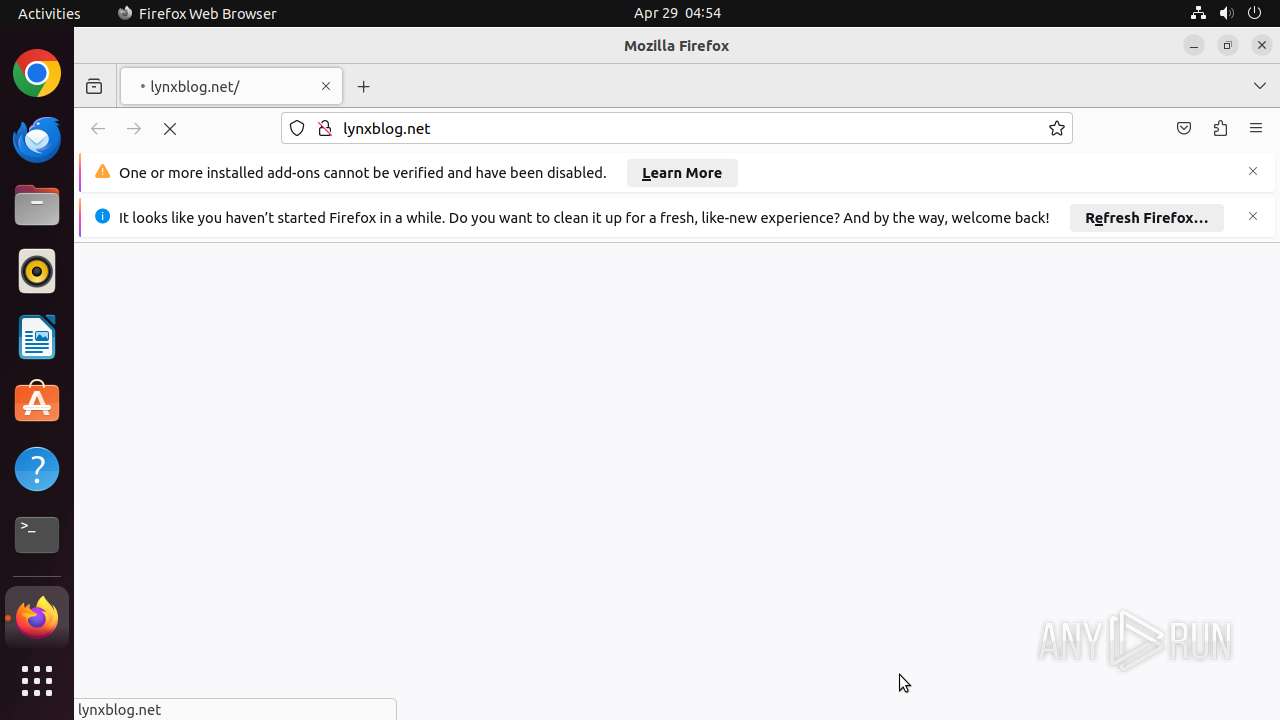
| URL: | lynxblog.net |
| Full analysis: | https://app.any.run/tasks/a6c8ccfc-0db9-41c5-ab45-c14eb464e14e |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 03:53:51 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | DFF4DDDEEA112CD305ADC448A749D276 |
| SHA1: | 18DFC0AA138CA3BE891E1681A0C2BE14C1EC3FDD |
| SHA256: | 450253A77683BD23F6079E5E49477D5EEAEAAFB557456291D1E7CB1C21C72B7D |
| SSDEEP: | 3:4m20n:490 |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 445)
SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 40651)
- firefox (PID: 40652)
Reads passwd file
- dumpe2fs (PID: 40672)
- dumpe2fs (PID: 40679)
Check the Environment Variables Related to System Identification (os-release)
- firefox (PID: 40652)
- snapctl (PID: 40706)
- snapctl (PID: 40745)
- snapctl (PID: 40701)
- snapctl (PID: 40739)
INFO
Checks timezone
- dumpe2fs (PID: 40672)
- dumpe2fs (PID: 40679)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
389
Monitored processes
169
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 40650 | /bin/sh -c "DISPLAY=:0 sudo -iu user firefox lynxblog\.net " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 40651 | sudo -iu user firefox lynxblog.net | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40652 | /snap/firefox/3358/usr/lib/firefox/firefox lynxblog.net | /snap/firefox/3358/usr/lib/firefox/firefox | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 40653 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40664 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40671 | /snap/snapd/20290/usr/lib/snapd/snap-confine --base core22 snap.firefox.firefox /usr/lib/snapd/snap-exec firefox lynxblog.net | /snap/snapd/20290/usr/lib/snapd/snap-confine | — | firefox |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40672 | dumpe2fs -h /dev/sda3 | /usr/sbin/dumpe2fs | — | udisksd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40673 | snap-update-ns --from-snap-confine firefox | /snap/snapd/20290/usr/lib/snapd/snap-update-ns | — | firefox |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40679 | dumpe2fs -h /dev/sda3 | /usr/sbin/dumpe2fs | — | udisksd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
49
DNS requests
72
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.48:80 | http://connectivity-check.ubuntu.com/ | US | — | — | whitelisted |
40652 | firefox | GET | — | 46.173.214.156:80 | http://lynxblog.net/ | RU | — | — | unknown |
40652 | firefox | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
40652 | firefox | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
40652 | firefox | POST | 200 | 2.22.231.8:80 | http://r11.o.lencr.org/ | NL | binary | 504 b | whitelisted |
40652 | firefox | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/FIY | US | binary | 471 b | whitelisted |
40652 | firefox | POST | 200 | 2.22.231.8:80 | http://r11.o.lencr.org/ | NL | binary | 504 b | whitelisted |
40652 | firefox | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/we2 | US | binary | 279 b | whitelisted |
40652 | firefox | POST | 200 | 2.22.231.13:80 | http://r10.o.lencr.org/ | NL | binary | 504 b | whitelisted |
40652 | firefox | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/3H4 | US | binary | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.48:80 | — | Canonical Group Limited | GB | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.48:80 | — | Canonical Group Limited | US | unknown |
40652 | firefox | 46.173.214.156:80 | lynxblog.net | Garant-Park-Internet LLC | RU | unknown |
40652 | firefox | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
40652 | firefox | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
40652 | firefox | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
40652 | firefox | 2.22.231.8:80 | r11.o.lencr.org | Akamai International B.V. | NL | whitelisted |
40652 | firefox | 142.250.185.138:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
40652 | firefox | 142.250.186.99:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
lynxblog.net |
| unknown |
detectportal.firefox.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40652 | firefox | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 5 |
2 ETPRO signatures available at the full report