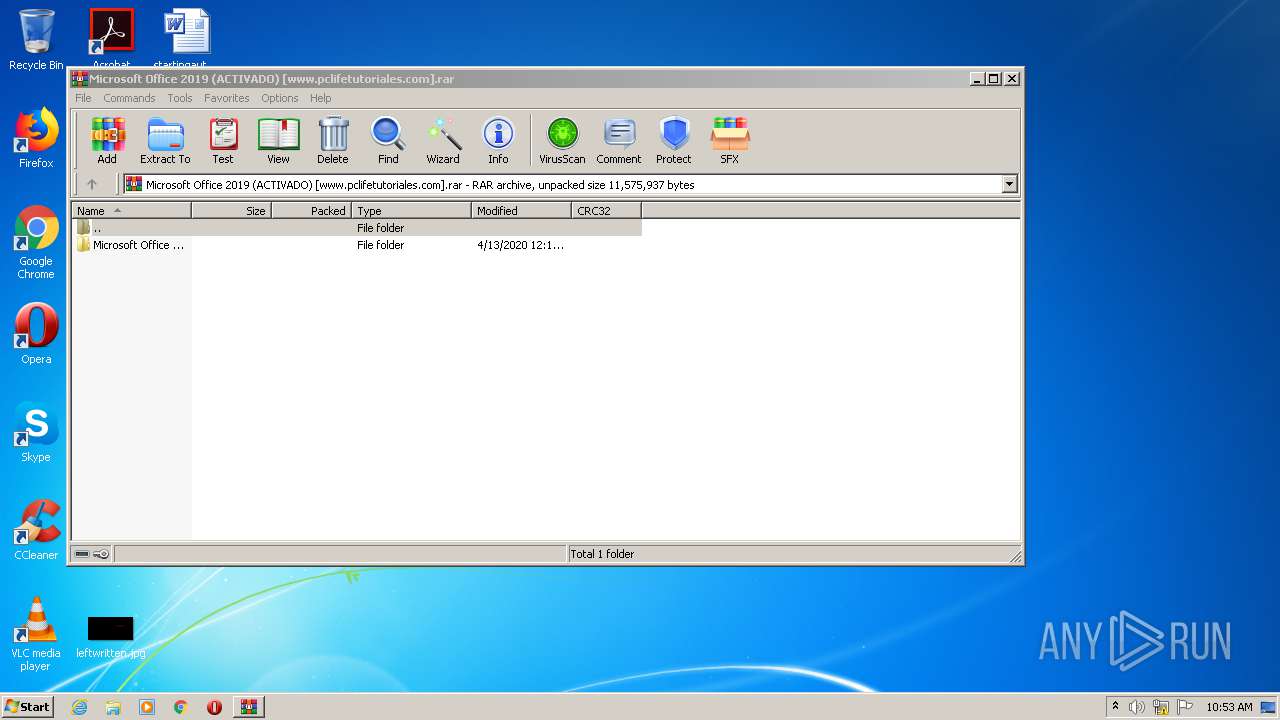
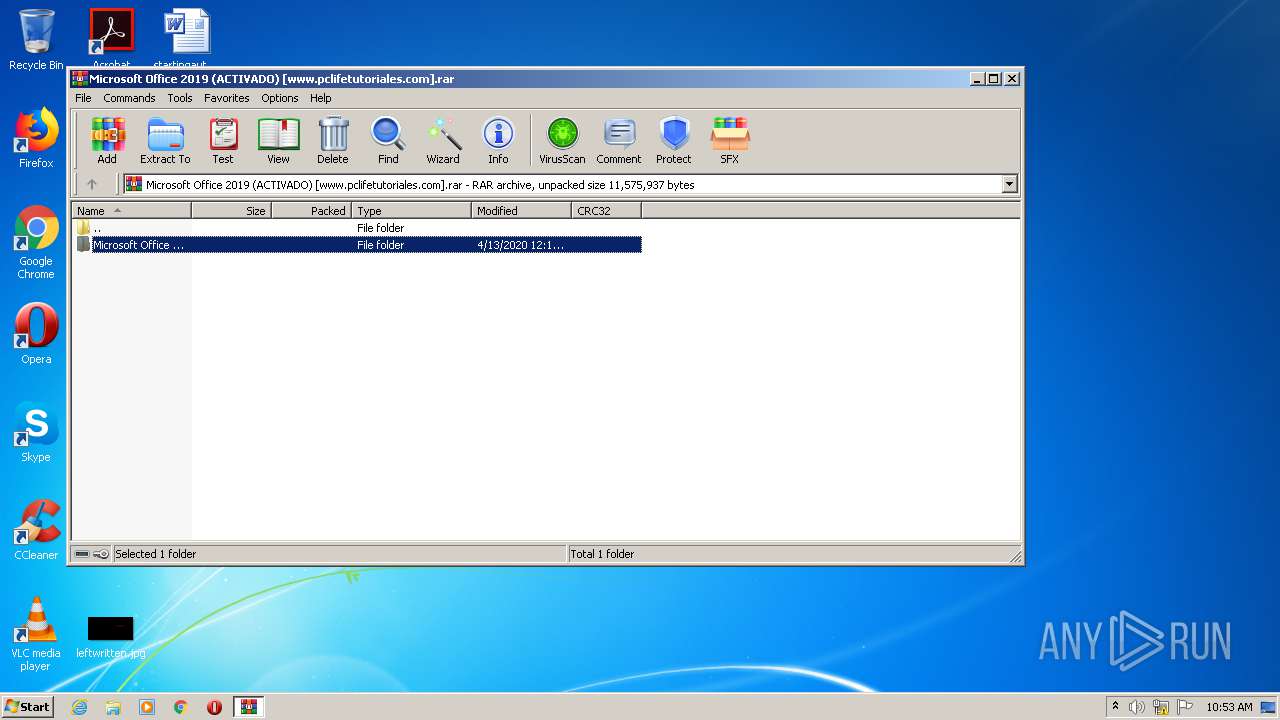
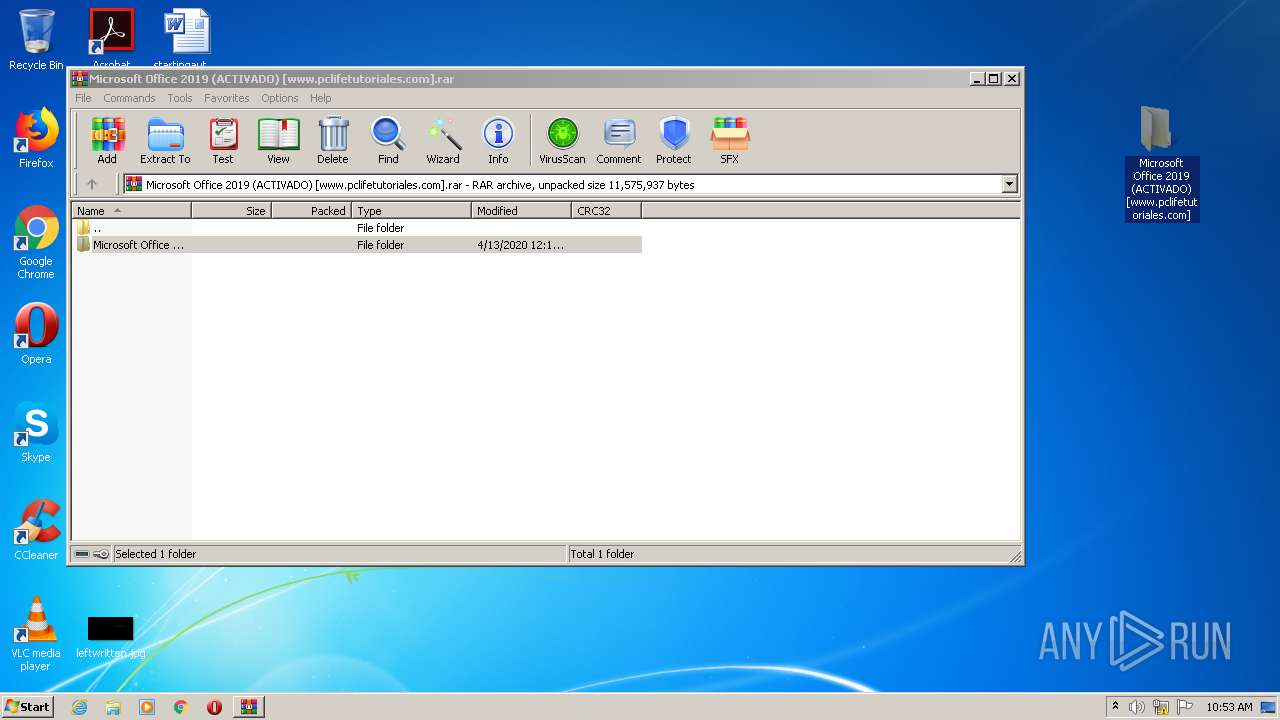
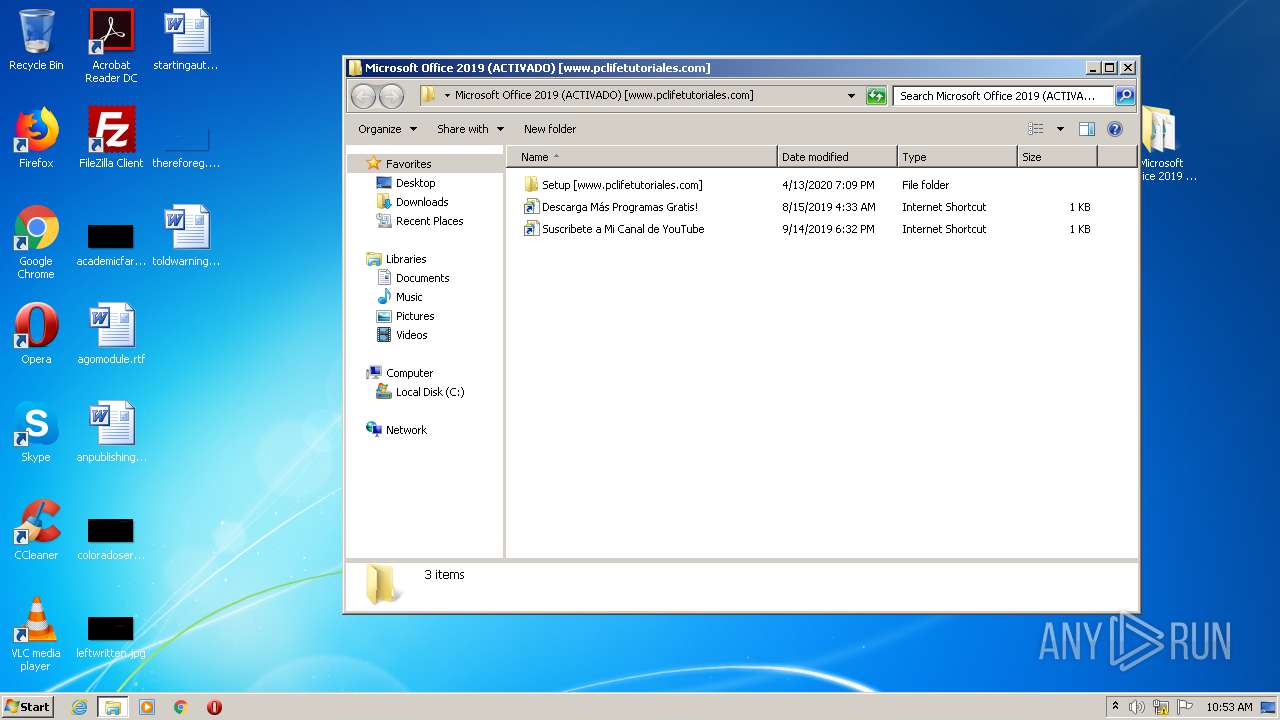
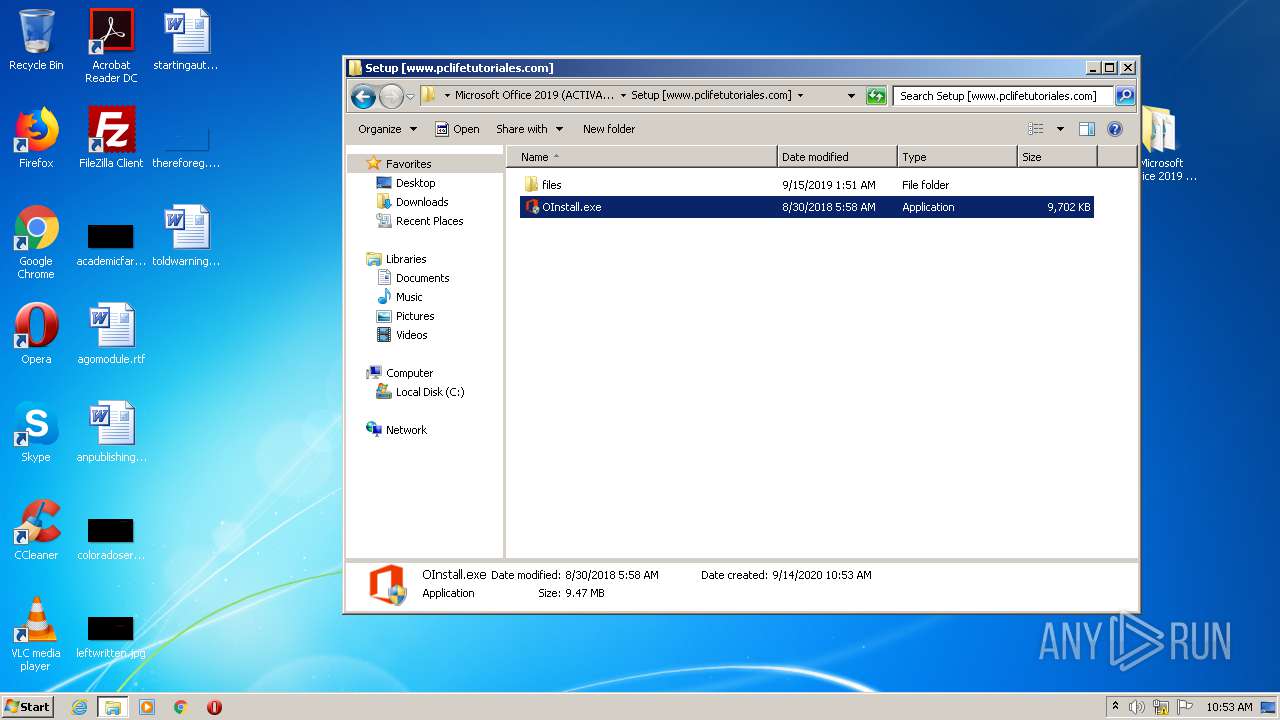
| File name: | Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com].rar |
| Full analysis: | https://app.any.run/tasks/c192661e-6c3e-4bcd-ad42-6094a8442a37 |
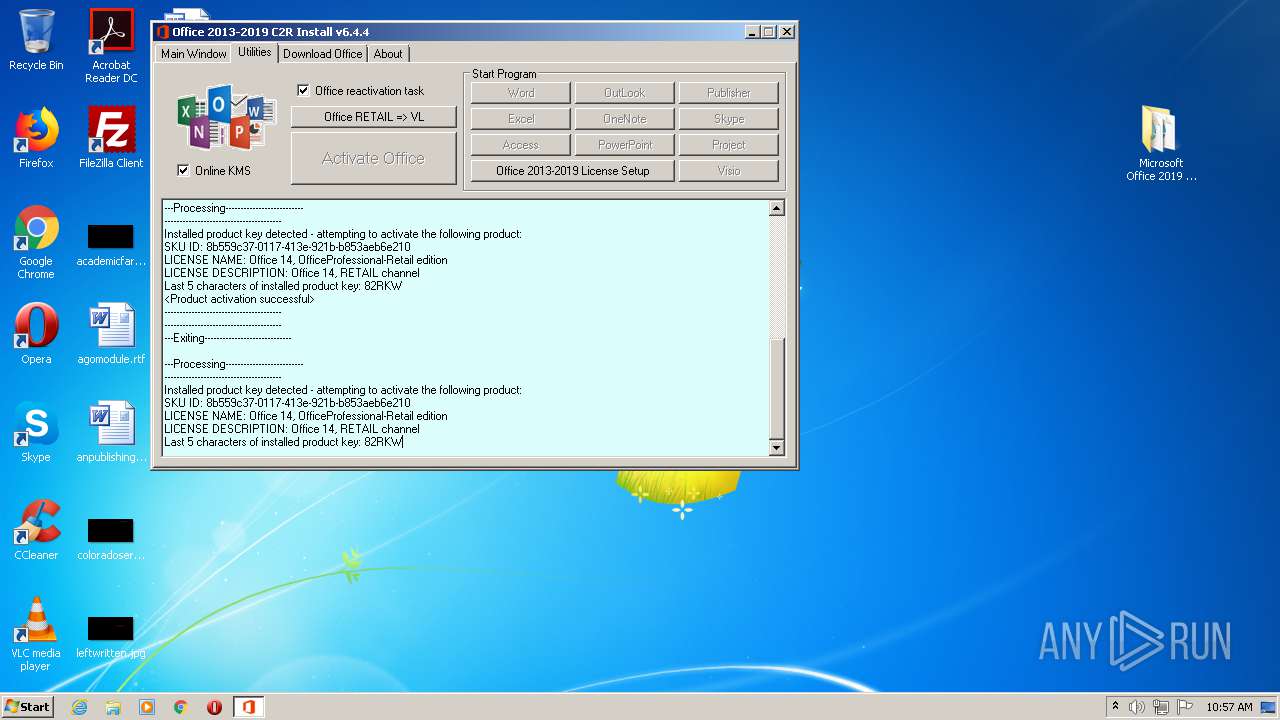
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2020, 09:53:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | A44C93BFA1A0E7BA8627467C0F3055B9 |
| SHA1: | FA6C373F08320EB4F3ABB3797DE75ECED5316933 |
| SHA256: | 45165AEDC12A322E1A4D35FAA7077BA2299E69D20392E0C36526F5F892A20ACE |
| SSDEEP: | 196608:034ixyoKk8oL4MppgtmZfbh1h4Czrv5gY6twXsqmJ9VPJDOi+Gx4XBophXaC6jPg:0Fxyod8oL4MpmK1hfHvOY6tI8tJNP4Xu |
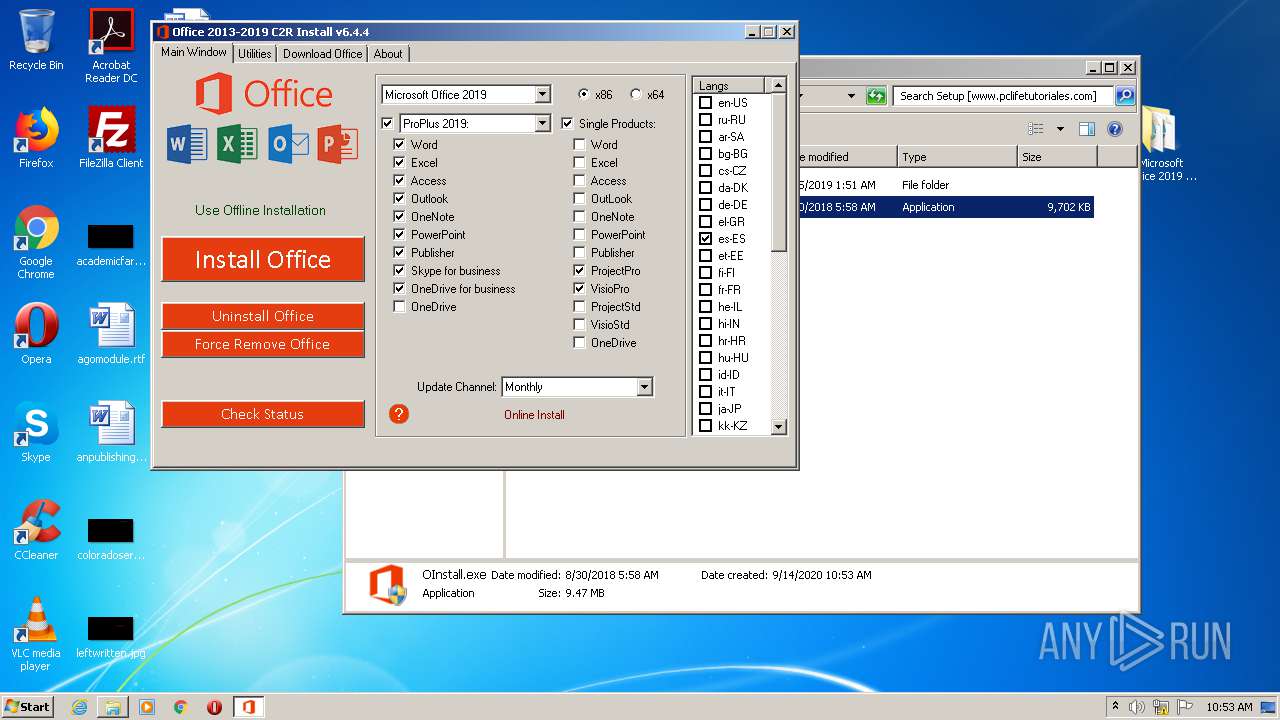
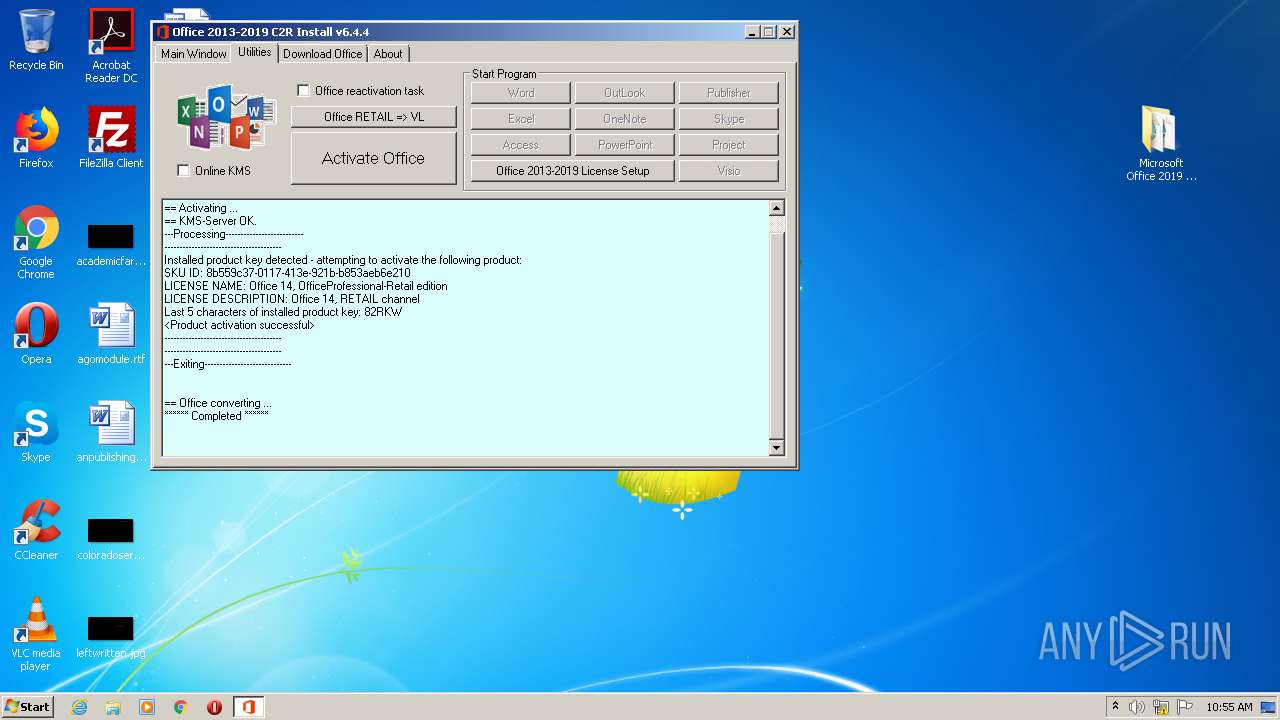
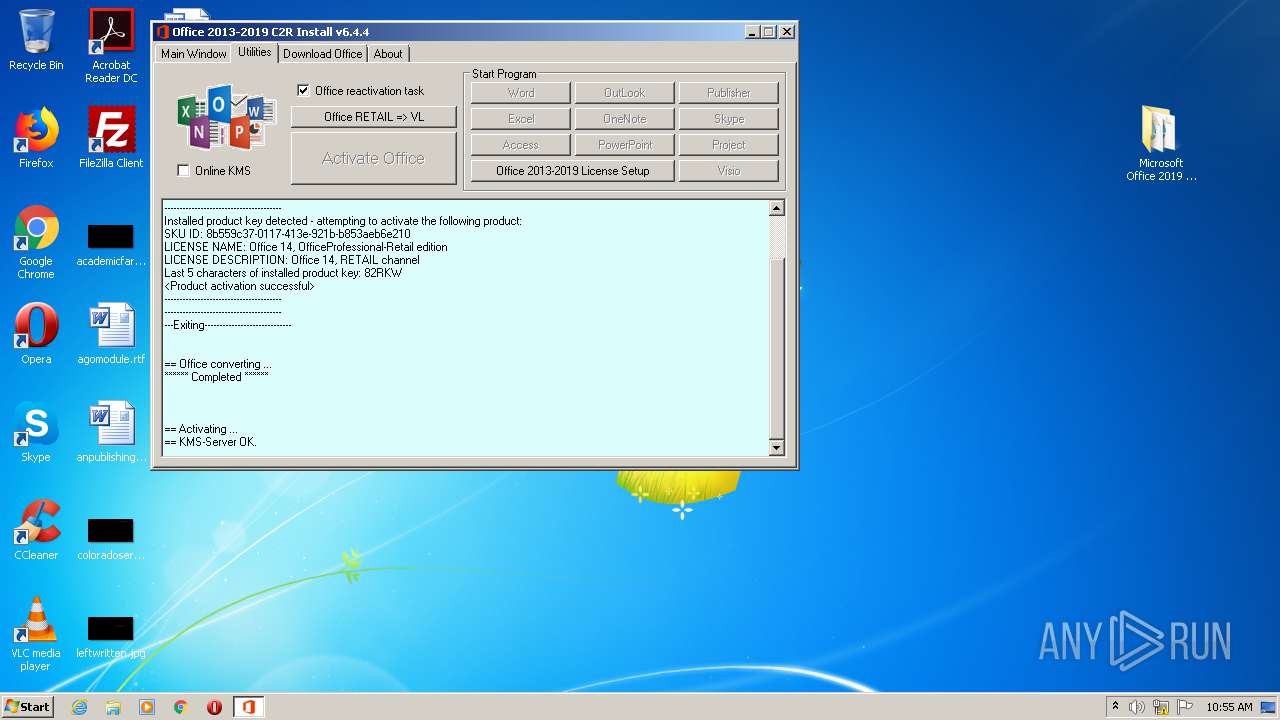
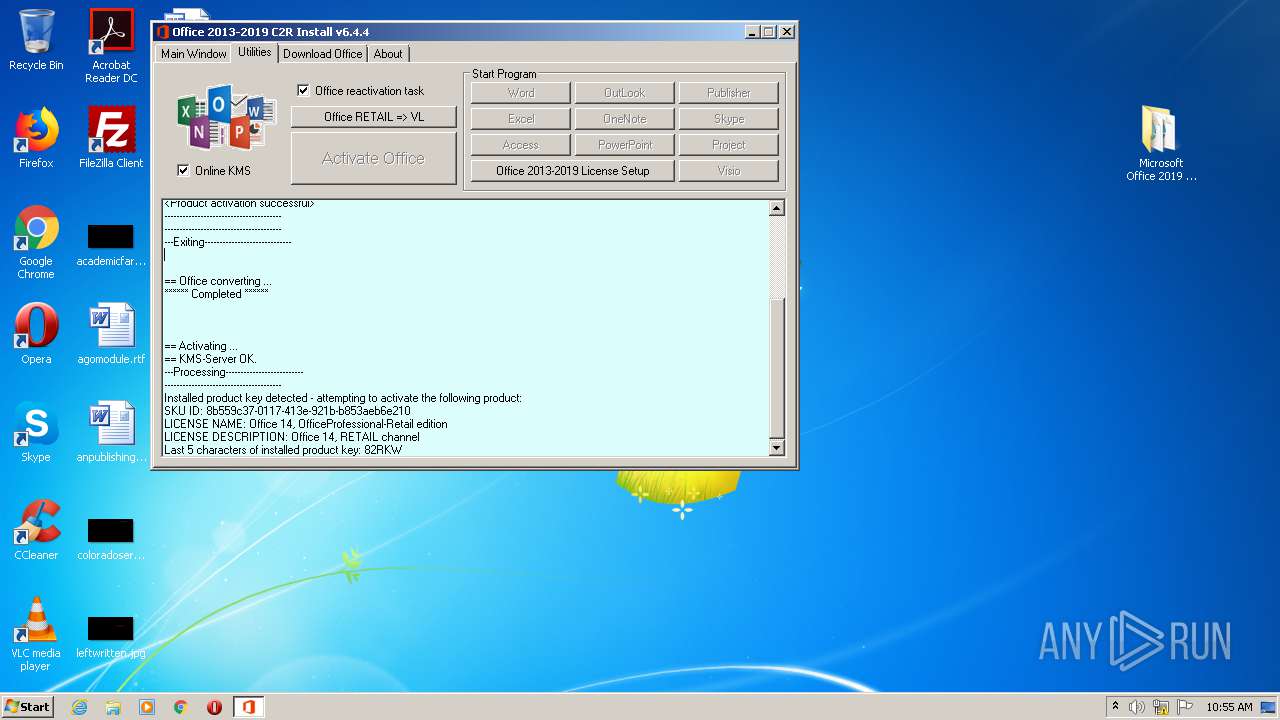
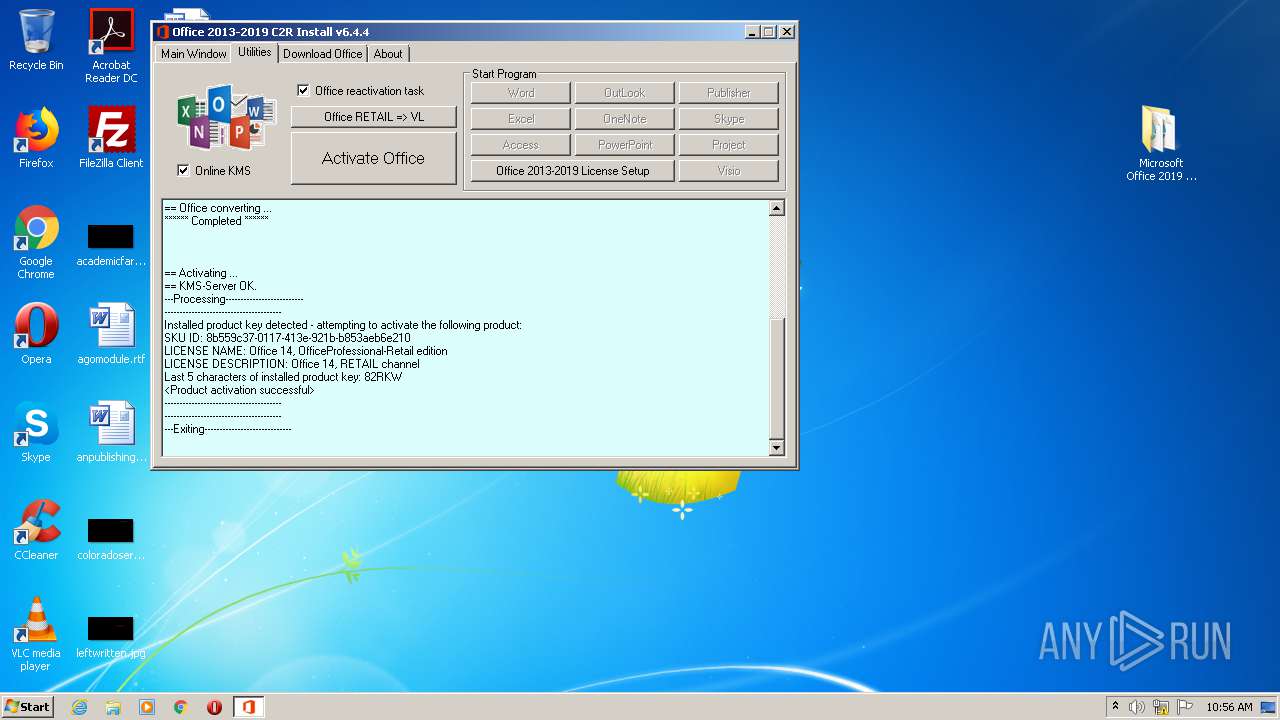
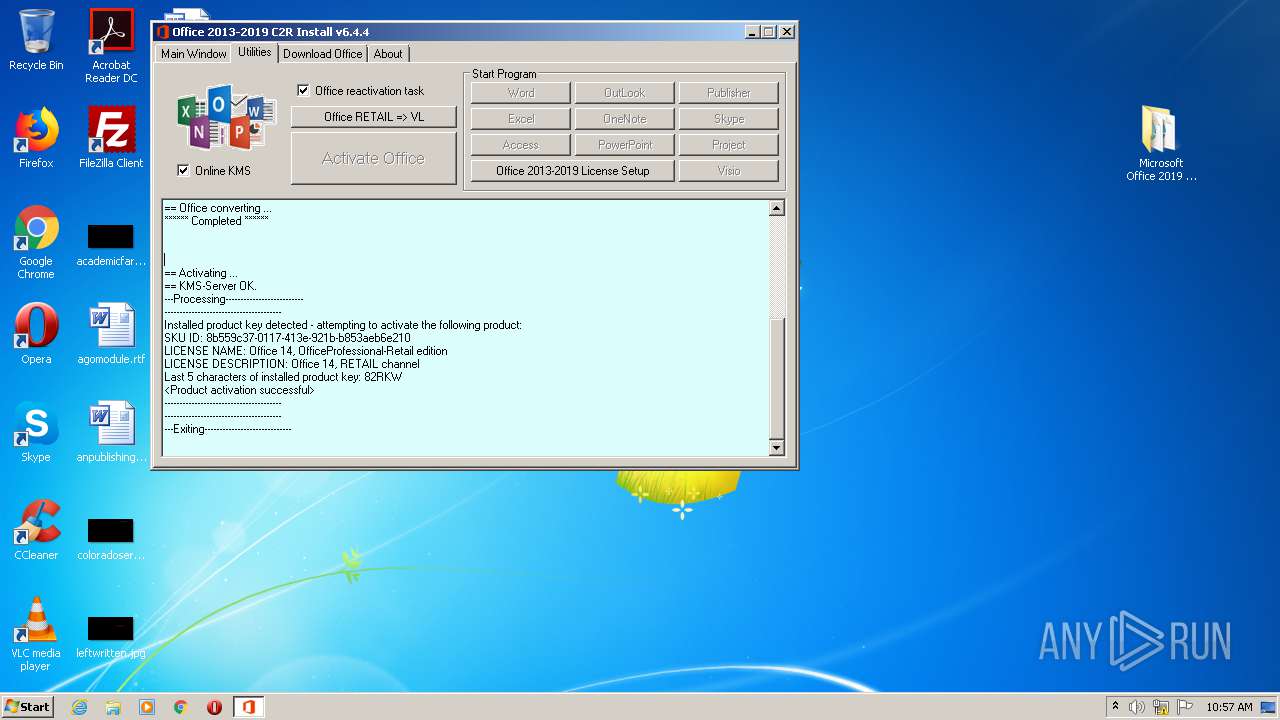
MALICIOUS
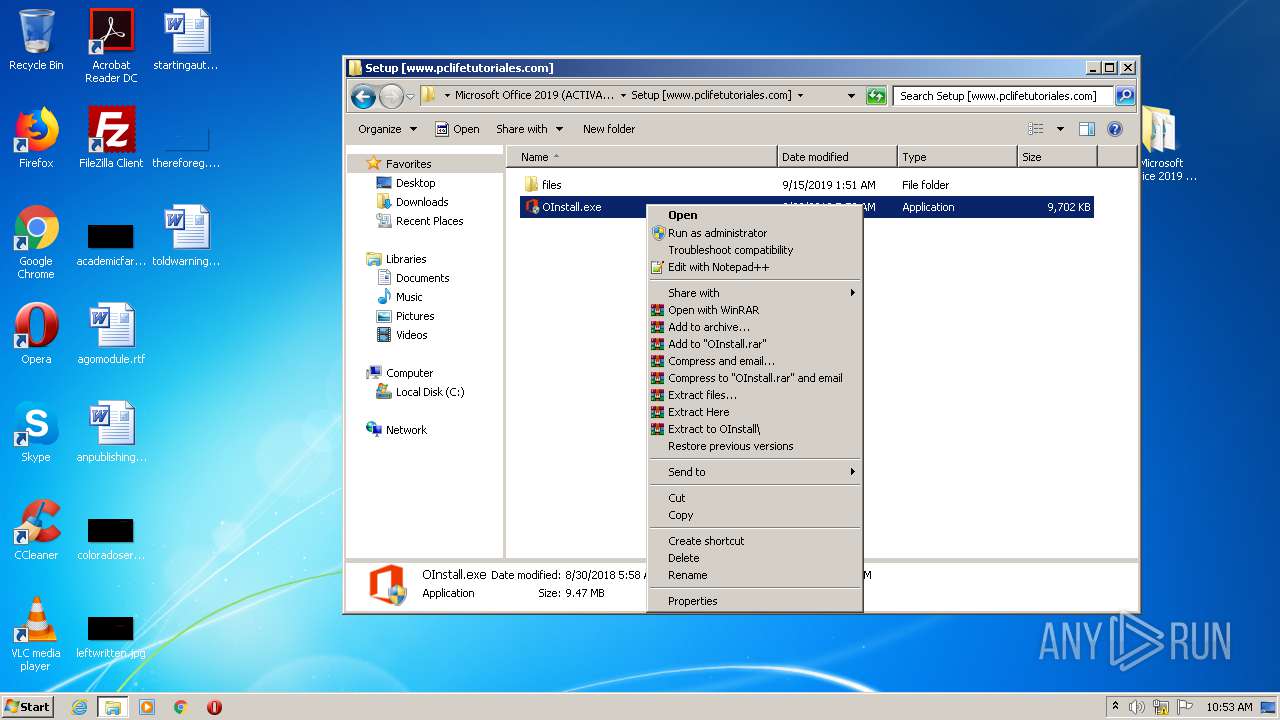
Application was dropped or rewritten from another process
- kmss.dat (PID: 2336)
- test.dat (PID: 2844)
- KMSS.exe (PID: 2200)
- test.dat (PID: 2284)
- OInstall.exe (PID: 2812)
- OInstall.exe (PID: 1808)
- test.dat (PID: 3176)
- KMSS.exe (PID: 868)
- test.dat (PID: 3324)
- test.dat (PID: 1268)
- test.dat (PID: 3572)
- test.dat (PID: 956)
- test.dat (PID: 2400)
- kmss.dat (PID: 892)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2168)
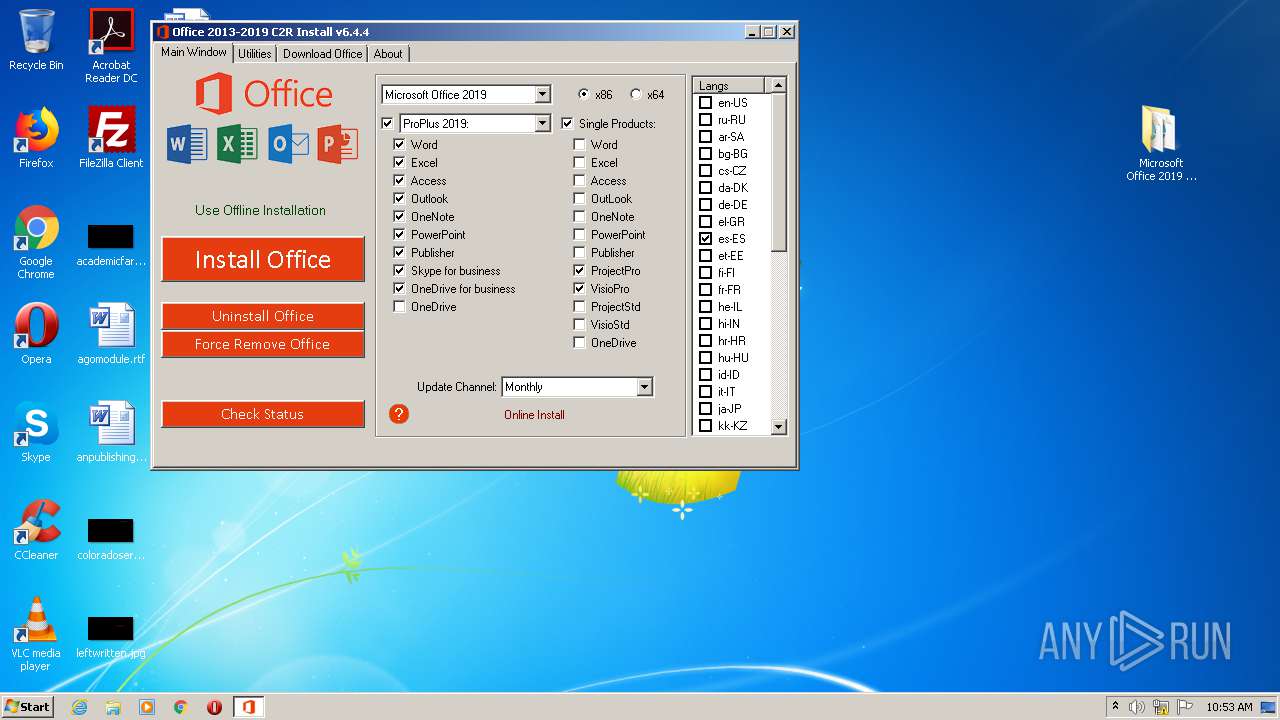
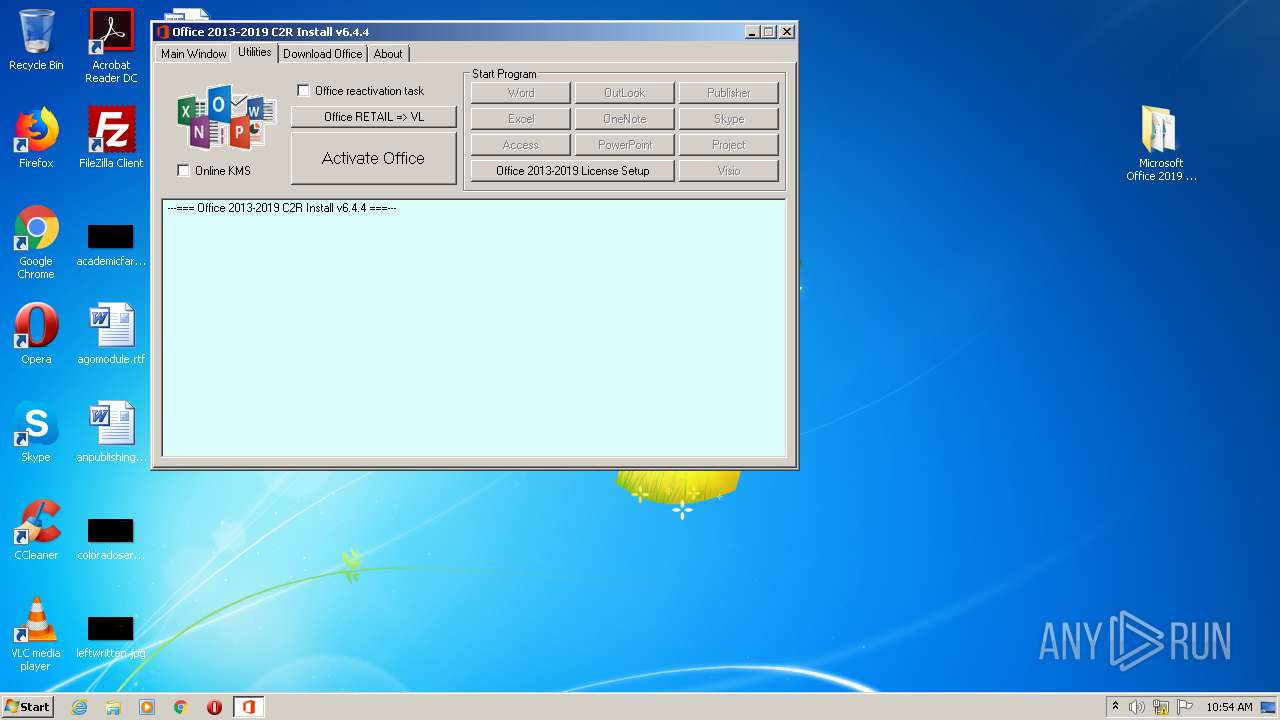
Starts NET.EXE for service management
- cmd.exe (PID: 2788)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 2444)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2964)
- cmd.exe (PID: 3828)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2512)
- schtasks.exe (PID: 1024)
- schtasks.exe (PID: 1392)
SUSPICIOUS
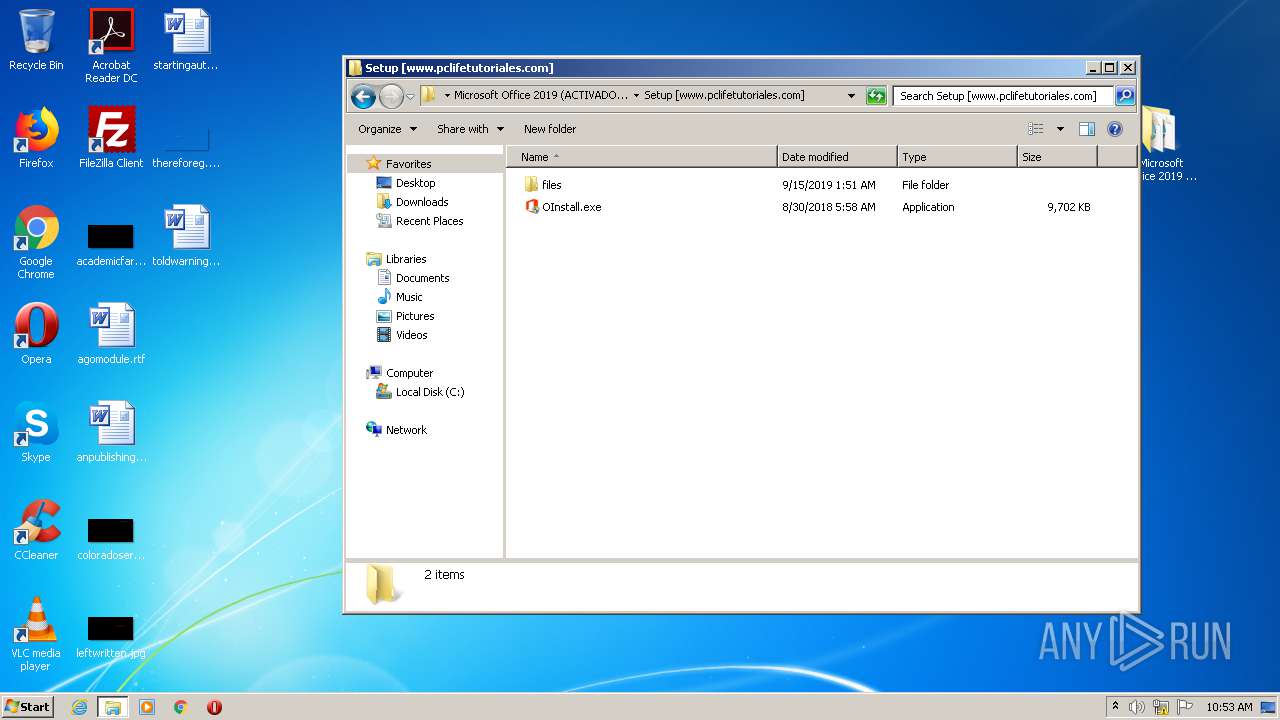
Executable content was dropped or overwritten
- OInstall.exe (PID: 2812)
- kmss.dat (PID: 2336)
- kmss.dat (PID: 892)
Starts application with an unusual extension
- cmd.exe (PID: 1908)
- cmd.exe (PID: 1124)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 1520)
- cmd.exe (PID: 1296)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 2308)
- cmd.exe (PID: 2952)
- cmd.exe (PID: 3684)
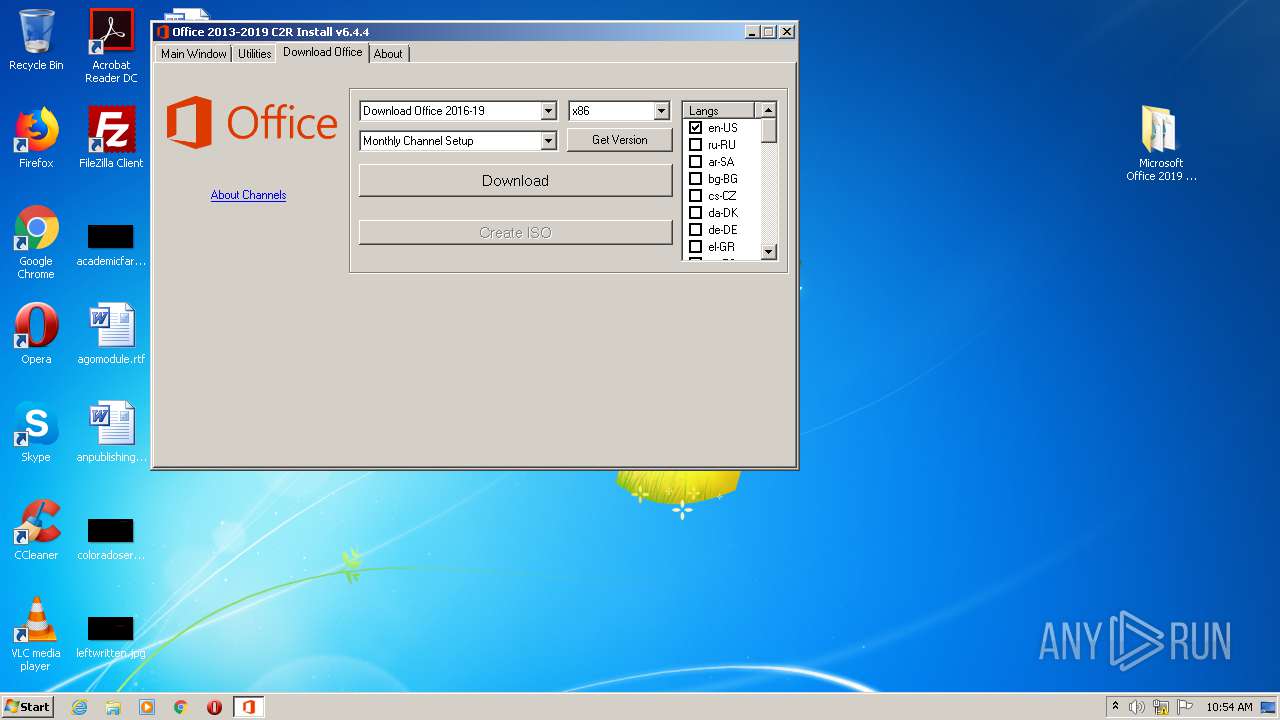
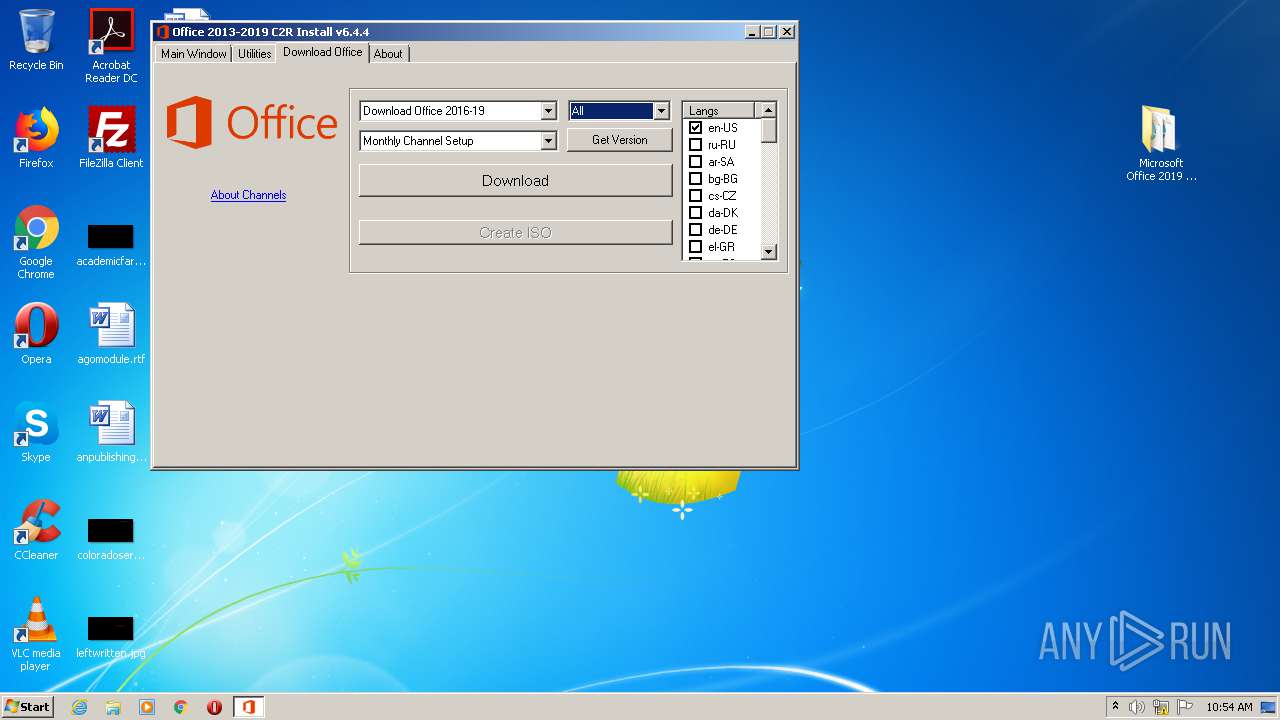
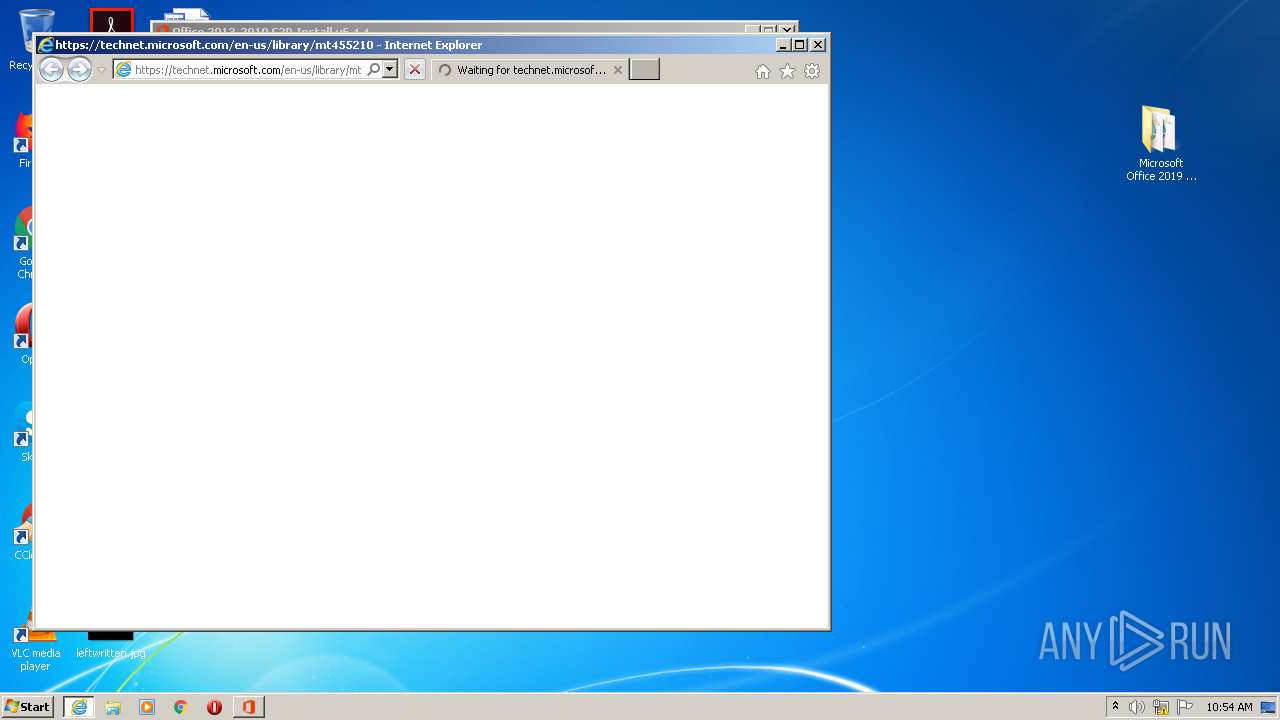
Starts Internet Explorer
- OInstall.exe (PID: 2812)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 2812)
Uses TASKKILL.EXE to kill process
- OInstall.exe (PID: 2812)
- cmd.exe (PID: 908)
- cmd.exe (PID: 3656)
- cmd.exe (PID: 2840)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3600)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 1268)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 1856)
Creates files in the Windows directory
- OInstall.exe (PID: 2812)
- cmd.exe (PID: 3584)
Executes scripts
- cmd.exe (PID: 3768)
- cmd.exe (PID: 584)
- cmd.exe (PID: 2572)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 3344)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 612)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 3912)
- cmd.exe (PID: 276)
- cmd.exe (PID: 2416)
Removes files from Windows directory
- OInstall.exe (PID: 2812)
INFO
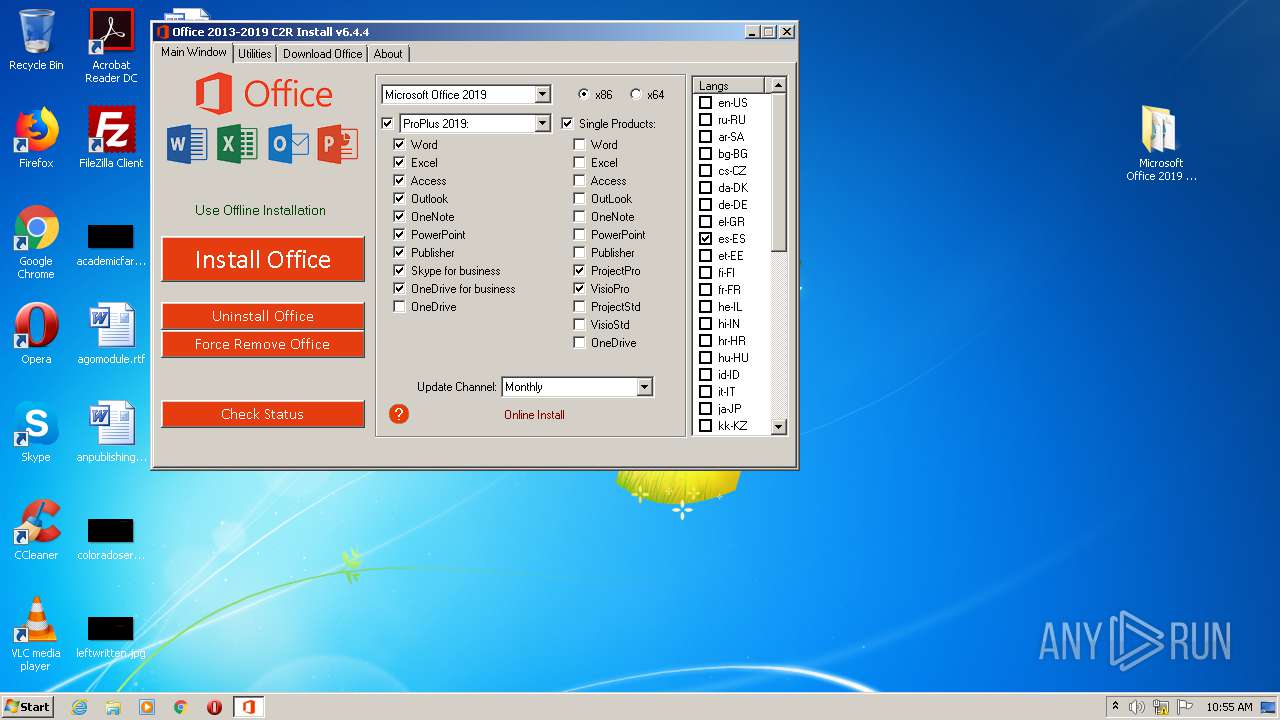
Manual execution by user
- OInstall.exe (PID: 2812)
- OInstall.exe (PID: 1808)
Reads Internet Cache Settings
- iexplore.exe (PID: 4024)
- iexplore.exe (PID: 1716)
Creates files in the user directory
- iexplore.exe (PID: 1716)
Reads internet explorer settings
- iexplore.exe (PID: 1716)
Changes internet zones settings
- iexplore.exe (PID: 4024)
Application launched itself
- iexplore.exe (PID: 4024)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1716)
Dropped object may contain Bitcoin addresses
- kmss.dat (PID: 2336)
- iexplore.exe (PID: 4024)
- kmss.dat (PID: 892)
- iexplore.exe (PID: 1716)
Reads settings of System Certificates
- iexplore.exe (PID: 4024)
Changes settings of System certificates
- iexplore.exe (PID: 1716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
194
Monitored processes
96
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /act | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | taskkill.exe /t /f /IM osppsvc.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /sethst:127.0.0.2 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 612 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /sethst:127.0.0.2 | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 684 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /dstatusall | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 868 | "C:\Users\admin\Desktop\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\bin\KMSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort | C:\Users\admin\Desktop\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\bin\KMSS.exe | — | OInstall.exe | |||||||||||
User: admin Company: MSFree Inc. Integrity Level: HIGH Description: KMS emulator by Ratiborus. Exit code: 1 Version: 2.0.5.0 Modules
| |||||||||||||||
| 892 | kmss.dat -y -pkmsauto | C:\Users\admin\Desktop\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\kmss.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 908 | "C:\Windows\System32\cmd.exe" /D /c taskkill.exe /t /f /IM osppsvc.exe | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | C:\Windows\Temp\test.dat kms789.com:1688 -l Windows -6 | C:\Windows\Temp\test.dat | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 868
Read events
2 477
Write events
386
Delete events
5
Modification events
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com].rar | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (1500) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
18
Suspicious files
24
Text files
23
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Descarga Más Programas Gratis!.url | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\Configure.xml | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\Uninstall.xml | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\x64\cleanospp.exe | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\x64\msvcr100.dll | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\x86\cleanospp.exe | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\files\x86\msvcr100.dll | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Setup [www.pclifetutoriales.com]\OInstall.exe | — | |
MD5:— | SHA256:— | |||
| 1500 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1500.5696\Microsoft Office 2019 (ACTIVADO) [www.pclifetutoriales.com]\Suscribete a Mi Canal de YouTube.url | — | |
MD5:— | SHA256:— | |||
| 1716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabBB65.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
36
DNS requests
29
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
760 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | NL | — | — | whitelisted |
2884 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | NL | — | — | whitelisted |
760 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | NL | — | — | whitelisted |
760 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | NL | — | — | whitelisted |
760 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120750 | NL | — | — | whitelisted |
760 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | NL | — | — | whitelisted |
2884 | wmiprvse.exe | POST | 302 | 104.108.39.131:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | NL | — | — | whitelisted |
1716 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
1716 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
1716 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1716 | iexplore.exe | 104.109.95.169:443 | technet.microsoft.com | Akamai International B.V. | NL | suspicious |
1716 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1716 | iexplore.exe | 104.109.90.99:443 | support.office.com | Akamai International B.V. | NL | unknown |
1716 | iexplore.exe | 184.30.215.136:443 | docs.microsoft.com | Akamai International B.V. | NL | suspicious |
1716 | iexplore.exe | 23.210.249.93:443 | c.s-microsoft.com | Akamai International B.V. | NL | whitelisted |
1716 | iexplore.exe | 23.210.248.233:443 | uhf.microsoft.com | Akamai International B.V. | NL | whitelisted |
760 | wmiprvse.exe | 104.108.39.131:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
1716 | iexplore.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
3176 | test.dat | 185.86.180.36:1688 | kms.digiboy.ir | Sindad Netwok Technology Ltd. | IR | unknown |
3176 | test.dat | 162.223.90.90:1688 | kms.digiboy.ir | ColoUp | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
technet.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
support.office.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
docs.microsoft.com |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
uhf.microsoft.com |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |