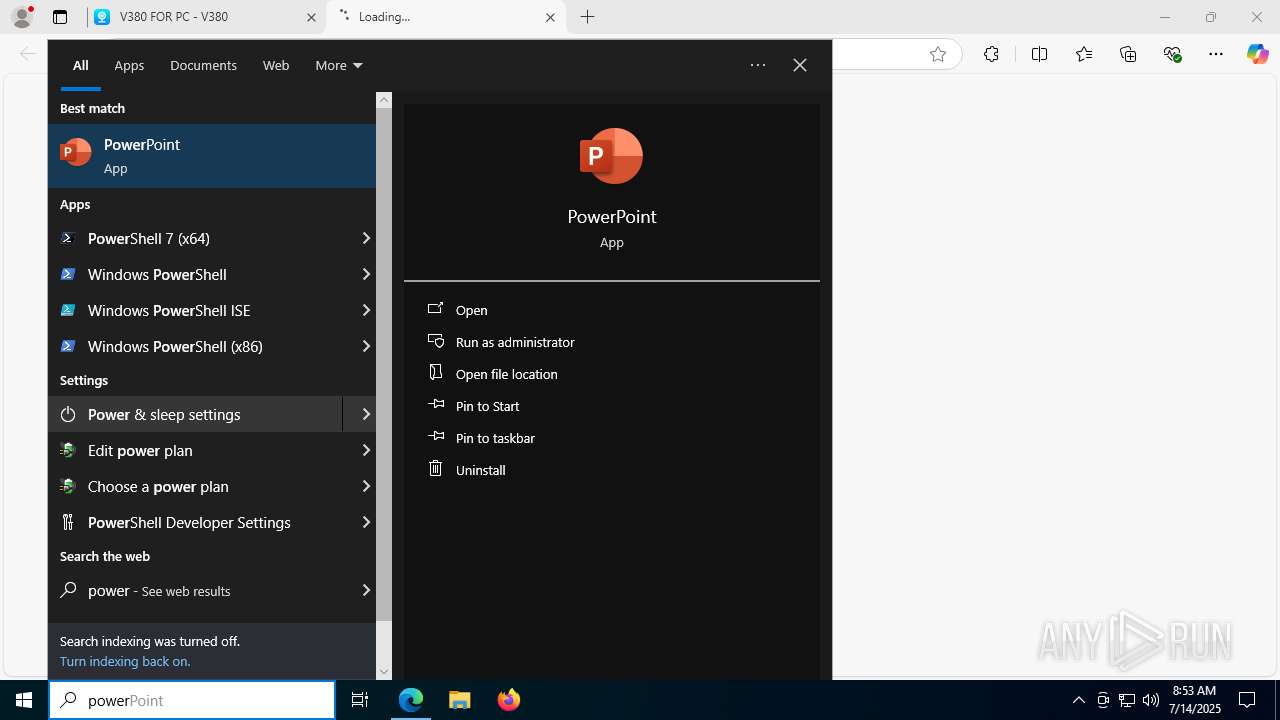
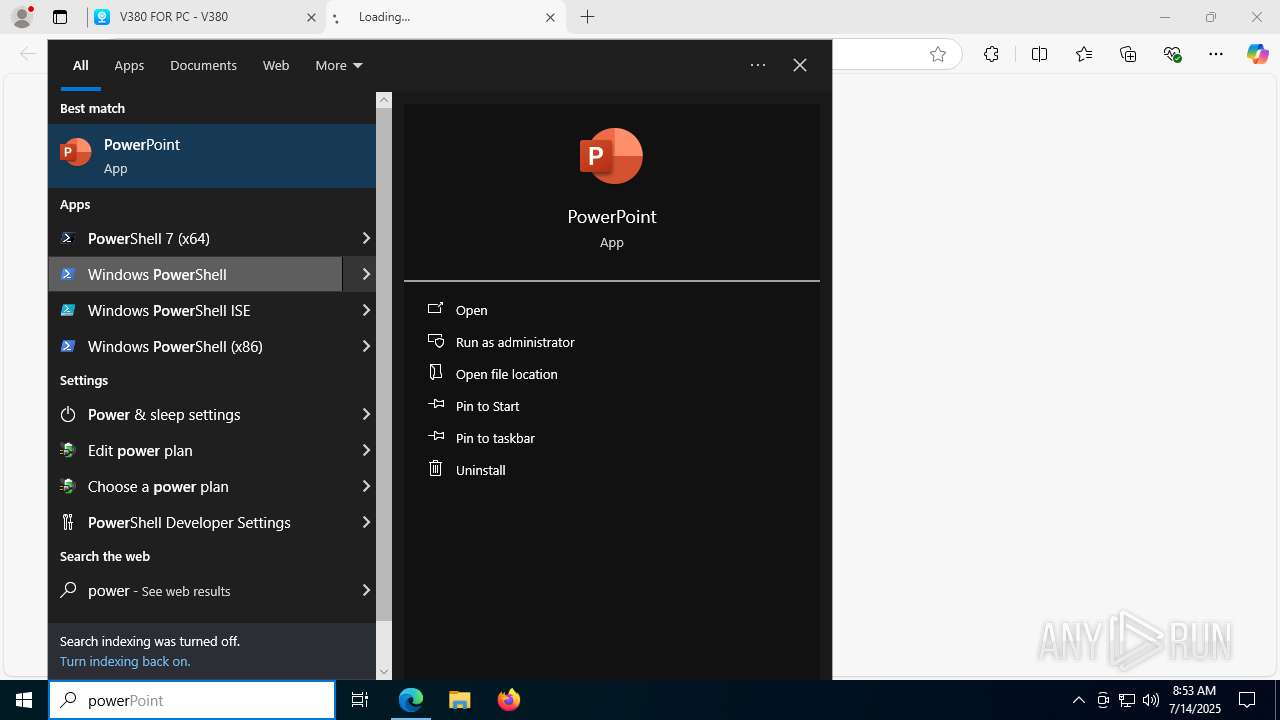
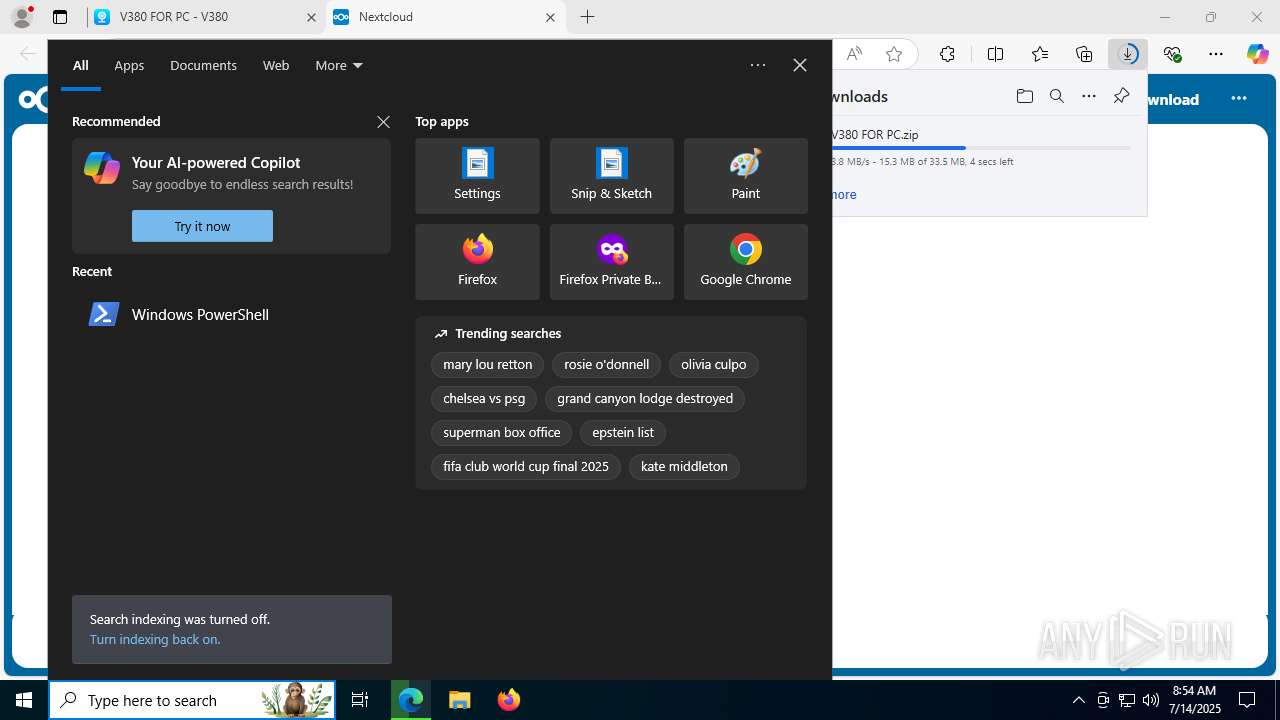
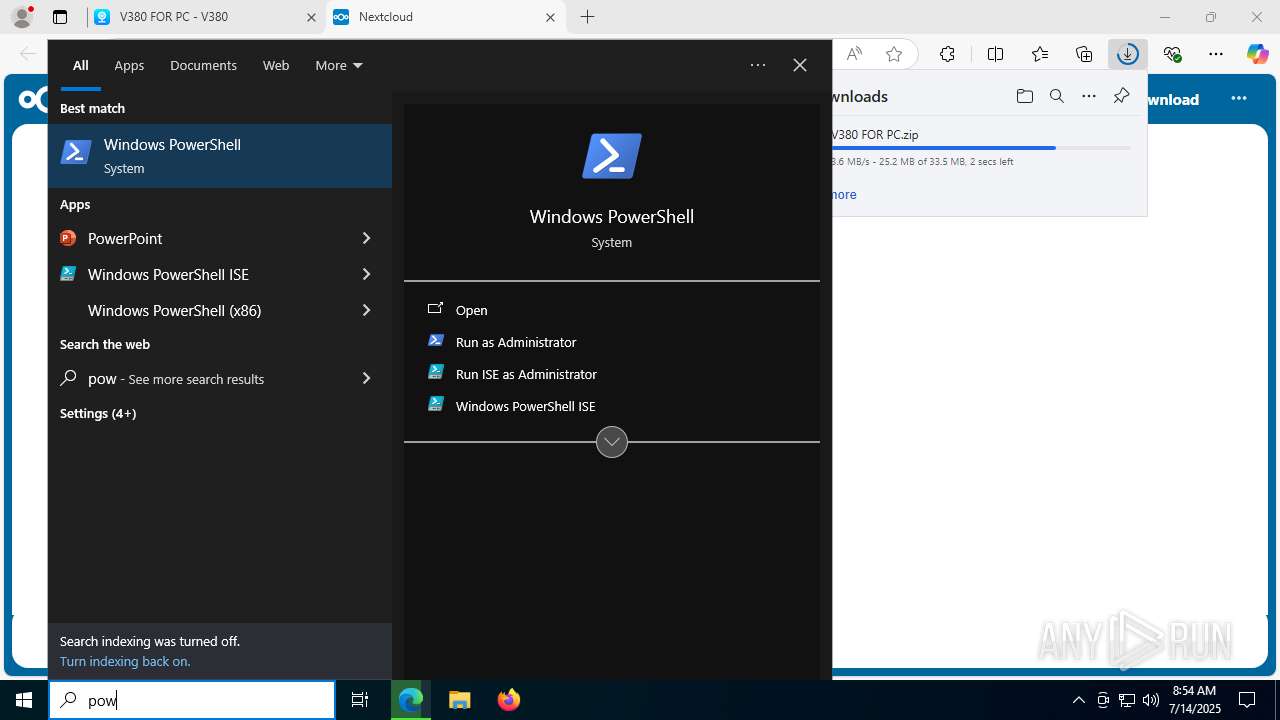
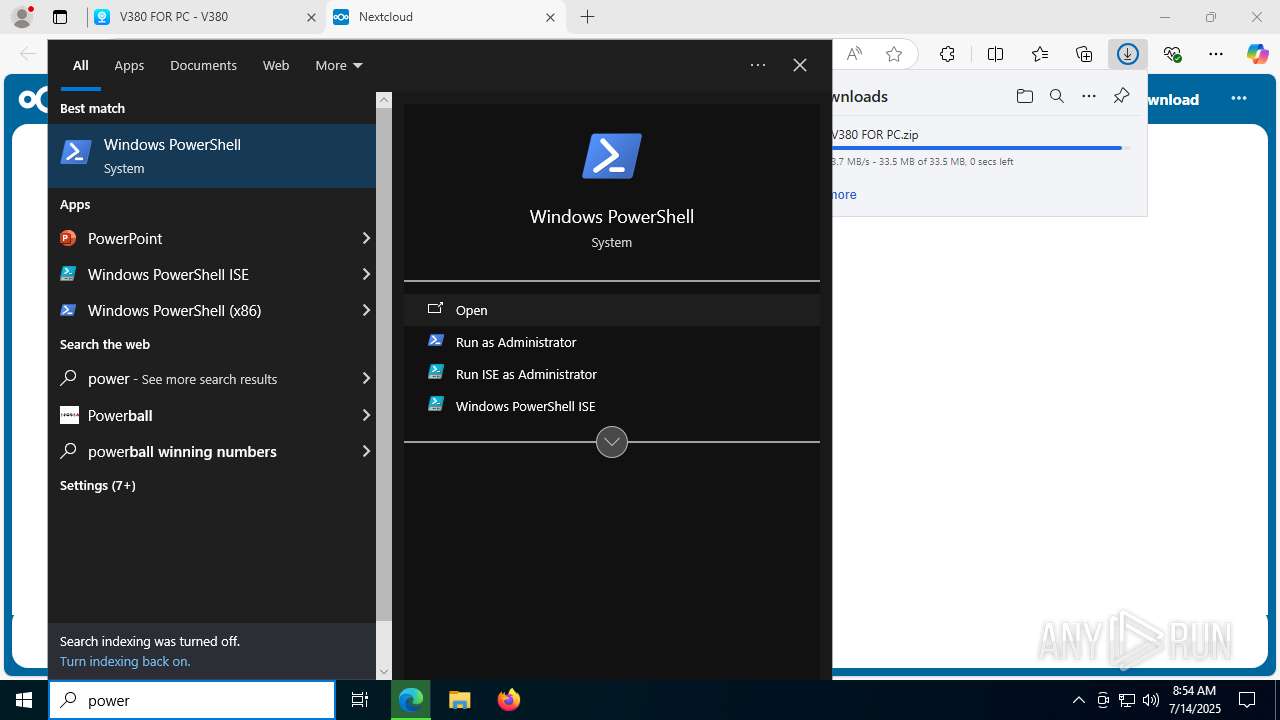
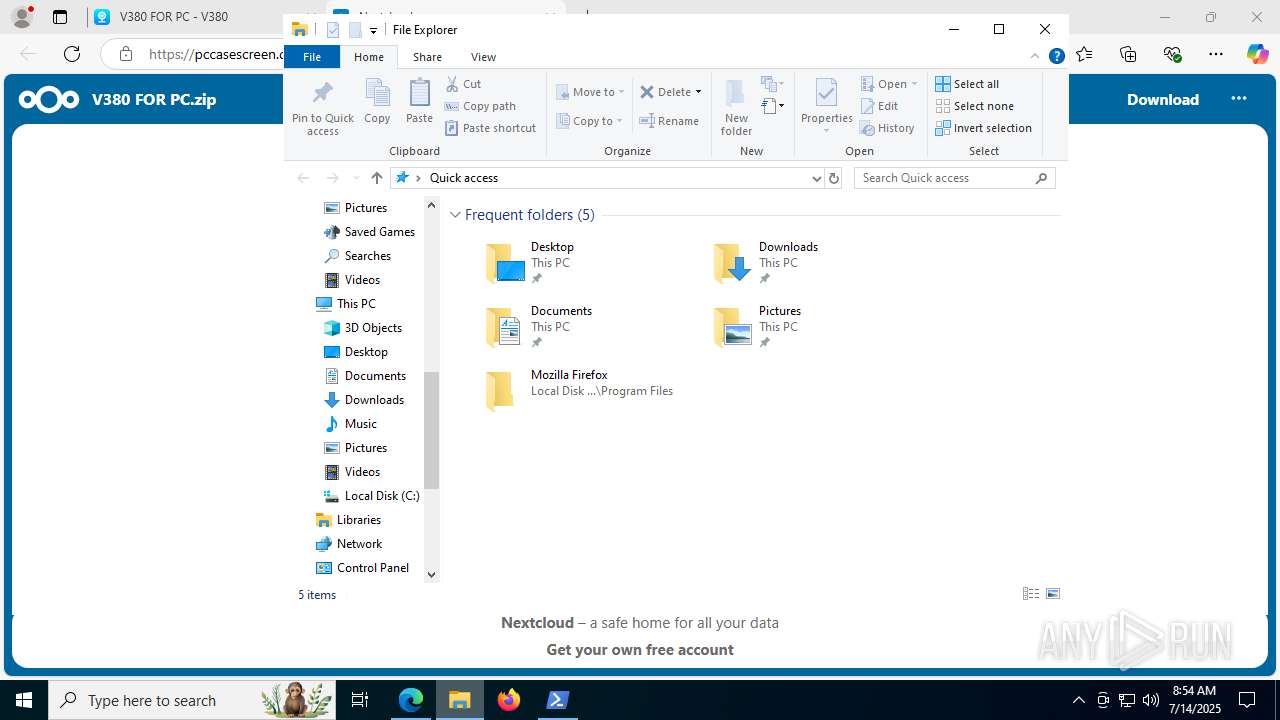
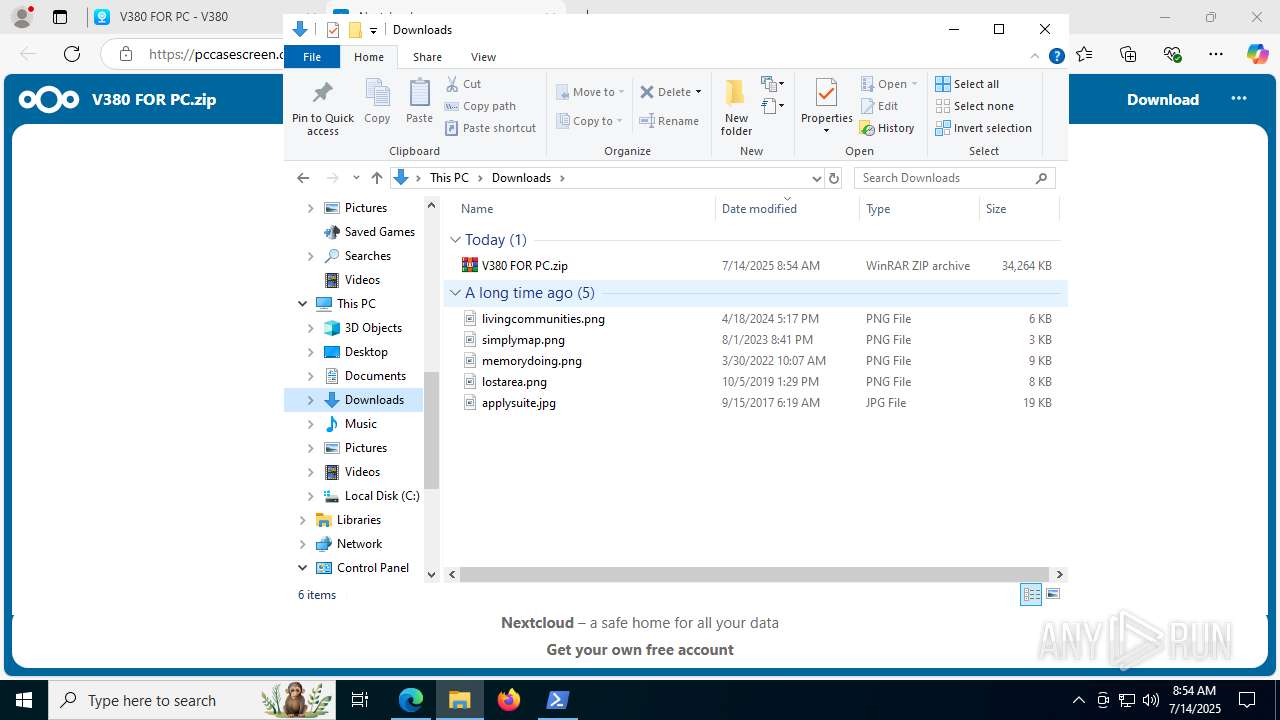
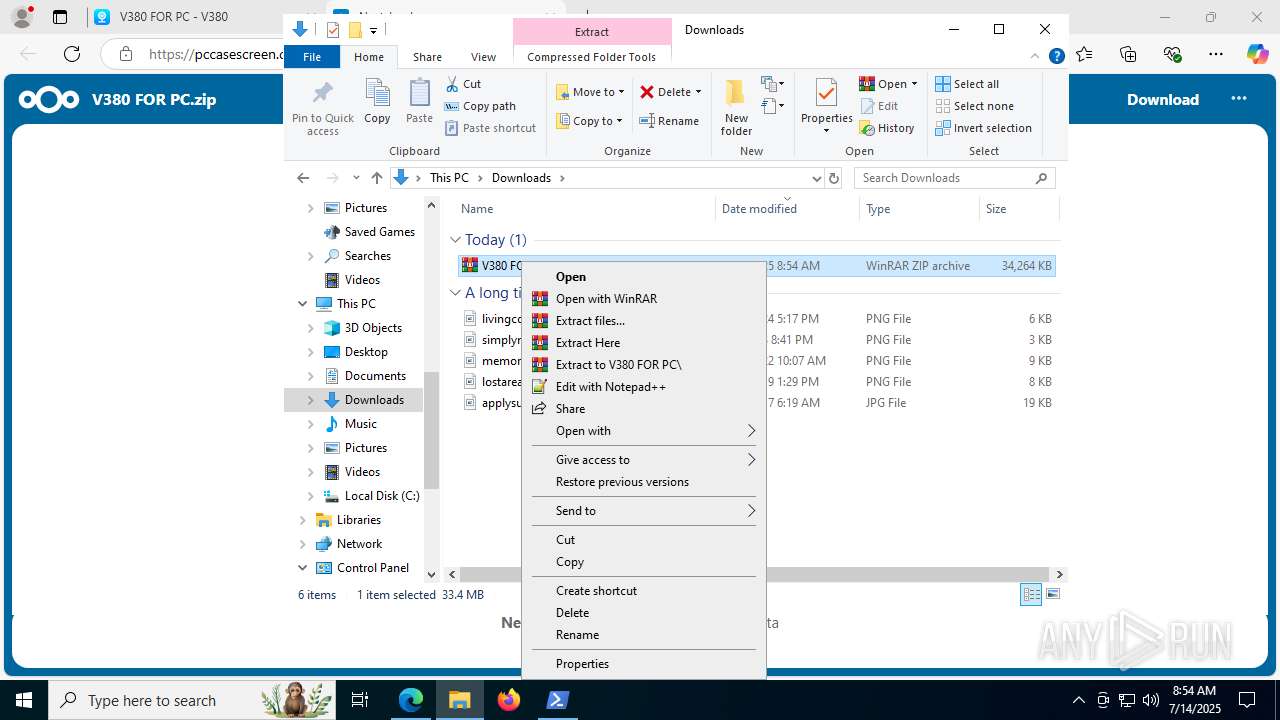
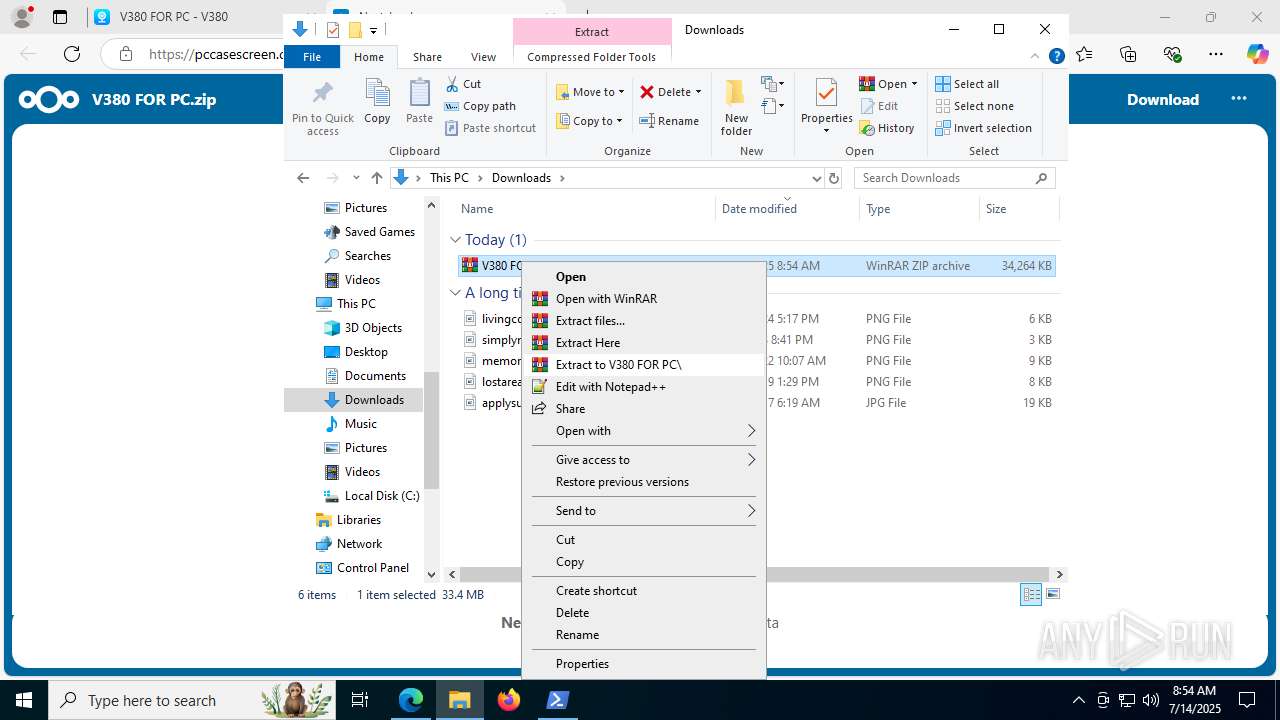
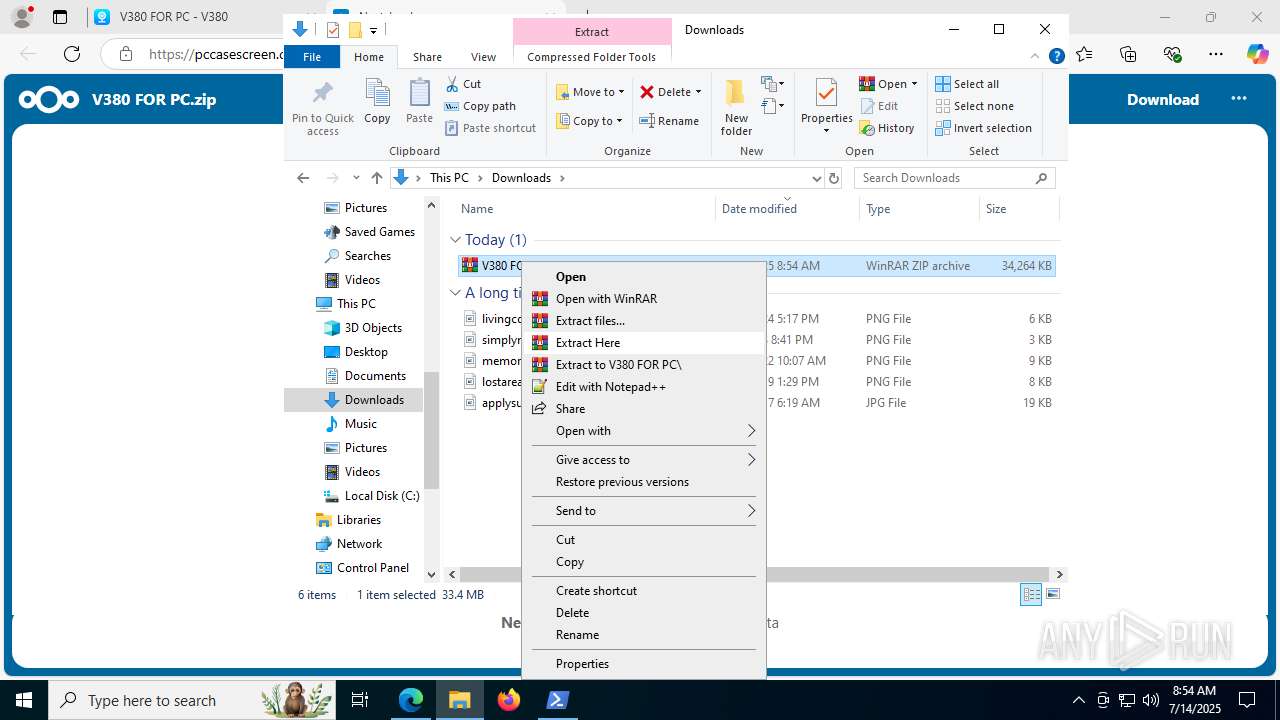
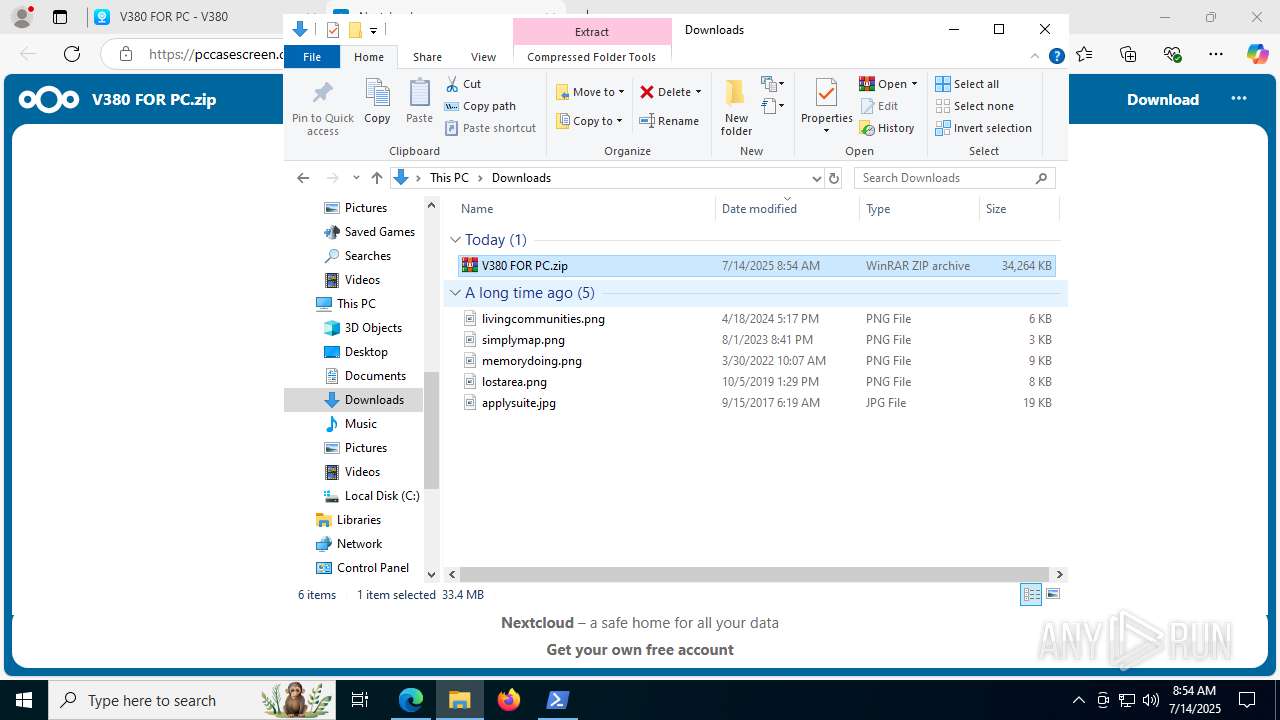
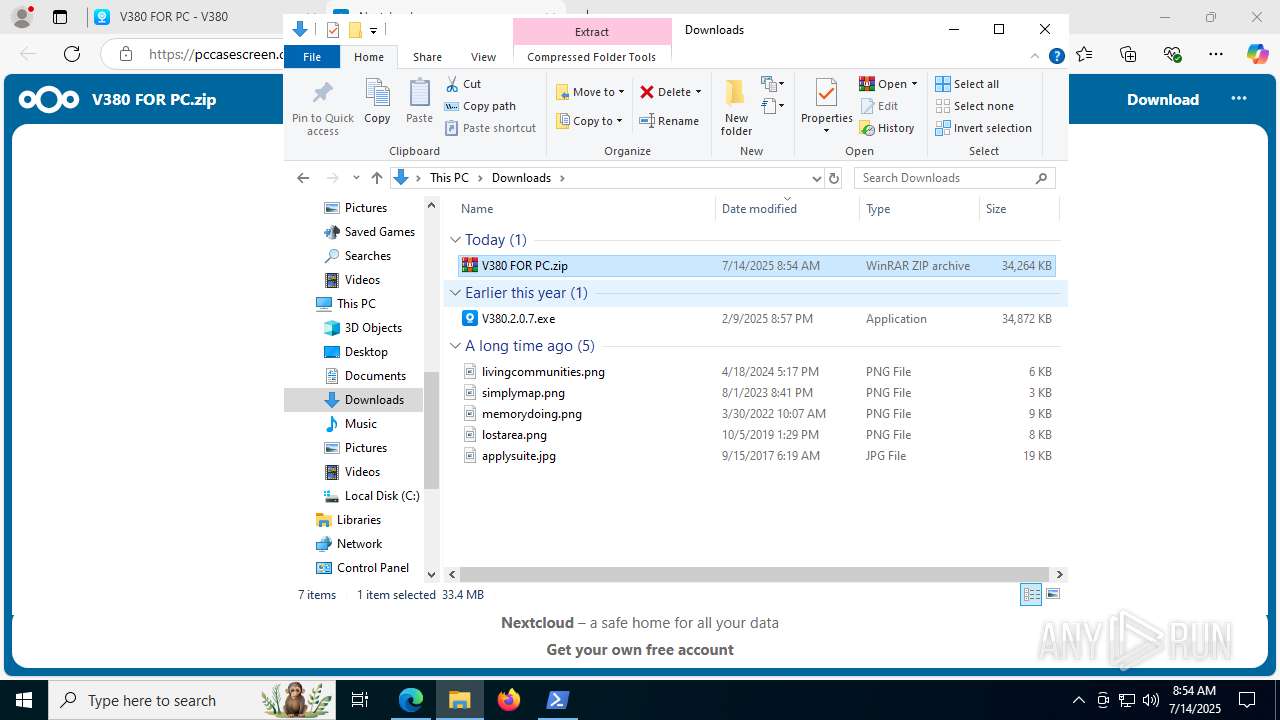
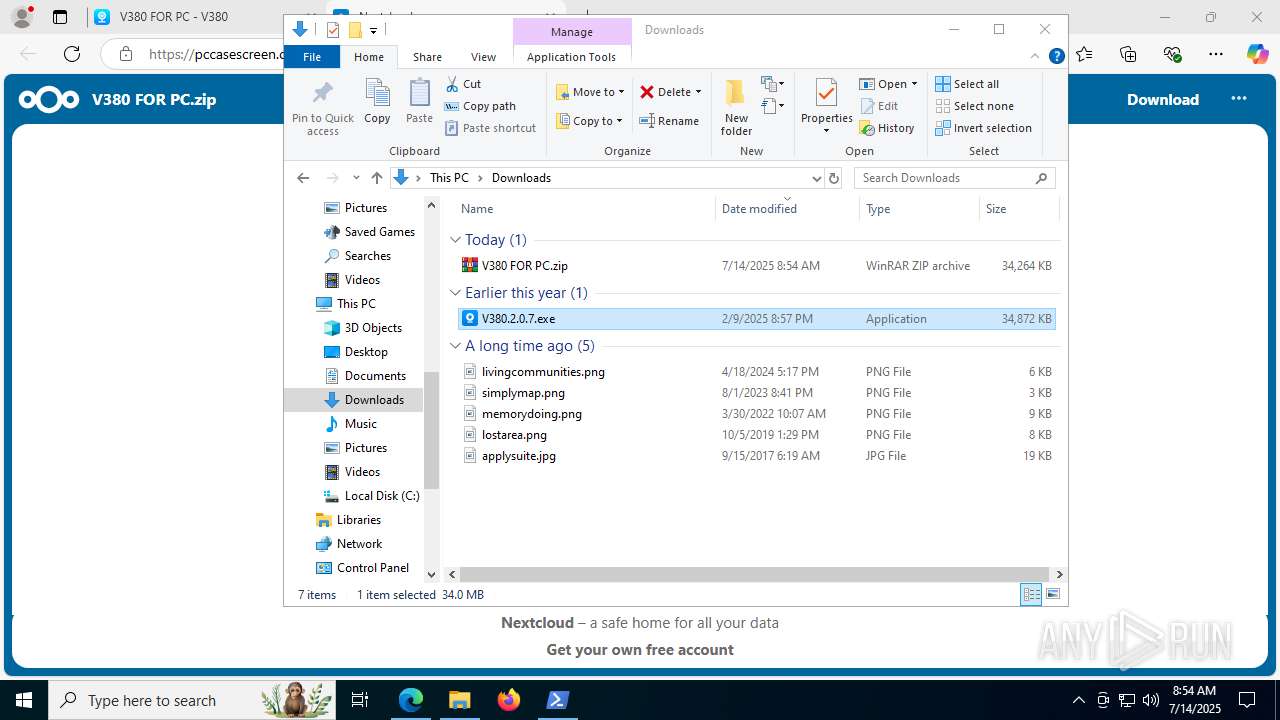
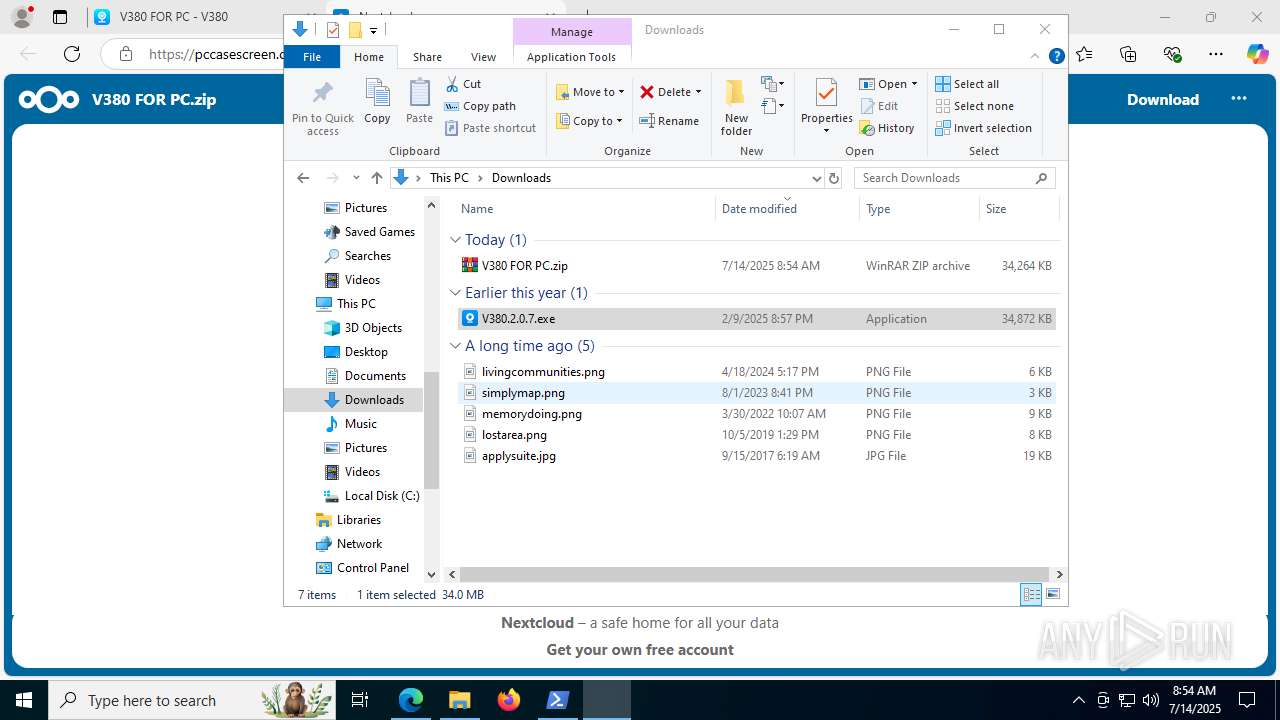
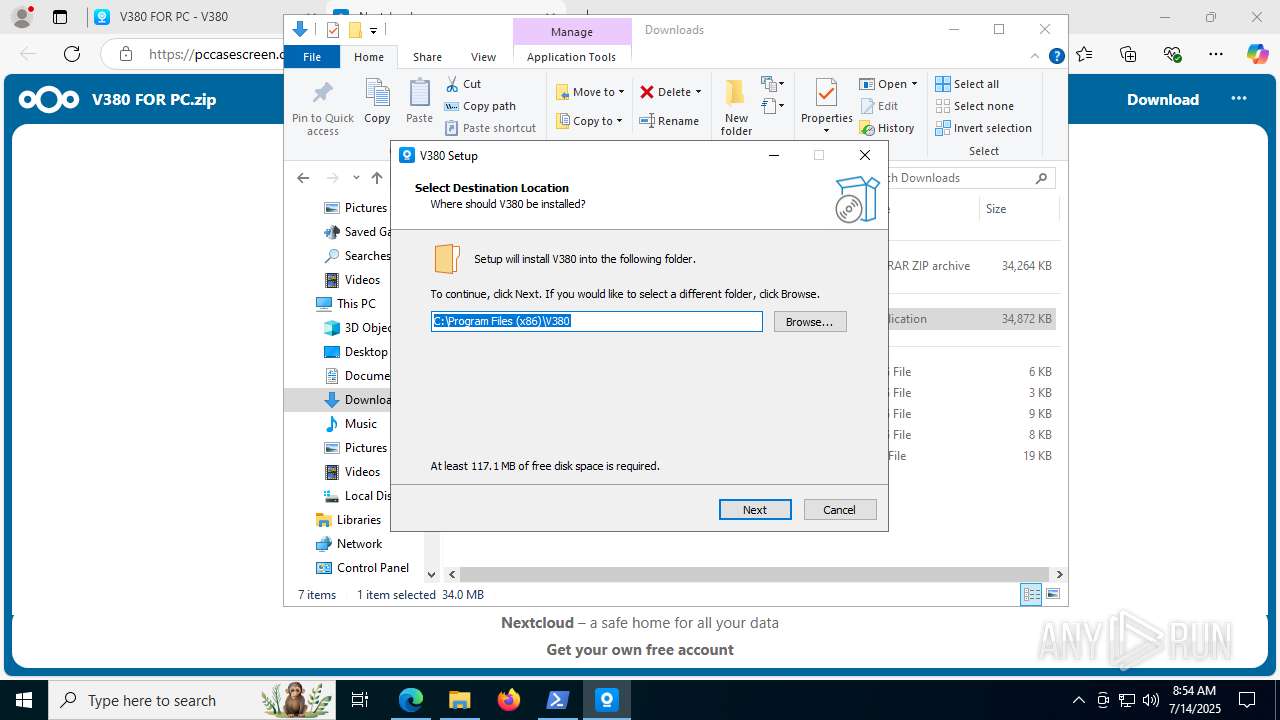
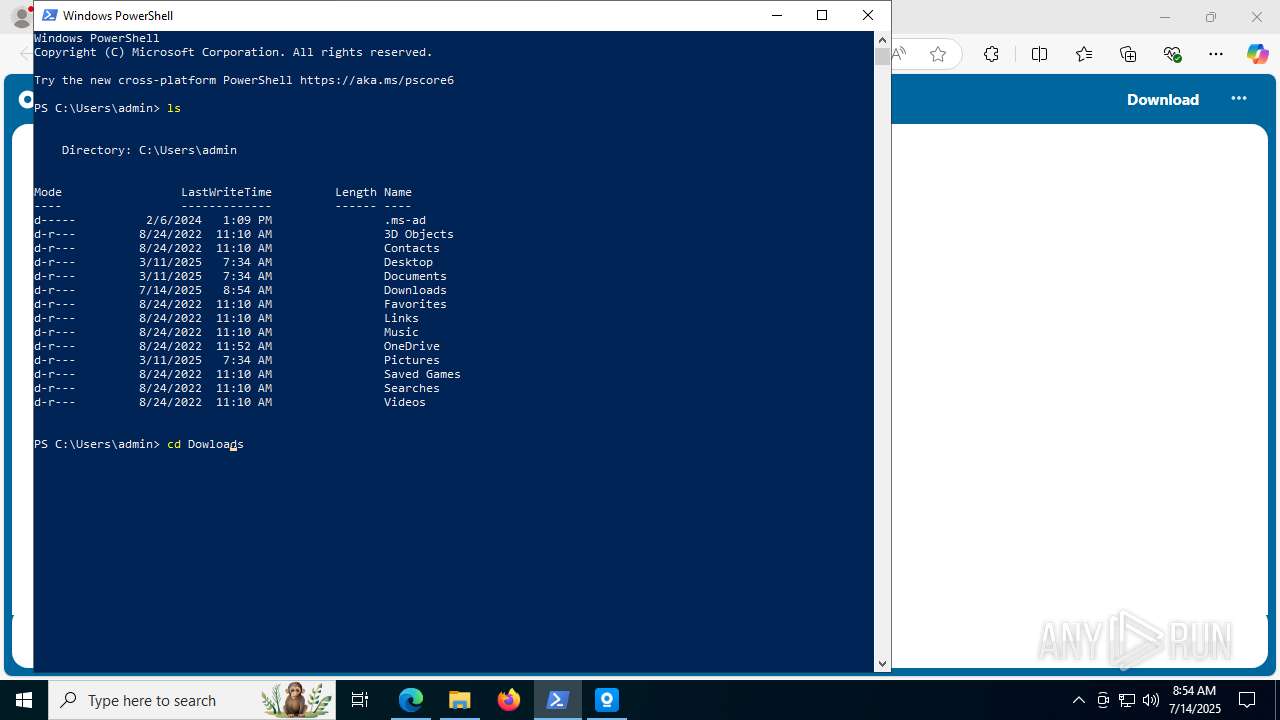
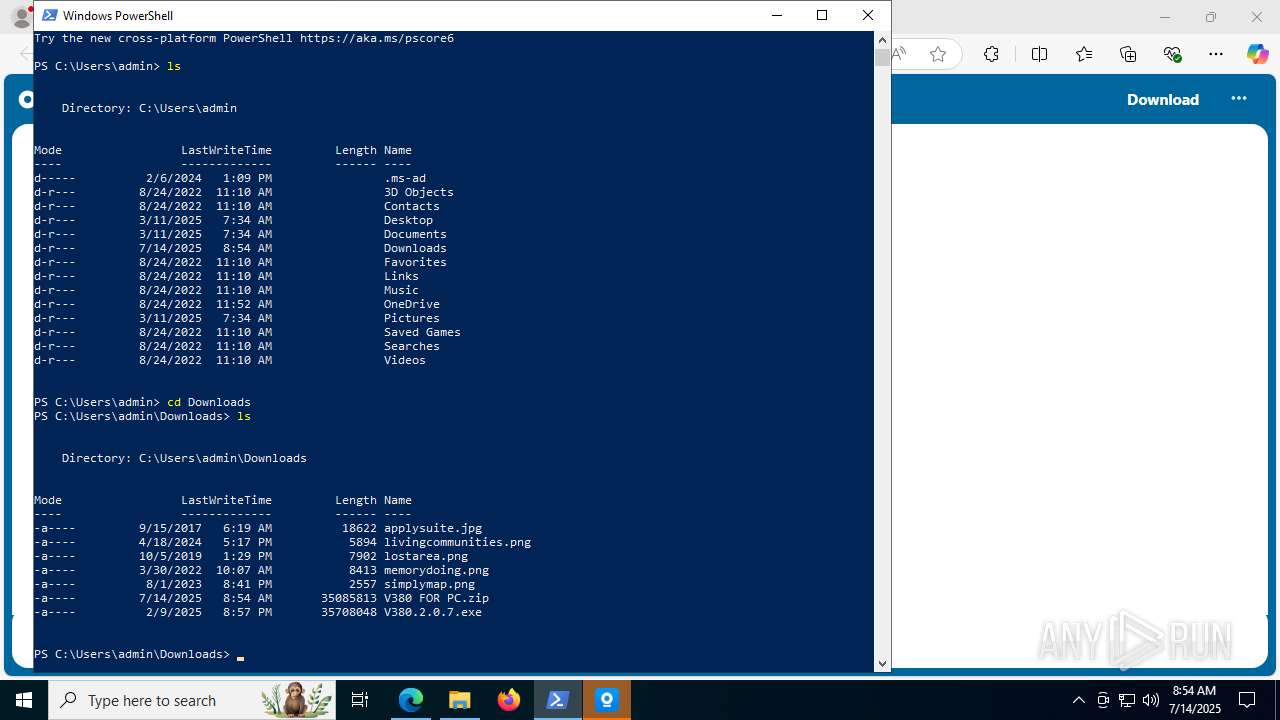
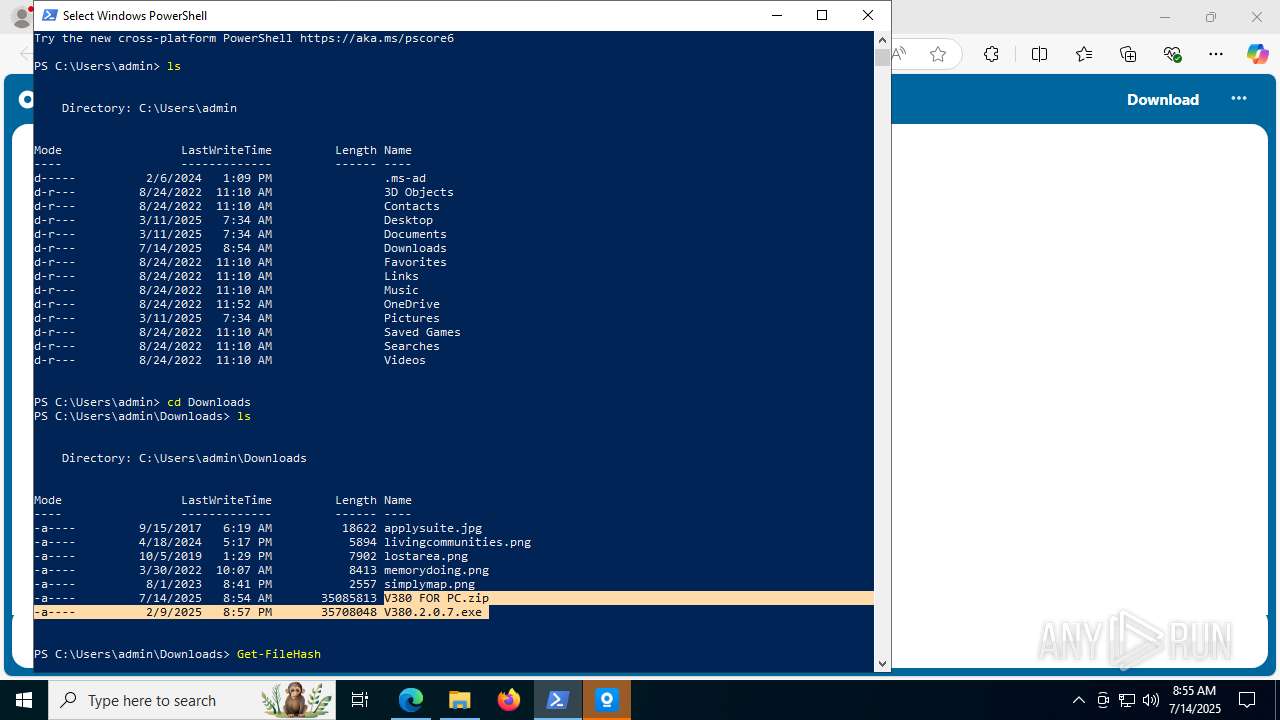
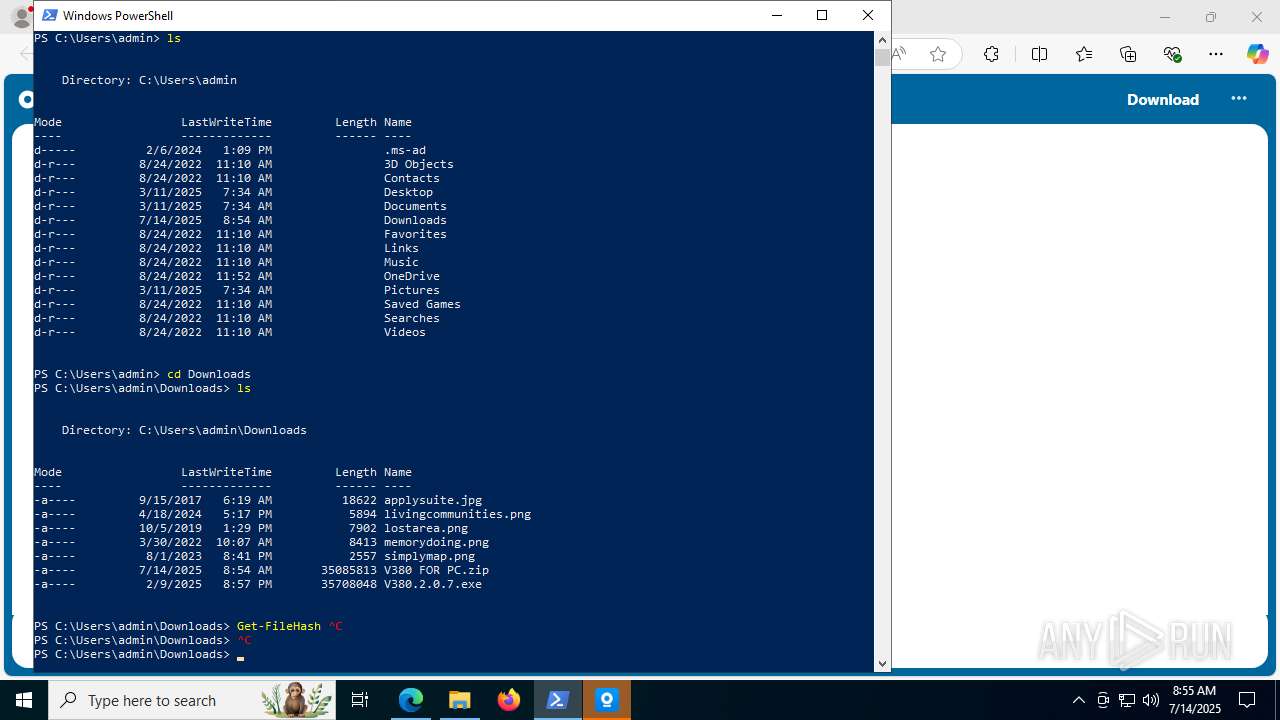
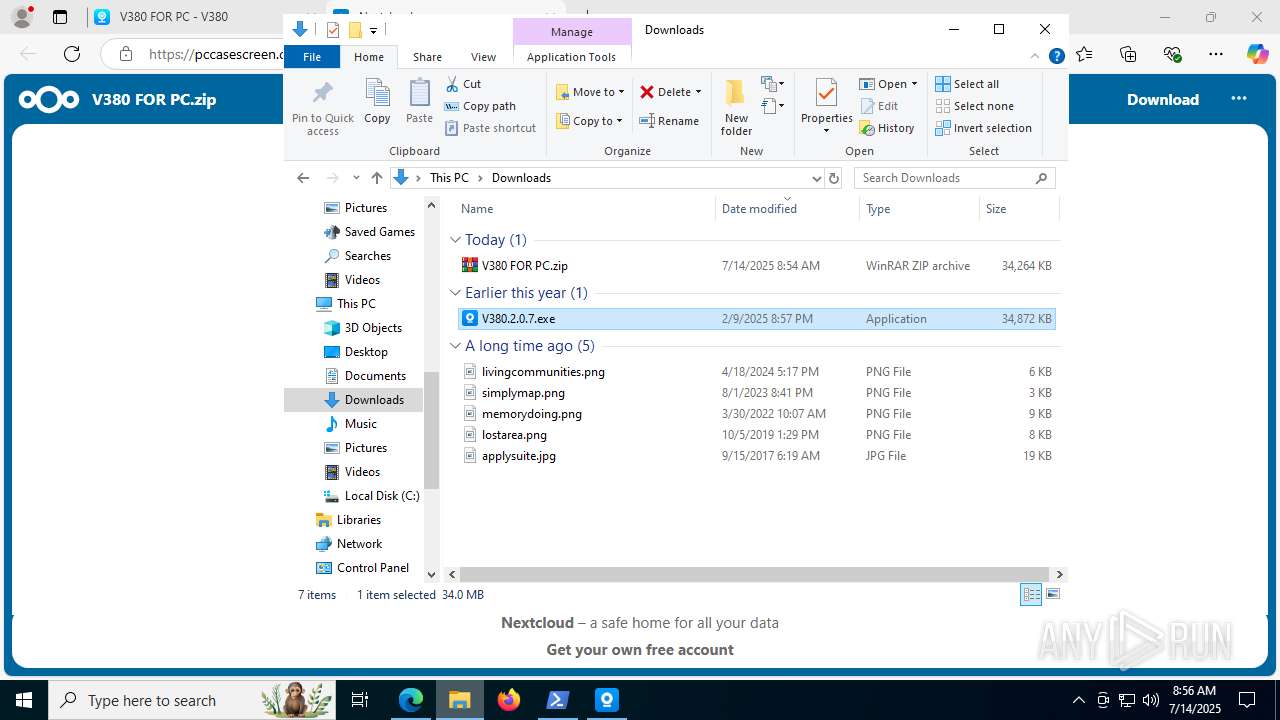
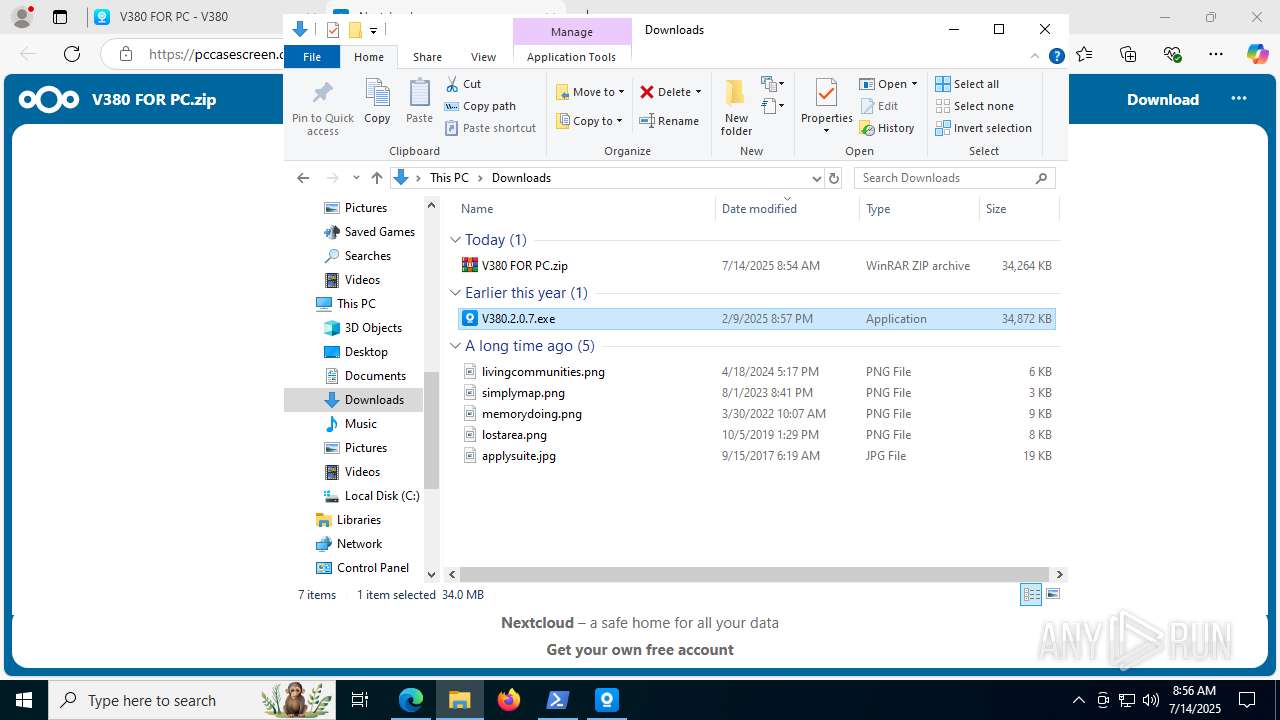
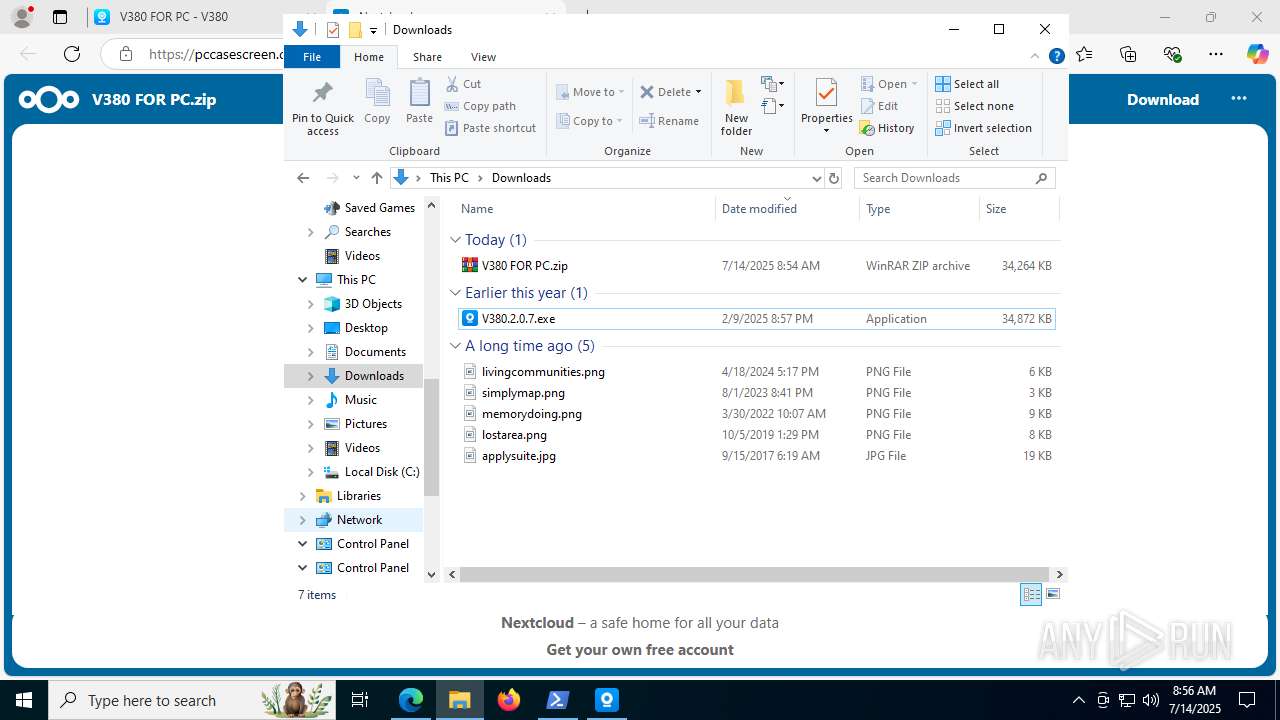
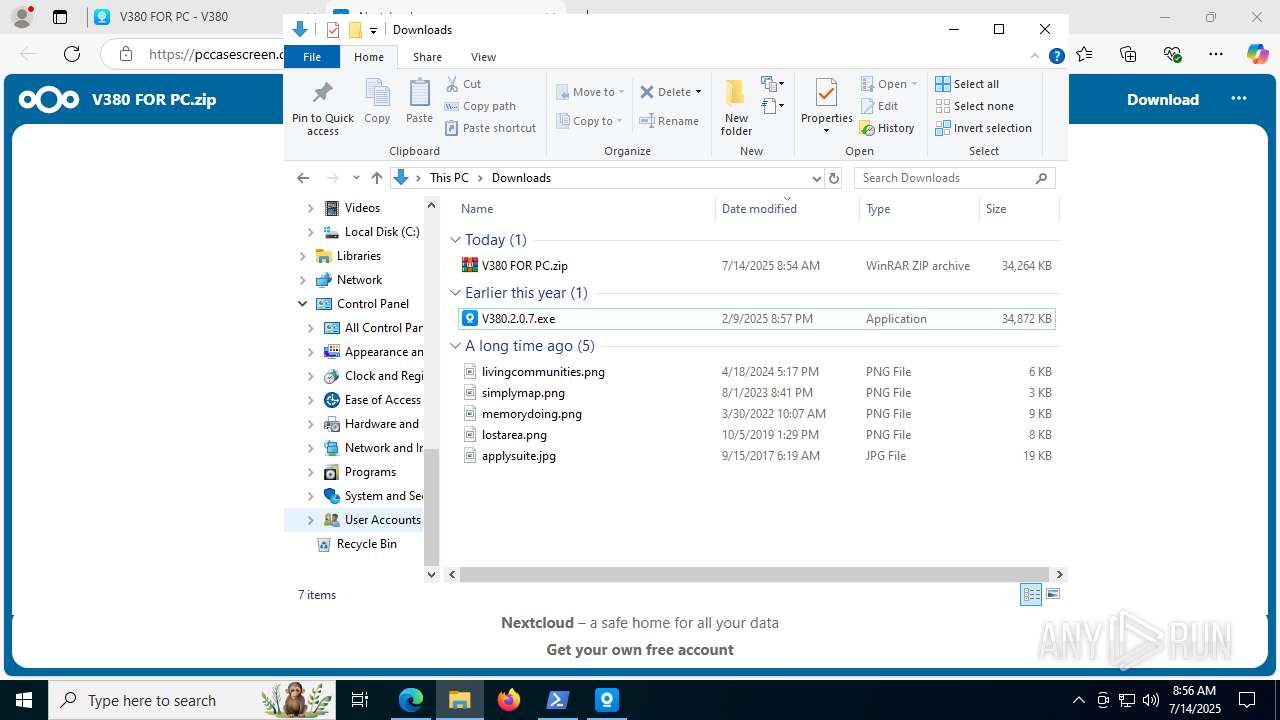
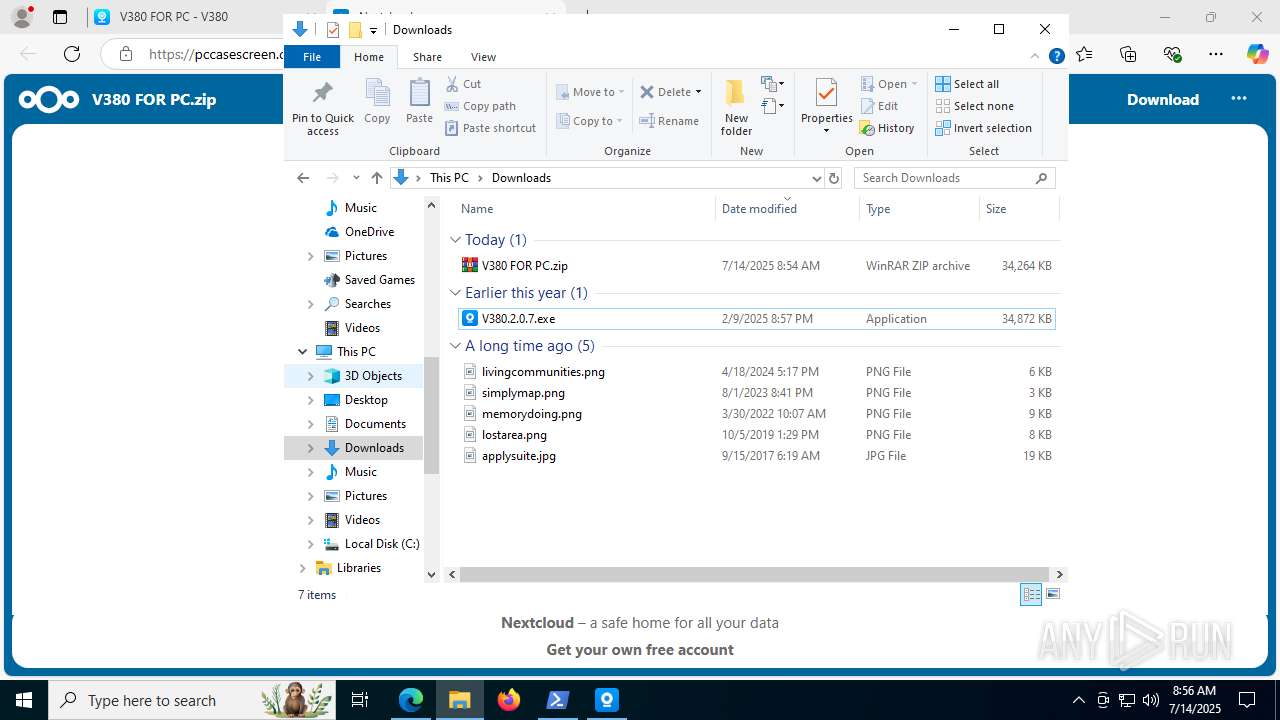
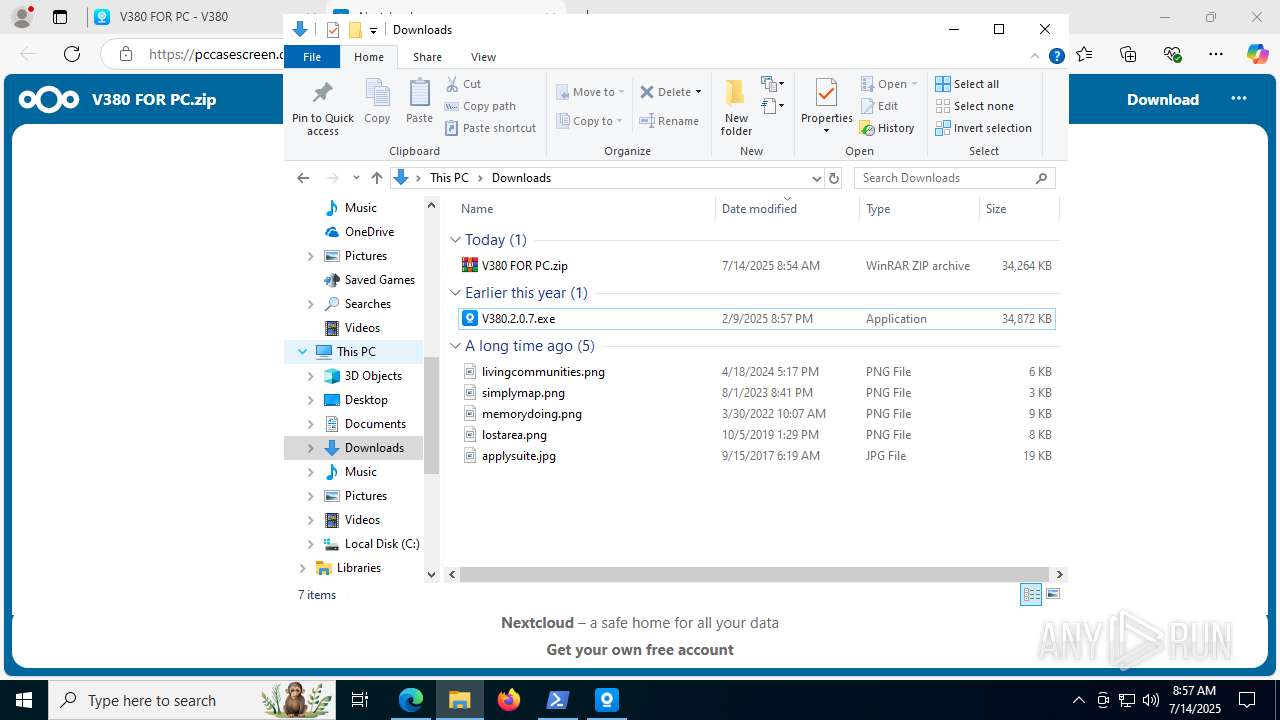
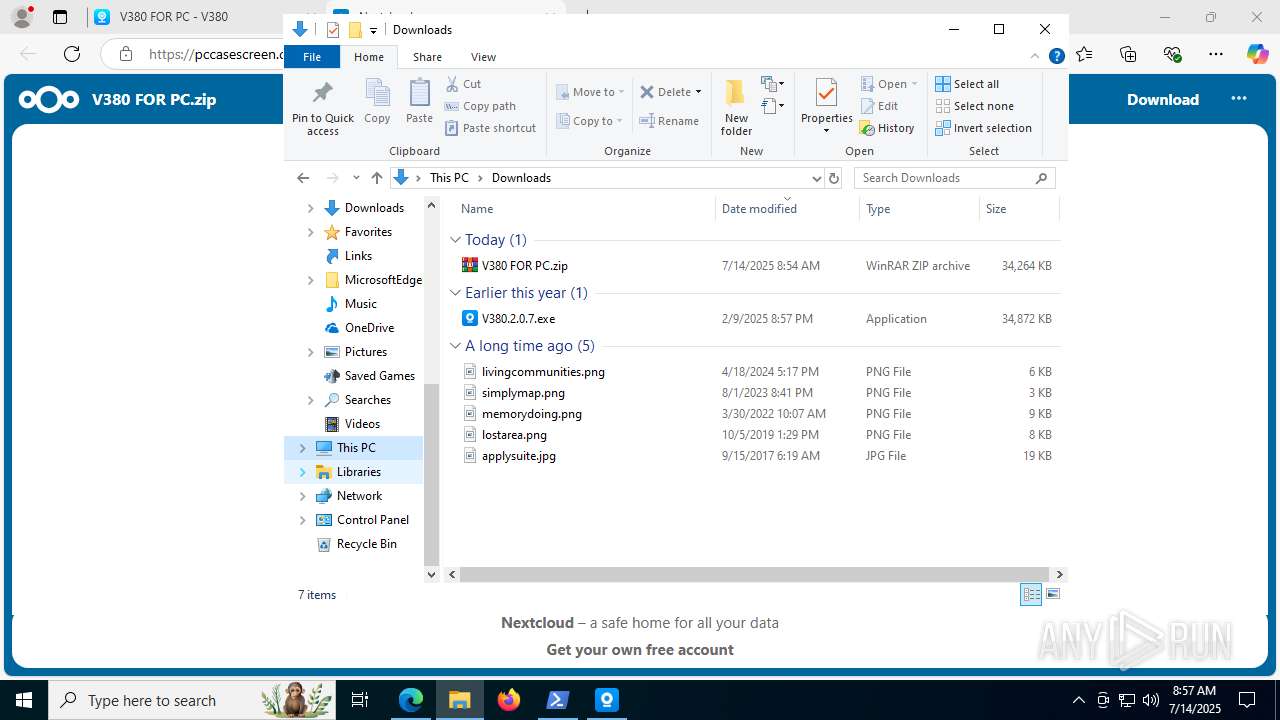
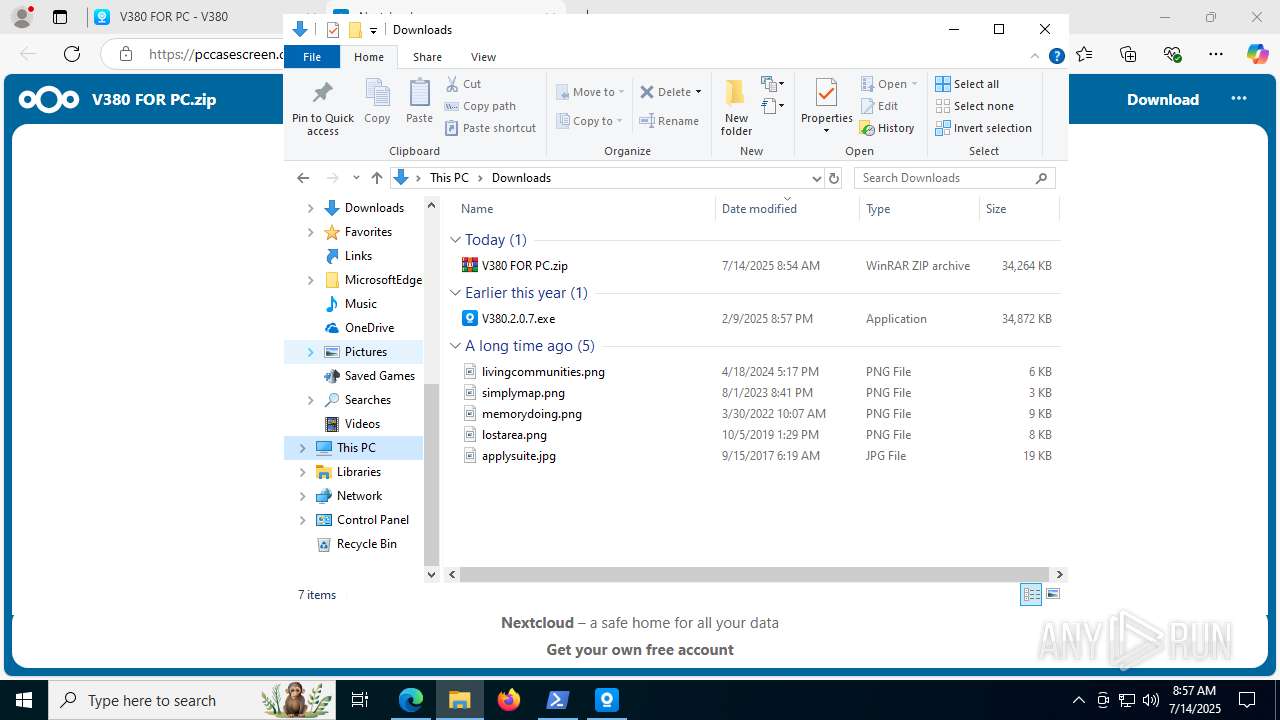
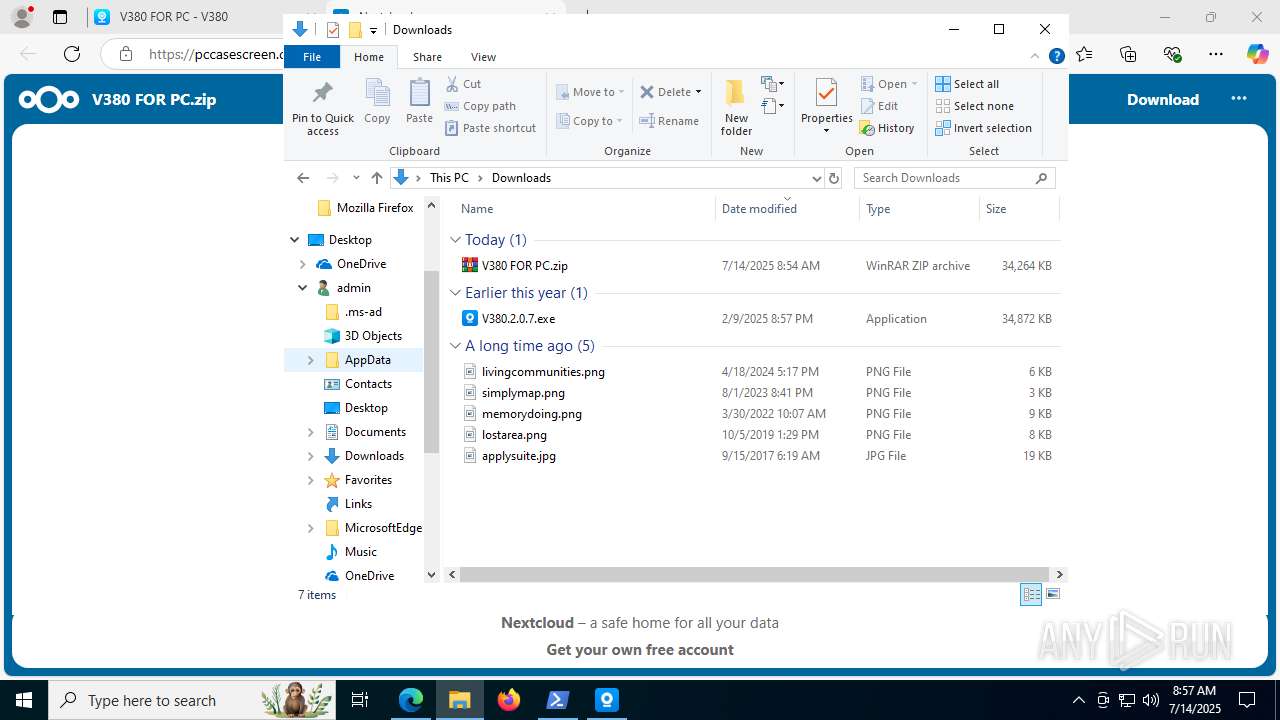
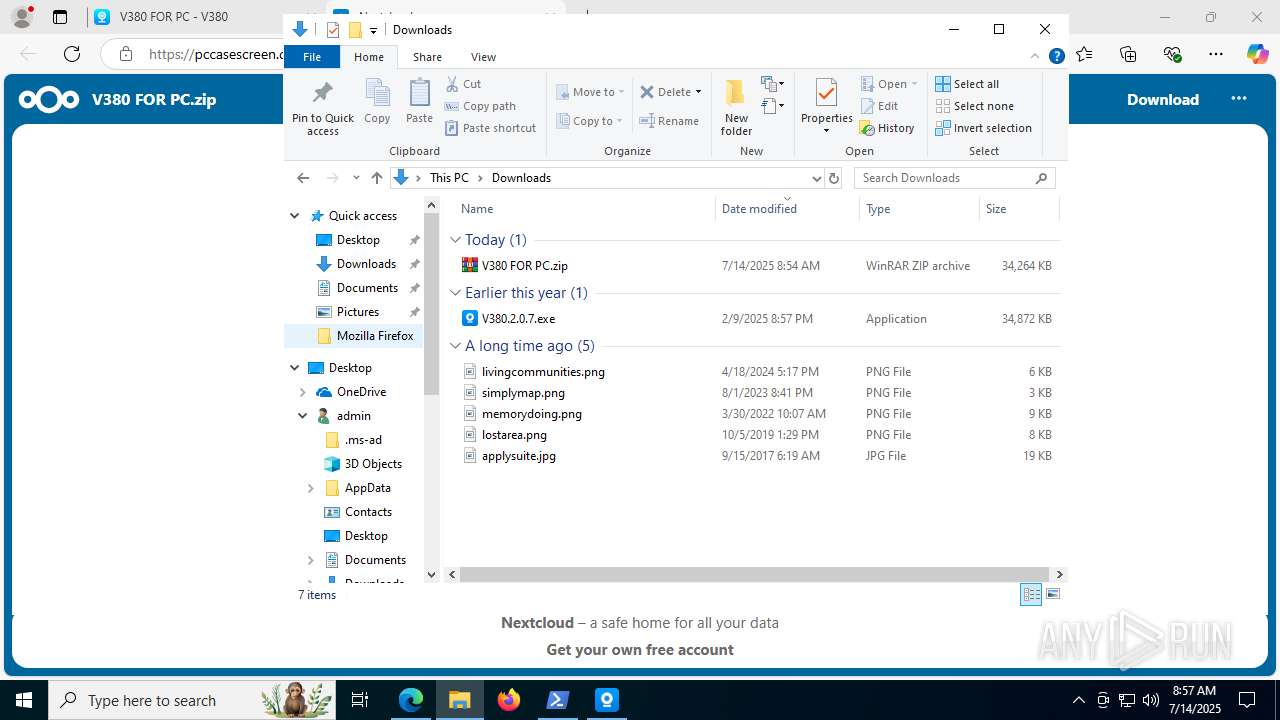
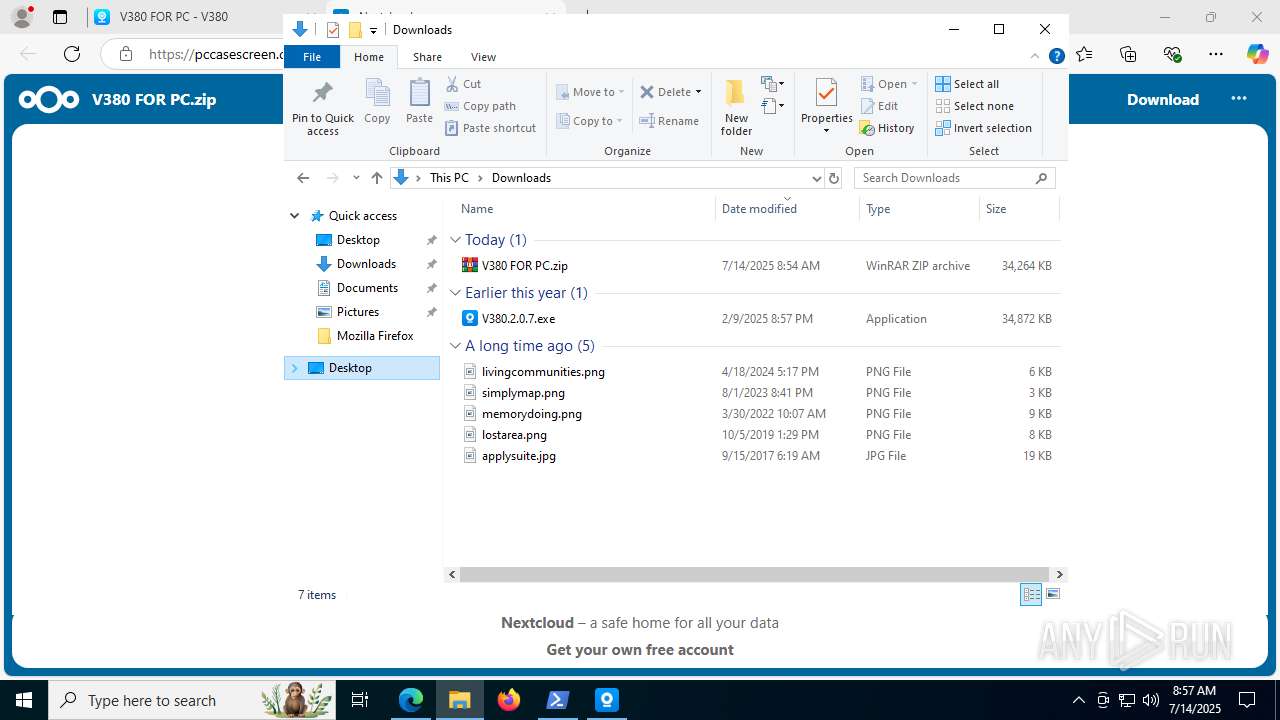
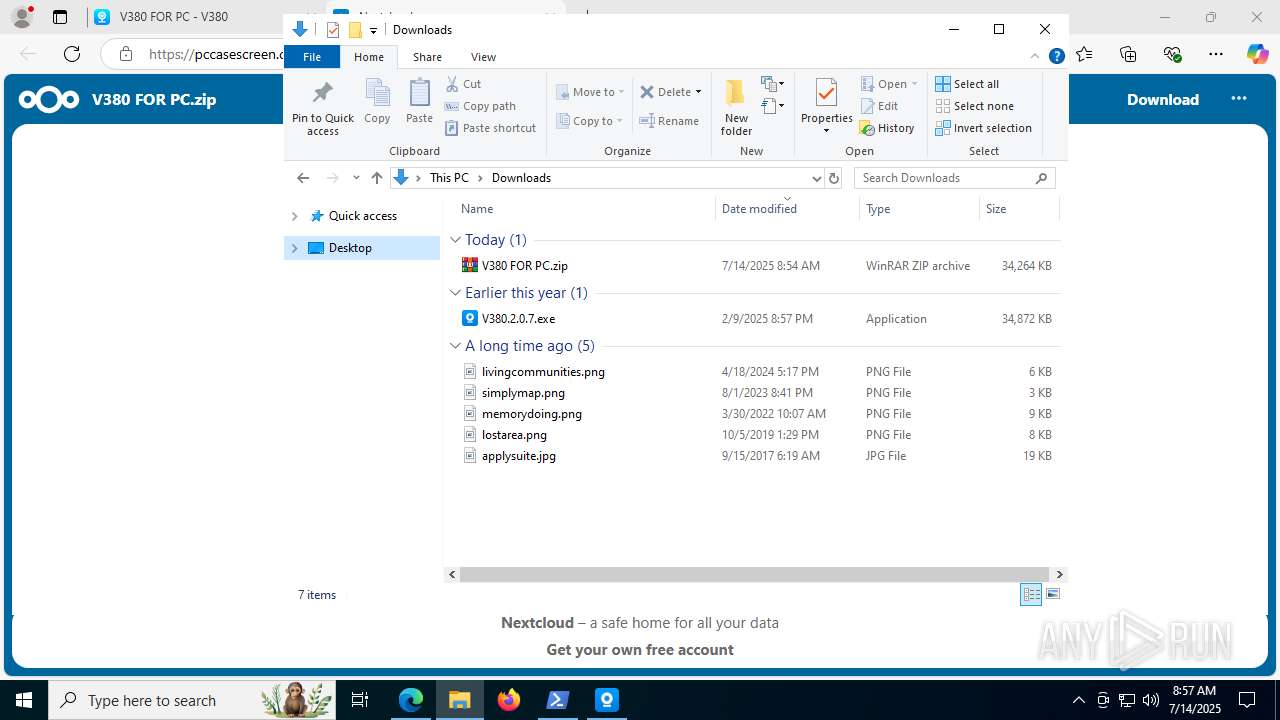
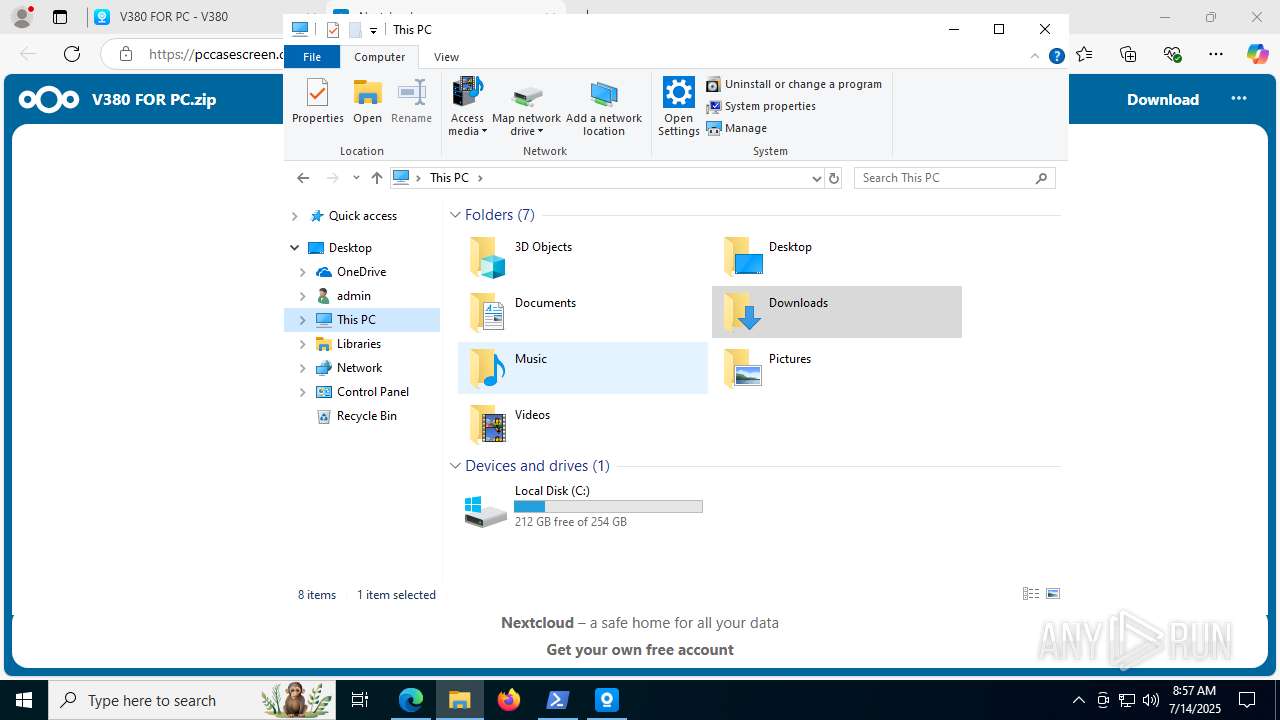
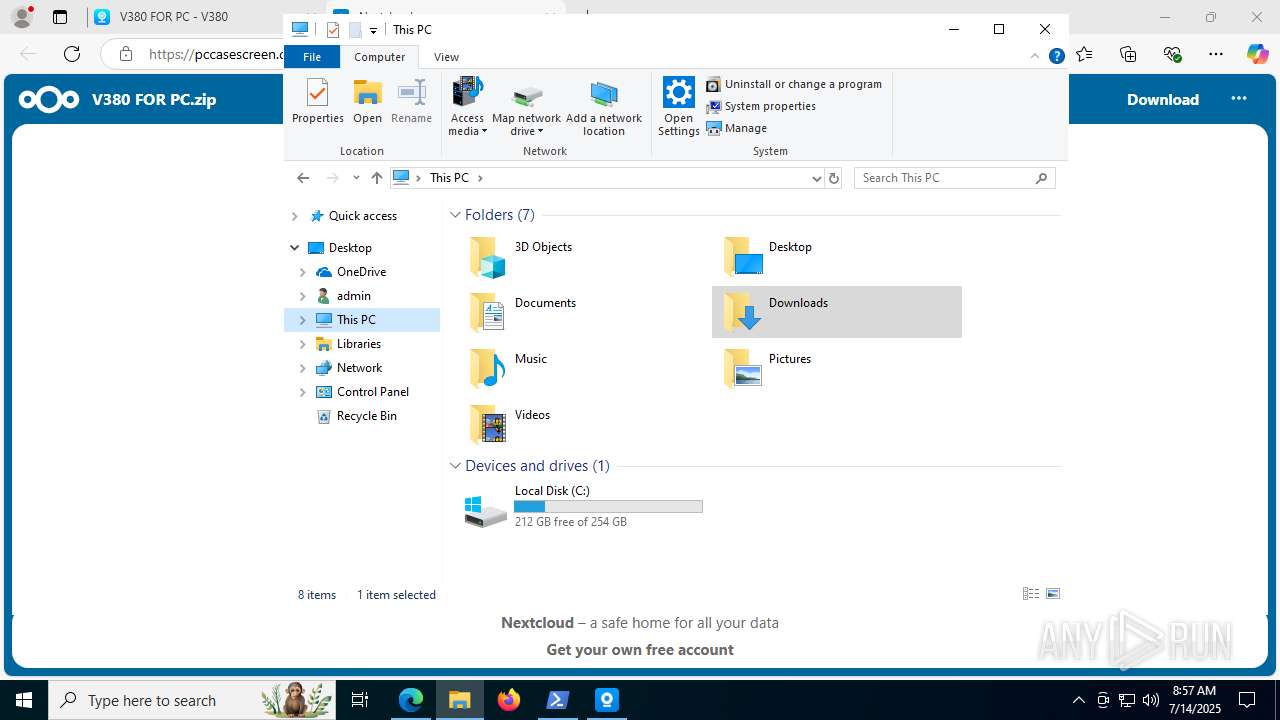
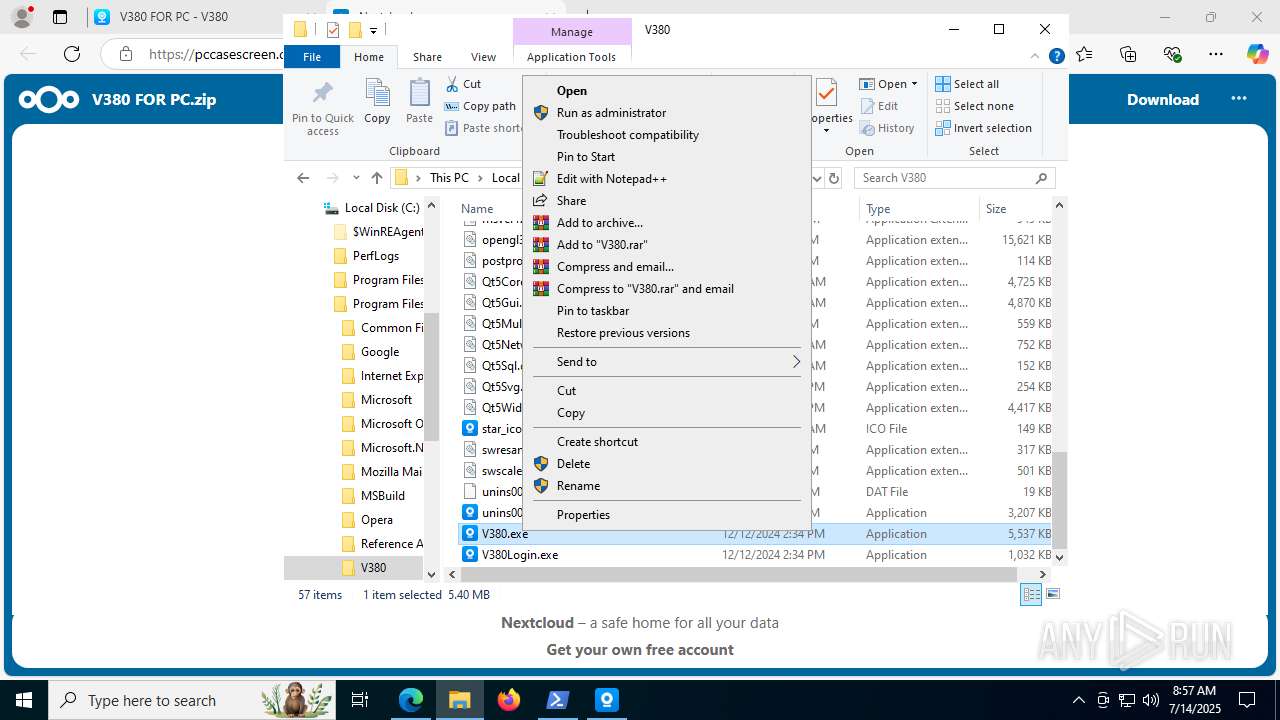
Manual execution by a user
- powershell.exe (PID: 5884)
- WinRAR.exe (PID: 2168)
- V380.2.0.7.exe (PID: 7244)
- V380.exe (PID: 8112)
Create files in a temporary directory
- V380.2.0.7.exe (PID: 7244)
- V380.2.0.7.exe (PID: 4324)
- V380.2.0.7.tmp (PID: 1932)
Process checks computer location settings
- V380.2.0.7.tmp (PID: 7236)
Detects InnoSetup installer (YARA)
- V380.2.0.7.exe (PID: 7244)
- V380.2.0.7.tmp (PID: 7236)
- V380.2.0.7.tmp (PID: 1932)
- V380.2.0.7.exe (PID: 4324)
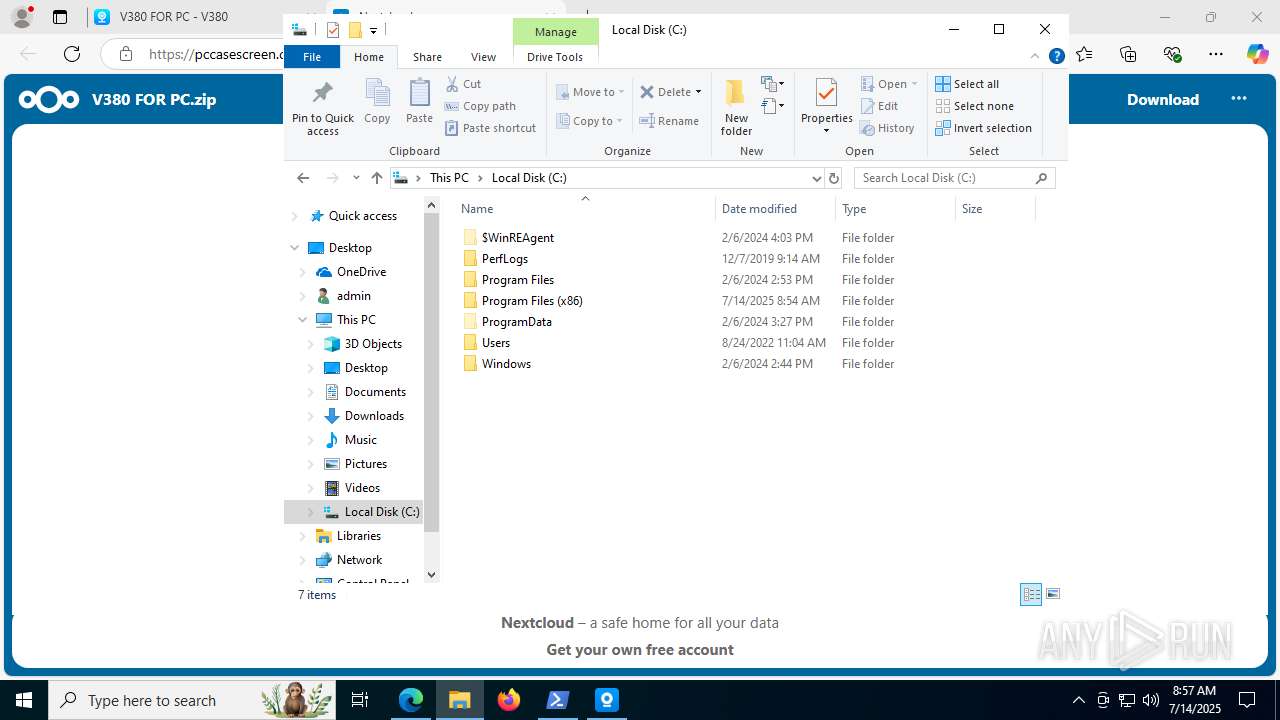
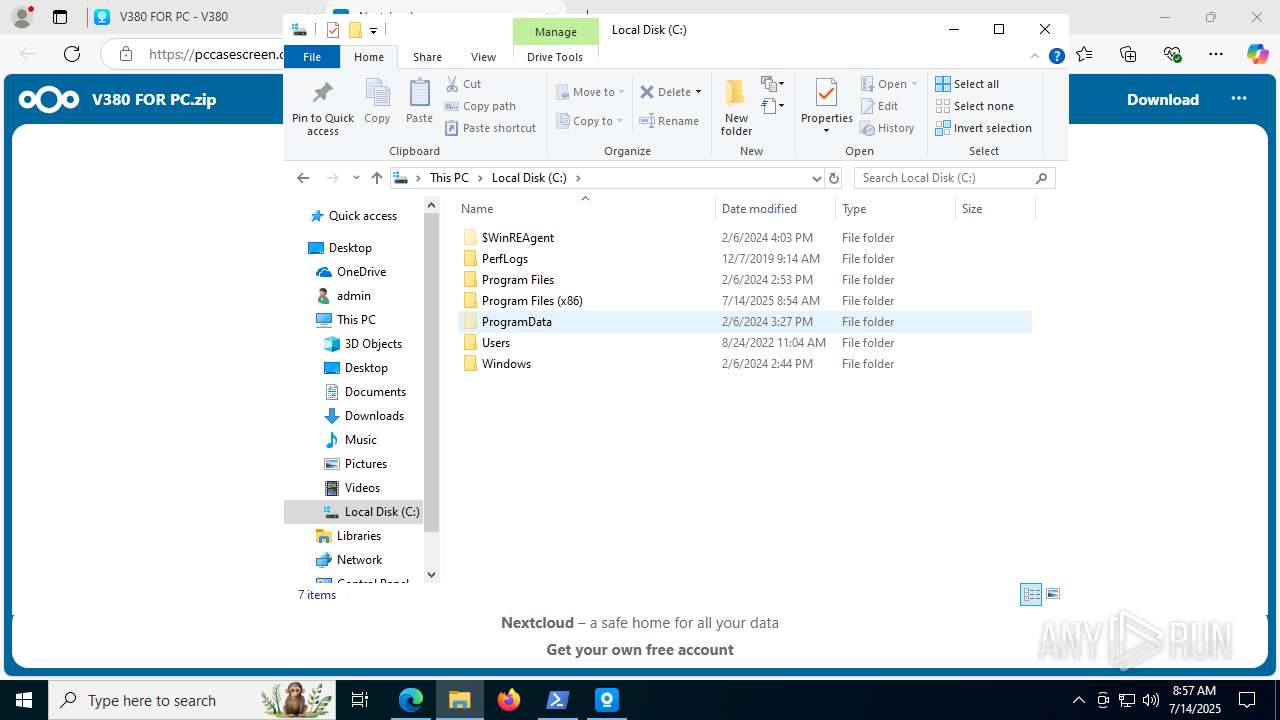
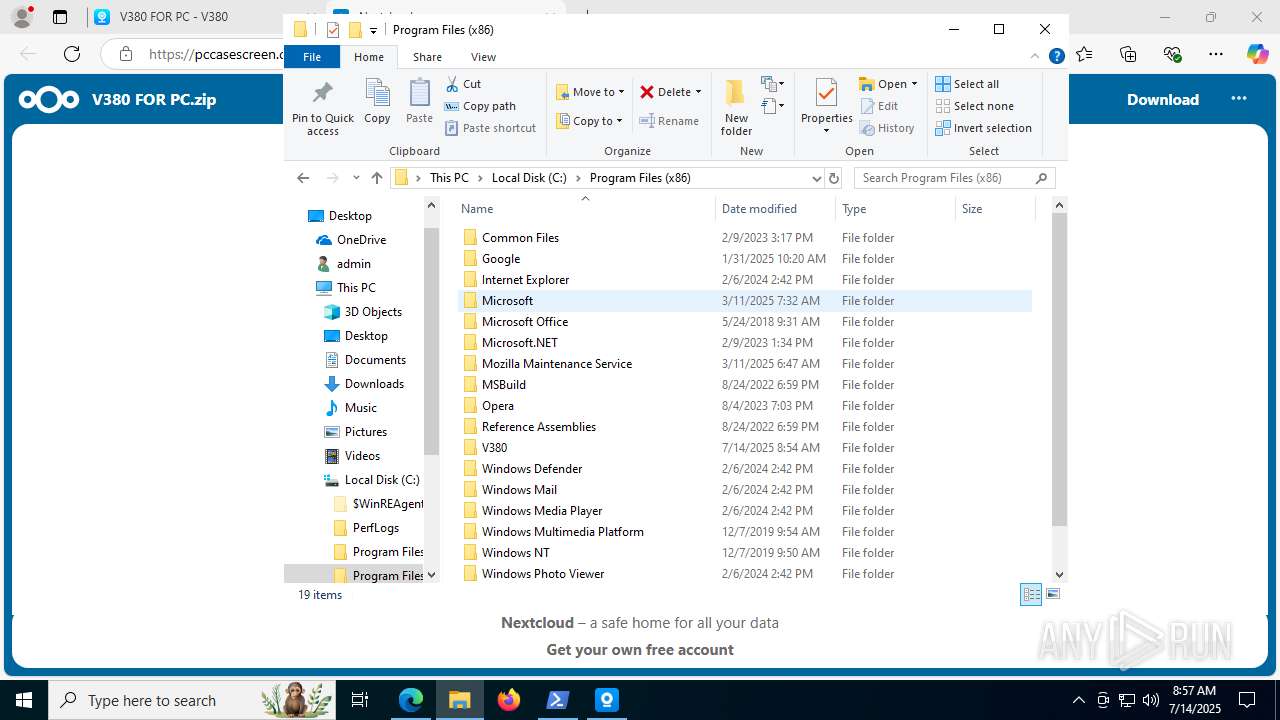
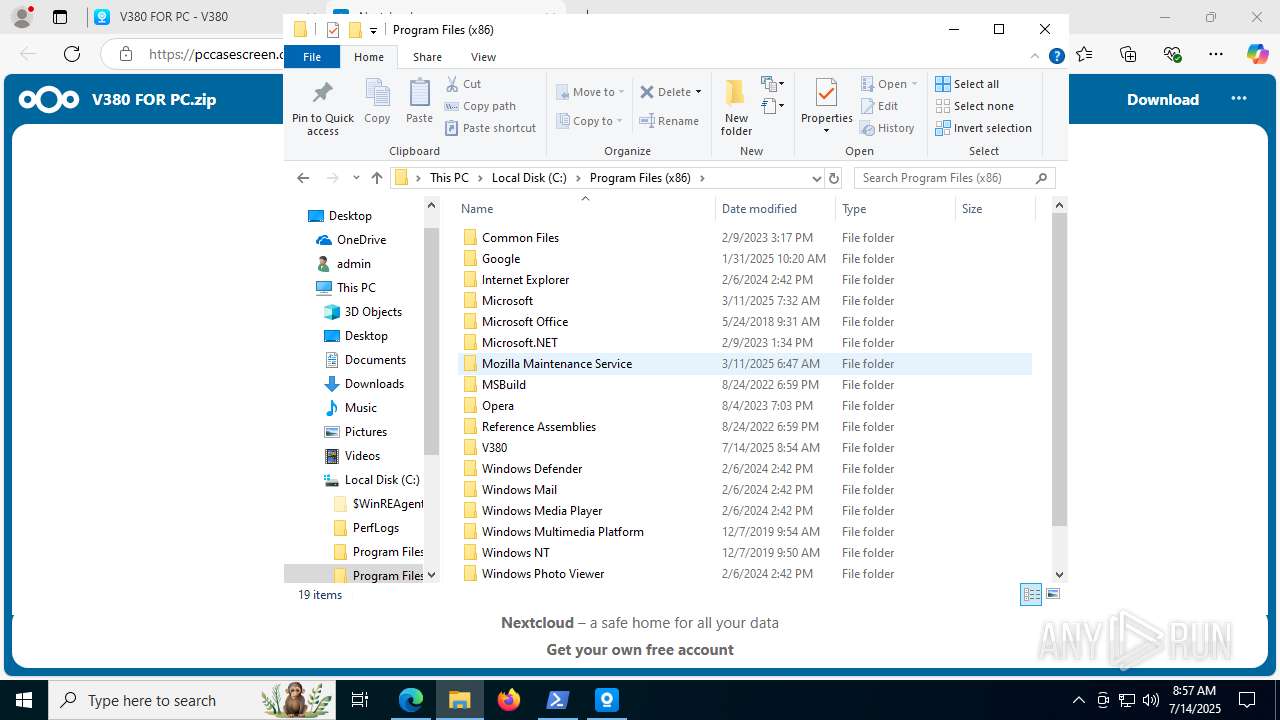
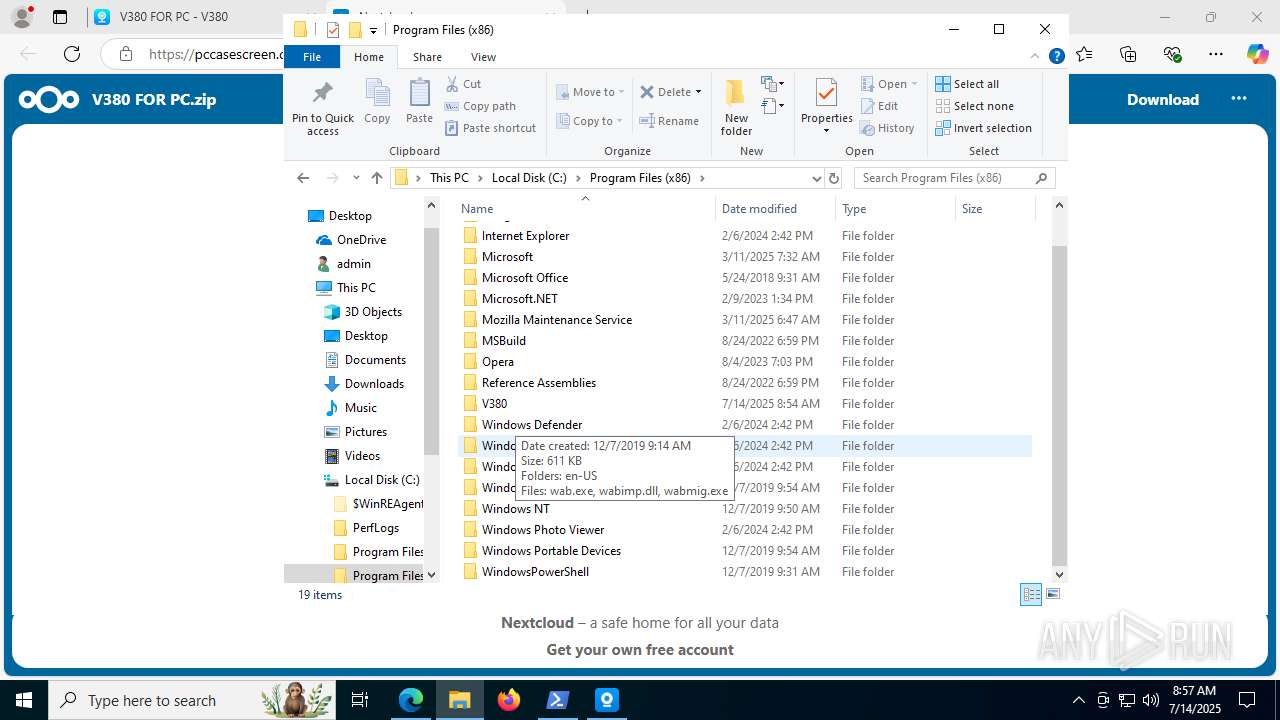
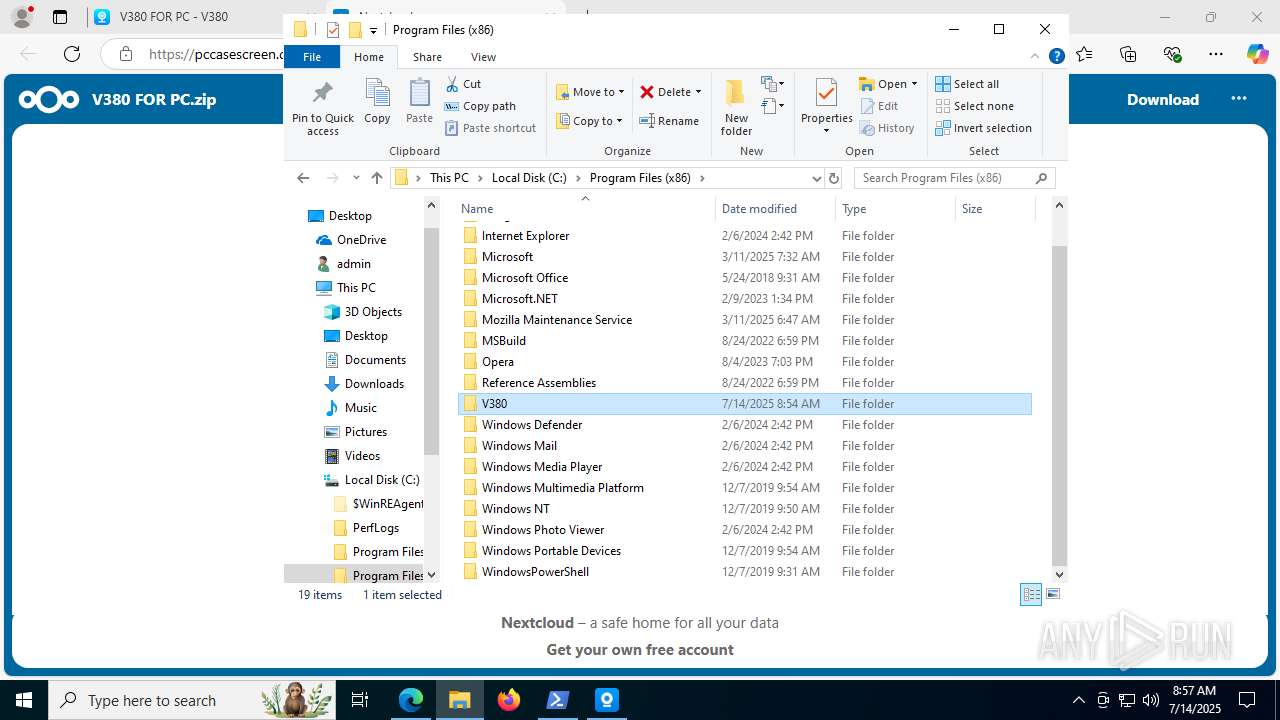
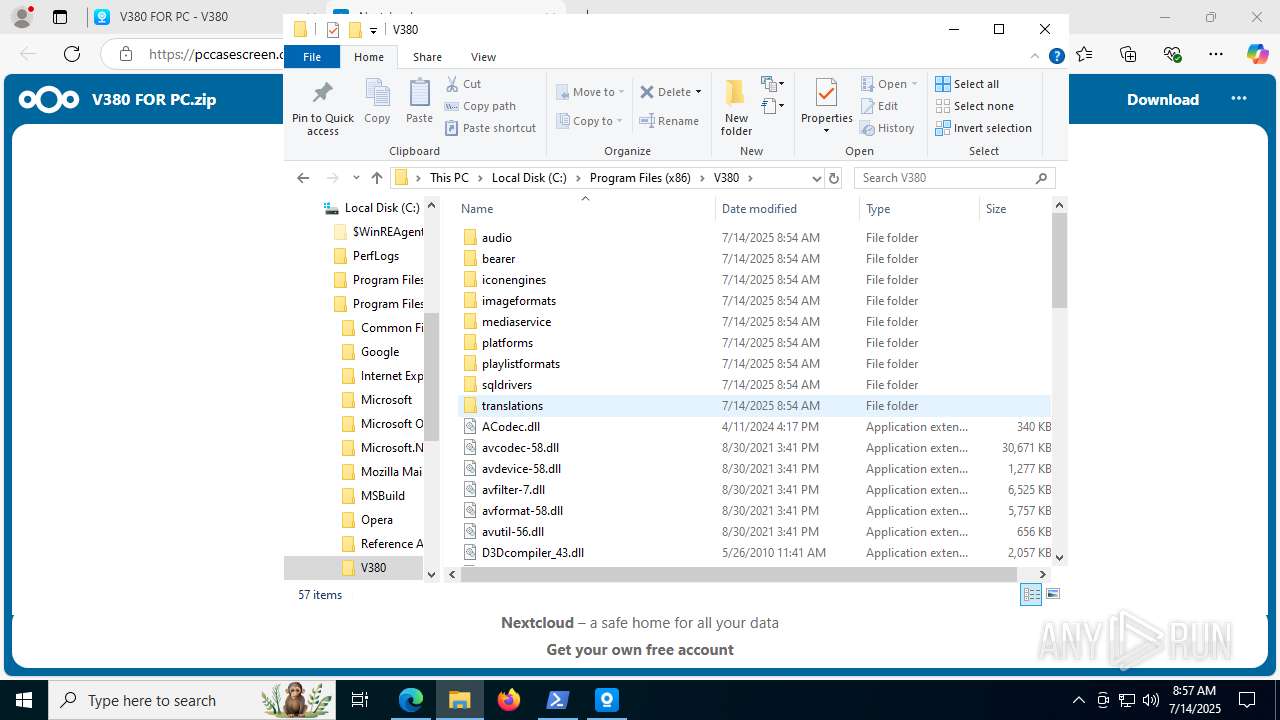
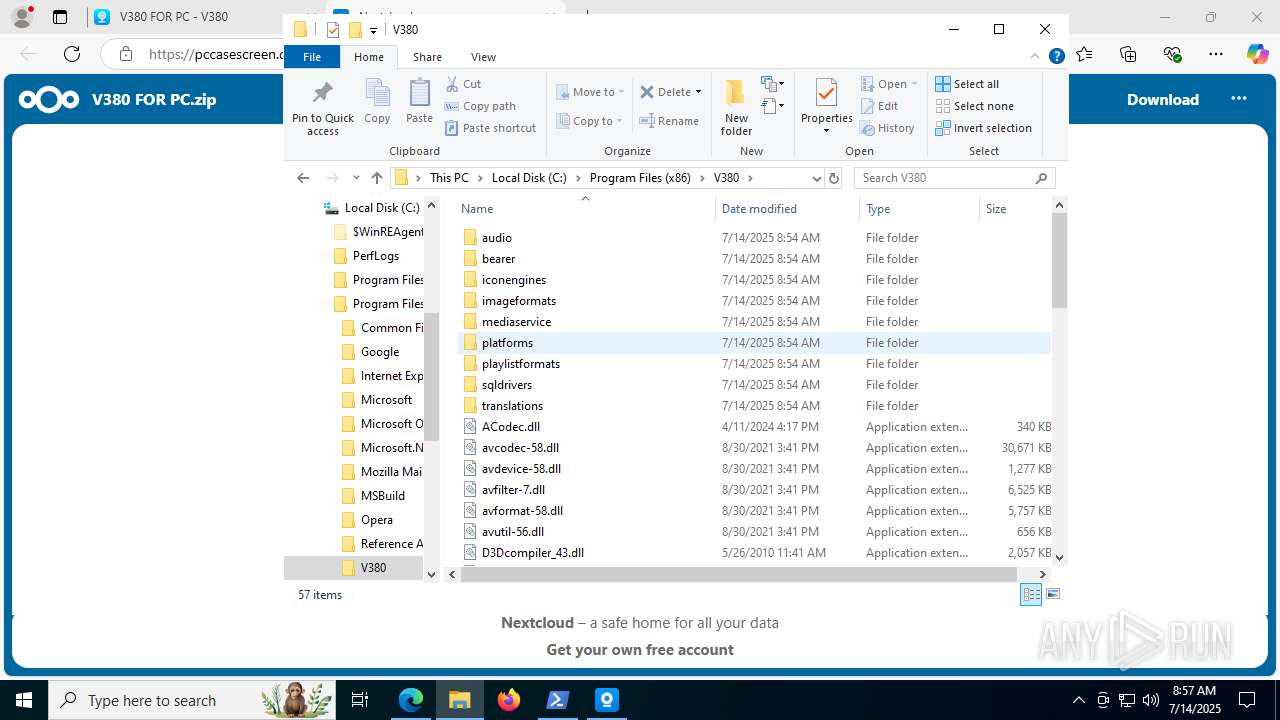
Creates files in the program directory
- V380.2.0.7.tmp (PID: 1932)
Creates files or folders in the user directory
- V380.2.0.7.tmp (PID: 1932)
- V380Login.exe (PID: 4816)
- WerFault.exe (PID: 8152)
The sample compiled with english language support
- V380.2.0.7.tmp (PID: 1932)
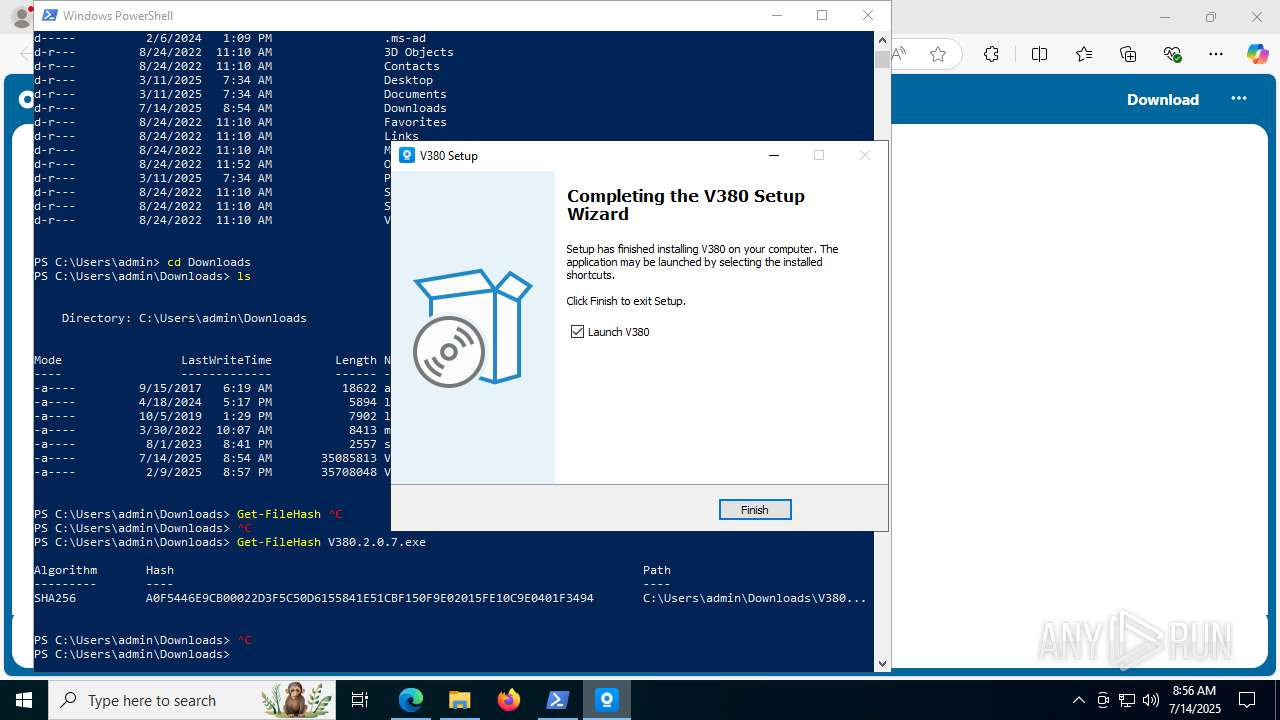
Creates a software uninstall entry
- V380.2.0.7.tmp (PID: 1932)
Checks proxy server information
- slui.exe (PID: 5284)
- WerFault.exe (PID: 8152)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5884)
Reads the software policy settings
- slui.exe (PID: 5284)
- WerFault.exe (PID: 8152)
Compiled with Borland Delphi (YARA)
- V380.2.0.7.exe (PID: 7244)
- V380.2.0.7.tmp (PID: 7236)
- V380.2.0.7.tmp (PID: 1932)
- V380.2.0.7.exe (PID: 4324)
Reads the machine GUID from the registry
- V380.exe (PID: 8112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
54
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2408,i,5967065687311328847,12286320058496311426,262144 --variations-seed-version --mojo-platform-channel-handle=2400 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2264,i,5967065687311328847,12286320058496311426,262144 --variations-seed-version --mojo-platform-channel-handle=2484 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1932 | "C:\Users\admin\AppData\Local\Temp\is-TD1LE.tmp\V380.2.0.7.tmp" /SL5="$901D0,34824985,927744,C:\Users\admin\Downloads\V380.2.0.7.exe" /SPAWNWND=$60232 /NOTIFYWND=$302B2 | C:\Users\admin\AppData\Local\Temp\is-TD1LE.tmp\V380.2.0.7.tmp | V380.2.0.7.exe | ||||||||||||
User: admin Company: M@cro-video Technologies Co. Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\V380 FOR PC.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7492,i,5967065687311328847,12286320058496311426,262144 --variations-seed-version --mojo-platform-channel-handle=4128 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7324,i,5967065687311328847,12286320058496311426,262144 --variations-seed-version --mojo-platform-channel-handle=7400 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2680,i,5967065687311328847,12286320058496311426,262144 --variations-seed-version --mojo-platform-channel-handle=2800 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4384f208,0x7ffc4384f214,0x7ffc4384f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4324 | "C:\Users\admin\Downloads\V380.2.0.7.exe" /SPAWNWND=$60232 /NOTIFYWND=$302B2 | C:\Users\admin\Downloads\V380.2.0.7.exe | V380.2.0.7.tmp | ||||||||||||
User: admin Company: M@cro-video Technologies Co. Integrity Level: HIGH Description: V380 Setup Exit code: 0 Version: 2.0.7 Modules
| |||||||||||||||
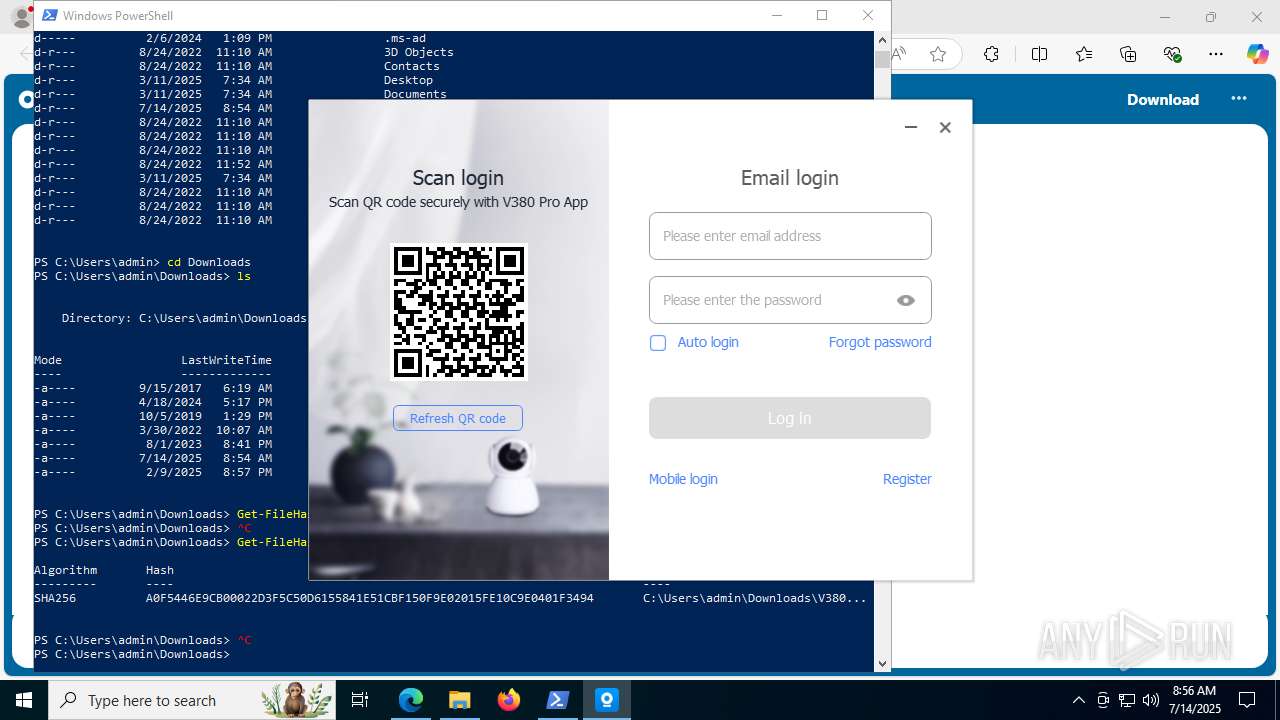
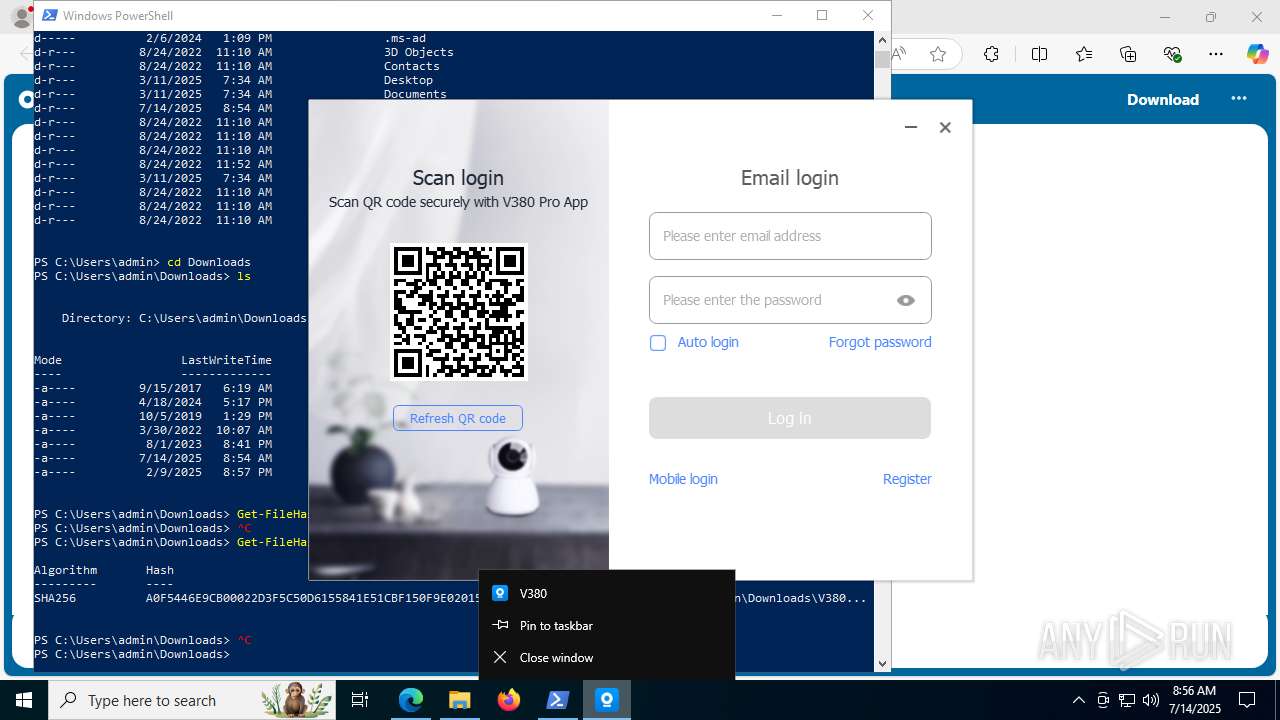
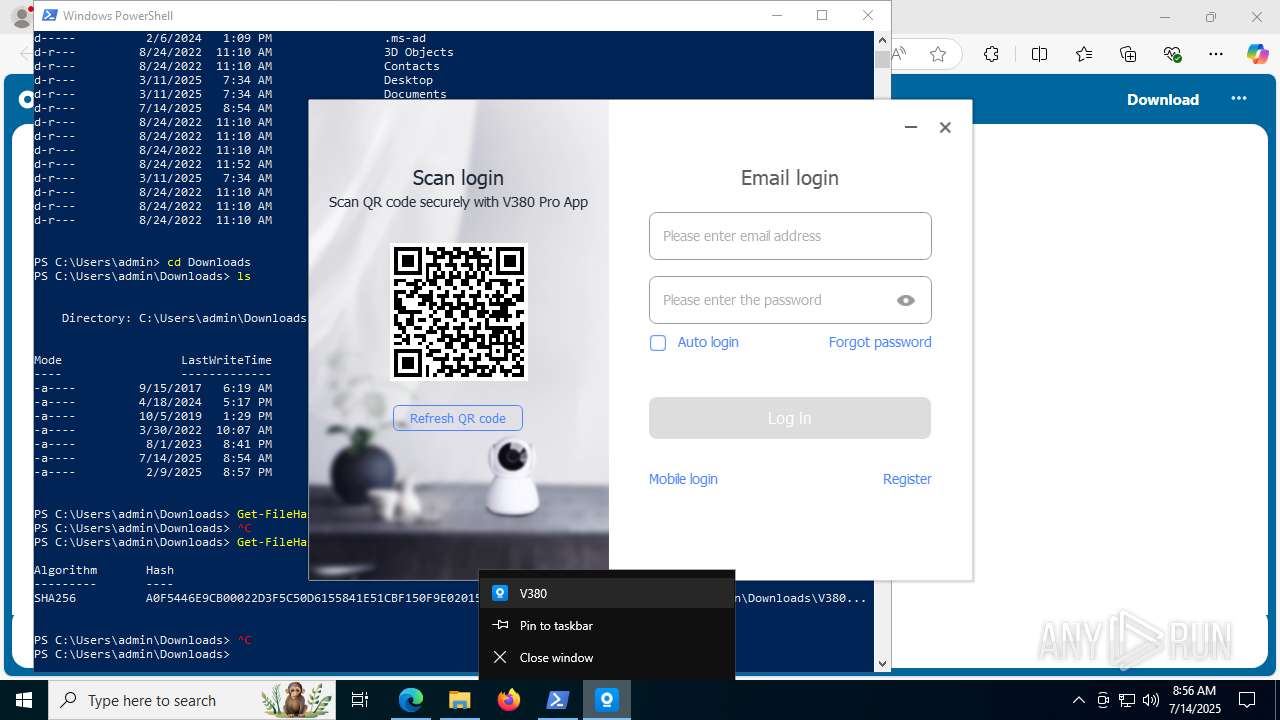
| 4816 | "C:\Program Files (x86)\V380\V380Login.exe" | C:\Program Files (x86)\V380\V380Login.exe | V380.2.0.7.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
24 189
Read events
24 129
Write events
57
Delete events
3
Modification events
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 809A701176982F00 | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5108C6A0-CDBF-46DE-8153-2C9FA0BDB9A6} | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D84295FD-AF79-490A-A104-A12DCBE5E54E} | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BD0E083D-91B7-4C9B-B6C7-4AA22086C193} | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {357D8E64-D253-4E2A-8D5C-D6E460F774F3} | |||
| (PID) Process: | (7080) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459642 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {58584075-C6E6-46A3-880A-BC567A13BC81} | |||
Executable files
140
Suspicious files
250
Text files
91
Unknown types
107
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17563e.TMP | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17563e.TMP | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17565d.TMP | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17565d.TMP | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17566d.TMP | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7080 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17566d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
178
DNS requests
144
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
592 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:W4uknc8m3cBidTYQMSLaIH_kS91myHOjttUGc6_f64w&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
436 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7620 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5556 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753010077&P2=404&P3=2&P4=AMPX9d5NHC1otMeWMWGUIv6b01Z%2fE07%2bfPt6fGUW63OOAi7V0Hp544Hw6SmWropgmkNVr%2bMepuOm1yoS8w6CwA%3d%3d | unknown | — | — | whitelisted |
5556 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753010077&P2=404&P3=2&P4=AMPX9d5NHC1otMeWMWGUIv6b01Z%2fE07%2bfPt6fGUW63OOAi7V0Hp544Hw6SmWropgmkNVr%2bMepuOm1yoS8w6CwA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5172 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
592 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
592 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
592 | msedge.exe | 52.102.113.17:443 | eur02.safelinks.protection.outlook.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
592 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
592 | msedge.exe | 2.23.227.199:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
eur02.safelinks.protection.outlook.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
v380.org |
| unknown |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
V380Login.exe | language num: 2
|
V380Login.exe | sigGetCountryCode: 113
|
V380Login.exe | E:\V380\v380pro\V380Login\LoginSystem\LoginSystem.cpp 220 GetQRCode success
|