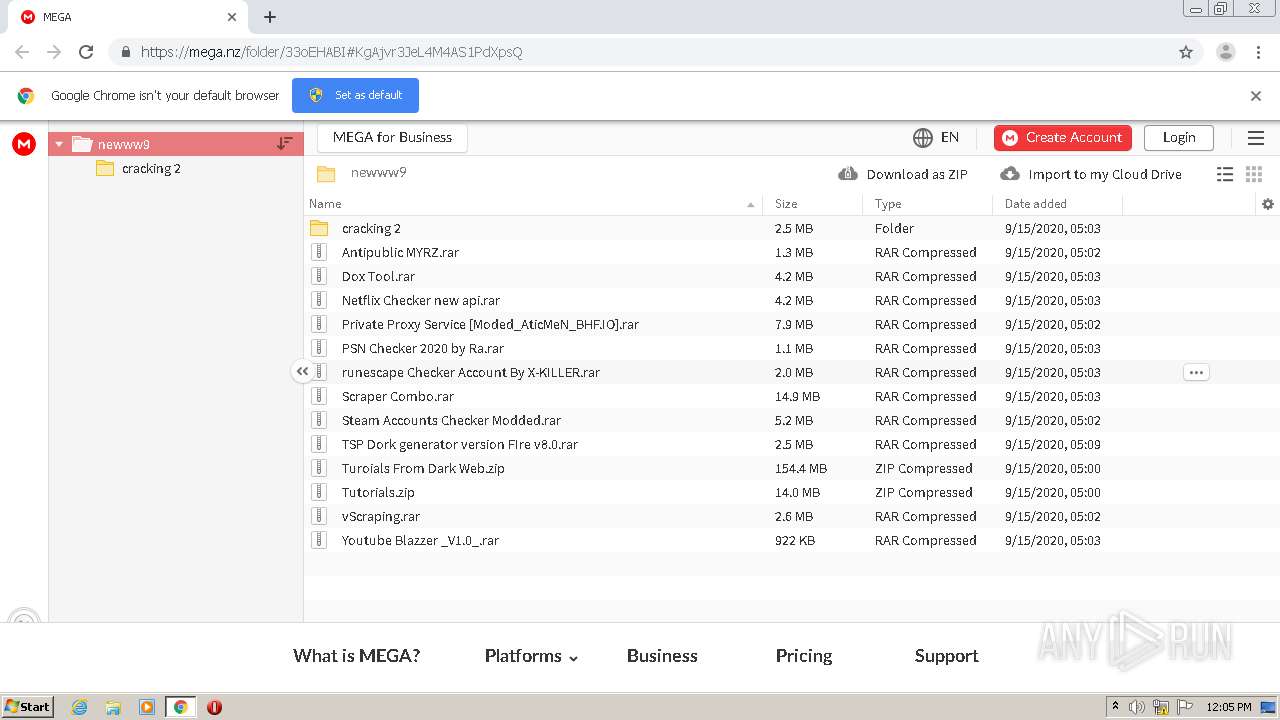
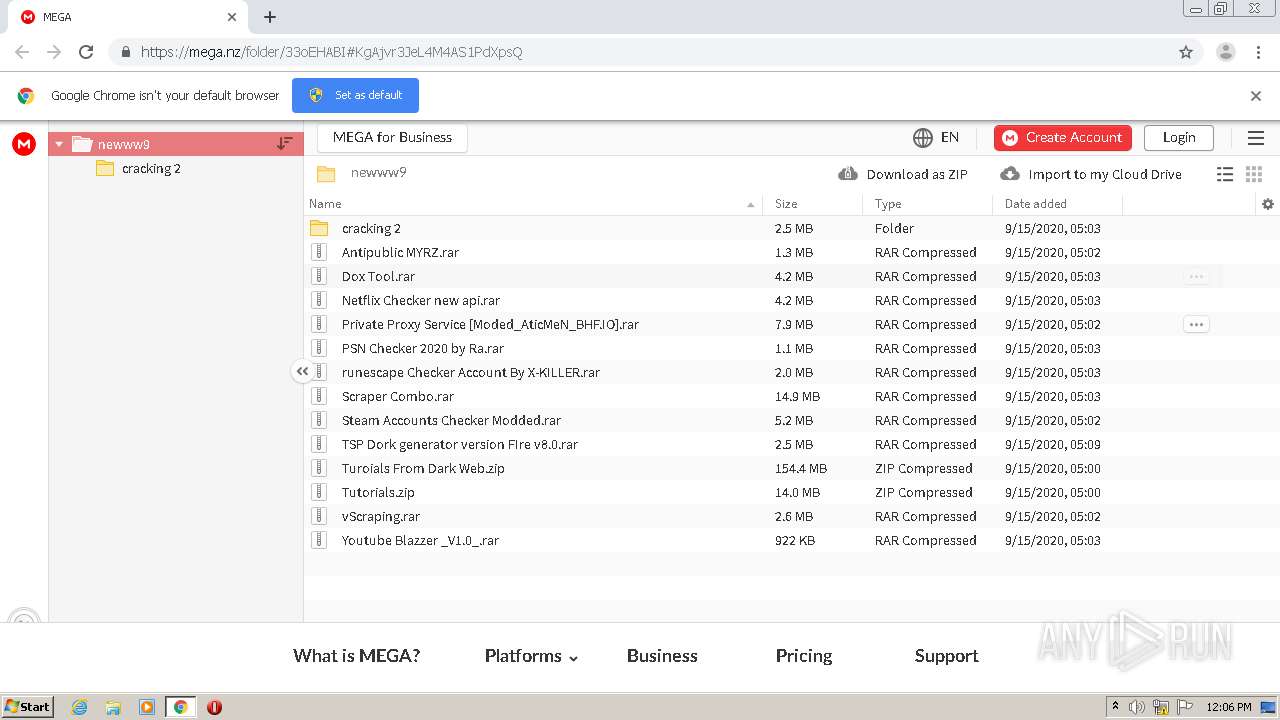
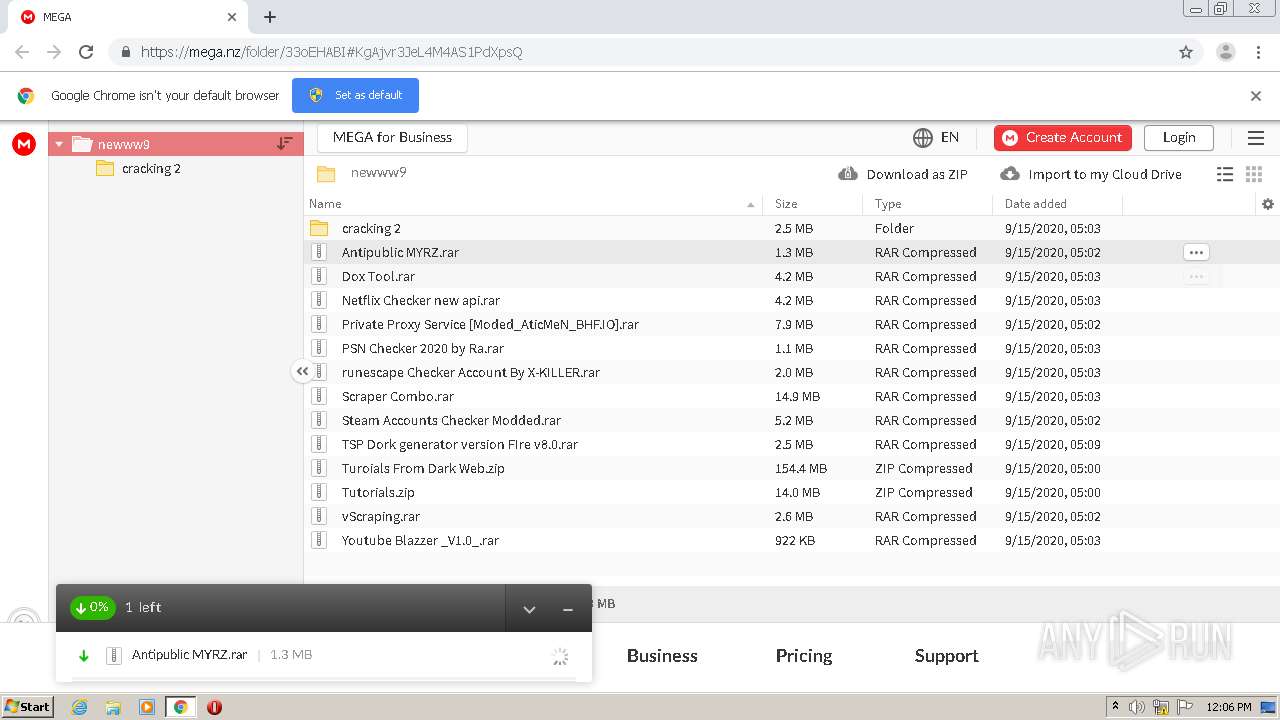
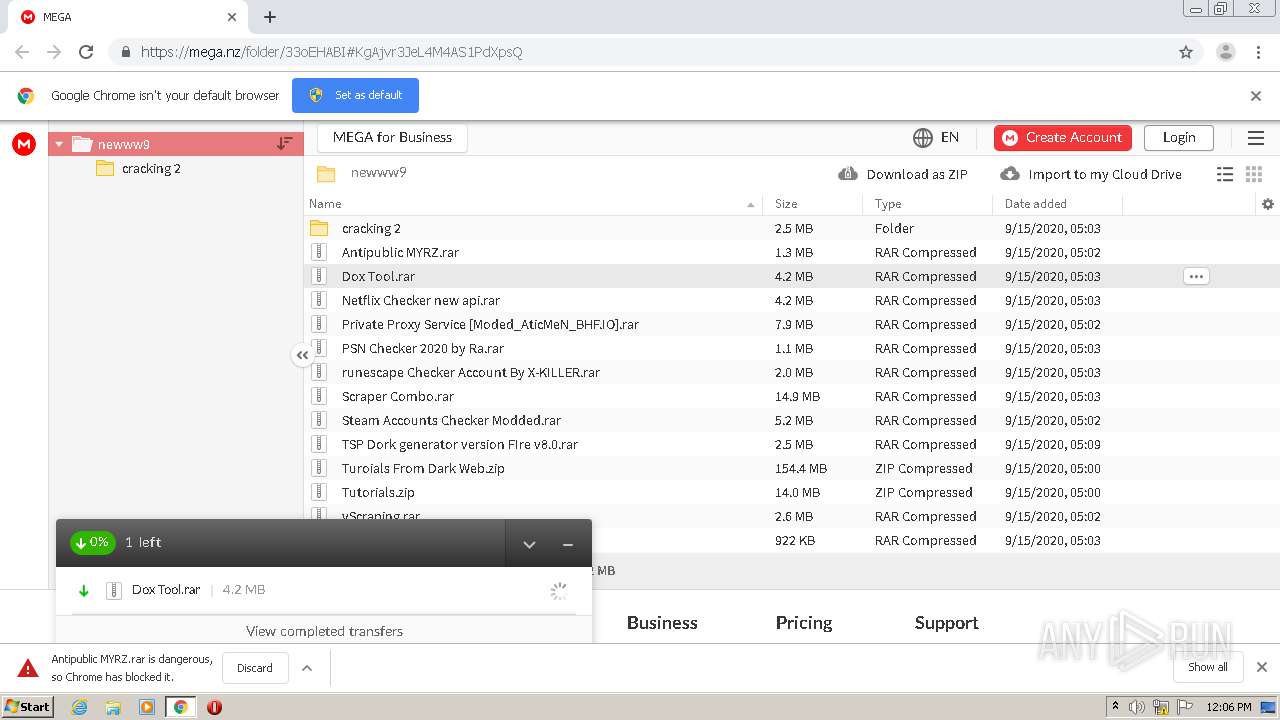
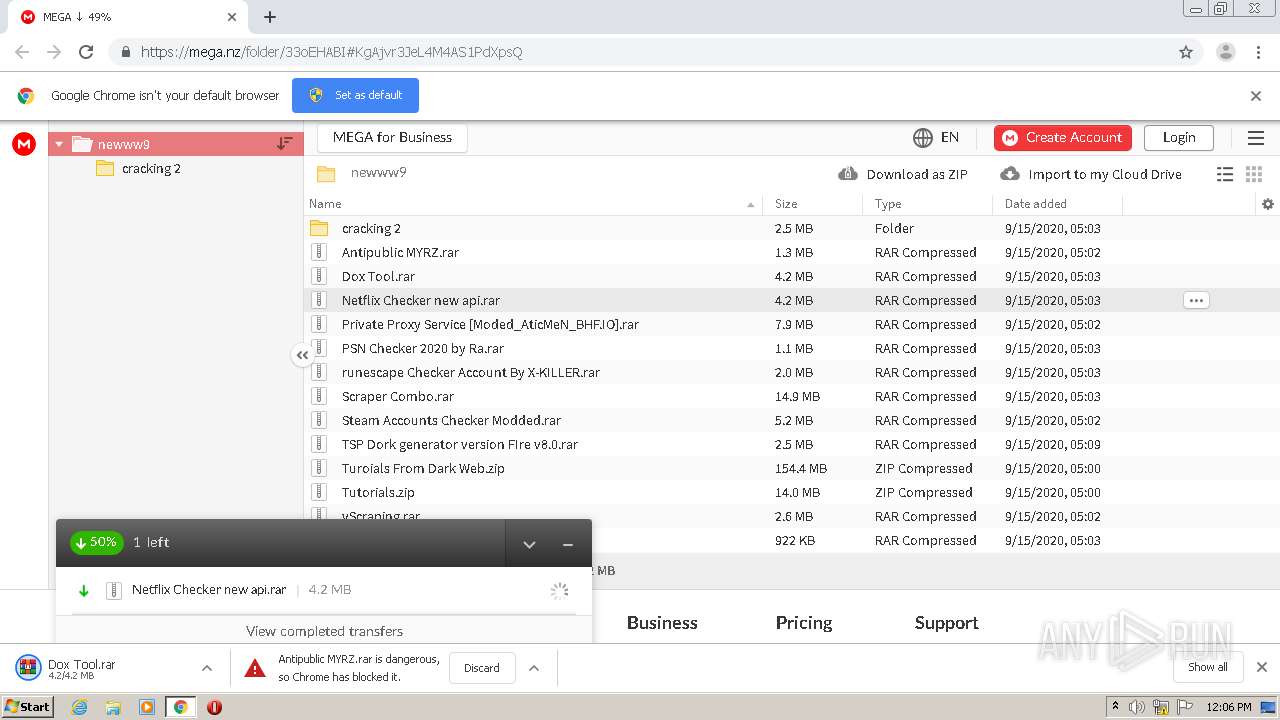
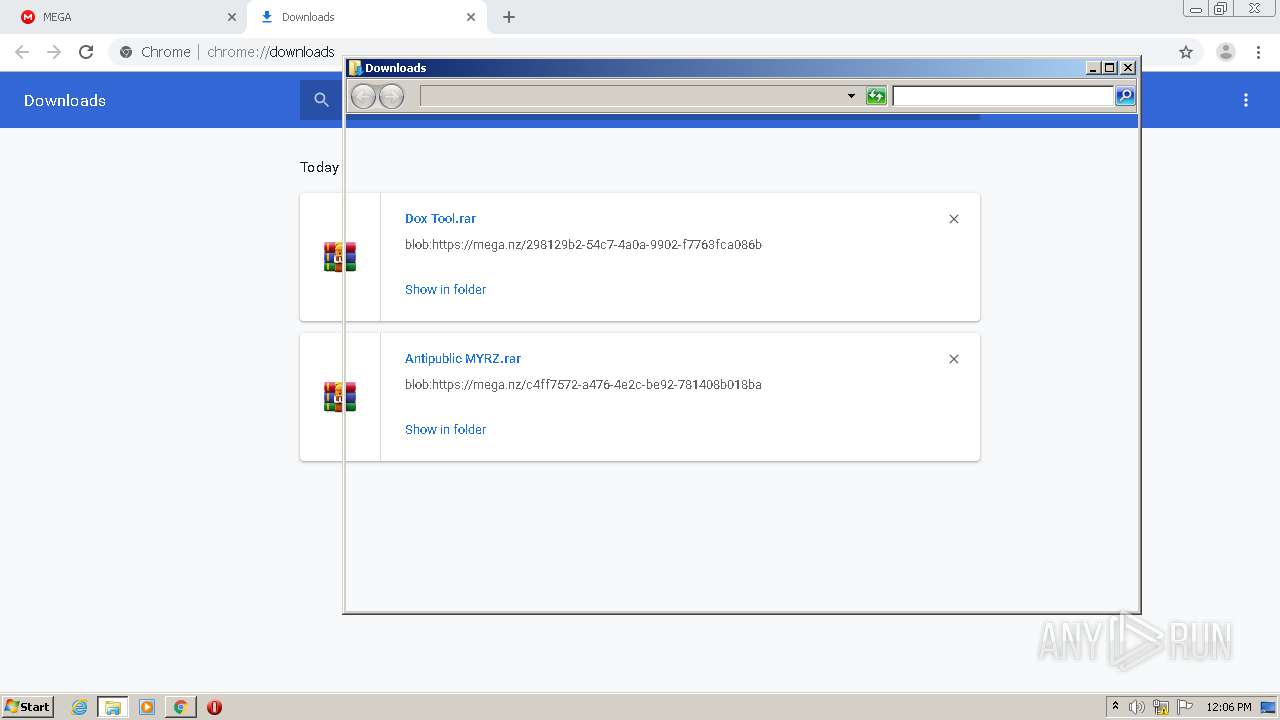
| URL: | https://mega.nz/folder/33oEHABI#KgAjvr3JeL4M4AS1PdXpsQ |
| Full analysis: | https://app.any.run/tasks/f35d1930-ac35-4581-99a1-0a2498b58d49 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 11:05:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D12BF4F196C554F08D6BDEFACE93E46 |
| SHA1: | 1029B1A2475C536E52FC892D5487D88E34FF55F1 |
| SHA256: | 45181C733A8C6C0E0C17737D365DEF51B054C2C2133FA38EB7CA4EAB3F753588 |
| SSDEEP: | 3:N8X/iuyKWytknLMSUL9l:26Nytk/gD |
MALICIOUS
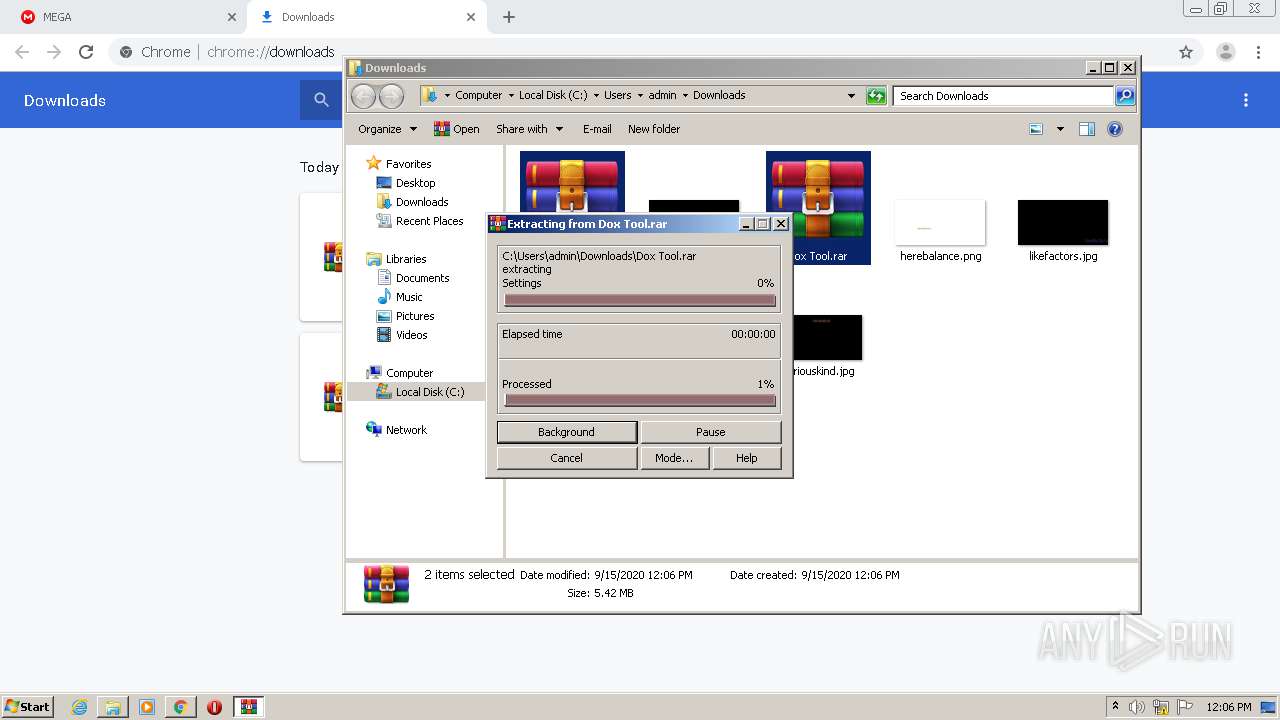
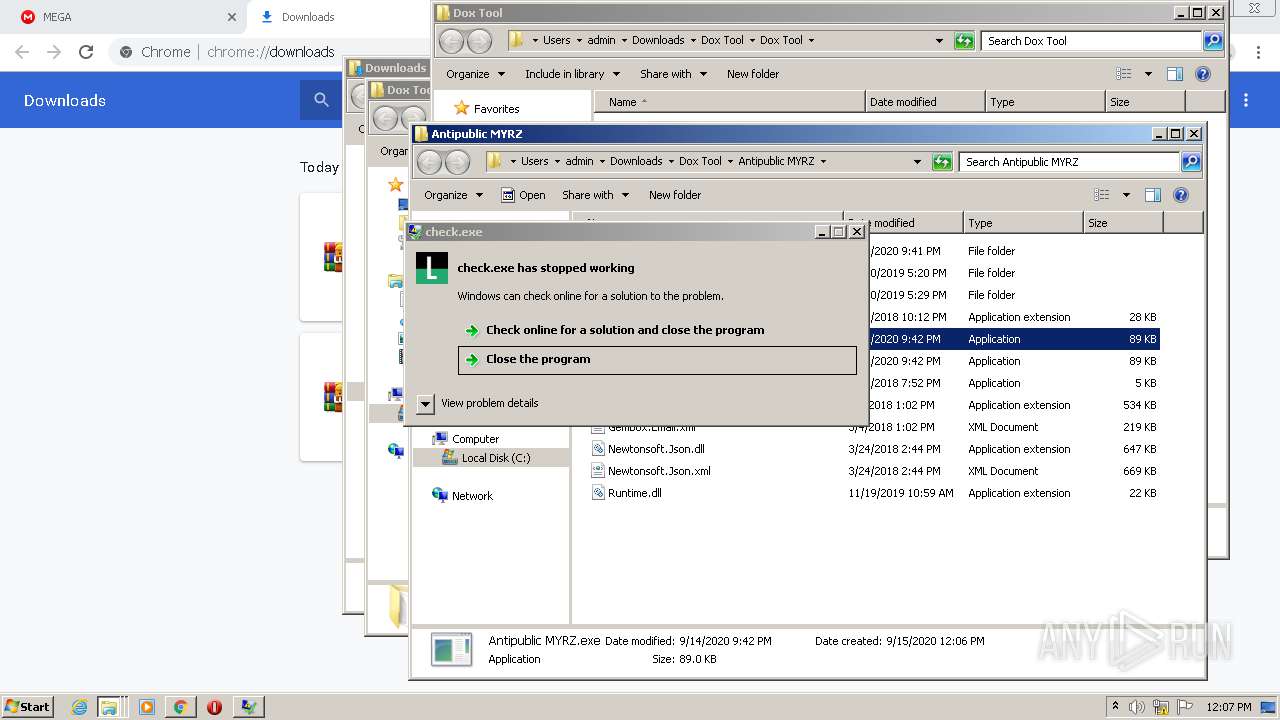
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 4052)
- check.exe (PID: 2840)
Application was dropped or rewritten from another process
- settings.exe (PID: 1948)
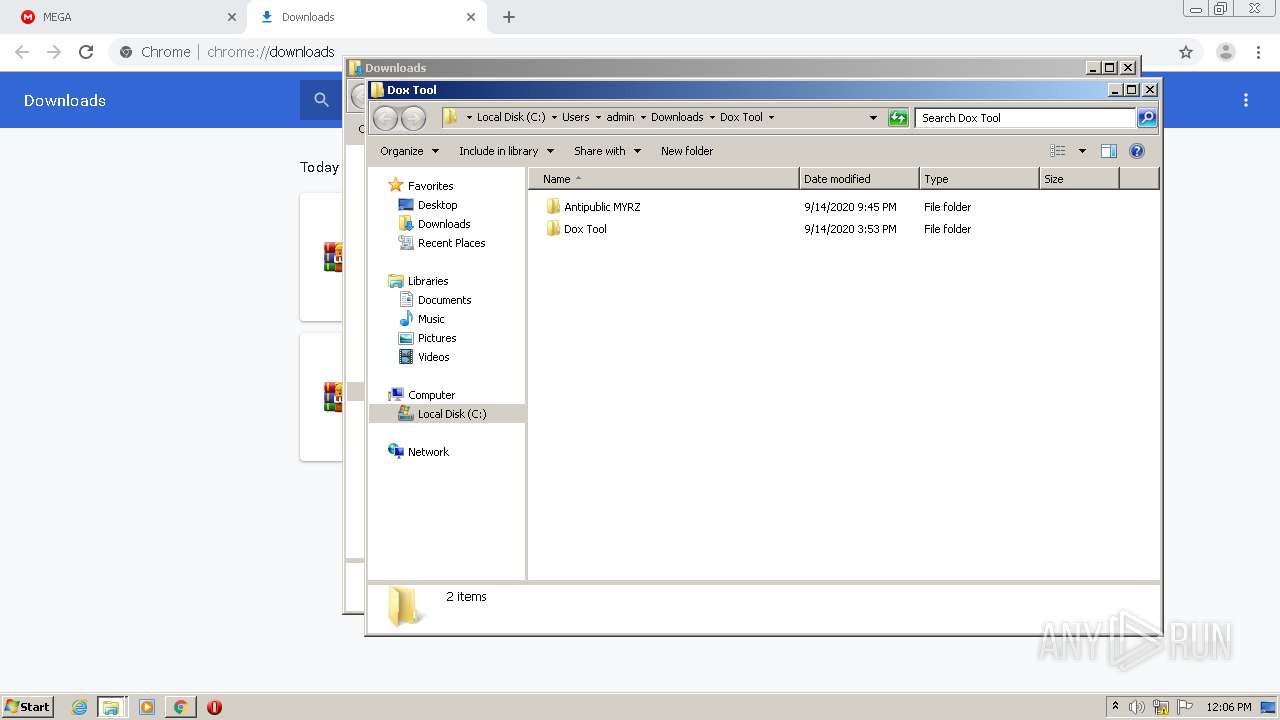
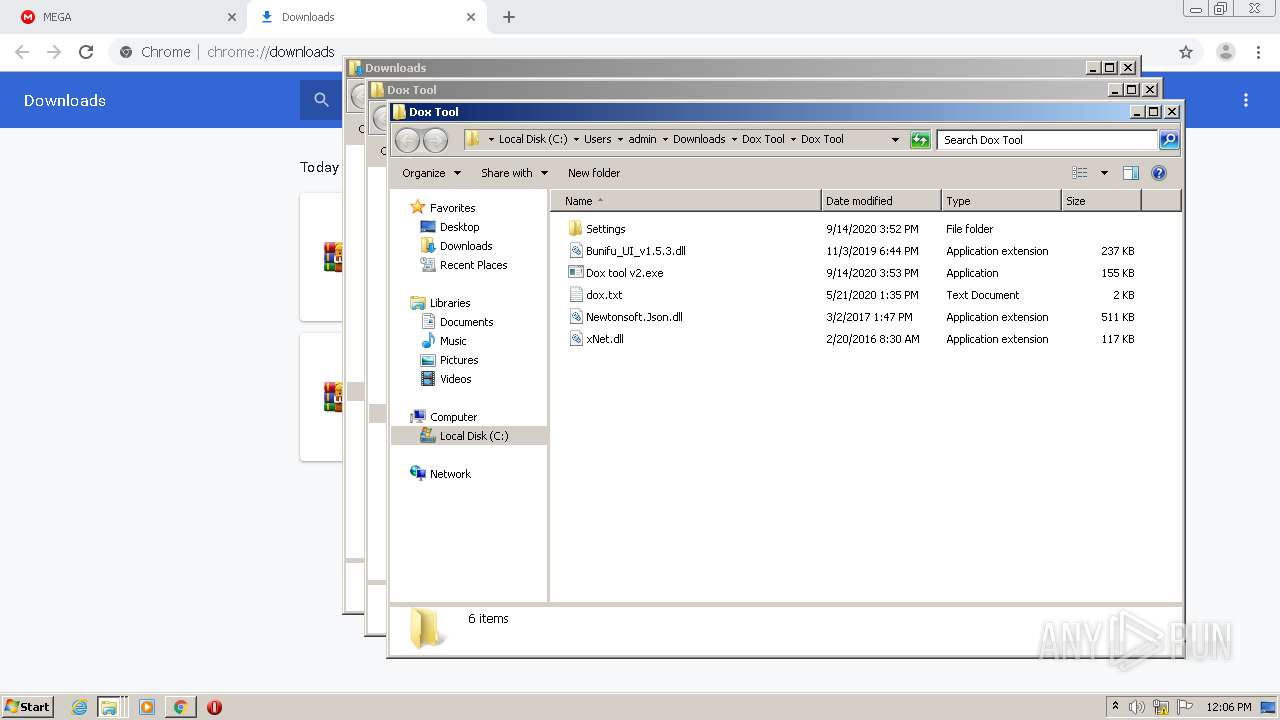
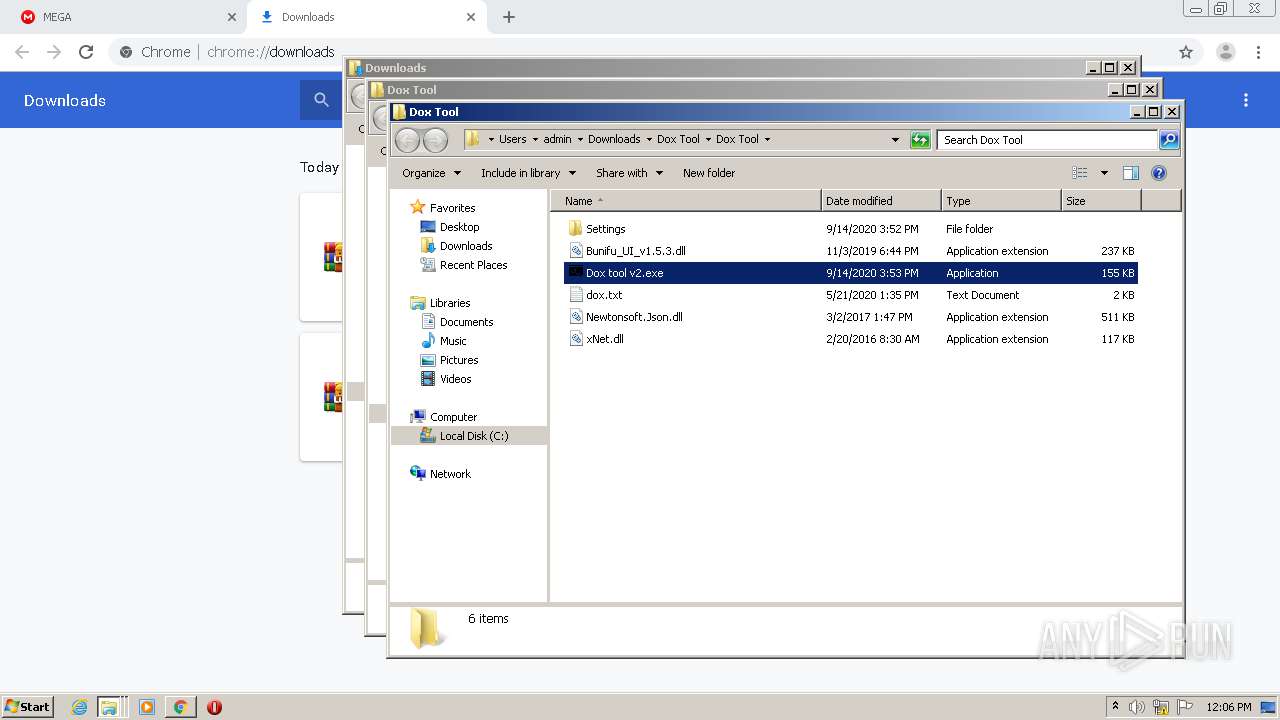
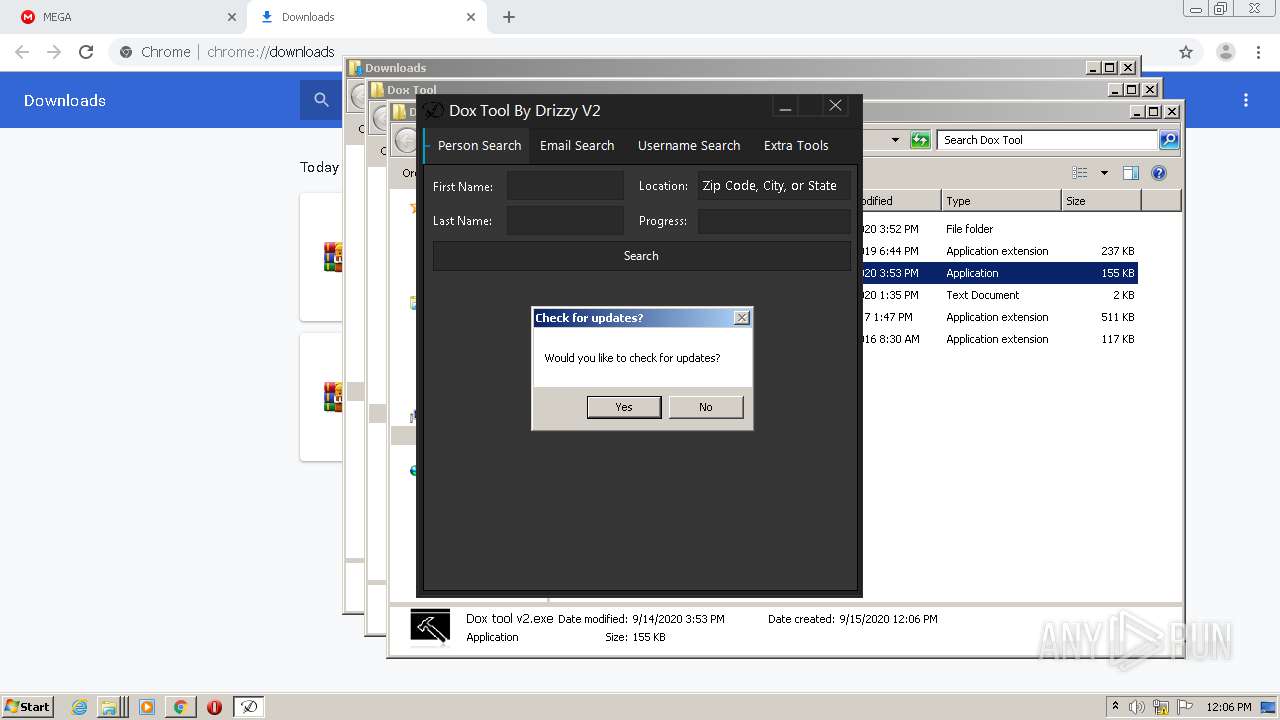
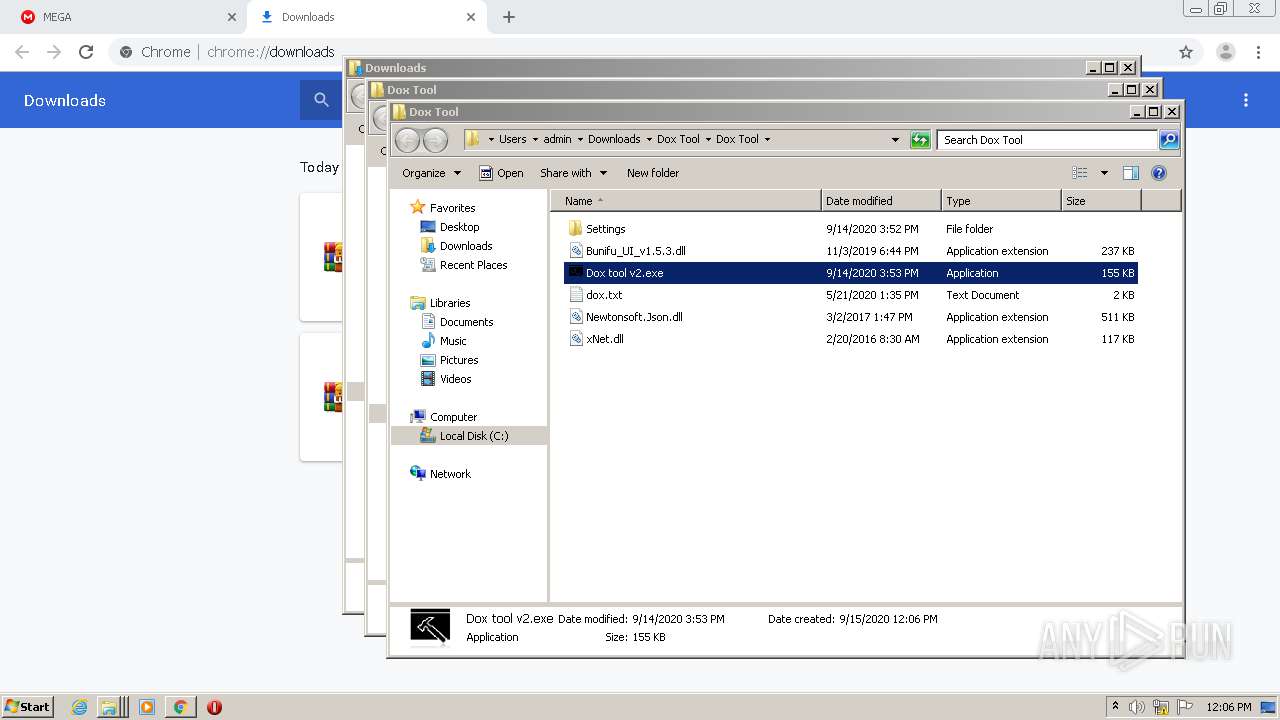
- Dox tool v2.exe (PID: 1256)
- check.exe (PID: 3228)
- ctfmom.exe (PID: 1688)
- Antipublic MYRZ.exe (PID: 2088)
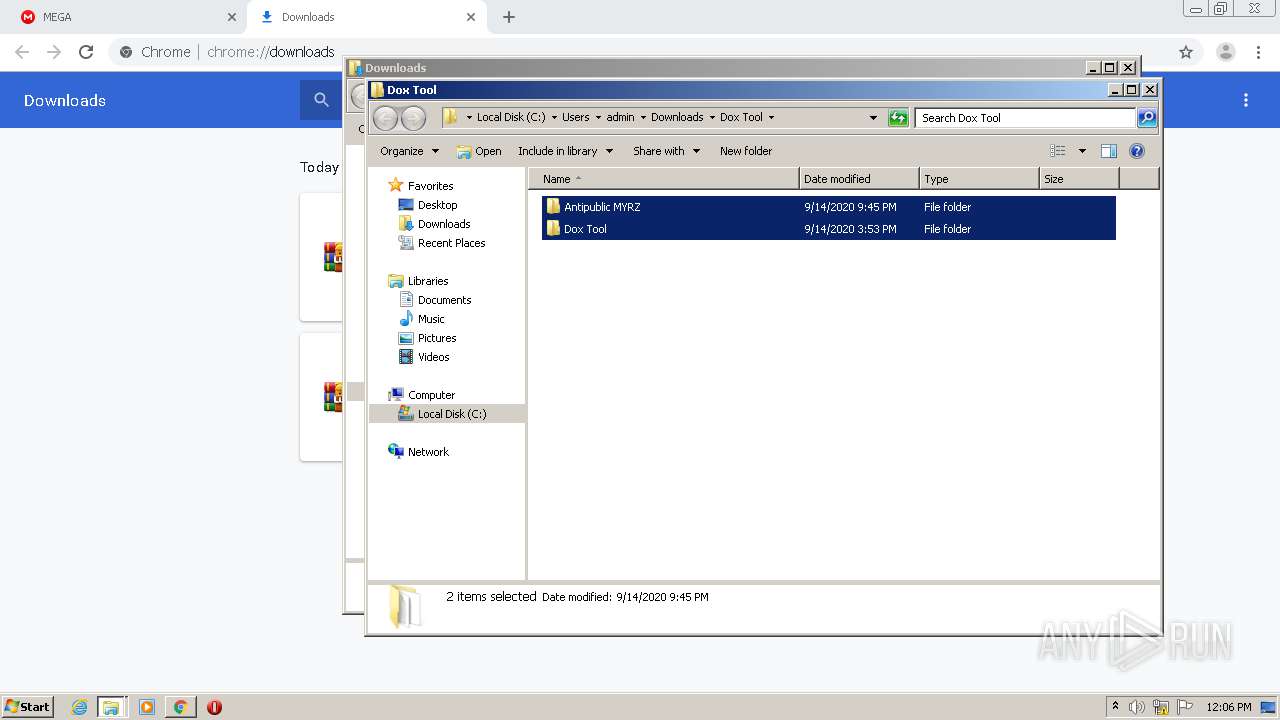
- runtime.exe (PID: 2560)
- check.exe (PID: 2840)
Writes to a start menu file
- check.exe (PID: 3228)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2832)
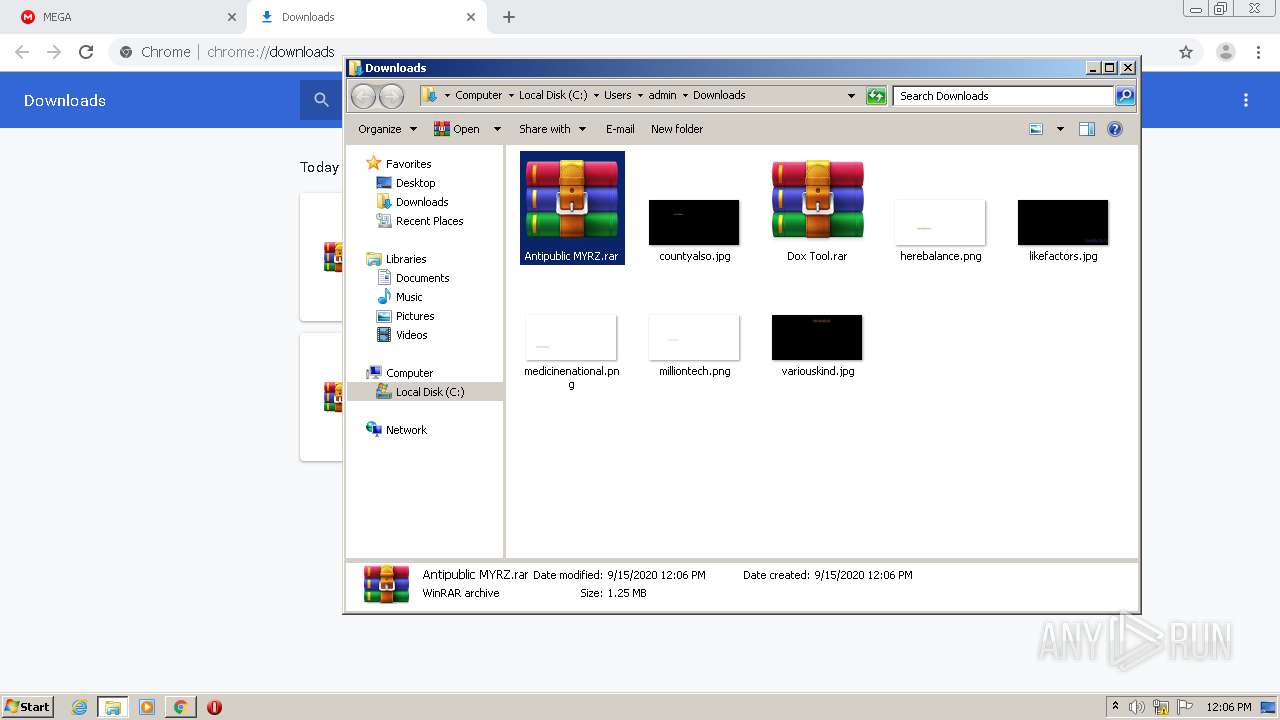
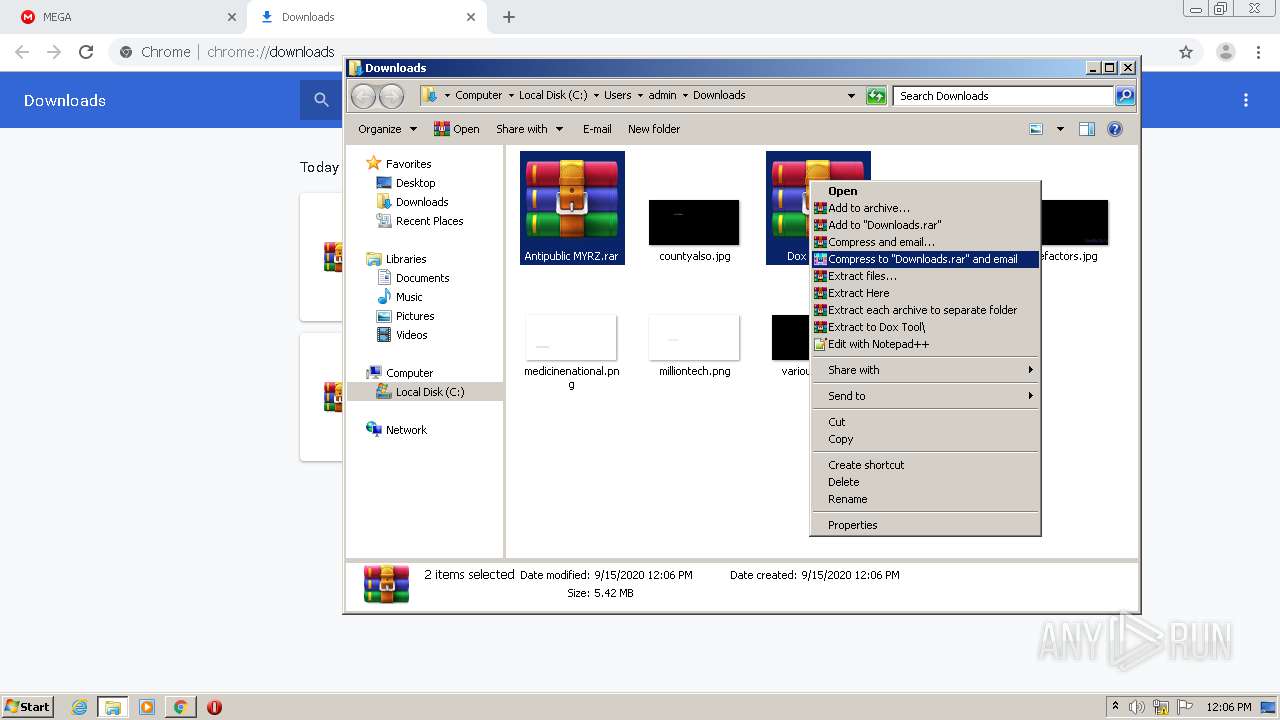
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2744)
- check.exe (PID: 3228)
- check.exe (PID: 2840)
Starts CMD.EXE for commands execution
- Dox tool v2.exe (PID: 1256)
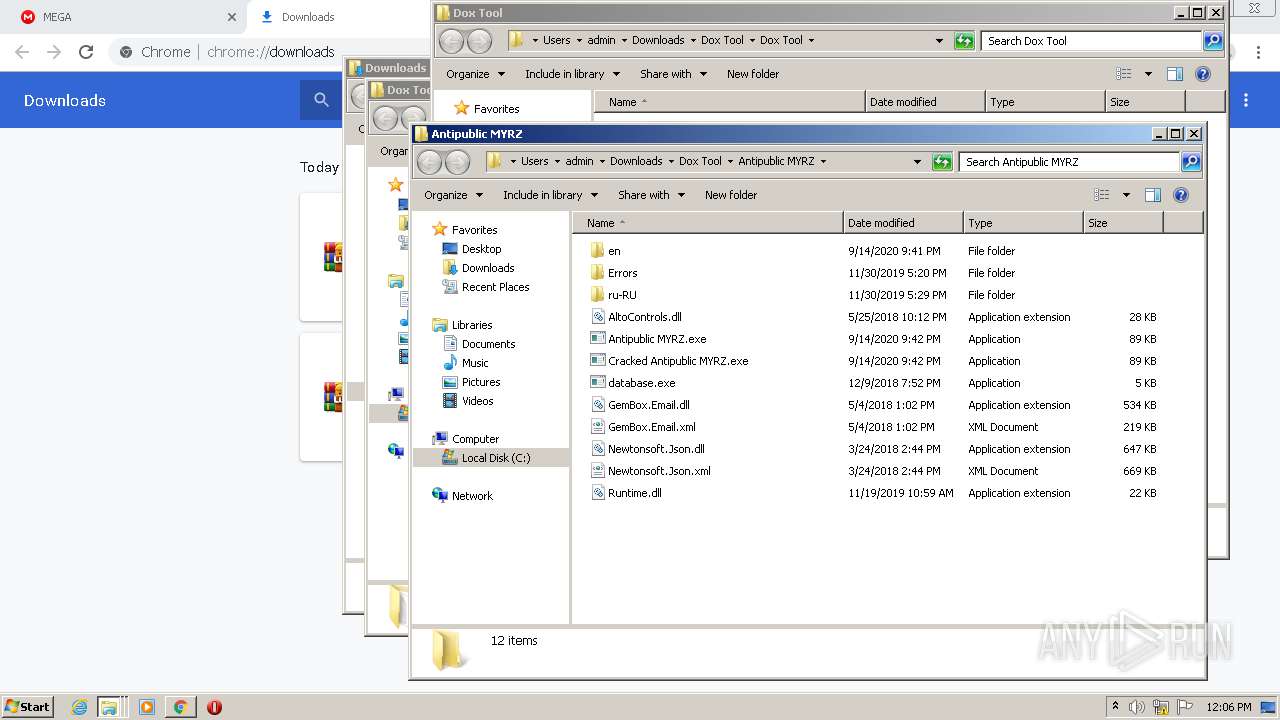
- Antipublic MYRZ.exe (PID: 2088)
Creates files in the user directory
- check.exe (PID: 3228)
INFO
Reads the hosts file
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2832)
Application launched itself
- chrome.exe (PID: 2832)
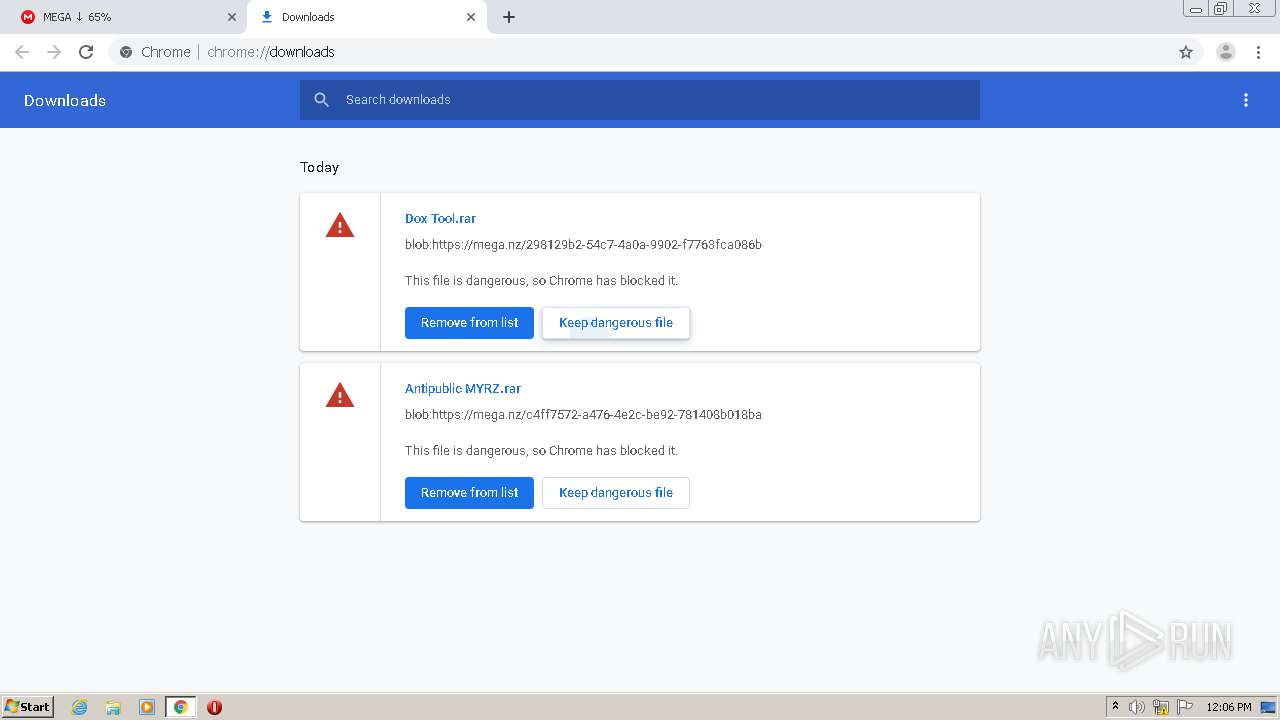
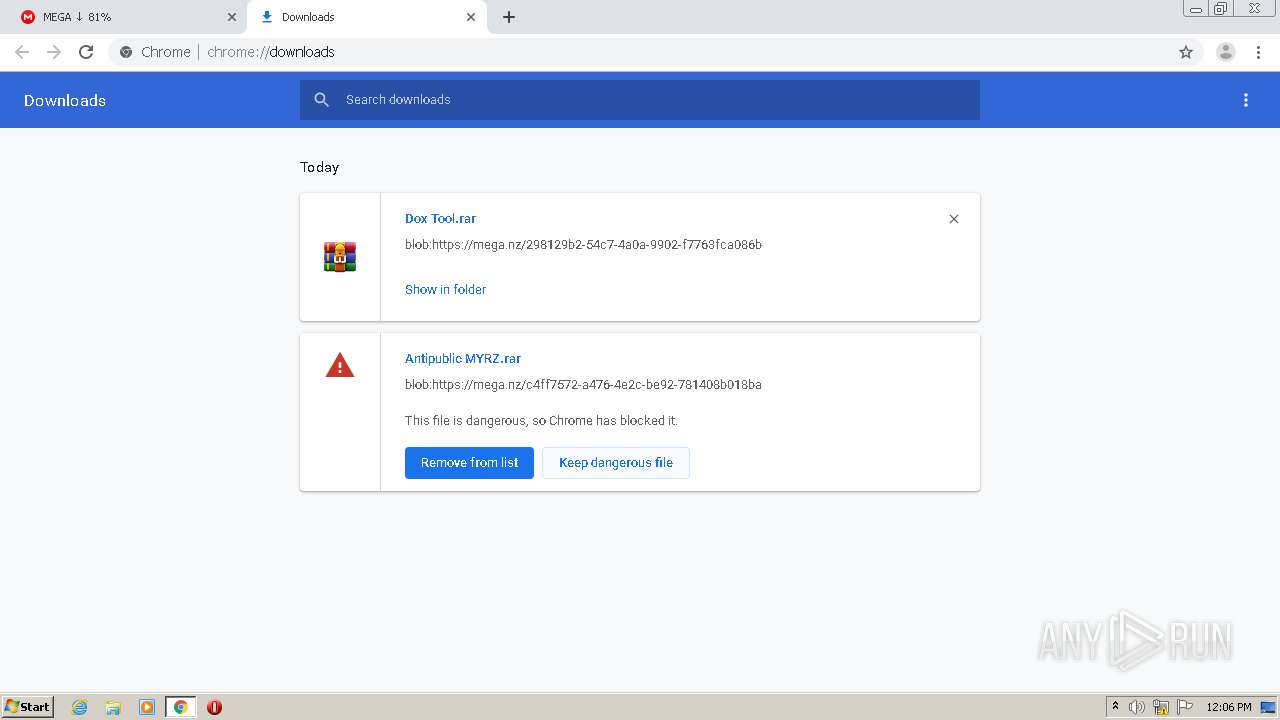
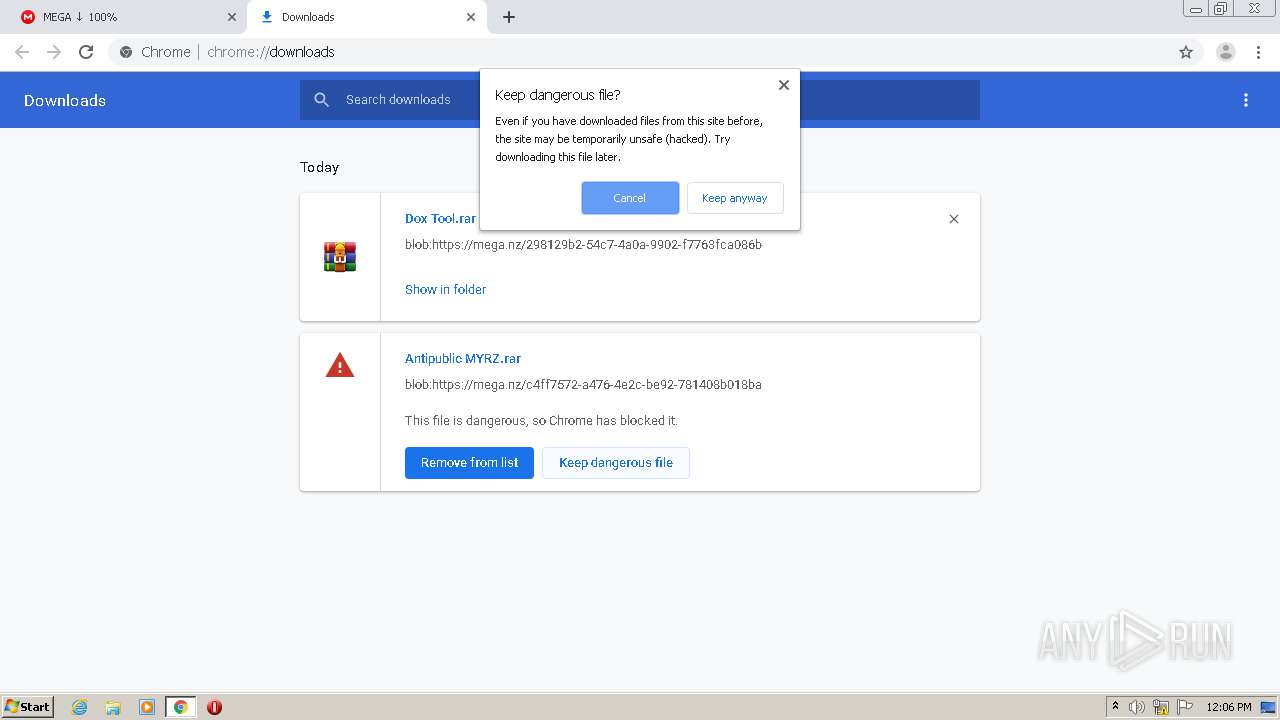
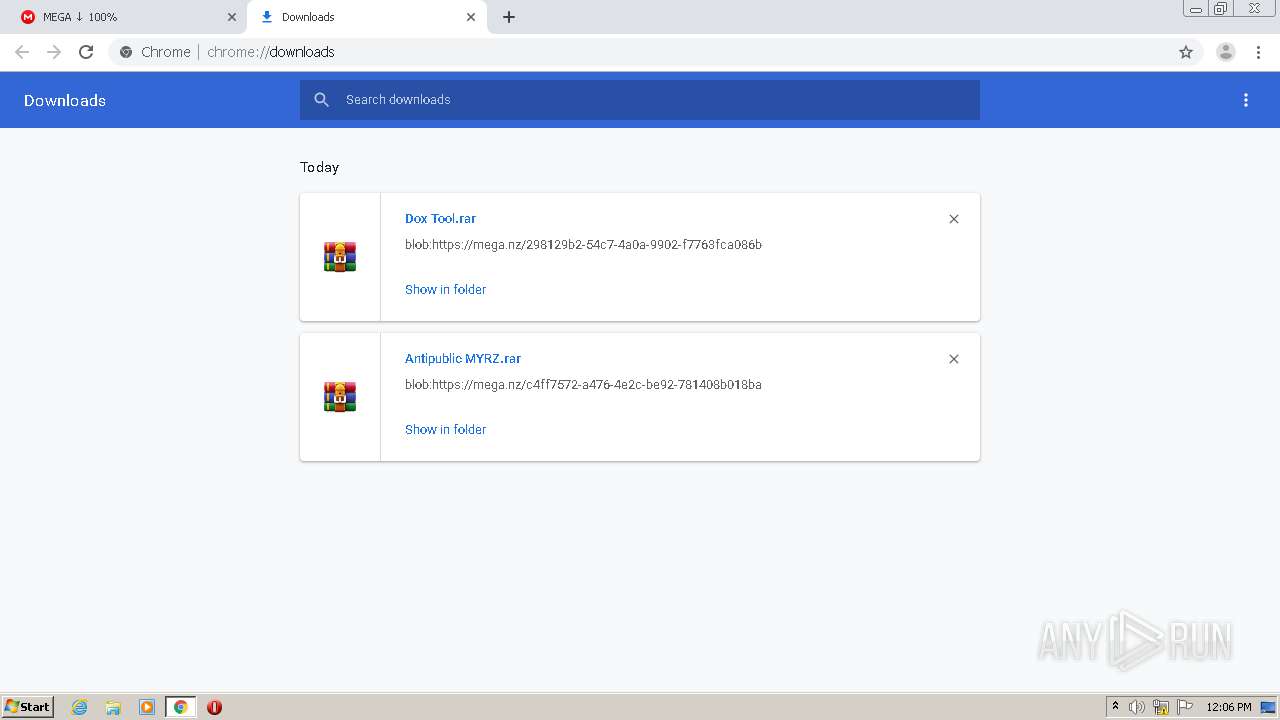
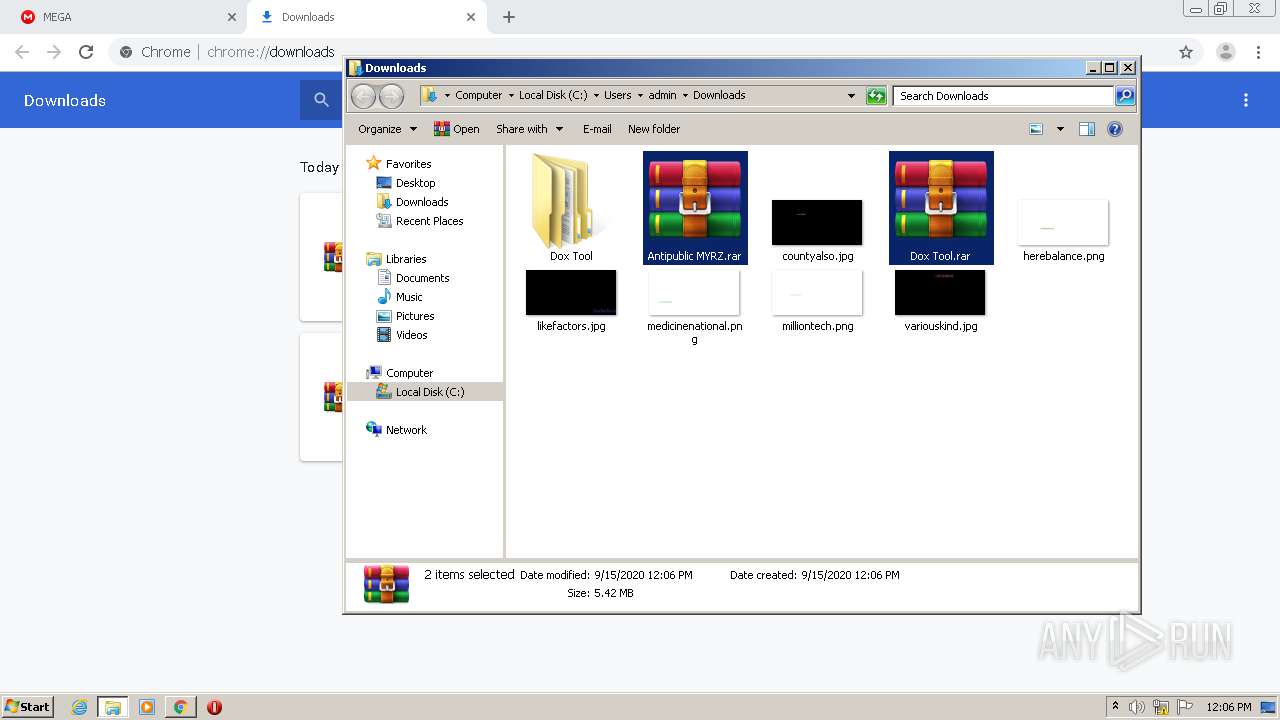
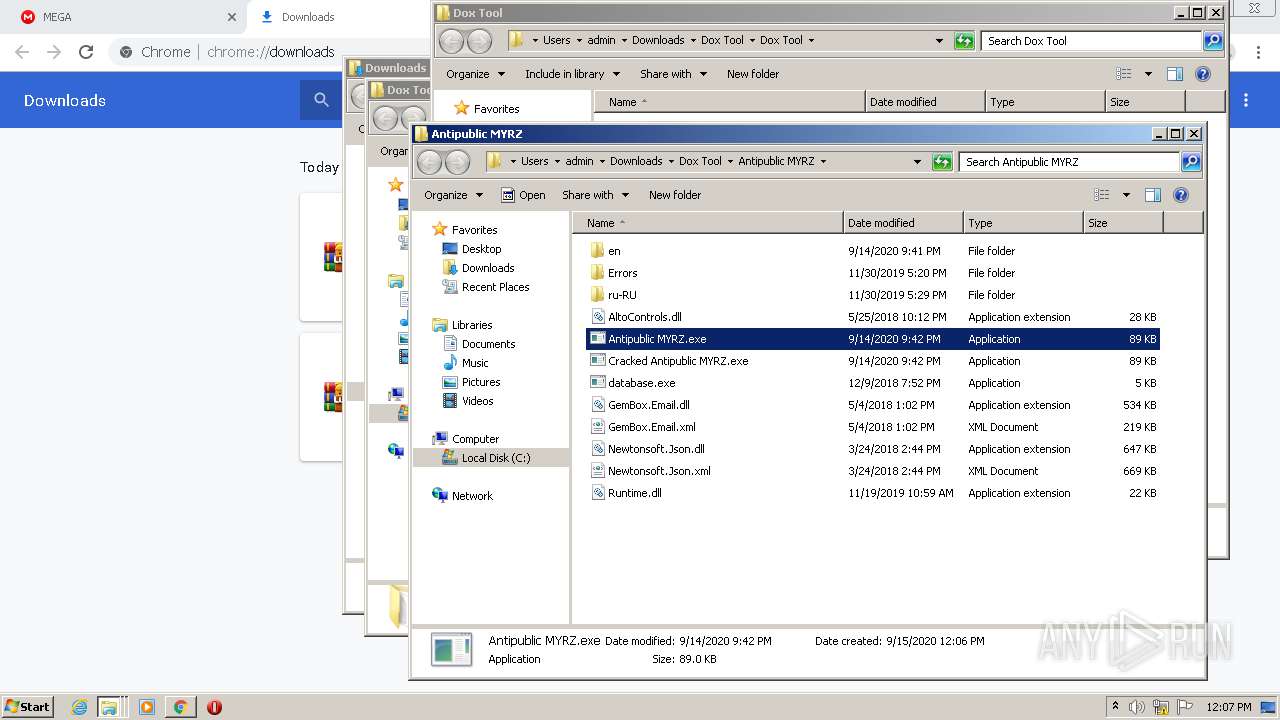
Manual execution by user
- WinRAR.exe (PID: 2744)
- Dox tool v2.exe (PID: 1256)
- Antipublic MYRZ.exe (PID: 2088)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2744)
- check.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
32
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\1B3.tmp\1C3.tmp\1C4.bat "C:\Users\admin\Downloads\Dox Tool\Antipublic MYRZ\Antipublic MYRZ.exe"" | C:\Windows\system32\cmd.exe | — | Antipublic MYRZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2736 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10976772624080682217 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10258067219604190057 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14531574194039159316 --mojo-platform-channel-handle=3908 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Users\admin\Downloads\Dox Tool\Dox Tool\Dox tool v2.exe" | C:\Users\admin\Downloads\Dox Tool\Dox Tool\Dox tool v2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9998904615466346631 --mojo-platform-channel-handle=3884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3029436525500621204 --mojo-platform-channel-handle=2976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Users\admin\AppData\Roaming\ctfmom.exe" | C:\Users\admin\AppData\Roaming\ctfmom.exe | — | check.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: SnakeLab Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8719435621346930127,11627363062051342561,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2942027925621874514 --mojo-platform-channel-handle=3880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 780
Read events
1 671
Write events
104
Delete events
5
Modification events
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13244641546997250 |
Value: 259 | |||
Executable files
51
Suspicious files
45
Text files
165
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6d6fdb76-29e5-4499-bcea-f0003d658a68.tmp | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF26e4aa.TMP | text | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF26e48b.TMP | text | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF26e4f8.TMP | text | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF26e640.TMP | — | |
MD5:— | SHA256:— | |||
| 2832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
53
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2252 | chrome.exe | GET | 200 | 173.194.187.232:80 | http://r3---sn-4g5ednly.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=89.187.165.47&mm=28&mn=sn-4g5ednly&ms=nvh&mt=1600167797&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 834 Kb | whitelisted |
2252 | chrome.exe | GET | 302 | 216.58.212.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2252 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 31.216.148.10:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
2252 | chrome.exe | 31.216.147.133:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
2252 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
2252 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 89.44.169.132:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
2252 | chrome.exe | 89.44.168.103:443 | gfs270n387.userstorage.mega.co.nz | Datacenter Luxembourg S.A. | LU | suspicious |
2252 | chrome.exe | 185.206.26.46:443 | gfs208n136.userstorage.mega.co.nz | — | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
www.google.com |
| malicious |
g.api.mega.co.nz |
| shared |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |