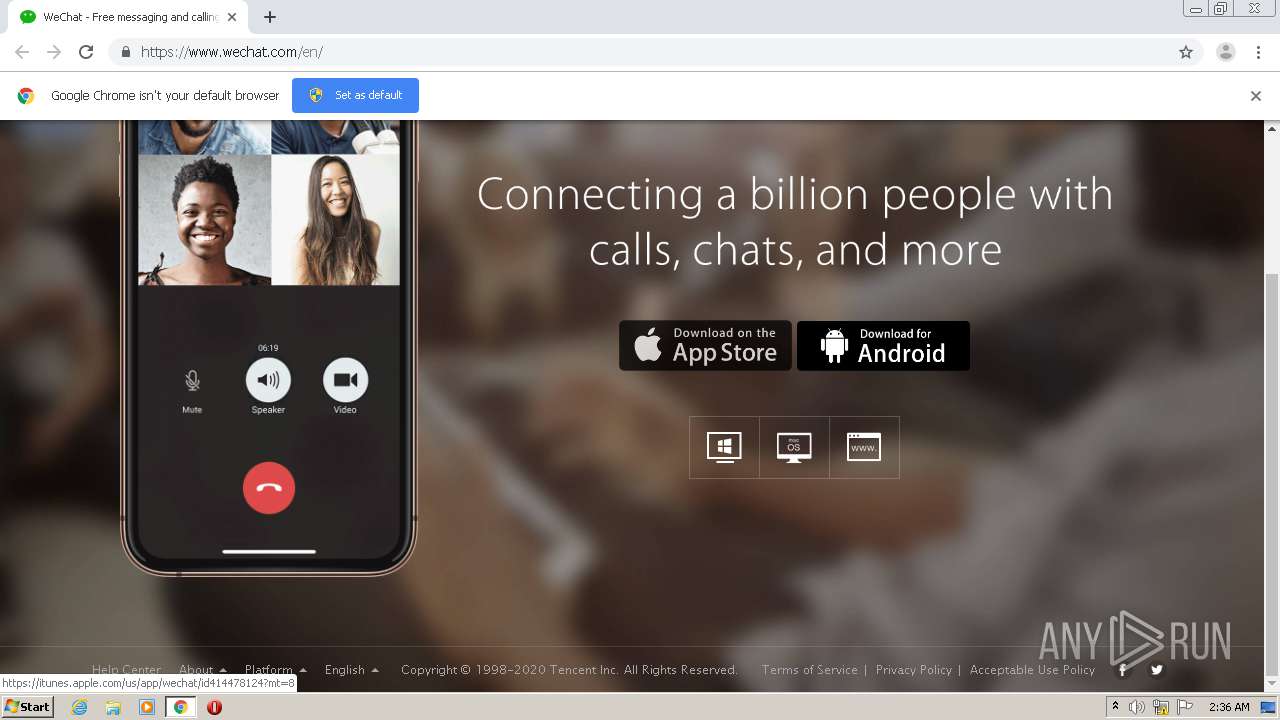
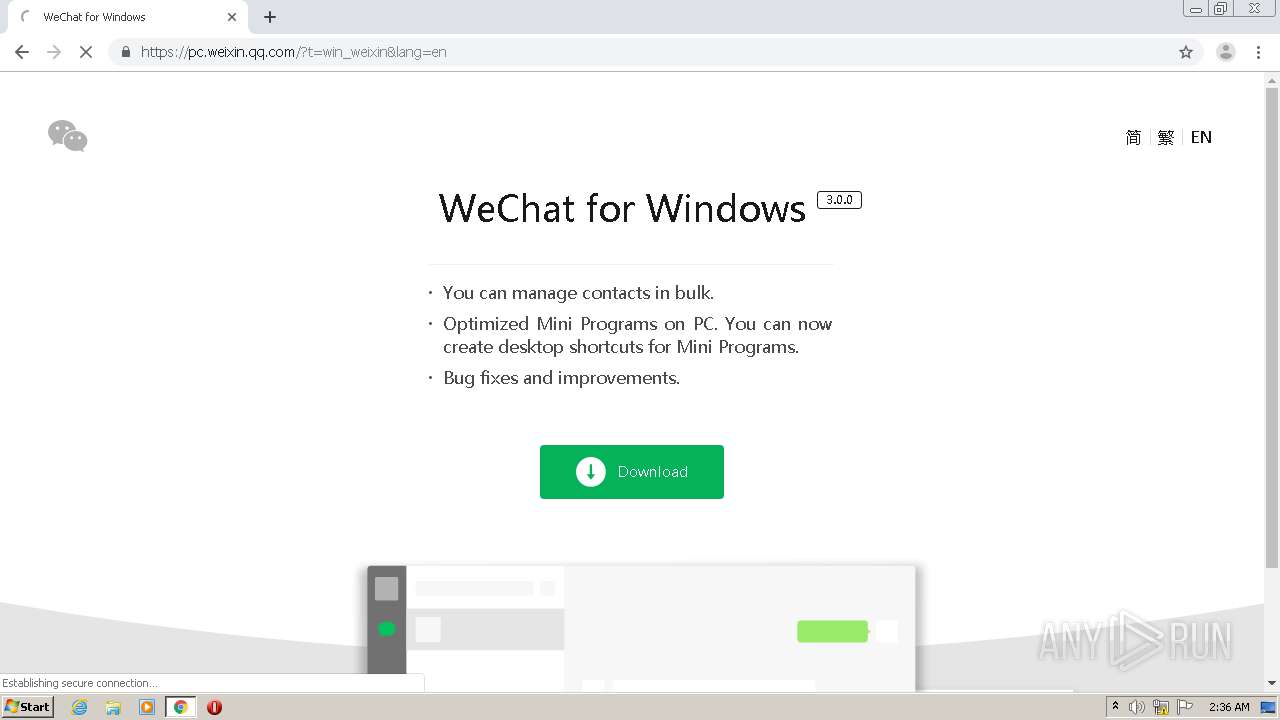
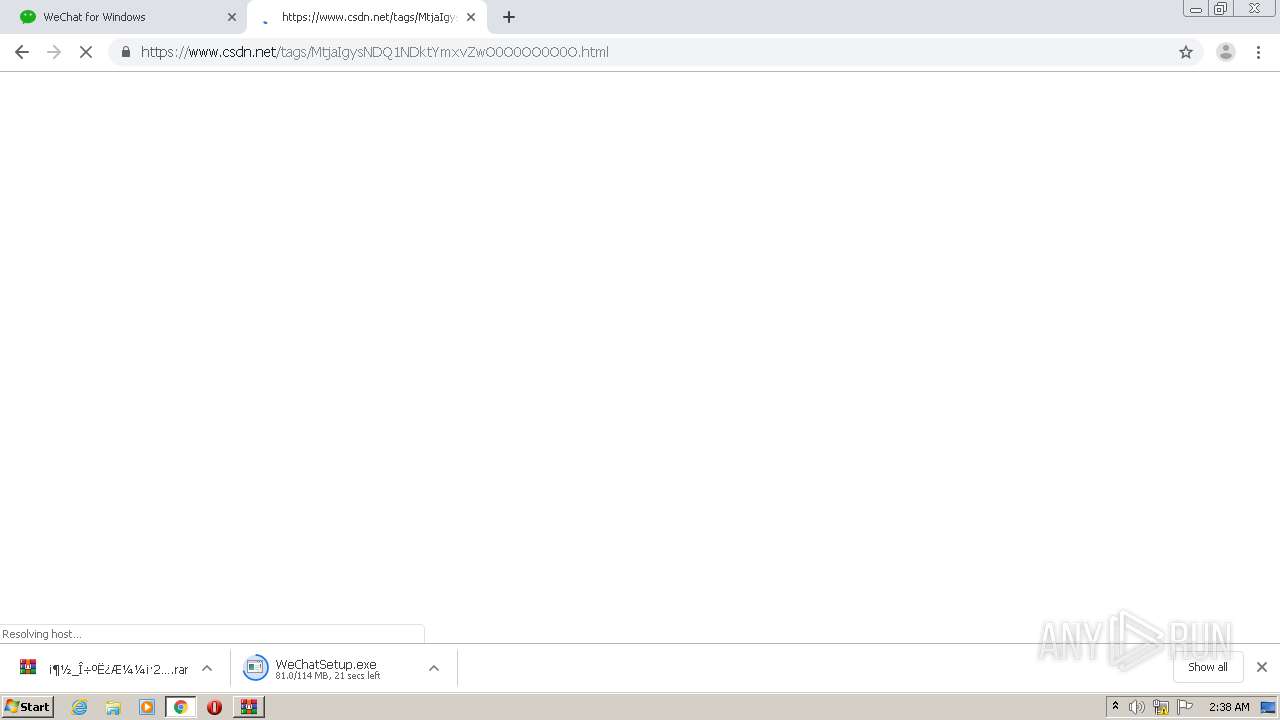
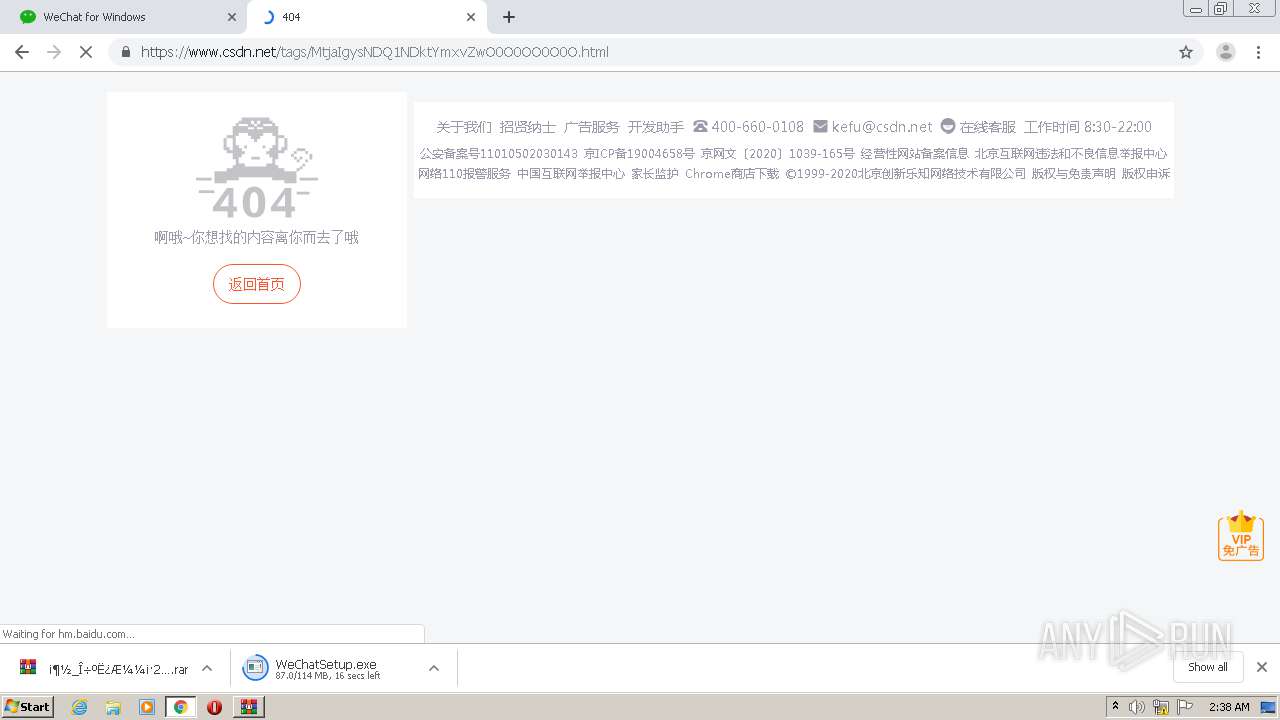
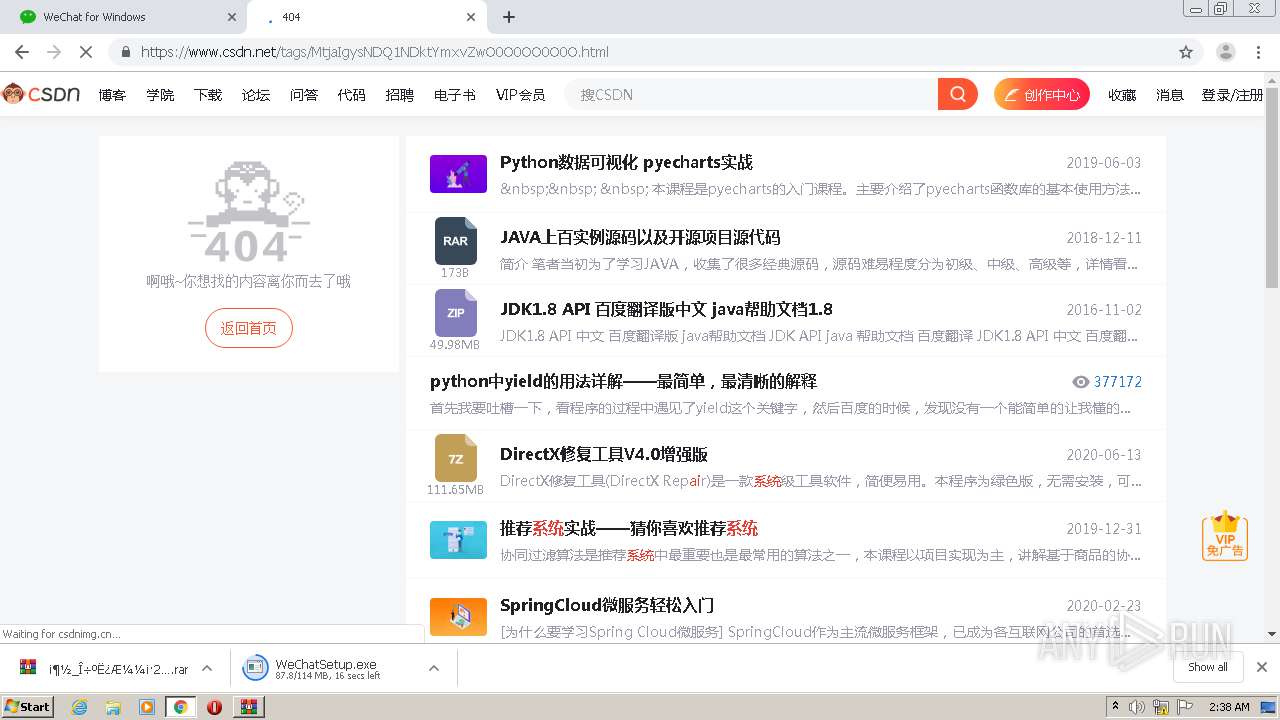
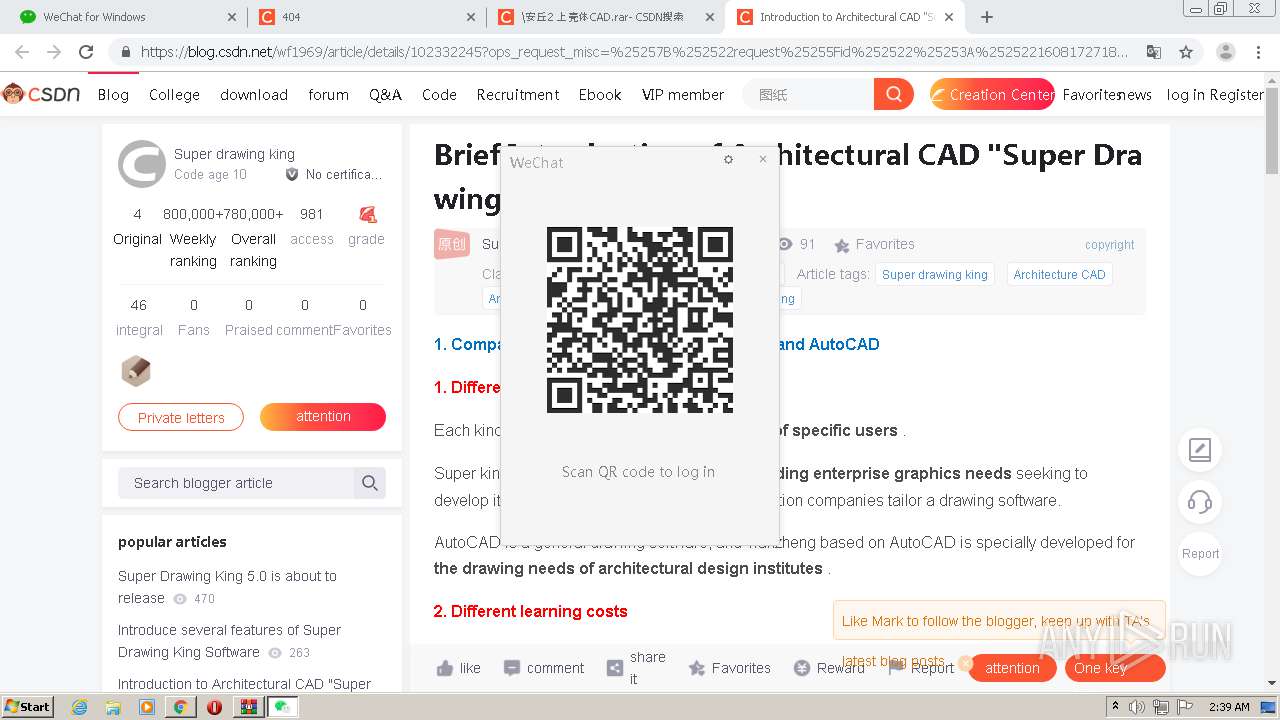
| URL: | https://www.wechat.com/en/ |
| Full analysis: | https://app.any.run/tasks/9bf50f0f-93c3-4ed0-b730-f7c969b527ab |
| Verdict: | Malicious activity |
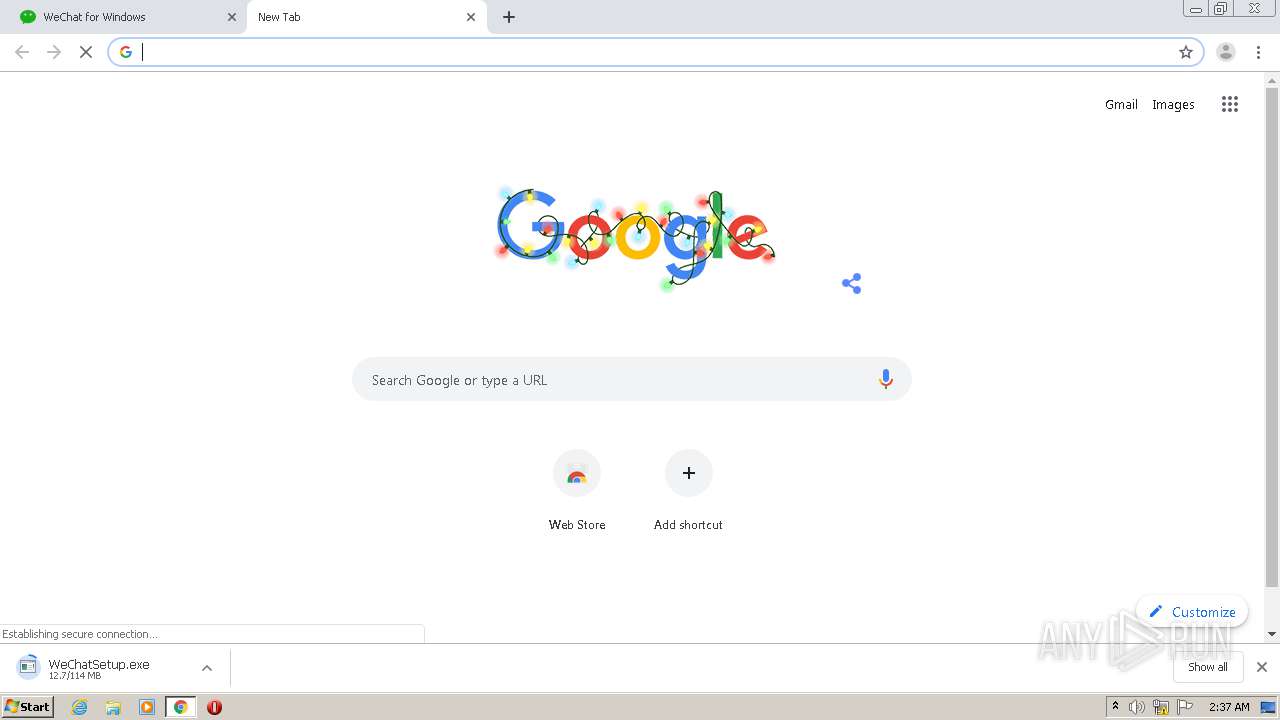
| Analysis date: | December 17, 2020, 02:36:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 89E94BE5399BA4876777E1AC69B690B8 |
| SHA1: | 7959B2FBFDB69CA9AE7900AF21084E9C893EA853 |
| SHA256: | 450304D57C81596AC8646A998B49369F0B589152C14593E31F8CF2F6066F26AD |
| SSDEEP: | 3:N8DSL5KKFn:2OL5KKFn |
MALICIOUS
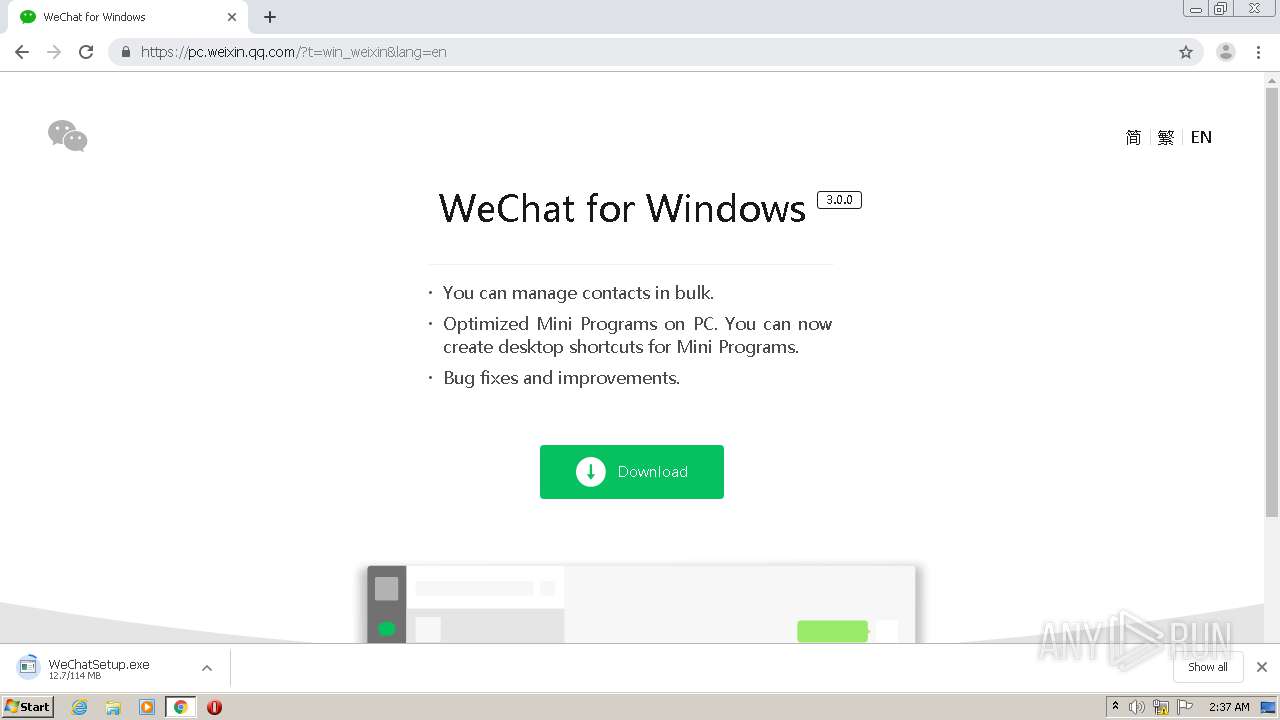
Loads dropped or rewritten executable
- WeChatSetup.exe (PID: 2992)
- WeChat.exe (PID: 2220)
Application was dropped or rewritten from another process
- WeChatSetup.exe (PID: 3488)
- WeChatSetup.exe (PID: 2992)
- WeChat.exe (PID: 2220)
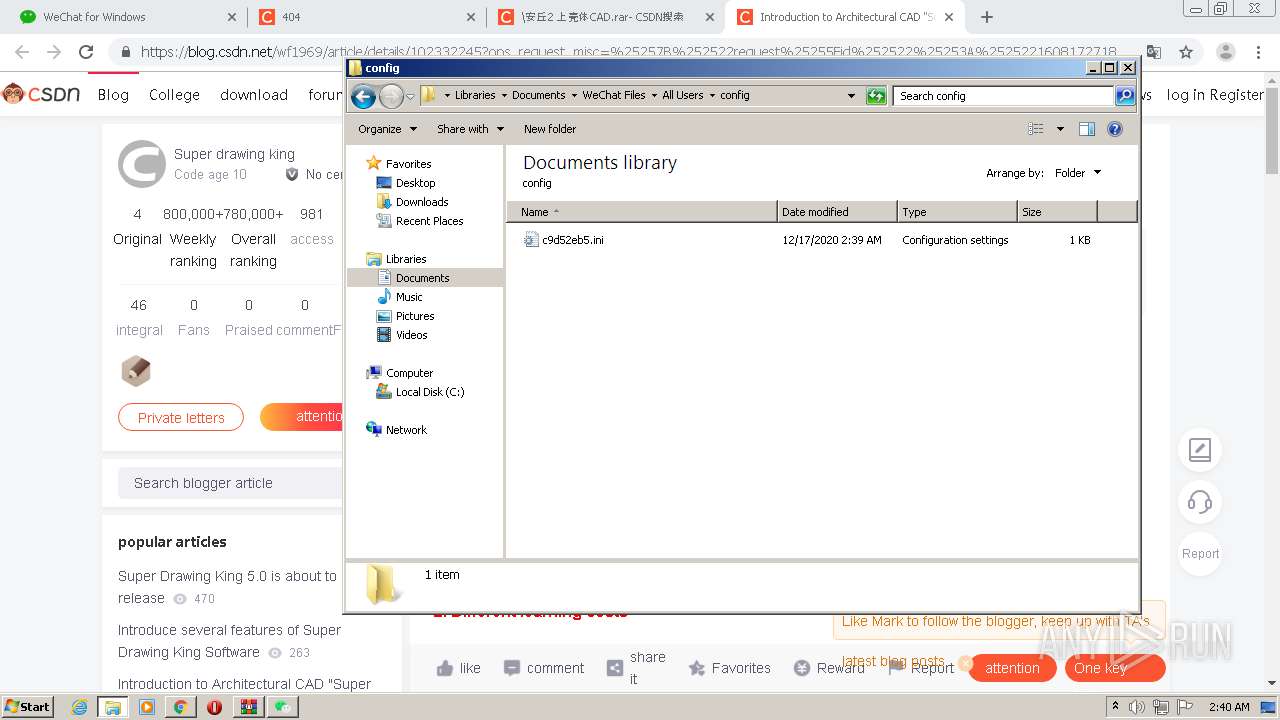
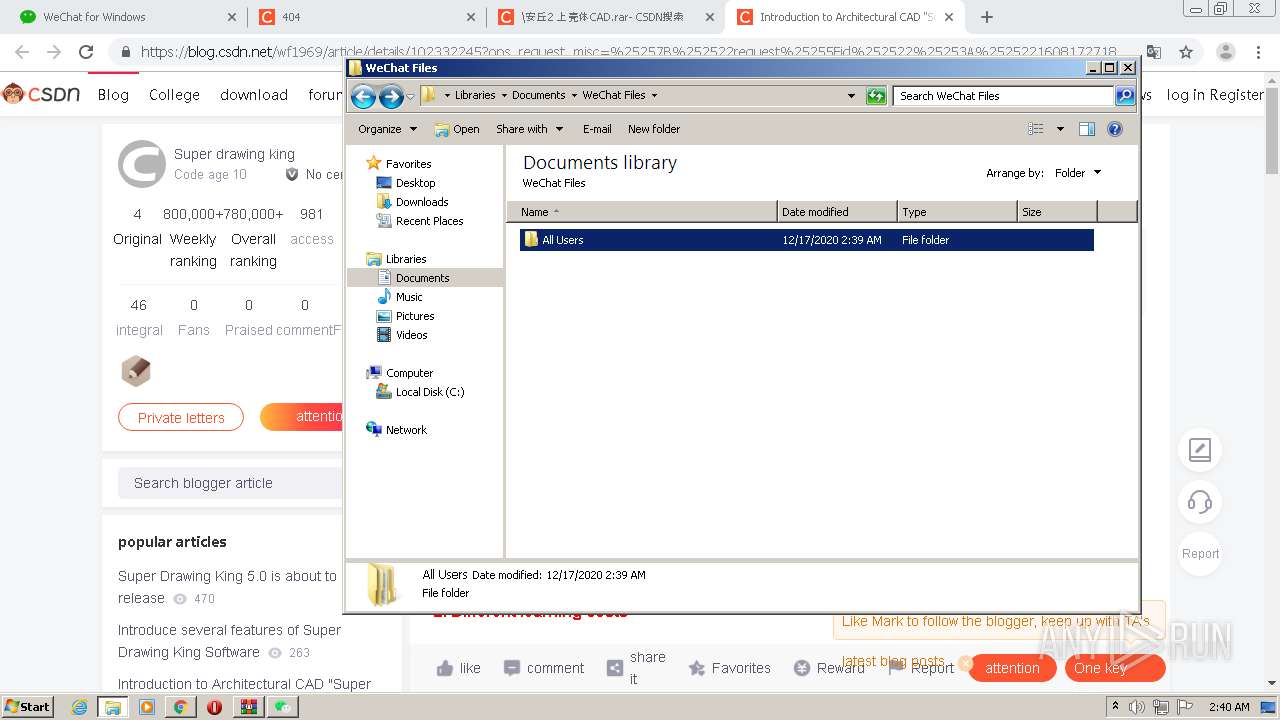
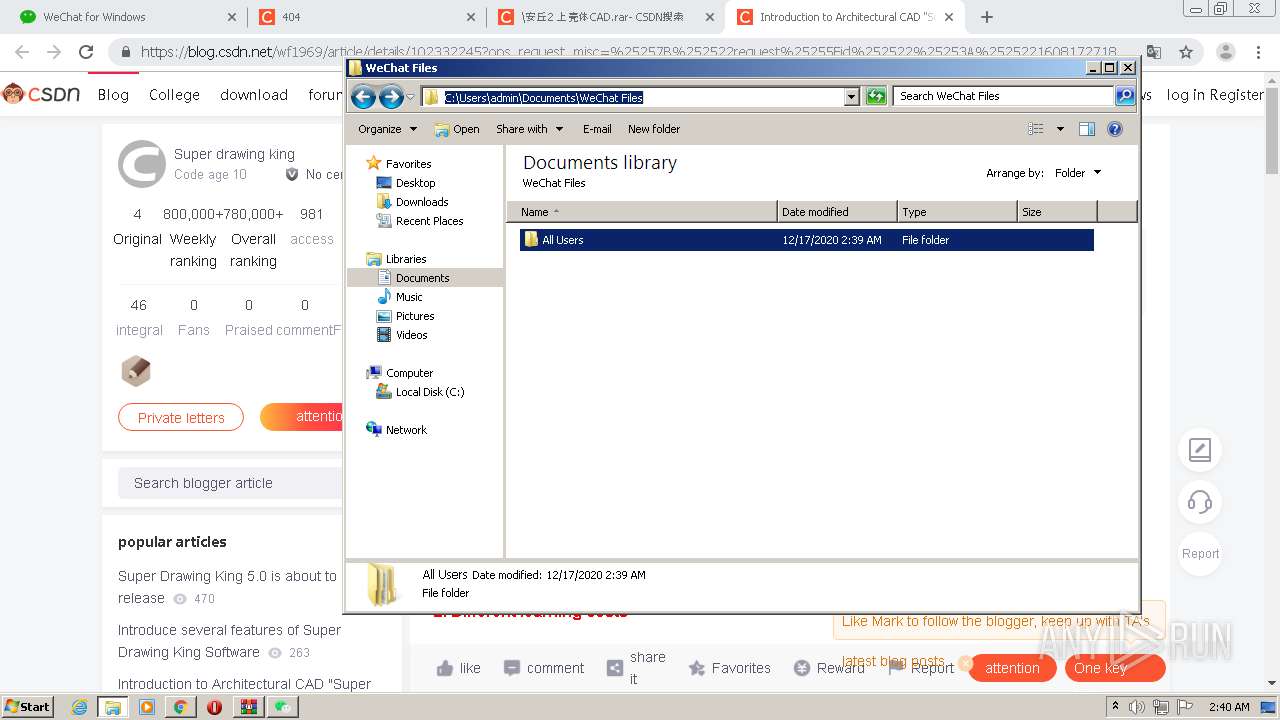
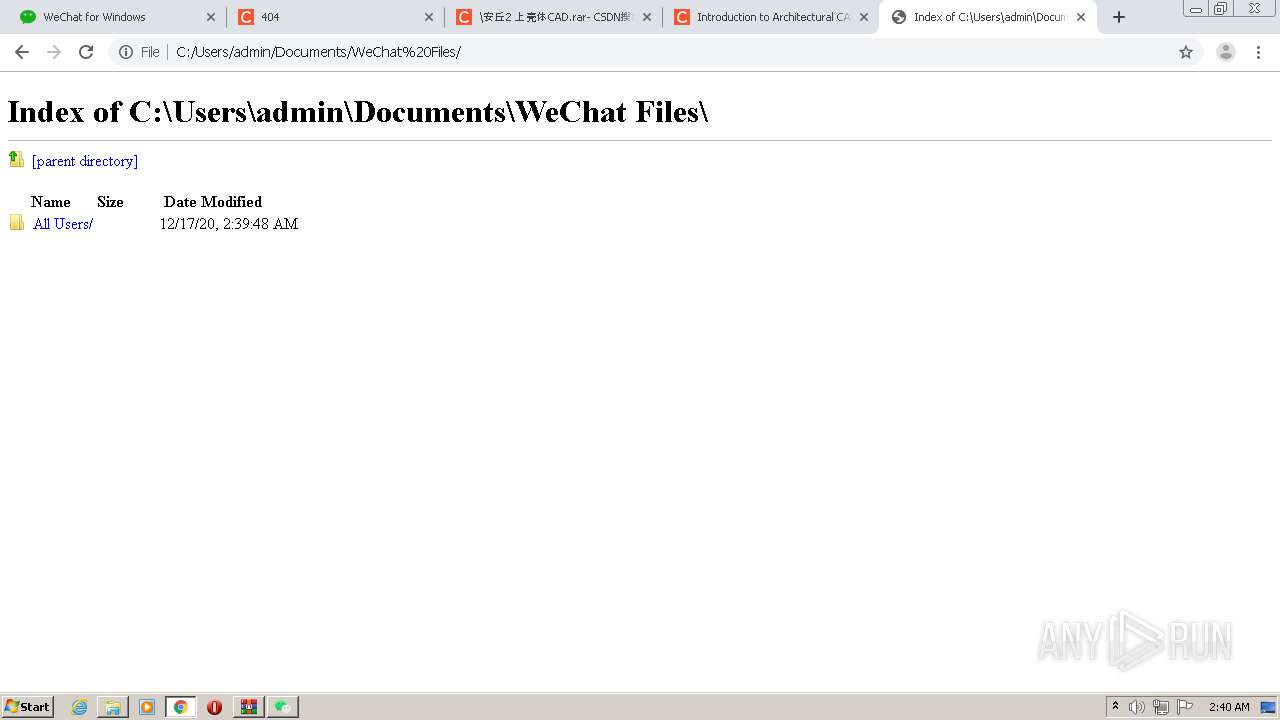
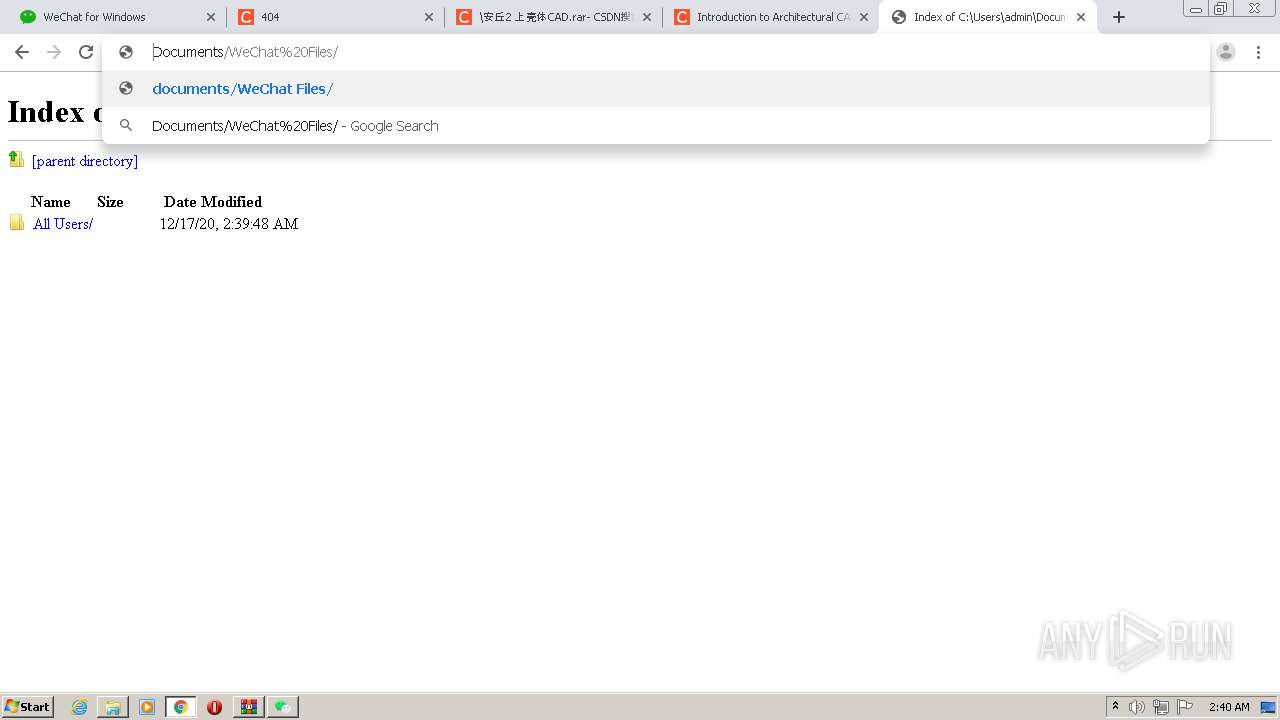
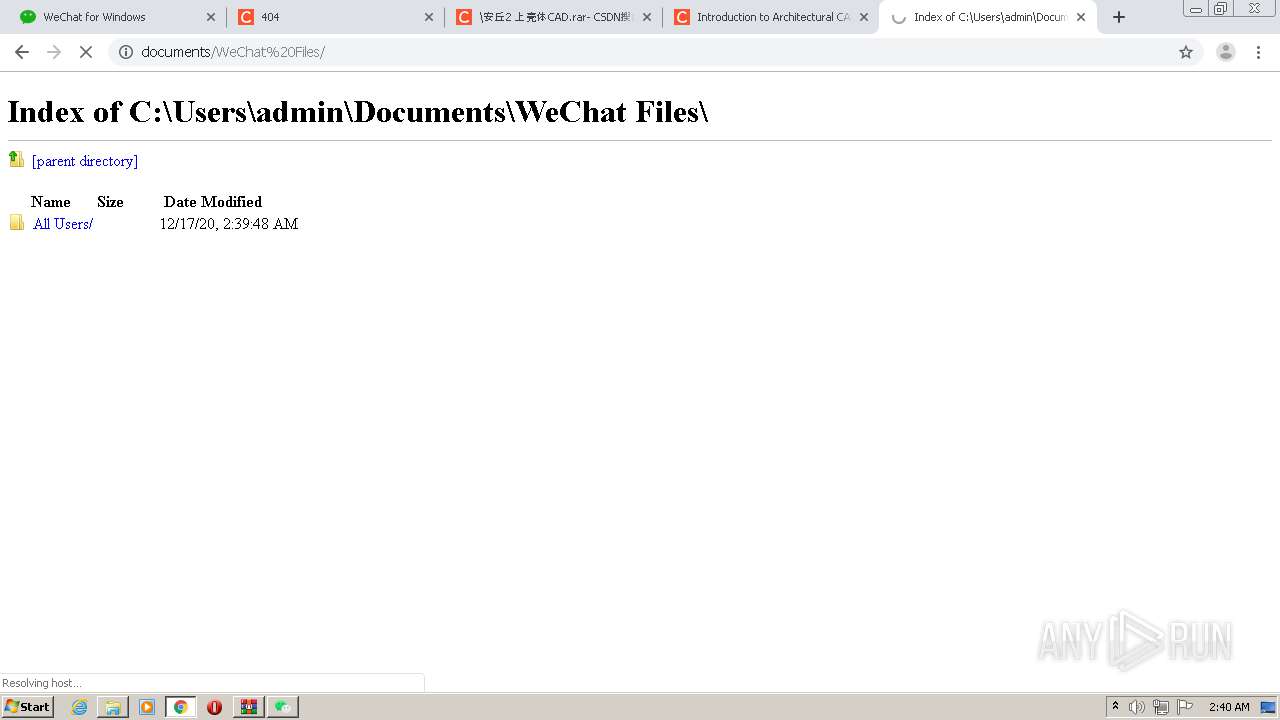
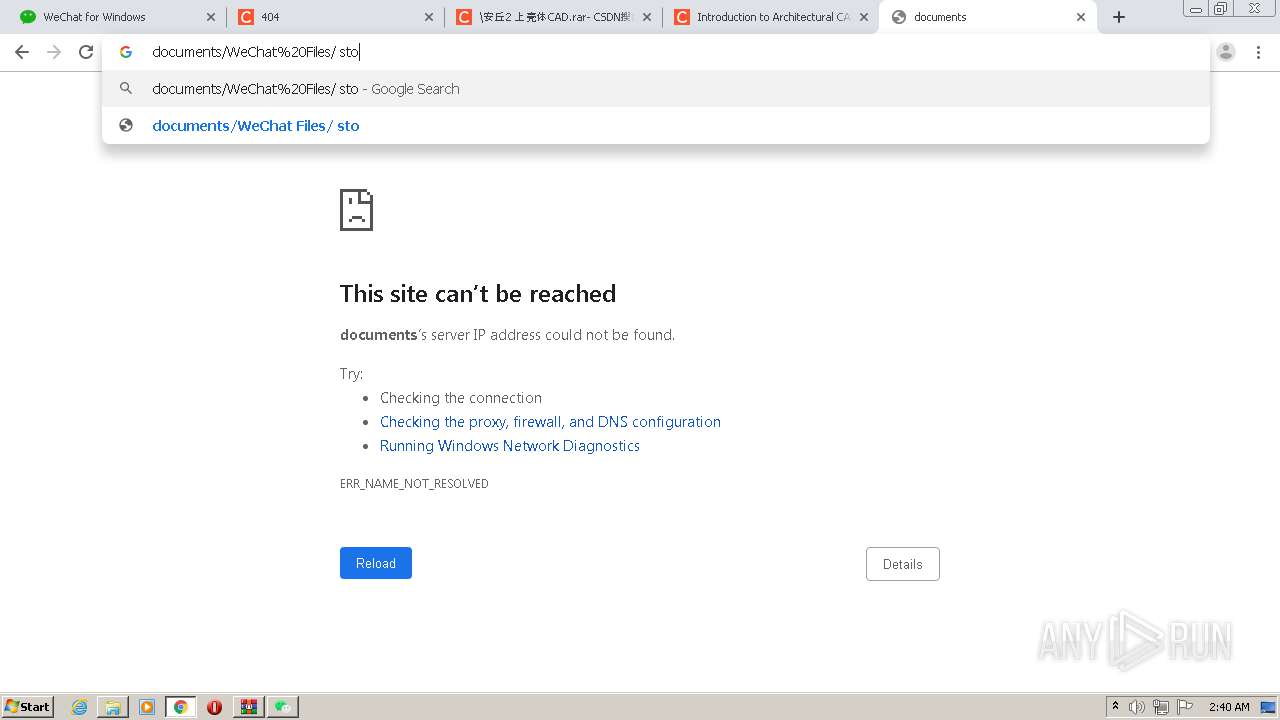
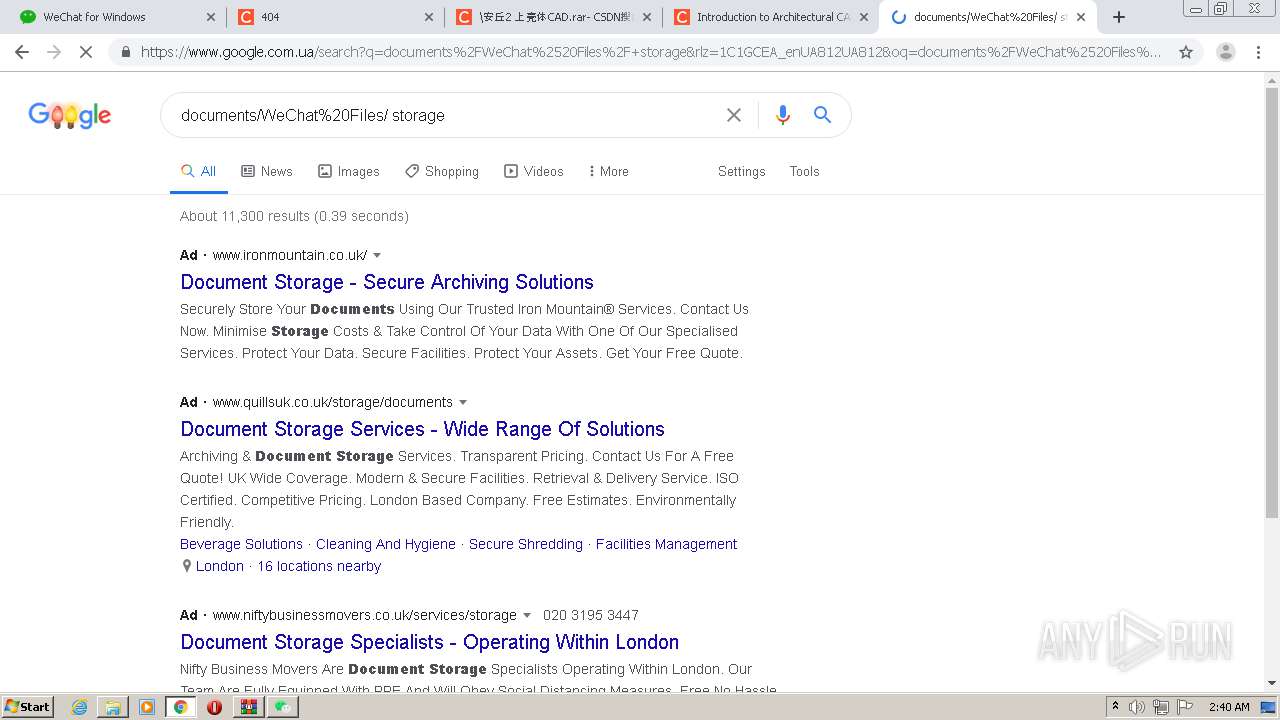
Actions looks like stealing of personal data
- WeChat.exe (PID: 2220)
SUSPICIOUS
Drops a file that was compiled in debug mode
- WeChatSetup.exe (PID: 2992)
Starts CMD.EXE for commands execution
- WeChatSetup.exe (PID: 2992)
Executable content was dropped or overwritten
- WeChatSetup.exe (PID: 2992)
- chrome.exe (PID: 2532)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2820)
- cmd.exe (PID: 1888)
Creates a directory in Program Files
- WeChatSetup.exe (PID: 2992)
Creates files in the program directory
- WeChatSetup.exe (PID: 2992)
Drops a file with too old compile date
- WeChatSetup.exe (PID: 2992)
Creates a software uninstall entry
- WeChatSetup.exe (PID: 2992)
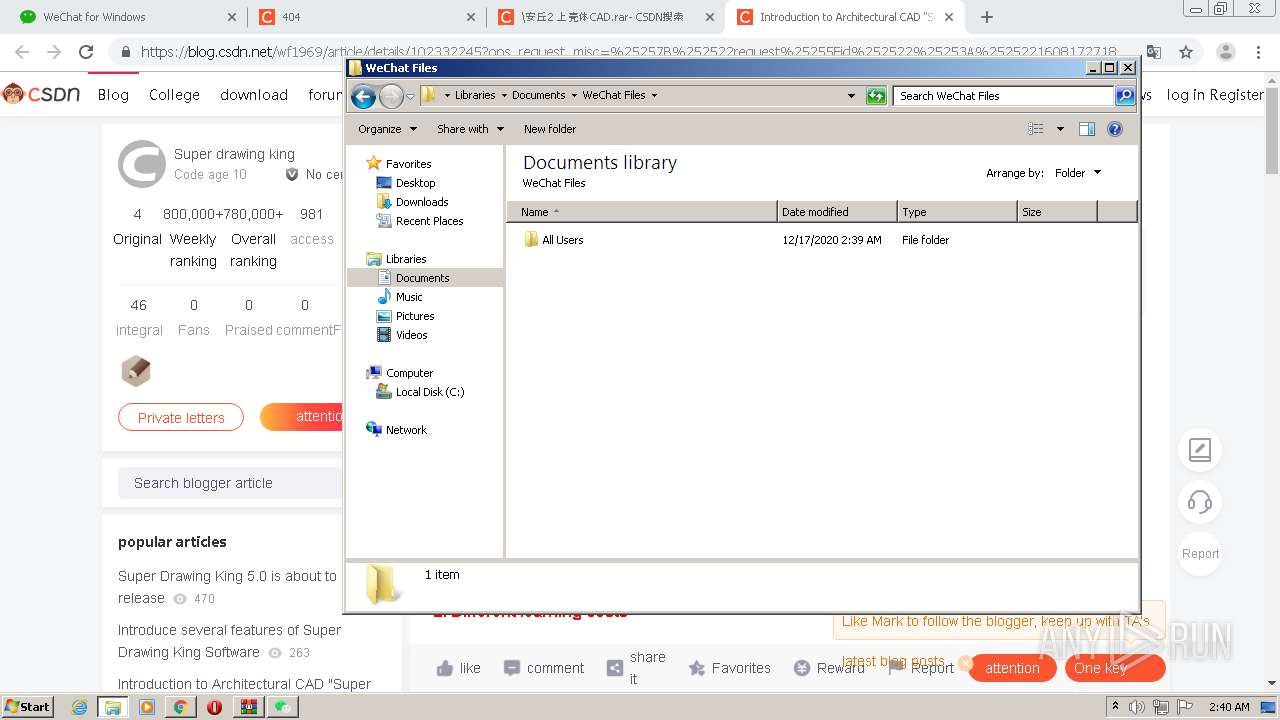
Creates files in the user directory
- WeChat.exe (PID: 2220)
INFO
Reads the hosts file
- chrome.exe (PID: 2532)
- WeChat.exe (PID: 2220)
- chrome.exe (PID: 2392)
- RdrCEF.exe (PID: 3592)
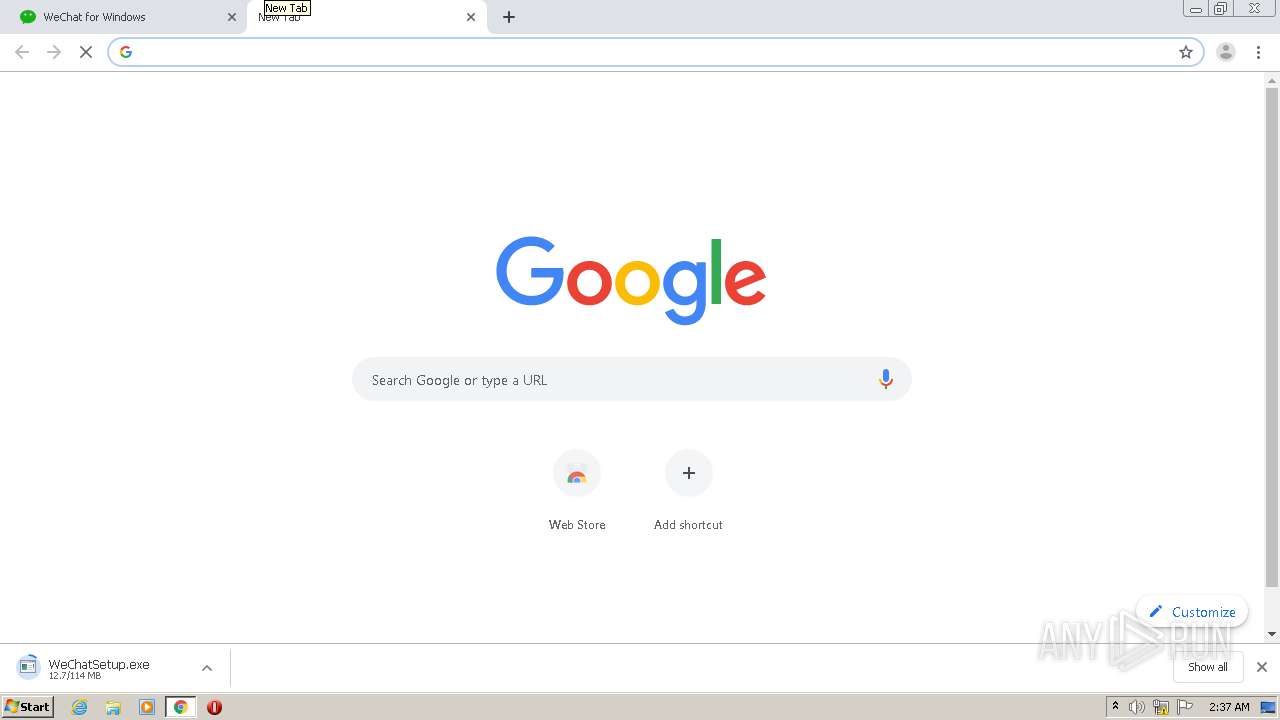
Application launched itself
- chrome.exe (PID: 2532)
- RdrCEF.exe (PID: 3592)
- AcroRd32.exe (PID: 2236)
Manual execution by user
- explorer.exe (PID: 3836)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2236)
Reads settings of System Certificates
- chrome.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
57
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | netsh advfirewall firewall add rule name="WeChat" dir=in action=allow program="C:\Program Files\Tencent\WeChat\WeChat.exe" enable=yes | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17987937541987481880 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
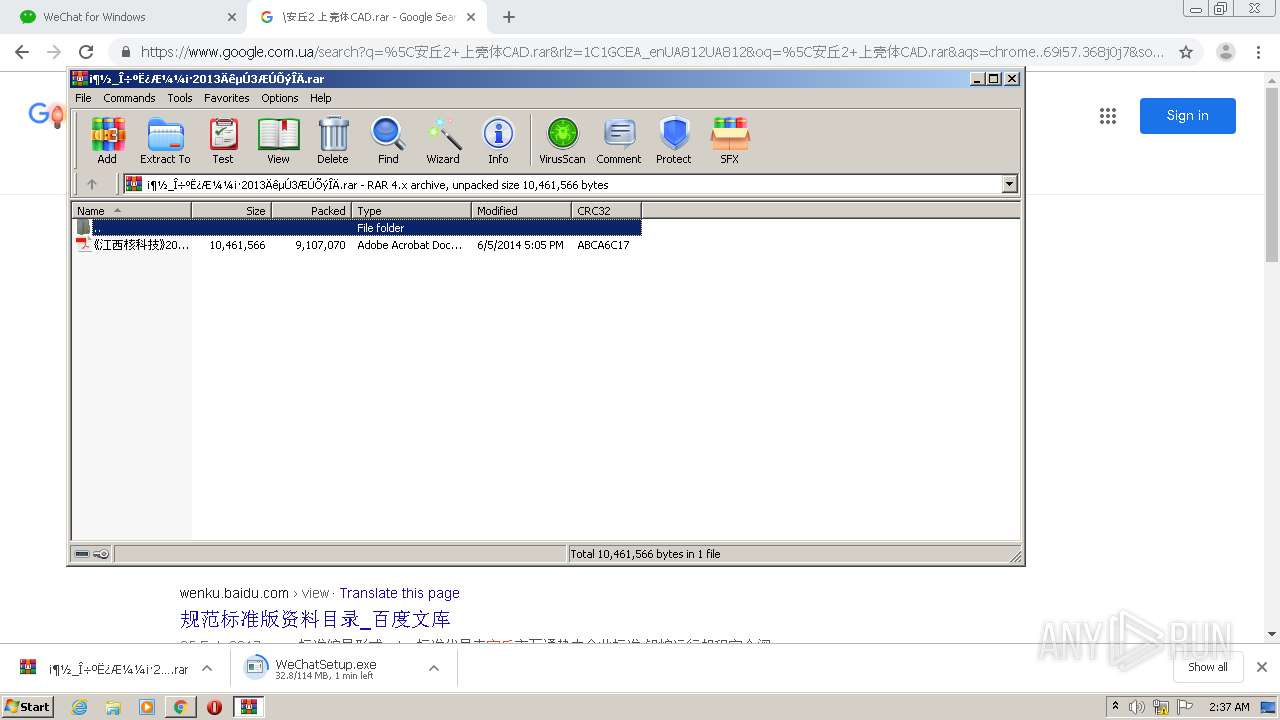
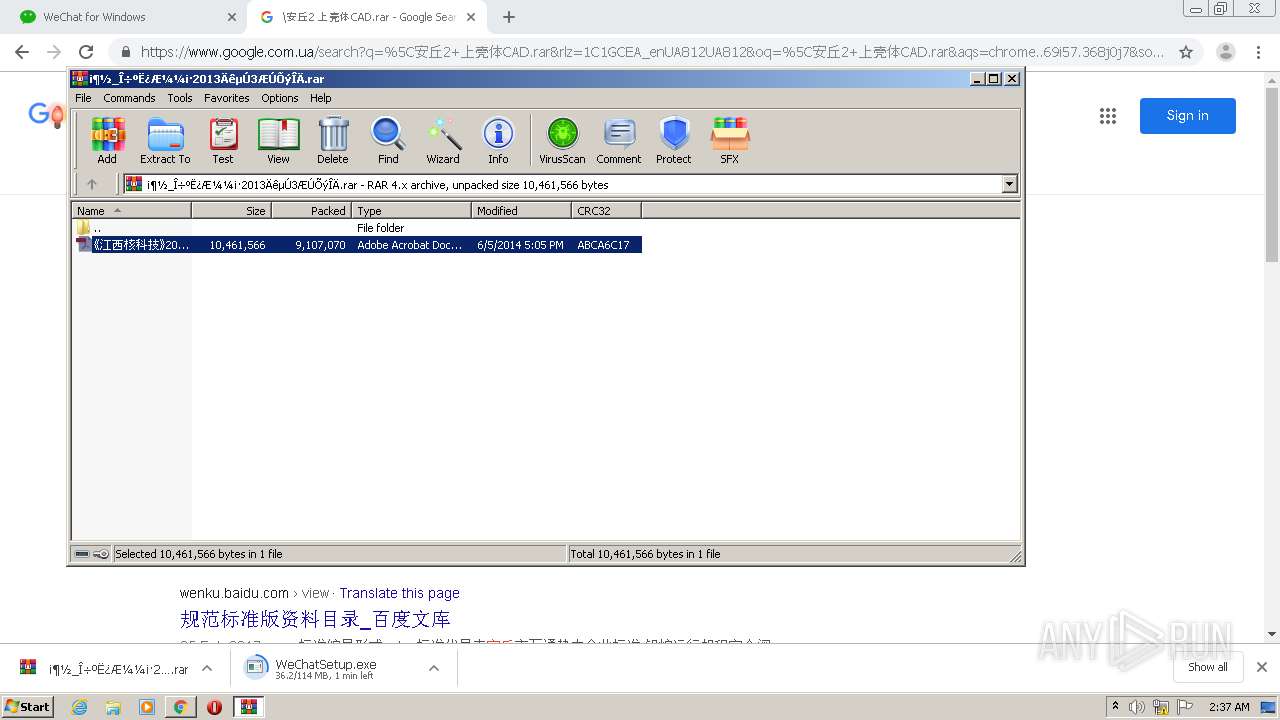
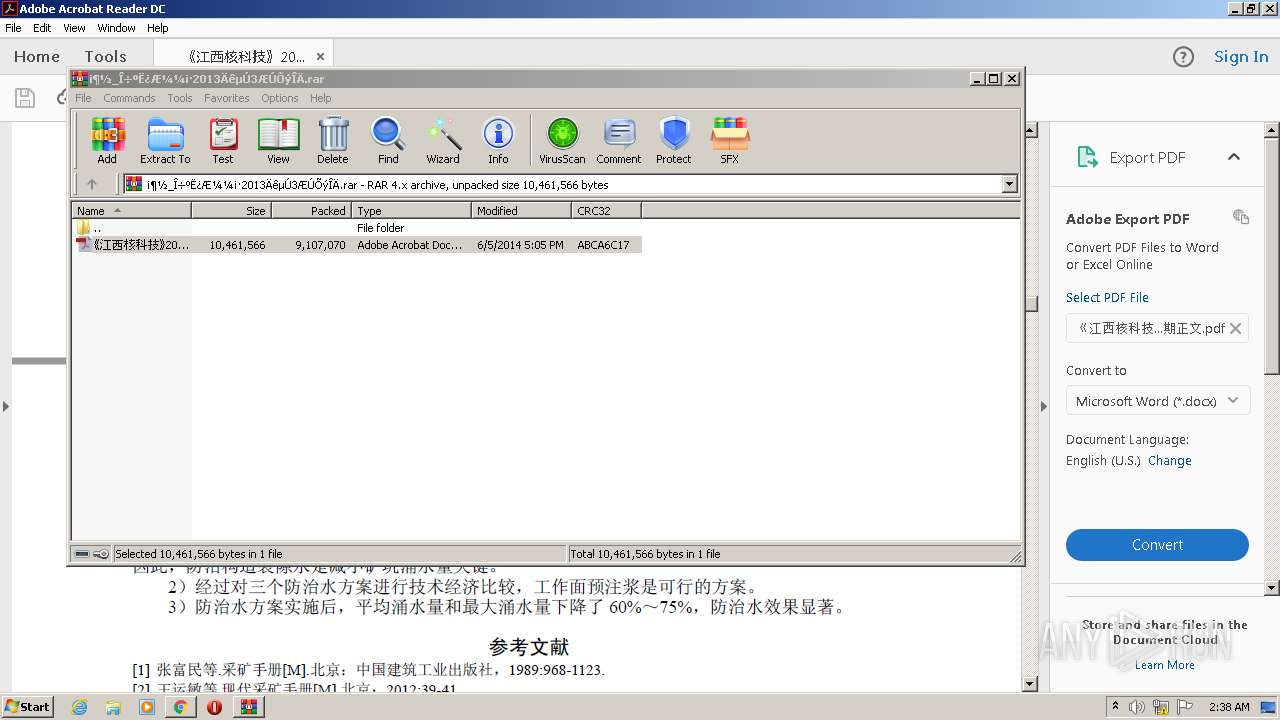
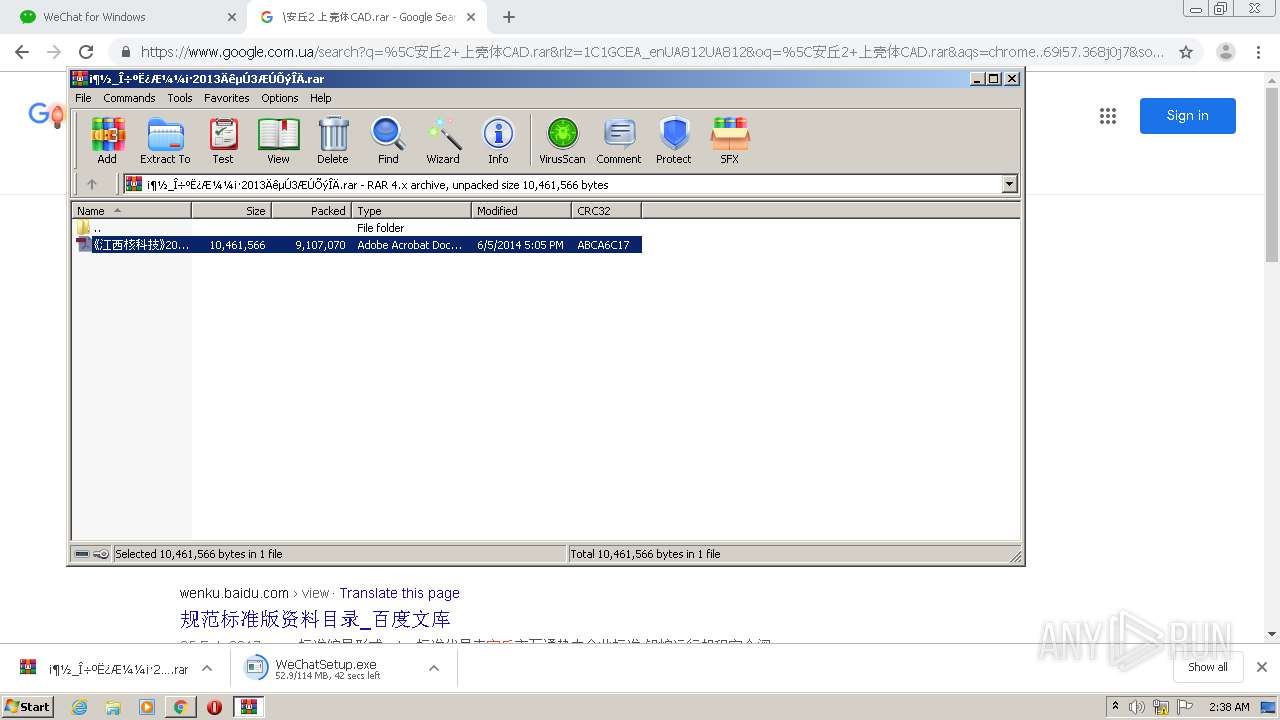
| 336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\¡¶½_Î÷ºË¿Æ¼¼¡·2013ÄêµÚ3ÆÚÕýÎÄ.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8297652589251469122 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9980655031620573950 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1401240380761972585 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6907901721700824428 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17862252005901485303 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6280820279395759963 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8792541378595596295,2334159481139442011,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5787355201114785482 --mojo-platform-channel-handle=5208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 226
Read events
1 885
Write events
338
Delete events
3
Modification events
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2532-13252646179585500 |
Value: 259 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
45
Suspicious files
319
Text files
203
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FDAC424-9E4.pma | — | |
MD5:— | SHA256:— | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6737f6d7-90e7-4046-a37c-11b8db80e105.tmp | — | |
MD5:— | SHA256:— | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF154187.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF154196.TMP | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1541b6.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15437b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
199
DNS requests
156
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
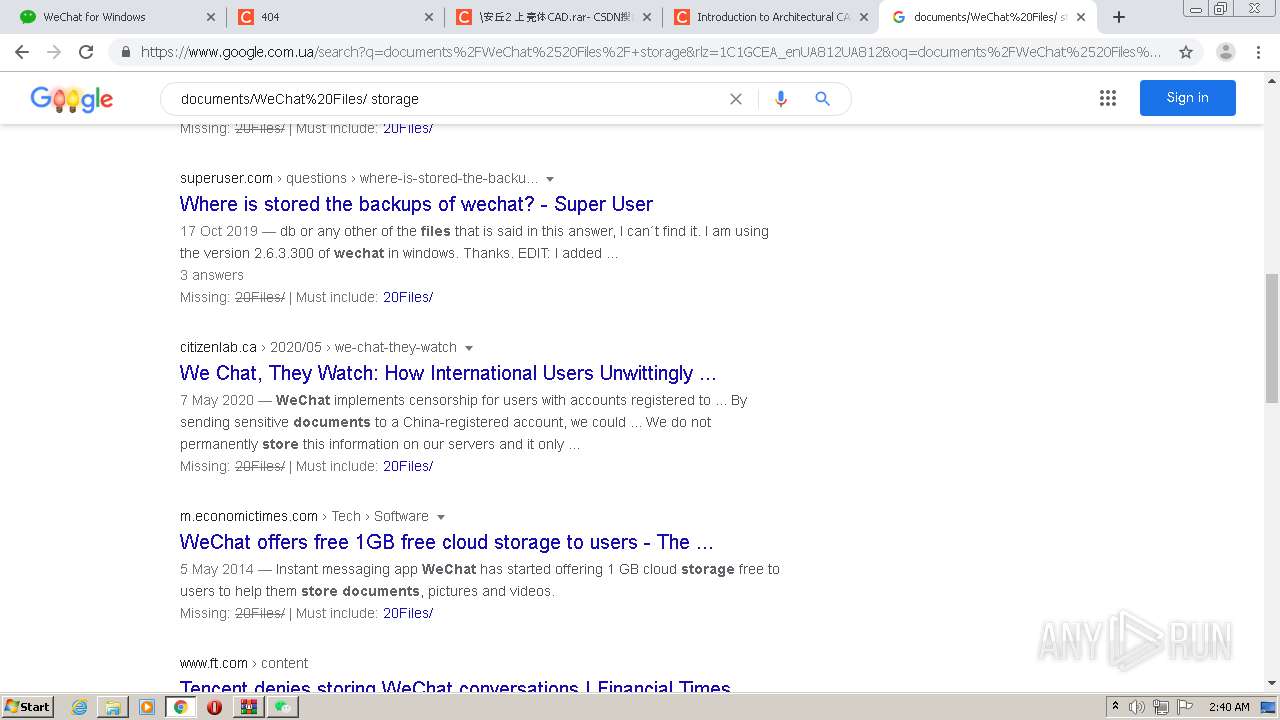
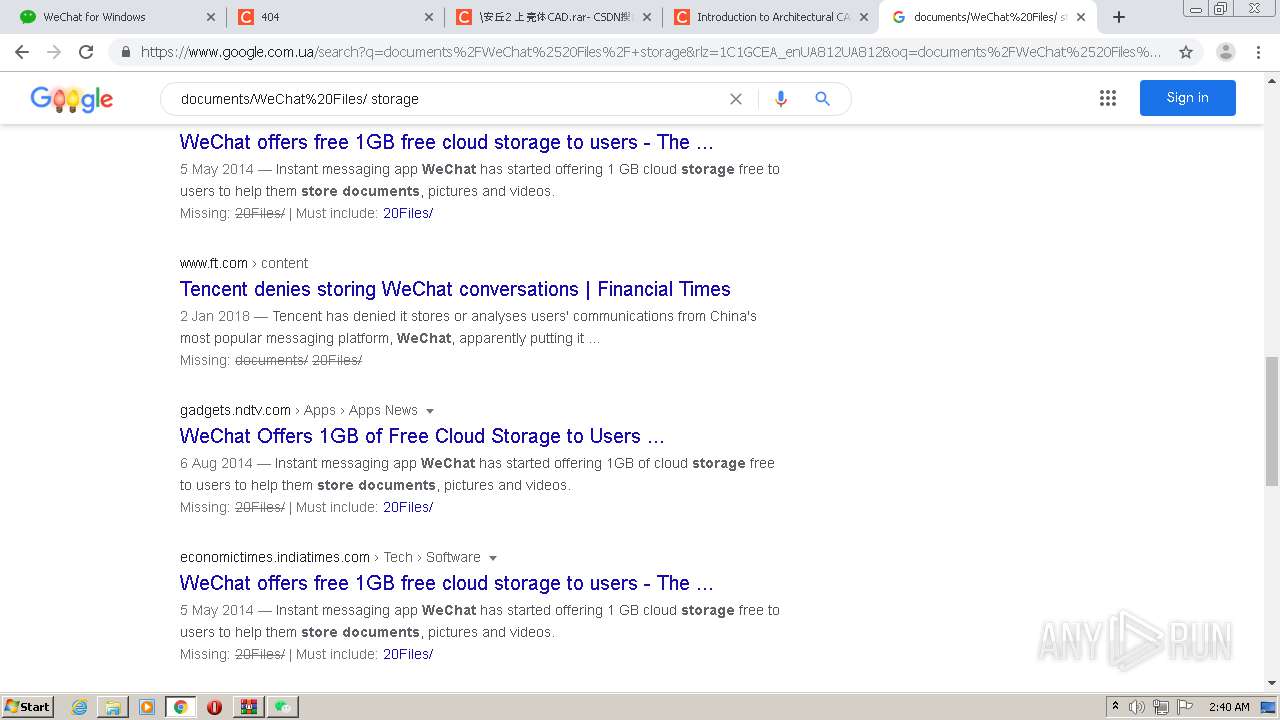
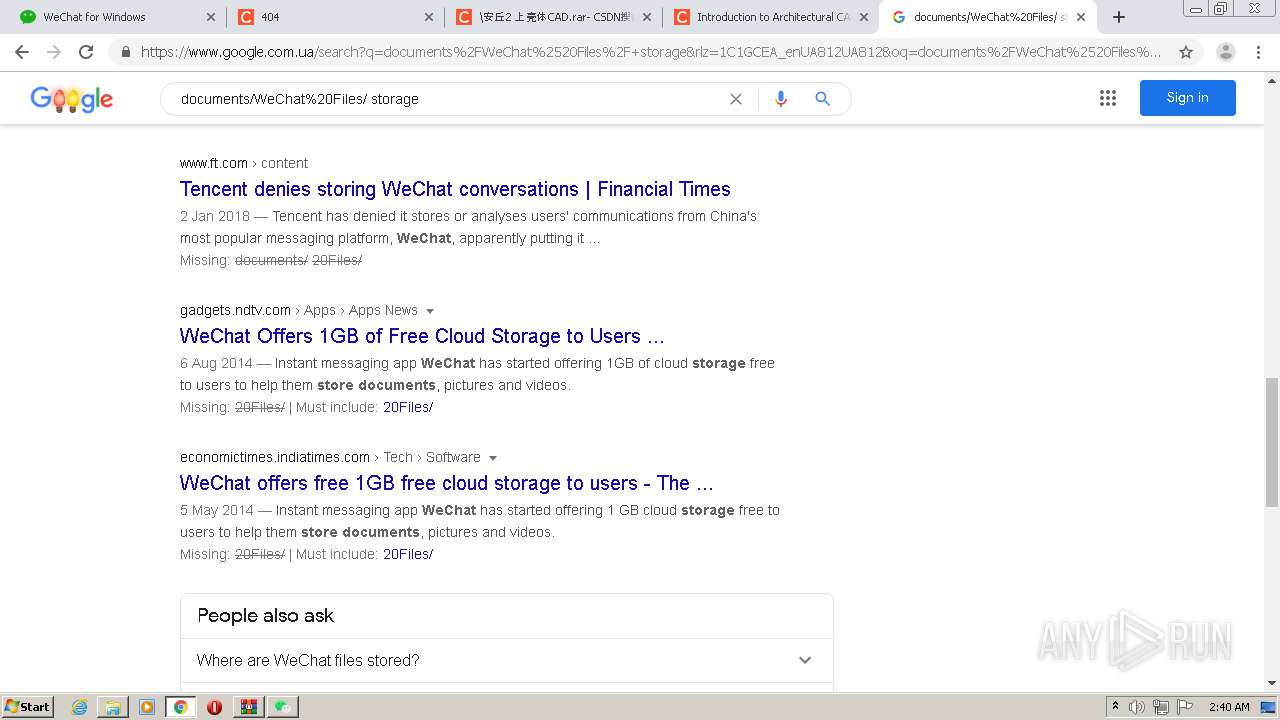
2220 | WeChat.exe | POST | 200 | 49.51.89.155:80 | http://49.51.89.155/mmtls/00004bc3 | CN | binary | 585 b | suspicious |
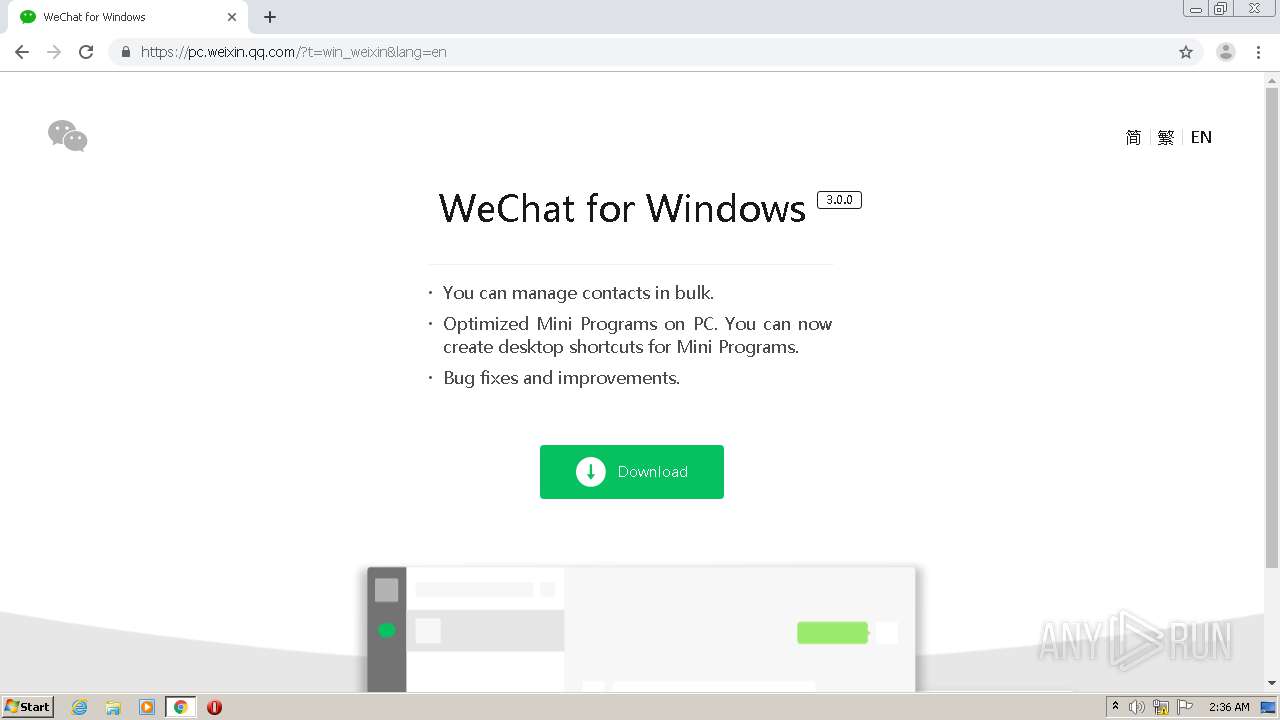
2392 | chrome.exe | GET | — | 203.205.235.205:80 | http://weixin.qq.com/cgi-bin/readtemplate?t=win_weixin&lang=en | CN | — | — | whitelisted |
2392 | chrome.exe | GET | 301 | 203.205.235.205:80 | http://weixin.qq.com/cgi-bin/readtemplate?t=win_weixin&lang=en | CN | — | — | whitelisted |
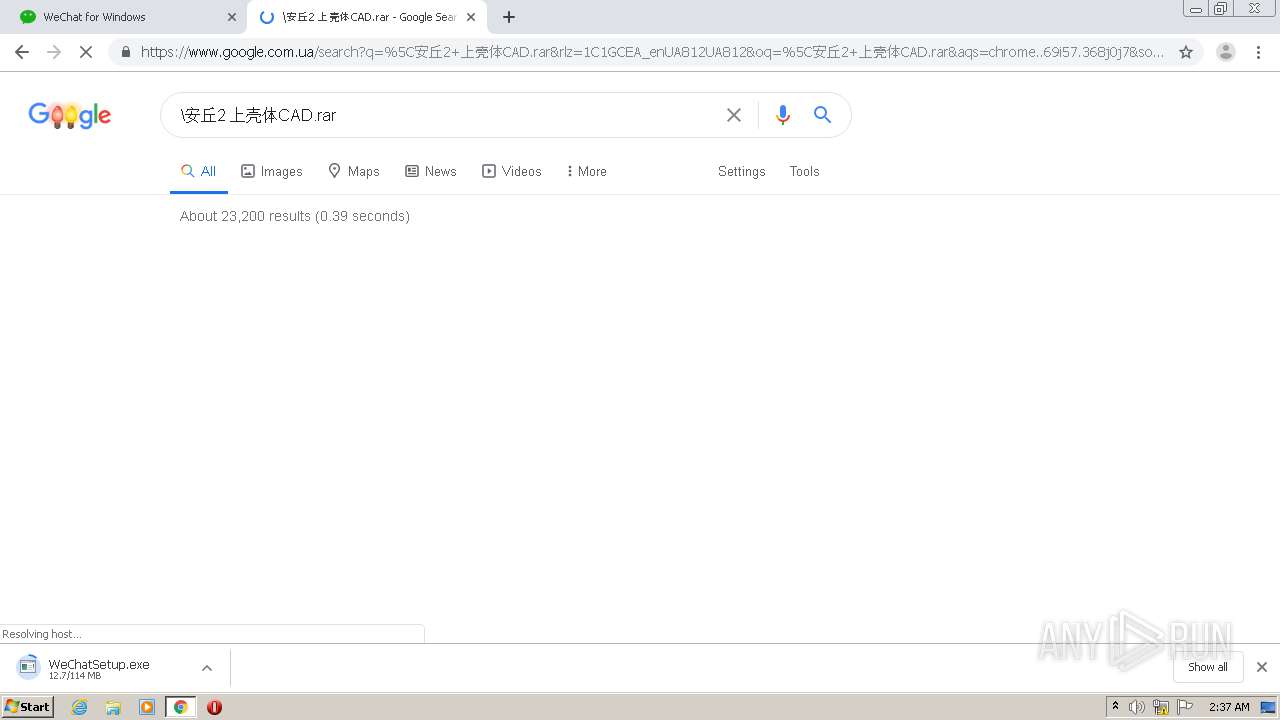
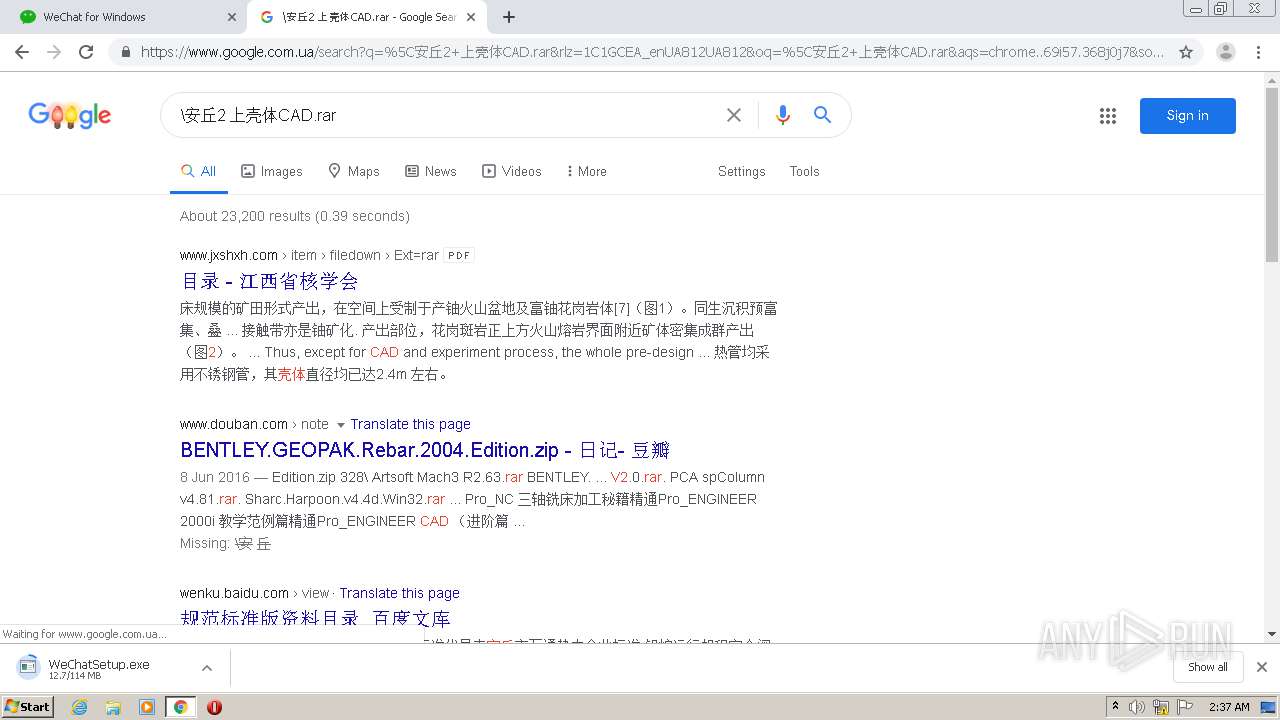
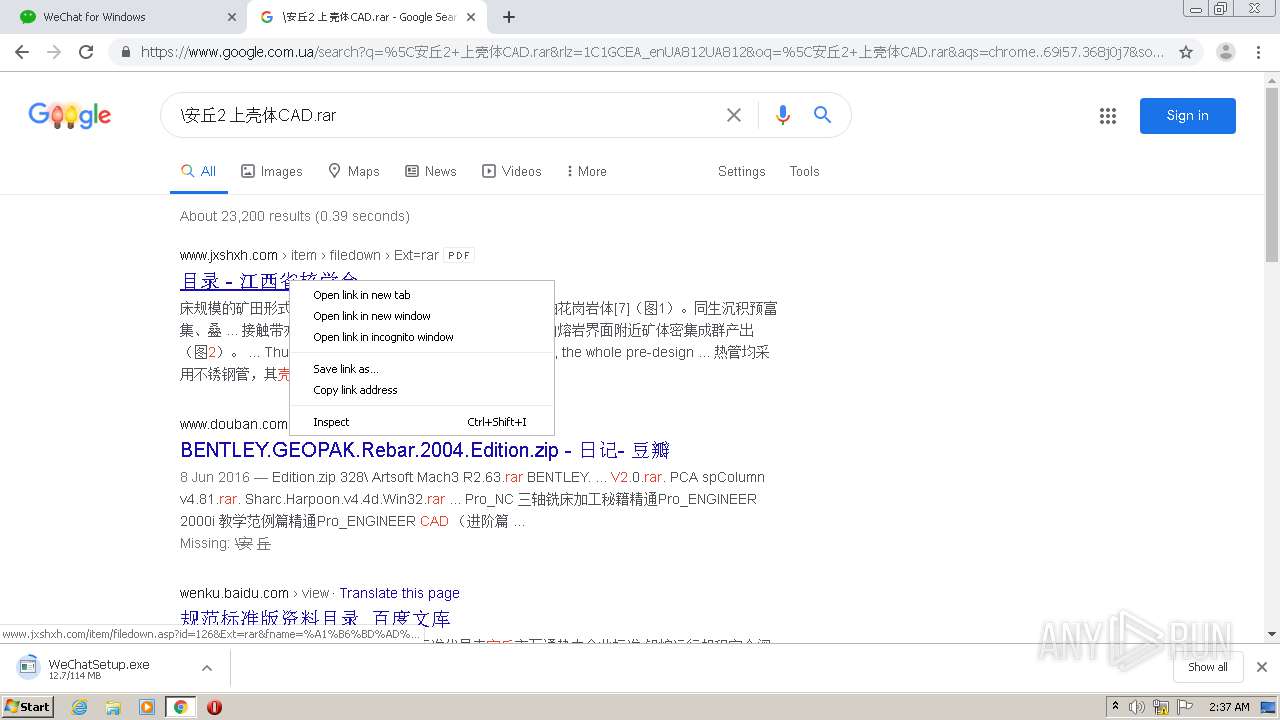
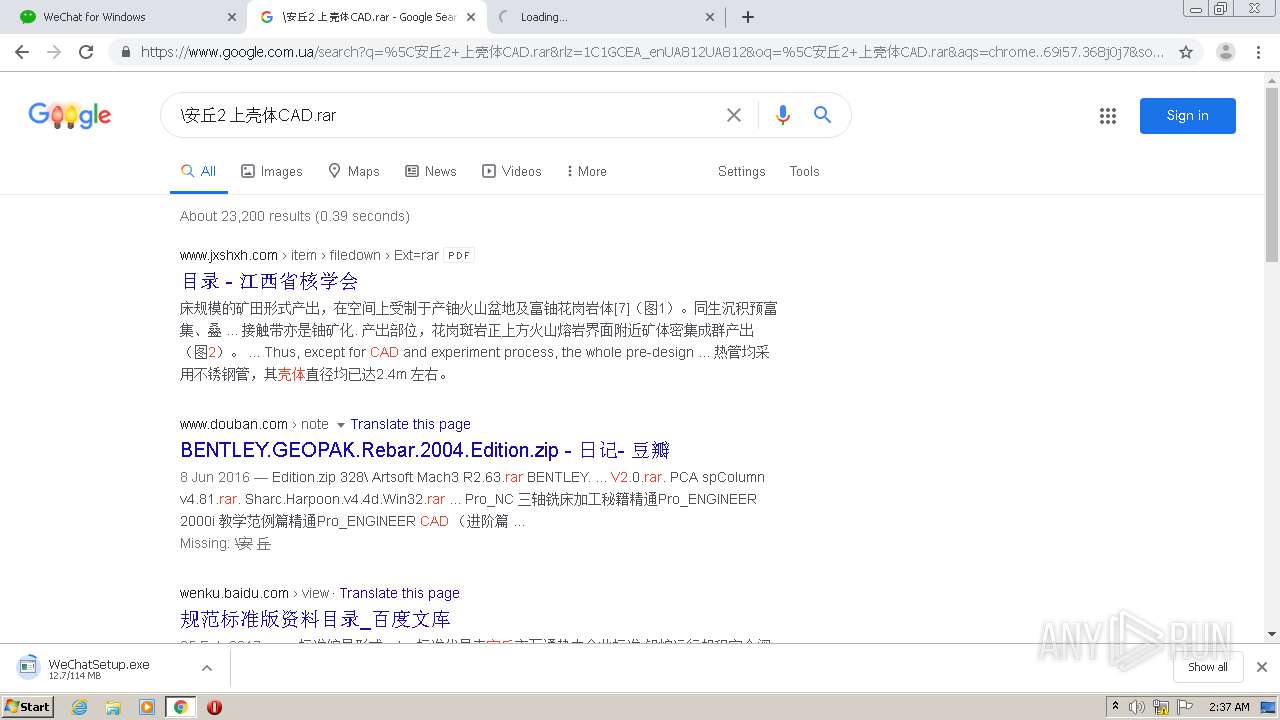
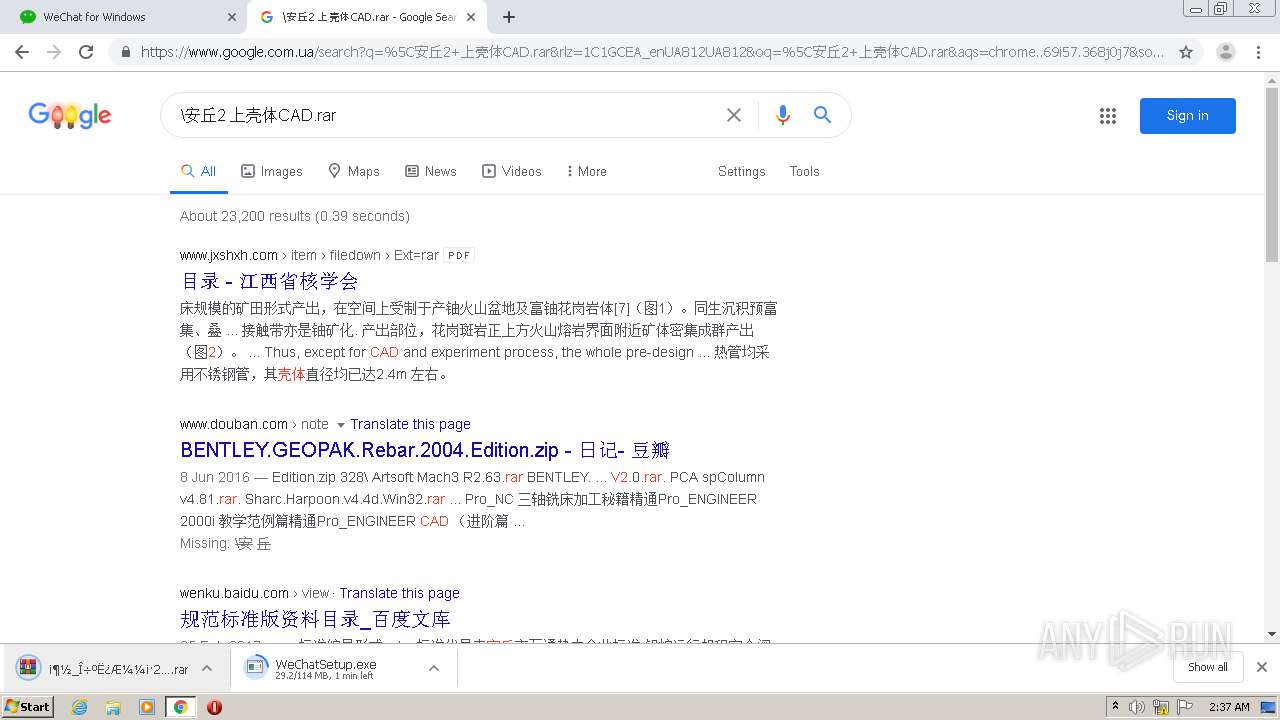
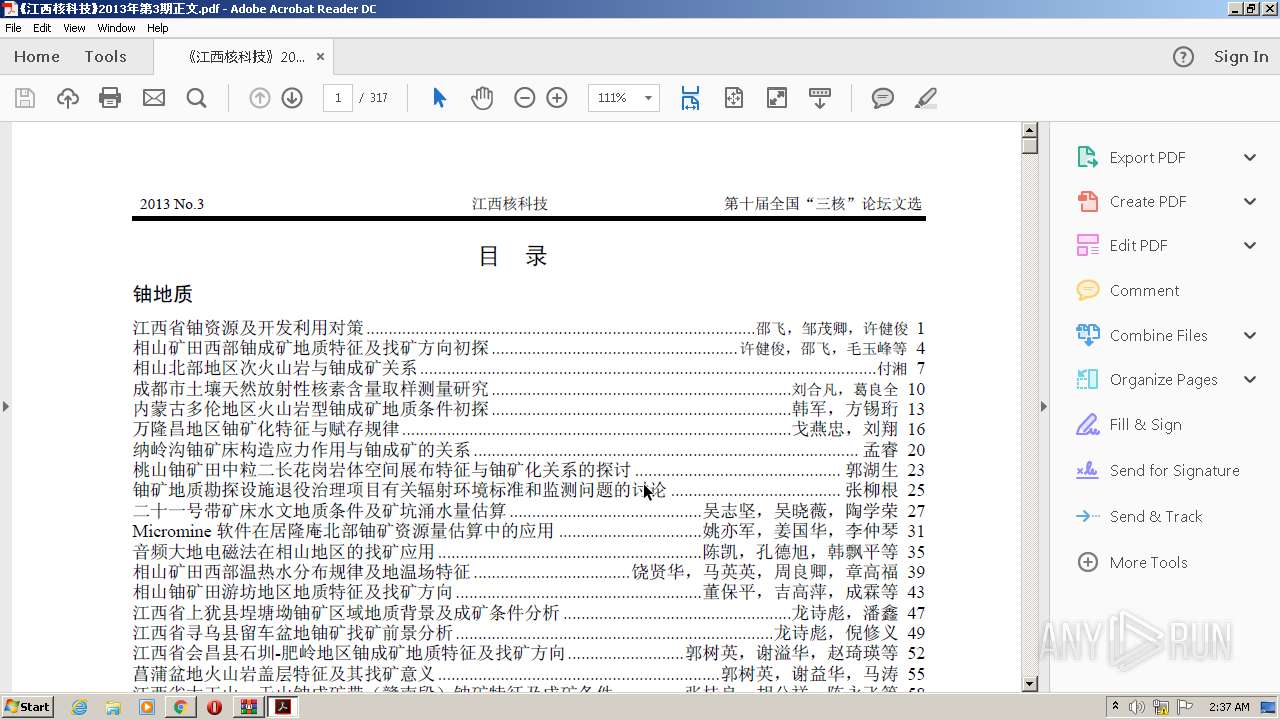
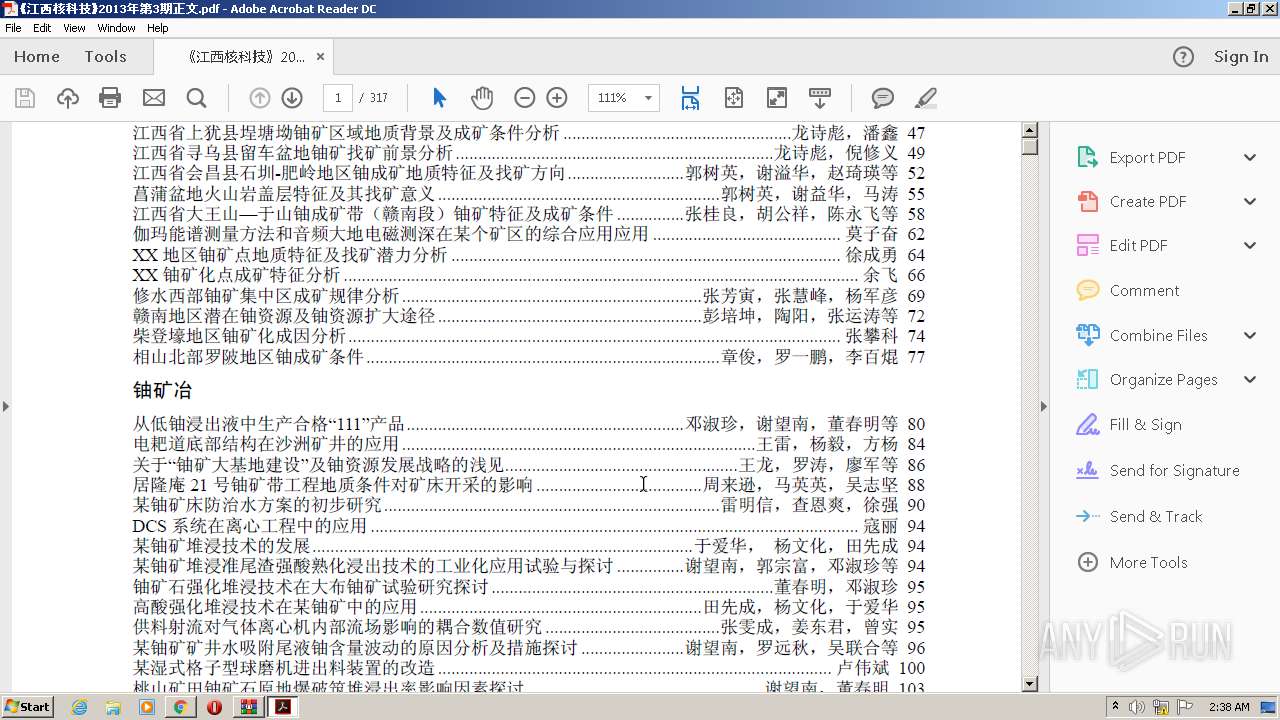
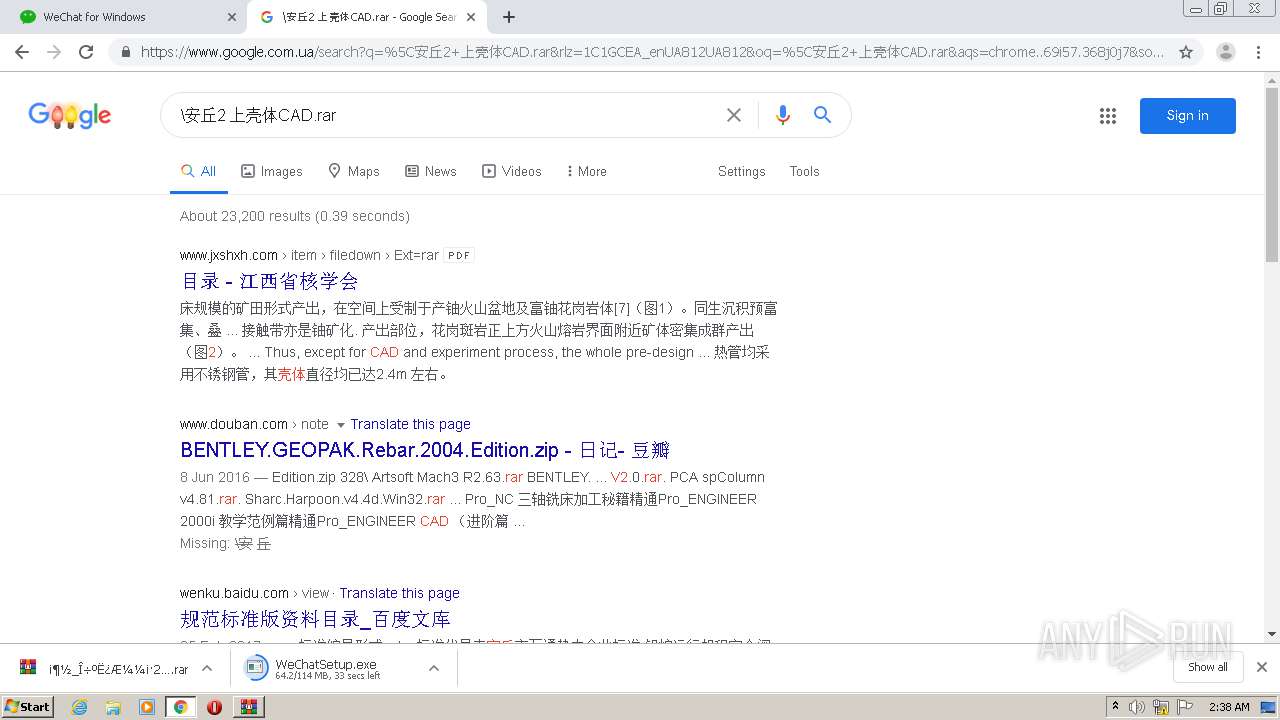
2392 | chrome.exe | GET | 200 | 117.41.181.31:80 | http://www.jxshxh.com/item/filedown.asp?id=126&Ext=rar&fname=%A1%B6%BD%AD%CE%F7%BA%CB%BF%C6%BC%BC%A1%B72013%C4%EA%B5%DA3%C6%DA%D5%FD%CE%C4%2Erar | CN | compressed | 8.69 Mb | unknown |
2220 | WeChat.exe | POST | 200 | 162.62.97.64:80 | http://162.62.97.64/mmtls/00004bc3 | US | binary | 2.69 Kb | unknown |
2392 | chrome.exe | GET | 301 | 203.205.235.205:80 | http://weixin.qq.com/cgi-bin/readtemplate?t=win_weixin&lang=en | CN | — | — | whitelisted |
2220 | WeChat.exe | POST | 200 | 49.51.89.155:80 | http://dns.weixin.qq.com/mmtls/00004bc3 | CN | binary | 4.87 Kb | suspicious |
2220 | WeChat.exe | POST | 200 | 203.205.255.78:8080 | http://wup.imtt.qq.com:8080/?encrypt=17&len=1024&v=3&iv=be1962e1ed5848de&id=a690d5f54b43ca535af266c3180769c7&qbkey=53B00F0EBF66DD02A6FFB5B6A700E3B991CB502C2317976E6D2761D5C8EFC3238BA4576B2B01AF8AE94E0C08C63089E253165D566A7D086920FEE58617FC6852CD8C43A69E301753F8488E956FF8F6382BAFDF31B410B5552CBEF2D2004D721A077840F5B06E9C7E3A76BEBB3141914B6F5DD21C3464061EB455761E80B53A44 | CN | binary | 160 b | suspicious |
2220 | WeChat.exe | POST | 200 | 203.205.255.78:8080 | http://wup.imtt.qq.com:8080/?encrypt=17&len=1024&v=3&iv=dc57e27ce275431b&id=a690d5f54b43ca535af266c3180769c7&qbkey=A6706F768E92A213F70717B82EA0977410C1F99C72F4D65898BF223400805CC962EBA5343A4875FD7DDDE0B4088CEE139FBF6E6289C50391EDD4D599518A4C7FDBC170E209C96C78AAD638907C07D2423CAEB8370680C5791C7AF247D3BCAD0ABDAFD705BA0538C58C0287DE90E07937CBA73C1B40F16B7129B625225BAABF0F | CN | binary | 112 b | suspicious |
2220 | WeChat.exe | POST | 200 | 162.62.97.147:80 | http://szminorshort.weixin.qq.com/mmtls/00004c04 | US | binary | 10.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
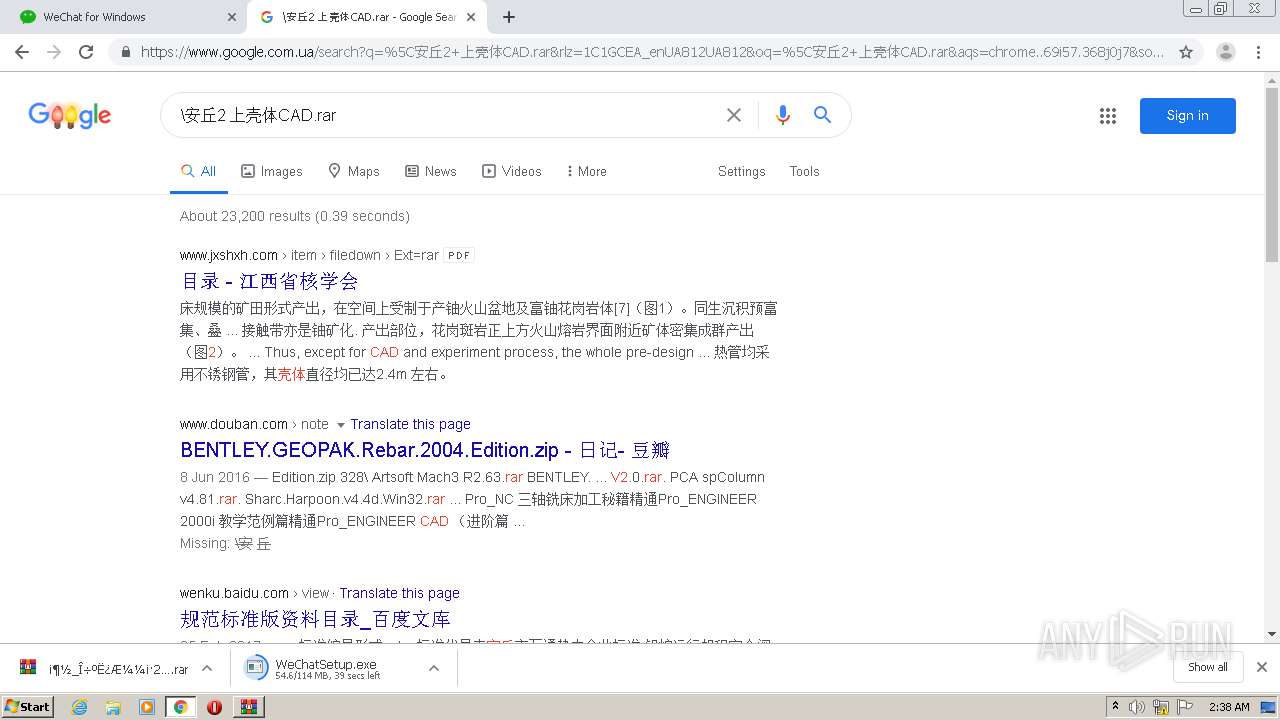
2392 | chrome.exe | 203.205.251.176:443 | www.wechat.com | — | CN | unknown |
2392 | chrome.exe | 150.109.206.154:443 | res.wx.qq.com | — | US | suspicious |
2392 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 203.205.254.110:443 | support.weixin.qq.com | — | CN | unknown |
2392 | chrome.exe | 203.205.235.205:80 | support.weixin.qq.com | — | CN | unknown |
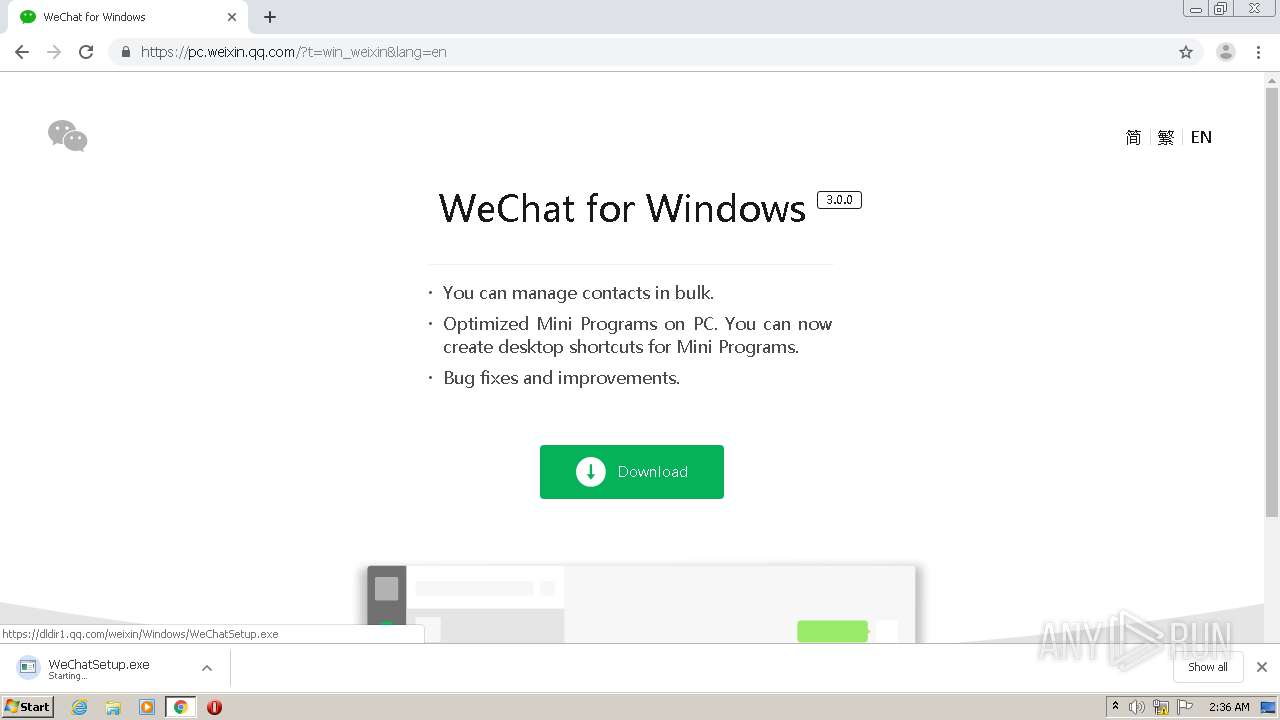
2392 | chrome.exe | 203.205.136.219:443 | dldir1.qq.com | Tencent Building, Kejizhongyi Avenue | CN | malicious |
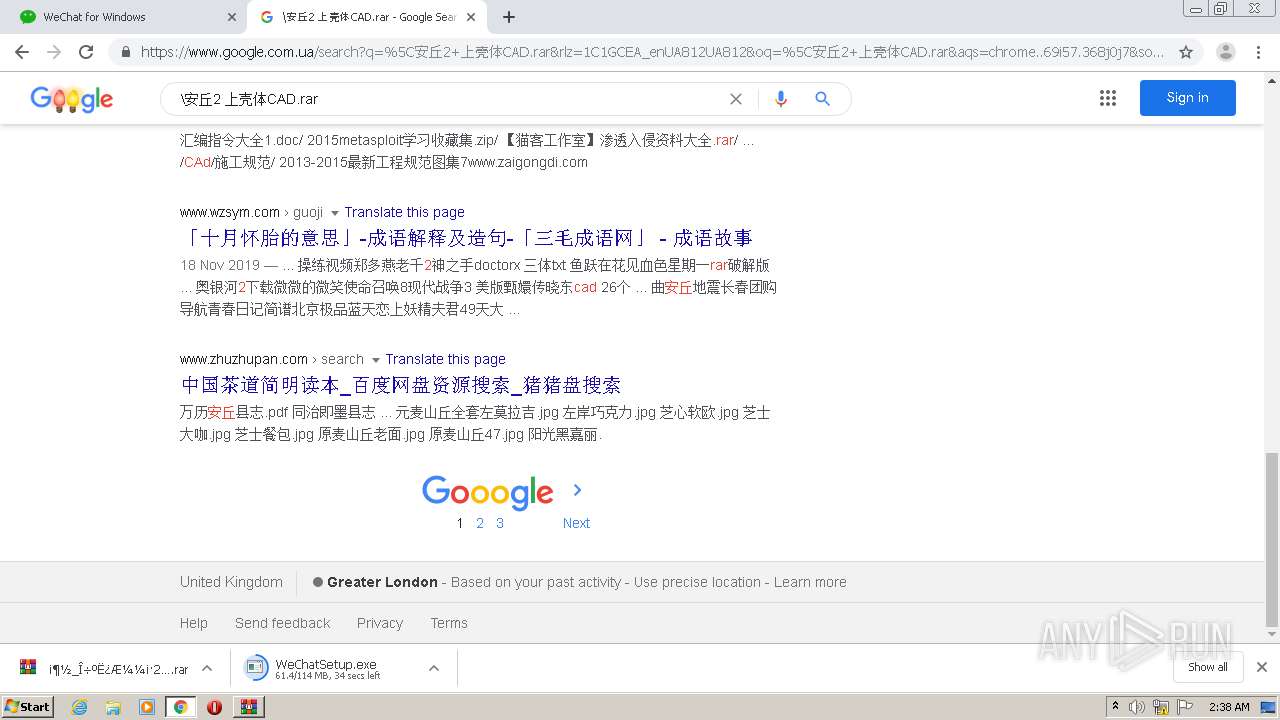
2392 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
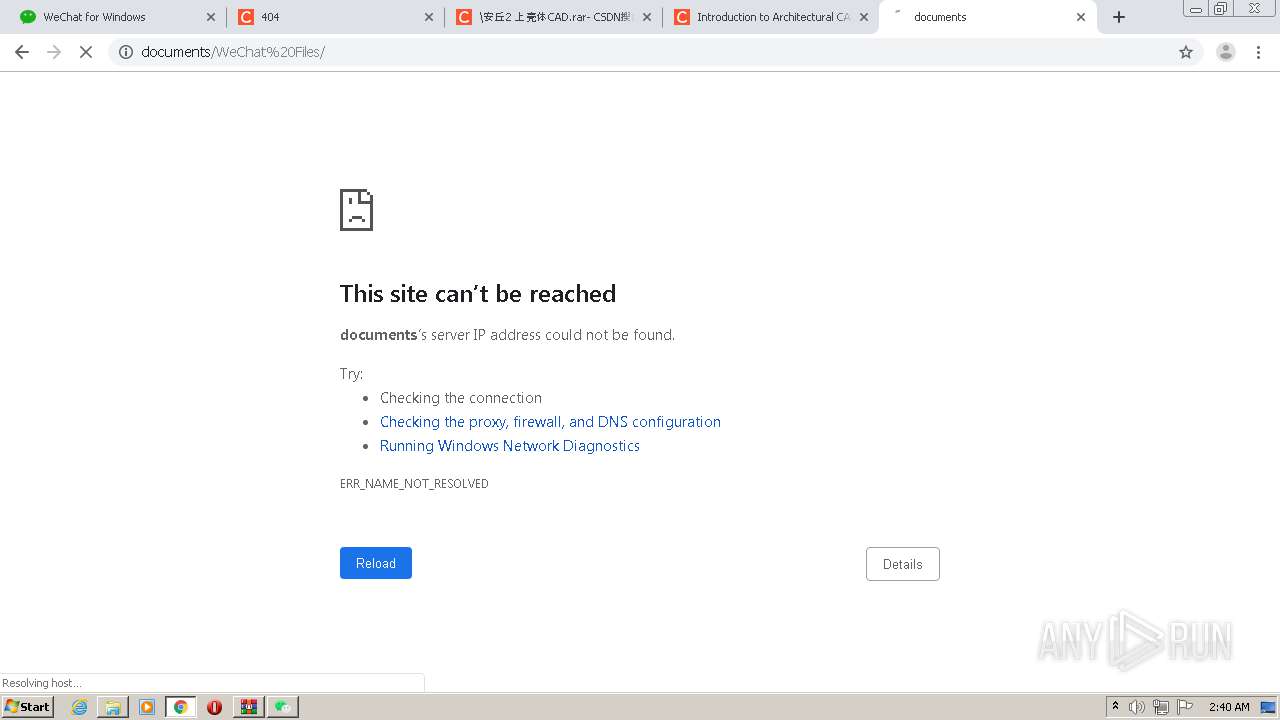
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.wechat.com |
| unknown |
accounts.google.com |
| shared |
res.wx.qq.com |
| whitelisted |
support.weixin.qq.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
weixin.qq.com |
| whitelisted |
pc.weixin.qq.com |
| unknown |
dldir1.qq.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2392 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
WeChat.exe | [1217/023948:INFO:exception_record.cc(518)] [QB]Process ID: 2220 Type: 1
|